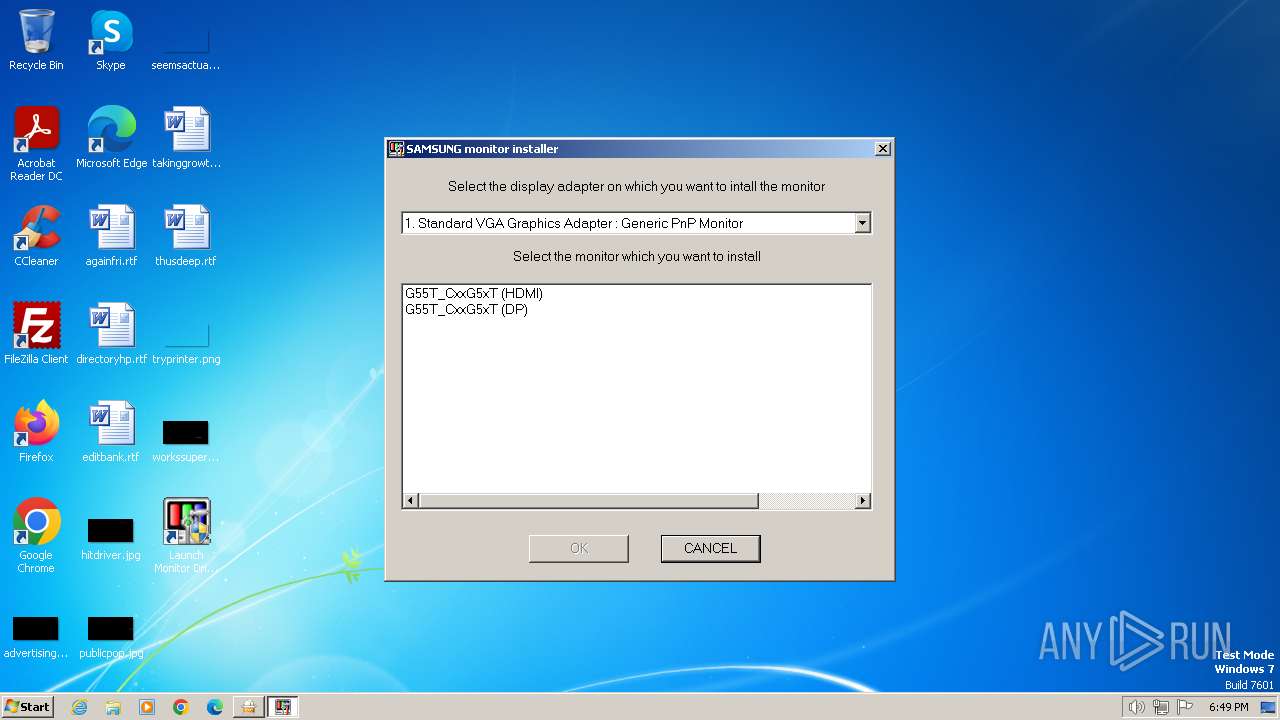
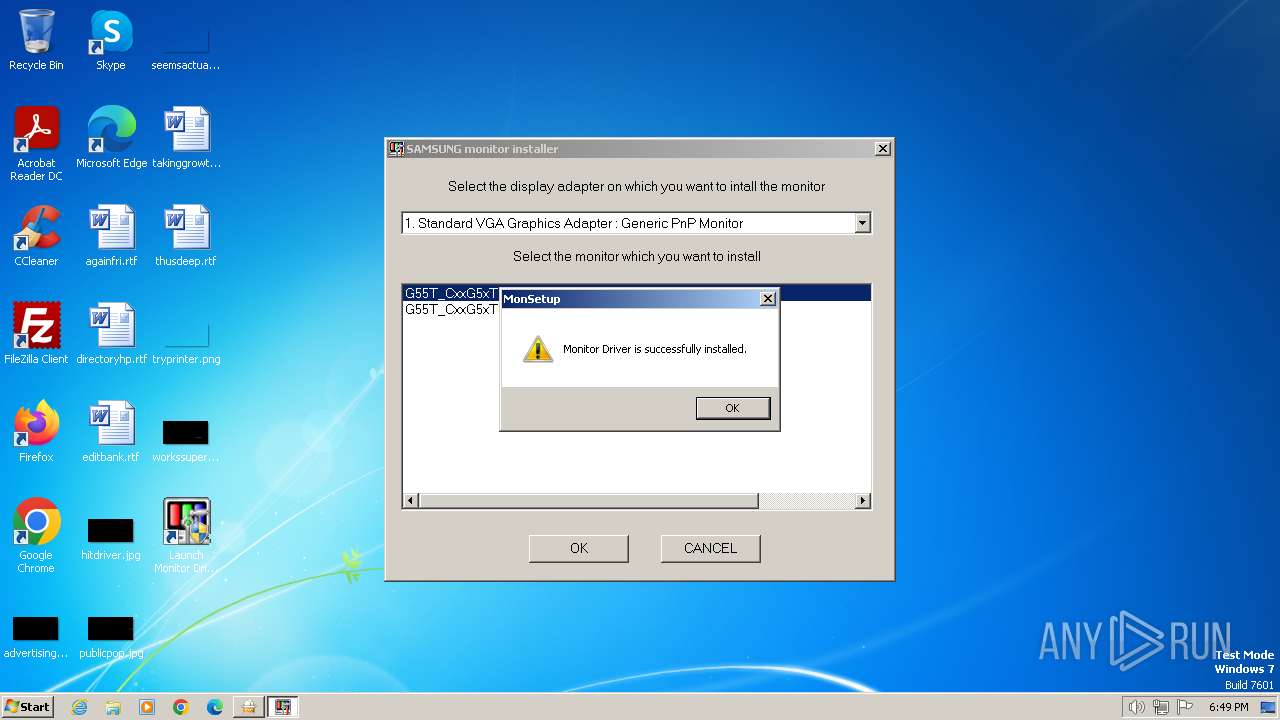
| File name: | CxxG5xT.exe |
| Full analysis: | https://app.any.run/tasks/ca67d259-8be0-48e0-b1cd-307dc9ff9eb0 |
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2024, 18:48:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | 3E4780B2020437038D5A2B1D1908F374 |
| SHA1: | 50B145B70FB04530132DEE8B0DC0EEC980744001 |
| SHA256: | 1864101F2FEB1F1B2F307EF13F0259290DCA56BBE6CDB272E4FC4C1458DFA256 |
| SSDEEP: | 98304:ihZKr6qX6kufZV5yFFRPdFyEiKT5dJAEZ0KKDNCqG9G6reVTyTIjFPiU9k1i23Yf:ajmaNv+WwurNlxi7PtToey |
MALICIOUS
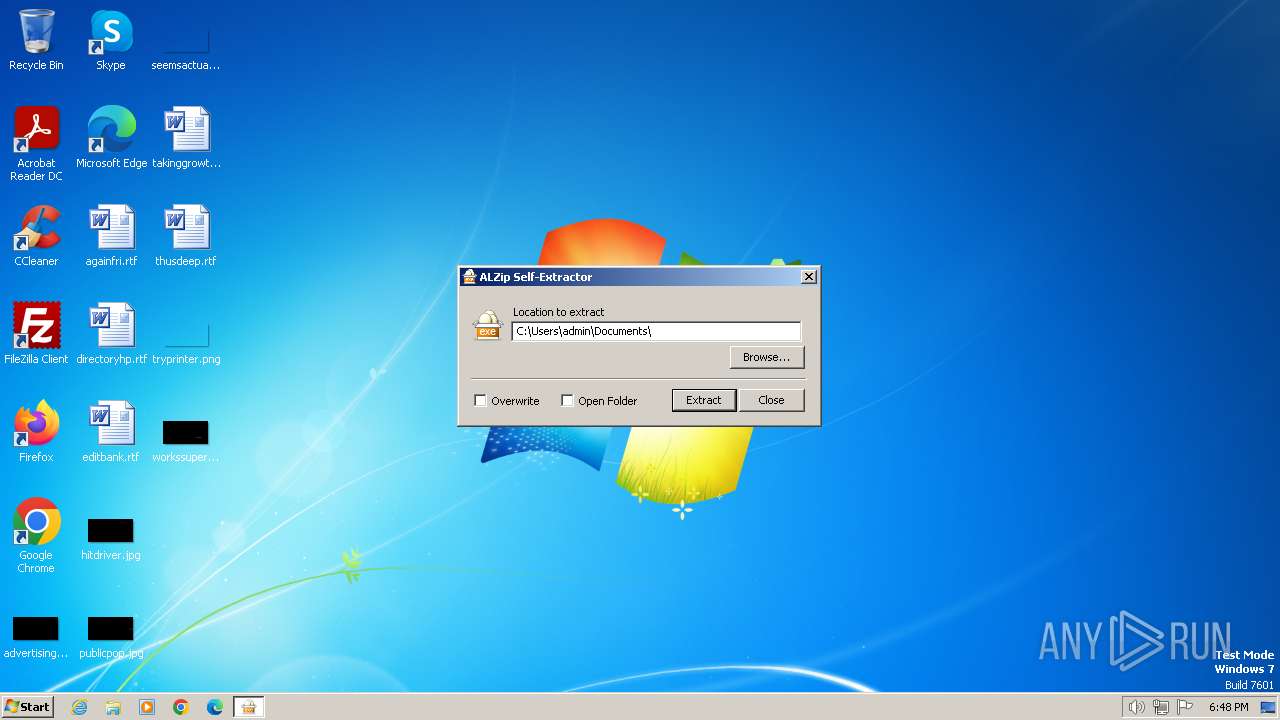
Drops the executable file immediately after the start
- CxxG5xT.exe (PID: 3652)
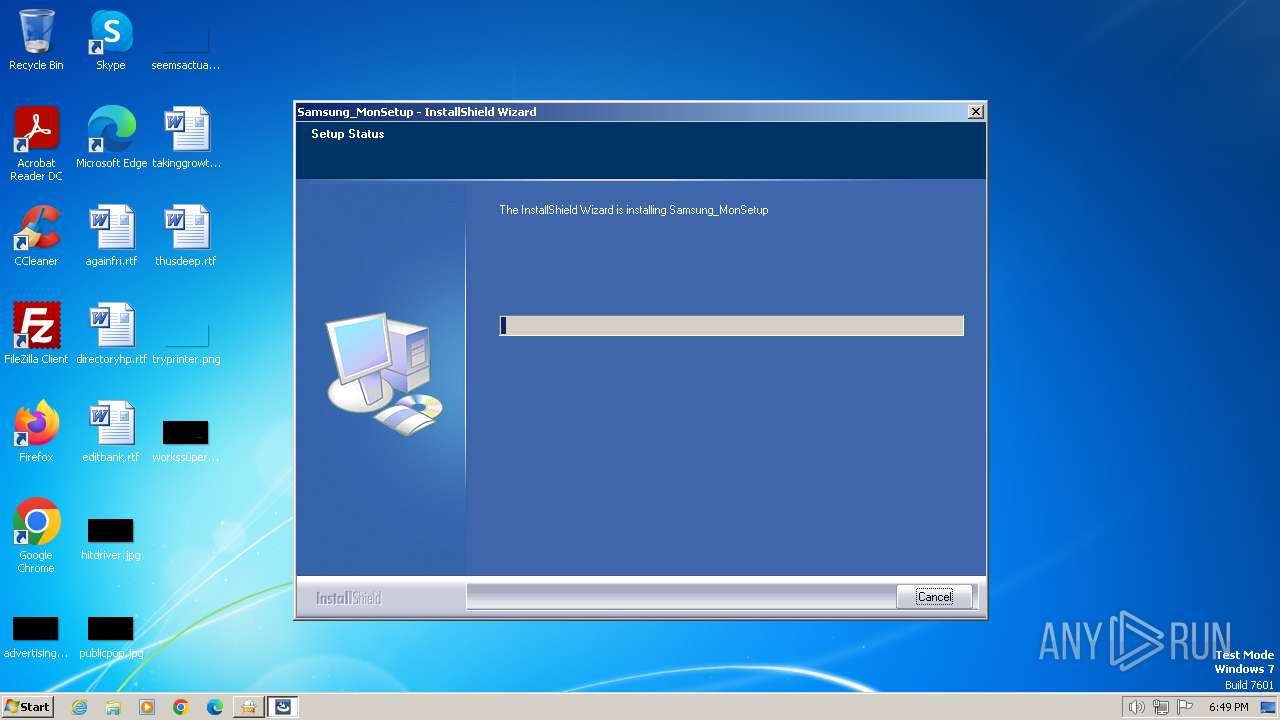
- Samsung_MonSetup_091006.exe (PID: 3460)
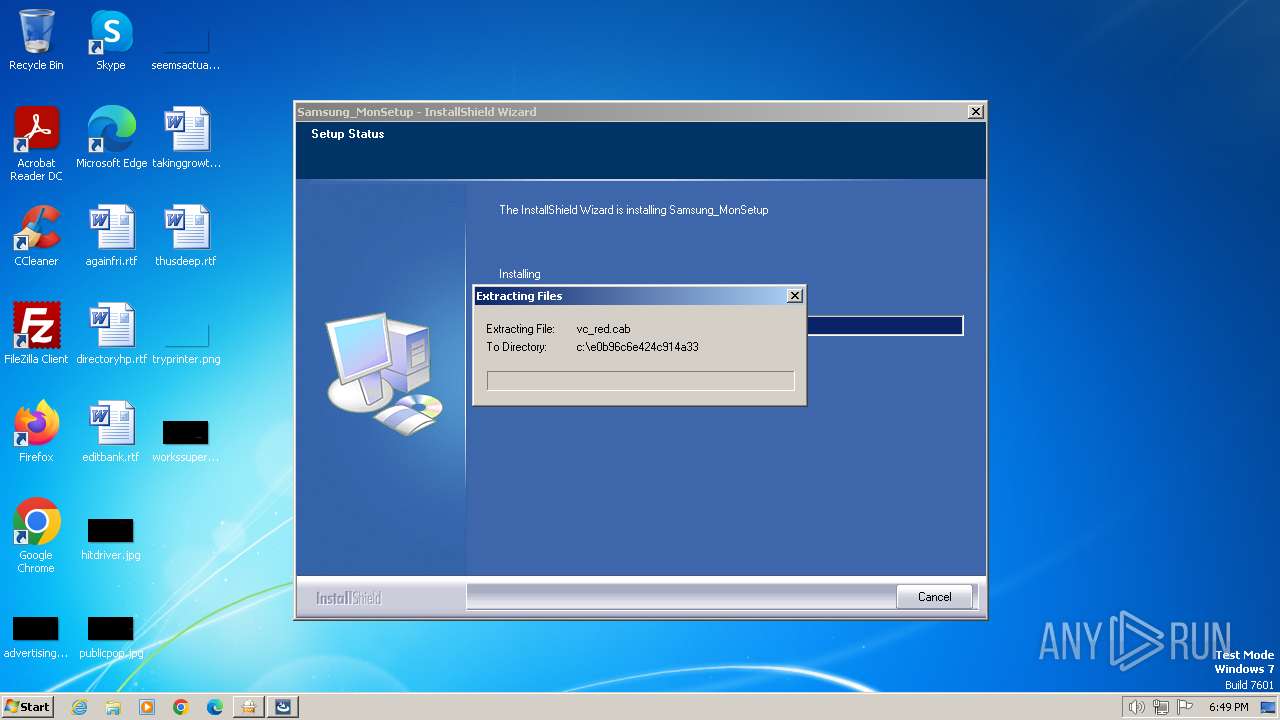
- vcredist_x86.exe (PID: 1860)
Creates a writable file in the system directory
- MonSetup.exe (PID: 1848)
SUSPICIOUS
Reads the Internet Settings
- CxxG5xT.exe (PID: 3652)
Reads security settings of Internet Explorer
- CxxG5xT.exe (PID: 3652)
- MonSetup.exe (PID: 1848)
Executable content was dropped or overwritten
- CxxG5xT.exe (PID: 3652)
- Samsung_MonSetup_091006.exe (PID: 3460)
- vcredist_x86.exe (PID: 1860)
Searches for installed software
- Samsung_MonSetup_091006.exe (PID: 3460)
- dllhost.exe (PID: 4044)
Process drops legitimate windows executable
- Samsung_MonSetup_091006.exe (PID: 3460)
- vcredist_x86.exe (PID: 1860)
Reads the Windows owner or organization settings
- Samsung_MonSetup_091006.exe (PID: 3460)
Creates a software uninstall entry
- Samsung_MonSetup_091006.exe (PID: 3460)
Checks Windows Trust Settings
- MonSetup.exe (PID: 1848)
Reads settings of System Certificates
- MonSetup.exe (PID: 1848)
Executes as Windows Service
- VSSVC.exe (PID: 3428)
INFO
Checks supported languages
- CxxG5xT.exe (PID: 3652)
- Samsung_MonSetup_091006.exe (PID: 3460)
- MonSetup.exe (PID: 1848)
- install.exe (PID: 2432)
- vcredist_x86.exe (PID: 1860)
Reads the machine GUID from the registry
- Samsung_MonSetup_091006.exe (PID: 3460)
- install.exe (PID: 2432)
- MonSetup.exe (PID: 1848)
- vcredist_x86.exe (PID: 1860)
Reads the computer name
- Samsung_MonSetup_091006.exe (PID: 3460)
- CxxG5xT.exe (PID: 3652)
- vcredist_x86.exe (PID: 1860)
- MonSetup.exe (PID: 1848)
- install.exe (PID: 2432)
Creates files or folders in the user directory
- Samsung_MonSetup_091006.exe (PID: 3460)
Creates files in the program directory
- Samsung_MonSetup_091006.exe (PID: 3460)
Create files in a temporary directory
- Samsung_MonSetup_091006.exe (PID: 3460)
- install.exe (PID: 2432)
Reads the software policy settings
- MonSetup.exe (PID: 1848)
Reads Environment values
- vcredist_x86.exe (PID: 1860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:10:07 01:04:24+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 192512 |
| InitializedDataSize: | 57344 |
| UninitializedDataSize: | 360448 |
| EntryPoint: | 0x873b0 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.10.1.1 |
| ProductVersionNumber: | 19.10.1.1 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Korean |
| CharacterSet: | Unicode |
| CompanyName: | ESTsoft Corp. |
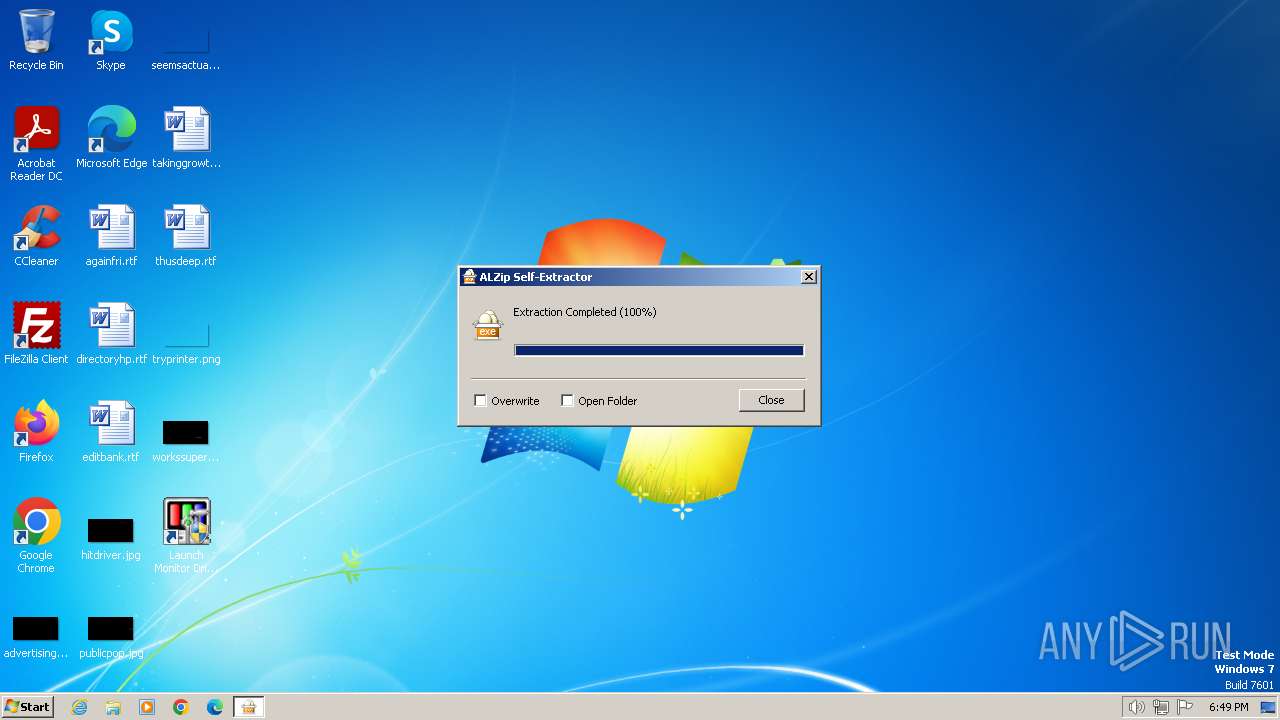
| FileDescription: | ALZip Self Extractor |
| FileVersion: | 19, 10, 1, 1 |
| InternalName: | EGGSFX |
| LegalCopyright: | Copyright (c) 1999 - present ESTsoft Corp. All right reserved. |
| OriginalFileName: | EGGSFX.sfx |
| ProductName: | ALZip |
| ProductVersion: | 19, 10, 1, 1 |
Total processes
50
Monitored processes
9
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 840 | C:\Windows\System32\rundll32.exe shell32.dll,SHCreateLocalServerRunDll {995C996E-D918-4a8c-A302-45719A6F4EA7} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1848 | "C:\Program Files\MonitorDriver\MonSetup.exe" | C:\Program Files\MonitorDriver\MonSetup.exe | — | Samsung_MonSetup_091006.exe | |||||||||||
User: admin Company: Samsung Electronics Integrity Level: HIGH Description: MonSetup32 Exit code: 0 Version: 2, 0, 0, 1 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\MonitorDriver\vcredist_x86.exe" "/q:a" | C:\Program Files\MonitorDriver\vcredist_x86.exe | Samsung_MonSetup_091006.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2008 Redistributable Setup Exit code: 0 Version: 9.0.21022.08 Modules
| |||||||||||||||
| 2044 | "C:\Users\admin\Documents\Samsung_MonSetup_091006.exe" | C:\Users\admin\Documents\Samsung_MonSetup_091006.exe | — | CxxG5xT.exe | |||||||||||
User: admin Company: Macrovision Corporation Integrity Level: MEDIUM Description: Setup.exe Exit code: 3221226540 Version: 12.0.49974 Modules
| |||||||||||||||
| 2432 | c:\e0b96c6e424c914a33\.\install.exe "/q:a" | C:\e0b96c6e424c914a33\install.exe | — | vcredist_x86.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: External Installer Exit code: 0 Version: 9.0.21022.8 built by: RTM Modules
| |||||||||||||||
| 3428 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3460 | "C:\Users\admin\Documents\Samsung_MonSetup_091006.exe" | C:\Users\admin\Documents\Samsung_MonSetup_091006.exe | CxxG5xT.exe | ||||||||||||
User: admin Company: Macrovision Corporation Integrity Level: HIGH Description: Setup.exe Exit code: 0 Version: 12.0.49974 Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\AppData\Local\Temp\CxxG5xT.exe" | C:\Users\admin\AppData\Local\Temp\CxxG5xT.exe | explorer.exe | ||||||||||||
User: admin Company: ESTsoft Corp. Integrity Level: MEDIUM Description: ALZip Self Extractor Exit code: 0 Version: 19, 10, 1, 1 Modules
| |||||||||||||||
| 4044 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
10 909
Read events
10 691
Write events
213
Delete events
5
Modification events
| (PID) Process: | (3652) CxxG5xT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3652) CxxG5xT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3652) CxxG5xT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3652) CxxG5xT.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3460) Samsung_MonSetup_091006.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000627DC8F9AD74DA01840D0000E80C0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3460) Samsung_MonSetup_091006.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000627DC8F9AD74DA01840D0000E80C0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3460) Samsung_MonSetup_091006.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 75 | |||
| (PID) Process: | (3460) Samsung_MonSetup_091006.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4000000000000000CA06D2F9AD74DA01840D0000E80C0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3460) Samsung_MonSetup_091006.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000D82DD9F9AD74DA01840D0000740F0000E80300000100000000000000000000001798488ECC204A41BEF5BAA03C4497A80000000000000000 | |||
| (PID) Process: | (3428) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000009A19E5F9AD74DA01640D000024090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
35
Suspicious files
28
Text files
33
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3652 | CxxG5xT.exe | C:\Users\admin\Documents\Samsung_MonSetup_091006.exe | executable | |
MD5:0924C3DFC4368C3DF1B8B42598D8D7AF | SHA256:0580B3FC29D2C76D2B758081CB288E28185D4CF95A7F7E49A6E75B175ABB5274 | |||
| 3652 | CxxG5xT.exe | C:\Users\admin\Documents\CxxG5xT.cat | cat | |
MD5:6A50EA66CDFC51BD7625107C702D56B1 | SHA256:FBF840EF74DAA55115FE84A9E787BC202254D697F296B334BFB10974D5C7AABF | |||
| 3460 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{91F5184C-B9DE-43B4-BA1A-D5DF089D6576}\Disk1\setup.isn | binary | |
MD5:5861DDBAD48F01E82AFB79D0A885FBDE | SHA256:D6C08E2C734AA99C6719B9BD59250F525C63F98737EB26FF03F38BF3CCFBD0C9 | |||
| 3460 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{91F5184C-B9DE-43B4-BA1A-D5DF089D6576}\Disk1\ISSetup.dll | executable | |
MD5:A06ED9FCD8F114E270AA64C46063D8C3 | SHA256:4663E033C1F188ED66D3C413064BFA104F6C307ED10A918AFD2B8373130A779A | |||
| 3652 | CxxG5xT.exe | C:\Users\admin\Documents\CxxG5xT.icm | icc | |
MD5:7ADC33726A2D3380FEF113C7DF5BA749 | SHA256:DCEF0E9E0B3F7B6414393DFB832E8ED3F2E400CEA4A28B448725ED8A169CA4DA | |||
| 3460 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{91F5184C-B9DE-43B4-BA1A-D5DF089D6576}\Disk1\setup.ini | ini | |
MD5:CB4A88BB62F87DD6EEB9A9D498D82CFE | SHA256:44F4779437FD14C3DA31E323636135553E21A68D40B2EC560991EA5C660DCF59 | |||
| 3652 | CxxG5xT.exe | C:\Users\admin\Documents\CxxG5xT.inf | binary | |
MD5:A953B9D7DFC4D5BD220509F5D2ED7C96 | SHA256:3F4286CB89CEA195AB485B3E796A8EA61EC018E539791652FECCA36150C0B71E | |||
| 3460 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{91F5184C-B9DE-43B4-BA1A-D5DF089D6576}\Disk1\setup.exe | executable | |
MD5:2D111130C27C36C91EA57D0E88B68BD6 | SHA256:C793C2BBC622872E281C472A1C50CAC2DD567B3A40C13094C44982FB56DF0CD8 | |||
| 3460 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{91F5184C-B9DE-43B4-BA1A-D5DF089D6576}\_Setup.dll | executable | |
MD5:D5222A5A2D95A6478993C7F72F63B621 | SHA256:E8E98441FCF762FF5FEBD4DFAB295E4ECB744467F345073C170B6B795252F3CE | |||
| 3460 | Samsung_MonSetup_091006.exe | C:\Users\admin\AppData\Local\Temp\{91F5184C-B9DE-43B4-BA1A-D5DF089D6576}\setup.ini | ini | |
MD5:CB4A88BB62F87DD6EEB9A9D498D82CFE | SHA256:44F4779437FD14C3DA31E323636135553E21A68D40B2EC560991EA5C660DCF59 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |