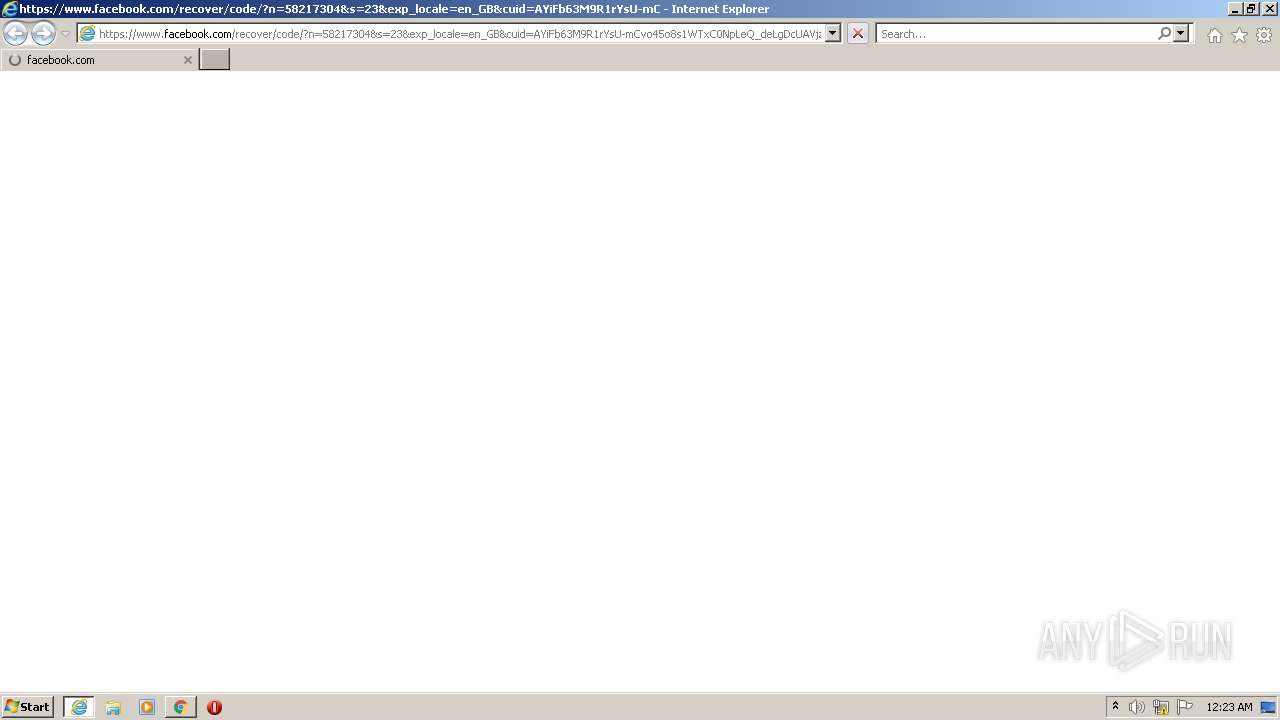
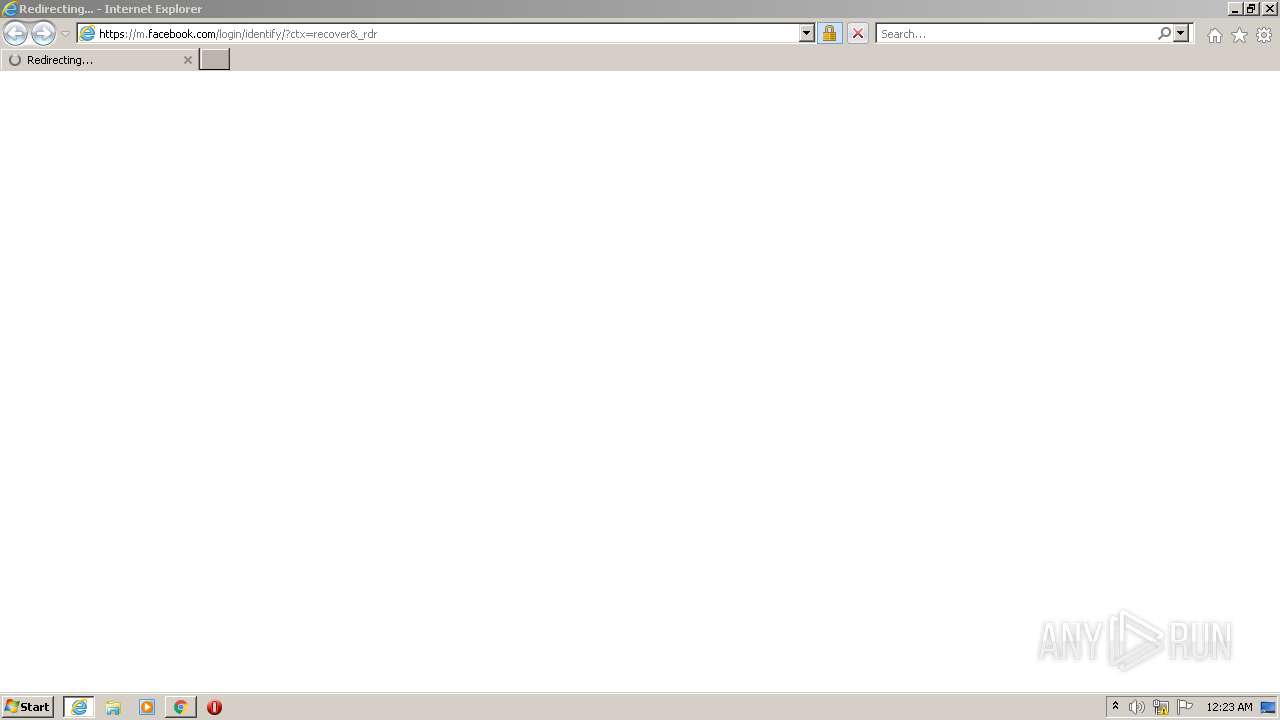
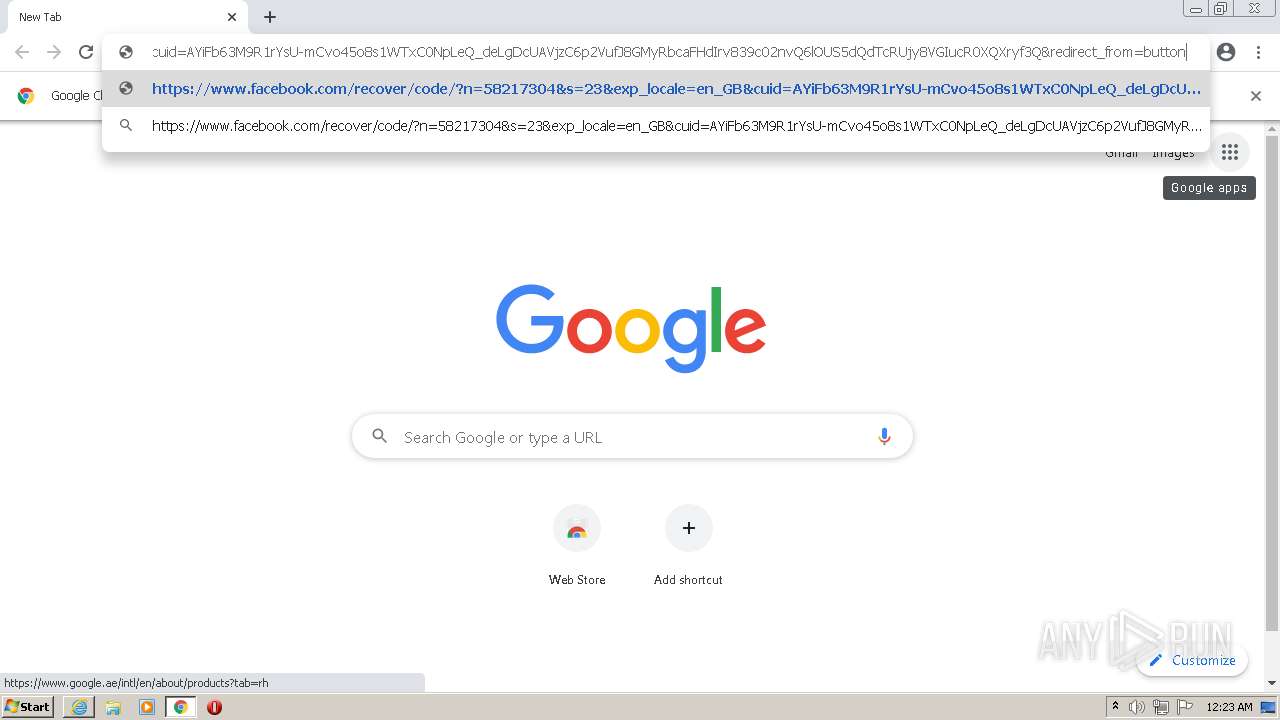
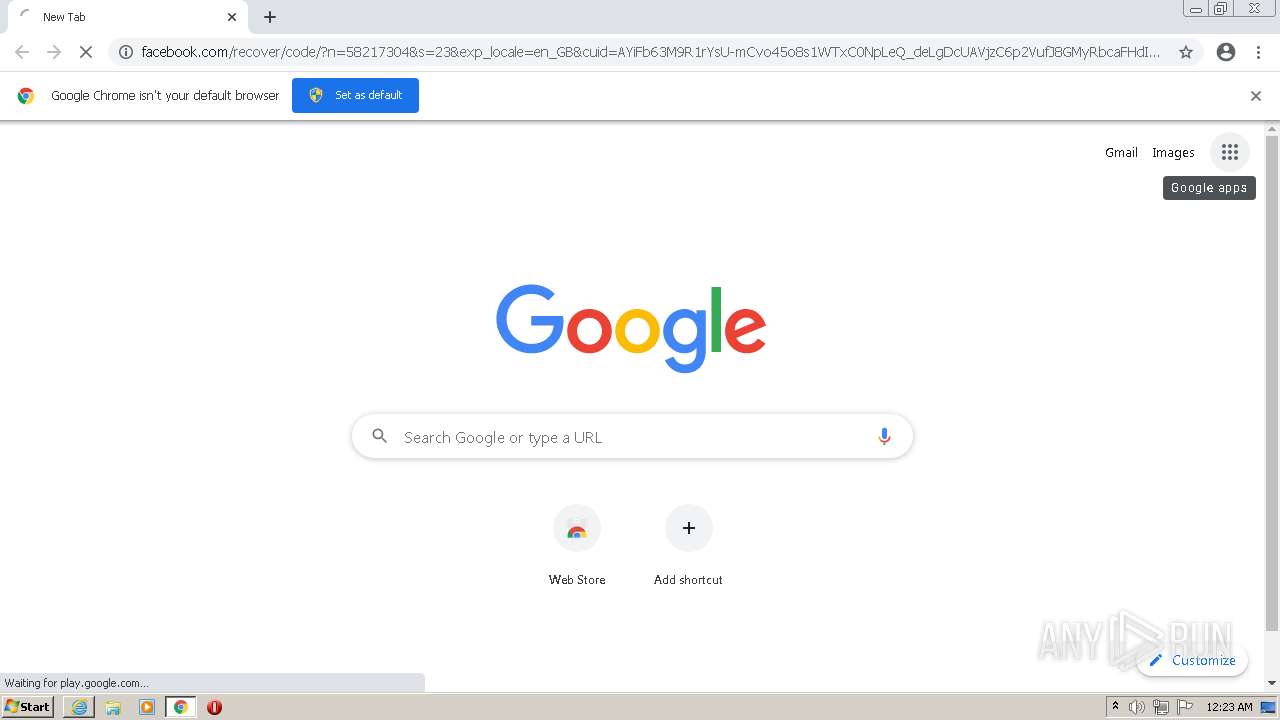
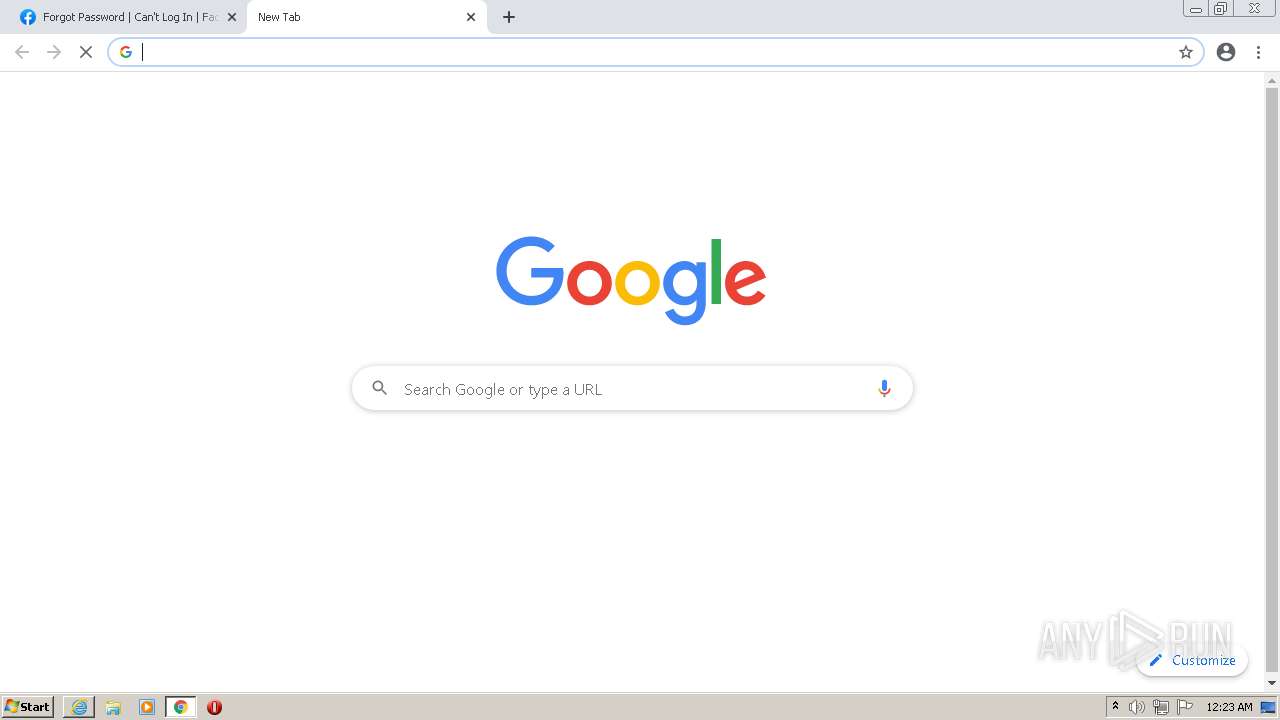
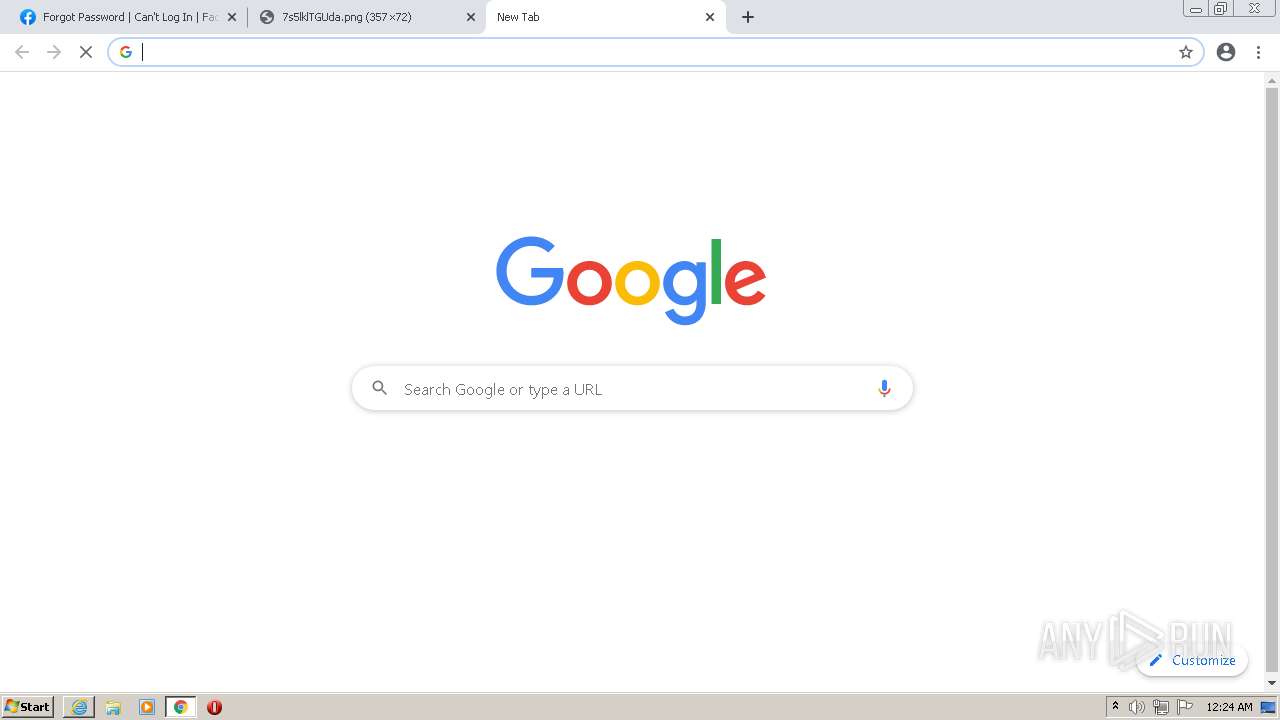
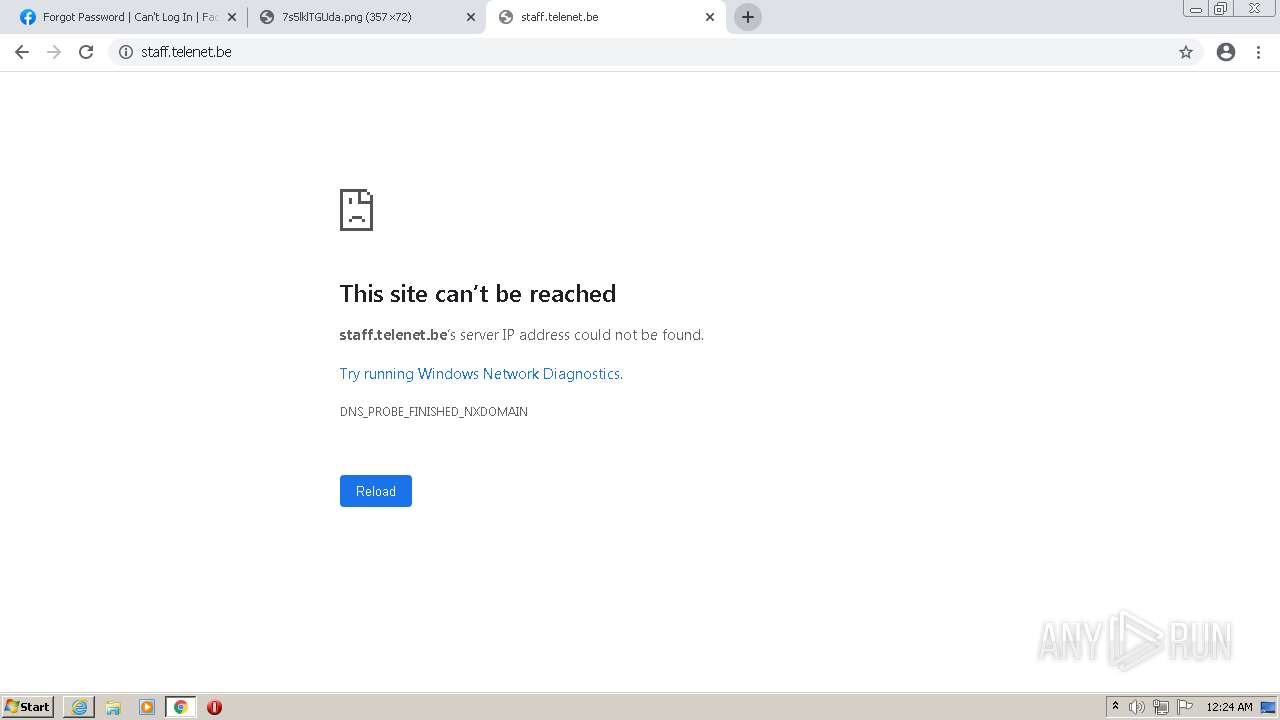
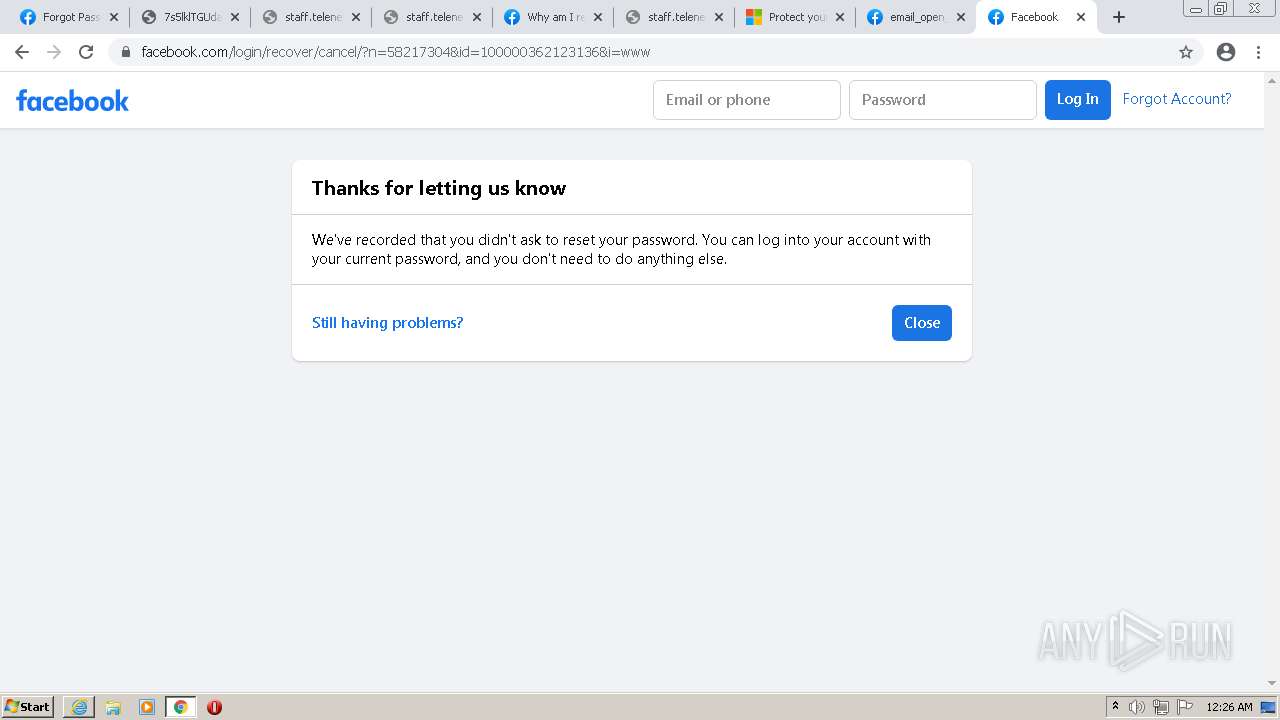
| URL: | https://www.facebook.com/recover/code/?n=58217304&s=23&exp_locale=en_GB&cuid=AYiFb63M9R1rYsU-mCvo45o8s1WTxC0NpLeQ_deLgDcUAVjzC6p2VufJ8GMyRbcaFHdIrv839c02nvQ6lOUS5dQdTcRUjy8VGIucR0XQXryf3Q&redirect_from=button |
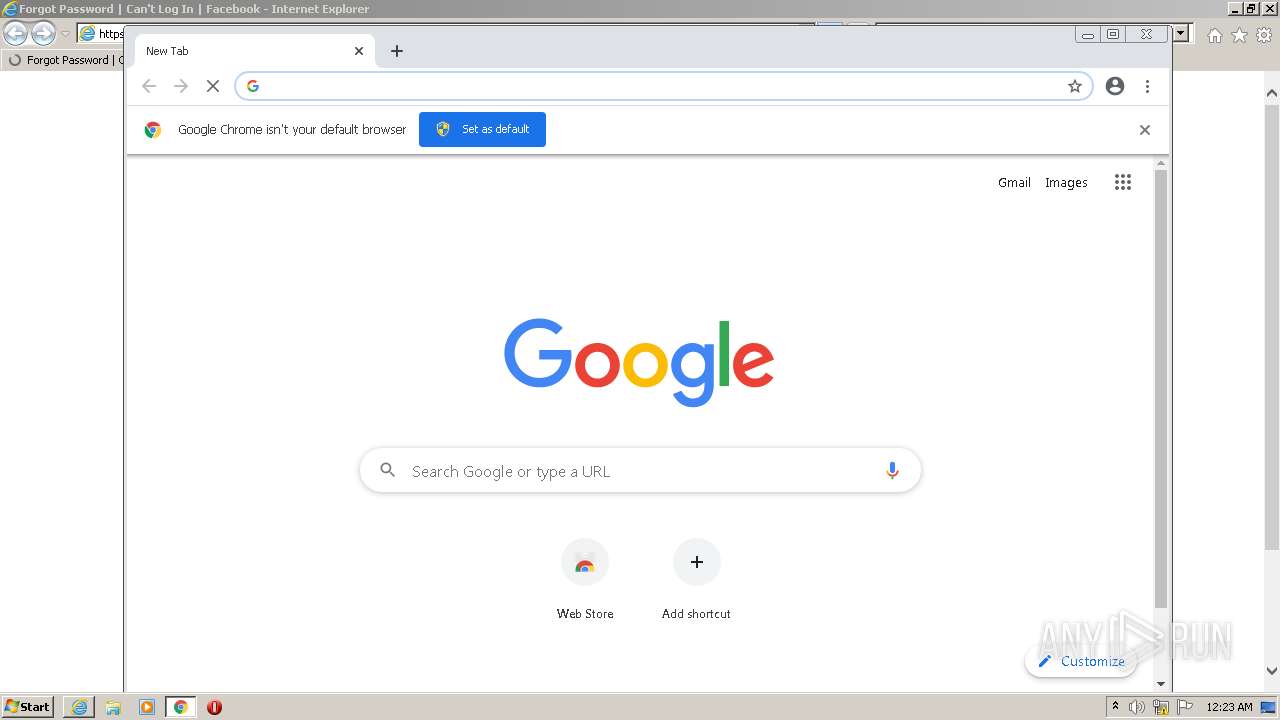
| Full analysis: | https://app.any.run/tasks/646bd61f-89e4-4a92-a355-c19fe6f1ef2e |
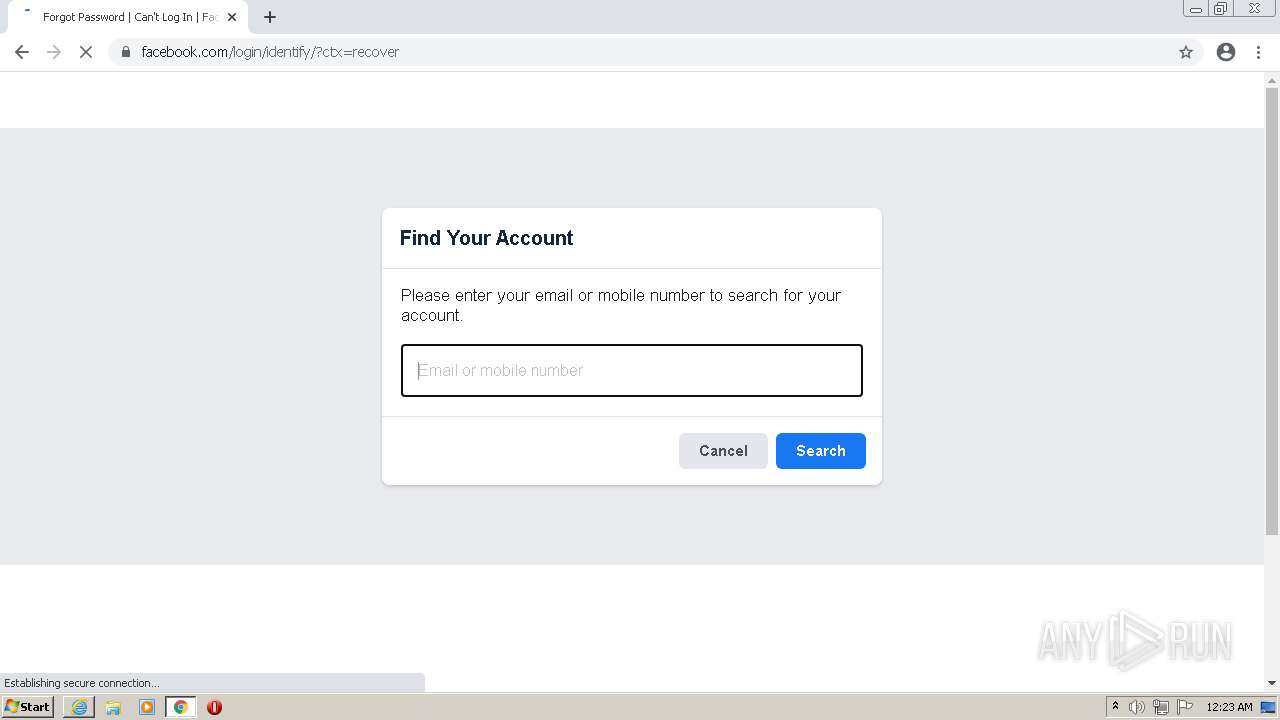
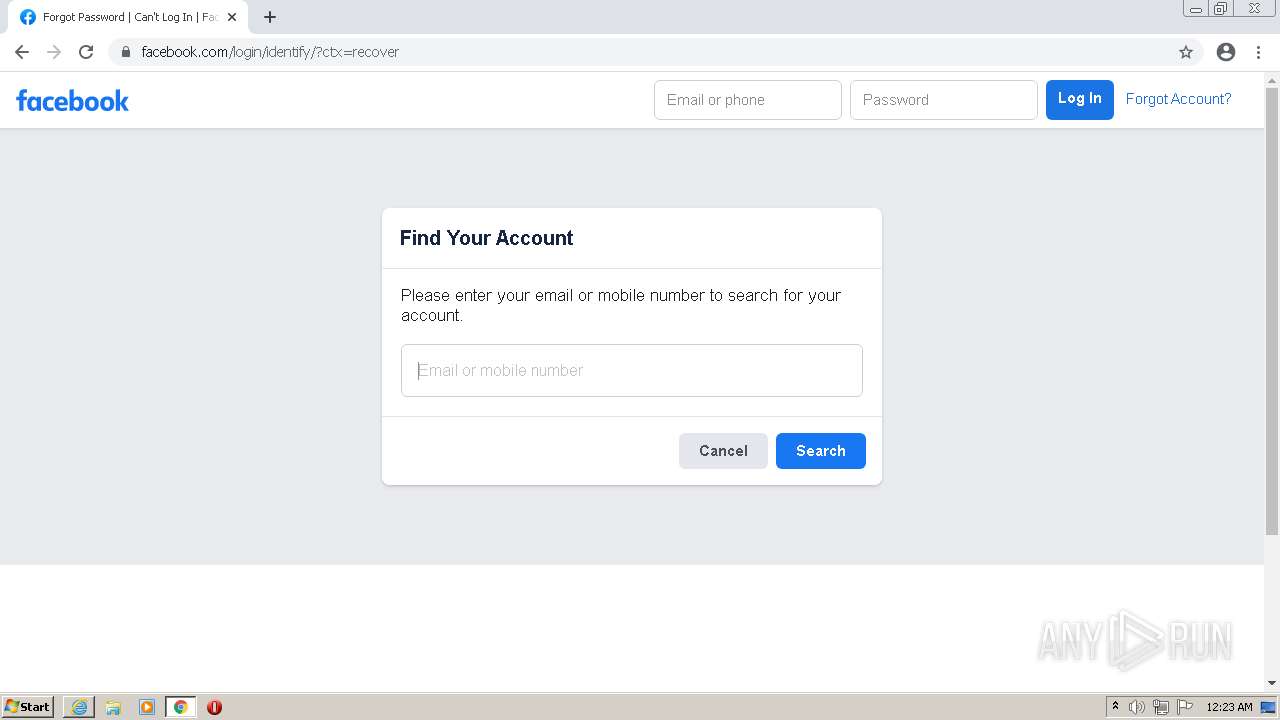
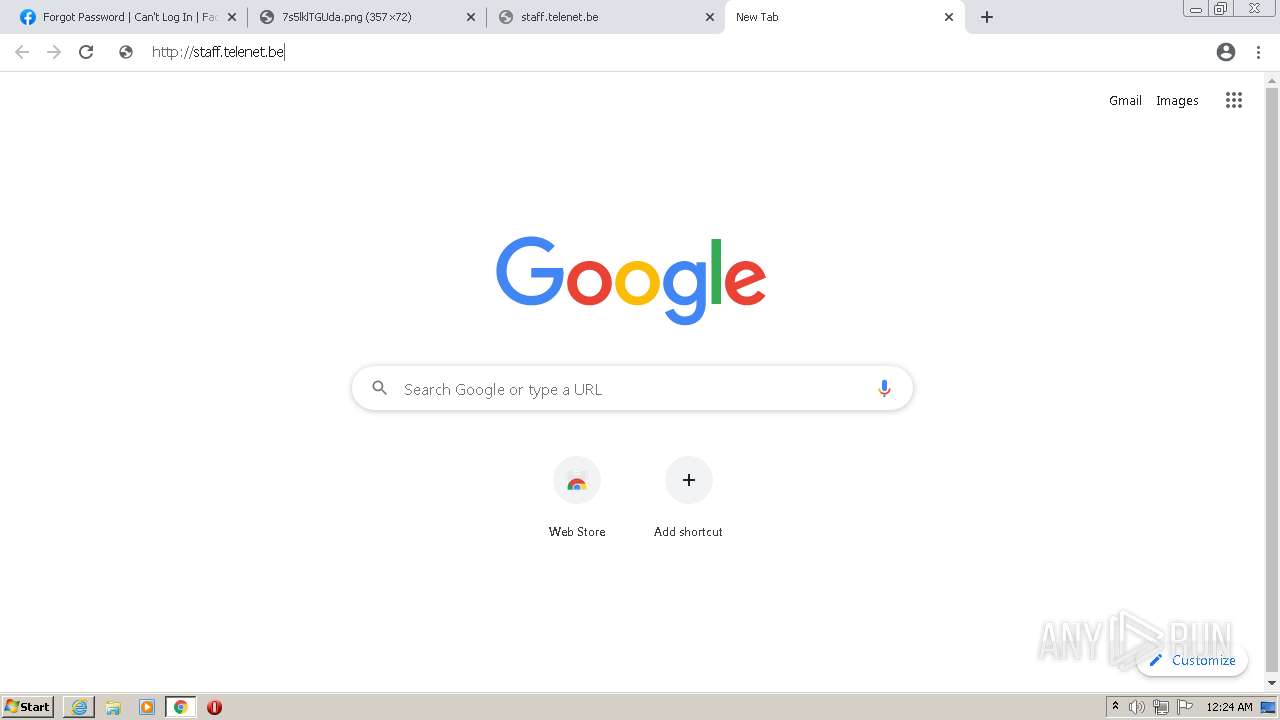
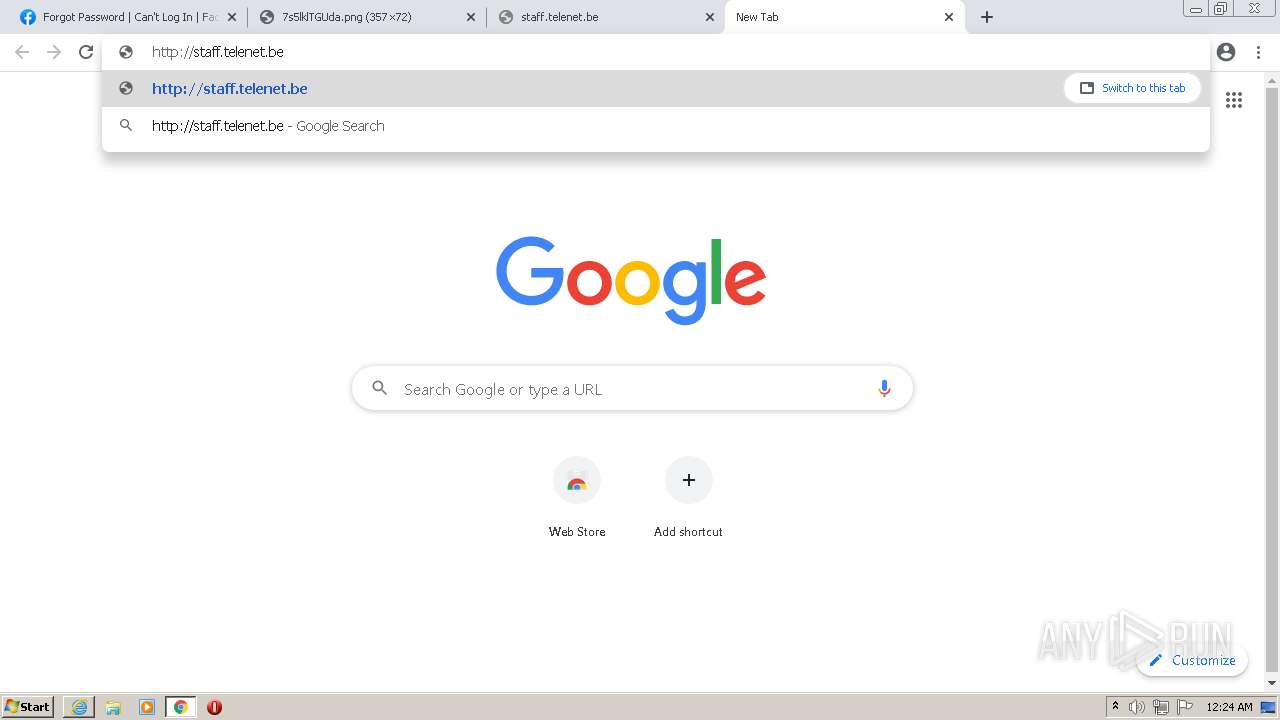
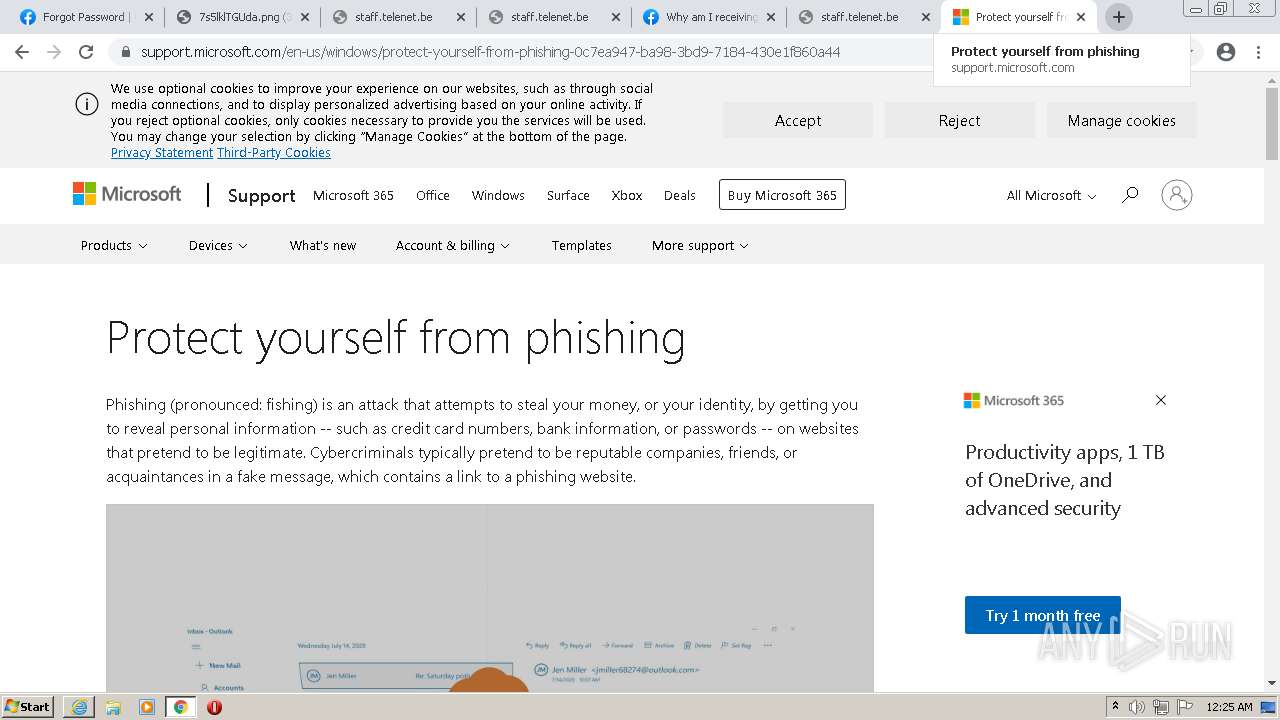
| Verdict: | Malicious activity |
| Analysis date: | April 03, 2022, 23:23:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 81C8292D623586B1B6E3C74F7C82A322 |
| SHA1: | 7412D5A7099C4D633CB13BAAD5E984AC1F208BCE |
| SHA256: | 1892F6D3160240F7D0DD038536A007D9D7EAF1CD872C22D64C22DAB2ED2BB9E4 |
| SSDEEP: | 6:2OLYX2yhPlitreQlidmcGVPXioIRmdUxlVQn:2+egZ3V6oymklOn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1772)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2440)
INFO
Changes internet zones settings
- iexplore.exe (PID: 4060)
Checks supported languages
- iexplore.exe (PID: 4060)
- iexplore.exe (PID: 1772)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 2700)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 1372)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 312)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 556)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 300)
- chrome.exe (PID: 1952)
- chrome.exe (PID: 2396)
- chrome.exe (PID: 2880)
- chrome.exe (PID: 1852)
- chrome.exe (PID: 3156)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 780)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 2664)
- chrome.exe (PID: 876)
- chrome.exe (PID: 964)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 1836)
- chrome.exe (PID: 2624)
- chrome.exe (PID: 2916)
- chrome.exe (PID: 1580)
- chrome.exe (PID: 3108)
- chrome.exe (PID: 2816)
- chrome.exe (PID: 1844)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 2184)
- chrome.exe (PID: 1776)
- chrome.exe (PID: 984)
- chrome.exe (PID: 1624)
- chrome.exe (PID: 2000)
- chrome.exe (PID: 2960)
- chrome.exe (PID: 2352)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 2656)
- chrome.exe (PID: 3072)
- chrome.exe (PID: 1972)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 1000)
- chrome.exe (PID: 4072)
- chrome.exe (PID: 3760)
- chrome.exe (PID: 2356)
- chrome.exe (PID: 3804)
- chrome.exe (PID: 2748)
- chrome.exe (PID: 4032)
- chrome.exe (PID: 1852)
- chrome.exe (PID: 1688)
- chrome.exe (PID: 848)
- chrome.exe (PID: 2004)
- chrome.exe (PID: 1876)
- chrome.exe (PID: 3028)
- chrome.exe (PID: 2900)
- chrome.exe (PID: 4020)
- chrome.exe (PID: 756)
- chrome.exe (PID: 3468)
- chrome.exe (PID: 3280)
- chrome.exe (PID: 2276)
- chrome.exe (PID: 1188)
Reads the computer name
- iexplore.exe (PID: 4060)
- iexplore.exe (PID: 1772)
- chrome.exe (PID: 2440)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 3060)
- chrome.exe (PID: 2176)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 2408)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 2656)
Application launched itself
- iexplore.exe (PID: 4060)
- chrome.exe (PID: 2440)
Reads settings of System Certificates
- iexplore.exe (PID: 1772)
- chrome.exe (PID: 3140)
- iexplore.exe (PID: 4060)
Reads internet explorer settings
- iexplore.exe (PID: 1772)
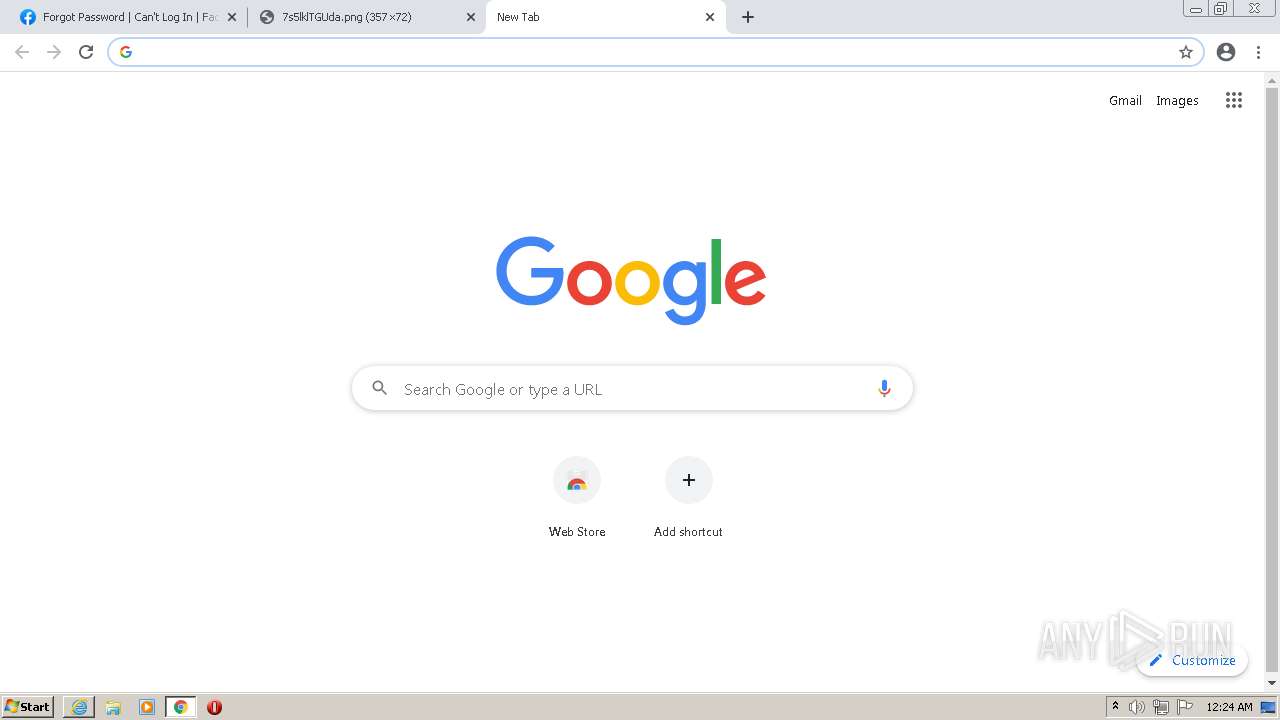
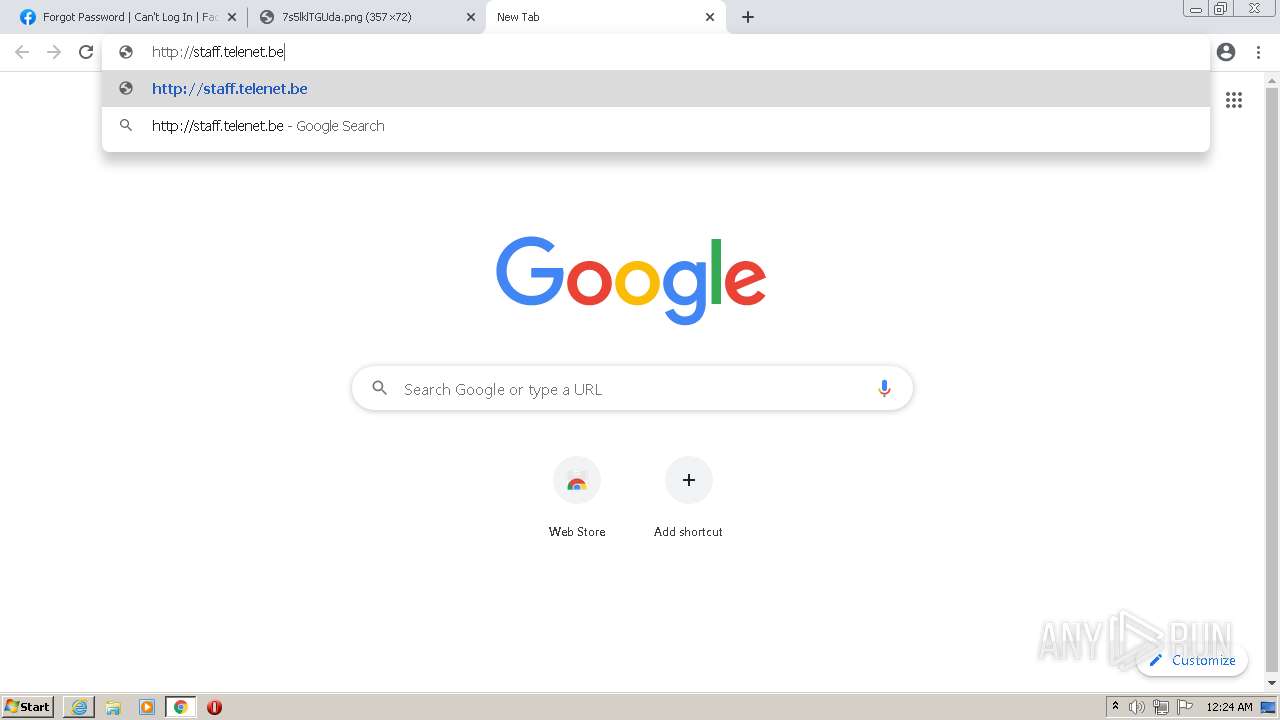
Manual execution by user
- chrome.exe (PID: 2440)
Reads the hosts file
- chrome.exe (PID: 2440)
- chrome.exe (PID: 3140)
Checks Windows Trust Settings
- iexplore.exe (PID: 1772)
- iexplore.exe (PID: 4060)
Creates files in the user directory
- iexplore.exe (PID: 1772)
- iexplore.exe (PID: 4060)
Reads the date of Windows installation
- chrome.exe (PID: 2408)
Adds / modifies Windows certificates
- iexplore.exe (PID: 4060)
Changes settings of System certificates
- iexplore.exe (PID: 4060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
104
Monitored processes
68
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17086745640936301177,18436867852176995540,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3400 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17086745640936301177,18436867852176995540,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1936 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,17086745640936301177,18436867852176995540,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2928 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,17086745640936301177,18436867852176995540,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=4272 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,17086745640936301177,18436867852176995540,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3424 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,17086745640936301177,18436867852176995540,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2868 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,17086745640936301177,18436867852176995540,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2952 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,17086745640936301177,18436867852176995540,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2820 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,17086745640936301177,18436867852176995540,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3300 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1040,17086745640936301177,18436867852176995540,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3920 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
30 990
Read events
30 640
Write events
340
Delete events
10
Modification events
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30951345 | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30951345 | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (4060) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
317
Text files
227
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2440 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-624A2C6C-988.pma | — | |
MD5:— | SHA256:— | |||
| 1772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\35DDEDF268117918D1D277A171D8DF7B_75D99C0EEE2BD228CAD2BA6907D7209C | binary | |
MD5:— | SHA256:— | |||
| 1772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | binary | |
MD5:— | SHA256:— | |||
| 1772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 1772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 1772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 1772 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\code[1].htm | html | |
MD5:— | SHA256:— | |||
| 1772 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\35DDEDF268117918D1D277A171D8DF7B_75D99C0EEE2BD228CAD2BA6907D7209C | der | |
MD5:— | SHA256:— | |||
| 1772 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\F9XLN80J.txt | text | |
MD5:— | SHA256:— | |||
| 1772 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\Ri9jLxJGCIO[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
118
DNS requests
79
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjg0QUFYSnN4MFUtaEQwNDZqVGRkVkFmZw/1.0.6.0_aemomkdncapdnfajjbbcbdebjljbpmpj.crx | US | — | — | whitelisted |
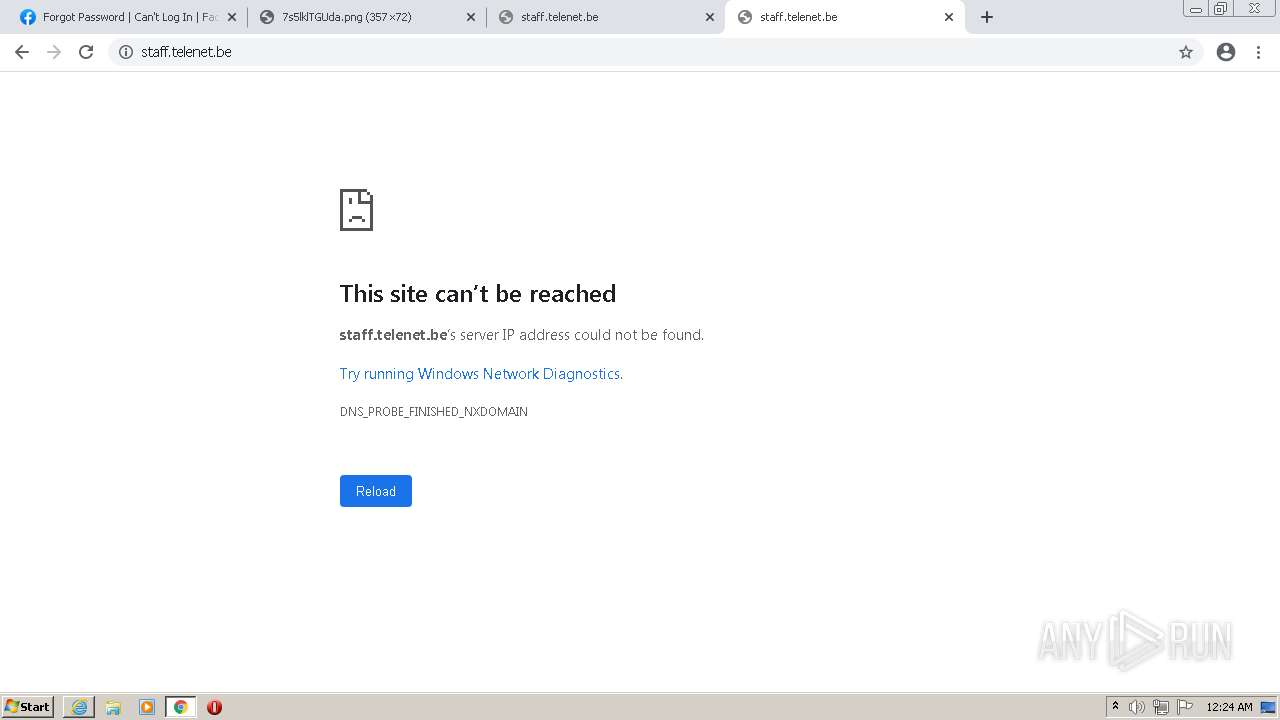
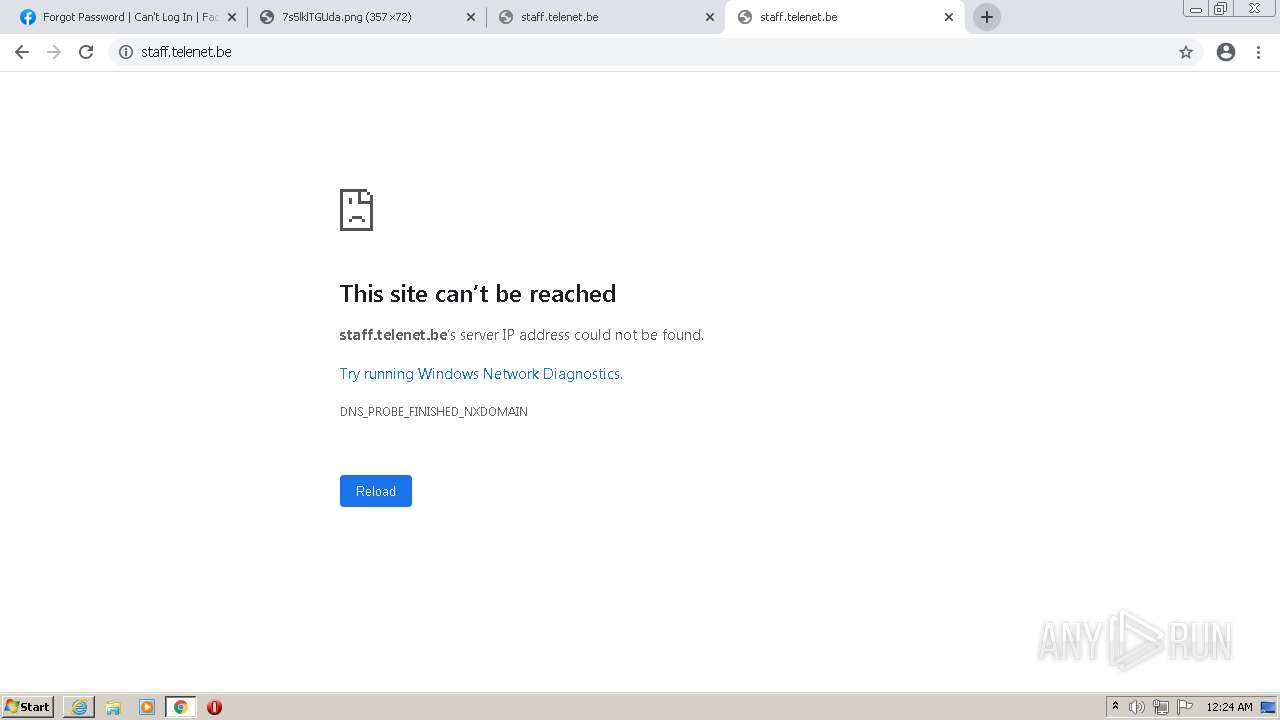
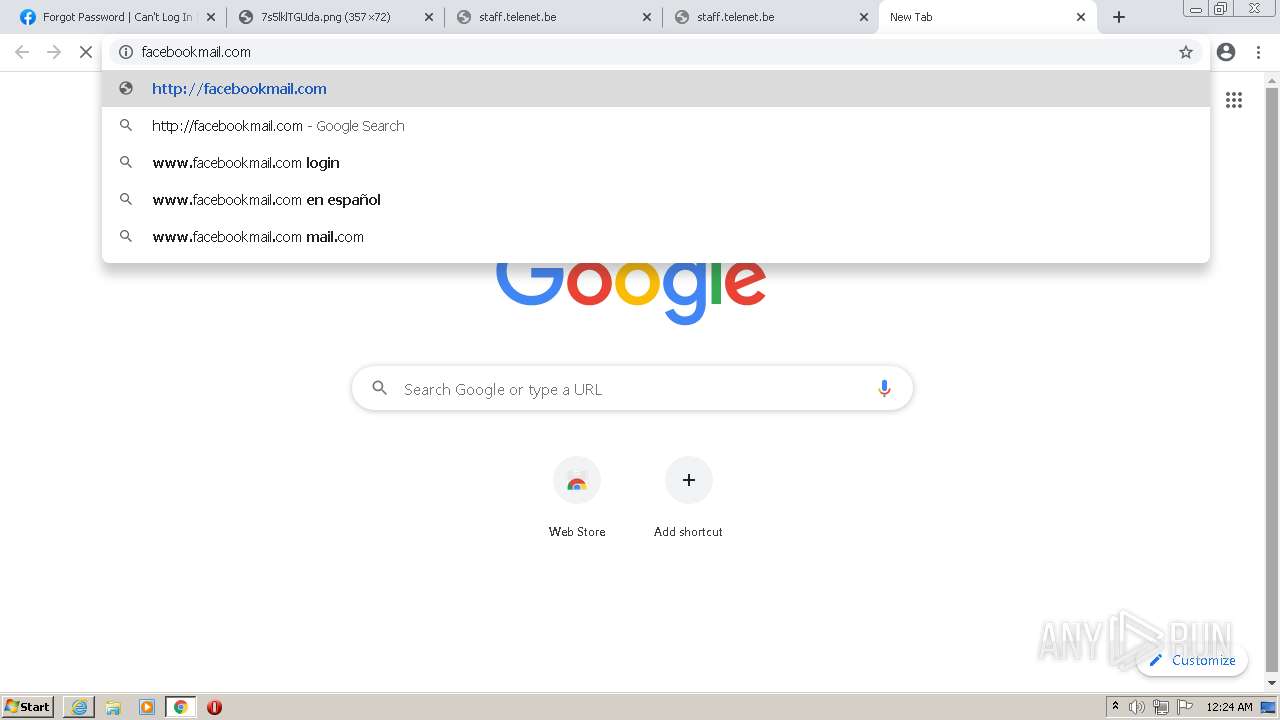
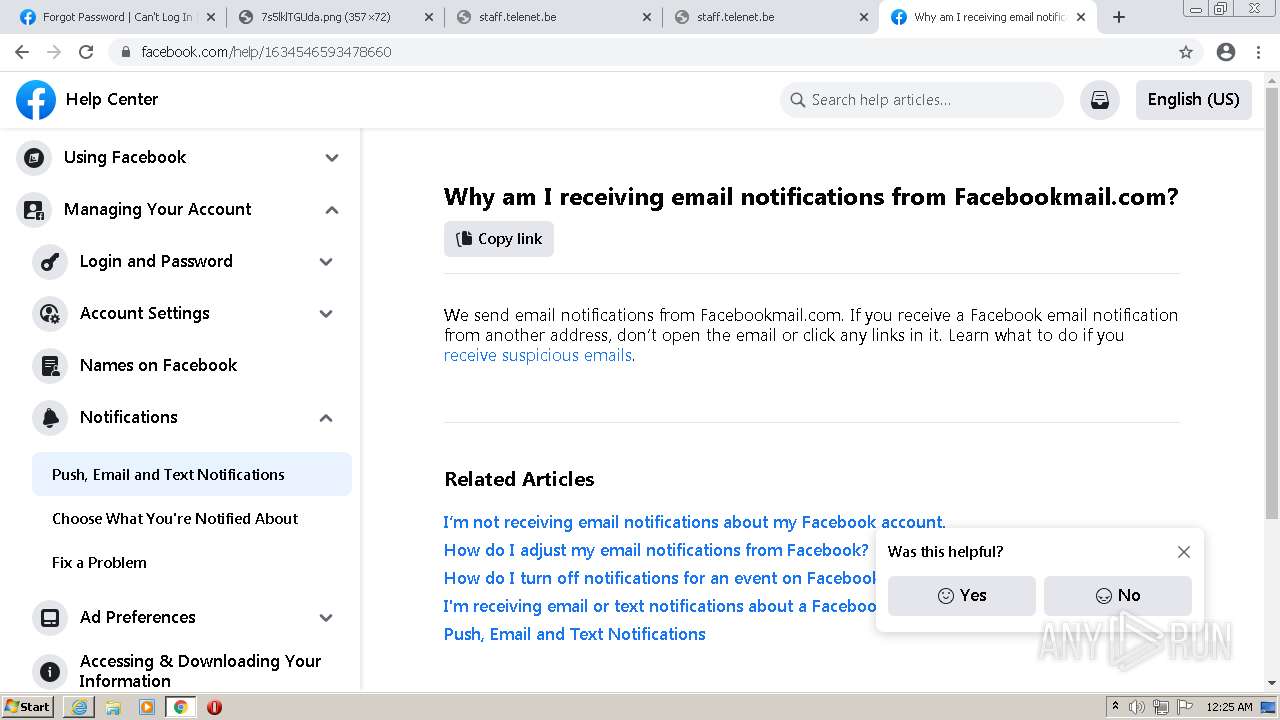
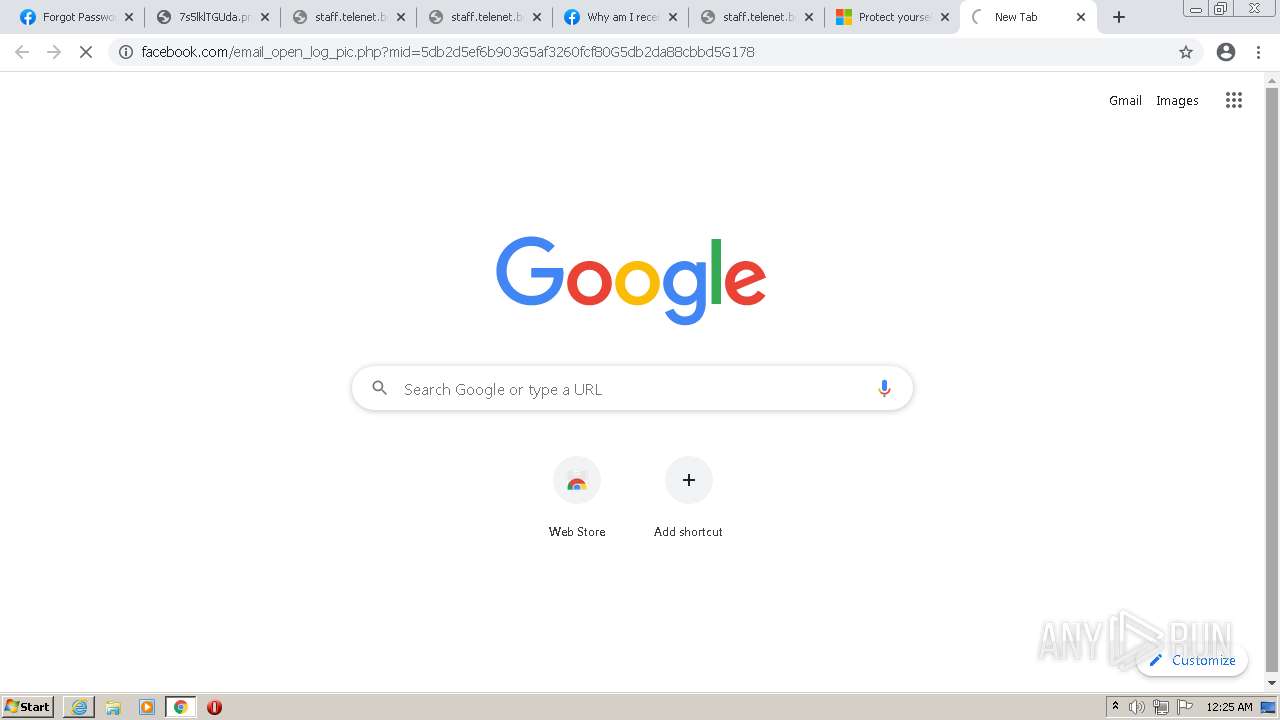
3140 | chrome.exe | GET | 301 | 31.13.92.10:80 | http://facebookmail.com/ | IE | — | — | malicious |
1772 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAx3ezgfh4BGrkBIzX6IhZQ%3D | US | der | 471 b | whitelisted |
1772 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
4060 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
4060 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
1772 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA4i%2BJVcKuAtUisfMoYeDrw%3D | US | der | 471 b | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 20.9 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 5.63 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4060 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3140 | chrome.exe | 142.250.184.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
4060 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3140 | chrome.exe | 142.250.186.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1772 | iexplore.exe | 157.240.236.35:443 | www.facebook.com | — | US | malicious |
1772 | iexplore.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
1772 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1772 | iexplore.exe | 31.13.92.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
1772 | iexplore.exe | 157.240.236.1:443 | static.xx.fbcdn.net | — | US | unknown |
3140 | chrome.exe | 142.250.186.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
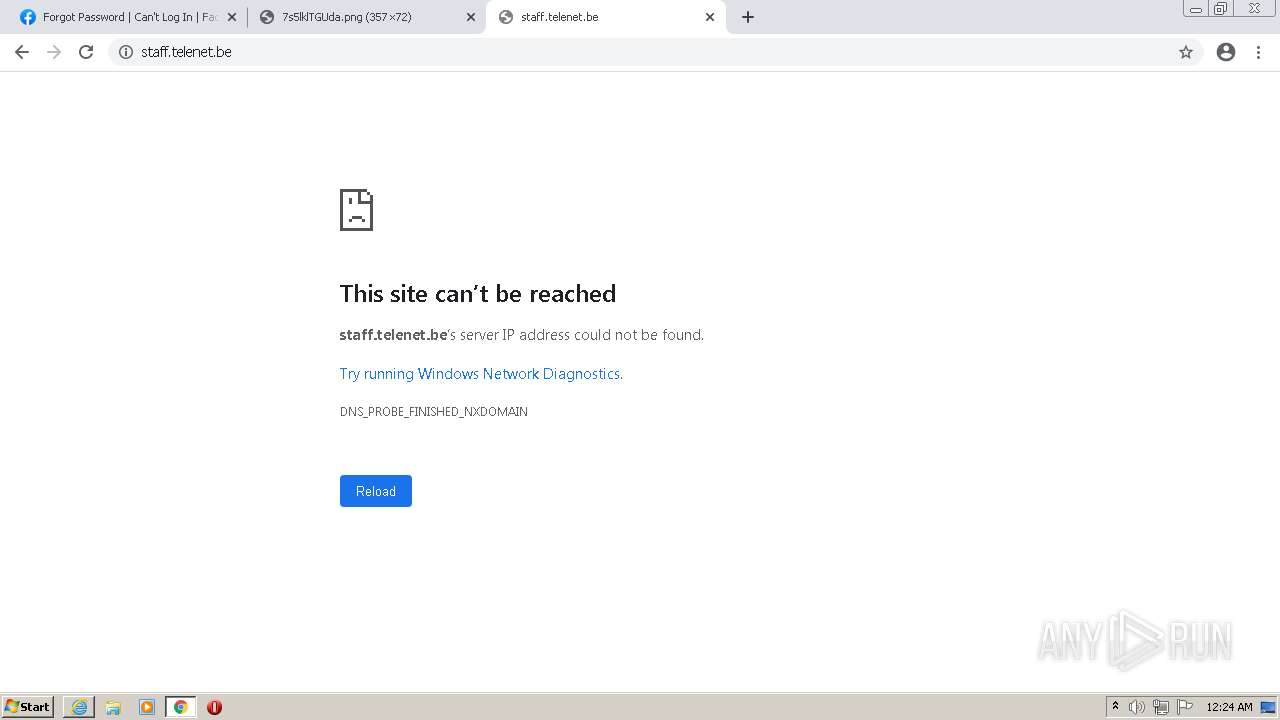
DNS requests
Domain | IP | Reputation |
|---|---|---|
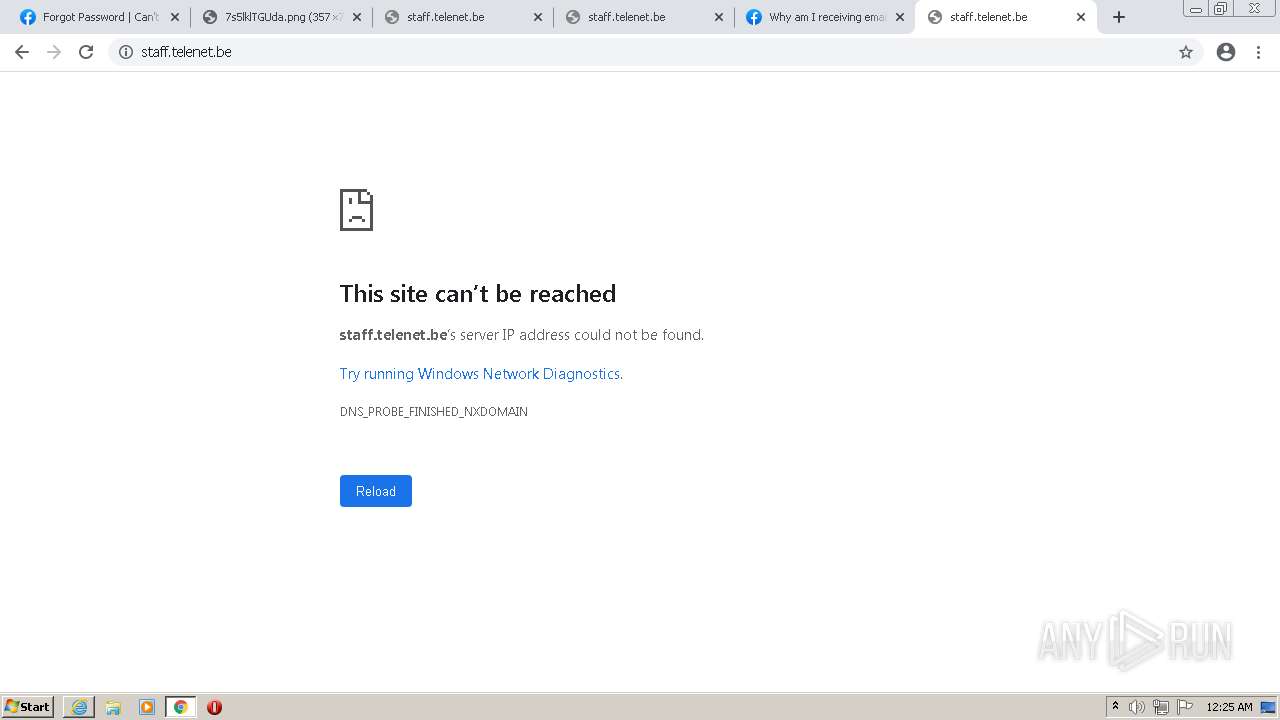
www.facebook.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
m.facebook.com |
| whitelisted |
static.xx.fbcdn.net |
| whitelisted |
facebook.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3140 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |