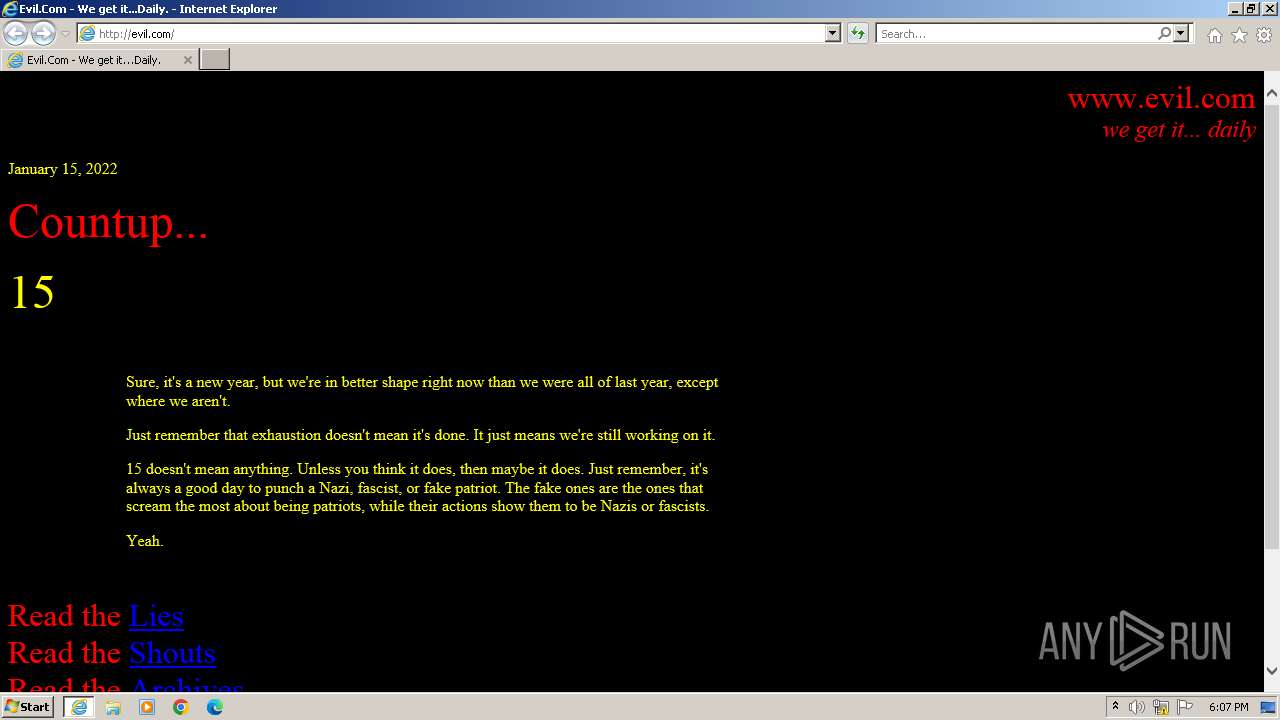
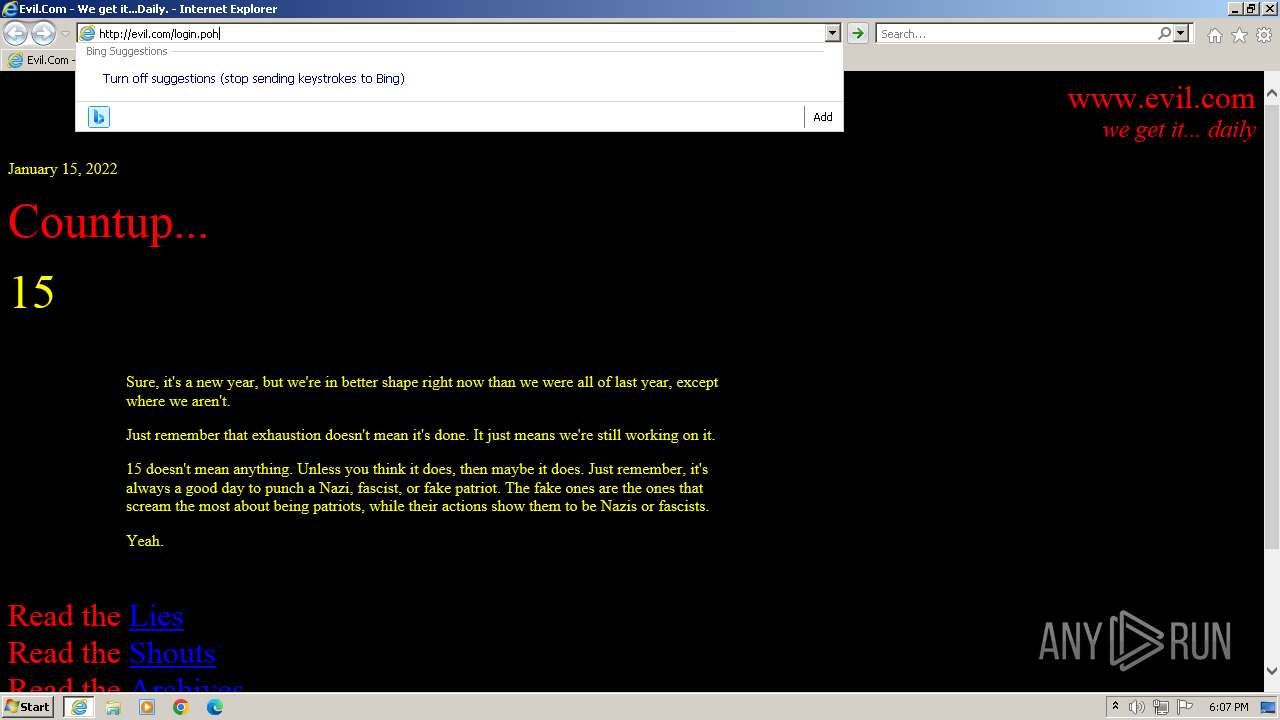
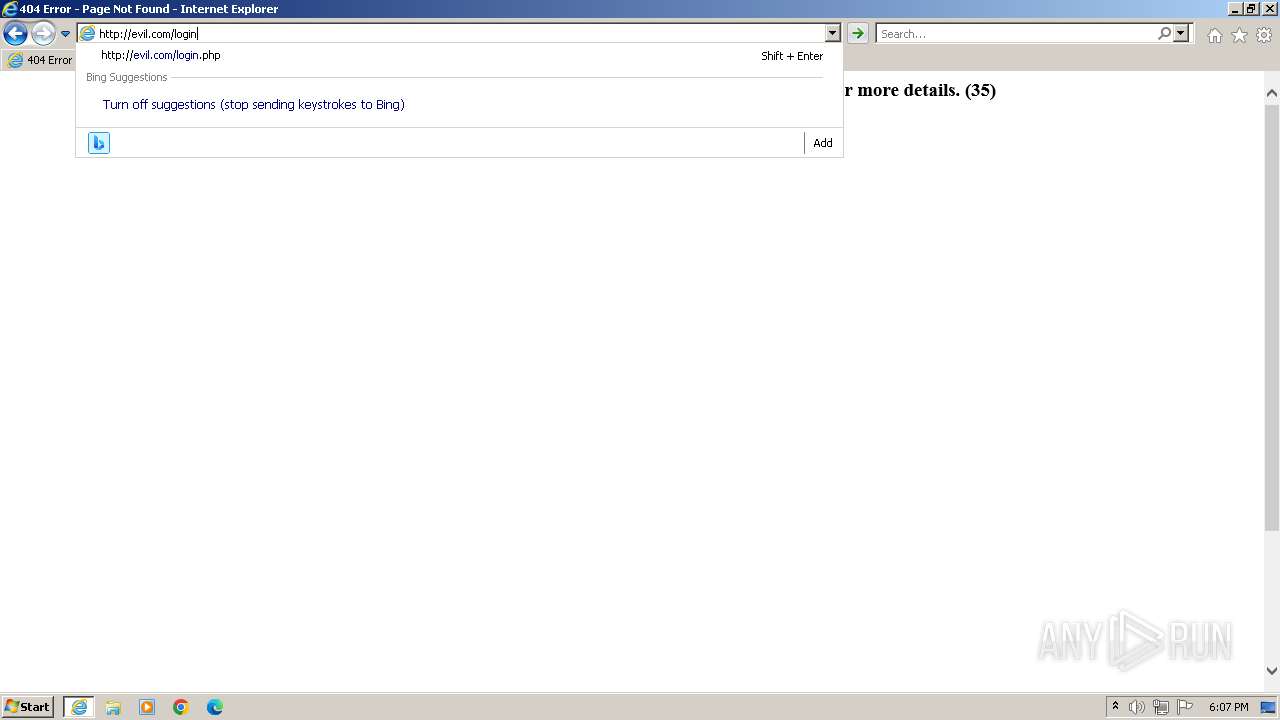
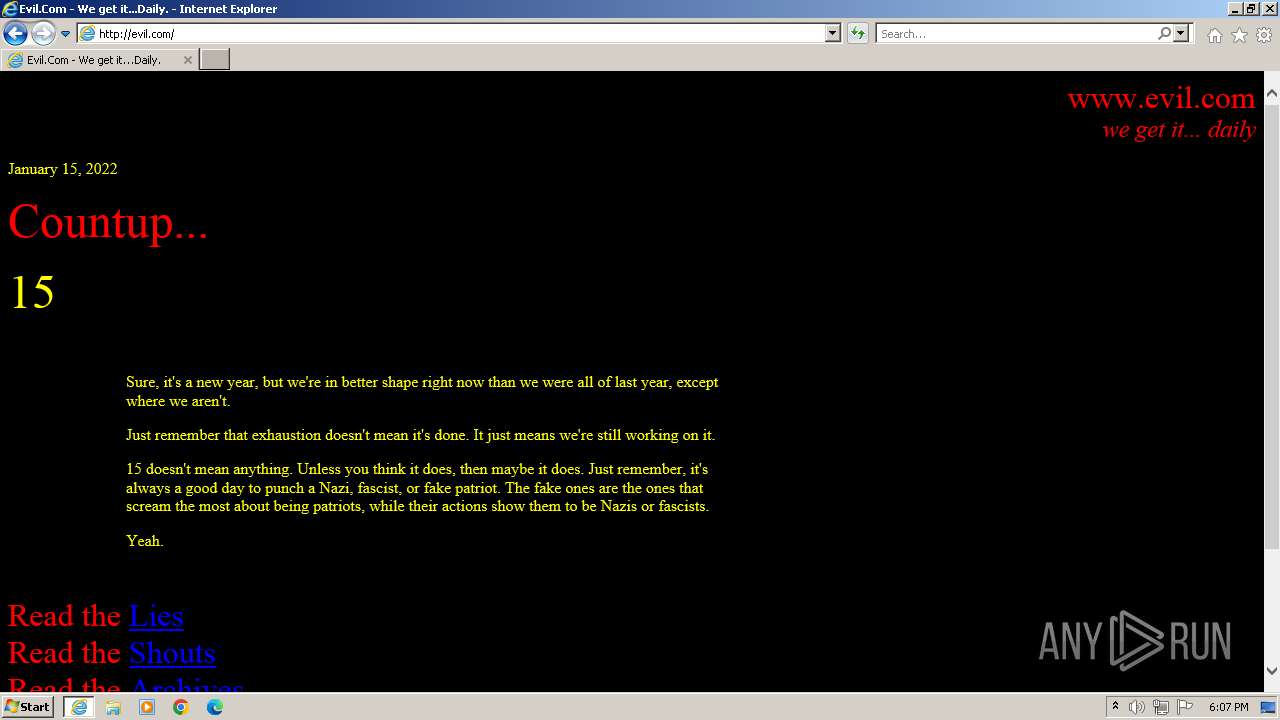
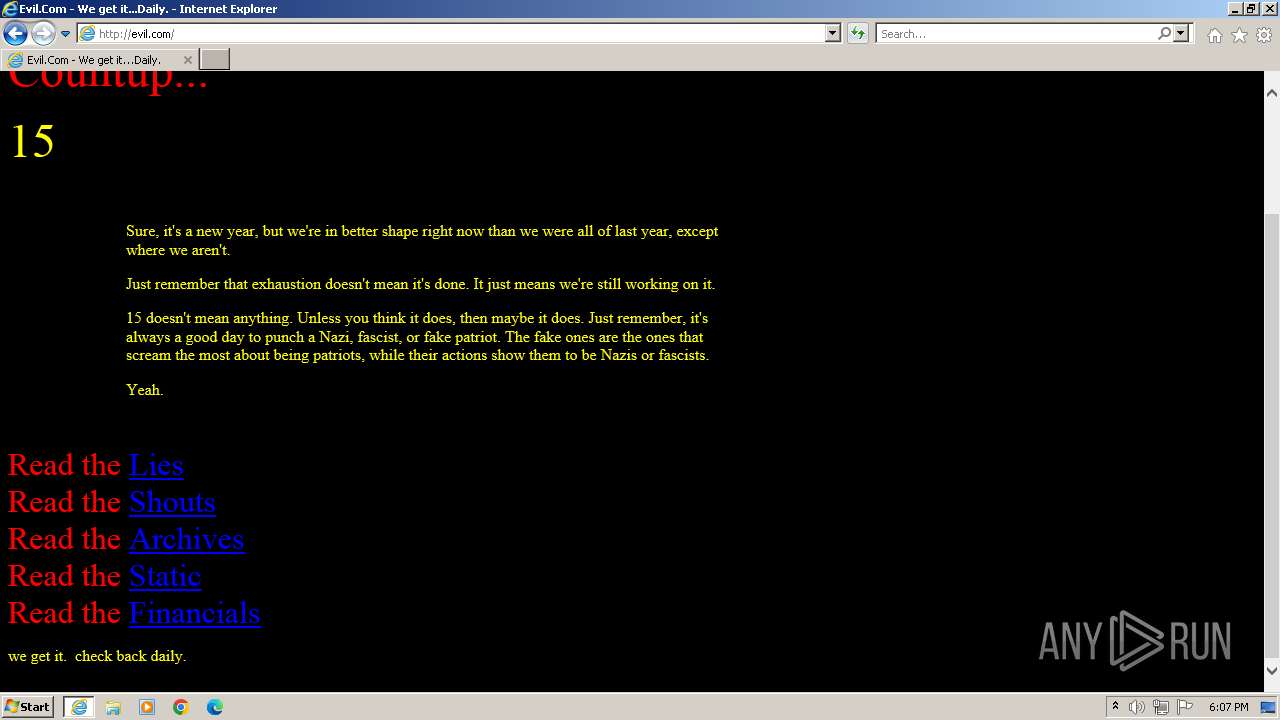
| URL: | evil.com |
| Full analysis: | https://app.any.run/tasks/1e0f1bcd-ea58-4f03-a7b7-eb18569af85e |
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2024, 17:07:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 6D3AF727A4E7B025FD59A5469B3A9C57 |
| SHA1: | E3DAA298655CA5BAD428A0B49CC7FAB19D3C3300 |
| SHA256: | 1867B49ABE26B512D11CB45294E41AFA6F728697705714911C5C001179F7F2BB |
| SSDEEP: | 3:22K:25 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads the computer name
- wmpnscfg.exe (PID: 1756)
Application launched itself
- iexplore.exe (PID: 3988)
Checks supported languages
- wmpnscfg.exe (PID: 1756)
Manual execution by a user
- wmpnscfg.exe (PID: 1756)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1756 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3988 | "C:\Program Files\Internet Explorer\iexplore.exe" "evil.com" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 4048 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3988 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
22 977
Read events
22 535
Write events
181
Delete events
261
Modification events
| (PID) Process: | (3988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 31109208 | |||
| (PID) Process: | (3988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31109208 | |||
| (PID) Process: | (3988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3988) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
17
Text files
64
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4048 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\WKCMR3AR.htm | html | |
MD5:F2C026AB002A6D7114C3920D15EC0826 | SHA256:7D1C49EFE9428C82172D6907CF48090F1AF2F201A04077AF83065731F28A1D01 | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EAF8AA29A62AB29E614331747385D816_F9E4DC0B9D5C777357D7DB8DEF51118A | binary | |
MD5:6362D4C90F352D14226F694C29FF05D6 | SHA256:E387724BF91D8EA2BE7DE787FCDAAB8D986742327EED5C82DE7B4C1BE03D847A | |||
| 3988 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:3FCCA49F4F199080F501B8CA33C9A489 | SHA256:94DFF5FF923A978BBA9A1FE3DD821A7821B763678C5EB971BAF28AD7BBD1D70B | |||
| 4048 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\5KSSKB4D.txt | text | |
MD5:7913940662BC4F8DDCC14A999F2B7982 | SHA256:6C7B44B88D3A60F82A6B127ECAA5F55DB4CD94D7FEB562BFBED6216707958A76 | |||
| 4048 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_C0427F5F77D9B3A439FC620EDAAB6177 | binary | |
MD5:DA4FD8DCD27EBA6B815DBBD65043A7D2 | SHA256:2CE00FA60CC62578BAA4CF9A9518648F6BE2B4FC7B1676A733360B53B7D2255C | |||
| 4048 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\3QBV9PJK.txt | text | |
MD5:B1293024B0FFB14046B41EDEE8DC78A7 | SHA256:0EA82998D1FCC0B4F2F0DCCE421545CF7DBD351337D773F5A39854063ECA2A5E | |||
| 4048 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\HWF3RPI7.txt | text | |
MD5:DF90A61D7CC6E6F129009E90809CC2BA | SHA256:34E6614DB3119F3584F03E053C67C9DEFC2A4C5BEF5C9F2C203F95CFE2A5EEE5 | |||
| 4048 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\ZYMCQC56.txt | text | |
MD5:63812F3AEB2269262CBD0157718EC617 | SHA256:0903DBF7B292820C15B3CD4B5E083C0759C6E7D4D17739A3AA68FB650FD40527 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
39
DNS requests
23
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4048 | iexplore.exe | GET | 404 | 66.96.146.129:80 | http://evil.com/archives/2013/201312/20131225_copy(1 | unknown | — | — | unknown |
4048 | iexplore.exe | GET | 200 | 66.96.146.129:80 | http://evil.com/ | unknown | — | — | unknown |
3988 | iexplore.exe | GET | 200 | 66.96.146.129:80 | http://evil.com/favicon.ico | unknown | — | — | unknown |
3988 | iexplore.exe | GET | 200 | 66.96.146.129:80 | http://evil.com/favicon.ico | unknown | — | — | unknown |
4048 | iexplore.exe | GET | 404 | 66.96.146.129:80 | http://evil.com/archives/2013/201312/20131225_copy(1 | unknown | — | — | unknown |
3988 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
1088 | svchost.exe | GET | 304 | 2.21.75.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a09afb62c623df15 | unknown | — | — | unknown |
4048 | iexplore.exe | GET | 200 | 66.96.146.129:80 | http://www.evil.com/projectX.htm | unknown | — | — | unknown |
3988 | iexplore.exe | GET | 200 | 66.96.146.129:80 | http://www.evil.com/favicon.ico | unknown | — | — | unknown |
4048 | iexplore.exe | GET | 200 | 66.96.146.129:80 | http://www.evil.com/history.htm | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1088 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4048 | iexplore.exe | 66.96.146.129:80 | evil.com | BIZLAND-SD | US | unknown |
3988 | iexplore.exe | 66.96.146.129:80 | evil.com | BIZLAND-SD | US | unknown |
3988 | iexplore.exe | 92.122.157.44:443 | www.bing.com | Akamai International B.V. | NL | unknown |
3988 | iexplore.exe | 2.21.75.240:80 | ctldl.windowsupdate.com | Akamai International B.V. | GB | unknown |
3988 | iexplore.exe | 2.21.75.229:80 | ctldl.windowsupdate.com | Akamai International B.V. | GB | unknown |
3988 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4048 | iexplore.exe | 13.107.5.80:443 | api.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
evil.com |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
www.searchvity.com |
| unknown |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
www.evil.com |
| unknown |