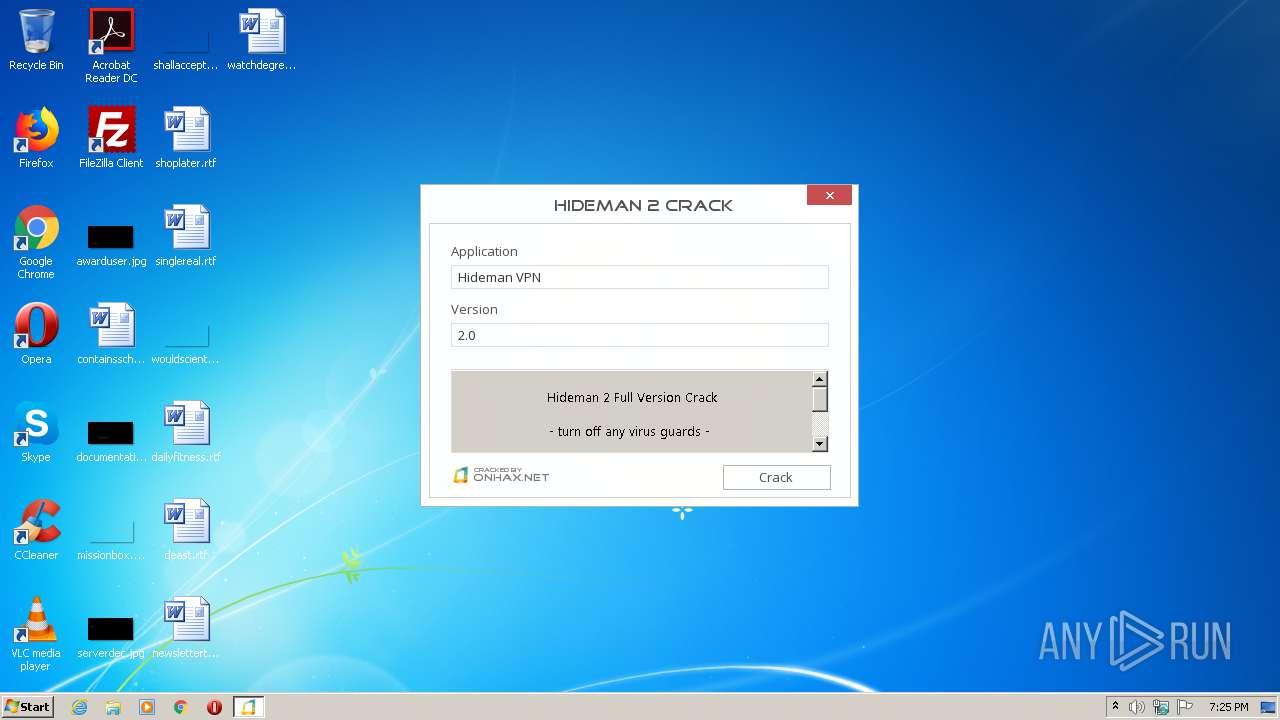
| File name: | Hideman 2 Crack.exe |
| Full analysis: | https://app.any.run/tasks/312230e2-0c56-4be8-8358-d84f43cf61aa |
| Verdict: | Malicious activity |
| Analysis date: | July 12, 2020, 18:25:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9AEC138E37ECD07E46204AA027876C20 |
| SHA1: | 143F211A454065A5FCA1D0ACA554C33E9EB217F5 |
| SHA256: | 17E62FEF4276930D79760A55AB56235D97E884679309097E70F022AE4D089ABB |
| SSDEEP: | 49152:3bPSu9ZLHLbnU0Nx1krkFvSVmx6eFm7VkgPdUeLP868XF:bLfU0Nvkgv5xs3d3Y6 |
MALICIOUS
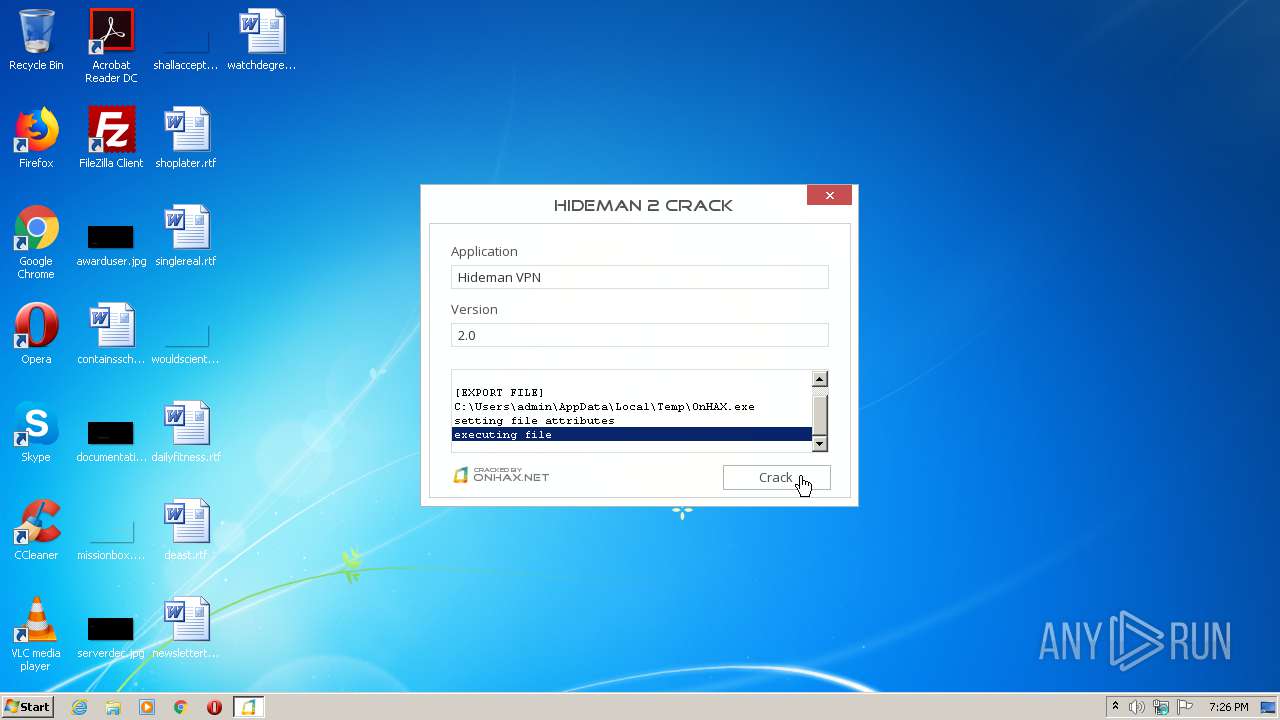
Application was dropped or rewritten from another process
- Hideman.exe (PID: 3852)
Loads dropped or rewritten executable
- Hideman 2 Crack.exe (PID: 3448)
Starts Visual C# compiler
- Hideman.exe (PID: 3852)
SUSPICIOUS
Creates files in the program directory
- Hideman 2 Crack.exe (PID: 3448)
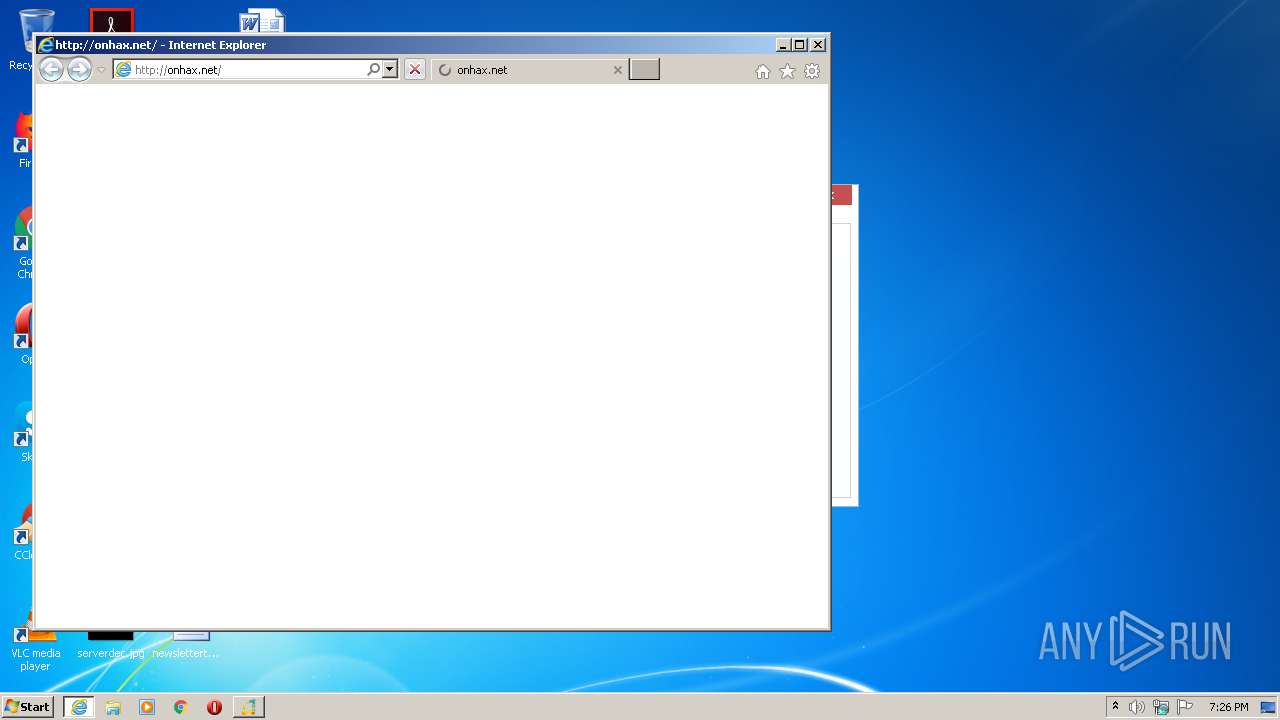
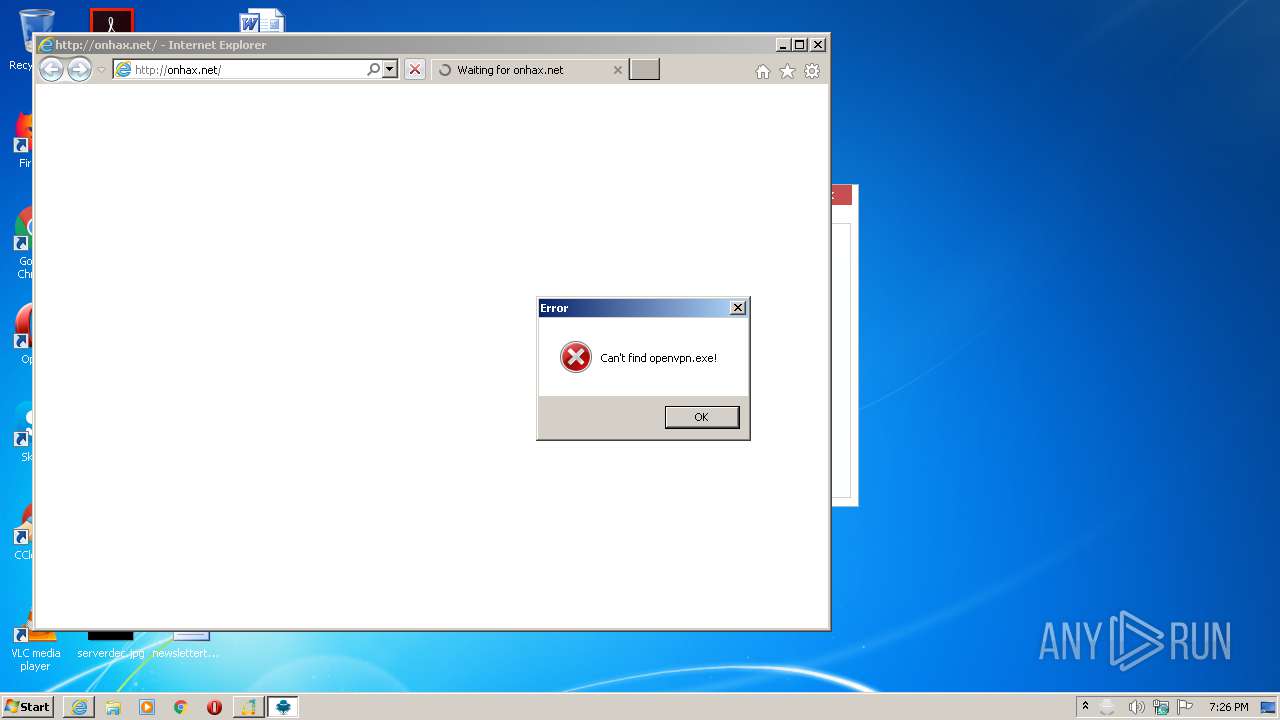
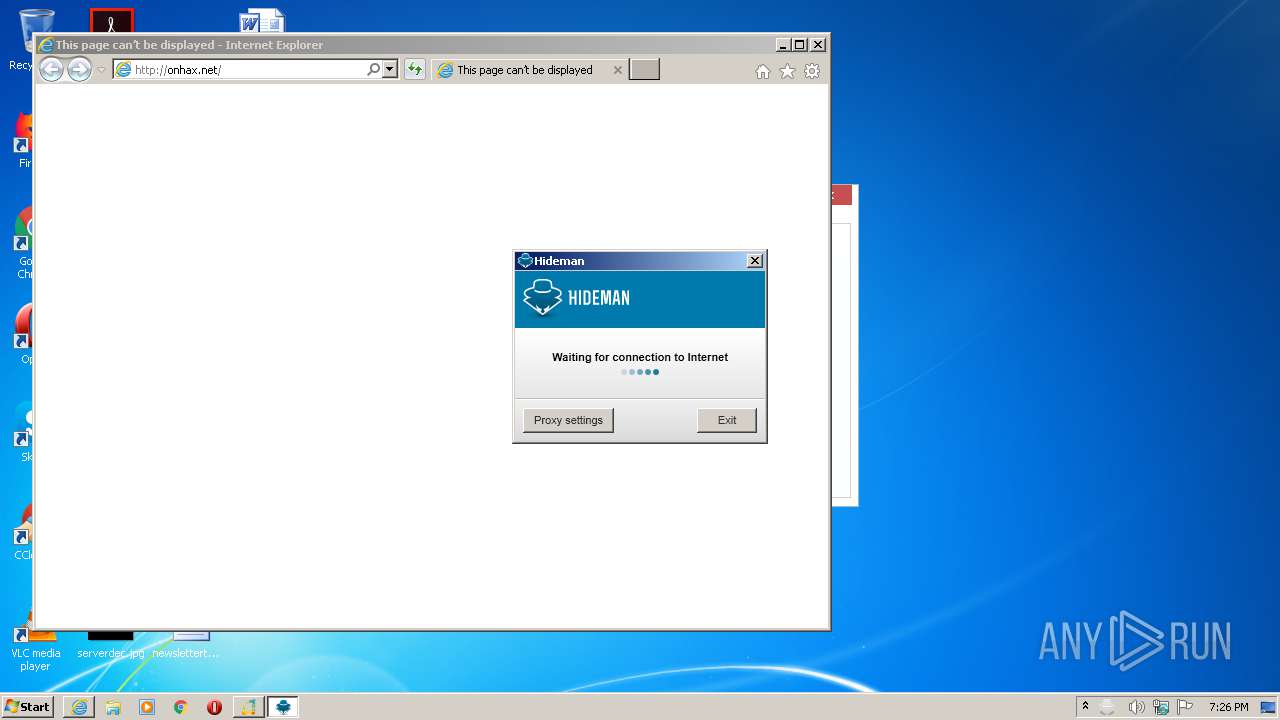
Starts Internet Explorer
- explorer.exe (PID: 2068)
Executed via COM
- explorer.exe (PID: 2068)
Executed as Windows Service
- PresentationFontCache.exe (PID: 532)
Executable content was dropped or overwritten
- Hideman 2 Crack.exe (PID: 3448)
INFO
Reads internet explorer settings
- iexplore.exe (PID: 4004)
Reads Internet Cache Settings
- iexplore.exe (PID: 2952)
- iexplore.exe (PID: 4004)
Application launched itself
- iexplore.exe (PID: 2952)
Changes internet zones settings
- iexplore.exe (PID: 2952)
Reads settings of System Certificates
- iexplore.exe (PID: 2952)
Changes settings of System certificates
- iexplore.exe (PID: 2952)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:21 21:59:46+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 512 |
| InitializedDataSize: | 2165248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x102b |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2012 20:59:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2012 20:59:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x0021032C | 0x00210400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99504 |
.reloc | 0x00215000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85663 | 898 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 4.48731 | 4136 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.74979 | 2344 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 5.06332 | 1064 | Latin 1 / Western European | UNKNOWN | RT_ICON |
500 | 2.48187 | 62 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
DLL | 7.99991 | 2138112 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
kernel32.dll |
Total processes
49
Monitored processes
11
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\jqtk2lsj.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | — | Hideman.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 532 | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | C:\Windows\Microsoft.Net\Framework\v3.0\WPF\PresentationFontCache.exe | — | services.exe | |||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: PresentationFontCache.exe Exit code: 0 Version: 3.0.6920.4902 built by: NetFXw7 Modules
| |||||||||||||||
| 2068 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2392 | "C:\Users\admin\AppData\Local\Temp\OnHAX.exe" | C:\Users\admin\AppData\Local\Temp\OnHAX.exe | — | Hideman 2 Crack.exe | |||||||||||
User: admin Company: On HAX Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2416 | "C:\Users\admin\AppData\Local\Temp\Hideman 2 Crack.exe" | C:\Users\admin\AppData\Local\Temp\Hideman 2 Crack.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2756 | explorer.exe http://onhax.net/ | C:\Windows\explorer.exe | — | OnHAX.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2952 | "C:\Program Files\Internet Explorer\iexplore.exe" http://onhax.net/ | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3448 | "C:\Users\admin\AppData\Local\Temp\Hideman 2 Crack.exe" | C:\Users\admin\AppData\Local\Temp\Hideman 2 Crack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3452 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESE590.tmp" "c:\Users\admin\AppData\Local\Temp\CSCE58F.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 3852 | "C:\Program Files\Hideman\bin\Hideman.exe" | C:\Program Files\Hideman\bin\Hideman.exe | — | Hideman 2 Crack.exe | |||||||||||
User: admin Company: Hideman Ltd. Integrity Level: HIGH Description: Hideman Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
Total events
3 217
Read events
1 150
Write events
1 399
Delete events
668
Modification events
| (PID) Process: | (3448) Hideman 2 Crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3448) Hideman 2 Crack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2068) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000B407EAE67958D601 | |||
| (PID) Process: | (3852) Hideman.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hideman_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3852) Hideman.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hideman_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3852) Hideman.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hideman_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3852) Hideman.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hideman_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3852) Hideman.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hideman_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3852) Hideman.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hideman_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3852) Hideman.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Hideman_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
4
Suspicious files
0
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3448 | Hideman 2 Crack.exe | C:\Users\admin\AppData\Local\Temp\OnHAX.exe | — | |
MD5:— | SHA256:— | |||
| 2392 | OnHAX.exe | C:\Users\admin\AppData\Local\Temp\~DFEED5A1ED6458936B.TMP | — | |
MD5:— | SHA256:— | |||
| 120 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCE58F.tmp | — | |
MD5:— | SHA256:— | |||
| 3452 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESE590.tmp | — | |
MD5:— | SHA256:— | |||
| 120 | csc.exe | C:\Users\admin\AppData\Local\Temp\jqtk2lsj.dll | — | |
MD5:— | SHA256:— | |||
| 120 | csc.exe | C:\Users\admin\AppData\Local\Temp\jqtk2lsj.out | — | |
MD5:— | SHA256:— | |||
| 2952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3448 | Hideman 2 Crack.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:— | SHA256:— | |||
| 3448 | Hideman 2 Crack.exe | C:\Program Files\Hideman\bin\Hideman.exe | executable | |
MD5:— | SHA256:— | |||
| 3448 | Hideman 2 Crack.exe | C:\Users\admin\AppData\Local\Temp\bassmod.dll | executable | |
MD5:E4EC57E8508C5C4040383EBE6D367928 | SHA256:8AD9E47693E292F381DA42DDC13724A3063040E51C26F4CA8E1F8E2F1DDD547F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
8
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2952 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2952 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onhax.net |
| malicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |