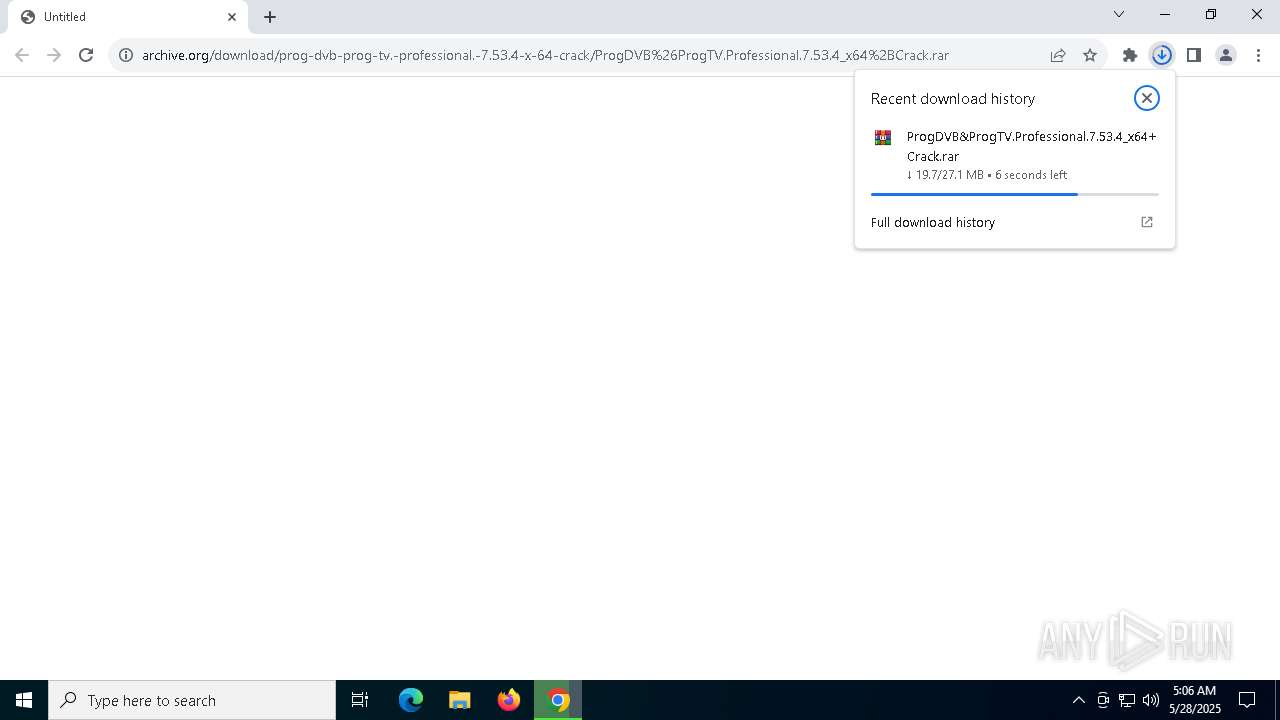
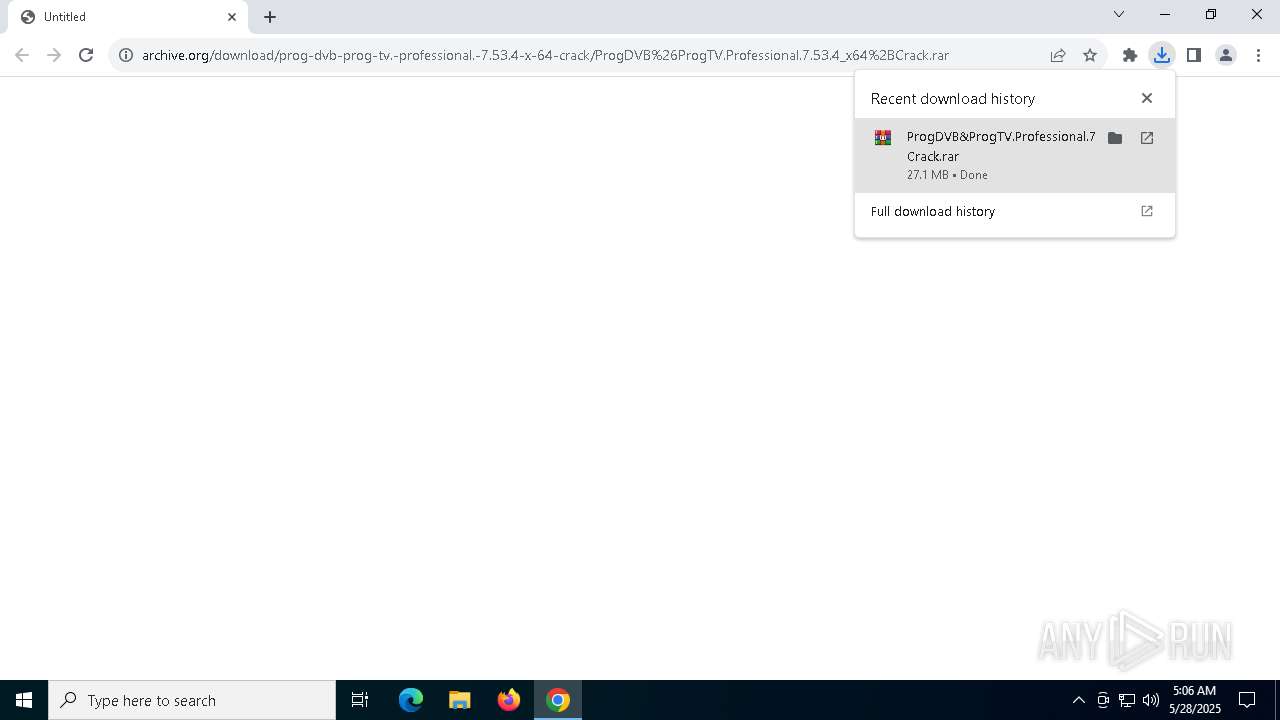
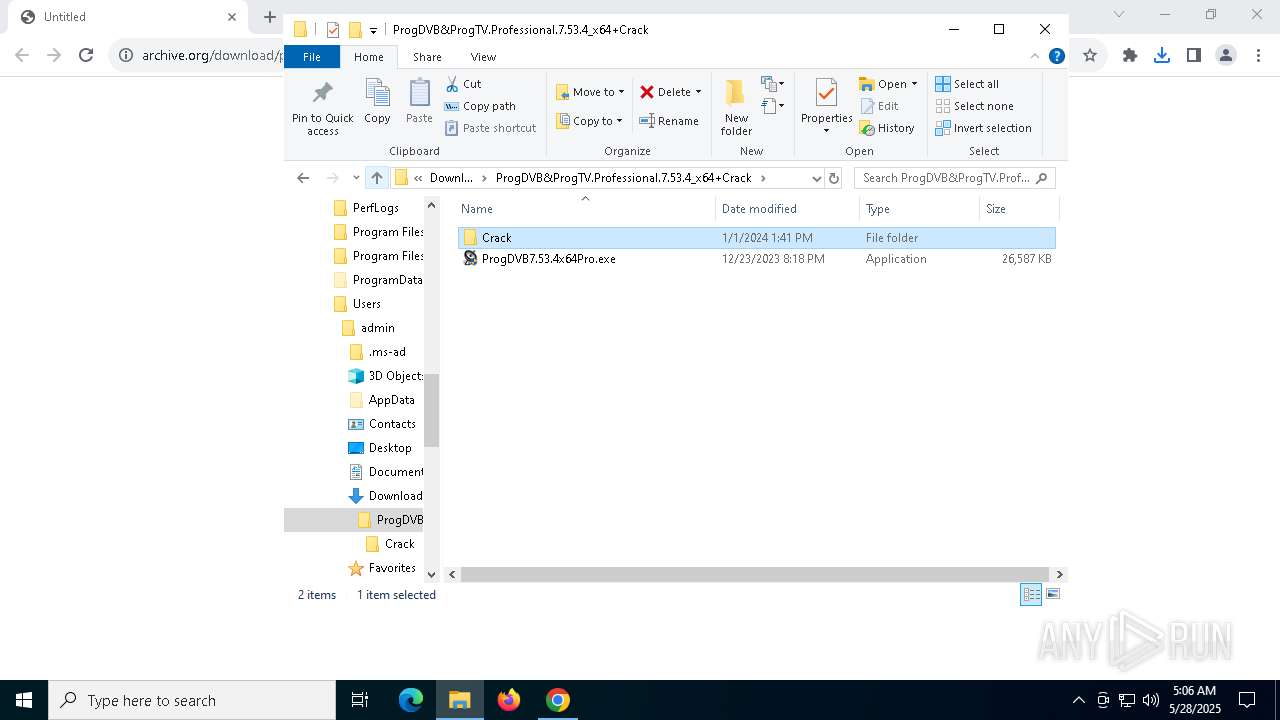
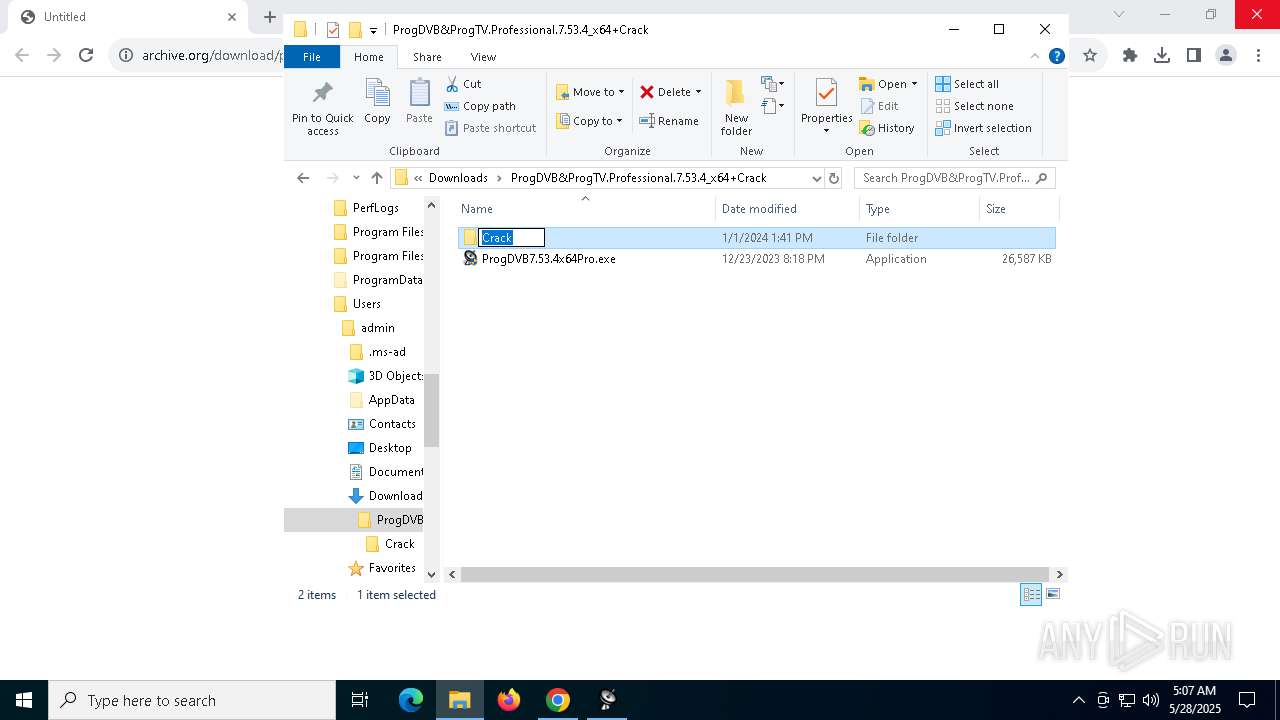
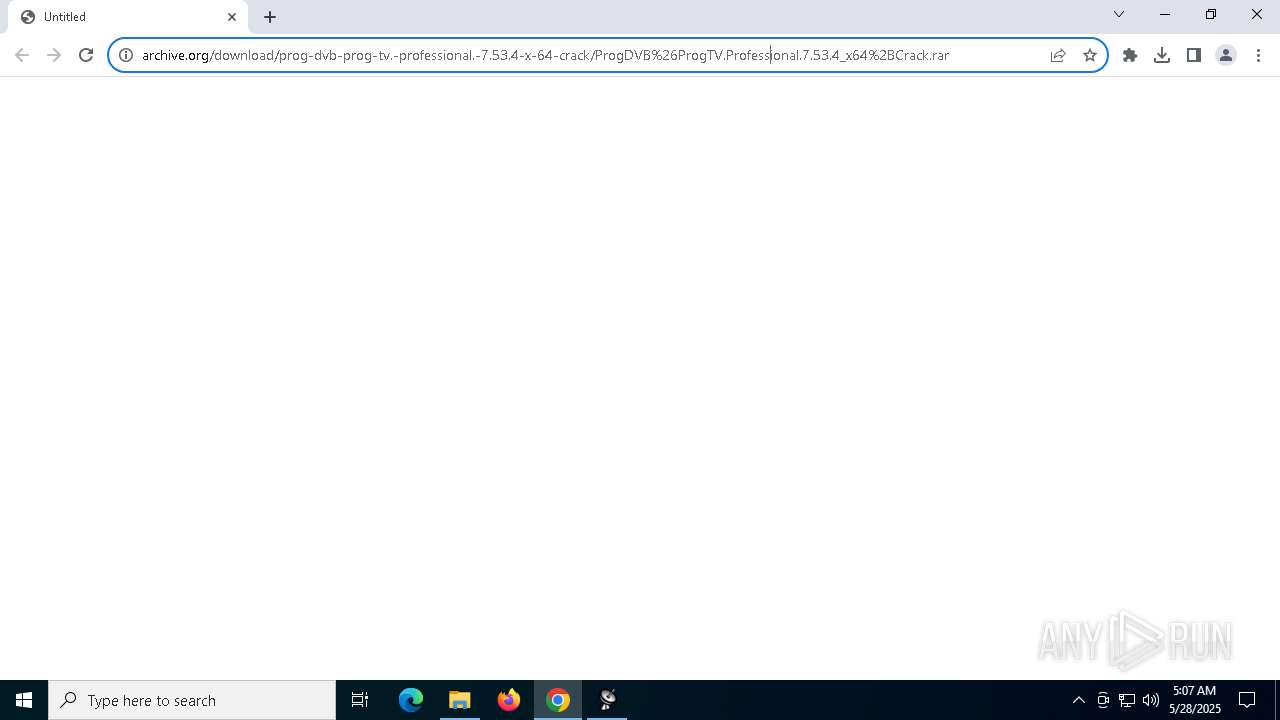
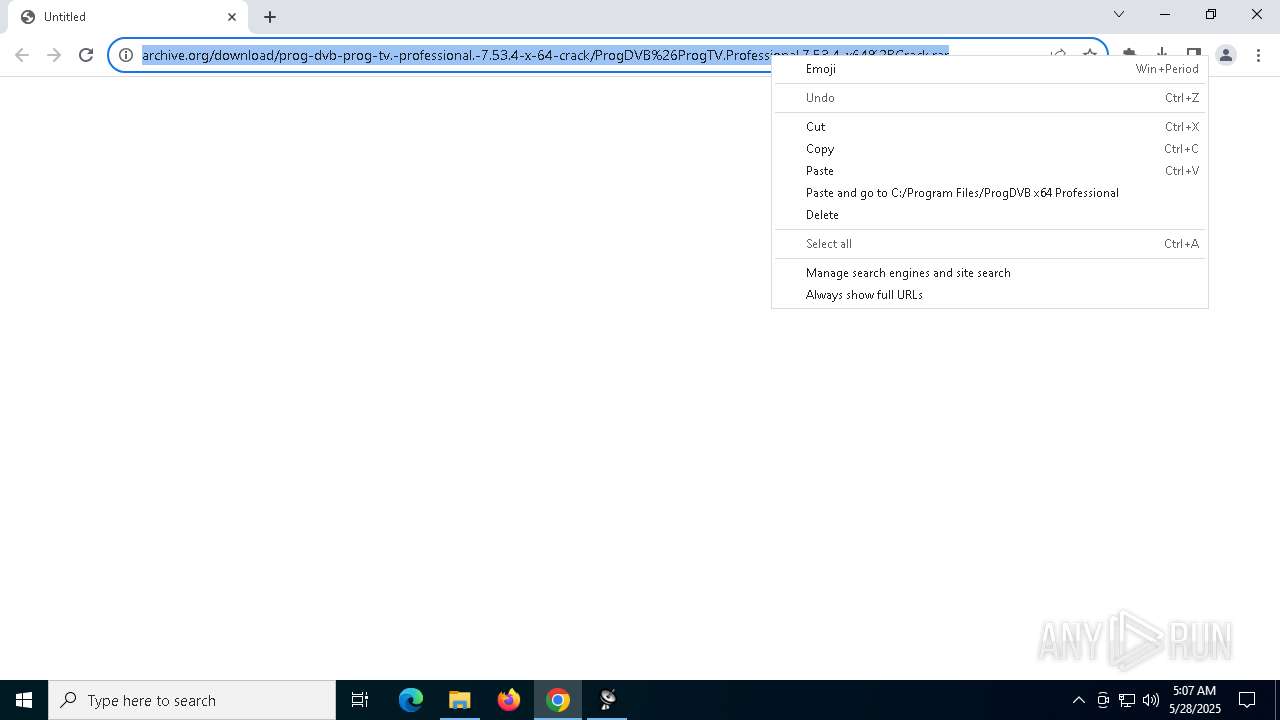
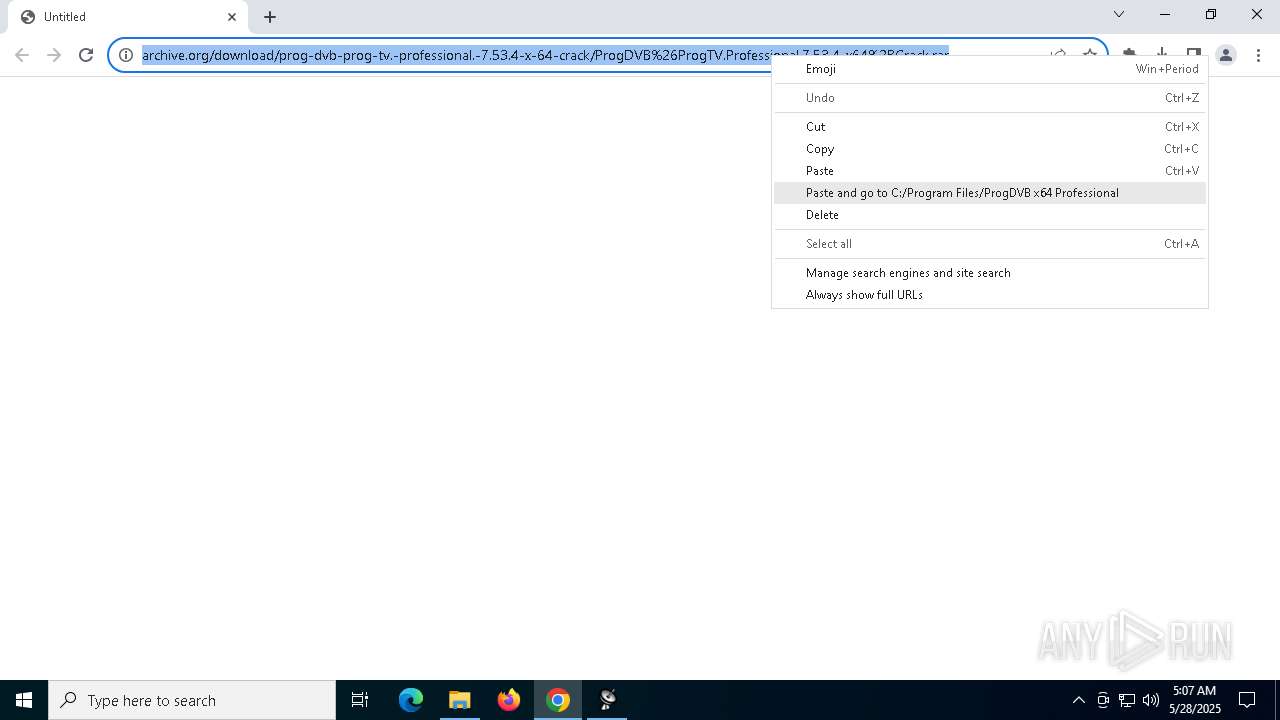
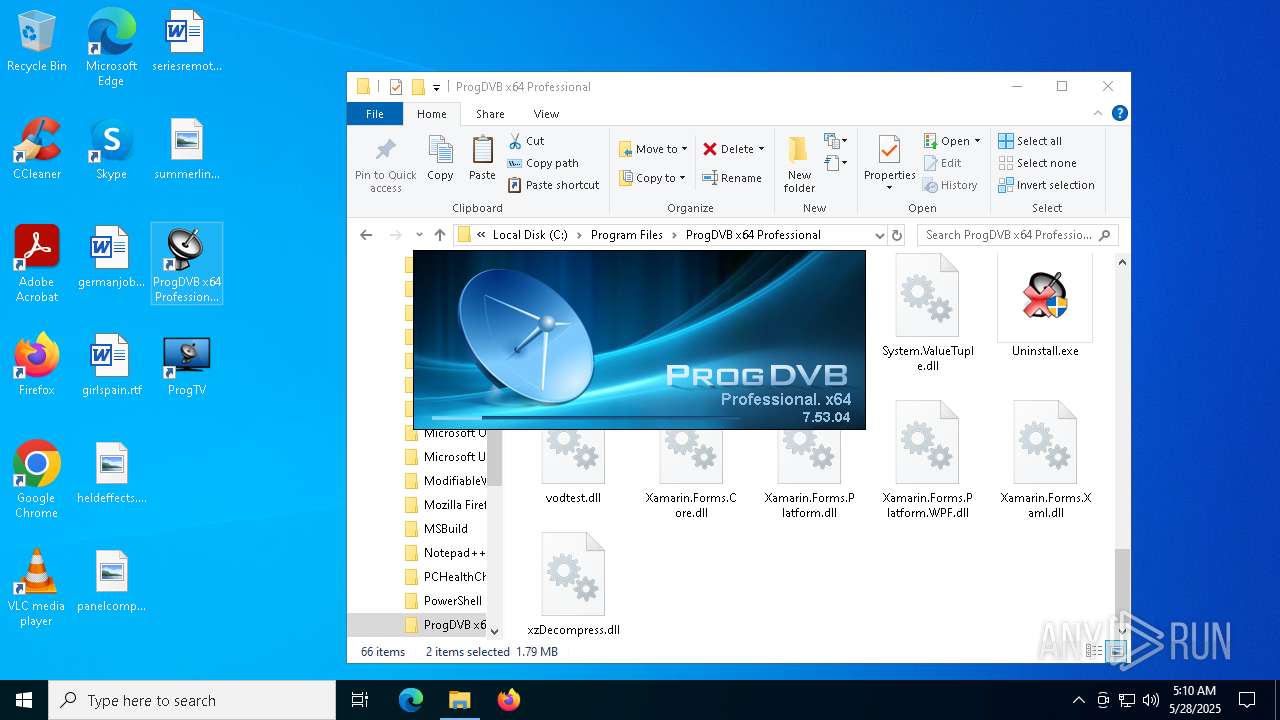
| URL: | https://archive.org/download/prog-dvb-prog-tv.-professional.-7.53.4-x-64-crack/ProgDVB%26ProgTV.Professional.7.53.4_x64%2BCrack.rar |
| Full analysis: | https://app.any.run/tasks/a9210136-b223-47ef-b583-81012cbc3cd9 |
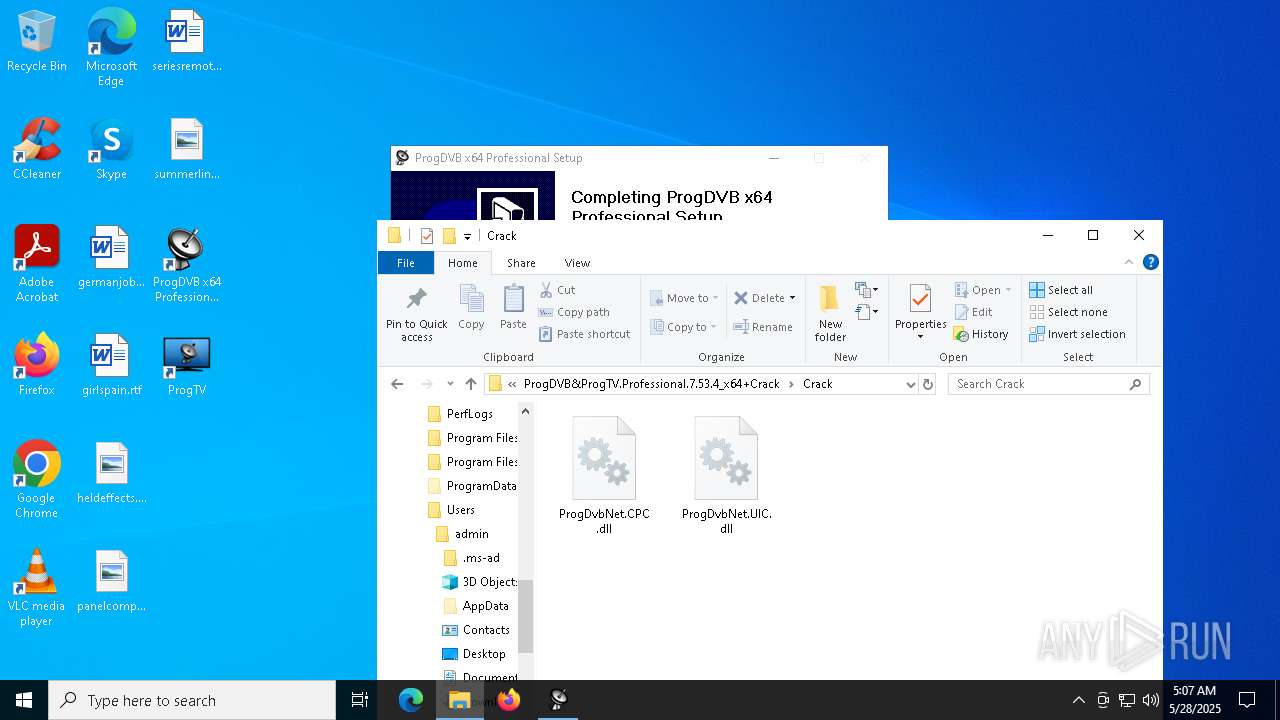
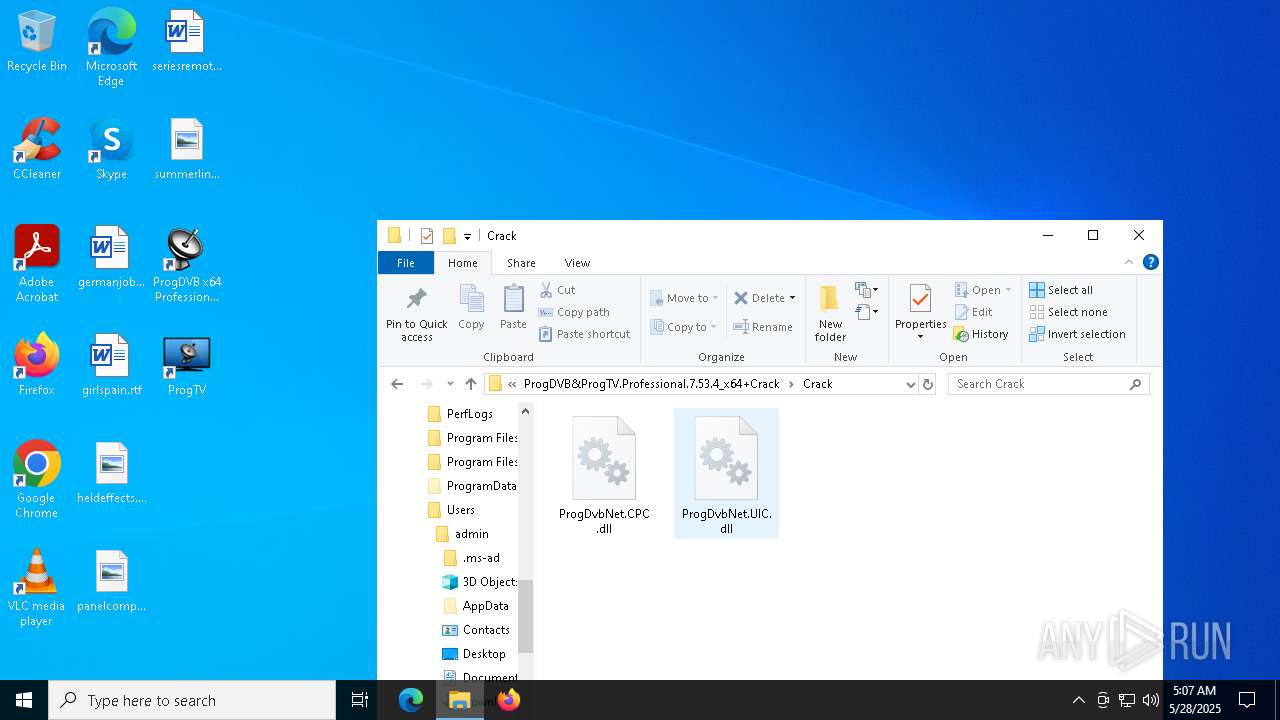
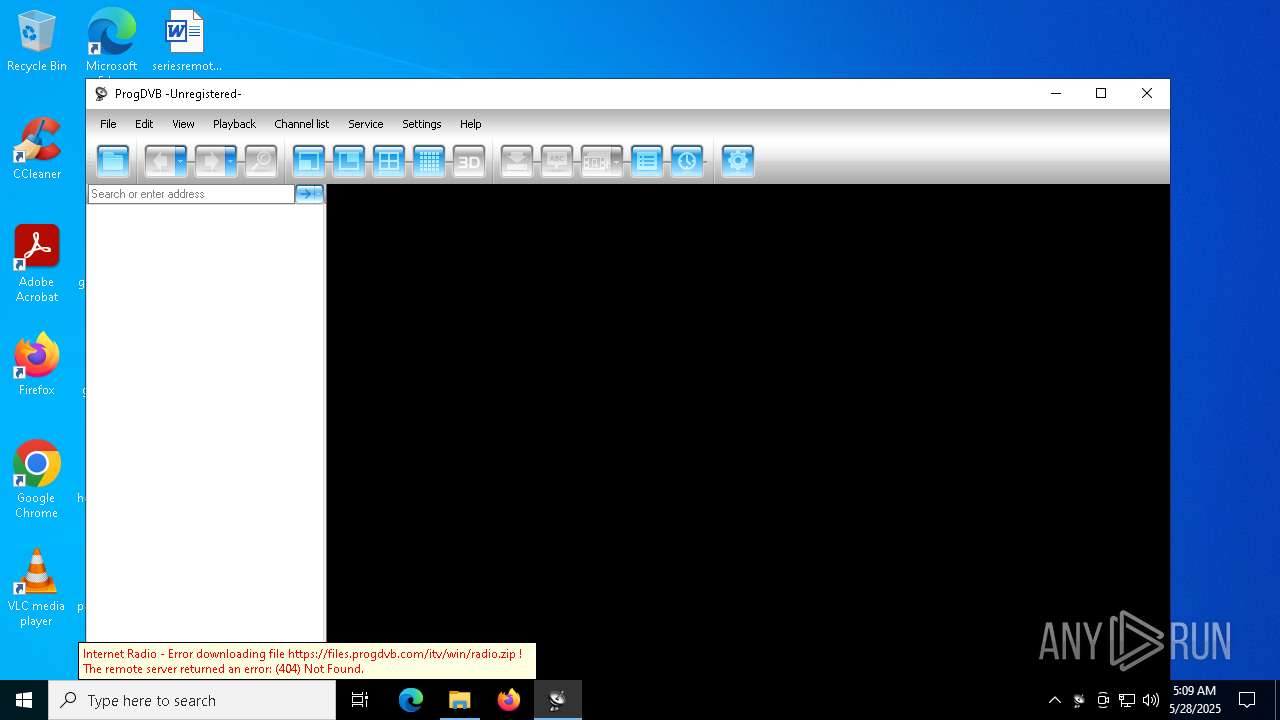
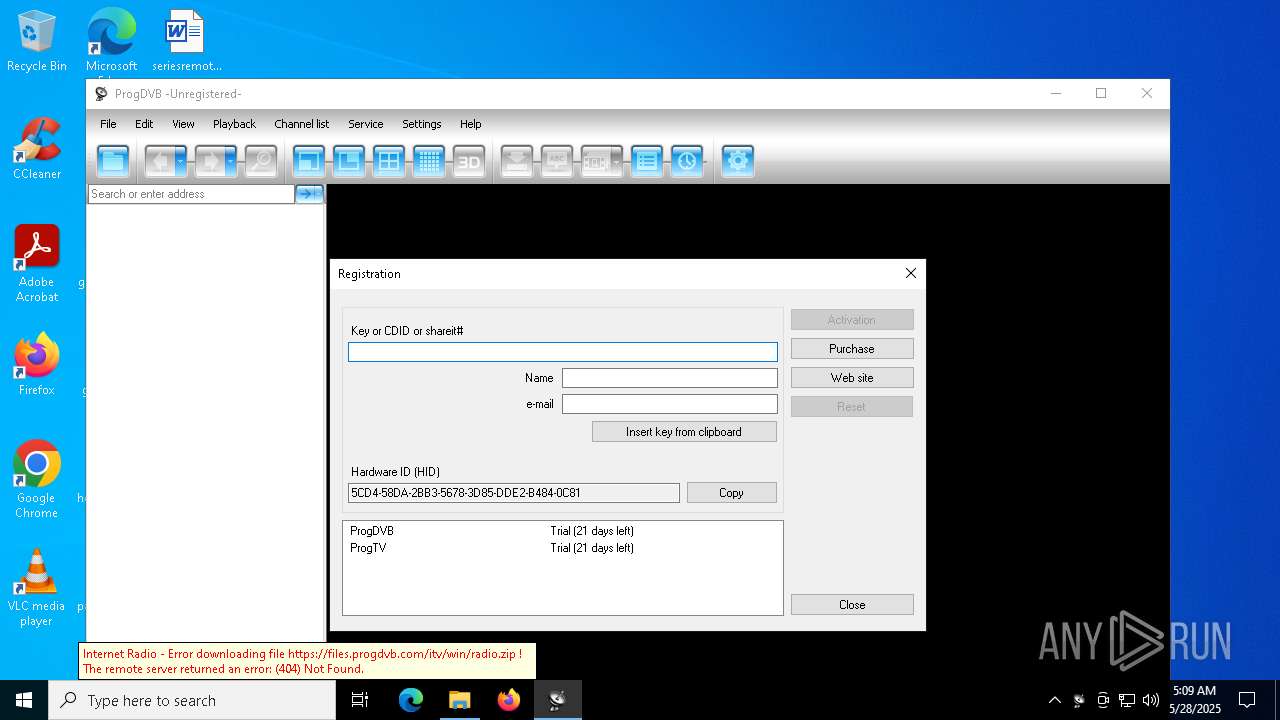
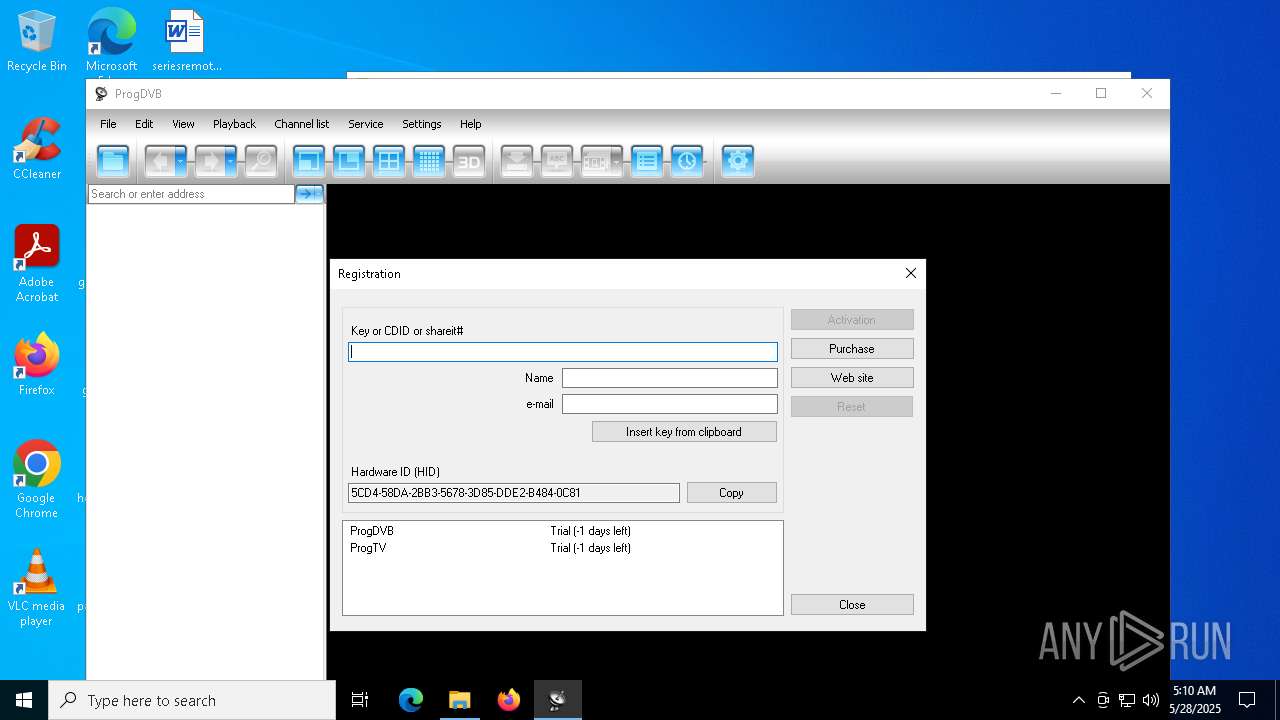
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2025, 05:05:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | CF361A8E54C508D65797DC2A25A56E27 |
| SHA1: | 8B82927A050206B5DE15D81519E3F82EB7B3F055 |
| SHA256: | 1838523AAD0DEEACBABB96112166A94157C549B68B40FD4EE3633008379639FE |
| SSDEEP: | 3:N8MFXJ2gdKZYIiQg8SlTsUCDXkQgmLXT7a:2MFXZcg8JXXgmLXi |
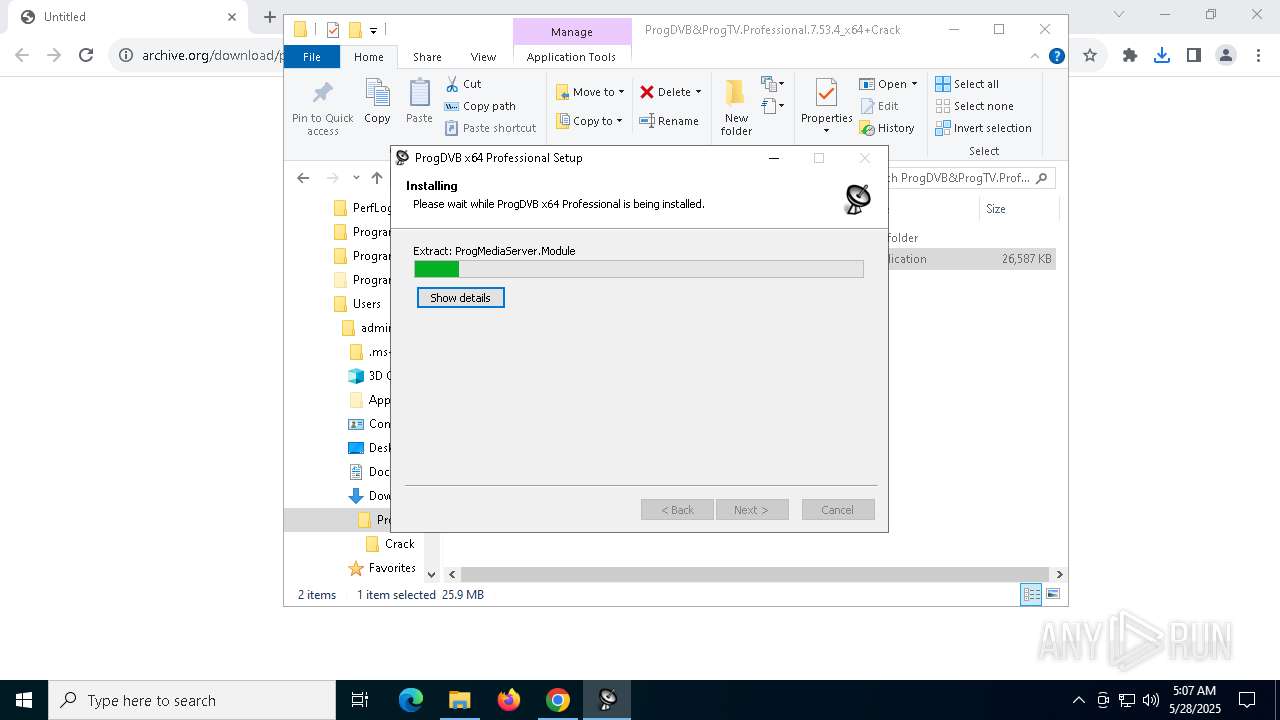
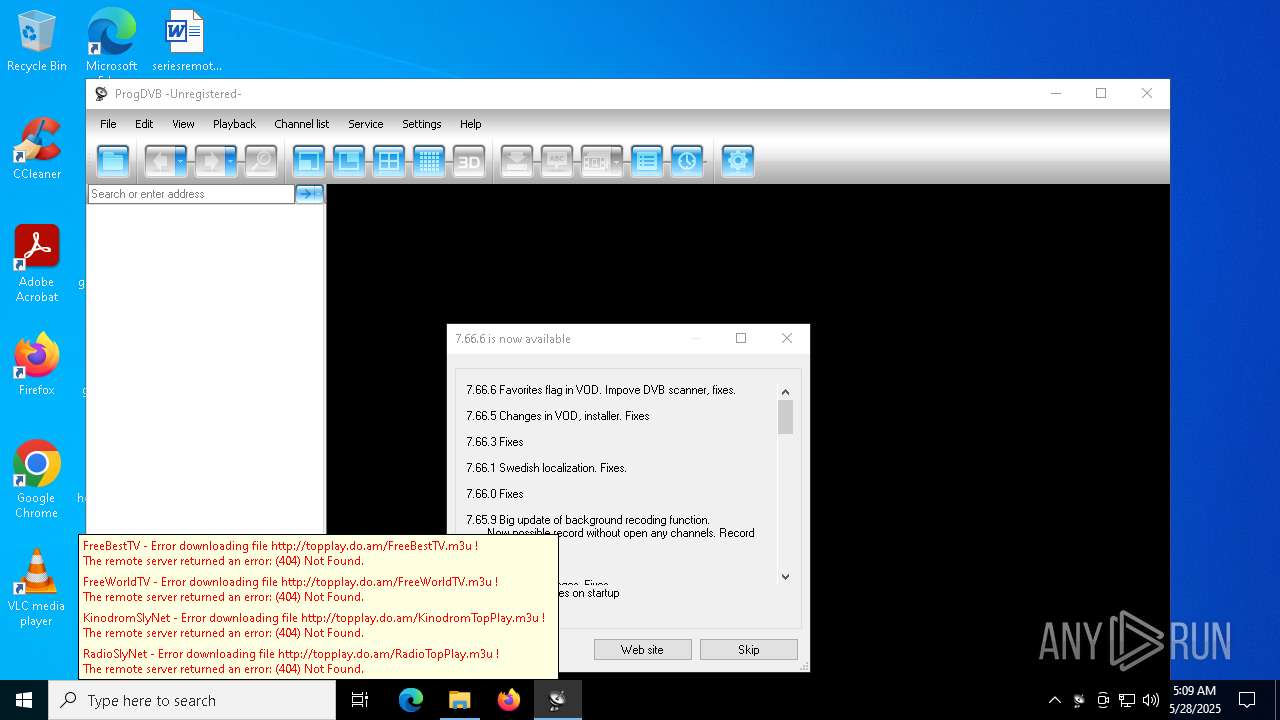
MALICIOUS
No malicious indicators.SUSPICIOUS
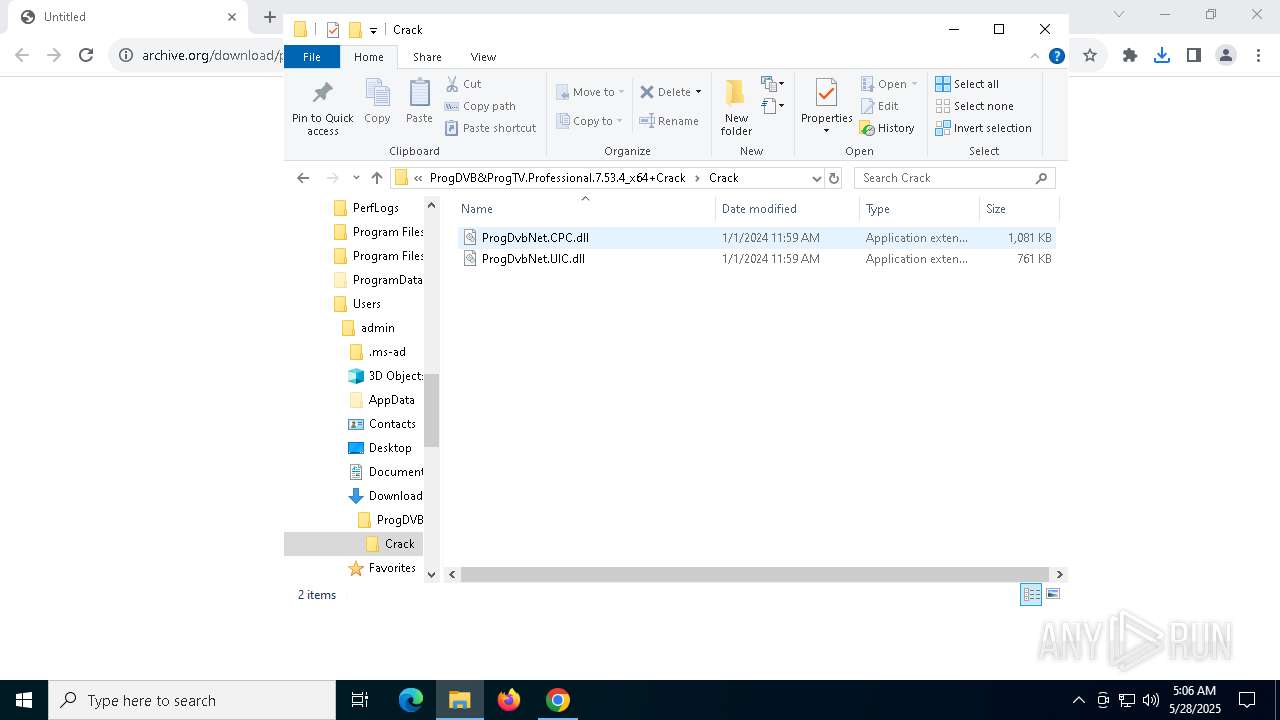
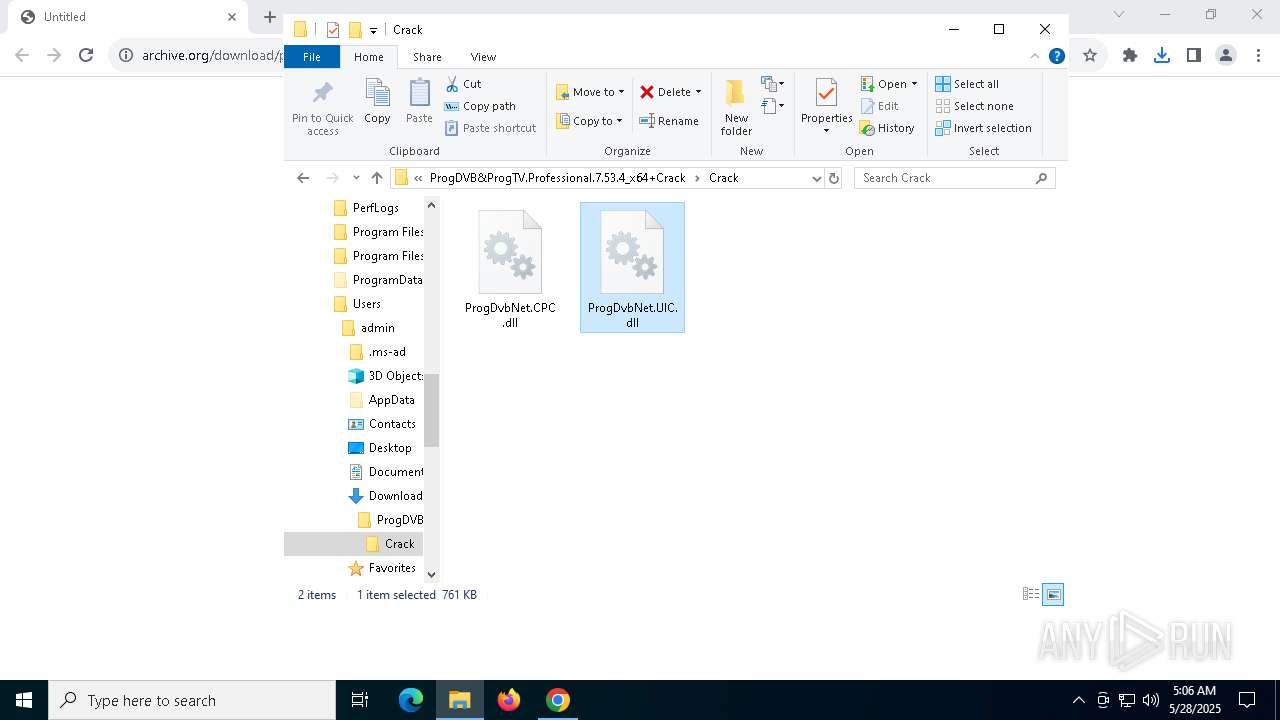
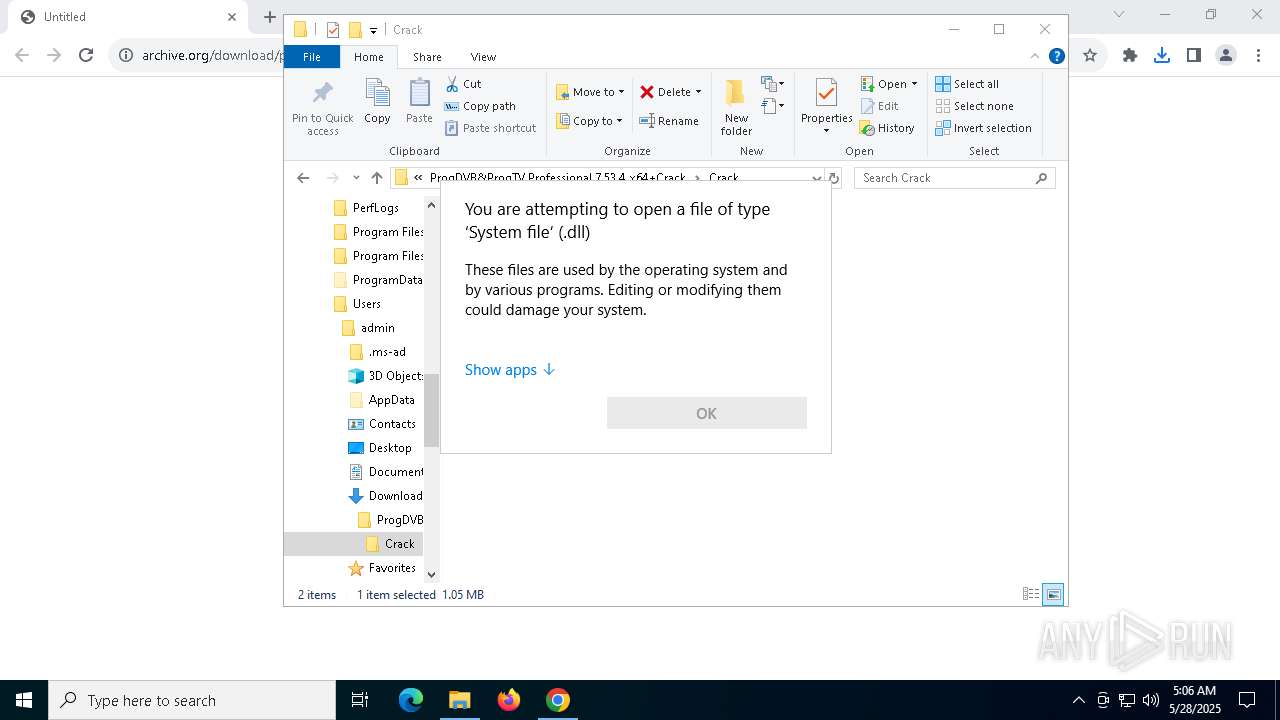
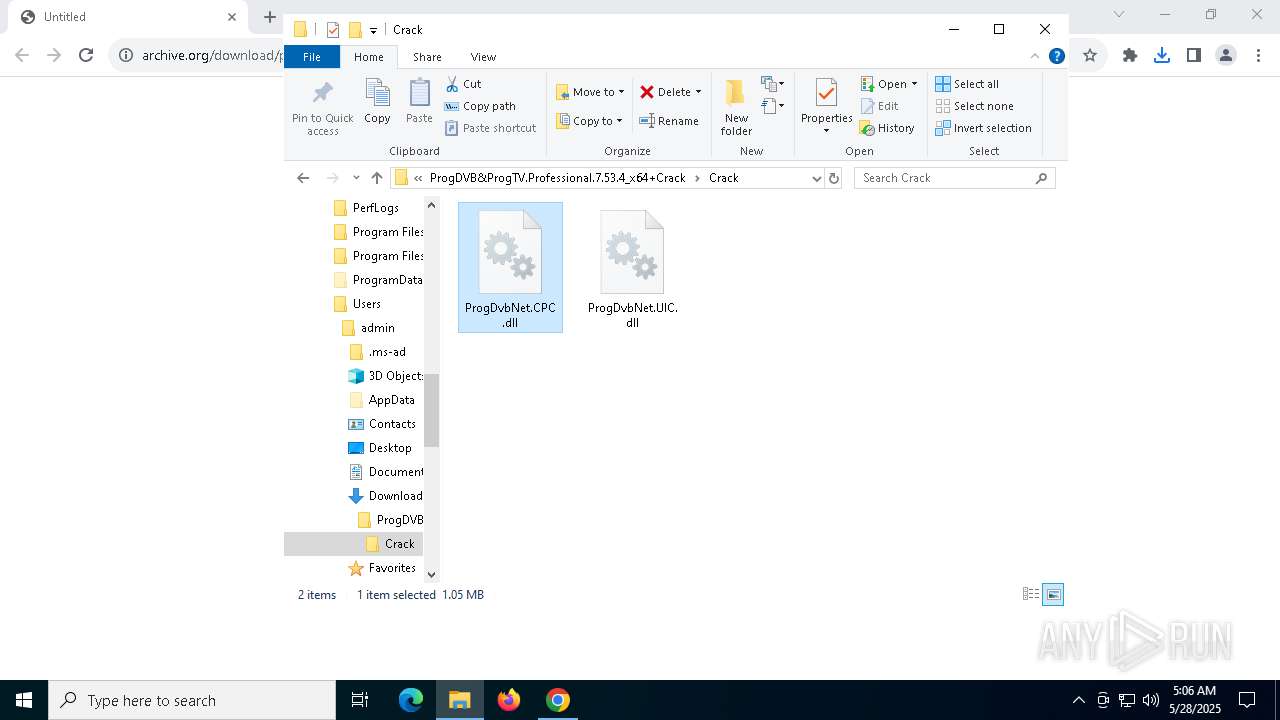
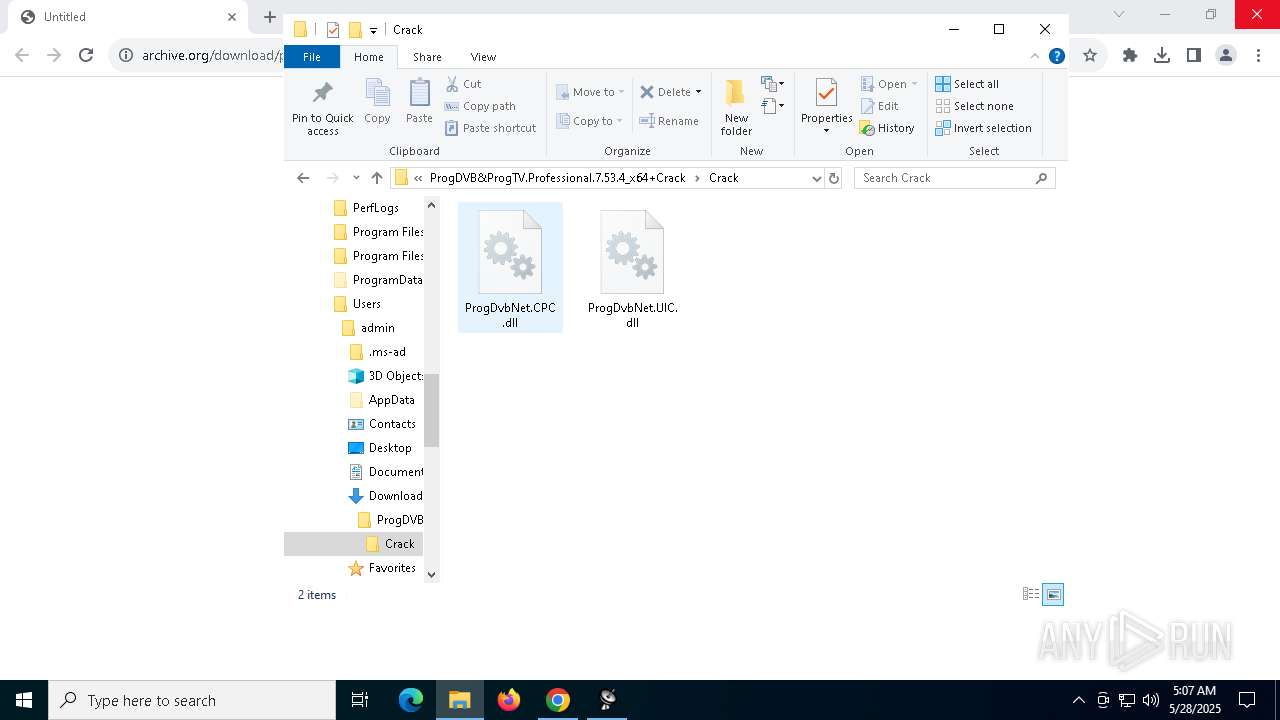
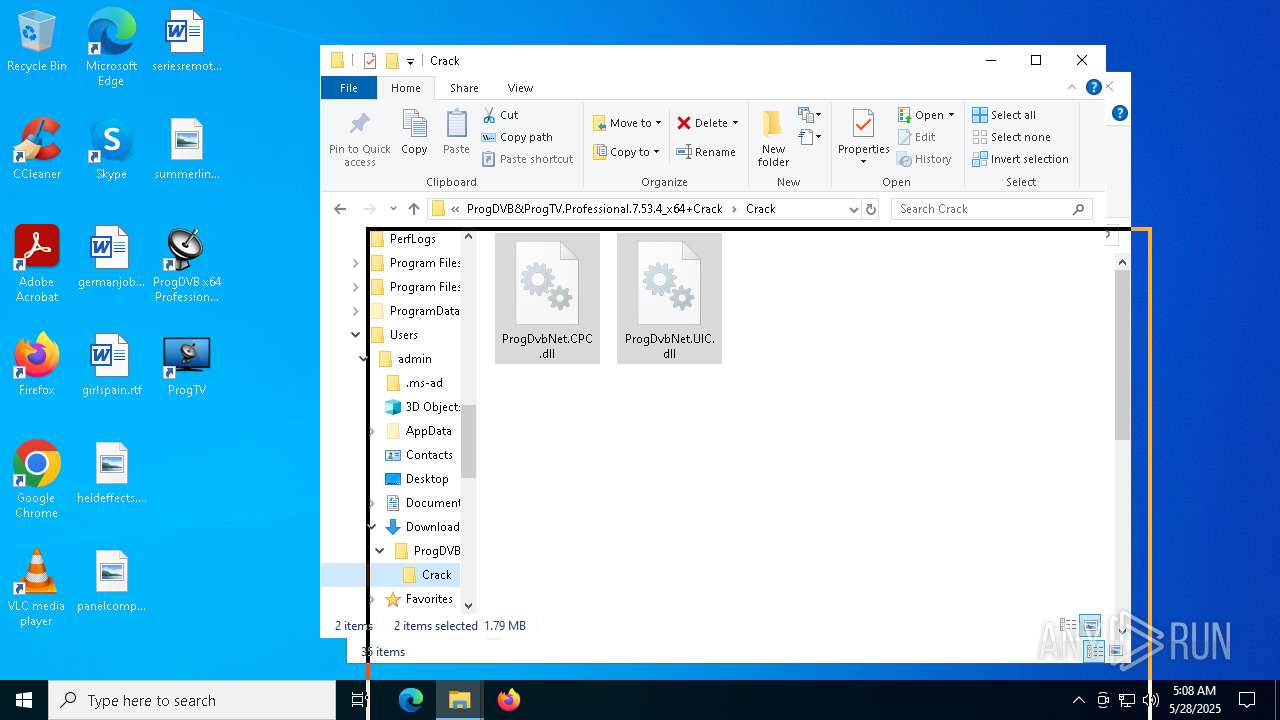
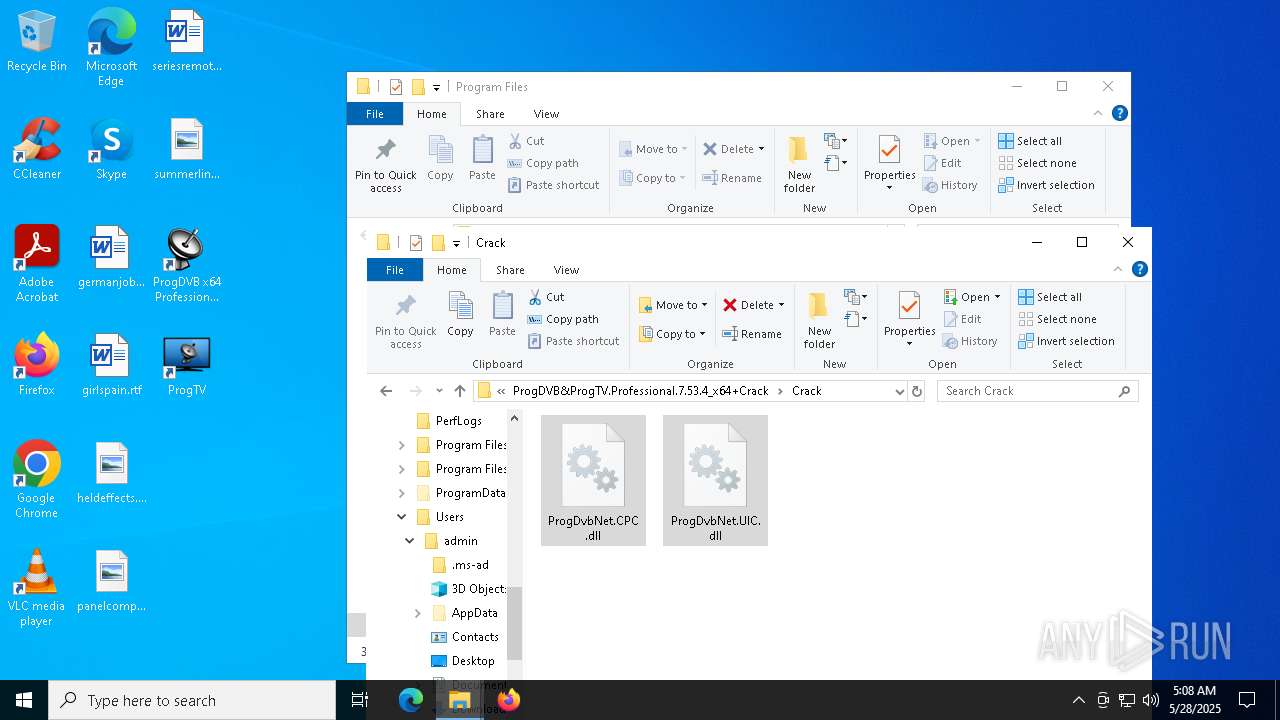
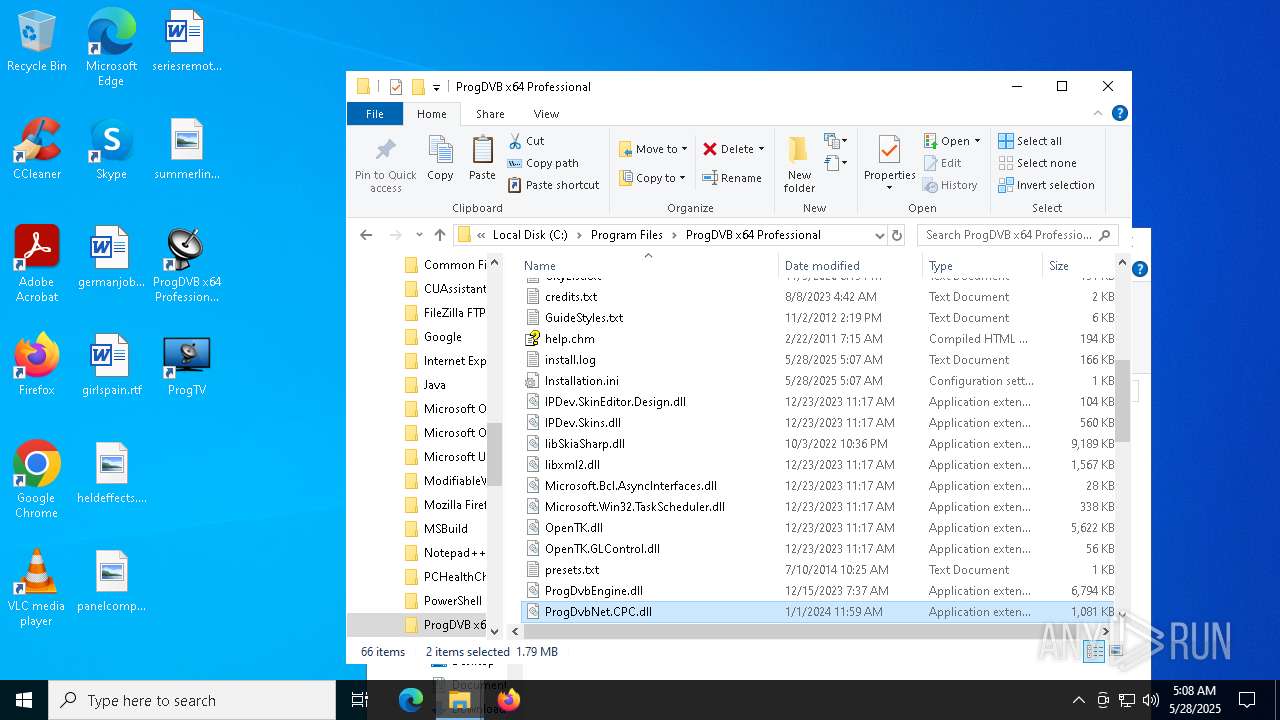
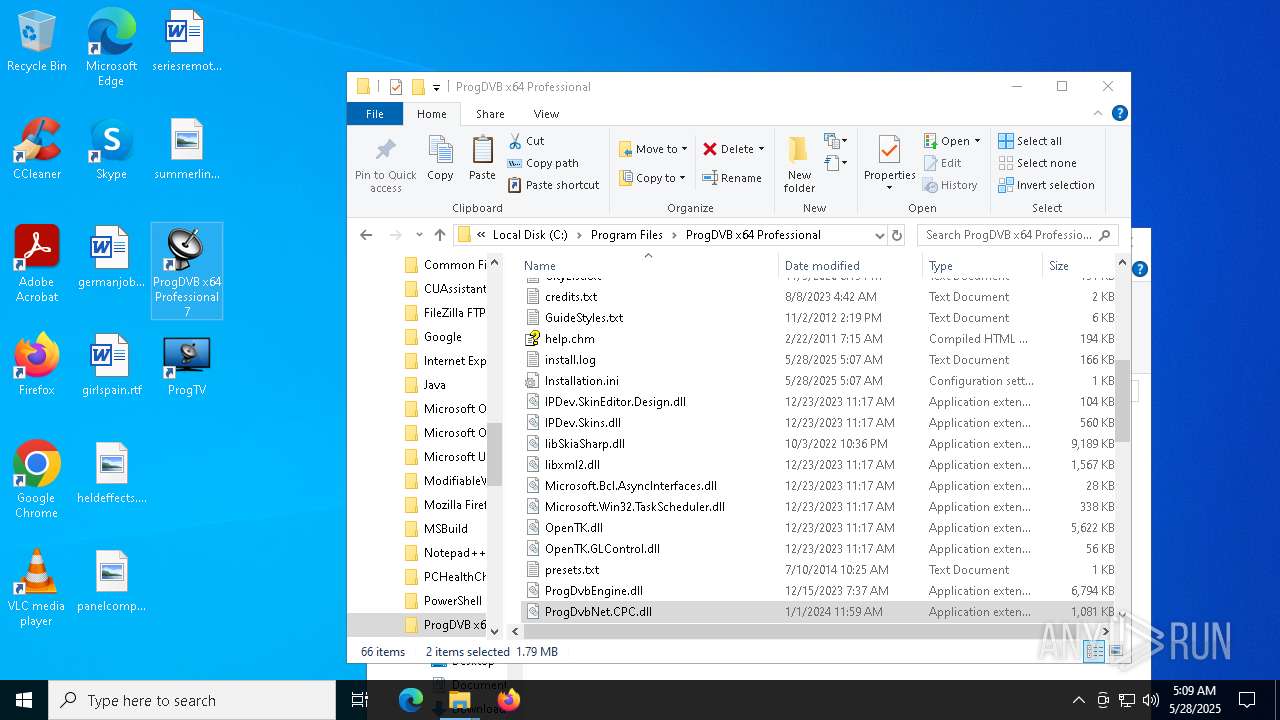
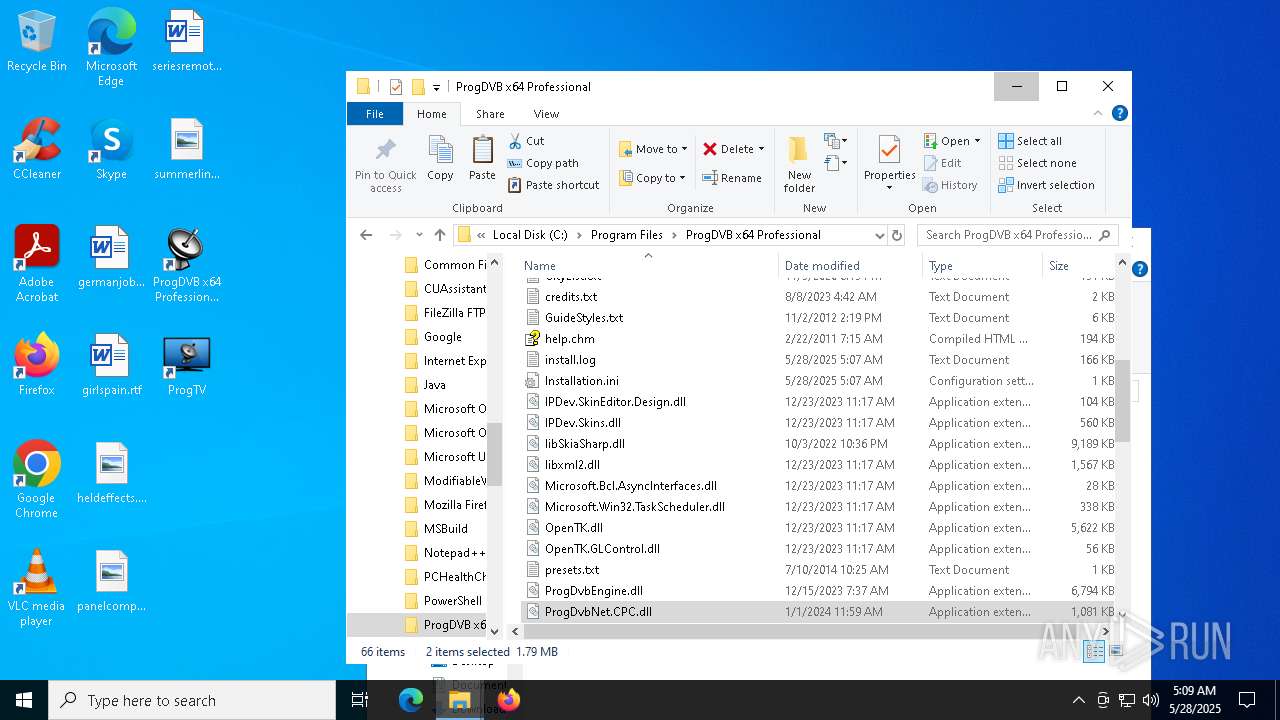
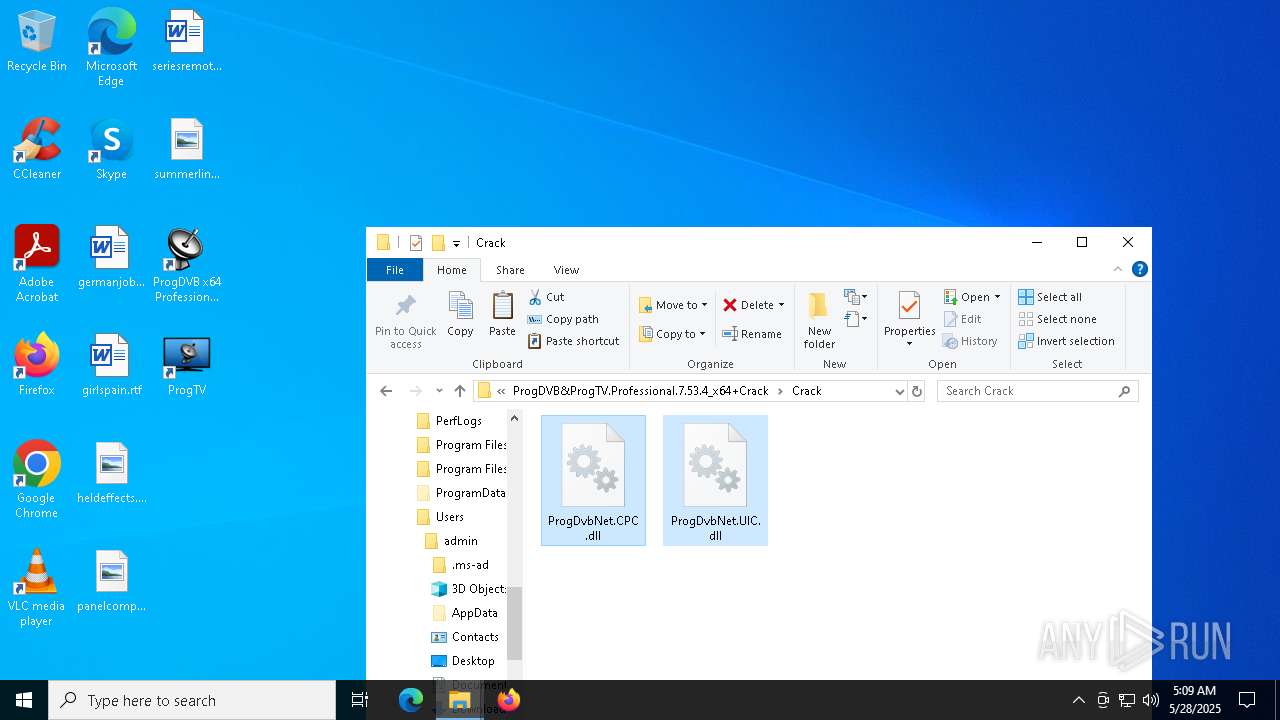
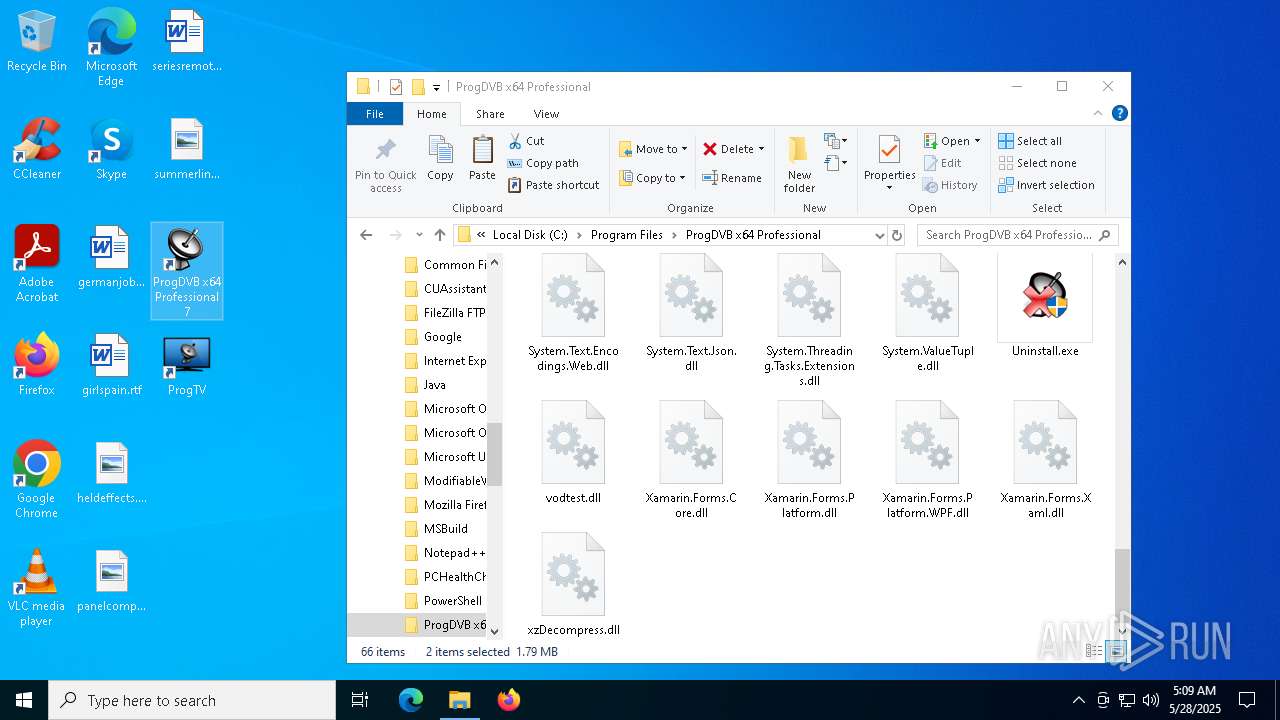
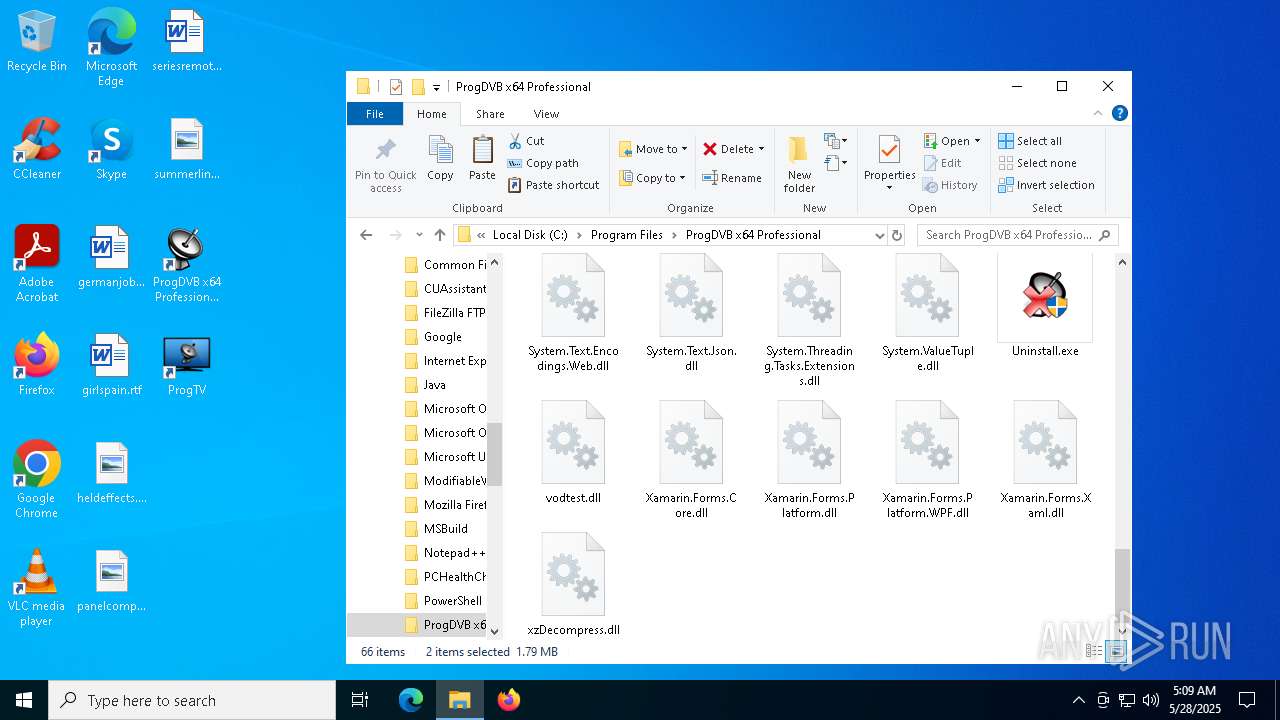
The process creates files with name similar to system file names
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
Malware-specific behavior (creating "System.dll" in Temp)
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
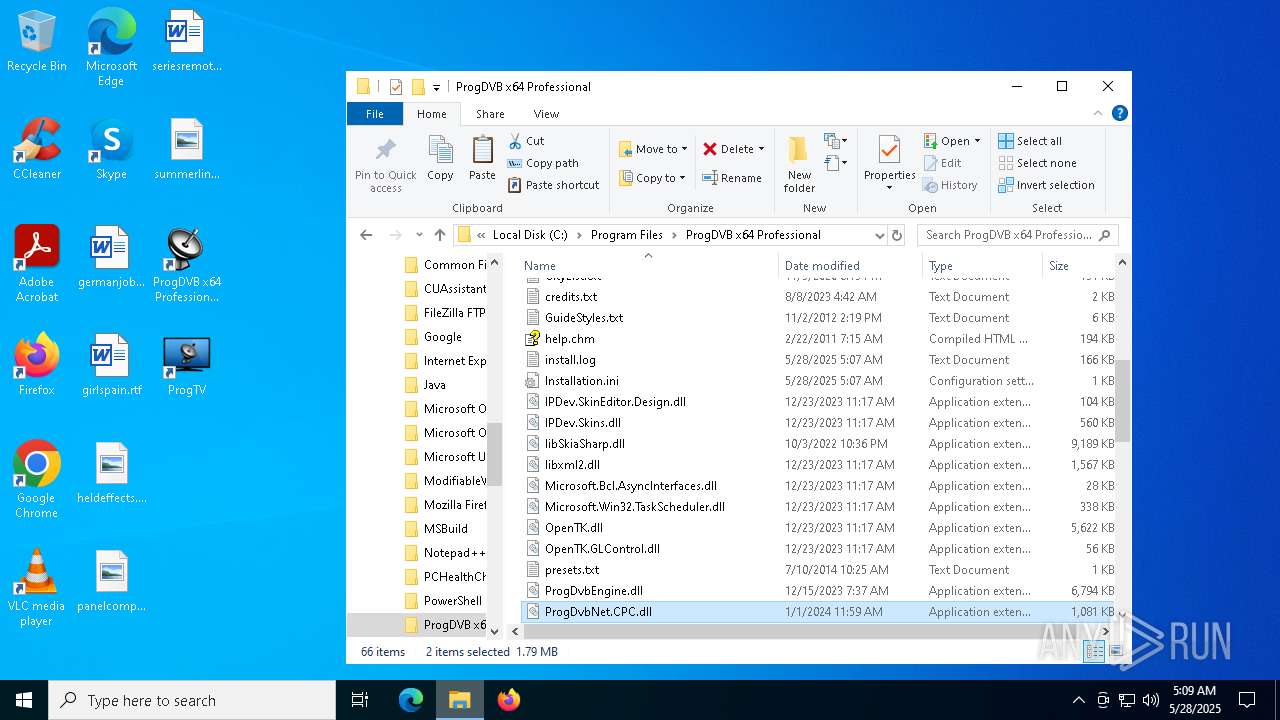
Executable content was dropped or overwritten
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
- mscorsvw.exe (PID: 668)
- mscorsvw.exe (PID: 4528)
- mscorsvw.exe (PID: 5772)
- mscorsvw.exe (PID: 7504)
- mscorsvw.exe (PID: 7932)
- mscorsvw.exe (PID: 7864)
- mscorsvw.exe (PID: 5452)
- mscorsvw.exe (PID: 3784)
- mscorsvw.exe (PID: 7052)
- mscorsvw.exe (PID: 4112)
- mscorsvw.exe (PID: 5936)
- mscorsvw.exe (PID: 2616)
- mscorsvw.exe (PID: 7152)
- mscorsvw.exe (PID: 5364)
- mscorsvw.exe (PID: 8072)
- mscorsvw.exe (PID: 6228)
- mscorsvw.exe (PID: 8088)
- mscorsvw.exe (PID: 7260)
- mscorsvw.exe (PID: 4376)
- mscorsvw.exe (PID: 6148)
- mscorsvw.exe (PID: 660)
- mscorsvw.exe (PID: 5892)
- mscorsvw.exe (PID: 4224)
- mscorsvw.exe (PID: 7852)
- mscorsvw.exe (PID: 7772)
- mscorsvw.exe (PID: 2796)
- mscorsvw.exe (PID: 7832)
- mscorsvw.exe (PID: 6208)
- mscorsvw.exe (PID: 720)
- mscorsvw.exe (PID: 6584)
- mscorsvw.exe (PID: 3032)
- mscorsvw.exe (PID: 7876)
- mscorsvw.exe (PID: 4892)
- mscorsvw.exe (PID: 4304)
- mscorsvw.exe (PID: 5404)
- mscorsvw.exe (PID: 6192)
- mscorsvw.exe (PID: 8100)
- mscorsvw.exe (PID: 6972)
- mscorsvw.exe (PID: 2516)
- mscorsvw.exe (PID: 776)
- mscorsvw.exe (PID: 5056)
- mscorsvw.exe (PID: 4120)
- mscorsvw.exe (PID: 6424)
- mscorsvw.exe (PID: 644)
- mscorsvw.exe (PID: 7504)
- mscorsvw.exe (PID: 3024)
- mscorsvw.exe (PID: 5452)
- mscorsvw.exe (PID: 7636)
- mscorsvw.exe (PID: 8168)
- mscorsvw.exe (PID: 1628)
- mscorsvw.exe (PID: 7904)
- mscorsvw.exe (PID: 6972)
- mscorsvw.exe (PID: 496)
- mscorsvw.exe (PID: 5176)
- mscorsvw.exe (PID: 4572)
- mscorsvw.exe (PID: 4448)
- mscorsvw.exe (PID: 5796)
- mscorsvw.exe (PID: 6712)
- mscorsvw.exe (PID: 3140)
- mscorsvw.exe (PID: 6324)
- mscorsvw.exe (PID: 7828)
- mscorsvw.exe (PID: 7992)
- mscorsvw.exe (PID: 7924)
- mscorsvw.exe (PID: 456)
- mscorsvw.exe (PID: 7840)
- mscorsvw.exe (PID: 1912)
- mscorsvw.exe (PID: 2084)
- mscorsvw.exe (PID: 4408)
- mscorsvw.exe (PID: 8088)
- mscorsvw.exe (PID: 3332)
- mscorsvw.exe (PID: 3760)
- mscorsvw.exe (PID: 4428)
- mscorsvw.exe (PID: 5756)
- mscorsvw.exe (PID: 8180)
There is functionality for taking screenshot (YARA)
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
Process drops legitimate windows executable
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
- mscorsvw.exe (PID: 668)
- mscorsvw.exe (PID: 7504)
- mscorsvw.exe (PID: 5772)
- mscorsvw.exe (PID: 7864)
- mscorsvw.exe (PID: 7932)
- mscorsvw.exe (PID: 3784)
- mscorsvw.exe (PID: 4112)
- mscorsvw.exe (PID: 5936)
- mscorsvw.exe (PID: 2616)
- mscorsvw.exe (PID: 5364)
- mscorsvw.exe (PID: 7152)
- mscorsvw.exe (PID: 8072)
- mscorsvw.exe (PID: 6228)
- mscorsvw.exe (PID: 5452)
- mscorsvw.exe (PID: 5892)
- mscorsvw.exe (PID: 4376)
- mscorsvw.exe (PID: 8088)
- mscorsvw.exe (PID: 6148)
- mscorsvw.exe (PID: 4224)
- mscorsvw.exe (PID: 660)
- mscorsvw.exe (PID: 7260)
- mscorsvw.exe (PID: 7852)
- mscorsvw.exe (PID: 7772)
- mscorsvw.exe (PID: 7832)
- mscorsvw.exe (PID: 2796)
- mscorsvw.exe (PID: 6208)
- mscorsvw.exe (PID: 720)
- mscorsvw.exe (PID: 6584)
- mscorsvw.exe (PID: 3032)
- mscorsvw.exe (PID: 7876)
- mscorsvw.exe (PID: 4892)
- mscorsvw.exe (PID: 4304)
- mscorsvw.exe (PID: 5404)
- mscorsvw.exe (PID: 776)
- mscorsvw.exe (PID: 6972)
- mscorsvw.exe (PID: 8100)
- mscorsvw.exe (PID: 6192)
- mscorsvw.exe (PID: 4120)
- mscorsvw.exe (PID: 7504)
- mscorsvw.exe (PID: 5452)
- mscorsvw.exe (PID: 7636)
- mscorsvw.exe (PID: 7904)
- mscorsvw.exe (PID: 644)
- mscorsvw.exe (PID: 496)
- mscorsvw.exe (PID: 4572)
- mscorsvw.exe (PID: 4448)
- mscorsvw.exe (PID: 6712)
- mscorsvw.exe (PID: 6324)
- mscorsvw.exe (PID: 7828)
- mscorsvw.exe (PID: 5756)
- mscorsvw.exe (PID: 6972)
- mscorsvw.exe (PID: 1912)
- mscorsvw.exe (PID: 7924)
- mscorsvw.exe (PID: 7840)
- mscorsvw.exe (PID: 4408)
- mscorsvw.exe (PID: 8088)
- mscorsvw.exe (PID: 3332)
INFO
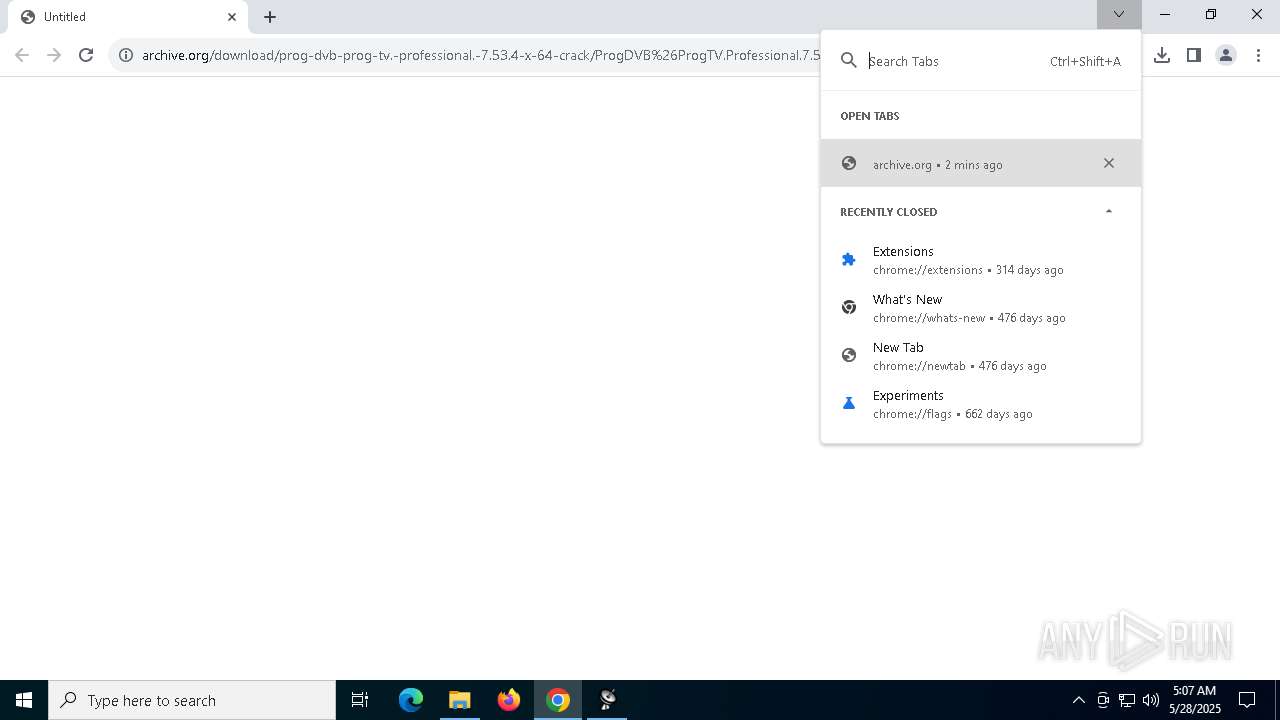
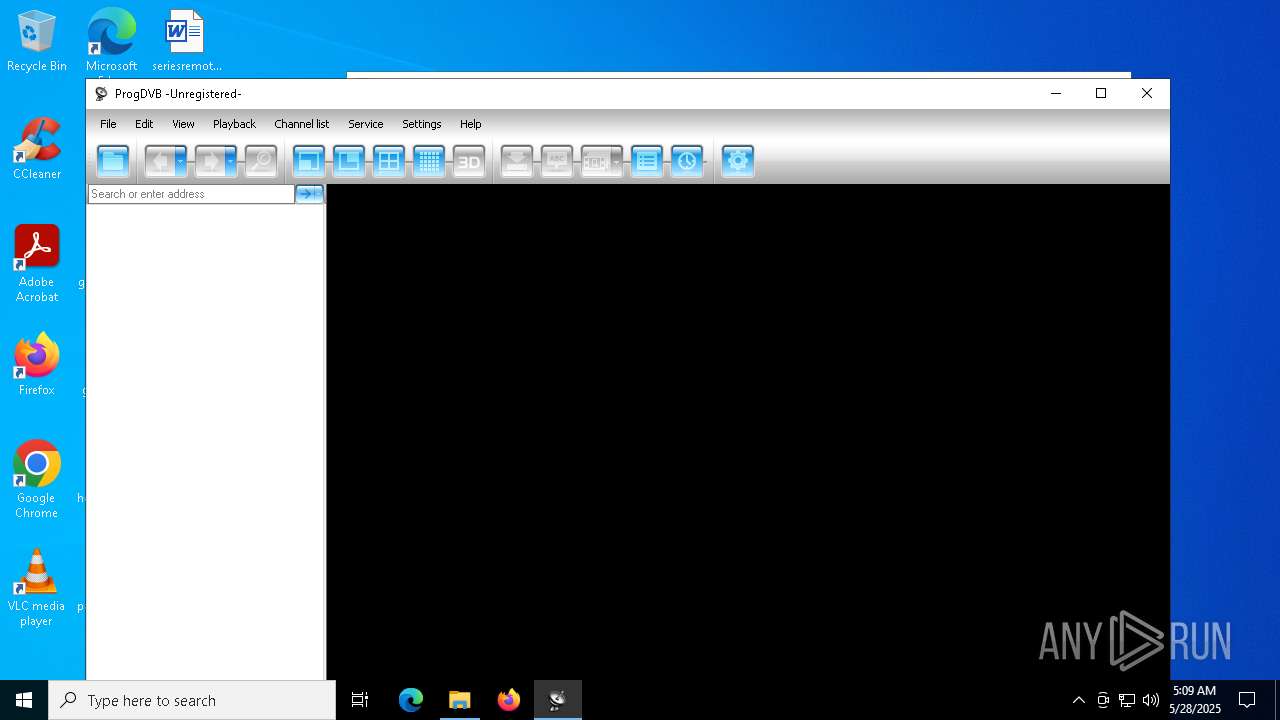
Application launched itself
- chrome.exe (PID: 5244)
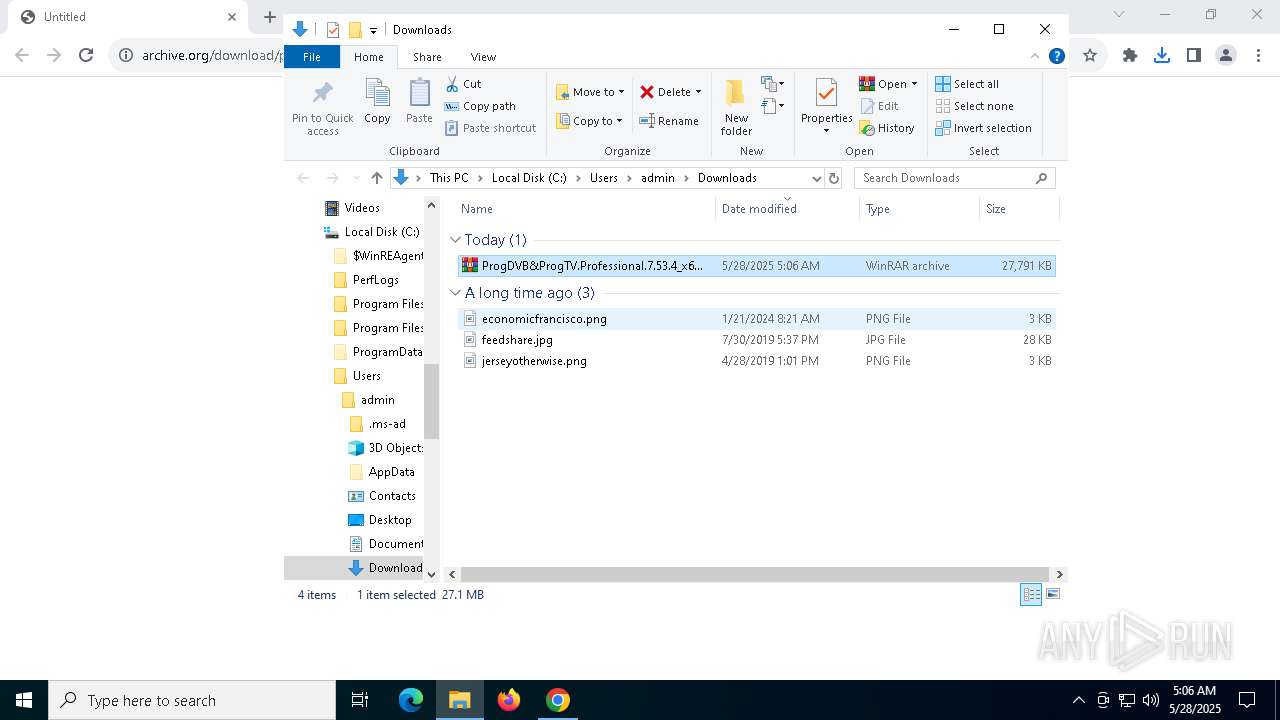
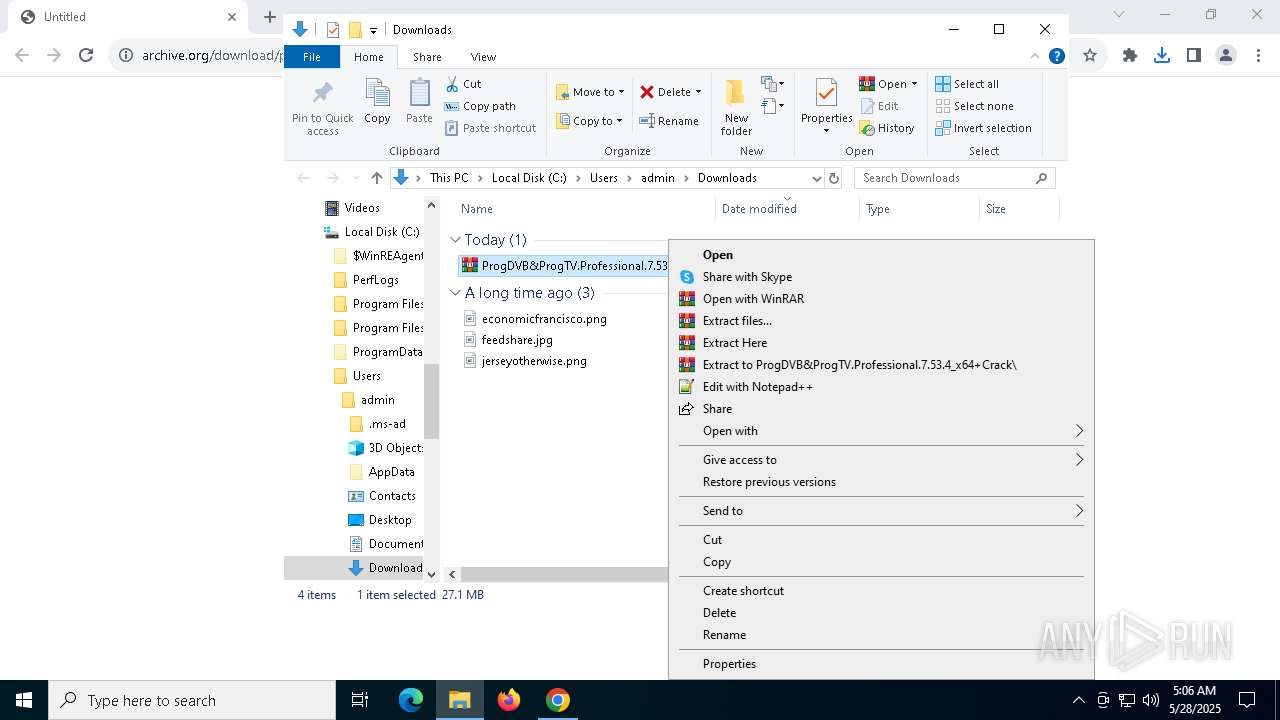
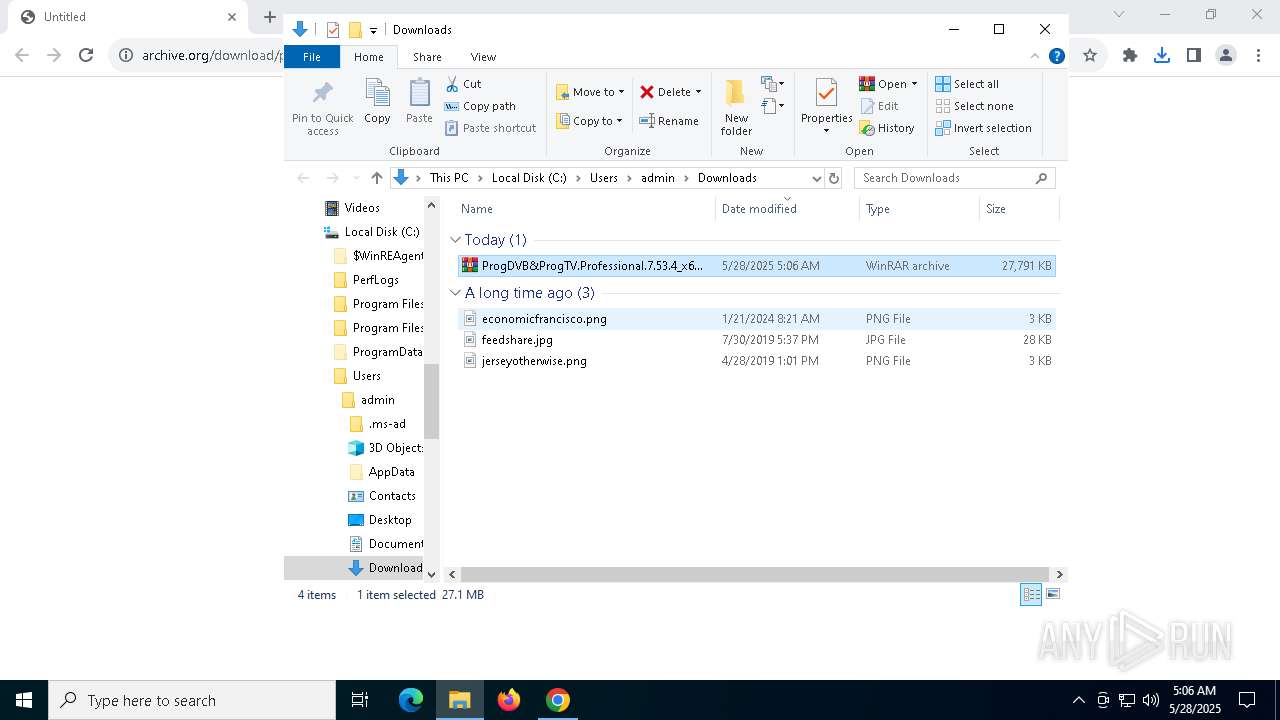
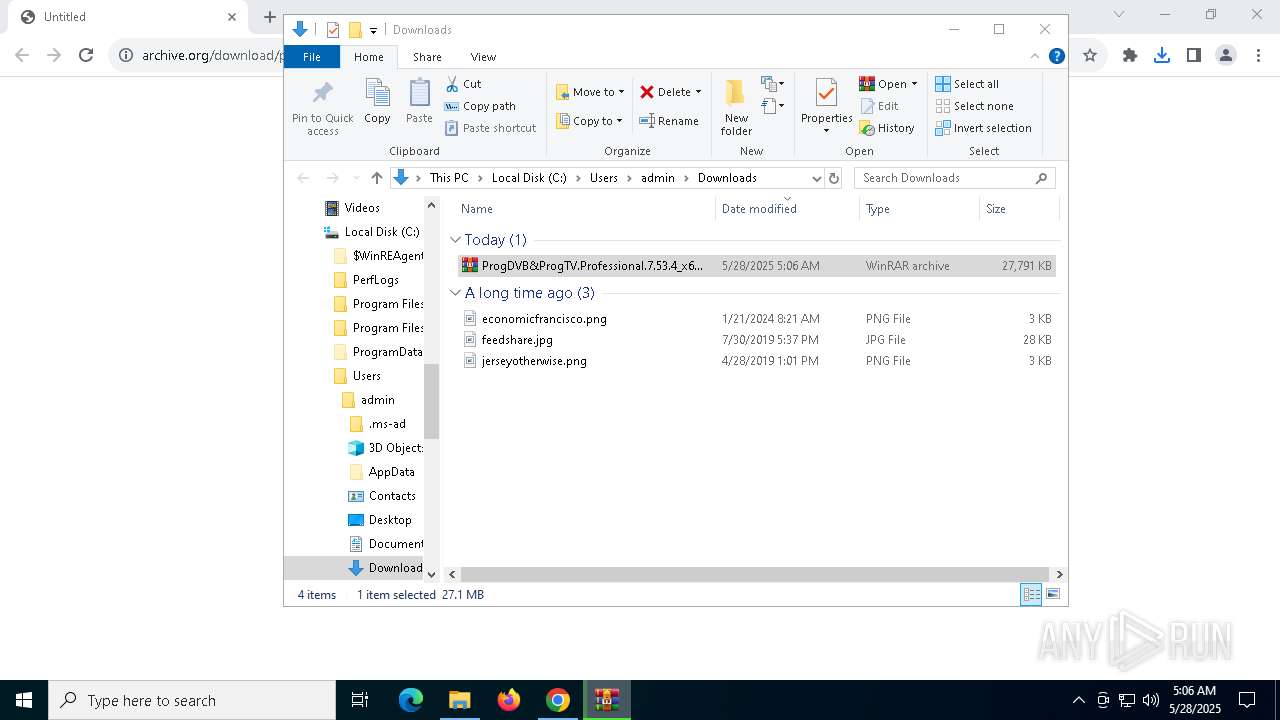
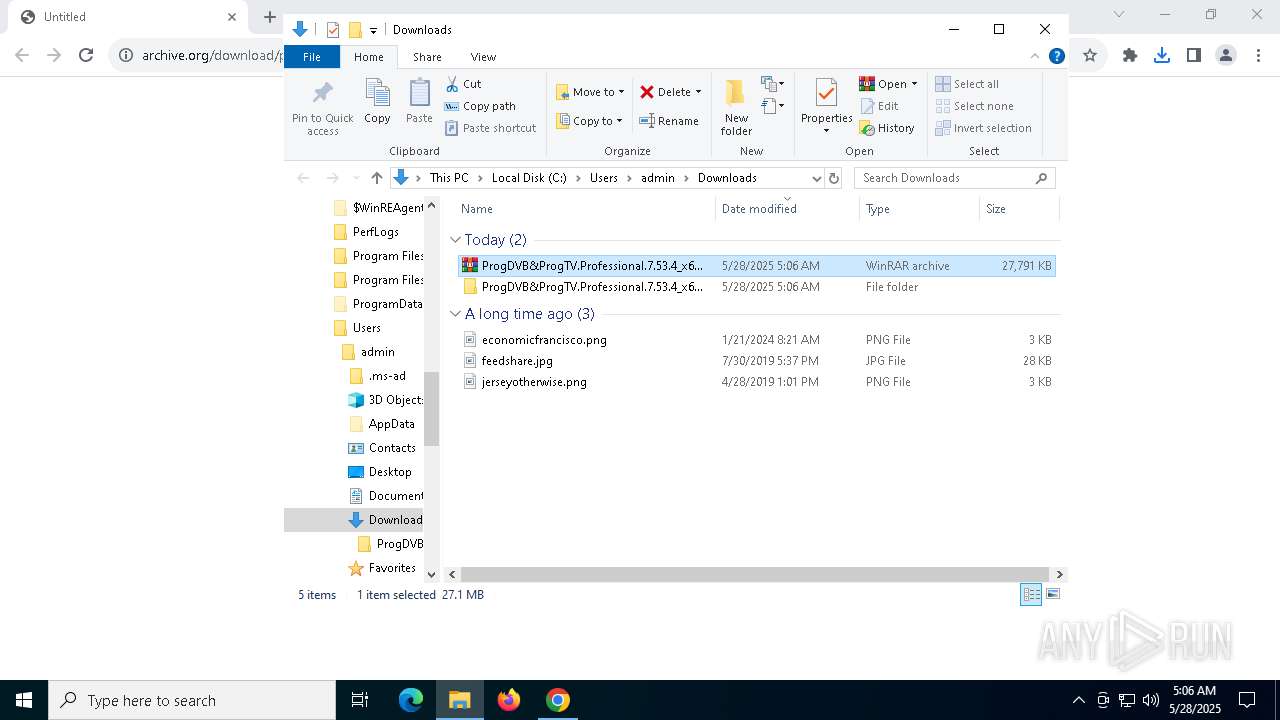
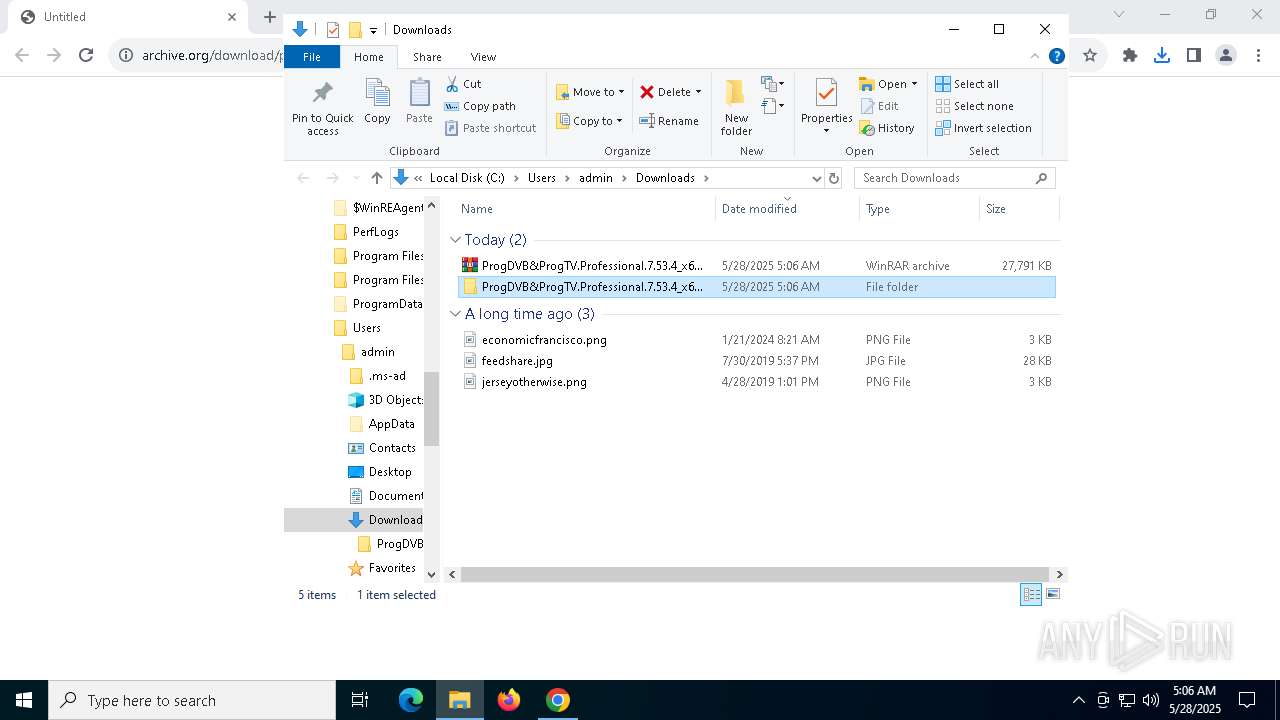
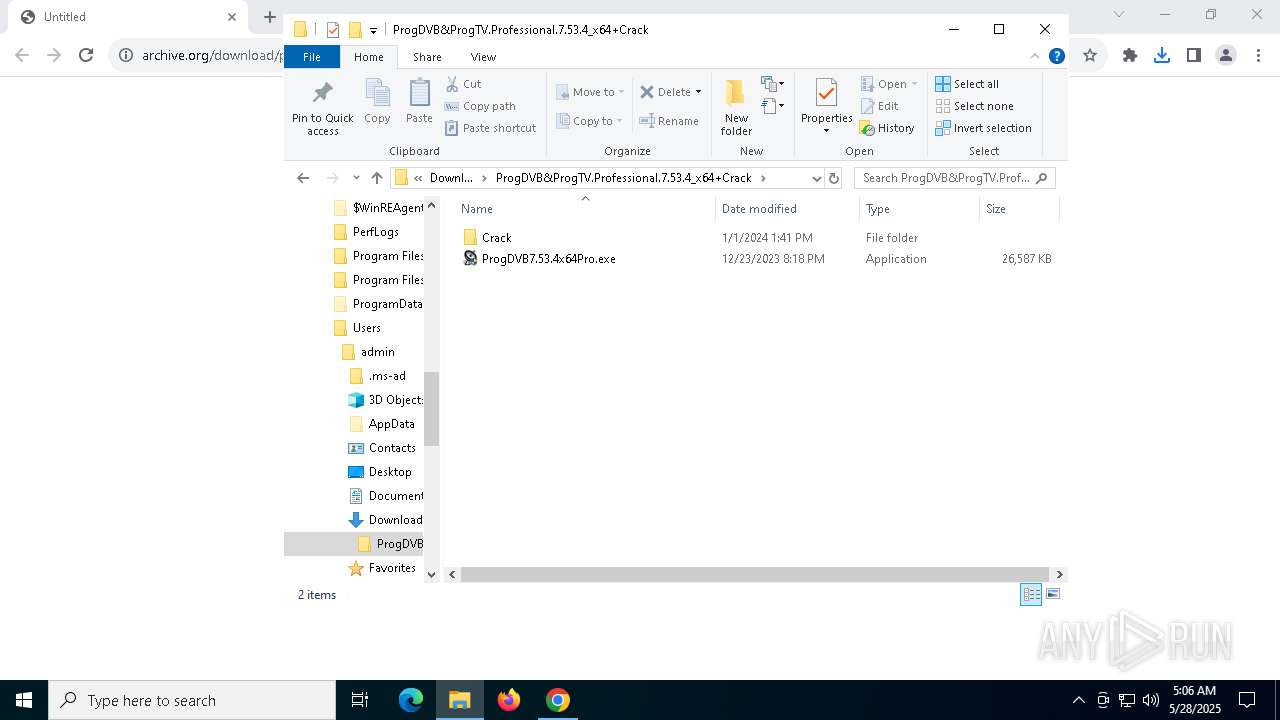
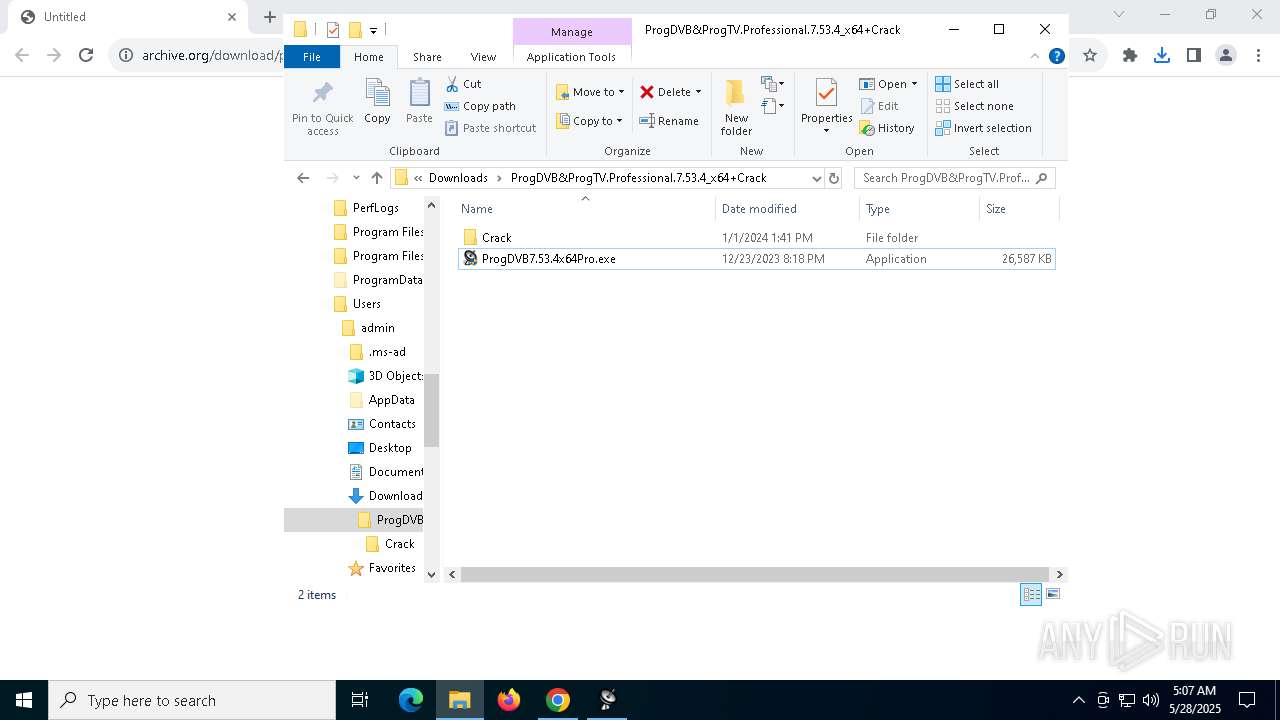
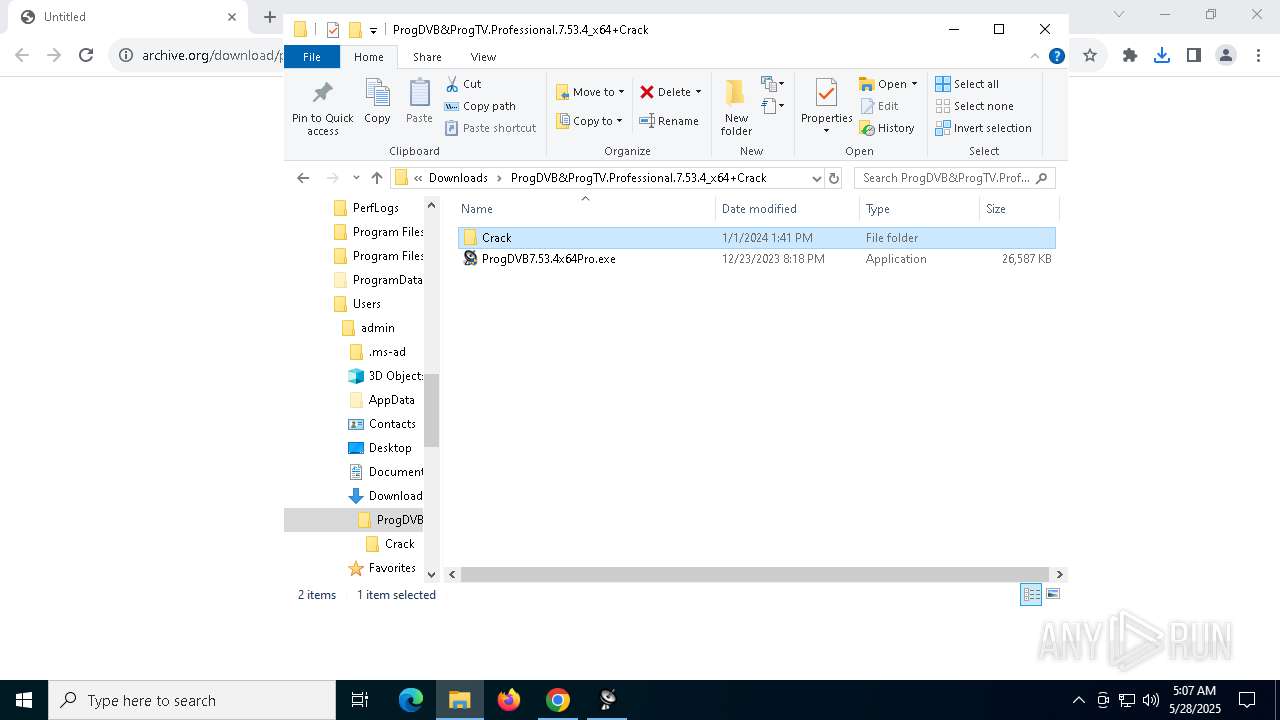
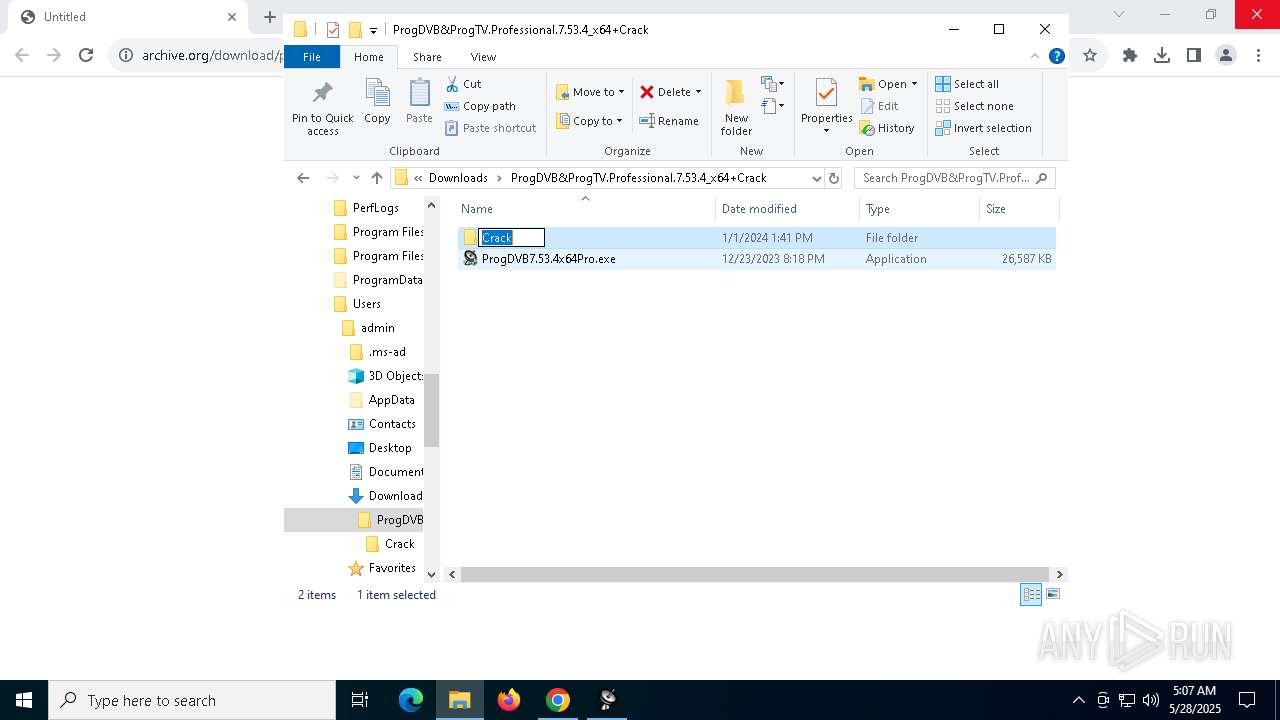
Launch of the file from Downloads directory
- chrome.exe (PID: 7744)
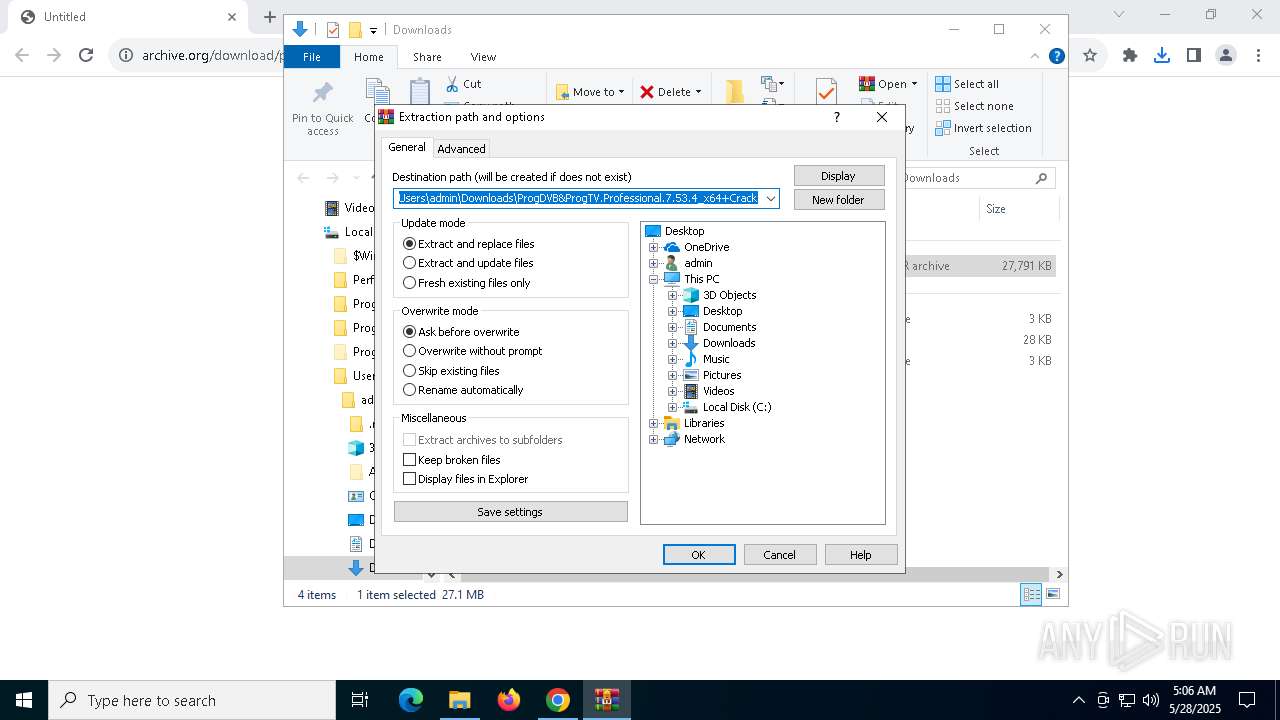
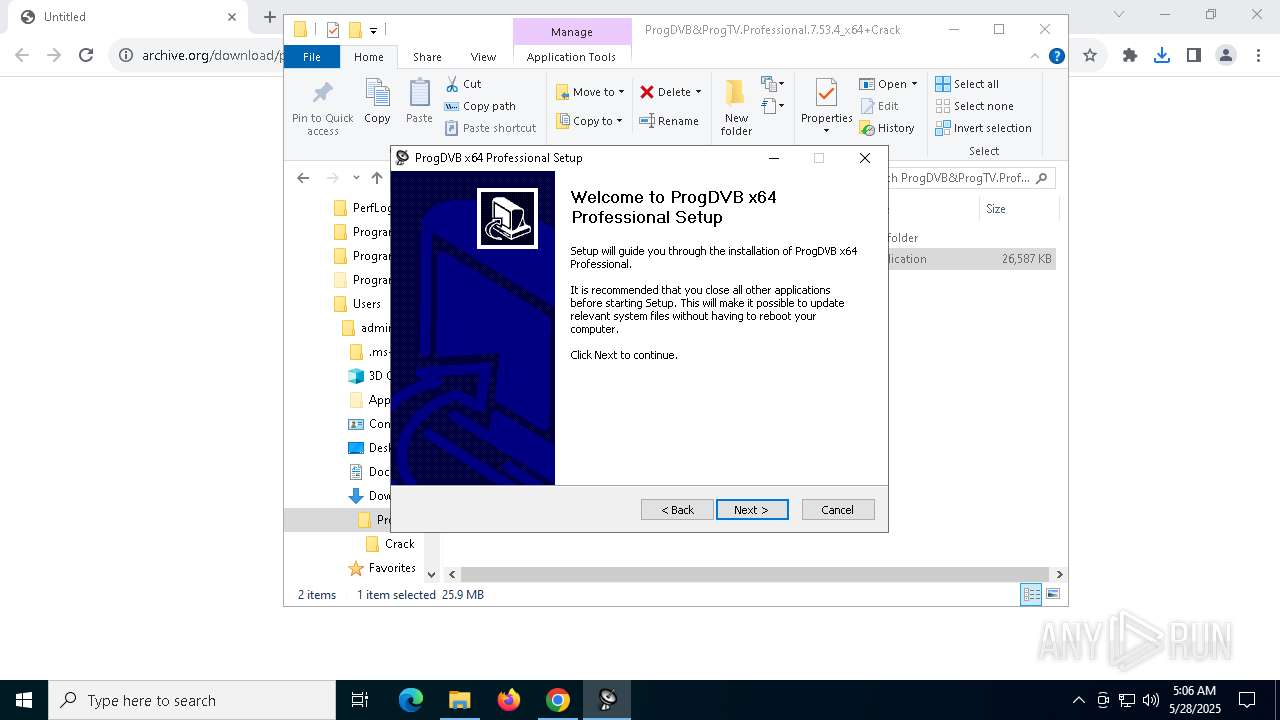
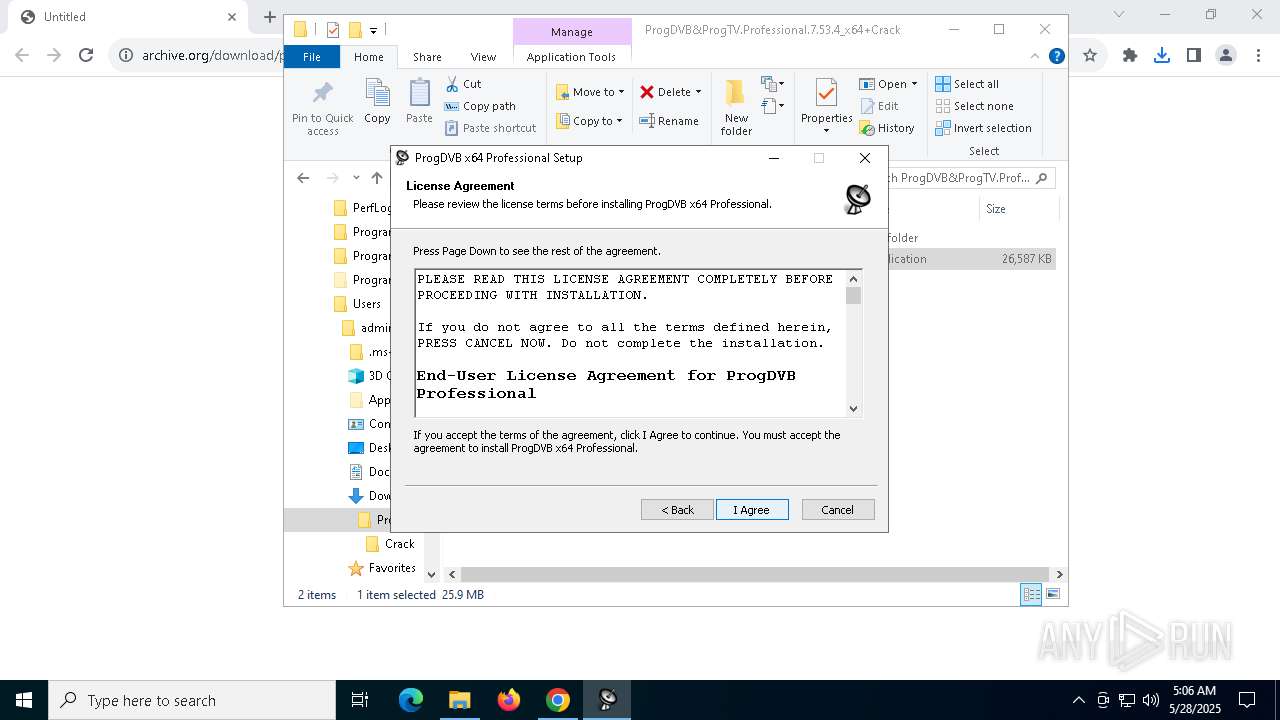
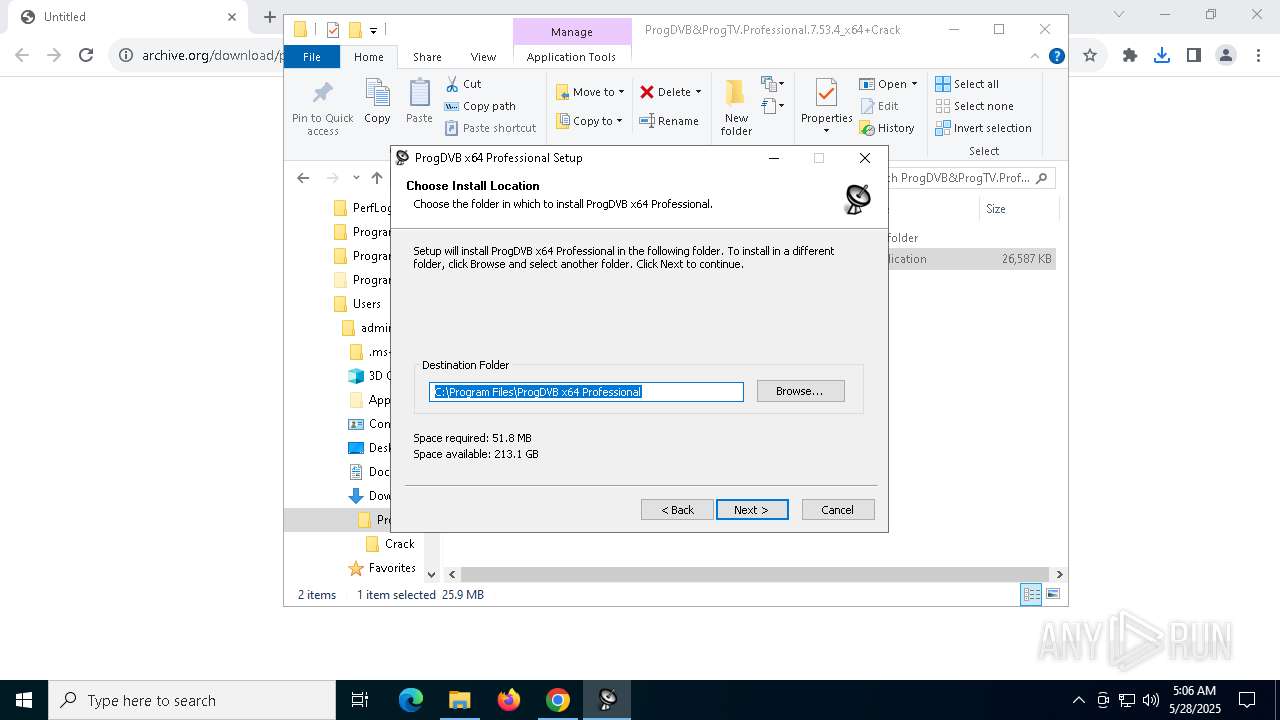
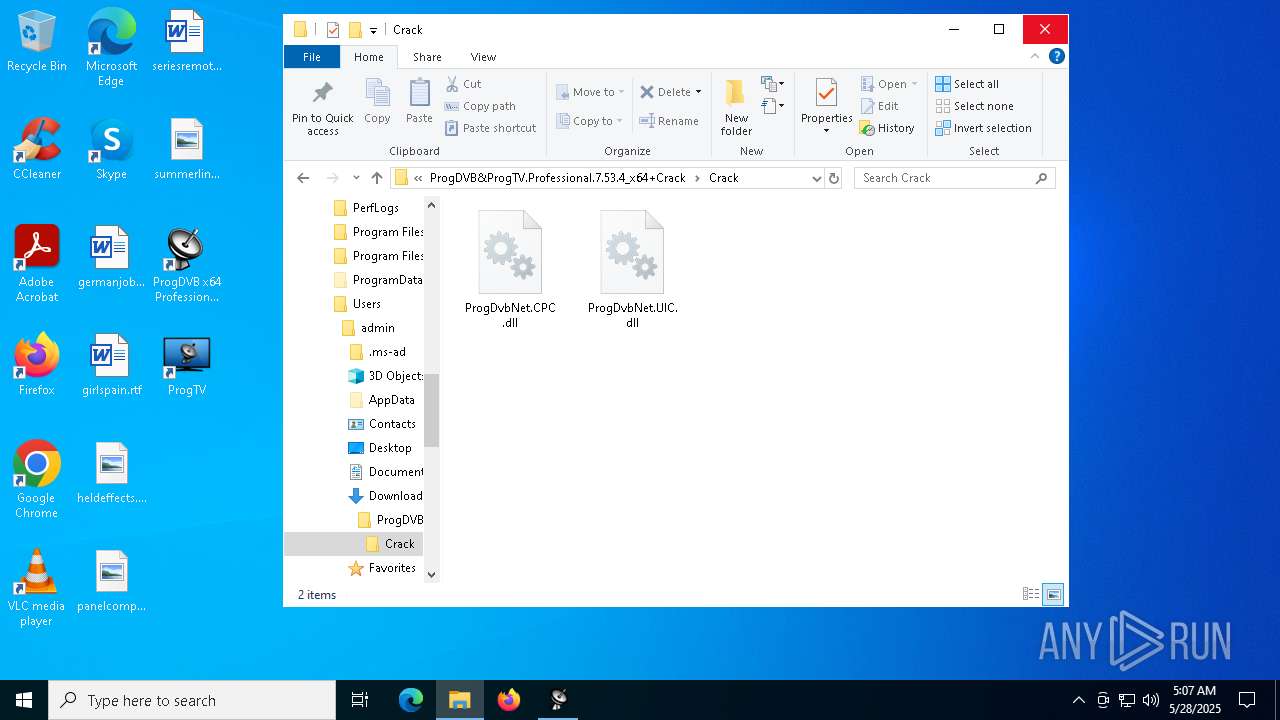
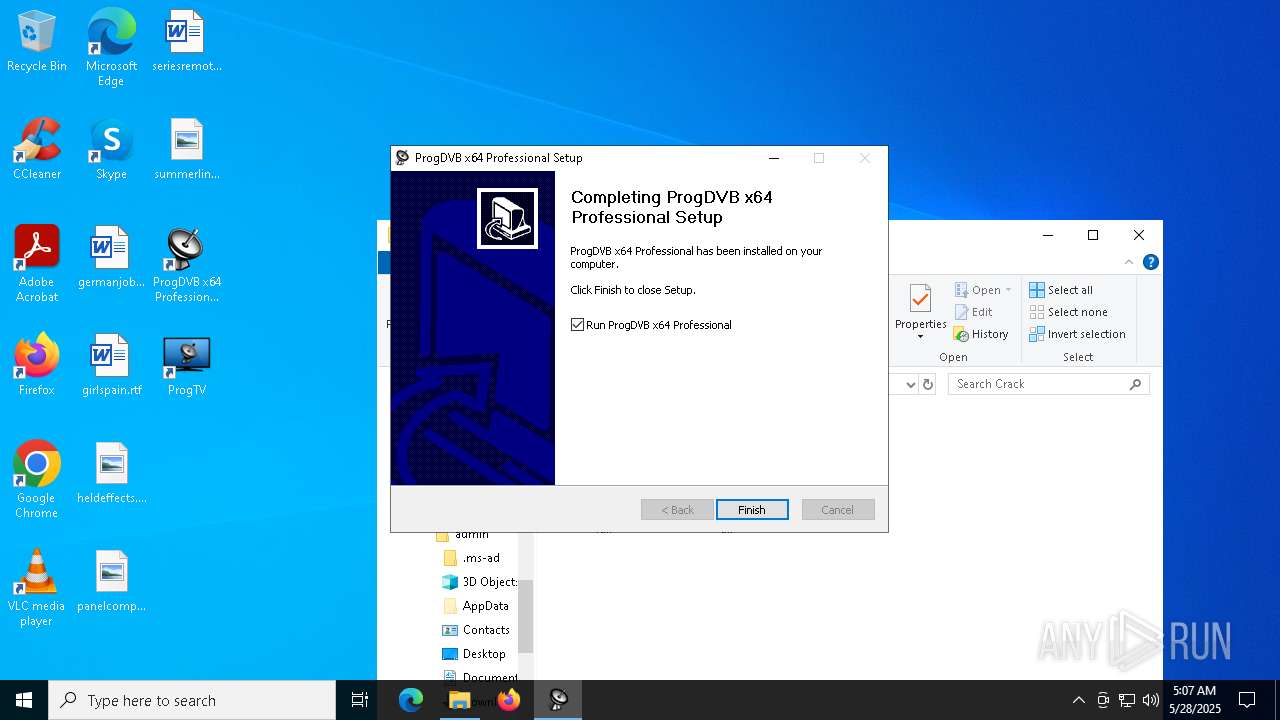
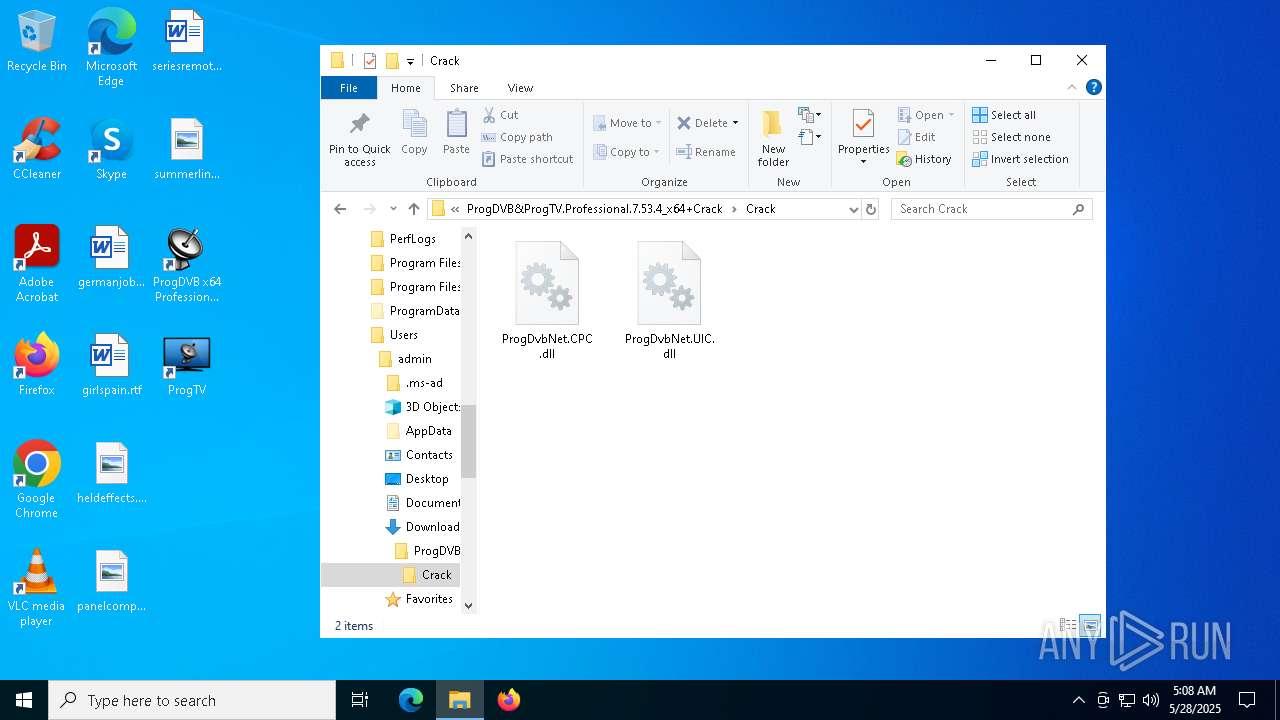
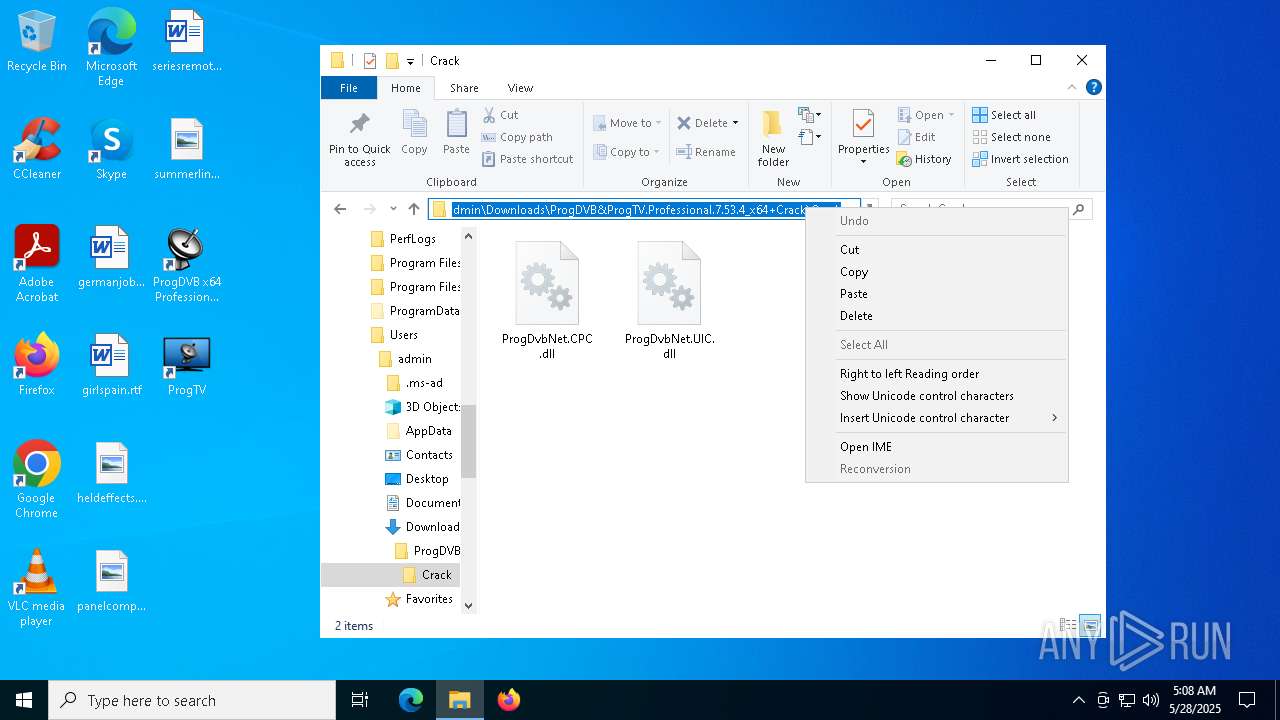
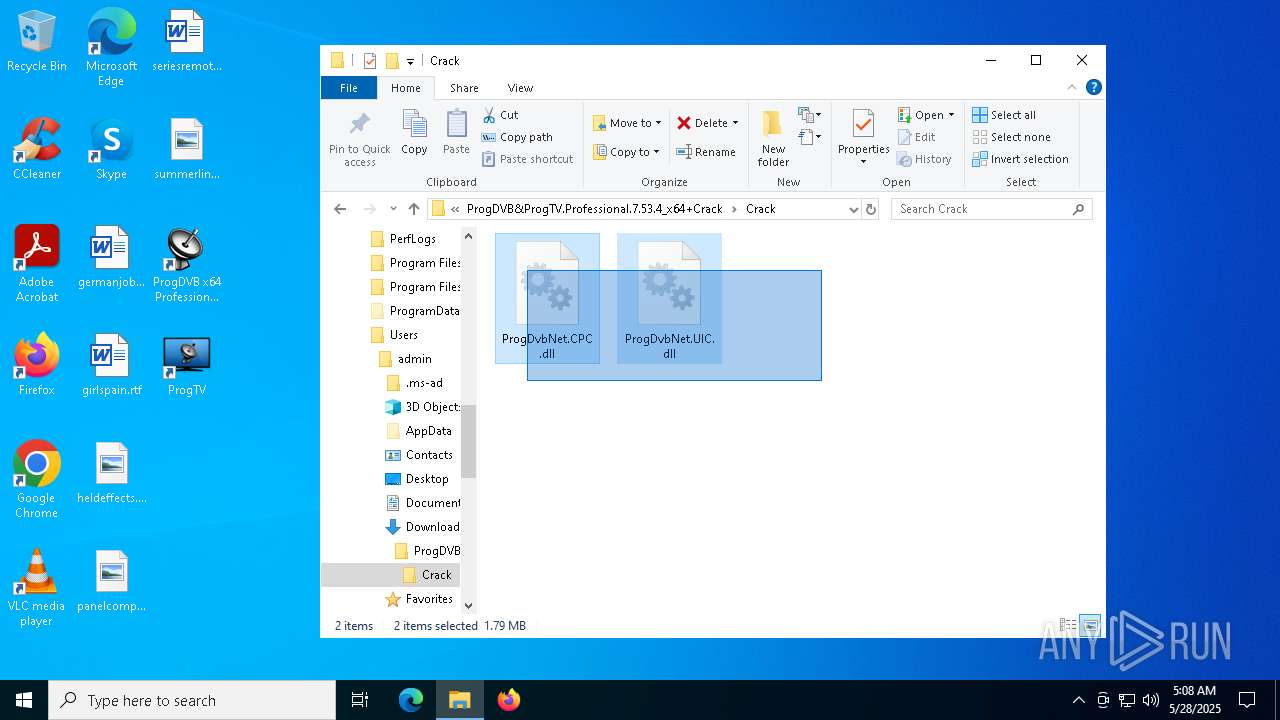
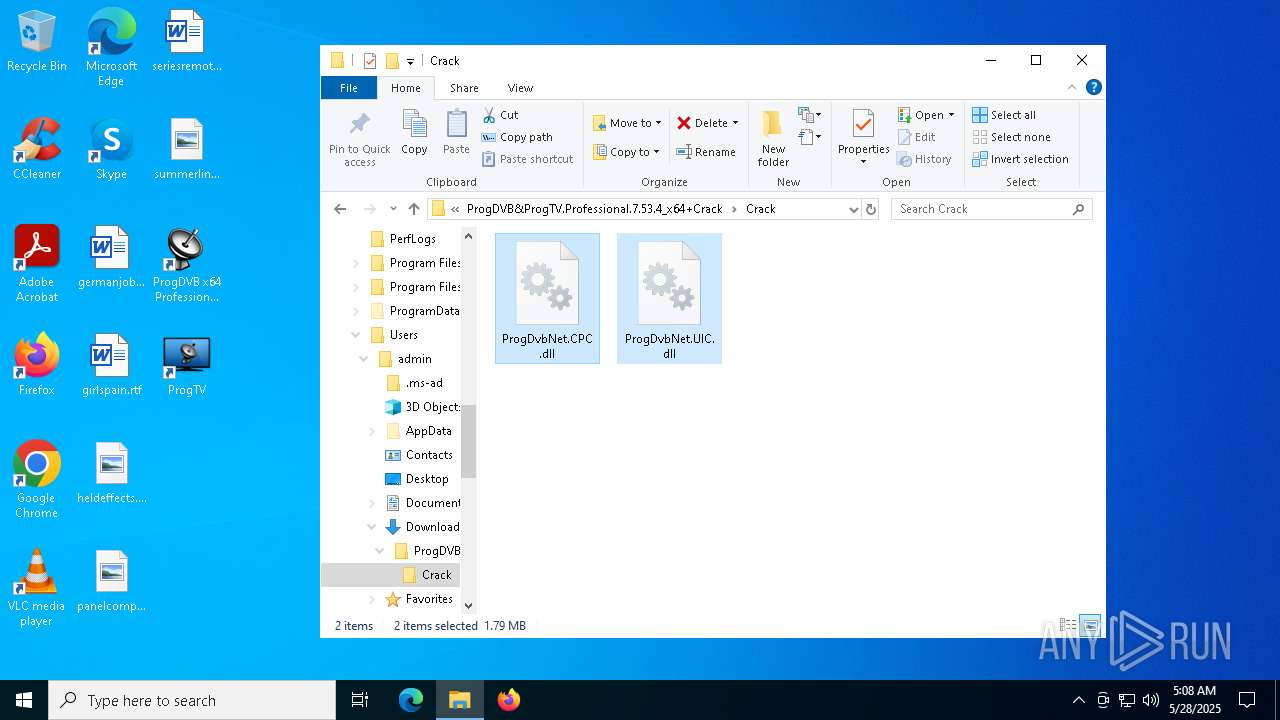
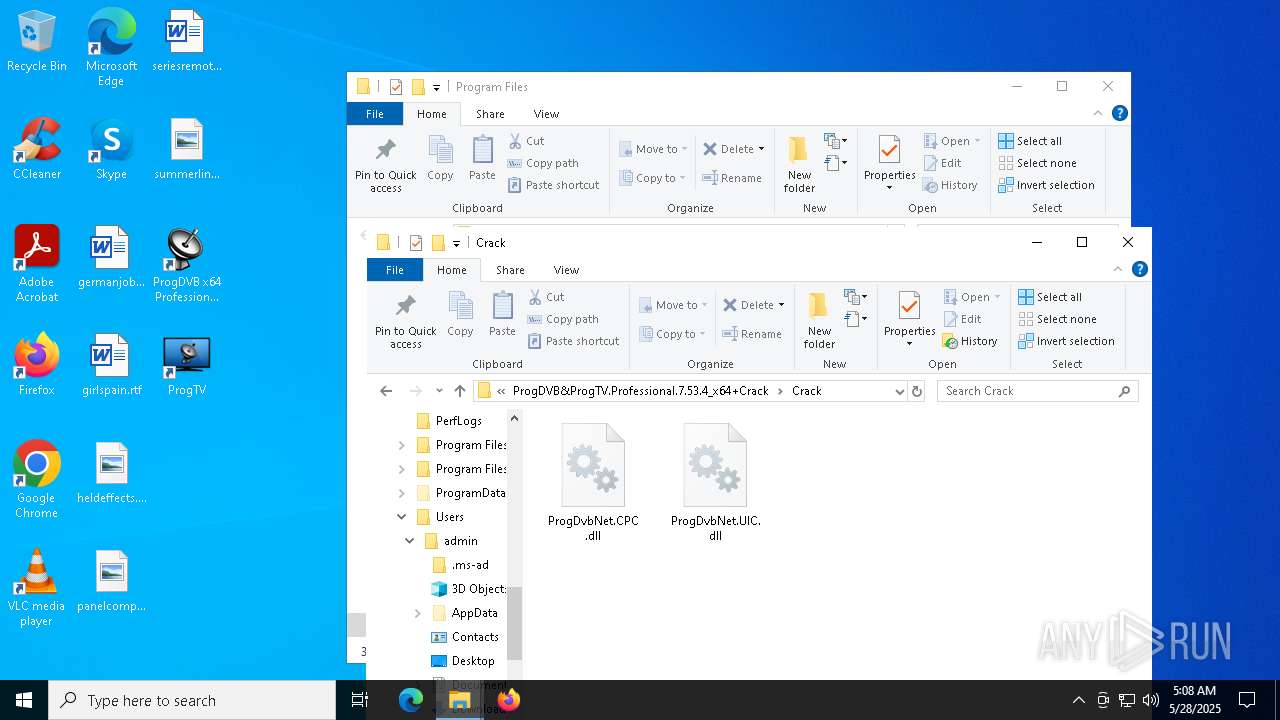
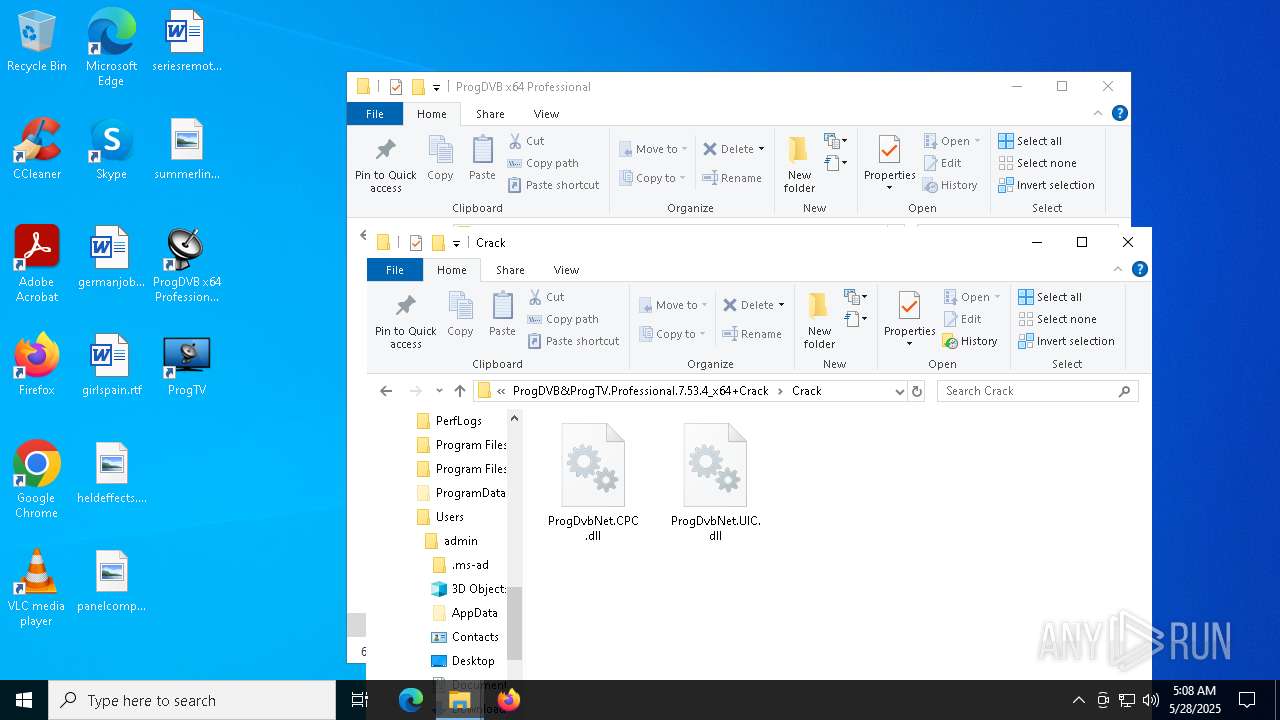
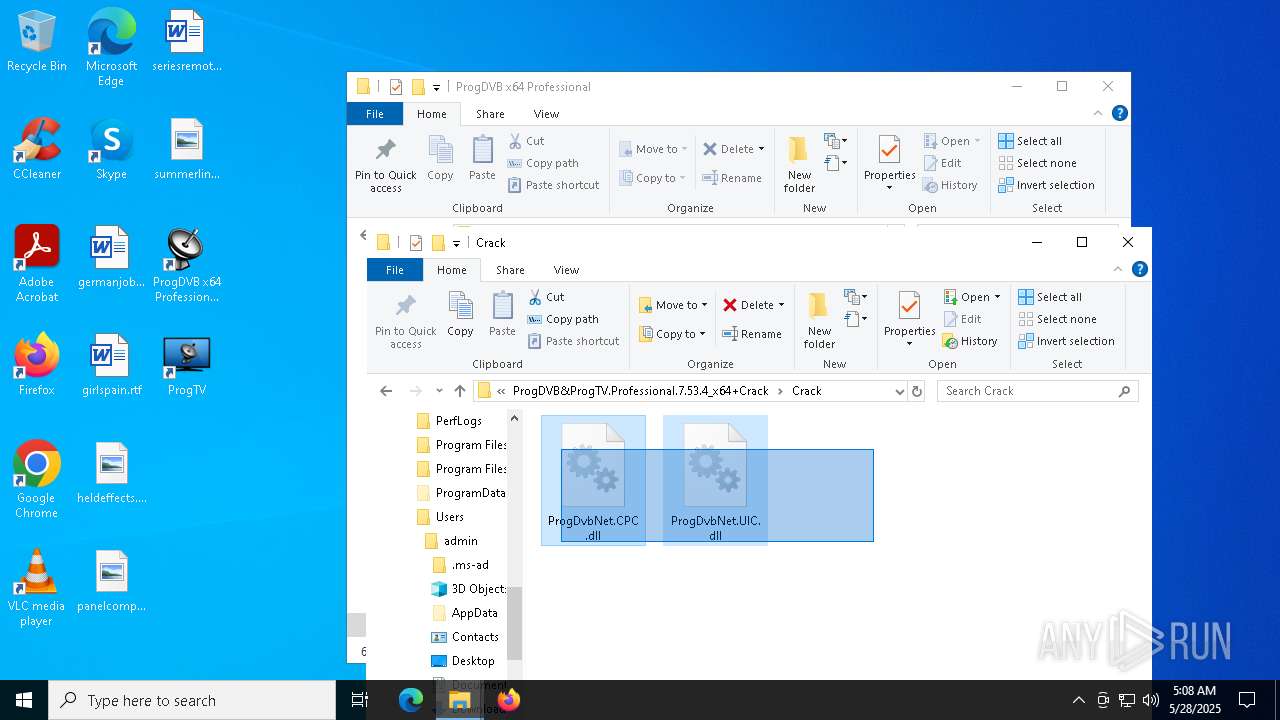
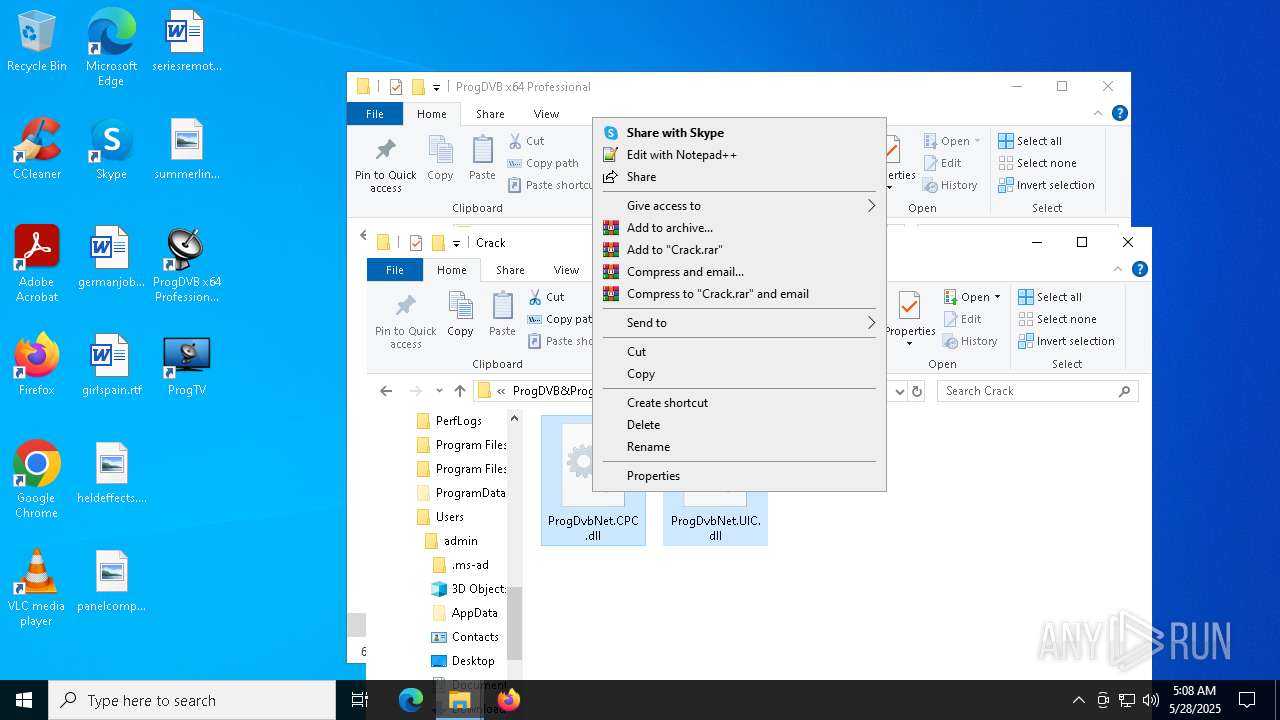
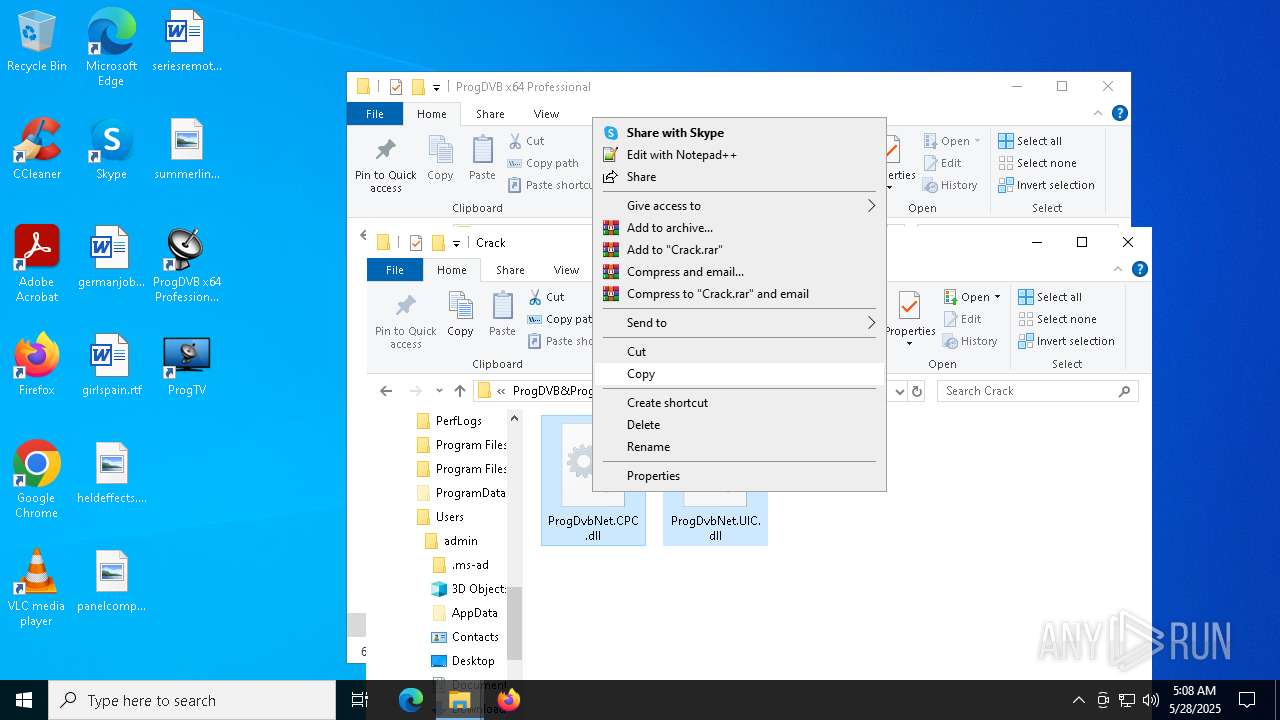
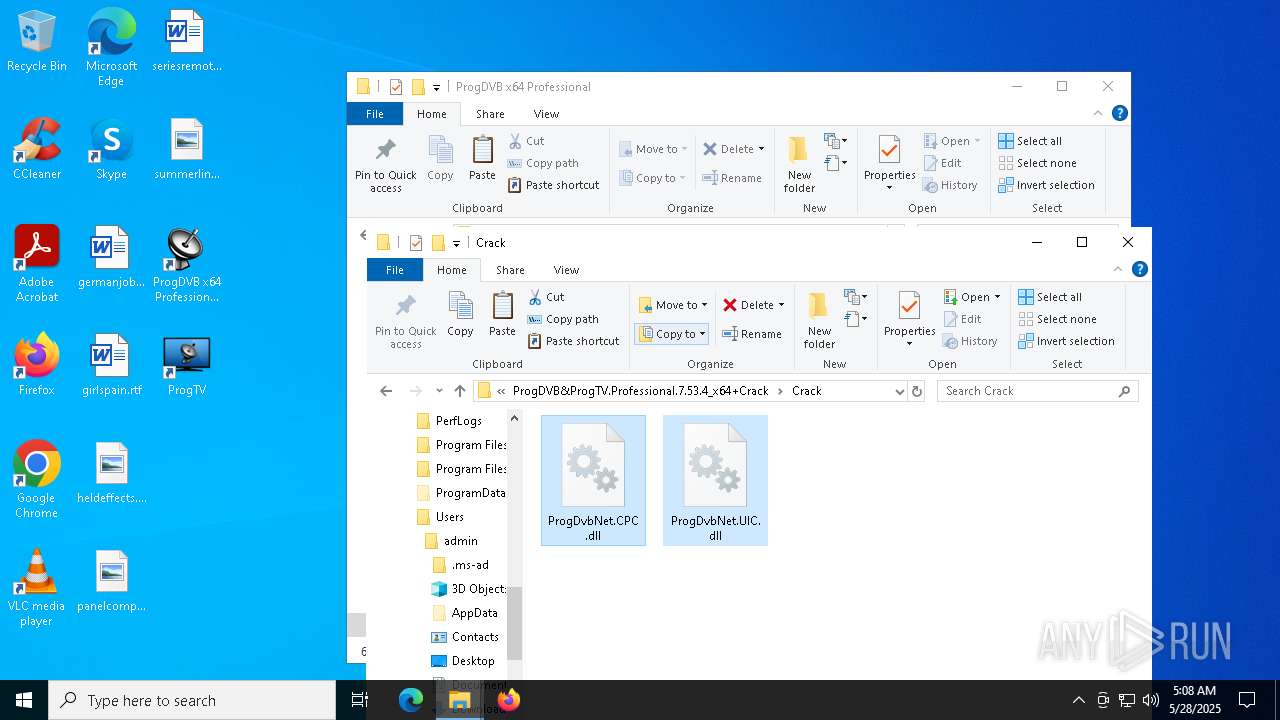
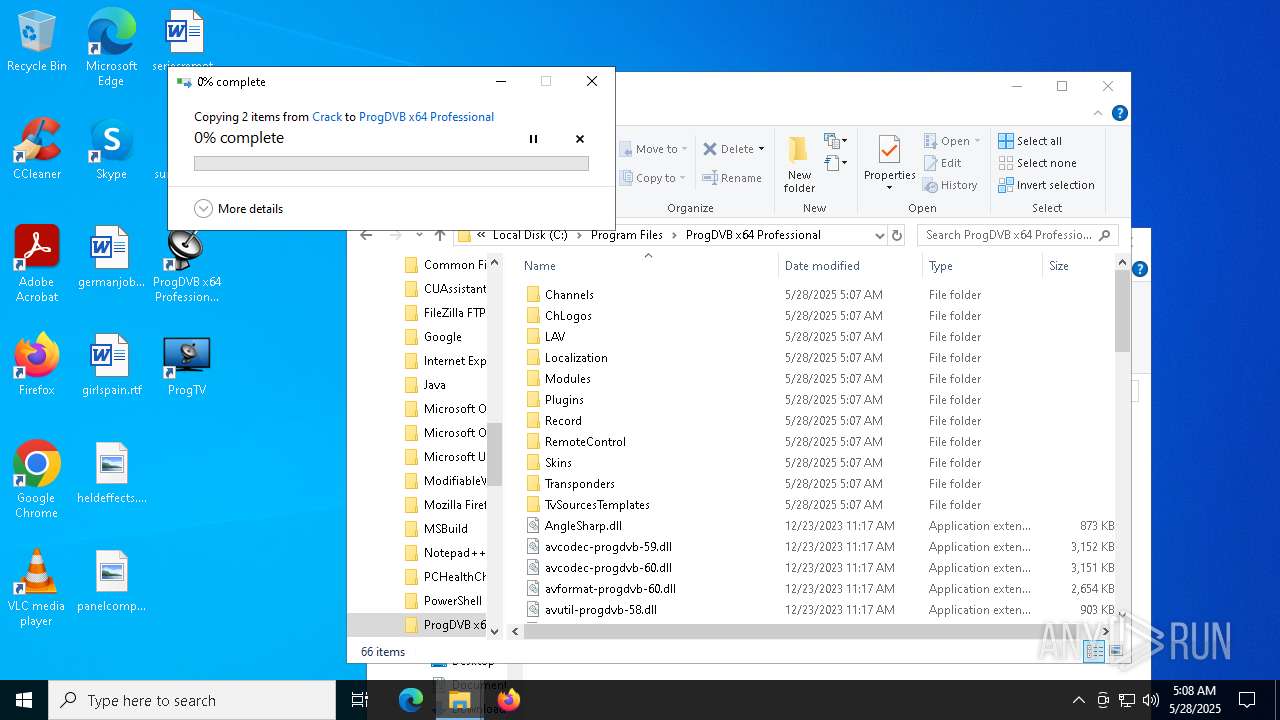
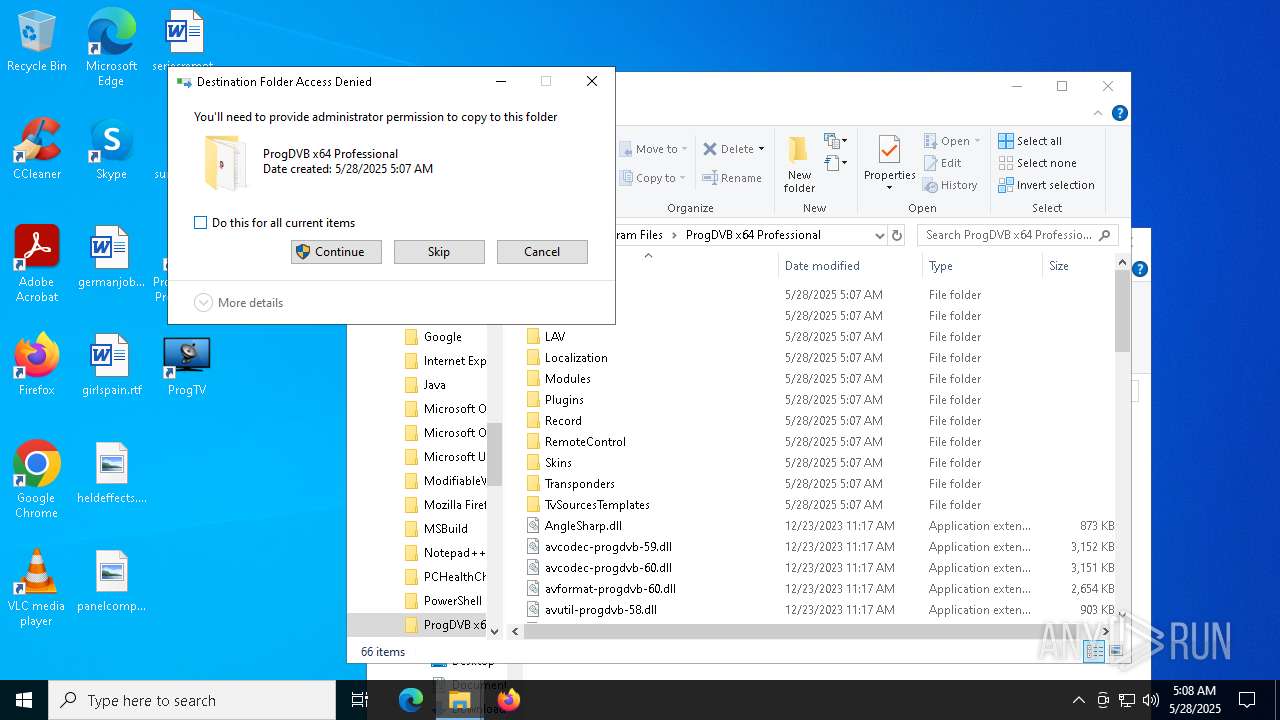
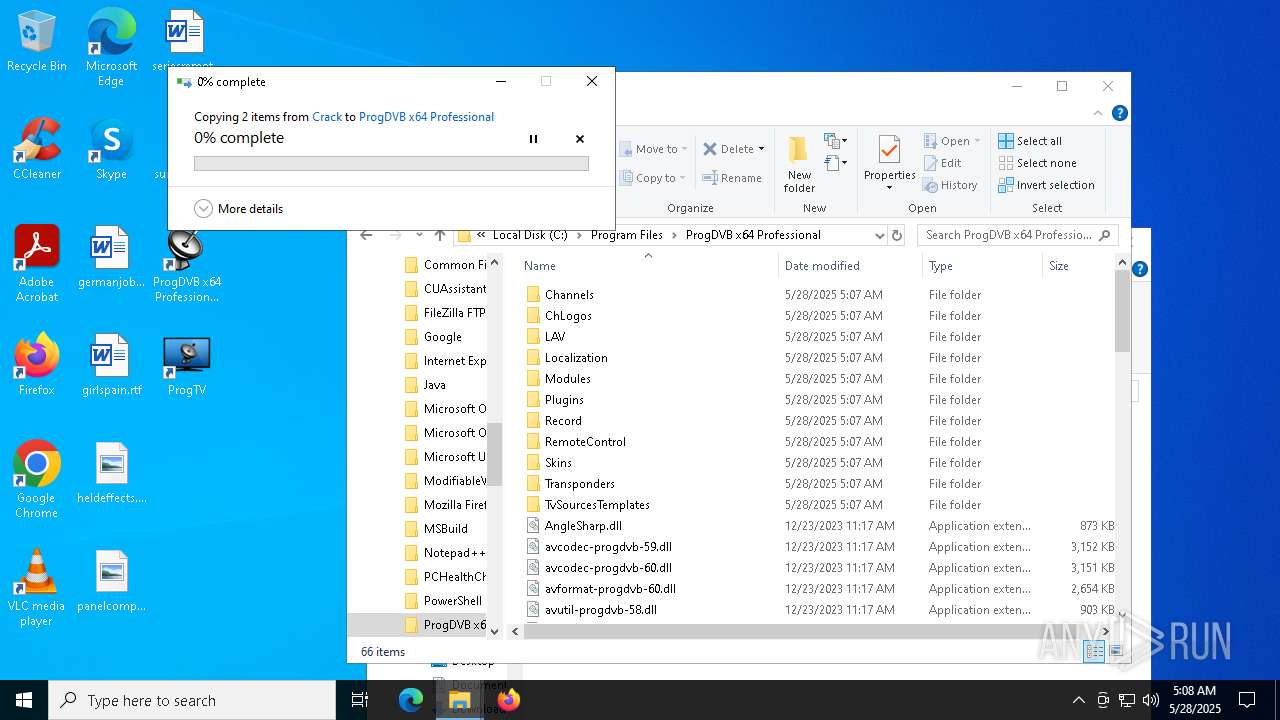
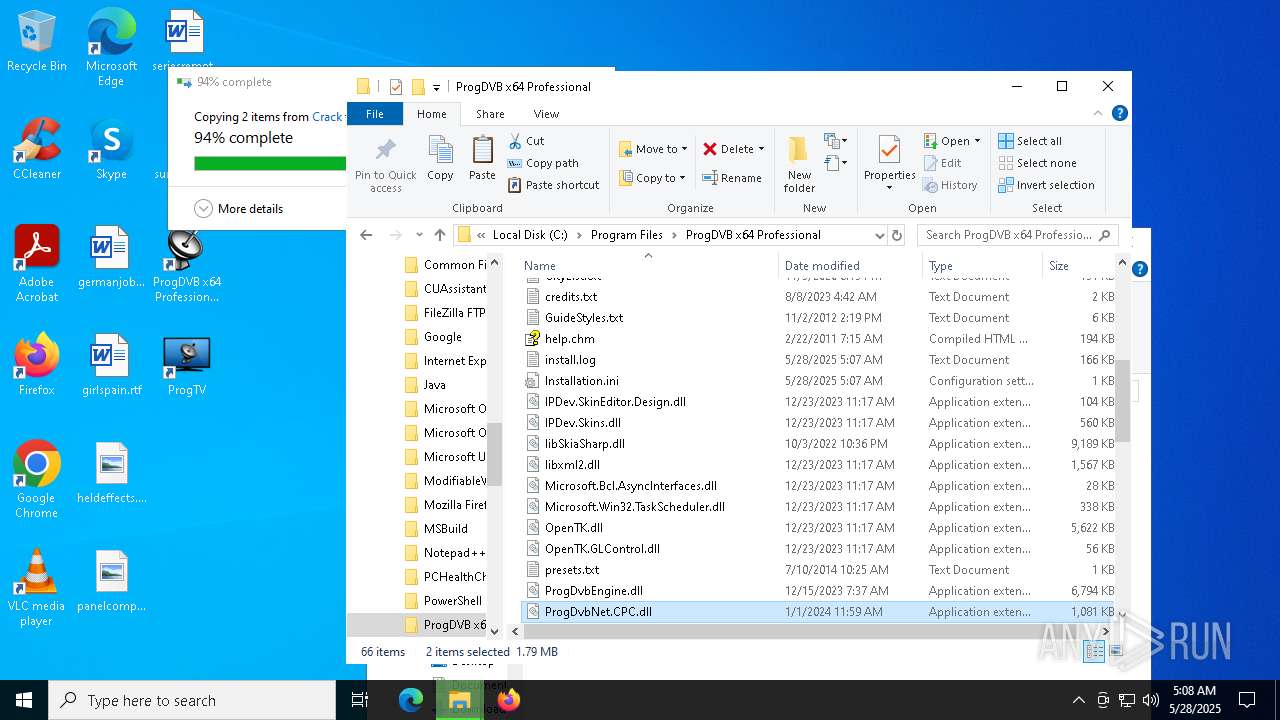
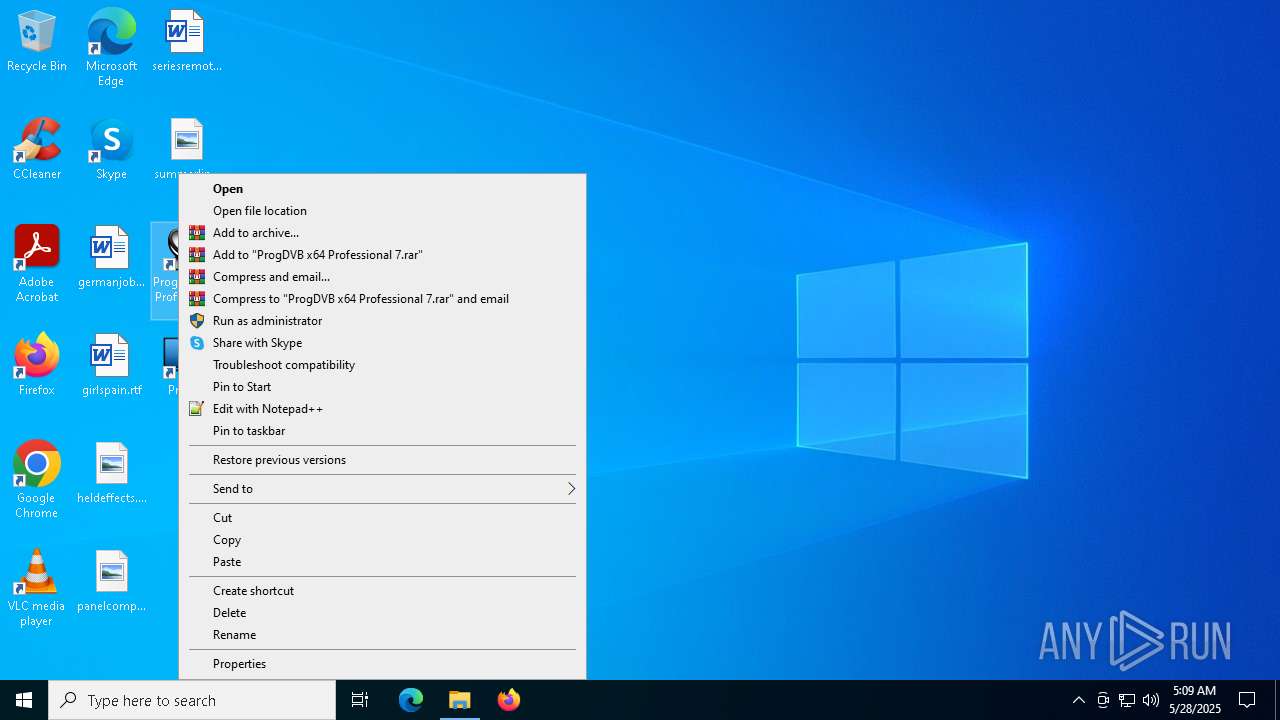
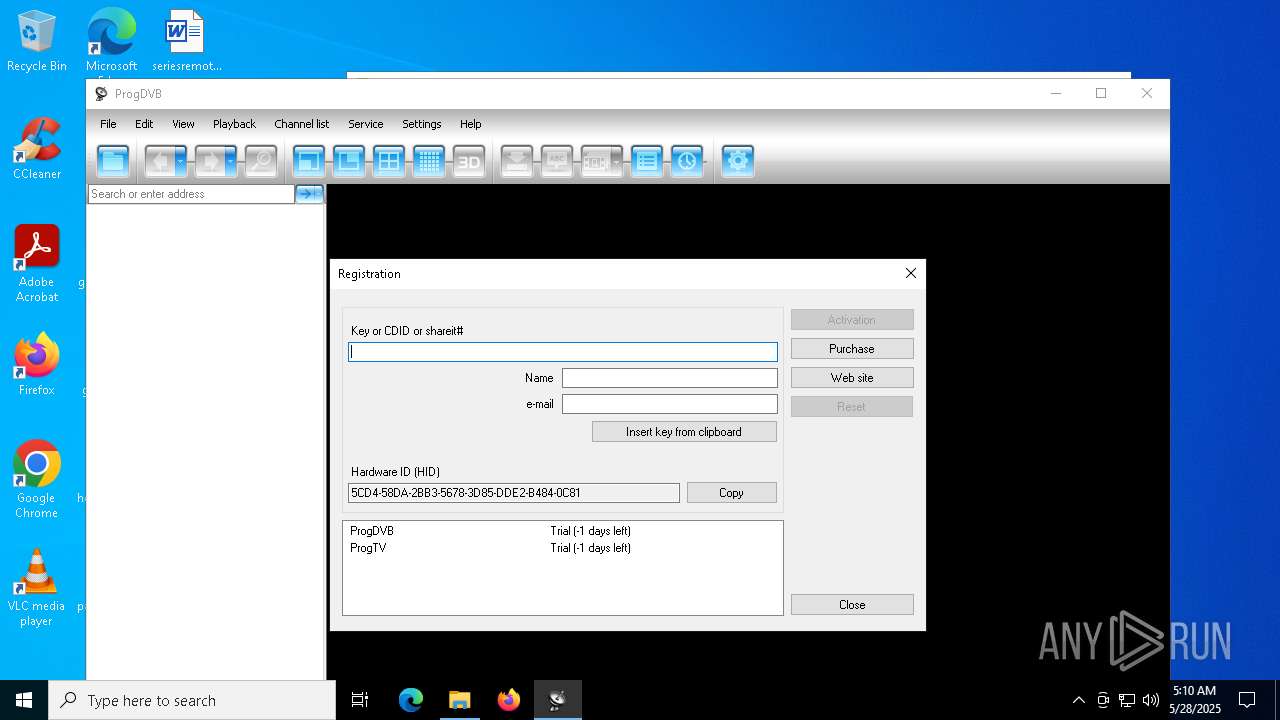
Manual execution by a user
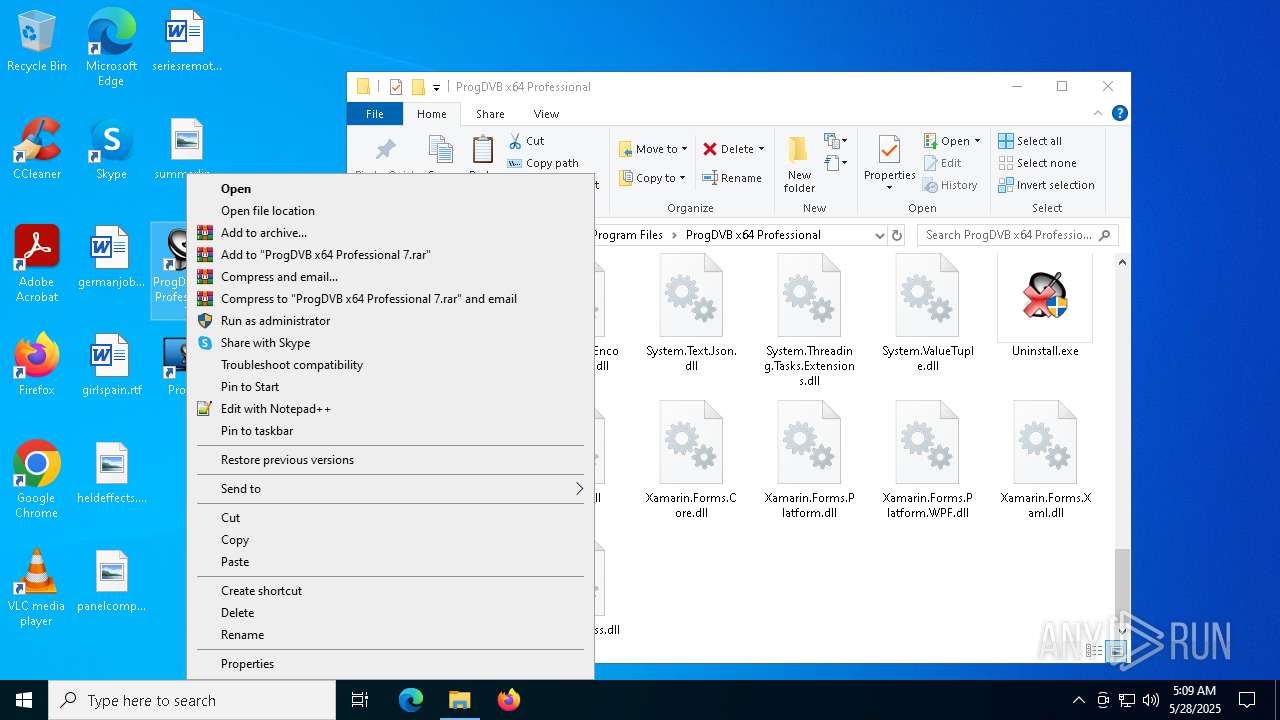
- WinRAR.exe (PID: 7944)
- ProgDVB7.53.4x64Pro.exe (PID: 1276)
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
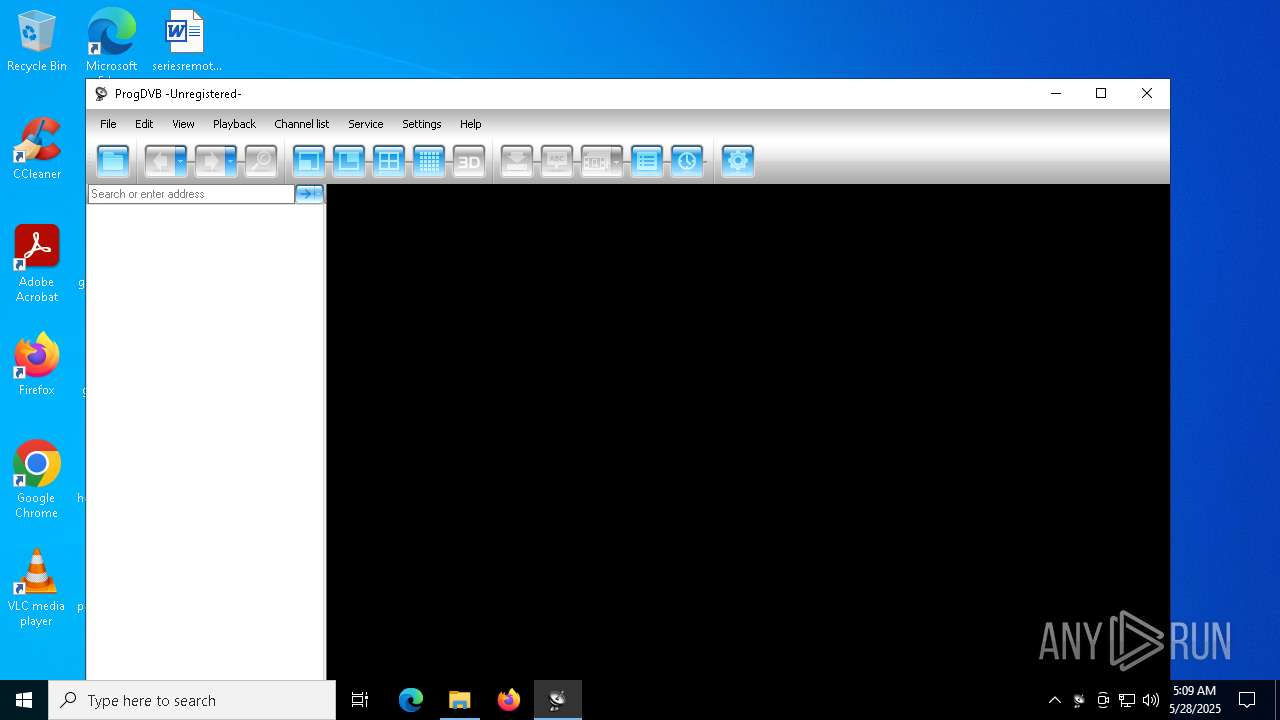
- ProgDvbNet.exe (PID: 7368)
- ProgDvbNet.exe (PID: 7808)
- ProgDvbNet.exe (PID: 1616)
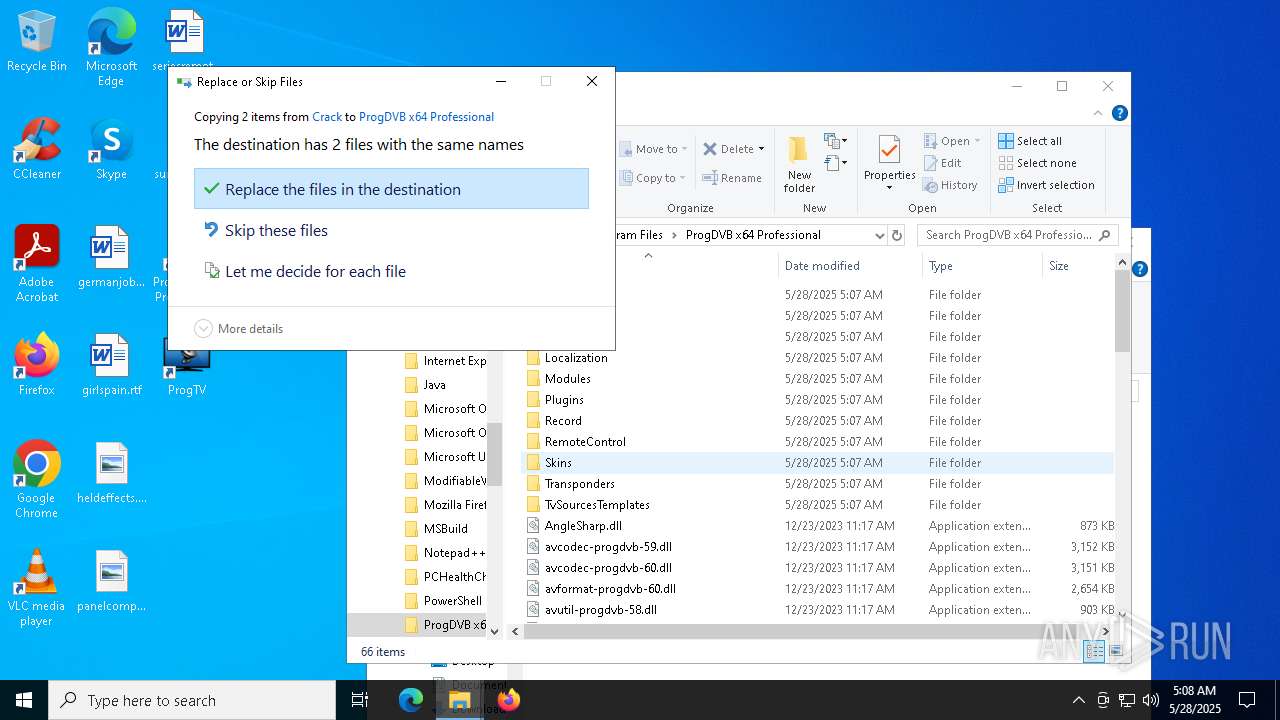
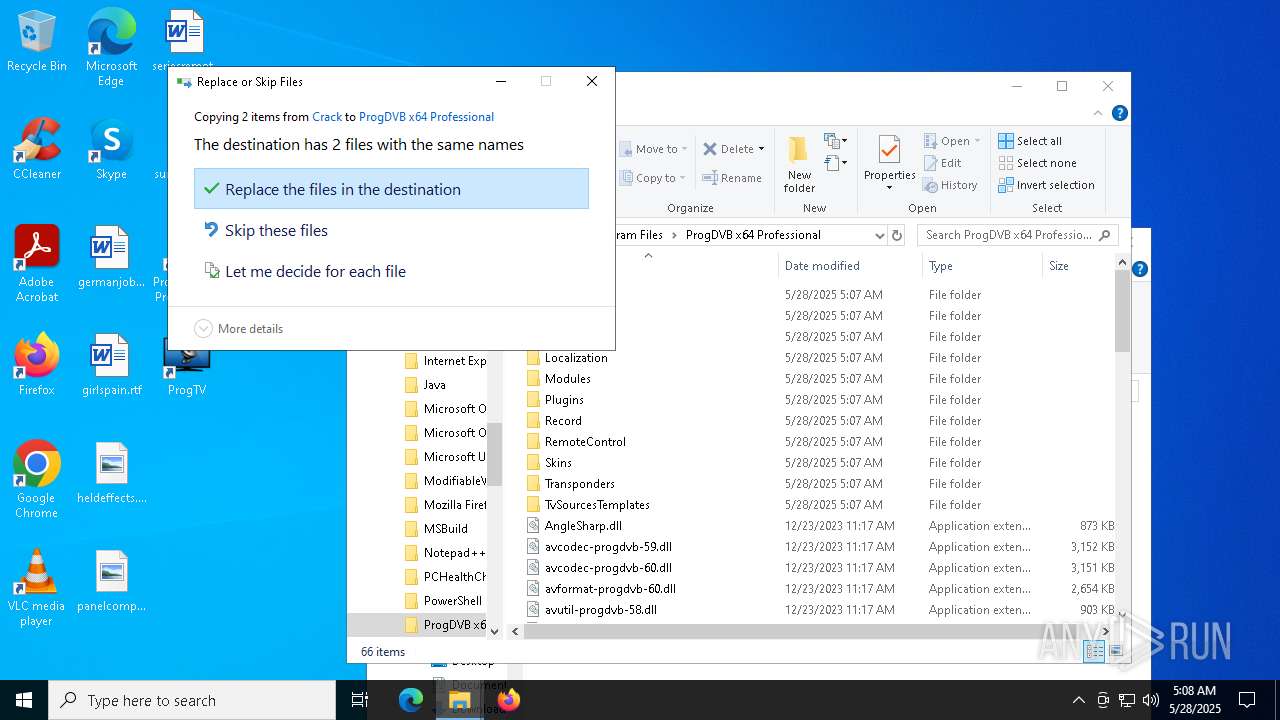
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7944)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 736)
Reads the software policy settings
- slui.exe (PID: 7792)
Create files in a temporary directory
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
Checks supported languages
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
Reads the computer name
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
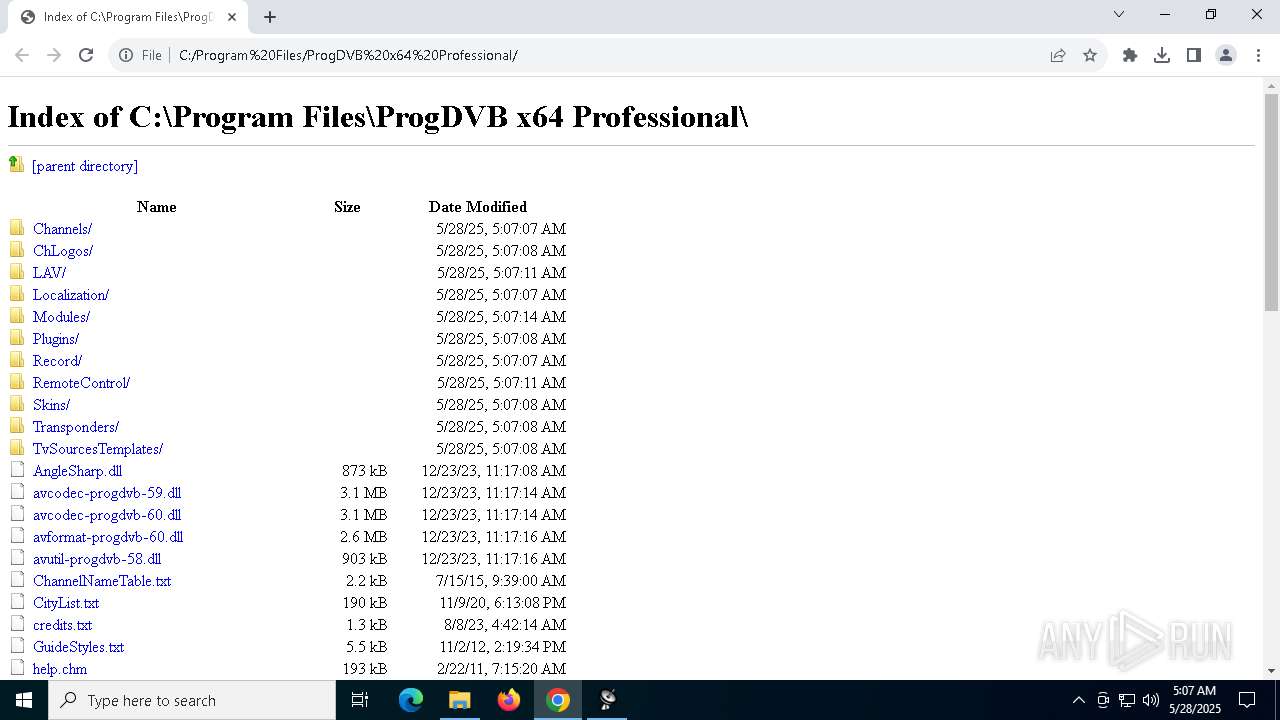
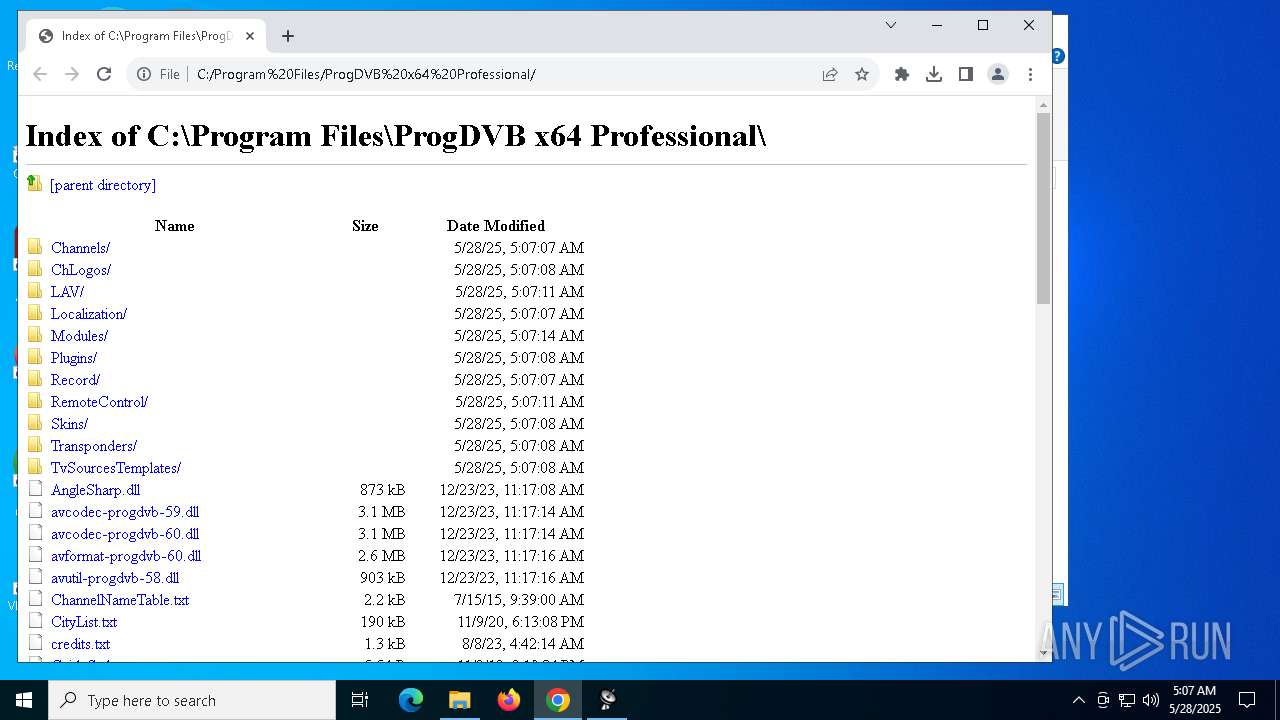
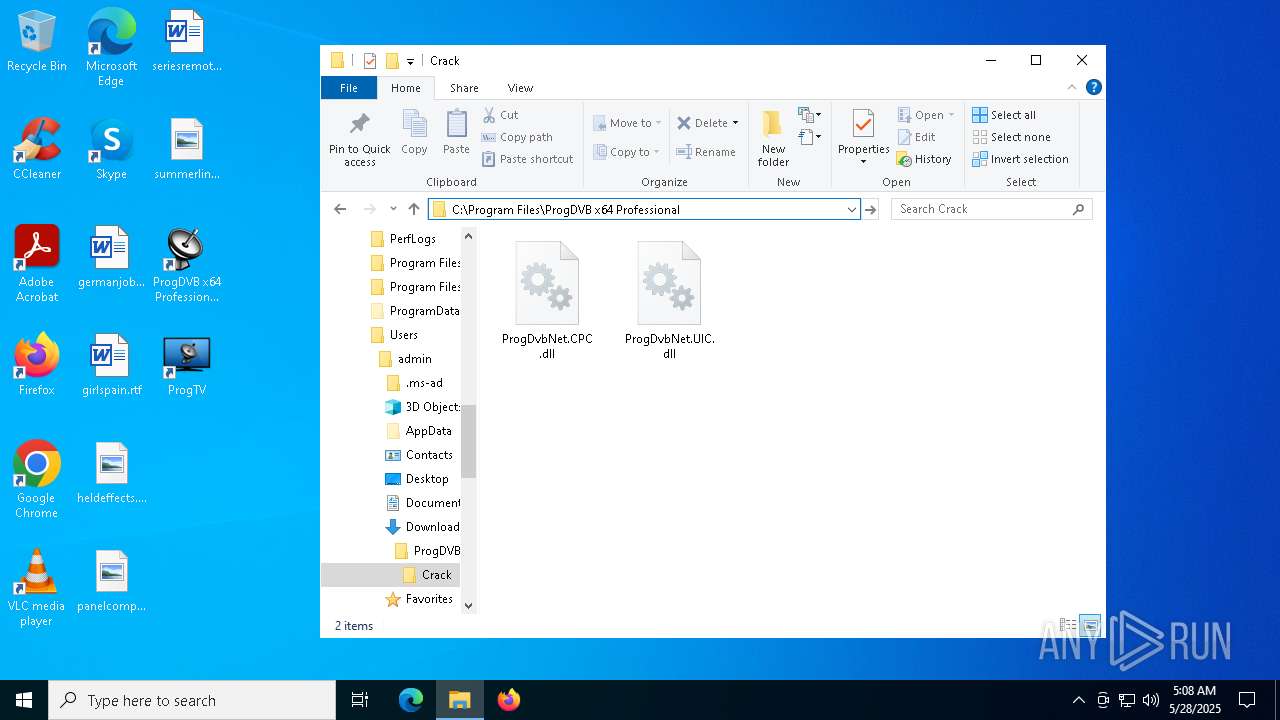
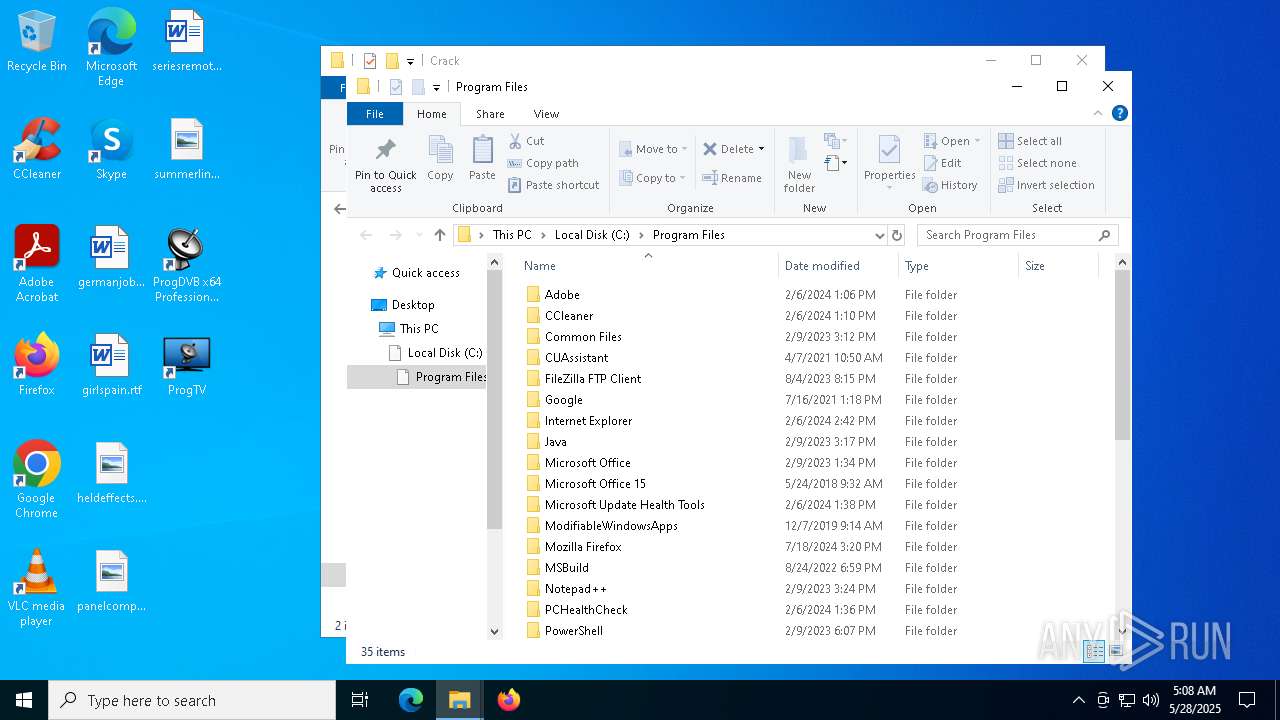
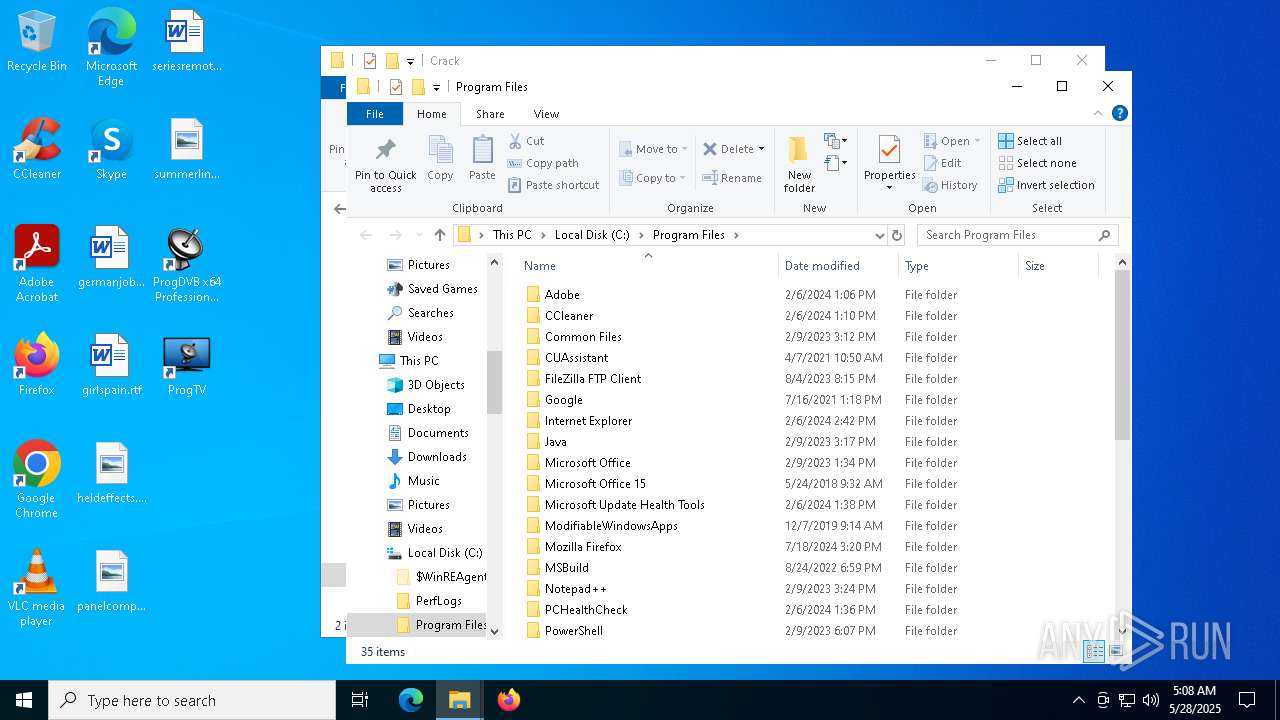
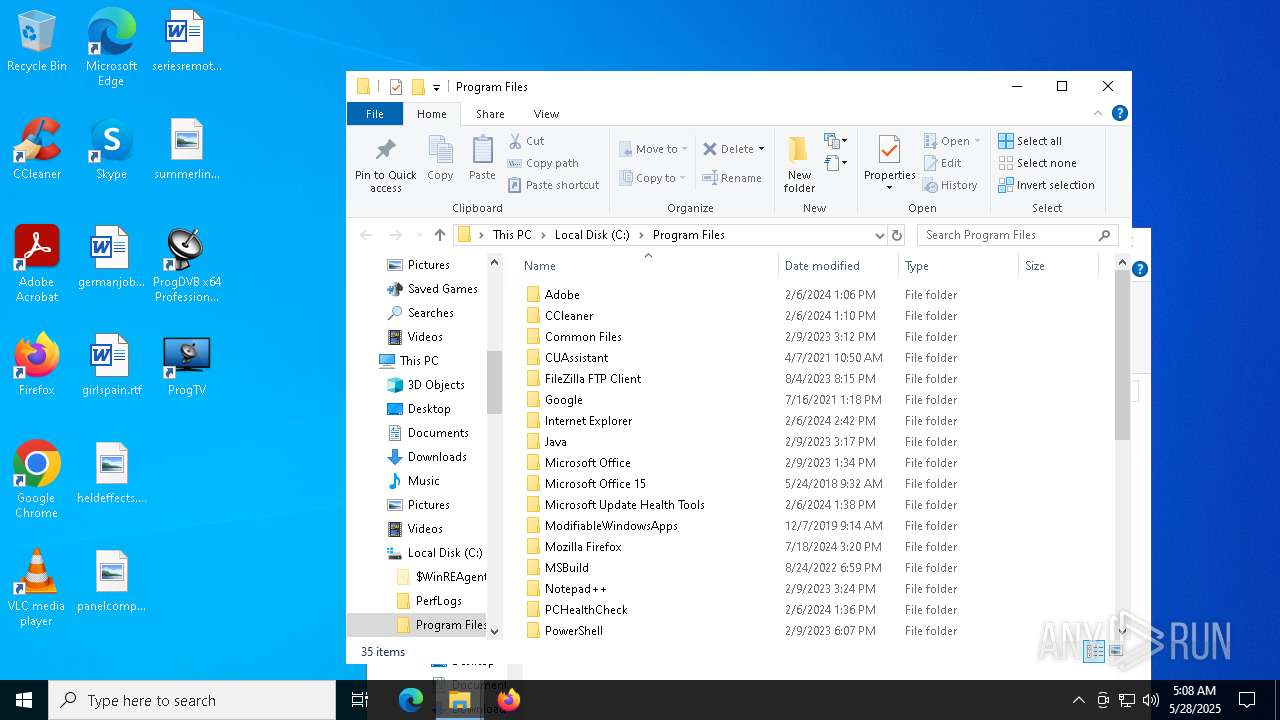
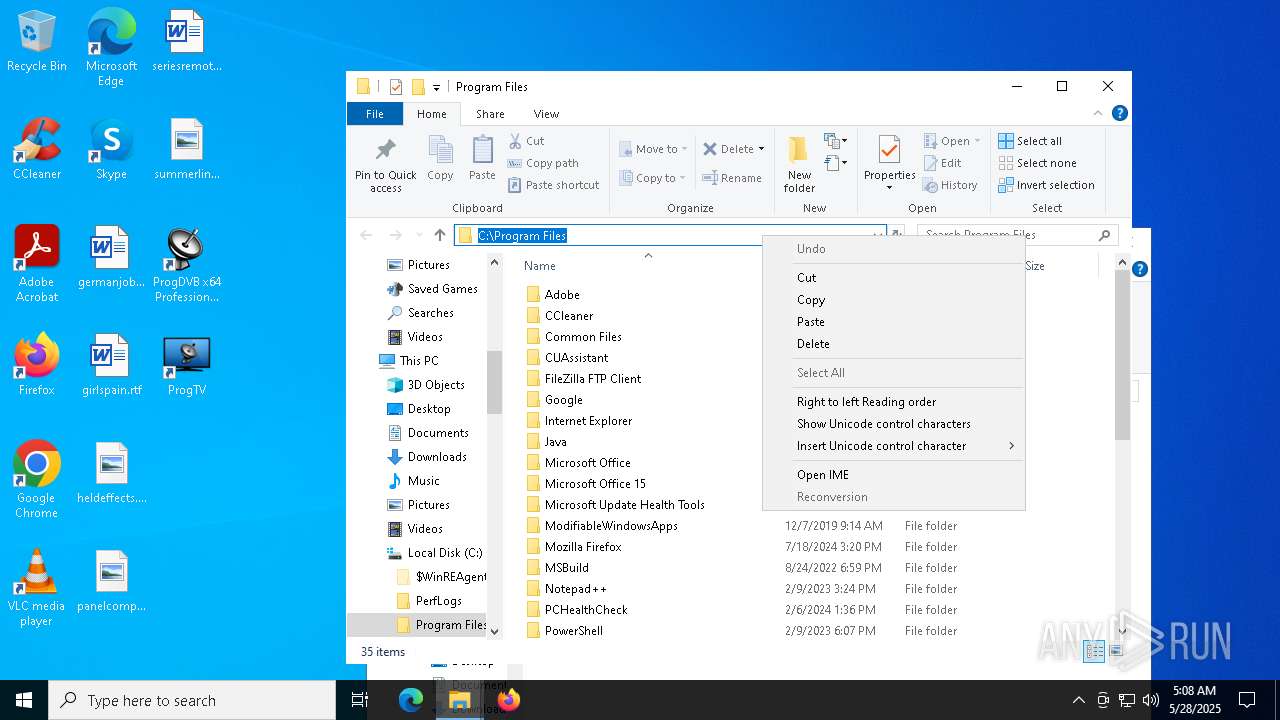
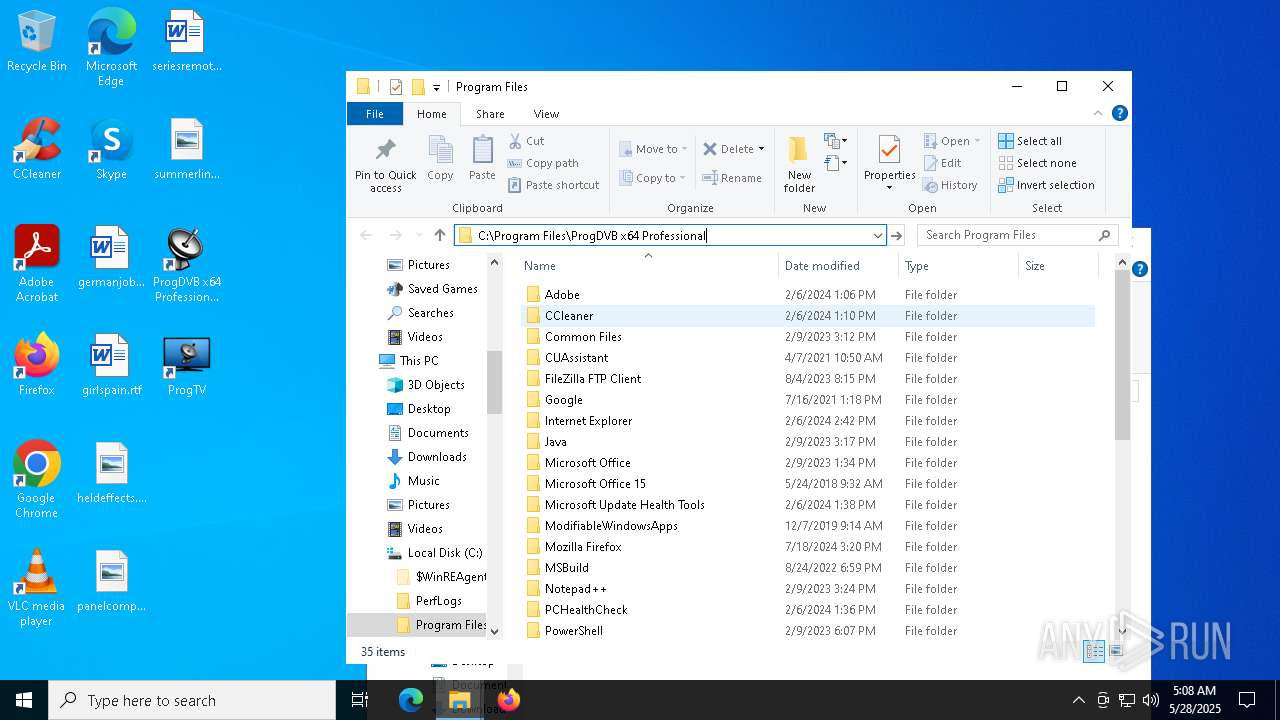
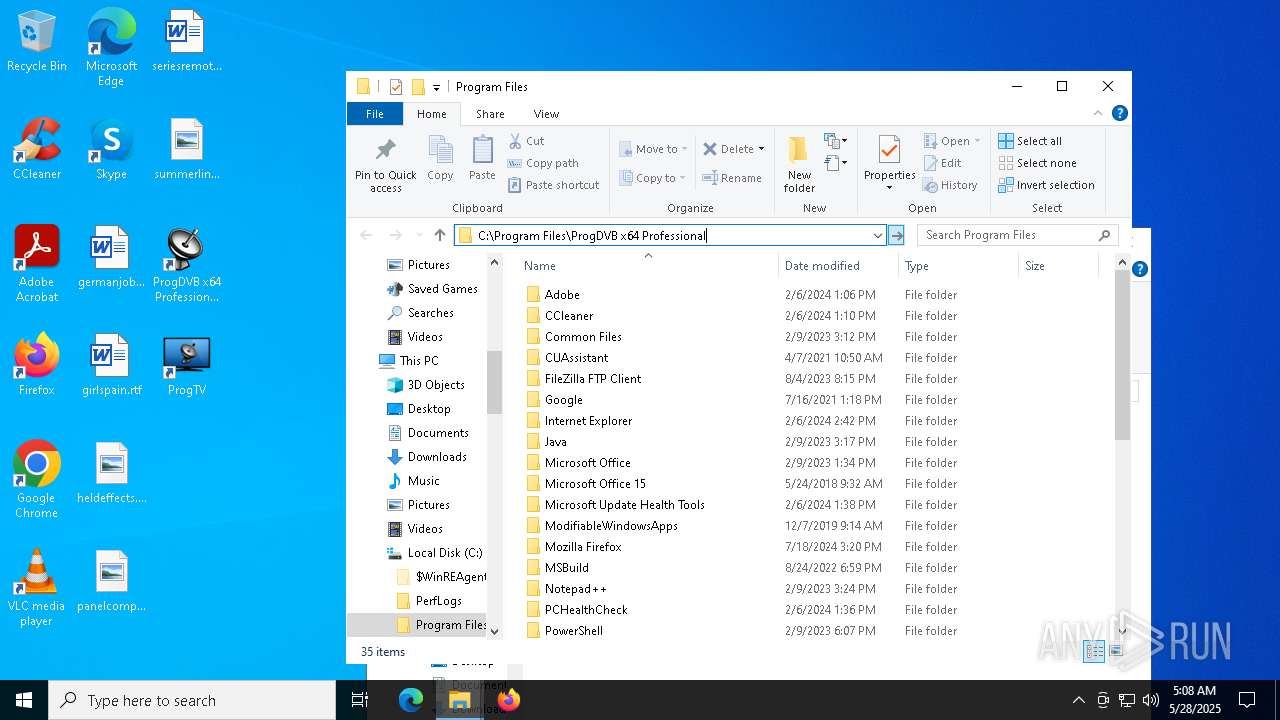
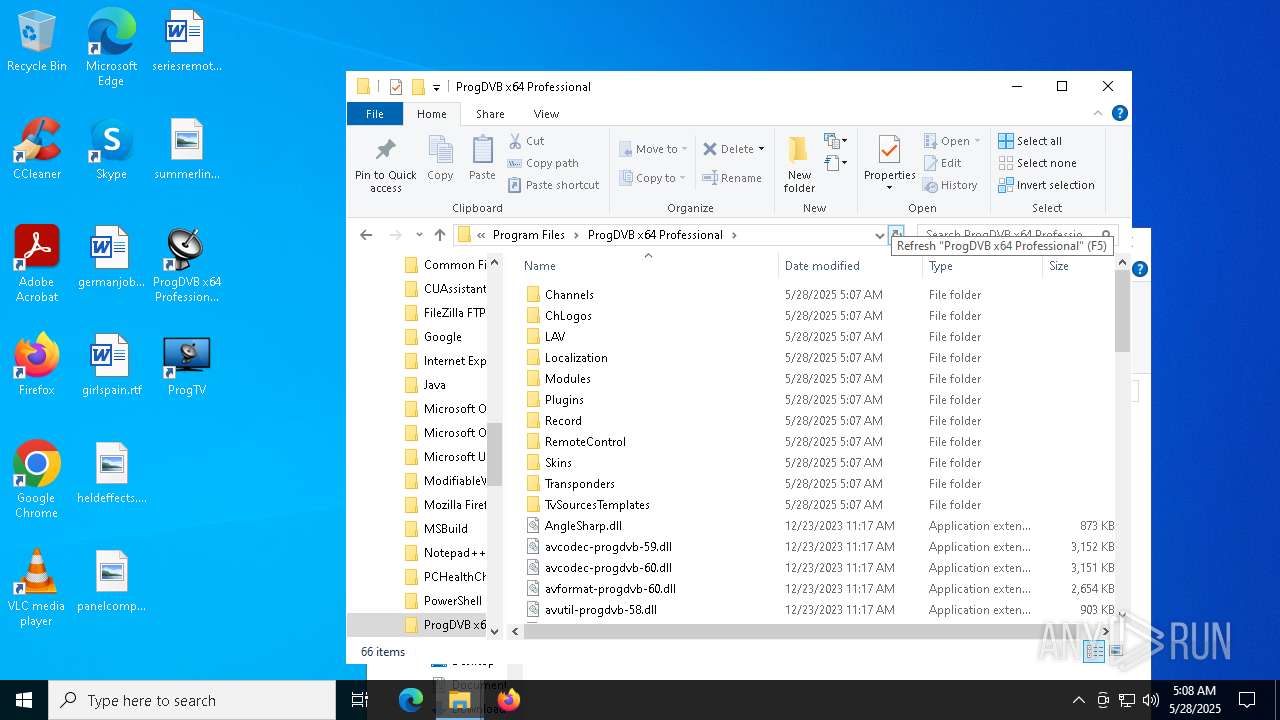
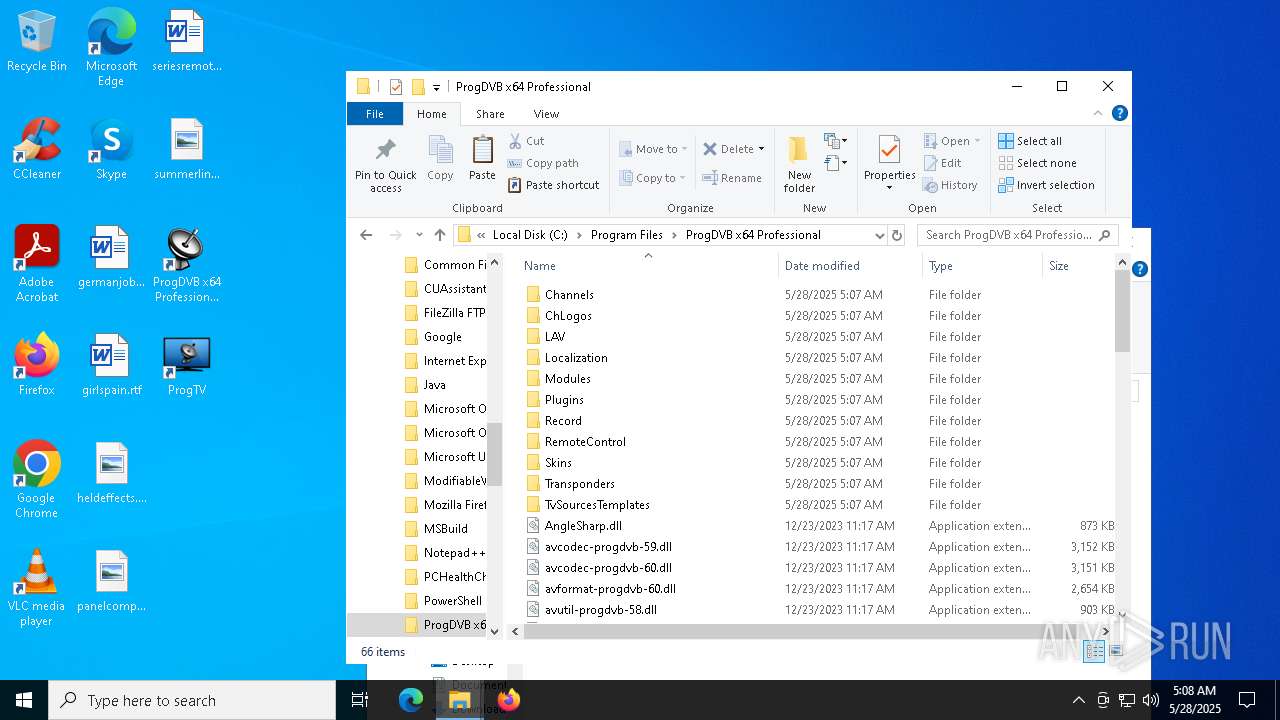
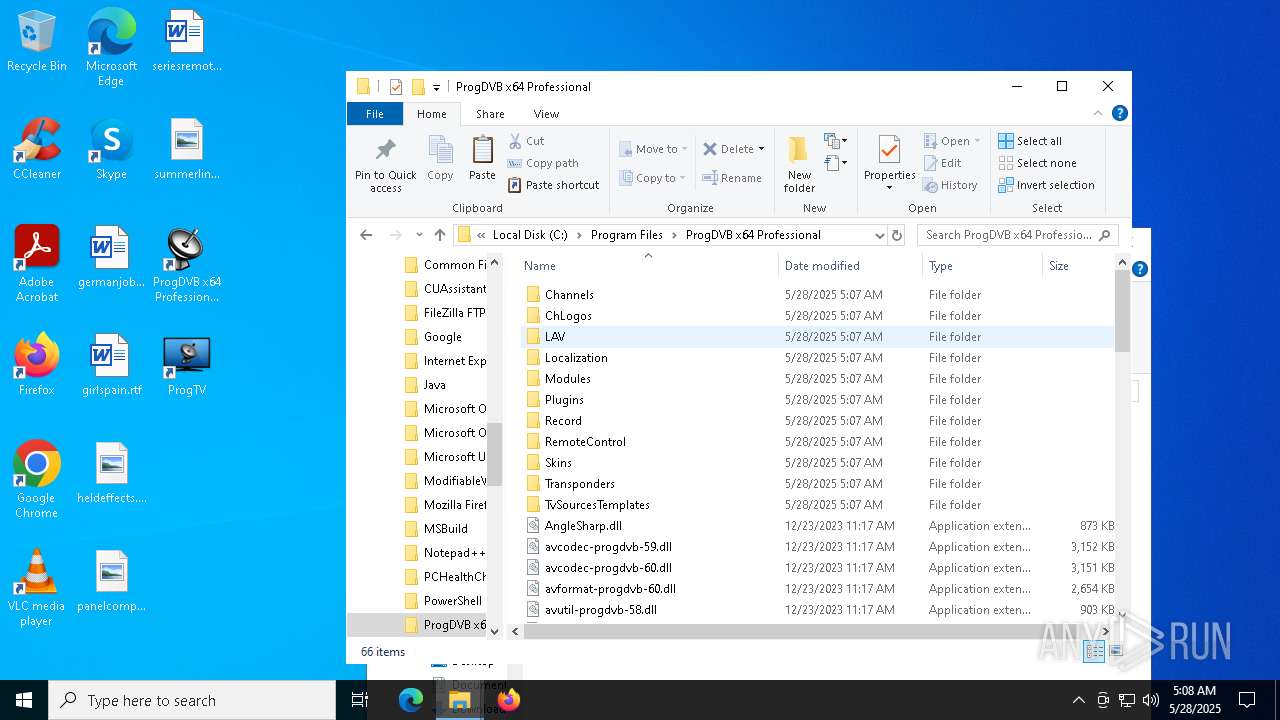
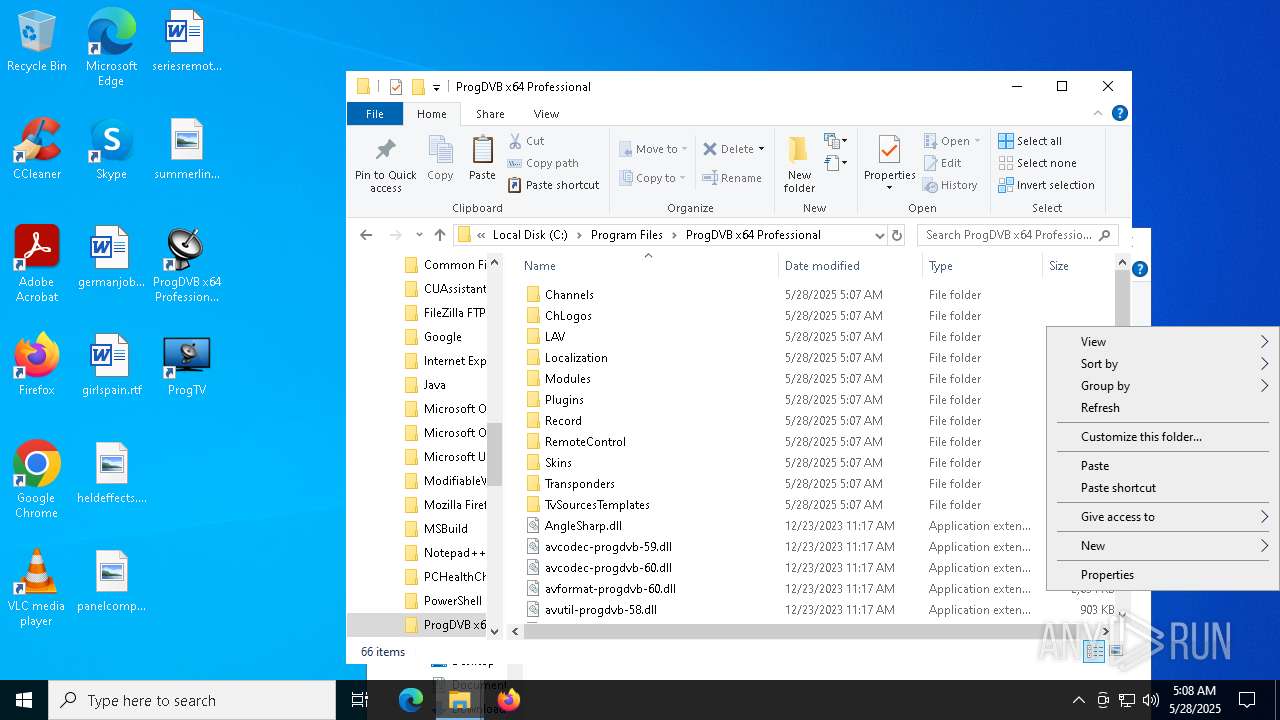
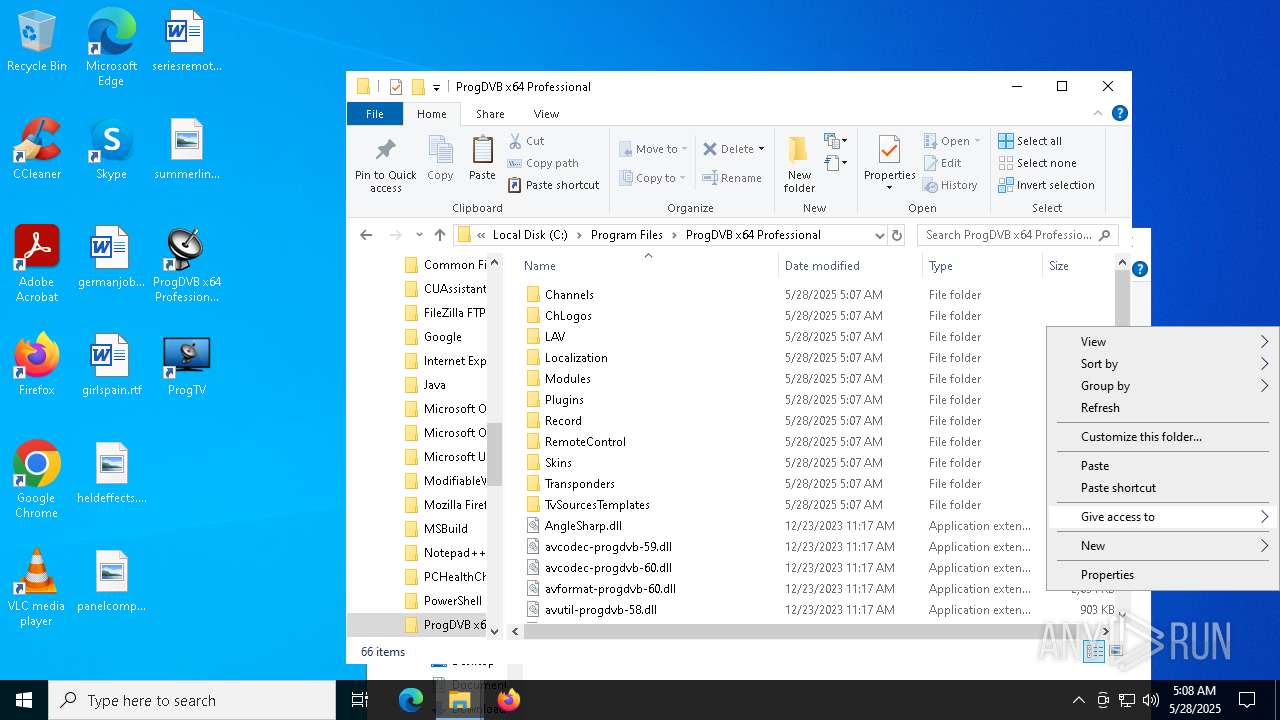
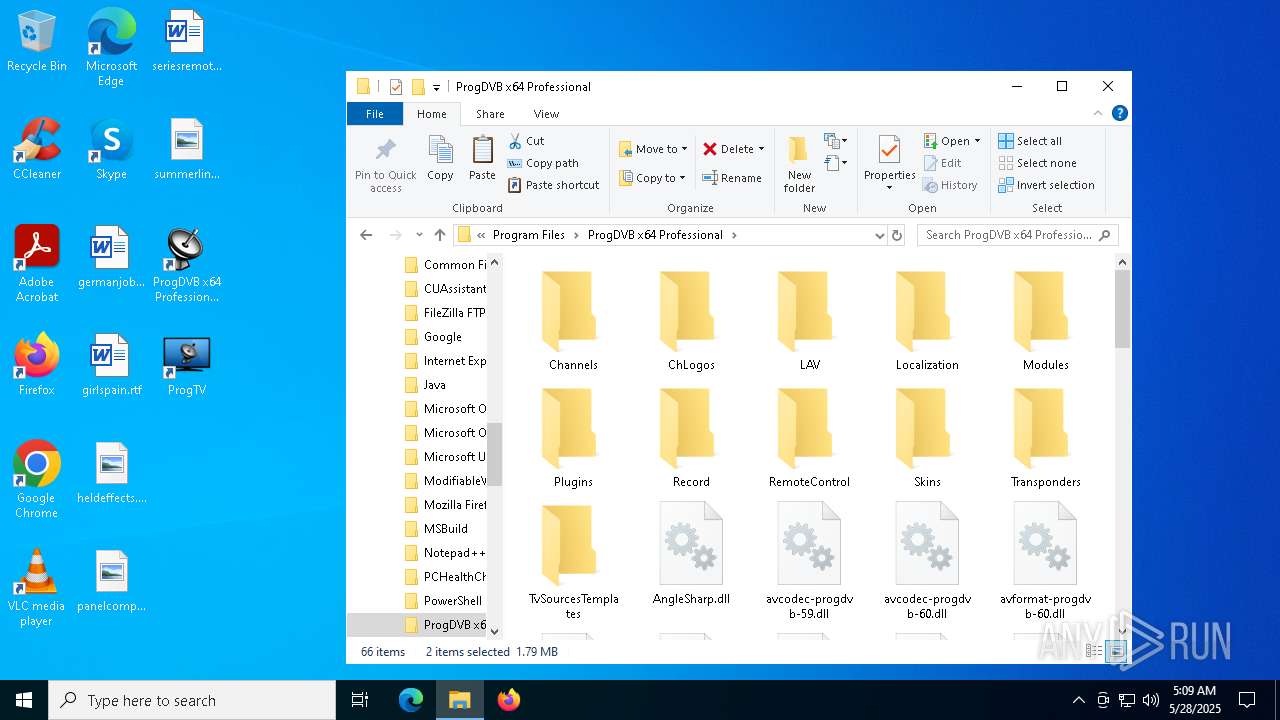
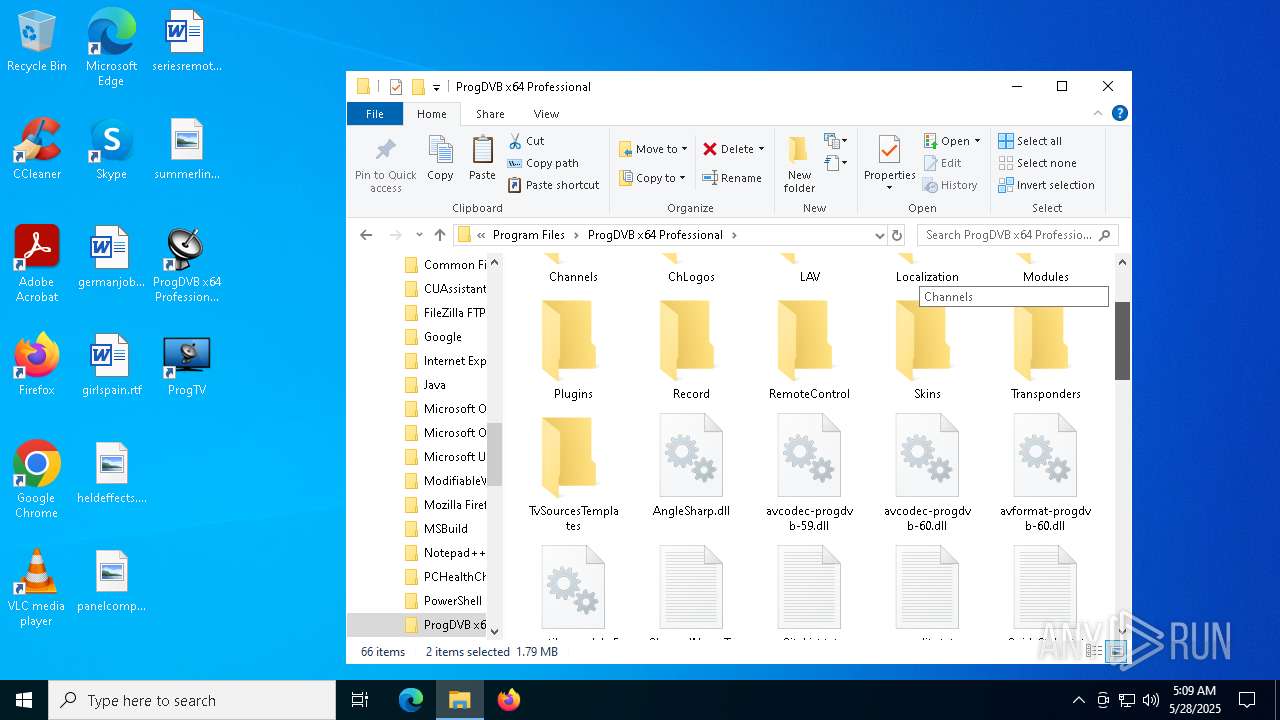
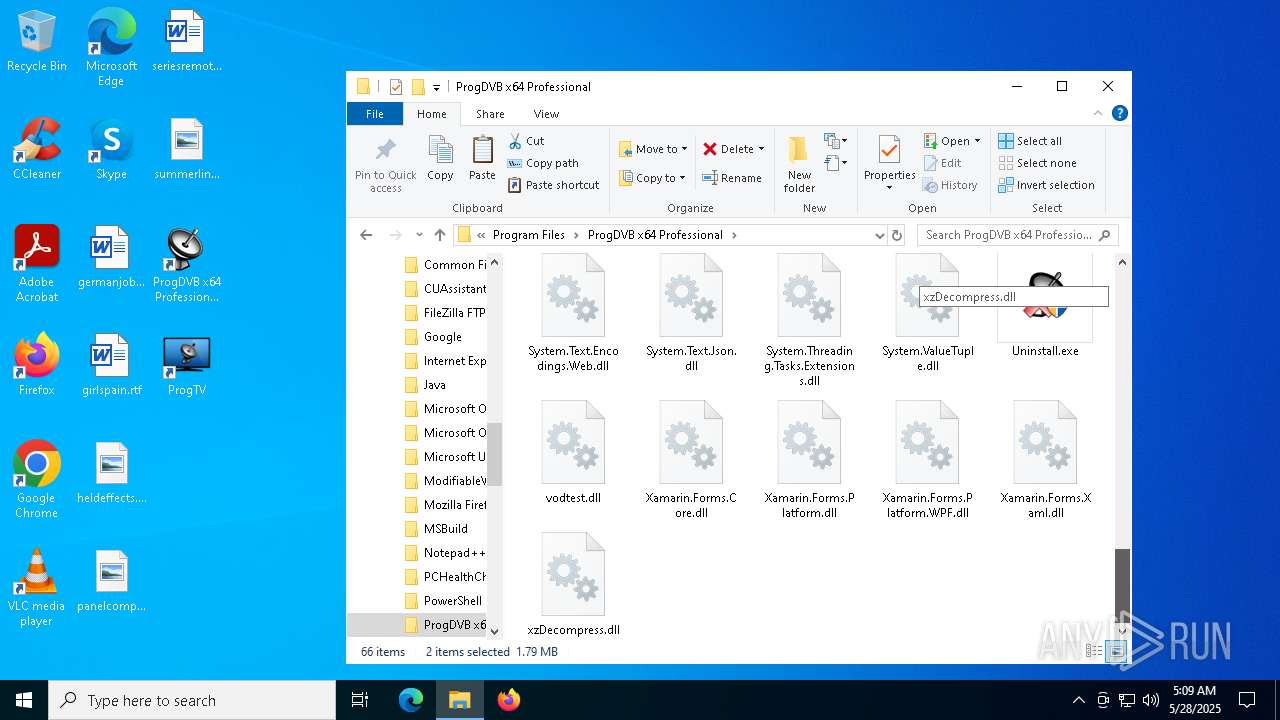
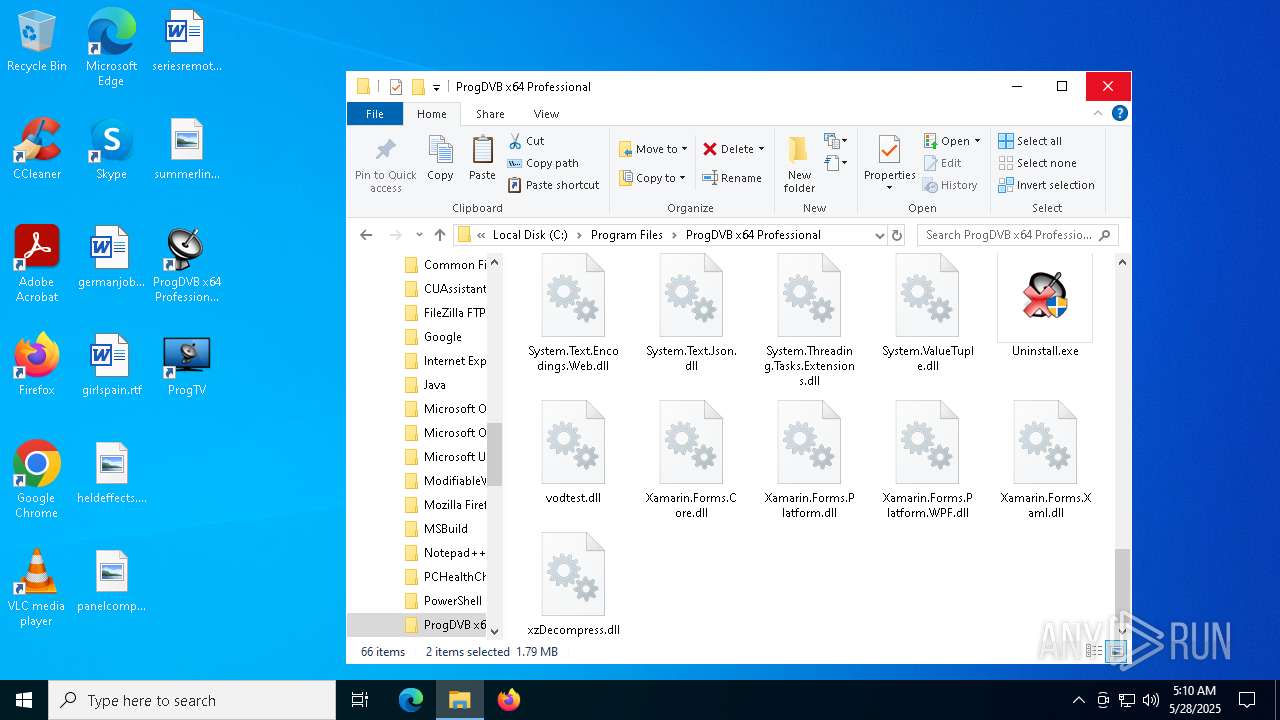
Creates files in the program directory
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
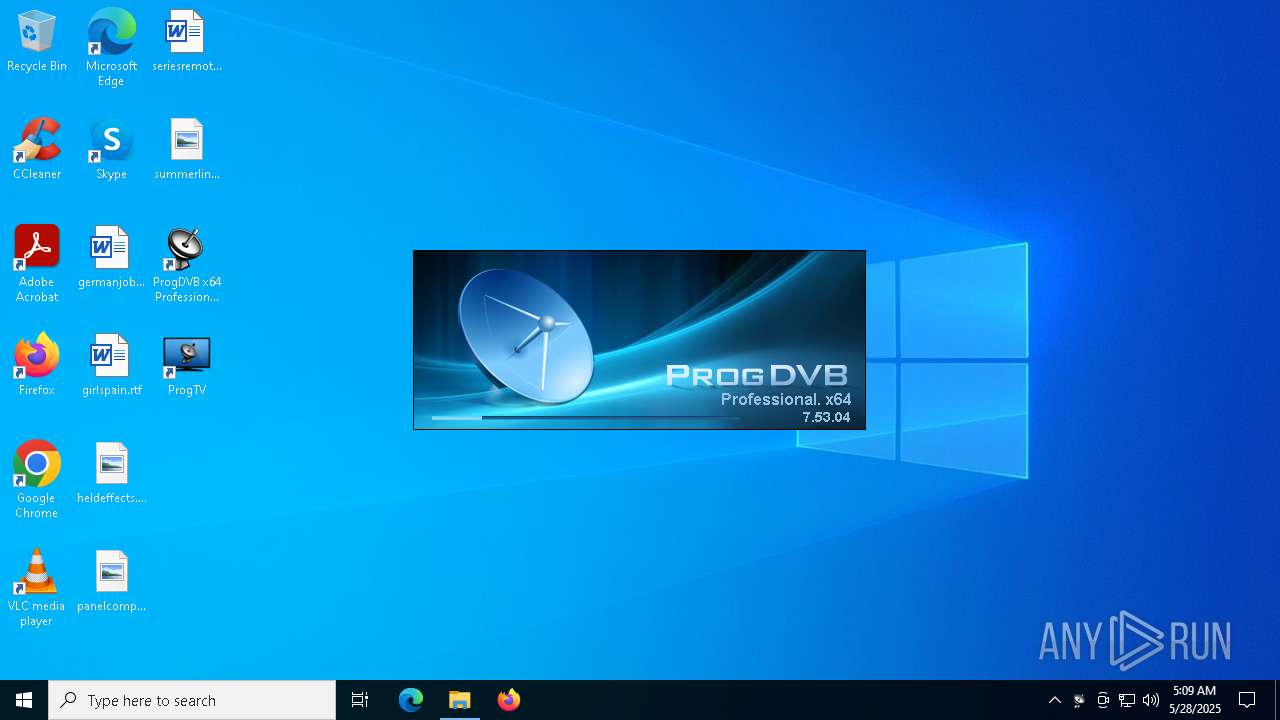
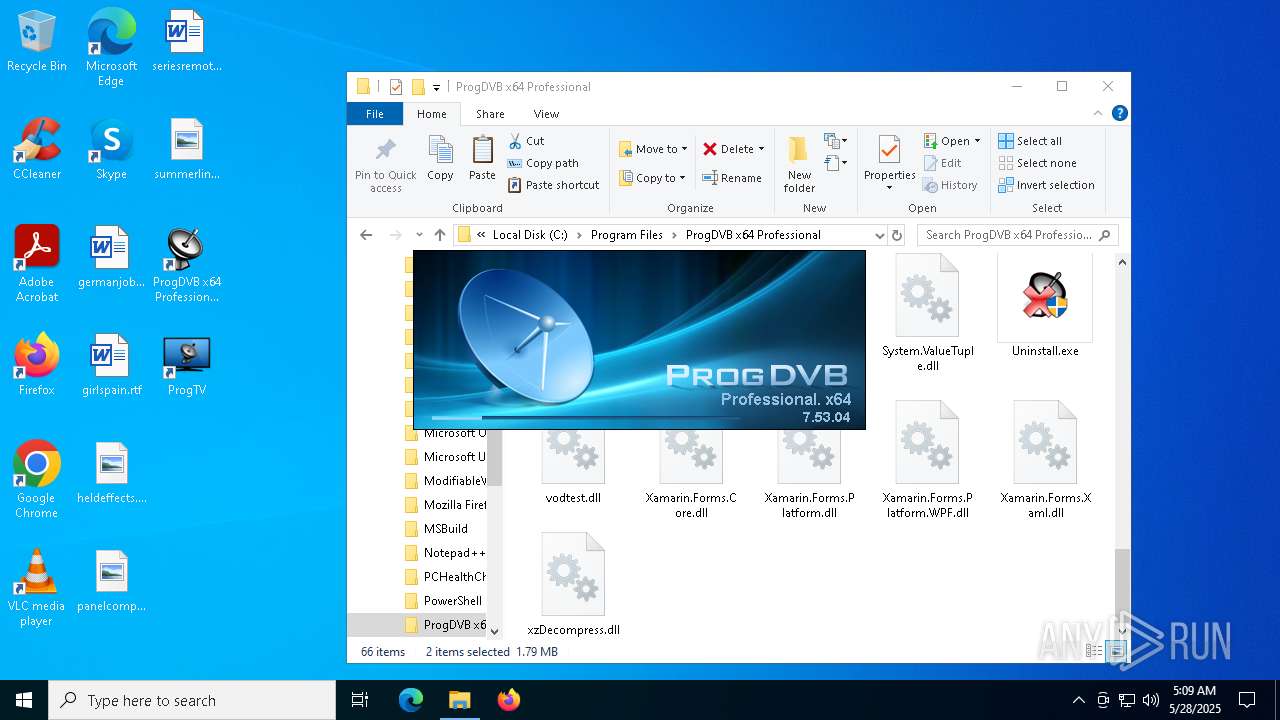
Themida protector has been detected
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
The sample compiled with english language support
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
- mscorsvw.exe (PID: 668)
- mscorsvw.exe (PID: 7504)
- mscorsvw.exe (PID: 5772)
- mscorsvw.exe (PID: 7932)
- mscorsvw.exe (PID: 7864)
- mscorsvw.exe (PID: 5452)
- mscorsvw.exe (PID: 4112)
- mscorsvw.exe (PID: 5936)
- mscorsvw.exe (PID: 5364)
- mscorsvw.exe (PID: 8072)
- mscorsvw.exe (PID: 7260)
- mscorsvw.exe (PID: 4376)
- mscorsvw.exe (PID: 8088)
- mscorsvw.exe (PID: 660)
- mscorsvw.exe (PID: 6228)
- mscorsvw.exe (PID: 7772)
- mscorsvw.exe (PID: 2796)
- mscorsvw.exe (PID: 5404)
- mscorsvw.exe (PID: 5452)
- mscorsvw.exe (PID: 7504)
- mscorsvw.exe (PID: 7636)
- mscorsvw.exe (PID: 7904)
- mscorsvw.exe (PID: 6972)
- mscorsvw.exe (PID: 4572)
The sample compiled with russian language support
- ProgDVB7.53.4x64Pro.exe (PID: 2692)
NGen native .NET image generation
- ngen.exe (PID: 6272)
- ngen.exe (PID: 1052)
- ngen.exe (PID: 2096)
- ngen.exe (PID: 7644)
- ngen.exe (PID: 720)
- ngen.exe (PID: 3300)
- ngen.exe (PID: 7744)
- ngen.exe (PID: 7964)
- ngen.exe (PID: 5024)
- ngen.exe (PID: 4424)
- ngen.exe (PID: 1616)
- ngen.exe (PID: 1328)
- ngen.exe (PID: 1280)
- ngen.exe (PID: 7260)
- ngen.exe (PID: 5228)
- ngen.exe (PID: 2780)
- ngen.exe (PID: 4012)
- ngen.exe (PID: 6072)
- ngen.exe (PID: 728)
- ngen.exe (PID: 3992)
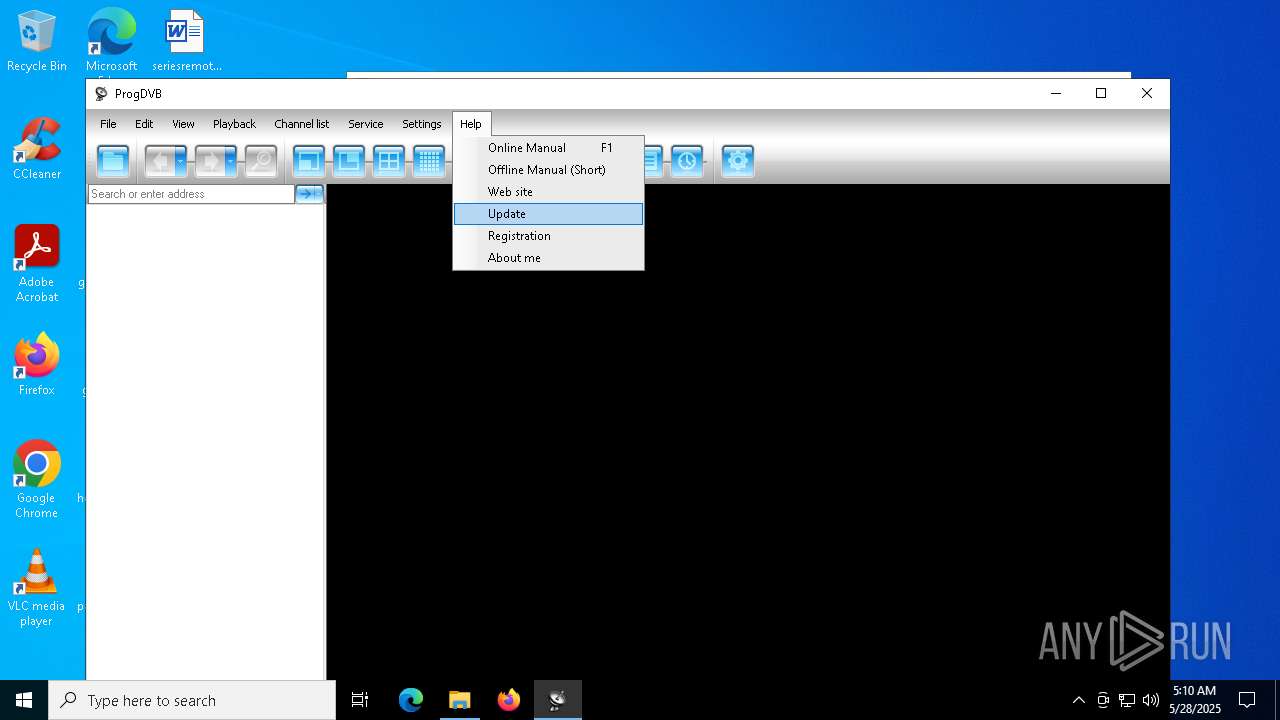
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
296
Monitored processes
151
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe -StartupEvent 1f8 -InterruptEvent 0 -NGENProcess 1e8 -Pipe 1f4 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.9093.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
| 456 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe -StartupEvent 3ac -InterruptEvent 0 -NGENProcess 3a0 -Pipe 2c4 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.9093.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
| 496 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe -StartupEvent 2f8 -InterruptEvent 0 -NGENProcess 2ec -Pipe 2f4 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.9093.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
| 644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5392 --field-trial-handle=1820,i,14844482415007198474,9467482984599129271,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 644 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe -StartupEvent 344 -InterruptEvent 0 -NGENProcess 370 -Pipe 3f4 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.9093.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5228 --field-trial-handle=1820,i,14844482415007198474,9467482984599129271,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 660 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe -StartupEvent 3e4 -InterruptEvent 0 -NGENProcess 3dc -Pipe 3e0 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.9093.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
| 668 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe -StartupEvent 304 -InterruptEvent 0 -NGENProcess 30c -Pipe 34c -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.9093.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
| 720 | "C:\WINDOWS\Microsoft.NET\Framework64\v4.0.30319\ngen.exe" uninstall "C:\Program Files\ProgDVB x64 Professional\ProgGuide.exe" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ngen.exe | — | ProgDVB7.53.4x64Pro.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Common Language Runtime native compiler Exit code: 4294967295 Version: 4.8.9093.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
| 720 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe -StartupEvent 304 -InterruptEvent 0 -NGENProcess 344 -Pipe 3f0 -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.9093.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
Total events
88 296
Read events
88 093
Write events
180
Delete events
23
Modification events
| (PID) Process: | (5244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5244) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5244) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (7744) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000007A98573D8ECFDB01 | |||
| (PID) Process: | (7944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (7944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
| (PID) Process: | (7944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 13 |
Value: | |||
| (PID) Process: | (7944) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 12 |
Value: | |||
Executable files
245
Suspicious files
502
Text files
214
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10bfe7.TMP | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10bff6.TMP | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10bff6.TMP | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10bff6.TMP | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10bff6.TMP | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5244 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
58
DNS requests
45
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2236 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2236 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2268 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
2268 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
2268 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/AMpg5-cnrANo_2018.8.8.0/2018.8.8.0_win64_win_third_party_module_list.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7332 | chrome.exe | 207.241.224.2:443 | archive.org | INTERNET-ARCHIVE | US | whitelisted |
5244 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
archive.org |
| whitelisted |
accounts.google.com |
| whitelisted |
dn721608.ca.archive.org |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.google.com |
| whitelisted |
login.live.com |
| whitelisted |