| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/54d0e7db-3061-48f2-989a-c85489bf9164 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 18:06:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8D817A807BC6236D160299C6F5854AEC |
| SHA1: | AF1E477498070D83DAEB3DF30C2B9206CCEDFB7E |
| SHA256: | 1795B435C805AF3B6EFFB4248B4588D832F224EFC4AC6FA12C1B5335A2F1C26D |
| SSDEEP: | 24576:dsCLse/Mq8mifcsDqpTEXYT4CnA/8zUv4obC0CO6CQYXMVyXJ5STK052zjMZSU:j1/LLuNqpT/E8zUv4a6CQki8mZ52HK |
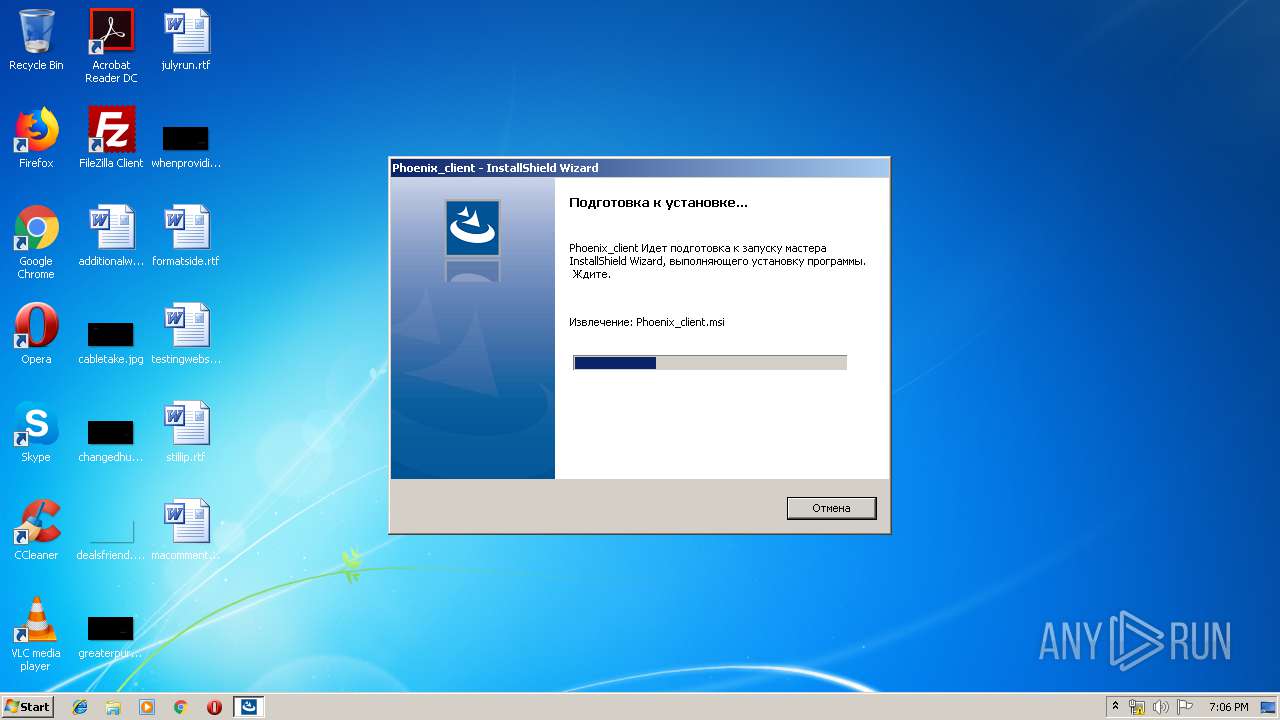
MALICIOUS
Changes the autorun value in the registry
- setup.exe (PID: 2340)
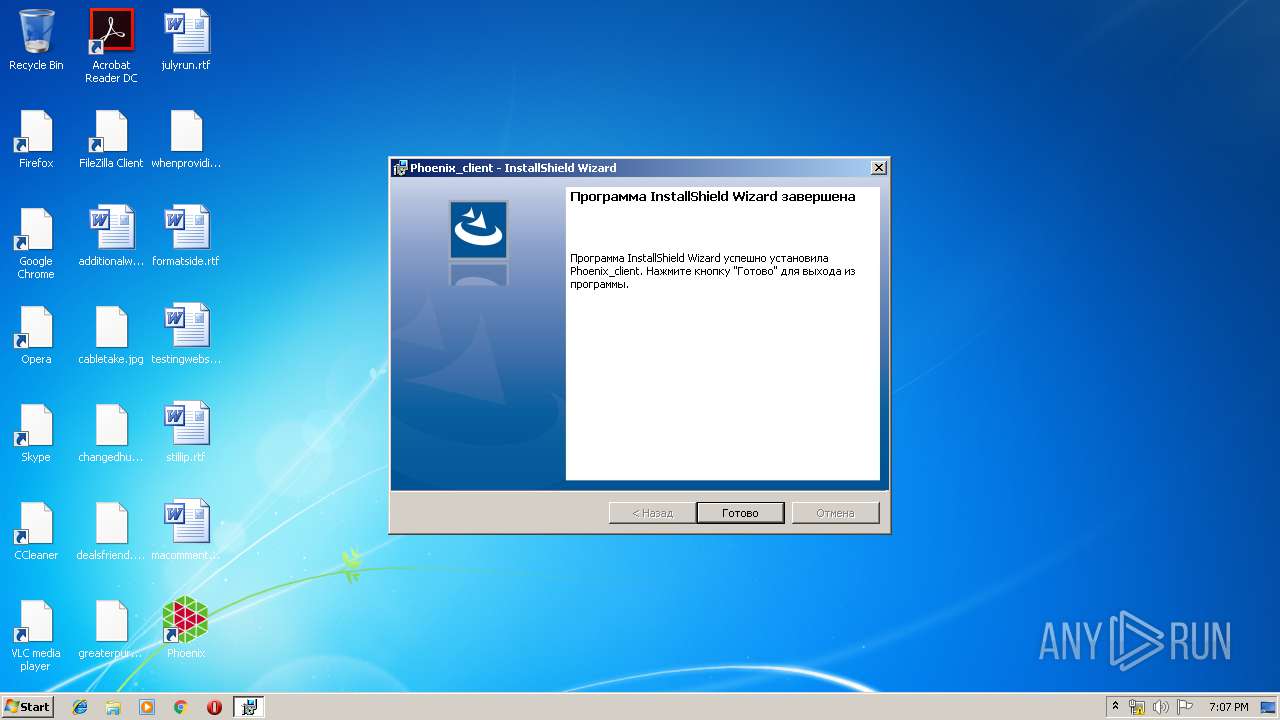
Application was dropped or rewritten from another process
- Phoenix_client.exe (PID: 2600)
Loads dropped or rewritten executable
- Phoenix_client.exe (PID: 2600)
SUSPICIOUS
Starts itself from another location
- setup.exe (PID: 3948)
- setup.exe (PID: 2156)
Executable content was dropped or overwritten
- setup.exe (PID: 3948)
- setup.exe (PID: 2156)
- setup.exe (PID: 2340)
- msiexec.exe (PID: 2188)
Application launched itself
- setup.exe (PID: 2340)
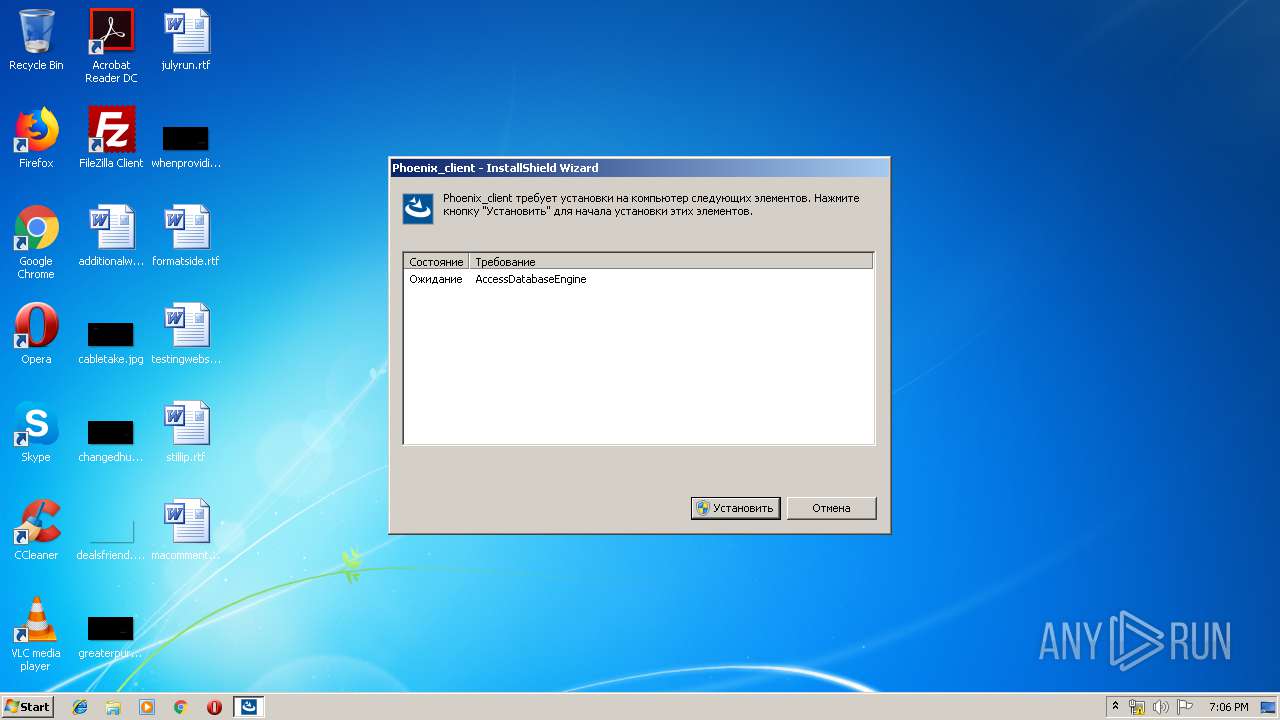
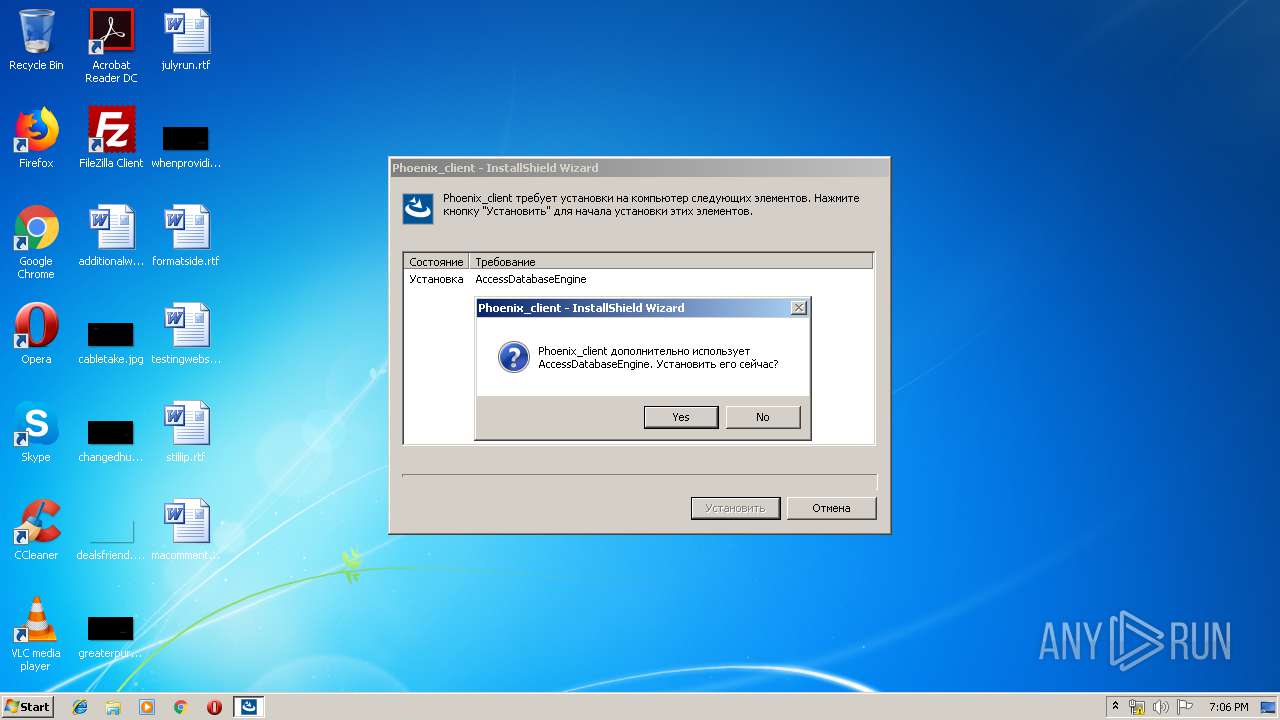
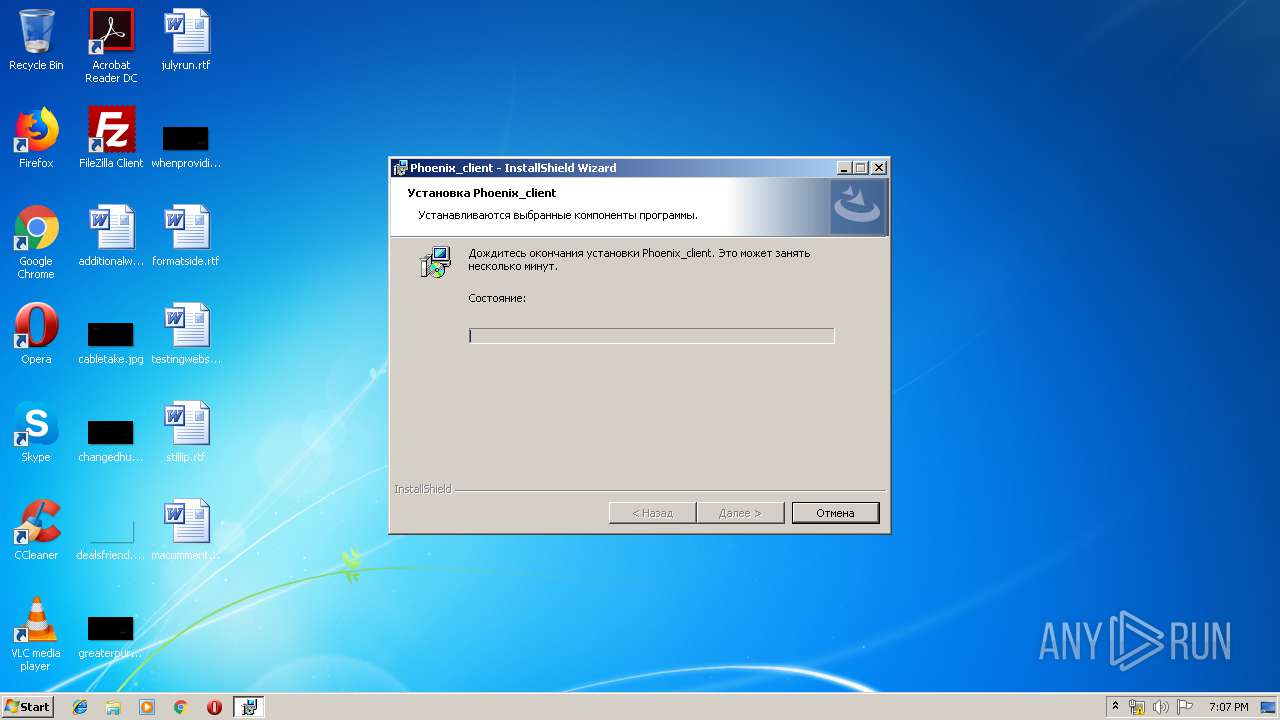
Starts Microsoft Installer
- setup.exe (PID: 2340)
INFO
Dropped object may contain Bitcoin addresses
- setup.exe (PID: 2340)
- setup.exe (PID: 4060)
Searches for installed software
- msiexec.exe (PID: 2188)
Low-level read access rights to disk partition
- vssvc.exe (PID: 680)
Changes settings of System certificates
- DrvInst.exe (PID: 3332)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3332)
Creates files in the program directory
- msiexec.exe (PID: 2188)
Creates a software uninstall entry
- msiexec.exe (PID: 2188)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:14 23:32:08+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 608256 |
| InitializedDataSize: | 677376 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5757a |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
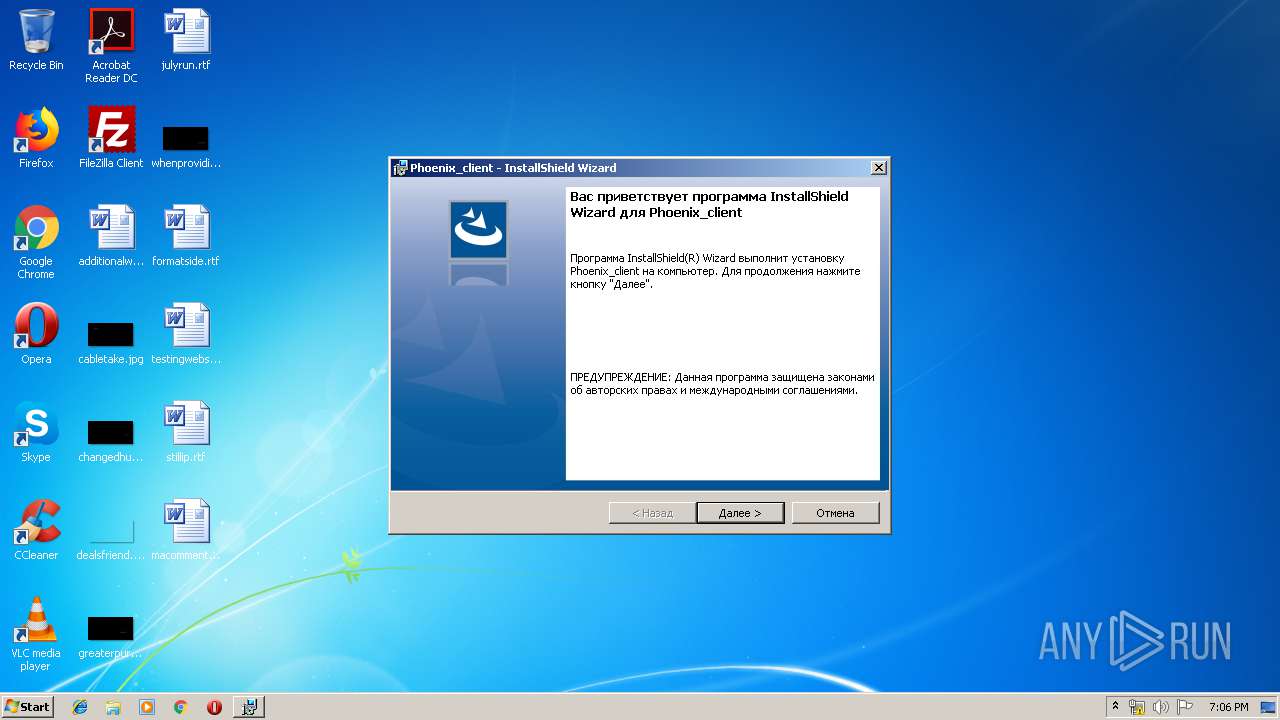
| CompanyName: | Українська біржа |
| FileDescription: | Setup Launcher Unicode |
| FileVersion: | 1.00.0000 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (c) 2018 Flexera. All Rights Reserved. |
| OriginalFileName: | InstallShield Setup.exe |
| ProductName: | Phoenix_client |
| ProductVersion: | 1.00.0000 |
| InternalBuildNumber: | 182945 |
| ISInternalVersion: | 24.0.464 |
| ISInternalDescription: | Setup Launcher Unicode |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-May-2018 21:32:08 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Українська біржа |
| FileDescription: | Setup Launcher Unicode |
| FileVersion: | 1.00.0000 |
| InternalName: | Setup |
| LegalCopyright: | Copyright (c) 2018 Flexera. All Rights Reserved. |
| OriginalFilename: | InstallShield Setup.exe |
| ProductName: | Phoenix_client |
| ProductVersion: | 1.00.0000 |
| Internal Build Number: | 182945 |
| ISInternalVersion: | 24.0.464 |
| ISInternalDescription: | Setup Launcher Unicode |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 14-May-2018 21:32:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00094669 | 0x00094800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.53712 |
.rdata | 0x00096000 | 0x0002E310 | 0x0002E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.58768 |
.data | 0x000C5000 | 0x0000AD90 | 0x00002800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.41589 |
.rsrc | 0x000D0000 | 0x0004CC90 | 0x0004CE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.56164 |
.reloc | 0x0011D000 | 0x00027B46 | 0x00027C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 2.4772 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07176 | 640 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.31163 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 2.94006 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 3.22977 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.5927 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
69 | 3.10251 | 352 | Latin 1 / Western European | English - United States | RT_STRING |
70 | 3.14661 | 574 | Latin 1 / Western European | English - United States | RT_STRING |
71 | 3.25053 | 888 | Latin 1 / Western European | English - United States | RT_STRING |
72 | 3.13124 | 594 | Latin 1 / Western European | English - United States | RT_STRING |
73 | 3.06893 | 500 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
RPCRT4.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
VERSION.dll (delay-loaded) |
Total processes
48
Monitored processes
11
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 680 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2156 | "C:\Users\admin\AppData\Local\Temp\{CAABA4B1-1815-40C0-90EB-6ED6048032AB}\setup.exe" /QC:\Users\admin\AppData\Local\Temp\setup.exe /l1049 /runprerequisites"" | C:\Users\admin\AppData\Local\Temp\{CAABA4B1-1815-40C0-90EB-6ED6048032AB}\setup.exe | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2188 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2340 | C:\Users\admin\AppData\Local\Temp\{CAABA4B1-1815-40C0-90EB-6ED6048032AB}\setup.exe /q"C:\Users\admin\AppData\Local\Temp\setup.exe" /tempdisk1folder"C:\Users\admin\AppData\Local\Temp\{CAABA4B1-1815-40C0-90EB-6ED6048032AB}" /IS_temp | C:\Users\admin\AppData\Local\Temp\{CAABA4B1-1815-40C0-90EB-6ED6048032AB}\setup.exe | setup.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
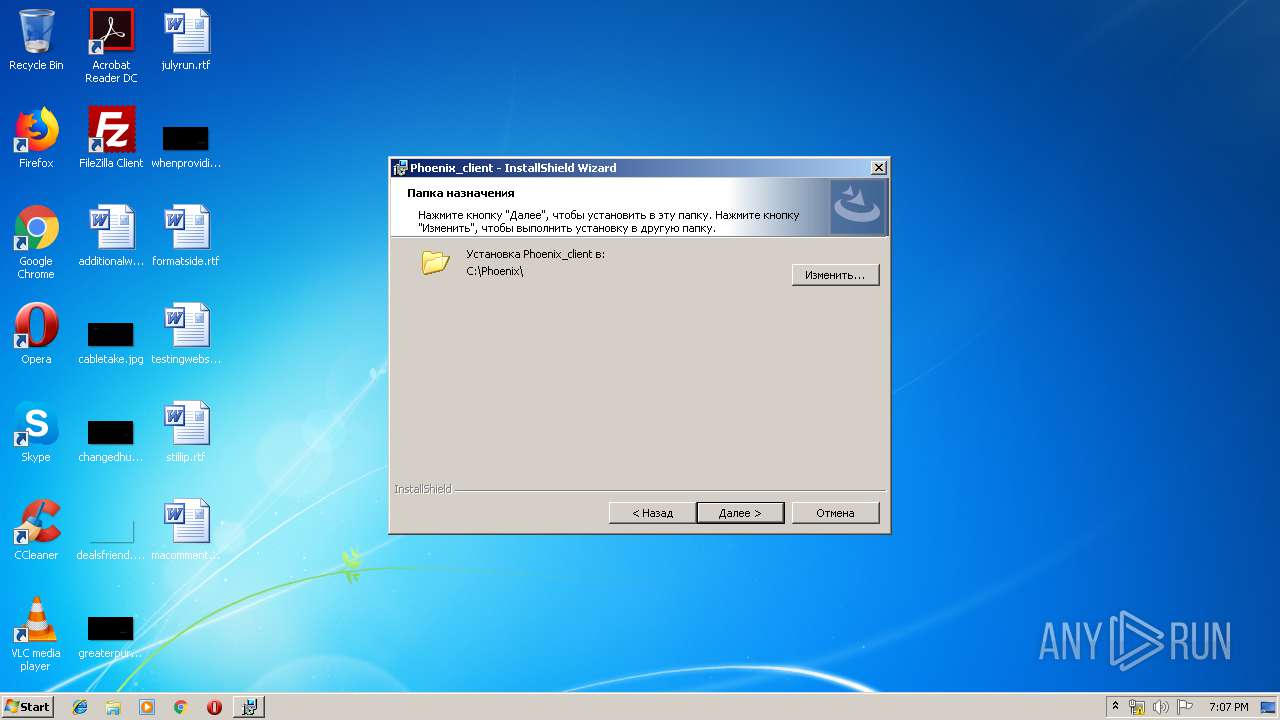
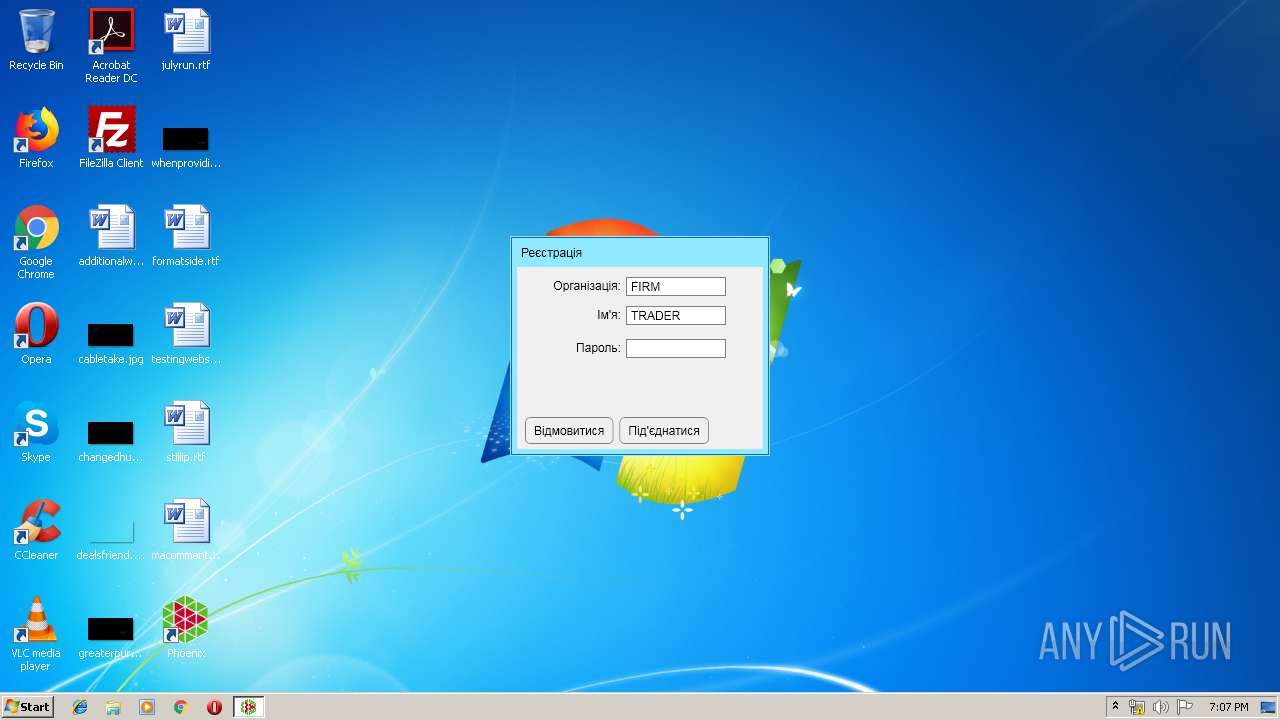
| 2600 | "C:\Phoenix\Phoenix_client.exe" | C:\Phoenix\Phoenix_client.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Phoenix client Exit code: 0 Version: 1.0.15.36 Modules
| |||||||||||||||
| 2684 | "C:\Windows\system32\MSIEXEC.EXE" /i "C:\Users\admin\AppData\Local\Temp\{CAABA4B1-1815-40C0-90EB-6ED6048032AB}\Phoenix_client.msi" SETUPEXEDIR="C:\Users\admin\AppData\Local\Temp" SETUPEXENAME="setup.exe" | C:\Windows\system32\MSIEXEC.EXE | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3332 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "00000560" "00000544" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3932 | C:\Windows\explorer.exe | C:\Windows\explorer.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3948 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
976
Read events
707
Write events
253
Delete events
16
Modification events
| (PID) Process: | (2340) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion |
| Operation: | write | Name: | %IS_PREREQ%-Phoenix_client |
Value: -1 | |||
| (PID) Process: | (2340) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | ISSetupPrerequisistes |
Value: "C:\Users\admin\AppData\Local\Temp\setup.exe" | |||
| (PID) Process: | (4060) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion |
| Operation: | delete value | Name: | %IS_PREREQ%-Phoenix_client |
Value: -1 | |||
| (PID) Process: | (2340) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | delete value | Name: | ISSetupPrerequisistes |
Value: "C:\Users\admin\AppData\Local\Temp\setup.exe" | |||
| (PID) Process: | (2188) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 40000000000000000A06B05BFFF9D4018C08000038090000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2188) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 40000000000000000A06B05BFFF9D4018C08000038090000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2188) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (2188) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000006027335CFFF9D4018C08000038090000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2188) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 400000000000000014EC375CFFF9D4018C08000084010000E8030000010000000000000000000000A98BB05C915E5F43BD02EE62B09A4A040000000000000000 | |||
| (PID) Process: | (680) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000F225525CFFF9D401A802000098060000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
10
Suspicious files
8
Text files
165
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3948 | setup.exe | C:\Users\admin\AppData\Local\Temp\~6C71.tmp | — | |
MD5:— | SHA256:— | |||
| 3948 | setup.exe | C:\Users\admin\AppData\Local\Temp\~6C72.tmp | — | |
MD5:— | SHA256:— | |||
| 3948 | setup.exe | C:\Users\admin\AppData\Local\Temp\~6C83.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | setup.exe | C:\Users\admin\AppData\Local\Temp\~6E07.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | setup.exe | C:\Users\admin\AppData\Local\Temp\~6E08.tmp | — | |
MD5:— | SHA256:— | |||
| 2340 | setup.exe | C:\Users\admin\AppData\Local\Temp\_is6E29..dll | — | |
MD5:— | SHA256:— | |||
| 2340 | setup.exe | C:\Users\admin\AppData\Local\Temp\_is6E78..dll | — | |
MD5:— | SHA256:— | |||
| 2340 | setup.exe | C:\Users\admin\AppData\Local\Temp\_is6EA8..dll | — | |
MD5:— | SHA256:— | |||
| 2340 | setup.exe | C:\Users\admin\AppData\Local\Temp\_is6ED8..dll | — | |
MD5:— | SHA256:— | |||
| 2156 | setup.exe | C:\Users\admin\AppData\Local\Temp\~7FBB.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
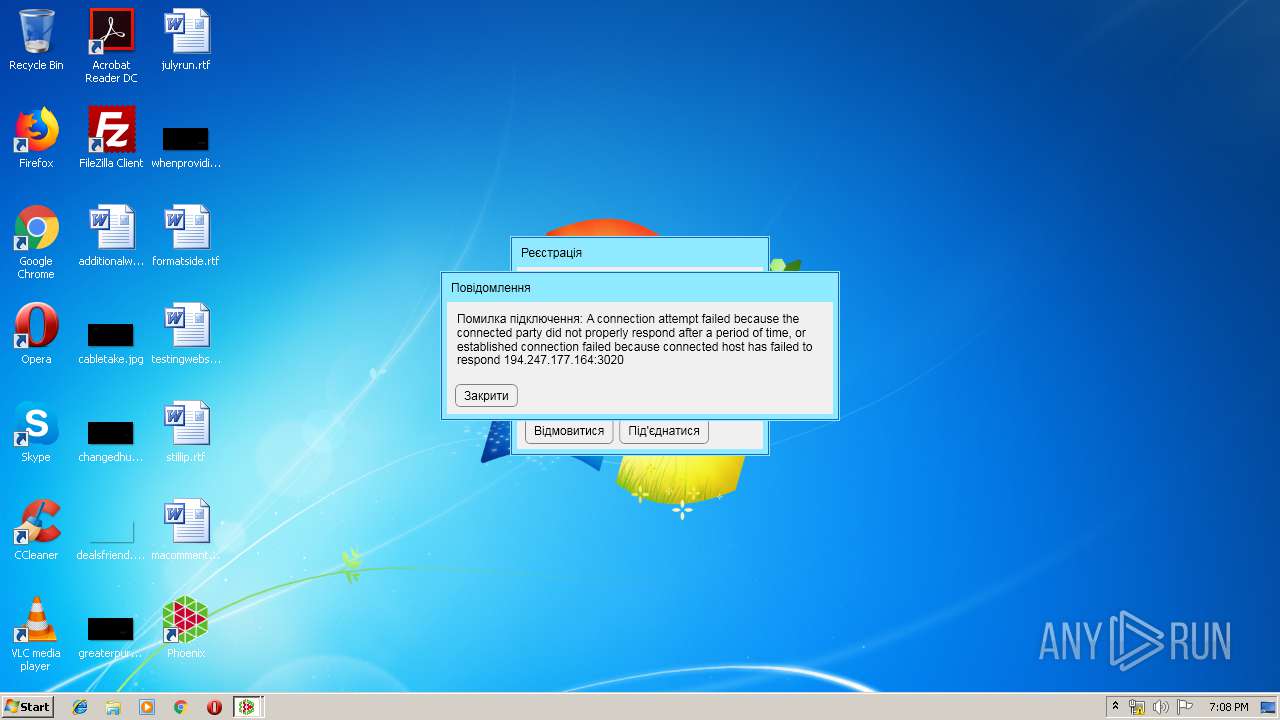
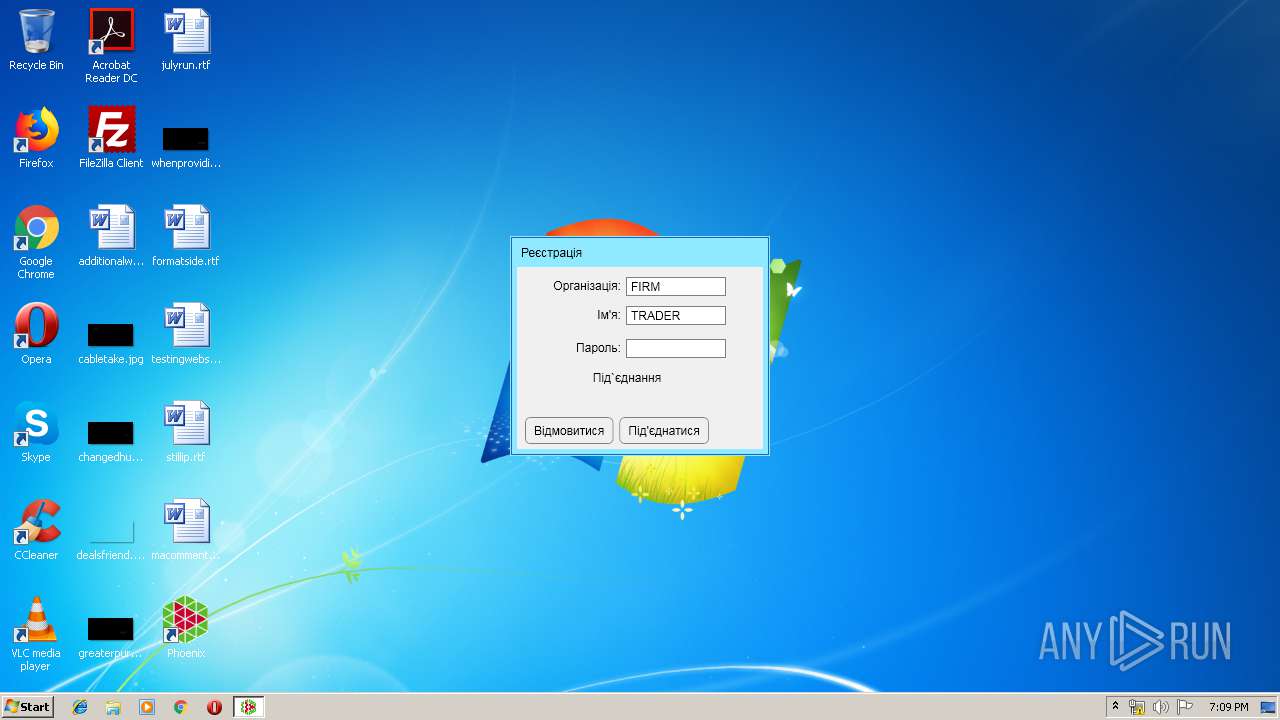
2600 | Phoenix_client.exe | 194.247.177.164:3020 | — | VAT Ukrainian Exchange | UA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |