| File name: | nssm.exe |
| Full analysis: | https://app.any.run/tasks/c494dcc0-7462-4975-914d-25062cc70bc8 |
| Verdict: | No threats detected |
| Analysis date: | June 12, 2020, 09:48:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3FAE8868A431A4132FB322C4CA9F6A81 |
| SHA1: | 42C253CA004BD385383B8FEF061544F7A71C1F2B |
| SHA256: | 181C161ABDBE6434CA7720DAA60A3EF66A55A82DC2D70D99392DE82BF79B9D9D |
| SSDEEP: | 24576:XYbXo6WcbOk1n++N6G3FH6kY/RtDAcpQOTc9B4SJvfMvnTOzHjwynC6Gj2N//:o7o6WhEt0tp+9qSJfnzF9GKZ/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads internet explorer settings
- mmc.exe (PID: 3024)
INFO
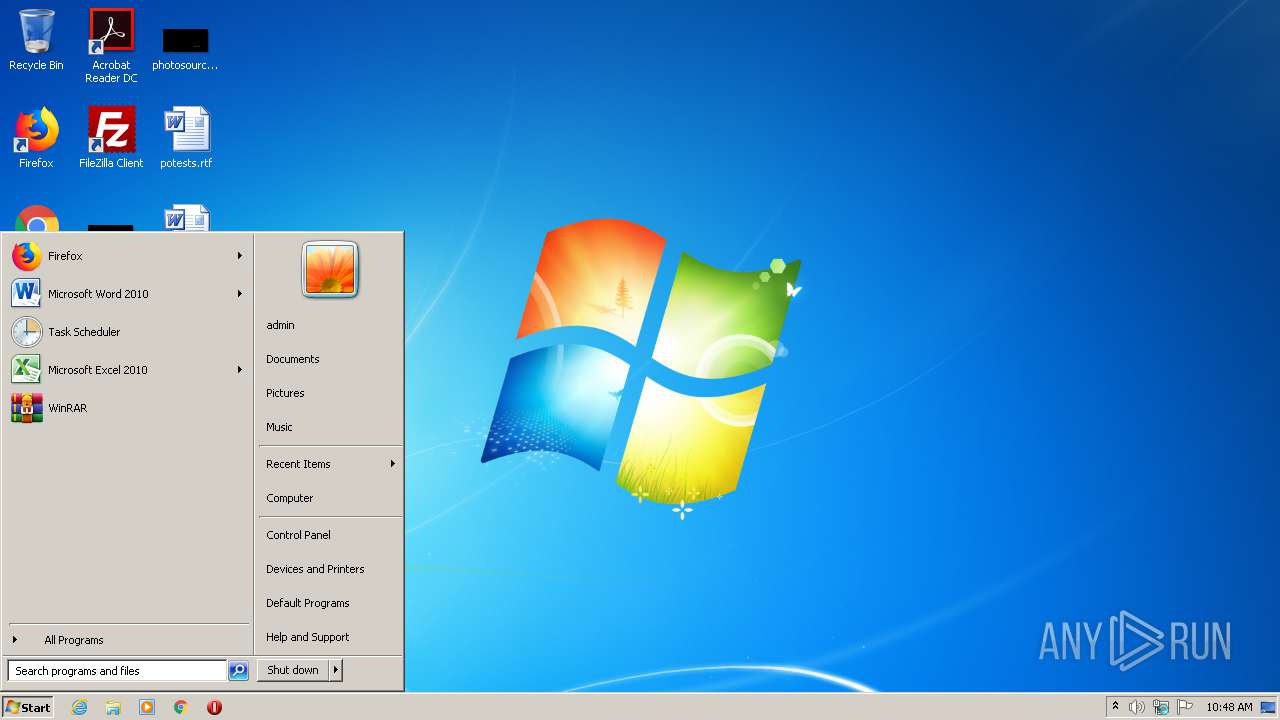
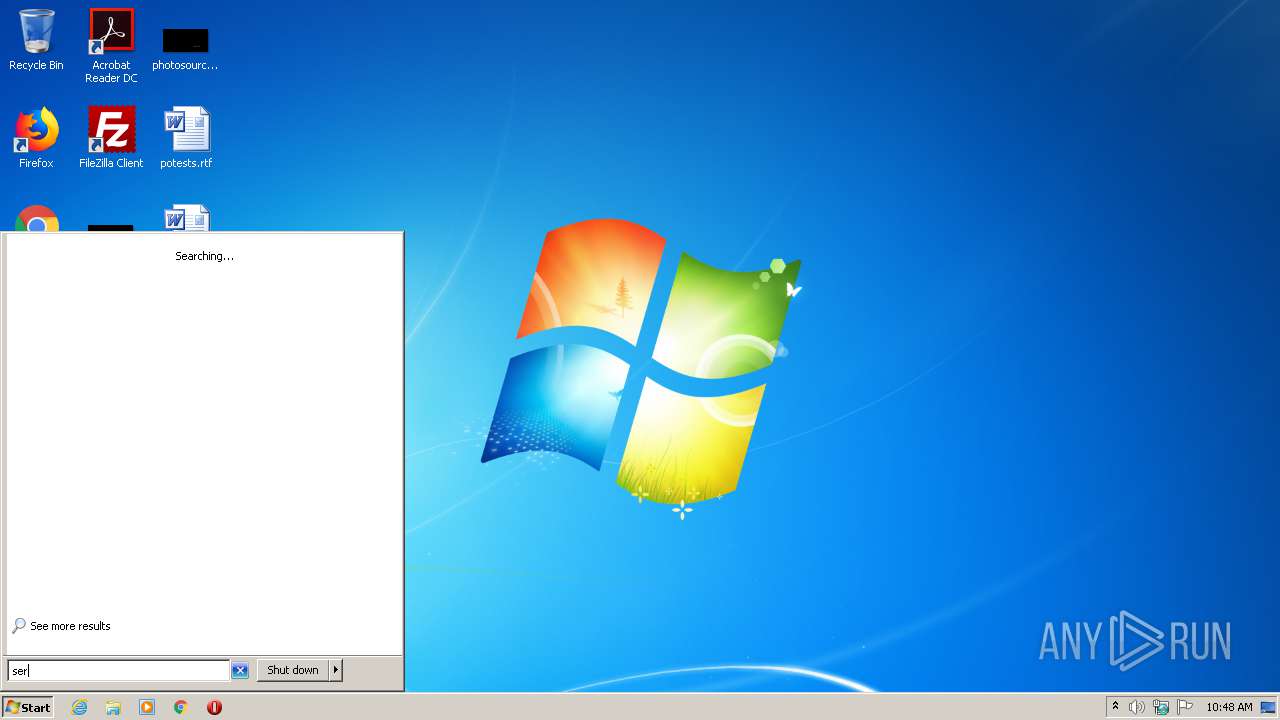
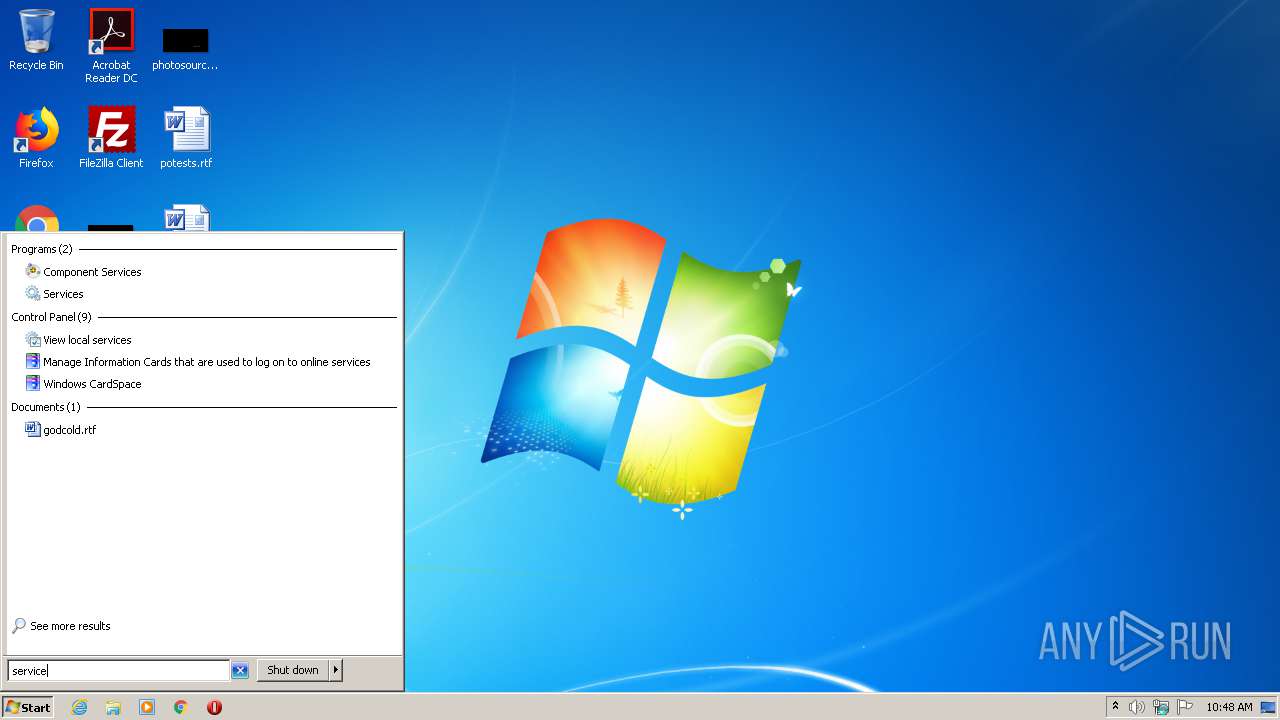
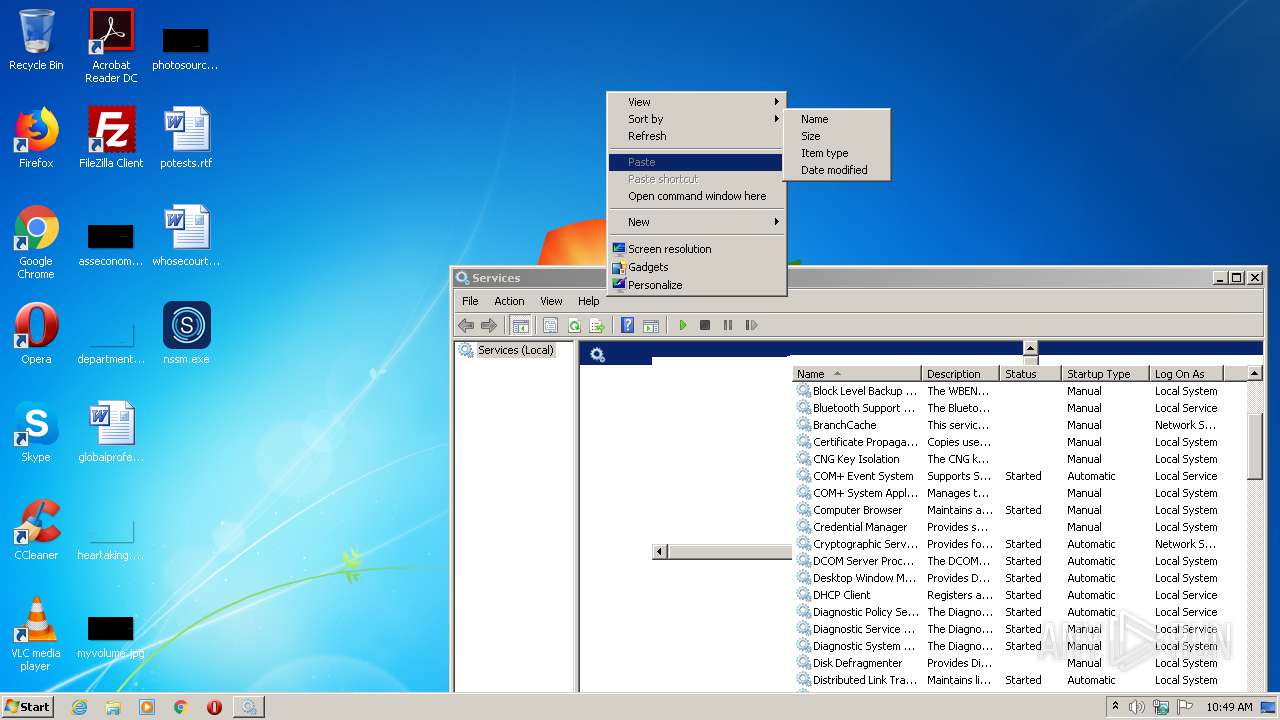
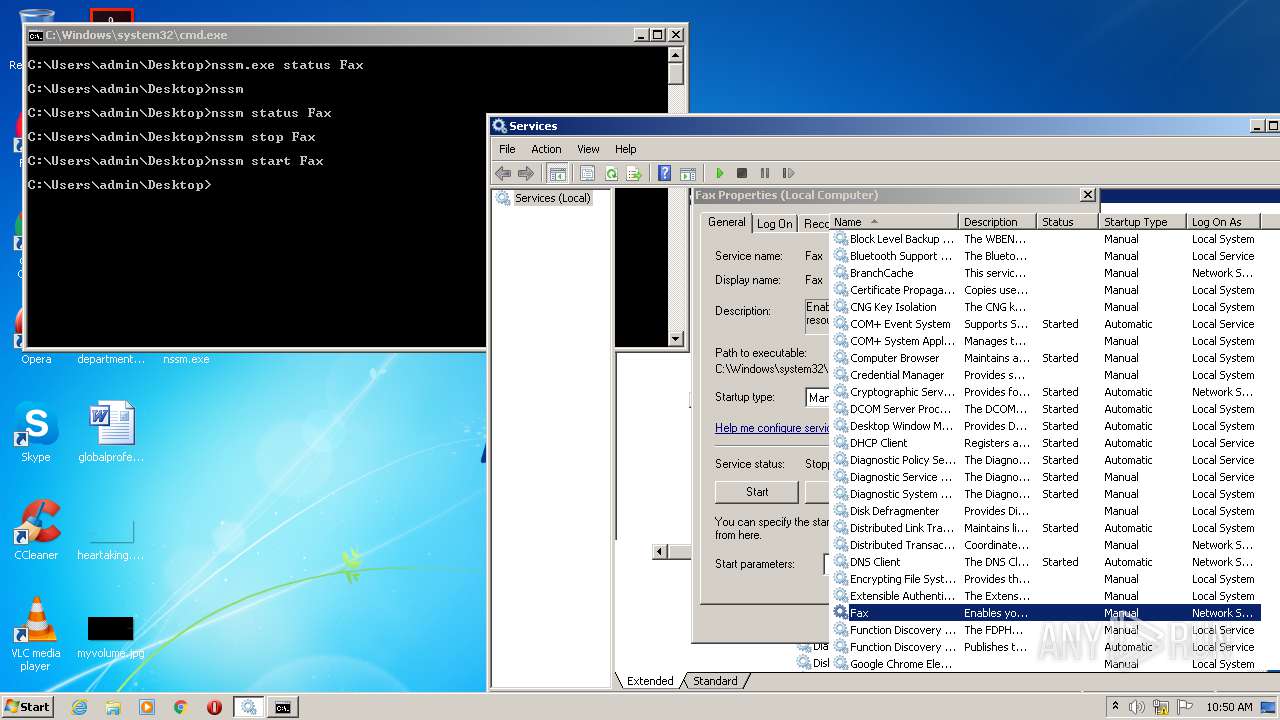
Manual execution by user
- mmc.exe (PID: 2340)
- mmc.exe (PID: 3024)
- cmd.exe (PID: 2560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (79.7) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (8.6) |
| .exe | | | Win16/32 Executable Delphi generic (3.9) |
| .exe | | | Generic Win/DOS Executable (3.8) |
| .exe | | | DOS Executable Generic (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:07:13 08:22:09+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 1914880 |
| InitializedDataSize: | 365056 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d4440 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.25.3.0 |
| ProductVersionNumber: | 2.25.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| FileVersion: | 2.25.3.0 |
| ProductVersion: | 2.25.3.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Jul-2018 06:22:09 |
| Detected languages: |
|
| FileVersion: | 2.25.3.0 |
| ProductVersion: | 2.25.3.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 13-Jul-2018 06:22:09 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001D1EC8 | 0x001D2000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46809 |
.itext | 0x001D3000 | 0x0000166C | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.09103 |
.data | 0x001D5000 | 0x00005188 | 0x00005200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.30137 |
.bss | 0x001DB000 | 0x00005798 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x001E1000 | 0x00003920 | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.16046 |
.didata | 0x001E5000 | 0x00000A3C | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.70076 |
.edata | 0x001E6000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.0919 |
.tls | 0x001E7000 | 0x00000040 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x001E8000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.37999 |
.reloc | 0x001E9000 | 0x0002AB80 | 0x0002AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.72381 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.86531 | 714 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.04312 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 4.40622 | 21640 | UNKNOWN | English - United States | RT_ICON |
4 | 4.79902 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 5.18079 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 4.25643 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4074 | 3.03633 | 356 | UNKNOWN | UNKNOWN | RT_STRING |
4075 | 3.20102 | 1012 | UNKNOWN | UNKNOWN | RT_STRING |
4076 | 3.33578 | 880 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
TMethodImplementationIntercept | 1 | 0x0006296C |
Total processes
45
Monitored processes
9
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
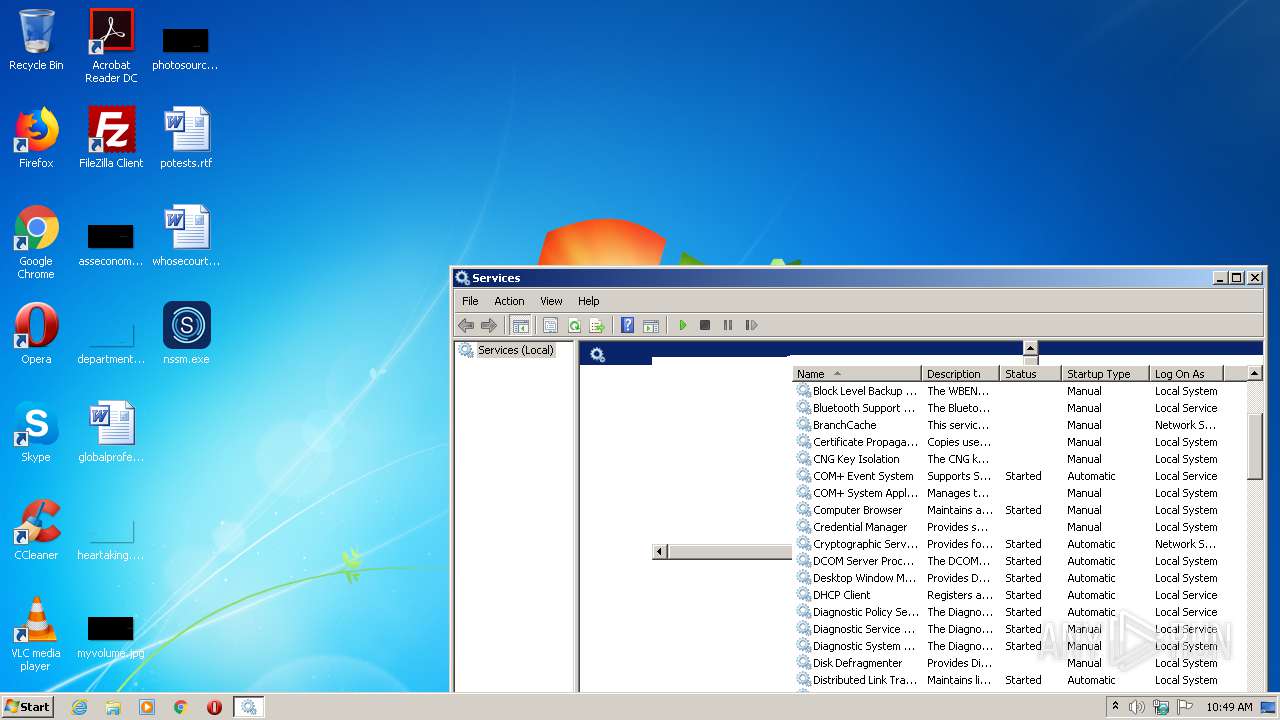
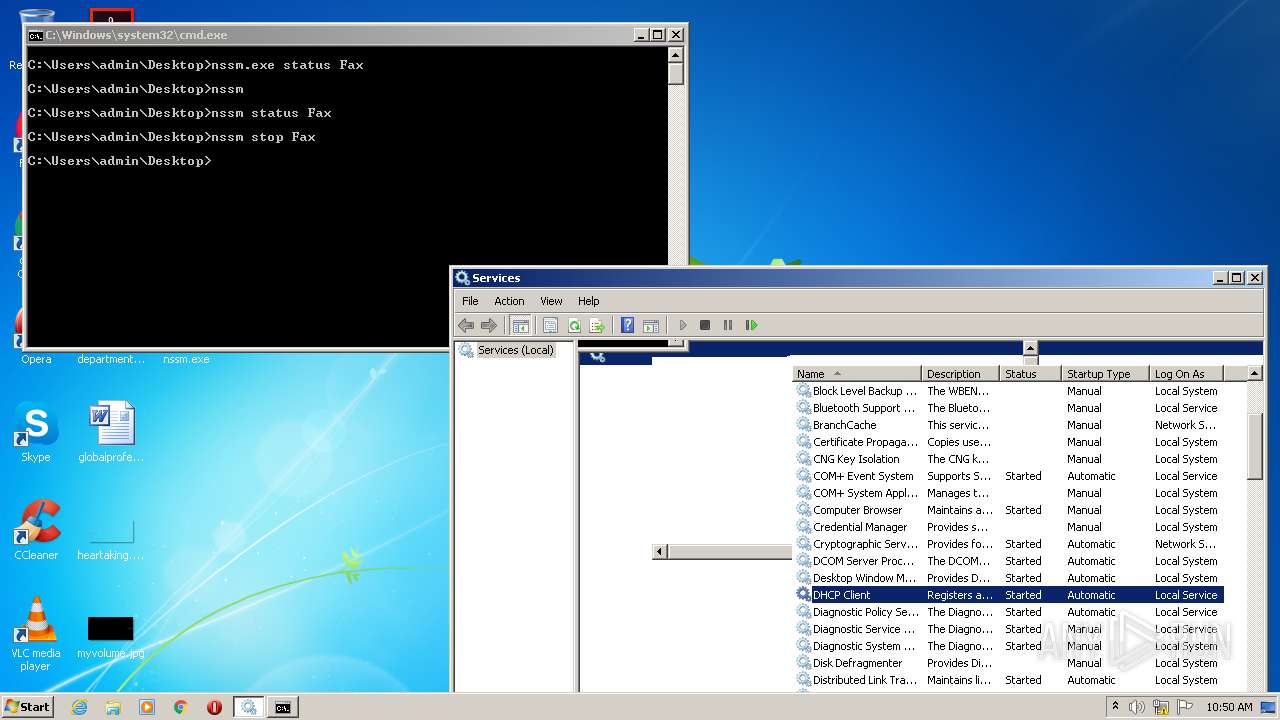
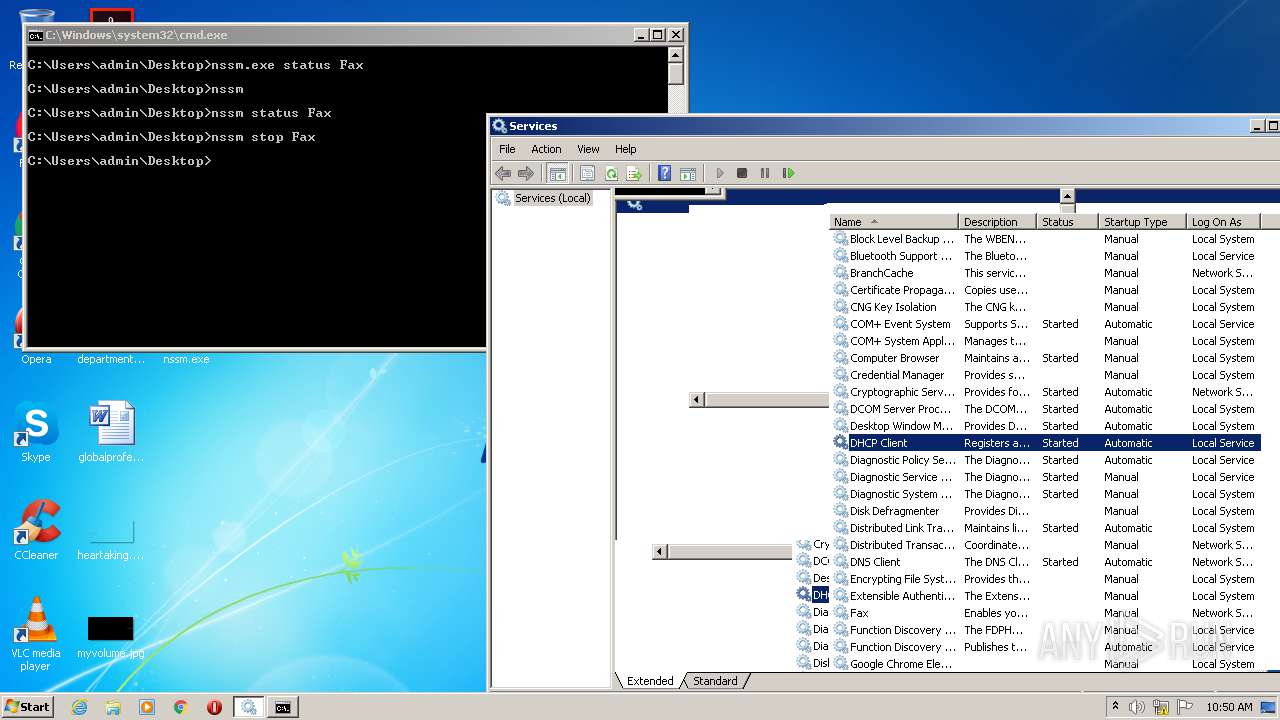
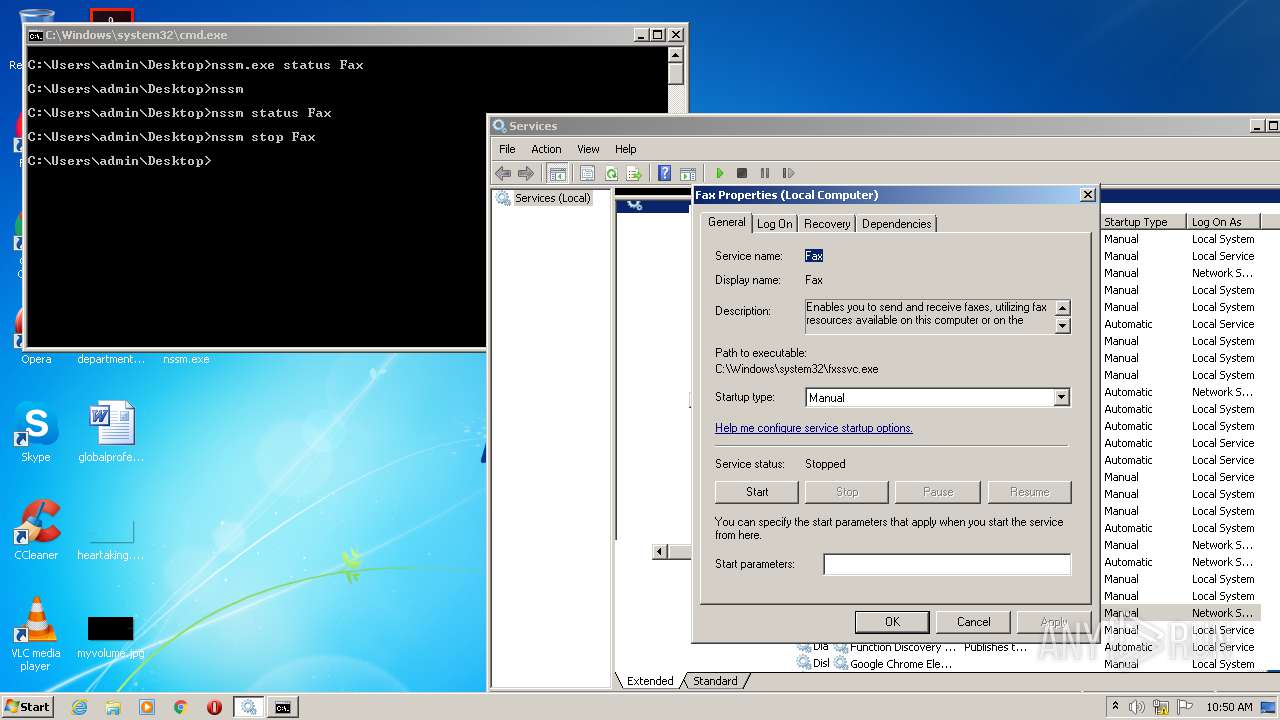
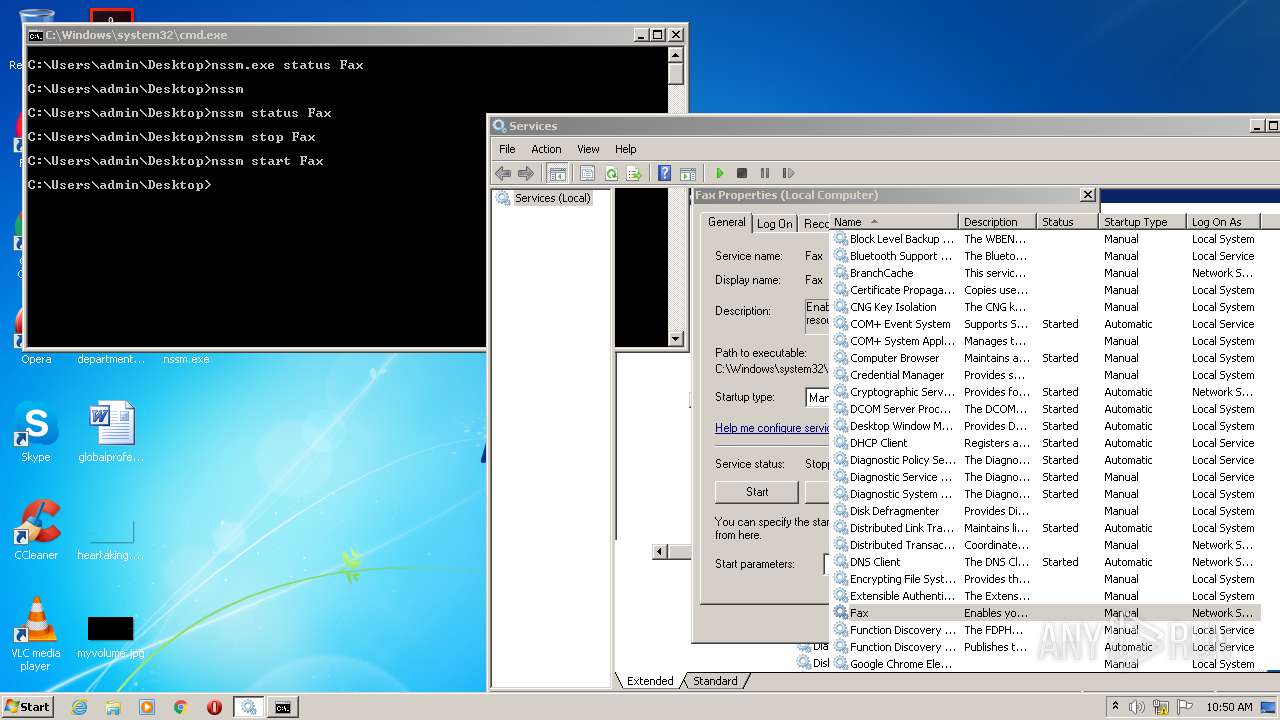
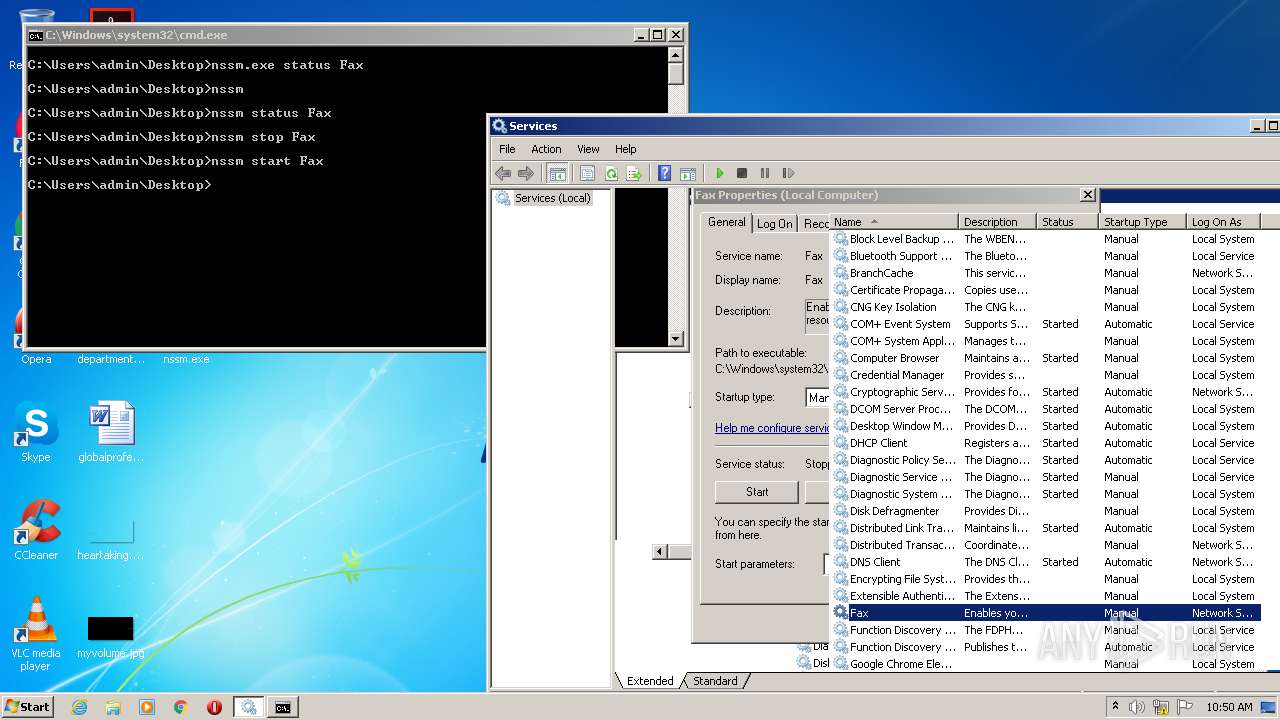
| 1728 | nssm.exe status Fax | C:\Users\admin\Desktop\nssm.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.25.3.0 Modules
| |||||||||||||||
| 2132 | nssm | C:\Users\admin\Desktop\nssm.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.25.3.0 Modules
| |||||||||||||||
| 2260 | nssm status Fax | C:\Users\admin\Desktop\nssm.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.25.3.0 Modules
| |||||||||||||||
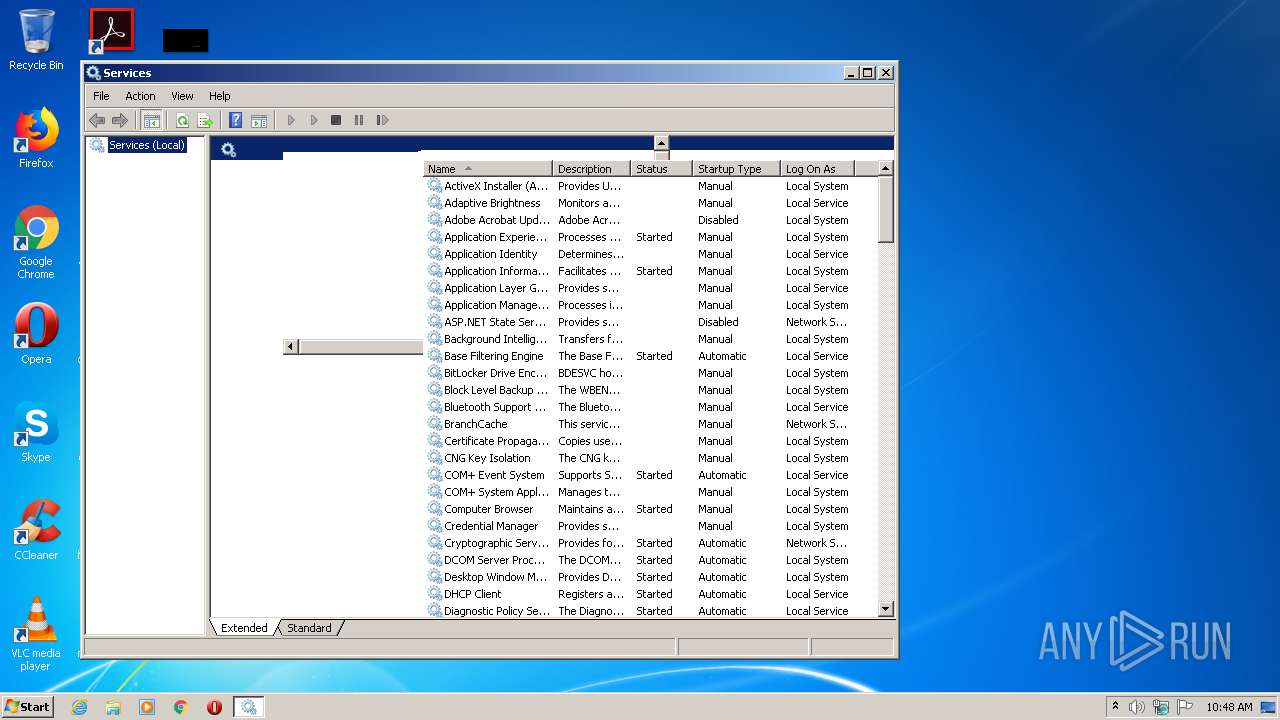
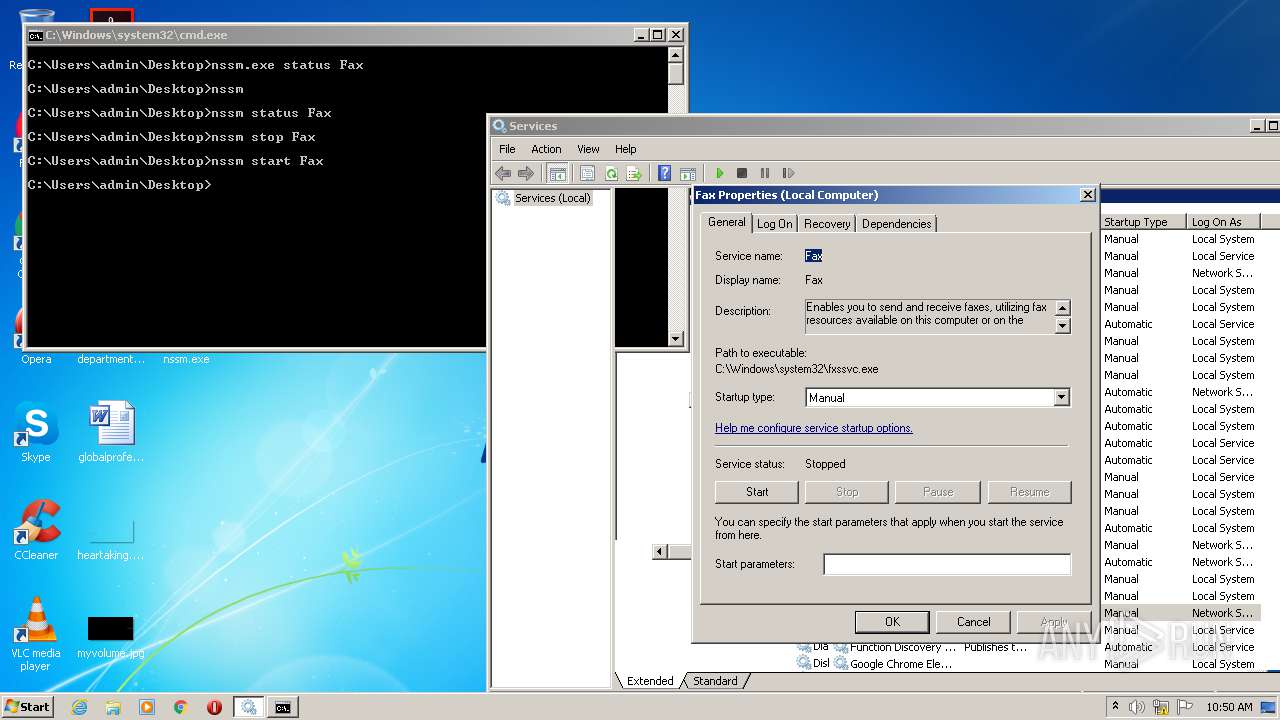
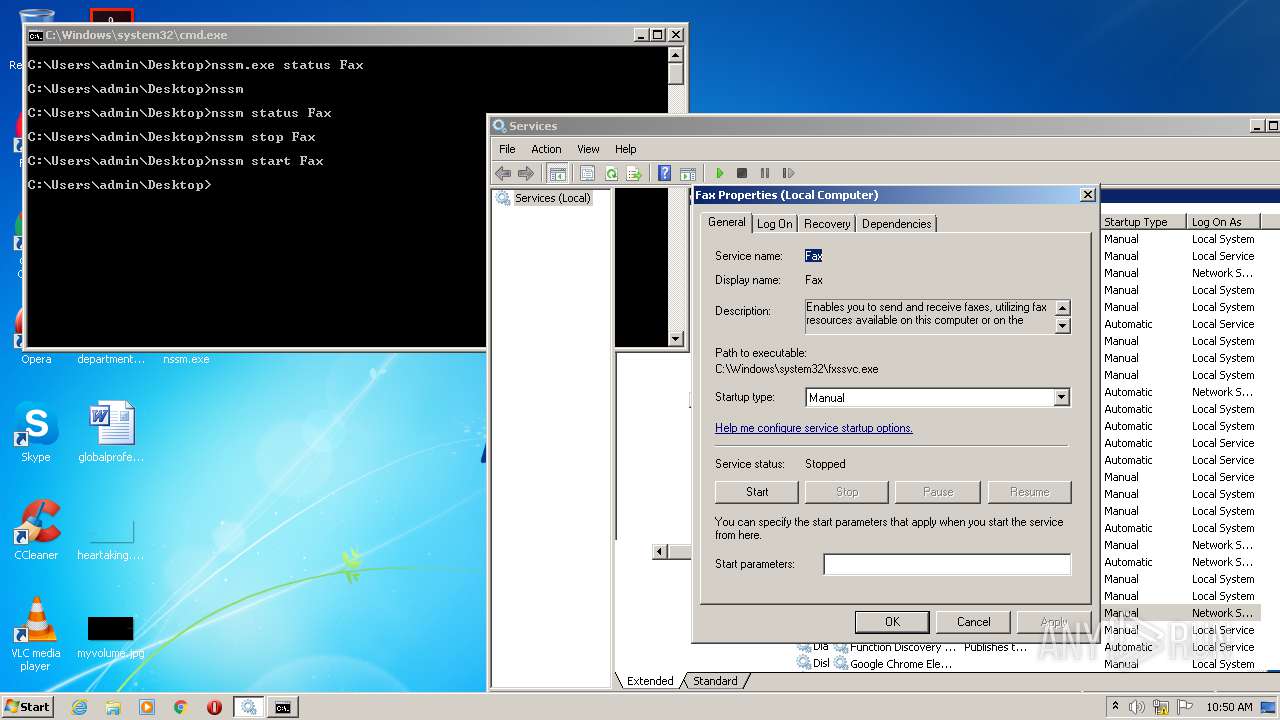
| 2340 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Management Console Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
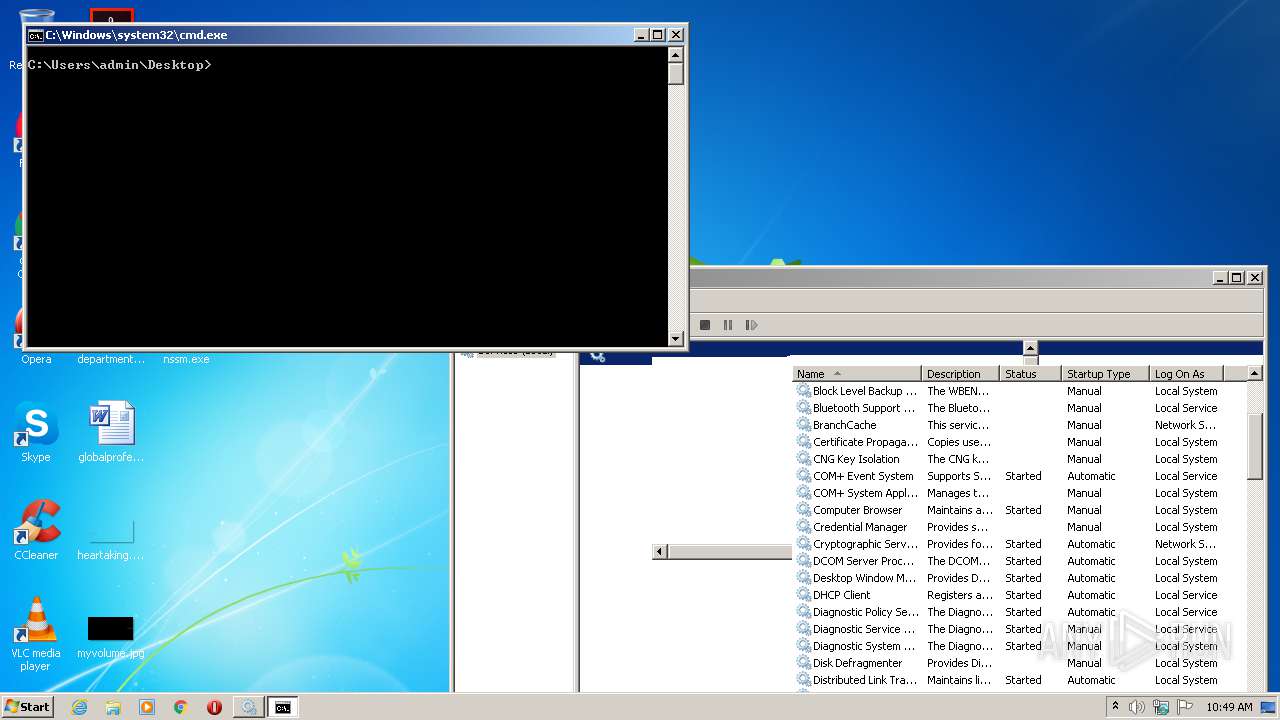
| 2560 | "cmd.exe" /s /k pushd "C:\Users\admin\Desktop" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\Desktop\nssm.exe" | C:\Users\admin\Desktop\nssm.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.25.3.0 Modules
| |||||||||||||||
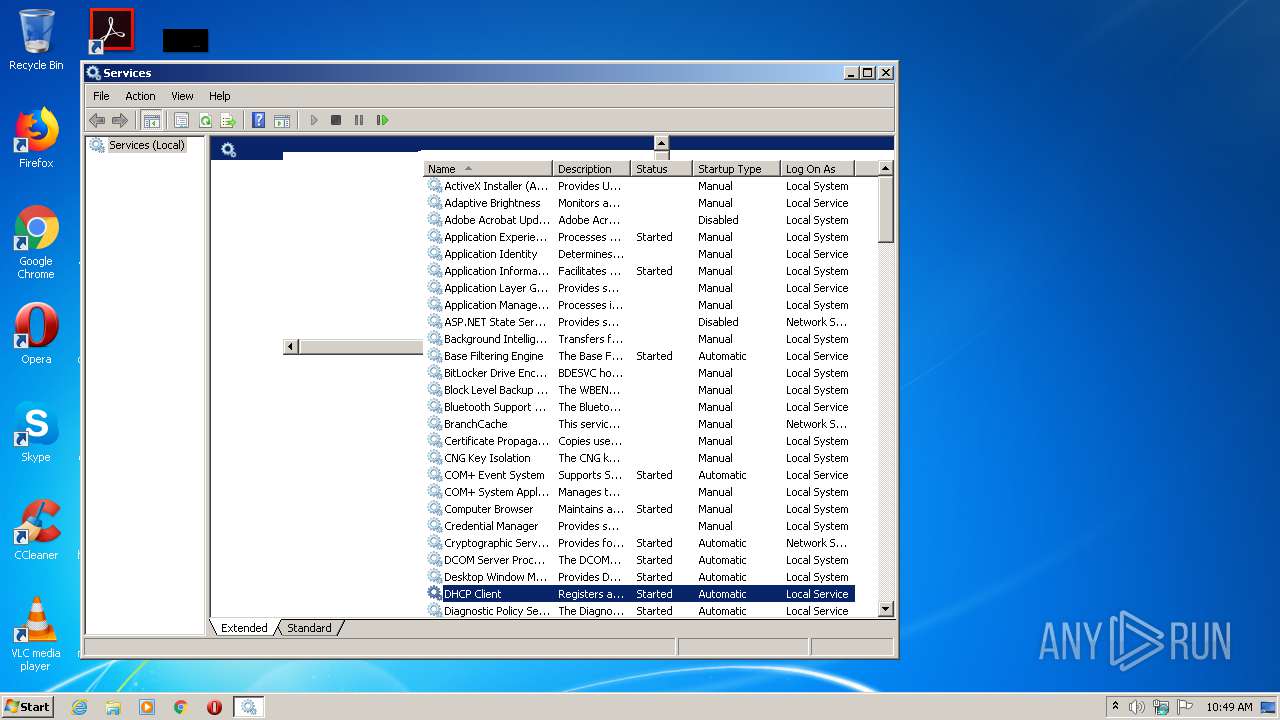
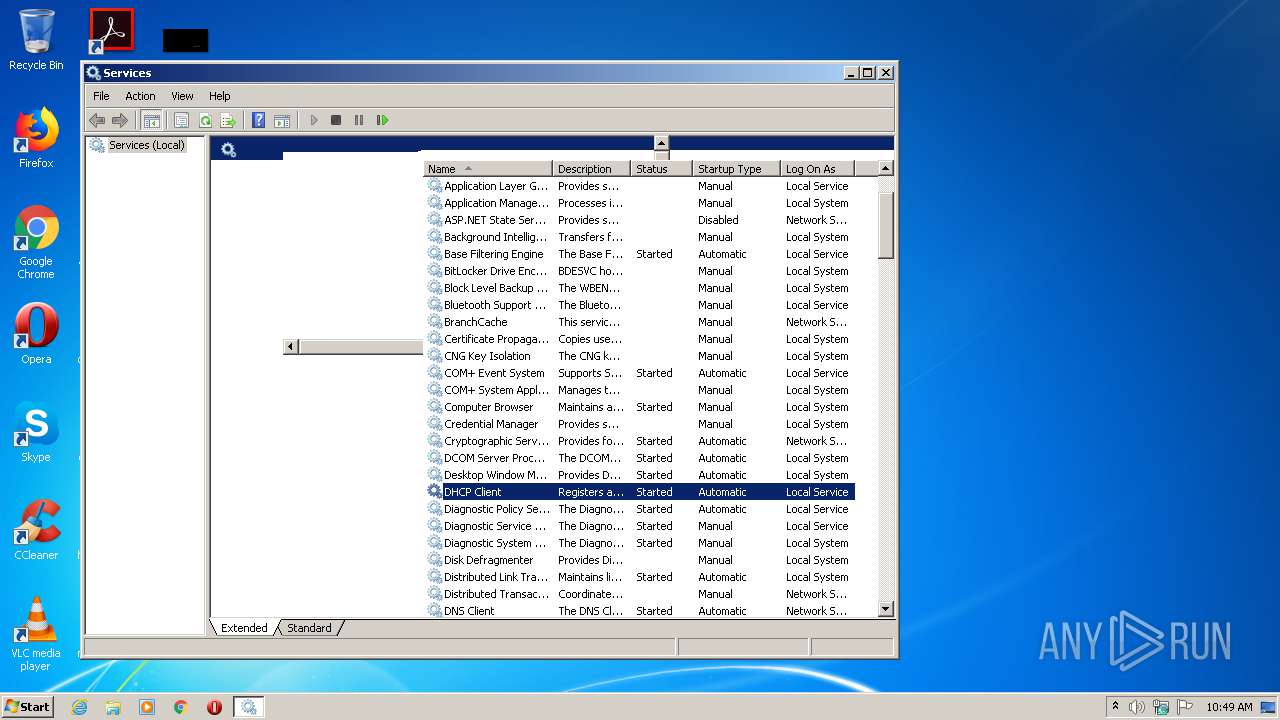
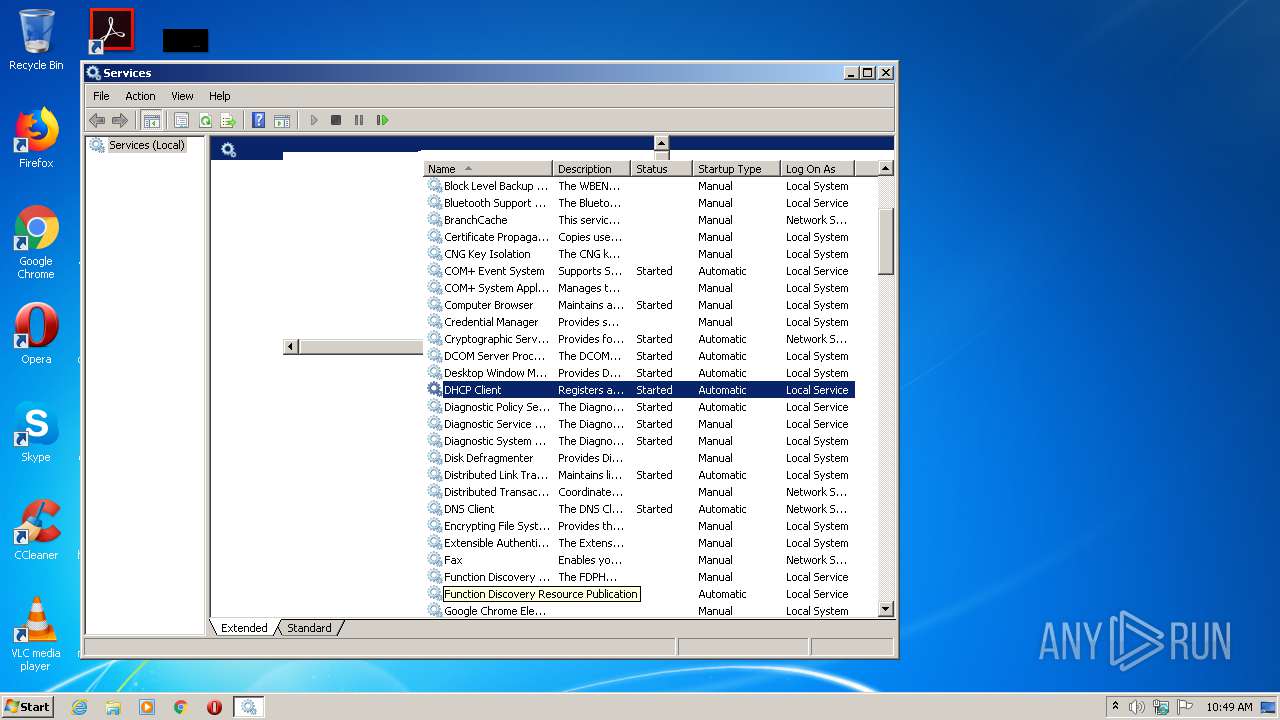
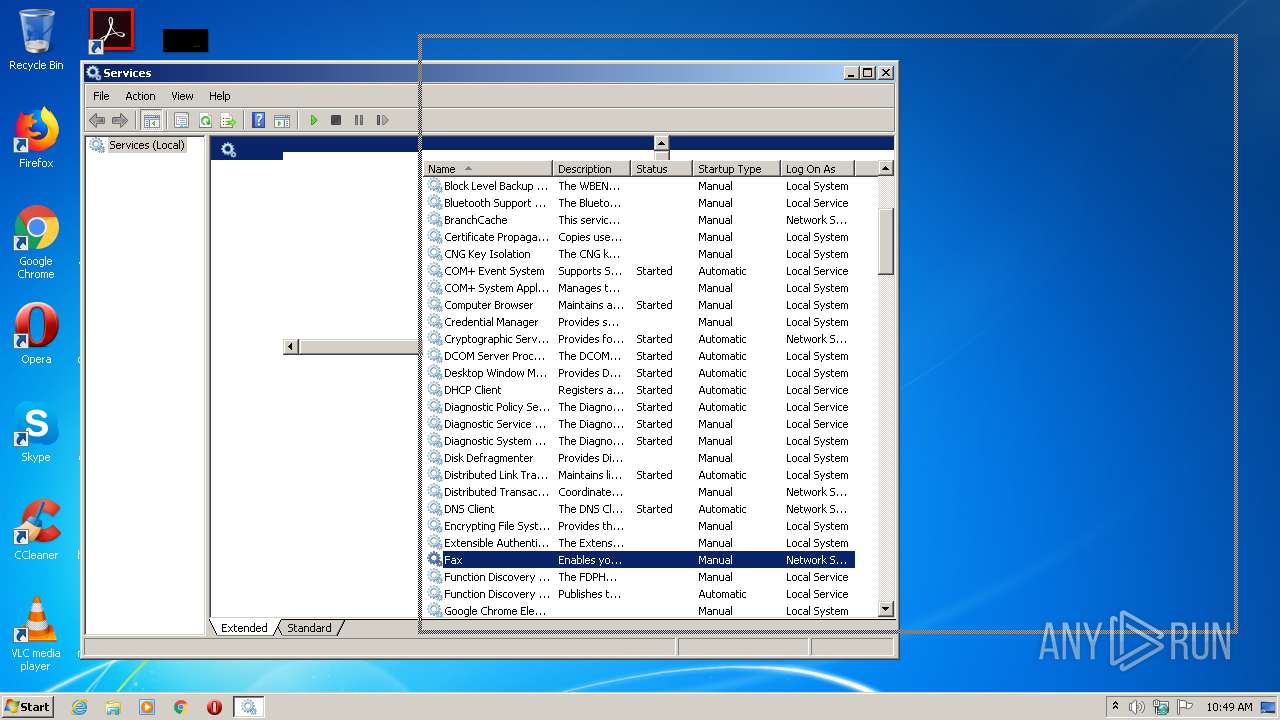
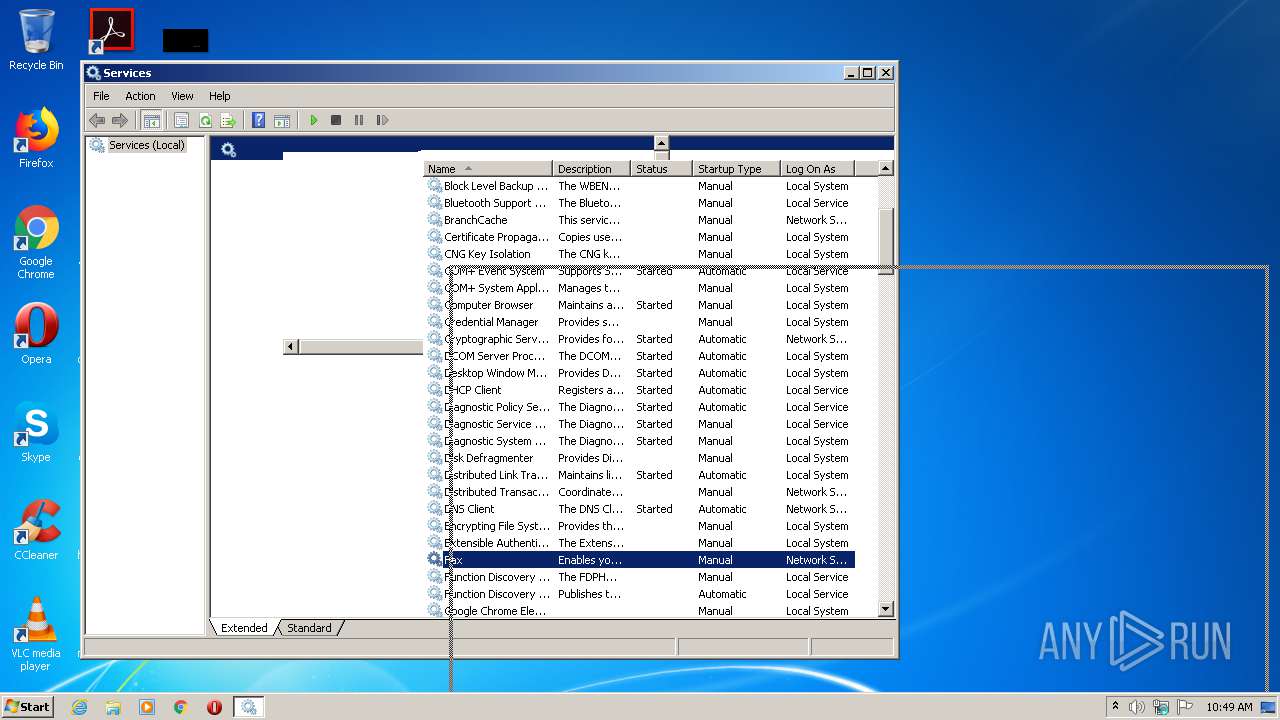
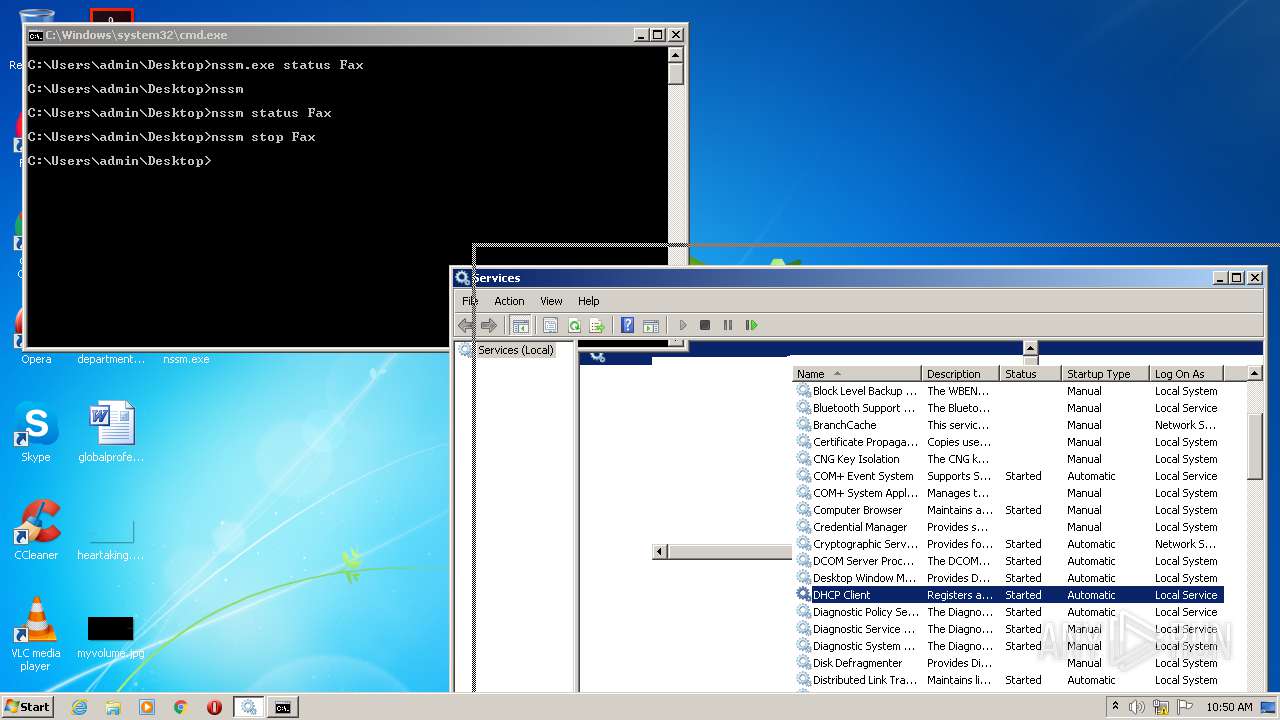
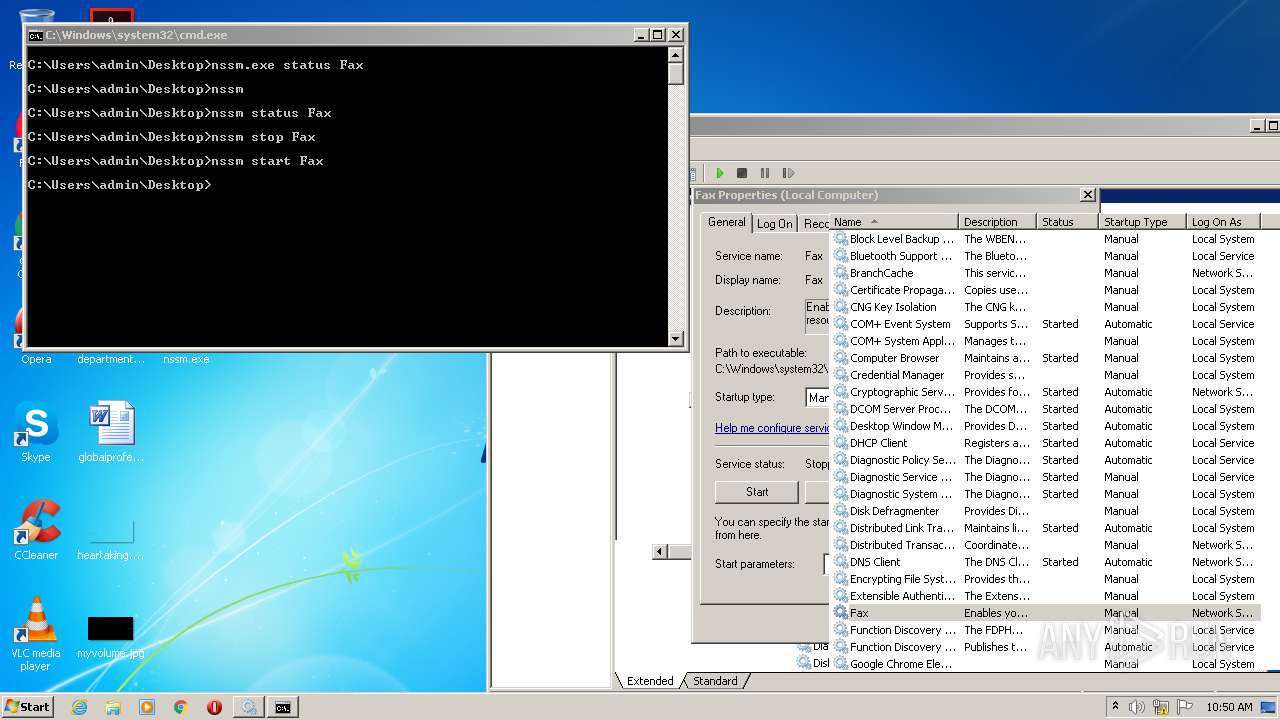
| 3024 | "C:\Windows\system32\mmc.exe" "C:\Windows\system32\services.msc" | C:\Windows\system32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
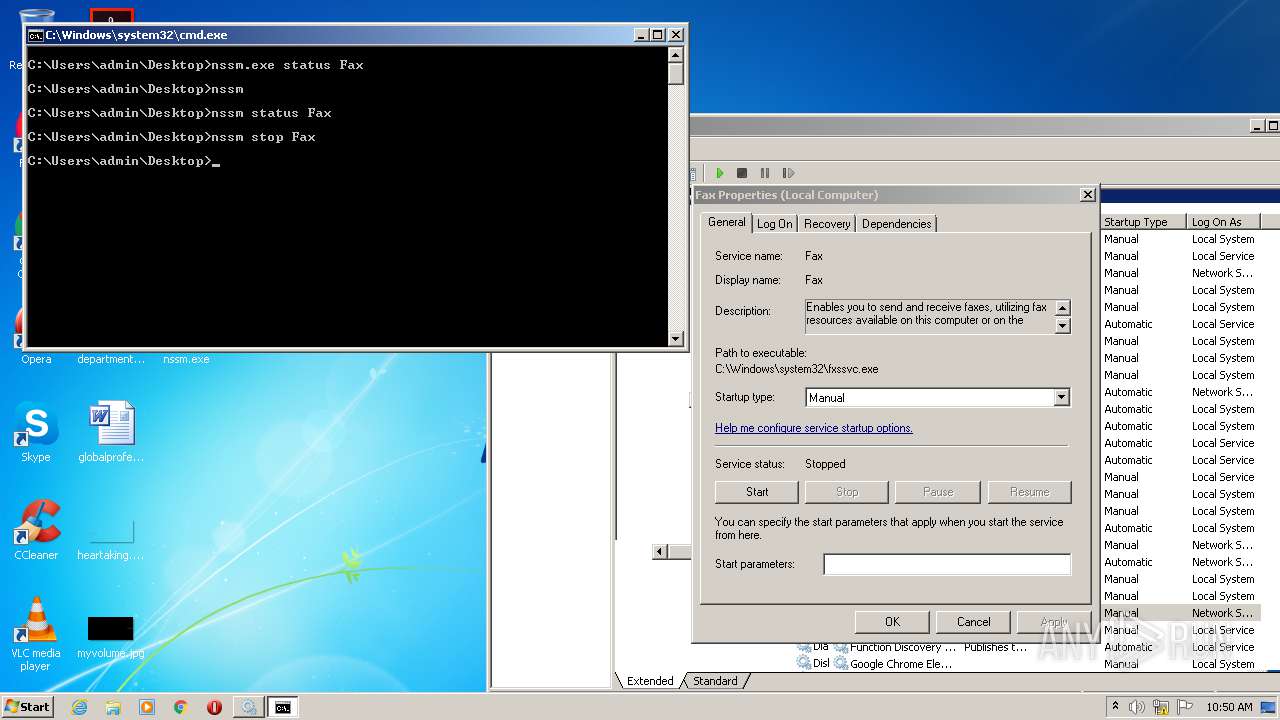
| 3164 | nssm stop Fax | C:\Users\admin\Desktop\nssm.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.25.3.0 Modules
| |||||||||||||||
| 3532 | nssm start Fax | C:\Users\admin\Desktop\nssm.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 2.25.3.0 Modules
| |||||||||||||||
Total events
151
Read events
134
Write events
17
Delete events
0
Modification events
| (PID) Process: | (3024) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3024) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3024) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3024) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3024) mmc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3024) mmc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3024) mmc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @filemgmt.dll,-3502 |
Value: Services | |||
| (PID) Process: | (3024) mmc.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\wbem\servdeps.dll,-1 |
Value: Service Dependencies | |||
Executable files
0
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3024 | mmc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\views[1] | — | |
MD5:— | SHA256:— | |||
| 3024 | mmc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\views[1] | html | |
MD5:A726593A8261930E4786375106FC6BFE | SHA256:E6BFDFBB9A0649EA9D38DE4255C355C581097E6A1035A54943260B22AD45F172 | |||
| 3024 | mmc.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\views[1] | html | |
MD5:A726593A8261930E4786375106FC6BFE | SHA256:E6BFDFBB9A0649EA9D38DE4255C355C581097E6A1035A54943260B22AD45F172 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report