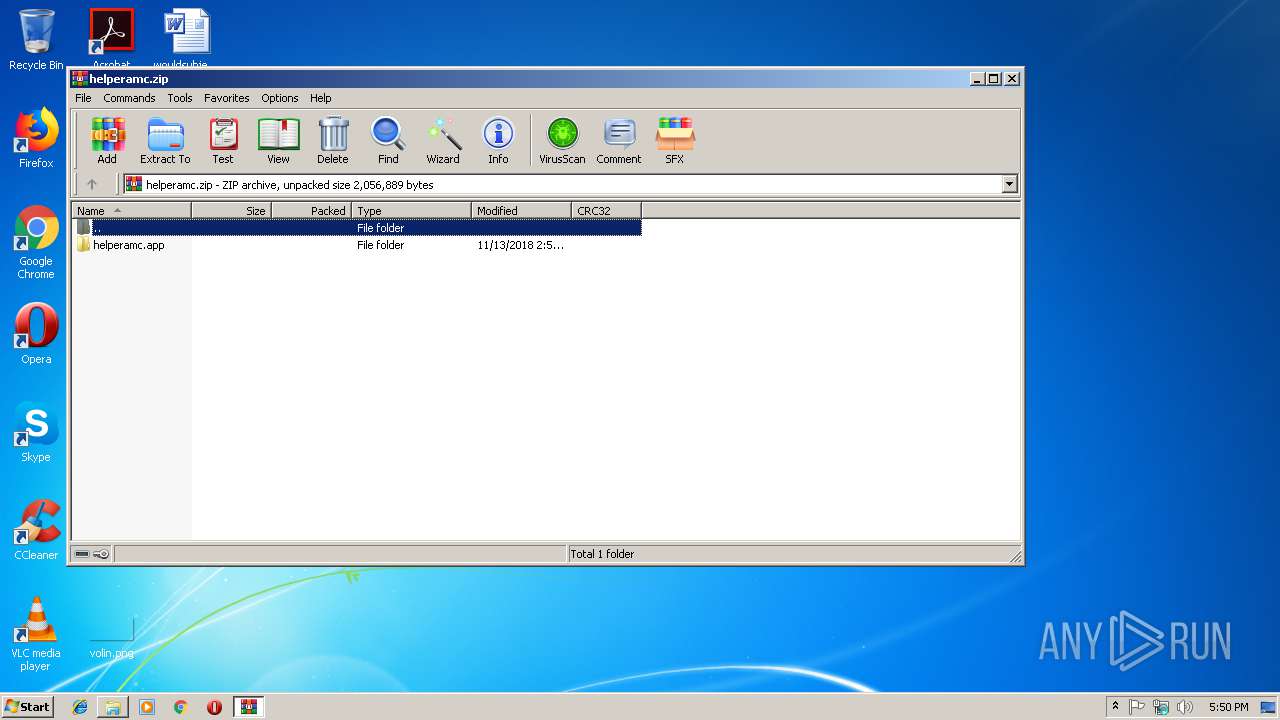
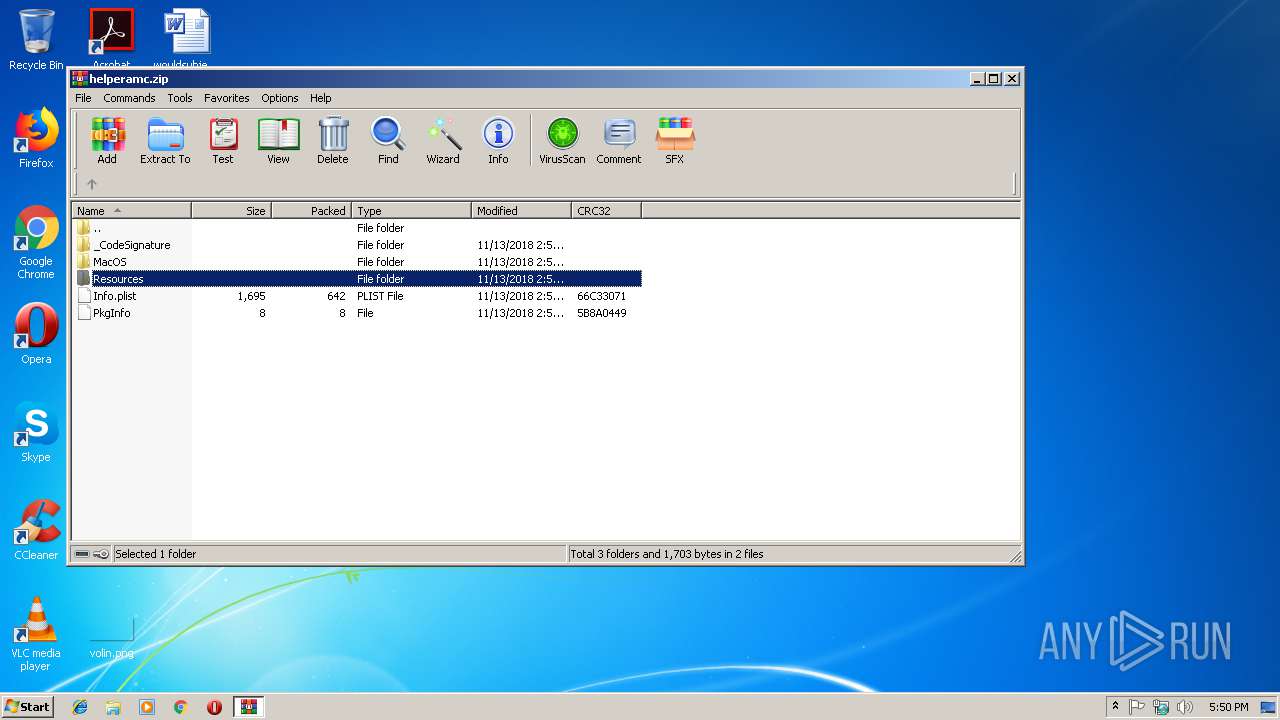
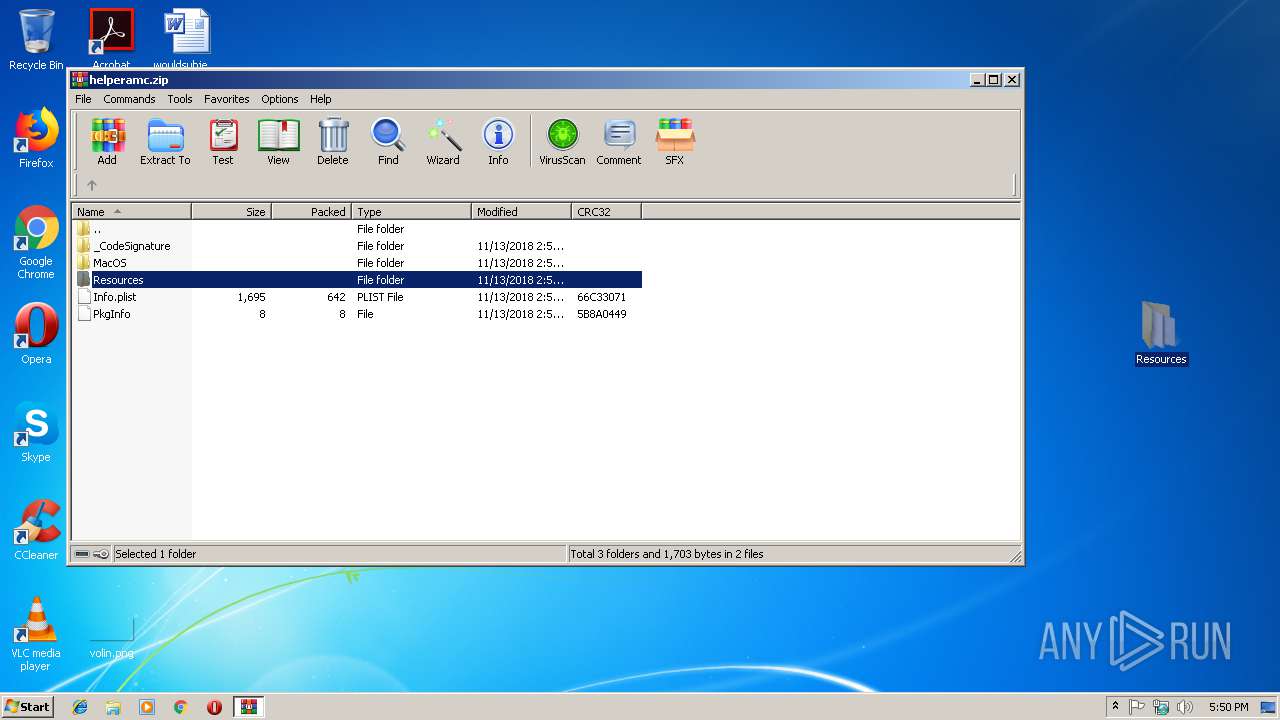
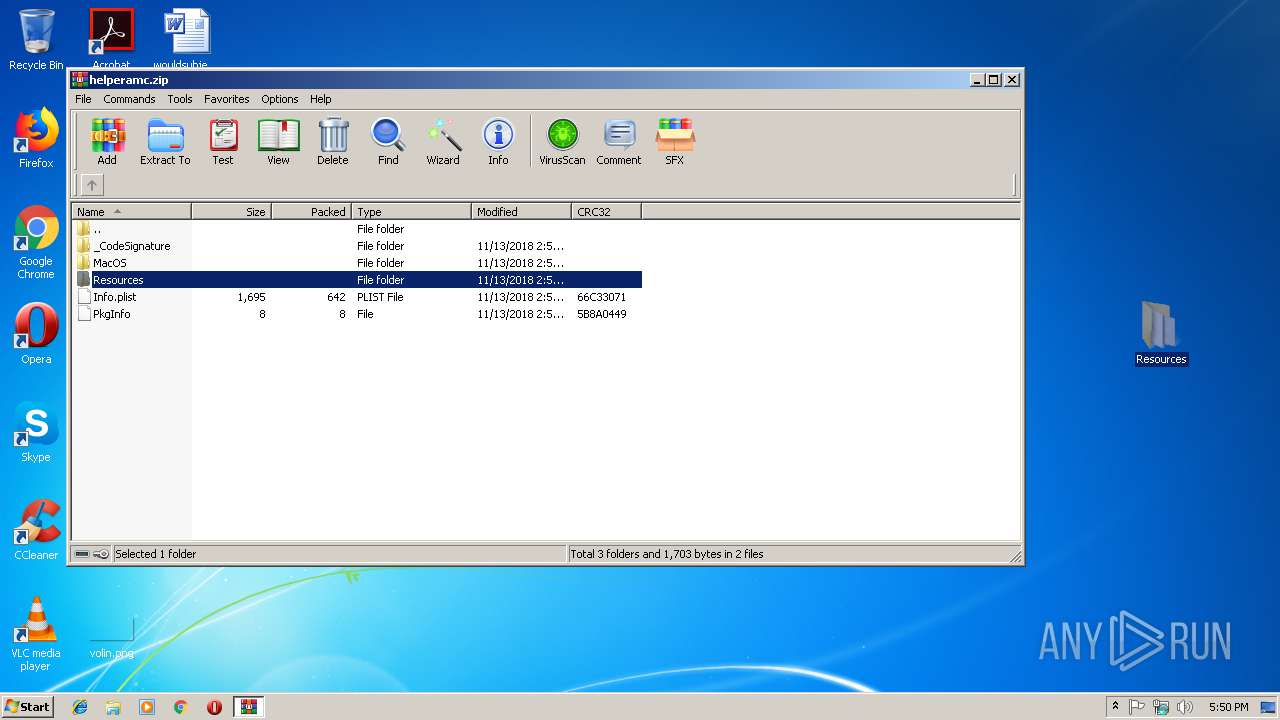
| File name: | helperamc.zip |
| Full analysis: | https://app.any.run/tasks/e1cef1c1-cf76-4c16-9dc5-5f69b2b5b0f8 |
| Verdict: | No threats detected |
| Analysis date: | February 13, 2019, 17:49:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 1A5A7532854AB45AC74B1C657FE47941 |
| SHA1: | B5C85C802918D919ECB718865E185463AFEB4C1A |
| SHA256: | 18042540B39D543E9E648E5D0B059D2E8C74889BB9353674BE59C94DA265F393 |
| SSDEEP: | 12288:N3MbzWwNOhPdM1VTqVcTWzSZ2iOpKl6gHBvscs/AcCpfCBw/7ulgeLMYO:VWywk32TW7jpKlvHBvscifCj7uKeLZO |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 2860)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xpi | | | Mozilla Firefox browser extension (66.6) |
|---|---|---|
| .zip | | | ZIP compressed archive (33.3) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:11:13 14:57:01 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
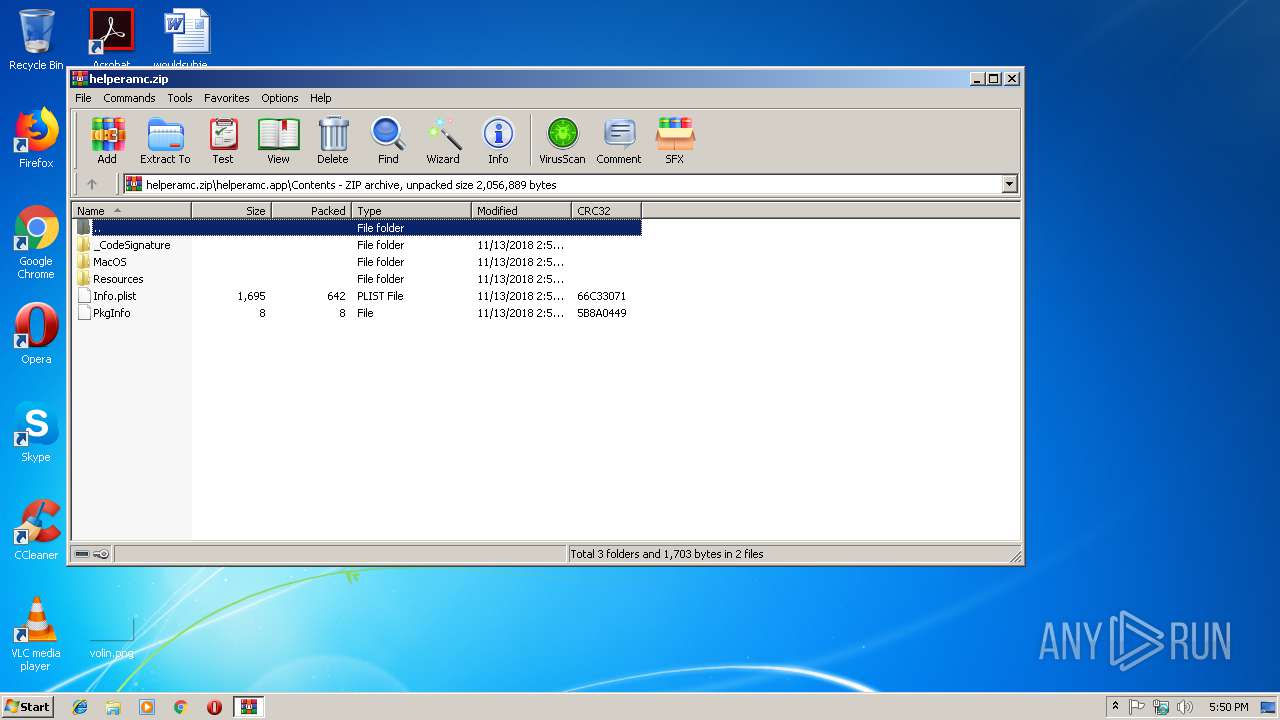
| ZipFileName: | helperamc.app/ |
Total processes
33
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
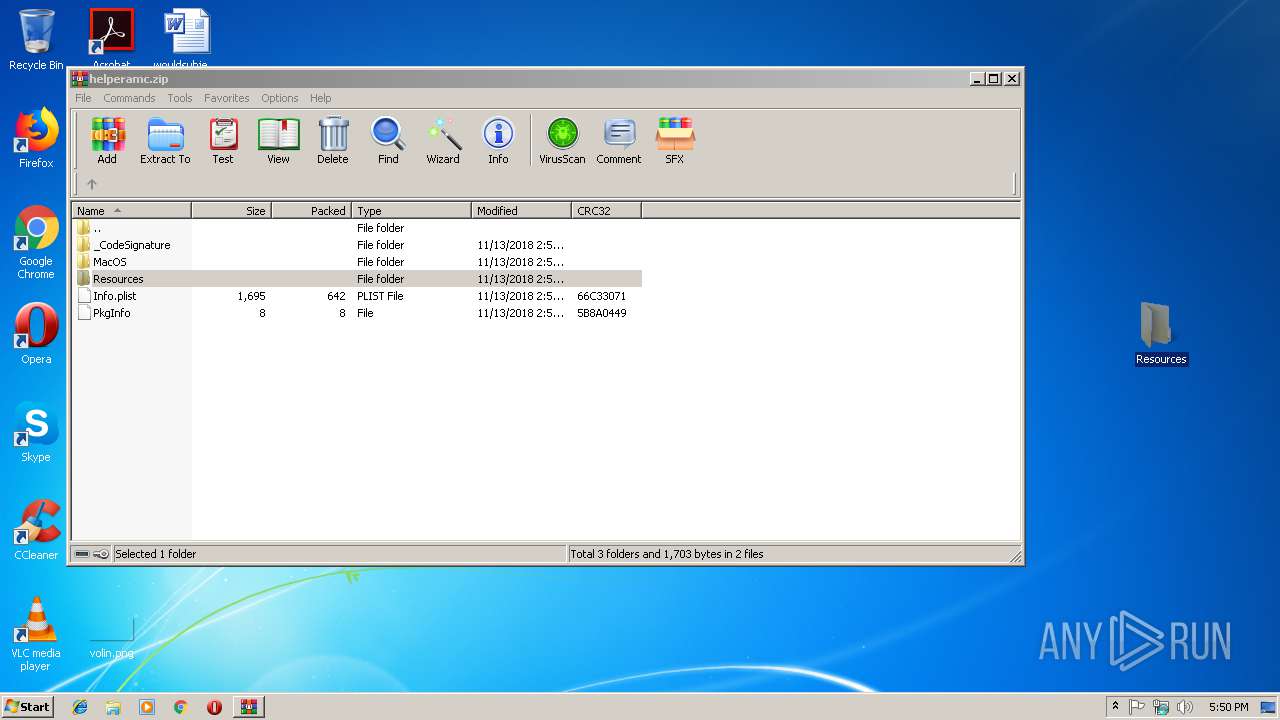
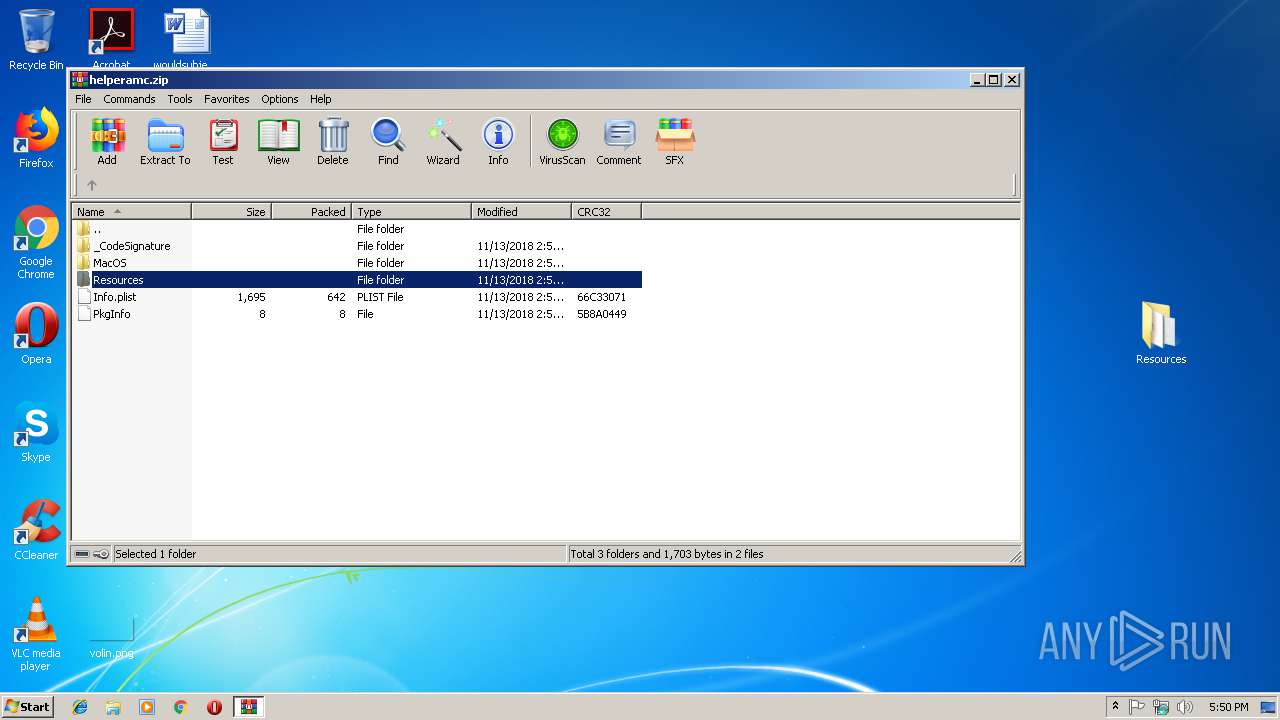
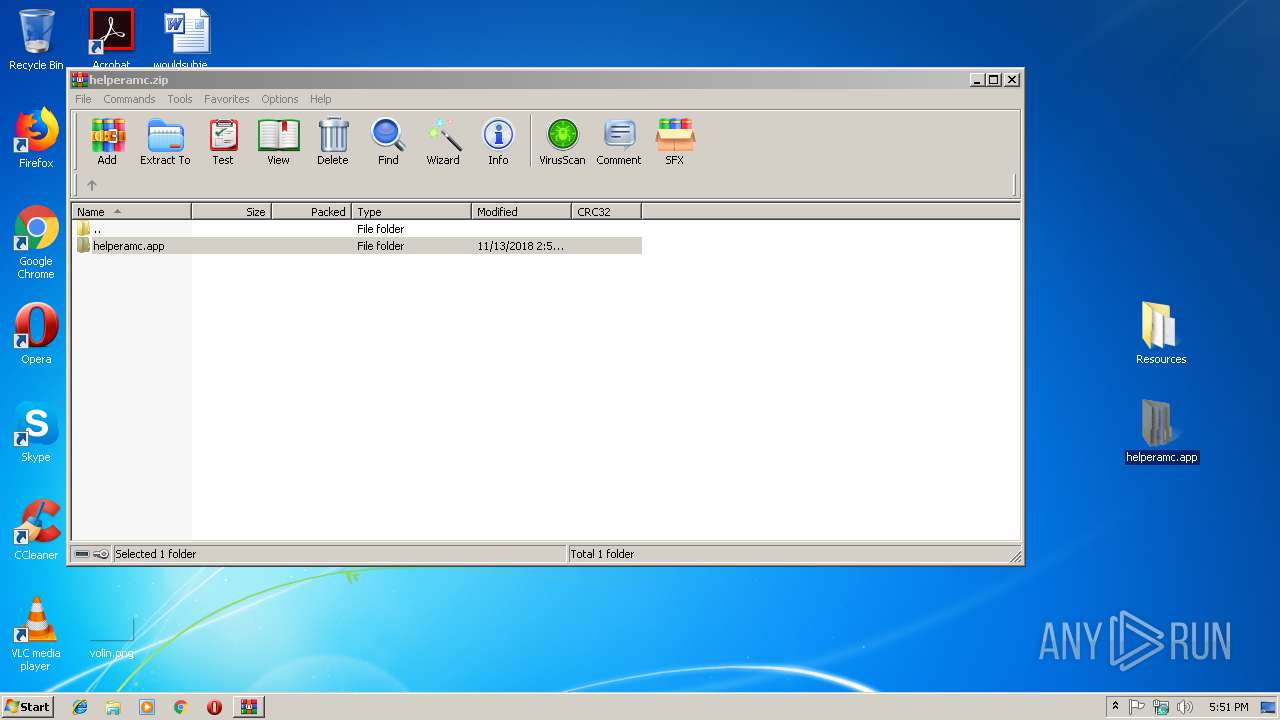
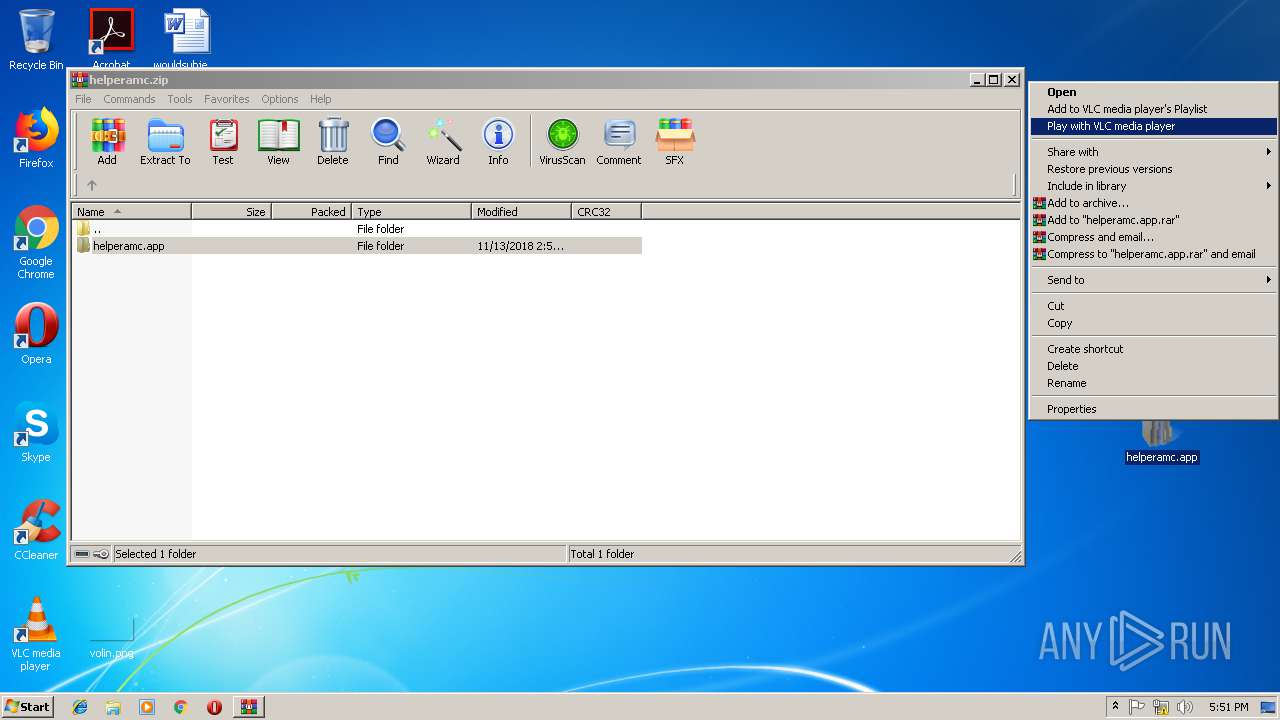
| 2860 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\helperamc.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
434
Read events
422
Write events
12
Delete events
0
Modification events
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\helperamc.zip | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4804 |
Value: JScript Script File | |||
| (PID) Process: | (2860) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\ieframe.dll,-912 |
Value: HTML Document | |||
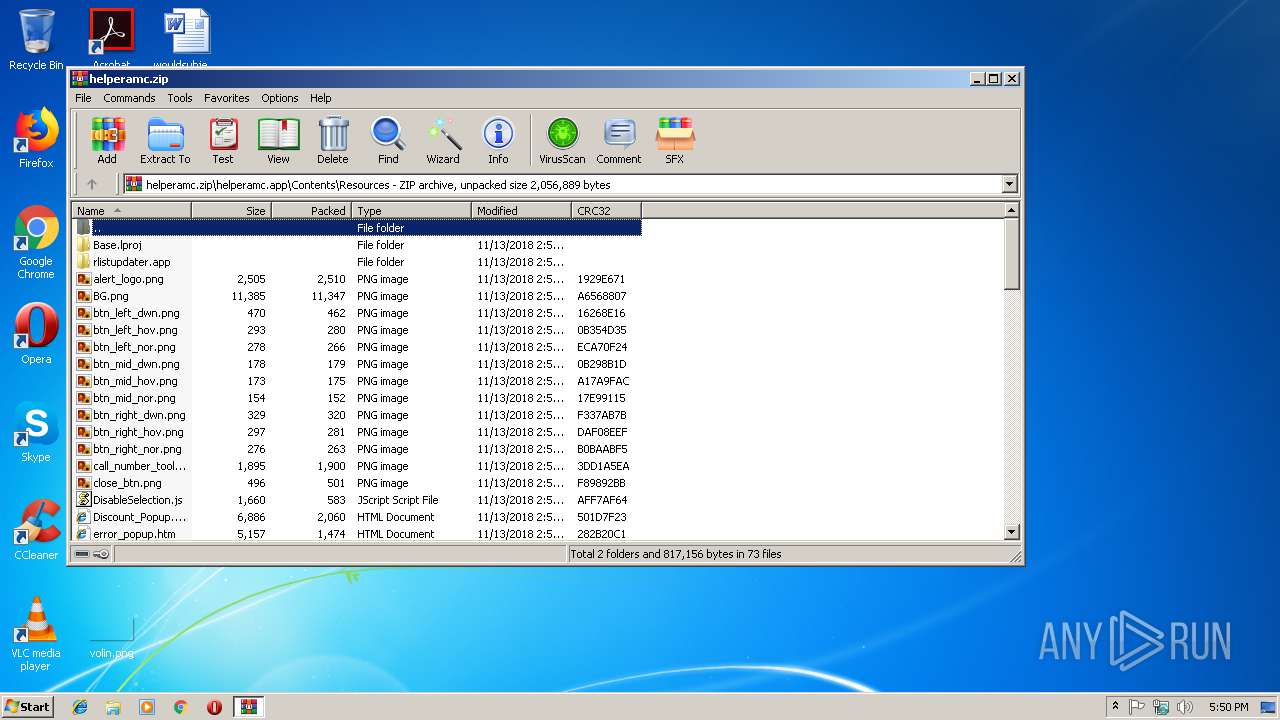
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
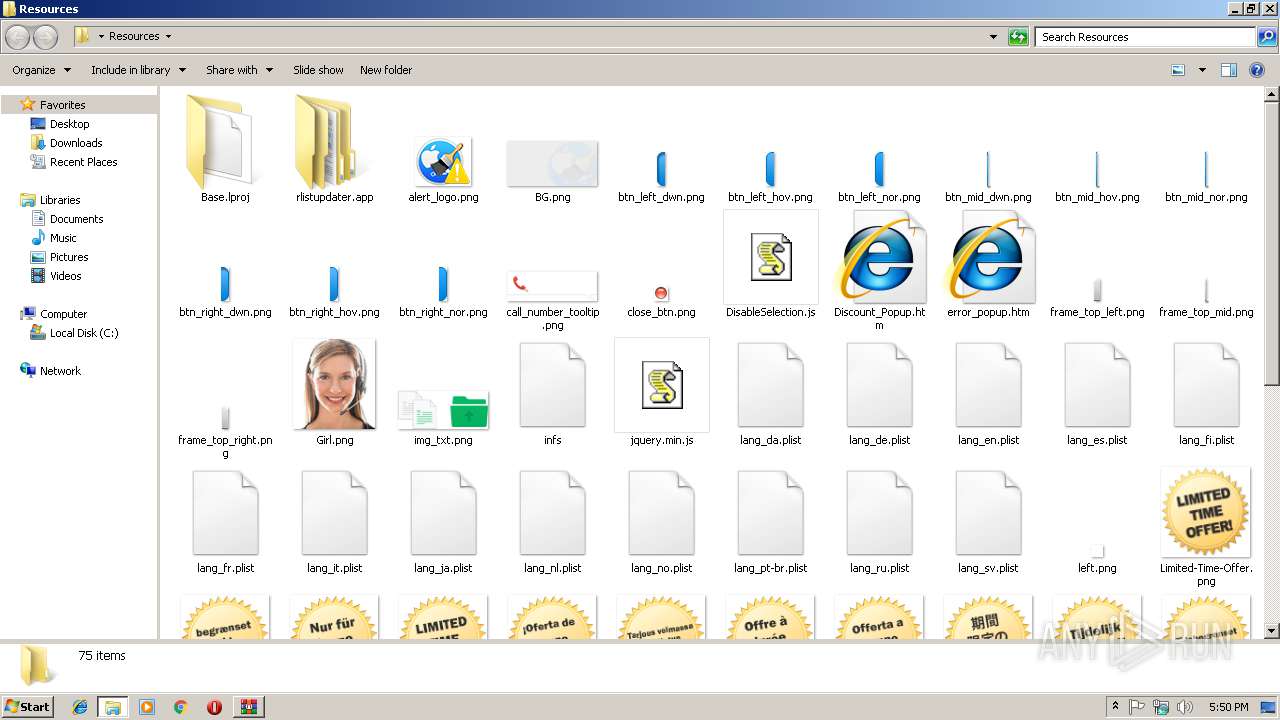
Dropped files
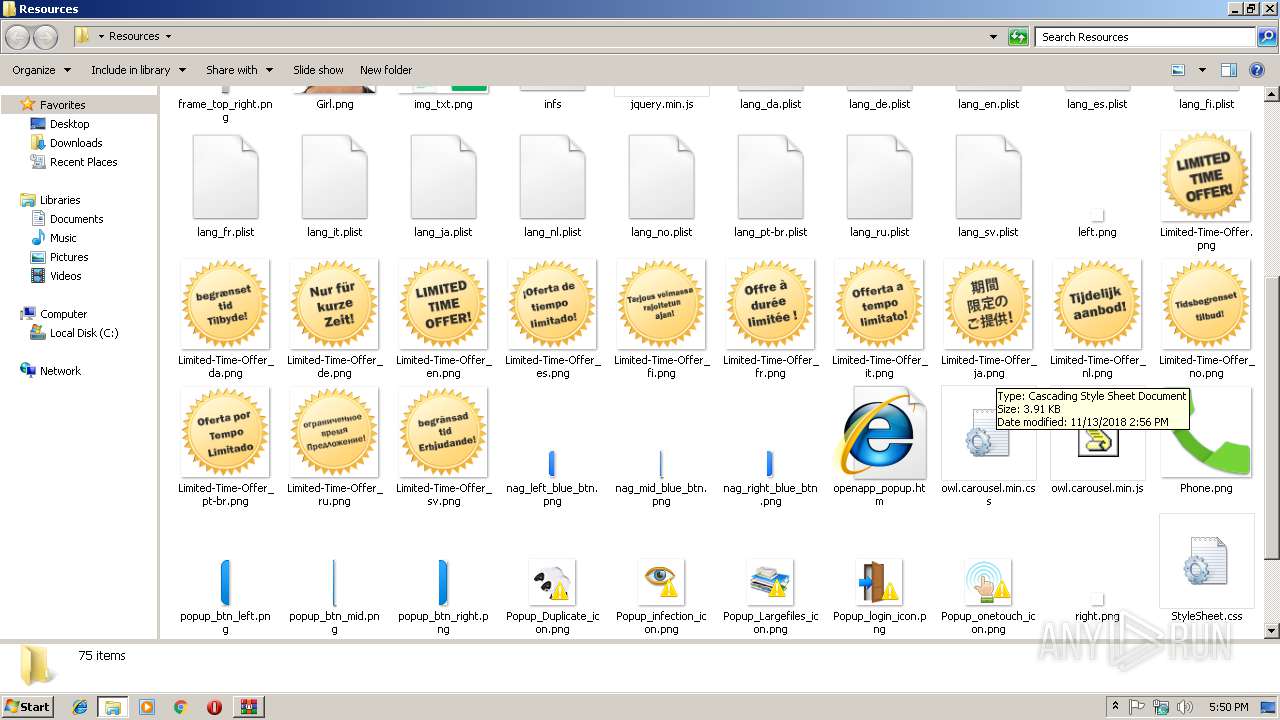
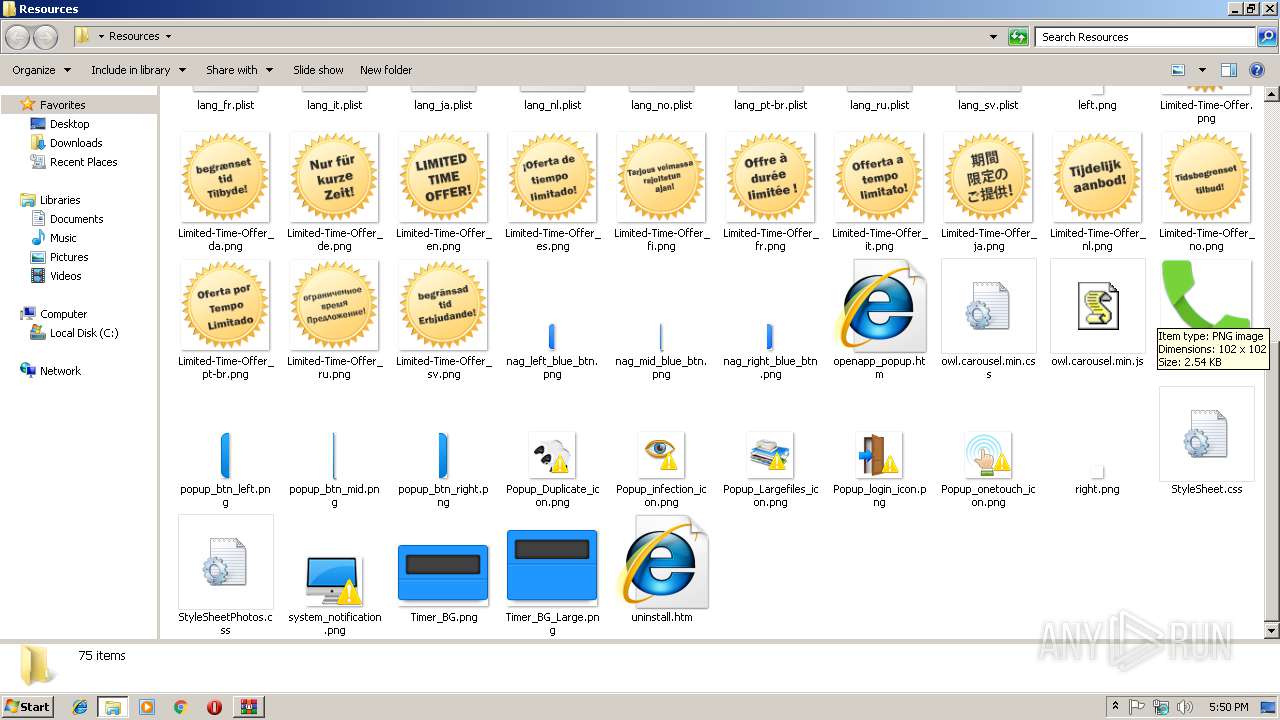
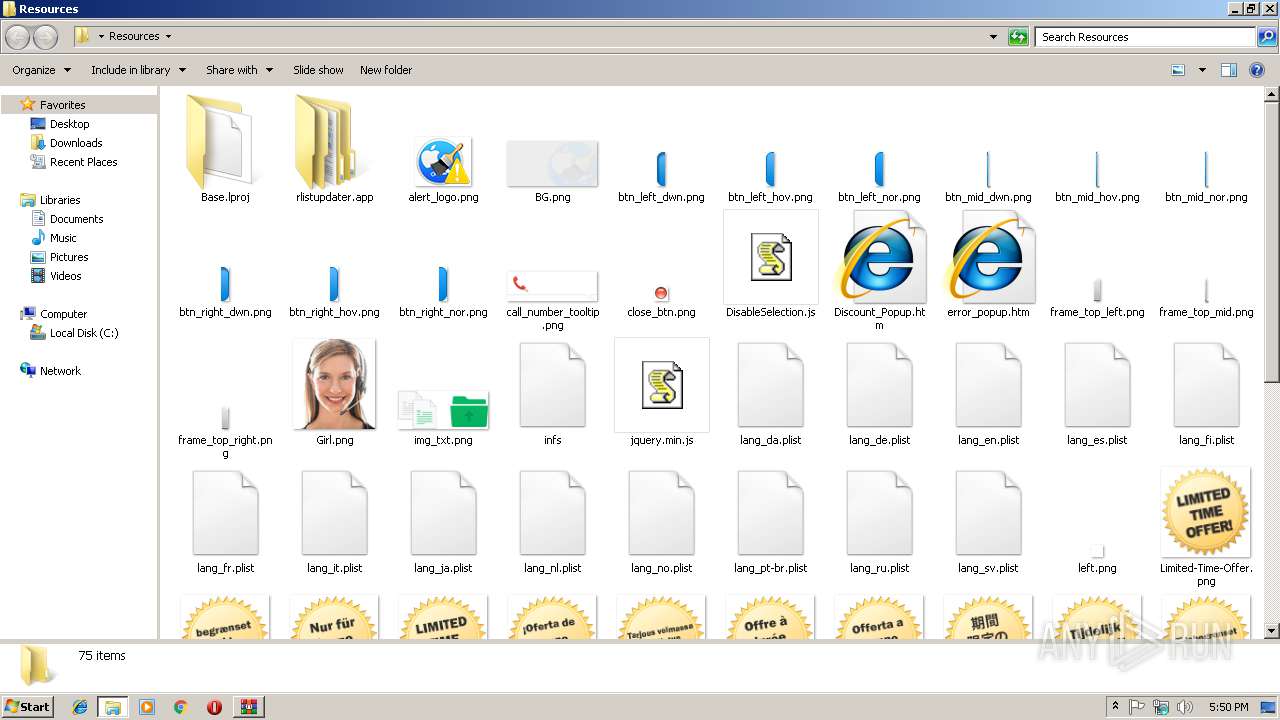
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2860.22829\helperamc.app\Contents\Resources\Limited-Time-Offer_no.png | — | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2860.22829\helperamc.app\Contents\Resources\lang_es.plist | — | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2860.22829\helperamc.app\Contents\Resources\Limited-Time-Offer_nl.png | — | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2860.22829\helperamc.app\Contents\Resources\Timer_BG_Large.png | — | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2860.22829\helperamc.app\Contents\Resources\nag_left_blue_btn.png | — | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2860.22829\helperamc.app\Contents\Resources\lang_da.plist | — | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2860.22829\helperamc.app\Contents\Resources\nag_mid_blue_btn.png | — | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2860.22829\helperamc.app\Contents\Resources\popup_btn_left.png | — | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2860.22829\helperamc.app\Contents\Resources\lang_de.plist | — | |
MD5:— | SHA256:— | |||
| 2860 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2860.22829\helperamc.app\Contents\Resources\frame_top_mid.png | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report