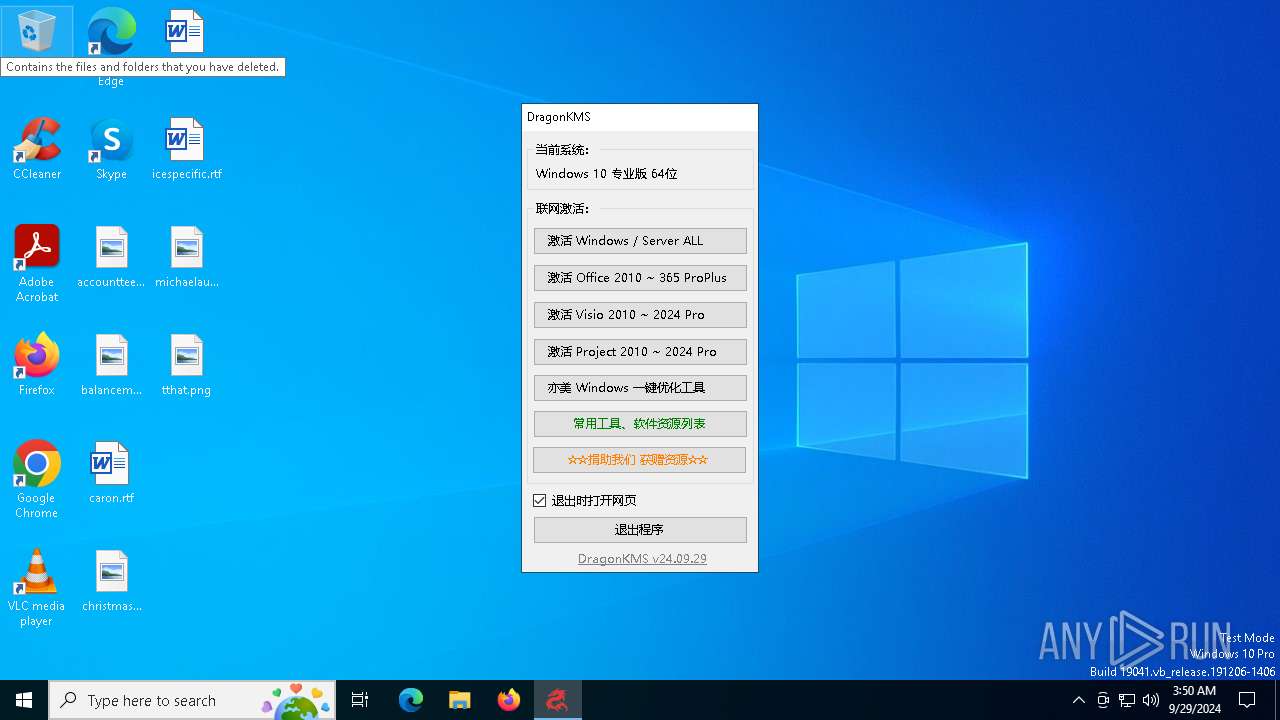
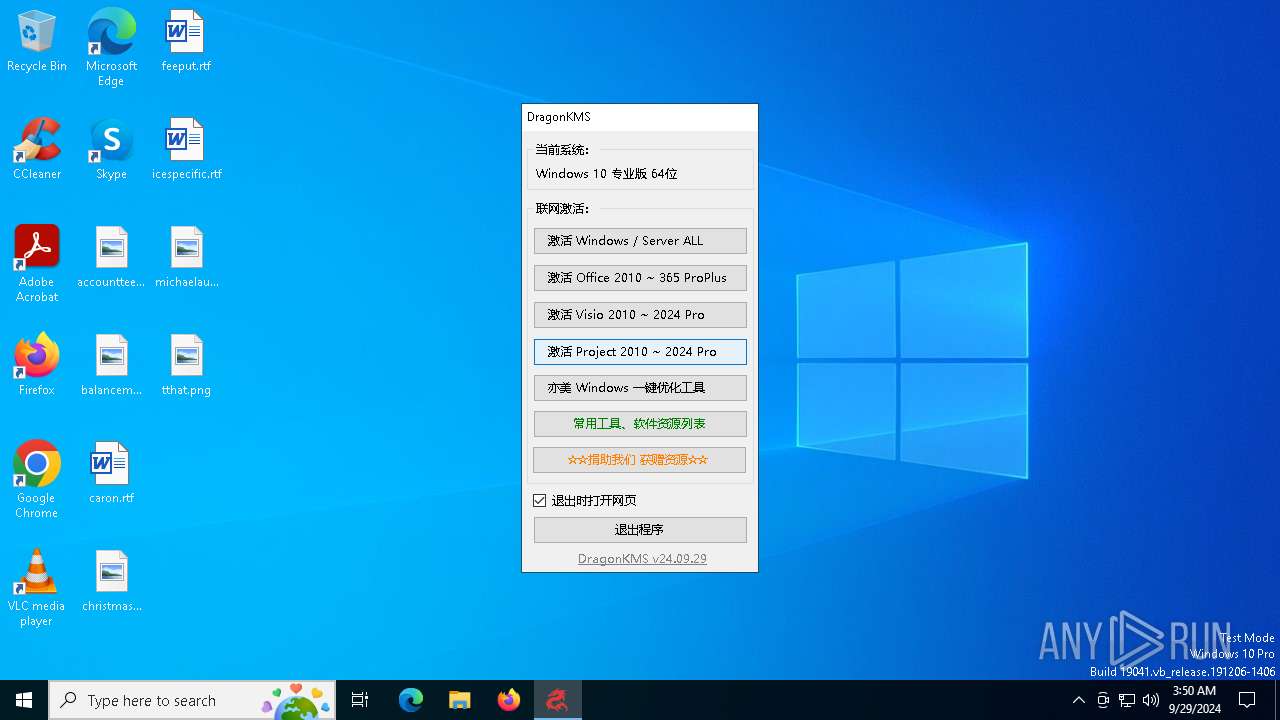
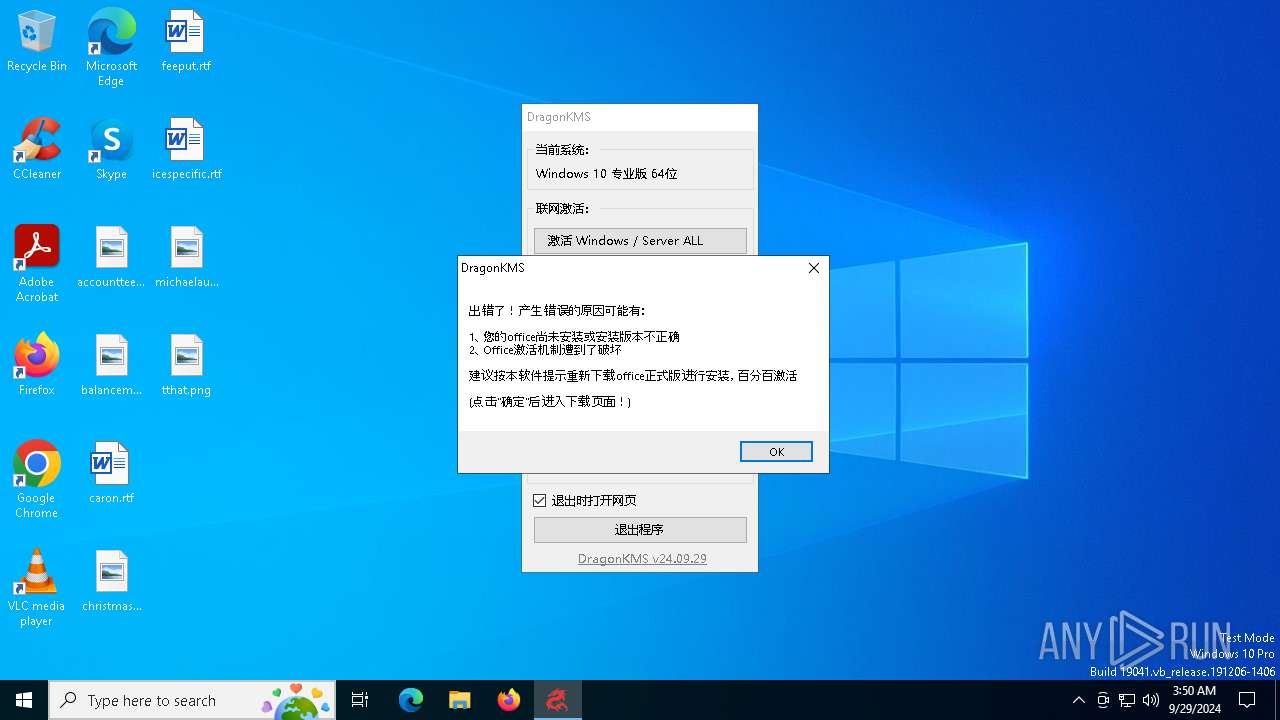
| File name: | DragonKMS v24.09.29.exe |
| Full analysis: | https://app.any.run/tasks/af2aa6f8-5863-439a-8ff6-f41dacaca412 |
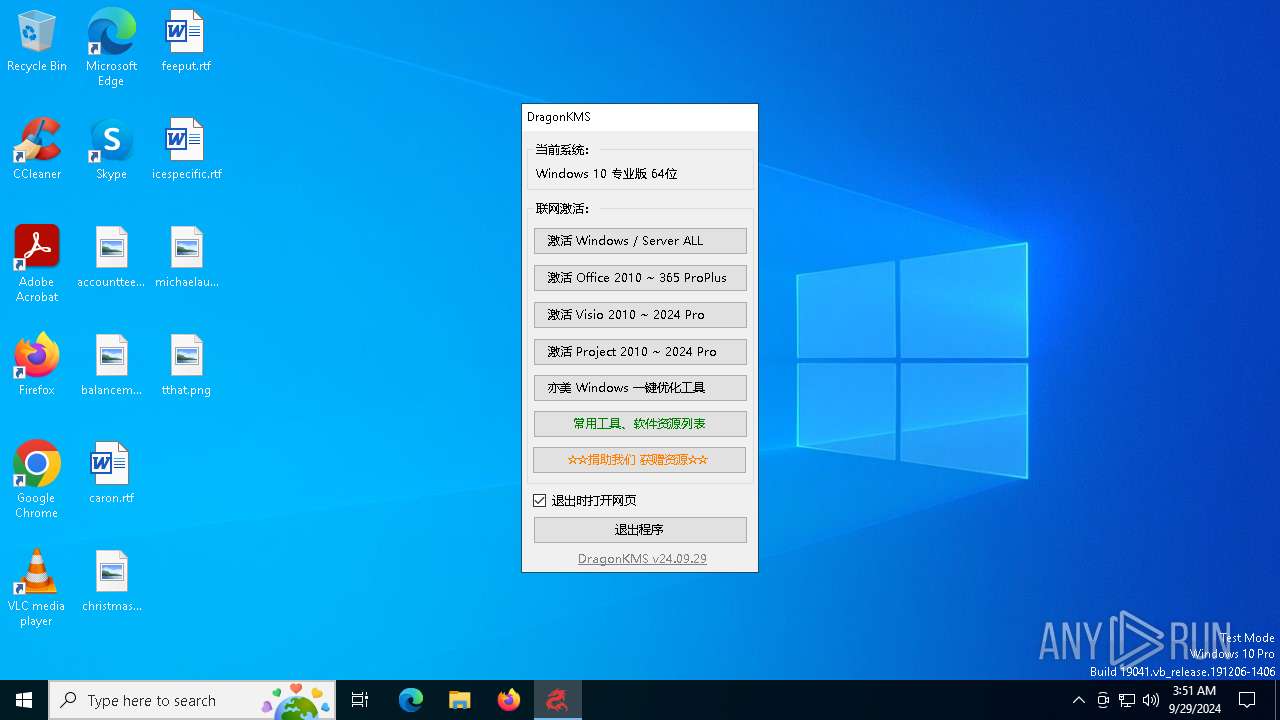
| Verdict: | Malicious activity |
| Analysis date: | September 29, 2024, 03:50:20 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 34B10383CBB9534D5A49EE98B144BB4B |
| SHA1: | 2F581B5E8D2BA123F9EB5EA20F483E4AD25175AE |
| SHA256: | 17C207FD6355FD74EA365ADA3ADA60485EDC4F1B09E2FD4D337E90595E83DADC |
| SSDEEP: | 3072:qdlvP6kVKJJnPRNRNRNRNRosA3y2E4ARWYu:P13333osMNE4y1 |
MALICIOUS
No malicious indicators.SUSPICIOUS
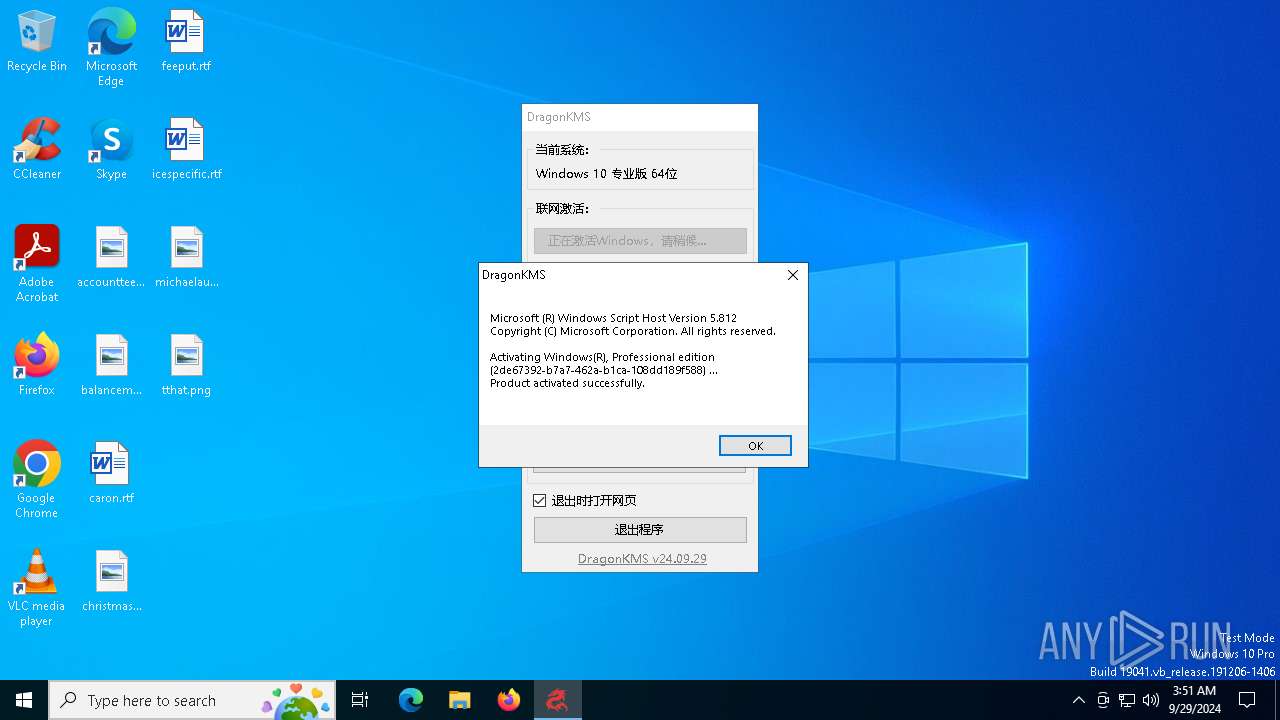
The process executes VB scripts
- cmd.exe (PID: 7620)
The process downloads a VBScript from the remote host
- cmd.exe (PID: 7620)
Starts CMD.EXE for commands execution
- DragonKMS v24.09.29.exe (PID: 1060)
Connects to unusual port
- SppExtComObj.Exe (PID: 4804)
Starts SC.EXE for service management
- cmd.exe (PID: 4560)
- cmd.exe (PID: 6660)
- cmd.exe (PID: 7344)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 3436)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 4560)
- cmd.exe (PID: 3820)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2180)
- cmd.exe (PID: 5128)
- cmd.exe (PID: 6540)
- cmd.exe (PID: 2244)
- cmd.exe (PID: 8108)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 7660)
- cmd.exe (PID: 5056)
- cmd.exe (PID: 7936)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 8028)
- cmd.exe (PID: 4216)
- cmd.exe (PID: 4948)
- cmd.exe (PID: 7084)
- cmd.exe (PID: 6204)
- cmd.exe (PID: 5684)
- cmd.exe (PID: 7952)
- cmd.exe (PID: 3044)
- cmd.exe (PID: 3468)
- cmd.exe (PID: 7232)
- cmd.exe (PID: 5780)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2244)
- cmd.exe (PID: 8124)
- cmd.exe (PID: 4948)
- cmd.exe (PID: 5780)
Modifies existing scheduled task
- schtasks.exe (PID: 2728)
- schtasks.exe (PID: 1072)
- schtasks.exe (PID: 2280)
- schtasks.exe (PID: 3992)
- schtasks.exe (PID: 6080)
- schtasks.exe (PID: 3508)
- schtasks.exe (PID: 6208)
- schtasks.exe (PID: 2580)
- schtasks.exe (PID: 7052)
- schtasks.exe (PID: 1636)
- schtasks.exe (PID: 6988)
- schtasks.exe (PID: 6924)
- schtasks.exe (PID: 2420)
- schtasks.exe (PID: 7400)
The process executes via Task Scheduler
- explorer.exe (PID: 2032)
- explorer.exe (PID: 5780)
- explorer.exe (PID: 8172)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 8124)
- cmd.exe (PID: 4948)
INFO
Disables trace logs
- DragonKMS v24.09.29.exe (PID: 1060)
Reads product name
- DragonKMS v24.09.29.exe (PID: 1060)
Reads the machine GUID from the registry
- DragonKMS v24.09.29.exe (PID: 1060)
Reads the computer name
- DragonKMS v24.09.29.exe (PID: 1060)
Reads Environment values
- DragonKMS v24.09.29.exe (PID: 1060)
Checks proxy server information
- DragonKMS v24.09.29.exe (PID: 1060)
Checks supported languages
- DragonKMS v24.09.29.exe (PID: 1060)
Application launched itself
- msedge.exe (PID: 5144)
- msedge.exe (PID: 3808)
- msedge.exe (PID: 1244)
Manual execution by a user
- msedge.exe (PID: 5144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2099:08:12 21:48:28+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 621568 |
| InitializedDataSize: | 104448 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x99bae |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 24.9.29.0 |
| ProductVersionNumber: | 24.9.29.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | 分享也是一种美,亦是美网络。 |
| CompanyName: | - |
| FileDescription: | DragonKMS |
| FileVersion: | 24.09.29 |
| InternalName: | DragonKMS.exe |
| LegalCopyright: | 这是一款免费软件。 |
| LegalTrademarks: | - |
| OriginalFileName: | DragonKMS.exe |
| ProductName: | DragonKMS |
| ProductVersion: | 24.09.29 |
| AssemblyVersion: | 24.9.29.0 |
Total processes
337
Monitored processes
202
Malicious processes
3
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore" /v "RPSessionInterval" /d 0 /t REG_DWORD /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 240 | reg add "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer" /v link /d "00000000" /t REG_BINARY /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | sc start WdiServiceHost | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 5 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 652 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SystemRestore" /v "RPSessionInterval" /d 0 /t REG_DWORD /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 696 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3368 --field-trial-handle=2340,i,10936711312306003692,458722892069976182,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 812 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Shell Icons" /v 29 /d "C:\WINDOWS\system32\imageres.dll,197" /t reg_sz /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 908 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Policies\Microsoft\Windows\Installer" /v "LimitSystemRestoreCheckpointing" /d 1 /t REG_DWORD /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1060 | "C:\Users\admin\AppData\Local\Temp\DragonKMS v24.09.29.exe" | C:\Users\admin\AppData\Local\Temp\DragonKMS v24.09.29.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: DragonKMS Version: 24.09.29 Modules
| |||||||||||||||
| 1072 | SCHTASKS /Change /DISABLE /TN "\Microsoft\Windows\Windows Error Reporting\QueueReporting" | C:\Windows\System32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
34 556
Read events
34 265
Write events
253
Delete events
38
Modification events
| (PID) Process: | (1060) DragonKMS v24.09.29.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DragonKMS v24_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1060) DragonKMS v24.09.29.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DragonKMS v24_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1060) DragonKMS v24.09.29.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DragonKMS v24_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1060) DragonKMS v24.09.29.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DragonKMS v24_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (1060) DragonKMS v24.09.29.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DragonKMS v24_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (1060) DragonKMS v24.09.29.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DragonKMS v24_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1060) DragonKMS v24.09.29.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DragonKMS v24_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1060) DragonKMS v24.09.29.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DragonKMS v24_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1060) DragonKMS v24.09.29.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DragonKMS v24_RASMANCS |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (1060) DragonKMS v24.09.29.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\DragonKMS v24_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
6
Suspicious files
98
Text files
127
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF3f87cb.TMP | — | |
MD5:— | SHA256:— | |||
| 5144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:1E9E15EF6E531C4557100F20C9C76F01 | SHA256:46CB063CC268B69B172660F166C4394D5B4EDD802388B3EC16766DEBDB9F86C3 | |||
| 5144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Code Cache\js\index-dir\todelete_0e78c708f087d4d8 | binary | |
MD5:95FC65CACF599A197741EB36DEB0F8AE | SHA256:B84BDA5415D69DA598F2015A9BFDB024727F3DE3F0E9E6B16FDD7533026A5565 | |||
| 5144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF3f87ea.TMP | — | |
MD5:— | SHA256:— | |||
| 5144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF3f87fa.TMP | — | |
MD5:— | SHA256:— | |||
| 5144 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF3f86c1.TMP | binary | |
MD5:D13C64FDD3F35BE7012E14C743DB58BC | SHA256:C7E5A49CECB65339CF2CB197E902E746F0821D3A91DA439BA75D3032C77C0A06 | |||
| 3808 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\bf65b8c8-062f-4289-be7b-21145a4aa34e.tmp | binary | |
MD5:5FDA6990C695C8B035FE28B843A988A7 | SHA256:015D6BC20794D827101913156D6515639FD074CF13FCA842FC432A46FD62CC7D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
66
TCP/UDP connections
120
DNS requests
57
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6784 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
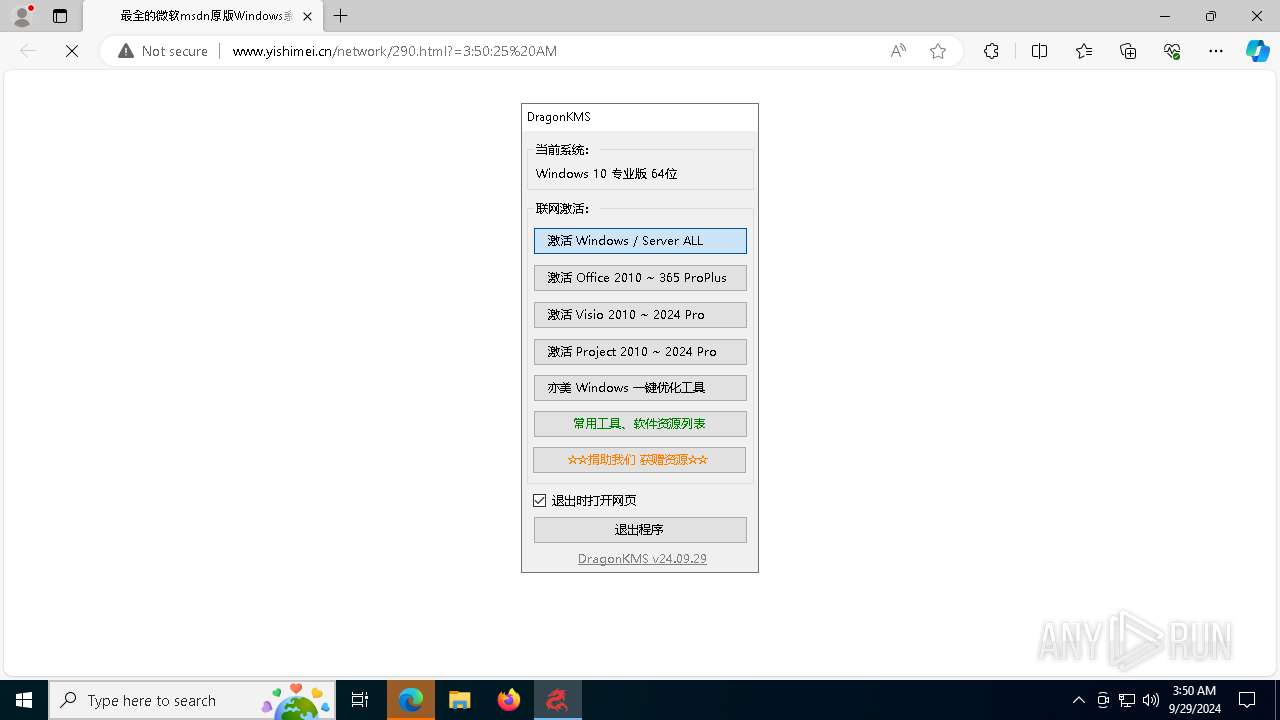
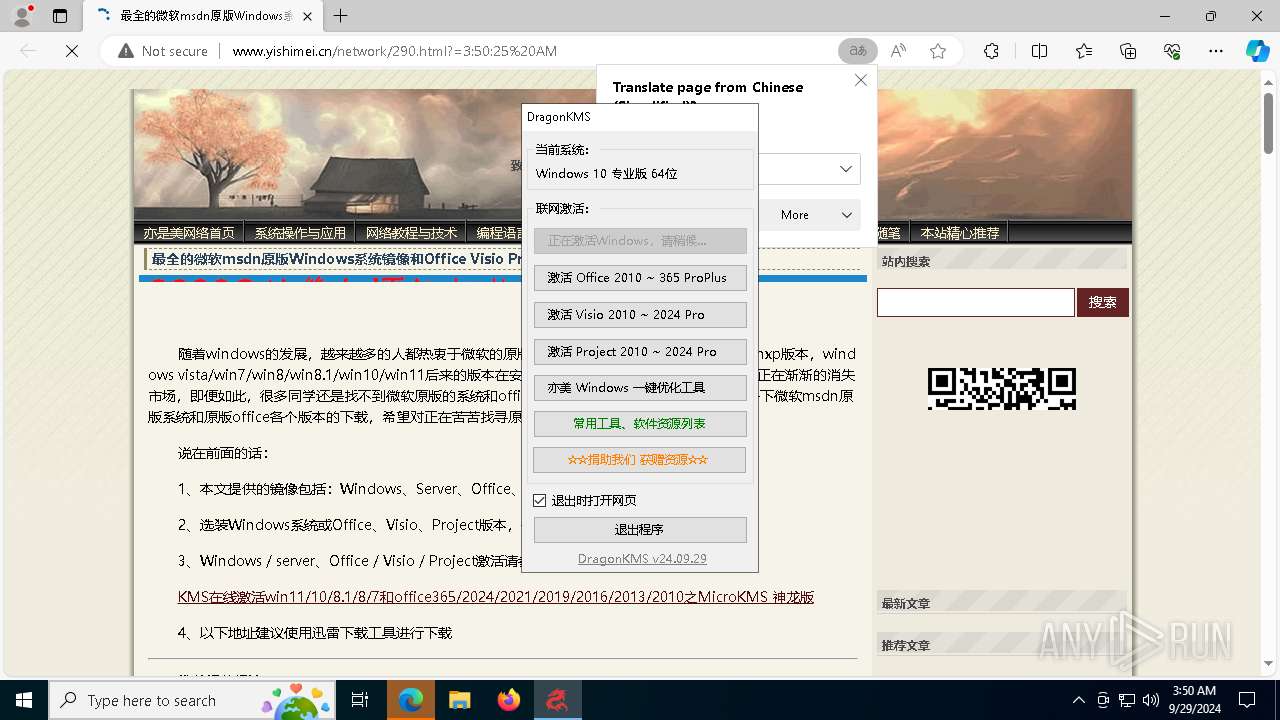
1060 | DragonKMS v24.09.29.exe | GET | 200 | 116.255.154.157:80 | http://www.yishimei.cn/go/DragonKMS/DragonKMS.html | unknown | — | — | unknown |
2836 | msedge.exe | GET | 200 | 116.255.154.157:80 | http://www.yishimei.cn/themes/j-spring/source/style.css.asp | unknown | — | — | unknown |
2836 | msedge.exe | GET | 200 | 116.255.154.157:80 | http://www.yishimei.cn/network/290.html?=3:50:25%20AM | unknown | — | — | unknown |
2836 | msedge.exe | GET | 200 | 116.255.154.157:80 | http://www.yishimei.cn/script/common.js | unknown | — | — | unknown |
2836 | msedge.exe | GET | 200 | 116.255.154.157:80 | http://www.yishimei.cn/script/ad_daohang.js | unknown | — | — | unknown |
2836 | msedge.exe | GET | 200 | 116.255.154.157:80 | http://www.yishimei.cn/function/c_html_js_add.asp | unknown | — | — | unknown |
2836 | msedge.exe | GET | 200 | 116.255.154.157:80 | http://www.yishimei.cn/script/ad_banner.js | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4308 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
880 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 184.30.17.189:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1144 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.yishimei.cn |
| unknown |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |