| File name: | wxqlgj.geekotg.com.exe |
| Full analysis: | https://app.any.run/tasks/f45b84cd-339a-44f6-96f4-c187b1c91323 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2020, 08:39:17 |
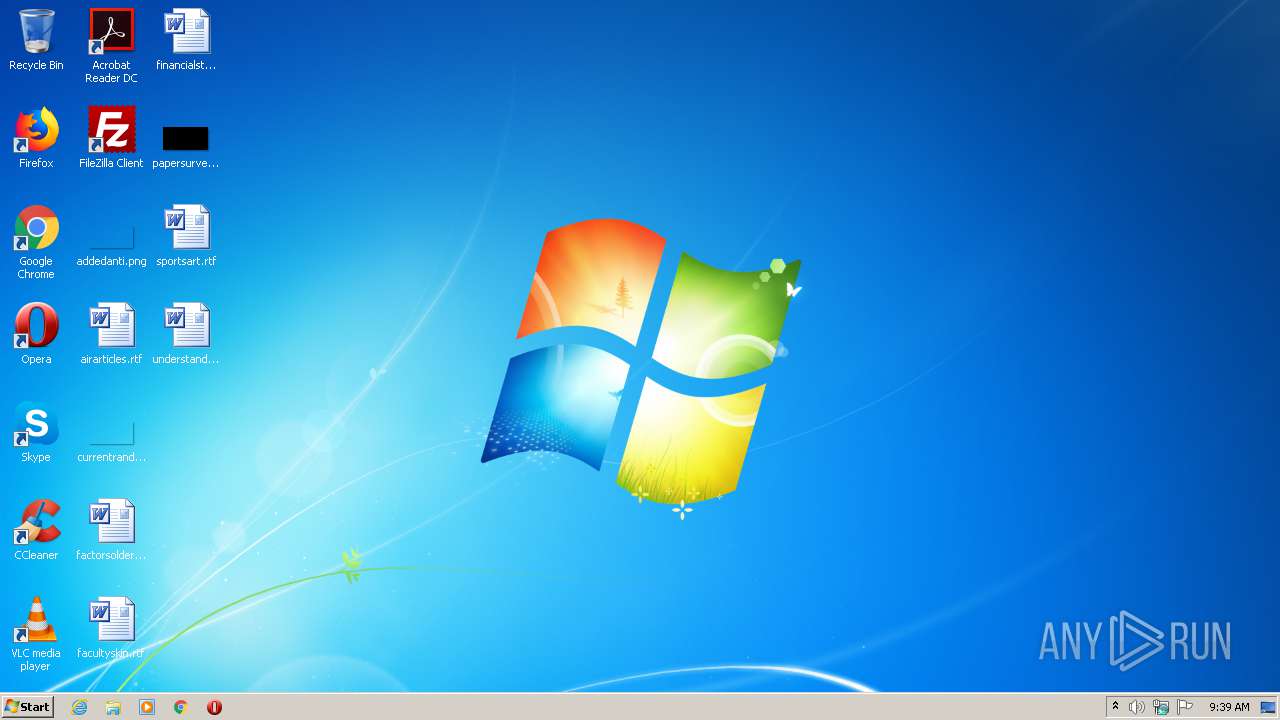
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 28897DE097B5A78A55FE5166C7BDC414 |
| SHA1: | 8D3B4DED7ED09ACDAEF7E68D70A007419BDA4ABC |
| SHA256: | 182F7D5FE505A56DF2D69110A1F1041F818546C2F6E4E53F10C938A61F2A4558 |
| SSDEEP: | 24576:SjzSNQDy1AOM8EHpU/QqBo52xphGa0t0FWUlbqJJ1FaBB1eHS60qSdY:sny1ATpGU4JlCJ1Fa1ey60BdY |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Internet Cache Settings
- wxqlgj.geekotg.com.exe (PID: 1744)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:02:19 08:21:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 1097728 |
| InitializedDataSize: | 28672 |
| UninitializedDataSize: | 1224704 |
| EntryPoint: | 0x237c50 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.2.0.8 |
| ProductVersionNumber: | 3.2.0.8 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
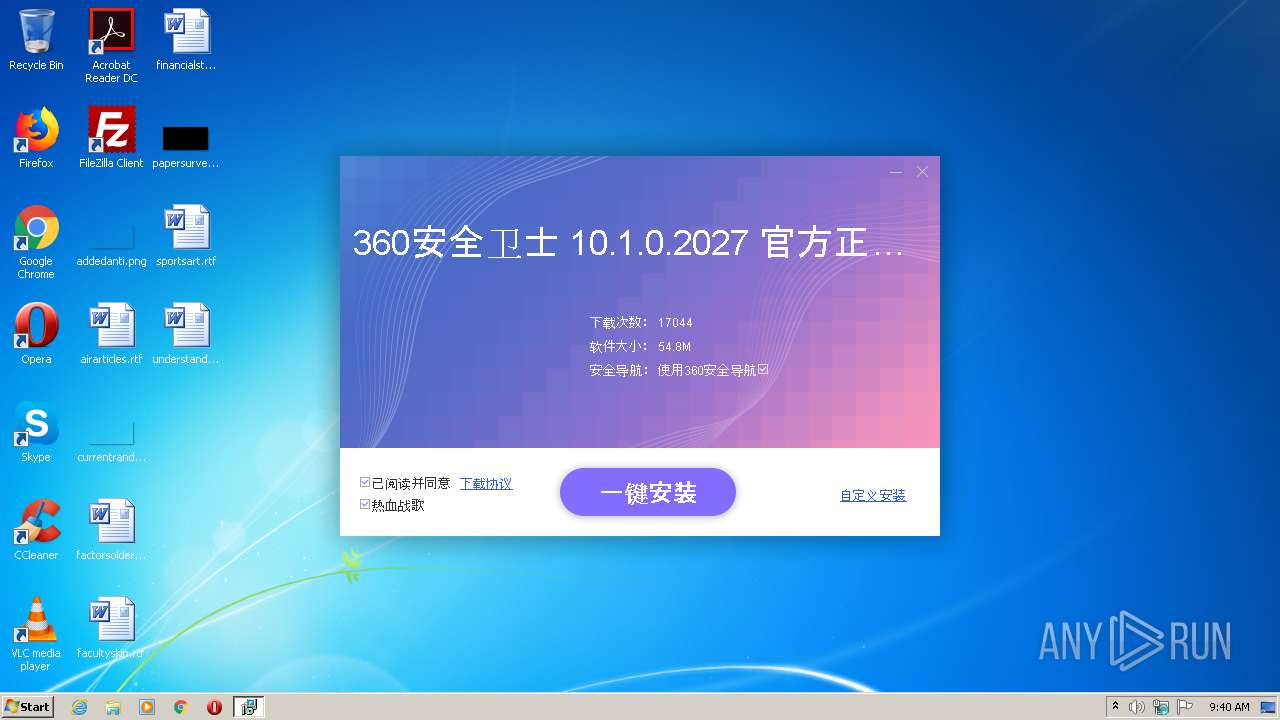
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | - |
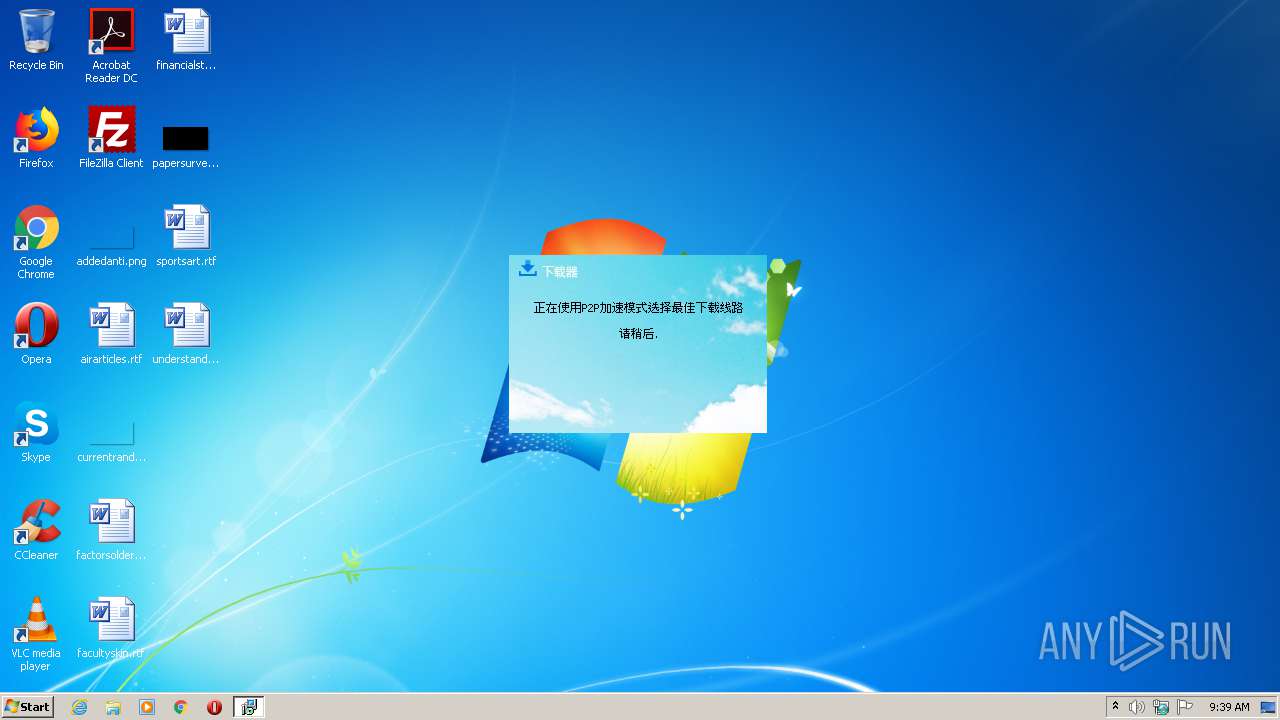
| FileDescription: | 软件下载器 |
| FileVersion: | 3.2.0.8 |
| InternalName: | FastDownloader.exe |
| LegalCopyright: | Copyright (C) 2018 |
| OriginalFileName: | FastDownloader.exe |
| ProductName: | 软件下载器 |
| ProductVersion: | 3.2.0.8 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Feb-2020 07:21:46 |
| Detected languages: |
|
| CompanyName: | - |
| FileDescription: | 软件下载器 |
| FileVersion: | 3.2.0.8 |
| InternalName: | FastDownloader.exe |
| LegalCopyright: | Copyright (C) 2018 |
| OriginalFilename: | FastDownloader.exe |
| ProductName: | 软件下载器 |
| ProductVersion: | 3.2.0.8 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000120 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 19-Feb-2020 07:21:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
PNG0 | 0x00001000 | 0x0012B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
PNG1 | 0x0012C000 | 0x0010C000 | 0x0010C000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.89206 |
.rsrc | 0x00238000 | 0x00007000 | 0x00006C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.02097 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06216 | 651 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.24731 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 3.27183 | 3752 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 3.91452 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 3.47417 | 1384 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 3.02843 | 9640 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 2.82055 | 4264 | UNKNOWN | Chinese - PRC | RT_ICON |
8 | 2.44525 | 1128 | UNKNOWN | Chinese - PRC | RT_ICON |
104 | 2.81158 | 118 | UNKNOWN | Chinese - PRC | RT_GROUP_ICON |
107 | 5.54037 | 76 | UNKNOWN | Chinese - PRC | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1744 | "C:\Users\admin\AppData\Local\Temp\wxqlgj.geekotg.com.exe" | C:\Users\admin\AppData\Local\Temp\wxqlgj.geekotg.com.exe | explorer.exe | ||||||||||||
User: admin Company: - Integrity Level: HIGH Description: 软件下载器 Exit code: 0 Version: 3.2.0.8 Modules
| |||||||||||||||
| 2740 | "C:\Users\admin\AppData\Local\Temp\wxqlgj.geekotg.com.exe" | C:\Users\admin\AppData\Local\Temp\wxqlgj.geekotg.com.exe | — | explorer.exe | |||||||||||
User: admin Company: - Integrity Level: MEDIUM Description: 软件下载器 Exit code: 3221226540 Version: 3.2.0.8 Modules
| |||||||||||||||
Total events
64
Read events
53
Write events
11
Delete events
0
Modification events
| (PID) Process: | (1744) wxqlgj.geekotg.com.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\RFC1156Agent\CurrentVersion\Parameters |
| Operation: | write | Name: | TrapPollTimeMilliSecs |
Value: 15000 | |||
| (PID) Process: | (1744) wxqlgj.geekotg.com.exe | Key: | HKEY_CURRENT_USER\Software\UIDowner |
| Operation: | write | Name: | usestime |
Value: 1 | |||
| (PID) Process: | (1744) wxqlgj.geekotg.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1744) wxqlgj.geekotg.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1744) wxqlgj.geekotg.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1744) wxqlgj.geekotg.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1744) wxqlgj.geekotg.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1744) wxqlgj.geekotg.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1744) wxqlgj.geekotg.com.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
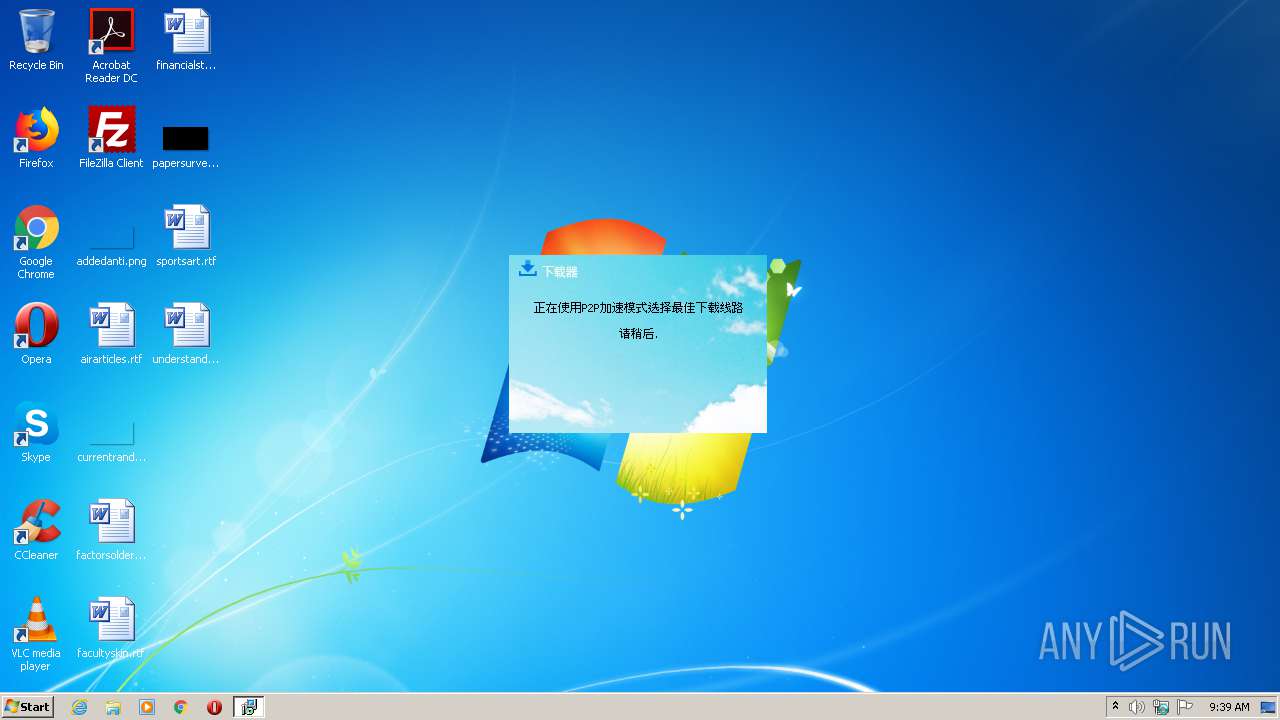
HTTP(S) requests
50
TCP/UDP connections
7
DNS requests
7
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1744 | wxqlgj.geekotg.com.exe | GET | 200 | 60.205.177.239:80 | http://downloader.aldtop.com/client/debug?ver=2.4.7&webid=28&softid=5&mac=570dba868abc2ed5e83cf2bd9e71b380&mode=lib&status=webxml&called=1 | CN | text | 3 b | malicious |
1744 | wxqlgj.geekotg.com.exe | GET | 200 | 121.207.229.145:80 | http://static.downerapi.com/upload/xml/360.xml?webid=28&channelid=&softid=5&token=5ea18bb987d01d0beaf4c9a9f23a1024 | CN | xml | 1.54 Kb | malicious |
1744 | wxqlgj.geekotg.com.exe | GET | 200 | 182.92.156.114:80 | http://api.aldtop.com/hp?ver=2.4.7&webid=&softid=&step=0&mac=570dba868abc2ed5e83cf2bd9e71b380&sdsoft=0&userev=0&rnd=41 | CN | text | 2.64 Kb | whitelisted |
1744 | wxqlgj.geekotg.com.exe | GET | 200 | 218.12.76.151:80 | http://resource.aldtop.com/2020/15948908445012.png | CN | binary | 1.43 Mb | suspicious |
1744 | wxqlgj.geekotg.com.exe | GET | 200 | 125.77.142.190:80 | http://img.aldtop.com/storage/upload/uKhixdbpTvJaU9uO8Llw5bqqGQnqbJ1ic80OCRum.png | CN | image | 11.7 Kb | suspicious |
1744 | wxqlgj.geekotg.com.exe | GET | 200 | 125.77.142.190:80 | http://img.aldtop.com/storage/upload/18BgB7AWUIyi55jJGqbQ6vWohpvFeyuEeMqmOUNK.png | CN | image | 4.57 Kb | suspicious |
1744 | wxqlgj.geekotg.com.exe | GET | 200 | 60.205.177.239:80 | http://downloader.downerapi.com/client/debug?step=0&theme=2&softid=5&webid=28&channelid=28&user=1aee16034c99644087655a3d51a4e437&session=63fad6e4549b72e71391eb76206ae618&city=0&sdsoft=0&system=6.1&ie=9.11.9600.17843&isdeveloper=0&webid=28&channelid=28&softid=5&filename=wxqlgj.geekotg.com.exe&filesize=1134944&filemd5=d41d8cd98f00b204e9800998ecf8427e&rnd=41489 | CN | text | 3 b | malicious |
1744 | wxqlgj.geekotg.com.exe | GET | 200 | 125.77.142.190:80 | http://img.aldtop.com/storage/upload/yo5jWQwgDDlXlD9TM6X9J3g4p8r32gFupyWGVM7W.png | CN | image | 5.15 Kb | suspicious |
1744 | wxqlgj.geekotg.com.exe | GET | 200 | 125.77.142.190:80 | http://img.aldtop.com/storage/upload/kKrrLCMtNhJoI2XqH3Zb1QIzKxIfZVB1vi3WjNCY.png | CN | image | 3.37 Kb | suspicious |
1744 | wxqlgj.geekotg.com.exe | GET | 200 | 60.205.177.239:80 | http://downloader.downerapi.com/client/ad/28?winver=6.1&sdsoft=0&webid=28&channelid=&softid=5&ver=4.0.3.20&usesnum=1&mac=1aee16034c99644087655a3d51a4e437&filename=wxqlgj.geekotg.com.exe&errcode=0&userev=0&encry=1&rnd=41463 | CN | text | 37.3 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1744 | wxqlgj.geekotg.com.exe | 121.207.229.145:80 | static.downerapi.com | Fuzhou | CN | unknown |
1744 | wxqlgj.geekotg.com.exe | 218.12.76.151:80 | resource.aldtop.com | CHINA UNICOM China169 Backbone | CN | malicious |
— | — | 182.92.156.114:80 | api.aldtop.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
1744 | wxqlgj.geekotg.com.exe | 125.77.142.190:80 | img.aldtop.com | No.31,Jin-rong Street | CN | unknown |
1744 | wxqlgj.geekotg.com.exe | 60.205.177.239:80 | downloader.downerapi.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
downloader.downerapi.com |
| unknown |
static.downerapi.com |
| unknown |
resource.aldtop.com |
| suspicious |
api.aldtop.com |
| whitelisted |
downloader.aldtop.com |
| unknown |
img.aldtop.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1744 | wxqlgj.geekotg.com.exe | A Network Trojan was detected | ET MALWARE User-Agent (User-Agent Mozilla/4.0 (compatible )) |
1744 | wxqlgj.geekotg.com.exe | A Network Trojan was detected | ET MALWARE User-Agent (User-Agent Mozilla/4.0 (compatible )) |
1744 | wxqlgj.geekotg.com.exe | A Network Trojan was detected | ET MALWARE User-Agent (User-Agent Mozilla/4.0 (compatible )) |
1744 | wxqlgj.geekotg.com.exe | A Network Trojan was detected | ET MALWARE User-Agent (User-Agent Mozilla/4.0 (compatible )) |
1744 | wxqlgj.geekotg.com.exe | A Network Trojan was detected | MALWARE [PTsecurity] Win32/RiskWare.Downer.A |