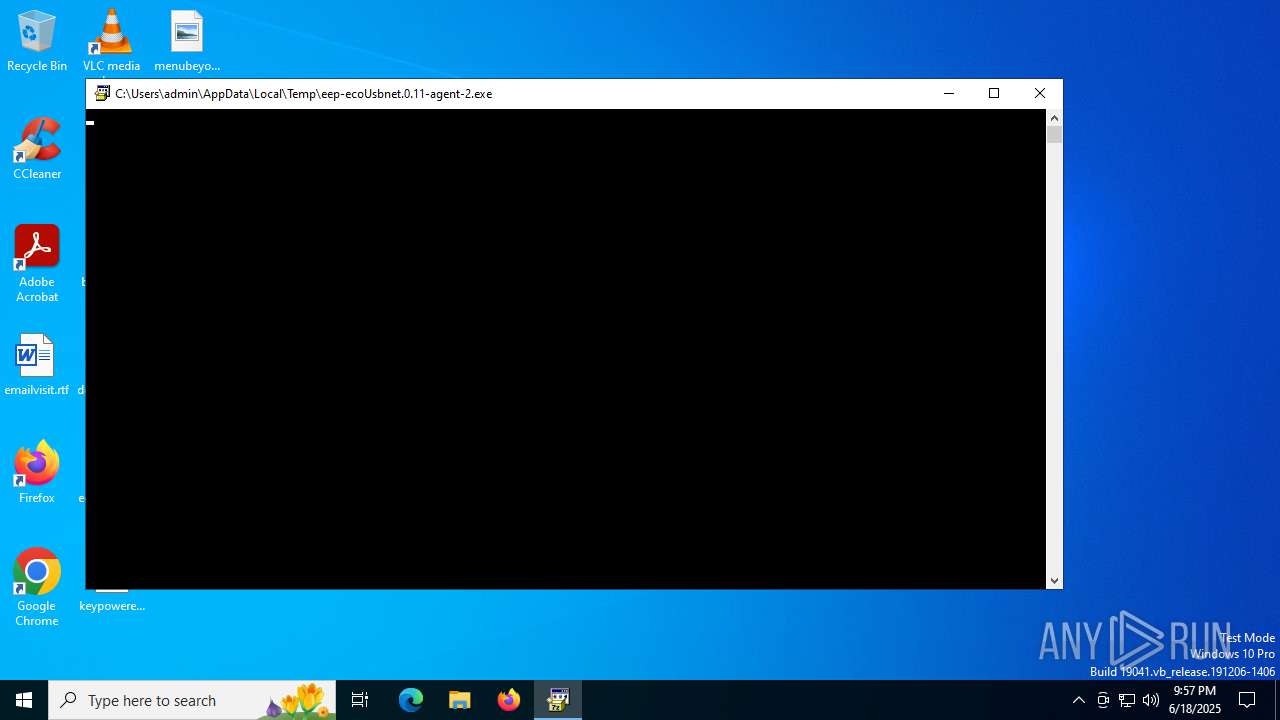
| File name: | eep-ecoUsbnet.0.11-agent-2.exe |
| Full analysis: | https://app.any.run/tasks/7ecdbee4-d3ca-4d59-a13c-d11a92f830a6 |
| Verdict: | Malicious activity |
| Analysis date: | June 18, 2025, 21:57:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 4 sections |
| MD5: | 2E3D76C7189549F502DAF330404CFD83 |
| SHA1: | 9C86C6B3A28F1E6AE5EEAA349206176675B241C8 |
| SHA256: | 183A572EE463BE33FF8A799DD1BDF80081251A666BDD5F84C669850433FA60C6 |
| SSDEEP: | 49152:+1wWm1HSRiMBdE/iWTh5FtX33FETTQurCgvkxPWwL3B8sO2k2yrciJE4AJlDUXTz:+1VwZudE6WT3UQuLvkgmmsO2kaUl0lIz |
MALICIOUS
No malicious indicators.SUSPICIOUS
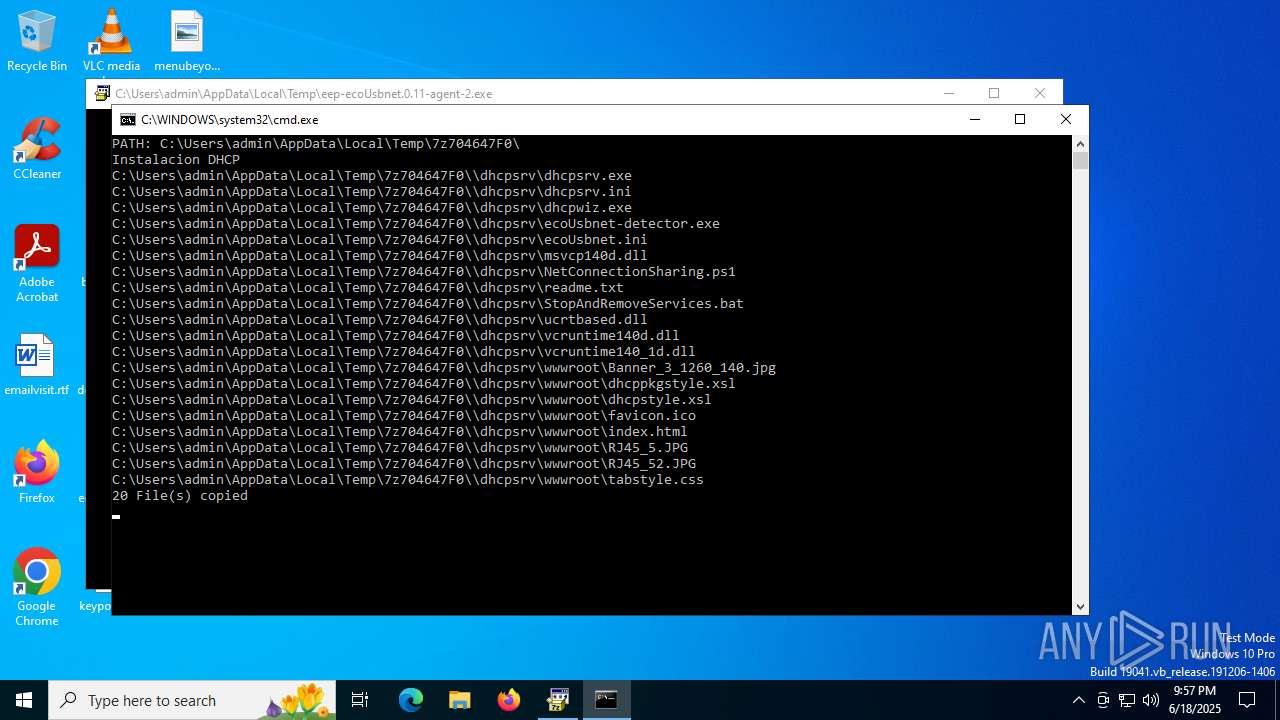
Drops 7-zip archiver for unpacking
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
Process drops legitimate windows executable
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
Reads security settings of Internet Explorer
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
- RD9700.sfx.exe (PID: 3588)
The process drops C-runtime libraries
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
- xcopy.exe (PID: 3932)
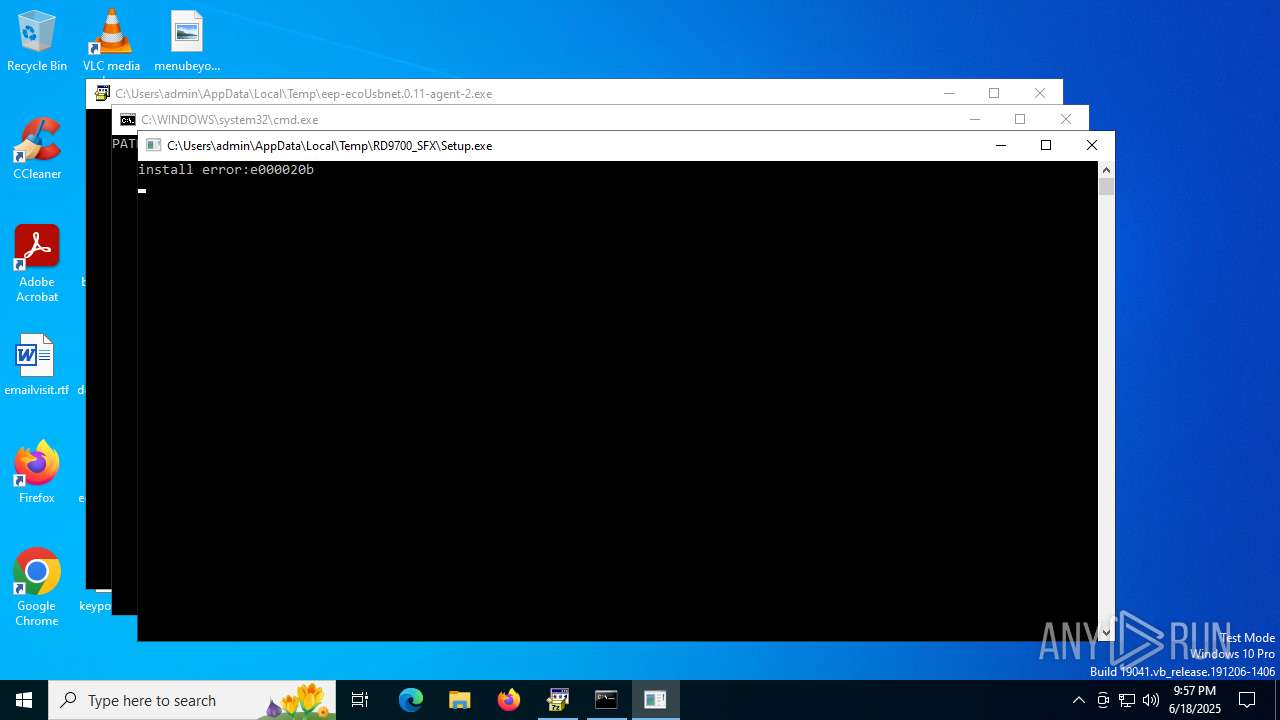
Executing commands from a ".bat" file
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
Starts CMD.EXE for commands execution
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
- cmd.exe (PID: 6320)
Executable content was dropped or overwritten
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
- RD9700.sfx.exe (PID: 3588)
- install.exe (PID: 4804)
- drvinst.exe (PID: 236)
- xcopy.exe (PID: 3932)
The executable file from the user directory is run by the CMD process
- RD9700.sfx.exe (PID: 3588)
Drops a system driver (possible attempt to evade defenses)
- RD9700.sfx.exe (PID: 3588)
- install.exe (PID: 4804)
- drvinst.exe (PID: 236)
Application launched itself
- cmd.exe (PID: 6320)
Creates files in the driver directory
- drvinst.exe (PID: 236)
Executes as Windows Service
- dhcpsrv.exe (PID: 3836)
- dhcpsrv.exe (PID: 2216)
- ecoUsbnet-detector.exe (PID: 3624)
Windows service management via SC.EXE
- sc.exe (PID: 4648)
- sc.exe (PID: 6980)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 6320)
Creates a new Windows service
- sc.exe (PID: 5764)
INFO
The sample compiled with english language support
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
- RD9700.sfx.exe (PID: 3588)
- install.exe (PID: 4804)
- drvinst.exe (PID: 236)
- xcopy.exe (PID: 3932)
Reads the computer name
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
- RD9700.sfx.exe (PID: 3588)
- install.exe (PID: 4804)
- drvinst.exe (PID: 236)
- dhcpsrv.exe (PID: 6388)
- dhcpsrv.exe (PID: 3836)
- dhcpsrv.exe (PID: 4836)
- dhcpsrv.exe (PID: 5620)
- dhcpsrv.exe (PID: 6344)
- dhcpsrv.exe (PID: 4968)
- dhcpsrv.exe (PID: 2216)
- ecoUsbnet-detector.exe (PID: 3624)
The sample compiled with russian language support
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
Process checks computer location settings
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
- RD9700.sfx.exe (PID: 3588)
Checks supported languages
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
- RD9700.sfx.exe (PID: 3588)
- Setup.exe (PID: 5400)
- install.exe (PID: 4804)
- drvinst.exe (PID: 236)
- dhcpsrv.exe (PID: 5620)
- dhcpsrv.exe (PID: 6388)
- dhcpsrv.exe (PID: 4836)
- dhcpsrv.exe (PID: 3836)
- dhcpsrv.exe (PID: 6344)
- dhcpsrv.exe (PID: 4968)
- dhcpsrv.exe (PID: 2216)
- ecoUsbnet-detector.exe (PID: 3624)
Create files in a temporary directory
- eep-ecoUsbnet.0.11-agent-2.exe (PID: 2032)
- RD9700.sfx.exe (PID: 3588)
- install.exe (PID: 4804)
Reads the machine GUID from the registry
- drvinst.exe (PID: 236)
Reads the software policy settings
- drvinst.exe (PID: 236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:11:18 18:41:51+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 22016 |
| InitializedDataSize: | 13312 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x644f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 9.20.0.0 |
| ProductVersionNumber: | 9.20.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Igor Pavlov |
| FileDescription: | 7z Setup SFX small |
| FileVersion: | 9.2 |
| InternalName: | 7zS2.sfx |
| LegalCopyright: | Copyright (c) 1999-2010 Igor Pavlov |
| OriginalFileName: | 7zS2.sfx.exe |
| ProductName: | 7-Zip |
| ProductVersion: | 9.2 |
Total processes
162
Monitored processes
25
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{4f8d759d-ff0f-7340-8d83-359b168891ef}\USB_Ethernet_Adaptor.inf" "9" "42361ddcb" "00000000000001D0" "WinSta0\Default" "00000000000001E0" "208" "C:\Users\admin\AppData\Local\Temp\RD9700_SFX\files\ABOVE_XP_64" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 724 | reg ADD HKEY_LOCAL_MACHINE\Software\Microsoft\Windows\CurrentVersion\SharedAccess /v EnableRebootPersistConnection /t REG_DWORD /d 1 /f | C:\Windows\SysWOW64\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\Users\admin\AppData\Local\Temp\eep-ecoUsbnet.0.11-agent-2.exe" | C:\Users\admin\AppData\Local\Temp\eep-ecoUsbnet.0.11-agent-2.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z Setup SFX small Exit code: 3221226540 Version: 9.20 Modules
| |||||||||||||||
| 2032 | "C:\Users\admin\AppData\Local\Temp\eep-ecoUsbnet.0.11-agent-2.exe" | C:\Users\admin\AppData\Local\Temp\eep-ecoUsbnet.0.11-agent-2.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Setup SFX small Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 2216 | "C:\dhcpsrv\dhcpsrv.exe" -service | C:\dhcpsrv\dhcpsrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Uwe A. Ruttkamp Integrity Level: SYSTEM Description: DHCP Server for Windows Version: V2.9.3.0 Modules
| |||||||||||||||
| 2464 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3588 | C:\Users\admin\AppData\Local\Temp\7z704647F0\drivers\rd9700\RD9700.sfx.exe | C:\Users\admin\AppData\Local\Temp\7z704647F0\drivers\rd9700\RD9700.sfx.exe | cmd.exe | ||||||||||||
User: admin Company: CoreChip Integrity Level: HIGH Description: USB Etherent Driver Install Exit code: 0 Version: 1.5.0 Modules
| |||||||||||||||
| 3624 | \dhcpsrv\ecoUsbnet-detector.exe | C:\dhcpsrv\ecoUsbnet-detector.exe | — | services.exe | |||||||||||
User: SYSTEM Company: ecoprintQ Chile Integrity Level: SYSTEM Description: ecoUsbnet-detector Version: 1.0.7.0 Modules
| |||||||||||||||
| 3836 | "C:\dhcpsrv\dhcpsrv.exe" -service | C:\dhcpsrv\dhcpsrv.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Uwe A. Ruttkamp Integrity Level: SYSTEM Description: DHCP Server for Windows Exit code: 0 Version: V2.9.3.0 Modules
| |||||||||||||||
Total events
6 110
Read events
6 107
Write events
3
Delete events
0
Modification events
| (PID) Process: | (4804) install.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (6128) reg.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\Tcpip\Parameters |
| Operation: | write | Name: | IPEnableRouter |
Value: 1 | |||
| (PID) Process: | (724) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\SharedAccess |
| Operation: | write | Name: | EnableRebootPersistConnection |
Value: 1 | |||
Executable files
24
Suspicious files
7
Text files
32
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2032 | eep-ecoUsbnet.0.11-agent-2.exe | C:\Users\admin\AppData\Local\Temp\7z704647F0\Red.bat | text | |
MD5:88997A797642B32DDE67EF0030AA1D5C | SHA256:9D0A07E18D511991C74E4CCD63A3E7DA34A9F0EAD85E6E2941C11A721191A82A | |||
| 2032 | eep-ecoUsbnet.0.11-agent-2.exe | C:\Users\admin\AppData\Local\Temp\7z704647F0\dhcpsrv\NetConnectionSharing.ps1 | text | |
MD5:14B56E162B29F3C8E7A8AB38F2482C60 | SHA256:B61A7A7A7DBA212D243D6CB106639768E790E7189ACBA15C837362E24D7CF624 | |||
| 2032 | eep-ecoUsbnet.0.11-agent-2.exe | C:\Users\admin\AppData\Local\Temp\7z704647F0\dhcpsrv\wwwroot\RJ45_5.JPG | image | |
MD5:85927D0A2601B1D2CCBE10C4625EE238 | SHA256:F45A9A600DABAA93EA7333FBAD828F78D98E72DF433848E6C42629093C545839 | |||
| 2032 | eep-ecoUsbnet.0.11-agent-2.exe | C:\Users\admin\AppData\Local\Temp\7z704647F0\dhcpsrv\StopAndRemoveServices.bat | text | |
MD5:45C58D50106F33F43A9AD02E13F70A19 | SHA256:F65CDC5AB596727B76C56F392FBA5D9E2E73340E45BEF529684E522A49C6F3EA | |||
| 2032 | eep-ecoUsbnet.0.11-agent-2.exe | C:\Users\admin\AppData\Local\Temp\7z704647F0\script_7z.txt | text | |
MD5:59D8E5C586E9D9D55BD0D846AF6D0595 | SHA256:732B6684D56FD93629955BC3F720EAF072BECA4F0A02A38678779AE9D613B7B5 | |||
| 2032 | eep-ecoUsbnet.0.11-agent-2.exe | C:\Users\admin\AppData\Local\Temp\7z704647F0\Install.bat | text | |
MD5:D6E83D88403904477230481F187BD2CD | SHA256:889A5D870408E4C23AC8955EB2C6B3B42F21FDD3FD17824ADDCDD05A0152DB78 | |||
| 2032 | eep-ecoUsbnet.0.11-agent-2.exe | C:\Users\admin\AppData\Local\Temp\7z704647F0\dhcpsrv\wwwroot\index.html | html | |
MD5:2A13F54A35C0B4EEC590F2C633637F96 | SHA256:C9A2DE7EBD14366EA64F9F8D233F60BDAA0EA1D66B3C52966FB4FC1FFD36B67E | |||
| 2032 | eep-ecoUsbnet.0.11-agent-2.exe | C:\Users\admin\AppData\Local\Temp\7z704647F0\dhcpsrv\ecoUsbnet-detector.exe | executable | |
MD5:CC170A6156CBD0A635BC2DE5200461AF | SHA256:3626FB004D16967E78CAE5E42D73FAF43151936FBC8F22D9BD8A28EFAC2E3E8F | |||
| 2032 | eep-ecoUsbnet.0.11-agent-2.exe | C:\Users\admin\AppData\Local\Temp\7z704647F0\dhcpsrv\dhcpsrv.ini | text | |
MD5:C7F46E39D31DDA6D88CB09ED8B8B6A24 | SHA256:17D99C2EBF35F0357EB6BC6E121C93888EE01BDC43EFA1B1AF2C84F8EA2BD2B3 | |||
| 2032 | eep-ecoUsbnet.0.11-agent-2.exe | C:\Users\admin\AppData\Local\Temp\7z704647F0\drivers\rd9700\RD9700.sfx.exe | executable | |
MD5:780D595DAB2213DBEC99094C4B914369 | SHA256:4A68212AB37A19A19125B50F1FEDD58E91B999ED907BA7AED907EE02D0C483A4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
20
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2632 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6224 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.25.51.59:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6224 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5116 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2632 | svchost.exe | 40.126.32.76:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2632 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 184.25.51.59:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |