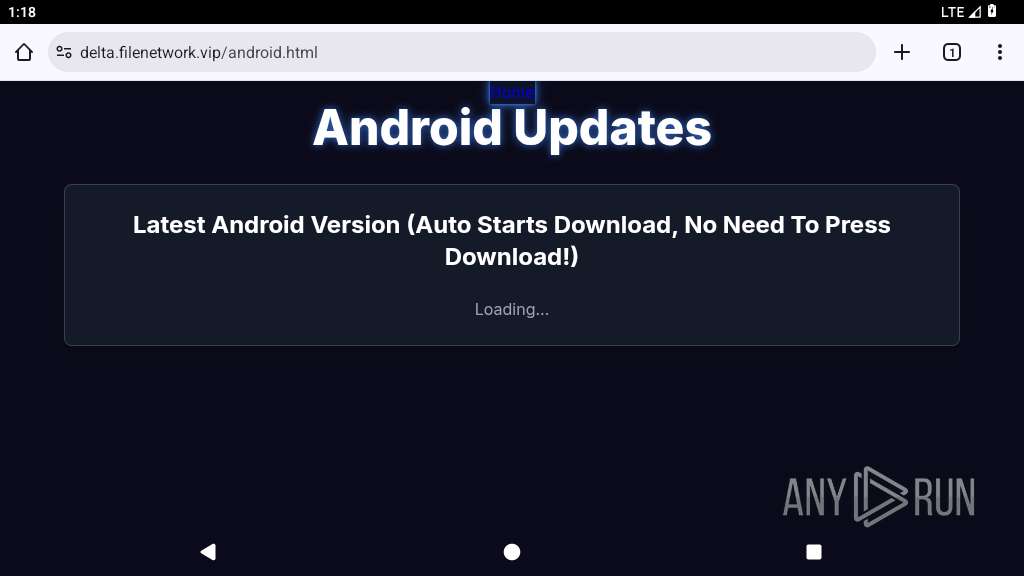
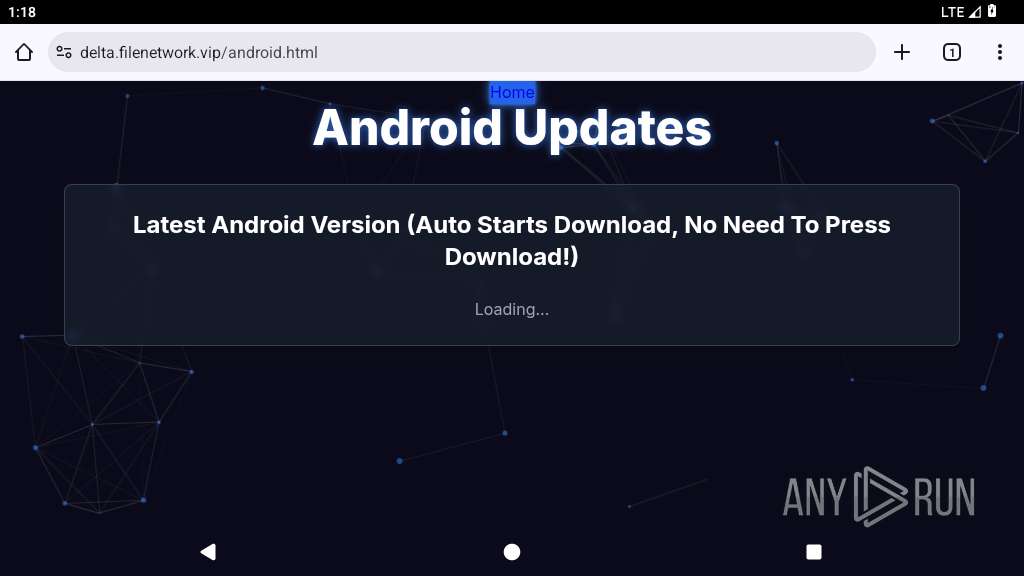
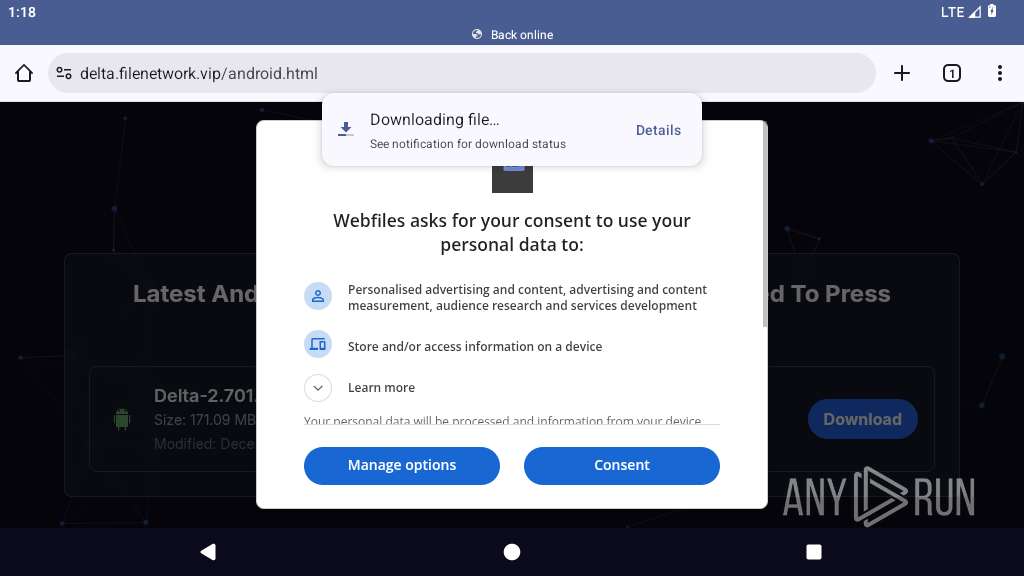
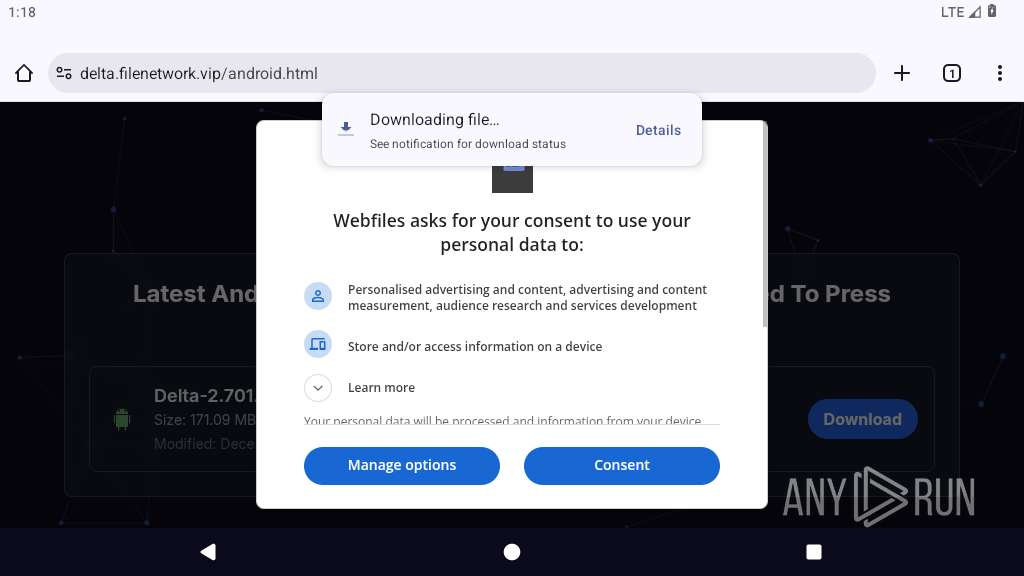
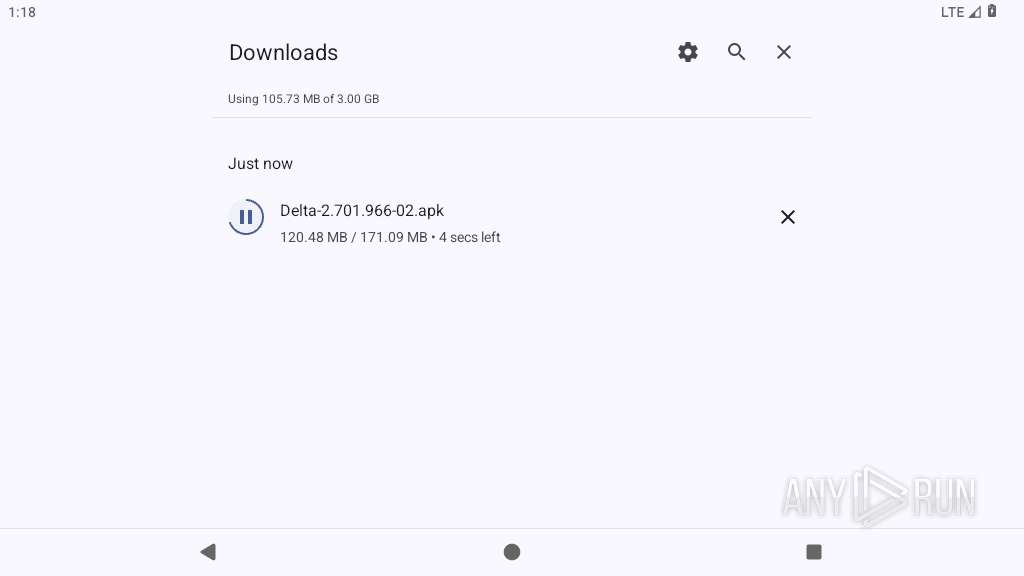
| URL: | https://delta.filenetwork.vip/file/Delta-2.701.966-02.apk |
| Full analysis: | https://app.any.run/tasks/60169185-df03-47a0-a7bd-81aaf50868b3 |
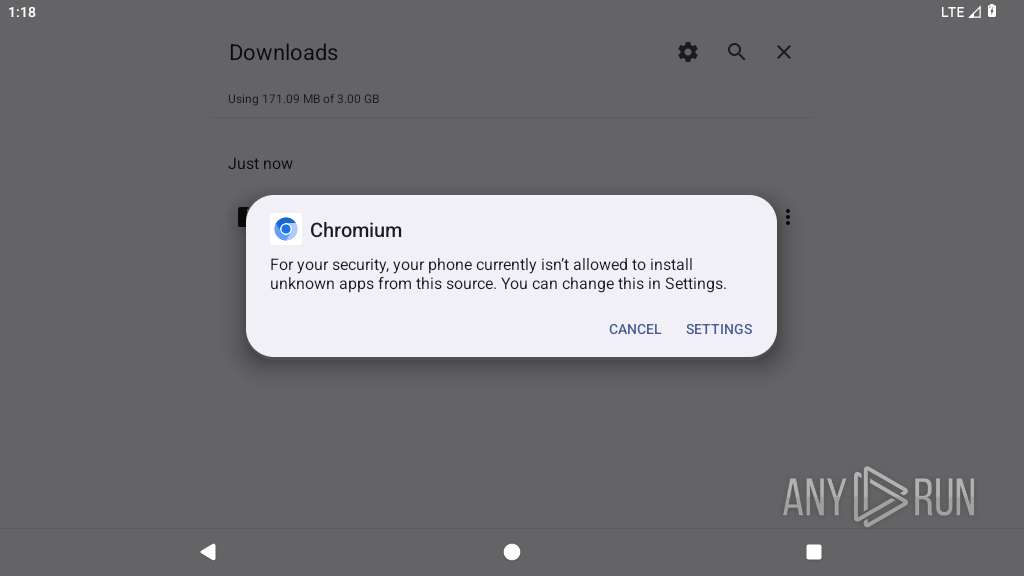
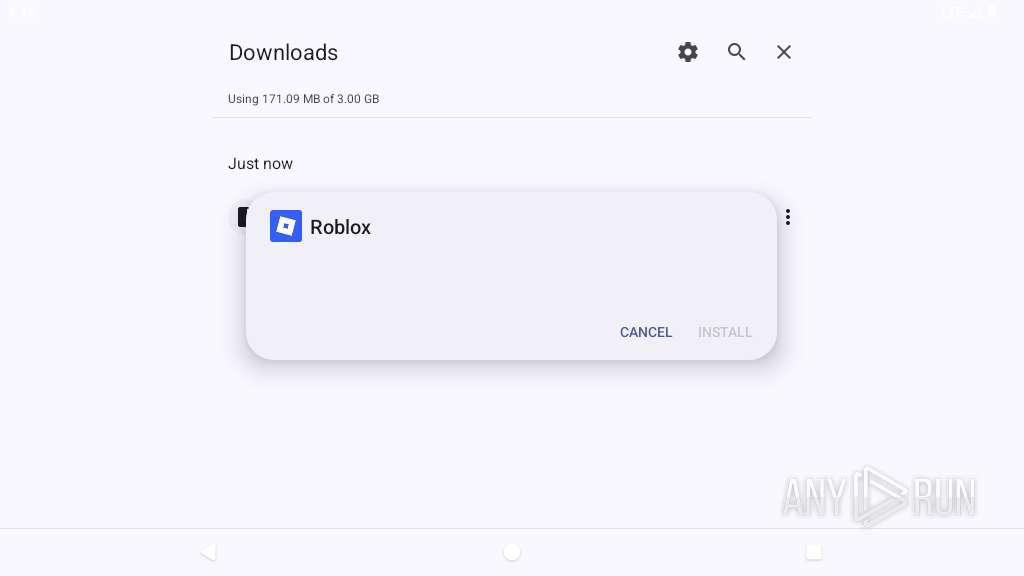
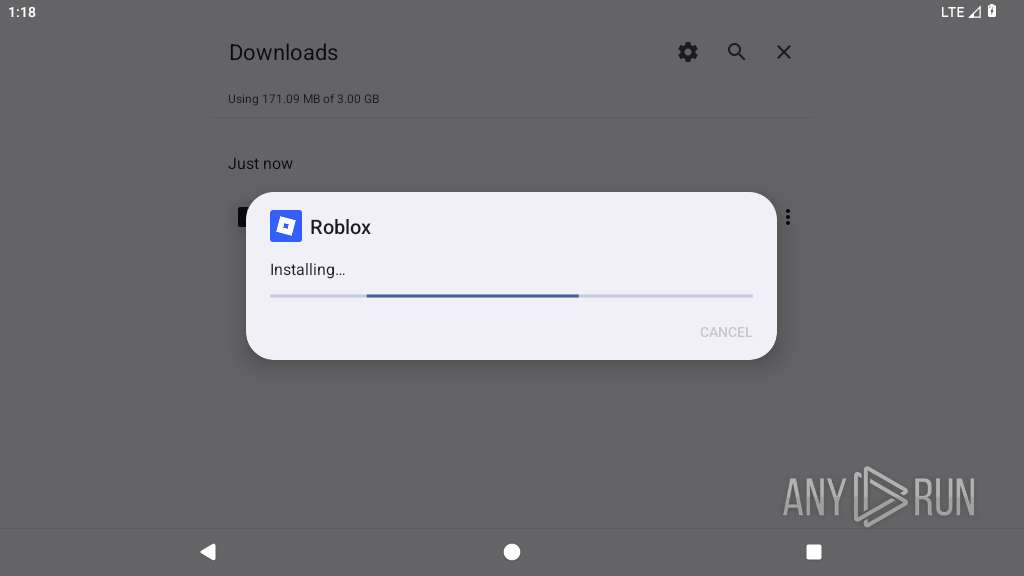
| Verdict: | Malicious activity |
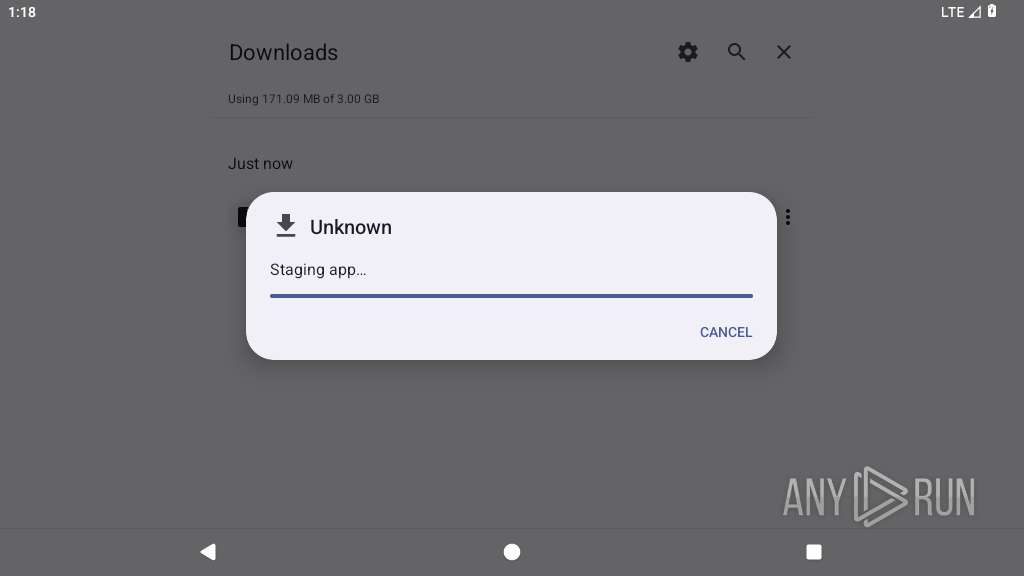
| Analysis date: | December 16, 2025, 13:18:20 |
| OS: | Android 14 |
| Indicators: | |
| MD5: | C0415737621F2F87DC80852C671B6ED9 |
| SHA1: | BC9E5A07701B28FA43DCB8B235D7BAF4E86B8AAF |
| SHA256: | 17D1C7E89E44839D28F18CC2C7FFA6B33A8FDDC7A680E365F00592B8FF7EC217 |
| SSDEEP: | 3:N8YBOEHgQEJR9SVLTIuO:2Y7HbEf9yEB |
MALICIOUS
Detects root access on device
- app_process64 (PID: 4387)
Executes system commands or scripts
- app_process64 (PID: 4387)
SUSPICIOUS
Collects data about the device's environment (JVM version)
- app_process64 (PID: 4387)
Accesses system-level resources
- app_process64 (PID: 4387)
Establishing a connection
- app_process64 (PID: 4387)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 4387)
Retrieves a list of running application processes
- app_process64 (PID: 4387)
Retrieves Android OS build information
- app_process64 (PID: 4387)
Launches a new activity
- app_process64 (PID: 4387)
Accesses memory information
- app_process64 (PID: 4387)
Connects to unusual port
- app_process64 (PID: 4387)
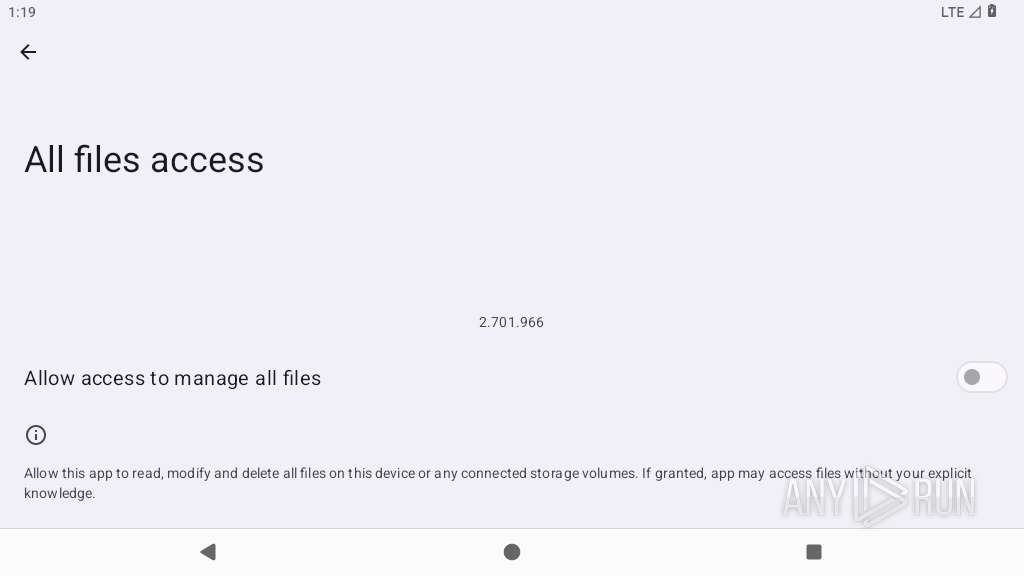
Accesses external device storage files
- app_process64 (PID: 4387)
Reads device serial number identifier
- app_process64 (PID: 4387)
INFO
Returns elapsed time since boot
- app_process64 (PID: 4387)
Loads a native library into the application
- app_process64 (PID: 4387)
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 4387)
Gets file name without full path
- app_process64 (PID: 4387)
Verifies whether the device is connected to the internet
- app_process64 (PID: 4387)
Detects device power status
- app_process64 (PID: 4387)
Dynamically registers broadcast event listeners
- app_process64 (PID: 4387)
Stores data using SQLite database
- app_process64 (PID: 4387)
Retrieves the value of a secure system setting
- app_process64 (PID: 4387)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 4387)
Gets the display metrics associated with the device's screen
- app_process64 (PID: 4387)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
144
Monitored processes
16
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 3957 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4017 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4031 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4043 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4087 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4117 | com.android.traceur | /system/bin/app_process64 | — | app_process64 |
User: u0_a54 Integrity Level: UNKNOWN Exit code: 512 | ||||
| 4155 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4210 | com.android.providers.partnerbookmarks | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4233 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4263 | /system/bin/dmesgd | /system/bin/dmesgd | — | init |
User: dmesgd Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
104
Text files
52
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4387 | app_process64 | /data/data/com.roblox.client/shared_modules/95d2031fd87e8fcac88aaf29661bd005/gloopversioncache.txt | text | |
MD5:— | SHA256:— | |||
| 4387 | app_process64 | /data/data/com.roblox.client/cache/journal.tmp | text | |
MD5:— | SHA256:— | |||
| 4387 | app_process64 | /data/data/com.roblox.client/shared_prefs/com.google.android.gms.measurement.prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 4387 | app_process64 | /data/data/com.roblox.client/shared_prefs/prefs.xml | xml | |
MD5:— | SHA256:— | |||
| 4387 | app_process64 | /data/data/com.roblox.client/no_backup/androidx.work.workdb-journal | binary | |
MD5:— | SHA256:— | |||
| 4387 | app_process64 | /data/data/com.roblox.client/no_backup/androidx.work.workdb-wal | binary | |
MD5:— | SHA256:— | |||
| 4387 | app_process64 | /data/data/com.roblox.client/files/PersistedInstallation6477830177994068885tmp | binary | |
MD5:— | SHA256:— | |||
| 4387 | app_process64 | /data/data/com.roblox.client/files/PersistedInstallation.W0RFRkFVTFRd+MToxMDAxNTUzMjA5MDk6YW5kcm9pZDphMmU0ODY1MDVhZDQzNGY1.json | binary | |
MD5:— | SHA256:— | |||
| 4387 | app_process64 | /data/data/com.roblox.client/databases/google_app_measurement_local.db | binary | |
MD5:— | SHA256:— | |||
| 4387 | app_process64 | /data/data/com.roblox.client/shared_prefs/FirebaseAppHeartBeat.xml | xml | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
38
TCP/UDP connections
73
DNS requests
98
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
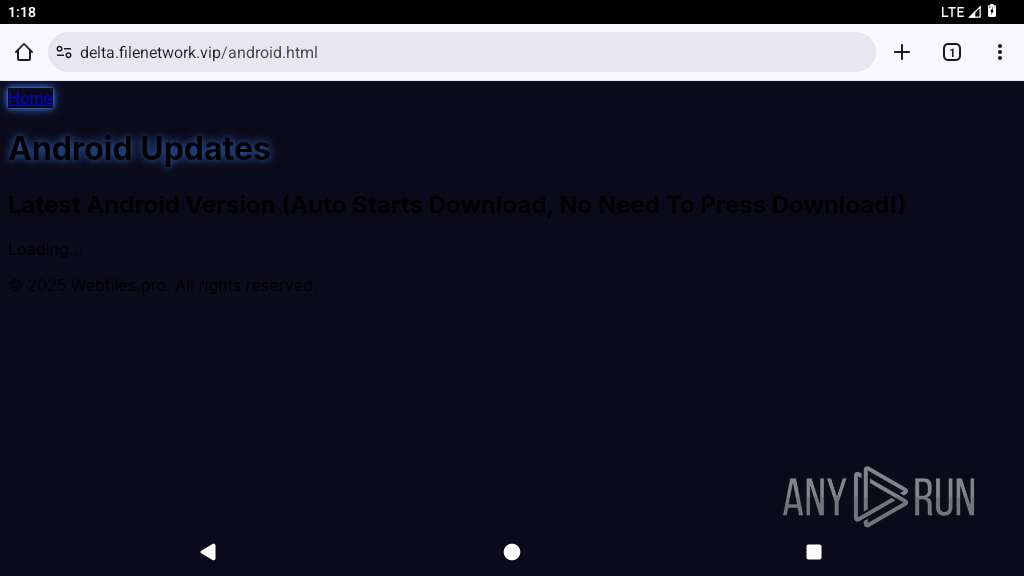
3957 | app_process64 | GET | 302 | 104.26.2.143:443 | https://cdn.tailwindcss.com/ | US | — | — | whitelisted |
1921 | app_process64 | GET | 204 | 142.250.185.196:443 | https://www.google.com/generate_204 | US | — | — | whitelisted |
3957 | app_process64 | POST | 204 | 216.239.32.36:443 | https://region1.google-analytics.com/g/collect?v=2&tid=G-YCFNYQXJVZ>m=45je5ca1v9228735425za200zd9228735425&_p=1765891112375&gcd=13l3l3l2l1l1&npa=1&dma_cps=syphamo&dma=1&cid=841028383.1765891114&ul=en-us&sr=1024x576&uaa=&uab=&uafvl=Chromium%3B137.0.7122.0%7CNot%252FA)Brand%3B24.0.0.0&uamb=1&uam=OnePlus_7_Pro&uap=Android&uapv=14.0.0&uaw=0&are=1&frm=0&pscdl=&_s=1&tag_exp=103116026~103200004~104527906~104528501~104684208~104684211~105391253~115583767~115938465~115938468~116184927~116184929~116251938~116251940&sid=1765891113&sct=1&seg=0&dl=https%3A%2F%2Fdelta.filenetwork.vip%2Fandroid.html&dt=Android%20Updates%20Delta&en=page_view&_fv=1&_nsi=1&_ss=1&_ee=1&tfd=2576 | US | — | — | whitelisted |
3957 | app_process64 | GET | 200 | 45.133.44.53:443 | https://js.capndr.com/advertising.js | NL | — | — | whitelisted |
3957 | app_process64 | GET | 200 | 45.133.44.52:443 | https://a1f6226fe8.a8659ff8d6.com/in/track?data=eyJ3bCI6MCwic3ViaWQiOjAsInVzZXJfaWQiOiIxNTc5NTY5MTMzMjk0NzgxODAwMCIsInRpbWV6b25lIjowLCJ2ZXIiOiIyLjQwLjEiLCJ0YWdfaWQiOjM4NTc4Nywic2NyZWVuX3Jlc29sdXRpb24iOiIxMDI0eDU3NiIsImFkYmxvY2siOjAsInRpbWV6b25lX29sc29uIjoiVVRDIiwidXRtX3NvdXJjZSI6IiIsInV0bV9tZWRpdW0iOiIiLCJ1dG1fY2FtcGFpZ24iOiIiLCJ1dG1fY29udGVudCI6IiIsIm1tIjowLCJpbml0X3N0YXJ0X2xhdGVuY3kiOjIuNTcsImlzX3YyIjowLCJpc192Ml9lbXB0eSI6MH0= | NL | — | — | whitelisted |
— | — | GET | 204 | 142.250.185.196:80 | http://www.google.com/gen_204 | US | — | — | whitelisted |
3957 | app_process64 | OPTIONS | 204 | 168.119.25.102:443 | https://ntvpforever.com/keywords | DE | — | — | whitelisted |
3957 | app_process64 | OPTIONS | 204 | 157.90.84.242:443 | https://fp.metricswpsh.com/fp?tag_id=385787 | DE | — | — | whitelisted |
1921 | app_process64 | GET | 204 | 142.250.185.227:80 | http://connectivitycheck.gstatic.com/generate_204 | US | — | — | whitelisted |
3957 | app_process64 | GET | 200 | 142.250.185.206:80 | http://clients2.google.com/time/1/current?cup2key=9:AdWPvcZ0Hy9iPaV4cXysG6uTPoZQrMVyTyjgyw8rEFk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 103 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
452 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 142.250.185.196:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.185.196:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.185.227:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
3957 | app_process64 | 142.250.185.206:80 | clients2.google.com | GOOGLE | US | whitelisted |
3957 | app_process64 | 74.125.133.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3957 | app_process64 | 104.20.40.221:443 | delta.filenetwork.vip | CLOUDFLARENET | US | whitelisted |
3957 | app_process64 | 142.250.185.196:443 | www.google.com | GOOGLE | US | whitelisted |
3957 | app_process64 | 23.109.253.230:443 | ch.callerslokman.com | SERVERS-COM | US | whitelisted |
3957 | app_process64 | 172.241.53.69:443 | dv.otitishanded.com | SERVERS-COM | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
delta.filenetwork.vip |
| whitelisted |
accounts.google.com |
| whitelisted |
ch.callerslokman.com |
| unknown |
dv.otitishanded.com |
| whitelisted |
zt.peeredupseize.com |
| whitelisted |
wh.balzadicyema.com |
| whitelisted |
dollishreman.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3957 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
3957 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
3957 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3957 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
1921 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
347 | netd | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
347 | netd | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Pages platform for frontend developers to collaborate and deploy websites (pages .dev) |
347 | netd | Misc activity | ET INFO DNS Query to Cloudflare Page Developer Domain (pages .dev) |
4387 | app_process64 | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |