| download: | ContentDirector_Setup.exe |
| Full analysis: | https://app.any.run/tasks/405aa48d-e7c9-4fc6-8a0f-b73c96ce2fd5 |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 14:07:17 |
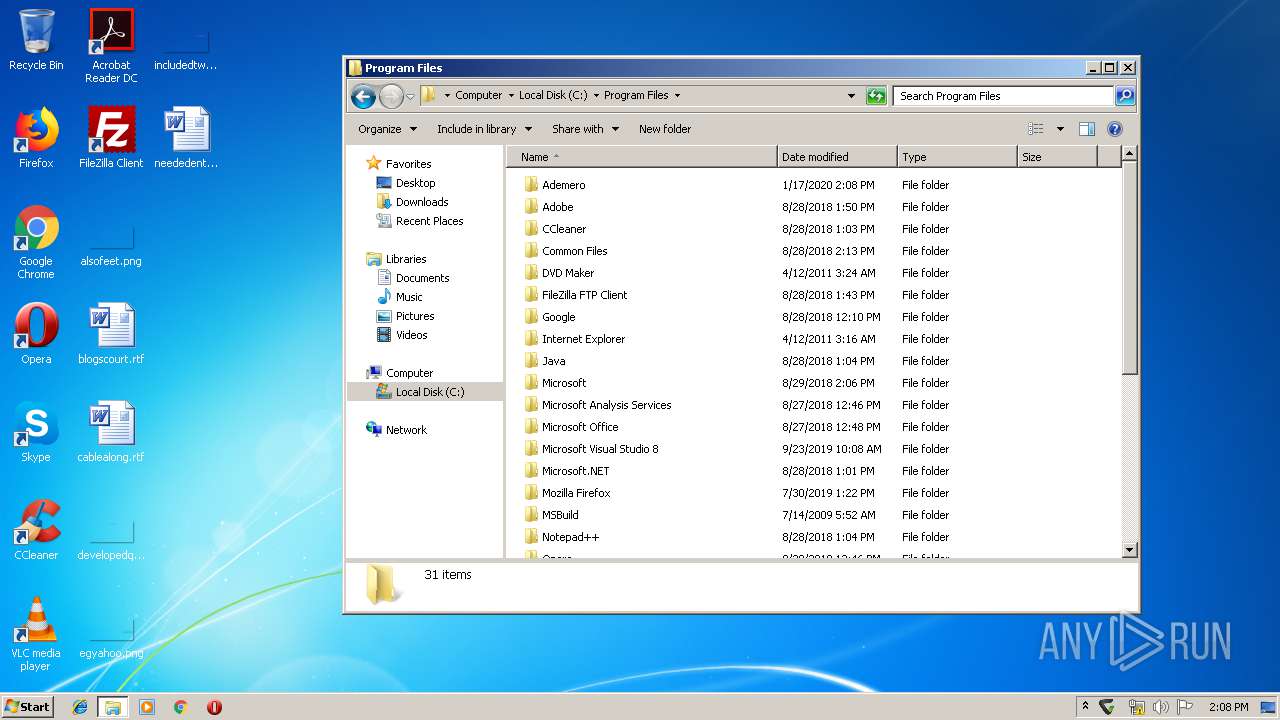
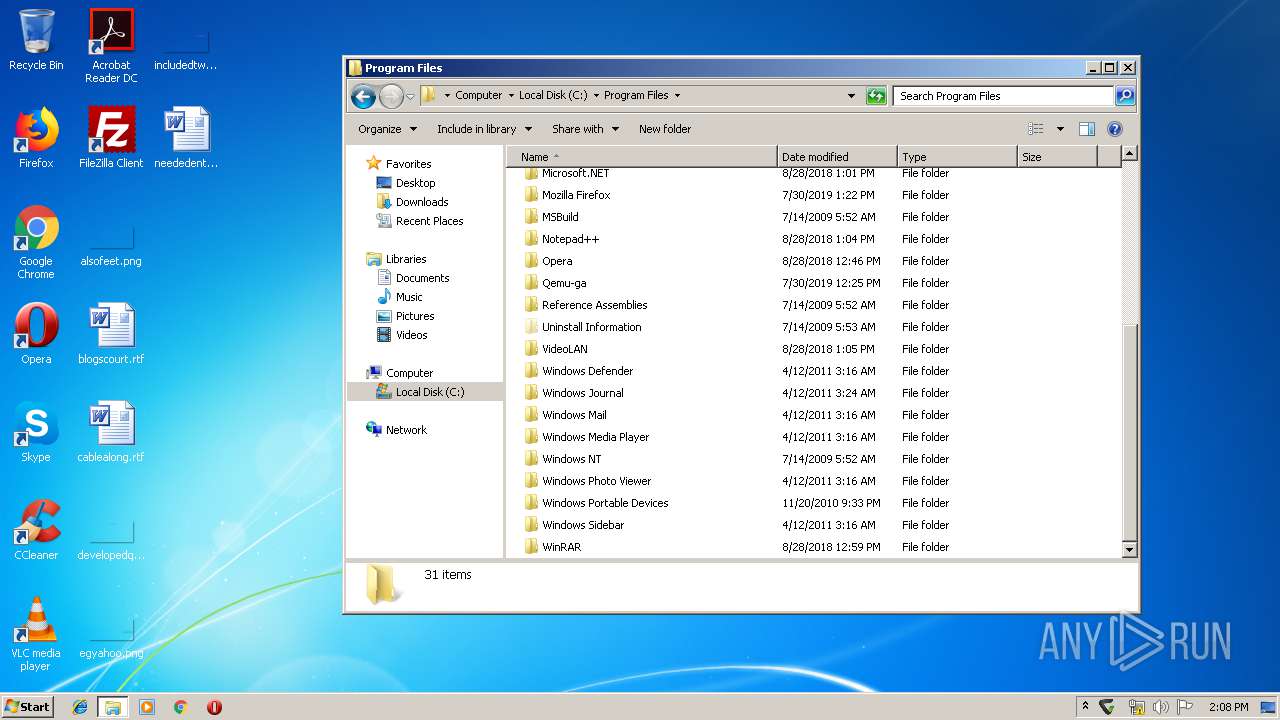
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 240C6C9BFF61D418947114B71D4A98AC |
| SHA1: | B65D2A037E3221AE160F0AE527962CCC3351D85C |
| SHA256: | 17A202821480A604CF8BD481921814DE9684BACABCE4577C9600C9F44D5C3EA5 |
| SSDEEP: | 196608:wA0JCtkPBHIb1cYzdpJnNW2tvdg9IHkLBR2WudVbinsrjz:wAwPBobr3hwIvdgGSBR1aknsrjz |
MALICIOUS
Application was dropped or rewritten from another process
- Ademero.ContentCentral.ContentDirector.exe (PID: 3732)
- Ademero.ContentCentral.ContentDirector.exe (PID: 3532)
- Ademero.ContentCentral.ContentDirector.exe (PID: 4092)
- certutil.exe (PID: 2120)
- certutil.exe (PID: 2472)
- Ademero.ContentCentral.ContentDirector.exe (PID: 3000)
- Ademero.ContentCentral.ContentDirector.exe (PID: 2200)
- certutil.exe (PID: 3088)
- certutil.exe (PID: 2916)
- certutil.exe (PID: 1748)
- certutil.exe (PID: 2836)
- certutil.exe (PID: 292)
- certutil.exe (PID: 2368)
- Ademero.ContentCentral.ContentDirector.exe (PID: 1888)
Loads dropped or rewritten executable
- Ademero.ContentCentral.ContentDirector.exe (PID: 3732)
- Ademero.ContentCentral.ContentDirector.exe (PID: 2200)
- Ademero.ContentCentral.ContentDirector.exe (PID: 4092)
- Ademero.ContentCentral.ContentDirector.exe (PID: 3000)
- certutil.exe (PID: 2916)
- certutil.exe (PID: 2472)
- certutil.exe (PID: 3088)
- certutil.exe (PID: 2120)
- certutil.exe (PID: 2836)
- certutil.exe (PID: 1748)
- certutil.exe (PID: 2368)
- certutil.exe (PID: 292)
- Ademero.ContentCentral.ContentDirector.exe (PID: 3532)
- Ademero.ContentCentral.ContentDirector.exe (PID: 1888)
Changes the autorun value in the registry
- Ademero.ContentCentral.ContentDirector.exe (PID: 2200)
Changes settings of System certificates
- Ademero.ContentCentral.ContentDirector.exe (PID: 3532)
SUSPICIOUS
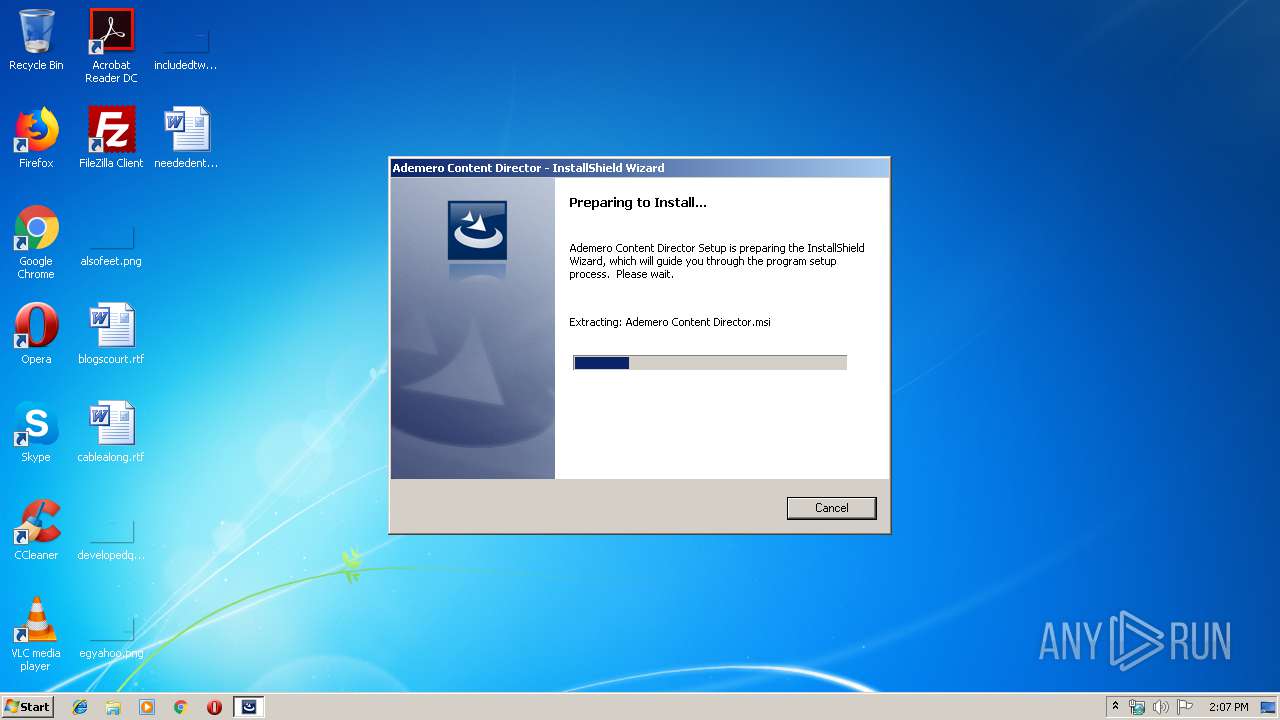
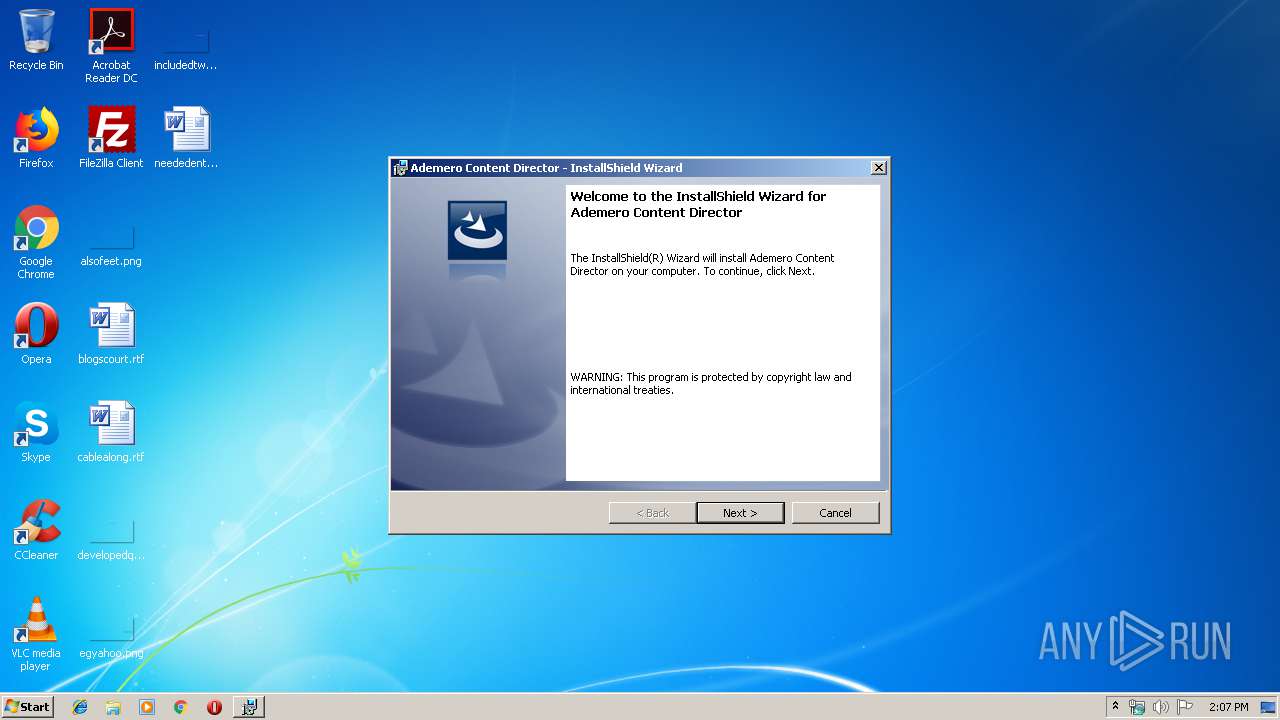
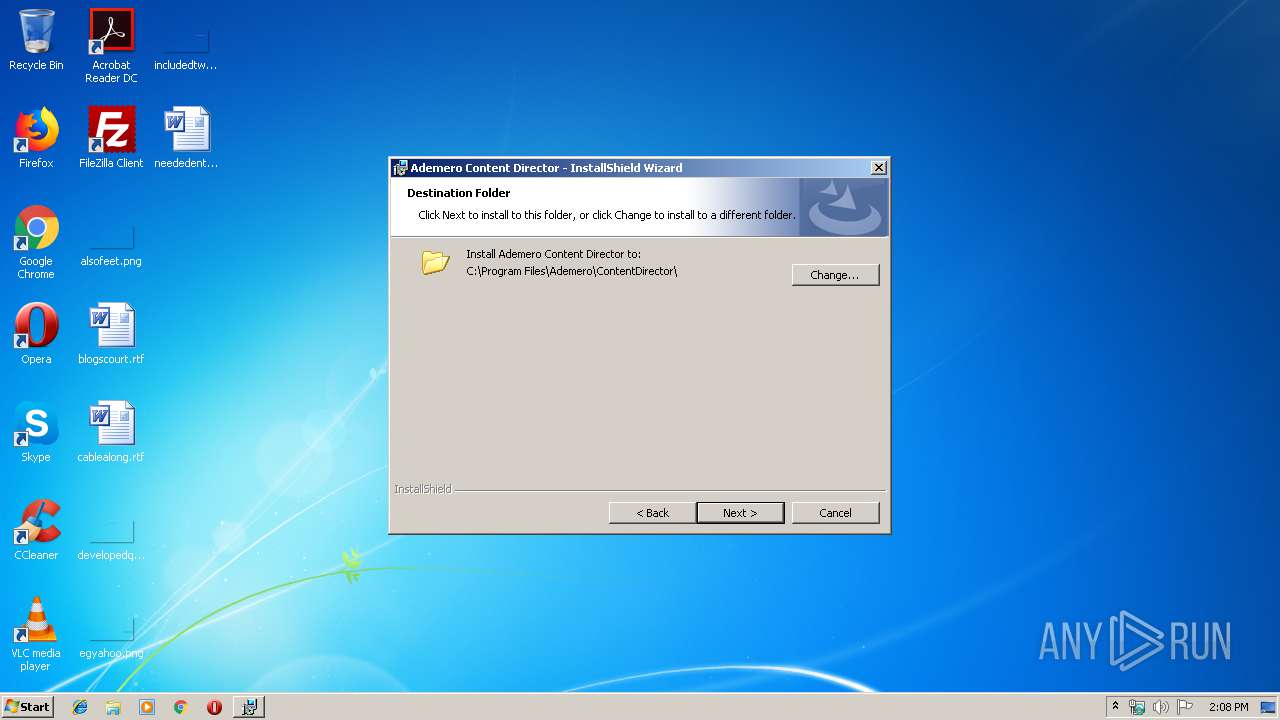
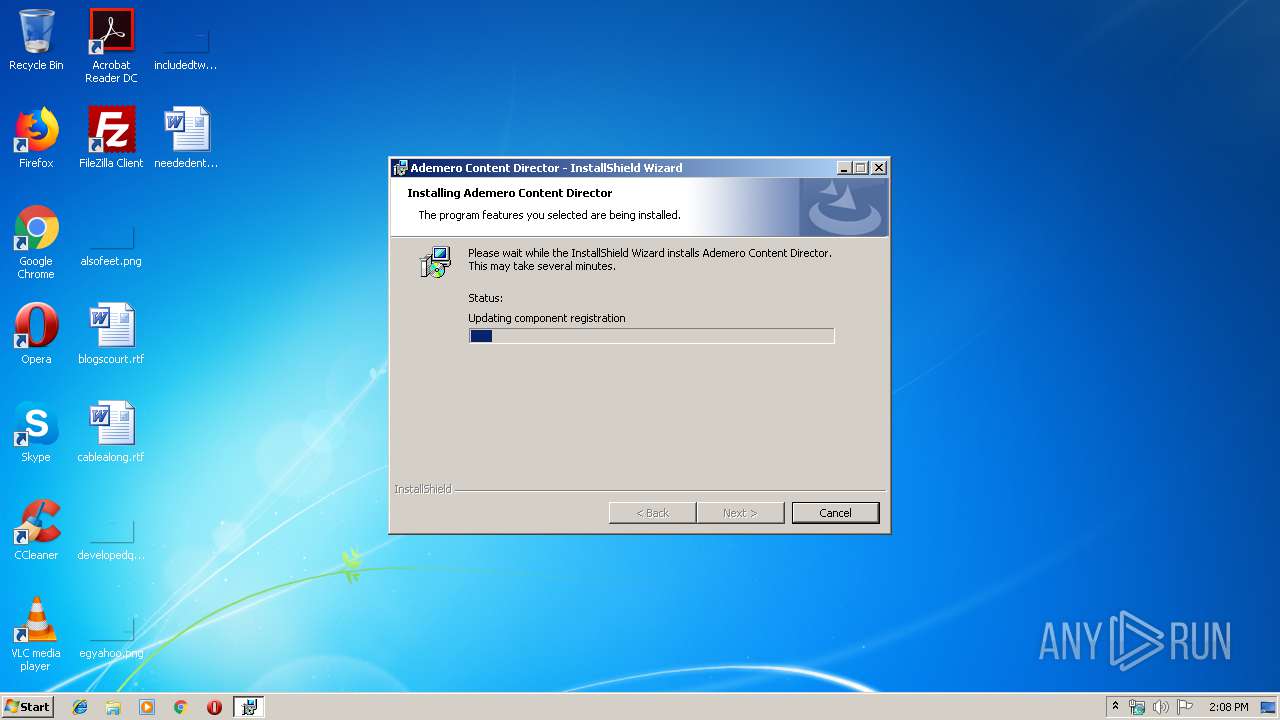
Starts Microsoft Installer
- ContentDirector_Setup.exe (PID: 1892)
Executable content was dropped or overwritten
- ContentDirector_Setup.exe (PID: 1892)
- msiexec.exe (PID: 3132)
Uses NETSH.EXE for network configuration
- Ademero.ContentCentral.ContentDirector.exe (PID: 3732)
Creates files in the user directory
- certutil.exe (PID: 2916)
- certutil.exe (PID: 3088)
Creates files in the program directory
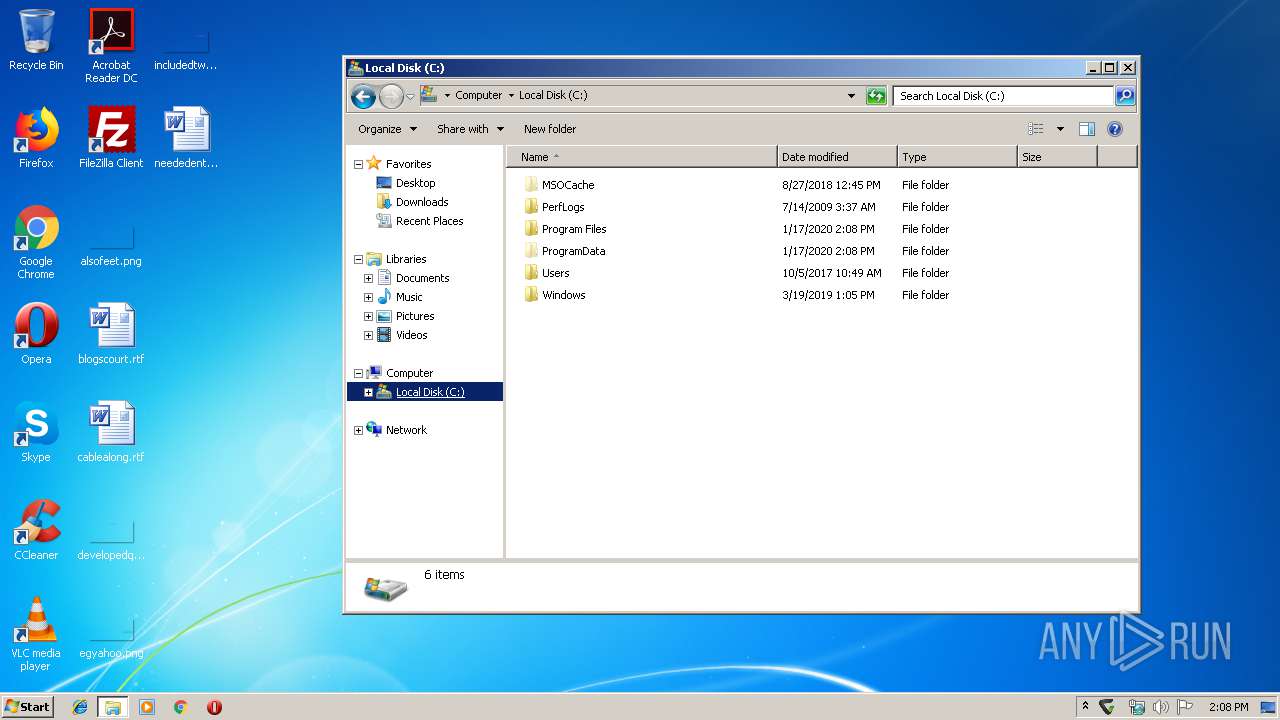
- Ademero.ContentCentral.ContentDirector.exe (PID: 3532)
INFO
Application launched itself
- msiexec.exe (PID: 3132)
Creates a software uninstall entry
- msiexec.exe (PID: 3132)
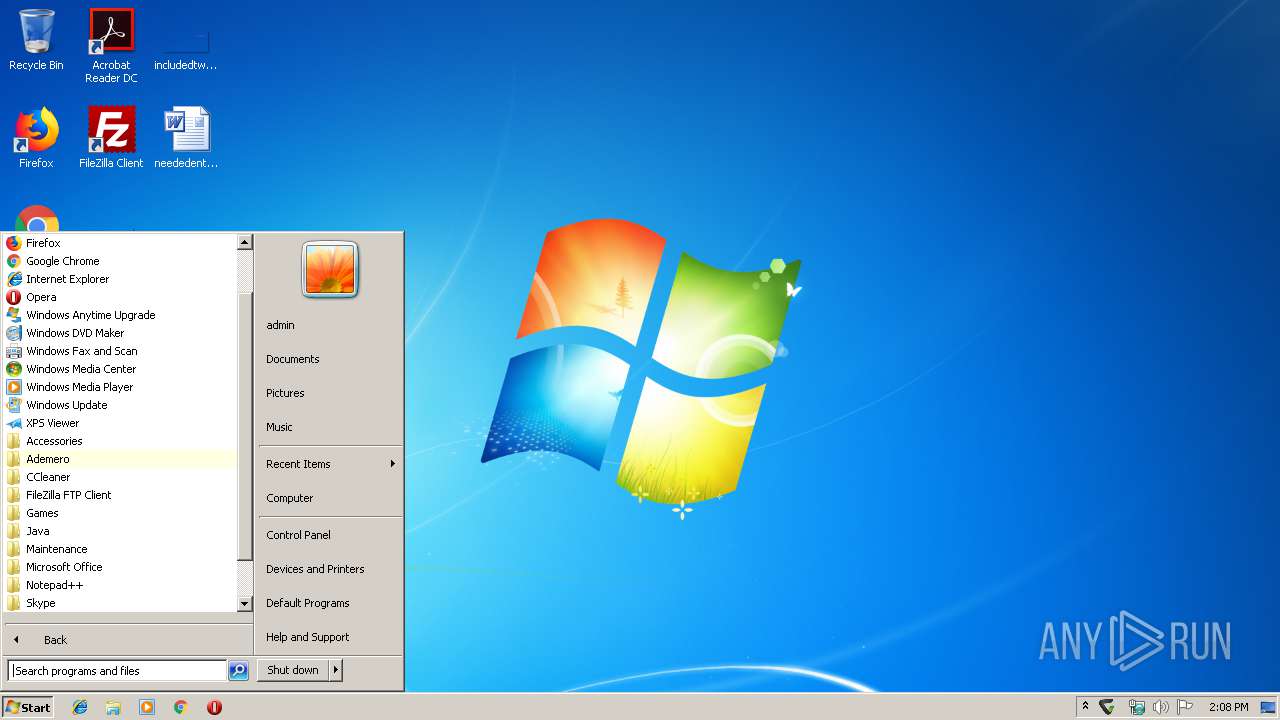
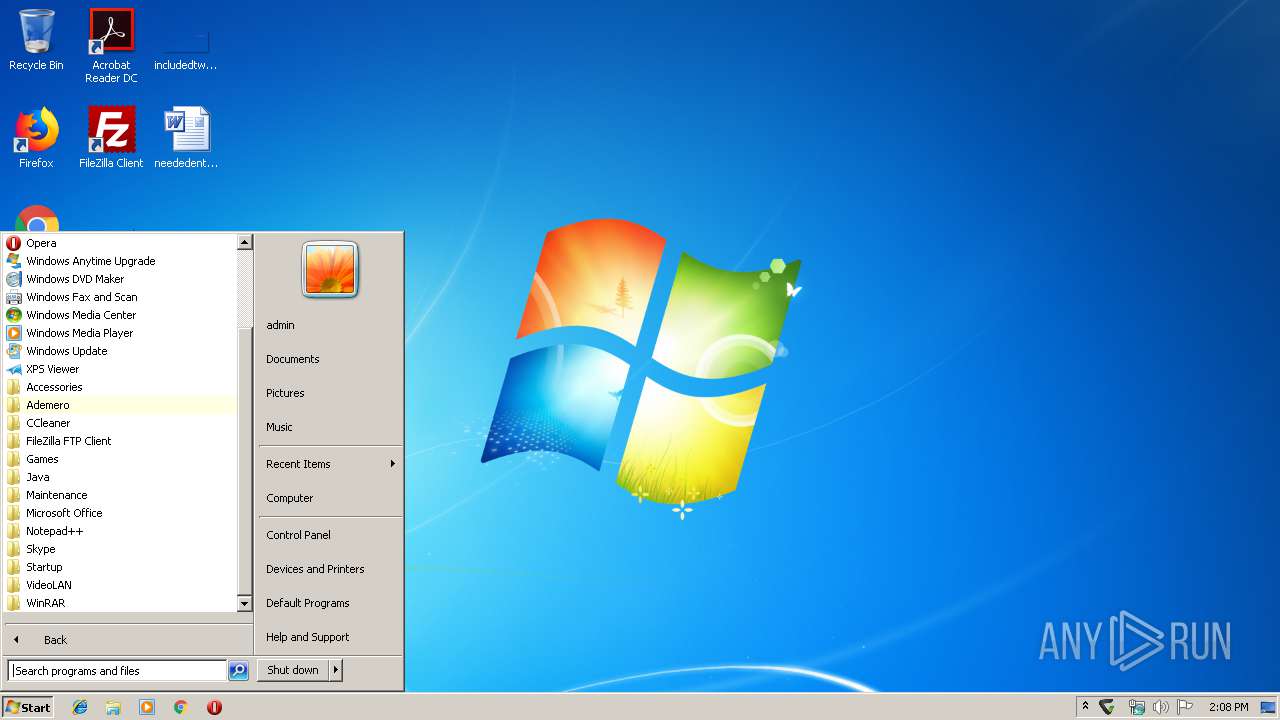
Manual execution by user
- explorer.exe (PID: 616)
Creates files in the program directory
- msiexec.exe (PID: 3132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:10:02 07:23:06+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 932864 |
| InitializedDataSize: | 536064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x98fab |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.5.6919.0 |
| ProductVersionNumber: | 7.5.6919.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Ademero, Inc. |
| FileDescription: | Setup Launcher Unicode |
| FileVersion: | 7.5.6919 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (c) 2013 Flexera Software LLC. All Rights Reserved. |
| OriginalFileName: | InstallShield Setup.exe |
| ProductName: | Ademero Content Director |
| ProductVersion: | 7.5.6919 |
| InternalBuildNumber: | 133442 |
| ISInternalVersion: | 20.0.496 |
| ISInternalDescription: | Setup Launcher Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Oct-2013 05:23:06 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Ademero, Inc. |
| FileDescription: | Setup Launcher Unicode |
| FileVersion: | 7.5.6919 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (c) 2013 Flexera Software LLC. All Rights Reserved. |
| OriginalFilename: | InstallShield Setup.exe |
| ProductName: | Ademero Content Director |
| ProductVersion: | 7.5.6919 |
| Internal Build Number: | 133442 |
| ISInternalVersion: | 20.0.496 |
| ISInternalDescription: | Setup Launcher Unicode |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 02-Oct-2013 05:23:06 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000E3BEB | 0x000E3C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.5964 |
.rdata | 0x000E5000 | 0x0003232E | 0x00032400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.75092 |
.data | 0x00118000 | 0x00008B48 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.58939 |
.rsrc | 0x00121000 | 0x0004DF54 | 0x0004E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.57427 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22609 | 1210 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.835 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.35696 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 6.14965 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 6.18448 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.85842 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 5.57777 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 5.81004 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 6.06596 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 3.22977 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
msi.dll (delay-loaded) |
Total processes
74
Monitored processes
24
Malicious processes
14
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Ademero\ContentDirector\NSS certutil\certutil.exe" -d "C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default" -A -t "C,c,c" -n "Ademero ServerAuth CA" -i "C:\Program Files\Ademero\ContentDirector\certificates\AdemeroServerAuthCA.crt" | C:\Program Files\Ademero\ContentDirector\NSS certutil\certutil.exe | — | Ademero.ContentCentral.ContentDirector.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 388 | "netsh.exe" http delete sslcert ipport=0.0.0.0:54987 | C:\Windows\system32\netsh.exe | — | Ademero.ContentCentral.ContentDirector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 616 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | "netsh.exe" http add sslcert ipport=0.0.0.0:54987 certhash=d3973cf80ad4ac87dfb3f24228a463945546376f appid={CF904B43-937C-43C9-8C59-1F028EF5CF28} | C:\Windows\system32\netsh.exe | — | Ademero.ContentCentral.ContentDirector.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Ademero\ContentDirector\NSS certutil\certutil.exe" -d "C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default" -D -n "Ademero ServerAuth CA" | C:\Program Files\Ademero\ContentDirector\NSS certutil\certutil.exe | — | Ademero.ContentCentral.ContentDirector.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 255 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Ademero\ContentDirector\Ademero.ContentCentral.ContentDirector.exe" -CreateEventLog | C:\Program Files\Ademero\ContentDirector\Ademero.ContentCentral.ContentDirector.exe | — | msiexec.exe | |||||||||||
User: admin Company: Ademero, Inc. Integrity Level: HIGH Description: Ademero.ContentCentral.ContentDirector Exit code: 0 Version: 7.5.6919.29662 Modules
| |||||||||||||||
| 1892 | "C:\Users\admin\AppData\Local\Temp\ContentDirector_Setup.exe" | C:\Users\admin\AppData\Local\Temp\ContentDirector_Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Ademero, Inc. Integrity Level: HIGH Description: Setup Launcher Unicode Exit code: 0 Version: 7.5.6919 Modules
| |||||||||||||||
| 2120 | "C:\Program Files\Ademero\ContentDirector\NSS certutil\certutil.exe" -d sql:"C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default" -D -n "Ademero ServerAuth CA" | C:\Program Files\Ademero\ContentDirector\NSS certutil\certutil.exe | — | Ademero.ContentCentral.ContentDirector.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 255 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Ademero\ContentDirector\Ademero.ContentCentral.ContentDirector.exe" -SetRunAtWindowsStartup | C:\Program Files\Ademero\ContentDirector\Ademero.ContentCentral.ContentDirector.exe | msiexec.exe | ||||||||||||
User: admin Company: Ademero, Inc. Integrity Level: HIGH Description: Ademero.ContentCentral.ContentDirector Exit code: 0 Version: 7.5.6919.29662 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Ademero\ContentDirector\NSS certutil\certutil.exe" -d sql:"C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default" -A -t "C,c,c" -n "Ademero ServerAuth CA" -i "C:\Program Files\Ademero\ContentDirector\certificates\AdemeroServerAuthCA.crt" | C:\Program Files\Ademero\ContentDirector\NSS certutil\certutil.exe | — | Ademero.ContentCentral.ContentDirector.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 255 Modules
| |||||||||||||||
Total events
831
Read events
490
Write events
329
Delete events
12
Modification events
| (PID) Process: | (3132) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 3C0C00005021EE843FCDD501 | |||
| (PID) Process: | (3132) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: B4D56B02D38BD2B648BB243E2E4957DC2A97F4CA071D491A4861D8FB7FFF0692 | |||
| (PID) Process: | (3132) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\InProgress |
| Operation: | write | Name: | |
Value: C:\Windows\Installer\3a0016.ipi | |||
| (PID) Process: | (3132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Folders |
| Operation: | write | Name: | C:\Config.Msi\ |
Value: | |||
| (PID) Process: | (3132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\3a0017.rbs |
Value: 30788927 | |||
| (PID) Process: | (3132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\Rollback\Scripts |
| Operation: | write | Name: | C:\Config.Msi\3a0017.rbsLow |
Value: 2366288608 | |||
| (PID) Process: | (3132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\Ademero\ContentDirector\Ademero.ContentCentral.ContentDirector.exe |
Value: 1 | |||
| (PID) Process: | (3132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Components\15D72EB4A2B8F1B44AADD4A0BF1AF2D6 |
| Operation: | write | Name: | A387D9ECA1D84324EA6D8A3BCF95809B |
Value: C?\Program Files\Ademero\ContentDirector\Ademero.ContentCentral.ContentDirector.exe | |||
| (PID) Process: | (3132) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Program Files\Ademero\ContentDirector\ar-SA\Ademero.ContentCentral.ContentDirector.resources.dll |
Value: 1 | |||
Executable files
23
Suspicious files
19
Text files
17
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1892 | ContentDirector_Setup.exe | C:\Users\admin\AppData\Local\Temp\~B7C1.tmp | — | |
MD5:— | SHA256:— | |||
| 1892 | ContentDirector_Setup.exe | C:\Users\admin\AppData\Local\Temp\~B7C2.tmp | — | |
MD5:— | SHA256:— | |||
| 4052 | MSIEXEC.EXE | C:\Users\admin\AppData\Local\Temp\MSICD4D.tmp | — | |
MD5:— | SHA256:— | |||
| 3132 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF380BEA0DBB54824C.TMP | — | |
MD5:— | SHA256:— | |||
| 1892 | ContentDirector_Setup.exe | C:\Users\admin\AppData\Local\Temp\{6333A508-8282-4581-9F81-5111FFB2F339}\_ISMSIDEL.INI | text | |
MD5:— | SHA256:— | |||
| 1892 | ContentDirector_Setup.exe | C:\Users\admin\AppData\Local\Temp\{6333A508-8282-4581-9F81-5111FFB2F339}\Setup.INI | text | |
MD5:— | SHA256:— | |||
| 1892 | ContentDirector_Setup.exe | C:\Users\admin\AppData\Local\Temp\{6333A508-8282-4581-9F81-5111FFB2F339}\Ademero Content Director.msi | executable | |
MD5:— | SHA256:— | |||
| 3132 | msiexec.exe | C:\Windows\Installer\3a0015.msi | executable | |
MD5:— | SHA256:— | |||
| 3132 | msiexec.exe | C:\Windows\Installer\MSI12E.tmp | binary | |
MD5:— | SHA256:— | |||
| 3132 | msiexec.exe | C:\Program Files\Ademero\ContentDirector\ar-SA\Ademero.ContentCentral.ContentDirector.resources.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report