| File name: | _93478.exe |
| Full analysis: | https://app.any.run/tasks/22ad59b2-b360-4ab3-9009-3201ea5cfc98 |
| Verdict: | Malicious activity |
| Analysis date: | June 06, 2019, 07:55:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EA02D95F0A8A0D3737D3750BB53DA4B6 |
| SHA1: | 090AAFE4E2C0A306A1A5BBC0C798E97F13D7117A |
| SHA256: | 18849ADCF96078DBF53D460322EFF5C5BA469F1D22A5D34DB31DE46F4EFA5068 |
| SSDEEP: | 196608:EDFoBU8EpVS9uZ1BKKIKo32Zfc1eQOTP1i0dfxk70Mkb04:KFtVSGKaaXO71L1EM5 |
MALICIOUS
Application was dropped or rewritten from another process
- HzzInstaller.exe (PID: 3700)
- HzzInstaller.exe (PID: 3508)
- hzzInit.exe (PID: 2716)
- HzzInstaller.exe (PID: 2428)
- HzzInstaller.exe (PID: 3012)
- TaskSetter.exe (PID: 2496)
- sll.exe (PID: 3700)
- TaskSetter.exe (PID: 2304)
- checkFirewall.exe (PID: 3596)
- start.exe (PID: 2744)
- nvsc.exe (PID: 3756)
- hzzSrvInit.exe (PID: 2280)
- sllsrv.exe (PID: 3048)
- comUpdate.exe (PID: 2936)
- start.exe (PID: 344)
- sll.exe (PID: 3692)
- hzzSrvInit.exe (PID: 3712)
- nvsc.exe (PID: 3404)
- sllsrv.exe (PID: 3312)
- checkFirewall.exe (PID: 2680)
Loads the Task Scheduler COM API
- TaskSetter.exe (PID: 2304)
- schtasks.exe (PID: 3844)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3160)
Loads dropped or rewritten executable
- sll.exe (PID: 3700)
- explorer.exe (PID: 252)
- nvsc.exe (PID: 3756)
- sllsrv.exe (PID: 3048)
- DllHost.exe (PID: 2532)
- ctfmon.exe (PID: 2000)
- comUpdate.exe (PID: 2936)
- sll.exe (PID: 3692)
- nvsc.exe (PID: 3404)
- sllsrv.exe (PID: 3312)
Changes settings of System certificates
- sllsrv.exe (PID: 3048)
SUSPICIOUS
Executable content was dropped or overwritten
- _93478.tmp (PID: 2964)
- _93478.exe (PID: 3300)
- _93478.exe (PID: 2384)
Creates files in the program directory
- sll.exe (PID: 3700)
- HzzInstaller.exe (PID: 3012)
- comUpdate.exe (PID: 2936)
Starts CMD.EXE for commands execution
- TaskSetter.exe (PID: 2304)
- hzzSrvInit.exe (PID: 2280)
Executed via Task Scheduler
- TaskSetter.exe (PID: 2496)
Adds / modifies Windows certificates
- sllsrv.exe (PID: 3048)
Executed as Windows Service
- sllsrv.exe (PID: 3048)
- sllsrv.exe (PID: 3312)
Removes files from Windows directory
- sllsrv.exe (PID: 3048)
- sllsrv.exe (PID: 3312)
Creates files in the Windows directory
- sllsrv.exe (PID: 3048)
- sllsrv.exe (PID: 3312)
Starts SC.EXE for service management
- cmd.exe (PID: 2776)
Reads CPU info
- sll.exe (PID: 3700)
Reads Environment values
- sll.exe (PID: 3700)
INFO
Application was dropped or rewritten from another process
- _93478.tmp (PID: 2396)
- HzzInstaller.exe (PID: 2340)
- _93478.tmp (PID: 2964)
- HzzInstaller.exe (PID: 3712)
Creates a software uninstall entry
- _93478.tmp (PID: 2964)
Creates files in the program directory
- _93478.tmp (PID: 2964)
Reads settings of System Certificates
- sll.exe (PID: 3700)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41984 |
| InitializedDataSize: | 17920 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaad0 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.6.0.0 |
| ProductVersionNumber: | 6.6.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | System Sll |
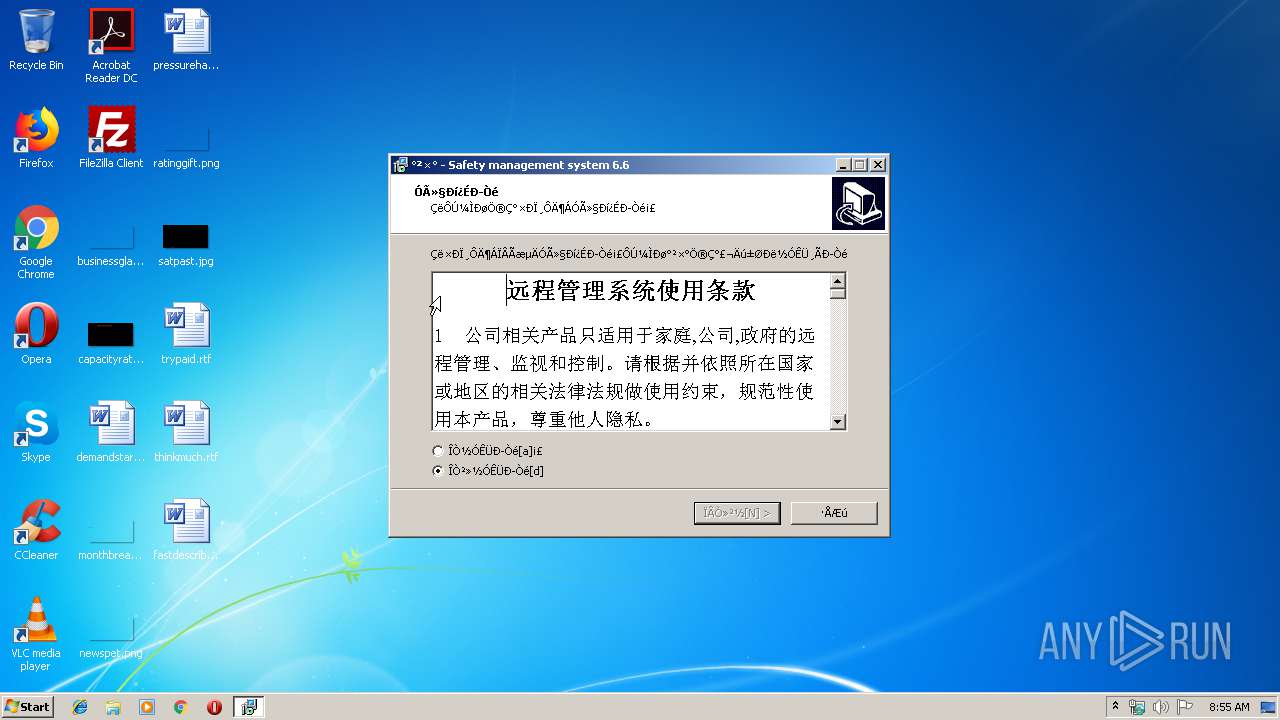
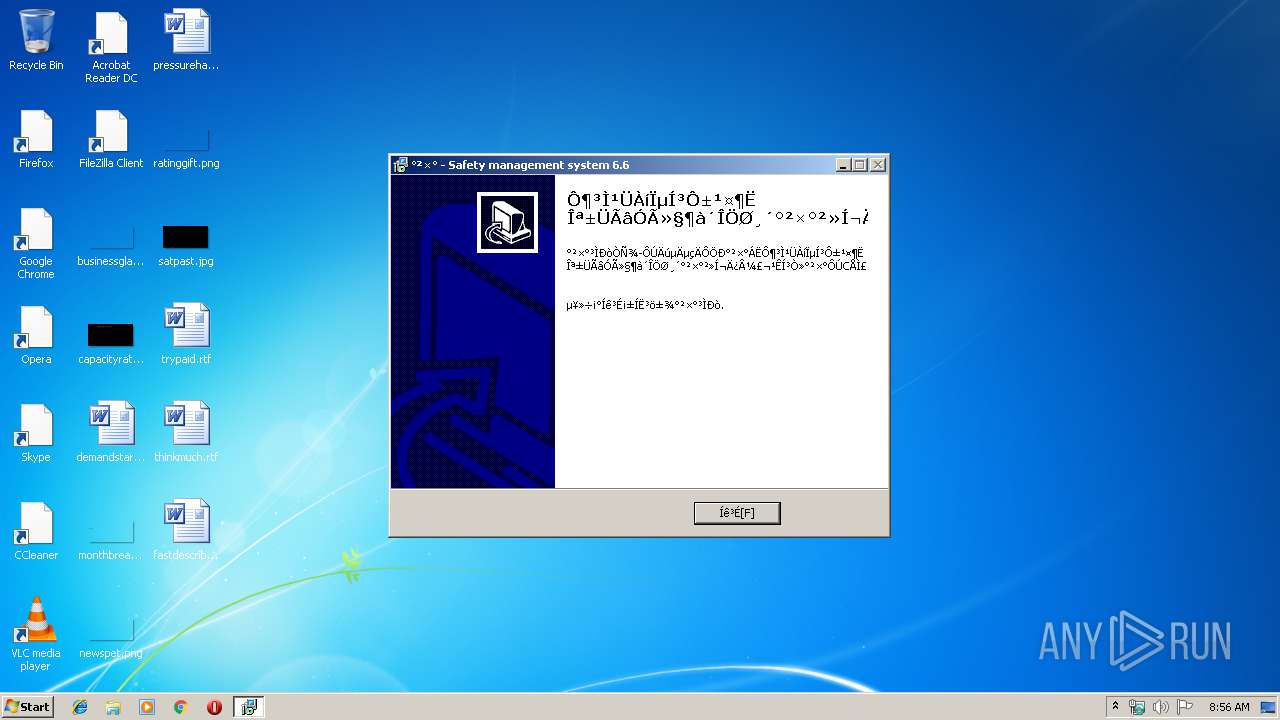
| FileDescription: | 远程管理系统员工端 为避免用户多次重复安装不同目录,故统一安装在C盘,不同意请取消安装 Setup |
| FileVersion: | 6.6 |
| LegalCopyright: | Copyright© 2014-2018 |
| ProductName: | 远程管理系统员工端 为避免用户多次重复安装不同目录,故统一安装在C盘,不同意请取消安装 |
| ProductVersion: | 6.6.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | System Sll |
| FileDescription: | 远程管理系统员工端 为避免用户多次重复安装不同目录,故统一安装在C盘,不同意请取消安装 Setup |
| FileVersion: | 6.6 |
| LegalCopyright: | Copyright© 2014-2018 |
| ProductName: | 远程管理系统员工端 为避免用户多次重复安装不同目录,故统一安装在C盘,不同意请取消安装 |
| ProductVersion: | 6.6.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x0000A208 | 0x0000A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60167 |
DATA | 0x0000C000 | 0x00000250 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.77135 |
BSS | 0x0000D000 | 0x00000E94 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000E000 | 0x0000097C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.48608 |
.tls | 0x0000F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00010000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.190489 |
.reloc | 0x00011000 | 0x00000920 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00012000 | 0x00002C00 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.69408 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4089 | 3.21823 | 754 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 2.86149 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.20731 | 180 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.04592 | 174 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
71
Monitored processes
33
Malicious processes
10
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ctfmon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 344 | "C:\Program Files\Common Files\System Sll\start.exe" hide | C:\Program Files\Common Files\System Sll\start.exe | — | sll.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2000 | C:\Windows\System32\ctfmon.exe | C:\Windows\System32\ctfmon.exe | — | taskeng.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CTF Loader Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Common Files\System Sll\hzzSrvInit.exe" /install | C:\Program Files\Common Files\System Sll\hzzSrvInit.exe | — | sll.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.2 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Common Files\System Sll\TaskSetter.exe" /install | C:\Program Files\Common Files\System Sll\TaskSetter.exe | — | _93478.tmp | |||||||||||
User: admin Company: Weifang Gray Dove Security Engineering Co.,Ltd. Integrity Level: HIGH Description: 防止系统主进程被意外关闭 Exit code: 0 Version: 1.0.0.15 Modules
| |||||||||||||||
| 2340 | "C:\Users\admin\AppData\Local\Temp\is-FB09D.tmp\HzzInstaller.exe" /checkparam /srcexe "C:\Users\admin\AppData\Local\Temp\_93478.exe" /pid 2964 | C:\Users\admin\AppData\Local\Temp\is-FB09D.tmp\HzzInstaller.exe | — | _93478.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.10 Modules
| |||||||||||||||
| 2384 | "C:\Users\admin\AppData\Local\Temp\_93478.exe" /SPAWNWND=$70284 /NOTIFYWND=$7011E | C:\Users\admin\AppData\Local\Temp\_93478.exe | _93478.tmp | ||||||||||||
User: admin Company: System Sll Integrity Level: HIGH Description: 远程管理系统员工端 为避免用户多次重复安装不同目录,故统一安装在C盘,不同意请取消安装 Setup Exit code: 0 Version: 6.6 Modules
| |||||||||||||||
| 2396 | "C:\Users\admin\AppData\Local\Temp\is-NAU36.tmp\_93478.tmp" /SL5="$7011E,7129959,58368,C:\Users\admin\AppData\Local\Temp\_93478.exe" | C:\Users\admin\AppData\Local\Temp\is-NAU36.tmp\_93478.tmp | — | _93478.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Common Files\System Sll\HzzInstaller.exe" /judgesys | C:\Program Files\Common Files\System Sll\HzzInstaller.exe | — | _93478.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.10 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Common Files\System Sll\TaskSetter.exe" /watch | C:\Program Files\Common Files\System Sll\TaskSetter.exe | — | taskeng.exe | |||||||||||
User: admin Company: Weifang Gray Dove Security Engineering Co.,Ltd. Integrity Level: HIGH Description: 防止系统主进程被意外关闭 Exit code: 0 Version: 1.0.0.15 Modules
| |||||||||||||||
Total events
1 021
Read events
882
Write events
138
Delete events
1
Modification events
| (PID) Process: | (2964) _93478.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2964) _93478.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3700) HzzInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\System Sll_is1 |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (2964) _93478.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\System Sll_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.6.1 (a) | |||
| (PID) Process: | (2964) _93478.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\System Sll_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Common Files\System Sll | |||
| (PID) Process: | (2964) _93478.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\System Sll_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Common Files\System Sll\ | |||
| (PID) Process: | (2964) _93478.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\System Sll_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Ô¶³Ì¹ÜÀíϵͳԱ¹¤¶Ë Ϊ±ÜÃâÓû§¶à´ÎÖظ´°²×°²»Í¬Ä¿Â¼£¬¹Êͳһ°²×°ÔÚCÅÌ£¬²»Í¬ÒâÇëÈ¡Ïû°²×° | |||
| (PID) Process: | (2964) _93478.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\System Sll_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2964) _93478.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\System Sll_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: Chinese | |||
| (PID) Process: | (2964) _93478.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\System Sll_is1 |
| Operation: | write | Name: | DisplayName |
Value: Safety management system 6.6 | |||
Executable files
82
Suspicious files
18
Text files
43
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2964 | _93478.tmp | C:\Program Files\Common Files\System Sll\is-QE92D.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | _93478.tmp | C:\Program Files\Common Files\System Sll\is-SV7LN.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | _93478.tmp | C:\Program Files\Common Files\System Sll\config\is-DL65I.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | _93478.tmp | C:\Program Files\Common Files\System Sll\config\hzz_test.xml | — | |
MD5:— | SHA256:— | |||
| 2964 | _93478.tmp | C:\Program Files\Common Files\System Sll\fmtm\is-U0212.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | _93478.tmp | C:\Program Files\Common Files\System Sll\fmtm\is-JS67O.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | _93478.tmp | C:\Program Files\Common Files\System Sll\fmtm\is-0AVRG.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | _93478.tmp | C:\Program Files\Common Files\System Sll\fmtm\is-KPUPE.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | _93478.tmp | C:\Program Files\Common Files\System Sll\fmtm\x64\is-O0RNC.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | _93478.tmp | C:\Program Files\Common Files\System Sll\fmtm\x64\is-6VVMA.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
21
DNS requests
9
Threats
11
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2936 | comUpdate.exe | GET | — | 123.59.116.117:8000 | http://update.hgzvip.net:8000/employee/update.dat?t=1422796892465 | CN | — | — | malicious |
2936 | comUpdate.exe | GET | — | 123.59.116.117:8000 | http://update.hgzvip.net:8000/employee/update/netrcd\main.ini | CN | — | — | malicious |
2936 | comUpdate.exe | GET | — | 123.59.116.117:8000 | http://update.hgzvip.net:8000/employee/update/DomainJump\DJ.log | CN | — | — | malicious |
2936 | comUpdate.exe | GET | — | 123.59.116.117:8000 | http://update.hgzvip.net:8000/employee/control.ini | CN | — | — | malicious |
2936 | comUpdate.exe | GET | — | 123.59.116.117:8000 | http://update.hgzvip.net:8000/employee/update/sll.exe.config | CN | — | — | malicious |
3700 | sll.exe | GET | 200 | 163.171.141.220:80 | http://api.ip138.com/query/?datatype=jsonp&token=cb7b47fb53f57902917d914c81030b28 | US | text | 34 b | suspicious |
3048 | sllsrv.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.2 Kb | whitelisted |
3048 | sllsrv.exe | GET | 200 | 2.16.186.64:80 | http://ocsp1.wosign.com/class3/code/ca1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTqEnJhU5dFi16HHVA7etSPSTXCygQU9QKqS9PgGo53UNYau%2BvfuYNwsE4CEB0XQkkfPiqe5cpALaflbWo%3D | unknown | der | 1.49 Kb | whitelisted |
3048 | sllsrv.exe | GET | 200 | 2.16.186.64:80 | http://ocsp1.wosign.com/ca1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQwinUuszX0zOc4yUA1%2Besb7TlGXgQU4WbPDtHxs0u3BiAU%2FocS1fb%2B%2Bz4CEEa7s0D6ucF5KJOMk9oQhnk%3D | unknown | der | 1.77 Kb | whitelisted |
3048 | sllsrv.exe | GET | 200 | 2.16.186.43:80 | http://ocsp.startssl.com/ca/MEgwRjBEMEIwQDAJBgUrDgMCGgUABBRBc6bT2N9qzRkeiWvn5WI5MHBpNQQUTgvvGqRAW6UXaYcwyjRoQ9BBrvICBxnChTDpOzY%3D | unknown | der | 1.72 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3700 | sll.exe | 188.131.140.109:4530 | microsoft.hgzvip.net | — | CN | malicious |
3048 | sllsrv.exe | 2.16.186.114:80 | aia.startssl.com | Akamai International B.V. | — | whitelisted |
3048 | sllsrv.exe | 205.185.216.10:80 | www.download.windowsupdate.com | Highwinds Network Group, Inc. | US | whitelisted |
3700 | sll.exe | 188.131.140.109:4531 | microsoft.hgzvip.net | — | CN | malicious |
3048 | sllsrv.exe | 2.16.186.64:80 | ocsp1.wosign.com | Akamai International B.V. | — | whitelisted |
3700 | sll.exe | 163.171.141.220:80 | api.ip138.com | — | US | suspicious |
3700 | sll.exe | 123.59.209.193:9900 | — | China Unicom Beijing Province Network | CN | malicious |
3048 | sllsrv.exe | 2.16.186.57:80 | crl.startssl.com | Akamai International B.V. | — | whitelisted |
3692 | sll.exe | 188.131.140.109:4530 | microsoft.hgzvip.net | — | CN | malicious |
3692 | sll.exe | 188.131.140.109:4531 | microsoft.hgzvip.net | — | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft.hgzvip.net |
| malicious |
safe.hgzvip.net |
| malicious |
aia.startssl.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ocsp1.wosign.com |
| whitelisted |
api.ip138.com |
| suspicious |
ocsp.startssl.com |
| whitelisted |
update.hgzvip.net |
| malicious |
crl.startssl.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3700 | sll.exe | A Network Trojan was detected | MALWARE [PTsecurity] Heur:Backdoor/Huigezi |
3700 | sll.exe | A Network Trojan was detected | MALWARE [PTsecurity] Heur:Backdoor/Huigezi |
2936 | comUpdate.exe | A Network Trojan was detected | ET MALWARE Suspicious User-Agent (Mozilla/4.0 (compatible ICS)) |
2936 | comUpdate.exe | A Network Trojan was detected | ET MALWARE Suspicious User-Agent (Mozilla/4.0 (compatible ICS)) |
2936 | comUpdate.exe | A Network Trojan was detected | ET MALWARE Suspicious User-Agent (Mozilla/4.0 (compatible ICS)) |
2936 | comUpdate.exe | A Network Trojan was detected | ET MALWARE Suspicious User-Agent (Mozilla/4.0 (compatible ICS)) |
3700 | sll.exe | A Network Trojan was detected | MALWARE [PTsecurity] Heur:Backdoor/Huigezi |
2936 | comUpdate.exe | A Network Trojan was detected | ET MALWARE Suspicious User-Agent (Mozilla/4.0 (compatible ICS)) |
3692 | sll.exe | A Network Trojan was detected | MALWARE [PTsecurity] Heur:Backdoor/Huigezi |
2 ETPRO signatures available at the full report