| File name: | PyMacroRecord_1.1.8_Setup.exe |
| Full analysis: | https://app.any.run/tasks/85171eda-be7e-4104-8283-719a227523c0 |
| Verdict: | Malicious activity |
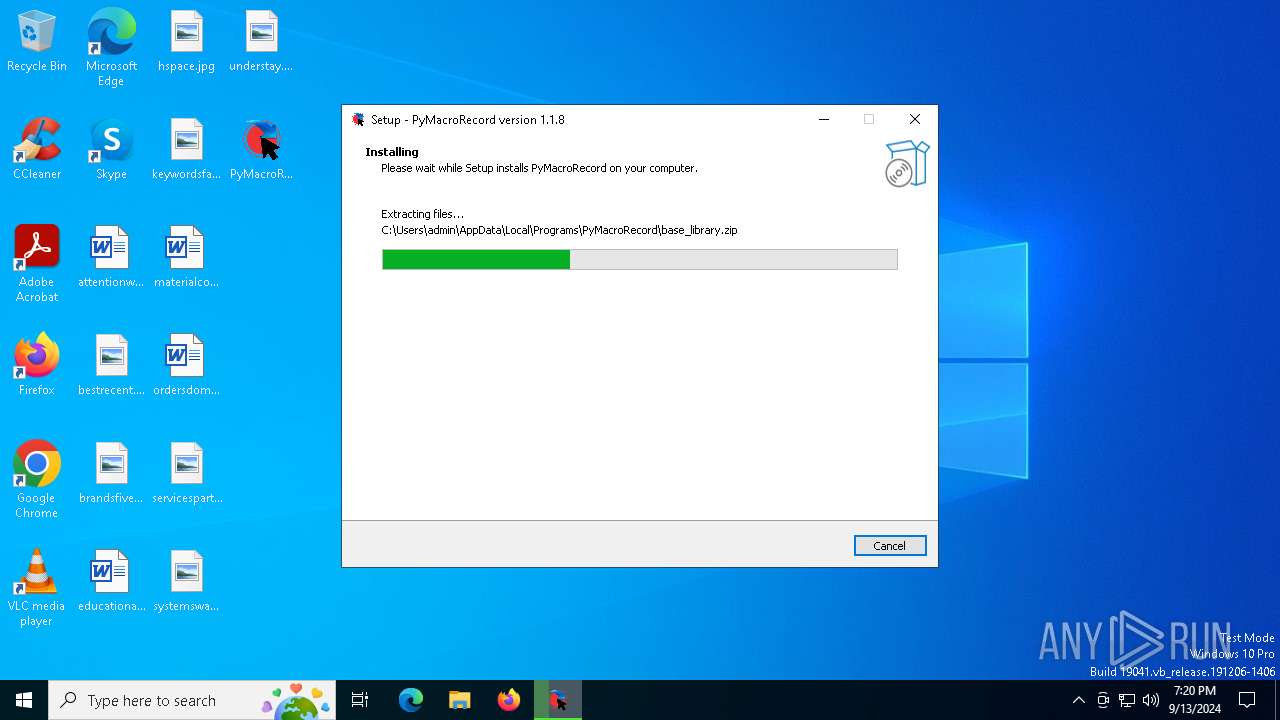
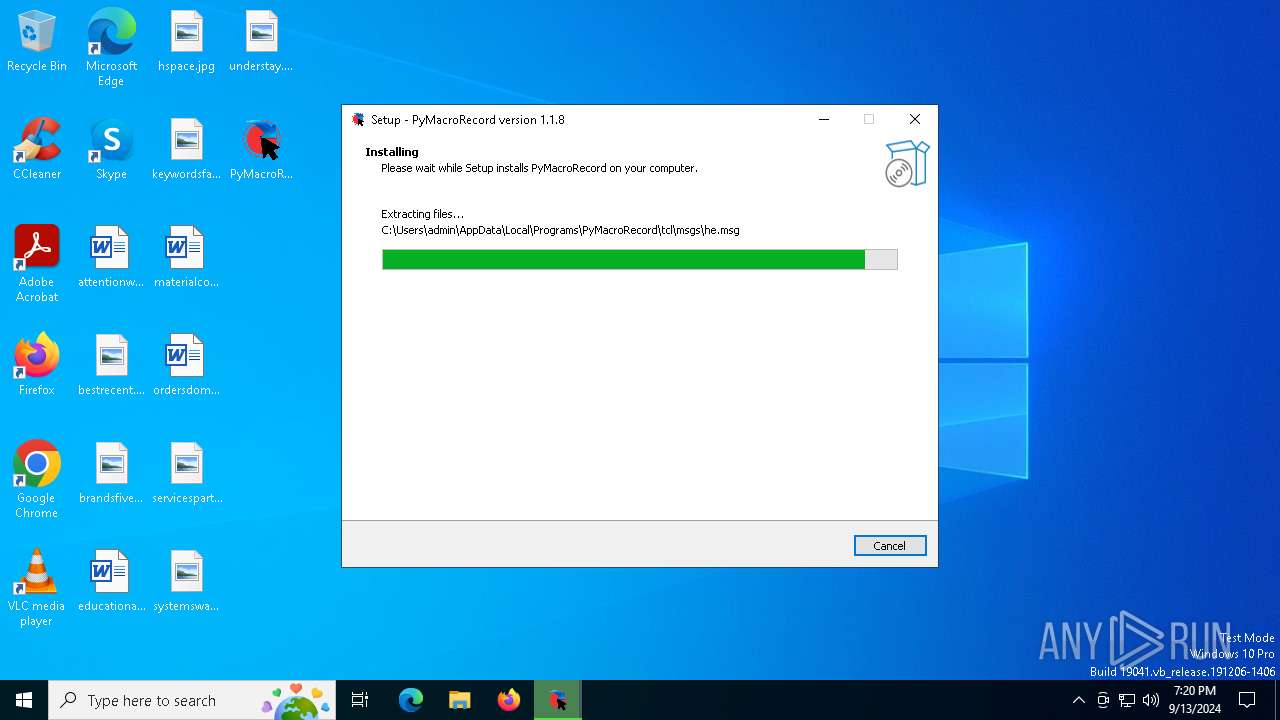
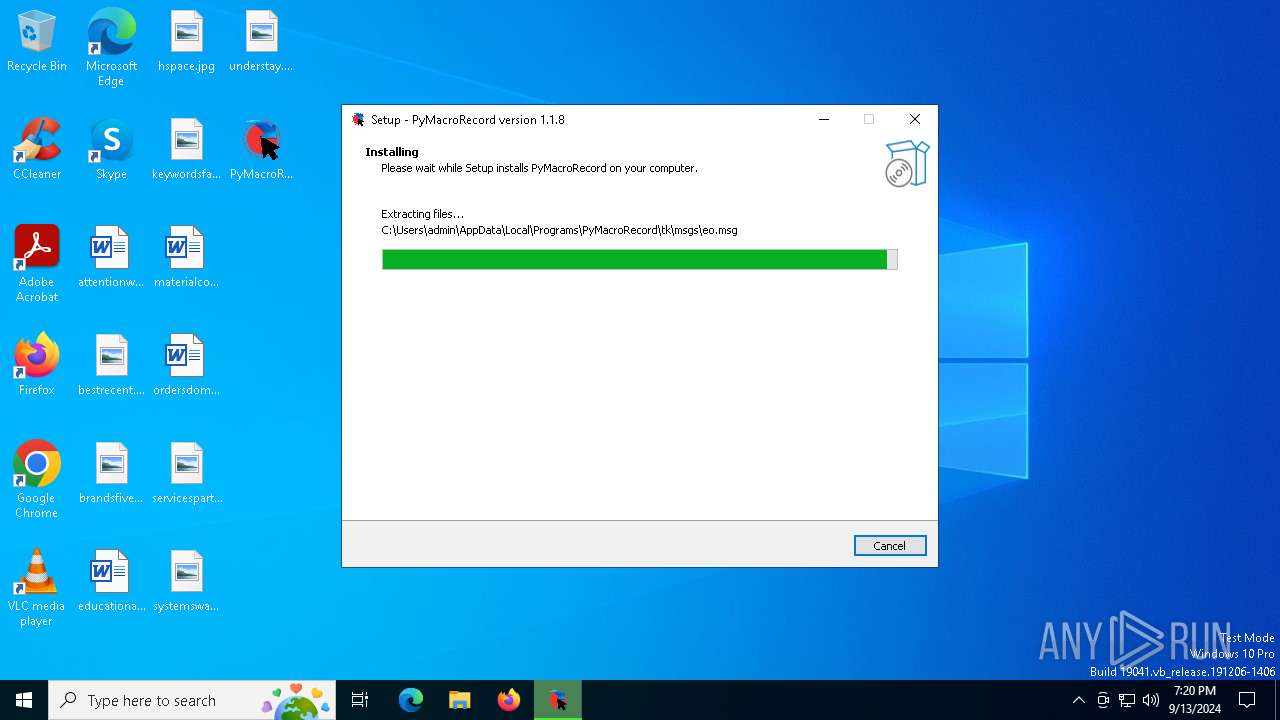
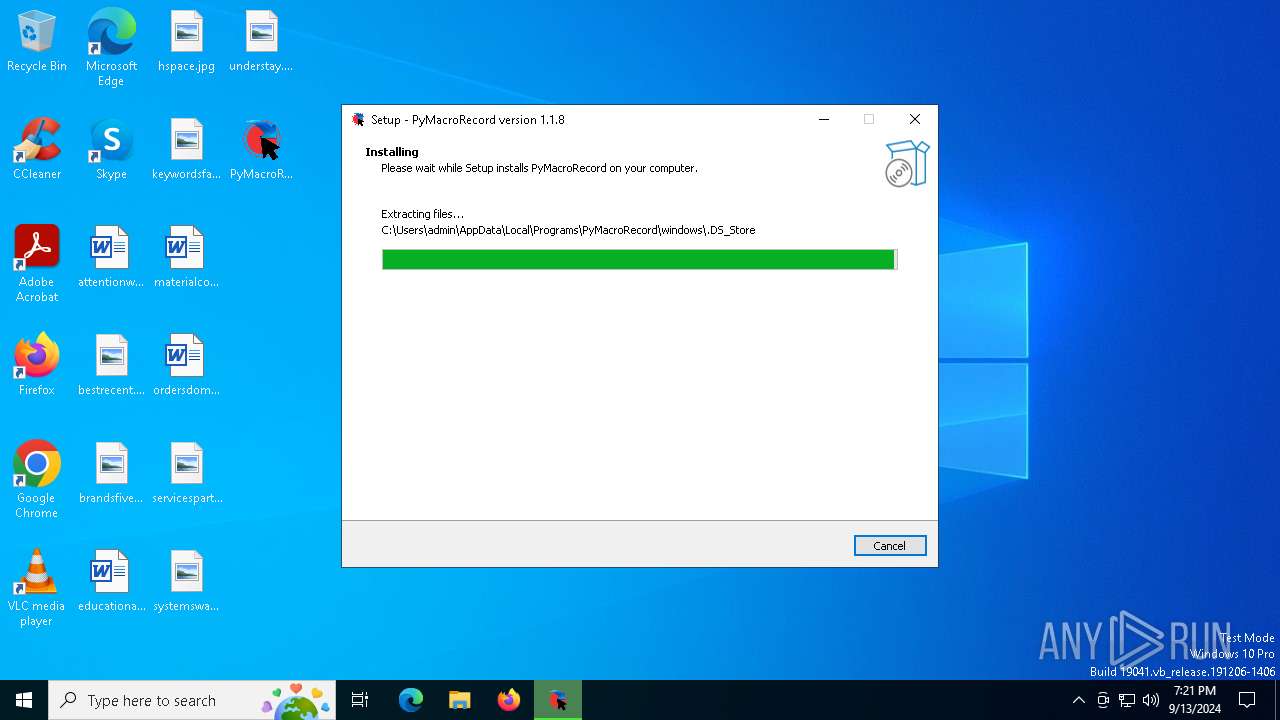
| Analysis date: | September 13, 2024, 19:20:00 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A8D51EA847469E1E10EF0FE0EDBAAB3D |
| SHA1: | F004326FFDD68C51821B828856D792E4DF9B32EE |
| SHA256: | 1883CCA1C4DD5C082FC6510C581147AF9E437FF7AE0138EA1BDB85EFECB0A312 |
| SSDEEP: | 98304:F+cD4dnBiVFoMyMhbN64GYJCuOYhiJb6jCZ6Pt8/gEIjvcCQ5QCqk7wAa9BH5tpY:oLNErBTvaPBl8uZZc3I+KvqPcUGdwy |
MALICIOUS
No malicious indicators.SUSPICIOUS
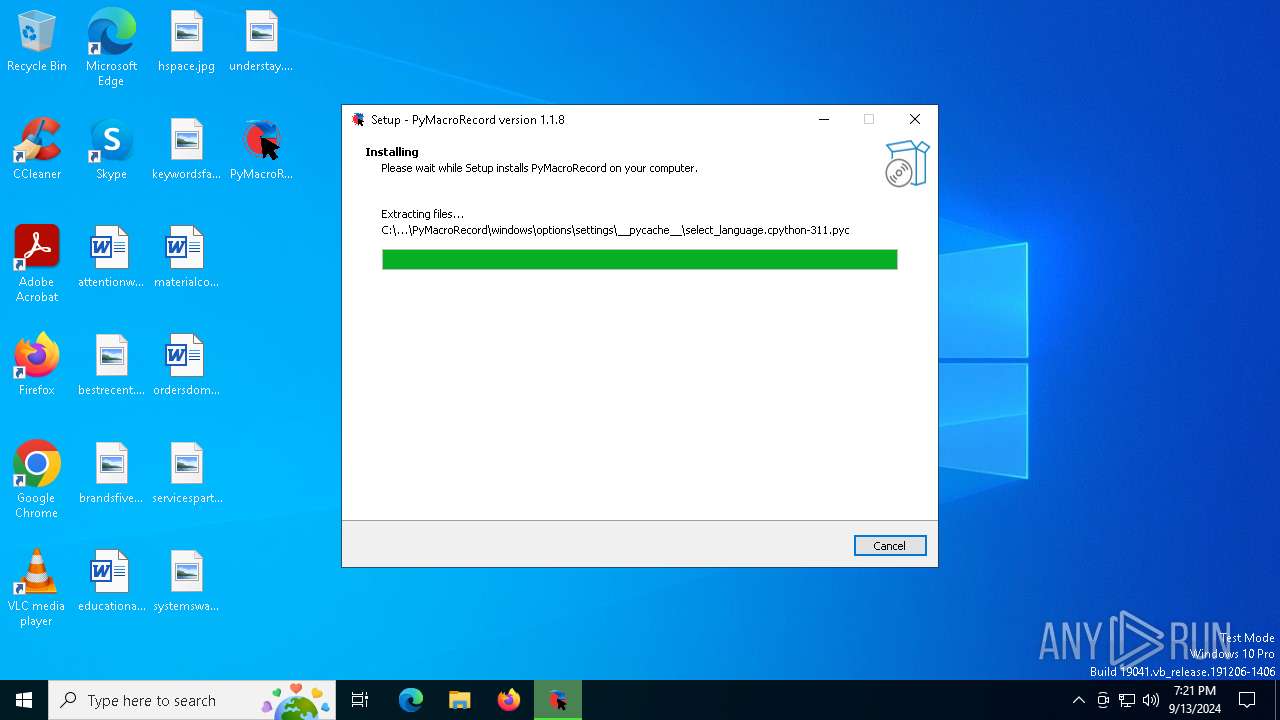
Executable content was dropped or overwritten
- PyMacroRecord_1.1.8_Setup.exe (PID: 5724)
- PyMacroRecord_1.1.8_Setup.tmp (PID: 6564)
Reads the Windows owner or organization settings
- PyMacroRecord_1.1.8_Setup.tmp (PID: 6564)
Process drops python dynamic module
- PyMacroRecord_1.1.8_Setup.tmp (PID: 6564)
There is functionality for taking screenshot (YARA)
- PyMacroRecord.exe (PID: 4344)
INFO
Create files in a temporary directory
- PyMacroRecord_1.1.8_Setup.exe (PID: 5724)
- PyMacroRecord_1.1.8_Setup.tmp (PID: 6564)
- PyMacroRecord.exe (PID: 4344)
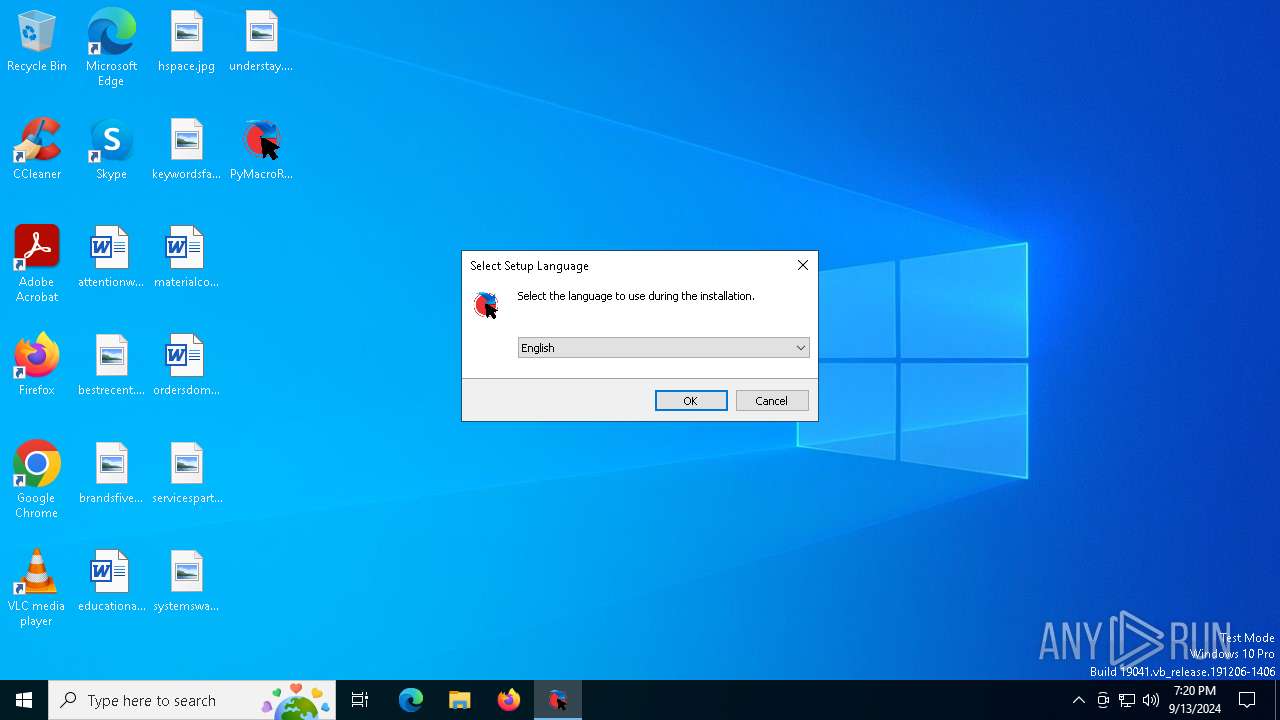
Checks supported languages
- PyMacroRecord_1.1.8_Setup.tmp (PID: 6564)
- PyMacroRecord_1.1.8_Setup.exe (PID: 5724)
- PyMacroRecord.exe (PID: 4344)
Creates files or folders in the user directory
- PyMacroRecord.exe (PID: 4344)
- PyMacroRecord_1.1.8_Setup.tmp (PID: 6564)
Reads the computer name
- PyMacroRecord_1.1.8_Setup.tmp (PID: 6564)
- PyMacroRecord.exe (PID: 4344)
UPX packer has been detected
- PyMacroRecord.exe (PID: 4344)
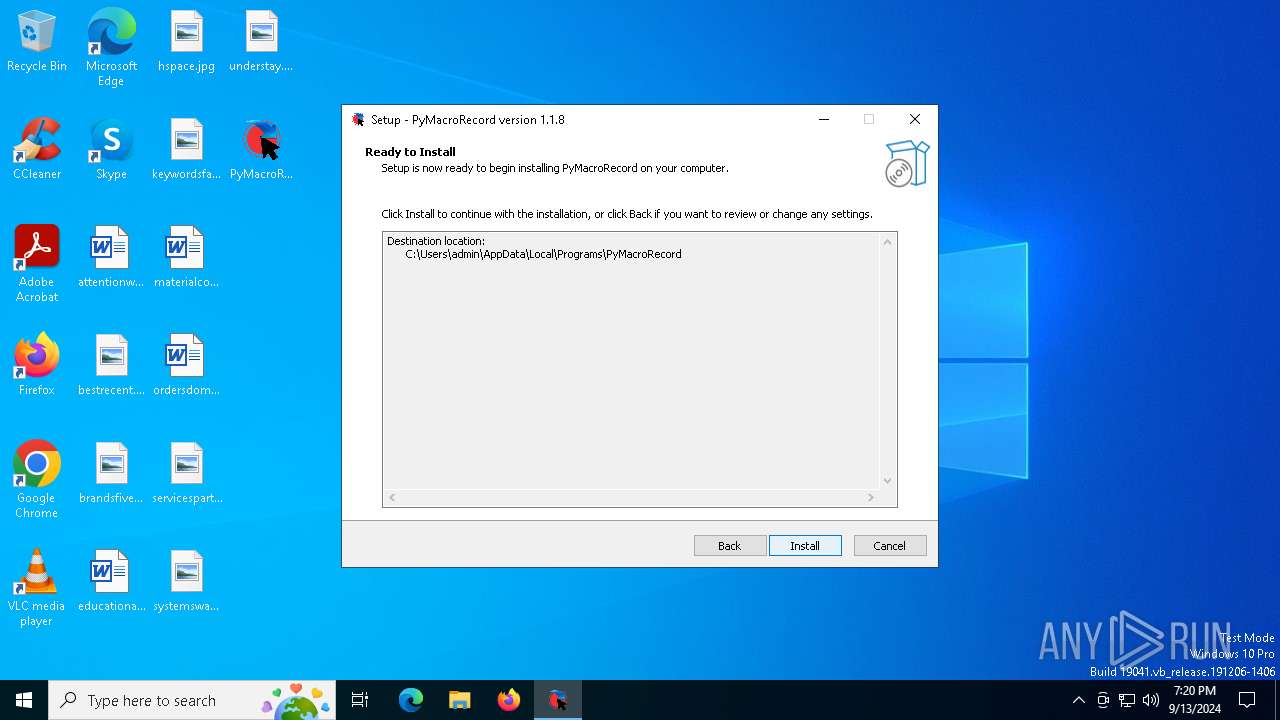
Creates a software uninstall entry
- PyMacroRecord_1.1.8_Setup.tmp (PID: 6564)
Checks proxy server information
- PyMacroRecord.exe (PID: 4344)
PyInstaller has been detected (YARA)
- PyMacroRecord.exe (PID: 4344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
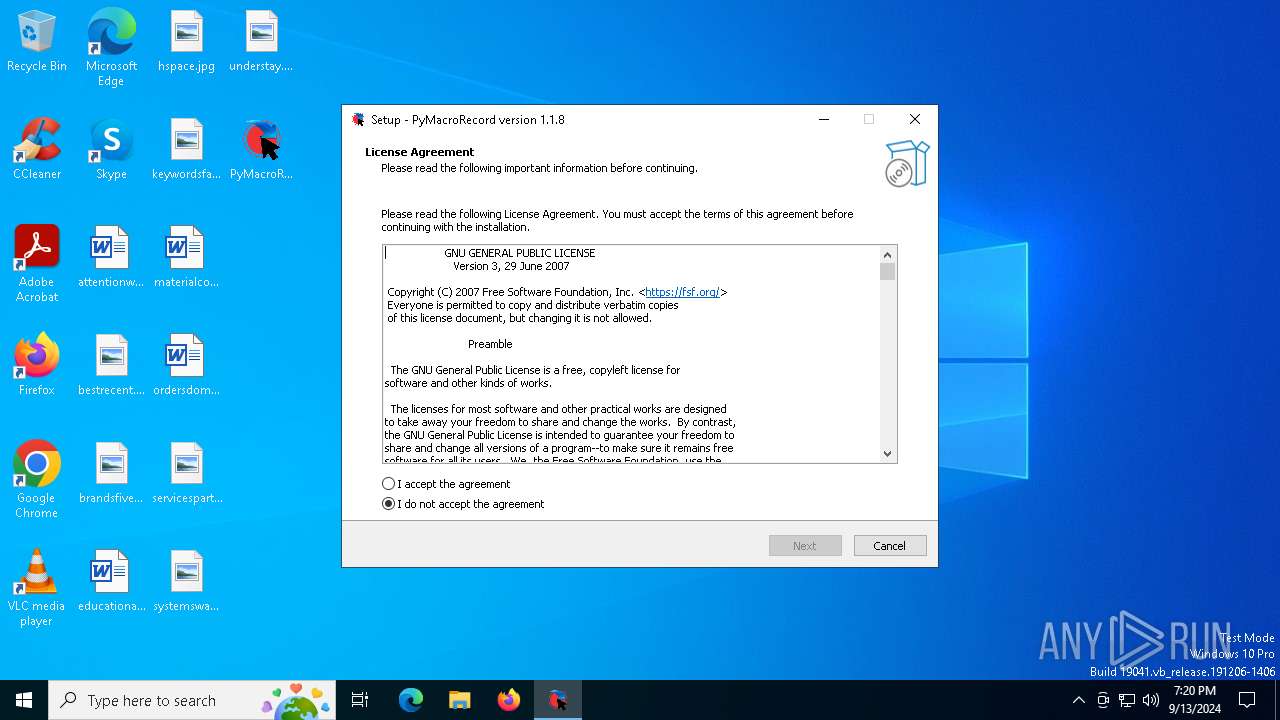
| .exe | | | Inno Setup installer (65.1) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (24.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.9) |
| .exe | | | Win32 Executable (generic) (2.6) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:15 14:54:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 70656 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | LOUDO |
| FileDescription: | PyMacroRecord Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | PyMacroRecord |
| ProductVersion: | 1.1.8 |
Total processes
126
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4344 | "C:\Users\admin\AppData\Local\Programs\PyMacroRecord\PyMacroRecord.exe" | C:\Users\admin\AppData\Local\Programs\PyMacroRecord\PyMacroRecord.exe | PyMacroRecord_1.1.8_Setup.tmp | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 5724 | "C:\Users\admin\Desktop\PyMacroRecord_1.1.8_Setup.exe" | C:\Users\admin\Desktop\PyMacroRecord_1.1.8_Setup.exe | explorer.exe | ||||||||||||
User: admin Company: LOUDO Integrity Level: MEDIUM Description: PyMacroRecord Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 6564 | "C:\Users\admin\AppData\Local\Temp\is-3131K.tmp\PyMacroRecord_1.1.8_Setup.tmp" /SL5="$503A8,12058526,813568,C:\Users\admin\Desktop\PyMacroRecord_1.1.8_Setup.exe" | C:\Users\admin\AppData\Local\Temp\is-3131K.tmp\PyMacroRecord_1.1.8_Setup.tmp | PyMacroRecord_1.1.8_Setup.exe | ||||||||||||
User: admin Company: LOUDO Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
590
Read events
562
Write events
28
Delete events
0
Modification events
| (PID) Process: | (6564) PyMacroRecord_1.1.8_Setup.tmp | Key: | HKEY_CLASSES_ROOT\.pmr\OpenWithProgids |
| Operation: | write | Name: | PyMacroRecordFile.pmr |
Value: | |||
| (PID) Process: | (6564) PyMacroRecord_1.1.8_Setup.tmp | Key: | HKEY_CLASSES_ROOT\Applications\PyMacroRecord.exe\SupportedTypes |
| Operation: | write | Name: | .myp |
Value: | |||
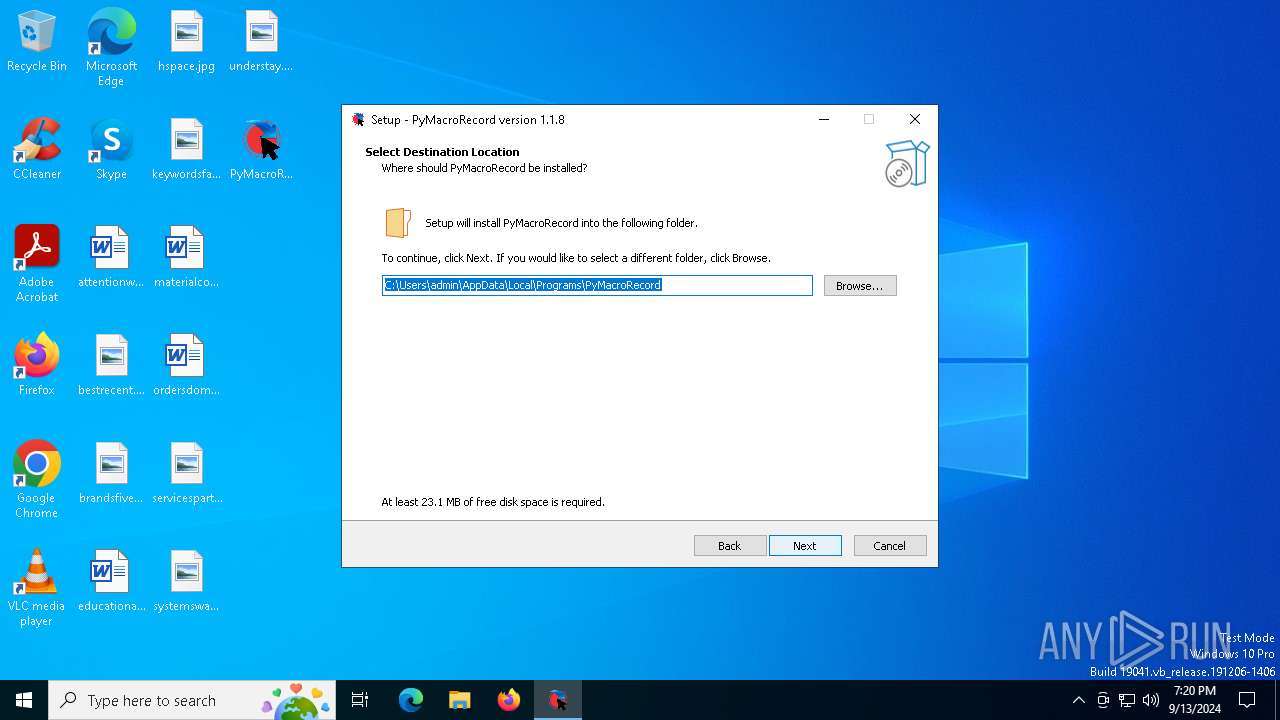
| (PID) Process: | (6564) PyMacroRecord_1.1.8_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{AD24EE86-03F0-4209-A794-57AFBC461017}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (6564) PyMacroRecord_1.1.8_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{AD24EE86-03F0-4209-A794-57AFBC461017}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Users\admin\AppData\Local\Programs\PyMacroRecord | |||
| (PID) Process: | (6564) PyMacroRecord_1.1.8_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{AD24EE86-03F0-4209-A794-57AFBC461017}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\PyMacroRecord\ | |||
| (PID) Process: | (6564) PyMacroRecord_1.1.8_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{AD24EE86-03F0-4209-A794-57AFBC461017}_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (6564) PyMacroRecord_1.1.8_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{AD24EE86-03F0-4209-A794-57AFBC461017}_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (6564) PyMacroRecord_1.1.8_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{AD24EE86-03F0-4209-A794-57AFBC461017}_is1 |
| Operation: | write | Name: | Inno Setup: Selected Tasks |
Value: | |||
| (PID) Process: | (6564) PyMacroRecord_1.1.8_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{AD24EE86-03F0-4209-A794-57AFBC461017}_is1 |
| Operation: | write | Name: | Inno Setup: Deselected Tasks |
Value: desktopicon | |||
| (PID) Process: | (6564) PyMacroRecord_1.1.8_Setup.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{AD24EE86-03F0-4209-A794-57AFBC461017}_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: english | |||
Executable files
145
Suspicious files
91
Text files
704
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6564 | PyMacroRecord_1.1.8_Setup.tmp | C:\Users\admin\AppData\Local\Programs\PyMacroRecord\PyMacroRecord.exe | executable | |
MD5:2F8A5664FFB42786EB785526A783EE6F | SHA256:2E734A7702937B1841CB2D567A8F21B3D42054BEA810E900B27B36AEBA7FAC6E | |||
| 6564 | PyMacroRecord_1.1.8_Setup.tmp | C:\Users\admin\AppData\Local\Programs\PyMacroRecord\is-UMM4M.tmp | executable | |
MD5:721B60B85094851C06D572F0BD5D88CD | SHA256:DAC867476CAA42FF8DF8F5DFE869FFD56A18DADEE17D47889AFB69ED6519AFBF | |||
| 6564 | PyMacroRecord_1.1.8_Setup.tmp | C:\Users\admin\AppData\Local\Programs\PyMacroRecord\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:721B60B85094851C06D572F0BD5D88CD | SHA256:DAC867476CAA42FF8DF8F5DFE869FFD56A18DADEE17D47889AFB69ED6519AFBF | |||
| 6564 | PyMacroRecord_1.1.8_Setup.tmp | C:\Users\admin\AppData\Local\Temp\is-DMBSM.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 6564 | PyMacroRecord_1.1.8_Setup.tmp | C:\Users\admin\AppData\Local\Programs\PyMacroRecord\is-034PM.tmp | executable | |
MD5:2F8A5664FFB42786EB785526A783EE6F | SHA256:2E734A7702937B1841CB2D567A8F21B3D42054BEA810E900B27B36AEBA7FAC6E | |||
| 6564 | PyMacroRecord_1.1.8_Setup.tmp | C:\Users\admin\AppData\Local\Programs\PyMacroRecord\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:0F7D418C05128246AFA335A1FB400CB9 | SHA256:5C9BC70586AD538B0DF1FCF5D6F1F3527450AE16935AA34BD7EB494B4F1B2DB9 | |||
| 6564 | PyMacroRecord_1.1.8_Setup.tmp | C:\Users\admin\AppData\Local\Programs\PyMacroRecord\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:557405C47613DE66B111D0E2B01F2FDB | SHA256:913EAAA7997A6AEE53574CFFB83F9C9C1700B1D8B46744A5E12D76A1E53376FD | |||
| 6564 | PyMacroRecord_1.1.8_Setup.tmp | C:\Users\admin\AppData\Local\Programs\PyMacroRecord\is-4NO18.tmp | executable | |
MD5:5A72A803DF2B425D5AAFF21F0F064011 | SHA256:629E52BA4E2DCA91B10EF7729A1722888E01284EED7DDA6030D0A1EC46C94086 | |||
| 6564 | PyMacroRecord_1.1.8_Setup.tmp | C:\Users\admin\AppData\Local\Programs\PyMacroRecord\is-0PUM0.tmp | executable | |
MD5:557405C47613DE66B111D0E2B01F2FDB | SHA256:913EAAA7997A6AEE53574CFFB83F9C9C1700B1D8B46744A5E12D76A1E53376FD | |||
| 6564 | PyMacroRecord_1.1.8_Setup.tmp | C:\Users\admin\AppData\Local\Programs\PyMacroRecord\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:5A72A803DF2B425D5AAFF21F0F064011 | SHA256:629E52BA4E2DCA91B10EF7729A1722888E01284EED7DDA6030D0A1EC46C94086 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
16
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1356 | svchost.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2016 | RUXIMICS.exe | GET | 200 | 104.119.109.218:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2120 | MoUsoCoreWorker.exe | 52.183.220.149:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1356 | svchost.exe | 52.183.220.149:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2016 | RUXIMICS.exe | 52.183.220.149:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2016 | RUXIMICS.exe | 104.119.109.218:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 104.119.109.218:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1356 | svchost.exe | 104.119.109.218:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1356 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
api.github.com |
| whitelisted |