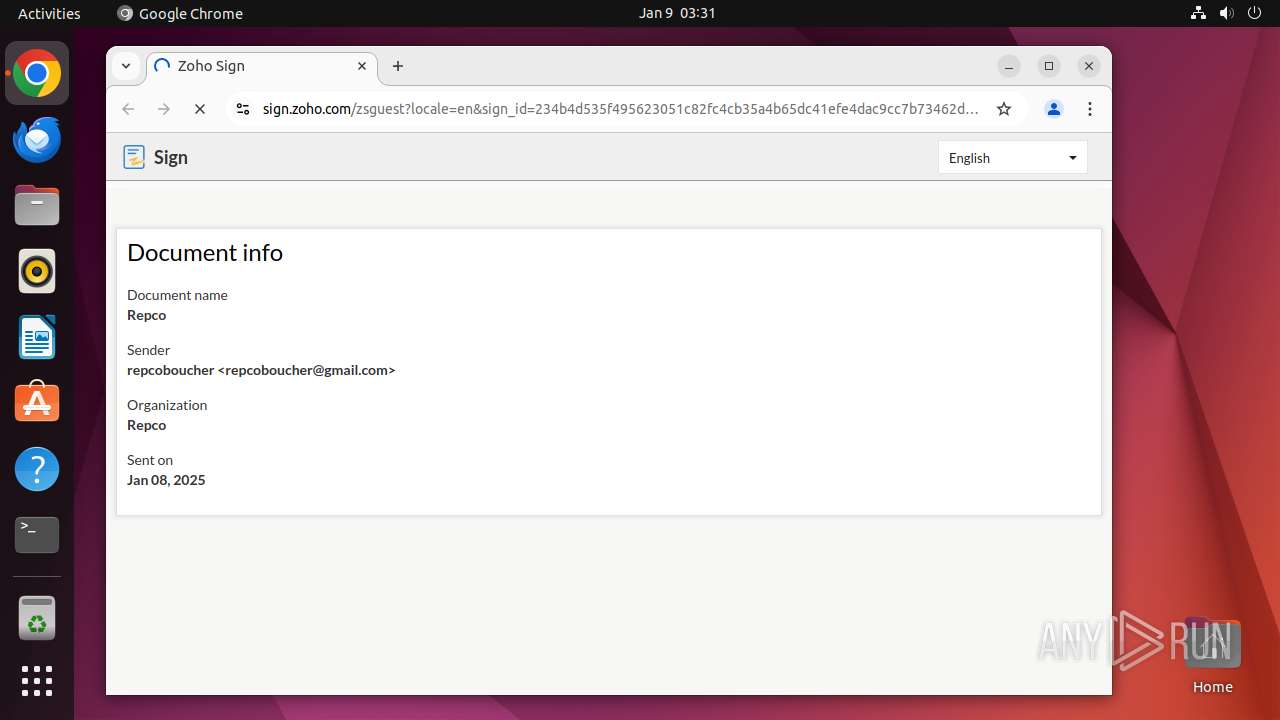
| URL: | https://url.us.m.mimecastprotect.com/s/Ni48CM8mVBCzmnZpKUwfzS8BUwc?domain=sign.zoho.com |
| Full analysis: | https://app.any.run/tasks/c30b091a-bc99-4199-8e42-ae271bdaeb75 |
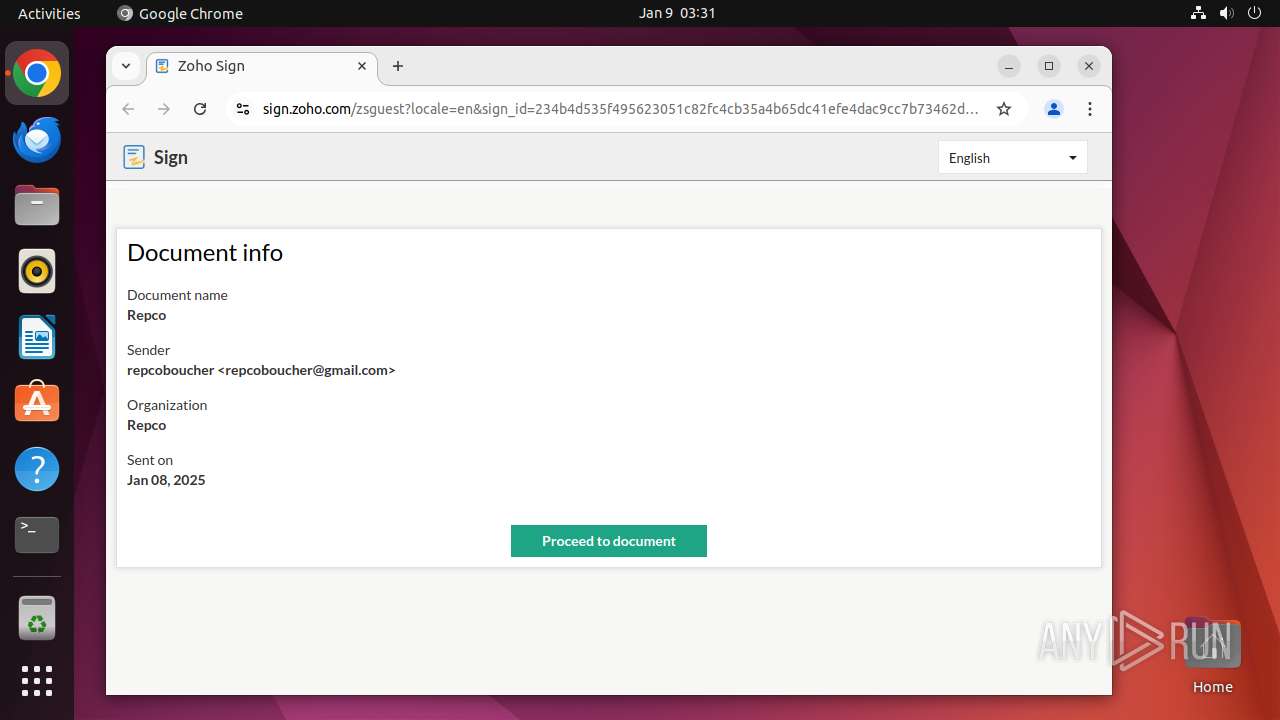
| Verdict: | Malicious activity |
| Analysis date: | January 09, 2025, 03:31:10 |
| OS: | Ubuntu 22.04.2 LTS |
| Tags: | |
| Indicators: | |
| MD5: | 1D7CB95D37846CEE26C072CE4BABB7A2 |
| SHA1: | F9DFD7447C51C50C77A563B09DEEB827F6F5A4F7 |
| SHA256: | 182FC29BC861A53E008F56923D87CF31B8AE39A209F0BB69D182C39D5CFB17F7 |
| SSDEEP: | 3:N8UjmTSC3Mf2/VIf2dnTKurWGI:2Ujw3Mfn2cn |
MALICIOUS
PHISHING has been detected (SURICATA)
- systemd-resolved (PID: 445)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
298
Monitored processes
91
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 445 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
| 38738 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://url\.us\.m\.mimecastprotect\.com/s/Ni48CM8mVBCzmnZpKUwfzS8BUwc?domain=sign\.zoho\.com " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 38739 | sudo -iu user google-chrome https://url.us.m.mimecastprotect.com/s/Ni48CM8mVBCzmnZpKUwfzS8BUwc?domain=sign.zoho.com | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 38740 | /usr/bin/google-chrome https://url.us.m.mimecastprotect.com/s/Ni48CM8mVBCzmnZpKUwfzS8BUwc?domain=sign.zoho.com | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 38741 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 38742 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 38743 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 38744 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 38745 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 38746 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
0
Suspicious files
195
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 38740 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 38740 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 38740 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 38740 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 38740 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 38740 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 38740 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
| 38740 | chrome | /home/user/.config/google-chrome/Default/DawnWebGPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 38740 | chrome | /home/user/.config/google-chrome/Default/DawnWebGPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 38740 | chrome | /home/user/.config/google-chrome/Default/DawnWebGPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
70
DNS requests
104
Threats
62
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.97:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
38785 | chrome | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/gcmjkmgdlgnkkcocmoeiminaijmmjnii/e34960f2d401eef17cbb082b4e74706241213d97e437d766de99d8bdb5fc264b | unknown | — | — | whitelisted |
38785 | chrome | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ads7ltfl2gw6hxwgakn3sxrkoijq_9.53.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.53.0_all_iky7dhj3jd5su3axccoshyd4xm.crx3 | unknown | — | — | whitelisted |
38785 | chrome | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acni2gj5xz367c6hglwpb2h5qx6q_20241228.712128858.14/obedbbhbpmojnkanicioggnmelmoomoc_20241228.712128858.14_all_ENGB500000_f6dvhnyplmtcw3caytf77ugz3q.crx3 | unknown | — | — | whitelisted |
38785 | chrome | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/lmelglejhemejginpboagddgdfbepgmp/067ac4883cf8ada706f78b91673d596c83cf9627bbcf5b7ce0631e9a52965cdf | unknown | — | — | whitelisted |
38785 | chrome | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acy5mdne3lup4k7xyd5szdvx6hqa_477/lmelglejhemejginpboagddgdfbepgmp_477_all_ZZ_acd5zgdfvdiu3zilux46fn7rljva.crx3 | unknown | — | — | whitelisted |
38785 | chrome | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/kiabhabjdbkjdpjbpigfodbdjmbglcoo/0fd59acc76376548e5c25892d8b4b22f98c9186c35706afa4fb81693defbddbe | unknown | — | — | whitelisted |
38785 | chrome | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adfsdndfrjkiabjh7i544brh454q_9468/hfnkpimlhhgieaddgfemjhofmfblmnib_9468_all_adv5sv3rvx7ygfe3iuykqdmq7jfq.crx3 | unknown | — | — | whitelisted |
38785 | chrome | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/fw4ggtylvtq6i65ti33m4vqijm_2024.12.14.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.12.14.01_all_e3s3pxuydvrca43mi6hdgphvru.crx3 | unknown | — | — | whitelisted |
38785 | chrome | GET | 403 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acqrj4kzqecdpjnekrbehcituafa_2025.1.8.0/niikhdgajlphfehepabhhblakbdgeefj_2025.01.08.00_all_hw756lmgdhcxnxdw3wekrfnvyq.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.96:80 | — | Canonical Group Limited | GB | unknown |
— | — | 185.125.190.18:80 | — | Canonical Group Limited | GB | unknown |
— | — | 185.125.190.97:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
38785 | chrome | 142.251.39.106:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
38785 | chrome | 142.251.36.3:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
38785 | chrome | 207.211.31.113:443 | url.us.m.mimecastprotect.com | NAVISITE-EAST-2 | US | unknown |
38785 | chrome | 142.250.102.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
38785 | chrome | 136.143.191.101:443 | sign.zoho.com | ZOHO-AS | US | whitelisted |
38785 | chrome | 172.217.23.202:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
url.us.m.mimecastprotect.com |
| unknown |
accounts.google.com |
| whitelisted |
sign.zoho.com |
| whitelisted |
static.zohocdn.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
129.100.168.192.in-addr.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
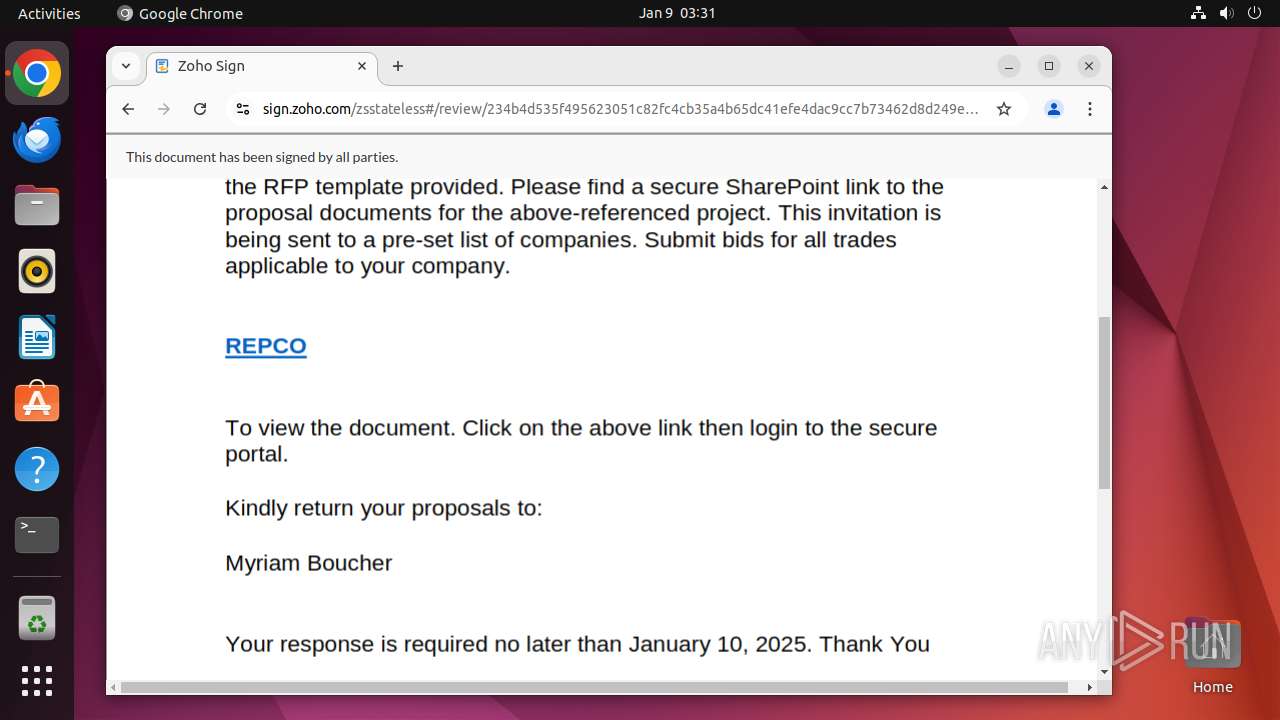
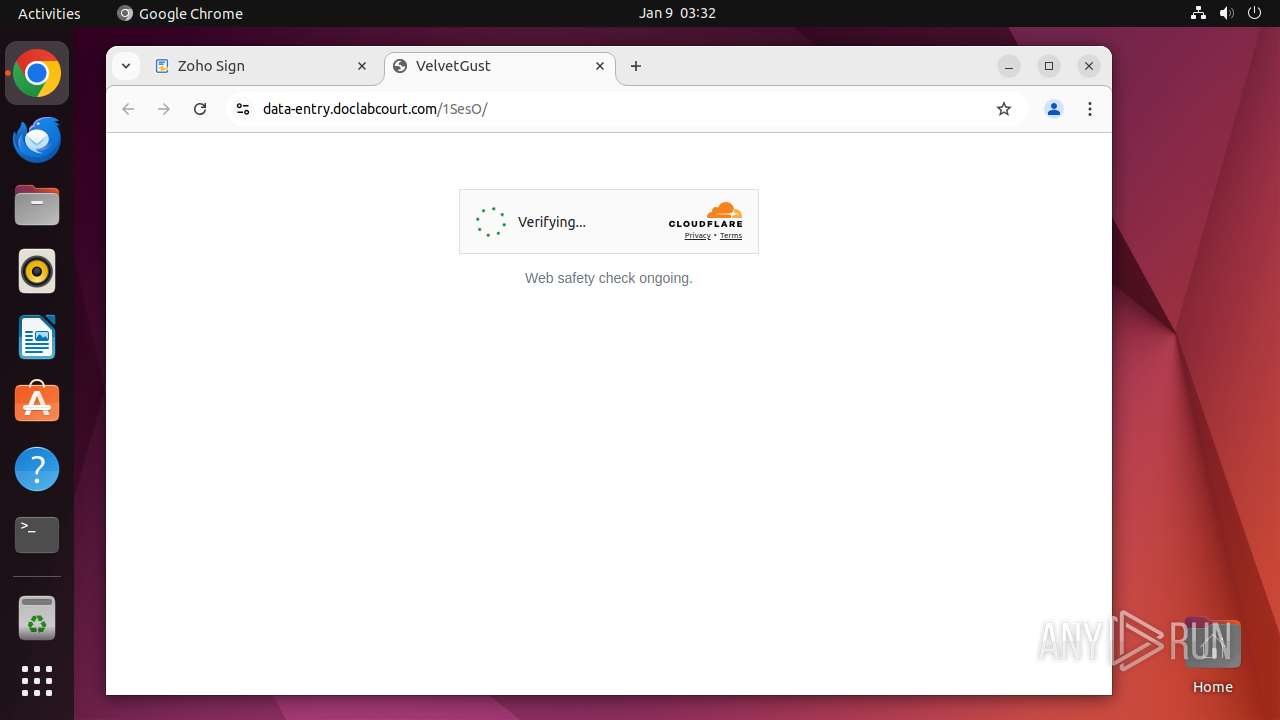
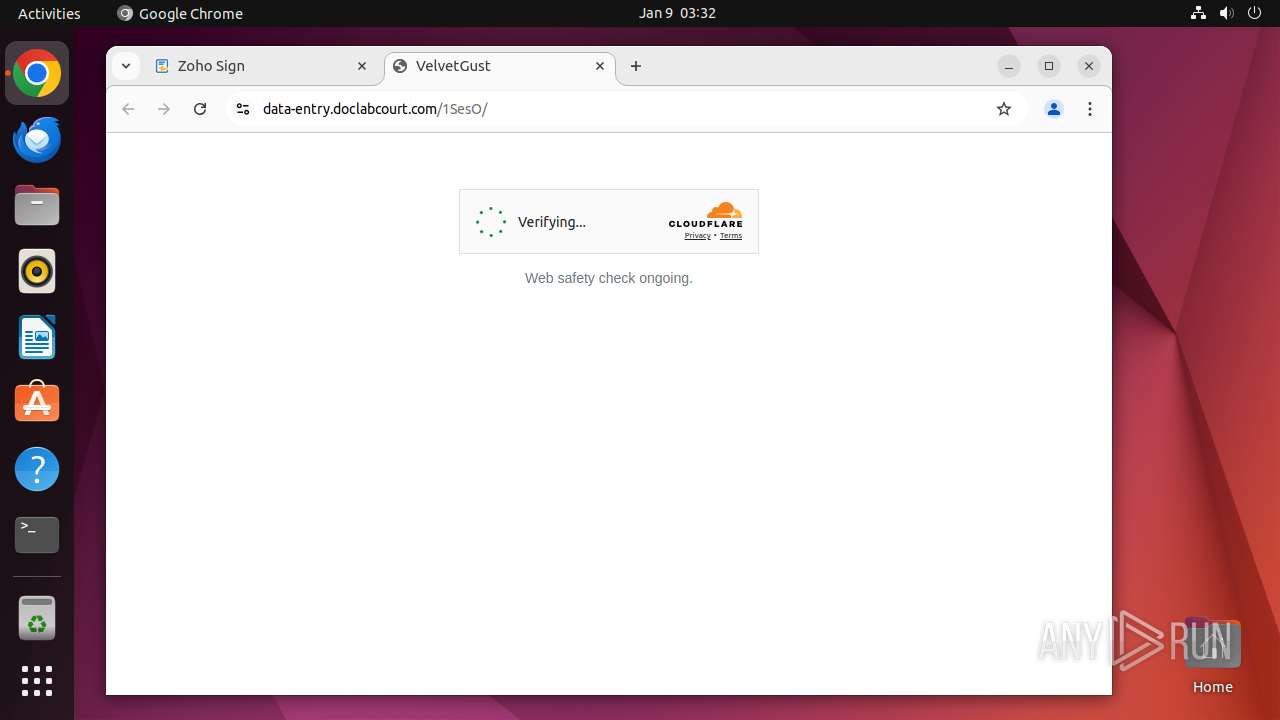
445 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .doclabcourt .com) |
445 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .doclabcourt .com) |
445 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .doclabcourt .com) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
445 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .doclabcourt .com) |
445 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Suspected Phishing domain by CrossDomain ( .doclabcourt .com) |
445 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |