| File name: | emSigner.msi |
| Full analysis: | https://app.any.run/tasks/e3d1a009-4f15-4088-b172-4155fd4e68bd |
| Verdict: | Malicious activity |
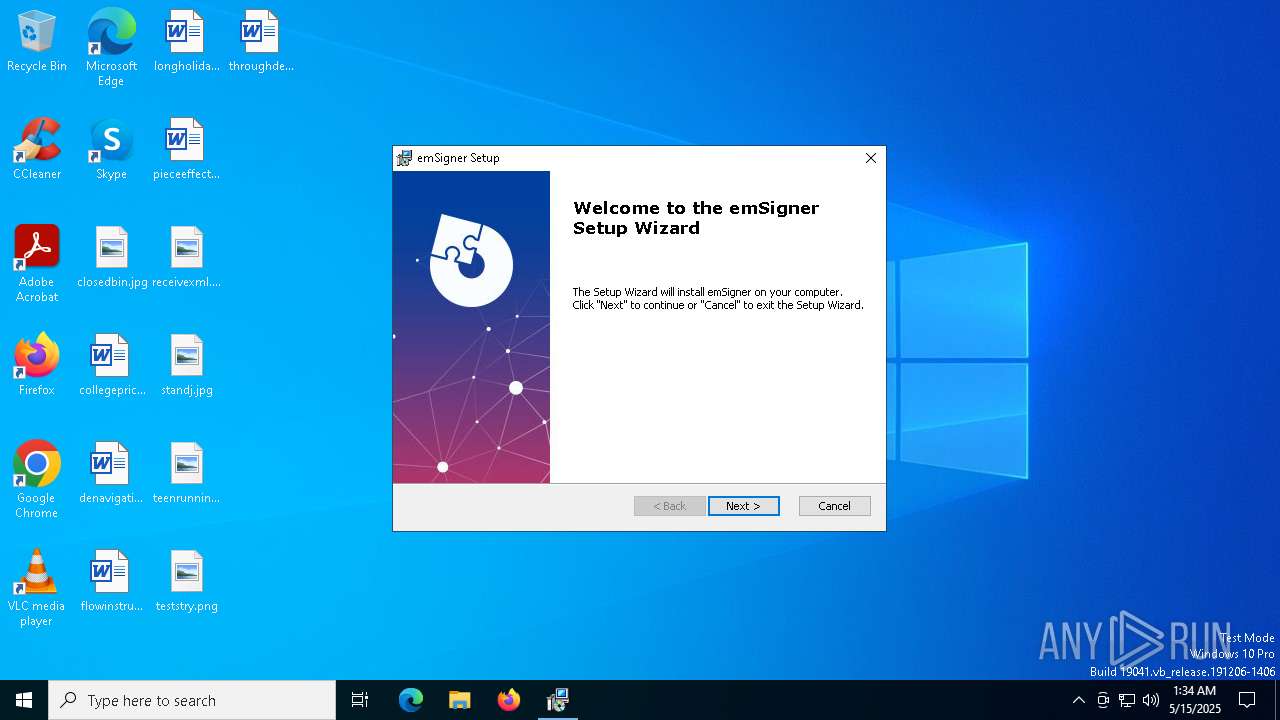
| Analysis date: | May 15, 2025, 01:34:07 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Sep 18 14:06:51 2020, Security: 0, Code page: 1252, Revision Number: {400812A2-8961-4C83-A9DF-54A86A1BEEAE}, Number of Words: 2, Subject: emSigner, Author: eMudhra Limited, Name of Creating Application: Advanced Installer 18.7 build 0a7fdead, Template: ;1033, Comments: This installer database contains the logic and data required to install emSigner., Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | 9C0C0CE07444876A184F97FD14200A71 |
| SHA1: | C5FF04974DF3645F3C86E4FE482CFC98BCB166A7 |
| SHA256: | 17F908F4B7E376C4B032177600E03976357D10D76C5D071FD48E7E50C2B5CB63 |
| SSDEEP: | 98304:/9IZo+TC69AbVGczJqmqN91QfRhUG6Sub3MYFj7yaLPajqGdiD9NLs0X7Or4ICr8:VFuglrkMVV |
MALICIOUS
No malicious indicators.SUSPICIOUS
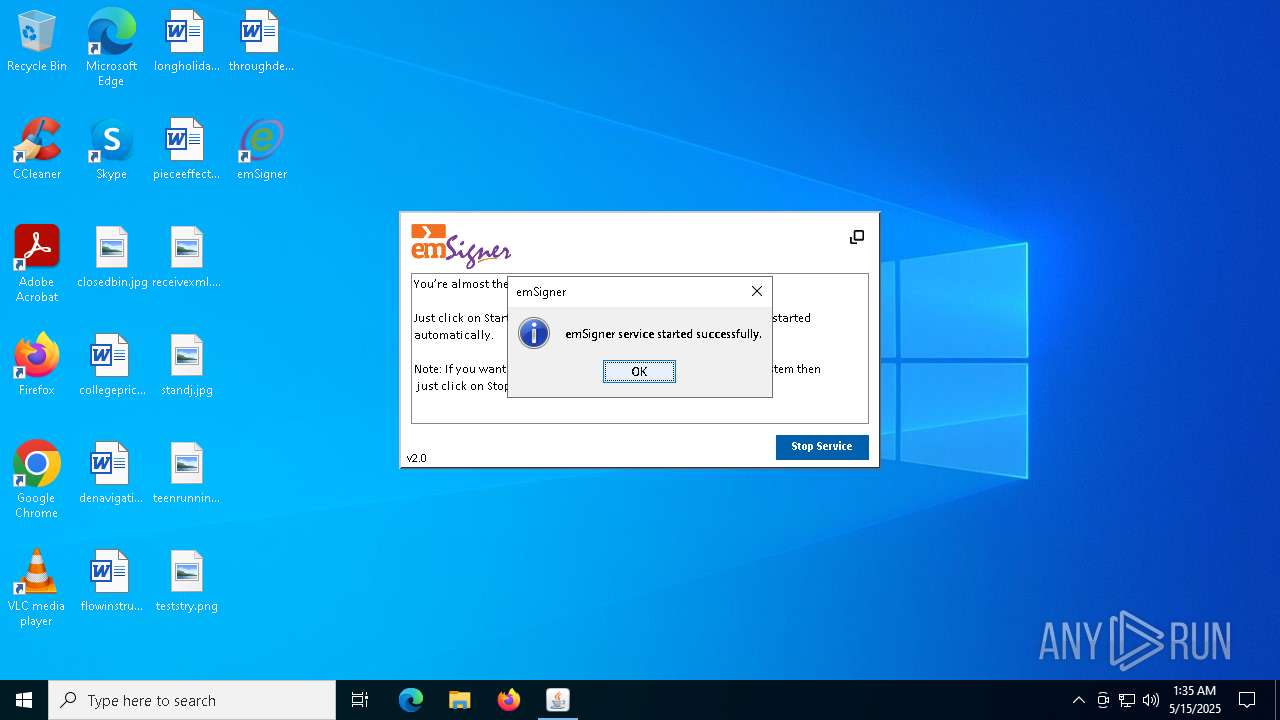
Executes as Windows Service
- VSSVC.exe (PID: 8048)
Detects AdvancedInstaller (YARA)
- msiexec.exe (PID: 7376)
- msiexec.exe (PID: 7448)
Starts CMD.EXE for commands execution
- javaw.exe (PID: 7848)
- cmd.exe (PID: 7812)
Executing commands from a ".bat" file
- javaw.exe (PID: 7848)
- cmd.exe (PID: 7812)
Application launched itself
- cmd.exe (PID: 7812)
INFO
Reads the computer name
- msiexec.exe (PID: 7488)
- msiexec.exe (PID: 7448)
Checks supported languages
- msiexec.exe (PID: 7448)
- msiexec.exe (PID: 7488)
Reads Environment values
- msiexec.exe (PID: 7488)
The sample compiled with english language support
- msiexec.exe (PID: 7376)
- msiexec.exe (PID: 7448)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7376)
- msiexec.exe (PID: 7448)
Manages system restore points
- SrTasks.exe (PID: 6388)
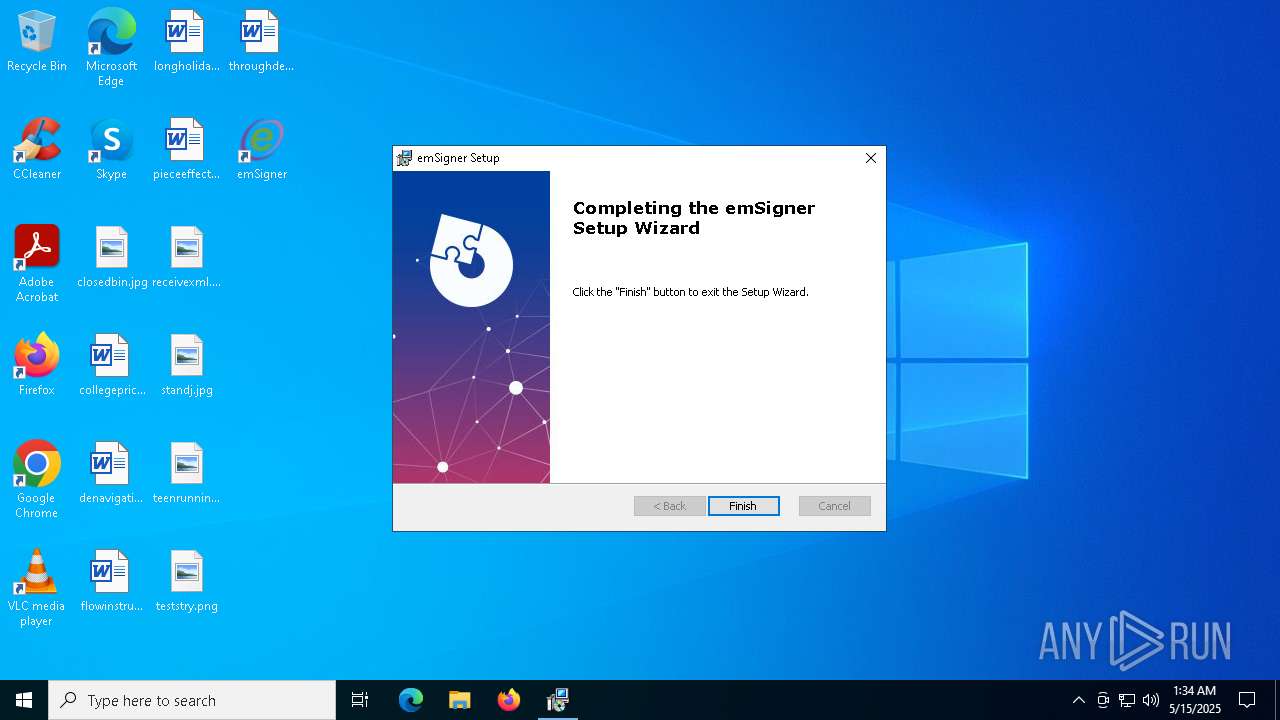
Manual execution by a user
- emSigner.exe (PID: 7792)
Application based on Java
- javaw.exe (PID: 7848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| LastPrinted: | 2009:12:11 11:47:44 |
|---|---|
| CreateDate: | 2009:12:11 11:47:44 |
| ModifyDate: | 2020:09:18 14:06:51 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {400812A2-8961-4C83-A9DF-54A86A1BEEAE} |
| Words: | 2 |
| Subject: | emSigner |
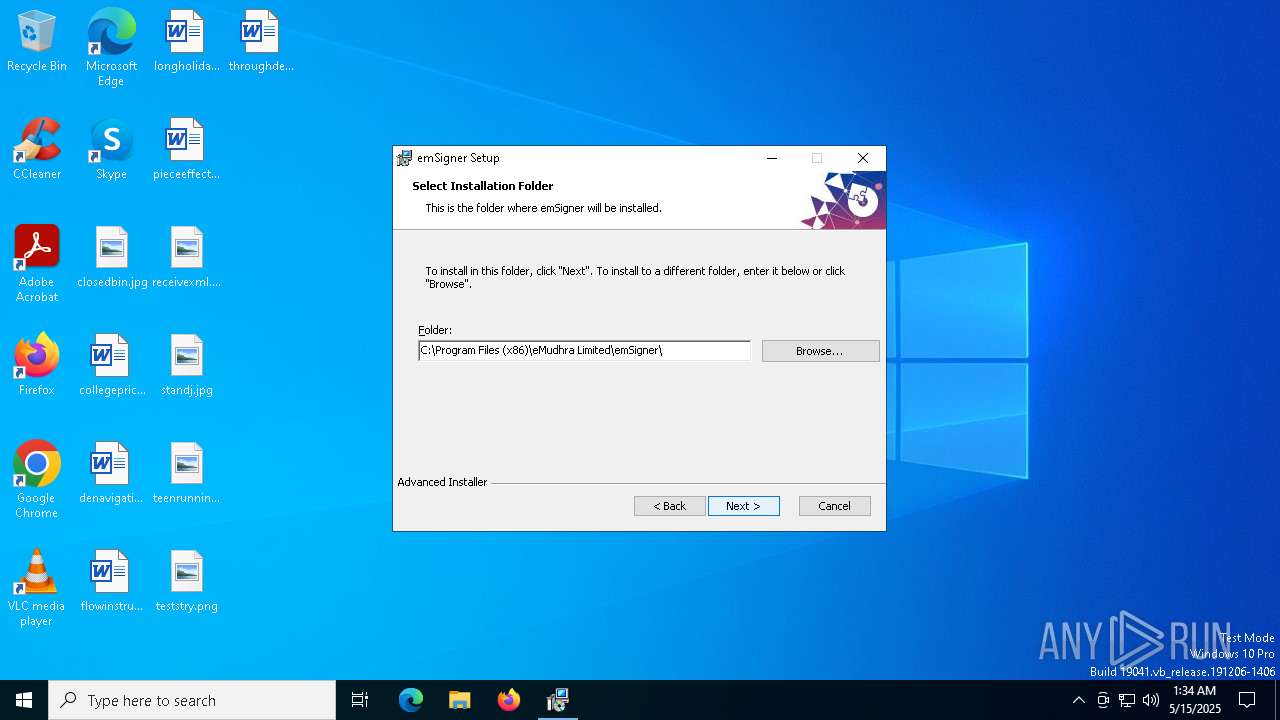
| Author: | eMudhra Limited |
| LastModifiedBy: | - |
| Software: | Advanced Installer 18.7 build 0a7fdead |
| Template: | ;1033 |
| Comments: | This installer database contains the logic and data required to install emSigner. |
| Title: | Installation Database |
| Keywords: | Installer, MSI, Database |
| Pages: | 200 |
Total processes
151
Monitored processes
20
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | C:\Windows\syswow64\MsiExec.exe -Embedding 3011C5CF5F10DC25E7019F6F14E879CB | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | certutil -delstore Root 22a176971590 | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 2147943140 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | xcopy eMweb c:\windows\eMweb /e /i /y | C:\Windows\System32\xcopy.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Extended Copy Utility Exit code: 4 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3676 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4436 | C:\WINDOWS\system32\cmd.exe /K certificate.bat | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5400 | certutil -addstore -f -enterprise -user root C:\WINDOWS\eMweb\local.crt | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 2147942405 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5608 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6388 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7376 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\emSigner.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7448 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
4 715
Read events
4 419
Write events
279
Delete events
17
Modification events
| (PID) Process: | (7448) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000E9F9717E39C5DB01181D00004C1F0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7448) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000E9F9717E39C5DB01181D00004C1F0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7448) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000C4B57F7F39C5DB01181D00004C1F0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7448) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000096CC817F39C5DB01181D00004C1F0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7448) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 4800000000000000CA30847F39C5DB01181D00004C1F0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7448) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000008694867F39C5DB01181D00004C1F0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7448) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (7448) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 4800000000000000277A0E8039C5DB01181D00004C1F0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8048) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4800000000000000A68C218039C5DB01701F0000941F0000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (8048) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4800000000000000A68C218039C5DB01701F0000341C0000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
24
Suspicious files
28
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7448 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 7448 | msiexec.exe | C:\Windows\Installer\1133af.msi | — | |
MD5:— | SHA256:— | |||
| 7448 | msiexec.exe | C:\Program Files (x86)\eMudhra Limited\emSigner\emSigner\emsigner.log | — | |
MD5:— | SHA256:— | |||
| 7376 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIBD95.tmp | executable | |
MD5:3D24A2AF1FB93F9960A17D6394484802 | SHA256:8D23754E6B8BB933D79861540B50DECA42E33AC4C3A6669C99FB368913B66D88 | |||
| 7376 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIBF7D.tmp | executable | |
MD5:3D24A2AF1FB93F9960A17D6394484802 | SHA256:8D23754E6B8BB933D79861540B50DECA42E33AC4C3A6669C99FB368913B66D88 | |||
| 7376 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIBE72.tmp | executable | |
MD5:3D24A2AF1FB93F9960A17D6394484802 | SHA256:8D23754E6B8BB933D79861540B50DECA42E33AC4C3A6669C99FB368913B66D88 | |||
| 7376 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIBE92.tmp | executable | |
MD5:3D24A2AF1FB93F9960A17D6394484802 | SHA256:8D23754E6B8BB933D79861540B50DECA42E33AC4C3A6669C99FB368913B66D88 | |||
| 7376 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIBE51.tmp | executable | |
MD5:3D24A2AF1FB93F9960A17D6394484802 | SHA256:8D23754E6B8BB933D79861540B50DECA42E33AC4C3A6669C99FB368913B66D88 | |||
| 7448 | msiexec.exe | C:\Program Files (x86)\eMudhra Limited\emSigner\emSigner\docs\emsigner.property.txt | text | |
MD5:A1739B45D07B5DF1F8610EAA30D4BE49 | SHA256:0713372374189837F241EF40248891281AF2BAFDD1B1D85D006E1710F95E827D | |||
| 7448 | msiexec.exe | C:\Program Files (x86)\eMudhra Limited\emSigner\emSigner\docs\websocket_java.html | html | |
MD5:B41448D4DF8231ED4EDCA96296E14ADE | SHA256:C043D82F415A6B84DD488D77CFC8970918009D811DF0A51A8A3D454BE5A12991 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
25
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7224 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7224 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |