| File name: | Cameyo.exe |
| Full analysis: | https://app.any.run/tasks/cda6c8f1-bad6-4a51-9541-3d3a9fc6ce13 |
| Verdict: | Malicious activity |
| Analysis date: | July 21, 2018, 19:57:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 15E3D8F6CA653D345B9061DC3E7B9981 |
| SHA1: | 9508A1F04408B54F080BC26F071AD2C3C3DF7910 |
| SHA256: | 1787EEAD7D6BB0D581139B941474E8C0A5B3C182EF653CAC7D527B64D82D2CEF |
| SSDEEP: | 393216:7k3cqAd420KGS35sHH8Edk1hbZ5NiQcP4LkEl9/AtO/p1h:EOhsnkJWQcBEjAtON |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- Cameyo.exe (PID: 1552)
Creates files in the user directory
- Cameyo.exe (PID: 1552)
INFO
Dropped object may contain URL's
- Cameyo.exe (PID: 1552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:10:18 08:20:34+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 1012224 |
| InitializedDataSize: | 1077248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcb50c |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileDescription: | Cameyo.Player |
| FileVersion: | 1.0.0.0 |
| InternalName: | WinPlayer.exe |
| LegalCopyright: | Copyright © 2015 |
| OriginalFileName: | WinPlayer.exe |
| ProductName: | Cameyo.Player |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Oct-2016 06:20:34 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Cameyo (cameyo.com) |
| FileDescription: | Loader |
| FileVersion: | 3, 1, 1446, 0 |
| InternalName: | Loader |
| LegalCopyright: | (c) Cameyo. All rights reserved. |
| OriginalFilename: | Loader.exe |
| ProductName: | Cameyo Application Virtualization |
| ProductVersion: | 3, 1, 1446, 0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 18-Oct-2016 06:20:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00020F70 | 0x00021000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.58829 |
.text | 0x00022000 | 0x000D6049 | 0x000D6200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64412 |
.rdata | 0x000F9000 | 0x0004425E | 0x00044400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.47604 |
.data | 0x0013E000 | 0x00008A1C | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.71739 |
DATA | 0x00147000 | 0x000014F4 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96373 |
BSS | 0x00149000 | 0x00000761 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0014A000 | 0x000BCE0C | 0x000BD000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.98004 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.02301 | 622 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.47517 | 67624 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.14452 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.34536 | 152104 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 3.6566 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 7.90295 | 9361 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.37939 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 2.99643 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 2.8193 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 2.61271 | 38056 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ACTIVEDS.dll |
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
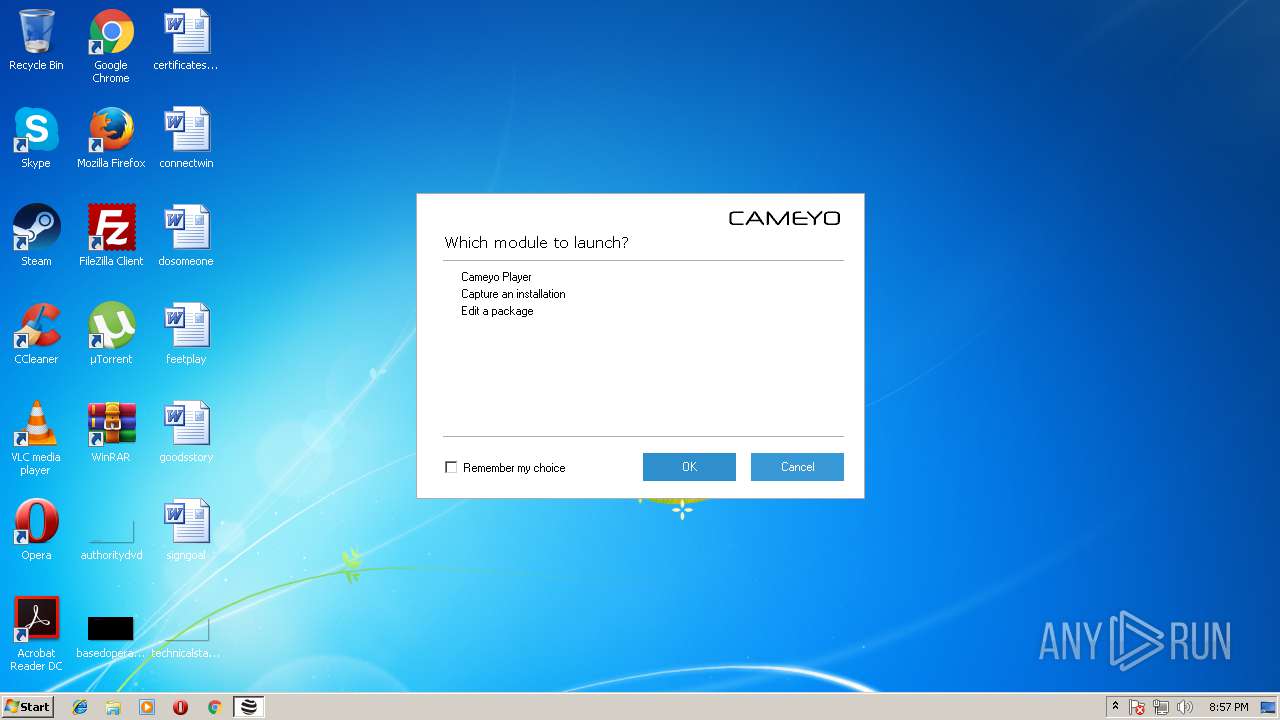
Total processes
31
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1552 | "C:\Users\admin\AppData\Local\Temp\Cameyo.exe" | C:\Users\admin\AppData\Local\Temp\Cameyo.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Cameyo.Player Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
83
Read events
53
Write events
30
Delete events
0
Modification events
| (PID) Process: | (1552) Cameyo.exe | Key: | HKEY_CURRENT_USER\Software\VOS\Cameyo |
| Operation: | write | Name: | BaseDirName |
Value: C:\Users\admin\AppData\Roaming\VOS\Cameyo | |||
| (PID) Process: | (1552) Cameyo.exe | Key: | HKEY_CURRENT_USER\Software\VOS\Cameyo |
| Operation: | write | Name: | CarrierExeName |
Value: C:\Users\admin\AppData\Local\Temp\Cameyo.exe | |||
| (PID) Process: | (1552) Cameyo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Cameyo_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1552) Cameyo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Cameyo_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1552) Cameyo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Cameyo_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1552) Cameyo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Cameyo_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1552) Cameyo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Cameyo_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1552) Cameyo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Cameyo_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1552) Cameyo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Cameyo_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1552) Cameyo.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Cameyo_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
21
Suspicious files
7
Text files
3
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1552 | Cameyo.exe | C:\Users\admin\AppData\Roaming\VOS\Cameyo\EngineStamps\AppVirtDll_Cameyo.dll.20161018-063509.746.stamp | — | |
MD5:— | SHA256:— | |||
| 1552 | Cameyo.exe | C:\Users\admin\AppData\Roaming\VOS\Cameyo\EngineStamps\AppVirtDll64_Cameyo.dll.20161018-063509.748.stamp | — | |
MD5:— | SHA256:— | |||
| 1552 | Cameyo.exe | C:\Users\admin\AppData\Roaming\VOS\Cameyo\EngineStamps\Cameyo.exe.20161018-063509.750.stamp | — | |
MD5:— | SHA256:— | |||
| 1552 | Cameyo.exe | C:\Users\admin\AppData\Roaming\VOS\Cameyo\EngineStamps\Cameyo64.exe.20161018-063509.750.stamp | — | |
MD5:— | SHA256:— | |||
| 1552 | Cameyo.exe | C:\Users\admin\AppData\Roaming\VOS\Cameyo\EngineStamps\VirtFiles.Prog.db.20161018-063518.029.stamp | — | |
MD5:— | SHA256:— | |||
| 1552 | Cameyo.exe | C:\Users\admin\AppData\Roaming\VOS\Cameyo\EngineStamps\SandboxCfg.db.20161018-063512.718.stamp | — | |
MD5:— | SHA256:— | |||
| 1552 | Cameyo.exe | C:\Users\admin\AppData\Roaming\VOS\Cameyo\EngineStamps\VirtReg.Prog.dat.20161018-063513.406.stamp | — | |
MD5:— | SHA256:— | |||
| 1552 | Cameyo.exe | C:\Users\admin\AppData\Roaming\VOS\Cameyo\CHANGES\VirtFiles.db.1916.tmp | — | |
MD5:— | SHA256:— | |||
| 1552 | Cameyo.exe | C:\Users\admin\AppData\Roaming\VOS\Cameyo\VirtReg.Prog.dat | hiv | |
MD5:6D9731B7AF04FBD4FDE4D3C5FF0B998A | SHA256:06172CBB122F8692F685F0DDCF432D982B079923272A38C4DFE7D8341646E12F | |||
| 1552 | Cameyo.exe | C:\Users\admin\AppData\Roaming\VOS\Cameyo\Cameyo64.exe | executable | |
MD5:B11D5663161F0959F196FA45EF941968 | SHA256:88B0351D4F61CC827EF0BED47F747AEE48DE254A7368D449A580732E89AF7147 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
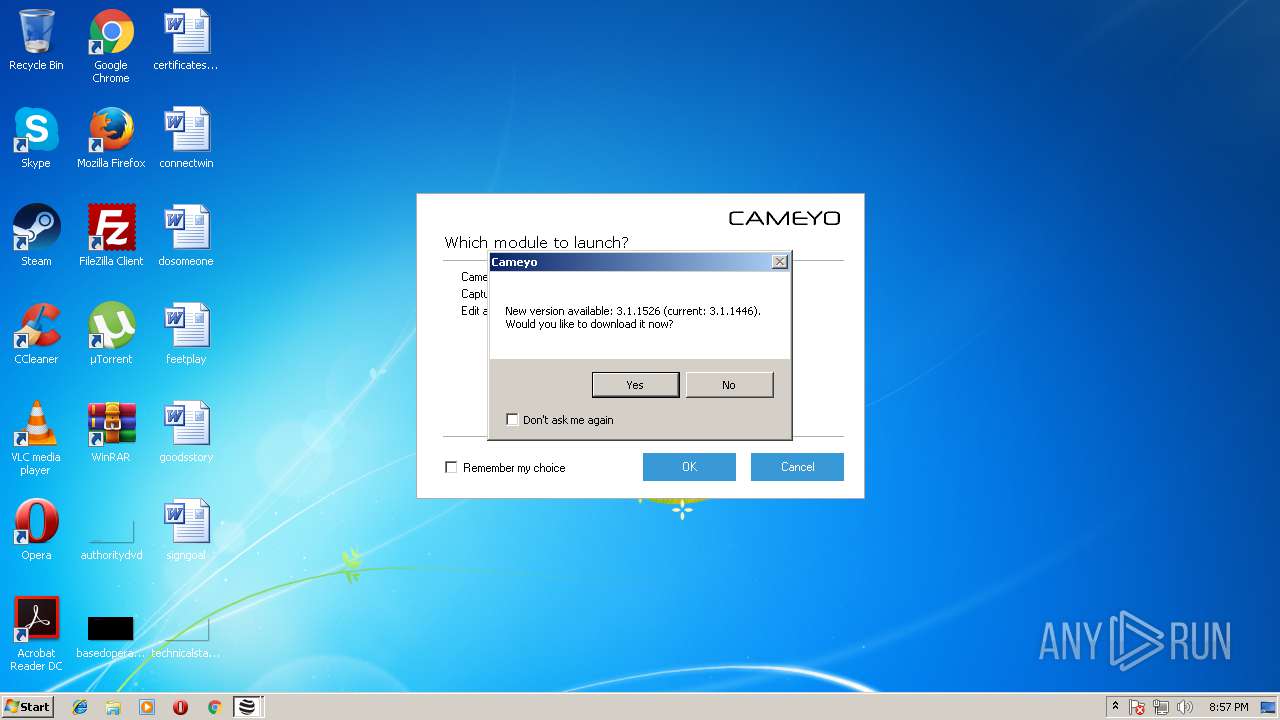
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1552 | Cameyo.exe | 158.69.27.194:443 | online.cameyo.com | OVH SAS | CA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
online.cameyo.com |
| unknown |