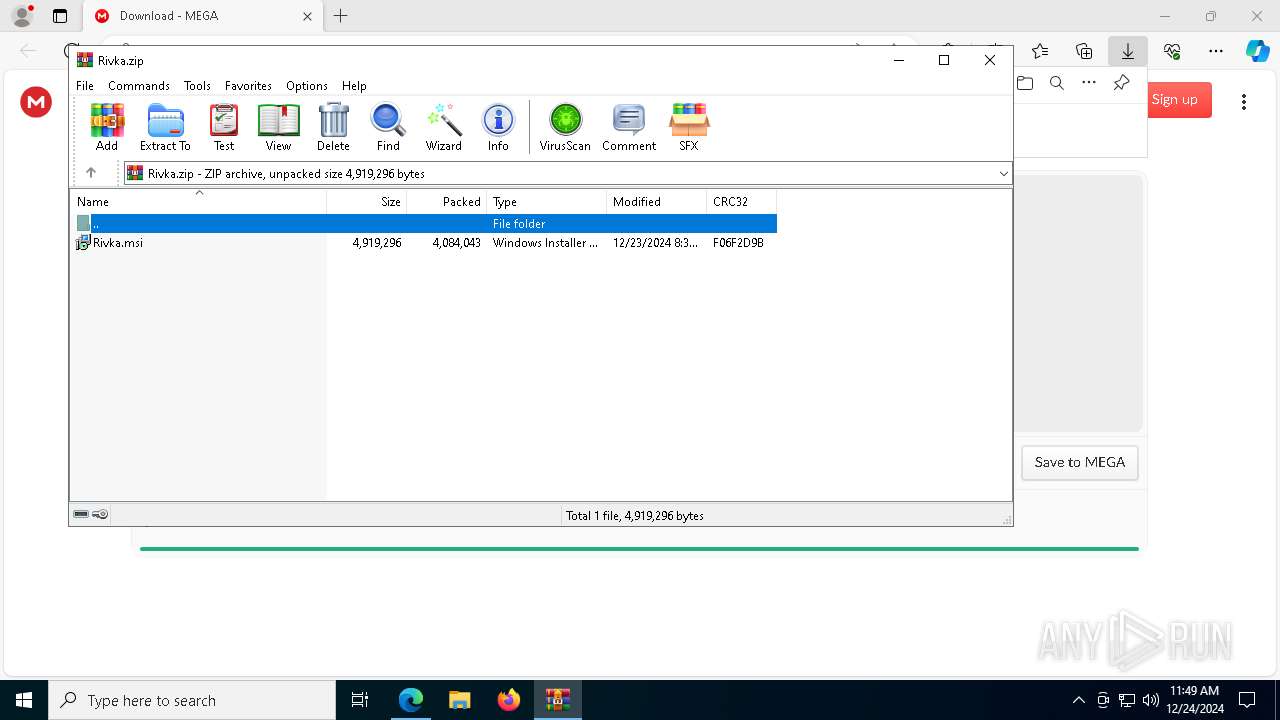
| URL: | https://mega.nz/file/2NcC0IQC#l6uCf50__VwOt-so17sxC6SUt6iFXBnmt_I9F8Yf_kI |
| Full analysis: | https://app.any.run/tasks/0753b02b-8006-44c7-803d-19ba7701ba93 |
| Verdict: | Malicious activity |
| Analysis date: | December 24, 2024, 11:49:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 8B9643D758AFBCFE09EA626B092D43F9 |
| SHA1: | 9777620016EEE41F6C30B2FA60612DB86E3B6828 |
| SHA256: | 18990239A7D9755085CC5D4497E1E376505891B1E02F2D34808A8836B80FD400 |
| SSDEEP: | 3:N8X/iWrxVVPDSVtSgaGhJn:2nVjPOgUJ |
MALICIOUS
Changes powershell execution policy (Bypass)
- pdq-connect-agent.exe (PID: 7628)
Bypass execution policy to execute commands
- powershell.exe (PID: 640)
- powershell.exe (PID: 3488)
- powershell.exe (PID: 6304)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 5980)
- powershell.exe (PID: 4668)
- powershell.exe (PID: 1480)
- powershell.exe (PID: 6788)
- powershell.exe (PID: 6760)
- powershell.exe (PID: 6804)
- powershell.exe (PID: 2124)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 8224)
- powershell.exe (PID: 5096)
- powershell.exe (PID: 7024)
- powershell.exe (PID: 7624)
- powershell.exe (PID: 5872)
- powershell.exe (PID: 6976)
- powershell.exe (PID: 4136)
- powershell.exe (PID: 5472)
- powershell.exe (PID: 4512)
- powershell.exe (PID: 4160)
- powershell.exe (PID: 4912)
- powershell.exe (PID: 8200)
- powershell.exe (PID: 8244)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 6664)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8120)
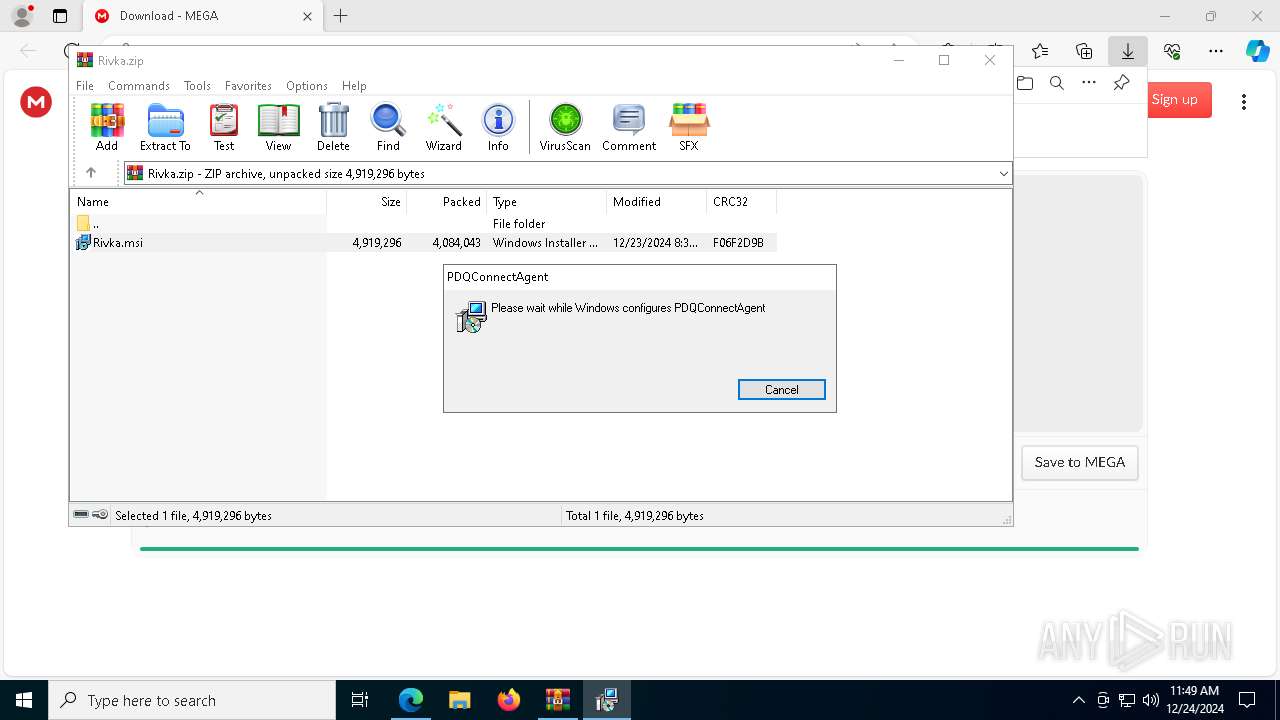
Executes as Windows Service
- VSSVC.exe (PID: 5464)
- pdq-connect-agent.exe (PID: 7628)
- pdq-connect-updater.exe (PID: 4932)
Executable content was dropped or overwritten
- rundll32.exe (PID: 5652)
- rundll32.exe (PID: 2792)
- rundll32.exe (PID: 5008)
- rundll32.exe (PID: 1684)
- rundll32.exe (PID: 7396)
- pdq-connect-agent.exe (PID: 7628)
- rundll32.exe (PID: 6004)
- rundll32.exe (PID: 1868)
- csc.exe (PID: 9996)
- csc.exe (PID: 10012)
- powershell.exe (PID: 6804)
- powershell.exe (PID: 5472)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 6088)
- msiexec.exe (PID: 5780)
- msiexec.exe (PID: 7268)
PDQConnect is probably used for system patching and software deployment
- sc.exe (PID: 7144)
Starts SC.EXE for service management
- rundll32.exe (PID: 7396)
Windows service management via SC.EXE
- sc.exe (PID: 7144)
Starts POWERSHELL.EXE for commands execution
- pdq-connect-agent.exe (PID: 7628)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 5872)
- powershell.exe (PID: 10232)
- powershell.exe (PID: 9184)
- powershell.exe (PID: 7284)
- powershell.exe (PID: 9568)
The process hide an interactive prompt from the user
- pdq-connect-agent.exe (PID: 7628)
The process hides Powershell's copyright startup banner
- pdq-connect-agent.exe (PID: 7628)
- powershell.exe (PID: 5872)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 10232)
- powershell.exe (PID: 9184)
- powershell.exe (PID: 9568)
- powershell.exe (PID: 7284)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 3488)
- powershell.exe (PID: 5472)
The process bypasses the loading of PowerShell profile settings
- pdq-connect-agent.exe (PID: 7628)
- powershell.exe (PID: 5872)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 10232)
- powershell.exe (PID: 9184)
- powershell.exe (PID: 9568)
- powershell.exe (PID: 7284)
CSC.EXE is used to compile C# code
- csc.exe (PID: 10012)
- csc.exe (PID: 9996)
Application launched itself
- powershell.exe (PID: 5872)
- powershell.exe (PID: 8308)
- powershell.exe (PID: 10232)
- powershell.exe (PID: 9184)
- powershell.exe (PID: 9568)
- powershell.exe (PID: 7284)
Process drops legitimate windows executable
- powershell.exe (PID: 5472)
- powershell.exe (PID: 6804)
Starts a Microsoft application from unusual location
- DismHost.exe (PID: 9104)
- DismHost.exe (PID: 8852)
INFO
Reads the computer name
- identity_helper.exe (PID: 7908)
- msiexec.exe (PID: 7268)
- pdq-connect-updater.exe (PID: 4932)
The process uses the downloaded file
- msedge.exe (PID: 4824)
- msedge.exe (PID: 8008)
- WinRAR.exe (PID: 8120)
- powershell.exe (PID: 3488)
- powershell.exe (PID: 640)
- powershell.exe (PID: 5528)
- powershell.exe (PID: 2124)
Creates files or folders in the user directory
- msiexec.exe (PID: 7972)
Reads Environment values
- identity_helper.exe (PID: 7908)
Checks proxy server information
- msiexec.exe (PID: 7972)
Reads the software policy settings
- msiexec.exe (PID: 7972)
- pdq-connect-agent.exe (PID: 7628)
Checks supported languages
- msiexec.exe (PID: 5496)
- identity_helper.exe (PID: 7908)
- pdq-connect-updater.exe (PID: 4932)
Manages system restore points
- SrTasks.exe (PID: 1864)
Application launched itself
- msiexec.exe (PID: 5496)
- msedge.exe (PID: 4824)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5496)
The sample compiled with english language support
- msiexec.exe (PID: 5496)
- powershell.exe (PID: 5472)
- powershell.exe (PID: 6804)
Create files in a temporary directory
- rundll32.exe (PID: 2792)
Creates files in the program directory
- pdq-connect-agent.exe (PID: 7628)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 3488)
- powershell.exe (PID: 7024)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 5472)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2124)
- powershell.exe (PID: 8244)
- powershell.exe (PID: 5472)
- powershell.exe (PID: 6804)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 7024)
Sends debugging messages
- DismHost.exe (PID: 8852)
- powershell.exe (PID: 5472)
- powershell.exe (PID: 6804)
- DismHost.exe (PID: 9104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
281
Monitored processes
142
Malicious processes
7
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 628 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1480 | "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | pdq-connect-agent.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1512 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --no-appcompat-clear --mojo-platform-channel-handle=6676 --field-trial-handle=2304,i,5984615238437853108,15808986789219333114,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1592 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1684 | rundll32.exe "C:\WINDOWS\Installer\MSI203E.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1319031 38 pdqconnectagent-setup!pdqconnectagent_setup.CustomActions.CreateEventSource | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1792 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1864 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1868 | rundll32.exe "C:\WINDOWS\Installer\MSI33DE.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1324031 77 pdqconnectupdater-setup!pdqconnectupdater_setup.CustomActions.CreateEventSource | C:\Windows\System32\rundll32.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
224 056
Read events
223 642
Write events
384
Delete events
30
Modification events
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 88B293FC98882F00 | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DF509EFC98882F00 | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263006 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {19F31FB7-9C62-44FE-9DDE-2B81DEA02722} | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 61A4C8FC98882F00 | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263006 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D7D2077B-BF9B-4582-BA81-C00D48BA53D8} | |||
| (PID) Process: | (4824) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263006 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F607C2E5-F157-4B0F-A227-A6B2726D2EB3} | |||
Executable files
142
Suspicious files
341
Text files
184
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135288.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135288.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135298.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135298.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1352a7.TMP | — | |
MD5:— | SHA256:— | |||
| 4824 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
103
DNS requests
76
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7008 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7972 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRhtVltVOu8OqBzmsd%2B%2FeFfks3xTQQUvGsiZZ2MaObmHgXx2HIl1LjgSMACEAvcoEuhCK%2FAlHGPdKmo6gs%3D | unknown | — | — | whitelisted |
7972 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7972 | msiexec.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEA5NZ%2FZDFskqO3oXzEaXao8%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8080 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9cf951df-e7db-4d00-b0fc-02131f5ca303?P1=1735348750&P2=404&P3=2&P4=UhP2mrr0C0HsWsUvmEjpFTu8L6fA6UESrWuEyEQlq31ugHGhLUlyCmvNlK6XaonNy6t5o4hArL5FpLwZIErLfQ%3d%3d | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6896 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2380 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.19.217.218:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6392 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4824 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6392 | msedge.exe | 31.216.144.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mega.nz |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6392 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6392 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6392 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6392 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
6392 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
6392 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6392 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6392 | msedge.exe | Misc activity | ET INFO File Sharing Related Domain in DNS Lookup (mega .nz) |
6392 | msedge.exe | Misc activity | ET INFO File Sharing Domain Observed in TLS SNI (mega .nz) |
6392 | msedge.exe | Misc activity | ET INFO Observed DNS Query to Filesharing Service (mega .co .nz) |
Process | Message |
|---|---|
powershell.exe | PID=5472 TID=9424 DismApi.dll: Host machine information: OS Version=10.0.19045, Running architecture=amd64, Number of processors=4 - DismInitializeInternal
|
powershell.exe | PID=5472 TID=9424 DismApi.dll: Parent process command line: "powershell.exe" -NoLogo -NonInteractive -NoProfile -ExecutionPolicy Bypass -Command - - DismInitializeInternal
|
powershell.exe | PID=5472 TID=9424 DismApi.dll: <----- Starting DismApi.dll session -----> - DismInitializeInternal
|
powershell.exe | PID=5472 TID=9424 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=5472 TID=9424 DismApi.dll: - DismInitializeInternal
|
powershell.exe | PID=5472 TID=9424 DismApi.dll: API Version 10.0.19041.3758 - DismInitializeInternal
|
powershell.exe | PID=5472 TID=9424 Enter DismInitializeInternal - DismInitializeInternal
|
powershell.exe | PID=5472 TID=9424 Input parameters: LogLevel: 2, LogFilePath: C:\WINDOWS\Logs\DISM\dism.log, ScratchDirectory: (null) - DismInitializeInternal
|
powershell.exe | PID=5472 TID=9424 Initialized SessionTable - DismInitializeInternal
|
powershell.exe | PID=5472 TID=9424 Lookup in table by path failed for: DummyPath-2BA51B78-C7F7-4910-B99D-BB7345357CDC - CTransactionalImageTable::LookupImagePath
|