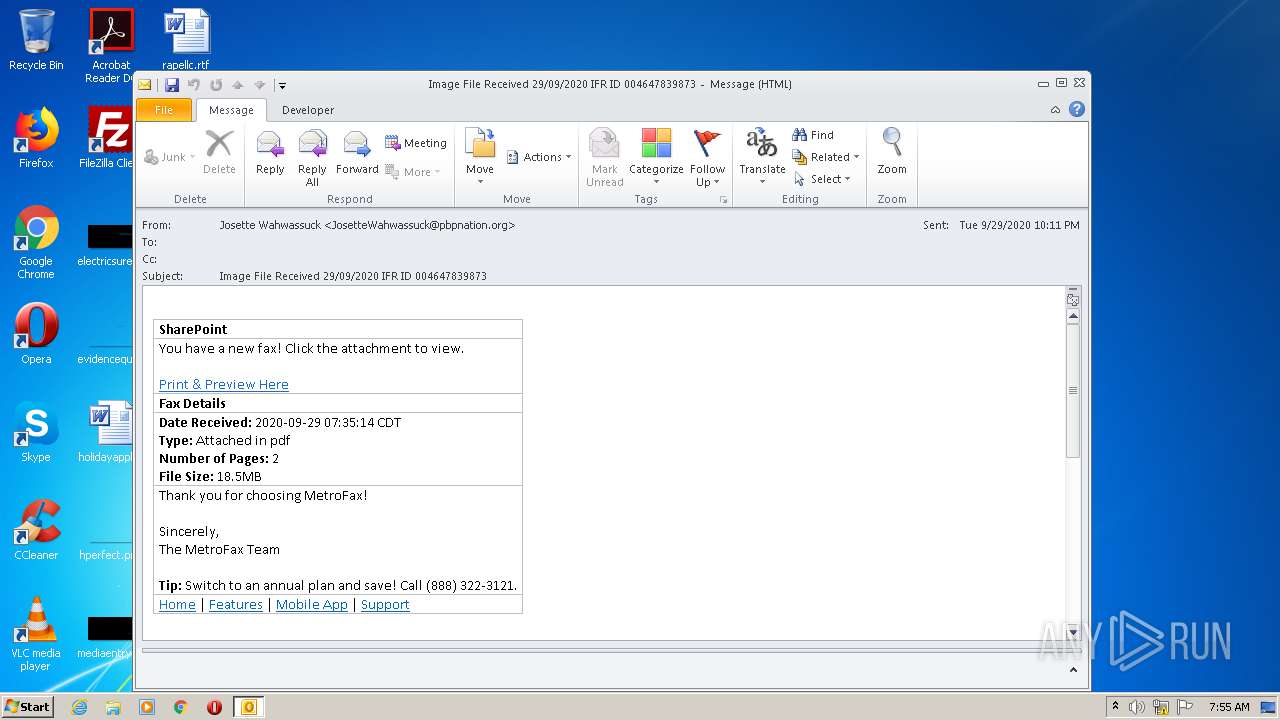
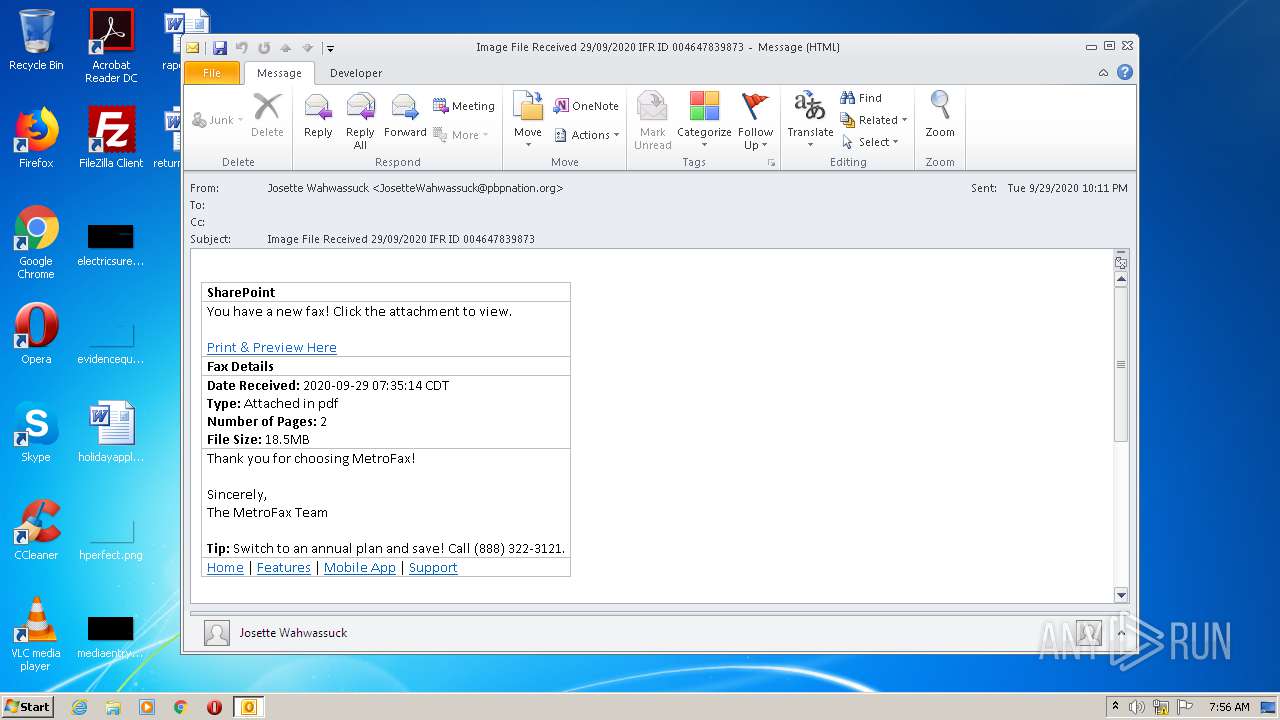
| File name: | Image File Received 29092020 IFR ID 004647839873.msg |
| Full analysis: | https://app.any.run/tasks/004464e3-5c7d-449a-97bc-ce8ee334efb4 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 06:55:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | D74EE106DCBF5C20B56101BE13544264 |
| SHA1: | ABC8F7F565DB125BF5C2F0D2EB61158527E61E88 |
| SHA256: | 18618EFCD4DC8ED4A414E0D252D65A72C00DB9E39DF549C25C57B2476E07E94A |
| SSDEEP: | 768:5OoOsN6NsKCsK+Y1rycuEAxDDBbd0nPOuz5TZq9J2Fg/LdUoom64wKT8iUZ:pWa2Y1rycujlDOPU2C2oR |
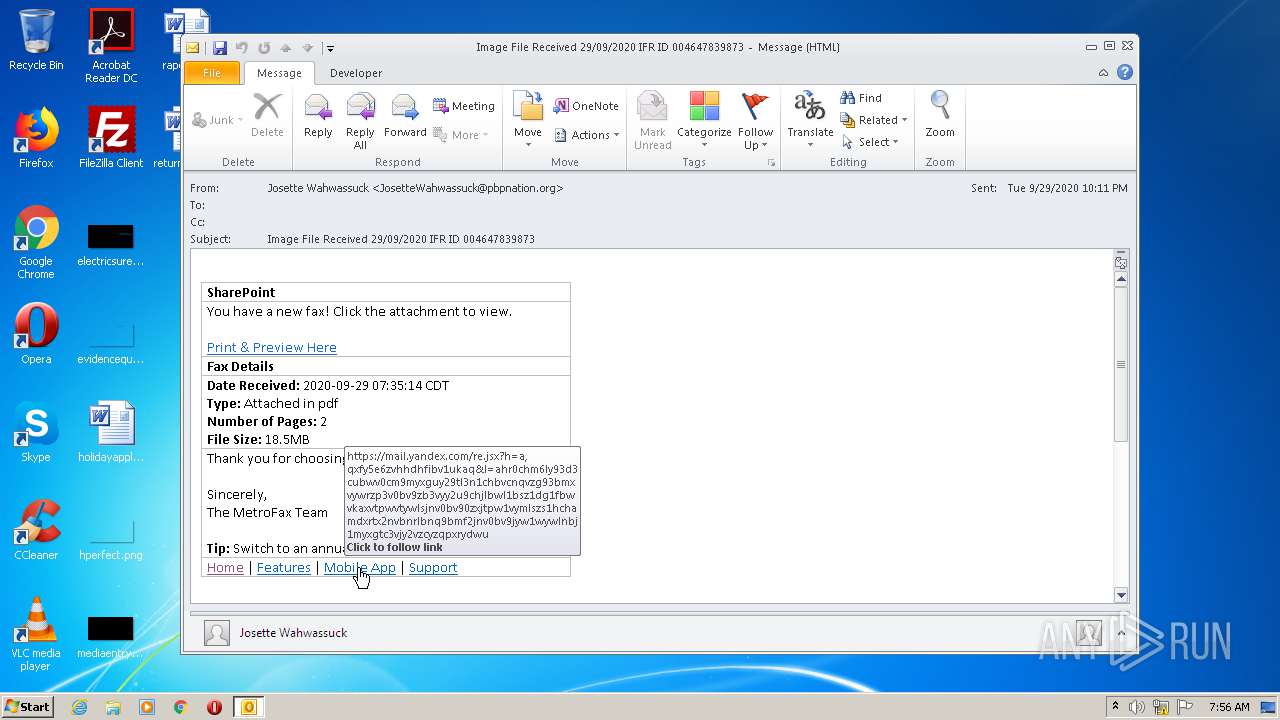
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 1332)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 1332)
Starts Internet Explorer
- OUTLOOK.EXE (PID: 1332)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2248)
- iexplore.exe (PID: 2392)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 1332)
- iexplore.exe (PID: 1492)
- iexplore.exe (PID: 2248)
- iexplore.exe (PID: 2392)
- iexplore.exe (PID: 3744)
Reads settings of System Certificates
- iexplore.exe (PID: 1492)
- iexplore.exe (PID: 2248)
- iexplore.exe (PID: 3744)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 1332)
Creates files in the user directory
- iexplore.exe (PID: 1492)
- iexplore.exe (PID: 3744)
Application launched itself
- iexplore.exe (PID: 2392)
- iexplore.exe (PID: 2248)
Reads internet explorer settings
- iexplore.exe (PID: 1492)
- iexplore.exe (PID: 3744)
Changes settings of System certificates
- iexplore.exe (PID: 2248)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
40
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1332 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Image File Received 29092020 IFR ID 004647839873.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2248 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
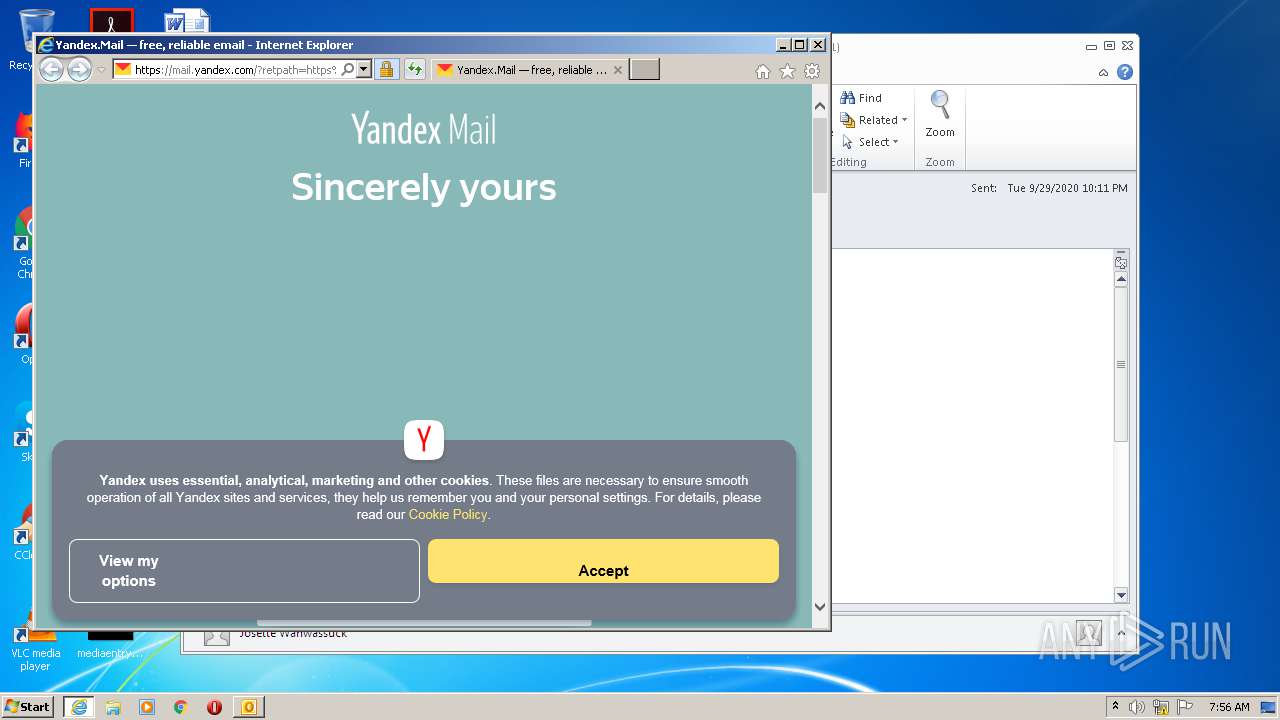
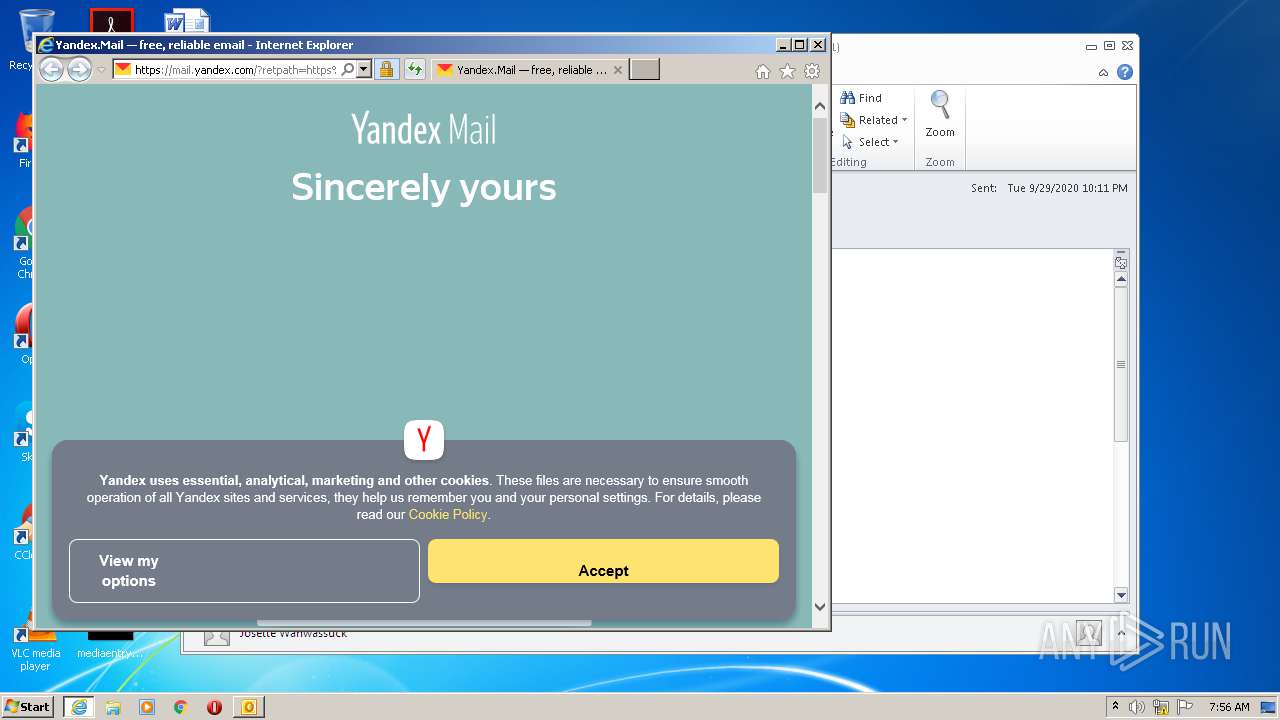
| 2248 | "C:\Program Files\Internet Explorer\iexplore.exe" https://mail.yandex.com/re.jsx?h=a,7DYWRjGPWil5dJIts96GoQ&l=aHR0cHM6Ly93d3cubWV0cm9mYXguY29tLz91dG1fc291cmNlPXByZW1pdW0mdXRtX21lZGl1bT1lbWFpbCZ1dG1fdGVybT1ob21lJnV0bV9jb250ZW50PW5hdiZ1dG1fY2FtcGFpZ249ZmF4LXN1Y2Nlc3Mmaj10cnVl | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2392 | "C:\Program Files\Internet Explorer\iexplore.exe" https://mail.yandex.com/re.jsx?h=a,aI7DMOvhTZ3ynw7s3HoYlg&l=aHR0cHM6Ly9wdWIubHVjaWRwcmVzcy5jb20vZDVjNWE2MDUtYzhlMC00ZWM0LWExNDktNDIzNjQ0YmU0NjEzLw | C:\Program Files\Internet Explorer\iexplore.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3744 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2392 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
2 410
Read events
1 665
Write events
721
Delete events
24
Modification events
| (PID) Process: | (1332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (1332) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
37
Text files
78
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1332 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA450.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabE243.tmp | — | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarE244.tmp | — | |
MD5:— | SHA256:— | |||
| 1332 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E887E036775F4159E2816B7B9E527E5F_CF8153DC44FEDCAC05D3FB121BE5ABB1 | der | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\1B1F4BA66CDBFEC85A20E11BF729AF23_AA85F8F9DAFF33153B5AEC2E983B94B6 | binary | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ZGJJQ1AU.htm | html | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E887E036775F4159E2816B7B9E527E5F_CF8153DC44FEDCAC05D3FB121BE5ABB1 | binary | |
MD5:— | SHA256:— | |||
| 1492 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\MYGQUX31.txt | text | |
MD5:— | SHA256:— | |||
| 1332 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
35
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1332 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
1492 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.58 Kb | whitelisted |
1492 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEQDkBUeDDgxkUpdvejVJwN1I | US | der | 1.63 Kb | whitelisted |
1492 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEGMmPh%2BpF%2FVdy5Q2h0nEnQk%3D | RU | der | 1.48 Kb | whitelisted |
1492 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEGMmPh%2BpF%2FVdy5Q2h0nEnQk%3D | RU | der | 1.48 Kb | whitelisted |
1492 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CECp5lw5VJUdi1sZ3IDVGUzE%3D | RU | der | 1.48 Kb | whitelisted |
1492 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CECp5lw5VJUdi1sZ3IDVGUzE%3D | RU | der | 1.48 Kb | whitelisted |
1492 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CECp5lw5VJUdi1sZ3IDVGUzE%3D | RU | der | 1.48 Kb | whitelisted |
3744 | iexplore.exe | GET | 200 | 5.45.205.244:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEC6Tkdyfl26sf%2Br5Aa05wdc%3D | RU | der | 1.48 Kb | whitelisted |
1492 | iexplore.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.58 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1492 | iexplore.exe | 77.88.21.37:443 | mail.yandex.com | YANDEX LLC | RU | whitelisted |
1332 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1492 | iexplore.exe | 151.139.236.246:80 | subca.ocsp-certum.com | netDNA | US | unknown |
1492 | iexplore.exe | 178.154.131.216:443 | yastatic.net | YANDEX LLC | RU | whitelisted |
1492 | iexplore.exe | 5.45.205.244:80 | yandex.ocsp-responder.com | YANDEX LLC | RU | whitelisted |
1492 | iexplore.exe | 77.88.21.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
2248 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2248 | iexplore.exe | 178.154.131.216:443 | yastatic.net | YANDEX LLC | RU | whitelisted |
2248 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2248 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
mail.yandex.com |
| shared |
subca.ocsp-certum.com |
| whitelisted |
yandex.ocsp-responder.com |
| whitelisted |
yastatic.net |
| whitelisted |
mc.yandex.ru |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |