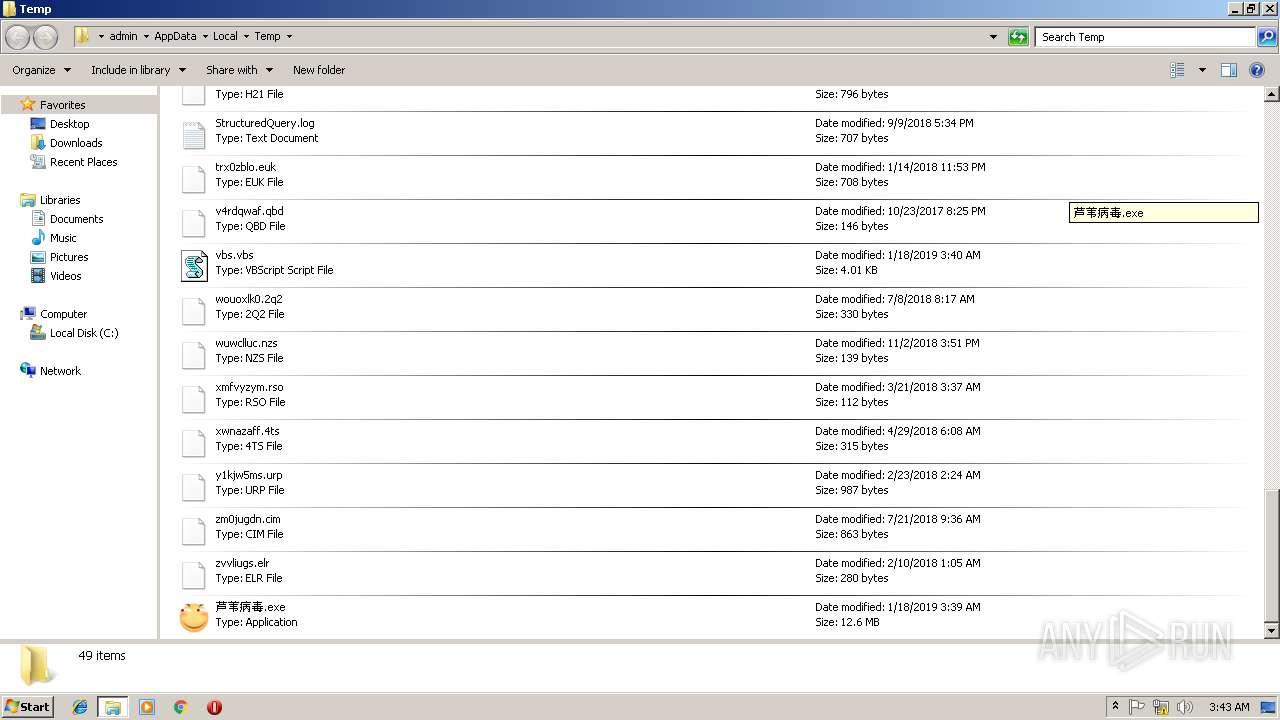
| File name: | 芦苇病毒.exe |
| Full analysis: | https://app.any.run/tasks/4a3573a3-6ded-4187-a1c2-7b82e70c548d |
| Verdict: | Malicious activity |
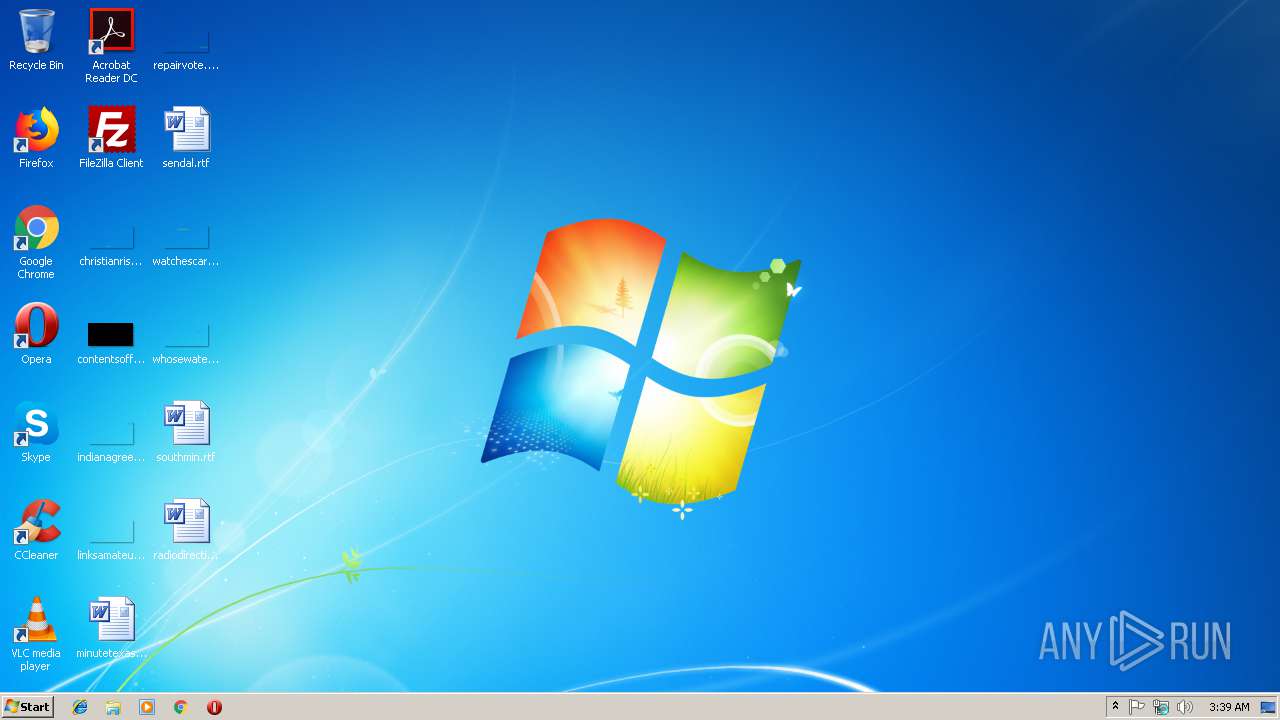
| Analysis date: | January 18, 2019, 03:39:10 |
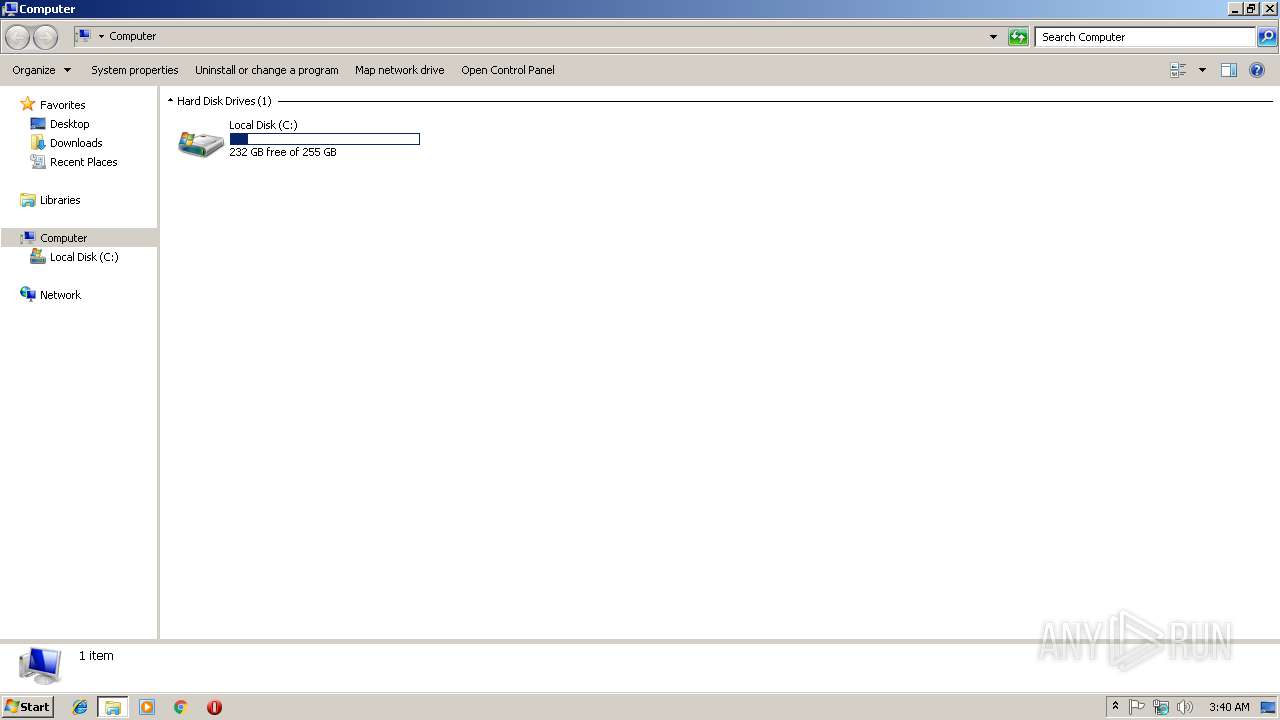
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C71091507F731C203B6C93BC91ADEDB6 |
| SHA1: | DCD5B64C10370556936115E1F149656CEA967ADE |
| SHA256: | 189BDD9D225537CDD803931A50EB308F6A952259FB74768879AA44DF7648E222 |
| SSDEEP: | 196608:B07lhv4+zaZK4DT81o3LAKmP0R/7pS2E5RV9BYb3mnSdK/zvwpyFl1v6psjLmE:G7zxzaZKt1o3IP0RsLRVk4fFl1v6pQF |
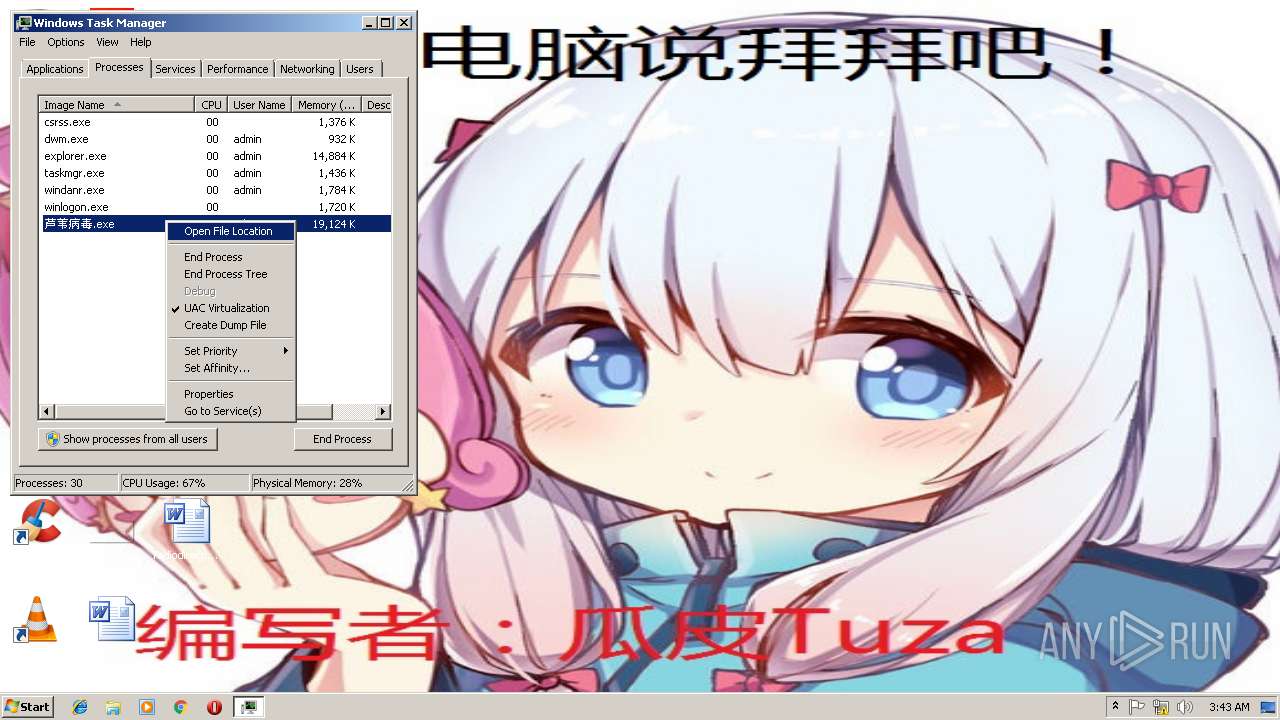
MALICIOUS
Loads dropped or rewritten executable
- 芦苇病毒.exe (PID: 3532)
Changes the autorun value in the registry
- 芦苇病毒.exe (PID: 3532)
SUSPICIOUS
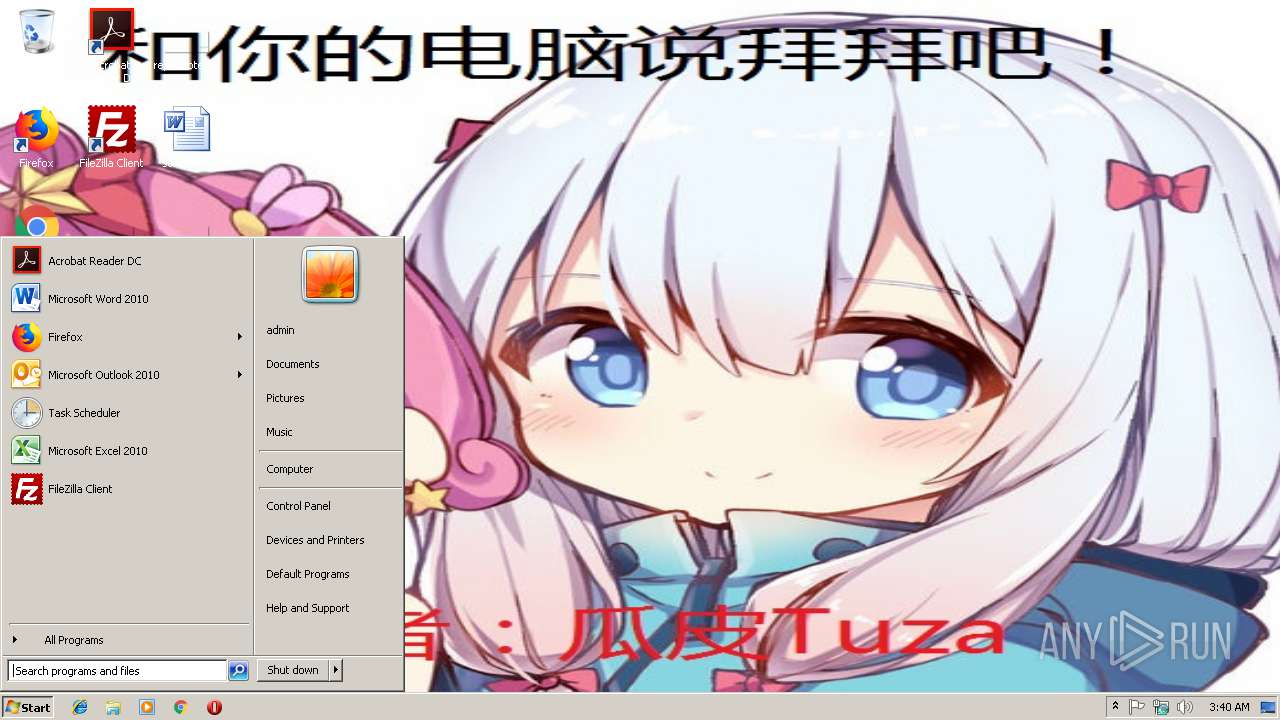
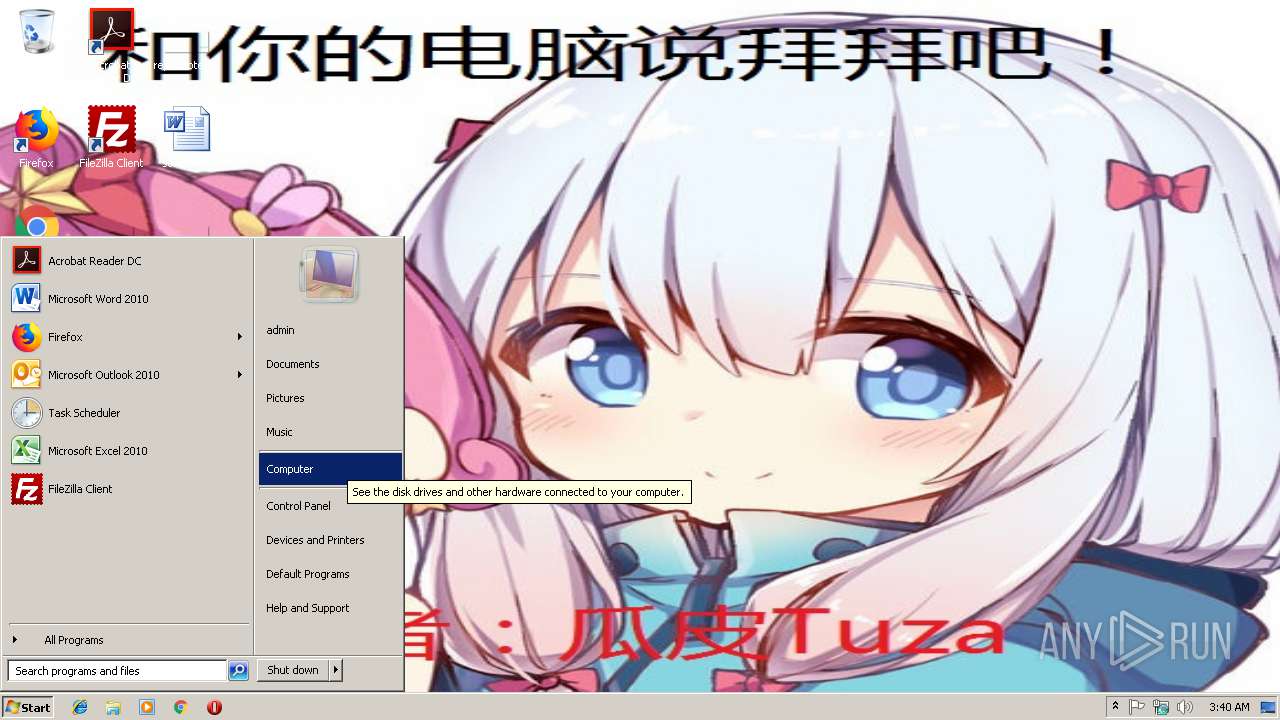
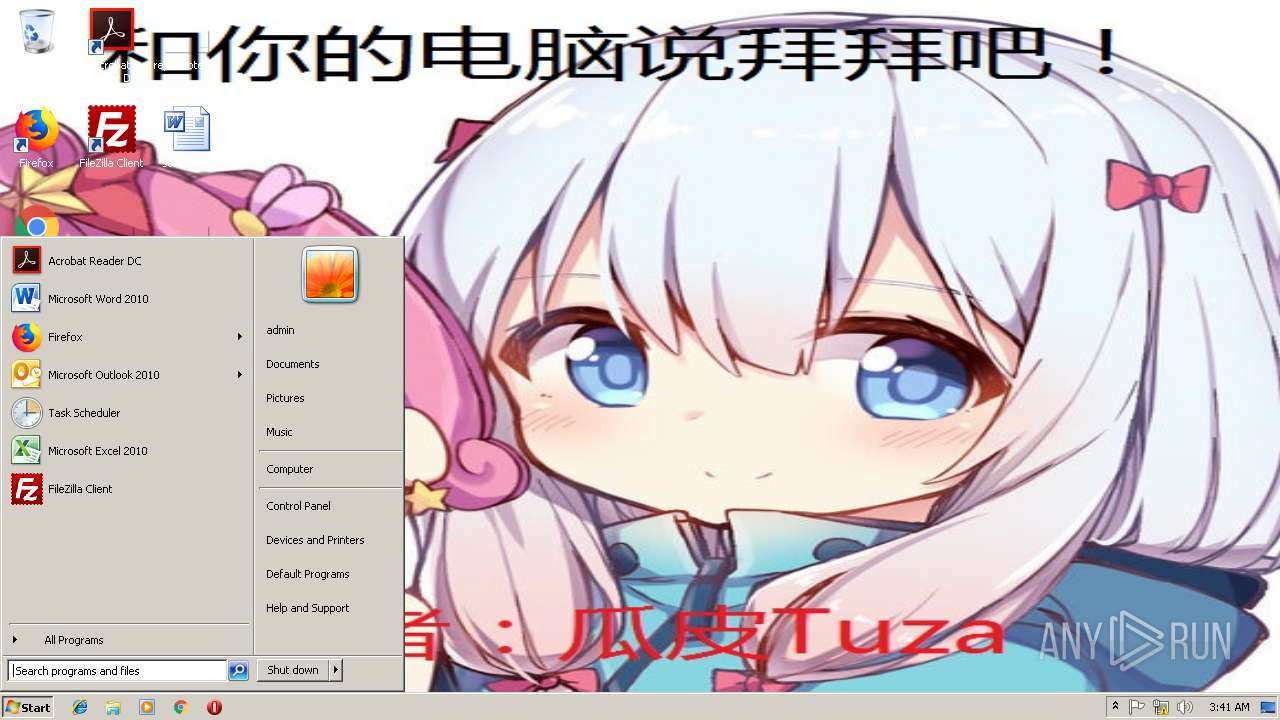
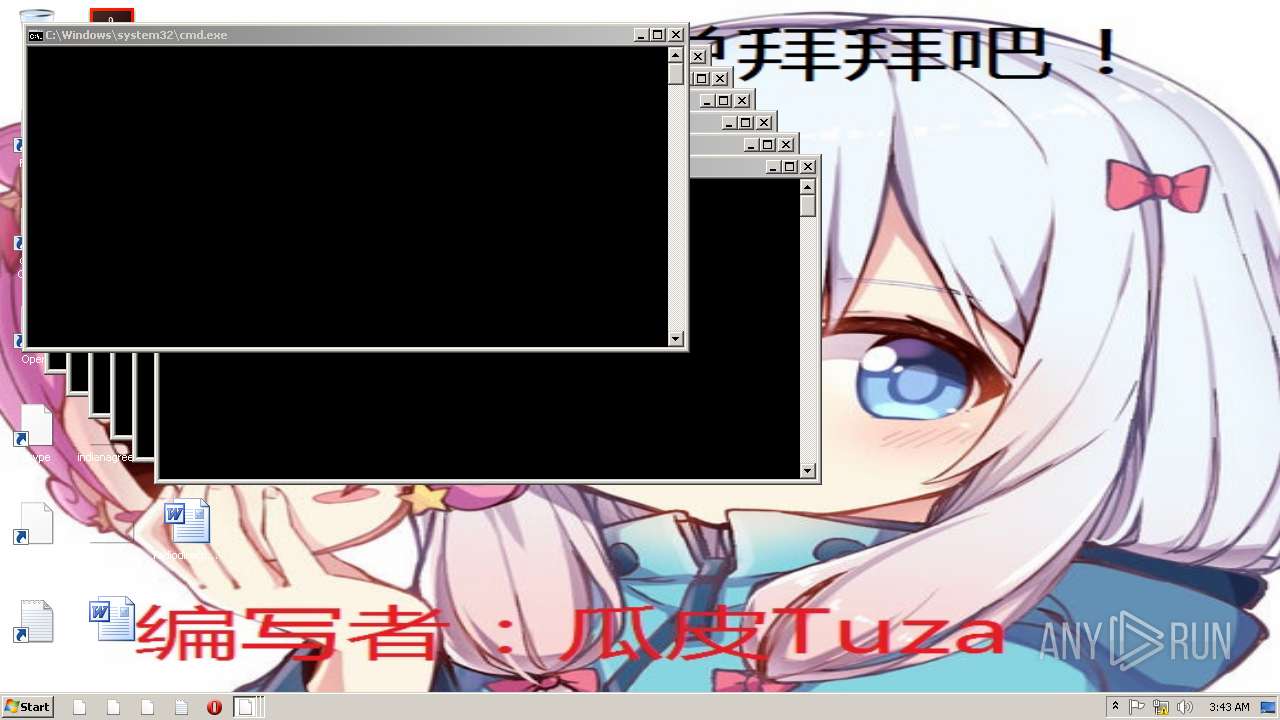
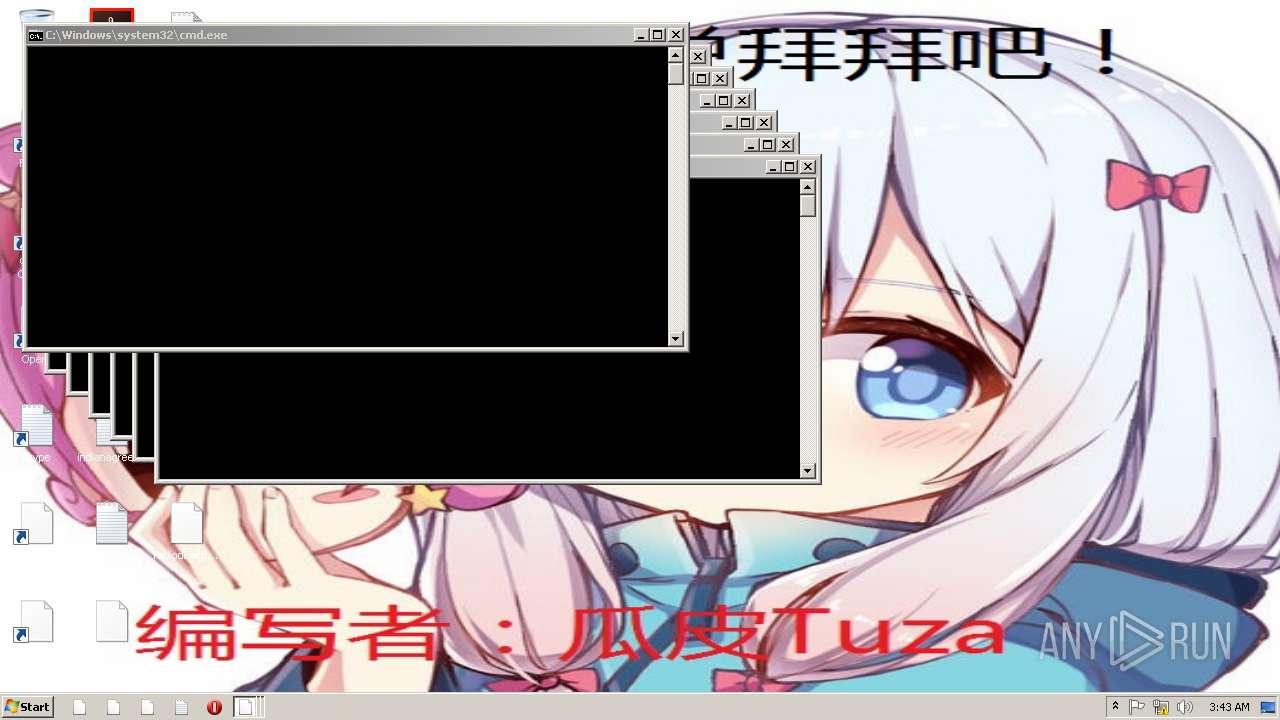
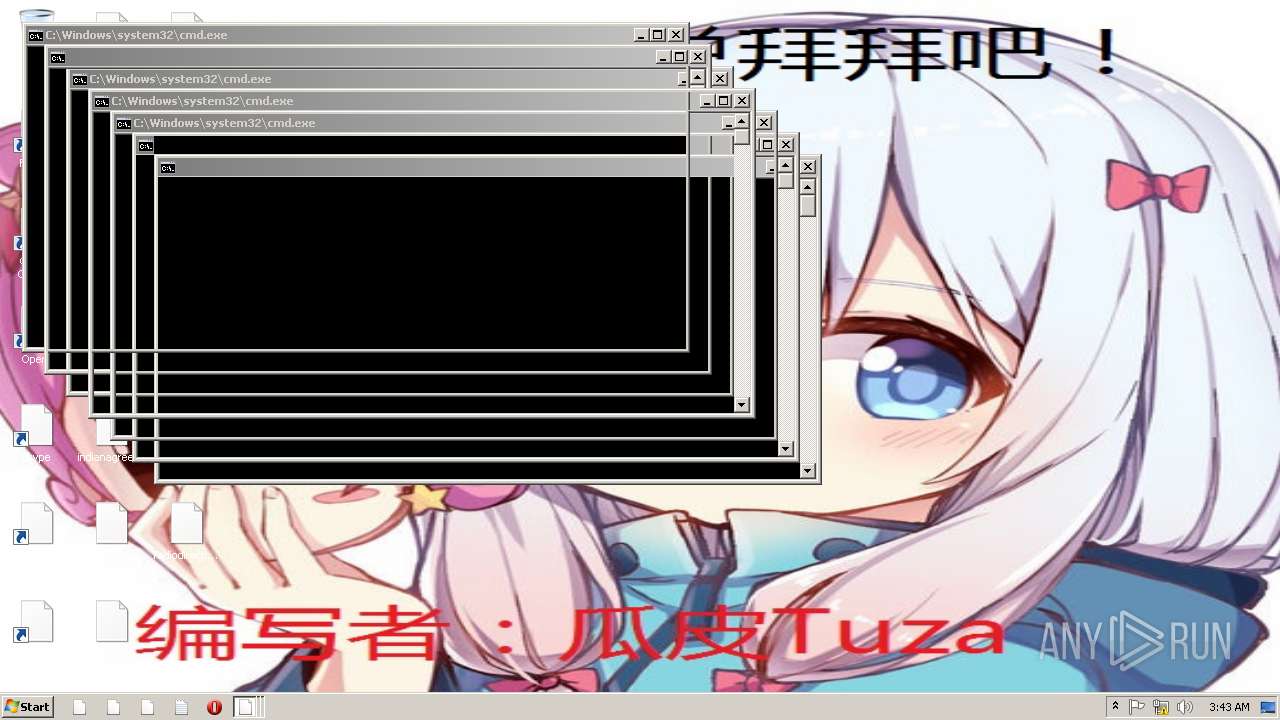
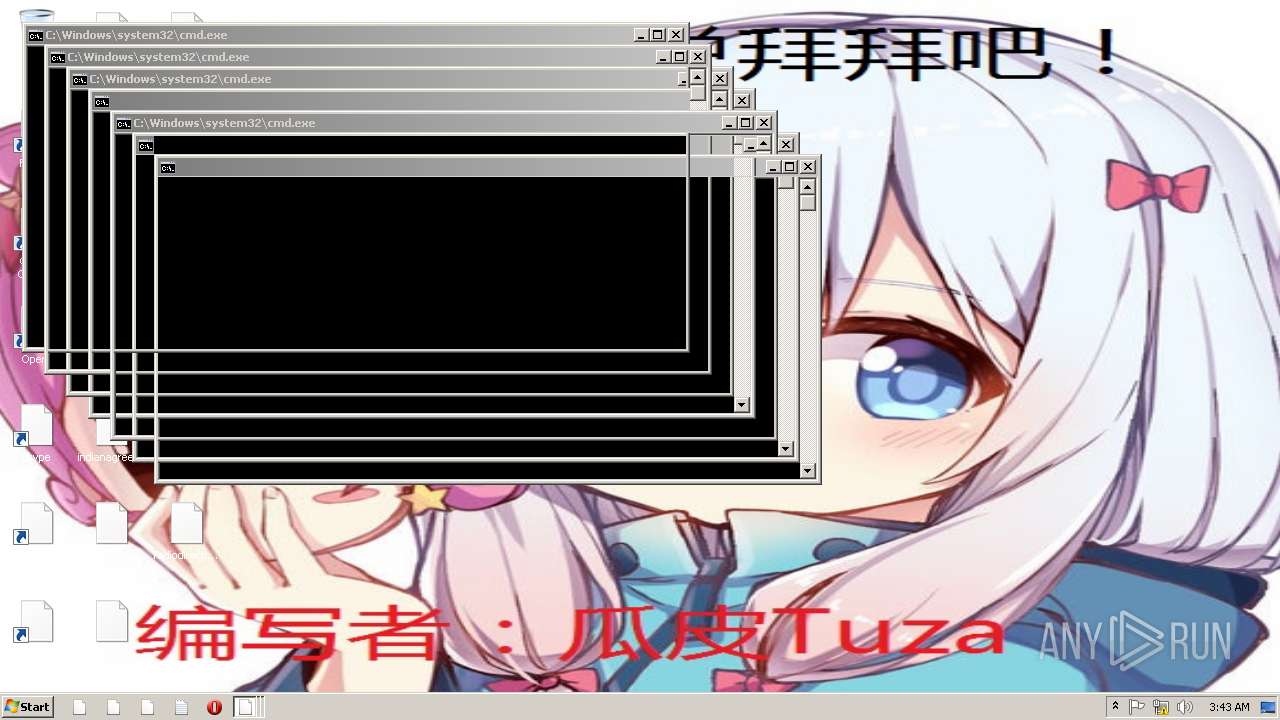
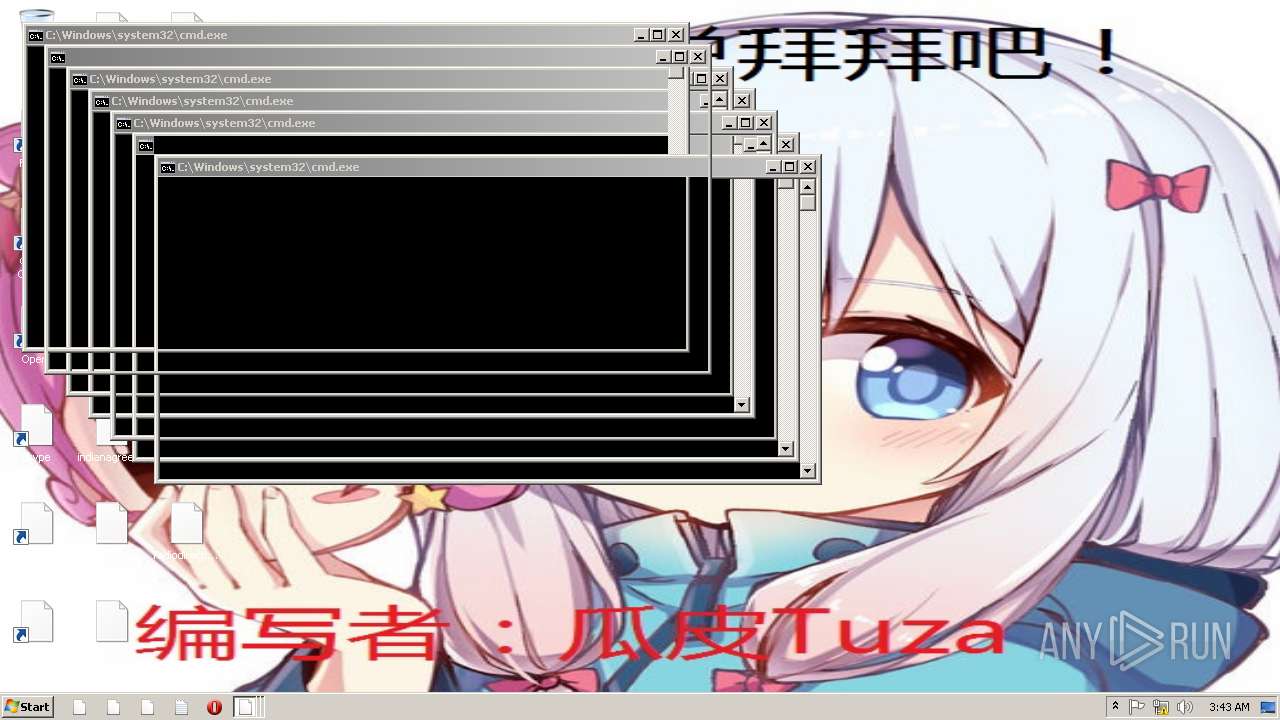
Changes the desktop background image
- 芦苇病毒.exe (PID: 3532)
Executable content was dropped or overwritten
- 芦苇病毒.exe (PID: 3532)
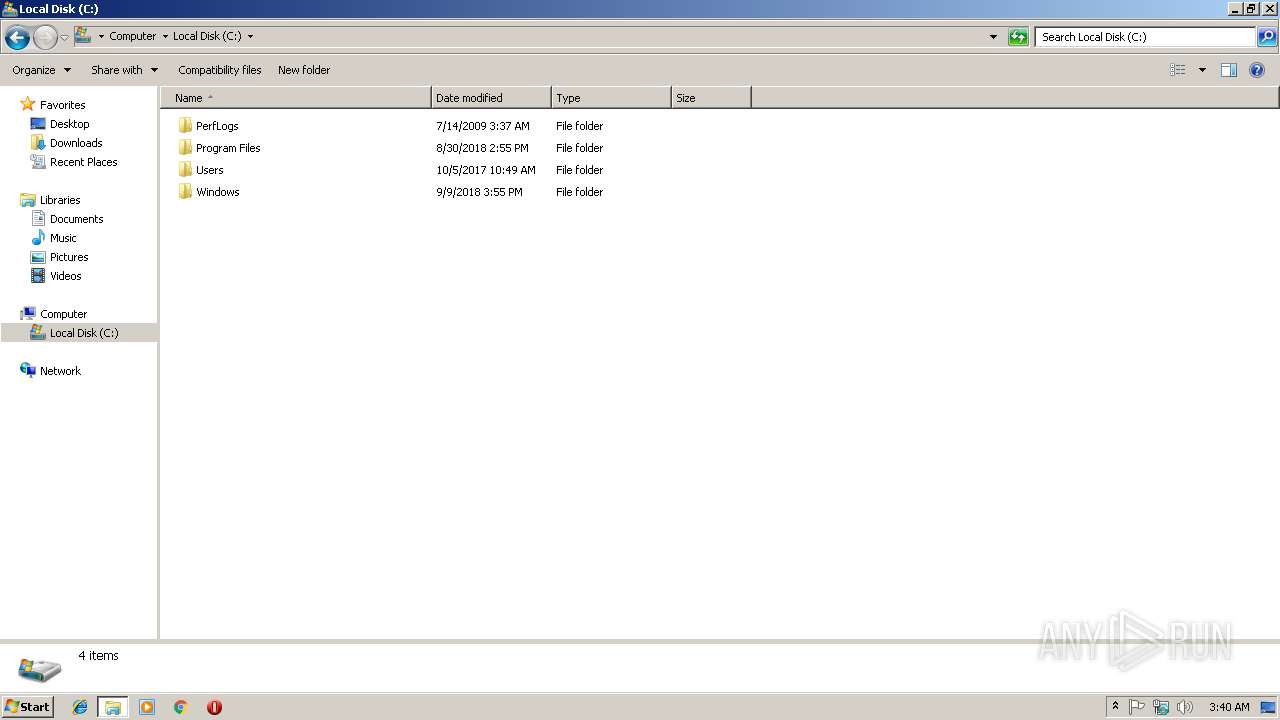
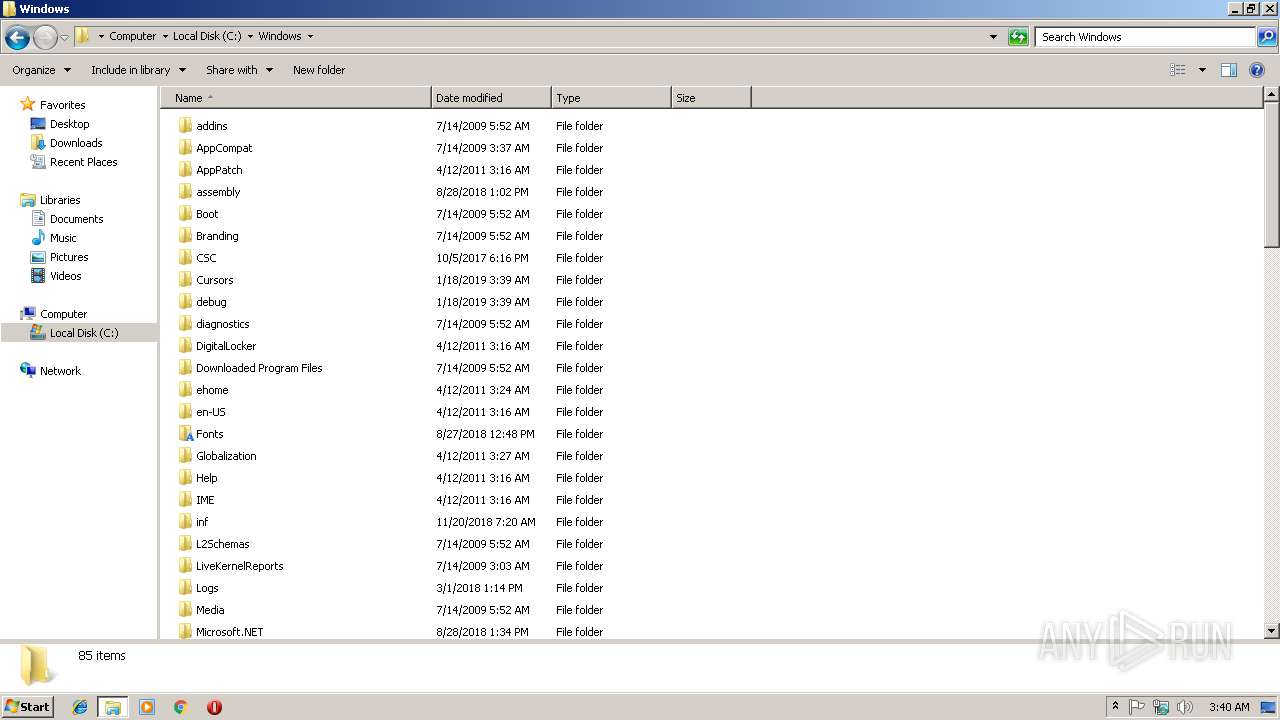
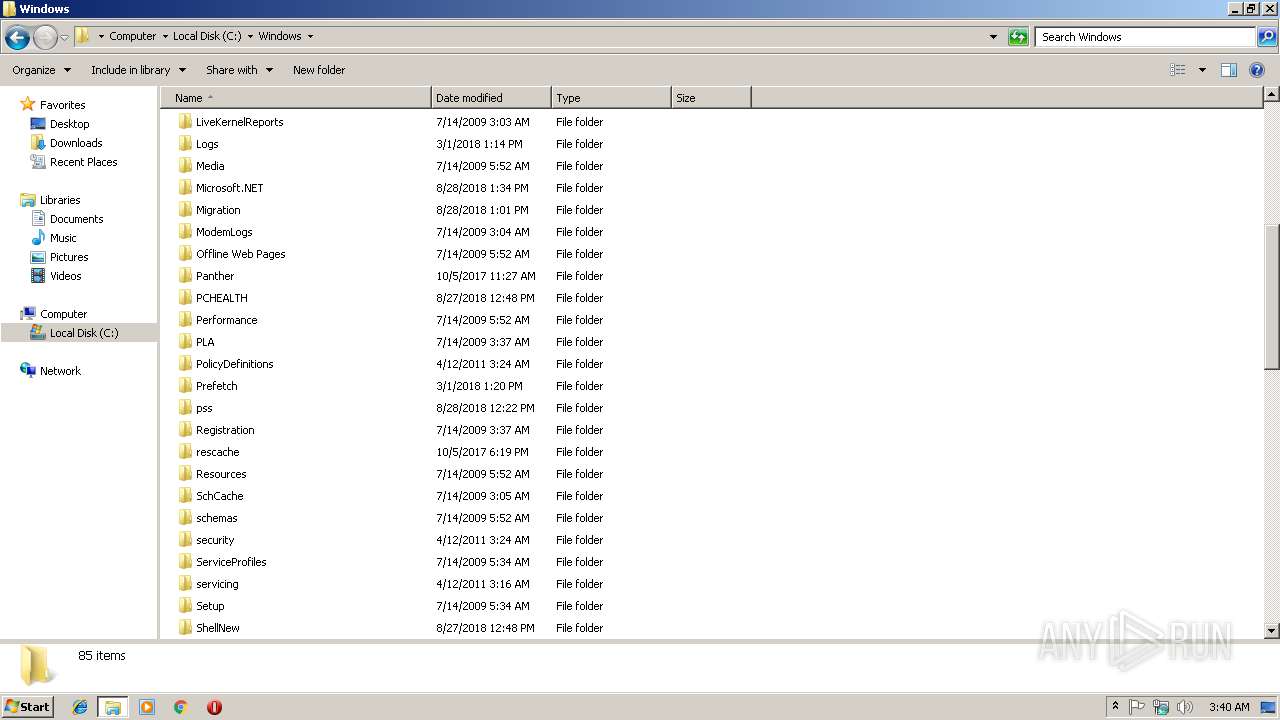
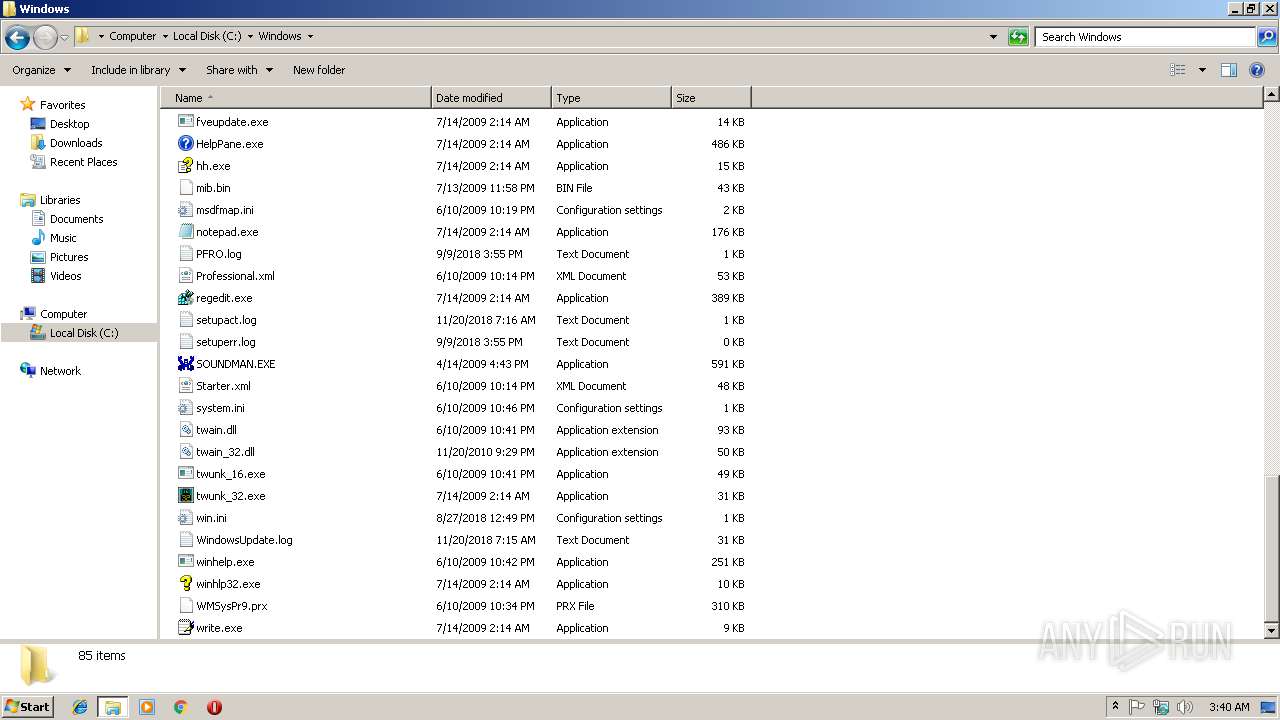
Removes files from Windows directory
- 芦苇病毒.exe (PID: 3532)
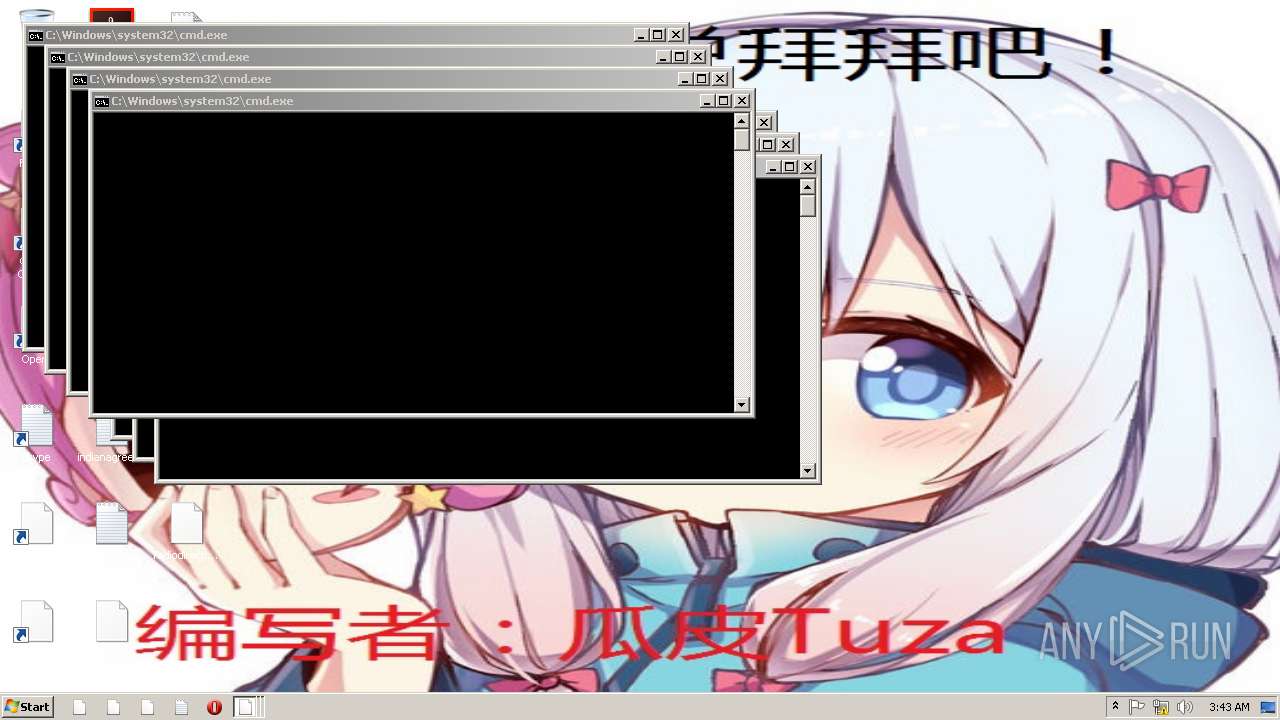
Uses TASKKILL.EXE to kill process
- 芦苇病毒.exe (PID: 3532)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (22.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (19.6) |
| .exe | | | UPX compressed Win32 Executable (19.2) |
| .exe | | | Win32 EXE Yoda's Crypter (18.8) |
| .scr | | | Windows screen saver (9.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:20 05:24:21+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 540672 |
| InitializedDataSize: | 12742656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x65088 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| FileDescription: | By-瓜皮Tuza |
| ProductName: | 绝地卢本伟同款自瞄 |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | QQ:1344895492 |
| LegalCopyright: | QQ:1344895492 版权所有 |
| Comments: | explorer.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 20-Jan-2018 04:24:21 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| FileDescription: | By-瓜皮Tuza |
| ProductName: | 绝地卢本伟同款自瞄 |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | QQ:1344895492 |
| LegalCopyright: | QQ:1344895492 版权所有 |
| Comments: | explorer.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 20-Jan-2018 04:24:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000831FA | 0x00084000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.54971 |
.rdata | 0x00085000 | 0x00BF958A | 0x00BFA000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.68247 |
.data | 0x00C7F000 | 0x0002E04A | 0x00012000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.18371 |
.rsrc | 0x00CAE000 | 0x0001AC18 | 0x0001B000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.49271 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 3.29582 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.06219 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.34384 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 5.79383 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.40677 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 7.9474 | 37456 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 4.89988 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 5.01114 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WINMM.dll |
WINSPOOL.DRV |
WS2_32.dll |
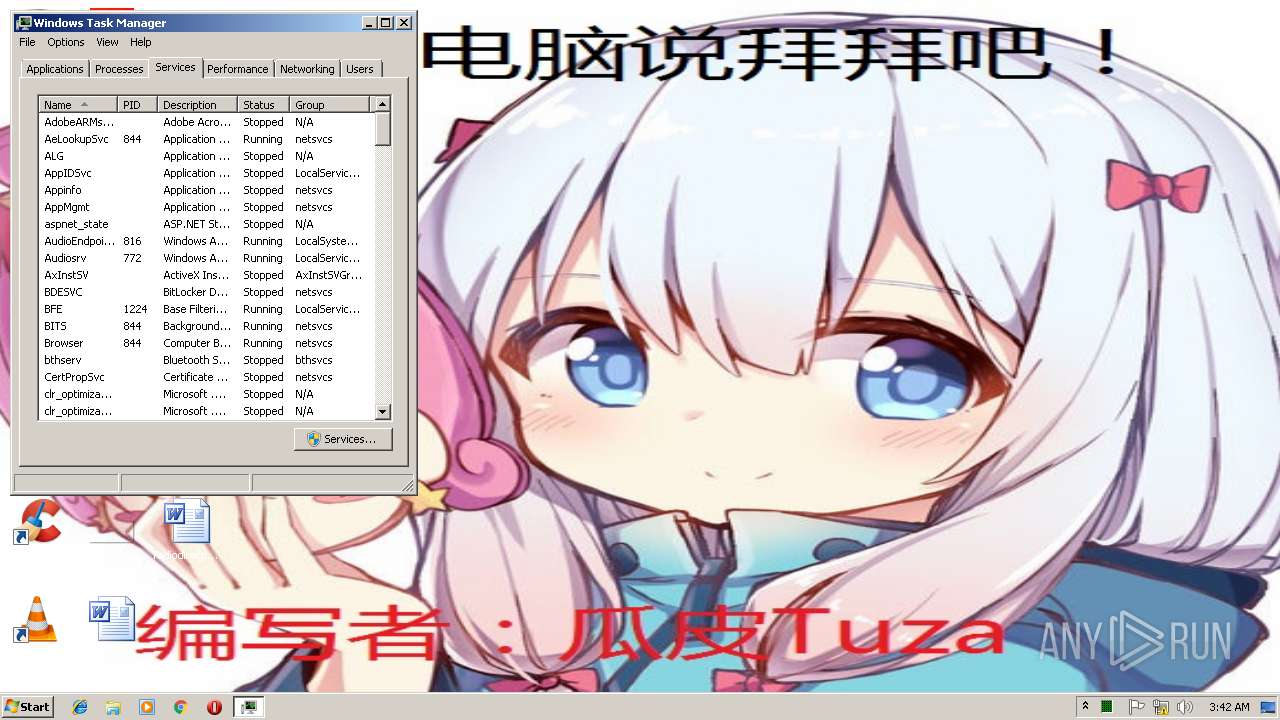
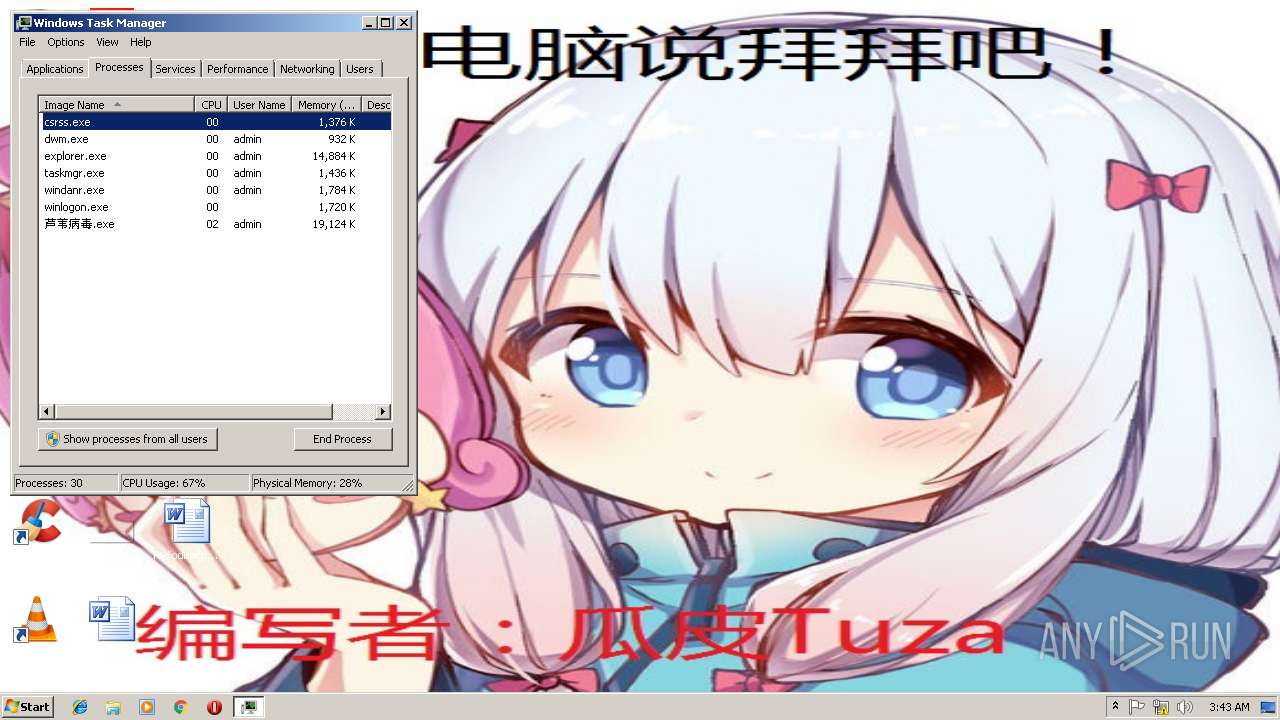
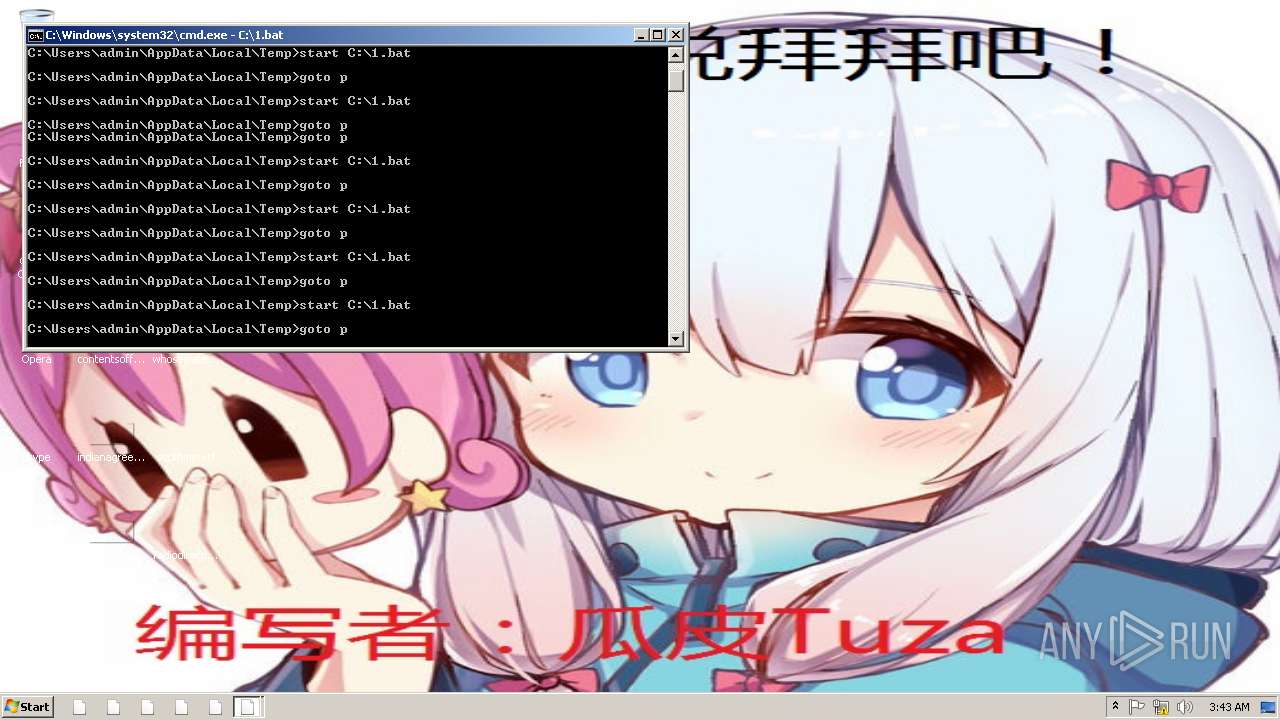
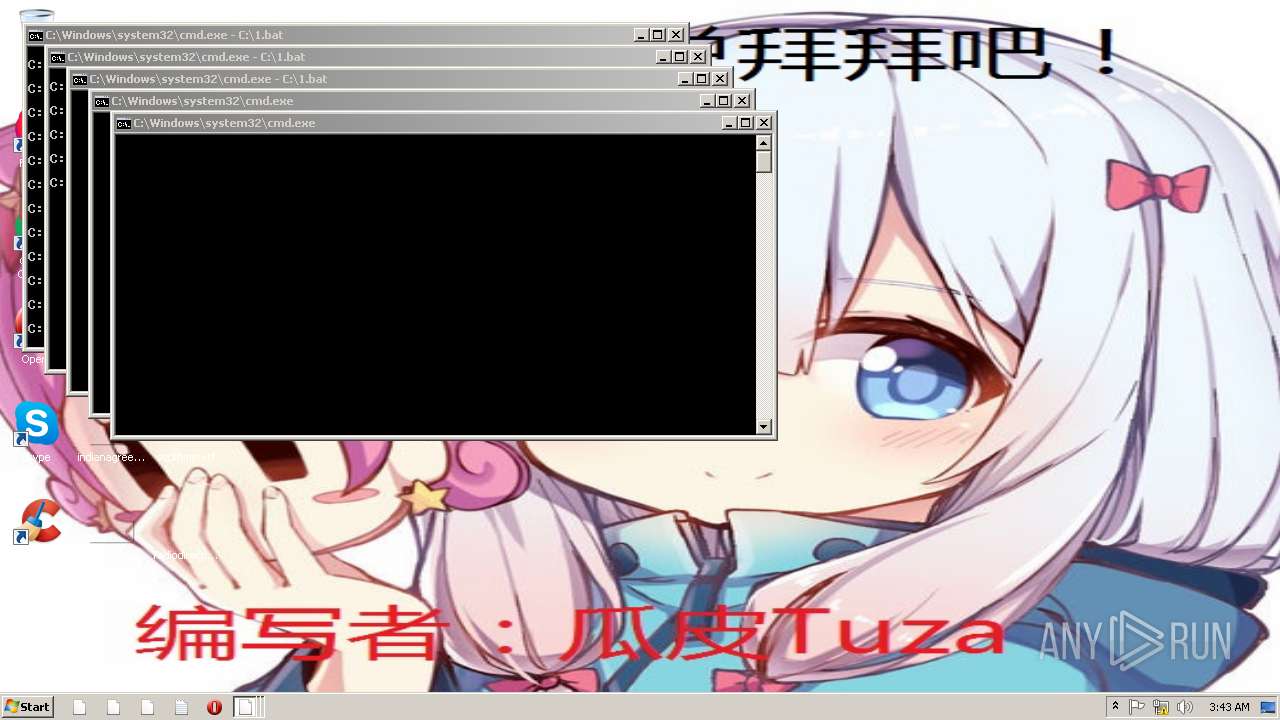
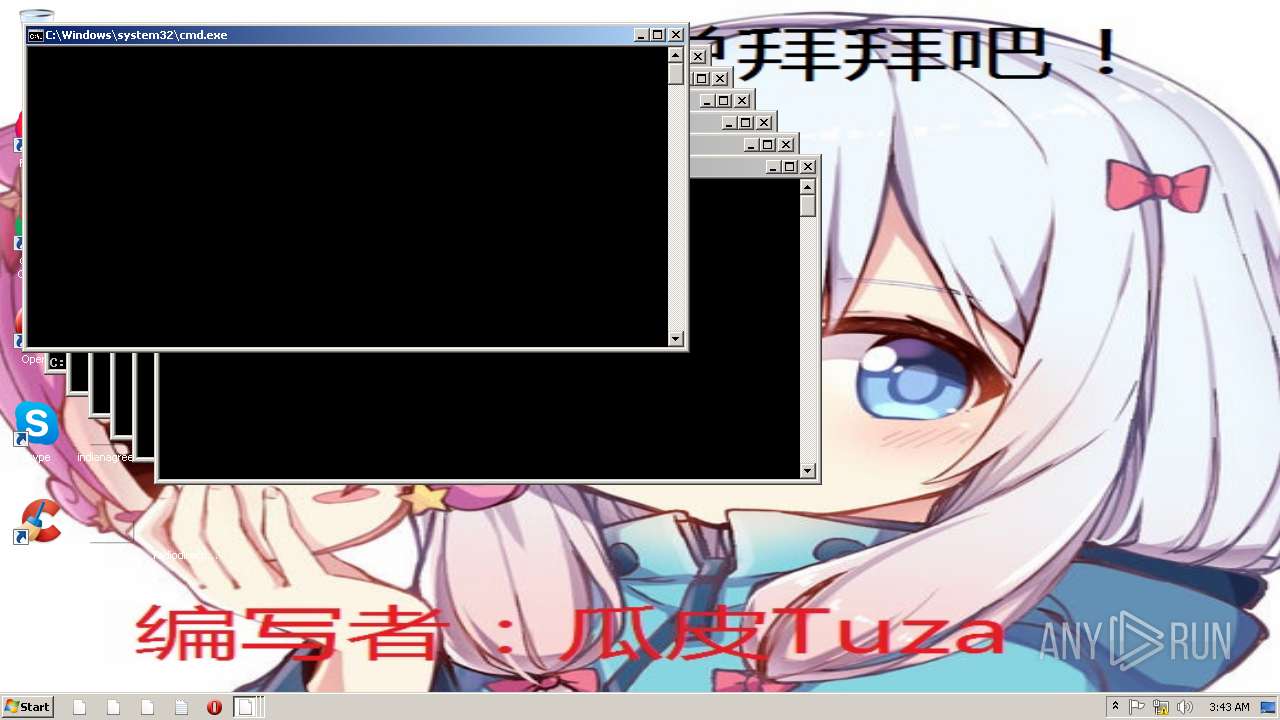
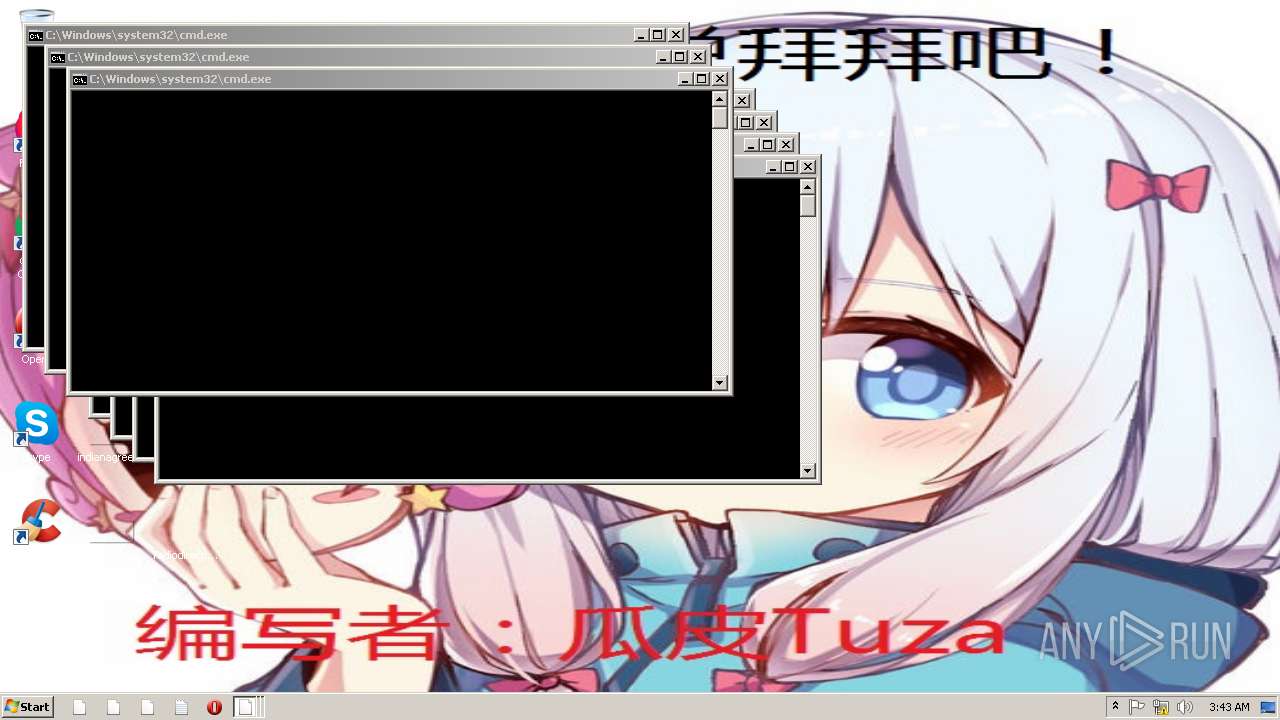
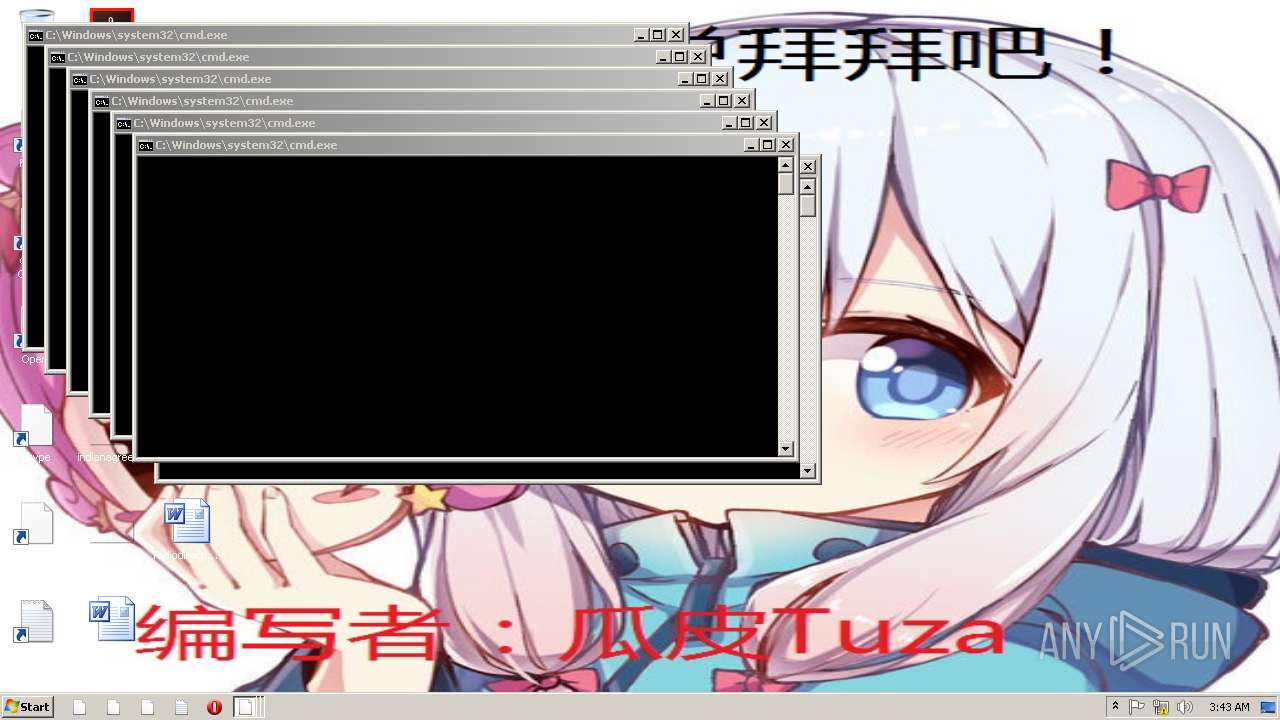
Total processes
44
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
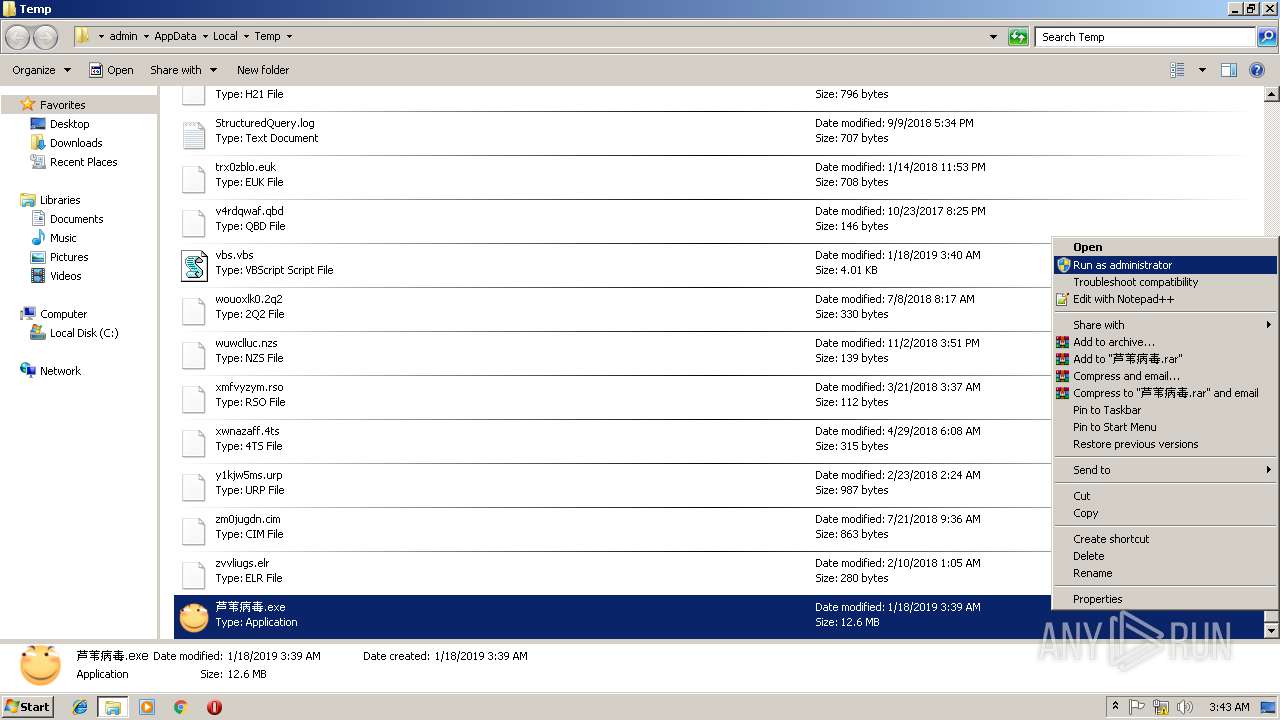
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2052 | taskkill /f /im 360tray.exe | C:\Windows\system32\taskkill.exe | — | 芦苇病毒.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3064 | taskkill /f /im 360tray.exe | C:\Windows\system32\taskkill.exe | — | 芦苇病毒.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3532 | "C:\Users\admin\AppData\Local\Temp\芦苇病毒.exe" | C:\Users\admin\AppData\Local\Temp\芦苇病毒.exe | explorer.exe | ||||||||||||
User: admin Company: QQ:1344895492 Integrity Level: MEDIUM Description: By-瓜皮Tuza Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3616 | taskkill /f /im 360tray.exe | C:\Windows\system32\taskkill.exe | — | 芦苇病毒.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4024 | taskkill /f /im 360tray.exe | C:\Windows\system32\taskkill.exe | — | 芦苇病毒.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4032 | taskkill /f /im 360tray.exe | C:\Windows\system32\taskkill.exe | — | 芦苇病毒.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
52
Read events
22
Write events
30
Delete events
0
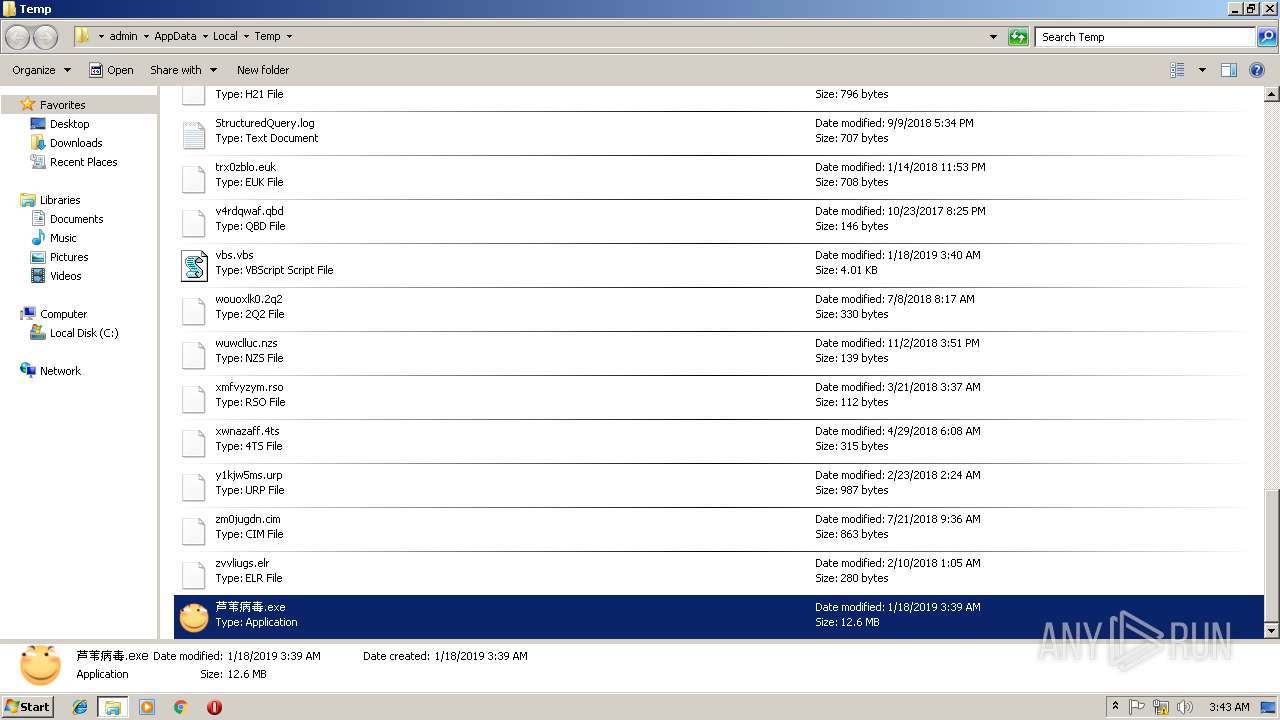
Modification events
| (PID) Process: | (3532) 芦苇病毒.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | Wallpaper |
Value: 1.bmp | |||
| (PID) Process: | (3532) 芦苇病毒.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | WallpaperStyle |
Value: 2 | |||
| (PID) Process: | (3532) 芦苇病毒.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | write | Name: | TileWallpaper |
Value: 2 | |||
| (PID) Process: | (3532) 芦苇病毒.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | ????.exe |
Value: C:\Users\admin\AppData\Local\Temp\????.exe | |||
| (PID) Process: | (3532) 芦苇病毒.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\exefile\DefaultIcon |
| Operation: | write | Name: | |
Value: c:\cc.ico | |||
| (PID) Process: | (3532) 芦苇病毒.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\360Safe\safemon |
| Operation: | write | Name: | ExecAccess |
Value: 0 | |||
| (PID) Process: | (3532) 芦苇病毒.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\360Safe\safemon |
| Operation: | write | Name: | MonAccess |
Value: 0 | |||
| (PID) Process: | (3532) 芦苇病毒.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\360Safe\safemon |
| Operation: | write | Name: | SiteAccess |
Value: 0 | |||
| (PID) Process: | (3532) 芦苇病毒.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\360Safe\safemon |
| Operation: | write | Name: | UDiskAccess |
Value: 0 | |||
| (PID) Process: | (3532) 芦苇病毒.exe | Key: | HKEY_CURRENT_USER\SoftWare \Microsoft \Windows \CurrentVersion \Policies\WinOldApp |
| Operation: | write | Name: | Disabled |
Value: 1 | |||
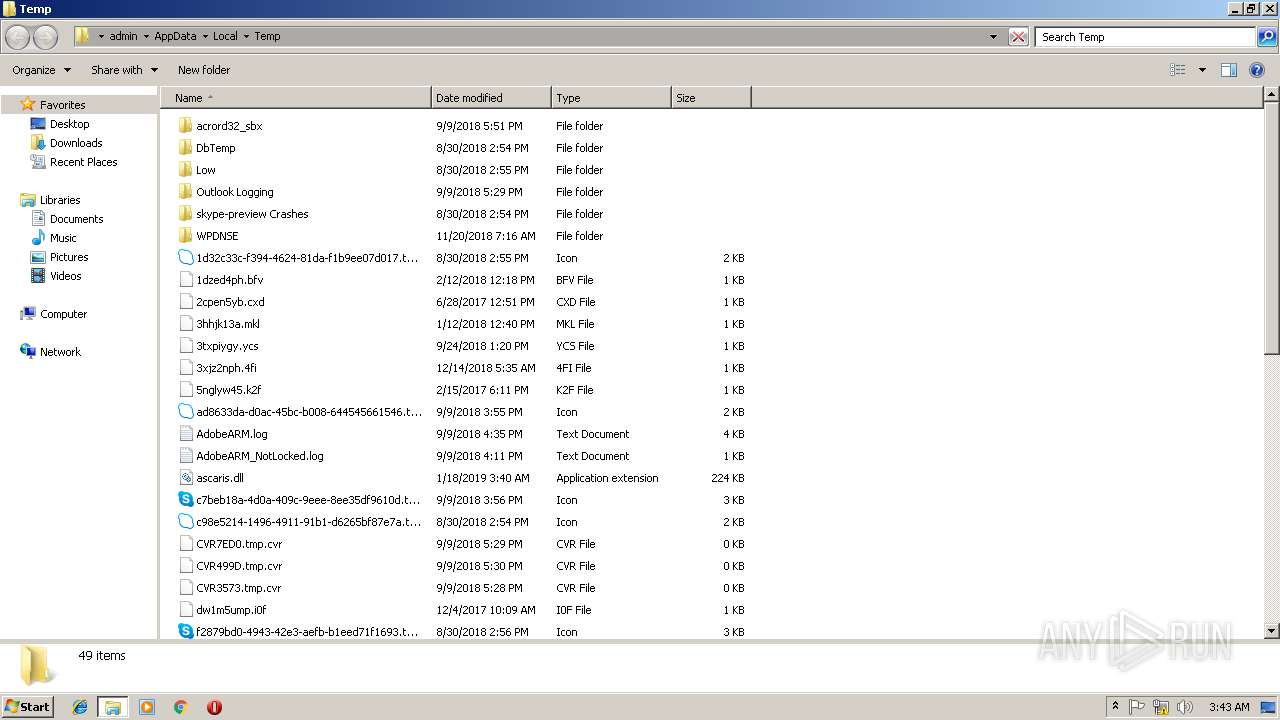
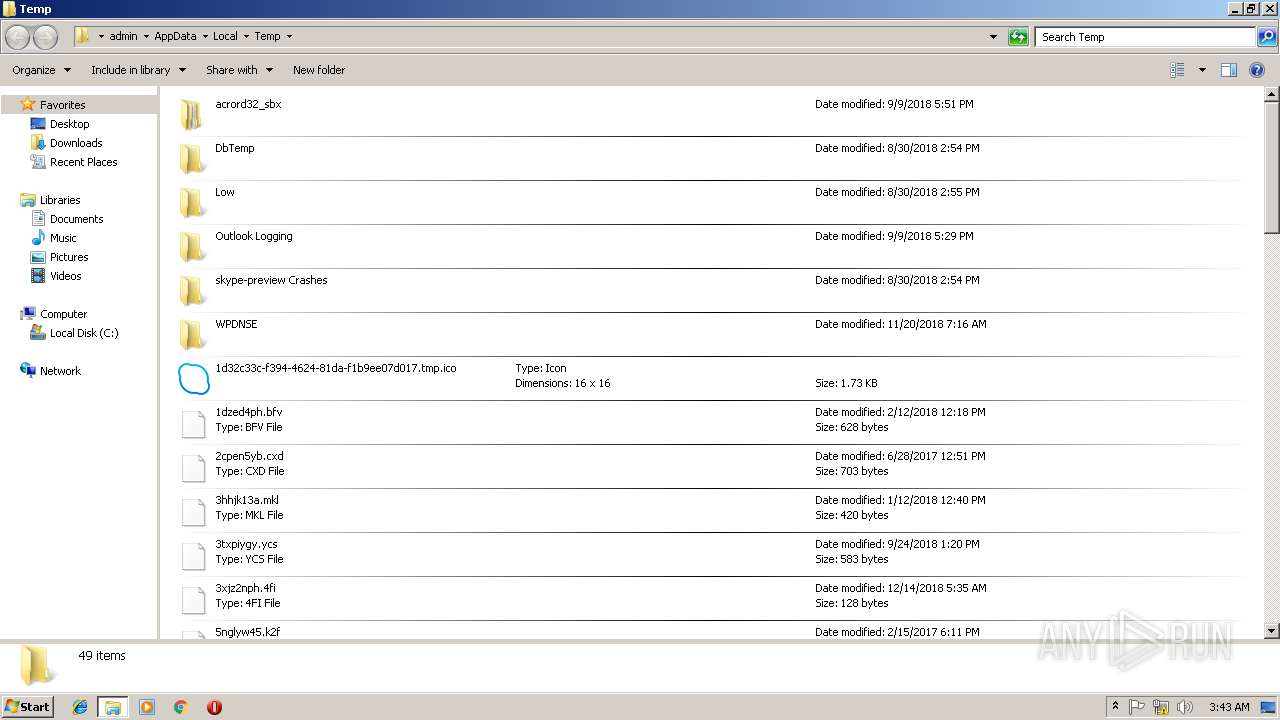
Executable files
1
Suspicious files
0
Text files
4
Unknown types
0
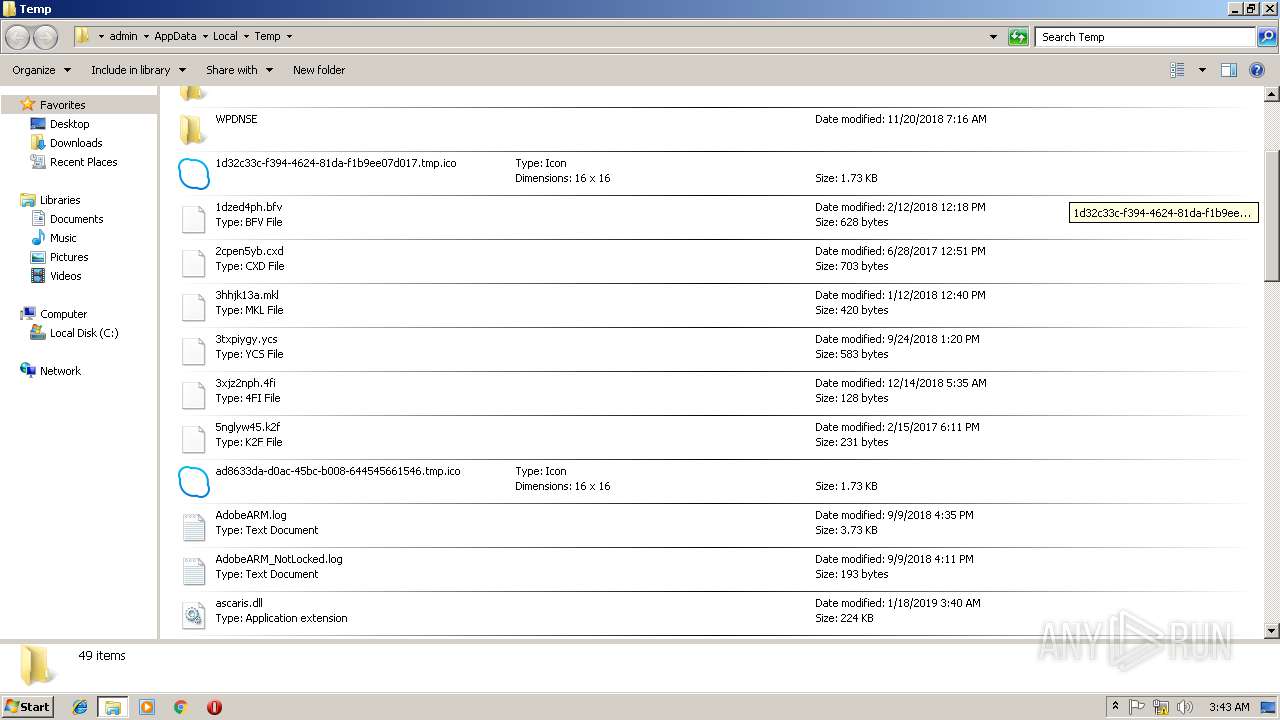
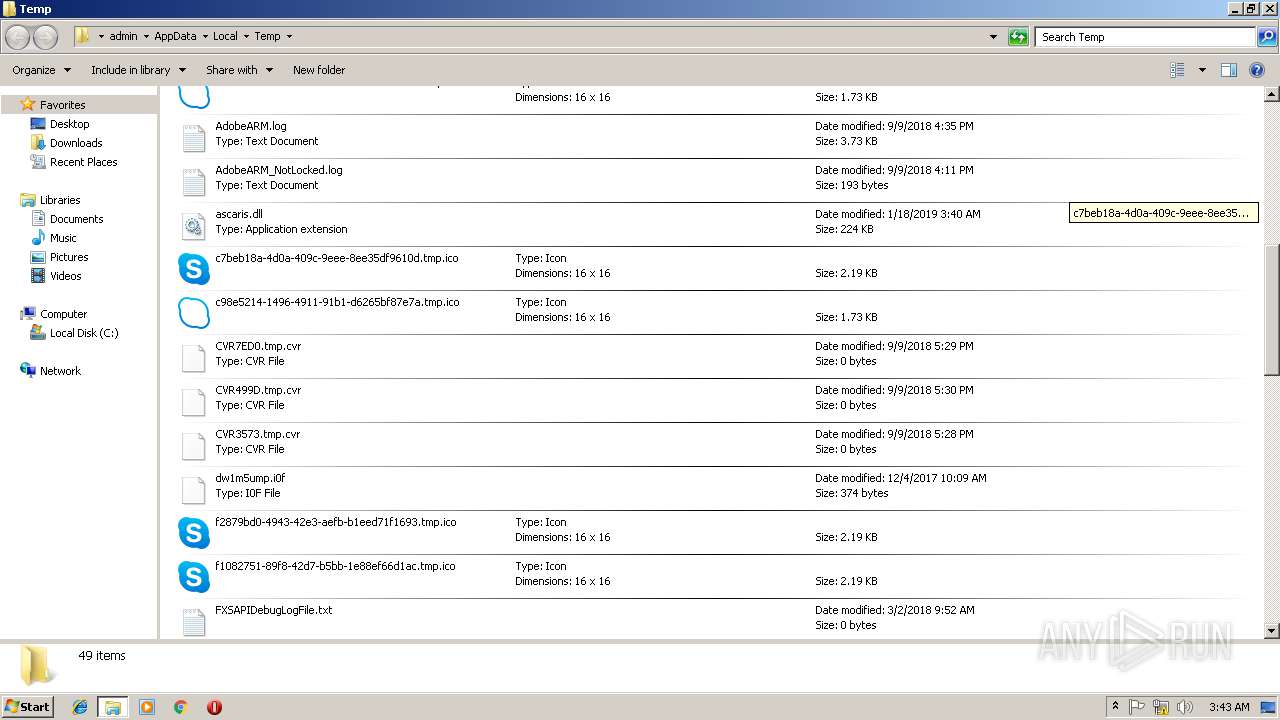
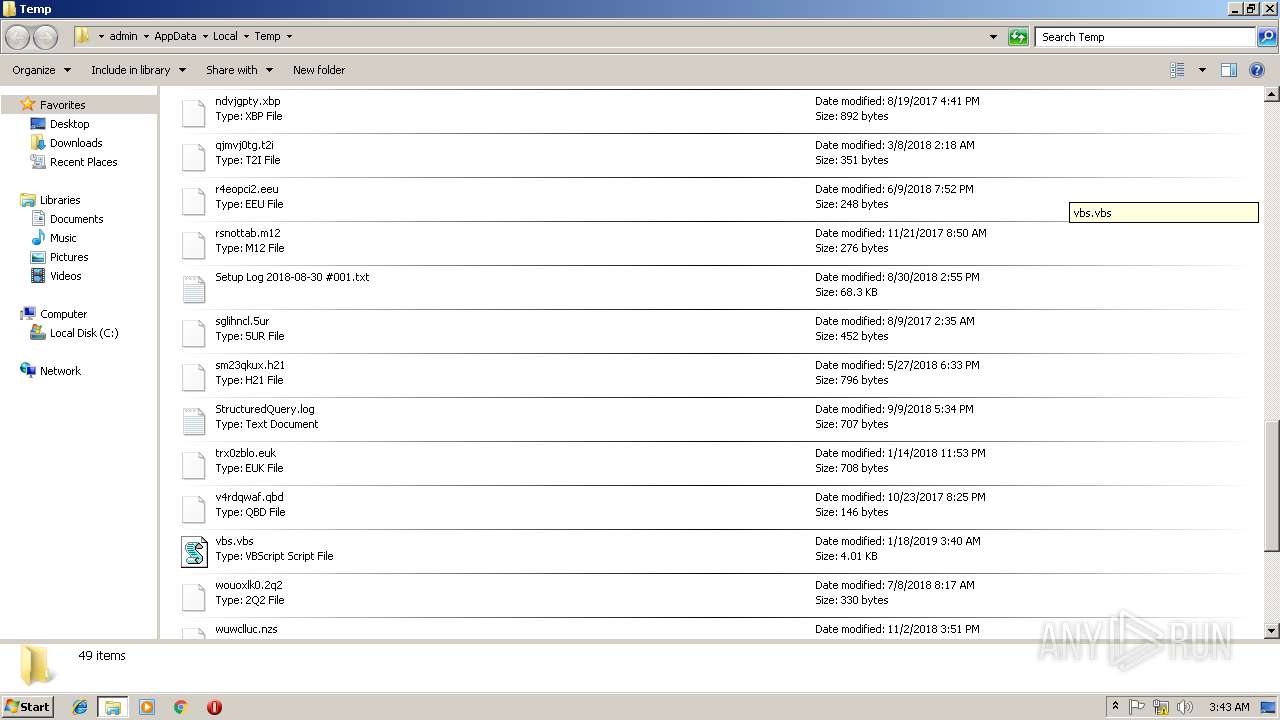
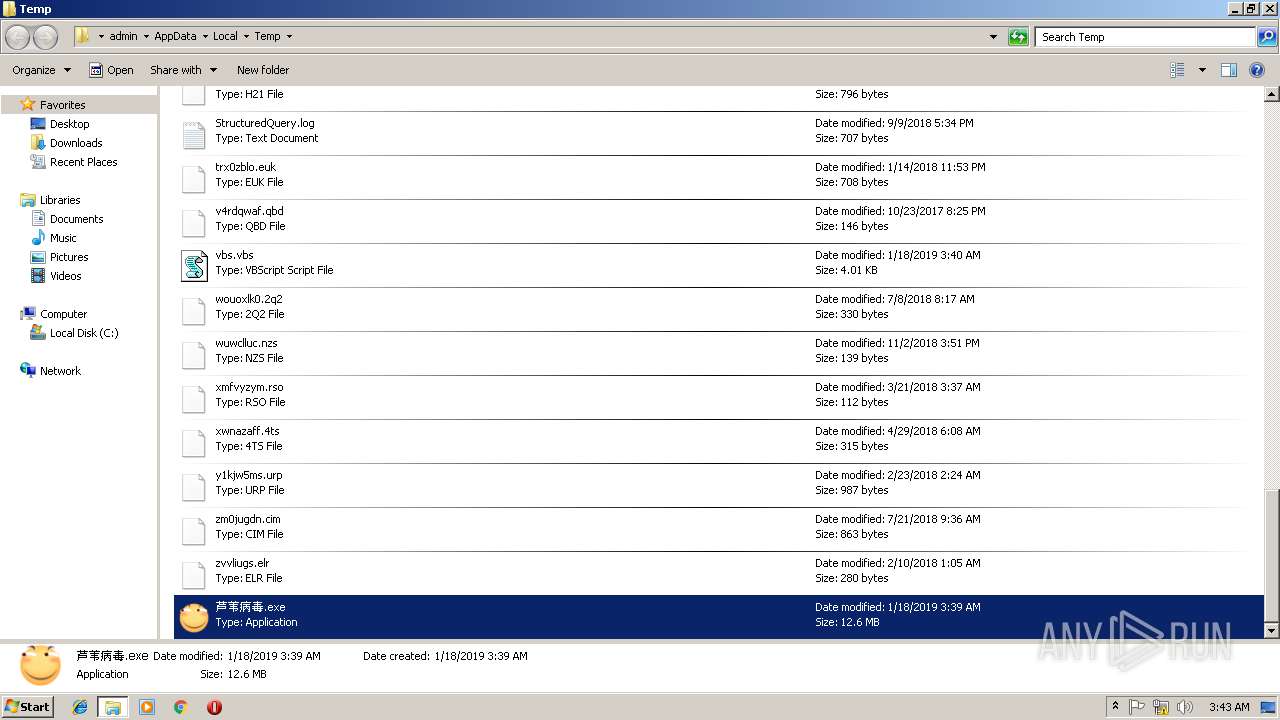
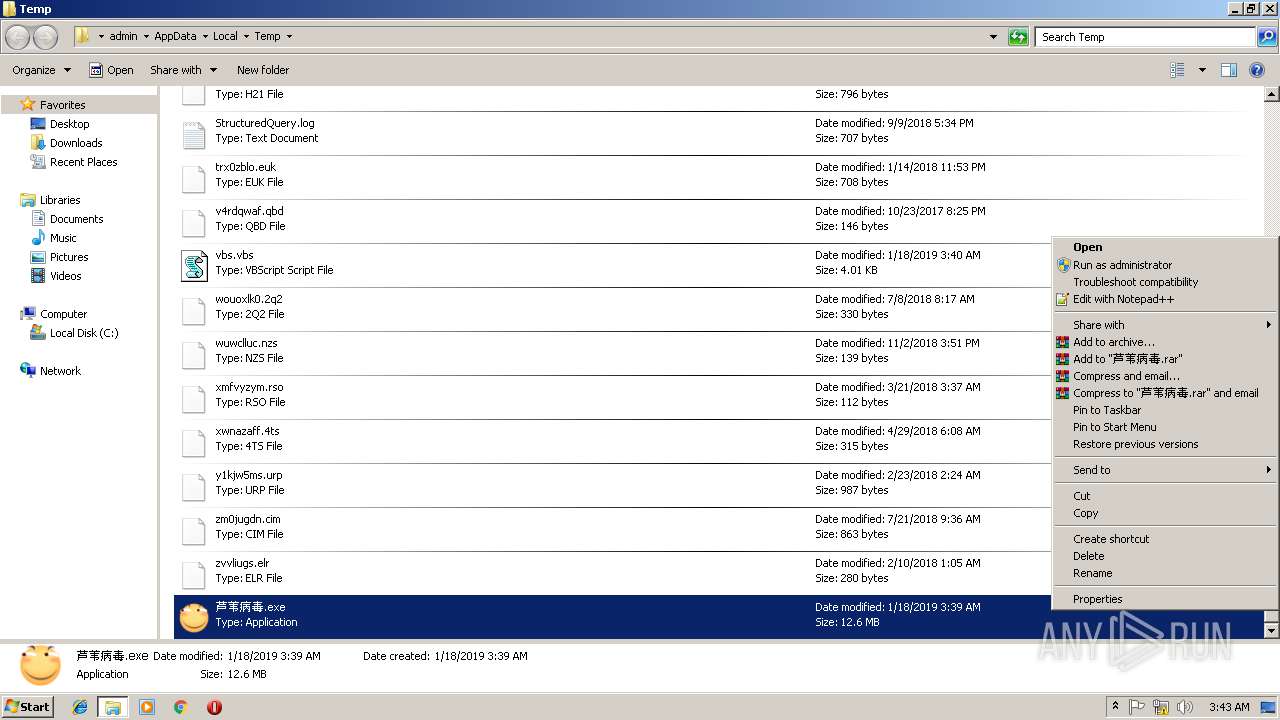
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3532 | 芦苇病毒.exe | C:\Users\admin\AppData\Local\Temp\ascaris.dll | executable | |
MD5:4520EEE1DA294B6C8428CEA200B81D18 | SHA256:9B2C140B6C47666024128B8AC9F1E8B2FE041CAF6D286EEC638018BEB48394CD | |||
| 3532 | 芦苇病毒.exe | C:\Users\admin\AppData\Local\Temp\vbs.vbs | text | |
MD5:53A7ED066ADC57F945D18D6EEB60ECCD | SHA256:05E2A61AEBE8C93B208489C28E08E8D505F14E1E5B10A9834F3B5ACD21FDFECF | |||
| 3532 | 芦苇病毒.exe | C:\Users\admin\AppData\Local\Temp\1.bmp | image | |
MD5:55153284F311C9F58190428B1787BC96 | SHA256:08188408DDB0D7B24BE8930B5254B15CD3D79EFC35E57CB7E9F68A5B08F97D08 | |||
| 3532 | 芦苇病毒.exe | C:\Users\admin\AppData\Local\VirtualStore\cc.ico | image | |
MD5:5150510F600863B4296B622E55675B8C | SHA256:D061FD24E026D41FF0754A746FBD66C69C6F365A7C50929A1FA0E2BD9336BD9A | |||
| 3532 | 芦苇病毒.exe | C:\Users\admin\AppData\Local\VirtualStore\main.cpp | text | |
MD5:6BB827376DDF346A49932B3636FB1283 | SHA256:DD71C9A53CD76F14164F124D2D5D1069924E1F94671F05866689C4AEEE1E2C8A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report