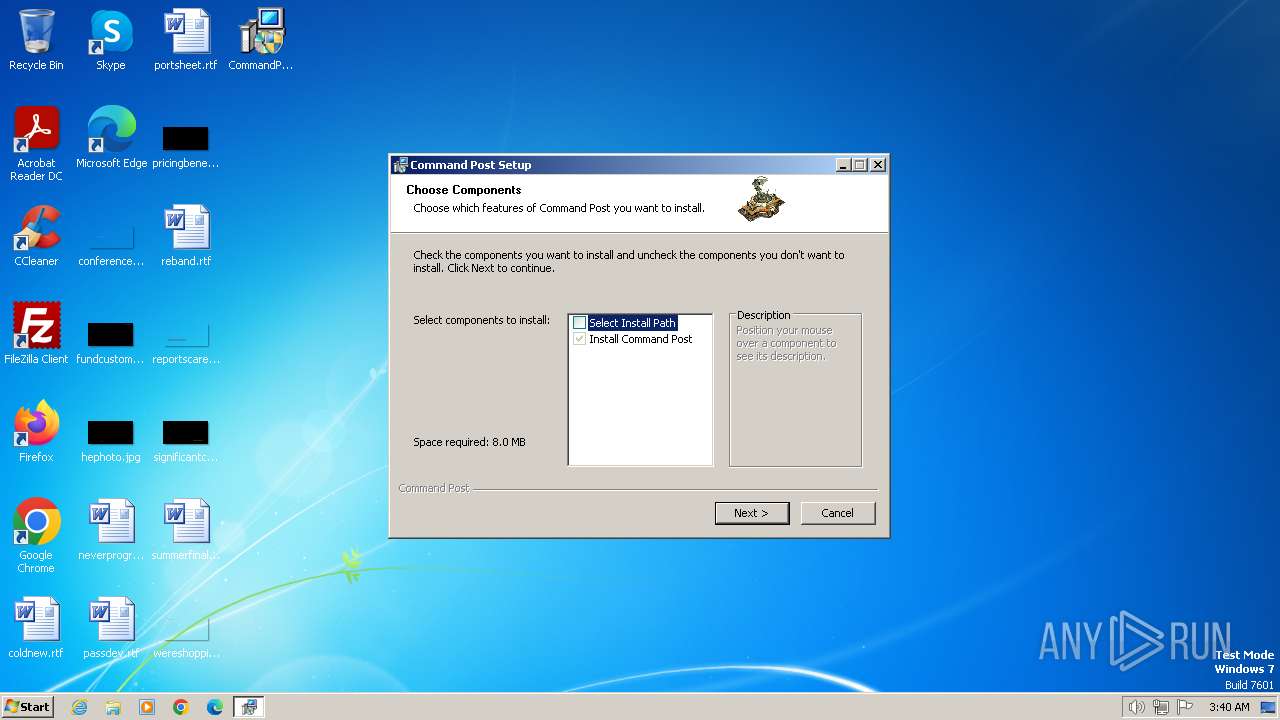
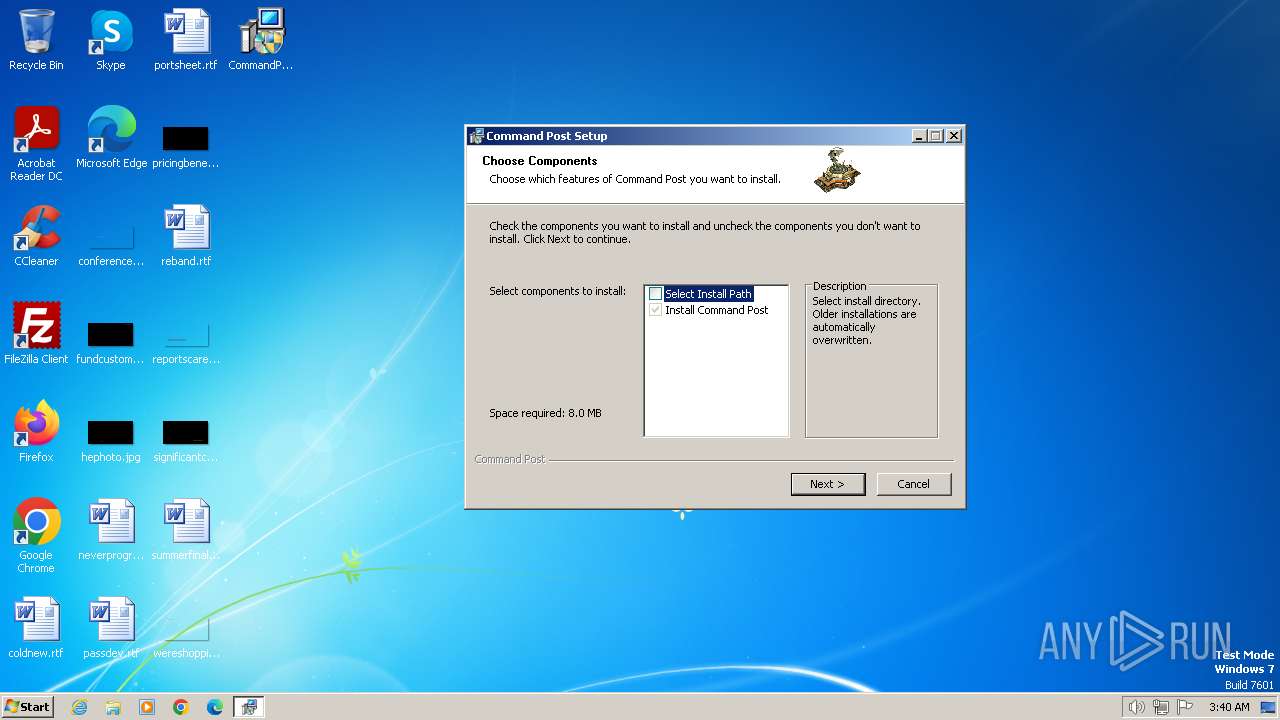
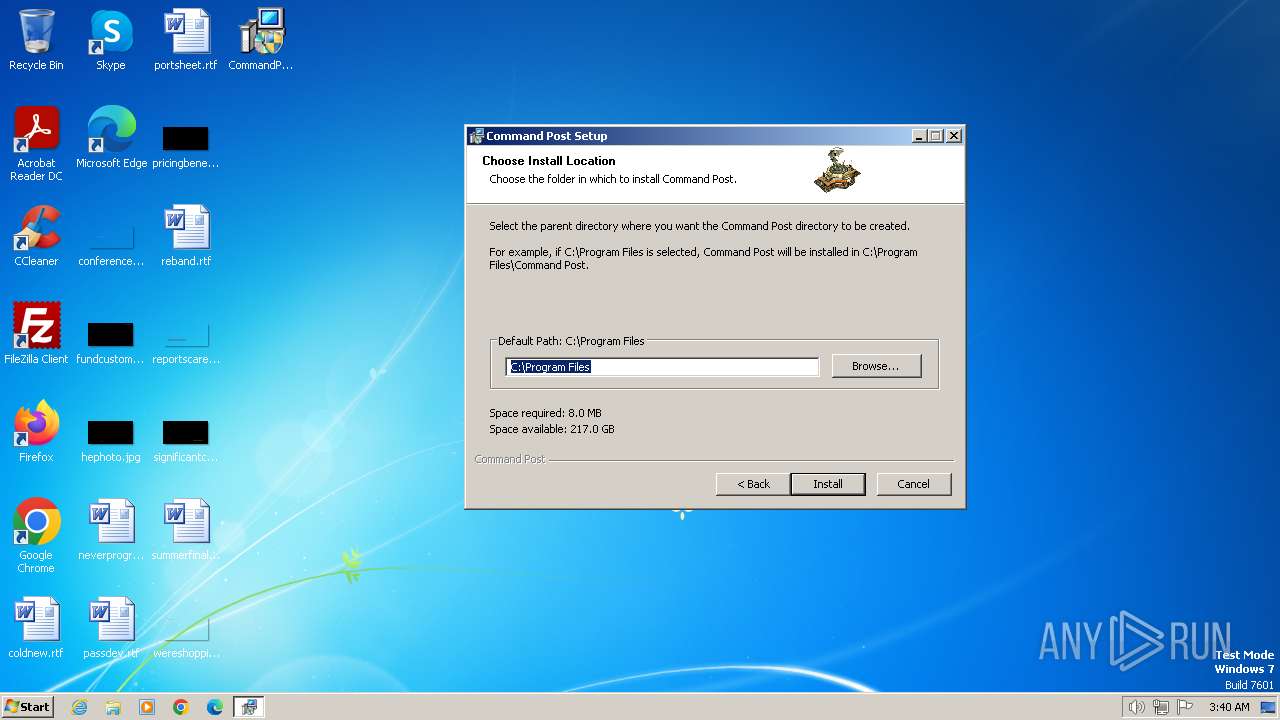
| File name: | CommandPostInstaller.exe |
| Full analysis: | https://app.any.run/tasks/6da5f159-97f6-40e6-b4b3-498a9f22a73b |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2024, 02:40:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 8CEB3A5E7DA3309B307A2407298A7CEE |
| SHA1: | C7B571E5020866E068C8B780782BE72CF5F8DF3F |
| SHA256: | 17C24104E8E5350EEB7E2A162DEC3F6A4D6C70F3F0849E6346FD383D998DCC12 |
| SSDEEP: | 98304:7J8hf4QF+9sK32tDOmU36f9qP9q+qjQ9pIzkQPU/yU6JQiZq3hL9nYedjWg/emtG:7a+Pyfd+i |
MALICIOUS
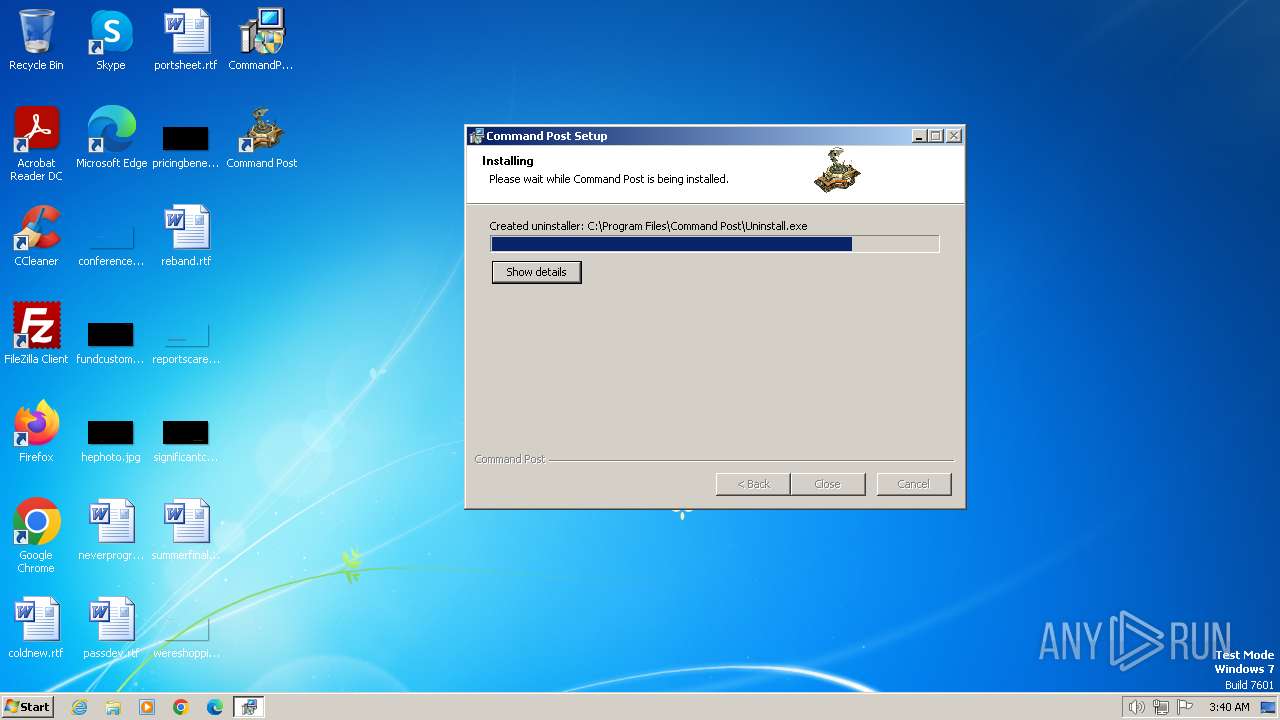
Drops the executable file immediately after the start
- CommandPostInstaller.exe (PID: 3392)
- CommandPost.exe (PID: 3516)
SUSPICIOUS
Creates a software uninstall entry
- CommandPostInstaller.exe (PID: 3392)
Reads the Internet Settings
- CommandPostInstaller.exe (PID: 3392)
- CommandPost.exe (PID: 3516)
Reads security settings of Internet Explorer
- CommandPostInstaller.exe (PID: 3392)
Non-standard symbols in registry
- CommandPost.exe (PID: 3516)
INFO
Reads the computer name
- CommandPostInstaller.exe (PID: 3392)
- CommandPost.exe (PID: 3516)
- CommandPost.exe (PID: 1556)
- wmpnscfg.exe (PID: 2972)
Checks supported languages
- CommandPostInstaller.exe (PID: 3392)
- CommandPost.exe (PID: 3516)
- CommandPost.exe (PID: 1556)
- wmpnscfg.exe (PID: 2972)
Create files in a temporary directory
- CommandPostInstaller.exe (PID: 3392)
Creates files in the program directory
- CommandPostInstaller.exe (PID: 3392)
- CommandPost.exe (PID: 3516)
Reads the machine GUID from the registry
- CommandPost.exe (PID: 3516)
- CommandPost.exe (PID: 1556)
Reads Environment values
- CommandPost.exe (PID: 3516)
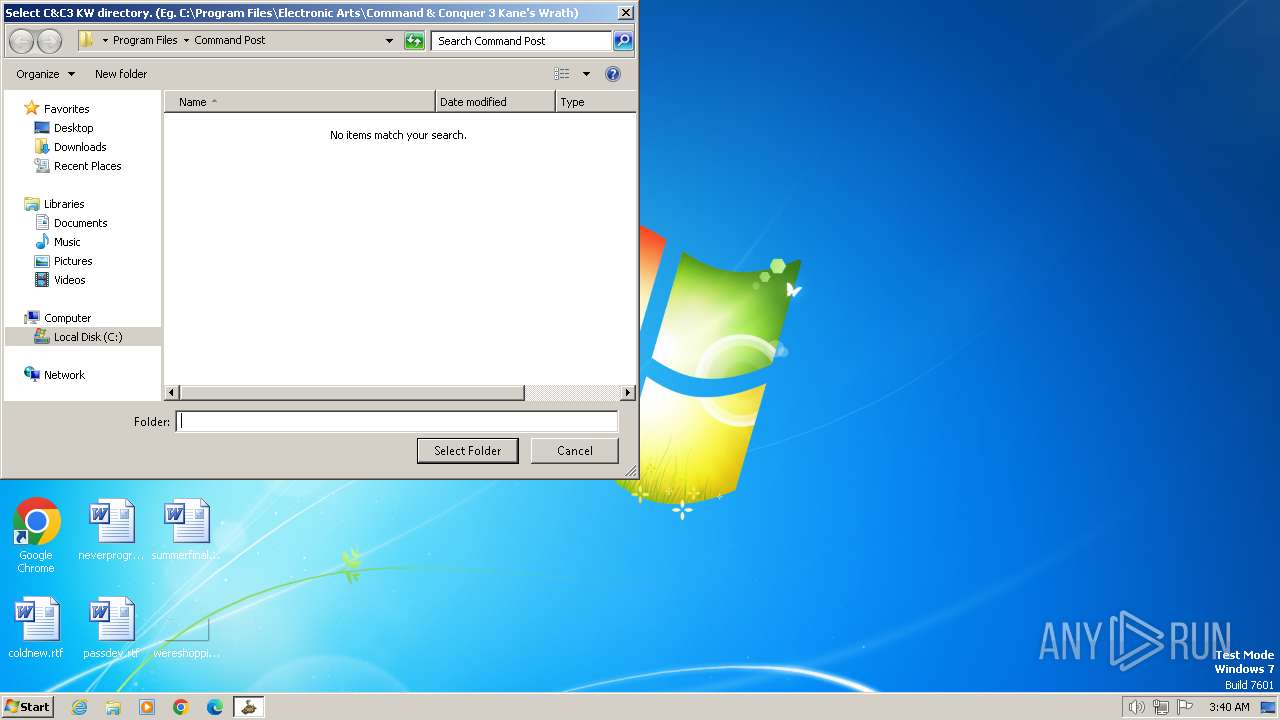
Manual execution by a user
- CommandPost.exe (PID: 1556)
- wmpnscfg.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:25 21:56:47+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3640 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
46
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
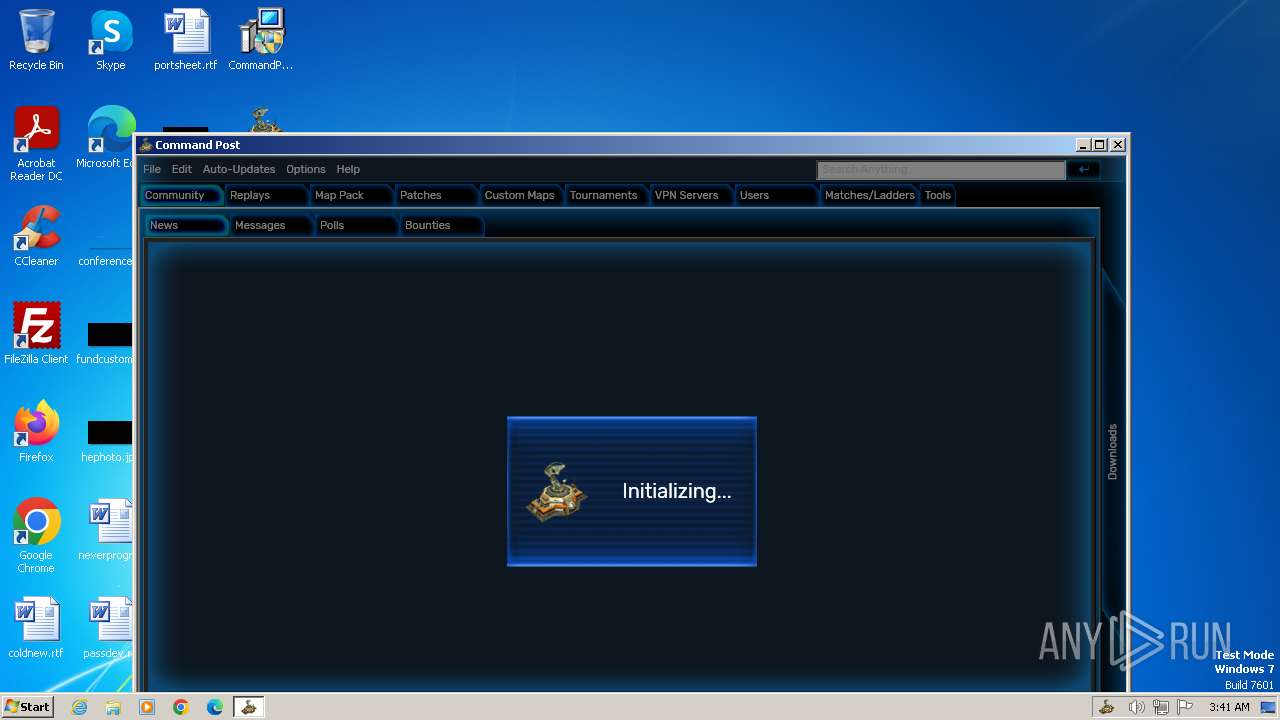
| 1556 | "C:\Program Files\Command Post\CommandPost.exe" | C:\Program Files\Command Post\CommandPost.exe | — | explorer.exe | |||||||||||
User: admin Company: CGF-UPLOADS Integrity Level: MEDIUM Description: Command Post Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2972 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3392 | "C:\Users\admin\Desktop\CommandPostInstaller.exe" | C:\Users\admin\Desktop\CommandPostInstaller.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 3516 | "C:\Program Files\Command Post\CommandPost.exe" -silent | C:\Program Files\Command Post\CommandPost.exe | — | CommandPostInstaller.exe | |||||||||||
User: admin Company: CGF-UPLOADS Integrity Level: HIGH Description: Command Post Version: 1.0.0.0 Modules
| |||||||||||||||
| 3992 | "C:\Users\admin\Desktop\CommandPostInstaller.exe" | C:\Users\admin\Desktop\CommandPostInstaller.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
14 191
Read events
14 035
Write events
111
Delete events
45
Modification events
| (PID) Process: | (3392) CommandPostInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CommandPost |
| Operation: | write | Name: | DisplayName |
Value: Command Post | |||
| (PID) Process: | (3392) CommandPostInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CommandPost |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\Command Post\Uninstall.exe" | |||
| (PID) Process: | (3392) CommandPostInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CommandPost |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (3392) CommandPostInstaller.exe | Key: | HKEY_CLASSES_ROOT\CommandPost |
| Operation: | write | Name: | URL Protocol |
Value: | |||
| (PID) Process: | (3392) CommandPostInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3392) CommandPostInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3392) CommandPostInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3392) CommandPostInstaller.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3392) CommandPostInstaller.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\nsg1BE2.tmp\nsProcess.dll | |||
| (PID) Process: | (3516) CommandPost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
Executable files
5
Suspicious files
3
Text files
4
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | CommandPostInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsg1BE2.tmp\modern-header.bmp | image | |
MD5:— | SHA256:— | |||
| 3392 | CommandPostInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsg1BE2.tmp\nsProcess.dll | executable | |
MD5:— | SHA256:— | |||
| 3392 | CommandPostInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsg1BE2.tmp\AccessControl.dll | executable | |
MD5:— | SHA256:— | |||
| 3392 | CommandPostInstaller.exe | C:\Program Files\Command Post\CommandPost.exe | executable | |
MD5:— | SHA256:— | |||
| 3392 | CommandPostInstaller.exe | C:\Program Files\Command Post\icon.ico | image | |
MD5:— | SHA256:— | |||
| 3392 | CommandPostInstaller.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Command Post.lnk | binary | |
MD5:— | SHA256:— | |||
| 3392 | CommandPostInstaller.exe | C:\Users\Public\Desktop\Command Post.lnk | binary | |
MD5:— | SHA256:— | |||
| 3392 | CommandPostInstaller.exe | C:\Program Files\Command Post\Uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 3392 | CommandPostInstaller.exe | C:\Users\admin\AppData\Local\Temp\nsq1BD1.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | CommandPost.exe | C:\Users\admin\Documents\CommandPost\config.json | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report