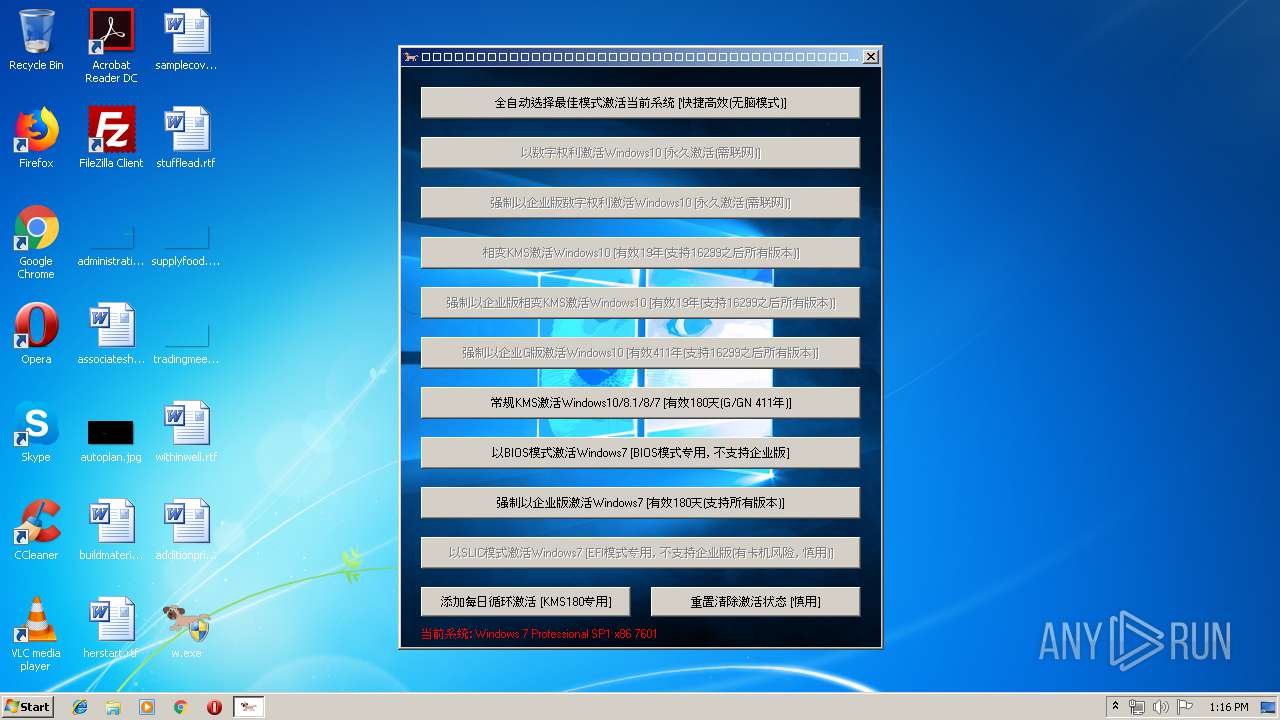
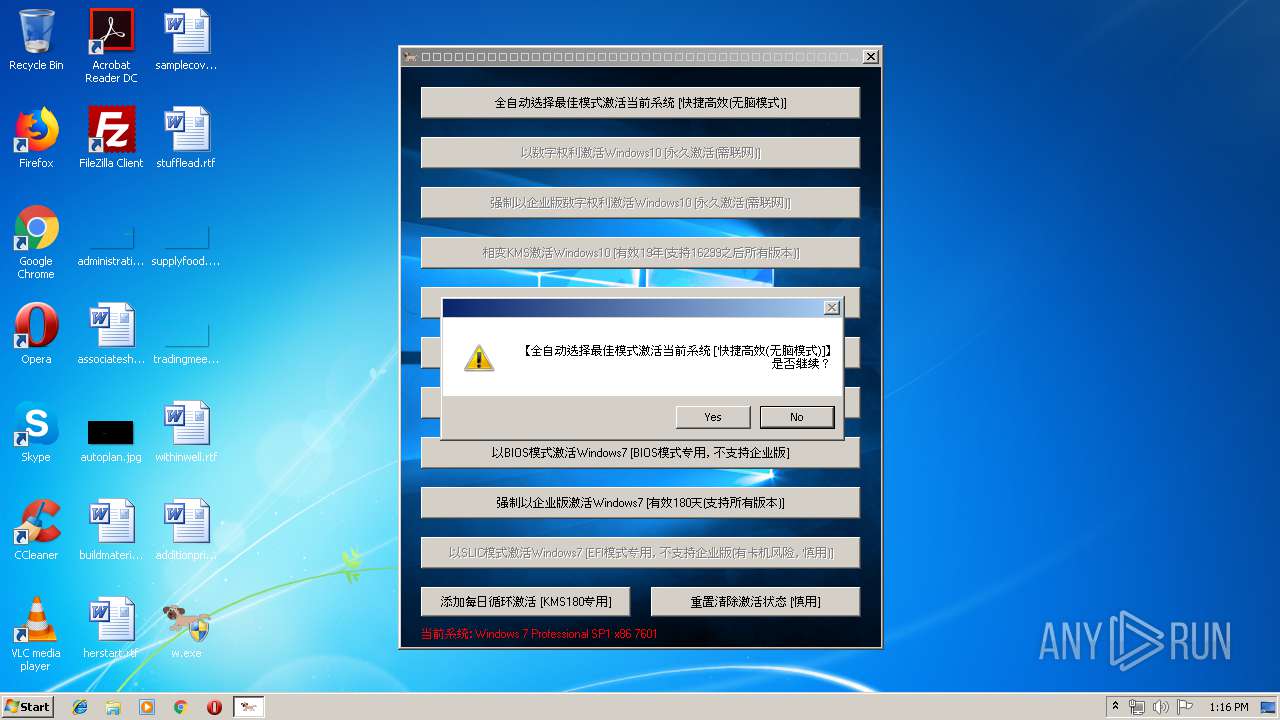
| File name: | w.exe |
| Full analysis: | https://app.any.run/tasks/3dd020bb-2e38-4445-b1f4-2dee1279d03e |
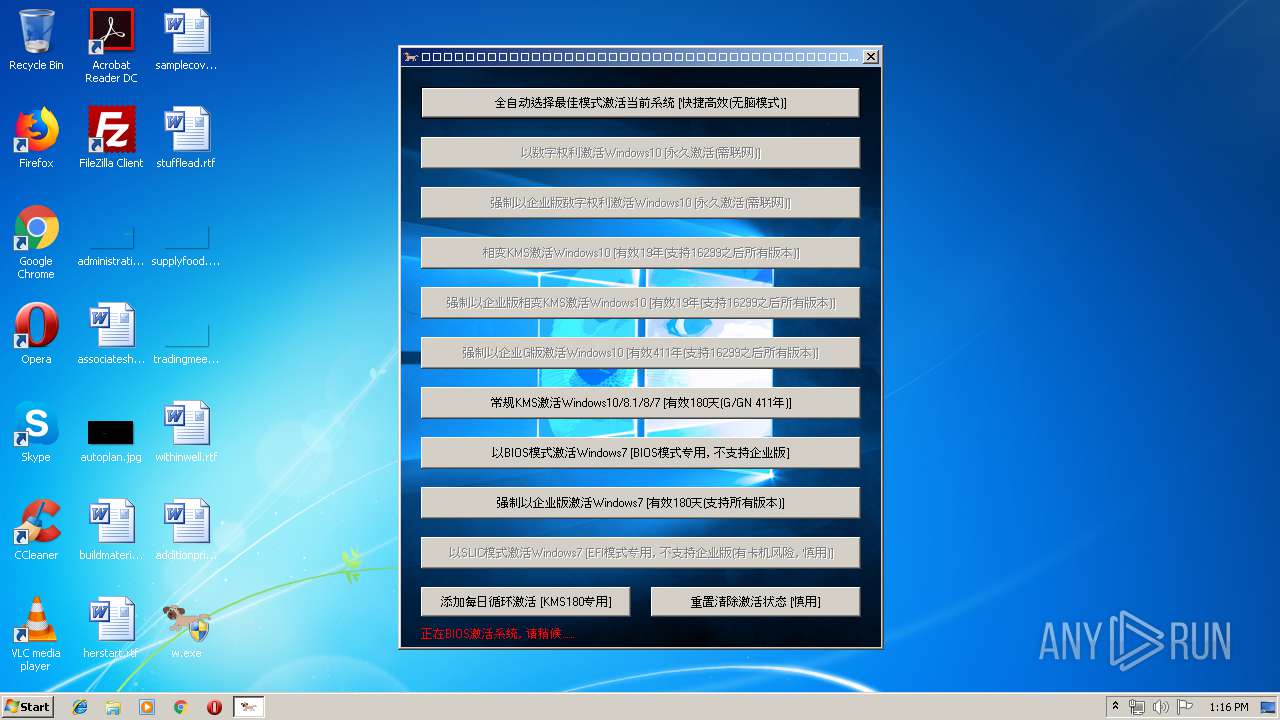
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 12:15:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | F8DA0C6F9D6E17D8F1AD1A826C1DF770 |
| SHA1: | 333B36B1B00EAF743A162492469B60FB6E91DA0C |
| SHA256: | 18083D1596B1F6E1F96D7B8E33ECAA11D4AAE7539A9764B18BFA25D74EB514A7 |
| SSDEEP: | 98304:E8HxyU87A21uL/TypwLvZyzo55WuhtESKyP6EBYxczd:E8wDuL/uwLvZunu8SKyBBYQd |
MALICIOUS
Starts NET.EXE for service management
- cmd.exe (PID: 2444)
Application was dropped or rewritten from another process
- WinLoader.dll (PID: 2892)
Loads dropped or rewritten executable
- cmd.exe (PID: 2628)
SUSPICIOUS
Starts SC.EXE for service management
- cmd.exe (PID: 1344)
- cmd.exe (PID: 2124)
- cmd.exe (PID: 3364)
Low-level read access rights to disk partition
- bcdedit.exe (PID: 3808)
Starts CMD.EXE for commands execution
- w.exe (PID: 2660)
- WinLoader.dll (PID: 2892)
- cmd.exe (PID: 3276)
- cmd.exe (PID: 2780)
Executable content was dropped or overwritten
- w.exe (PID: 2660)
Starts application with an unusual extension
- cmd.exe (PID: 2628)
Application launched itself
- cmd.exe (PID: 3276)
- cmd.exe (PID: 2780)
Uses ICACLS.EXE to modify access control list
- cmd.exe (PID: 3120)
- cmd.exe (PID: 2596)
Executes scripts
- cmd.exe (PID: 2208)
- cmd.exe (PID: 3912)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (64.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.6) |
| .exe | | | Win32 Executable (generic) (10.6) |
| .exe | | | Generic Win/DOS Executable (4.7) |
| .exe | | | DOS Executable Generic (4.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:01 13:49:19+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 339968 |
| InitializedDataSize: | 3665920 |
| UninitializedDataSize: | 4247552 |
| EntryPoint: | 0x45f3e0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.12.0.1 |
| ProductVersionNumber: | 0.12.0.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 0.12.0.1 |
| Comments: | Windows超级土狗 |
| FileDescription: | Windows超级土狗 |
| ProductVersion: | 0.12.0.1 |
| LegalCopyright: | Free |
| Productname: | Windows超级土狗 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Apr-2019 11:49:19 |
| Detected languages: |
|
| FileVersion: | 0.12.0.1 |
| Comments: | Windows超级土狗 |
| FileDescription: | Windows超级土狗 |
| ProductVersion: | 0.12.0.1 |
| LegalCopyright: | Free |
| Productname: | Windows超级土狗 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Apr-2019 11:49:19 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0040D000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0040E000 | 0x00053000 | 0x00052200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99815 |
.rsrc | 0x00461000 | 0x0037F000 | 0x0037EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99819 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.33385 | 1629 | Latin 1 / Western European | Chinese - PRC | RT_MANIFEST |
2 | 3.37556 | 16936 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
7 | 7.86716 | 1428 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
8 | 7.89305 | 1674 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
9 | 7.82729 | 1168 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
10 | 7.86326 | 1532 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
11 | 7.89633 | 1628 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
12 | 7.80883 | 1126 | Latin 1 / Western European | English - United Kingdom | RT_STRING |
99 | 2.0815 | 20 | Latin 1 / Western European | English - United Kingdom | RT_GROUP_ICON |
169 | 1.84274 | 20 | Latin 1 / Western European | English - United Kingdom | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.DLL |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
84
Monitored processes
33
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | C:\Windows\system32\cmd.exe /c bcdedit.exe | C:\Windows\system32\cmd.exe | — | w.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1344 | C:\Windows\system32\cmd.exe /c sc.exe query sppsvc | C:\Windows\system32\cmd.exe | — | w.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1572 | C:\Windows\system32\cmd.exe /c wmic.exe path SoftwareLicensingProduct where (Name like "Windows%%" and LicenseStatus="1" and GracePeriodRemaining="0" and PartialProductKey is not NULL) get Name | C:\Windows\system32\cmd.exe | — | w.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1844 | C:\Windows\System32\cscript.exe //nologo C:\Windows\System32\slmgr.vbs -ilc "C:\Dell.XRM-MS" | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2124 | C:\Windows\system32\cmd.exe /c sc.exe config sppsvc start= auto | C:\Windows\system32\cmd.exe | — | w.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2156 | C:\Windows\system32\net1 start sppsvc /y | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2208 | cmd.exe /A /C "C:\Windows\System32\cscript.exe //nologo C:\Windows\System32\slmgr.vbs -ilc "C:\Dell.XRM-MS"" | C:\Windows\system32\cmd.exe | — | WinLoader.dll | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2316 | cmd.exe /c takeown /f C:\ldrscan\bootwin | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2344 | icacls C:\ldrscan\bootwin /grant *S-1-1-0:(F) | C:\Windows\system32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2444 | C:\Windows\system32\cmd.exe /c net.exe start sppsvc /y | C:\Windows\system32\cmd.exe | — | w.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
223
Read events
223
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2660 | w.exe | C:\Users\admin\AppData\Local\Temp\aut7581.tmp | — | |
MD5:— | SHA256:— | |||
| 2660 | w.exe | C:\Users\admin\AppData\Local\Temp\131606758342275\windoge.jpd | — | |
MD5:— | SHA256:— | |||
| 2660 | w.exe | C:\Users\admin\AppData\Local\Temp\autD6AE.tmp | — | |
MD5:— | SHA256:— | |||
| 2660 | w.exe | C:\Users\admin\AppData\Local\Temp\autD5A4.tmp | binary | |
MD5:— | SHA256:— | |||
| 2892 | WinLoader.dll | C:\System Volume Information\MountPointManagerRemoteDatabase | binary | |
MD5:— | SHA256:— | |||
| 2660 | w.exe | C:\Users\admin\AppData\Local\Temp\131606758342275\WinLoader.dll | executable | |
MD5:— | SHA256:— | |||
| 2892 | WinLoader.dll | C:\Dell.XRM-MS | xml | |
MD5:18B1E45BF56F40C3C4BBE65831178216 | SHA256:D072A059D3ED3E75C98B85B41E4319E8D5CFAE0E0C239B62436A3AD34003AB4A | |||
| 2660 | w.exe | C:\Users\admin\AppData\Local\Temp\131606758342275\Keys.ini | text | |
MD5:3BA4950BCF43B1C7B714A1D93B57EA86 | SHA256:1384C5FD758A1BD8C9372594503E22D71B0877D332886A1B7D50CB86C4A0A13C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report