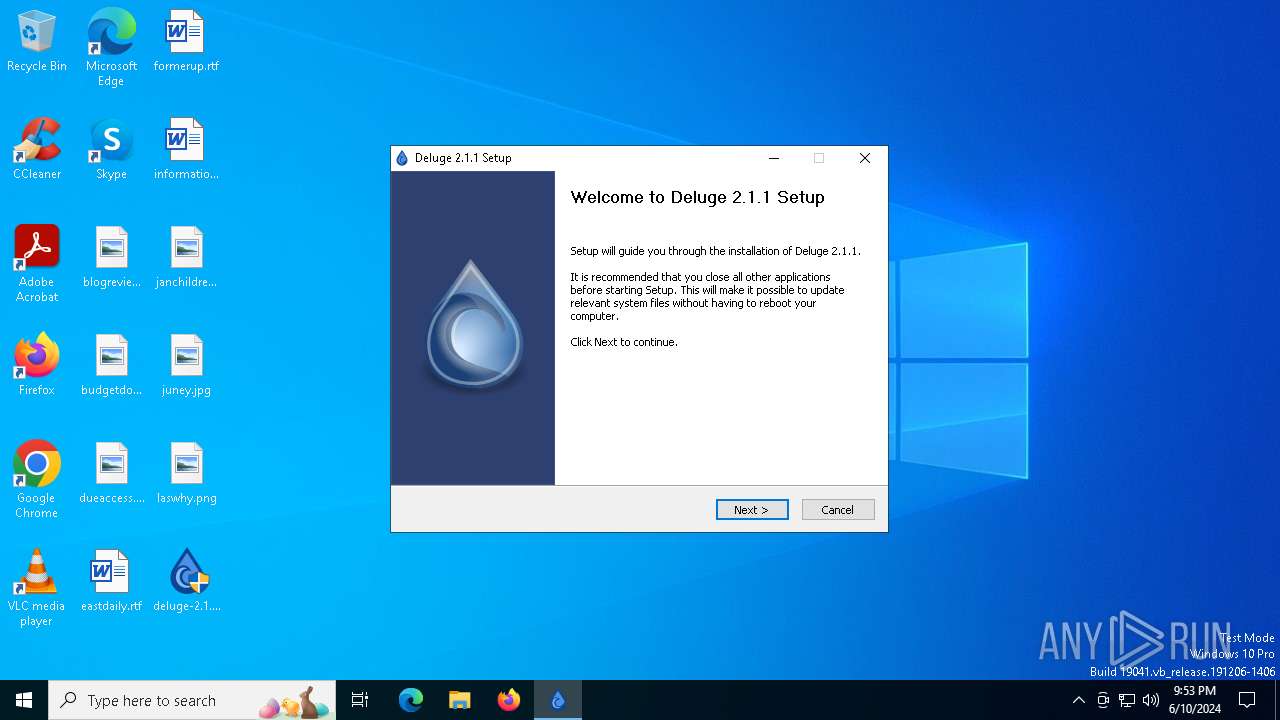
| File name: | deluge-2.1.1-win64-setup.exe |
| Full analysis: | https://app.any.run/tasks/2318070a-9dac-41b1-a6bc-3acca19433d6 |
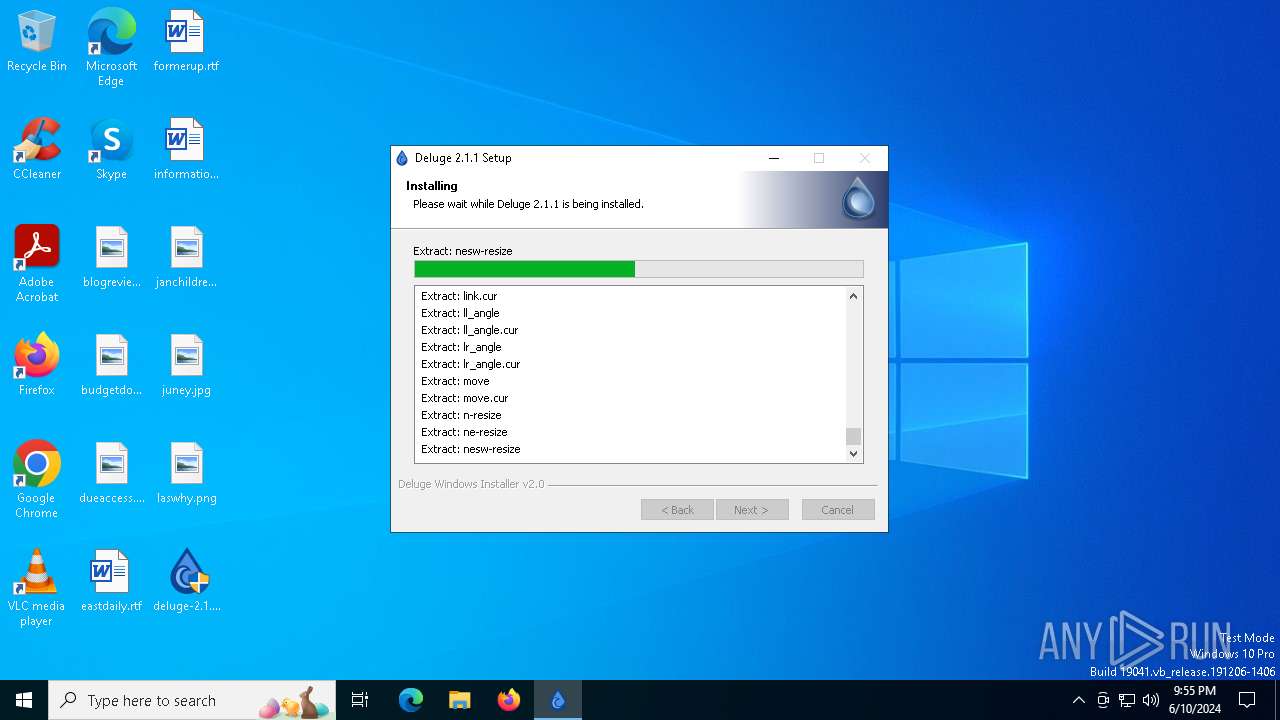
| Verdict: | Malicious activity |
| Analysis date: | June 10, 2024, 21:52:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4B1C4CFEAD927342414FA541FBE35150 |
| SHA1: | CF1B22A1C860139CCD647D186E315E800A893F02 |
| SHA256: | 183F401F088CBB973633DBEEB16DED1326B7AA567ACFC9DE32855D5BE14653AE |
| SSDEEP: | 393216:PibMEMQ6/gqhk5r/GLdm2b3nGYRGI7h0qsgOeUI1DFF00tblU982t1d:aQEMQihk5jp2bXLh/VnUYDz0fF |
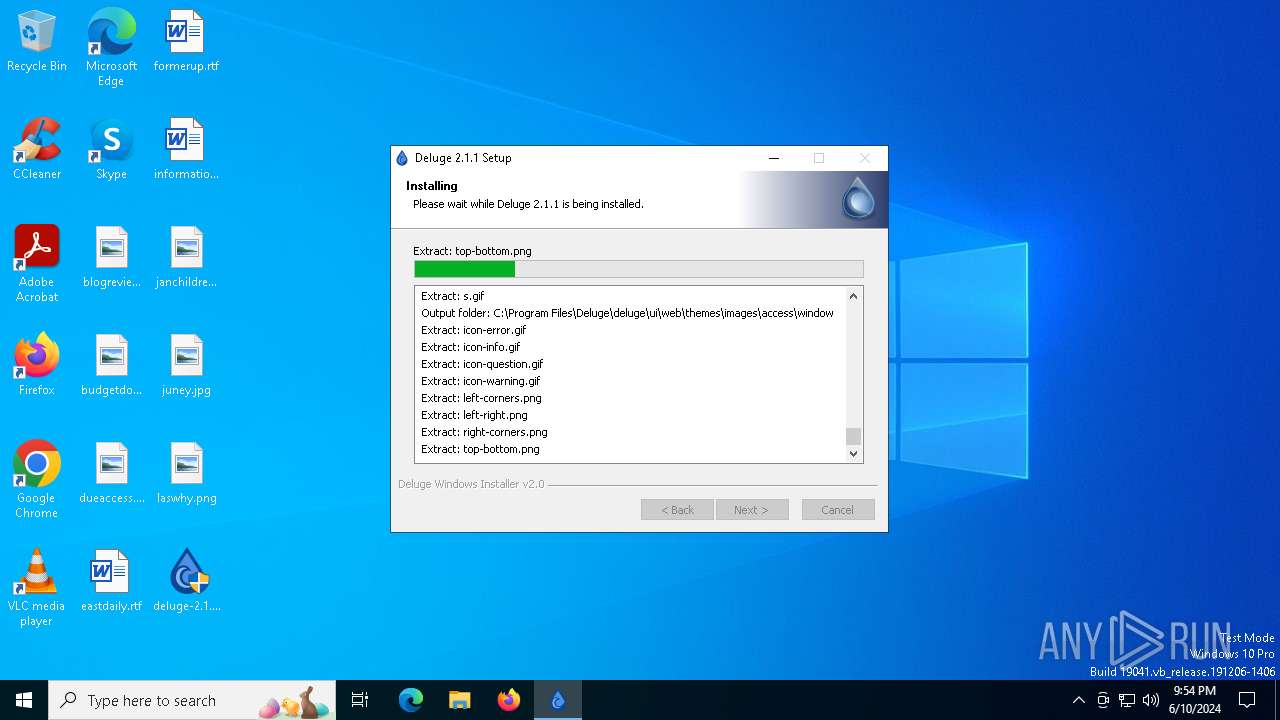
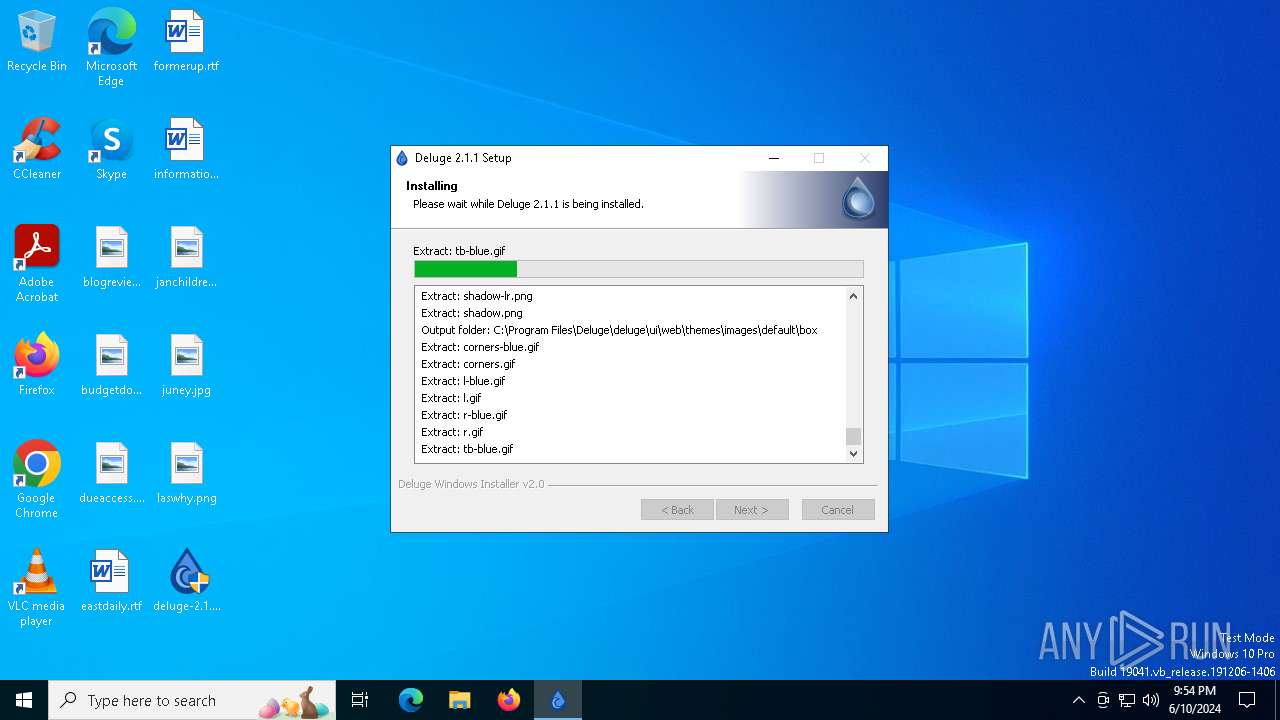
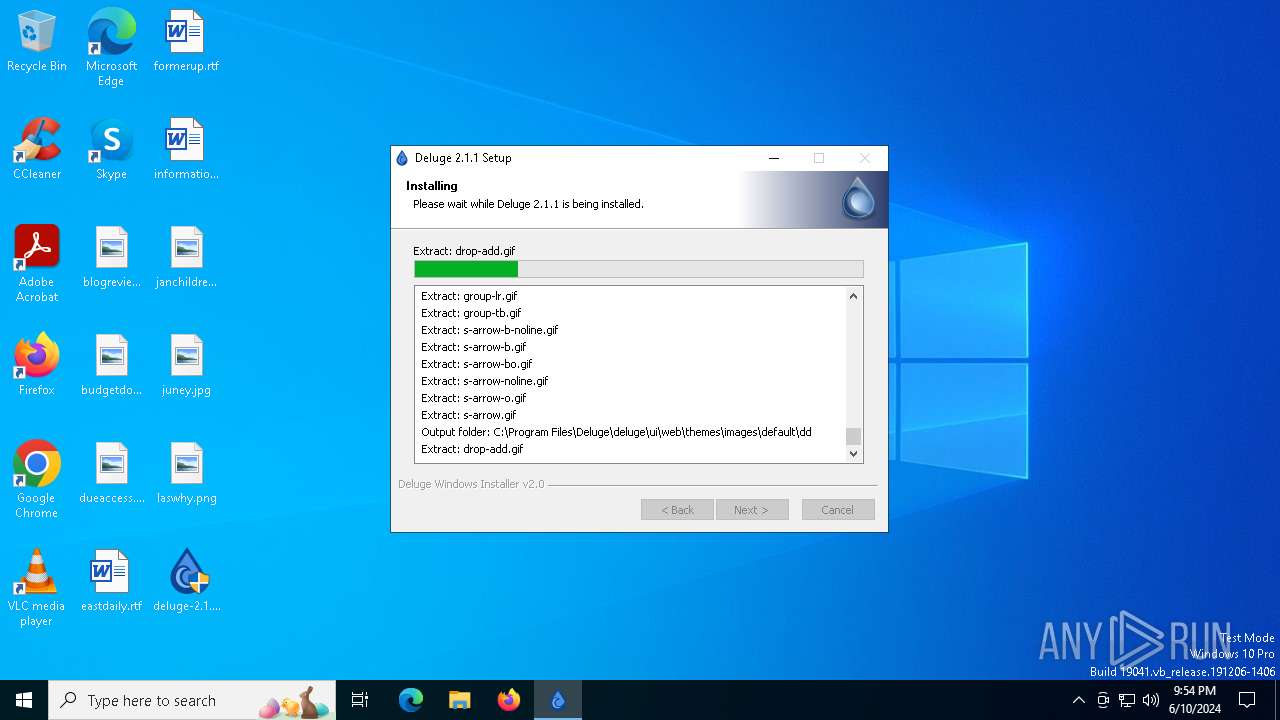
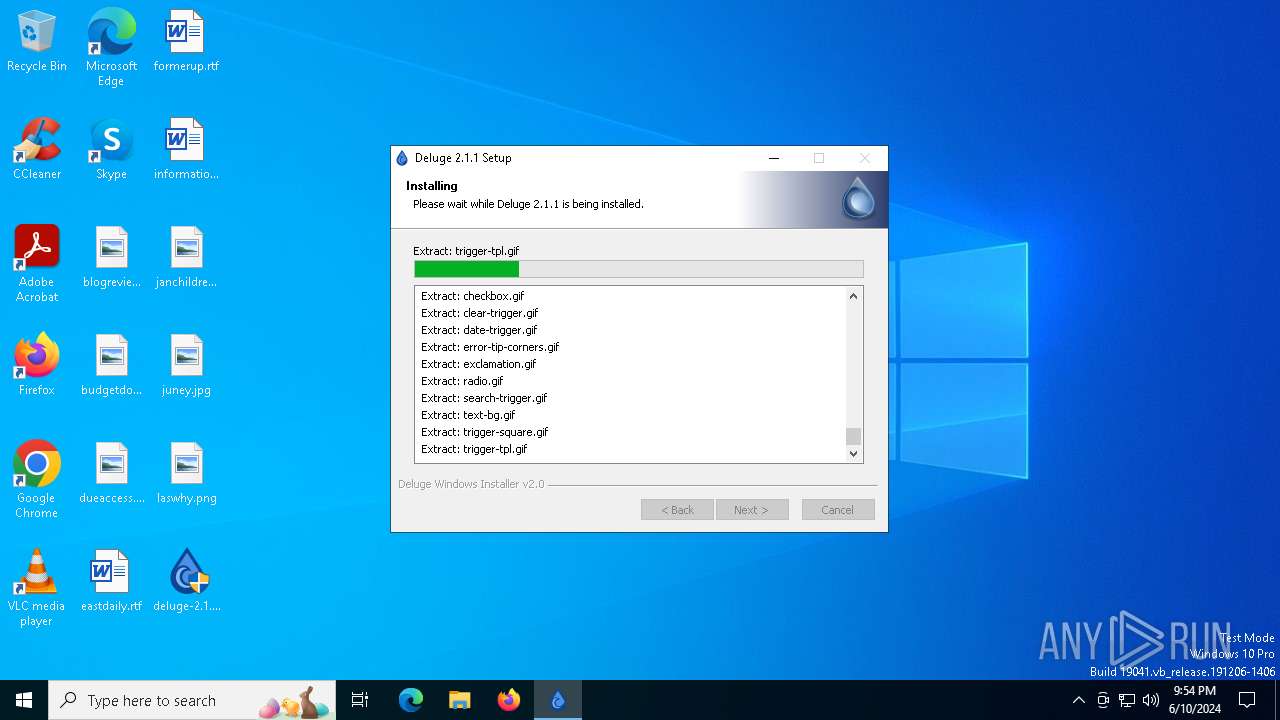
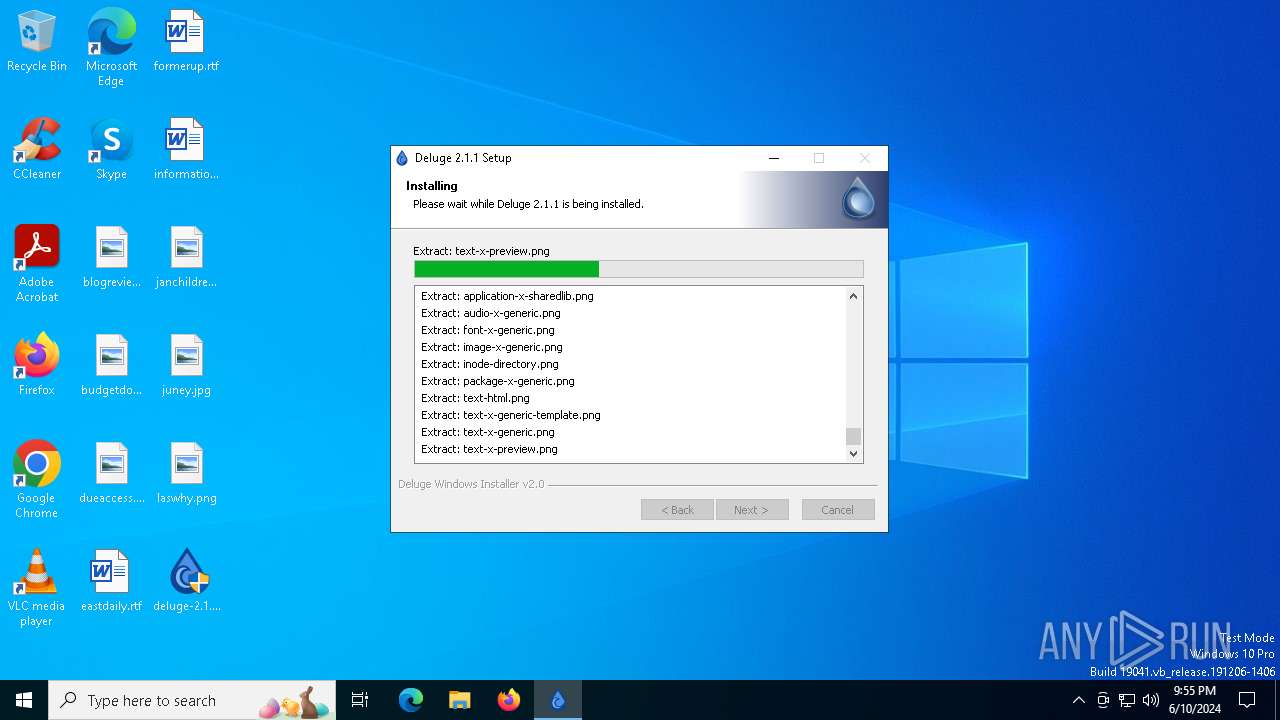
MALICIOUS
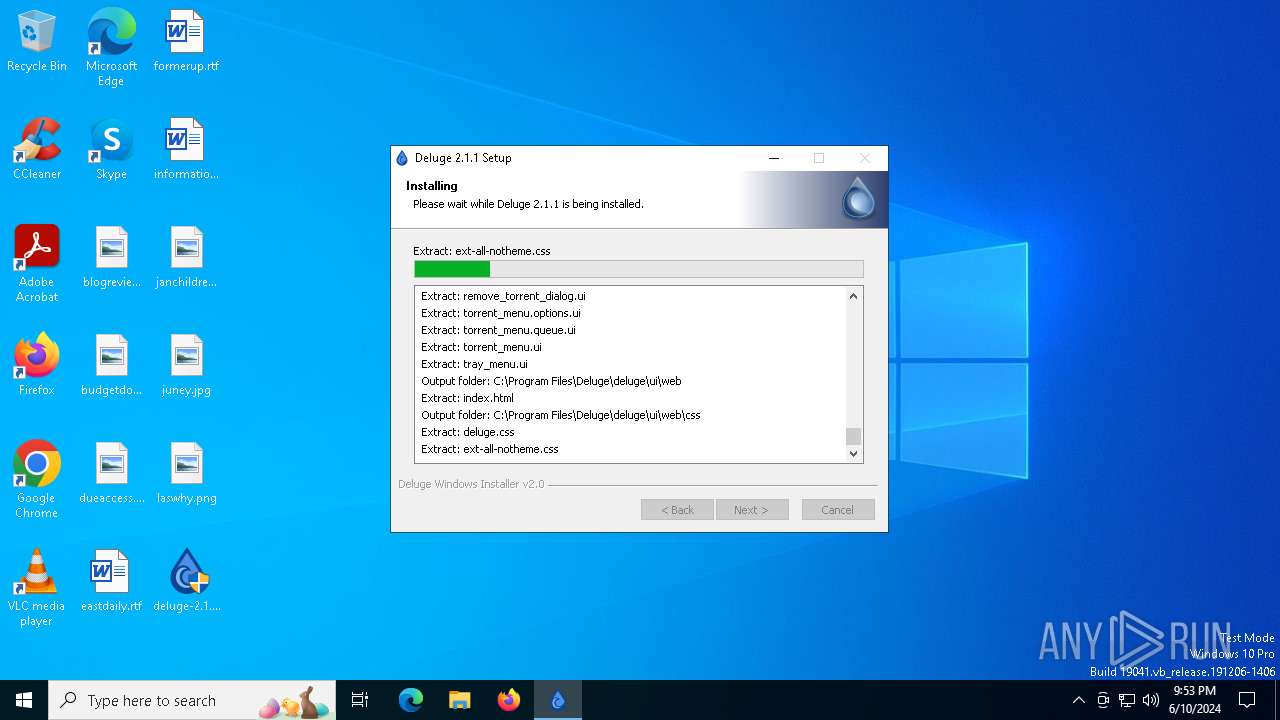
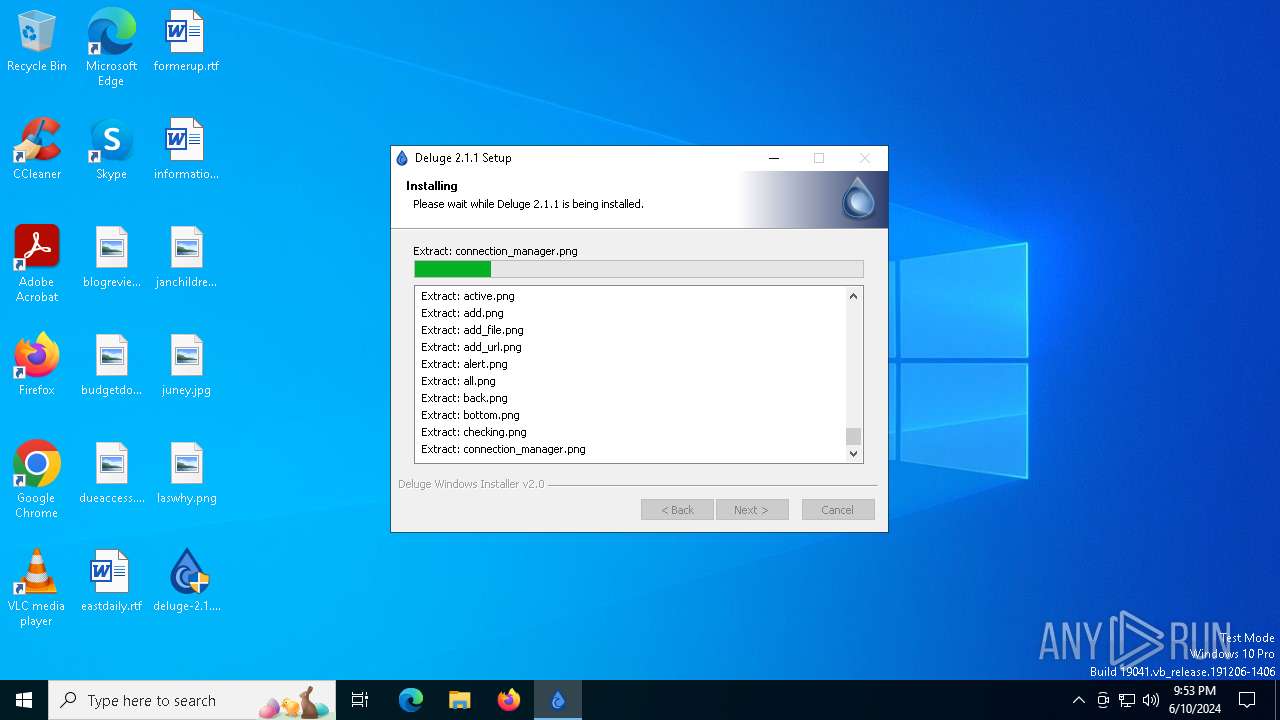
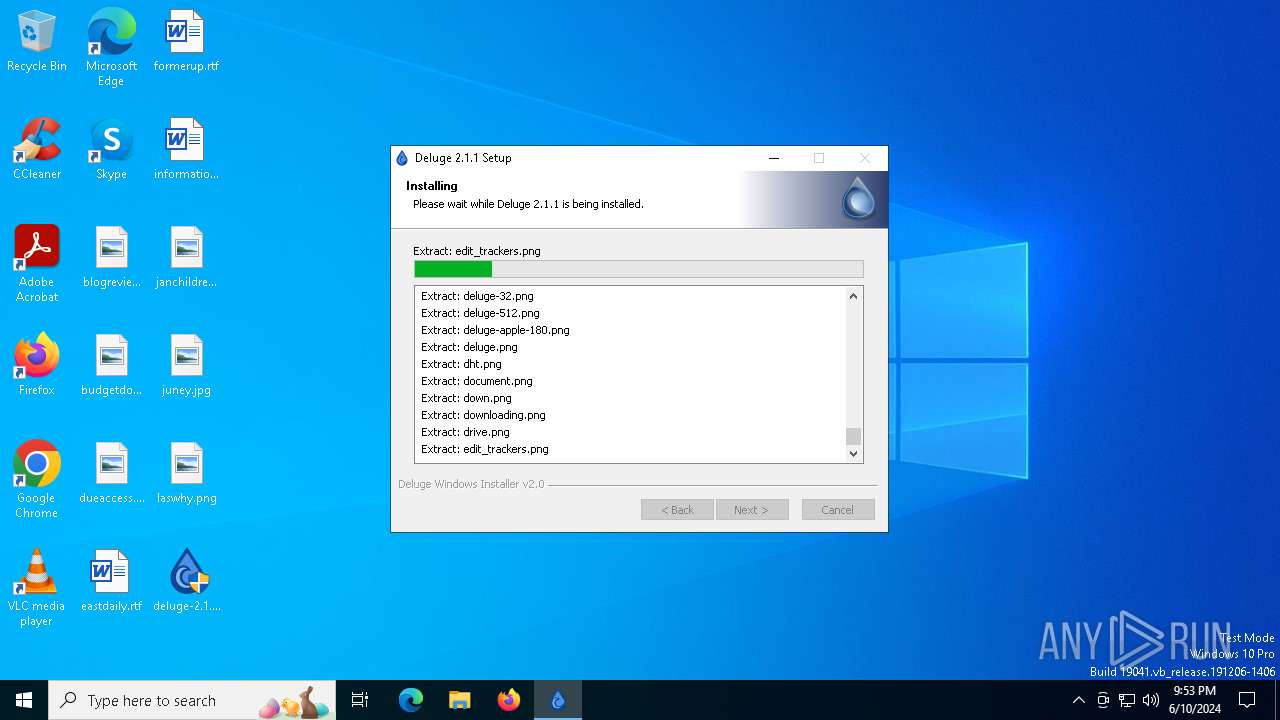
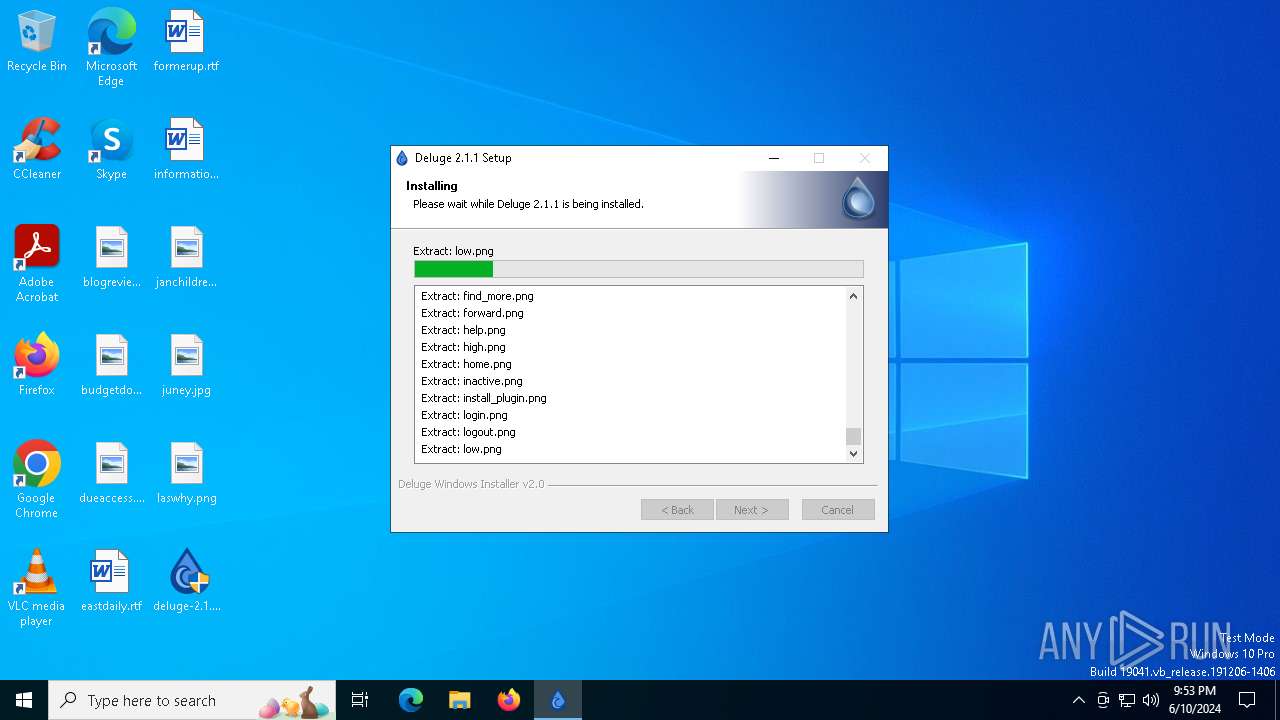
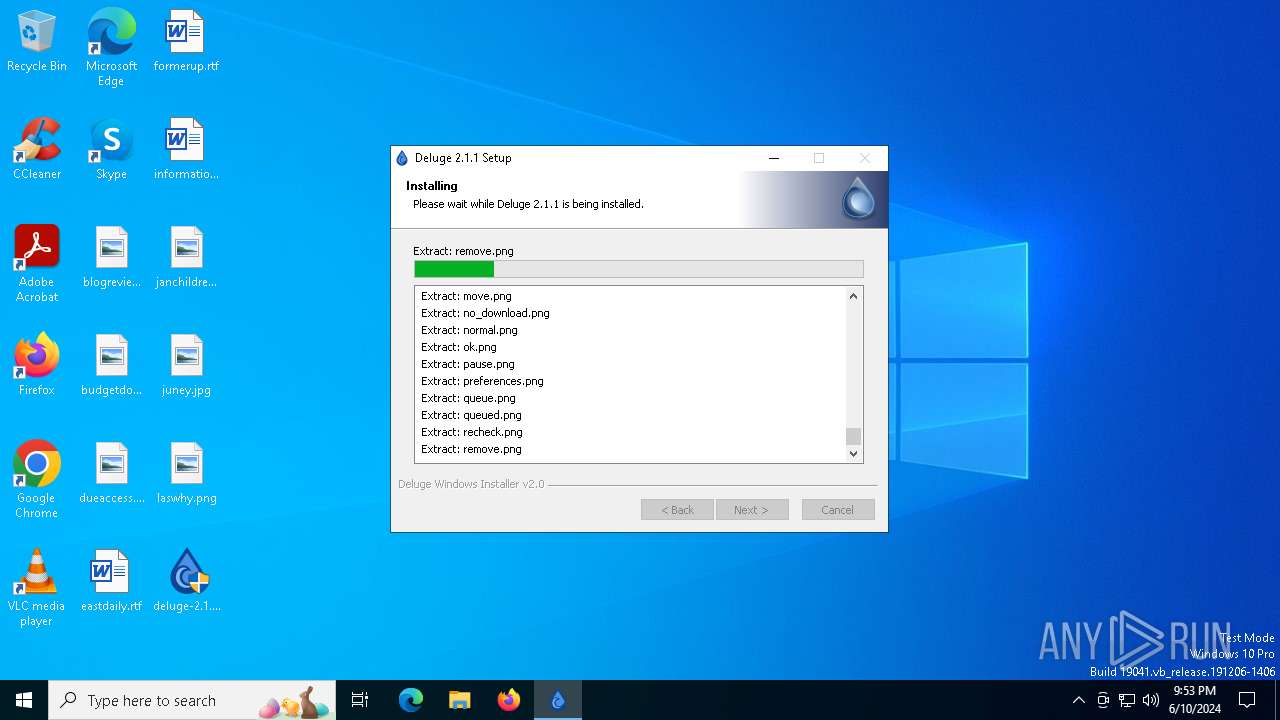
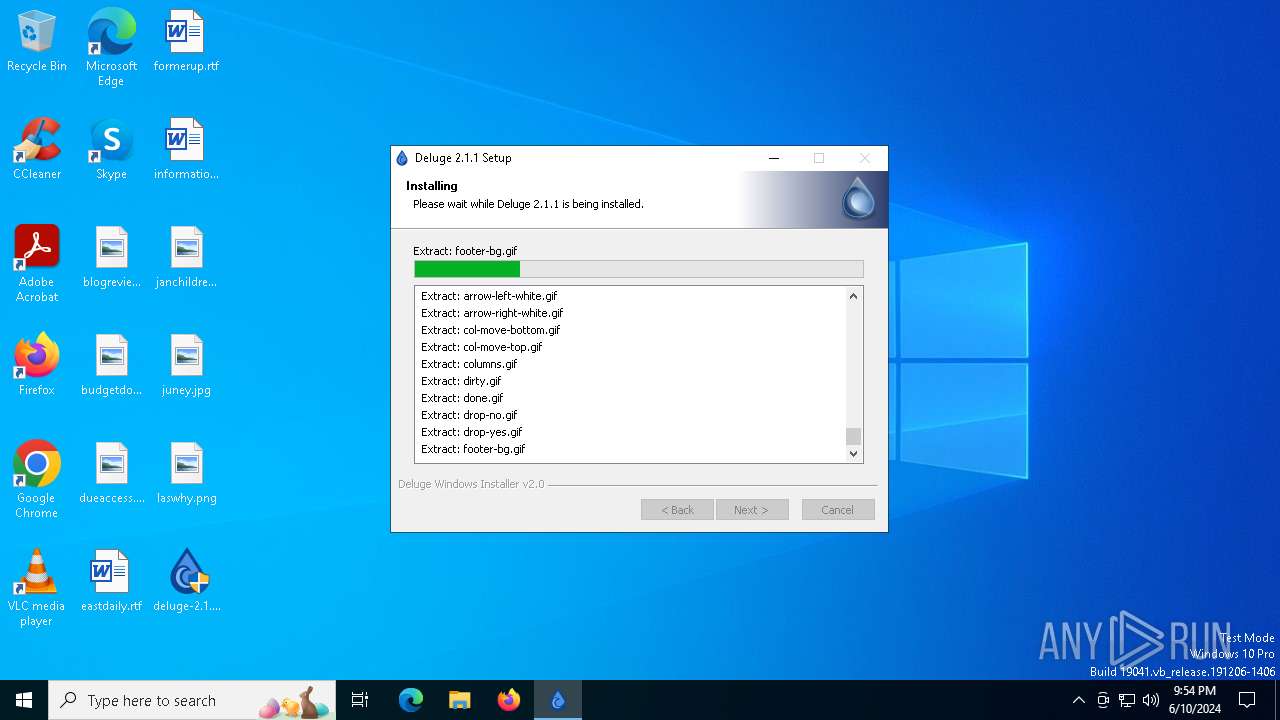
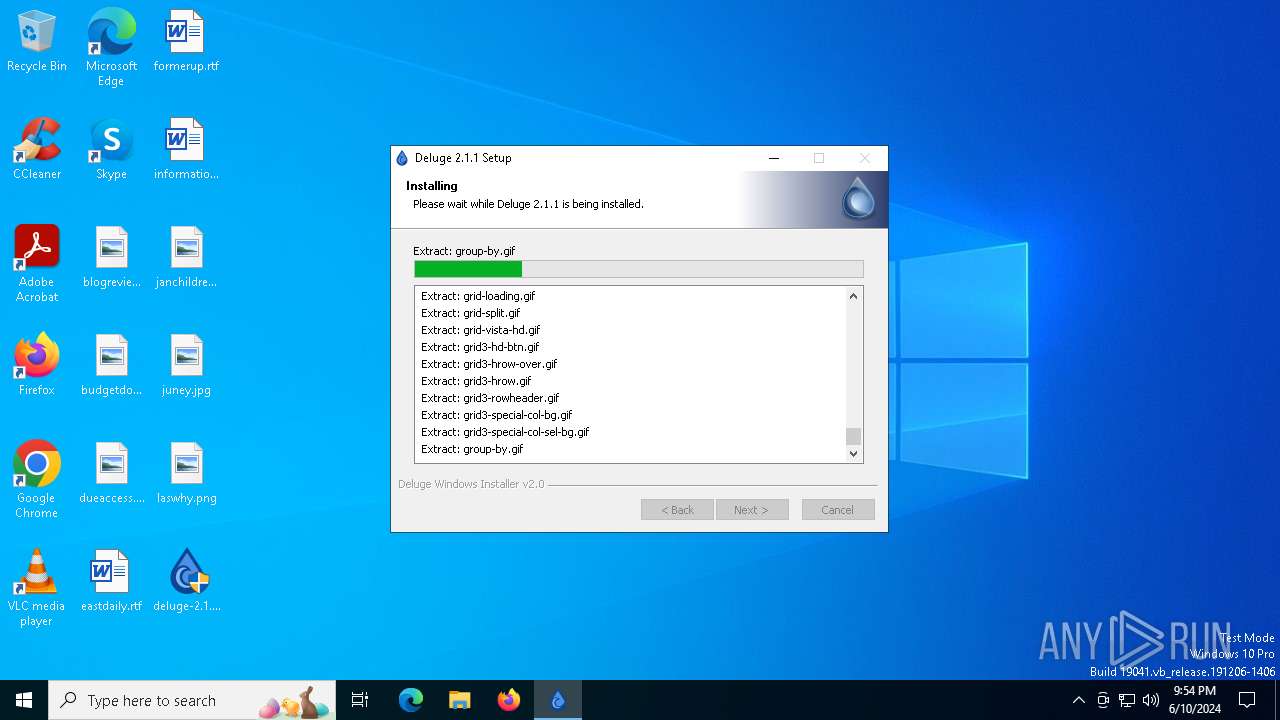
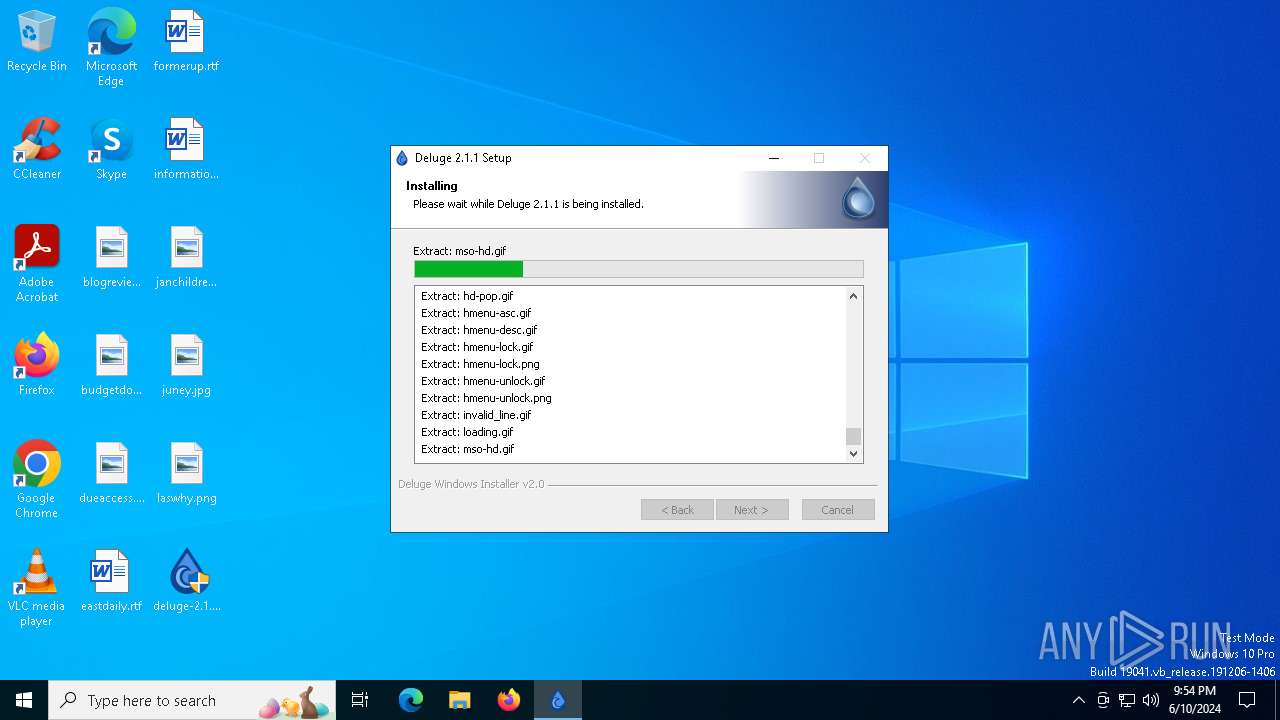
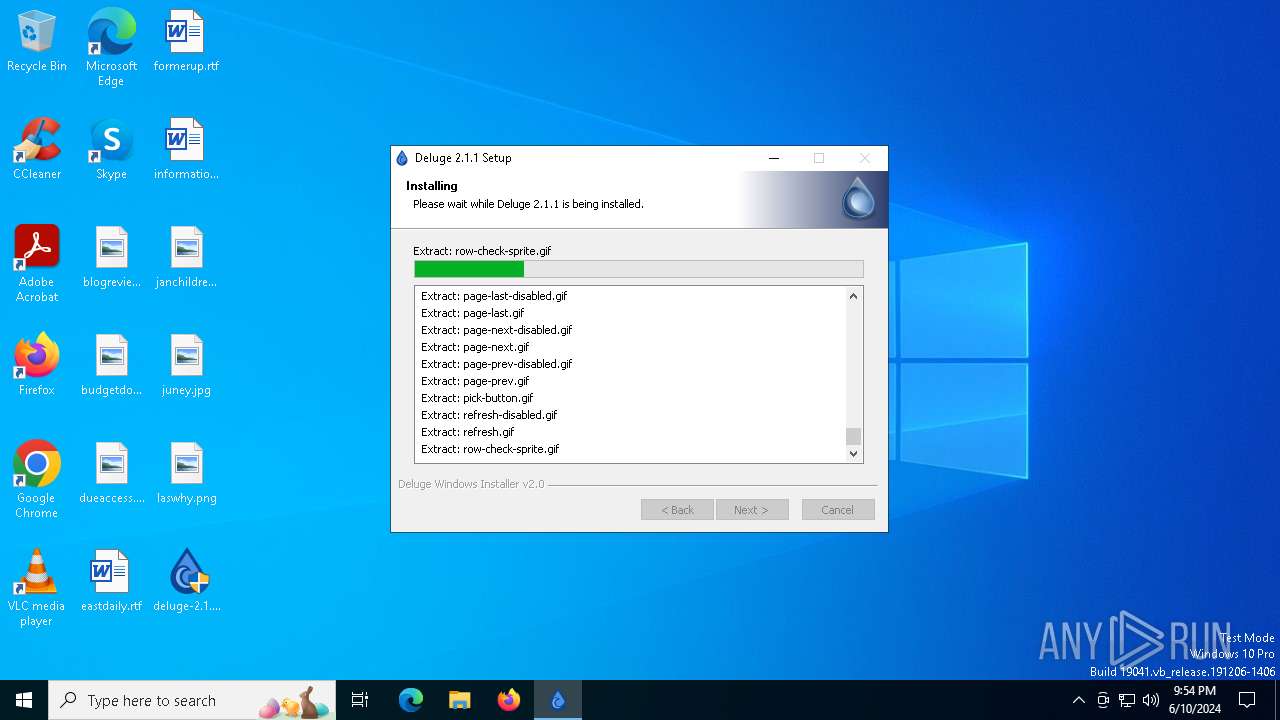
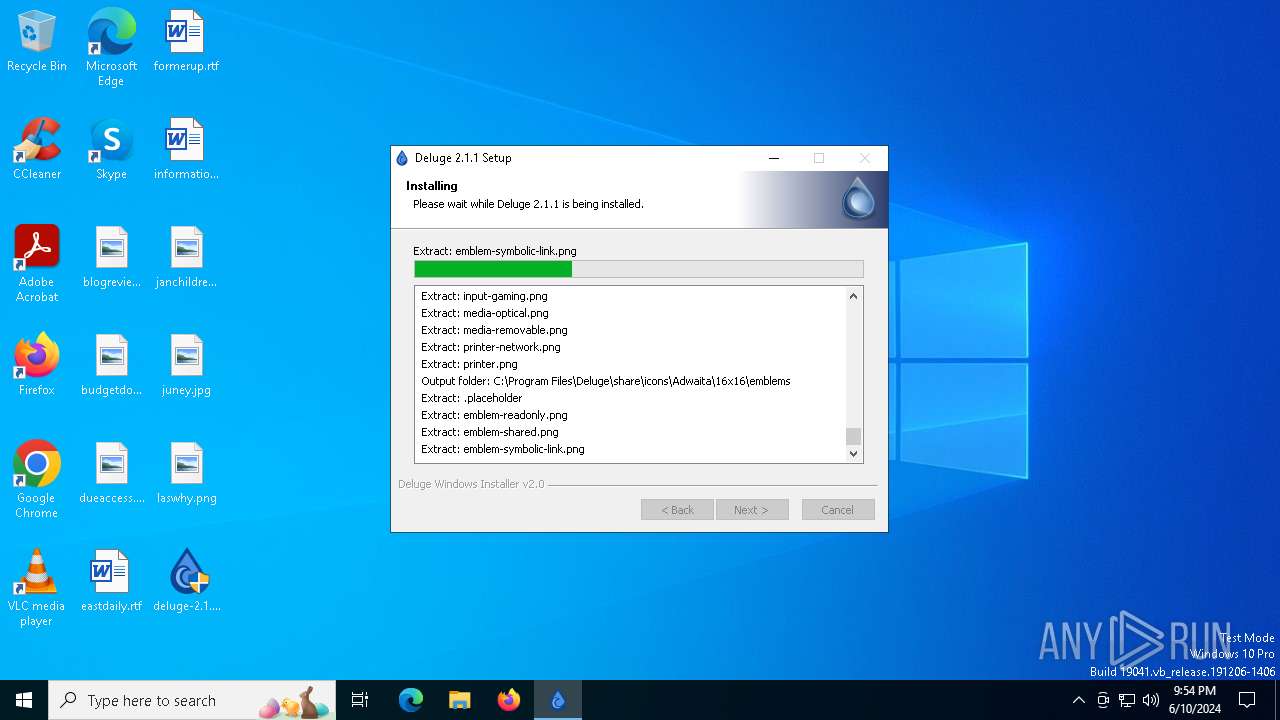
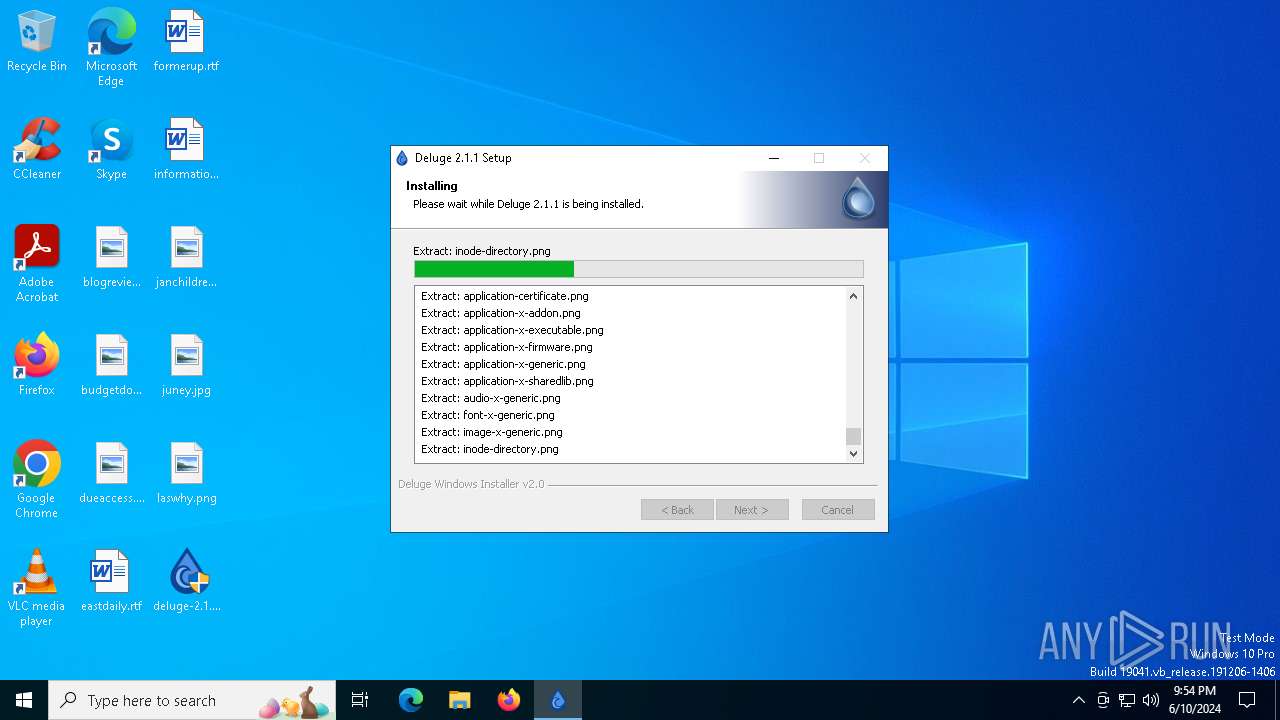
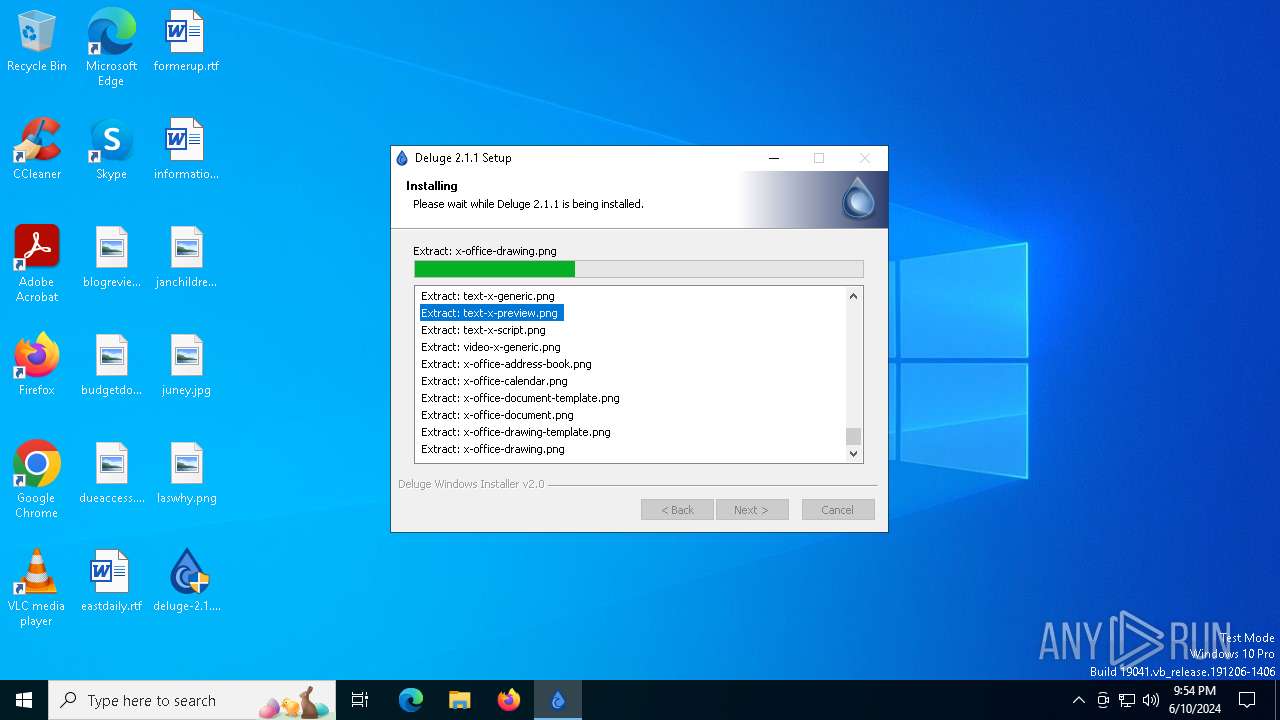
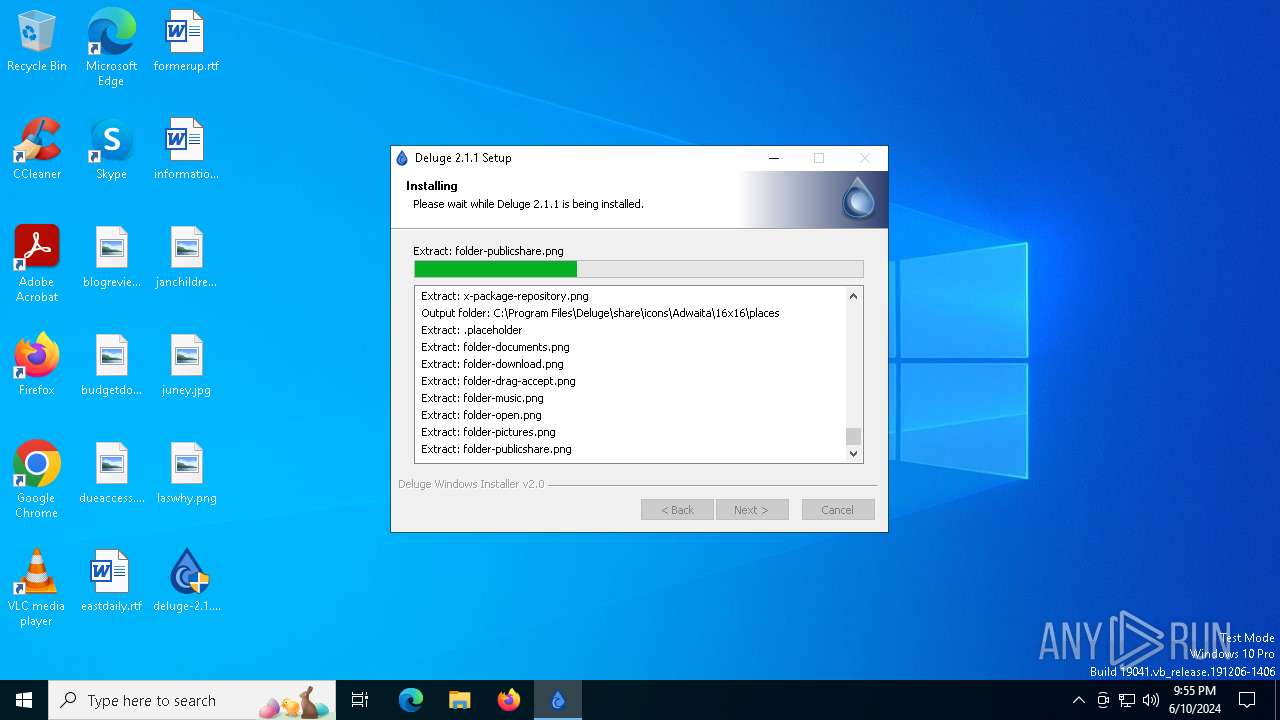
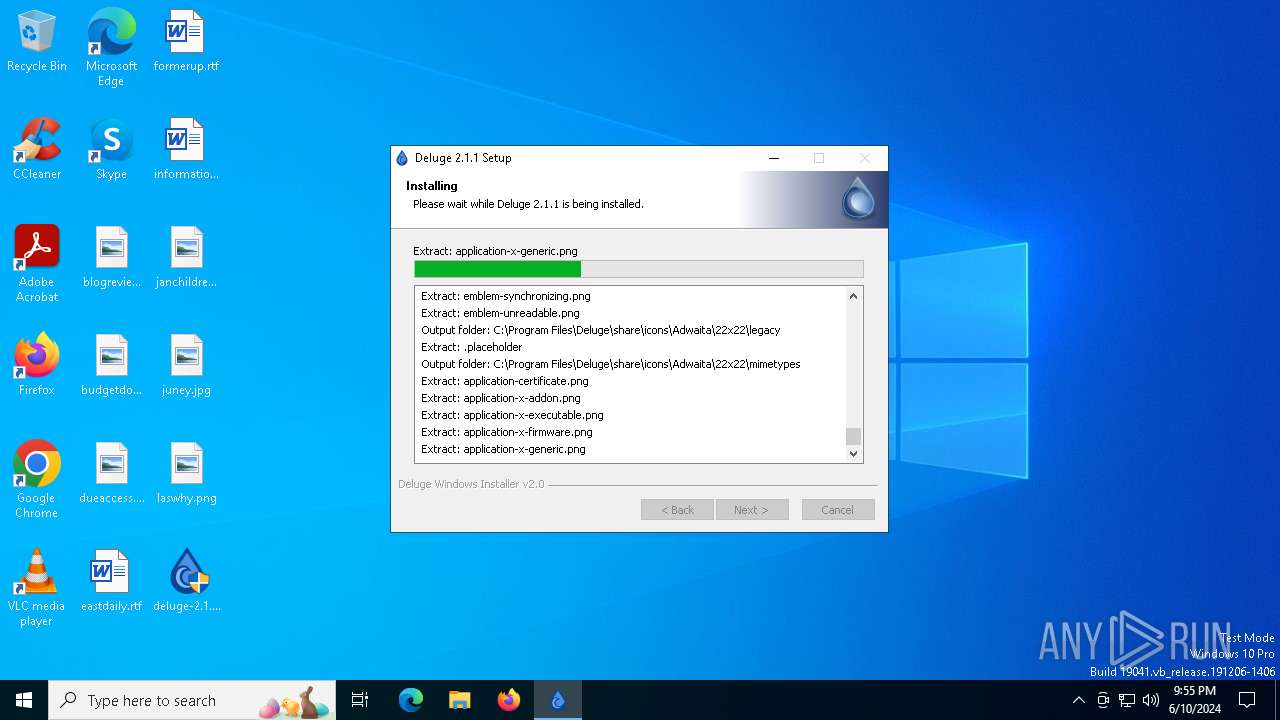
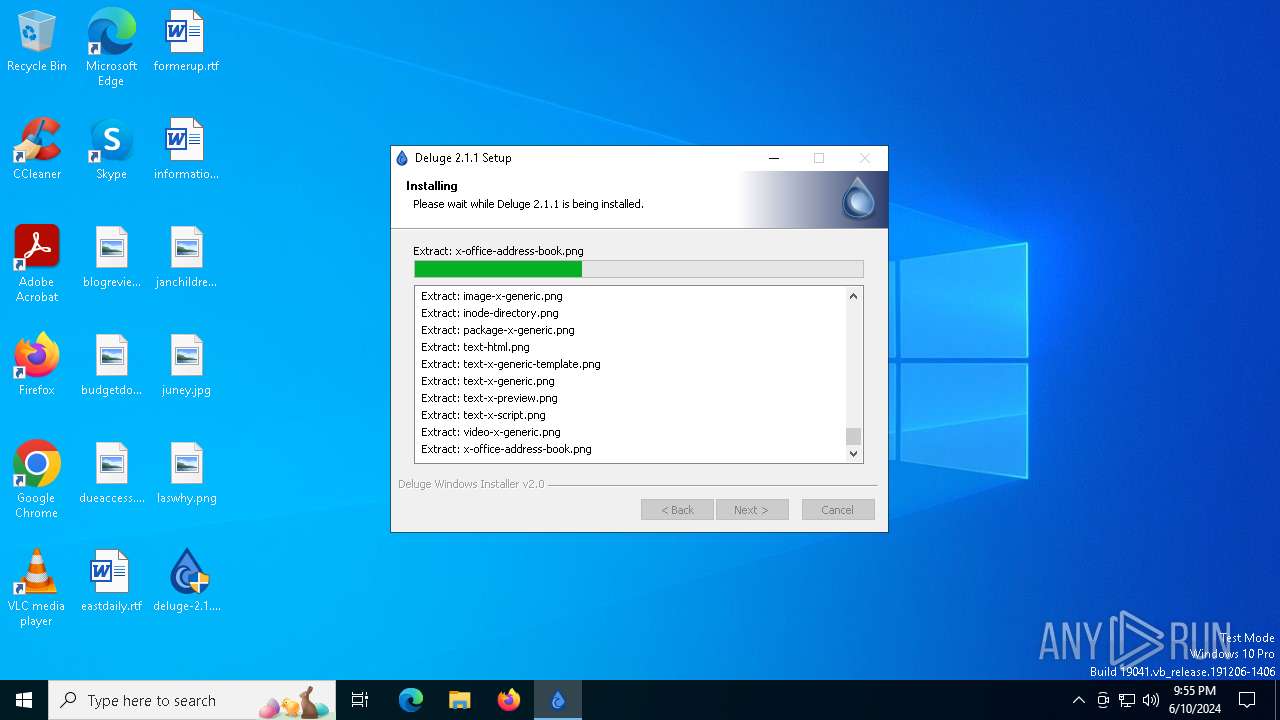
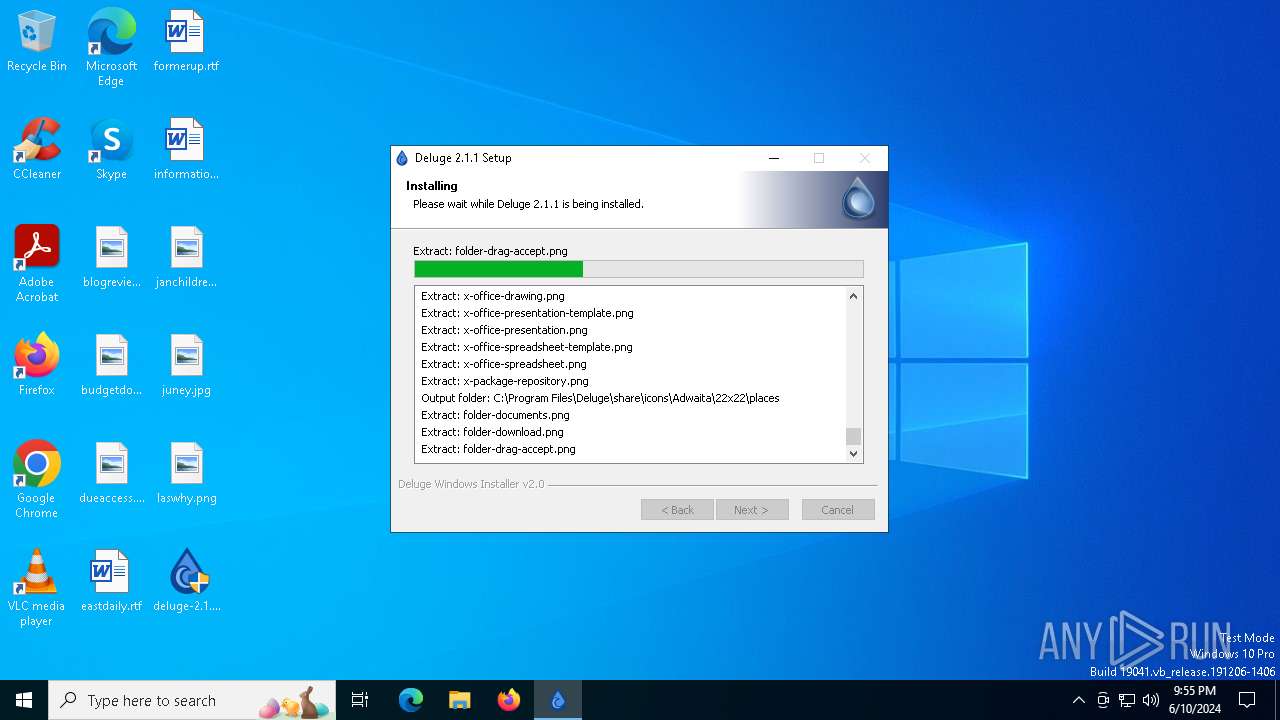
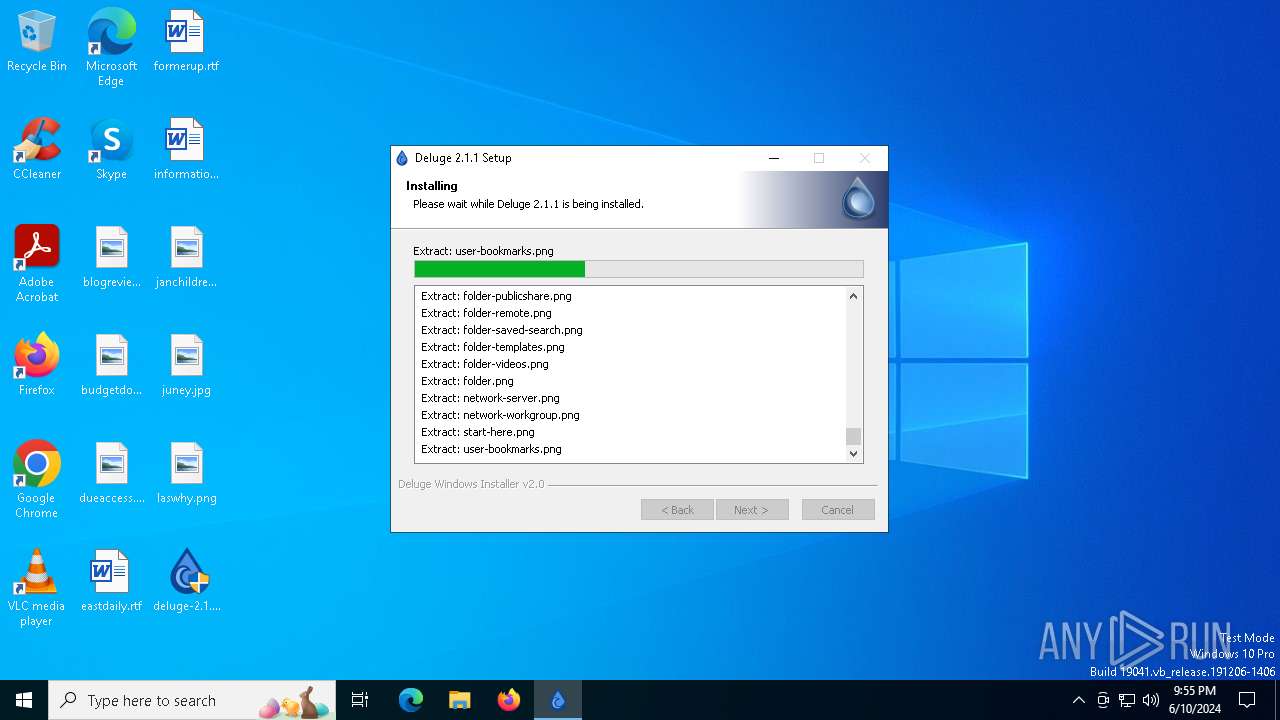
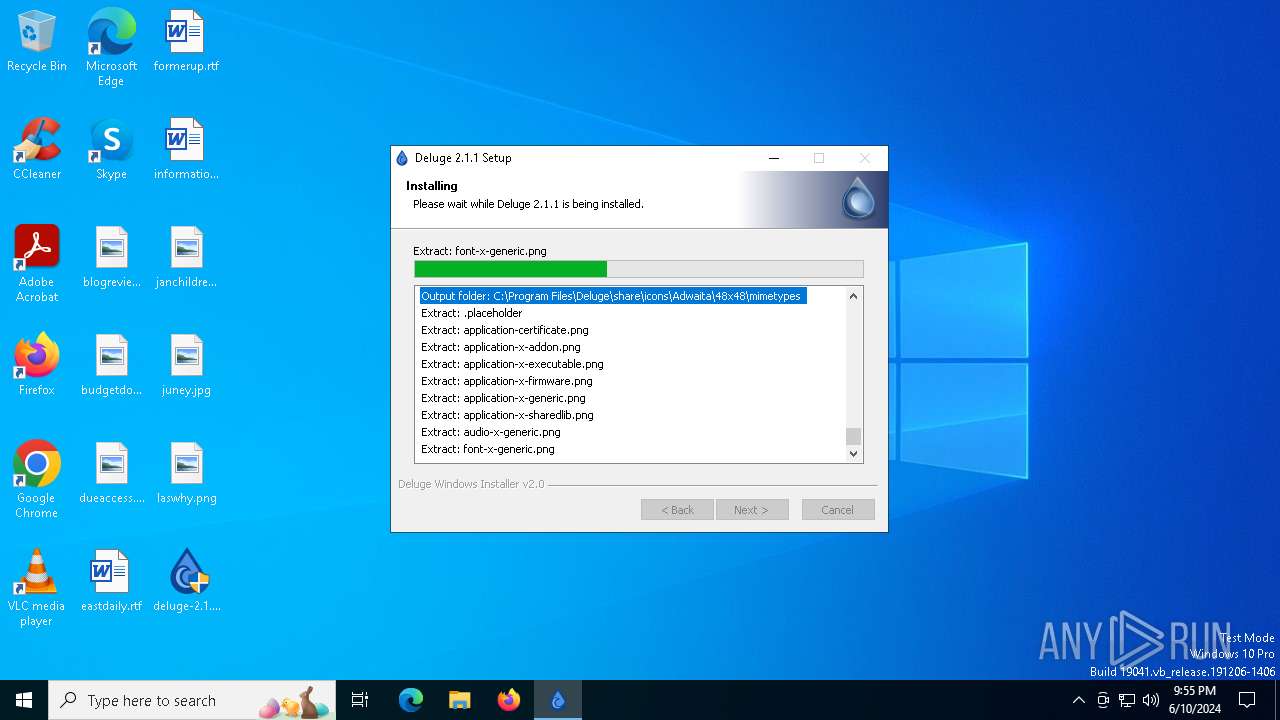
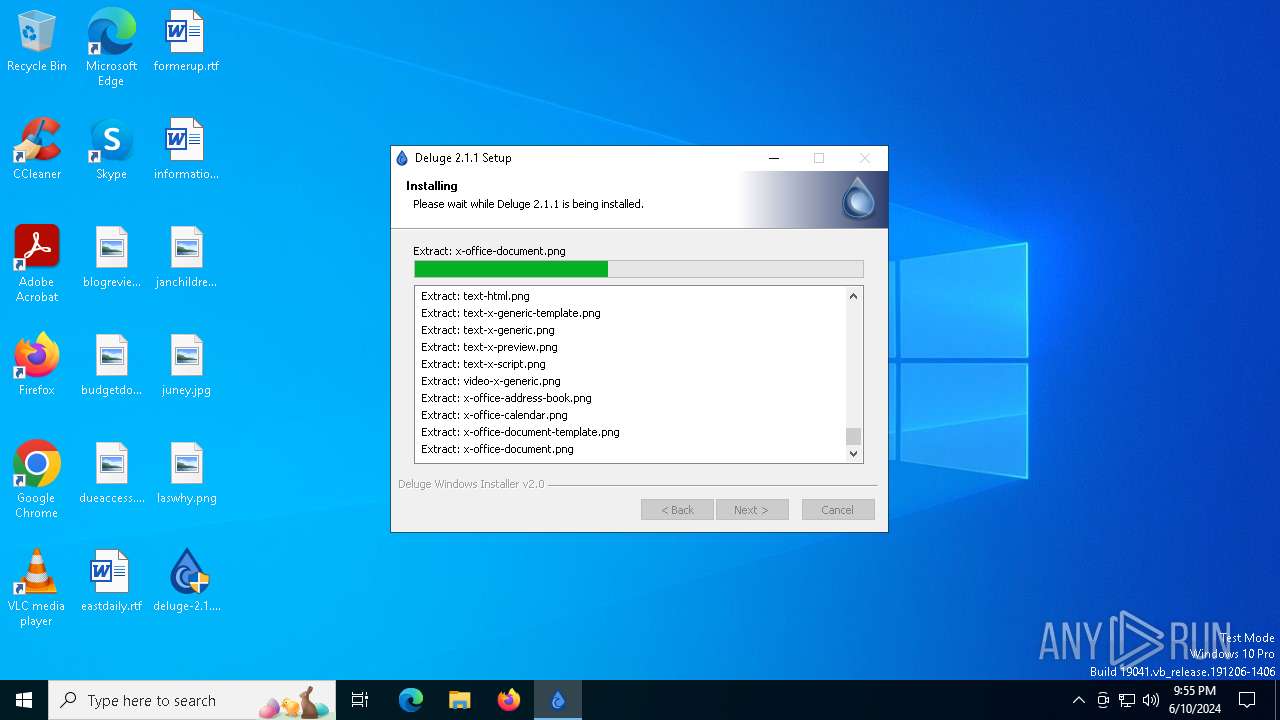
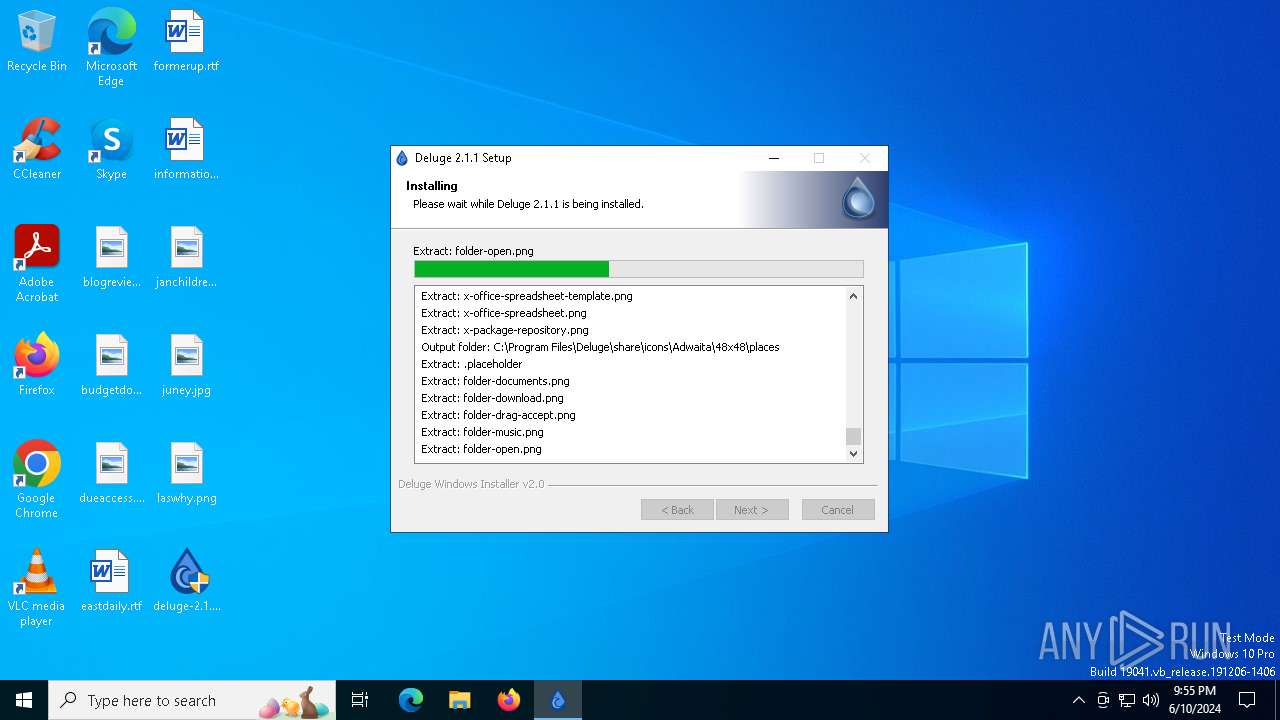
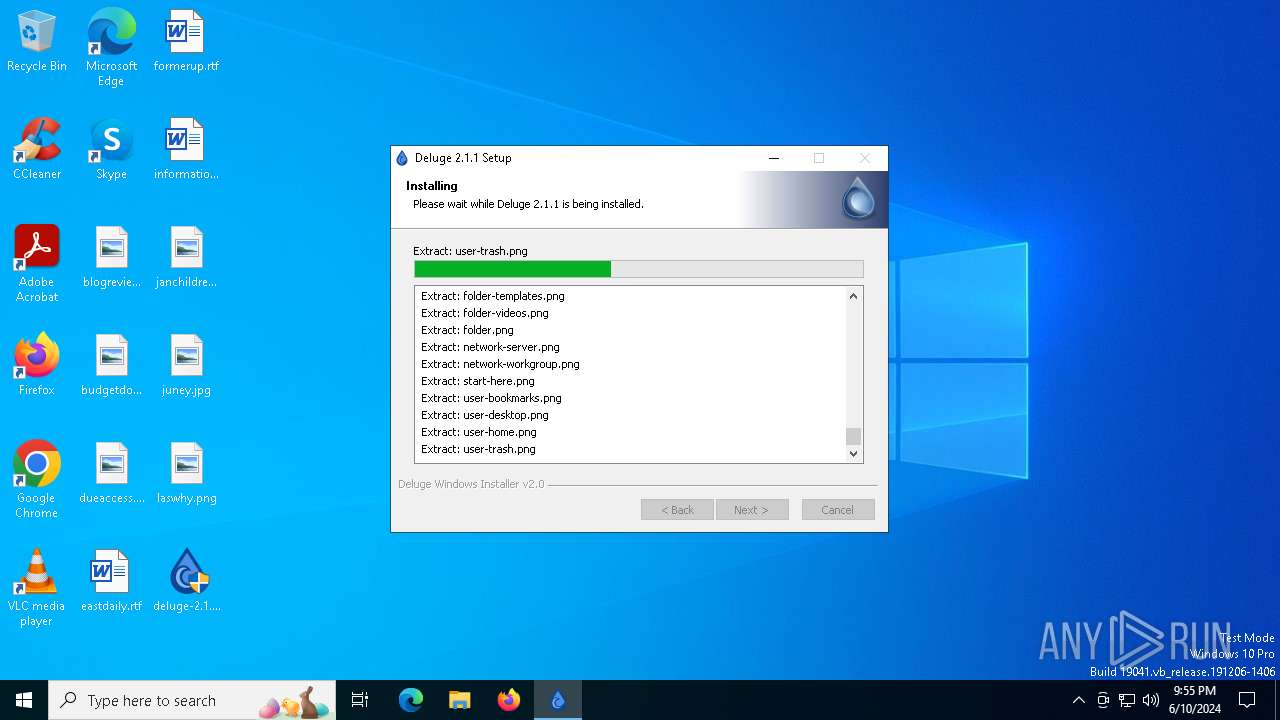
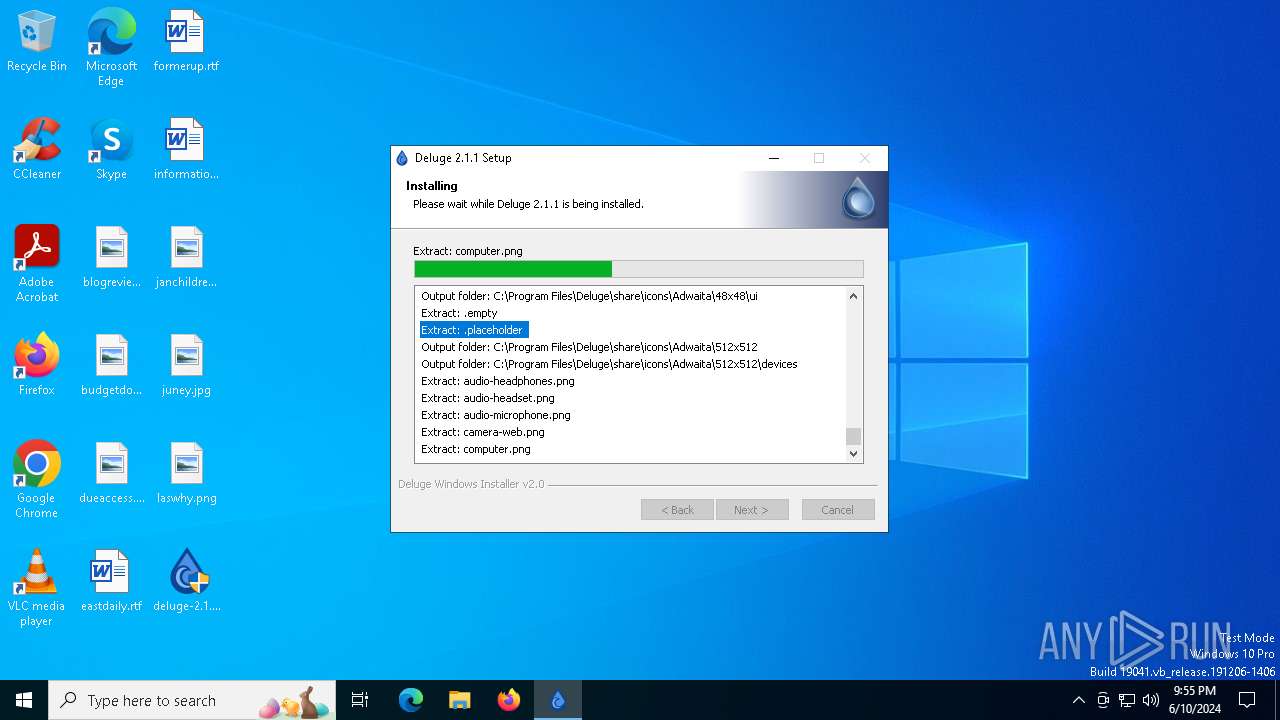
Drops the executable file immediately after the start
- deluge-2.1.1-win64-setup.exe (PID: 6560)
SUSPICIOUS
The process creates files with name similar to system file names
- deluge-2.1.1-win64-setup.exe (PID: 6560)
Malware-specific behavior (creating "System.dll" in Temp)
- deluge-2.1.1-win64-setup.exe (PID: 6560)
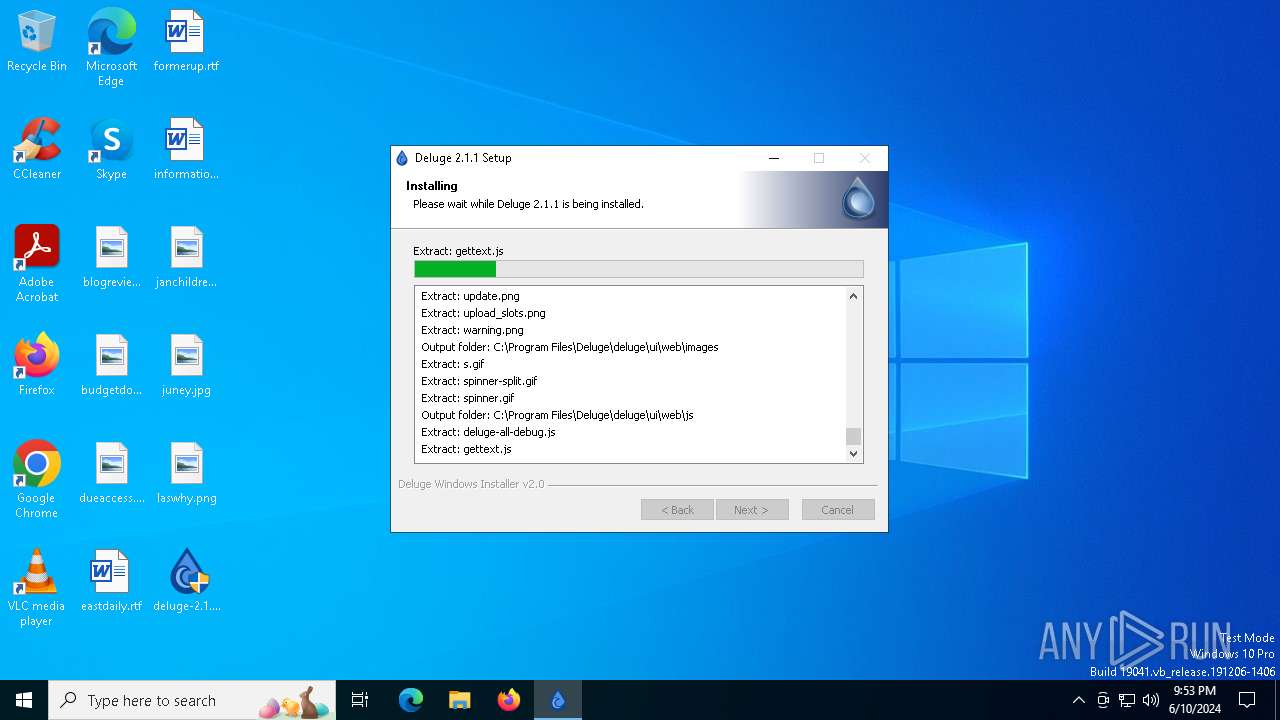
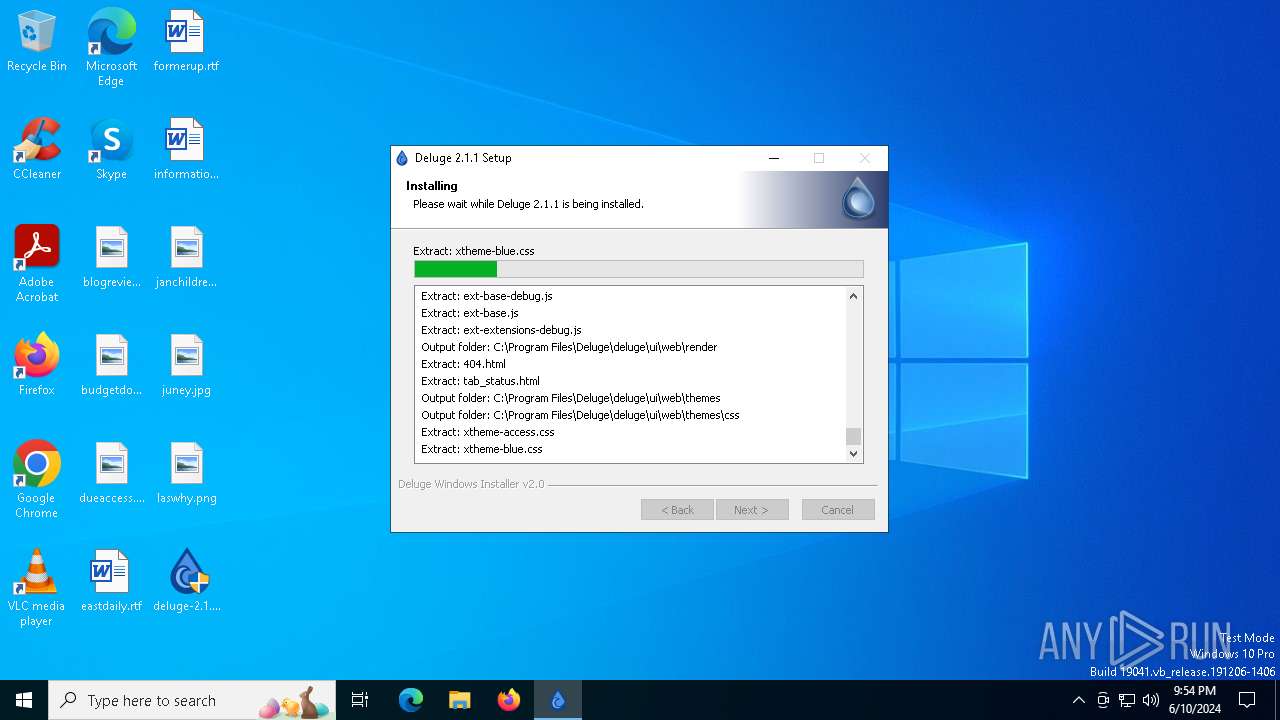
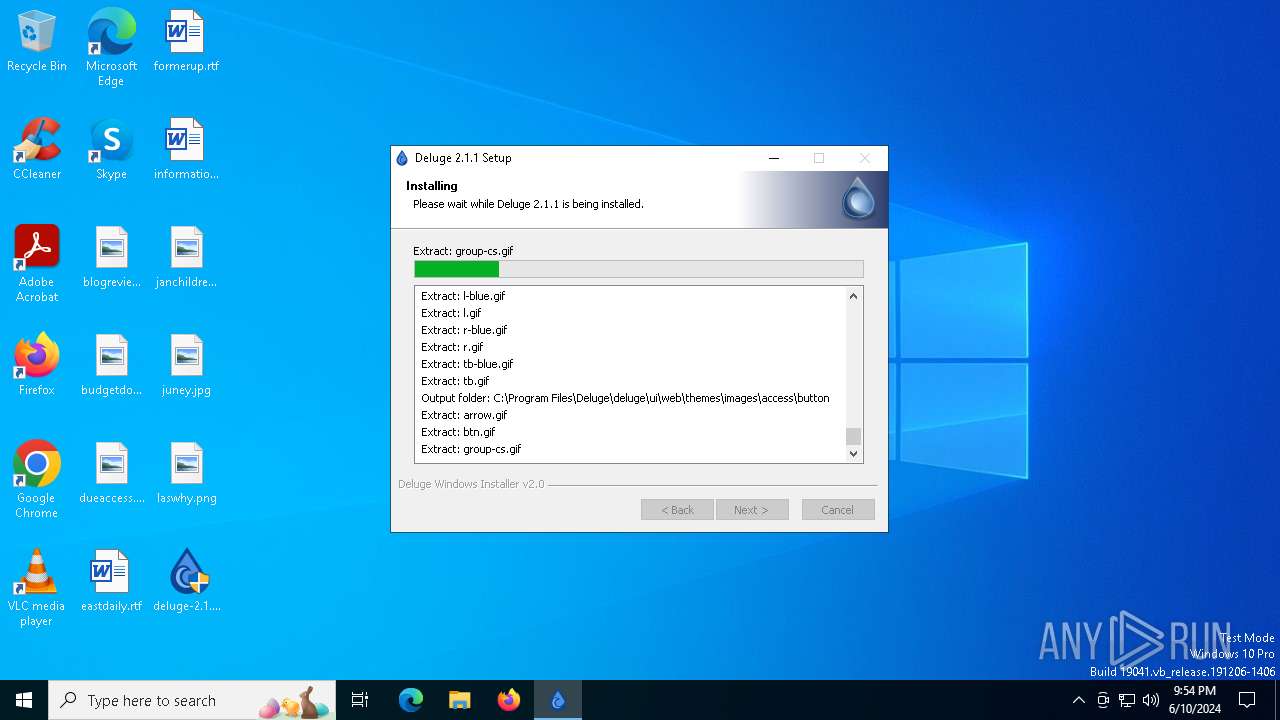
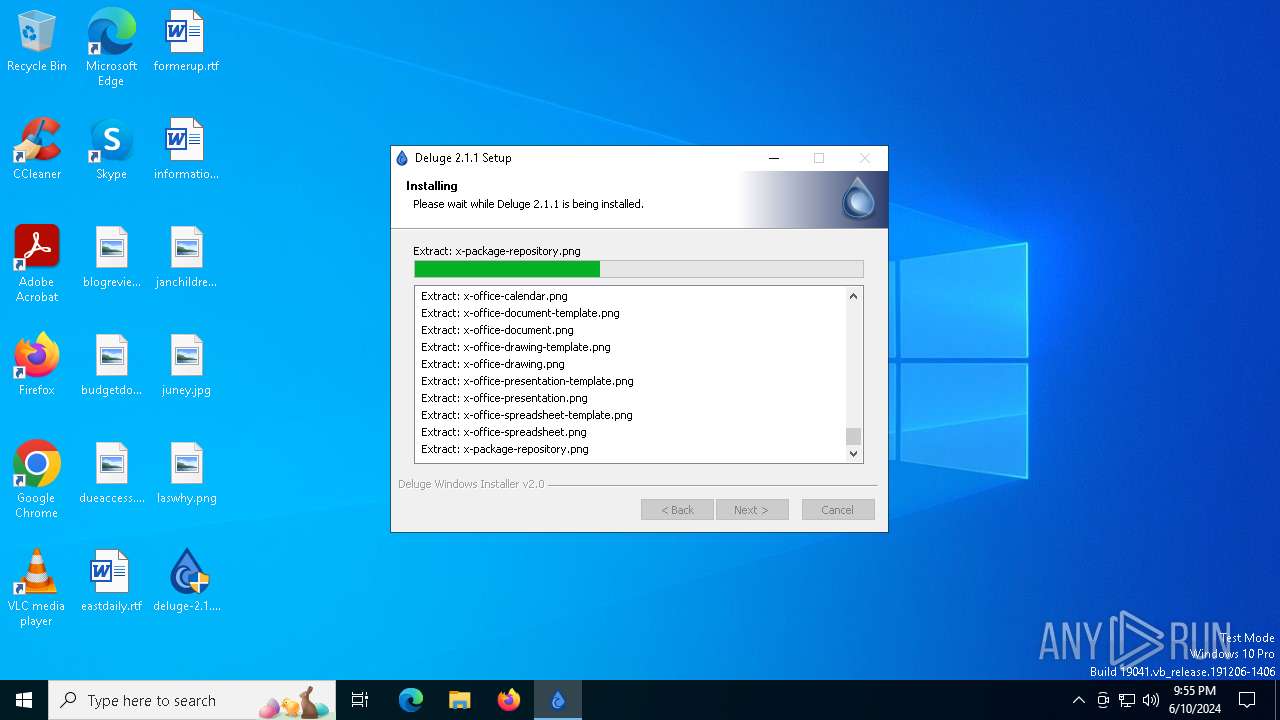
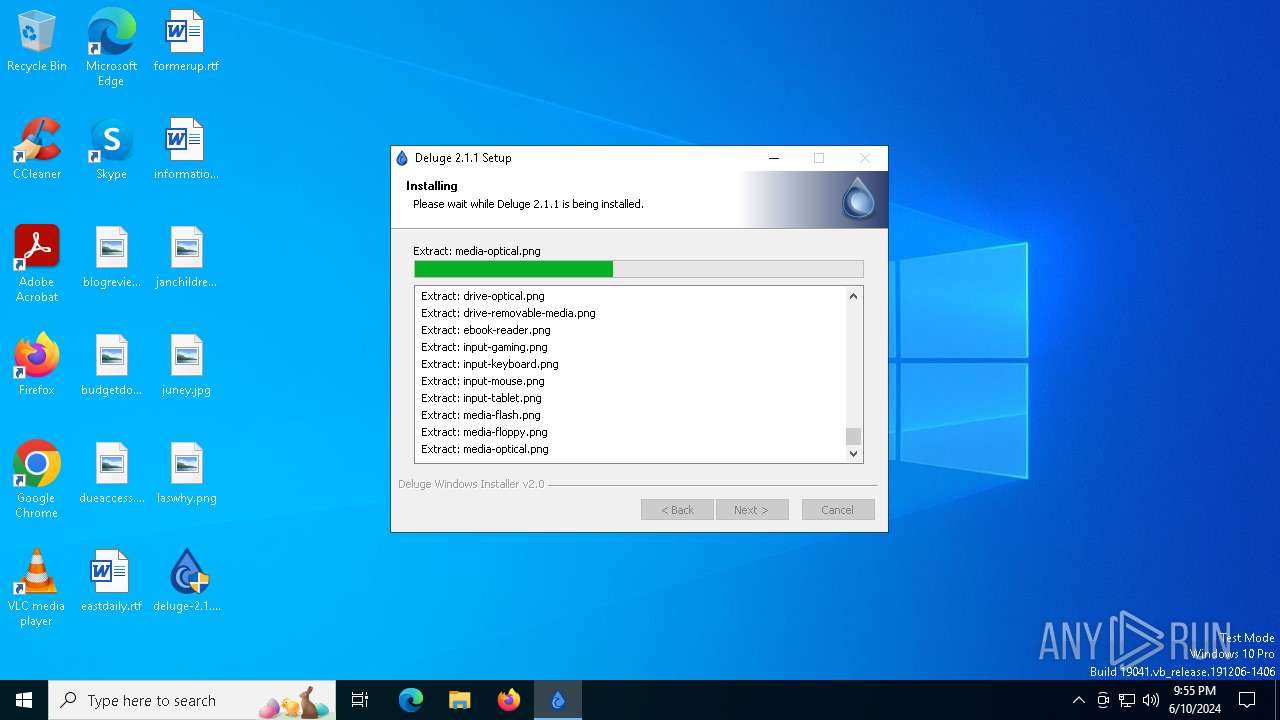
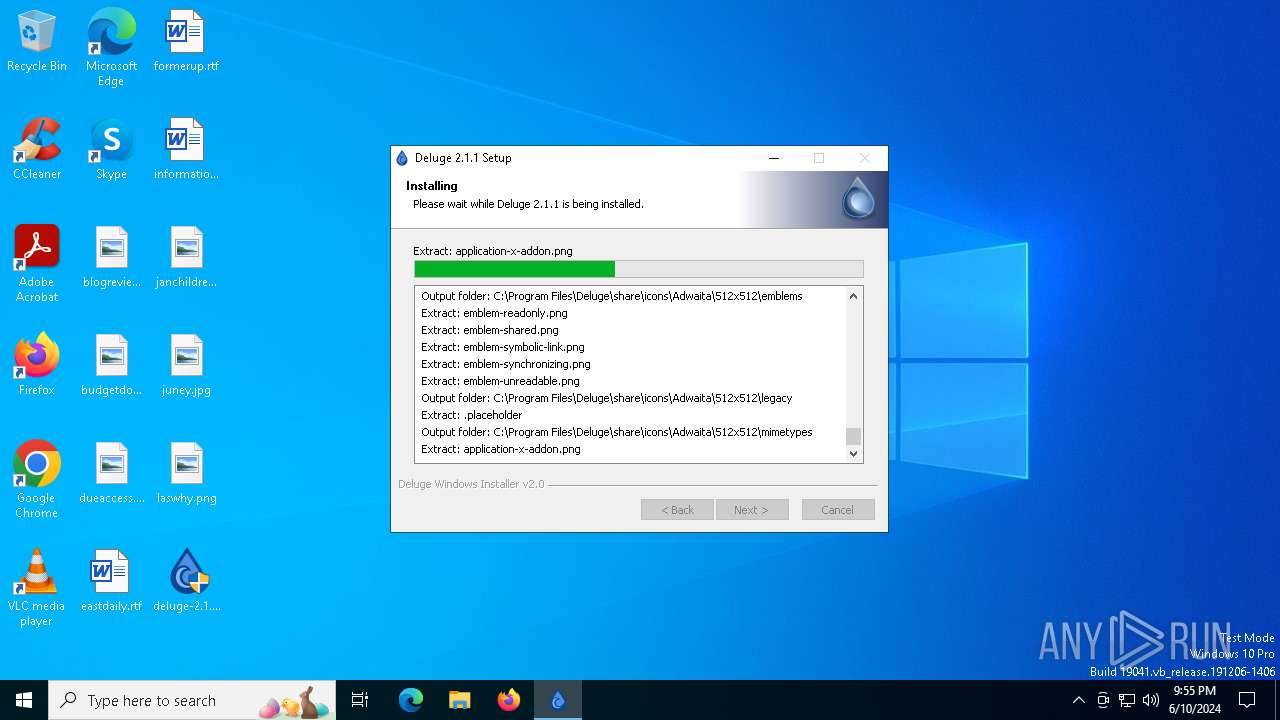
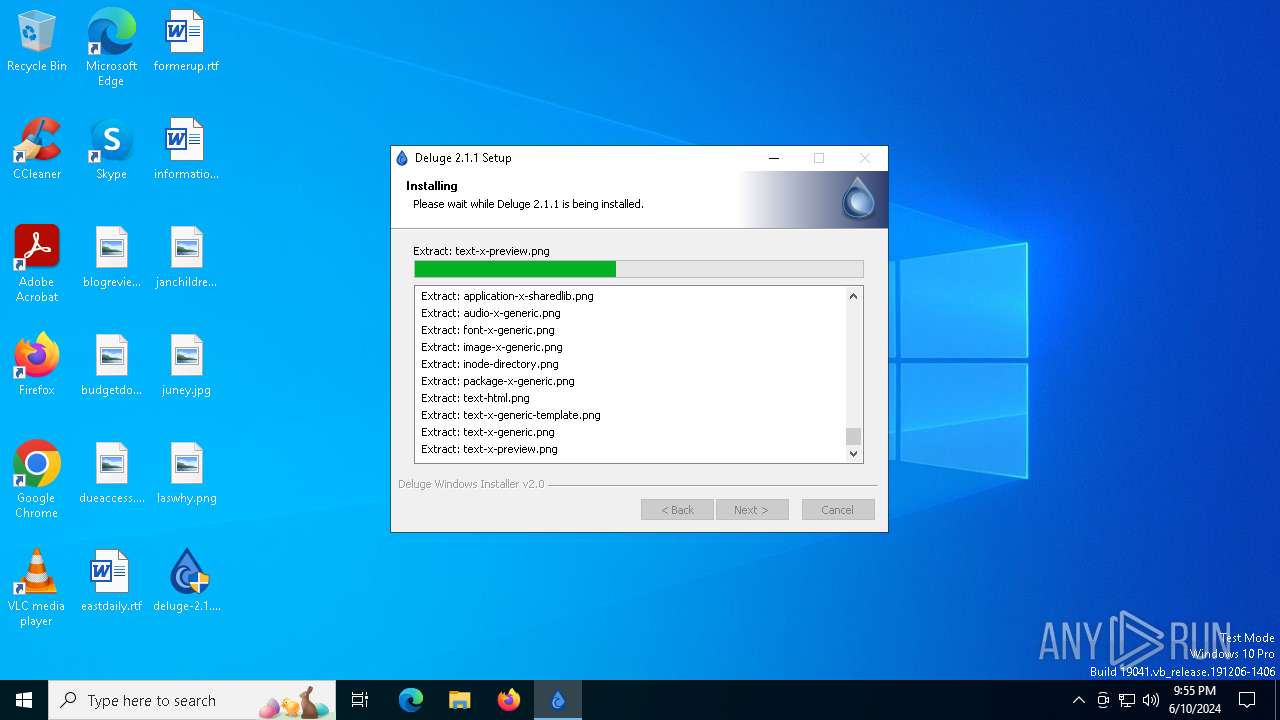
Executable content was dropped or overwritten
- deluge-2.1.1-win64-setup.exe (PID: 6560)
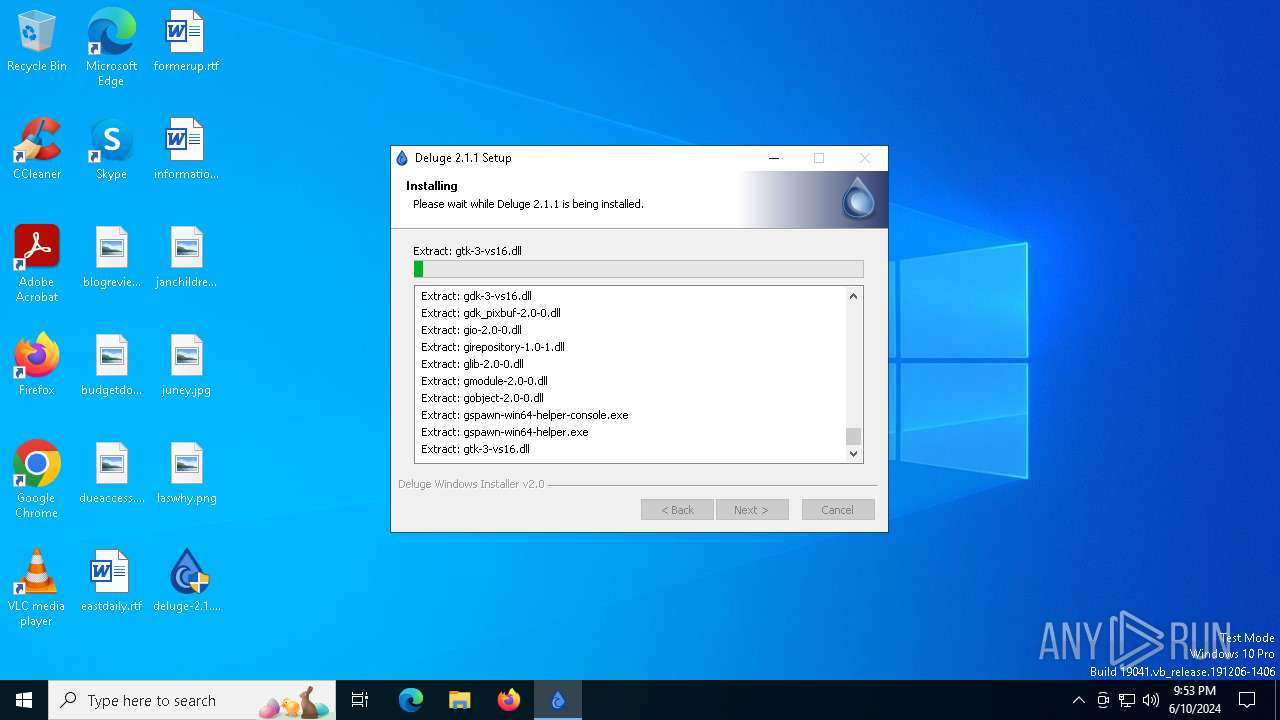
Process drops legitimate windows executable
- deluge-2.1.1-win64-setup.exe (PID: 6560)
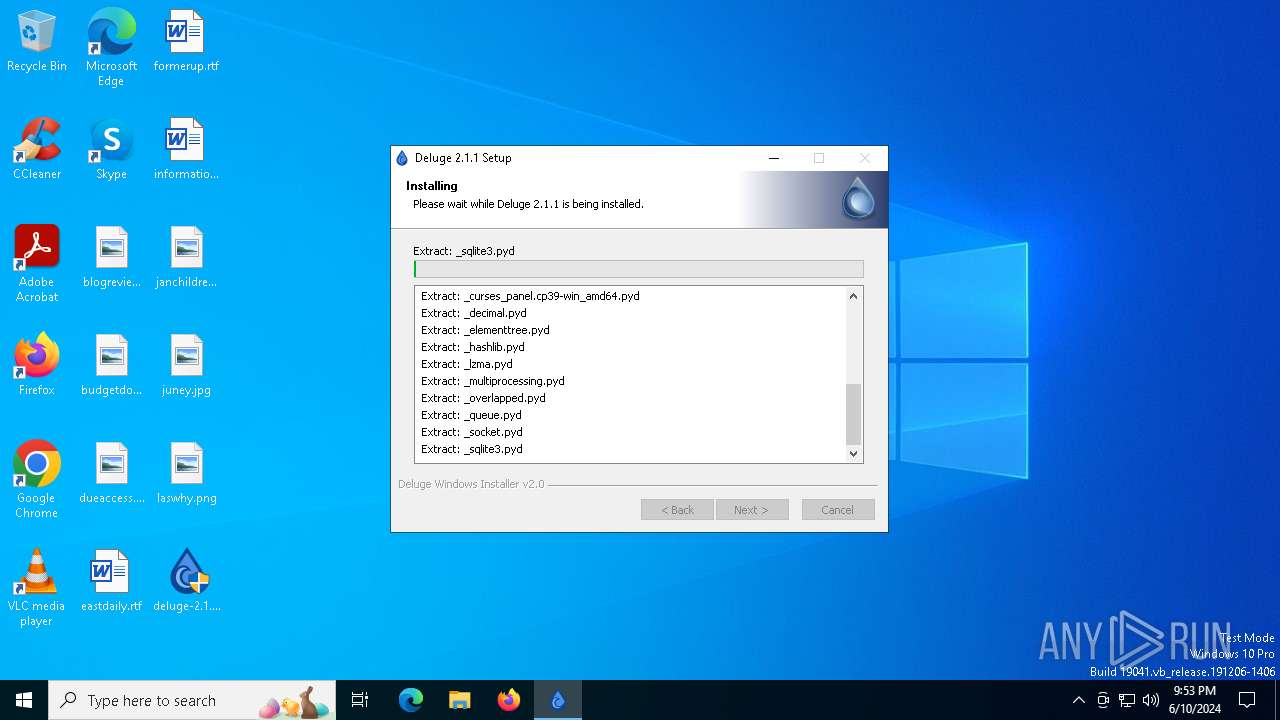
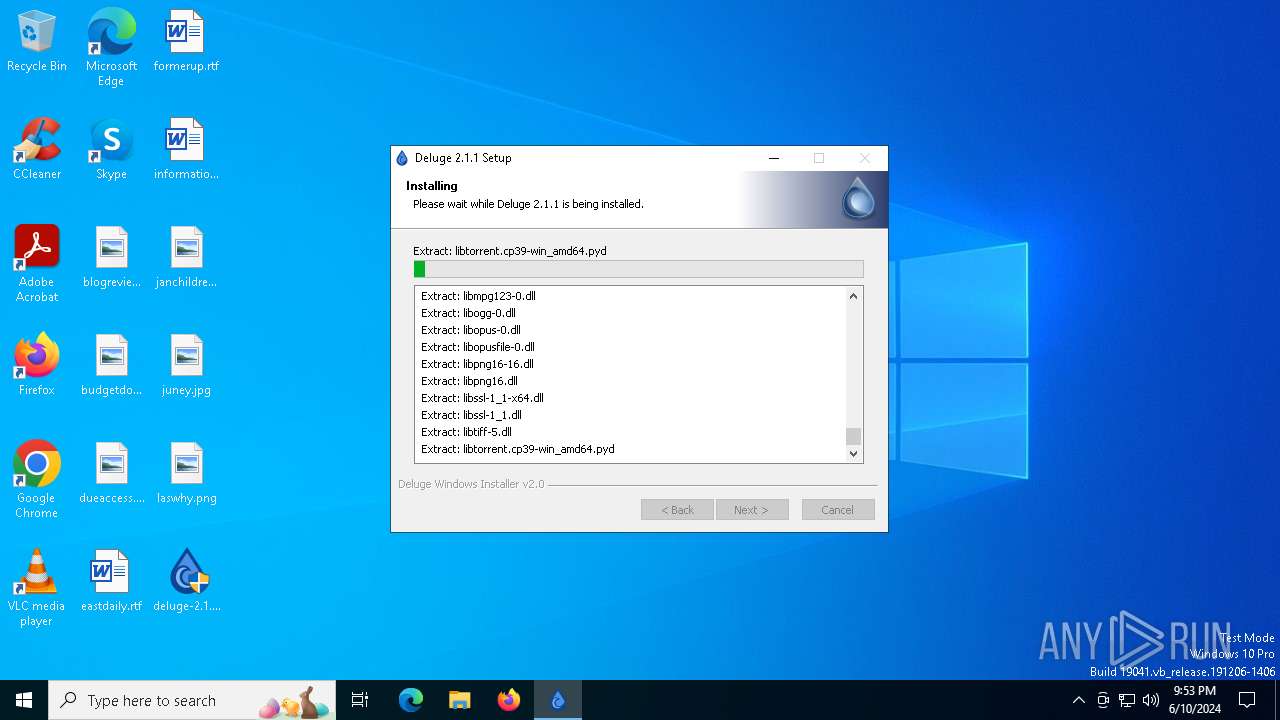
Process drops python dynamic module
- deluge-2.1.1-win64-setup.exe (PID: 6560)
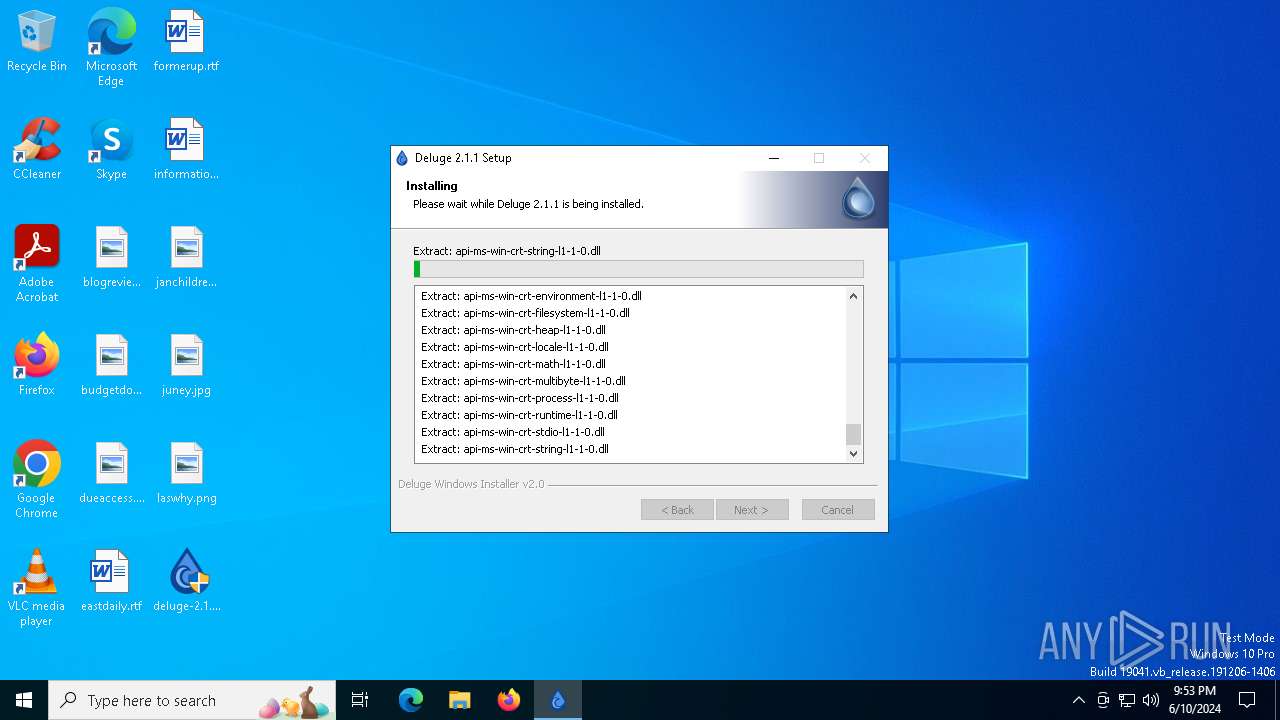
The process drops C-runtime libraries
- deluge-2.1.1-win64-setup.exe (PID: 6560)
INFO
Checks supported languages
- deluge-2.1.1-win64-setup.exe (PID: 6560)
Reads the computer name
- deluge-2.1.1-win64-setup.exe (PID: 6560)
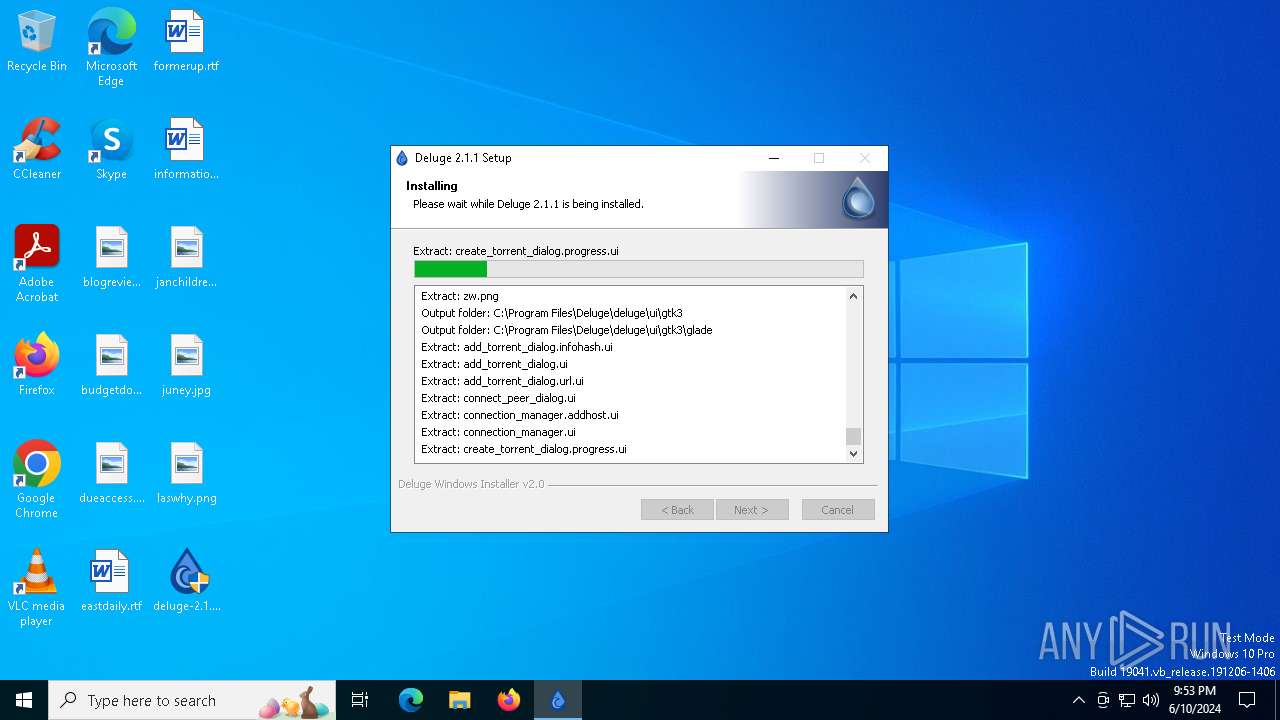
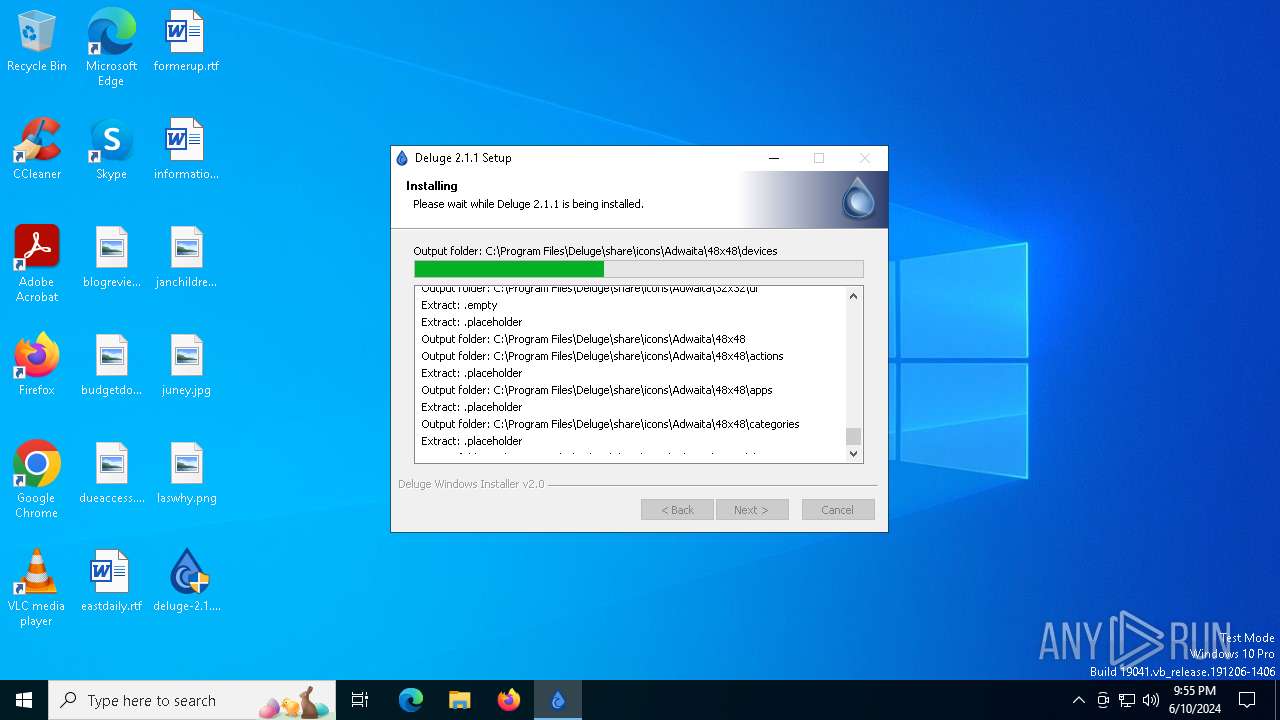
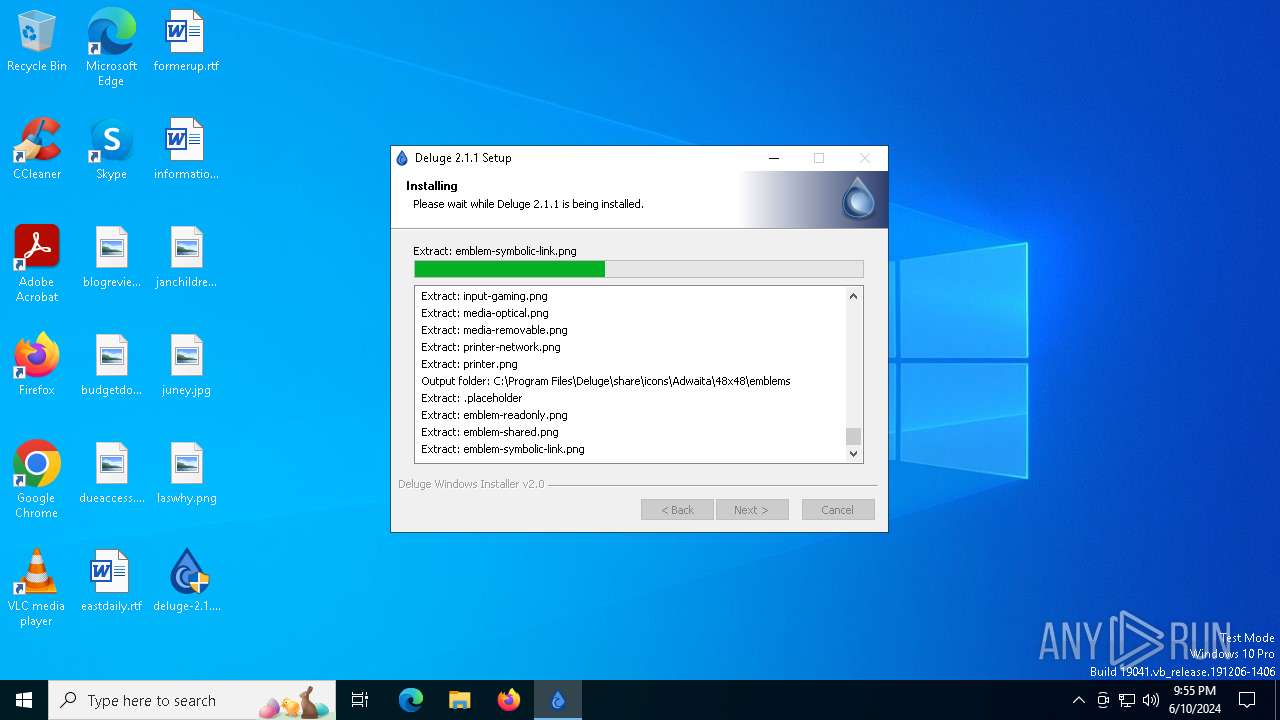
Creates files in the program directory
- deluge-2.1.1-win64-setup.exe (PID: 6560)
Create files in a temporary directory
- deluge-2.1.1-win64-setup.exe (PID: 6560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:56:47+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3640 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.0.0 |
| ProductVersionNumber: | 2.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
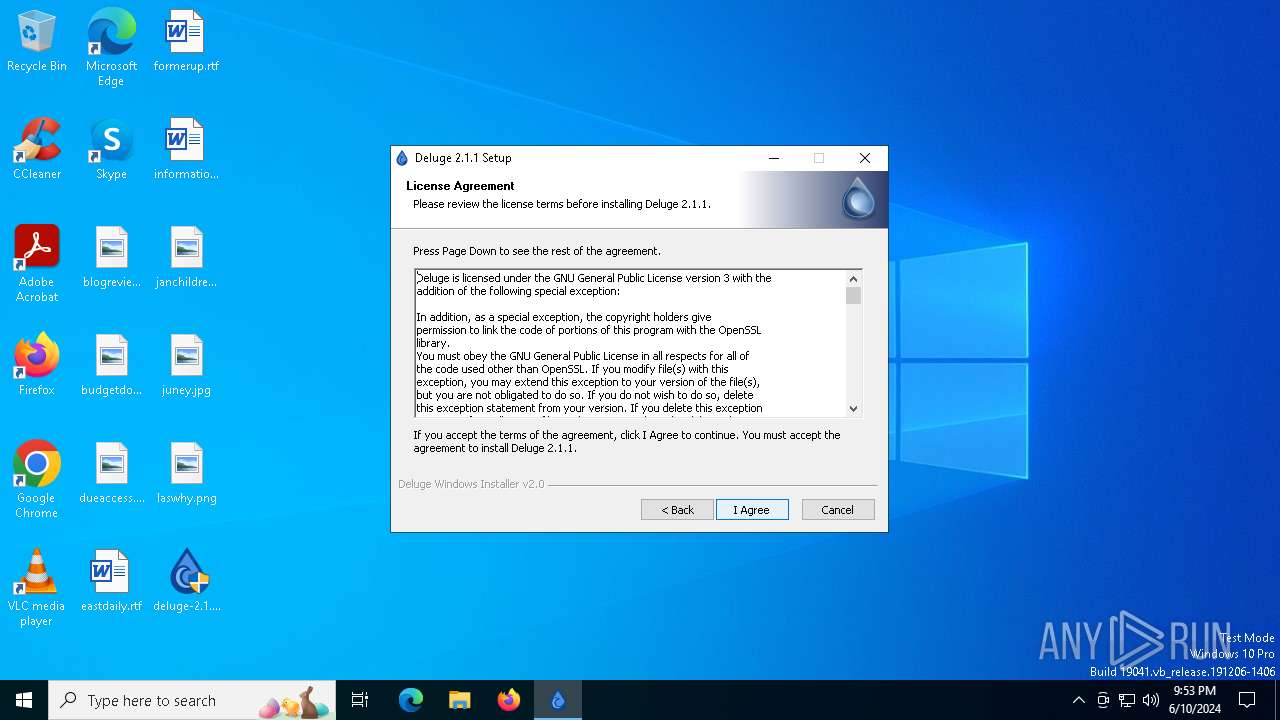
| Comments: | Deluge Bittorrent Client |
| CompanyName: | Deluge Team |
| FileDescription: | Deluge Application Installer |
| FileVersion: | 2.0.0.0 |
| LegalCopyright: | Deluge Team |
| OriginalFileName: | deluge-2.1.1-win64-setup.exe |
| ProductName: | Deluge |
| ProductVersion: | 2.1.1.0 |
Total processes
111
Monitored processes
2
Malicious processes
1
Suspicious processes
0
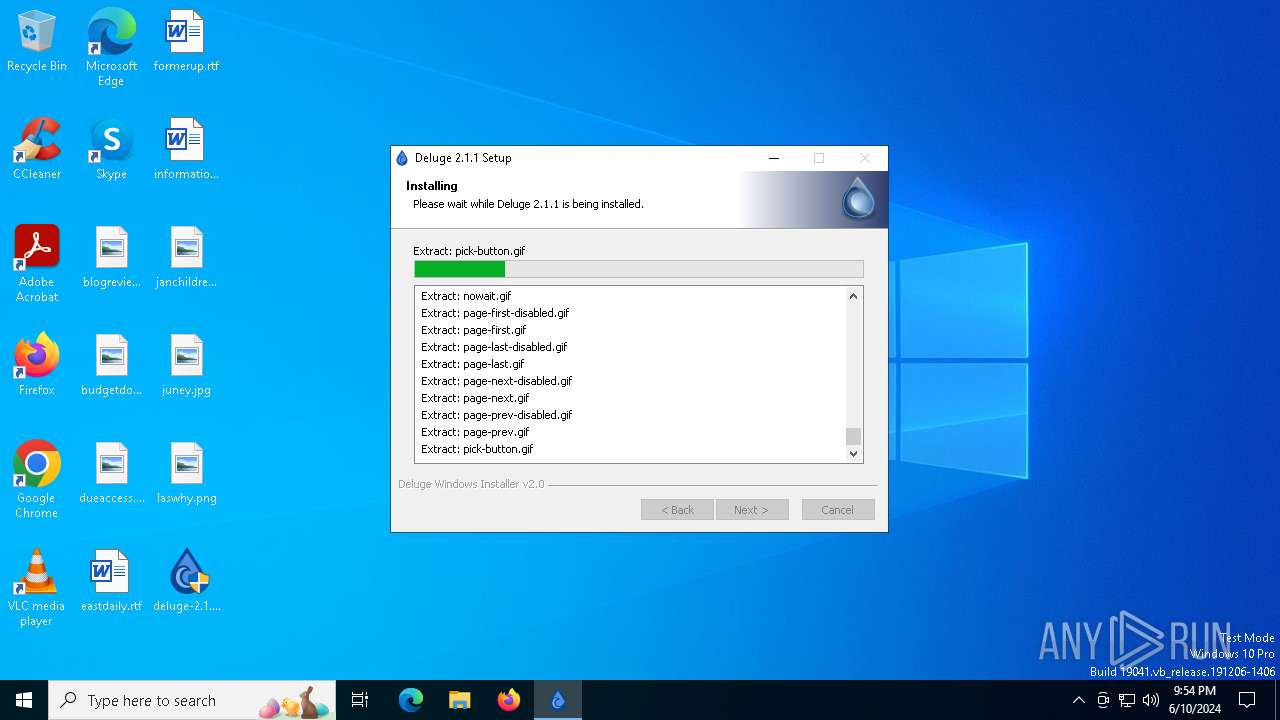
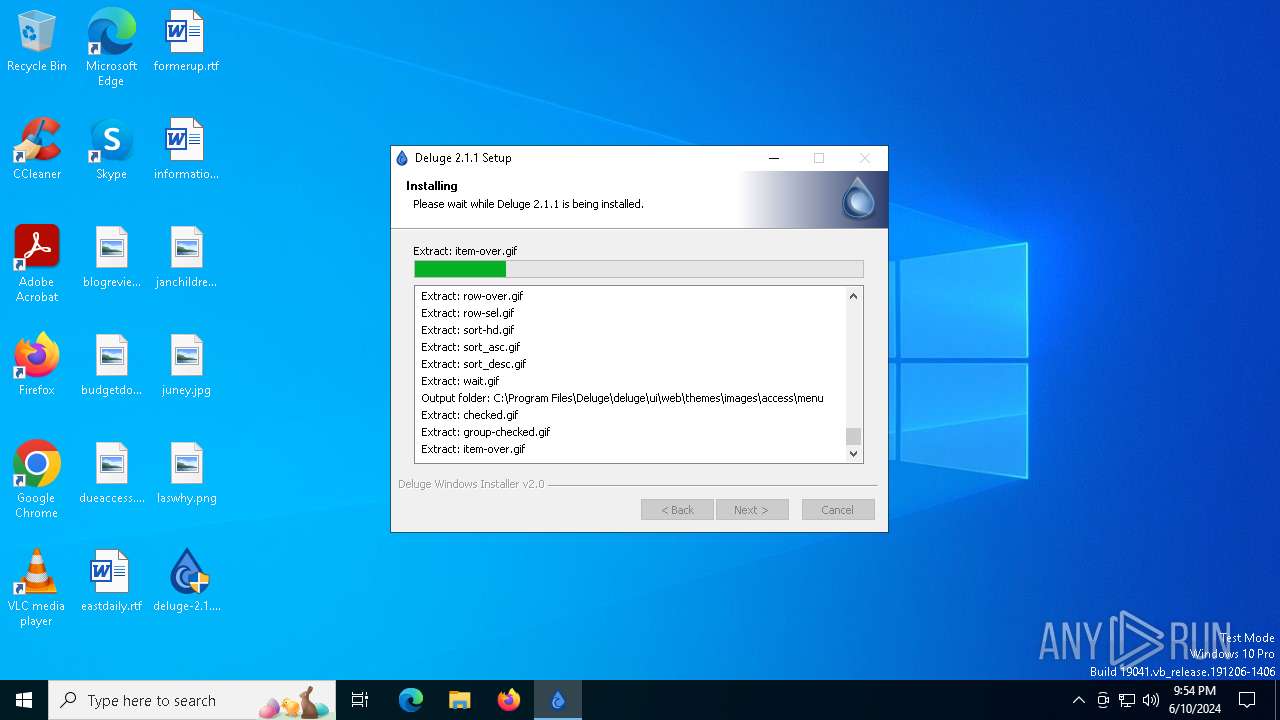
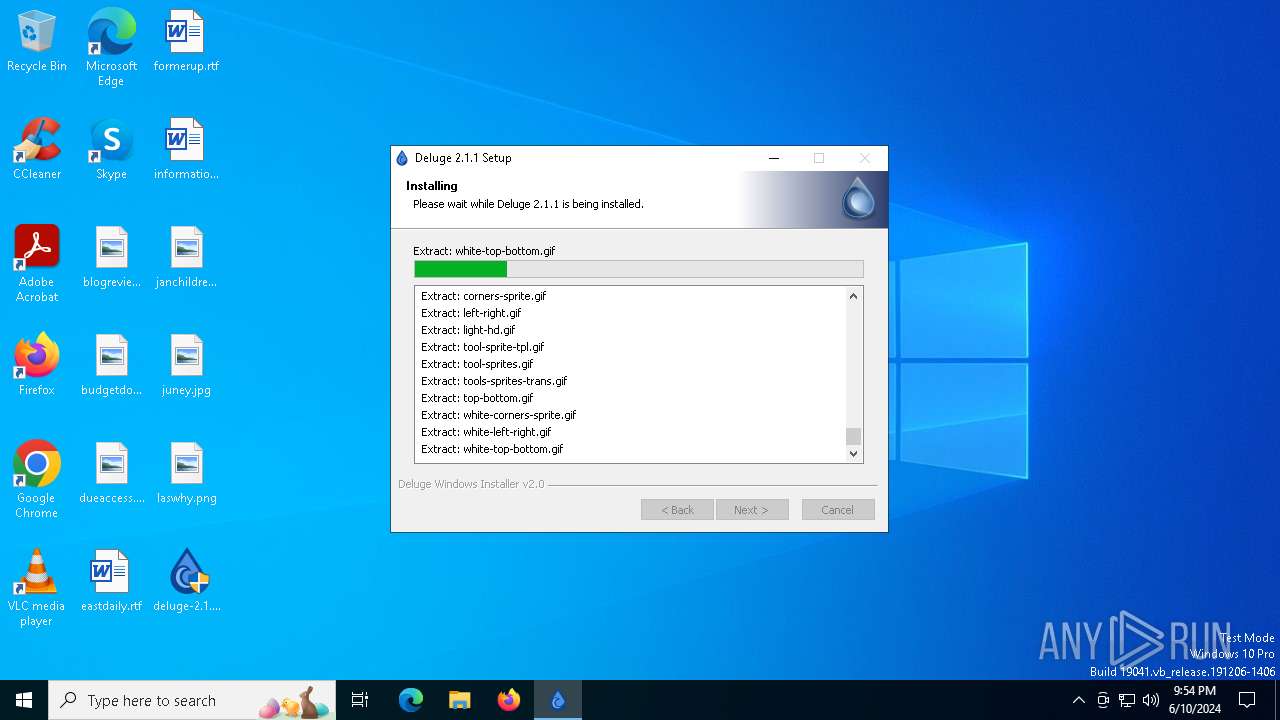
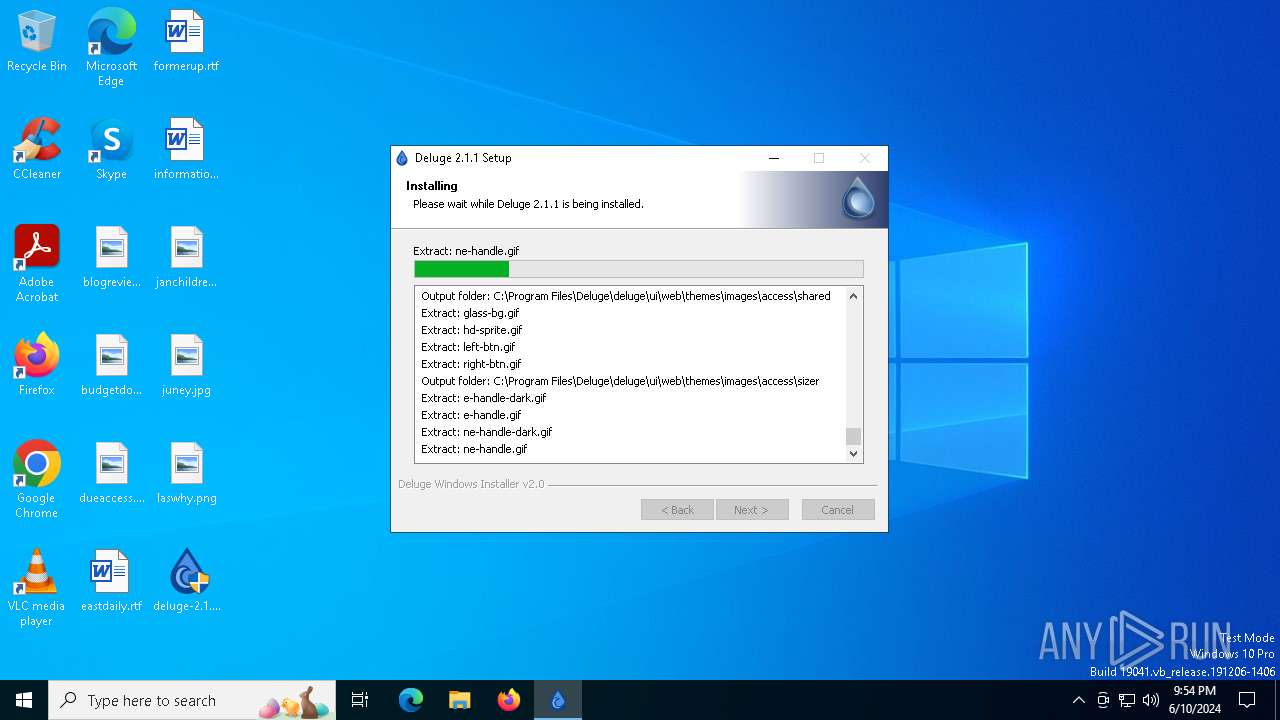
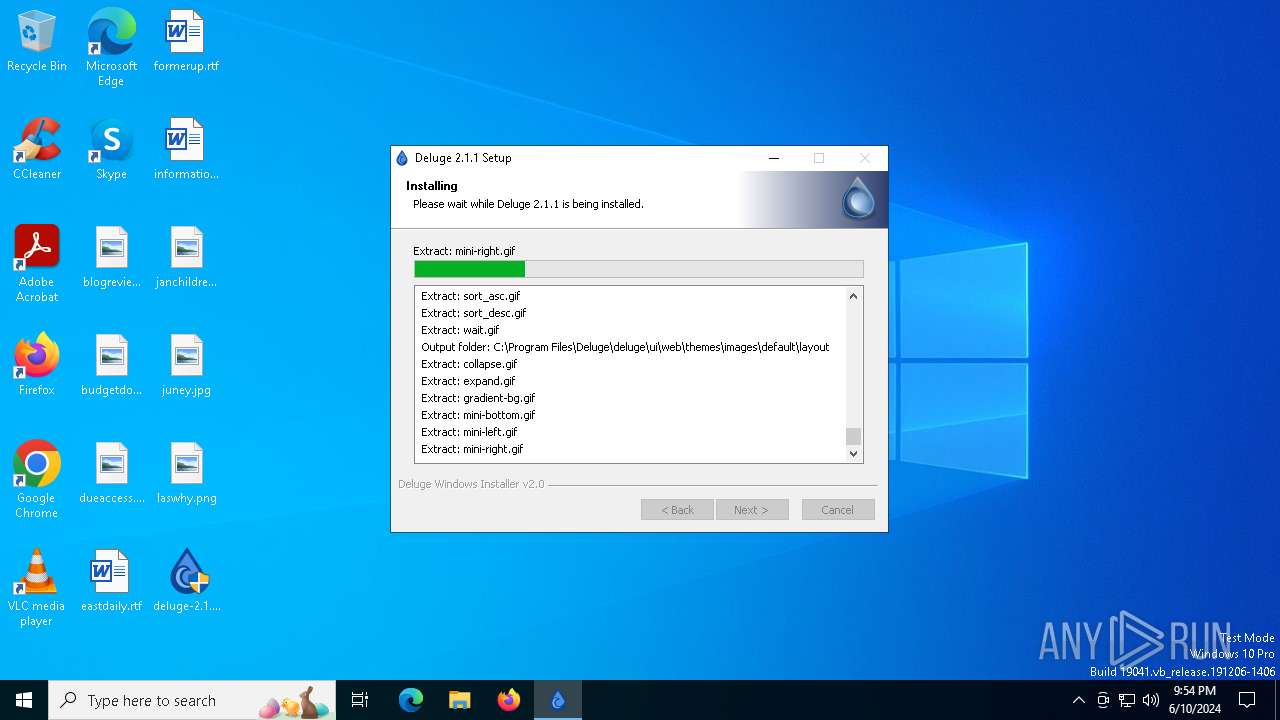
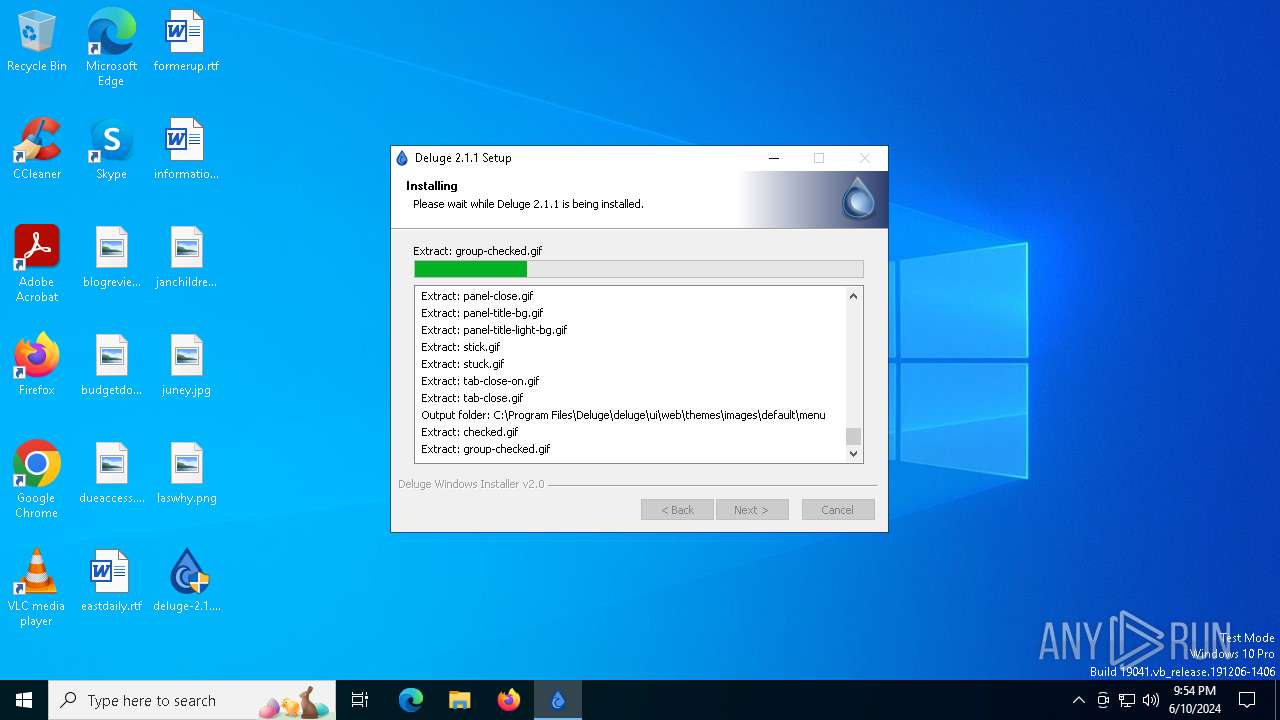
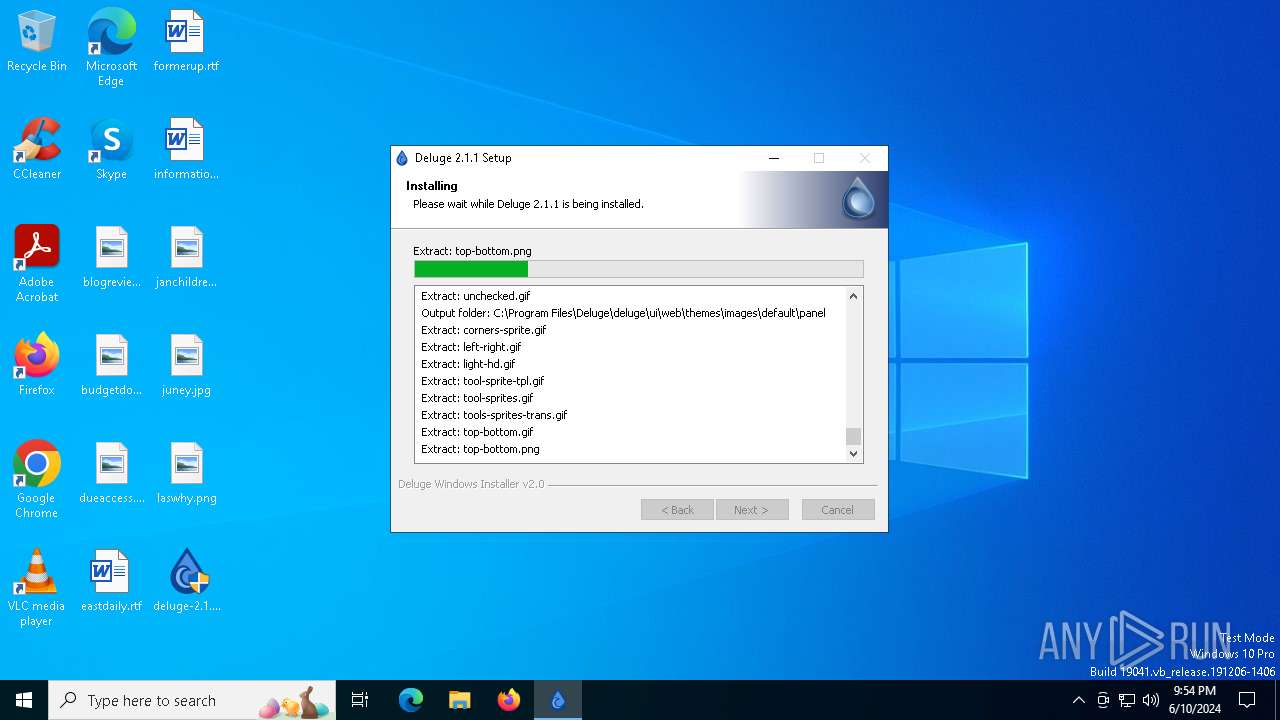
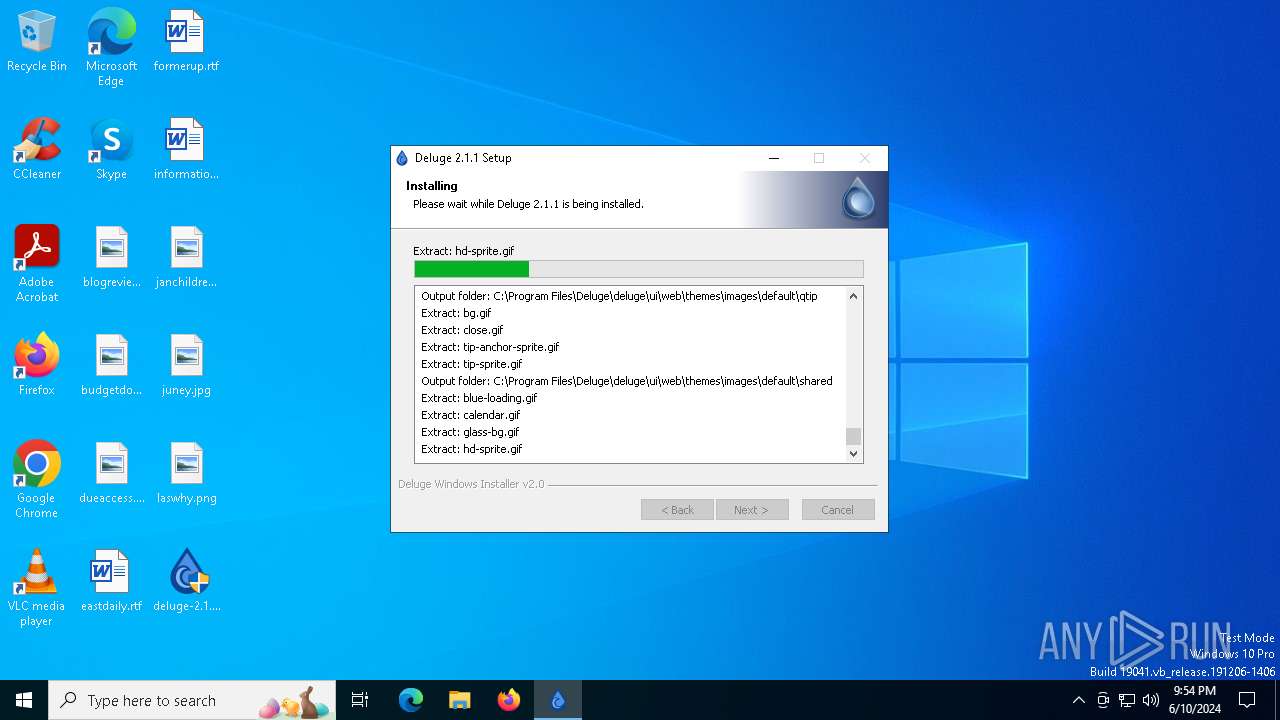
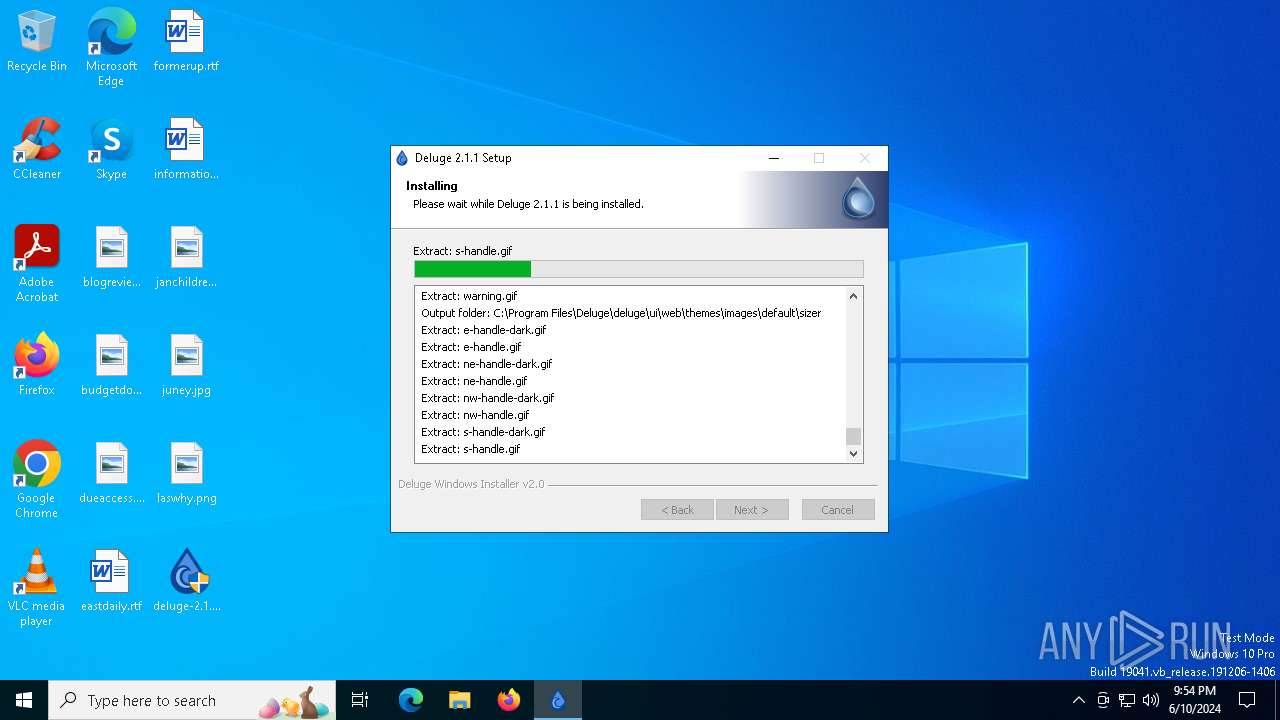
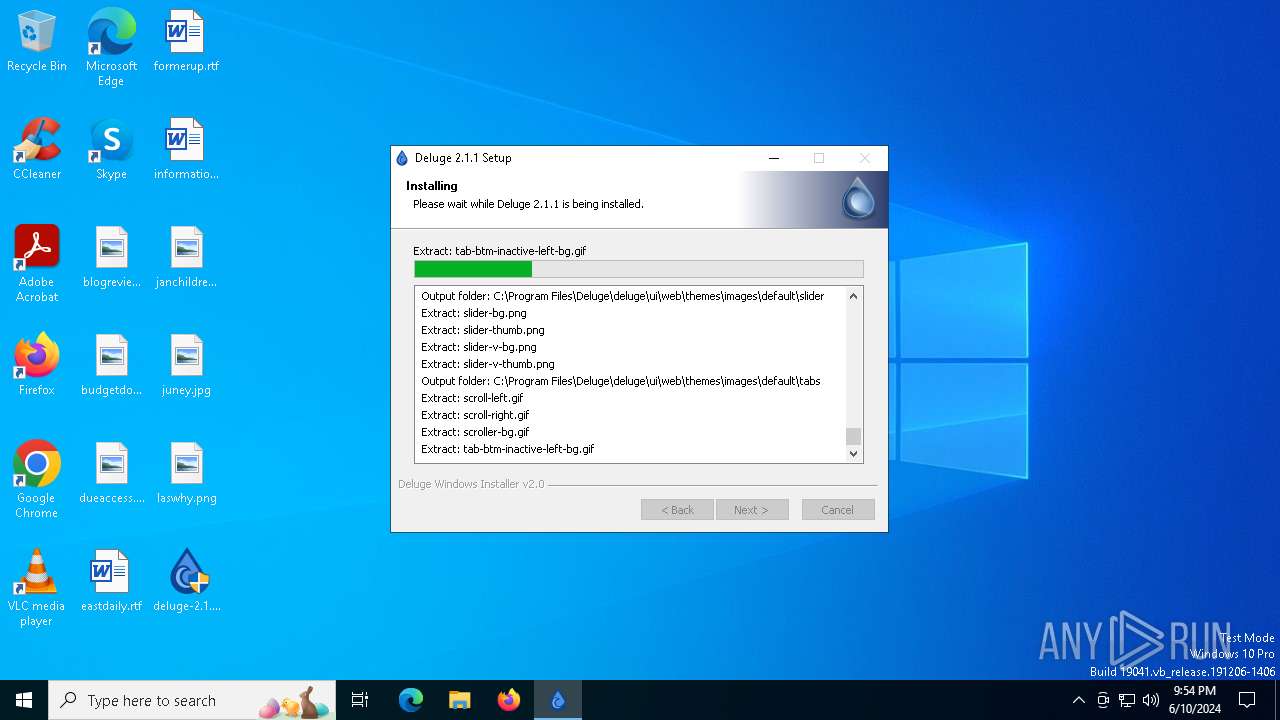
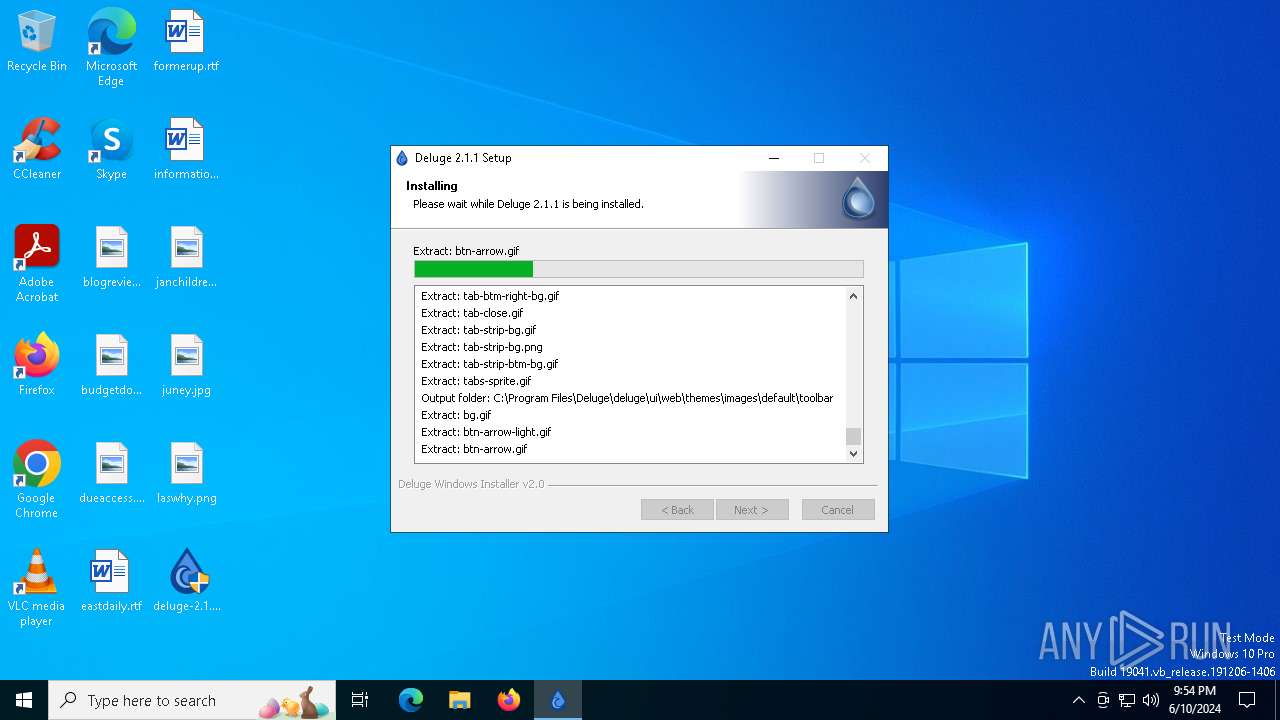
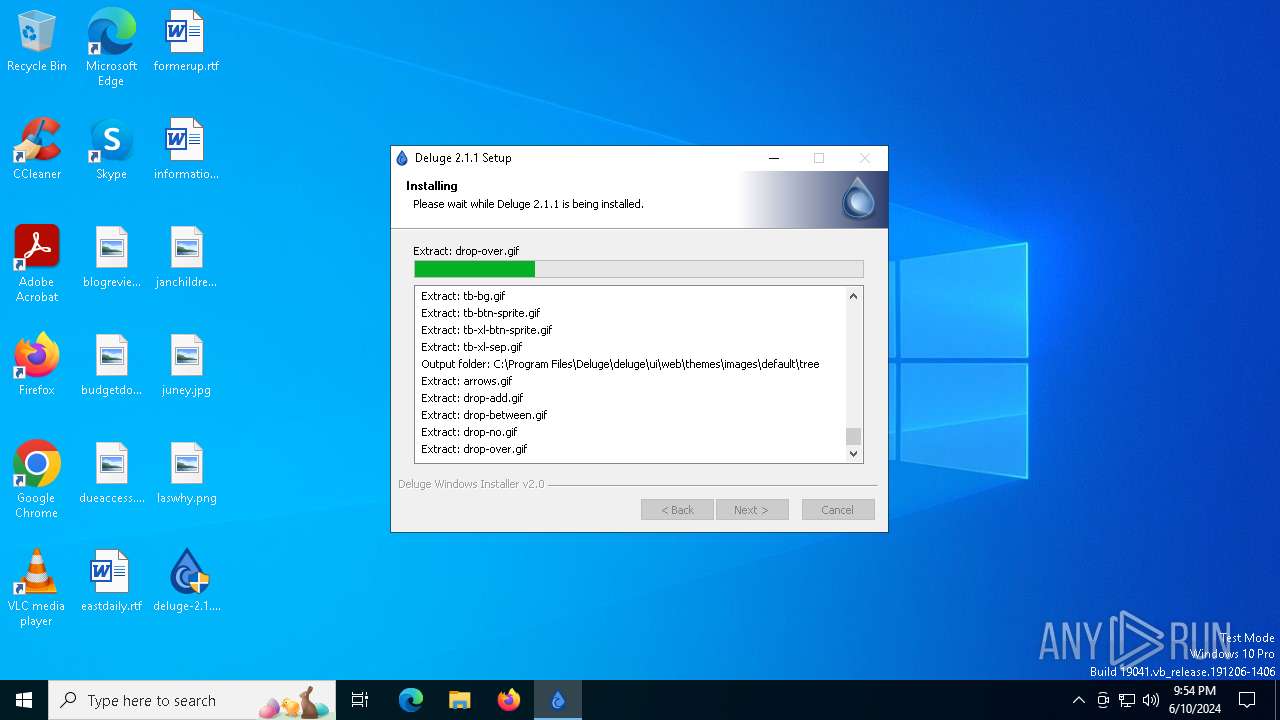
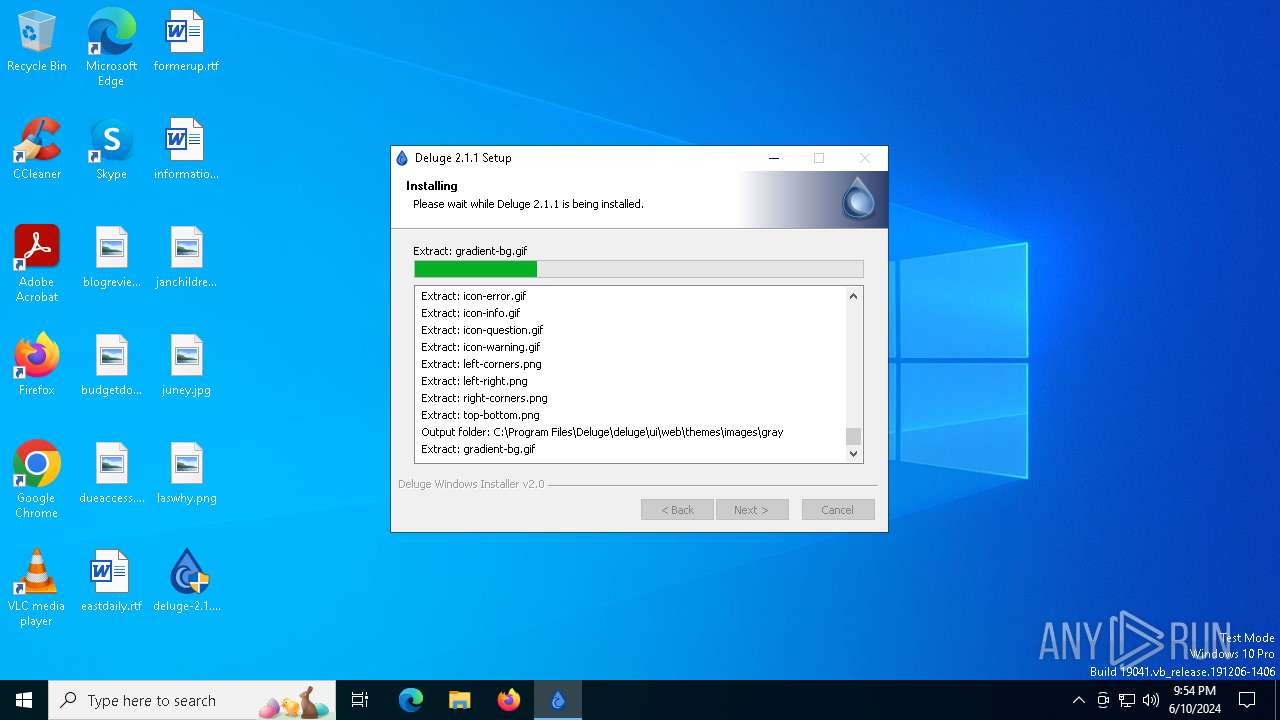
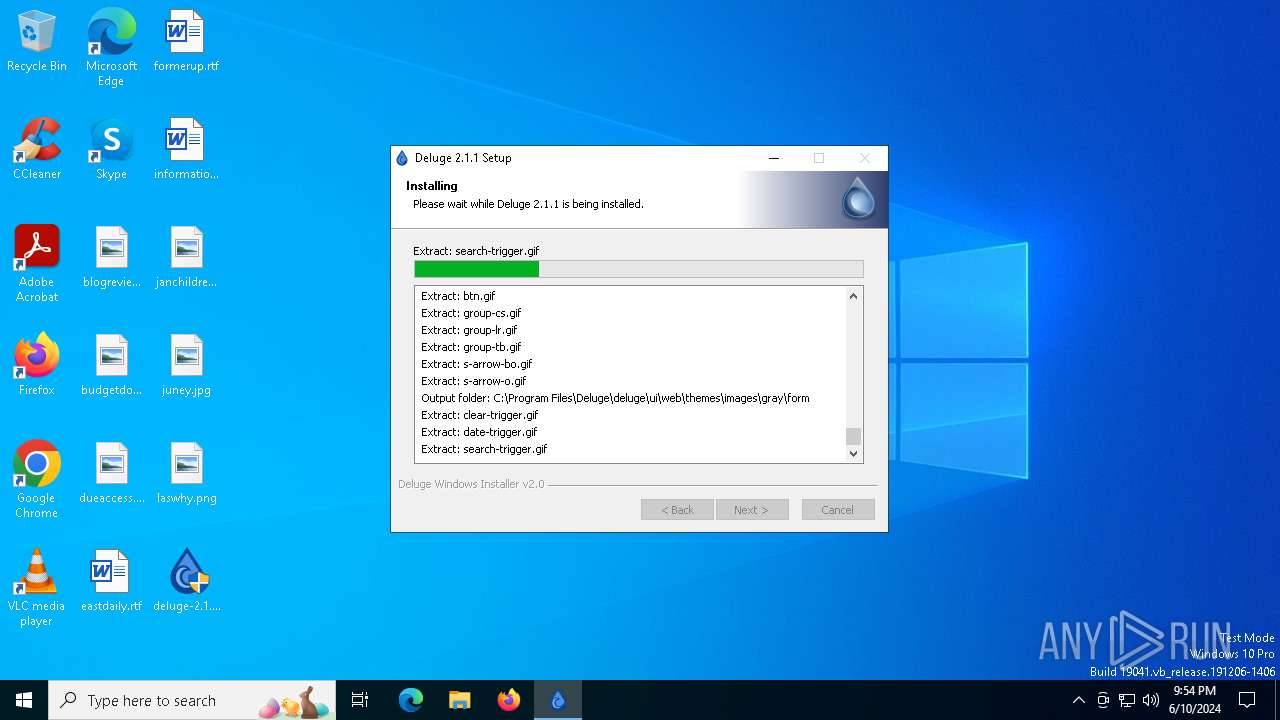
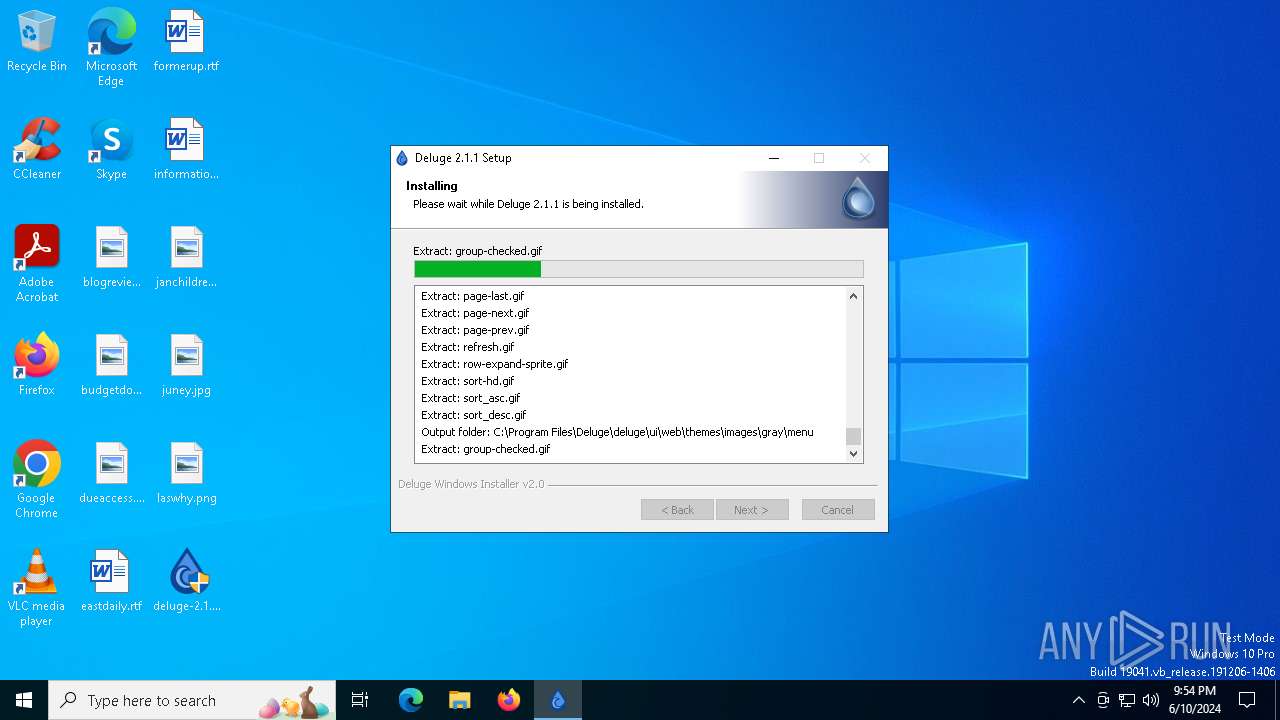
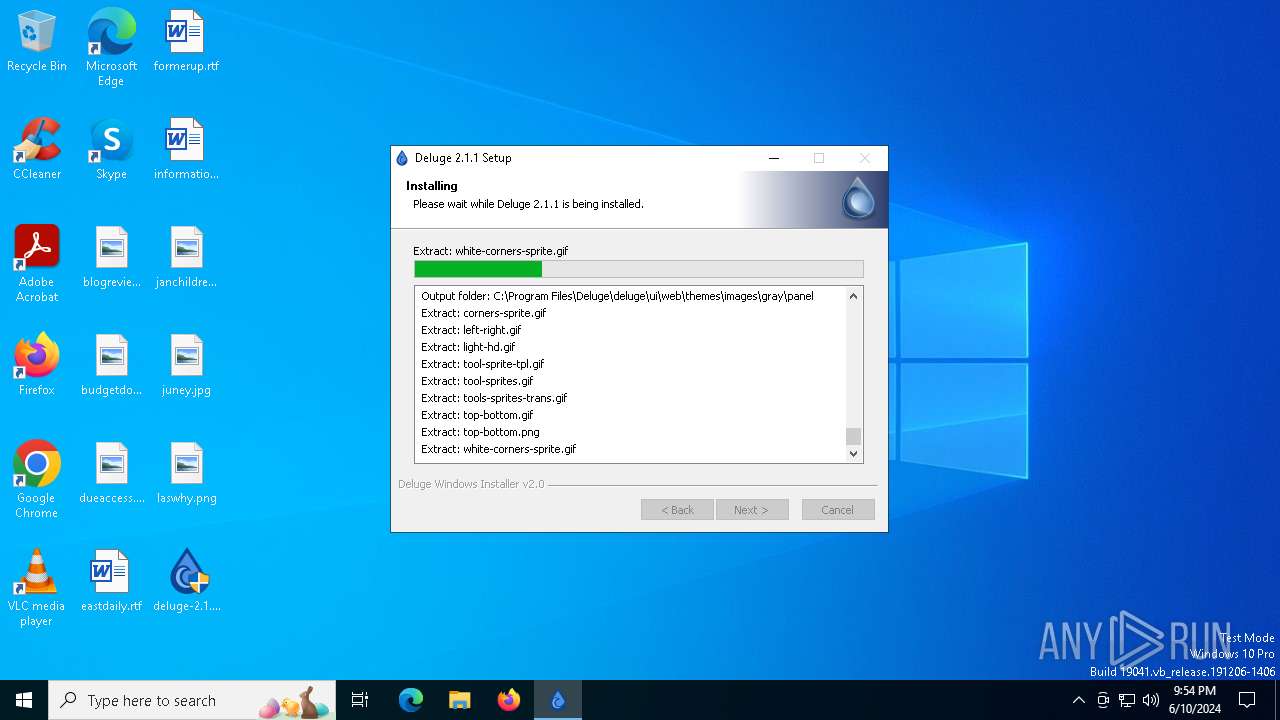
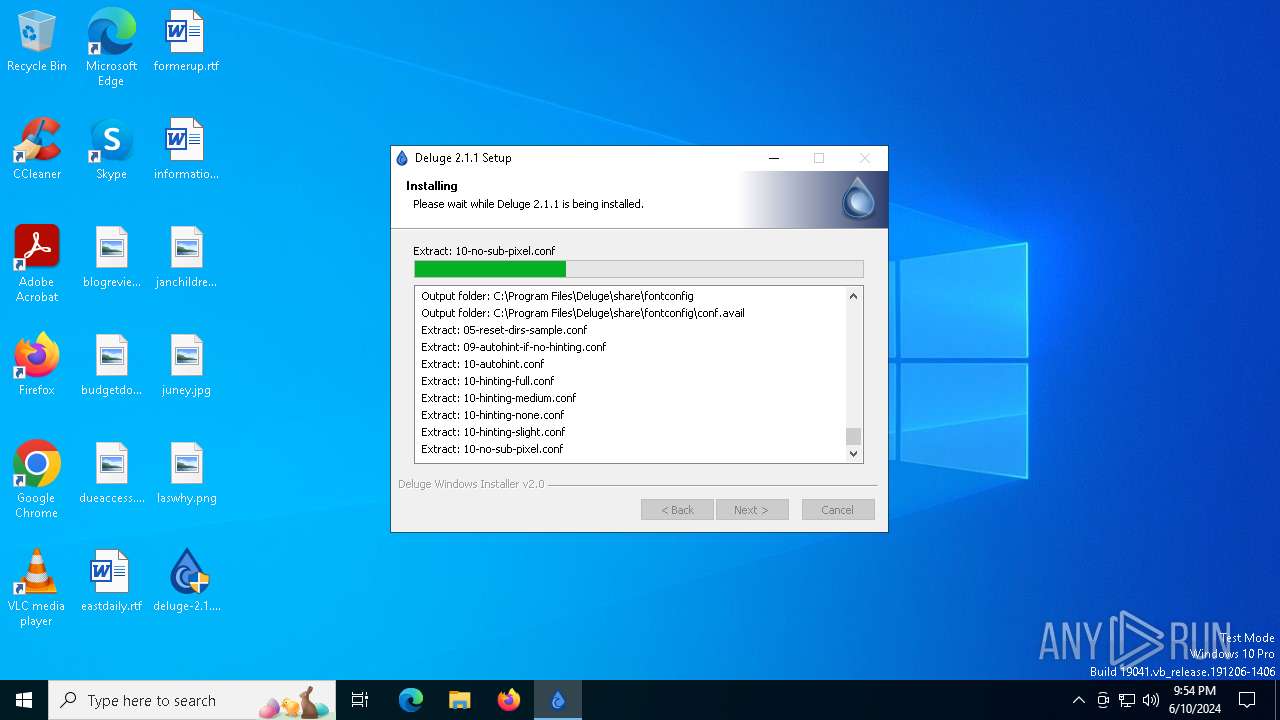
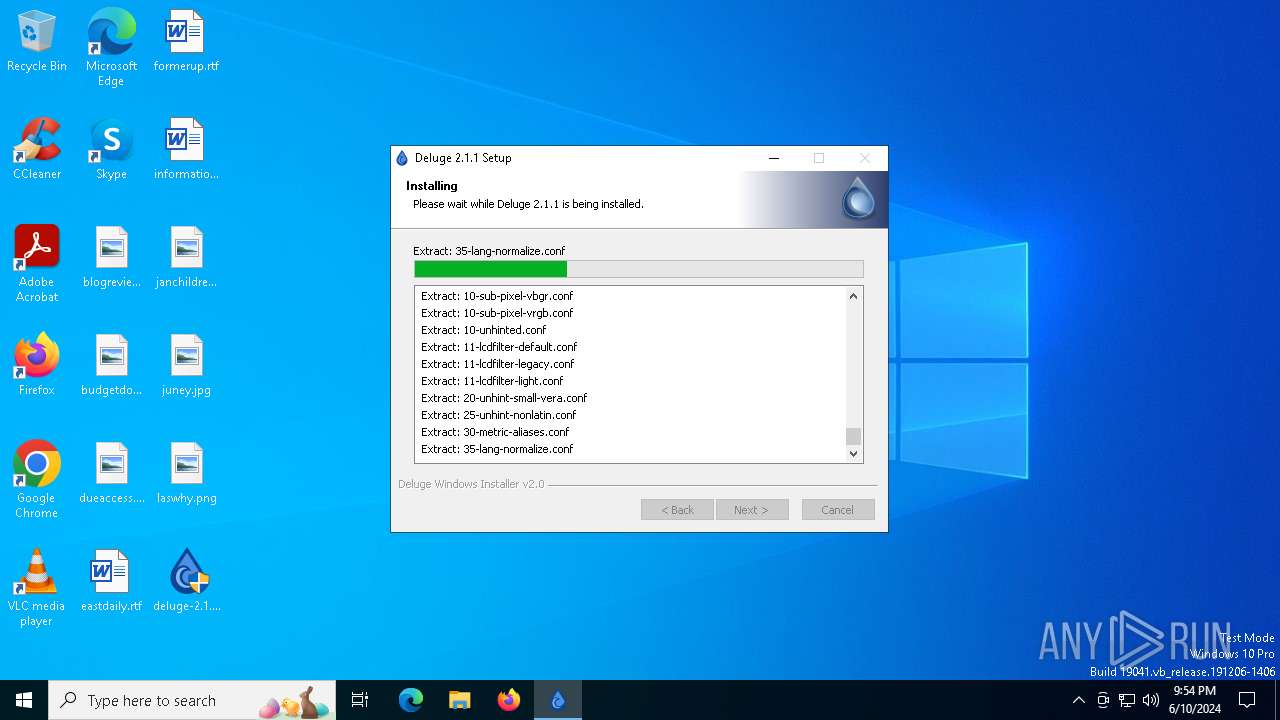
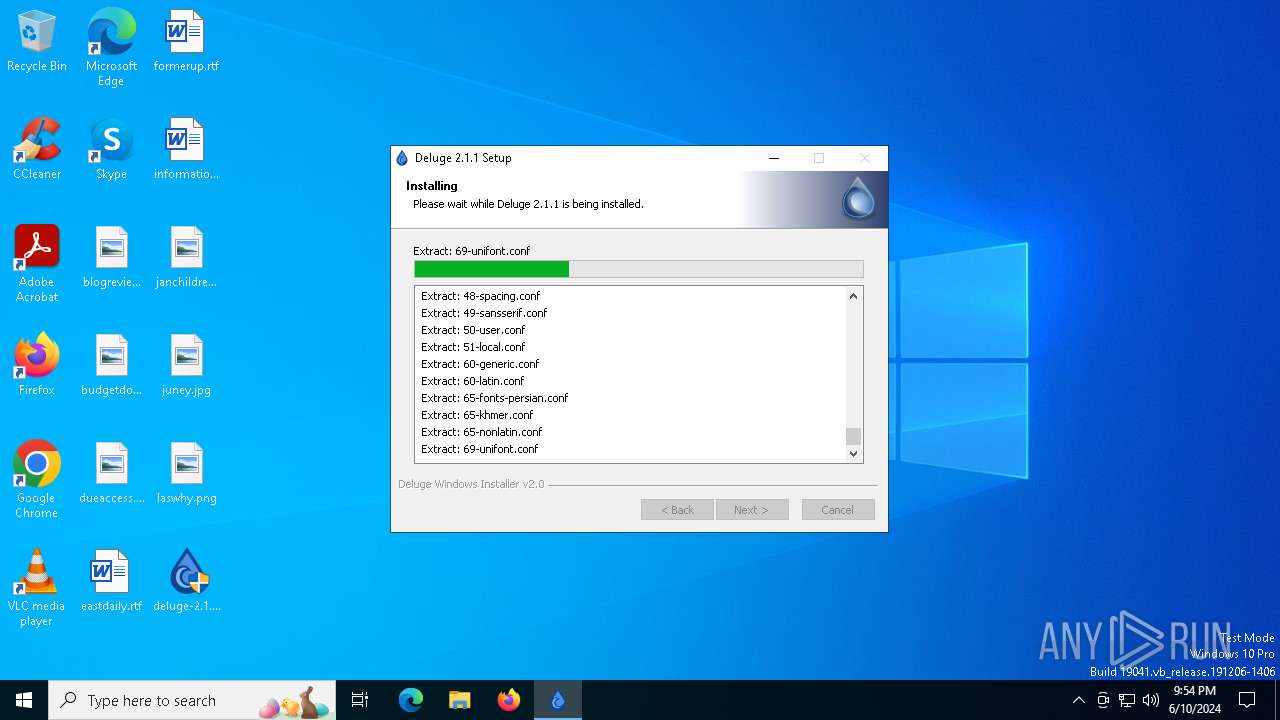
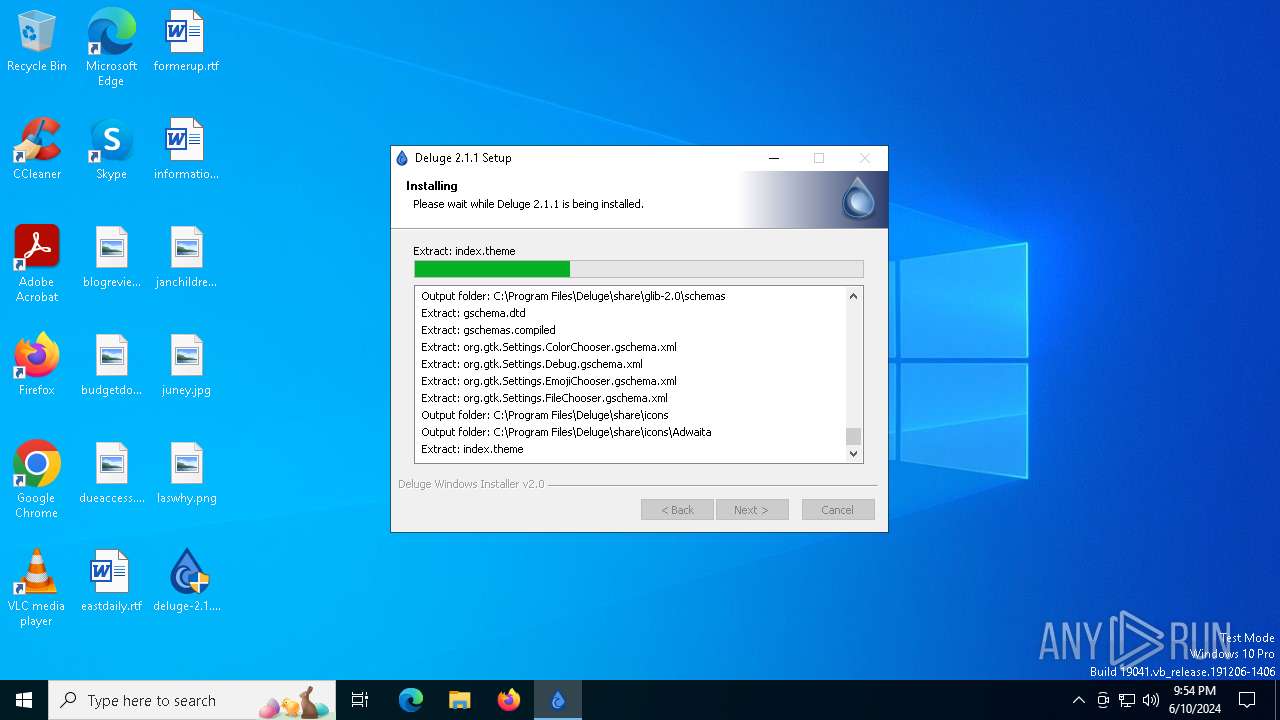
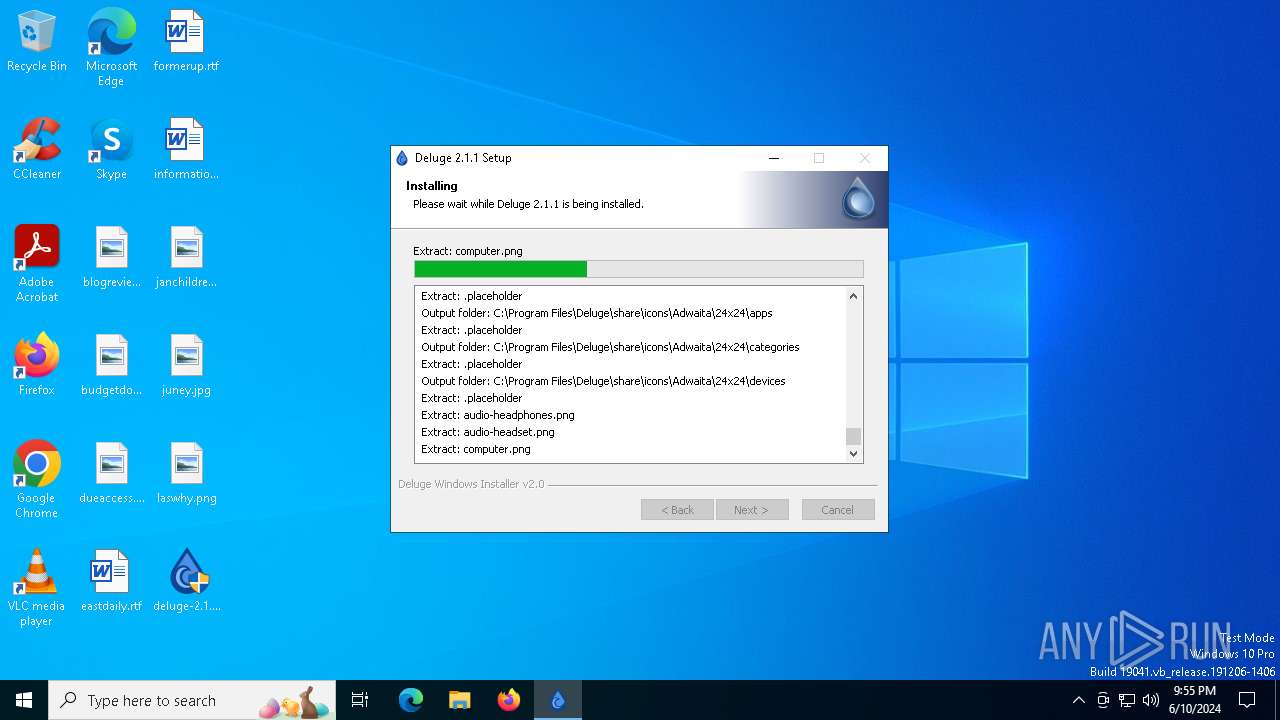
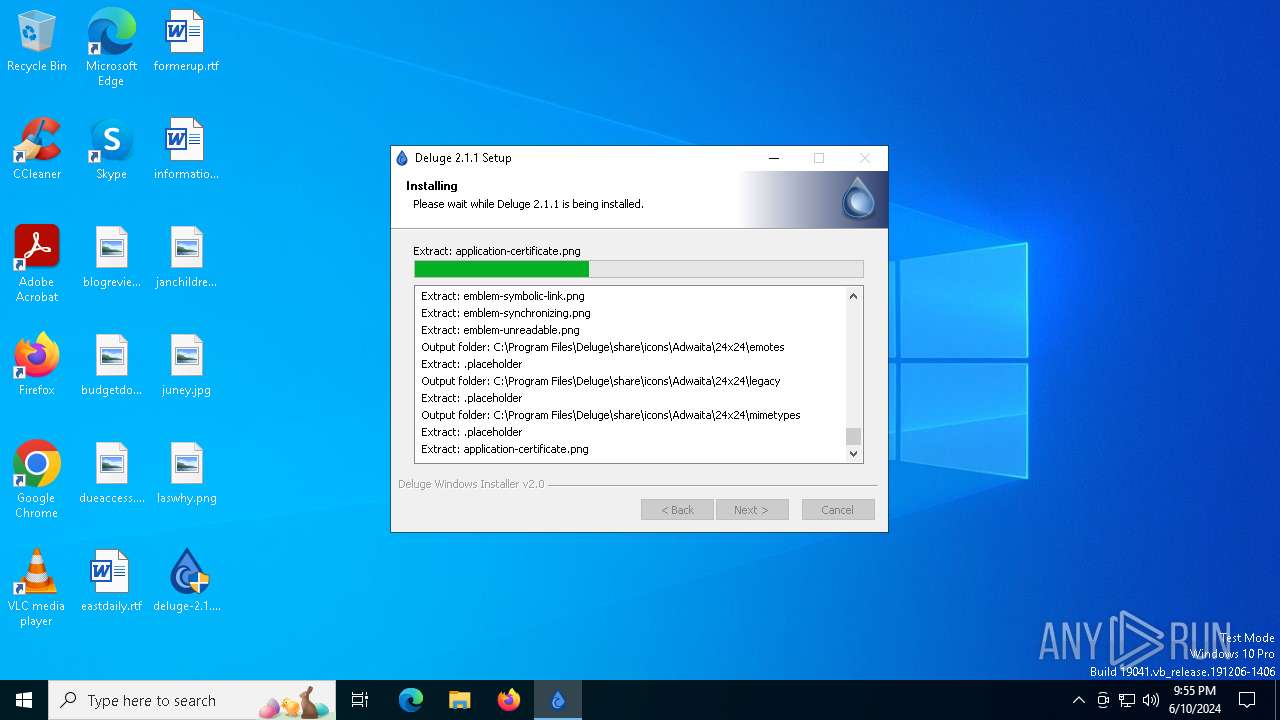
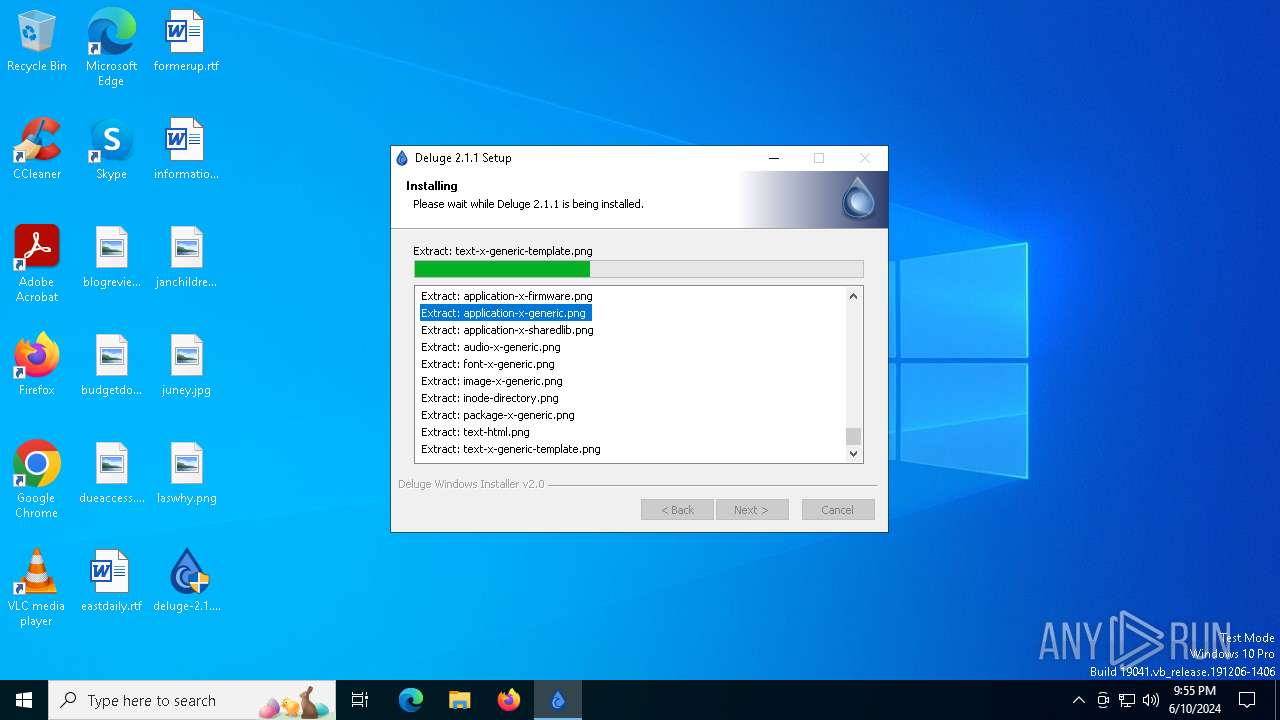
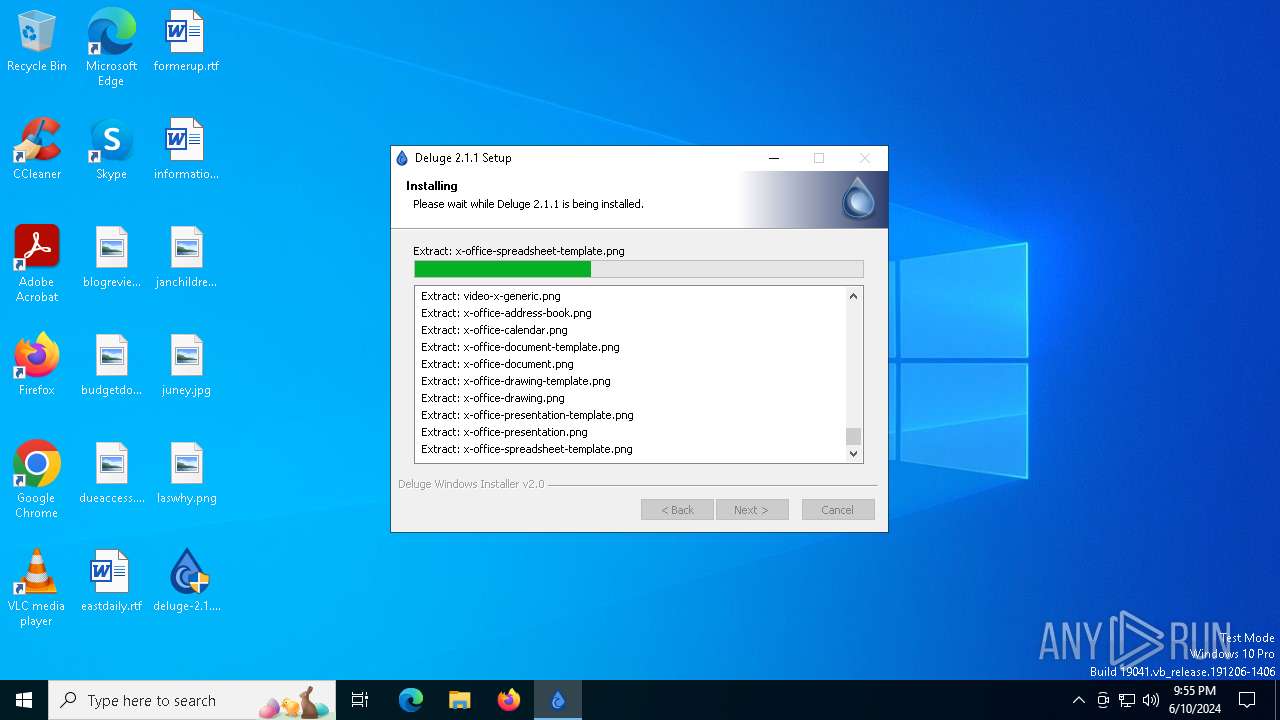
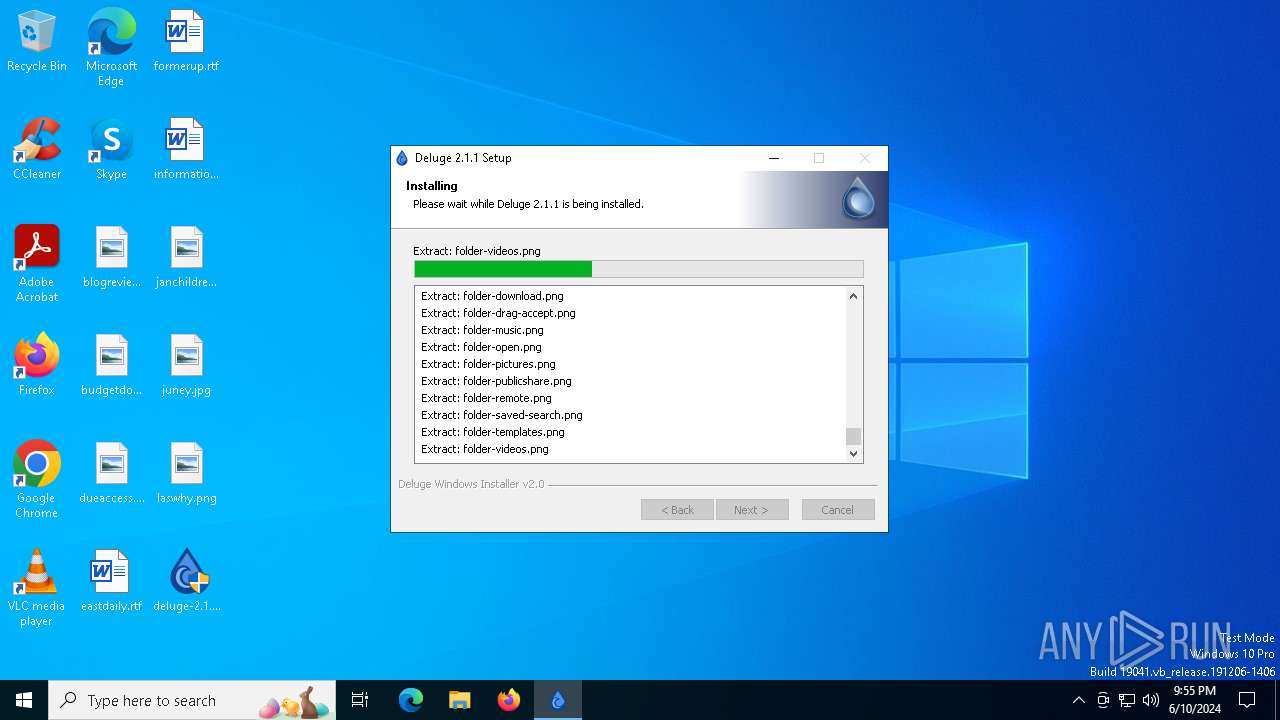
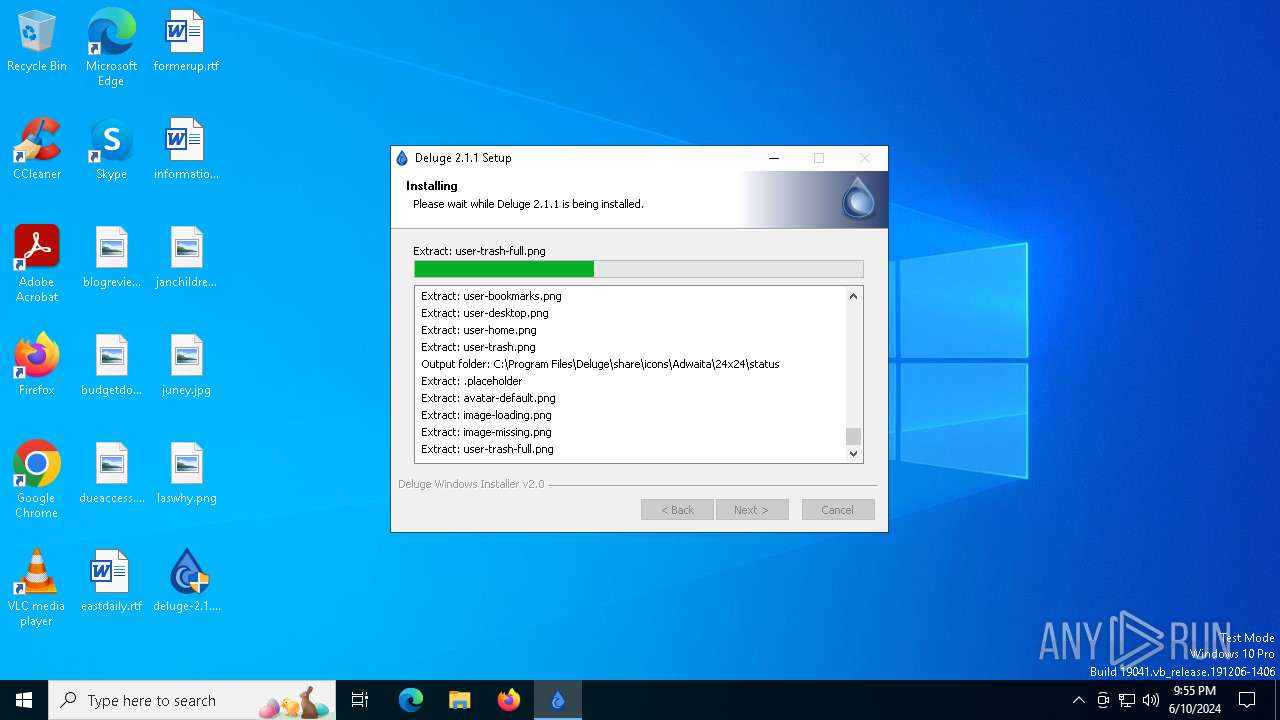
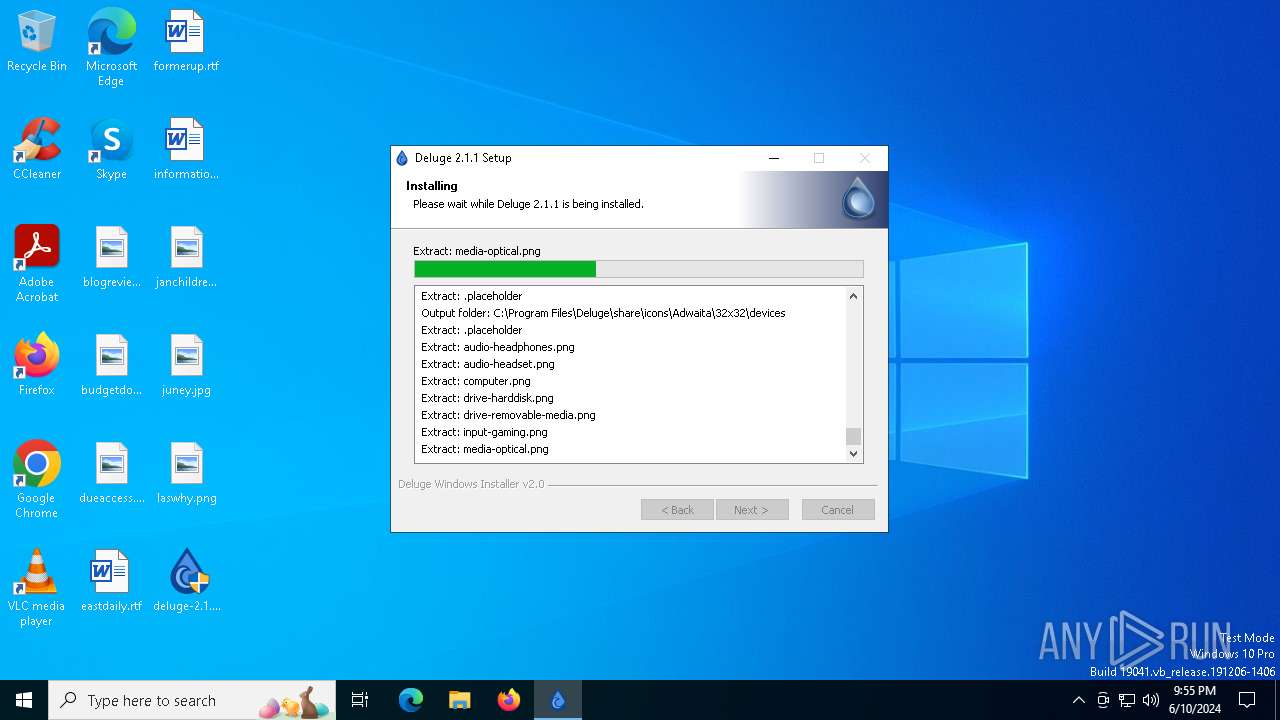
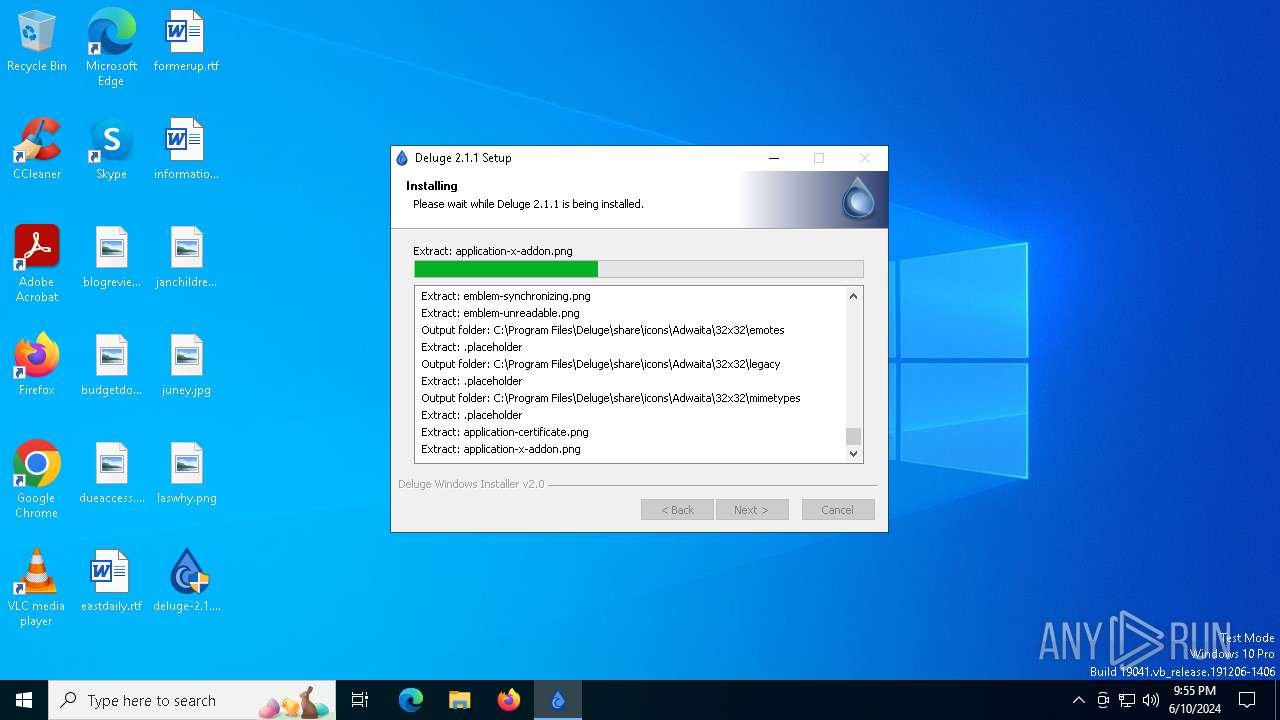
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6512 | "C:\Users\admin\Desktop\deluge-2.1.1-win64-setup.exe" | C:\Users\admin\Desktop\deluge-2.1.1-win64-setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Deluge Team Integrity Level: MEDIUM Description: Deluge Application Installer Exit code: 3221226540 Version: 2.0.0.0 Modules
| |||||||||||||||
| 6560 | "C:\Users\admin\Desktop\deluge-2.1.1-win64-setup.exe" | C:\Users\admin\Desktop\deluge-2.1.1-win64-setup.exe | explorer.exe | ||||||||||||
User: admin Company: Deluge Team Integrity Level: HIGH Description: Deluge Application Installer Version: 2.0.0.0 Modules
| |||||||||||||||
Total events
572
Read events
572
Write events
0
Delete events
0
Modification events
Executable files
205
Suspicious files
239
Text files
1 481
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6560 | deluge-2.1.1-win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsy707C.tmp\modern-header.bmp | image | |
MD5:92016B43B022594E035C13F84C9C8783 | SHA256:2EB485BB2731F23B04064571BA4F3B465F2FD1CF13CC5CDE13BA2C84BE6E68C8 | |||
| 6560 | deluge-2.1.1-win64-setup.exe | C:\Program Files\Deluge\_bz2.pyd | executable | |
MD5:B024A6F227EAFA8D43EDFC1A560FE651 | SHA256:C0DD9496B19BA9536A78A43A97704E7D4BEF3C901D196ED385E771366682819D | |||
| 6560 | deluge-2.1.1-win64-setup.exe | C:\Users\admin\AppData\Local\Temp\nsy707C.tmp\modern-wizard.bmp | image | |
MD5:33A41A56364A4ACD1D88153DDD4AF716 | SHA256:98D9C64CF6E0B137C78B09E65C46D688A2723F53570801AF766BBA16732157C8 | |||
| 6560 | deluge-2.1.1-win64-setup.exe | C:\Program Files\Deluge\SDL2.dll | executable | |
MD5:2F4A57E7A4FF7F6EE01BB07D77D89EBC | SHA256:F34CD90B131CEB45B7F32D41680A13FD4B13E5F48F0D1649CBF441833105310C | |||
| 6560 | deluge-2.1.1-win64-setup.exe | C:\Program Files\Deluge\SDL2_ttf.dll | executable | |
MD5:14E57C1868EFC1FB2E4787754E233364 | SHA256:507DC8A977D543B3E06BD3FCE41F5759D64B2B21AE829CD2EF41B77BF66968C4 | |||
| 6560 | deluge-2.1.1-win64-setup.exe | C:\Program Files\Deluge\SDL2_mixer.dll | executable | |
MD5:8668D84320ACEE48BC64D080DD66A403 | SHA256:900EEB69B67266946F541BC6DA5460E6CB9ED4F92816A1710A84625AD123808C | |||
| 6560 | deluge-2.1.1-win64-setup.exe | C:\Program Files\Deluge\SDL2_image.dll | executable | |
MD5:B8D249A5E394B4E6A954C557AF1B80E6 | SHA256:1E364AF75FEE0C83506FBDFD4D5B0E386C4E9C6A33DDBDDAC61DDB131E360194 | |||
| 6560 | deluge-2.1.1-win64-setup.exe | C:\Program Files\Deluge\VCRUNTIME140.dll | executable | |
MD5:F34EB034AA4A9735218686590CBA2E8B | SHA256:9D2B40F0395CC5D1B4D5EA17B84970C29971D448C37104676DB577586D4AD1B1 | |||
| 6560 | deluge-2.1.1-win64-setup.exe | C:\Program Files\Deluge\_asyncio.pyd | executable | |
MD5:A3F434F6CFD2F339876E7D345FE178FB | SHA256:102043B17C20043E4624F60E444131382363B69FF0E683C13FA17AF156766483 | |||
| 6560 | deluge-2.1.1-win64-setup.exe | C:\Program Files\Deluge\_ctypes.pyd | executable | |
MD5:A1E9B3CC6B942251568E59FD3C342205 | SHA256:A8703F949C9520B76CB1875D1176A23A2B3EF1D652D6DFAC6E1DE46DC08B2AA3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
18
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5140 | MoUsoCoreWorker.exe | GET | 200 | 23.72.36.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5548 | svchost.exe | GET | 200 | 23.72.36.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5548 | svchost.exe | GET | 200 | 23.40.146.45:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
— | — | POST | 200 | 40.79.173.41:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1984 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5548 | svchost.exe | 23.72.36.120:80 | crl.microsoft.com | Akamai International B.V. | IE | unknown |
5140 | MoUsoCoreWorker.exe | 23.72.36.120:80 | crl.microsoft.com | Akamai International B.V. | IE | unknown |
5548 | svchost.exe | 23.40.146.45:80 | www.microsoft.com | AKAMAI-AS | MX | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2908 | OfficeClickToRun.exe | 104.208.16.91:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |