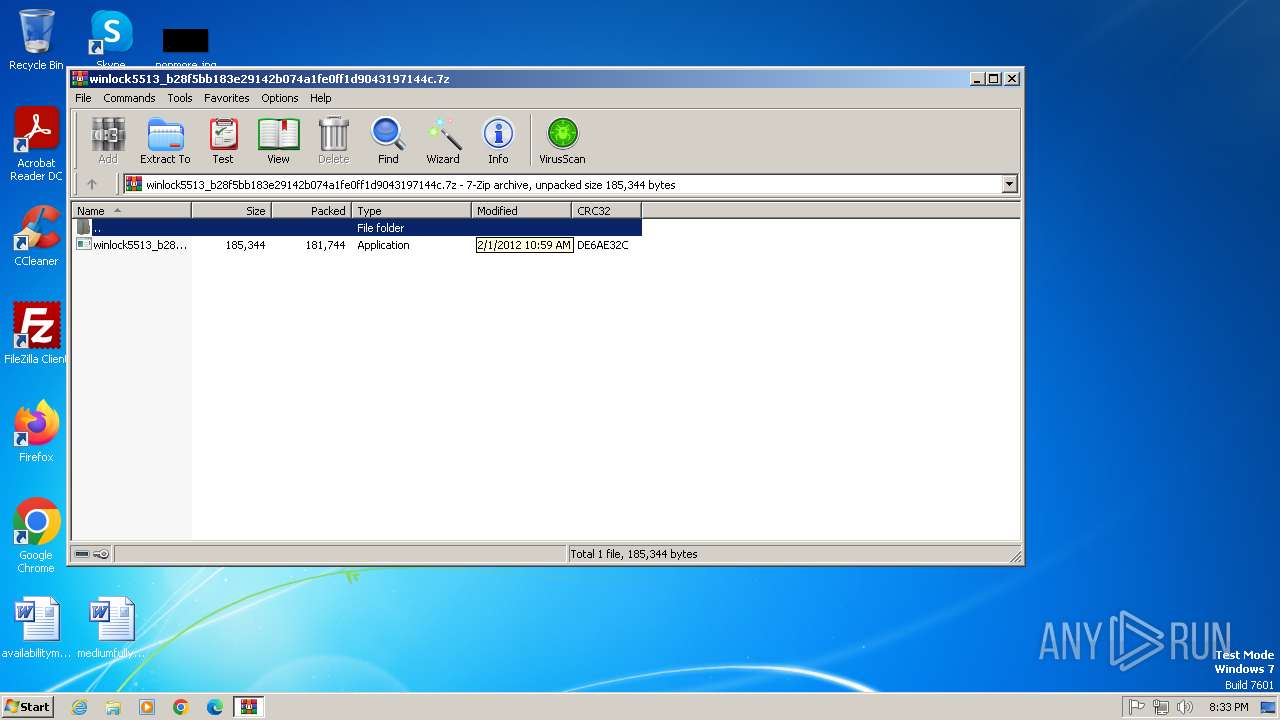
| File name: | winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.7z |
| Full analysis: | https://app.any.run/tasks/5f991a08-2227-4e02-9828-a69403f6a144 |
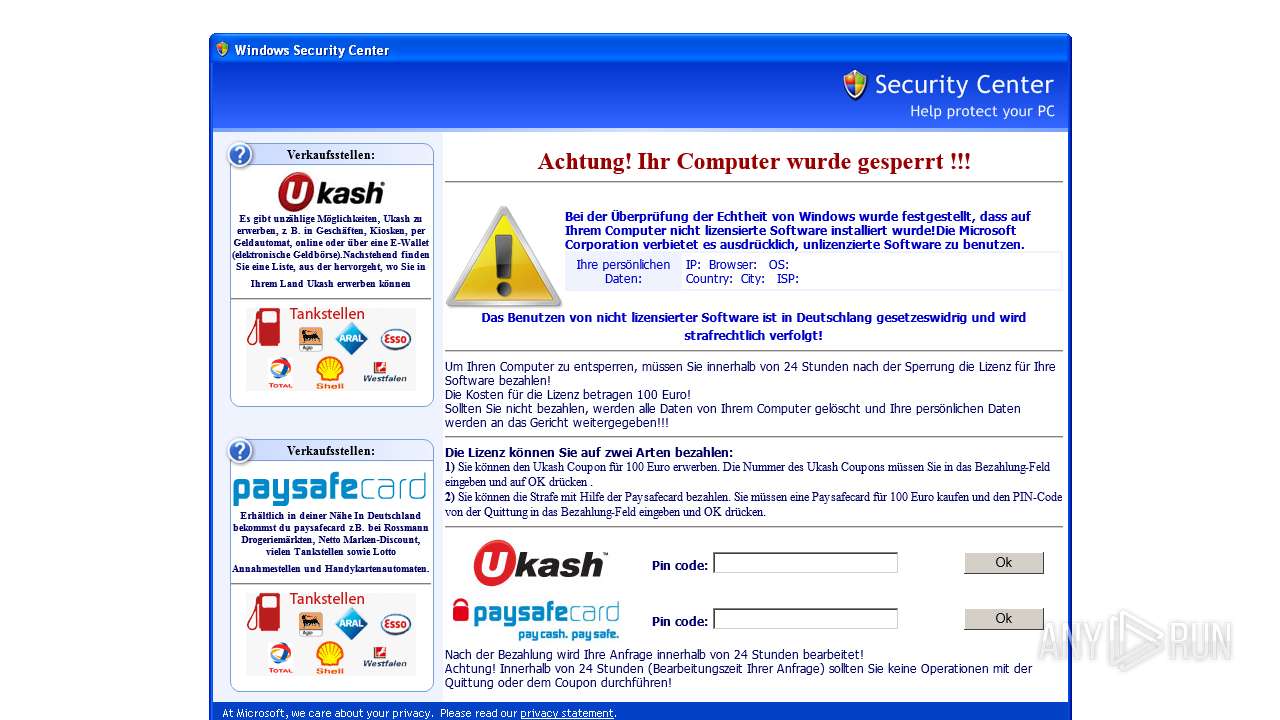
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 19:33:51 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 129497B9011F47A75946E810C1870767 |
| SHA1: | 13B57F0E714BD9D01CF34E0FAE23E4EB934049C8 |
| SHA256: | 17AF8ACCDD6FD2F8C418CD14C2C4B20A6BB22EF121A4E5AFA7972EAF3AB5BEBC |
| SSDEEP: | 6144:LjSRwnI/IxpTNelmxl8j5NqEtoUFO7MhCJZG:LjKwI/WpZelE8HqejFO7MhCJZG |
MALICIOUS
Changes the autorun value in the registry
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
SUSPICIOUS
Reads the Internet Settings
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
Reads Microsoft Outlook installation path
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
Reads security settings of Internet Explorer
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
Reads Internet Explorer settings
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
Connects to the server without a host name
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
Checks for external IP
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1224)
The sample compiled with english language support
- WinRAR.exe (PID: 1224)
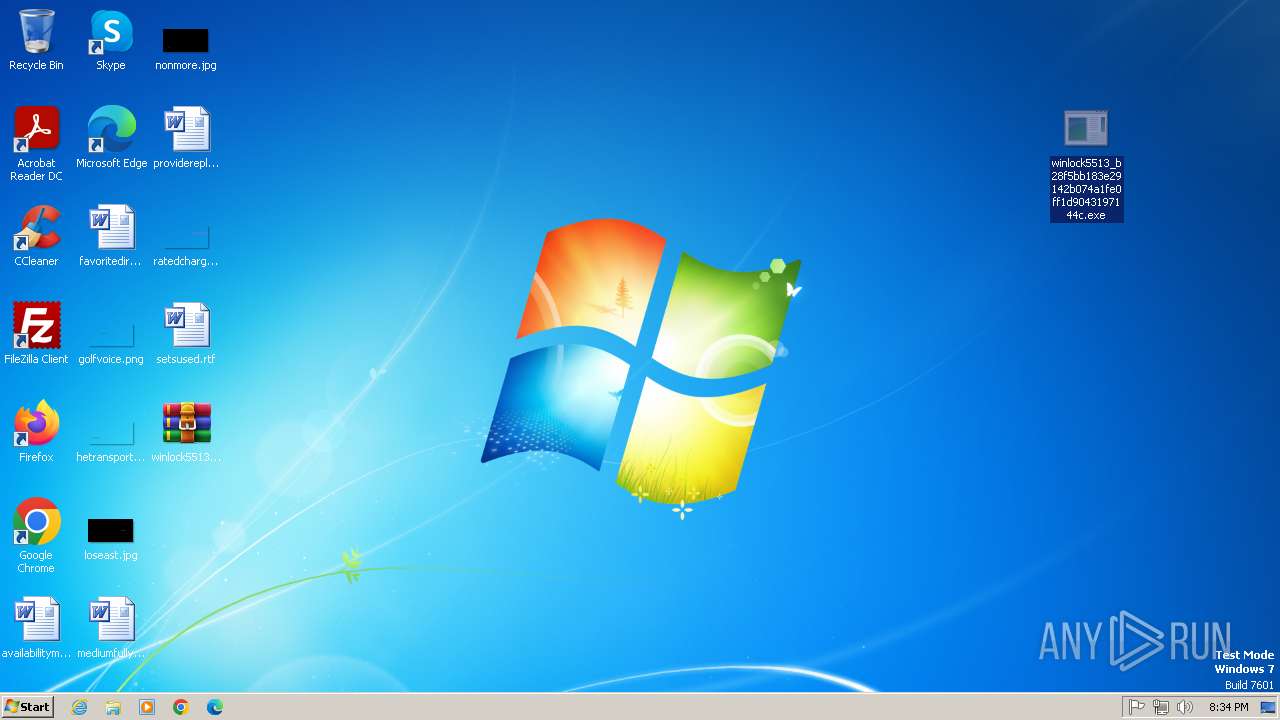
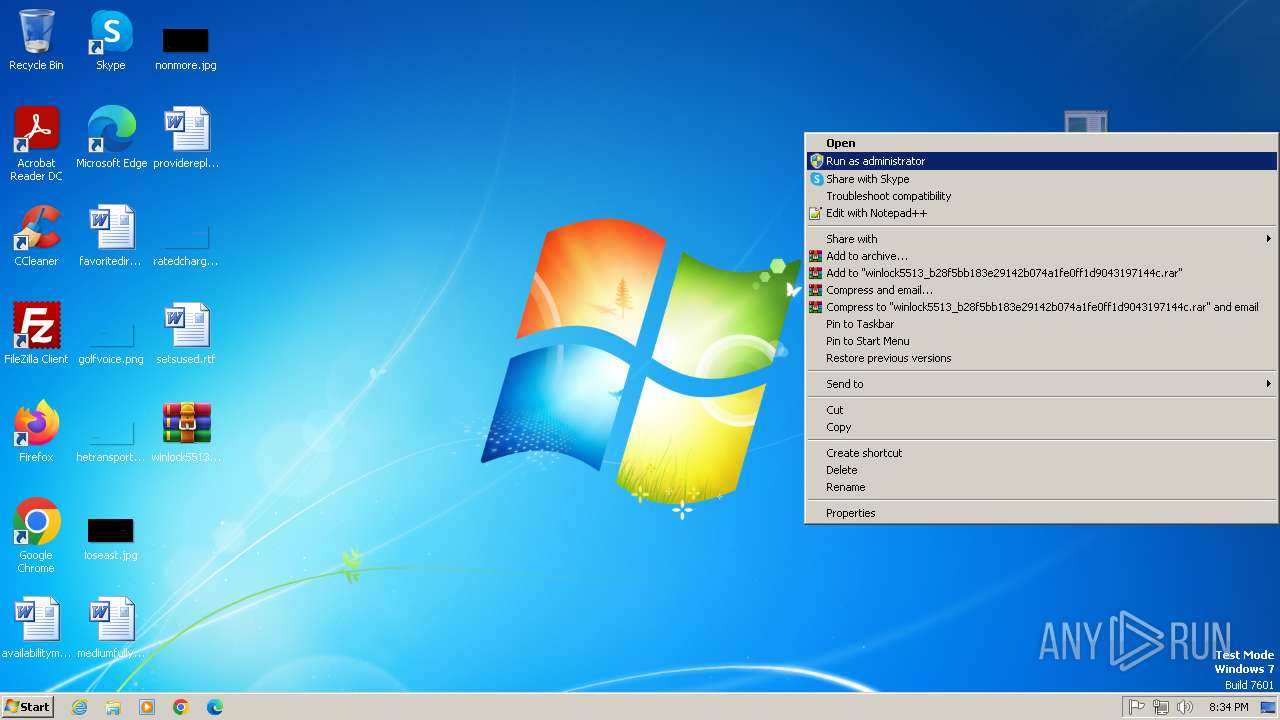
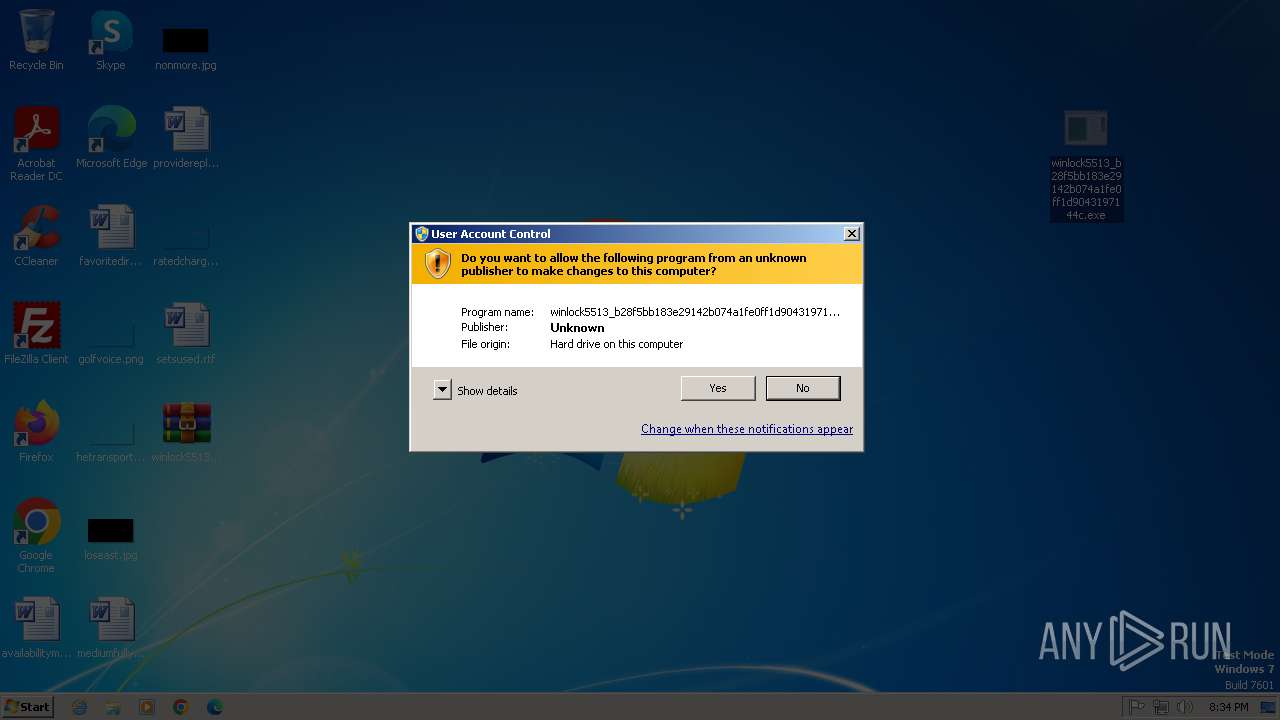
Manual execution by a user
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
Checks supported languages
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
Reads the computer name
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
Checks proxy server information
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
Reads the machine GUID from the registry
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
Creates files or folders in the user directory
- winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe (PID: 2536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2012:02:01 10:59:06+00:00 |
| ArchivedFileName: | winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe |
Total processes
40
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
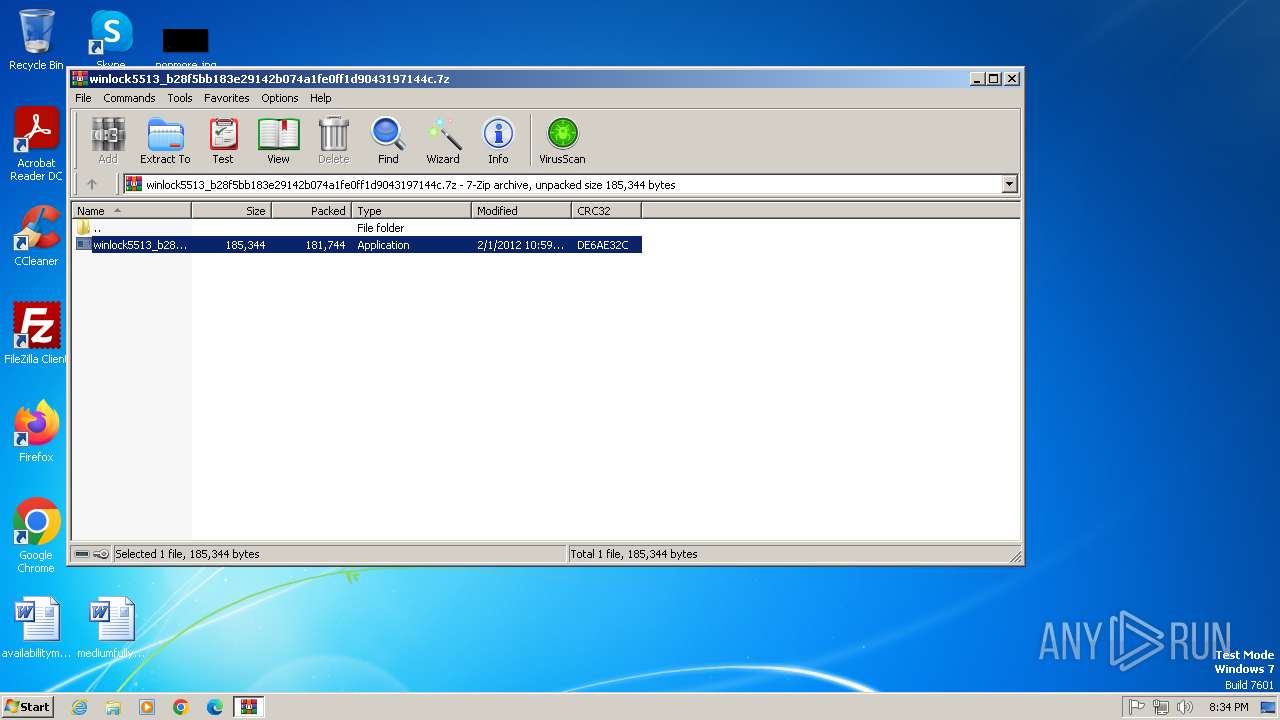
| 1224 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2536 | "C:\Users\admin\Desktop\winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe" | C:\Users\admin\Desktop\winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe | explorer.exe | ||||||||||||
User: admin Company: Orb Networks Integrity Level: HIGH Description: Akron Cakes Crook Version: 4.9 Modules
| |||||||||||||||
Total events
3 597
Read events
3 400
Write events
191
Delete events
6
Modification events
| (PID) Process: | (1224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1224) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (1224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (1224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.7z | |||
| (PID) Process: | (1224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1224) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
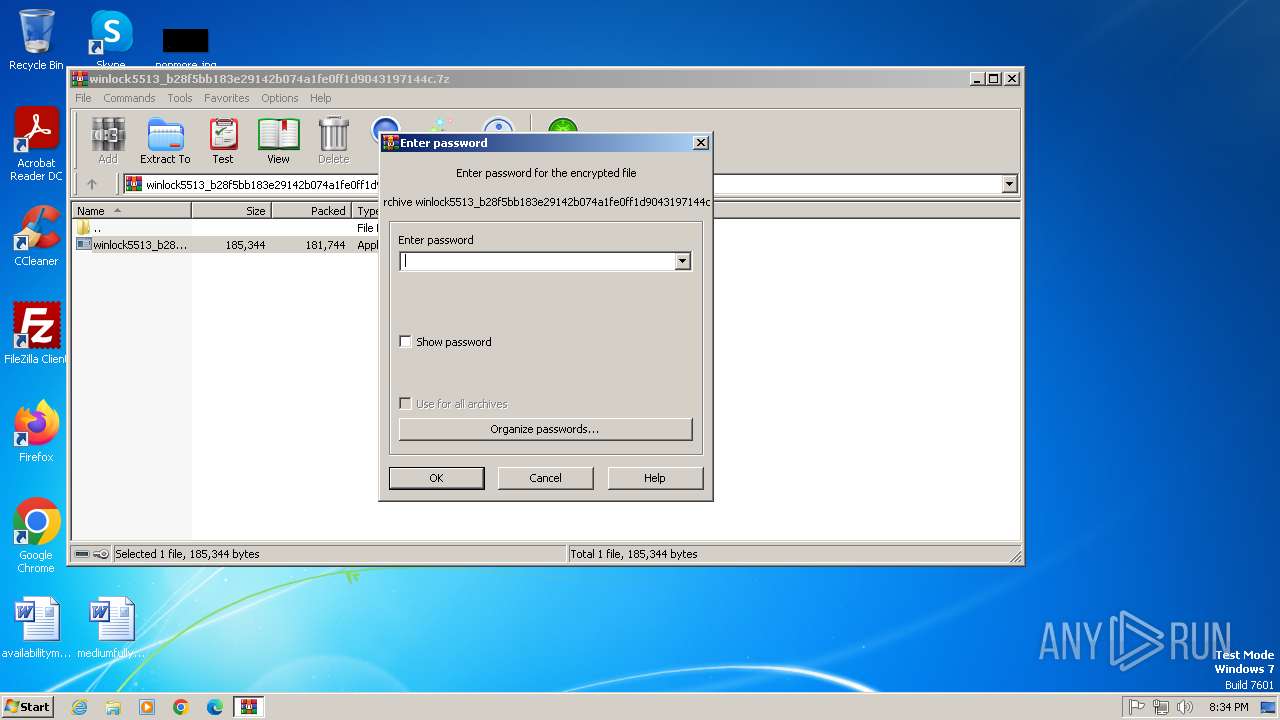
| 1224 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1224.44931\winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe | executable | |
MD5:6AC9F81C2BE49C77DBEC0AD5F6FC95C6 | SHA256:96270A34FA72C31BC736ECEFADC74E8DC3EBC6EF55C0E4C06DC3FBD4FD2D64F6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2536 | winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe | GET | 404 | 86.63.168.110:80 | http://86.63.168.110/i.php?a=105 | unknown | — | — | malicious |
2536 | winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe | GET | 404 | 149.248.7.185:80 | http://tools.ip2location.com/ib2/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
2536 | winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe | 86.63.168.110:80 | — | Sia Nano IT | LV | malicious |
2536 | winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe | 149.248.7.185:80 | tools.ip2location.com | AS-CHOOPA | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
tools.ip2location.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2536 | winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe | A Network Trojan was detected | ET MALWARE Fake Variation of Mozilla 4.0 - Likely Trojan |
2536 | winlock5513_b28f5bb183e29142b074a1fe0ff1d9043197144c.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup - ip2location.com |