| File name: | utput |
| Full analysis: | https://app.any.run/tasks/0b3e8a1e-def8-435d-bf01-a9c32d76fd1b |
| Verdict: | Malicious activity |
| Analysis date: | September 16, 2021, 12:13:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B671BE6B50B0885A1F402D3451773253 |
| SHA1: | 2A0799BC9D977DA3675FAE7F2E1AF5B76D8C66F6 |
| SHA256: | 1890B0626E3E902EC1611D666A80EBFE6DCF17E2D810687CE2C145E992FB7560 |
| SSDEEP: | 196608:SICJdW1TlVeKrBFbd/yCgh1Nks9HQ8MbdYo/5HtDaFY:S9+TlIKjzarhmdNBHtaFY |
MALICIOUS
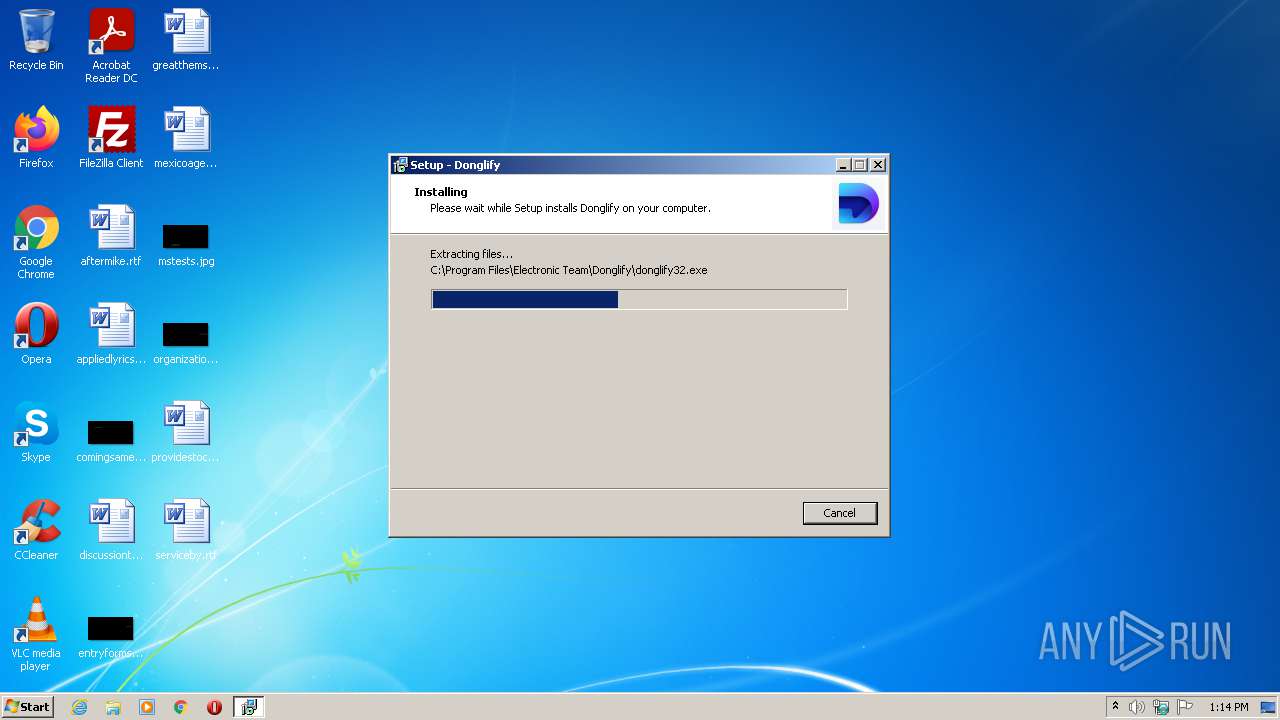
Drops executable file immediately after starts
- utput.exe (PID: 2980)
- utput.tmp (PID: 1268)
- setup_server_donglify.exe (PID: 2136)
- utput.exe (PID: 928)
- DrvInst.exe (PID: 2452)
- DrvInst.exe (PID: 3068)
- DrvInst.exe (PID: 1628)
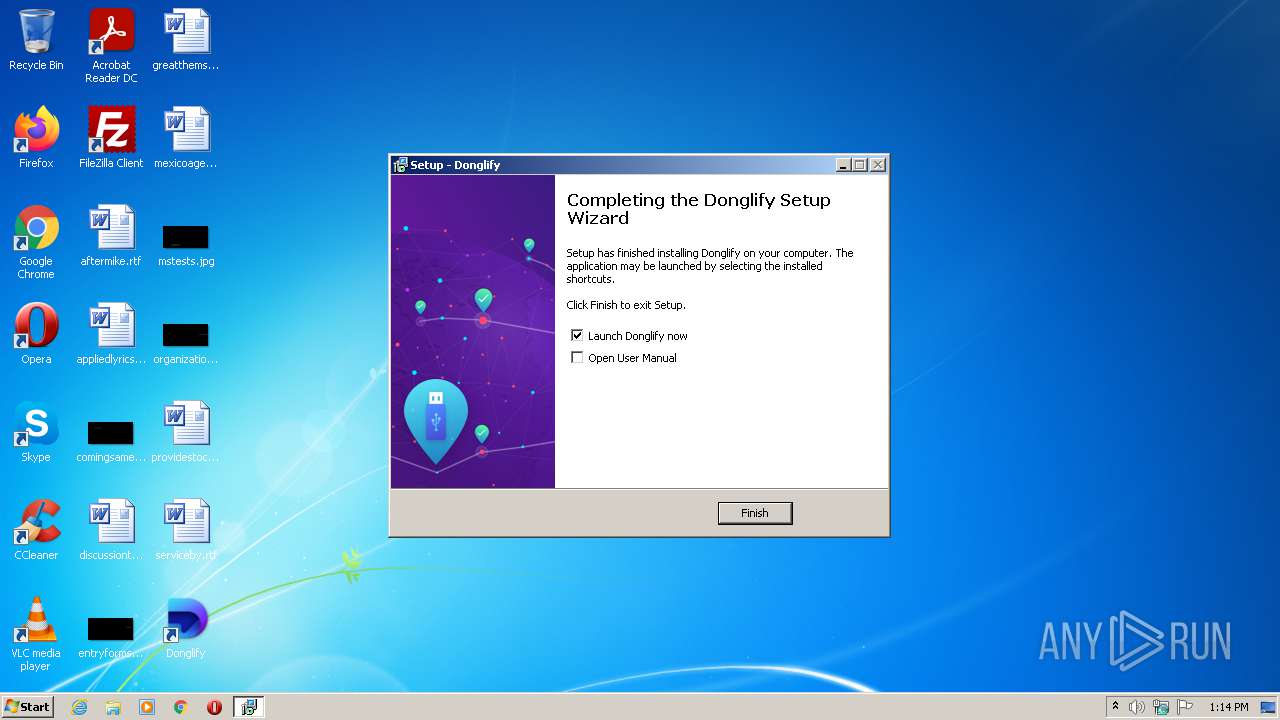
Application was dropped or rewritten from another process
- setup_server_donglify.exe (PID: 2136)
- donglify32.exe (PID: 3776)
- donglify32.exe (PID: 956)
- donglify32.exe (PID: 2840)
- donglify-gui.exe (PID: 2400)
Changes the autorun value in the registry
- utput.tmp (PID: 1268)
Loads dropped or rewritten executable
- donglify-gui.exe (PID: 2400)
SUSPICIOUS
Executable content was dropped or overwritten
- utput.exe (PID: 2980)
- utput.exe (PID: 928)
- utput.tmp (PID: 1268)
- setup_server_donglify.exe (PID: 2136)
- DrvInst.exe (PID: 2452)
- DrvInst.exe (PID: 3068)
- DrvInst.exe (PID: 1628)
Checks supported languages
- utput.tmp (PID: 3496)
- utput.exe (PID: 2980)
- utput.tmp (PID: 1268)
- utput.exe (PID: 928)
- setup_server_donglify.exe (PID: 2136)
- DrvInst.exe (PID: 2452)
- DrvInst.exe (PID: 3068)
- DrvInst.exe (PID: 1628)
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3612)
- donglify32.exe (PID: 3776)
- donglify32.exe (PID: 2840)
- donglify32.exe (PID: 956)
- donglify-gui.exe (PID: 2400)
Reads the computer name
- utput.tmp (PID: 3496)
- setup_server_donglify.exe (PID: 2136)
- DrvInst.exe (PID: 2452)
- utput.tmp (PID: 1268)
- DrvInst.exe (PID: 3068)
- DrvInst.exe (PID: 1628)
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3612)
- donglify32.exe (PID: 3776)
- donglify32.exe (PID: 956)
- donglify-gui.exe (PID: 2400)
- donglify32.exe (PID: 2840)
Drops a file that was compiled in debug mode
- utput.tmp (PID: 1268)
- setup_server_donglify.exe (PID: 2136)
- DrvInst.exe (PID: 2452)
- DrvInst.exe (PID: 3068)
- DrvInst.exe (PID: 1628)
Reads the Windows organization settings
- utput.tmp (PID: 1268)
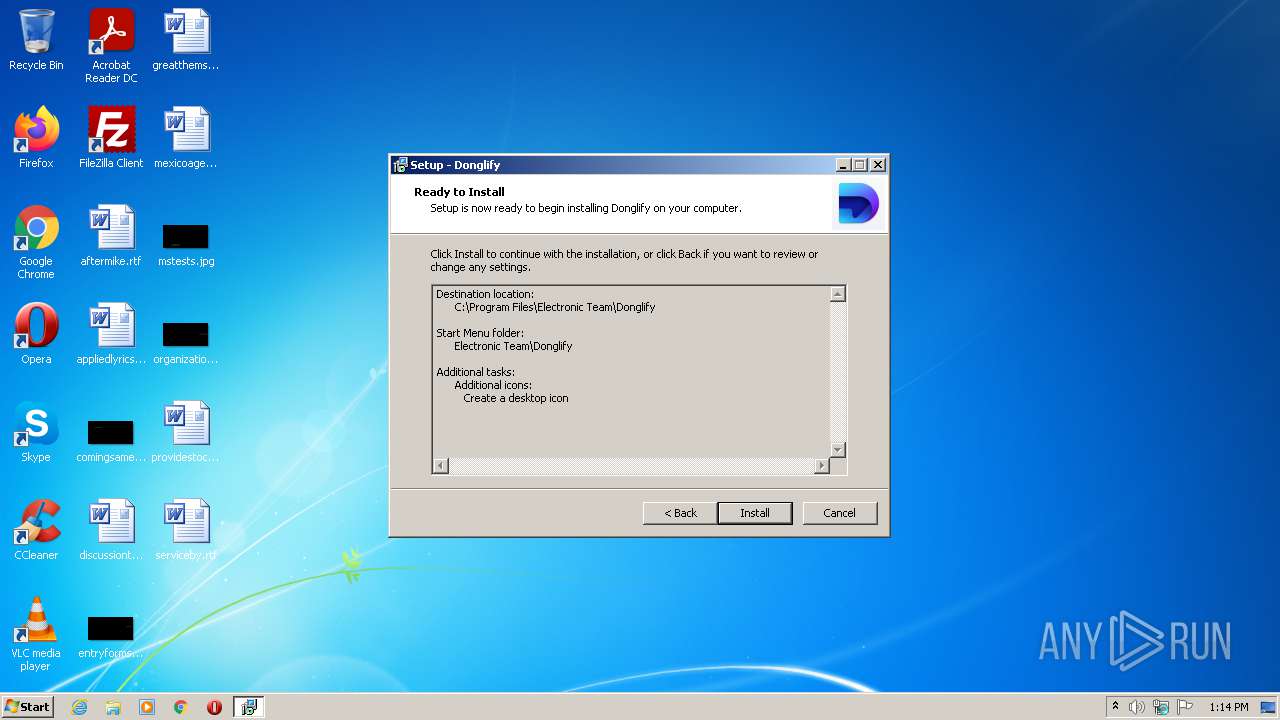
Creates a directory in Program Files
- utput.tmp (PID: 1268)
Creates files in the Windows directory
- setup_server_donglify.exe (PID: 2136)
- DrvInst.exe (PID: 2452)
- DrvInst.exe (PID: 3068)
- DrvInst.exe (PID: 1628)
- DrvInst.exe (PID: 3612)
Creates files in the driver directory
- DrvInst.exe (PID: 2452)
- setup_server_donglify.exe (PID: 2136)
- DrvInst.exe (PID: 3068)
- DrvInst.exe (PID: 1628)
Removes files from Windows directory
- DrvInst.exe (PID: 2452)
- setup_server_donglify.exe (PID: 2136)
- DrvInst.exe (PID: 3068)
- DrvInst.exe (PID: 1628)
Reads Windows owner or organization settings
- utput.tmp (PID: 1268)
Executed via COM
- DrvInst.exe (PID: 2452)
- DrvInst.exe (PID: 3068)
- DrvInst.exe (PID: 1628)
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3612)
Uses NETSH.EXE for network configuration
- utput.tmp (PID: 1268)
Creates or modifies windows services
- setup_server_donglify.exe (PID: 2136)
Reads Environment values
- netsh.exe (PID: 1560)
- netsh.exe (PID: 2696)
Executed as Windows Service
- donglify32.exe (PID: 2840)
Creates files in the program directory
- donglify32.exe (PID: 2840)
- donglify-gui.exe (PID: 2400)
Reads CPU info
- donglify32.exe (PID: 2840)
Reads internet explorer settings
- donglify-gui.exe (PID: 2400)
Reads Microsoft Outlook installation path
- donglify-gui.exe (PID: 2400)
INFO
Application was dropped or rewritten from another process
- utput.tmp (PID: 3496)
- utput.tmp (PID: 1268)
Creates files in the program directory
- utput.tmp (PID: 1268)
Dropped object may contain Bitcoin addresses
- utput.tmp (PID: 1268)
Checks Windows Trust Settings
- DrvInst.exe (PID: 2452)
- setup_server_donglify.exe (PID: 2136)
- DrvInst.exe (PID: 3068)
- DrvInst.exe (PID: 1628)
- DrvInst.exe (PID: 3612)
- DrvInst.exe (PID: 3420)
- donglify-gui.exe (PID: 2400)
Loads dropped or rewritten executable
- utput.tmp (PID: 1268)
Reads settings of System Certificates
- setup_server_donglify.exe (PID: 2136)
- DrvInst.exe (PID: 2452)
- DrvInst.exe (PID: 3068)
- DrvInst.exe (PID: 3612)
- DrvInst.exe (PID: 3420)
- donglify-gui.exe (PID: 2400)
- DrvInst.exe (PID: 1628)
Creates a software uninstall entry
- utput.tmp (PID: 1268)
Checks supported languages
- netsh.exe (PID: 1560)
- netsh.exe (PID: 2696)
Reads the computer name
- netsh.exe (PID: 2696)
- netsh.exe (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
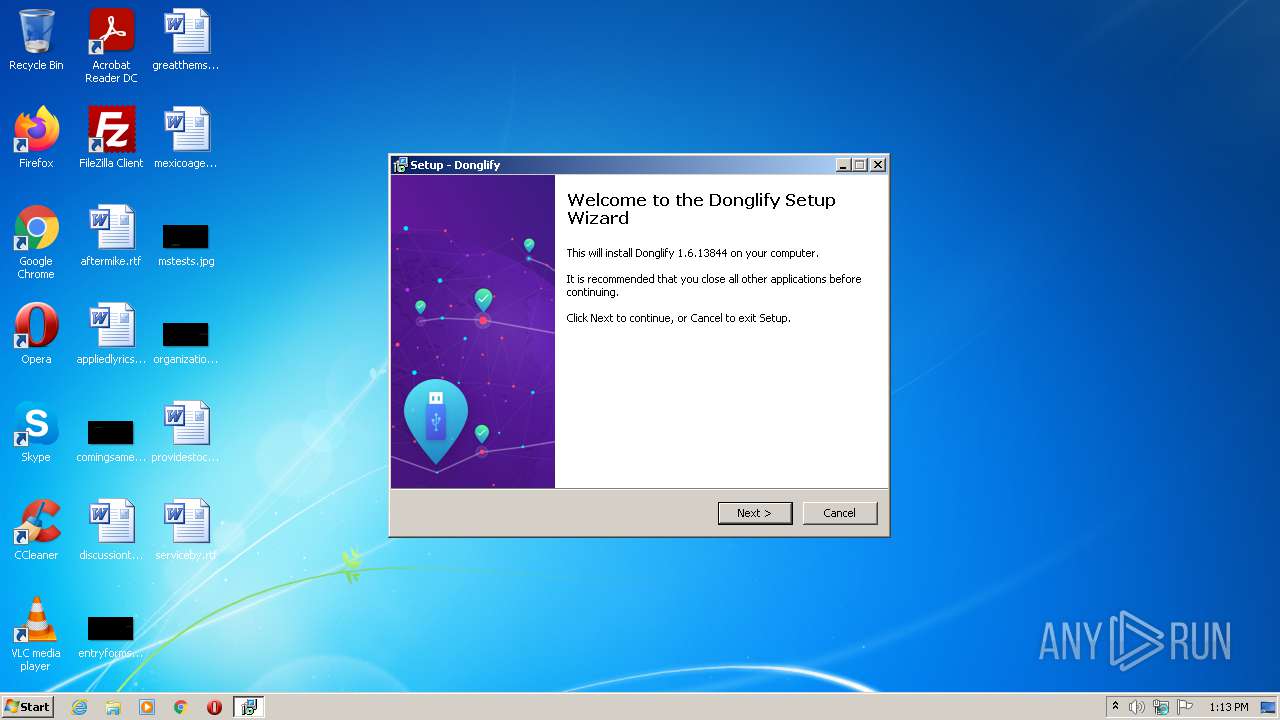
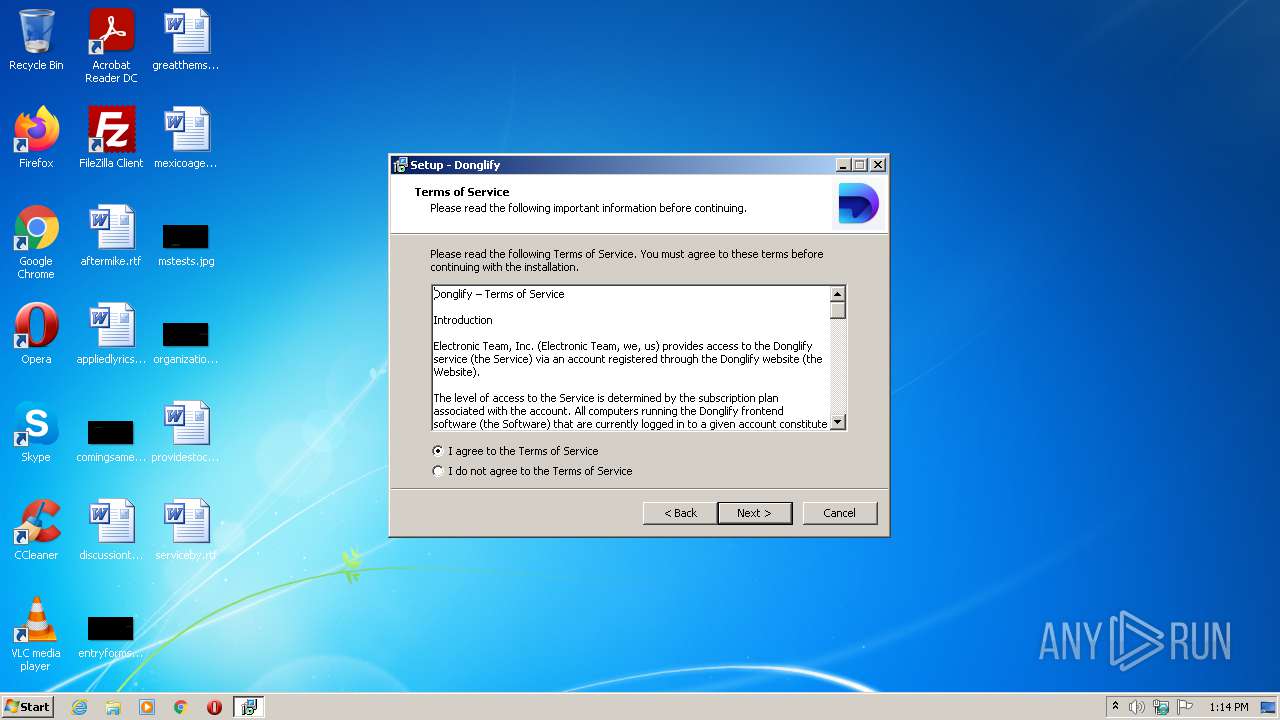
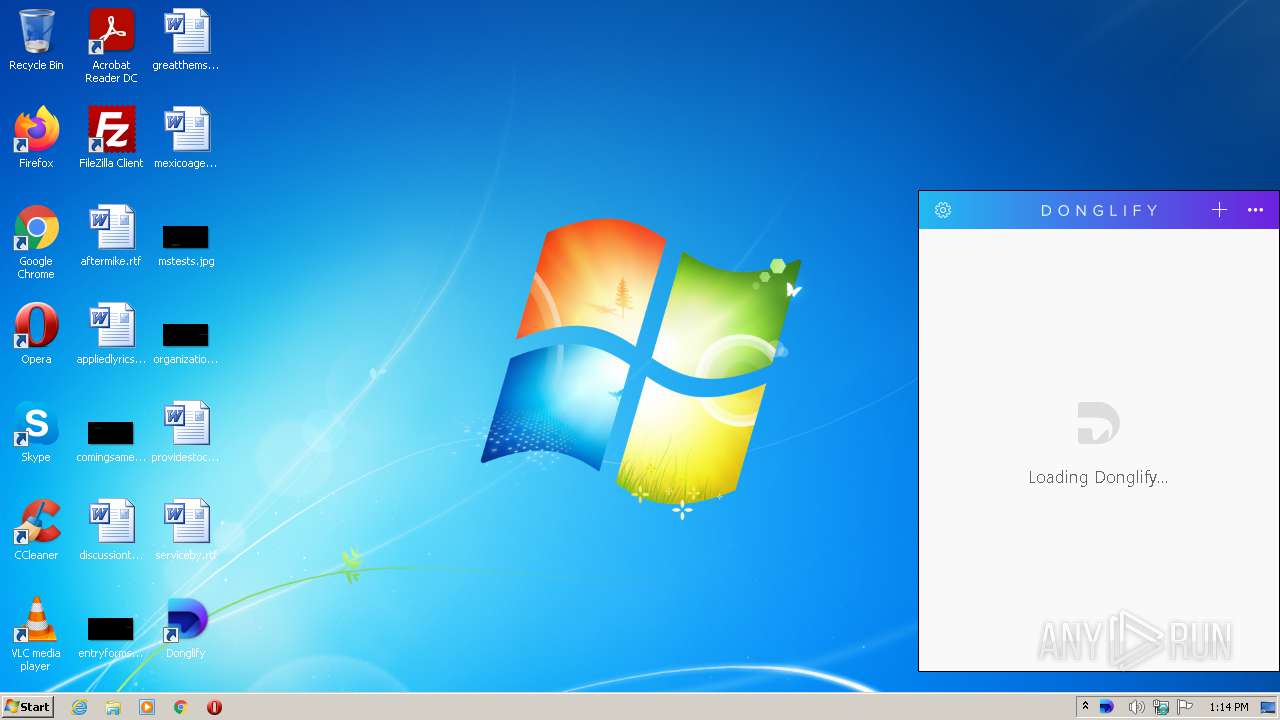
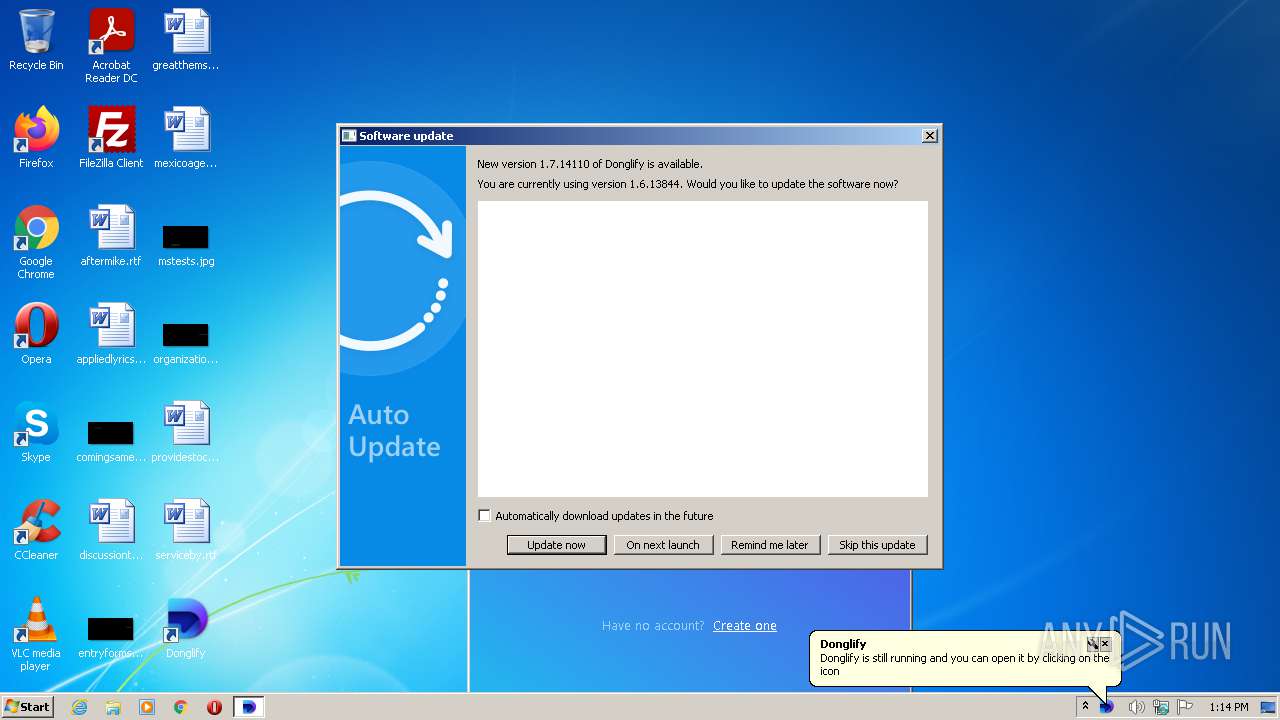
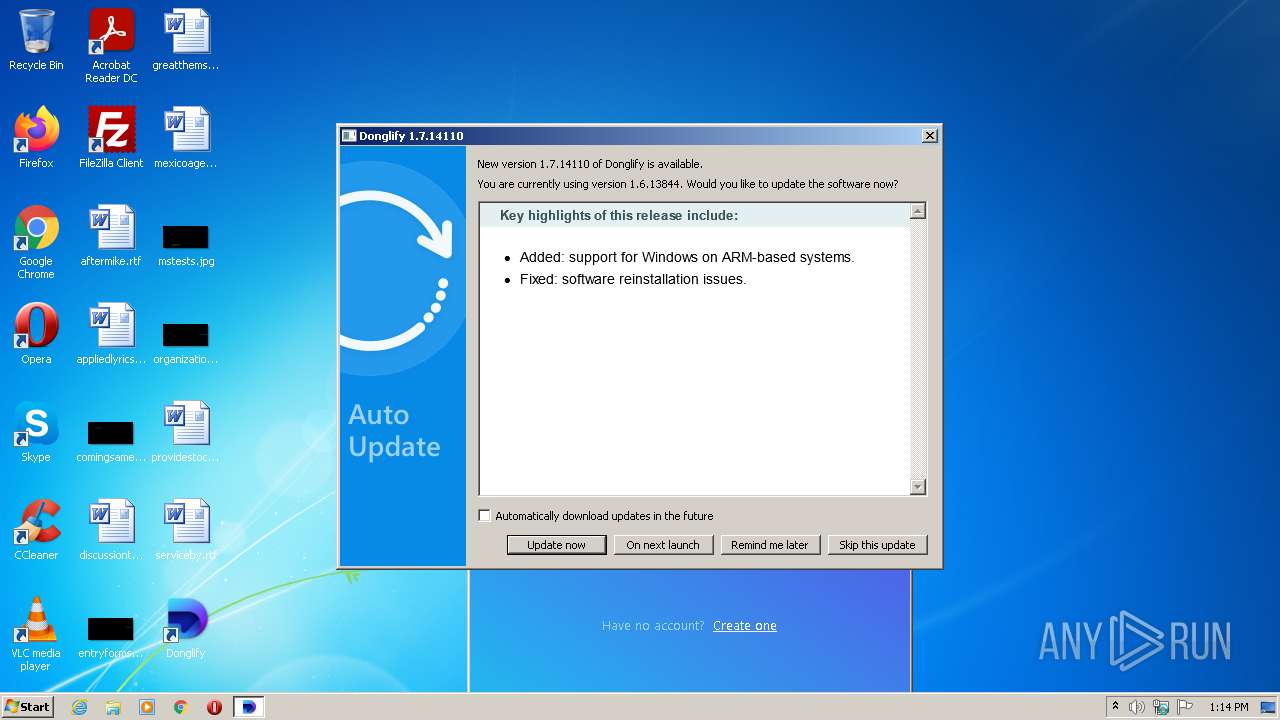
| ProductVersion: | 1.6.13844 |
|---|---|
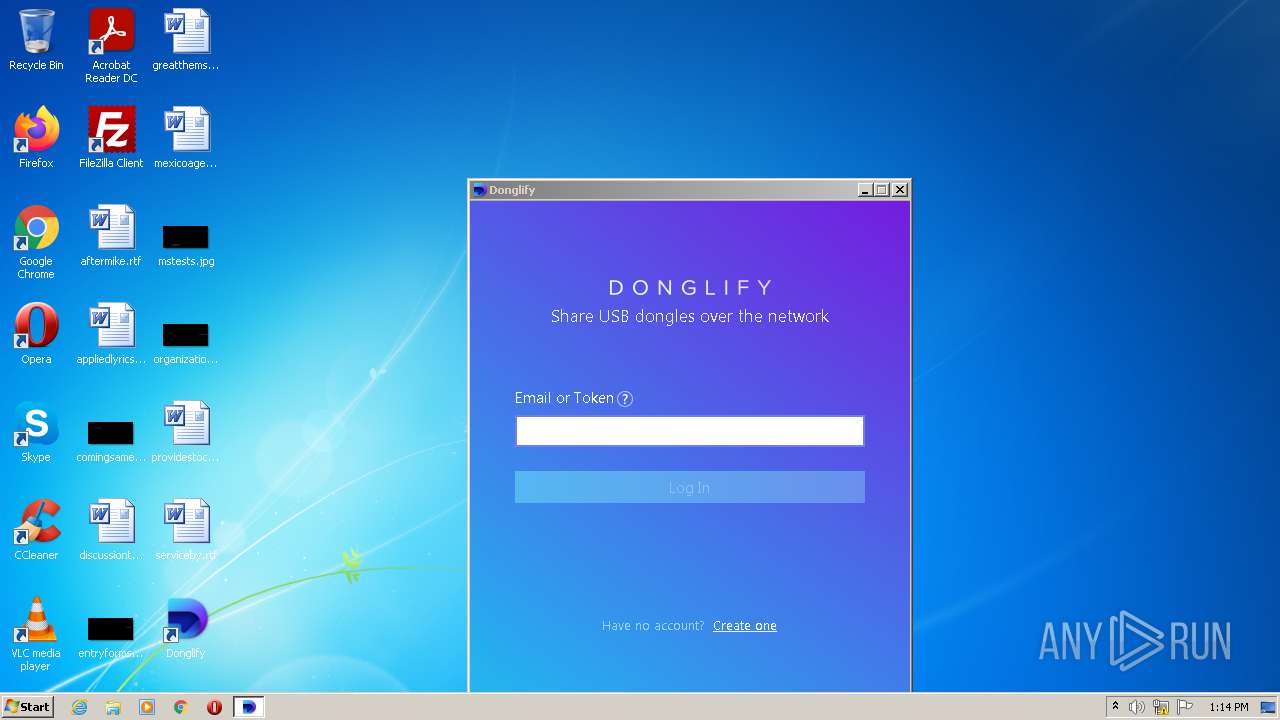
| ProductName: | Donglify |
| LegalCopyright: | Copyright 2000-2021 Electronic Team, Inc. All rights reserved. |
| FileVersion: | Donglify 1.6.13844 |
| FileDescription: | Donglify |
| CompanyName: | Electronic Team, Inc. |
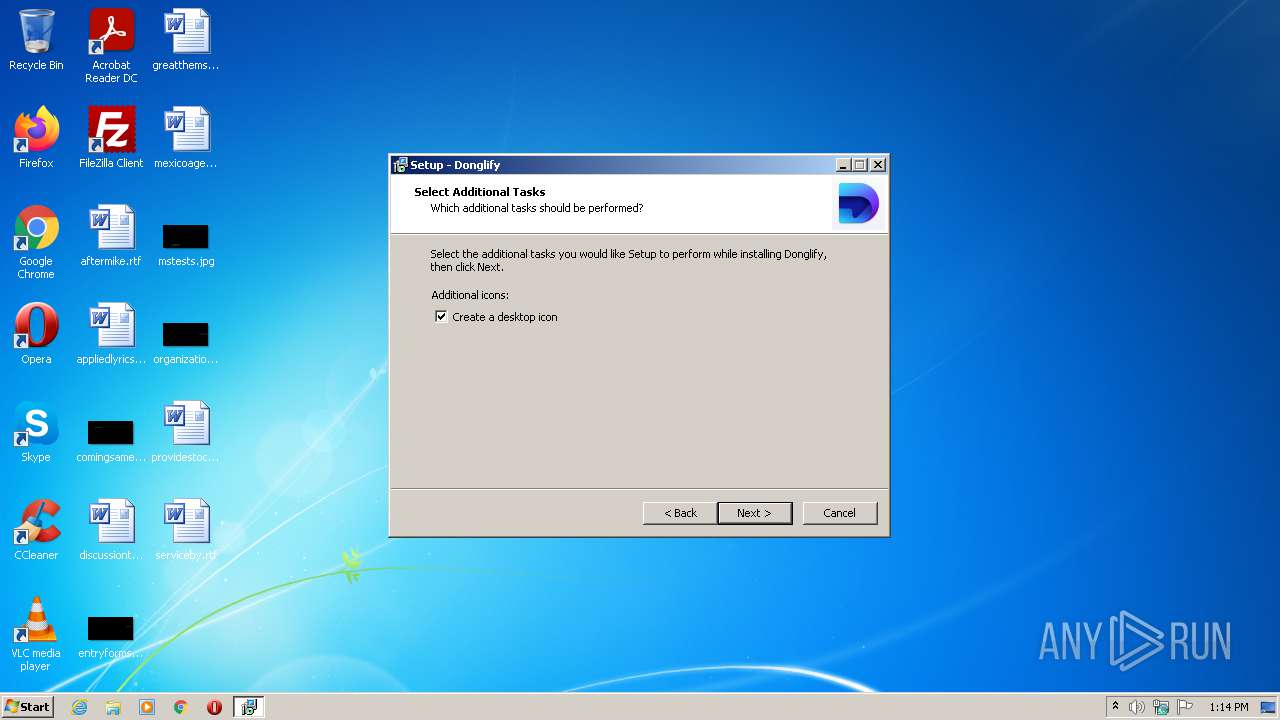
| Comments: | This installation was built with Inno Setup. |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.6.13844.0 |
| FileVersionNumber: | 1.6.13844.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | 6 |
| OSVersion: | 5 |
| EntryPoint: | 0x117dc |
| UninitializedDataSize: | - |
| InitializedDataSize: | 53760 |
| CodeSize: | 66560 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Electronic Team, Inc. |
| FileDescription: | Donglify |
| FileVersion: | Donglify 1.6.13844 |
| LegalCopyright: | Copyright 2000-2021 Electronic Team, Inc. All rights reserved. |
| ProductName: | Donglify |
| ProductVersion: | 1.6.13844 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.14821 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
61
Monitored processes
16
Malicious processes
7
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 928 | "C:\Users\admin\AppData\Local\Temp\utput.exe" /SPAWNWND=$1013C /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\utput.exe | utput.tmp | ||||||||||||
User: admin Company: Electronic Team, Inc. Integrity Level: HIGH Description: Donglify Exit code: 0 Version: Donglify 1.6.13844 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Electronic Team\Donglify\donglify32.exe" enable | C:\Program Files\Electronic Team\Donglify\donglify32.exe | — | utput.tmp | |||||||||||
User: admin Company: Electronic Team, Inc. Integrity Level: HIGH Description: Donglify Service Exit code: 4294967295 Version: 1.6.13844 Modules
| |||||||||||||||
| 1268 | "C:\Users\admin\AppData\Local\Temp\is-UU7LM.tmp\utput.tmp" /SL5="$2013E,6956686,121344,C:\Users\admin\AppData\Local\Temp\utput.exe" /SPAWNWND=$1013C /NOTIFYWND=$20138 | C:\Users\admin\AppData\Local\Temp\is-UU7LM.tmp\utput.tmp | utput.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1560 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name=Donglify_gui dir=in action=allow program="C:\Program Files\Electronic Team\Donglify\donglify-gui.exe" enable=yes | C:\Windows\system32\netsh.exe | — | utput.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1628 | DrvInst.exe "2" "211" "ROOT\SYSTEM\0001" "C:\Windows\INF\oem6.inf" "vuh.inf:Electronic.NTx86:VUHUB_Device:9.1.2285.0:vuhub" "625e1bb63" "000005C8" "000005E4" "000005E8" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Electronic Team\Donglify\drivers\USB\nt6x32\setup_server_donglify.exe" | C:\Program Files\Electronic Team\Donglify\drivers\USB\nt6x32\setup_server_donglify.exe | utput.tmp | ||||||||||||
User: admin Company: Electronic Team, Inc. Integrity Level: HIGH Description: Setup USB drivers Exit code: 0 Version: 2.6.2 Modules
| |||||||||||||||
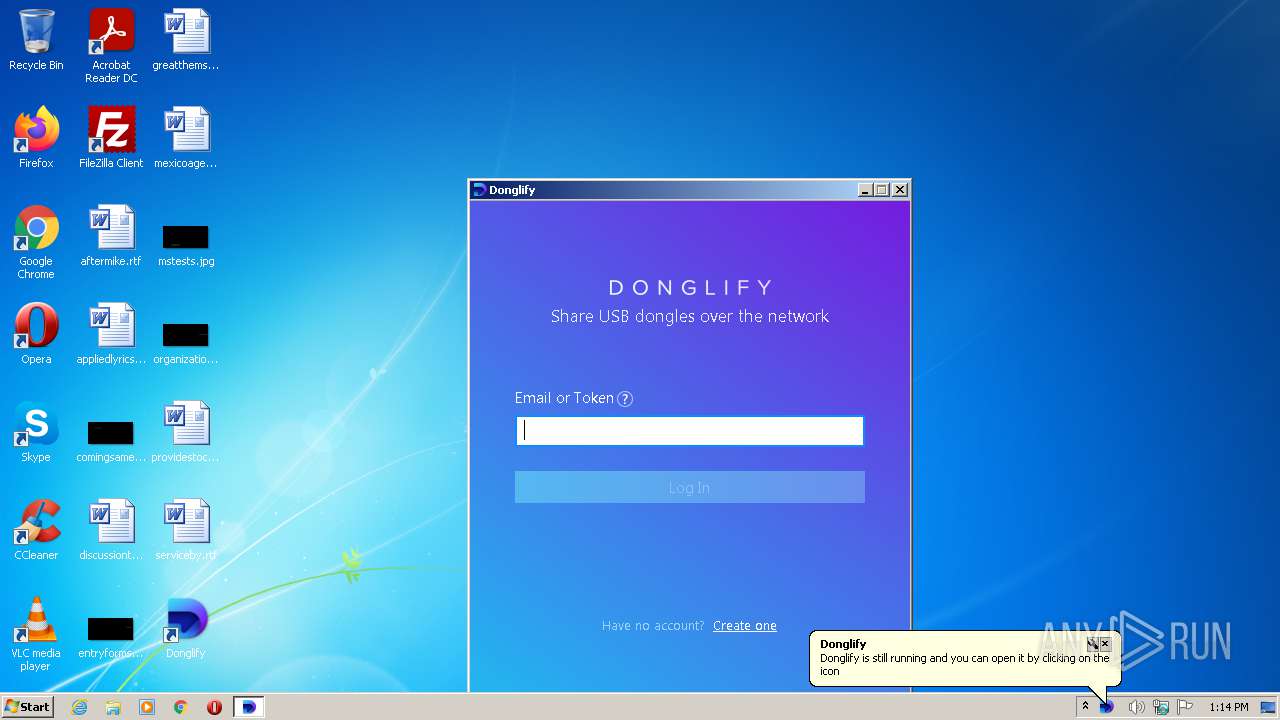
| 2400 | "C:\Program Files\Electronic Team\Donglify\donglify-gui.exe" | C:\Program Files\Electronic Team\Donglify\donglify-gui.exe | utput.tmp | ||||||||||||
User: admin Company: Electronic Team, Inc. Integrity Level: MEDIUM Description: Donglify GUI Exit code: 0 Version: 1.6.13844 Modules
| |||||||||||||||
| 2452 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{137cbcc7-7bb8-43f2-8f47-6a5dc7bc7c13}\UsbStub.inf" "0" "69267d327" "000005C8" "WinSta0\Default" "000005CC" "208" "C:\Program Files\Electronic Team\Donglify\drivers\USB\nt6x32" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | "C:\Windows\system32\netsh.exe" advfirewall firewall add rule name=Donglify_service dir=in action=allow program="C:\Program Files\Electronic Team\Donglify\donglify32.exe" enable=yes | C:\Windows\system32\netsh.exe | — | utput.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Electronic Team\Donglify\donglify32.exe" | C:\Program Files\Electronic Team\Donglify\donglify32.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Electronic Team, Inc. Integrity Level: SYSTEM Description: Donglify Service Exit code: 0 Version: 1.6.13844 Modules
| |||||||||||||||
Total events
24 814
Read events
24 546
Write events
262
Delete events
6
Modification events
| (PID) Process: | (1268) utput.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: F4040000E547C24DF4AAD701 | |||
| (PID) Process: | (1268) utput.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: D0A145A4AF65DF99B8D624F3BB9E849E1980B3EC0E66AE16A64D6E70F705A420 | |||
| (PID) Process: | (1268) utput.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1268) utput.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Electronic Team\Donglify\AutoUpdate.dll | |||
| (PID) Process: | (1268) utput.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 523688061C774C476D3E4989CE91062A76C5140B4E0BB161D5D7AEC83FE158AC | |||
| (PID) Process: | (2136) setup_server_donglify.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (2136) setup_server_donglify.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2452) DrvInst.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2136) setup_server_donglify.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class\{BA60D326-EE12-4957-B702-7F5EDBE9ECE5} |
| Operation: | write | Name: | Class |
Value: EUsbStub | |||
| (PID) Process: | (3068) DrvInst.exe | Key: | HKEY_USERS\.DEFAULT\Software\Classes\Local Settings\MuiCache\171\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
32
Suspicious files
35
Text files
14
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | utput.exe | C:\Users\admin\AppData\Local\Temp\is-TD5AK.tmp\utput.tmp | executable | |
MD5:— | SHA256:— | |||
| 1268 | utput.tmp | C:\Program Files\Electronic Team\Donglify\is-BRE5K.tmp | executable | |
MD5:— | SHA256:— | |||
| 1268 | utput.tmp | C:\Program Files\Electronic Team\Donglify\unins000.exe | executable | |
MD5:— | SHA256:— | |||
| 928 | utput.exe | C:\Users\admin\AppData\Local\Temp\is-UU7LM.tmp\utput.tmp | executable | |
MD5:— | SHA256:— | |||
| 1268 | utput.tmp | C:\Program Files\Electronic Team\Donglify\donglify32.exe | executable | |
MD5:— | SHA256:— | |||
| 1268 | utput.tmp | C:\Program Files\Electronic Team\Donglify\is-I5FNS.tmp | executable | |
MD5:— | SHA256:— | |||
| 1268 | utput.tmp | C:\Program Files\Electronic Team\Donglify\is-3PL2Q.tmp | executable | |
MD5:— | SHA256:— | |||
| 1268 | utput.tmp | C:\Program Files\Electronic Team\Donglify\drivers\USB\nt6x32\is-AMKI1.tmp | executable | |
MD5:D212BBAF21AA448B5A1EEC5214E7C02A | SHA256:6CF405F72D78EDA427DD806283DCC6764C8A61776DC4A7C351395DCCAB7BA4D3 | |||
| 1268 | utput.tmp | C:\Program Files\Electronic Team\Donglify\drivers\USB\nt6x32\fusbhub.sys | executable | |
MD5:D212BBAF21AA448B5A1EEC5214E7C02A | SHA256:6CF405F72D78EDA427DD806283DCC6764C8A61776DC4A7C351395DCCAB7BA4D3 | |||
| 1268 | utput.tmp | C:\Program Files\Electronic Team\Donglify\drivers\USB\nt6x32\is-MO1TU.tmp | executable | |
MD5:CA3948B2F9A1F72AA24B34F5F3E24912 | SHA256:708A687F0F6ABCE3A58BB865307C66436731015733857415D97D9FD652961446 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2400 | donglify-gui.exe | GET | 200 | 2.16.186.81:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?614ec868cacccff9 | unknown | compressed | 4.70 Kb | whitelisted |
2400 | donglify-gui.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 471 b | whitelisted |
2400 | donglify-gui.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2400 | donglify-gui.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEFHaWjEYFdW1AwAAAADMrDQ%3D | US | der | 471 b | whitelisted |
2400 | donglify-gui.exe | GET | 200 | 142.250.186.99:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2400 | donglify-gui.exe | 195.181.175.49:443 | cdn.electronic.us | Datacamp Limited | DE | suspicious |
2400 | donglify-gui.exe | 2.16.186.81:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2400 | donglify-gui.exe | 142.250.184.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2400 | donglify-gui.exe | 142.250.186.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2400 | donglify-gui.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.electronic.us |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |