| File name: | file_id4649039ids1s.exe |
| Full analysis: | https://app.any.run/tasks/989d1439-bd41-42d2-bf73-a4f90f1ee47d |
| Verdict: | Malicious activity |
| Analysis date: | November 07, 2021, 09:17:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C68370AAA888E311939BF5A86ECAB098 |
| SHA1: | 7A78A6F89E7A14E1A8708840EFAC885CB17B05A6 |
| SHA256: | 18867D0DF4235538A341449ABA7D6281F5009346766D1026AB785C69793514E9 |
| SSDEEP: | 49152:lTcwZvyNlILWmbG7aNpz4gSK7OW2aRETTmSDQdeVuAbO:BcwsCWmbG7aVl72agySkL |
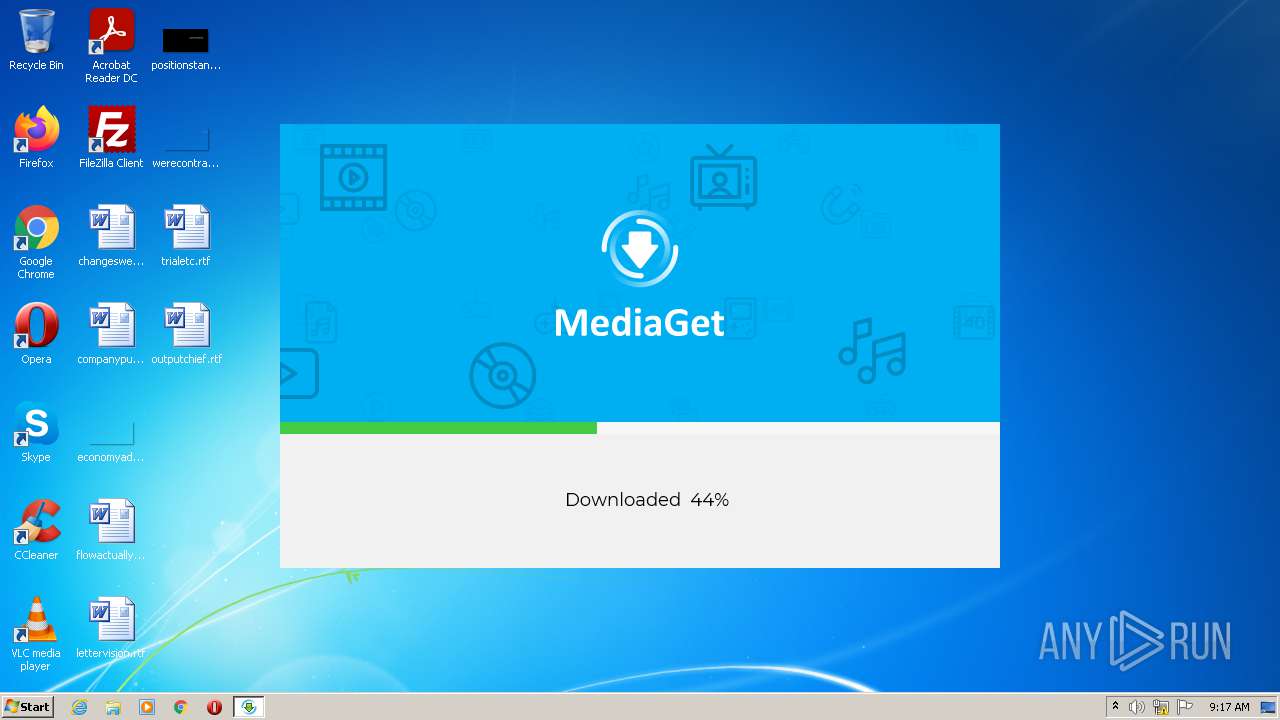
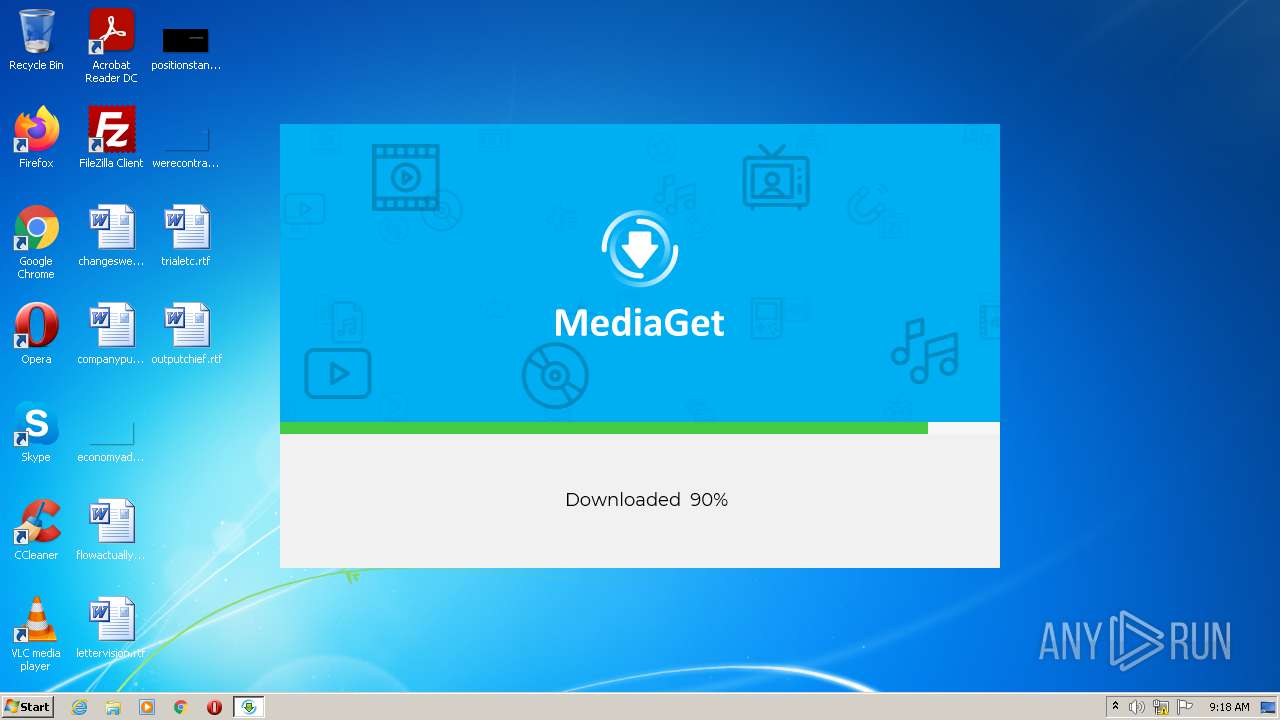
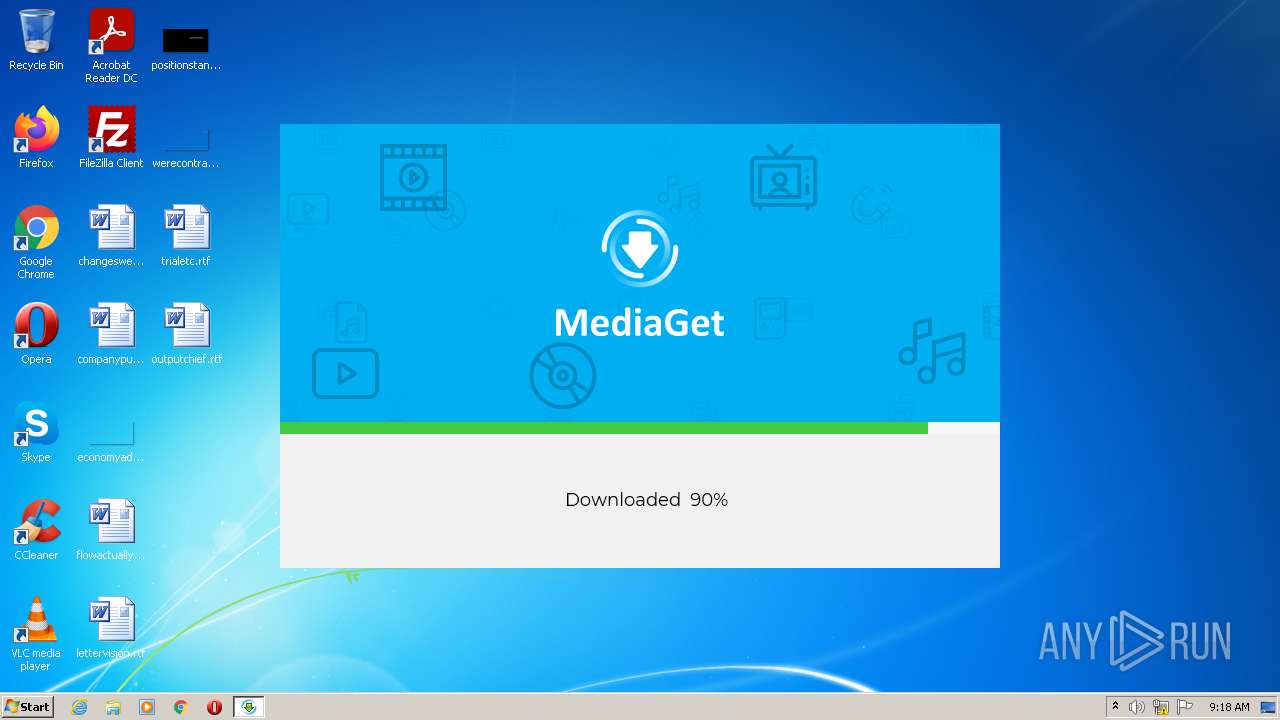
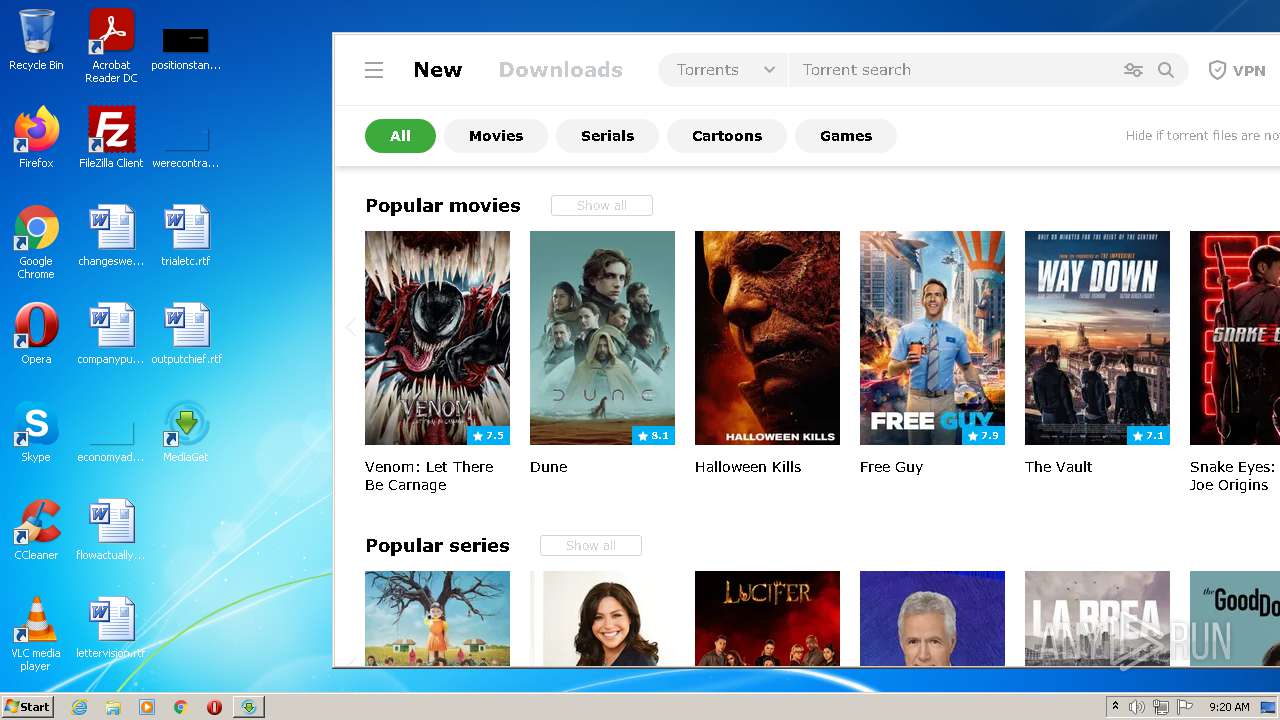
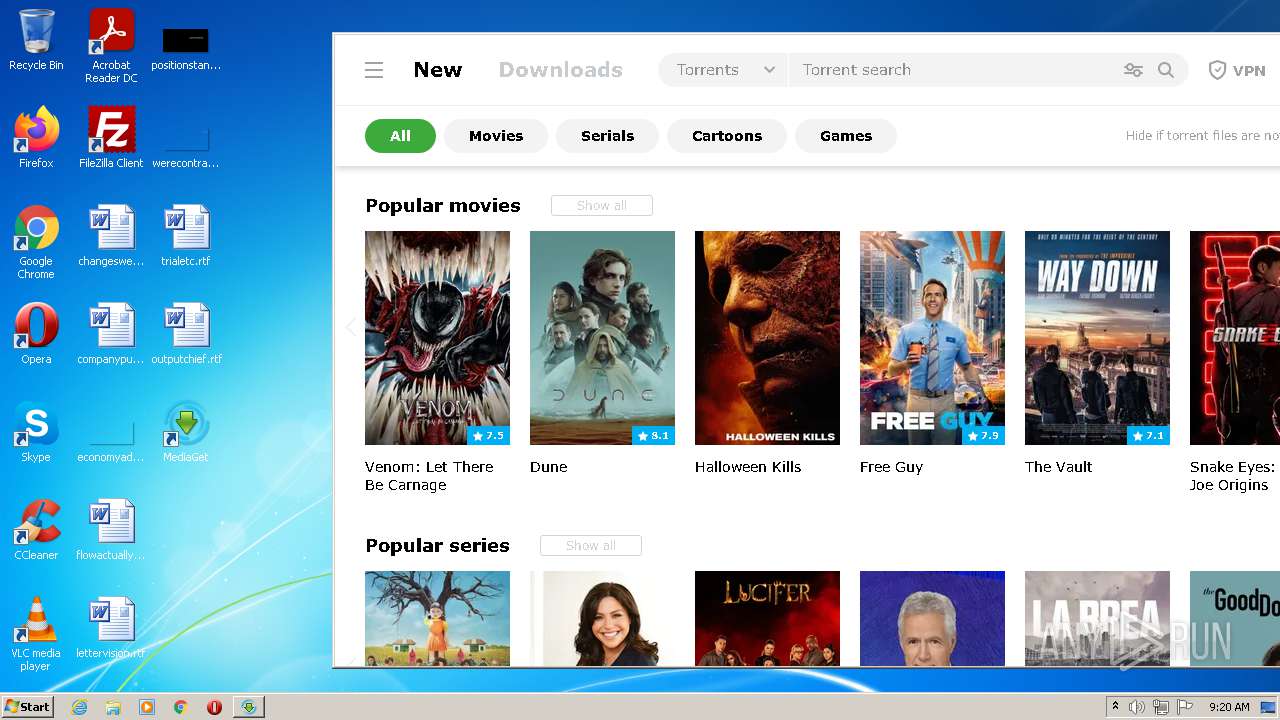
MALICIOUS
Actions looks like stealing of personal data
- file_id4649039ids1s.exe (PID: 2328)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3856)
- net_updater32.exe (PID: 880)
- mediaget_crashpad_handler.exe (PID: 2160)
- mediaget.exe (PID: 912)
- QtWebEngineProcess.exe (PID: 756)
- QtWebEngineProcess.exe (PID: 3912)
- QtWebEngineProcess.exe (PID: 2000)
- luminati-m-controller.exe (PID: 276)
- QtWebEngineProcess.exe (PID: 2120)
- net_updater32.exe (PID: 3336)
- net_svc.exe (PID: 2700)
- net_updater32.exe (PID: 3008)
Drops executable file immediately after starts
- lum_inst.exe (PID: 3368)
- lum_inst.tmp (PID: 2392)
- luminati-m-controller.exe (PID: 276)
Changes settings of System certificates
- net_updater32.exe (PID: 880)
- QtWebEngineProcess.exe (PID: 756)
Application was dropped or rewritten from another process
- lum_inst.exe (PID: 3368)
- net_updater32.exe (PID: 880)
- test_wpf.exe (PID: 3680)
- net_updater32.exe (PID: 1436)
- mediaget.exe (PID: 912)
- mediaget_crashpad_handler.exe (PID: 2160)
- net_updater32.exe (PID: 3336)
- QtWebEngineProcess.exe (PID: 756)
- QtWebEngineProcess.exe (PID: 3912)
- QtWebEngineProcess.exe (PID: 2000)
- luminati-m-controller.exe (PID: 276)
- test_wpf.exe (PID: 980)
- QtWebEngineProcess.exe (PID: 2120)
- test_wpf.exe (PID: 3260)
- idle_report.exe (PID: 3200)
- net_svc.exe (PID: 2700)
- net_svc.exe (PID: 2428)
- net_svc.exe (PID: 500)
- net_updater32.exe (PID: 3004)
- net_updater32.exe (PID: 3008)
- test_wpf.exe (PID: 1240)
- idle_report.exe (PID: 3876)
- idle_report.exe (PID: 2964)
Changes the autorun value in the registry
- mediaget.exe (PID: 912)
SUSPICIOUS
Reads the computer name
- file_id4649039ids1s.exe (PID: 2328)
- lum_inst.tmp (PID: 2392)
- net_updater32.exe (PID: 880)
- test_wpf.exe (PID: 3680)
- net_updater32.exe (PID: 1436)
- mediaget.exe (PID: 912)
- net_updater32.exe (PID: 3336)
- QtWebEngineProcess.exe (PID: 756)
- test_wpf.exe (PID: 980)
- luminati-m-controller.exe (PID: 276)
- test_wpf.exe (PID: 3260)
- idle_report.exe (PID: 3200)
- net_svc.exe (PID: 2700)
- net_updater32.exe (PID: 3004)
- net_updater32.exe (PID: 3008)
- test_wpf.exe (PID: 1240)
- idle_report.exe (PID: 2964)
- idle_report.exe (PID: 3876)
Checks supported languages
- file_id4649039ids1s.exe (PID: 2328)
- lum_inst.tmp (PID: 2392)
- lum_inst.exe (PID: 3368)
- net_updater32.exe (PID: 880)
- test_wpf.exe (PID: 3680)
- net_updater32.exe (PID: 1436)
- mediaget.exe (PID: 912)
- mediaget_crashpad_handler.exe (PID: 2160)
- net_updater32.exe (PID: 3336)
- QtWebEngineProcess.exe (PID: 756)
- QtWebEngineProcess.exe (PID: 2000)
- QtWebEngineProcess.exe (PID: 3912)
- luminati-m-controller.exe (PID: 276)
- test_wpf.exe (PID: 980)
- QtWebEngineProcess.exe (PID: 2120)
- test_wpf.exe (PID: 3260)
- idle_report.exe (PID: 3200)
- net_svc.exe (PID: 2428)
- net_svc.exe (PID: 2700)
- net_svc.exe (PID: 500)
- cmd.exe (PID: 1848)
- net_updater32.exe (PID: 3004)
- net_updater32.exe (PID: 3008)
- test_wpf.exe (PID: 1240)
- idle_report.exe (PID: 2964)
- idle_report.exe (PID: 3876)
Reads Microsoft Outlook installation path
- file_id4649039ids1s.exe (PID: 2328)
Creates files in the user directory
- file_id4649039ids1s.exe (PID: 2328)
Drops a file that was compiled in debug mode
- file_id4649039ids1s.exe (PID: 2328)
- lum_inst.tmp (PID: 2392)
- net_updater32.exe (PID: 880)
- net_updater32.exe (PID: 3336)
- net_svc.exe (PID: 2700)
- net_updater32.exe (PID: 3004)
- luminati-m-controller.exe (PID: 276)
- net_updater32.exe (PID: 3008)
- mediaget.exe (PID: 912)
Executable content was dropped or overwritten
- file_id4649039ids1s.exe (PID: 2328)
- lum_inst.exe (PID: 3368)
- lum_inst.tmp (PID: 2392)
- net_updater32.exe (PID: 880)
- luminati-m-controller.exe (PID: 276)
- net_updater32.exe (PID: 3336)
- net_svc.exe (PID: 2700)
- mediaget.exe (PID: 912)
- net_updater32.exe (PID: 3004)
- net_updater32.exe (PID: 3008)
Reads internet explorer settings
- file_id4649039ids1s.exe (PID: 2328)
Reads the Windows organization settings
- lum_inst.tmp (PID: 2392)
Drops a file with too old compile date
- file_id4649039ids1s.exe (PID: 2328)
Reads Windows owner or organization settings
- lum_inst.tmp (PID: 2392)
Creates a software uninstall entry
- file_id4649039ids1s.exe (PID: 2328)
Drops a file with a compile date too recent
- file_id4649039ids1s.exe (PID: 2328)
- net_svc.exe (PID: 2700)
- net_updater32.exe (PID: 3004)
- net_updater32.exe (PID: 3008)
Adds / modifies Windows certificates
- net_updater32.exe (PID: 880)
- QtWebEngineProcess.exe (PID: 756)
Reads Environment values
- net_updater32.exe (PID: 880)
- mediaget.exe (PID: 912)
- luminati-m-controller.exe (PID: 276)
- net_updater32.exe (PID: 3336)
- net_updater32.exe (PID: 3008)
Application launched itself
- net_updater32.exe (PID: 880)
- net_svc.exe (PID: 2700)
Creates files in the program directory
- net_updater32.exe (PID: 880)
Changes default file association
- file_id4649039ids1s.exe (PID: 2328)
- mediaget.exe (PID: 912)
Executed as Windows Service
- net_updater32.exe (PID: 3336)
- net_updater32.exe (PID: 3008)
Creates files in the Windows directory
- net_updater32.exe (PID: 3336)
- net_updater32.exe (PID: 3004)
Removes files from Windows directory
- net_updater32.exe (PID: 3336)
Starts CMD.EXE for commands execution
- net_svc.exe (PID: 2700)
INFO
Reads settings of System Certificates
- file_id4649039ids1s.exe (PID: 2328)
- net_updater32.exe (PID: 880)
- net_updater32.exe (PID: 1436)
- net_updater32.exe (PID: 3336)
- mediaget.exe (PID: 912)
- QtWebEngineProcess.exe (PID: 756)
- net_svc.exe (PID: 2700)
- net_updater32.exe (PID: 3004)
- net_updater32.exe (PID: 3008)
Dropped object may contain Bitcoin addresses
- file_id4649039ids1s.exe (PID: 2328)
Application was dropped or rewritten from another process
- lum_inst.tmp (PID: 2392)
Checks Windows Trust Settings
- net_updater32.exe (PID: 880)
- net_updater32.exe (PID: 3336)
- net_svc.exe (PID: 2700)
- net_updater32.exe (PID: 3008)
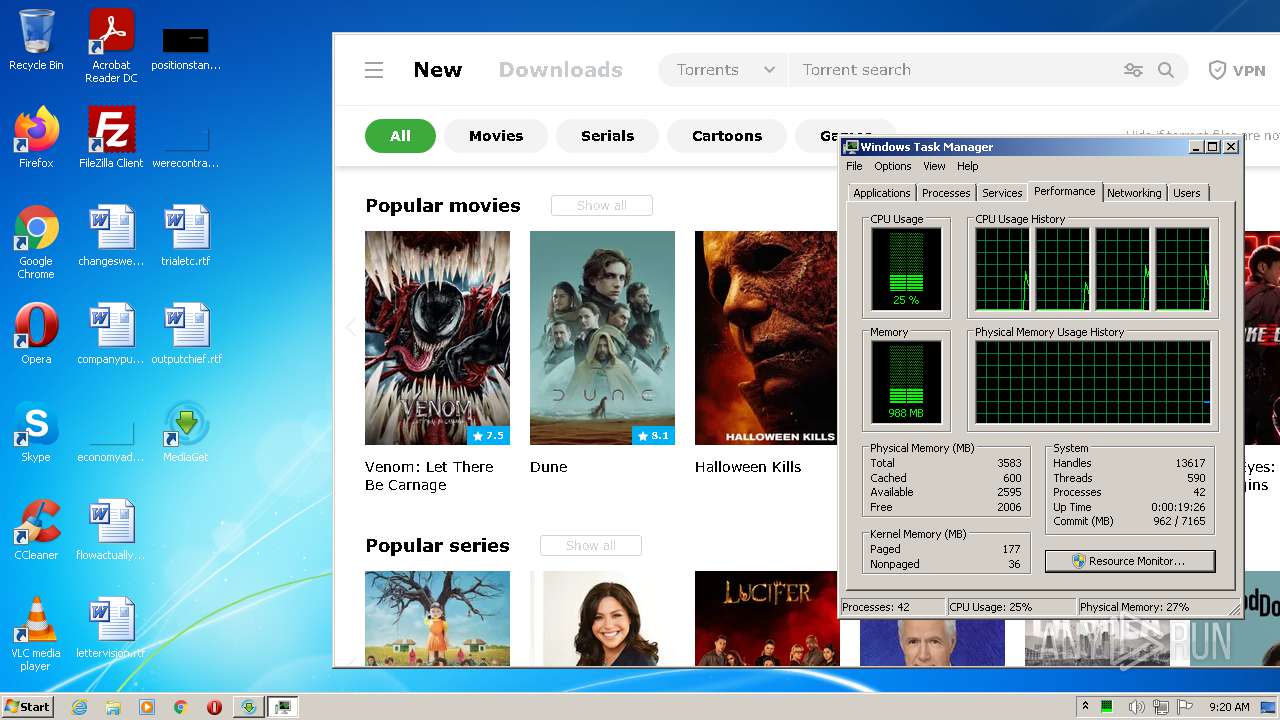
Reads the computer name
- WISPTIS.EXE (PID: 2820)
- taskmgr.exe (PID: 2168)
Checks supported languages
- WISPTIS.EXE (PID: 2820)
- taskmgr.exe (PID: 2168)
Reads the hosts file
- QtWebEngineProcess.exe (PID: 756)
- mediaget.exe (PID: 912)
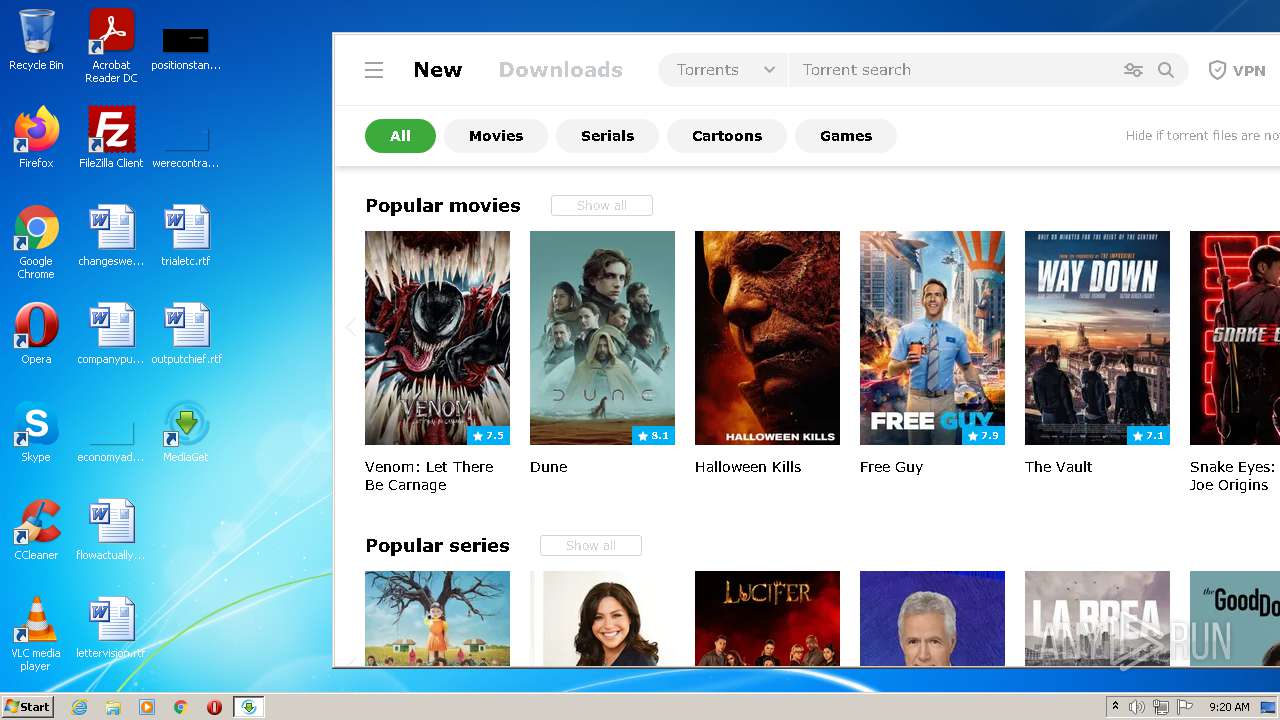
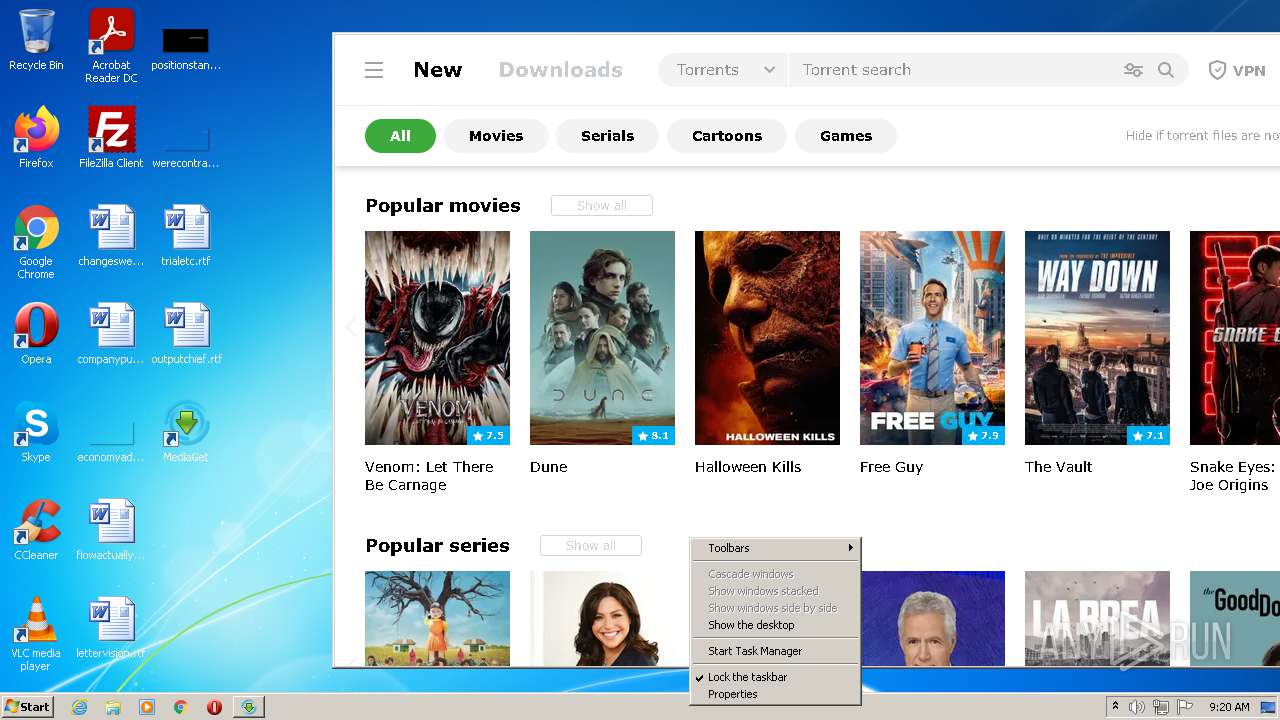
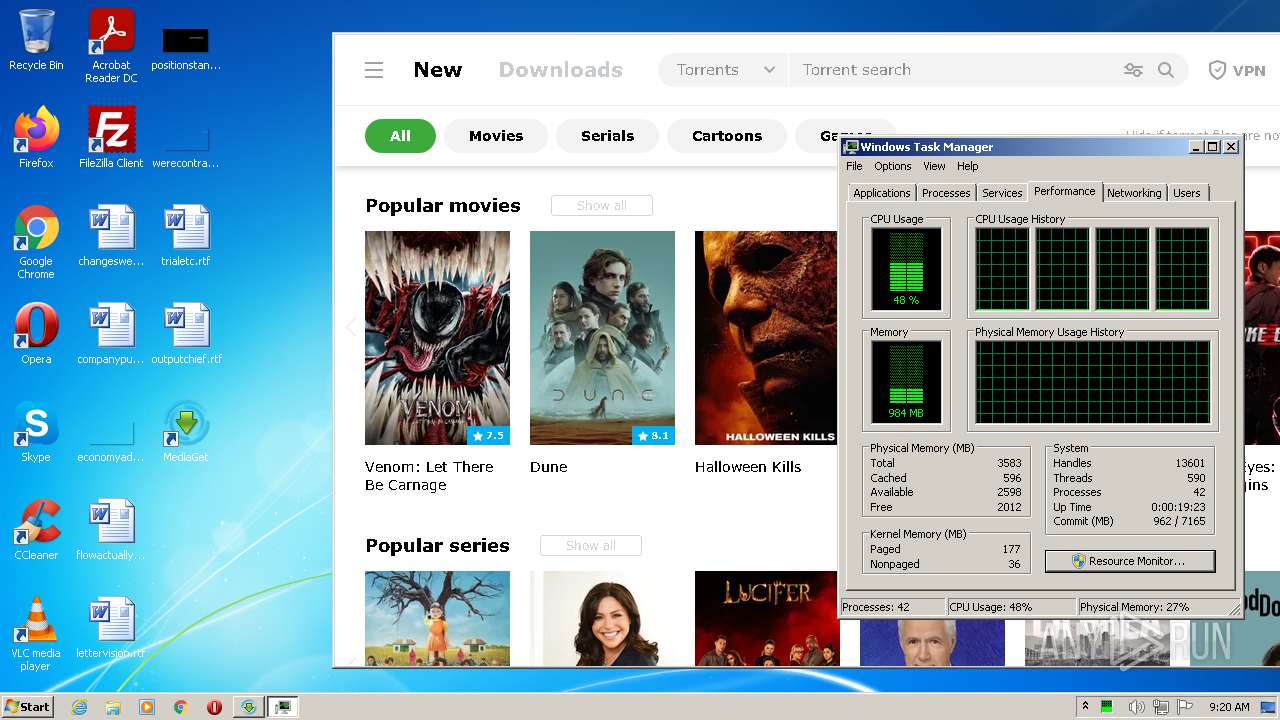
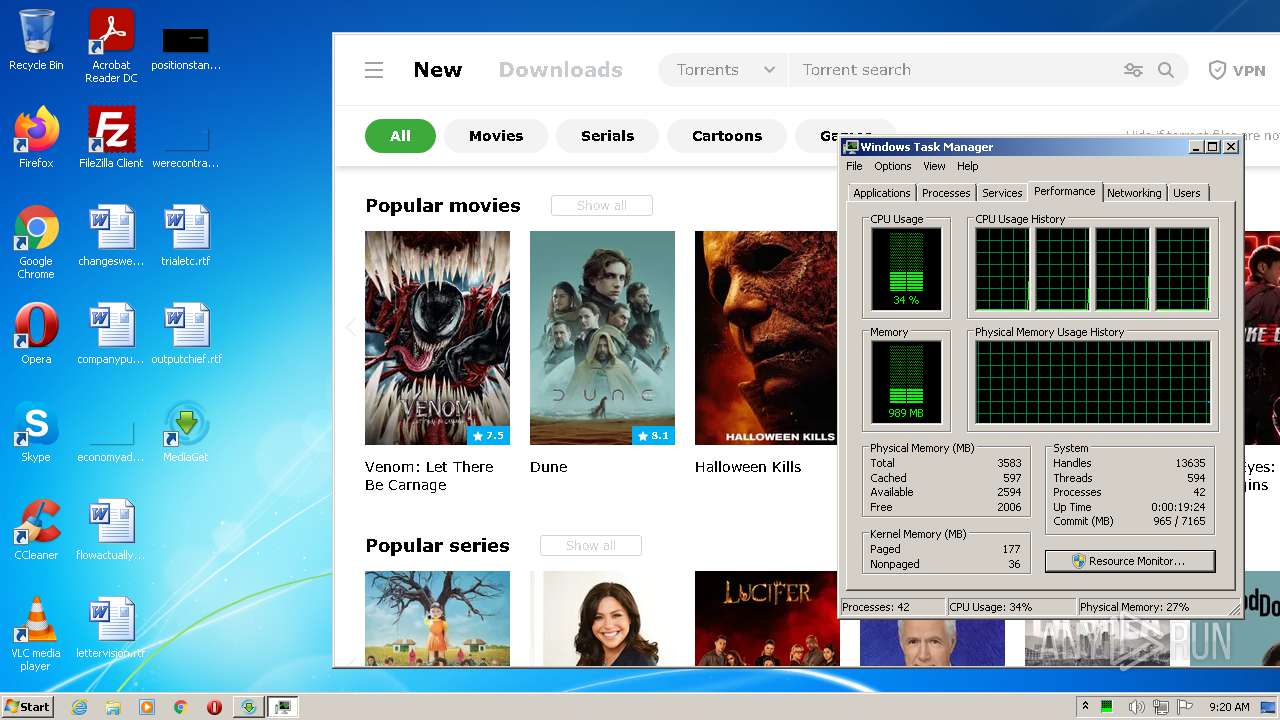
Manual execution by user
- taskmgr.exe (PID: 2168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:10:07 15:36:26+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 562688 |
| InitializedDataSize: | 1778176 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x81e12 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1 |
| InternalName: | - |
| LegalCopyright: | - |
| OriginalFileName: | - |
| ProductName: | - |
| ProductVersion: | 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Oct-2021 13:36:26 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0 |
| InternalName: | - |
| LegalCopyright: | - |
| OriginalFilename: | - |
| ProductName: | - |
| ProductVersion: | 1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 07-Oct-2021 13:36:26 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00089554 | 0x00089600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64957 |
.rdata | 0x0008B000 | 0x000241BC | 0x00024200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.62407 |
.data | 0x000B0000 | 0x00004D80 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.80282 |
.rsrc | 0x000B5000 | 0x001824B0 | 0x00182600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.94496 |
.reloc | 0x00238000 | 0x00009C4C | 0x00009E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.57896 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22706 | 820 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.18073 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.05232 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.75162 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
128 | 2.62308 | 62 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
129 | 1.67172 | 170 | Latin 1 / Western European | English - United States | UNKNOWN |
HTML | 7.99985 | 1220261 | Latin 1 / Western European | Russian - Russia | ARCHIVE_7Z |
PRELOADER-EN | 7.99585 | 44712 | Latin 1 / Western European | Russian - Russia | ARCHIVE_7Z |
PRELOADER-RU | 7.99605 | 45905 | Latin 1 / Western European | Russian - Russia | ARCHIVE_7Z |
CABUNDLE | 6.0253 | 227153 | Latin 1 / Western European | Russian - Russia | CRT |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCR90.dll |
OLEAUT32.dll |
OPENGL32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
78
Monitored processes
31
Malicious processes
17
Suspicious processes
7
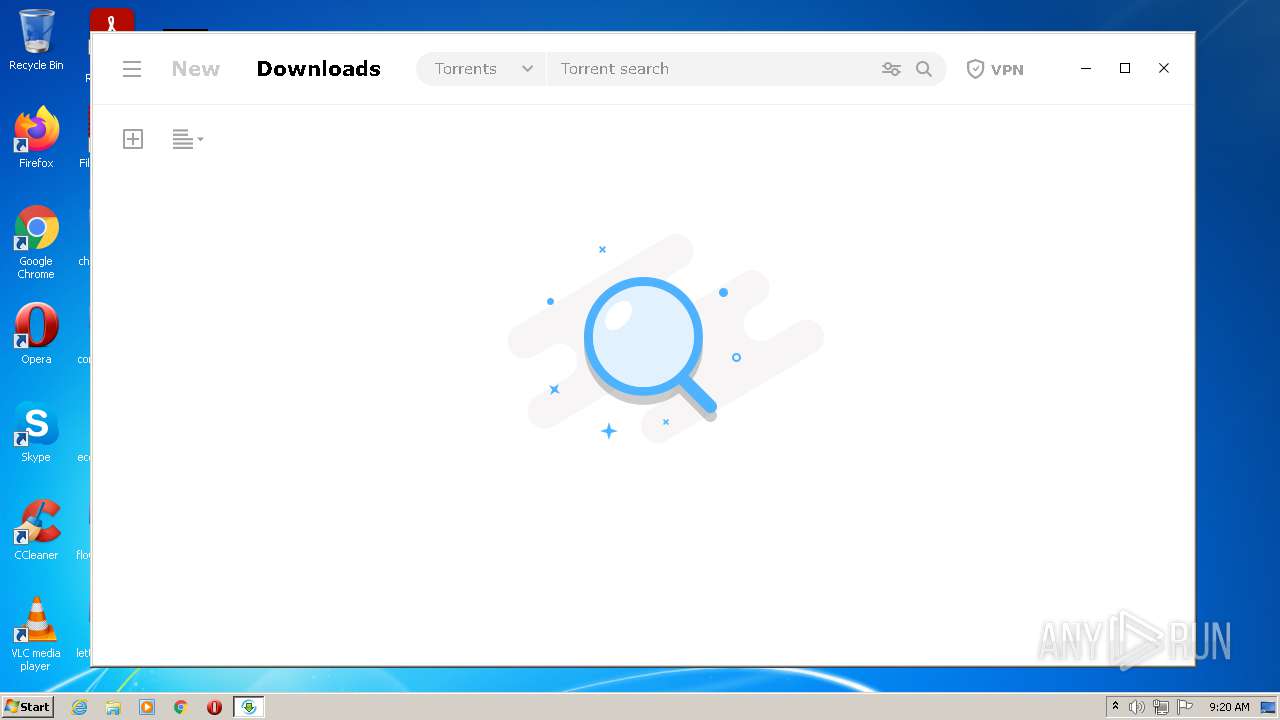
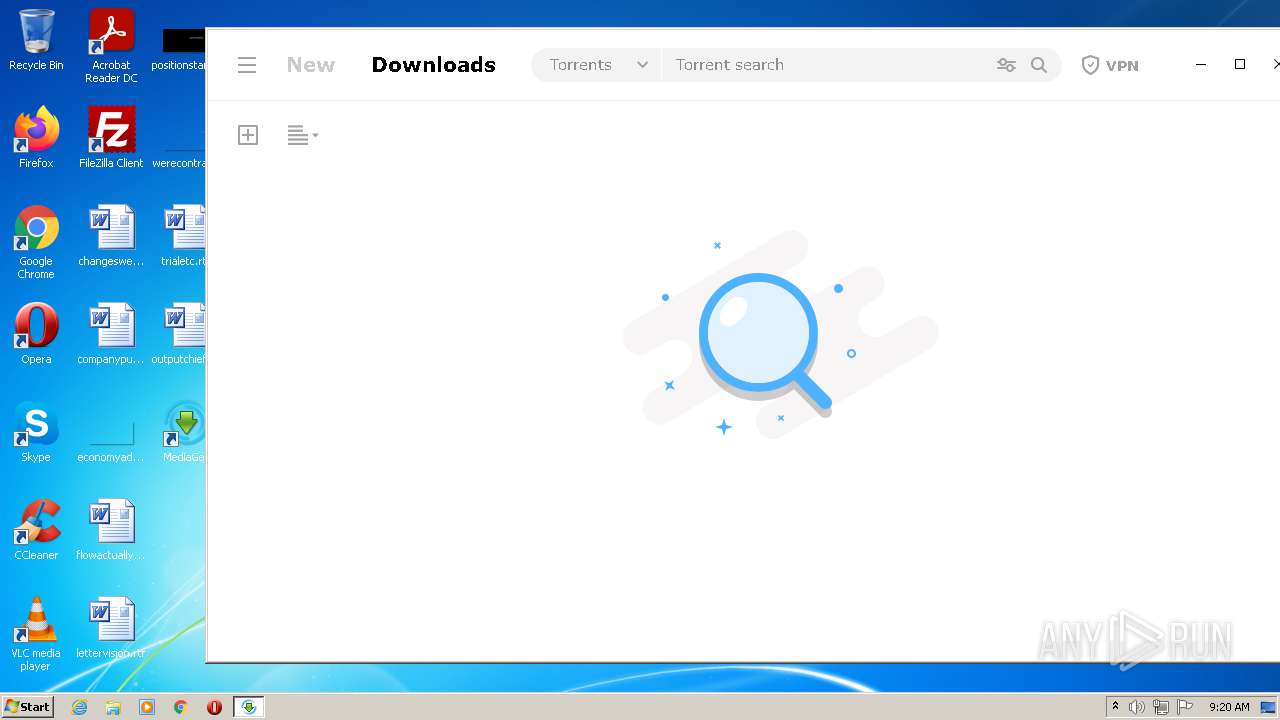
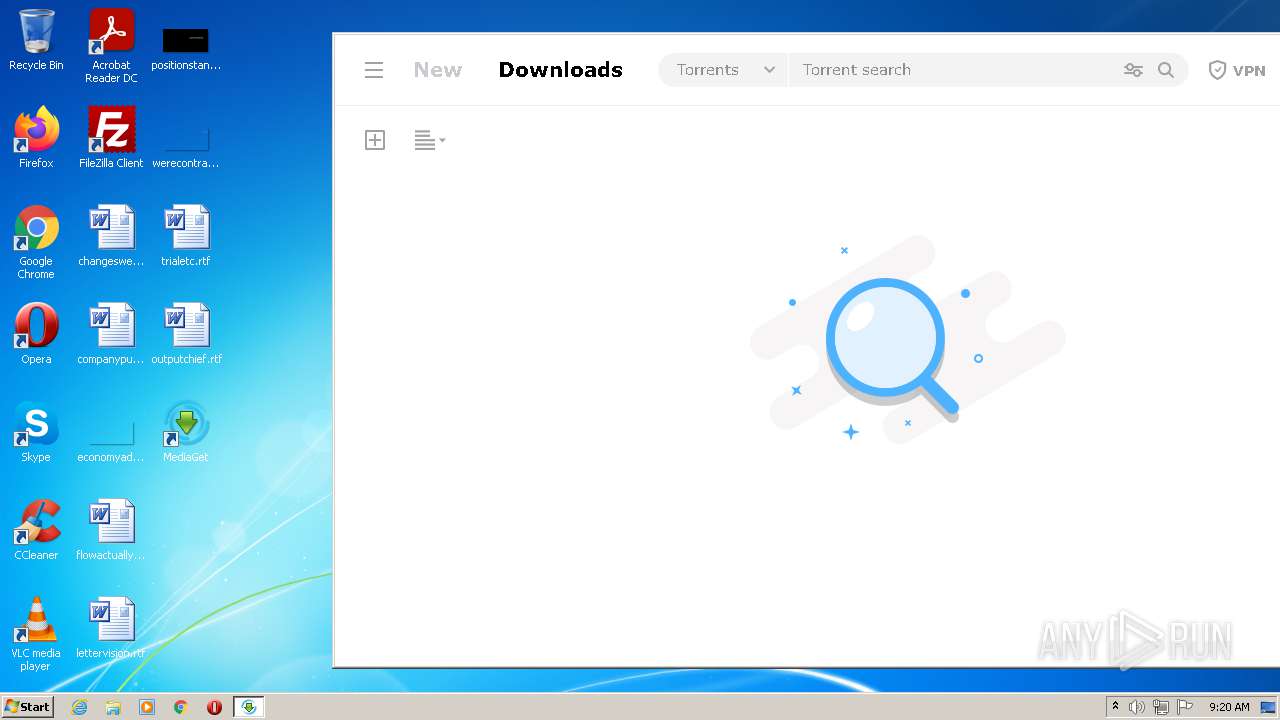
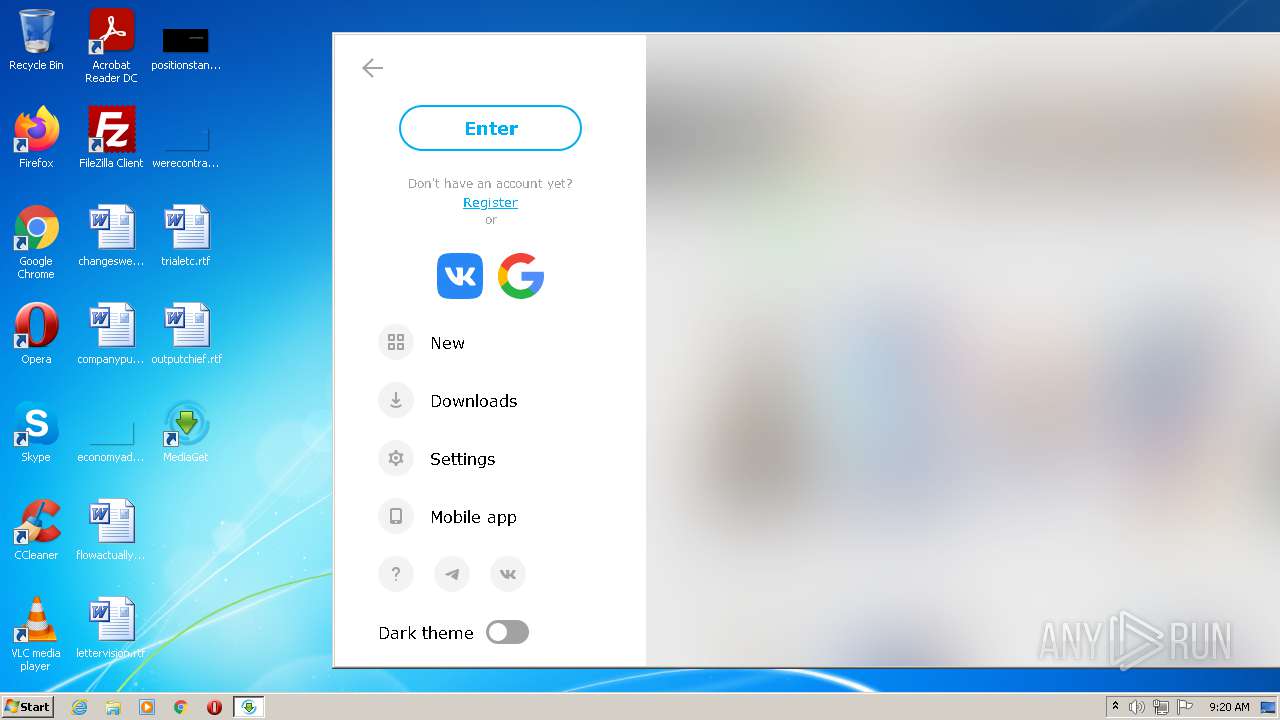
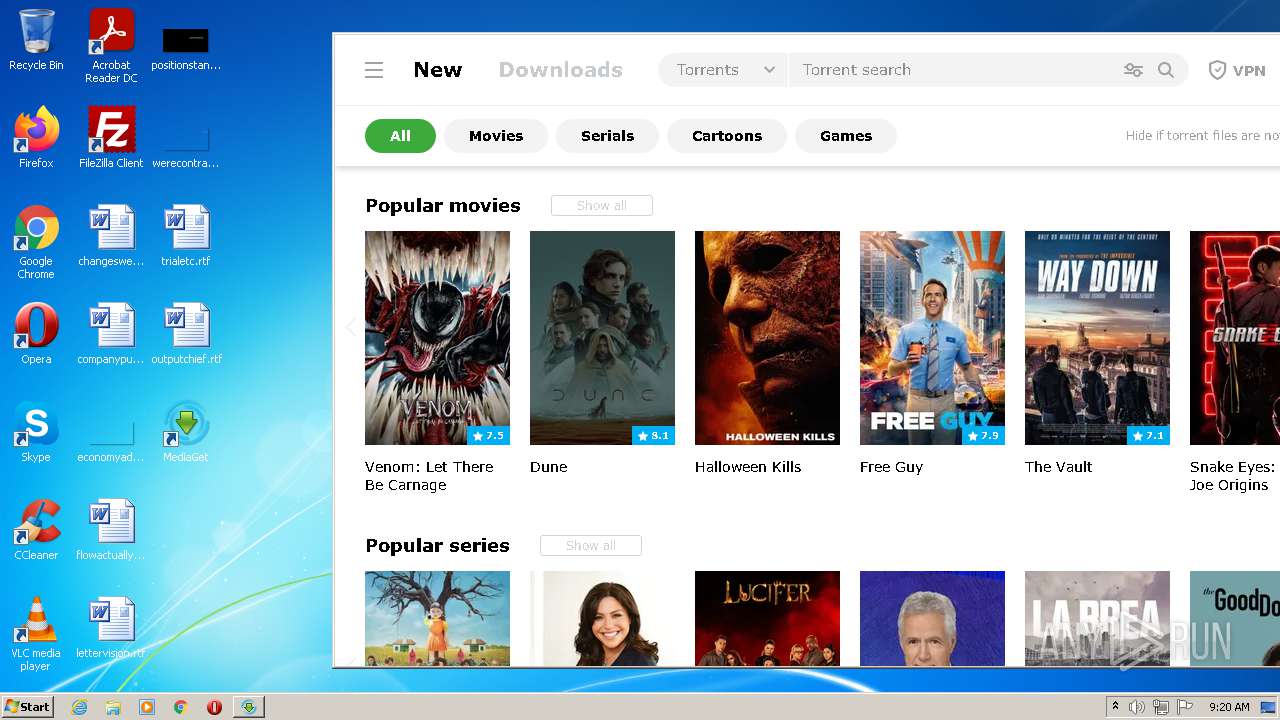
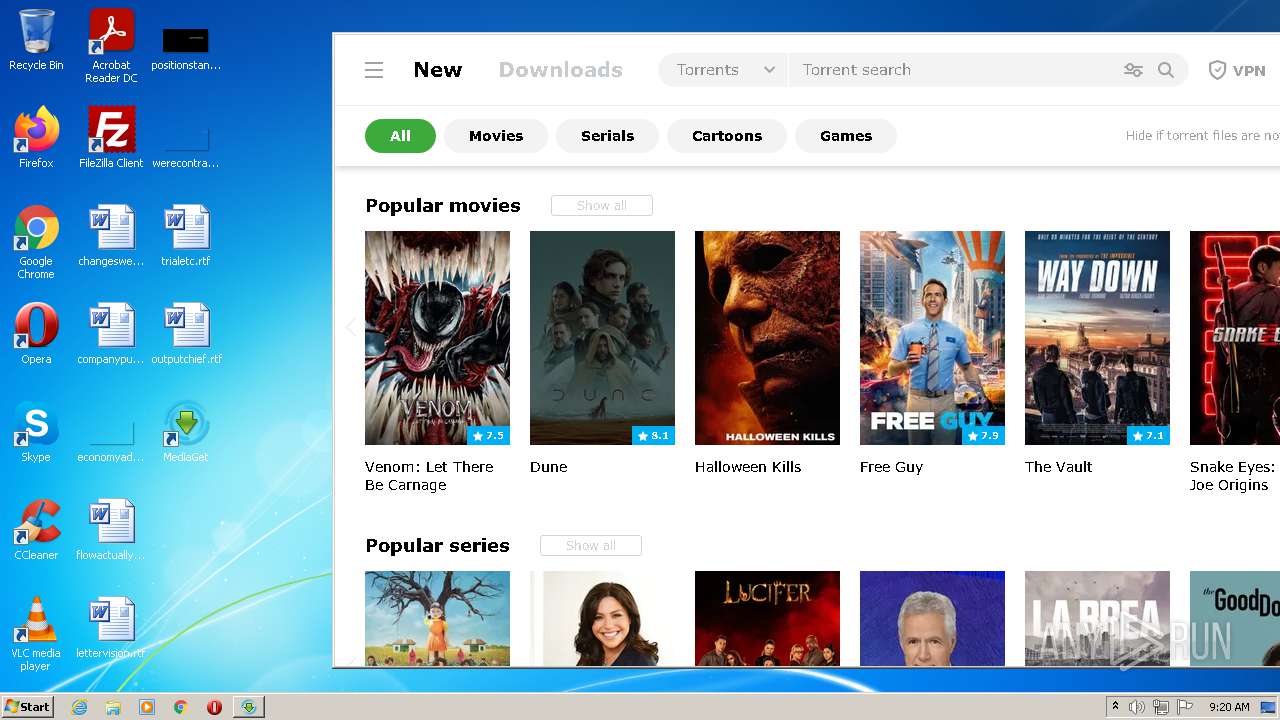
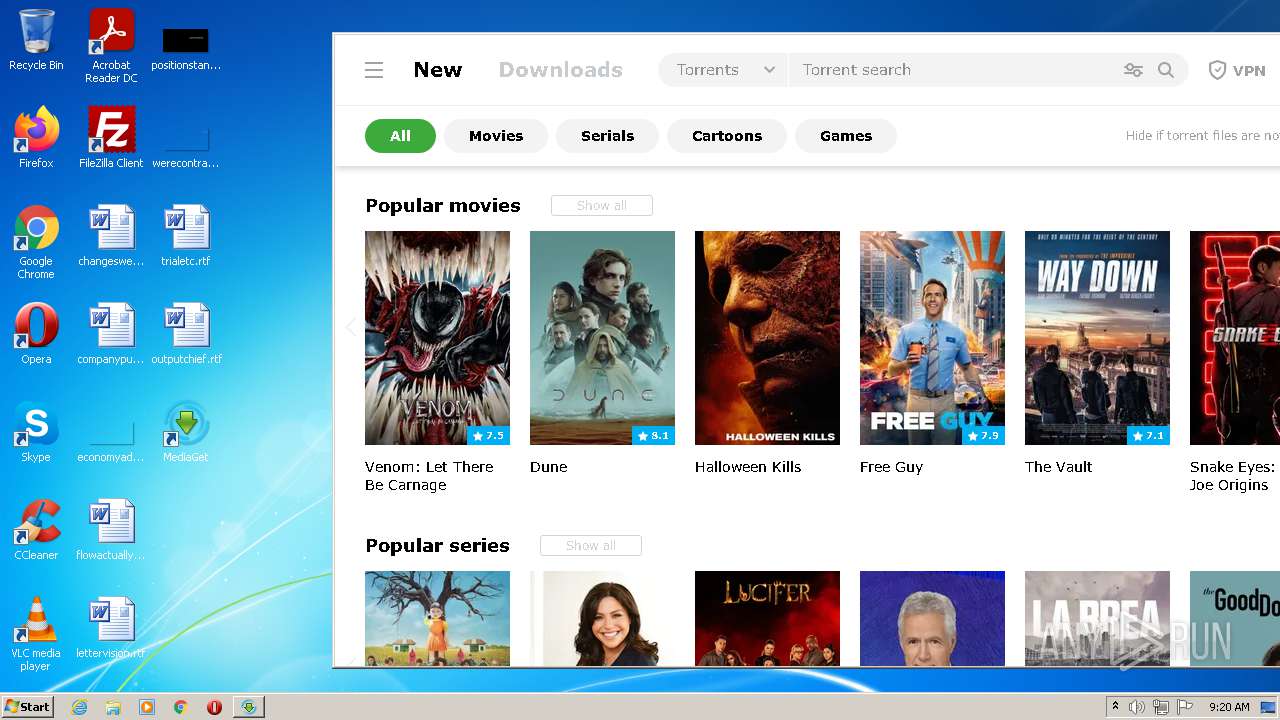
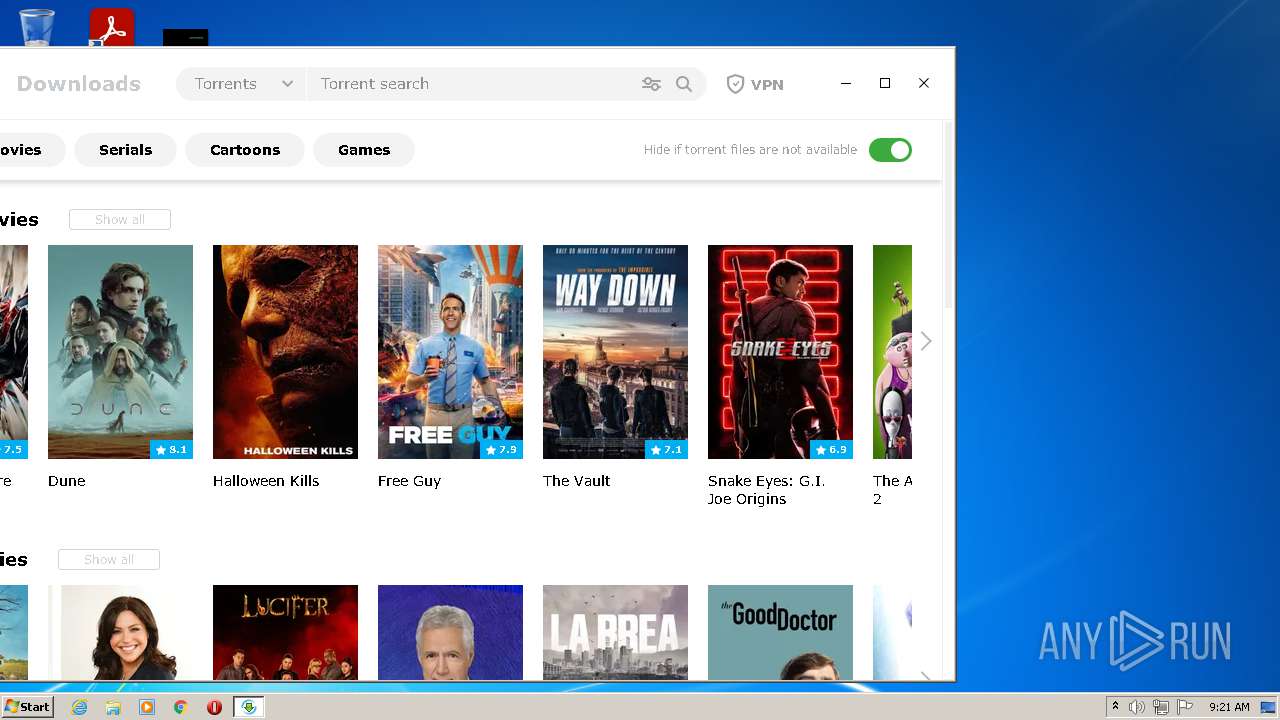
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | C:\Users\admin\MediaGet2\Luminati-m\luminati-m-controller.exe is_switch_on | C:\Users\admin\MediaGet2\Luminati-m\luminati-m-controller.exe | mediaget.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 101 Modules
| |||||||||||||||
| 500 | "C:\Users\admin\MediaGet2\Luminati-m\luminati\net_svc.exe" --report-idle | C:\Users\admin\MediaGet2\Luminati-m\luminati\net_svc.exe | — | net_svc.exe | |||||||||||
User: admin Company: Luminati Networks Ltd. Integrity Level: MEDIUM Description: Luminati SDK Engine Exit code: 0 Version: 1.245.997 Modules
| |||||||||||||||
| 756 | "C:\Users\admin\MediaGet2\QtWebEngineProcess.exe" --type=utility --enable-features=AllowContentInitiatedDataUrlNavigations,TracingServiceInProcess --disable-features=BackgroundFetch,ConsolidatedMovementXY,DnsOverHttpsUpgrade,FormControlsRefresh,MojoVideoCapture,PictureInPicture,SmsReceiver,UseSkiaRenderer,WebPayments,WebUSB --lang=en-US --service-sandbox-type=network --application-name=MediaGet2 --webengine-schemes=qrc:sLV --mojo-platform-channel-handle=1736 /prefetch:8 | C:\Users\admin\MediaGet2\QtWebEngineProcess.exe | mediaget.exe | ||||||||||||
User: admin Company: The Qt Company Ltd. Integrity Level: HIGH Description: C++ Application Development Framework Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
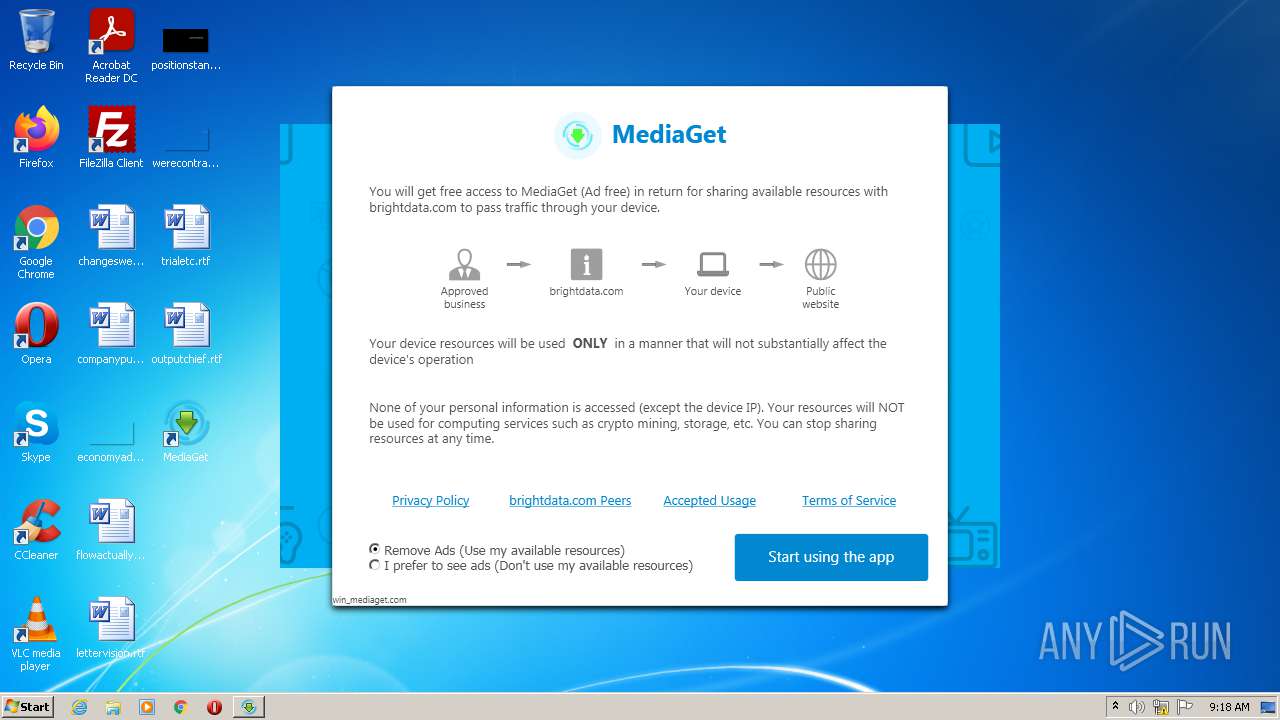
| 880 | "C:\Users\admin\MediaGet2\Luminati-m\net_updater32.exe" --install-ui win_mediaget.com --dlg-app-name MediaGet --dlg-tos-link "https://mediaget.com/license" --dlg-benefit-txt "MediaGet (Ad free)" --dlg-logo-link "https://mediaget.com/installer/binaries/mg-icon-400.png" --dlg-not-peer-txt ads --dlg-peer-txt remove_ads | C:\Users\admin\MediaGet2\Luminati-m\net_updater32.exe | lum_inst.tmp | ||||||||||||
User: admin Company: Luminati Networks Ltd. Integrity Level: HIGH Description: Luminati SDK Updater Exit code: 1 Version: 1.240.55 Modules
| |||||||||||||||
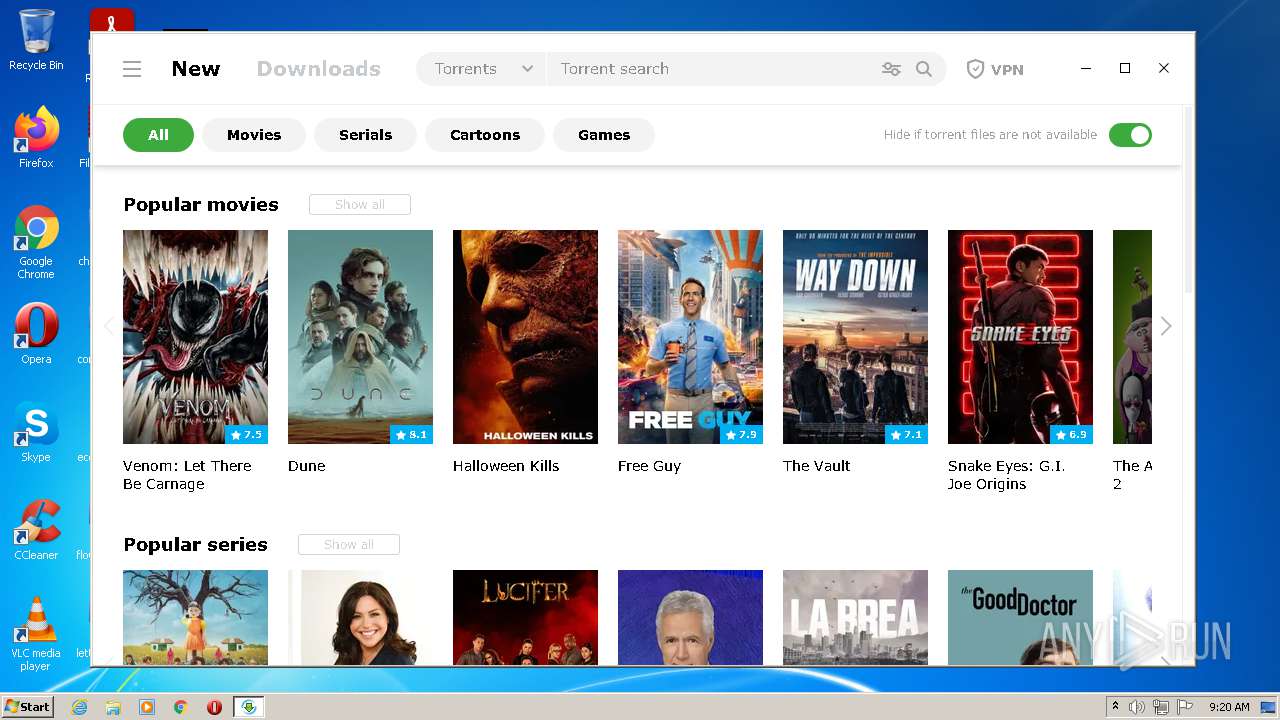
| 912 | "C:\Users\admin\MediaGet2\mediaget.exe" --installer | C:\Users\admin\MediaGet2\mediaget.exe | file_id4649039ids1s.exe | ||||||||||||
User: admin Company: MediaGet Integrity Level: HIGH Description: MediaGet torrent client Exit code: 0 Modules
| |||||||||||||||
| 980 | C:\Users\admin\MediaGet2\Luminati-m\test_wpf.exe | C:\Users\admin\MediaGet2\Luminati-m\test_wpf.exe | — | luminati-m-controller.exe | |||||||||||
User: admin Company: Luminati Networks Ltd. Integrity Level: HIGH Description: test_wpf Exit code: 0 Version: 1.240.55 Modules
| |||||||||||||||
| 1240 | C:\Users\admin\MediaGet2\Luminati-m\test_wpf.exe | C:\Users\admin\MediaGet2\Luminati-m\test_wpf.exe | — | net_updater32.exe | |||||||||||
User: SYSTEM Company: Bright Data Ltd. Integrity Level: SYSTEM Description: test_wpf Exit code: 0 Version: 1.260.260 Modules
| |||||||||||||||
| 1436 | "C:\Users\admin\MediaGet2\Luminati-m\net_updater32.exe" --install win_mediaget.com --no-cleanup | C:\Users\admin\MediaGet2\Luminati-m\net_updater32.exe | net_updater32.exe | ||||||||||||
User: admin Company: Luminati Networks Ltd. Integrity Level: HIGH Description: Luminati SDK Updater Exit code: 0 Version: 1.240.55 Modules
| |||||||||||||||
| 1848 | C:\Windows\system32\cmd.exe /d /s /c ""C:/Users/admin/MediaGet2/Luminati-m/luminati/temp/net_updater32.exe" "--install" "win_mediaget.com" "--remote"" | C:\Windows\system32\cmd.exe | — | net_svc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2000 | "C:\Users\admin\MediaGet2\QtWebEngineProcess.exe" --type=renderer --disable-speech-api --enable-threaded-compositing --enable-features=AllowContentInitiatedDataUrlNavigations,TracingServiceInProcess --disable-features=BackgroundFetch,ConsolidatedMovementXY,DnsOverHttpsUpgrade,FormControlsRefresh,MojoVideoCapture,PictureInPicture,SmsReceiver,UseSkiaRenderer,WebPayments,WebUSB --disable-gpu-compositing --lang=en-US --webengine-schemes=qrc:sLV --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=2524 /prefetch:1 | C:\Users\admin\MediaGet2\QtWebEngineProcess.exe | — | mediaget.exe | |||||||||||
User: admin Company: The Qt Company Ltd. Integrity Level: LOW Description: C++ Application Development Framework Exit code: 0 Version: 5.15.2.0 Modules
| |||||||||||||||
Total events
45 426
Read events
44 752
Write events
607
Delete events
67
Modification events
| (PID) Process: | (2328) file_id4649039ids1s.exe | Key: | HKEY_CURRENT_USER\Software\Media Get LLC\MediaGet2-systemScope\mediaget_info |
| Operation: | write | Name: | hasDownloadedUpdate |
Value: false | |||
| (PID) Process: | (2328) file_id4649039ids1s.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2328) file_id4649039ids1s.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2328) file_id4649039ids1s.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2328) file_id4649039ids1s.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2328) file_id4649039ids1s.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2328) file_id4649039ids1s.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2328) file_id4649039ids1s.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2328) file_id4649039ids1s.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2328) file_id4649039ids1s.exe | Key: | HKEY_CURRENT_USER\Software\MediaGet |
| Operation: | write | Name: | (default) |
Value: C:\Users\admin\MediaGet2\mediaget.exe | |||
Executable files
142
Suspicious files
147
Text files
298
Unknown types
55
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2328 | file_id4649039ids1s.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\1940E63DBCBF0B5D910855E5C0ABB6C3 | der | |
MD5:— | SHA256:— | |||
| 2328 | file_id4649039ids1s.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\img2\cancel-page-new-en.png | image | |
MD5:— | SHA256:— | |||
| 2328 | file_id4649039ids1s.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\archive.7z | compressed | |
MD5:— | SHA256:— | |||
| 2328 | file_id4649039ids1s.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\img2\cancel-page-new2-ru.png | image | |
MD5:— | SHA256:— | |||
| 2328 | file_id4649039ids1s.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2328 | file_id4649039ids1s.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\page-wait.png | image | |
MD5:260D2169A4421CBB34EACDA43319AB36 | SHA256:F8F5F8F933F389C156703E00DC00205B7991E87AB0D3CDD6F65FBDAB2697671B | |||
| 2328 | file_id4649039ids1s.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2328 | file_id4649039ids1s.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\preloader.html | html | |
MD5:99FE6F416A71D610999A774A5931CA60 | SHA256:CD86C3E177C1F5A6AF3D45AD76665F42EA2B45D80821D180B286FAC0F845EE15 | |||
| 2328 | file_id4649039ids1s.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\img2\bundle1-check-off.png | image | |
MD5:A5E92D07D4F8804726D7D8429791DD48 | SHA256:F2541446FDD1AA134A66B9A6F91EBF7F880F0A6120E0BFBC85E7BEE3A6D49DB7 | |||
| 2328 | file_id4649039ids1s.exe | C:\Users\admin\AppData\Local\Temp\mediaget-installer-tmp\img2\bundle1-check-on.png | image | |
MD5:3E30B7AE8F178D065D094AAE7829ECA8 | SHA256:F894CCDDA93A17A8B7B0DCE1D295E490C2B66444E05A8F5B319515CF83378361 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
130
DNS requests
54
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
756 | QtWebEngineProcess.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CECosiqdXosrVzE6LrmbYt3c%3D | RU | der | 1.48 Kb | whitelisted |
756 | QtWebEngineProcess.exe | GET | 200 | 95.100.153.123:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | unknown | der | 1.50 Kb | whitelisted |
756 | QtWebEngineProcess.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEE4I%2FiUGSyiBCgAAAAEQNAg%3D | US | der | 471 b | whitelisted |
2328 | file_id4649039ids1s.exe | GET | 200 | 92.123.195.83:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPS%2B8NSiKObqhDnR4BRPcDc9A%3D%3D | unknown | der | 503 b | shared |
756 | QtWebEngineProcess.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDwz%2Fr0hq6lmQoAAAABEDeb | US | der | 472 b | whitelisted |
— | — | GET | 200 | 3.94.40.55:80 | http://lumtest.com/myip.json | US | text | 266 b | suspicious |
756 | QtWebEngineProcess.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
756 | QtWebEngineProcess.exe | GET | 200 | 142.250.185.163:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
— | — | GET | 200 | 3.94.72.89:80 | http://3.94.72.89:80/myip.json | US | text | 266 b | suspicious |
3336 | net_updater32.exe | GET | 200 | 104.18.30.182:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEB2iSDBvmyYY0ILgln0z02o%3D | US | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2328 | file_id4649039ids1s.exe | 92.123.195.83:80 | r3.o.lencr.org | Akamai International B.V. | — | whitelisted |
880 | net_updater32.exe | 142.93.74.196:443 | perr.l-err.biz | — | CA | suspicious |
2328 | file_id4649039ids1s.exe | 51.15.43.19:443 | mediaget.com | Online S.a.s. | NL | unknown |
2328 | file_id4649039ids1s.exe | 51.158.177.208:443 | mediaget.com | — | GB | unknown |
880 | net_updater32.exe | 51.158.177.208:443 | mediaget.com | — | GB | unknown |
2328 | file_id4649039ids1s.exe | 104.89.32.83:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | suspicious |
— | — | 142.93.74.196:443 | perr.l-err.biz | — | CA | suspicious |
1436 | net_updater32.exe | 162.125.66.18:443 | www.dropbox.com | Dropbox, Inc. | DE | suspicious |
880 | net_updater32.exe | 162.125.66.18:443 | www.dropbox.com | Dropbox, Inc. | DE | suspicious |
3336 | net_updater32.exe | 142.93.74.196:443 | perr.l-err.biz | — | CA | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mediaget.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
www.dropbox.com |
| shared |
perr.l-err.biz |
| suspicious |
perr.lum-sdk.io |
| suspicious |
clientsdk.lum-sdk.io |
| suspicious |
dht.libtorrent.org |
| suspicious |
router.bittorrent.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
880 | net_updater32.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
— | — | Potential Corporate Privacy Violation | ET P2P BitTorrent DHT ping request |
— | — | Potential Corporate Privacy Violation | ET P2P Vuze BT UDP Connection (5) |
3 ETPRO signatures available at the full report
Process | Message |
|---|---|
mediaget.exe | > __thiscall Application::Application(int &,char *[])
|
mediaget.exe | os version: "6.1.7601v" __ os name: "Windows 7 Version 6.1 (Build 7601: SP 1)"
|
mediaget.exe | > int __thiscall Application::exec(void)
|
mediaget.exe | > __thiscall MediagetServerSettings::MediagetServerSettings(void)
|
mediaget.exe | INSTALL ID: "" _ OLD ID: ""
|
mediaget.exe | reseller - "" installId ""
|
mediaget.exe | > void __thiscall MediagetServerSettings::flushSettings(void)
|