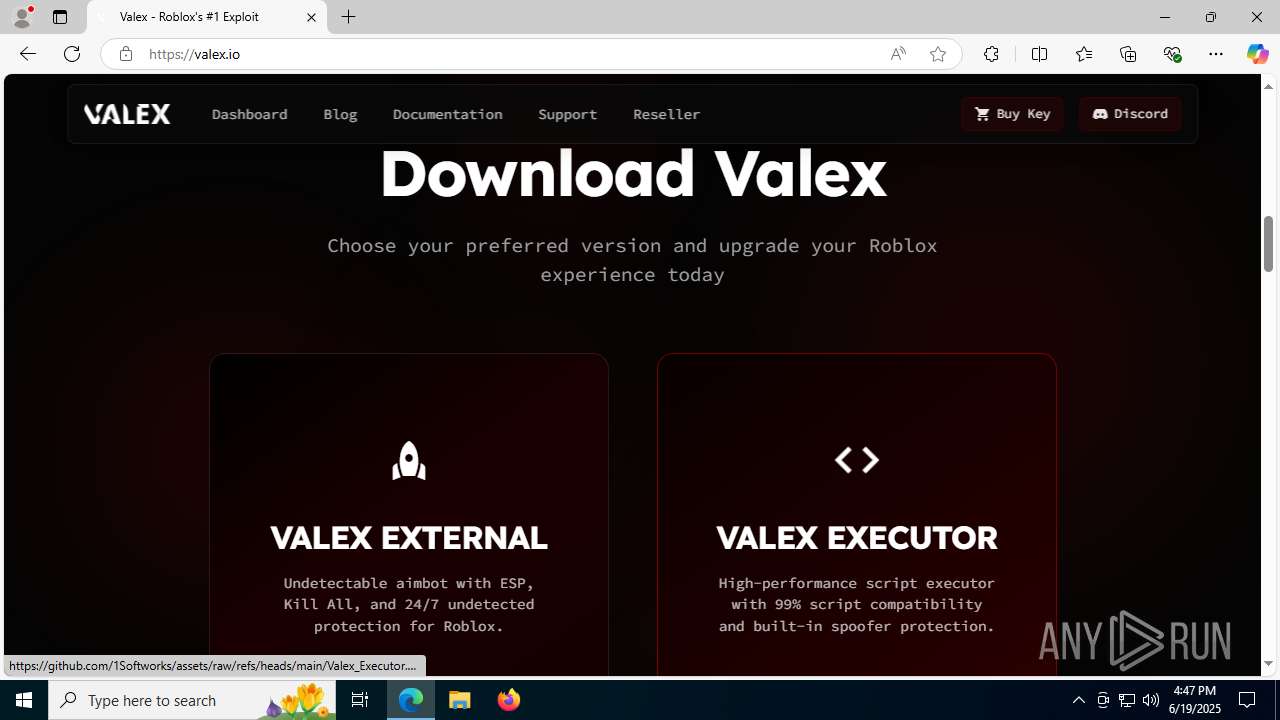
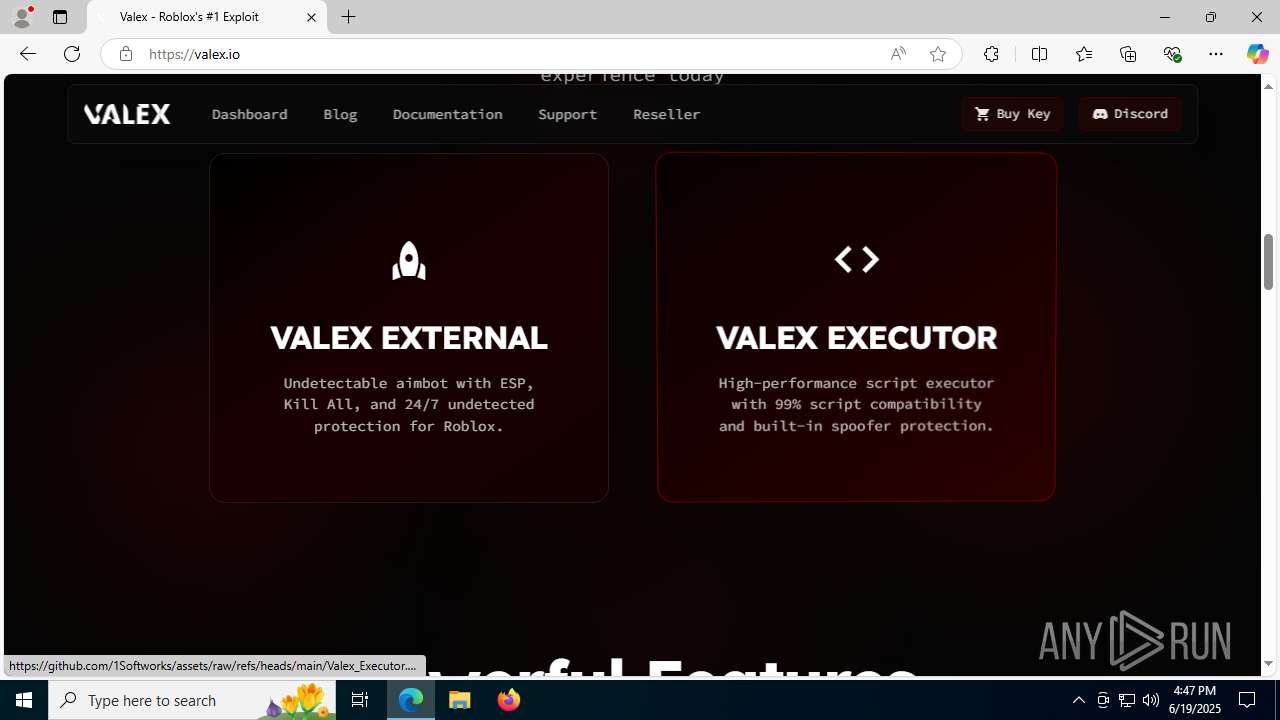
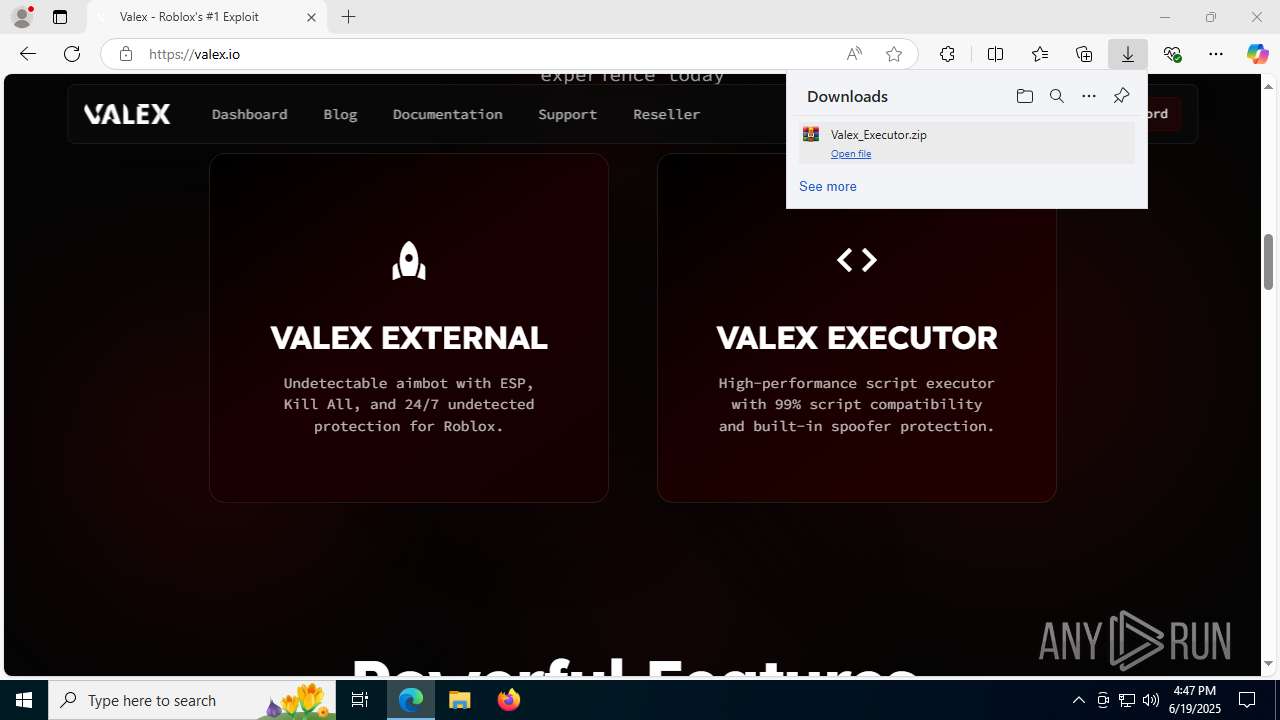
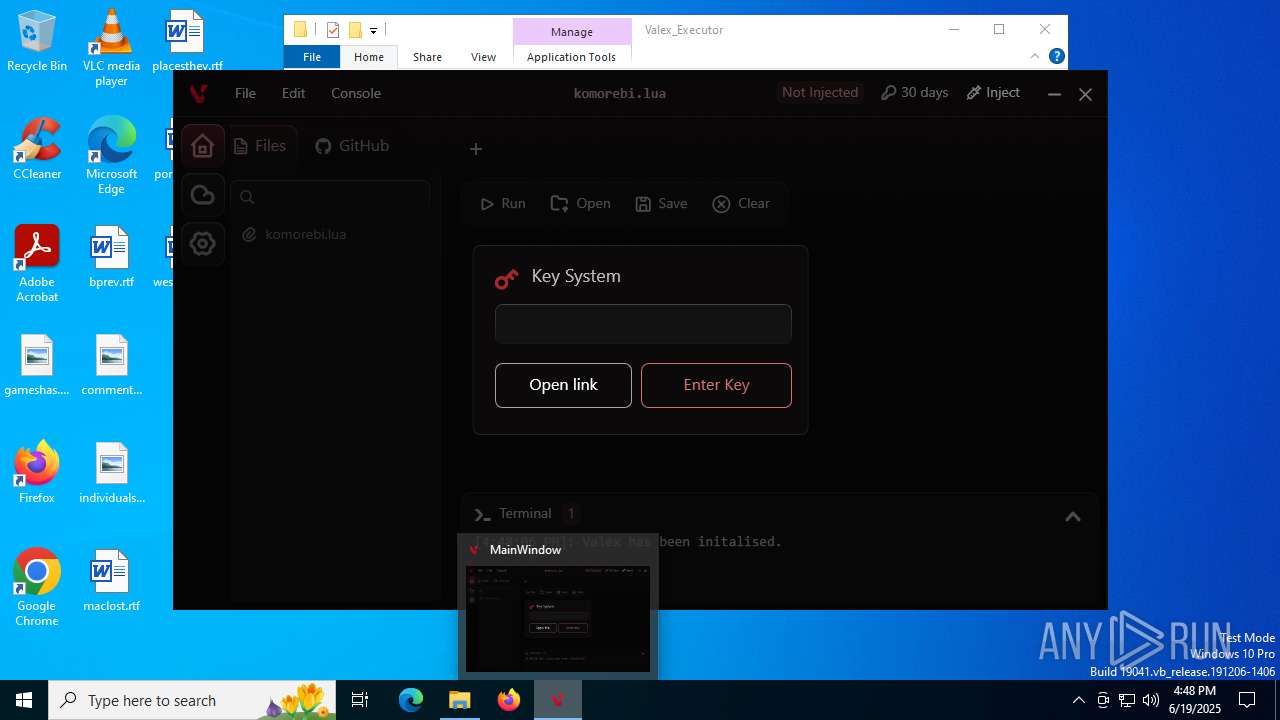
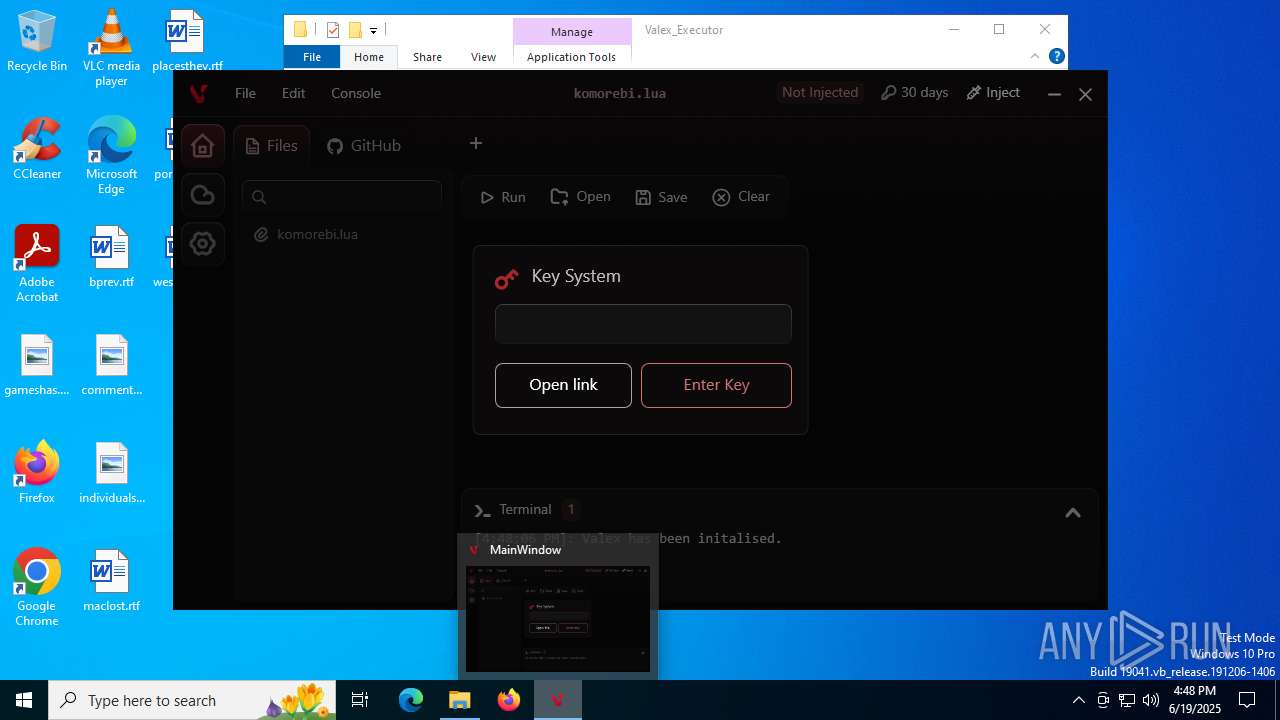
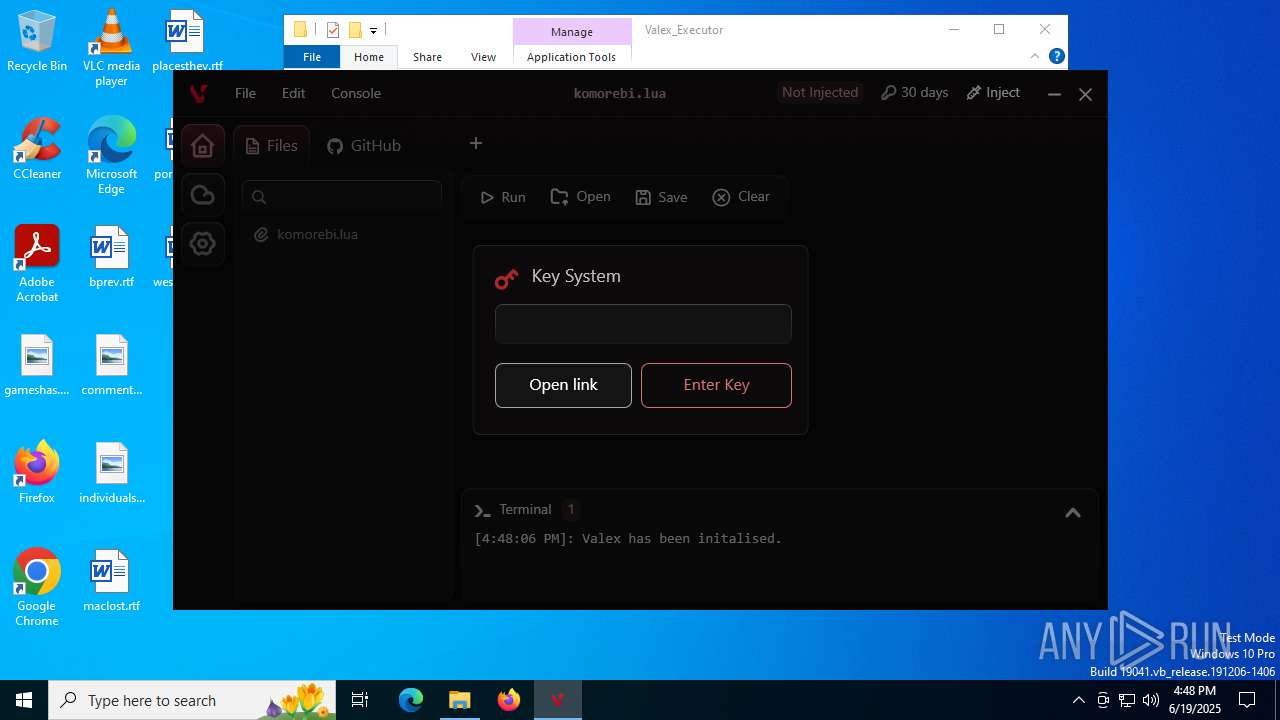
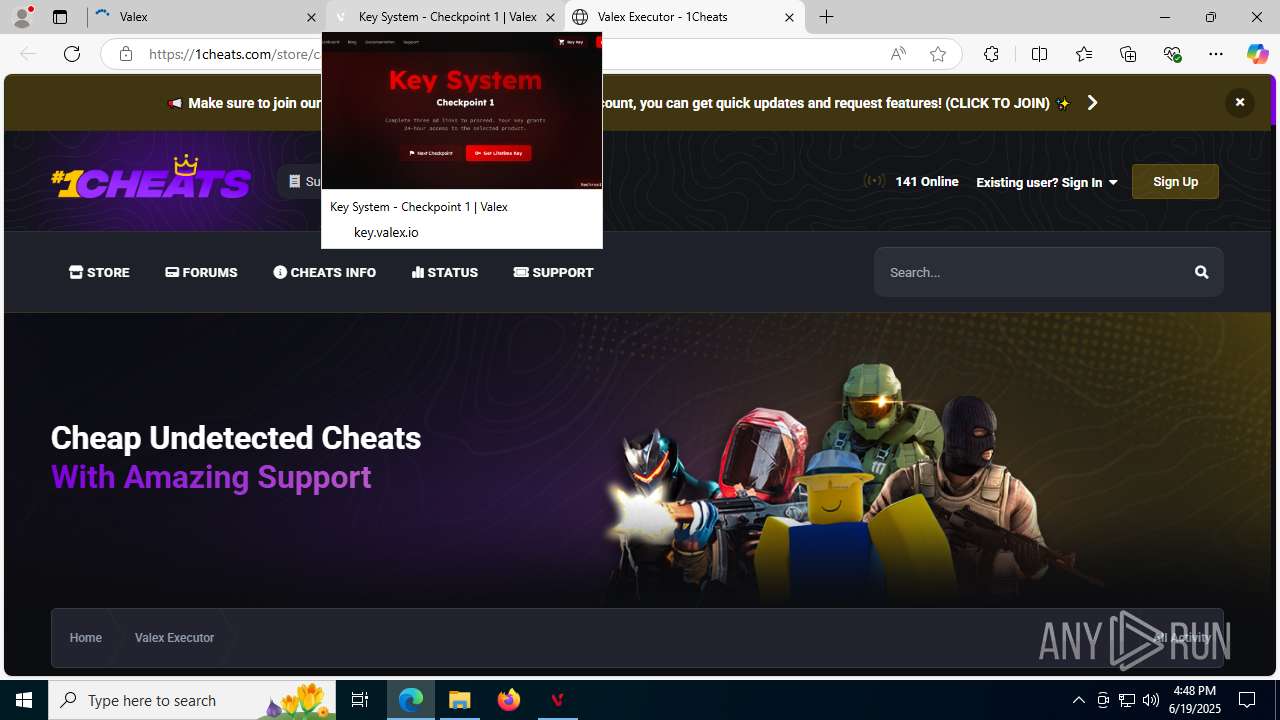
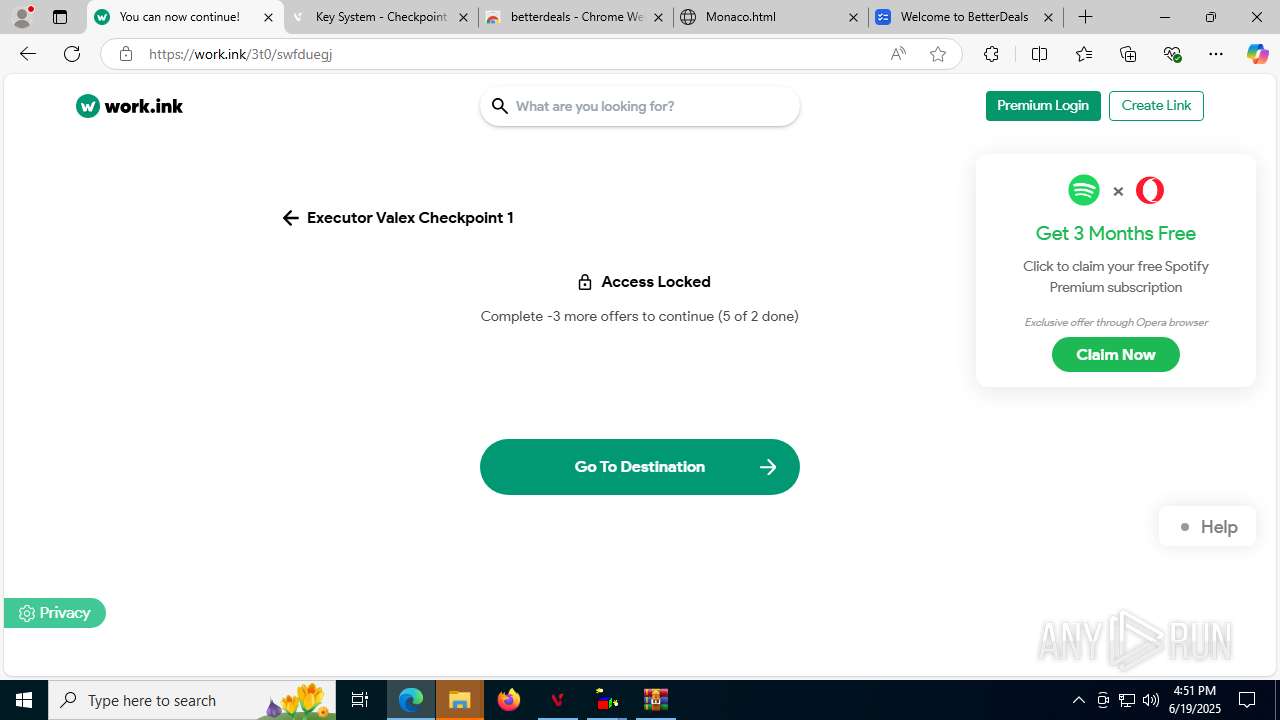
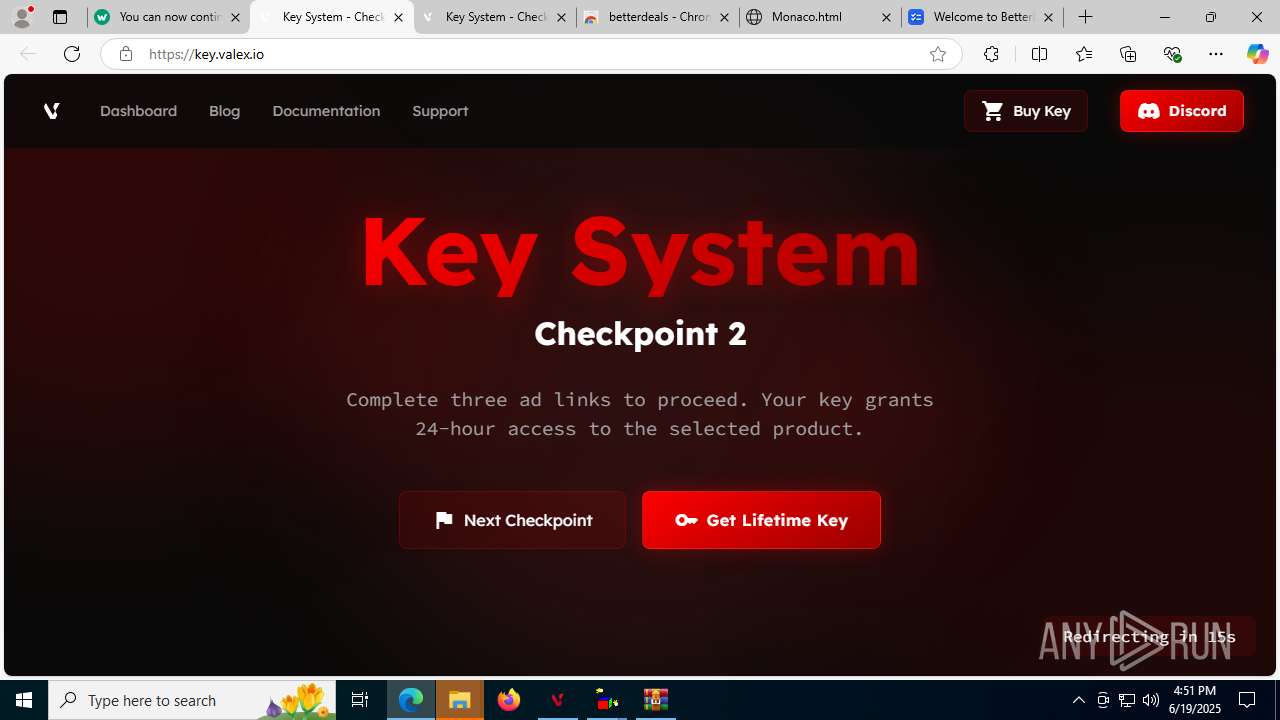
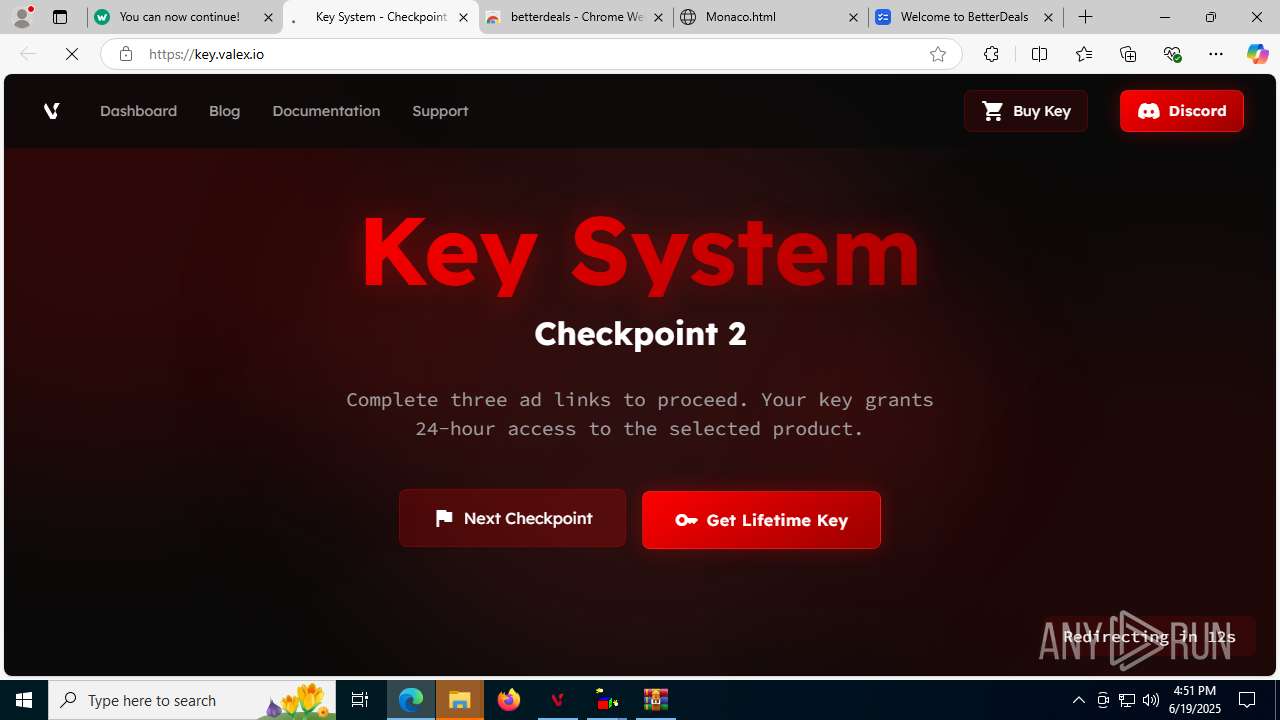
| URL: | valex.io |
| Full analysis: | https://app.any.run/tasks/dba06283-429f-4b52-b8a8-5fb907f82b3e |
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2025, 16:47:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 74BE0E6CEF72D2B0D11BBA7C79429DDF |
| SHA1: | 9D956C0513742535D9E95529E31DE32FC73C3597 |
| SHA256: | 18A1868143323D6E5C12CF796FF5BC62CC94BEB725FCA80CA1D21683E4B4A1F4 |
| SSDEEP: | 3:0un:0u |
MALICIOUS
No malicious indicators.SUSPICIOUS
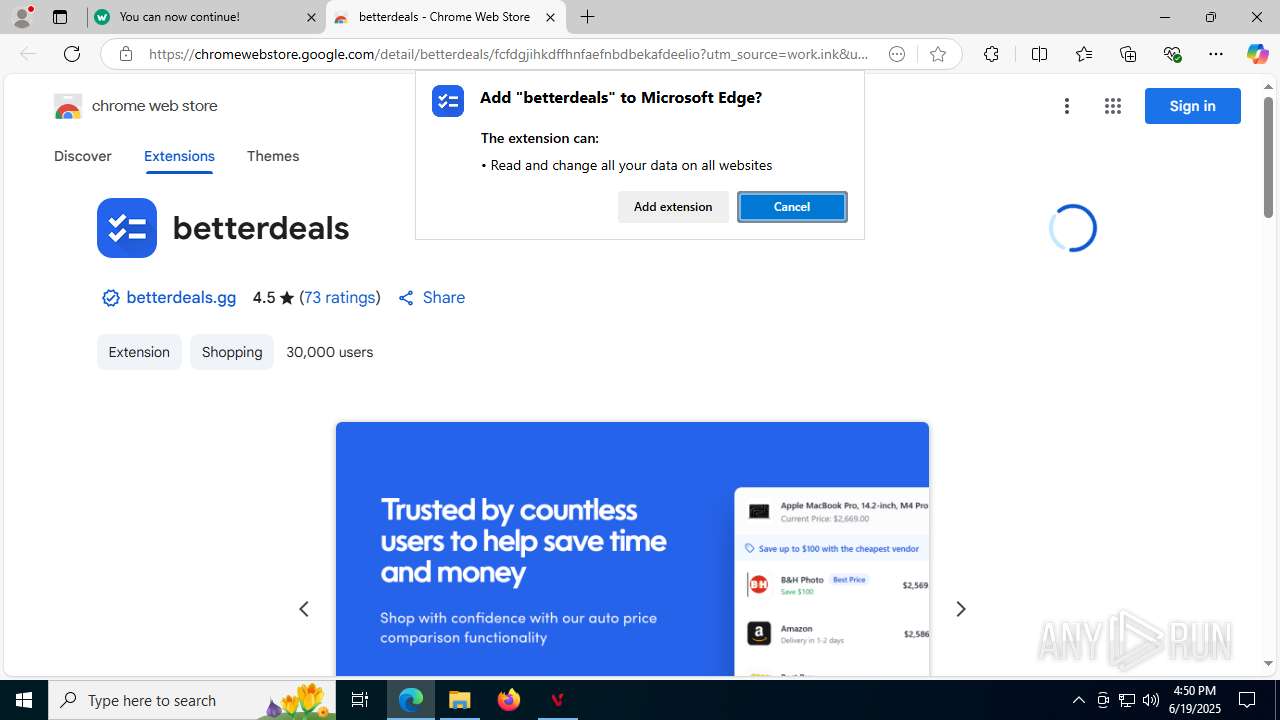
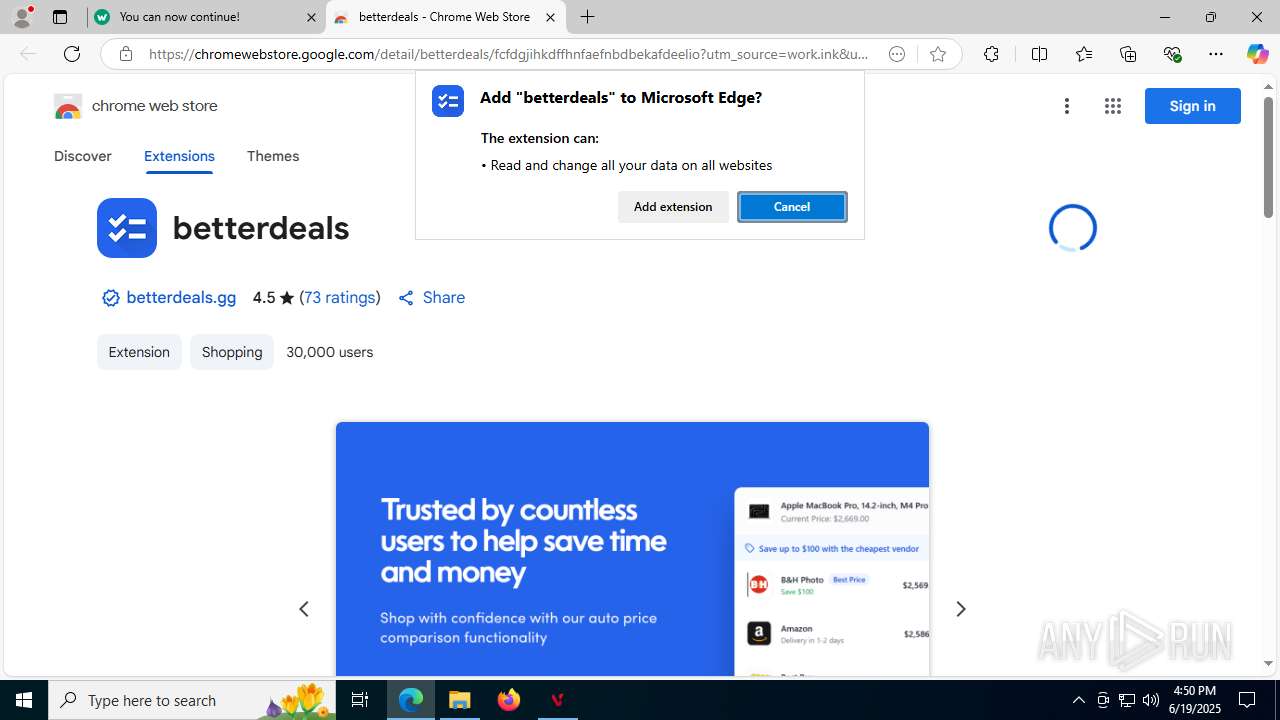
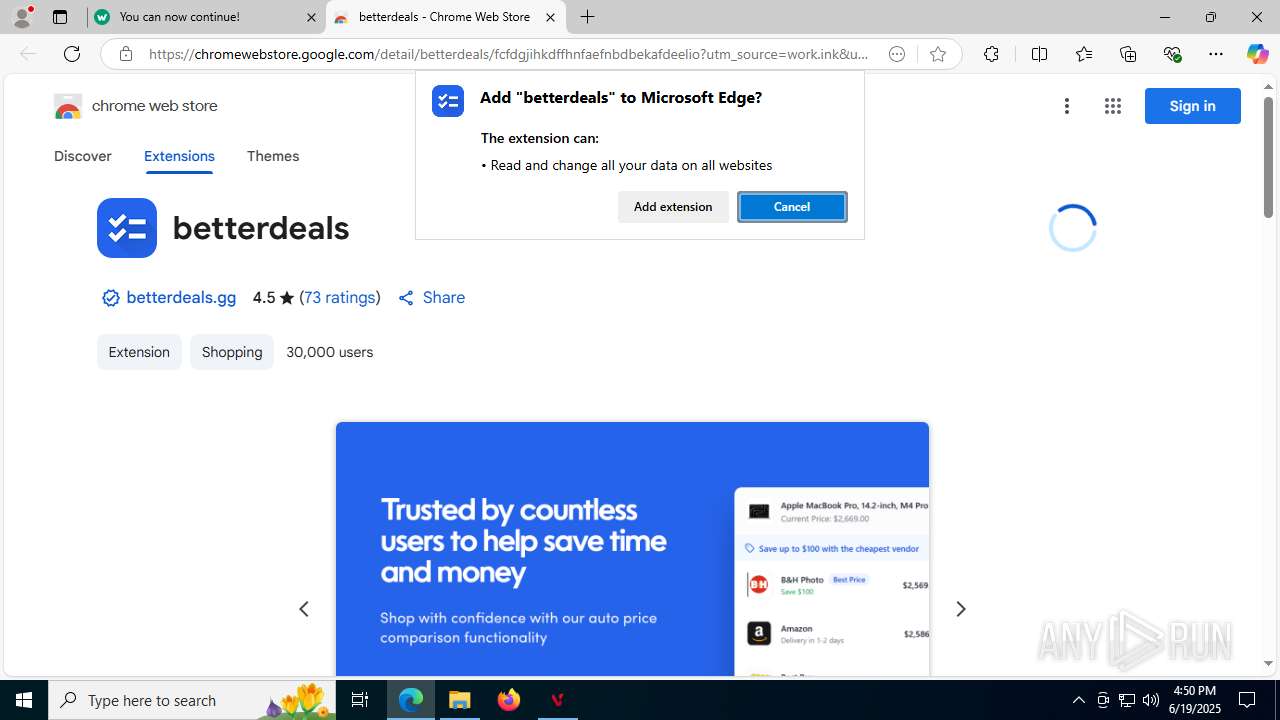
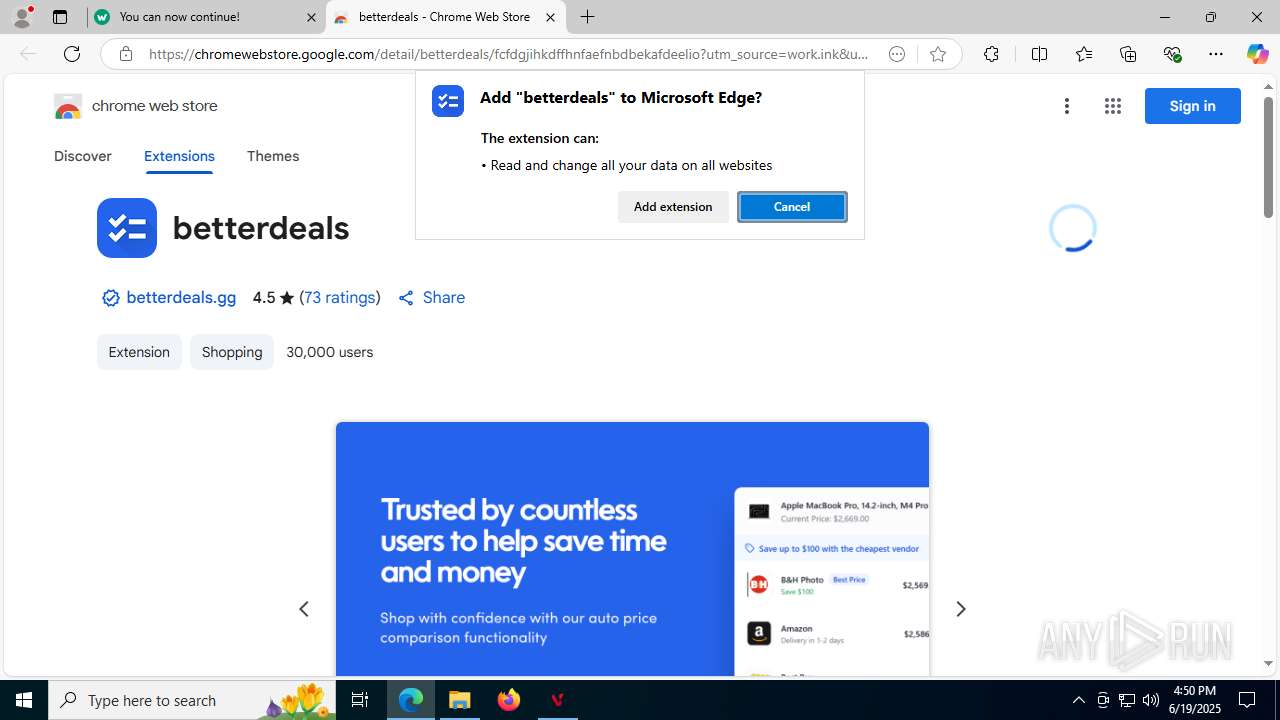
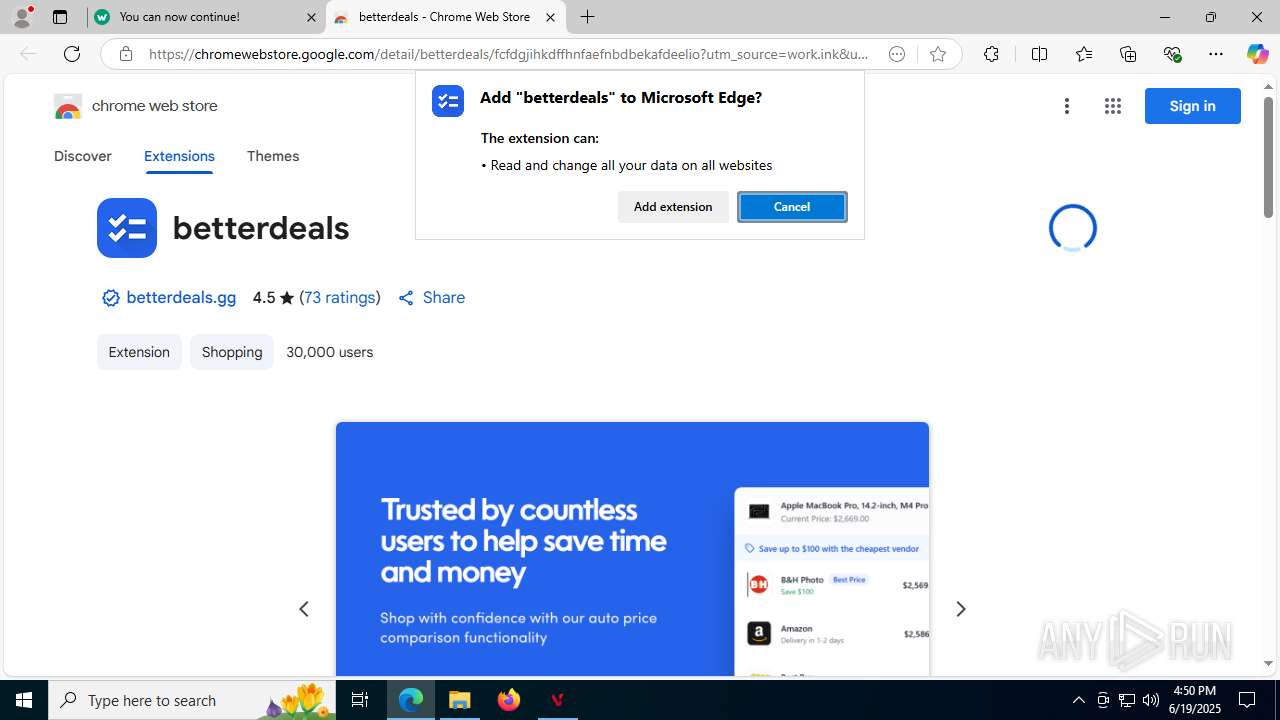
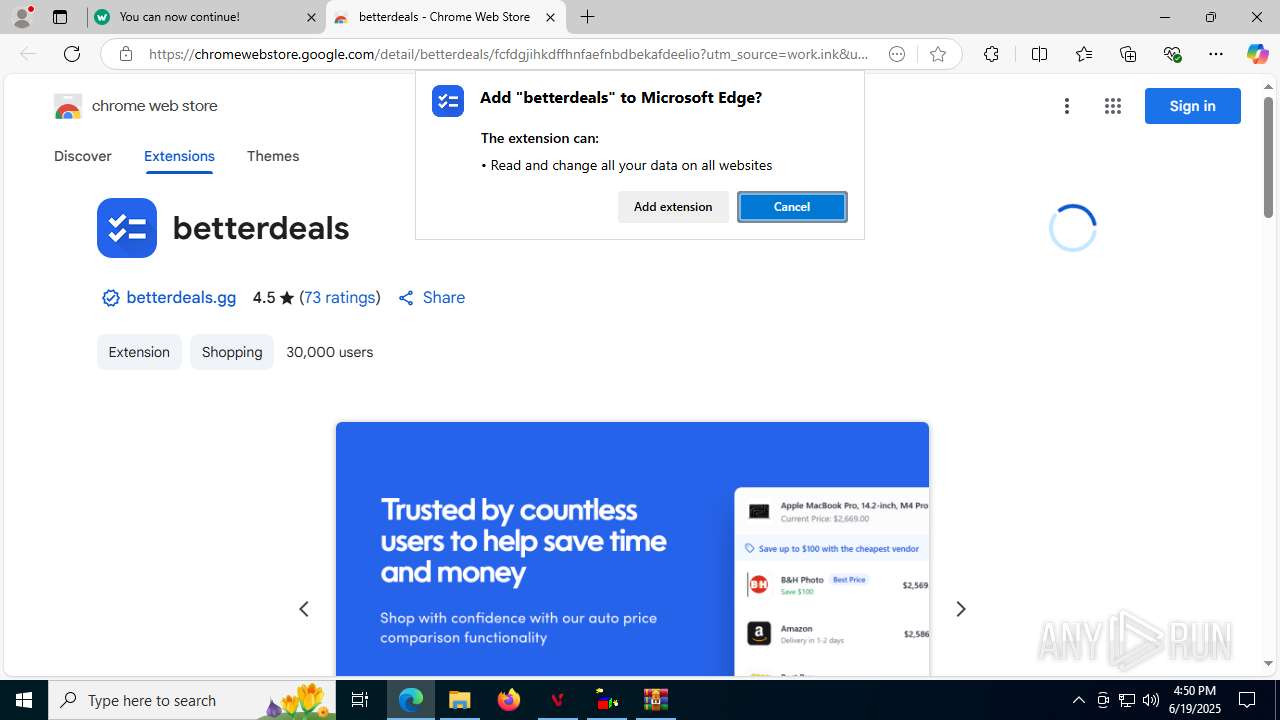
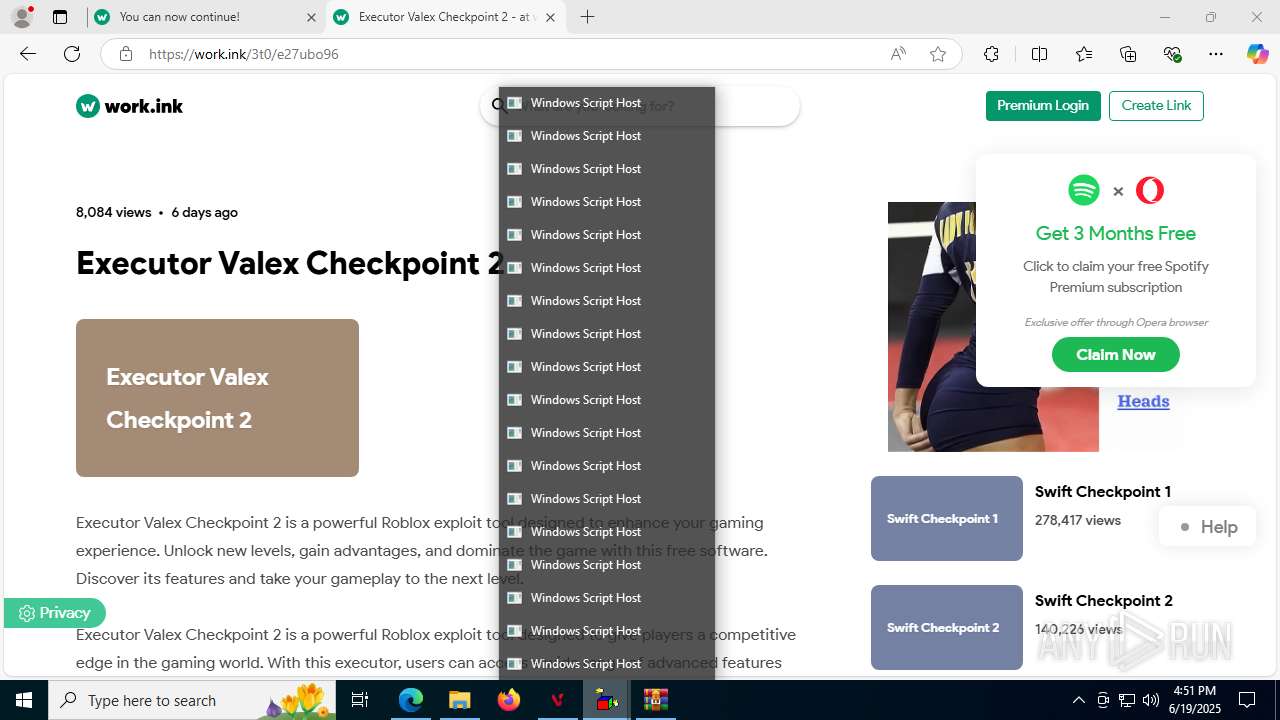
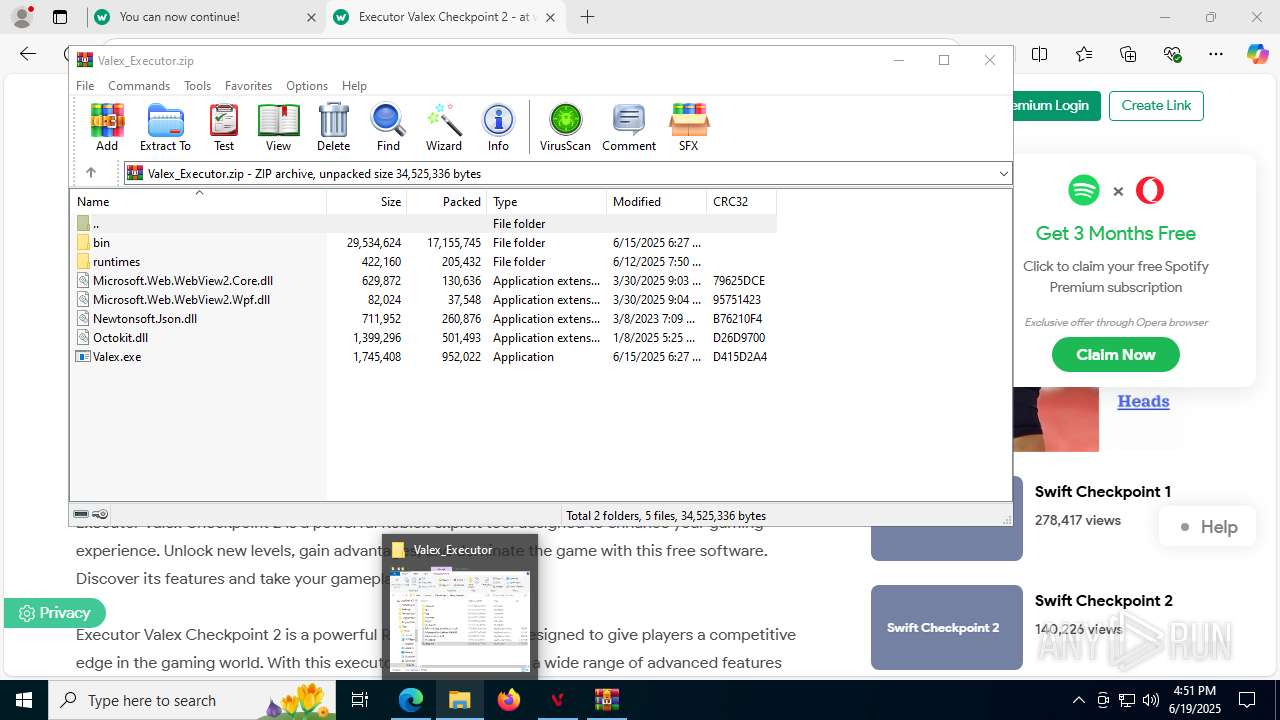
Process drops legitimate windows executable
- msedge.exe (PID: 1192)
- msedge.exe (PID: 3752)
- WinRAR.exe (PID: 7304)
Reads security settings of Internet Explorer
- Valex.exe (PID: 1812)
- ShellExperienceHost.exe (PID: 7348)
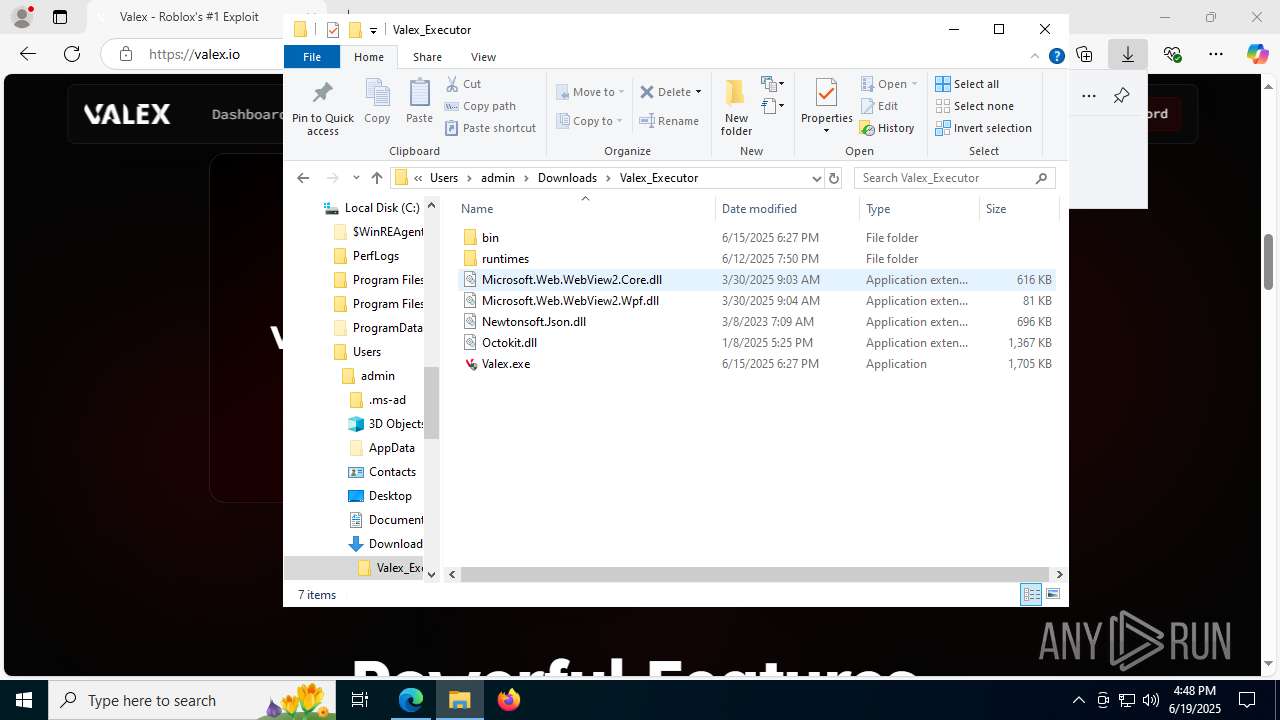
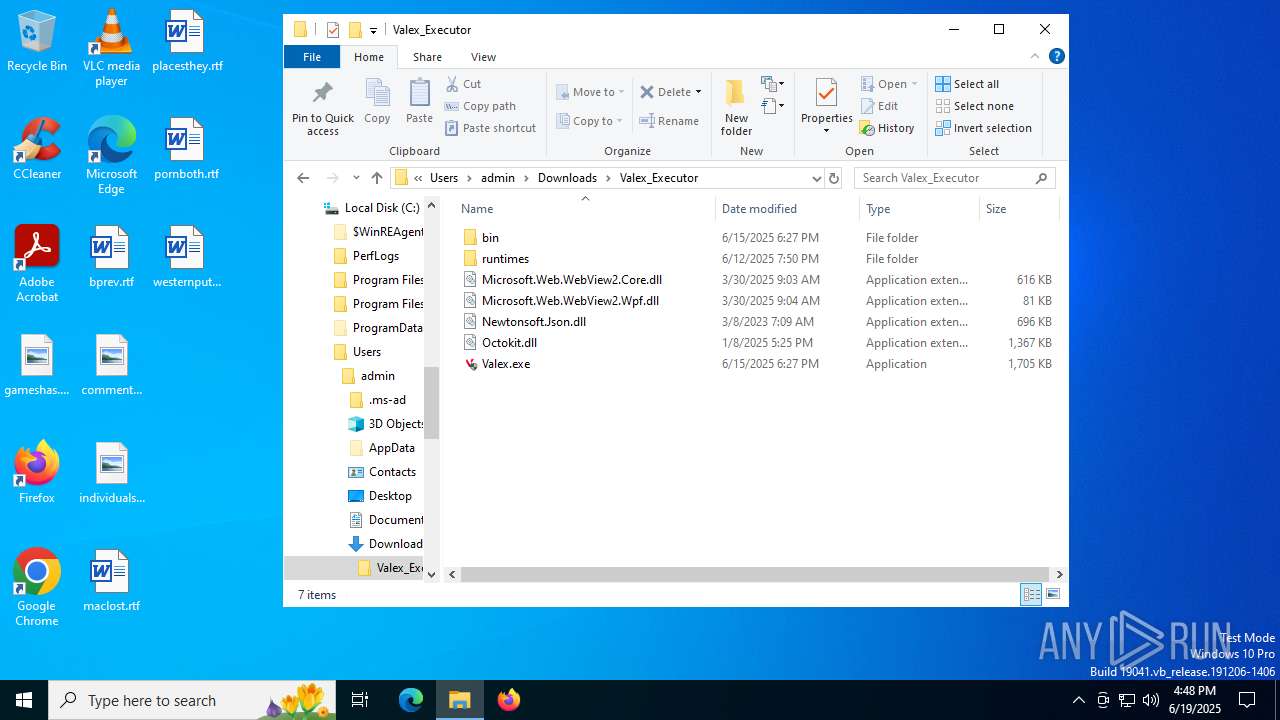
Executes application which crashes
- valex.exe (PID: 8960)
- Valex.exe (PID: 9104)
INFO
Reads Environment values
- identity_helper.exe (PID: 7744)
- identity_helper.exe (PID: 6176)
Checks supported languages
- identity_helper.exe (PID: 7744)
- identity_helper.exe (PID: 6176)
- Valex.exe (PID: 1812)
- valex.exe (PID: 8960)
- Valex.exe (PID: 9104)
- ShellExperienceHost.exe (PID: 7348)
Reads the computer name
- identity_helper.exe (PID: 7744)
- identity_helper.exe (PID: 6176)
- Valex.exe (PID: 1812)
- valex.exe (PID: 8960)
- Valex.exe (PID: 9104)
- ShellExperienceHost.exe (PID: 7348)
The sample compiled with english language support
- msedge.exe (PID: 1192)
- msedge.exe (PID: 3752)
- WinRAR.exe (PID: 7304)
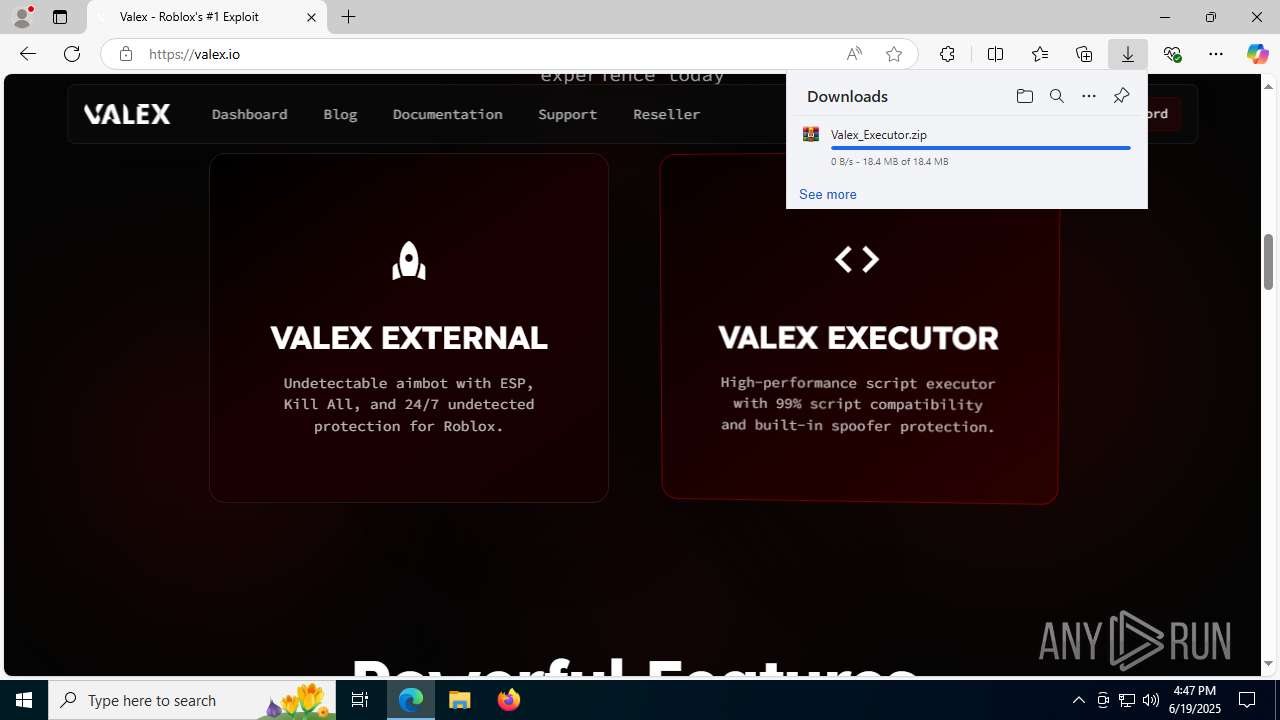
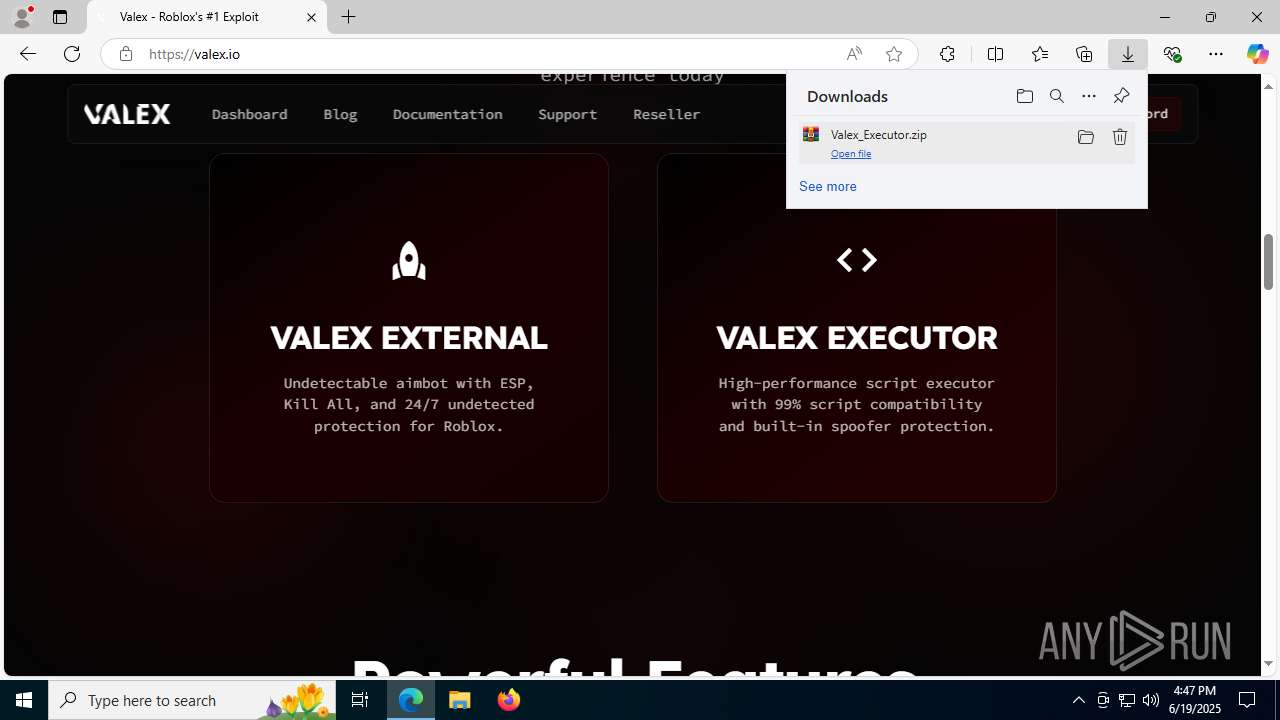
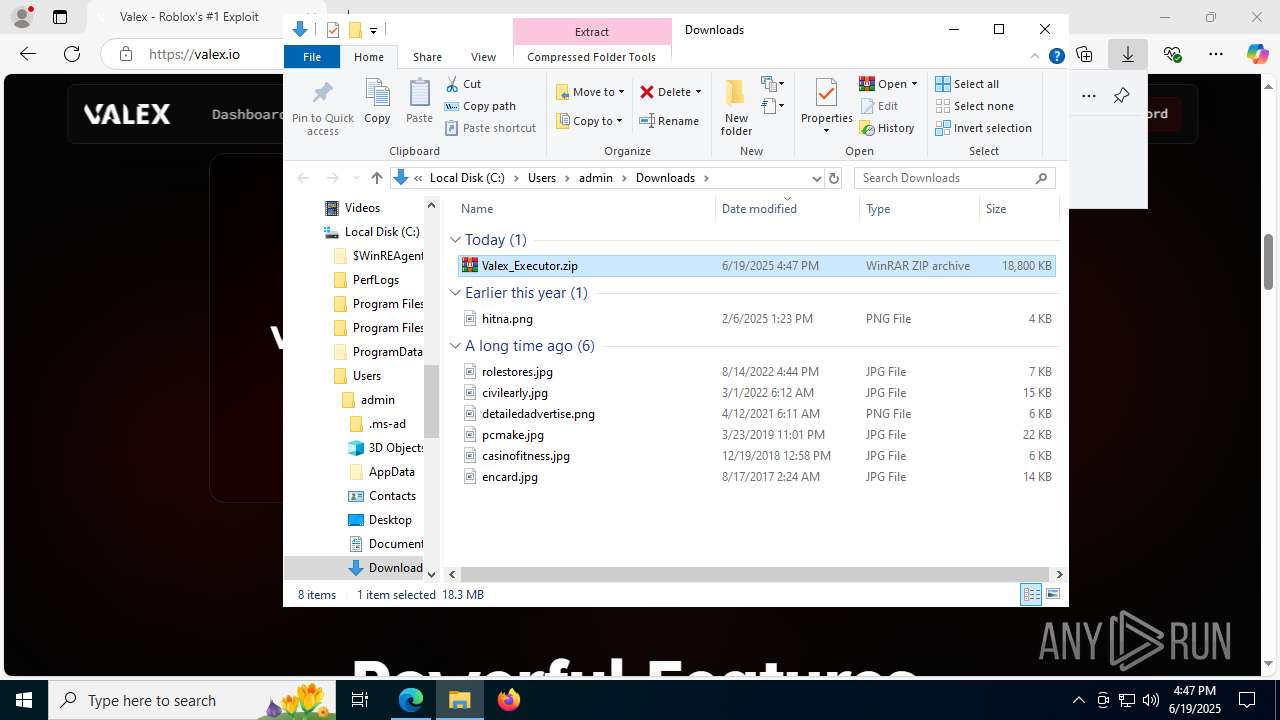
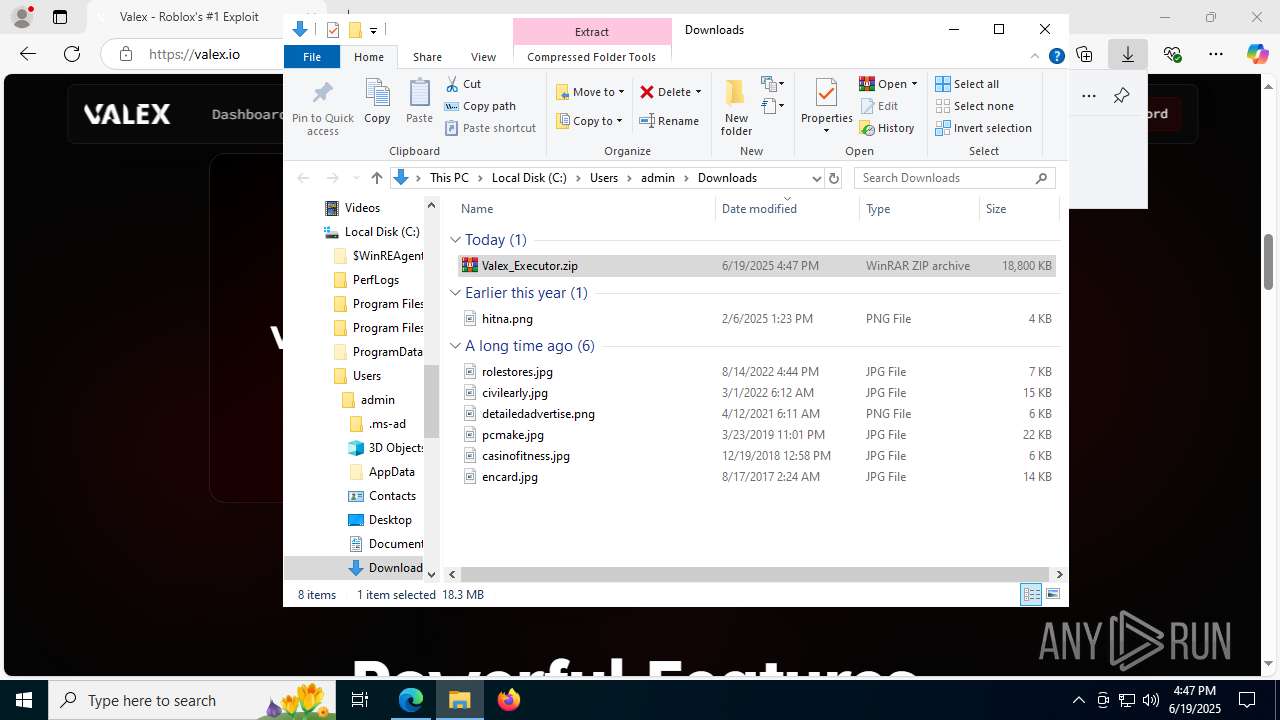
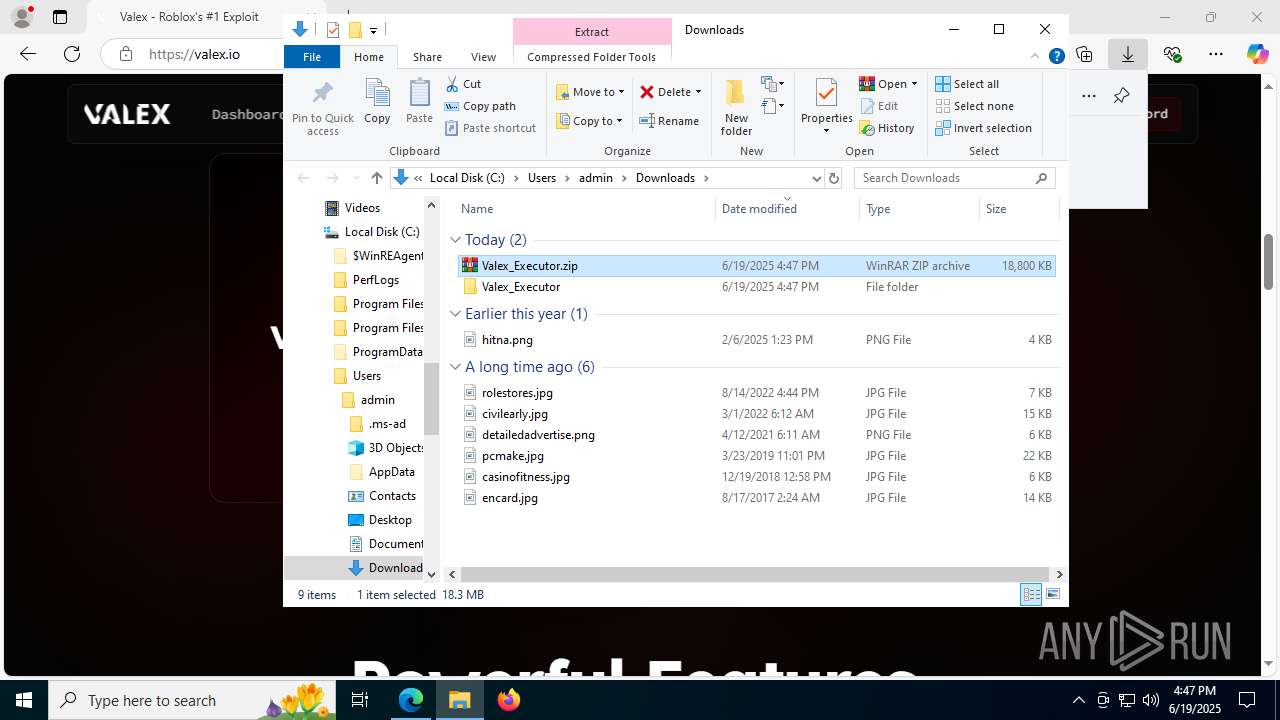
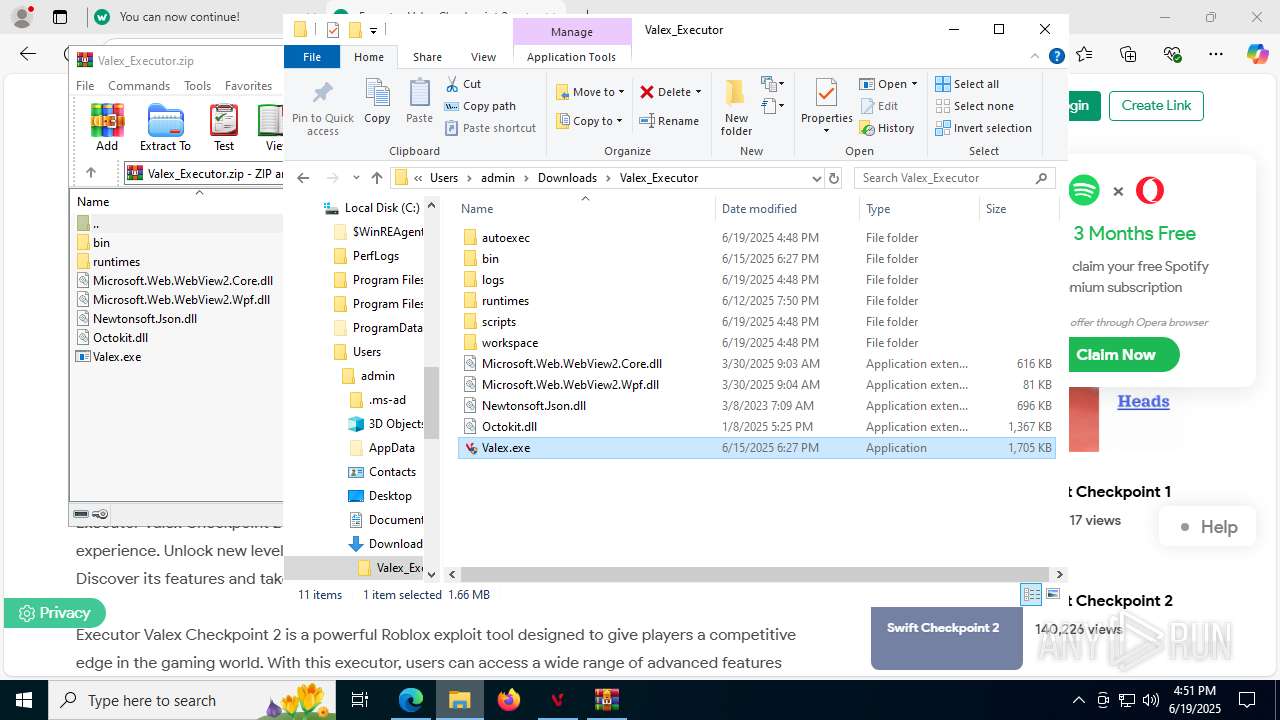
Launching a file from the Downloads directory
- msedge.exe (PID: 3752)
Application launched itself
- msedge.exe (PID: 3752)
- msedge.exe (PID: 6220)
- msedge.exe (PID: 7892)
- msedge.exe (PID: 7500)
- msedge.exe (PID: 7640)
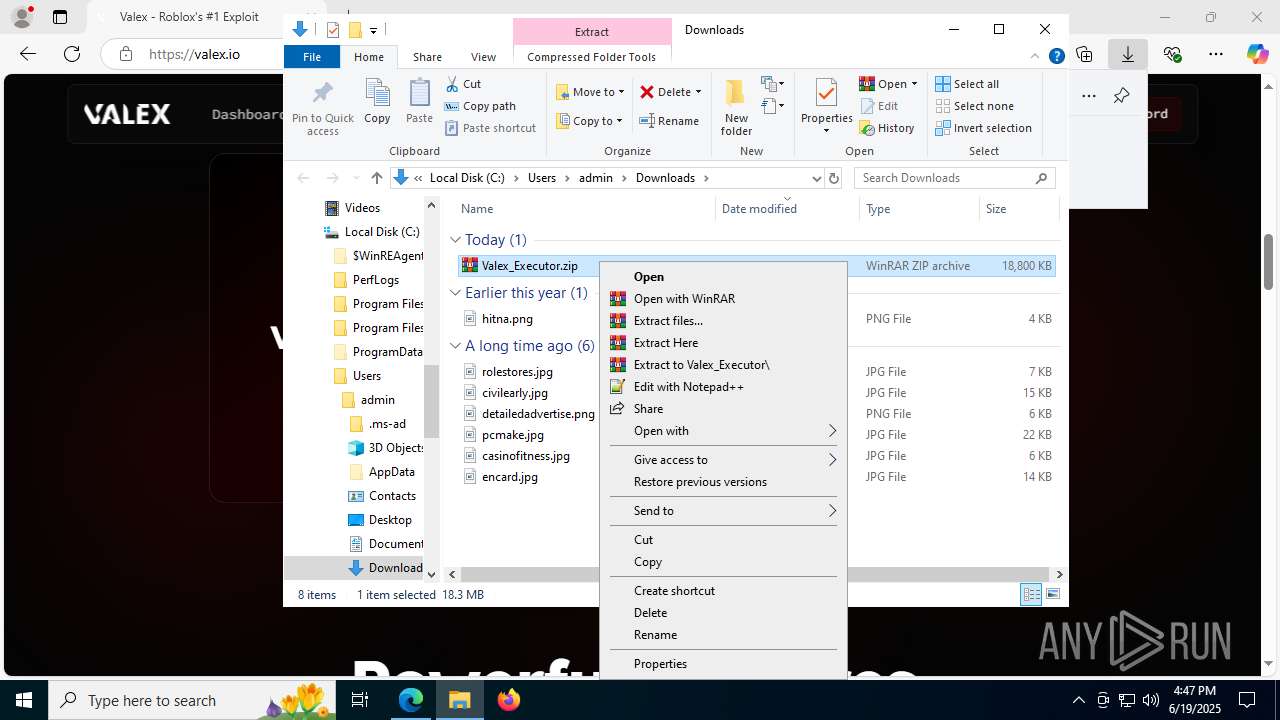
Manual execution by a user
- WinRAR.exe (PID: 7304)
- Valex.exe (PID: 1812)
- Valex.exe (PID: 8172)
- WinRAR.exe (PID: 4664)
- wscript.exe (PID: 3196)
- wscript.exe (PID: 4544)
- iexplore.exe (PID: 7380)
- wscript.exe (PID: 3972)
- wscript.exe (PID: 8376)
- wscript.exe (PID: 6772)
- wscript.exe (PID: 4844)
- wscript.exe (PID: 4112)
- wscript.exe (PID: 420)
- wscript.exe (PID: 8240)
- wscript.exe (PID: 5960)
- wscript.exe (PID: 7184)
- wscript.exe (PID: 1652)
- wscript.exe (PID: 8196)
- wscript.exe (PID: 2040)
- Valex.exe (PID: 8932)
- valex.exe (PID: 8960)
- wscript.exe (PID: 9056)
- wscript.exe (PID: 3400)
- wscript.exe (PID: 7104)
- wscript.exe (PID: 8772)
- Valex.exe (PID: 9104)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7304)
Checks proxy server information
- Valex.exe (PID: 1812)
- slui.exe (PID: 7500)
- Valex.exe (PID: 9104)
- WerFault.exe (PID: 5628)
- WerFault.exe (PID: 8224)
Reads the software policy settings
- slui.exe (PID: 7500)
- Valex.exe (PID: 1812)
- Valex.exe (PID: 9104)
- WerFault.exe (PID: 5628)
- WerFault.exe (PID: 8224)
JScript runtime error (SCRIPT)
- wscript.exe (PID: 8240)
- wscript.exe (PID: 3972)
- wscript.exe (PID: 6772)
- wscript.exe (PID: 4112)
- wscript.exe (PID: 420)
- wscript.exe (PID: 3196)
- wscript.exe (PID: 4544)
- wscript.exe (PID: 8376)
- wscript.exe (PID: 7104)
- wscript.exe (PID: 1652)
- wscript.exe (PID: 8196)
- wscript.exe (PID: 2040)
- wscript.exe (PID: 4844)
- wscript.exe (PID: 8772)
Disables trace logs
- Valex.exe (PID: 1812)
- Valex.exe (PID: 9104)
Reads the machine GUID from the registry
- Valex.exe (PID: 1812)
- Valex.exe (PID: 9104)
Creates files or folders in the user directory
- WerFault.exe (PID: 5628)
- WerFault.exe (PID: 8224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
282
Monitored processes
128
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Downloads\Valex_Executor\bin\Monaco\vs\editor\editor.main.nls.zh-tw.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3600,i,16241732655481489015,4281333439439036188,262144 --variations-seed-version --mojo-platform-channel-handle=3660 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=20 --always-read-main-dll --field-trial-handle=6832,i,16241732655481489015,4281333439439036188,262144 --variations-seed-version --mojo-platform-channel-handle=4508 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1128 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=26 --always-read-main-dll --field-trial-handle=5716,i,4821395044288649263,11572394873399385619,262144 --variations-seed-version --mojo-platform-channel-handle=4940 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2248,i,16241732655481489015,4281333439439036188,262144 --variations-seed-version --mojo-platform-channel-handle=2508 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2744,i,16241732655481489015,4281333439439036188,262144 --variations-seed-version --mojo-platform-channel-handle=2760 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --pdf-upsell-enabled --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=29 --always-read-main-dll --field-trial-handle=7452,i,4821395044288649263,11572394873399385619,262144 --variations-seed-version --mojo-platform-channel-handle=6636 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1604 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc43a4f208,0x7ffc43a4f214,0x7ffc43a4f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1652 | "C:\Windows\System32\WScript.exe" C:\Users\admin\Downloads\Valex_Executor\bin\Monaco\vs\editor\editor.main.nls.js | C:\Windows\System32\wscript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1760 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6160,i,4821395044288649263,11572394873399385619,262144 --variations-seed-version --mojo-platform-channel-handle=6660 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
27 762
Read events
27 593
Write events
166
Delete events
3
Modification events
| (PID) Process: | (3752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3752) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E77B2CC985962F00 | |||
| (PID) Process: | (3752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262942 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {82A35E3C-5E8C-4A1F-A8C6-E6F2C3346888} | |||
| (PID) Process: | (3752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262942 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {B5EEDA9B-01D4-47E4-8E83-AB5E8533C7C2} | |||
| (PID) Process: | (3752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262942 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D42876FF-37FE-4D5E-A272-EEDC6D2C1F79} | |||
| (PID) Process: | (3752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262942 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4F3736B9-4193-4A68-9C64-B65F404A46A3} | |||
| (PID) Process: | (3752) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262942 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {086C9EF5-CDE5-4E03-8A21-AE03C0FA10ED} | |||
Executable files
10
Suspicious files
636
Text files
479
Unknown types
123
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1766c8.TMP | — | |
MD5:— | SHA256:— | |||
| 3752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1766d8.TMP | — | |
MD5:— | SHA256:— | |||
| 3752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1766d8.TMP | — | |
MD5:— | SHA256:— | |||
| 3752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1766d8.TMP | — | |
MD5:— | SHA256:— | |||
| 3752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1766d8.TMP | — | |
MD5:— | SHA256:— | |||
| 3752 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
364
DNS requests
465
Threats
46
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7788 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 868 b | whitelisted |
7788 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
8480 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750791428&P2=404&P3=2&P4=ORL0aPiffx%2f0CV7uBIwO3wK3ek5R3yPqC4Bu8LeVCvFIk3C%2fdZMMbTsccI1EVNvv1ZkEKyLwKkuMLxpiIkSKag%3d%3d | US | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
8480 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750791428&P2=404&P3=2&P4=ORL0aPiffx%2f0CV7uBIwO3wK3ek5R3yPqC4Bu8LeVCvFIk3C%2fdZMMbTsccI1EVNvv1ZkEKyLwKkuMLxpiIkSKag%3d%3d | US | binary | 1.09 Kb | whitelisted |
8480 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1750791429&P2=404&P3=2&P4=FpdP%2bVe1lUrF5COiUwmDBcnjE0qmOO3awuQxWXKsr%2bh7aKRxw%2faOYfSUKTbVVpIfeE6lhyMDOlLClEiBTWd6Cg%3d%3d | US | compressed | 764 b | whitelisted |
8480 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1750791428&P2=404&P3=2&P4=ORL0aPiffx%2f0CV7uBIwO3wK3ek5R3yPqC4Bu8LeVCvFIk3C%2fdZMMbTsccI1EVNvv1ZkEKyLwKkuMLxpiIkSKag%3d%3d | US | compressed | 764 b | whitelisted |
8480 | svchost.exe | GET | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1750791429&P2=404&P3=2&P4=FpdP%2bVe1lUrF5COiUwmDBcnjE0qmOO3awuQxWXKsr%2bh7aKRxw%2faOYfSUKTbVVpIfeE6lhyMDOlLClEiBTWd6Cg%3d%3d | US | binary | 2.98 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5348 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1192 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1192 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
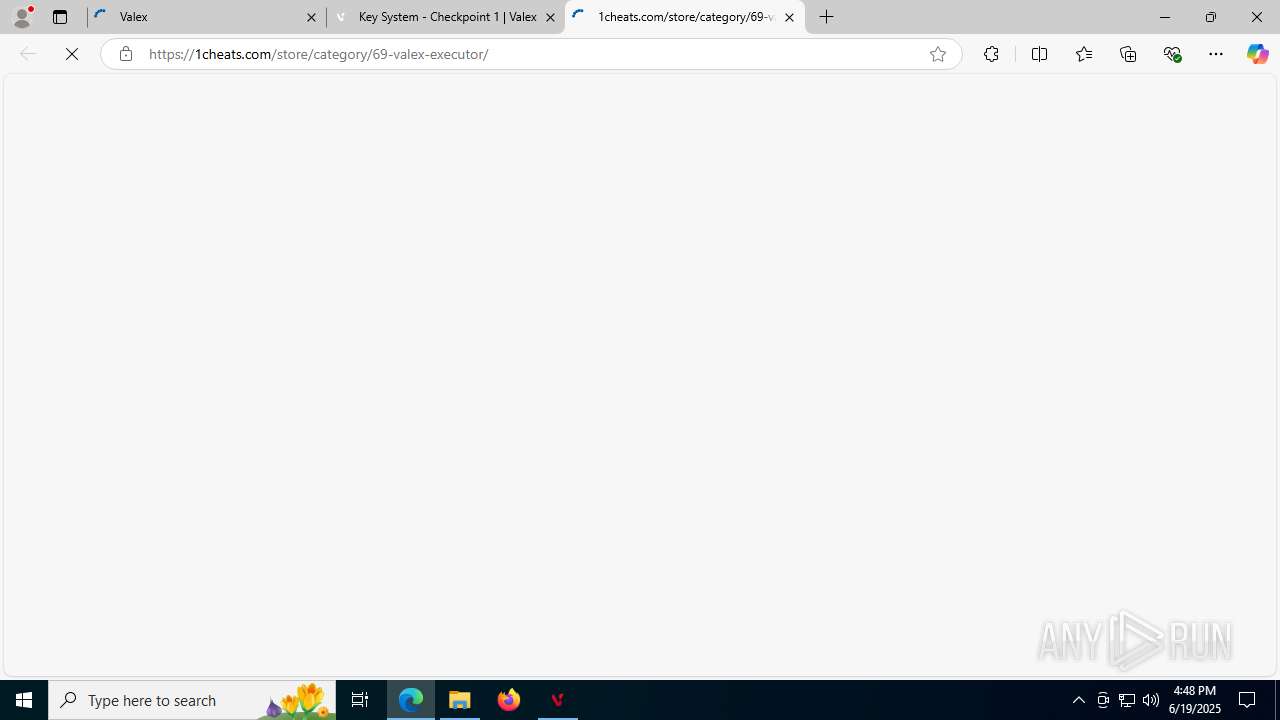
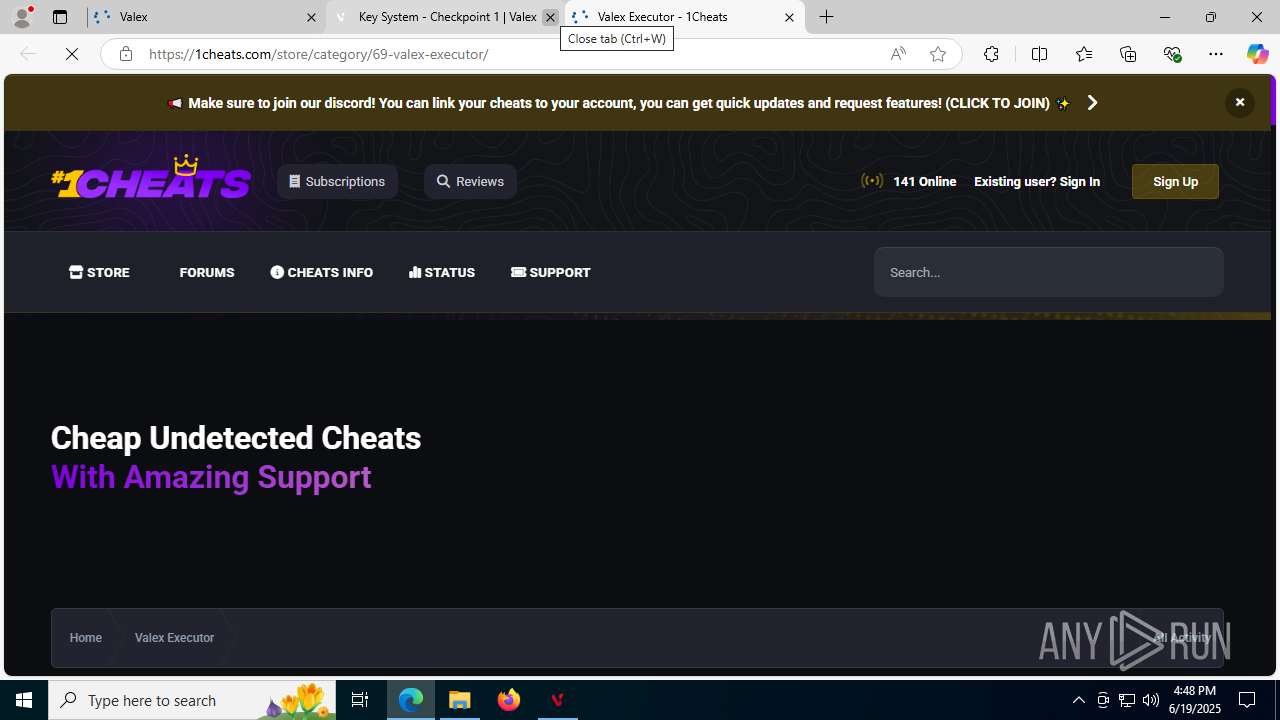
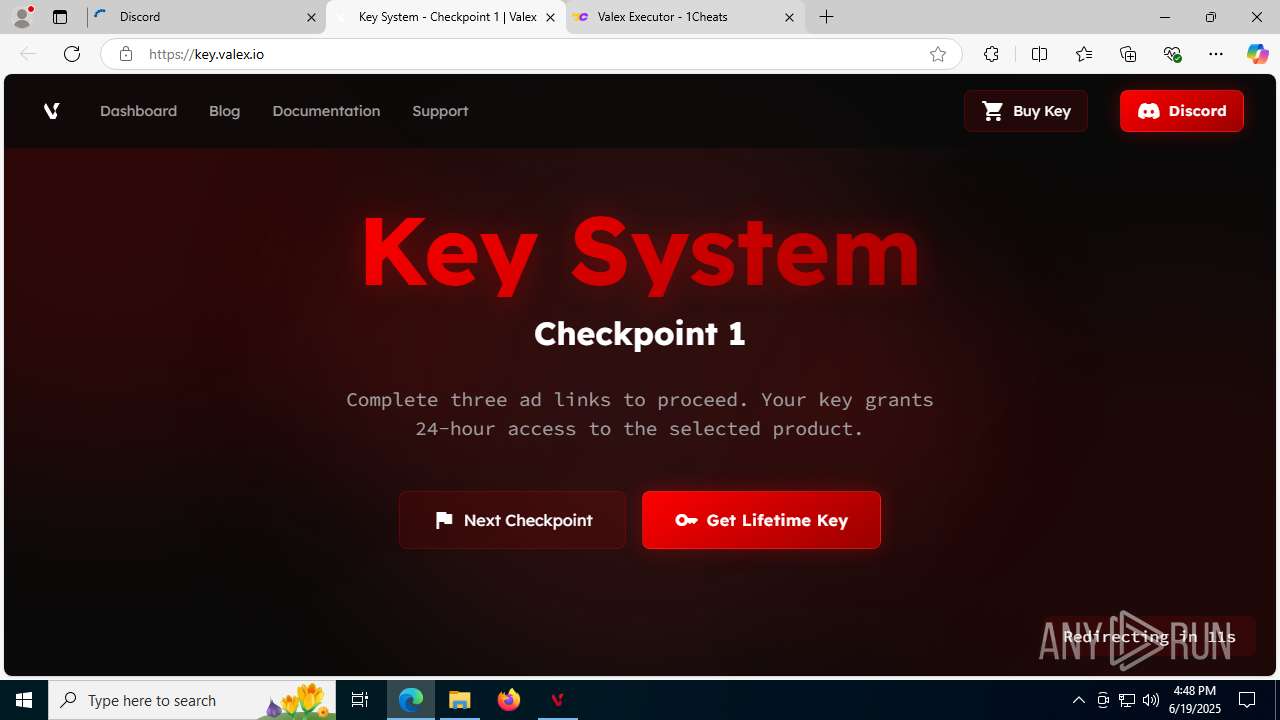
1192 | msedge.exe | 104.21.64.1:443 | valex.io | CLOUDFLARENET | — | unknown |
1192 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1192 | msedge.exe | 92.123.104.45:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
valex.io |
| unknown |
copilot.microsoft.com |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
www.bing.com |
| whitelisted |
challenges.cloudflare.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1192 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1192 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
1192 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
1192 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
1192 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1192 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1192 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
1192 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2200 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
1812 | Valex.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain (keyauth .win) in TLS SNI |