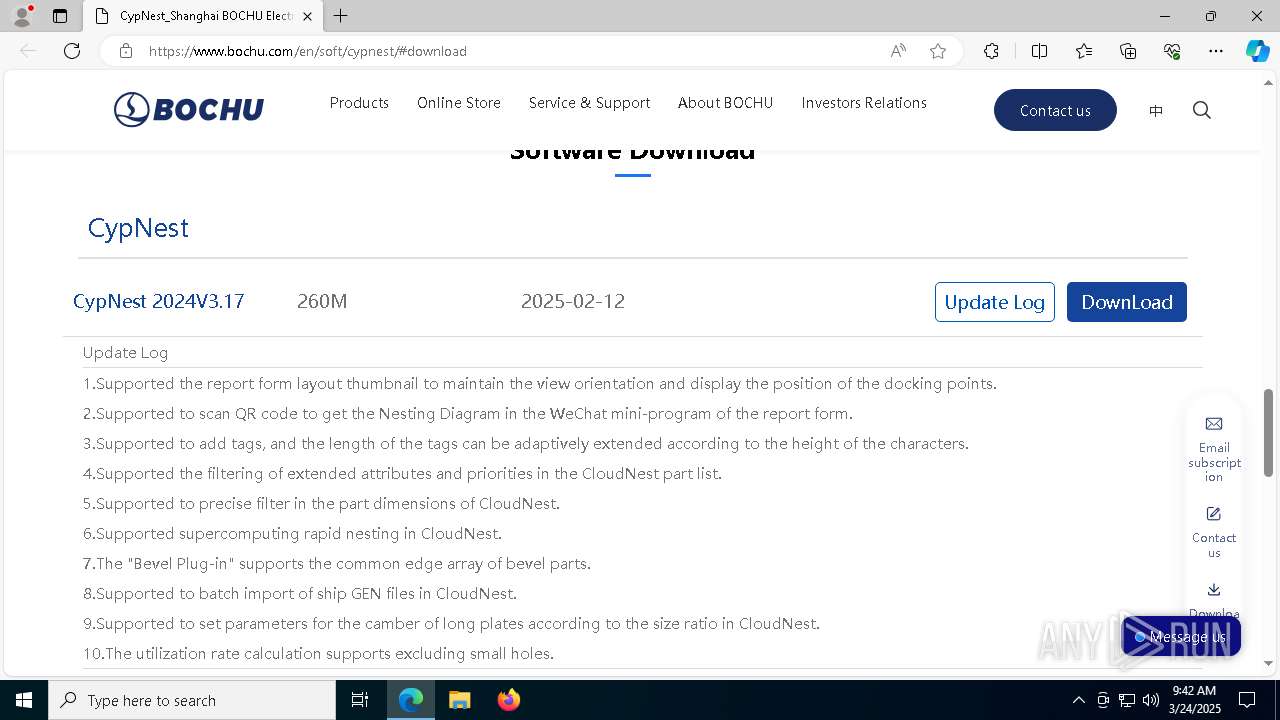
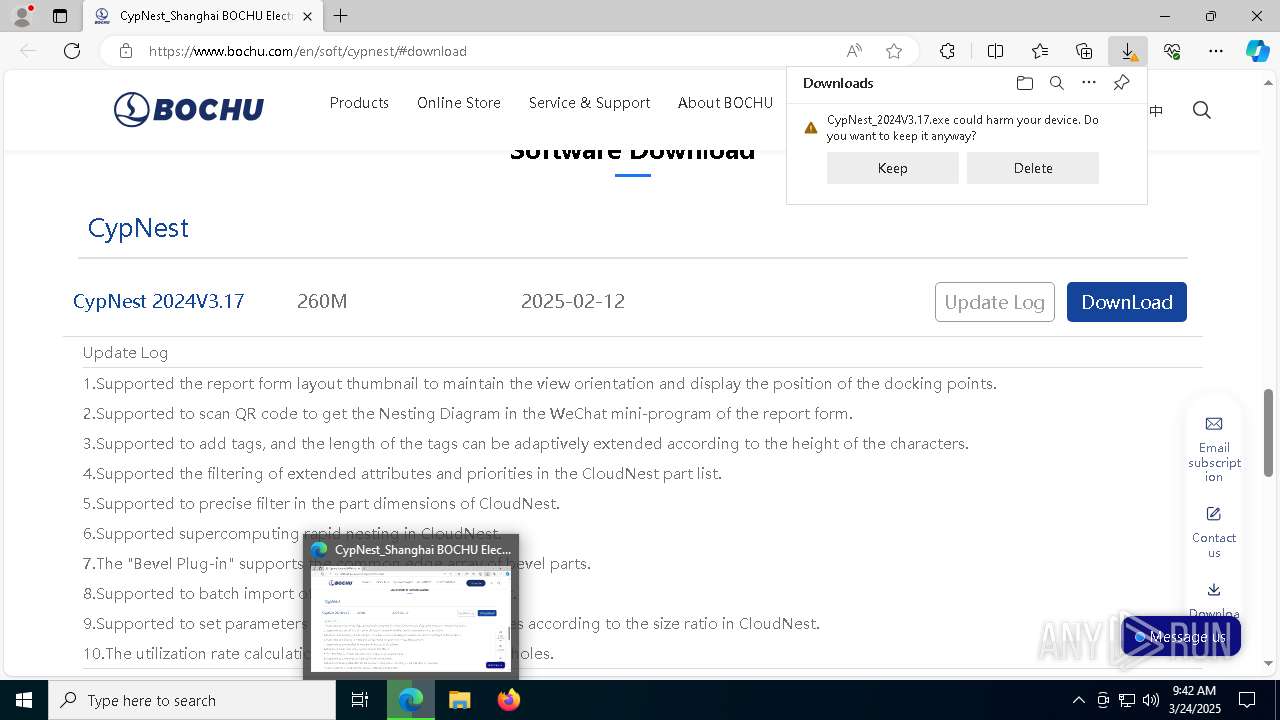
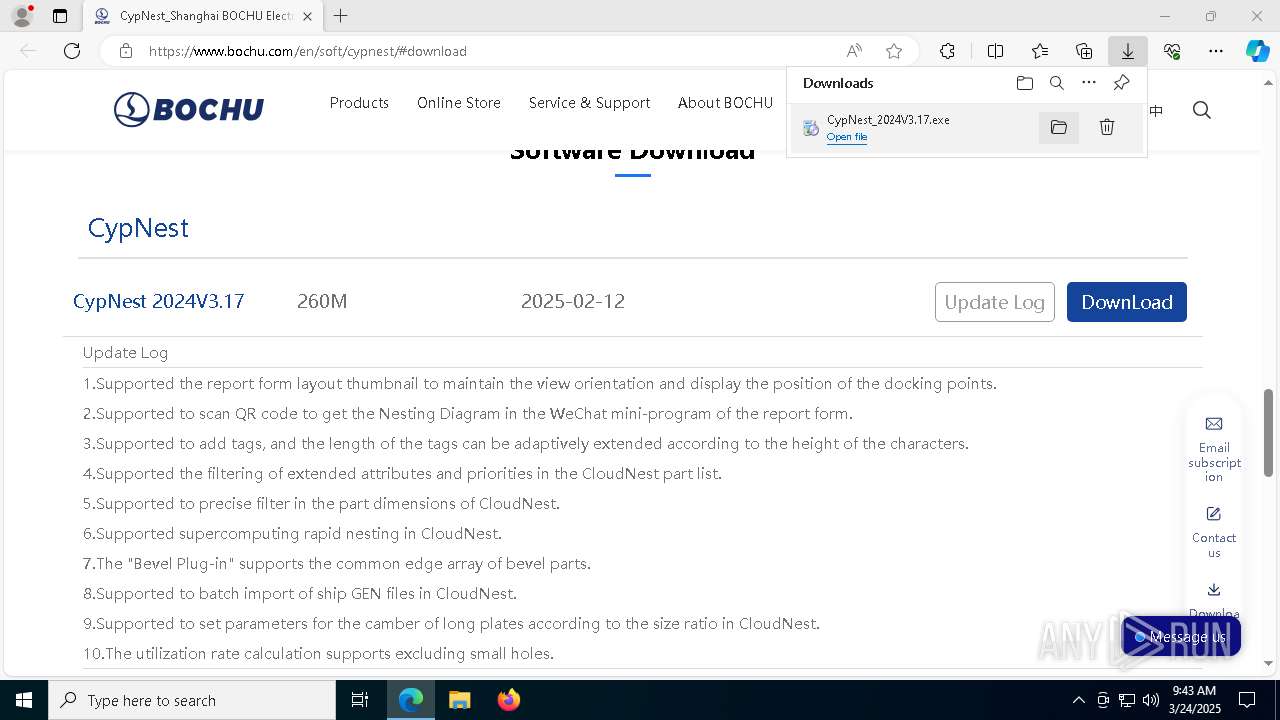
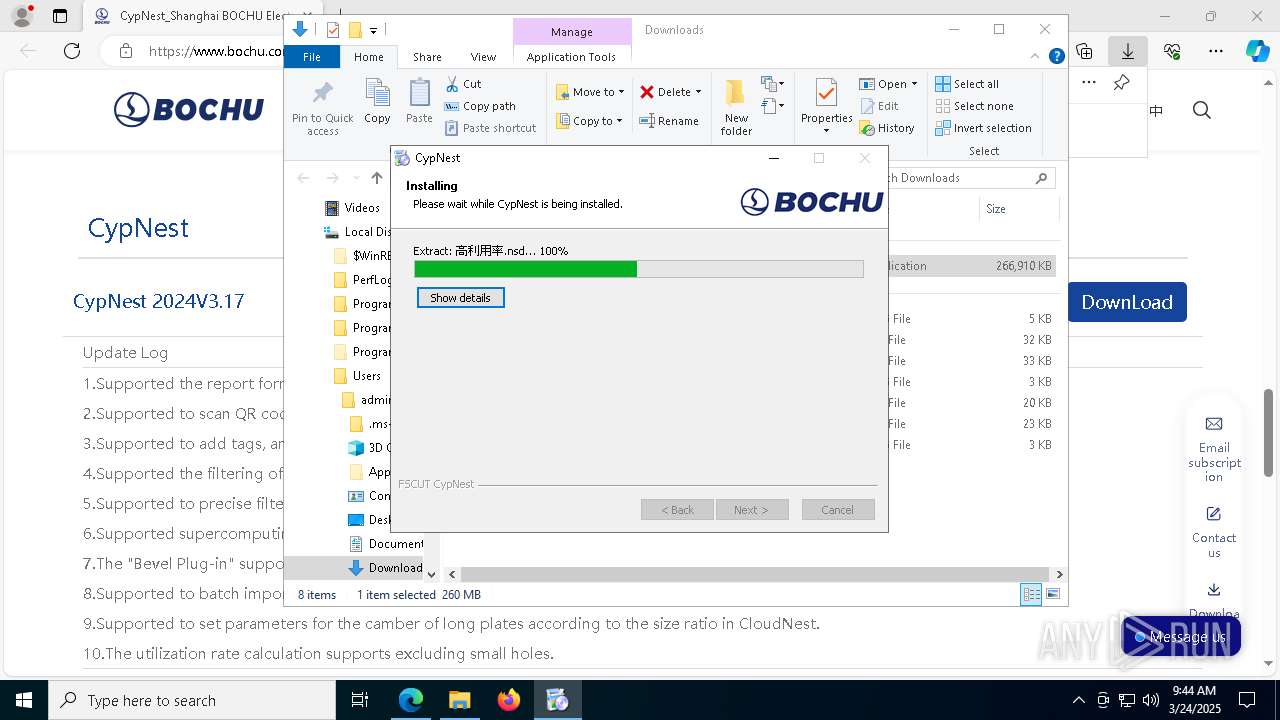
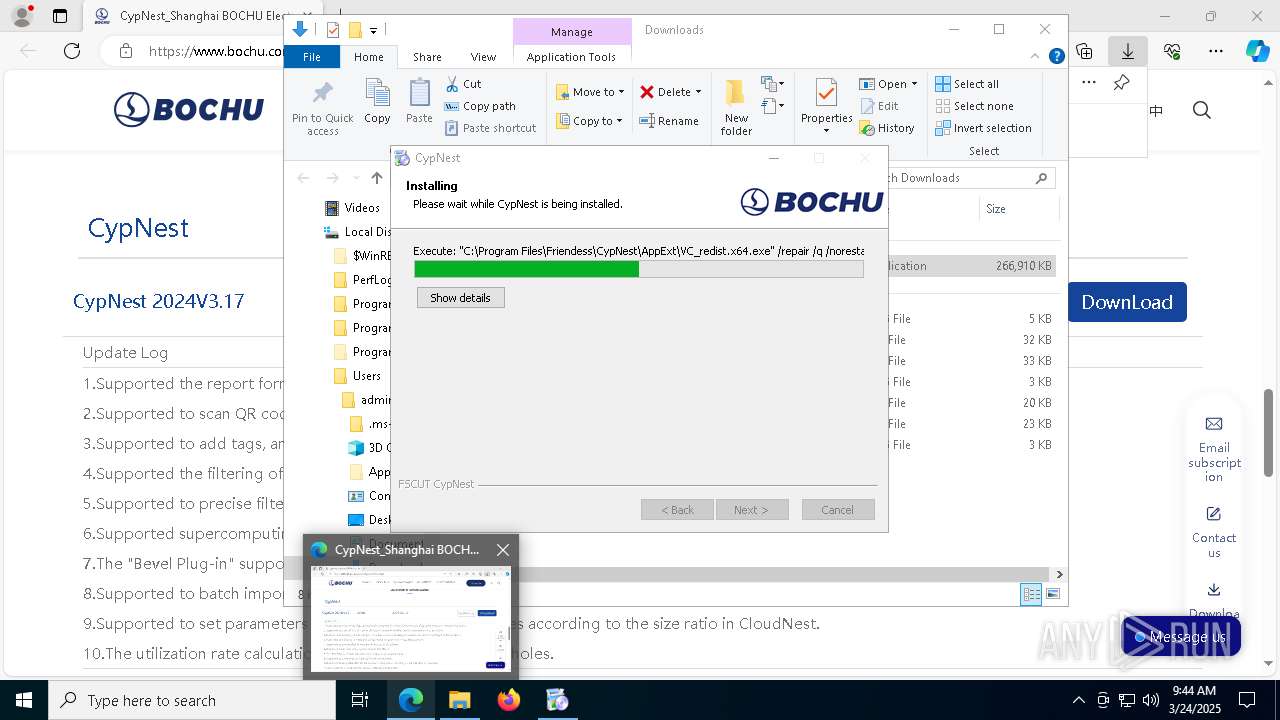
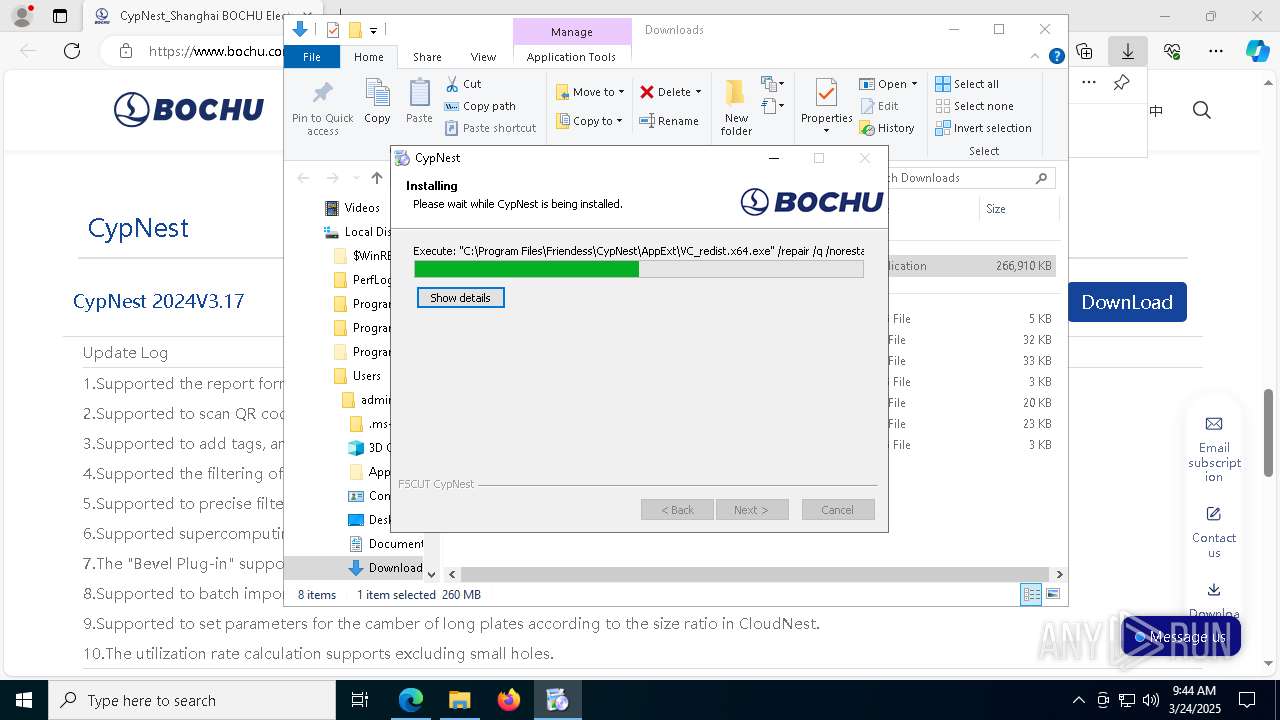
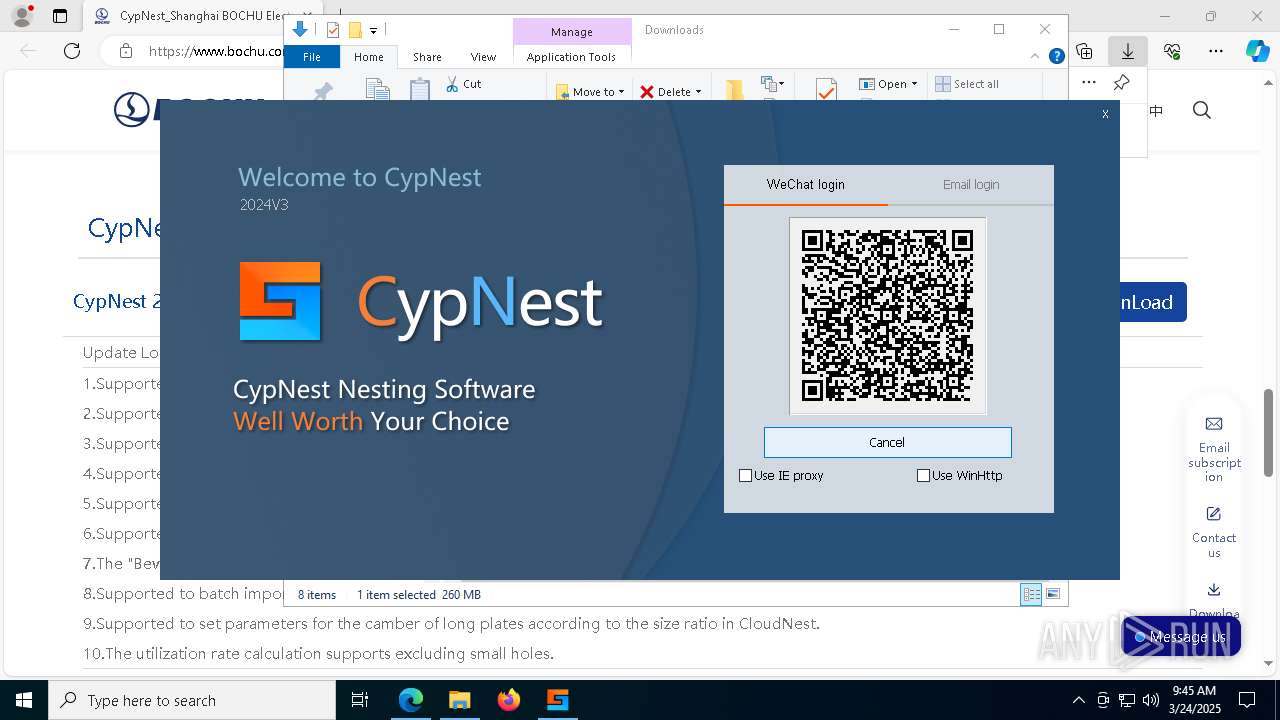
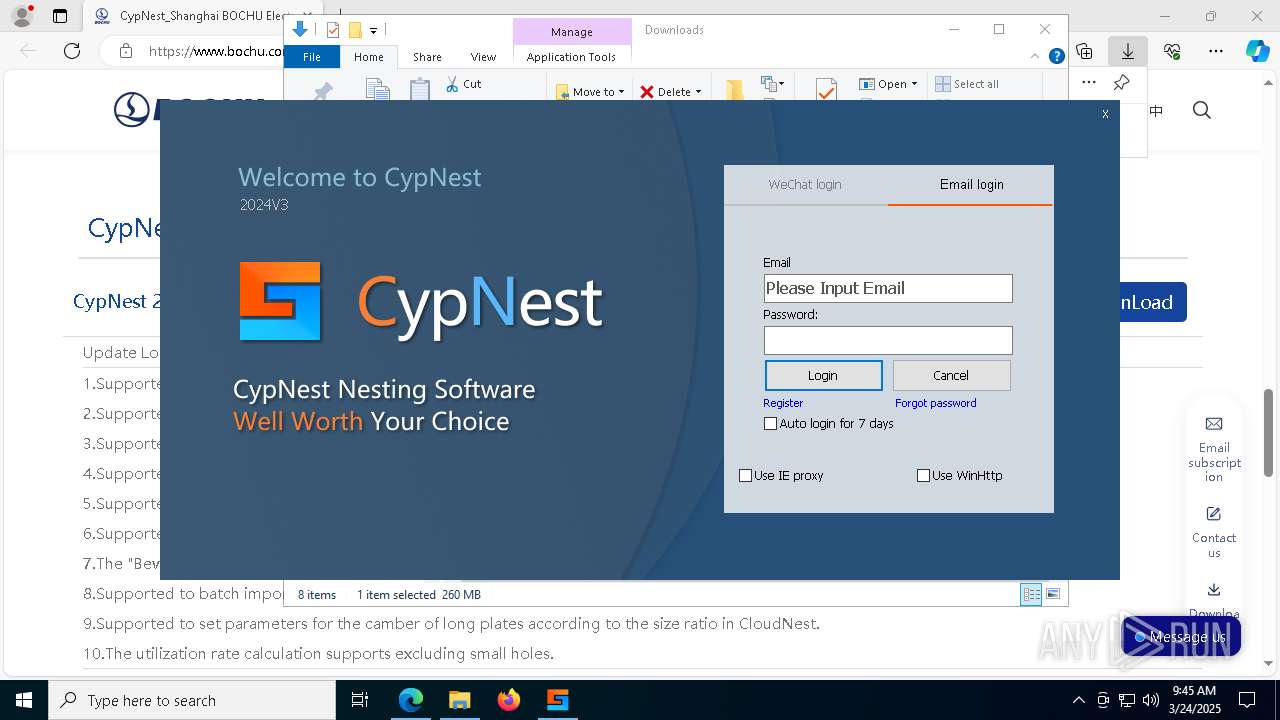
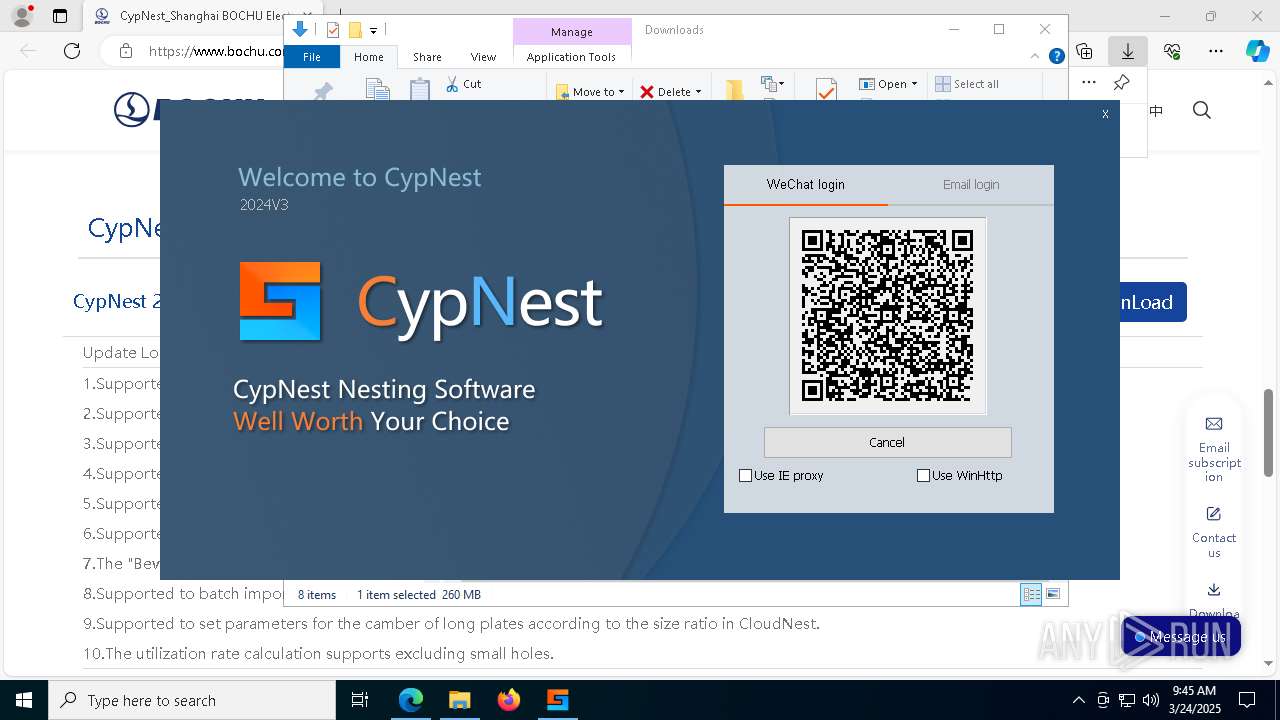
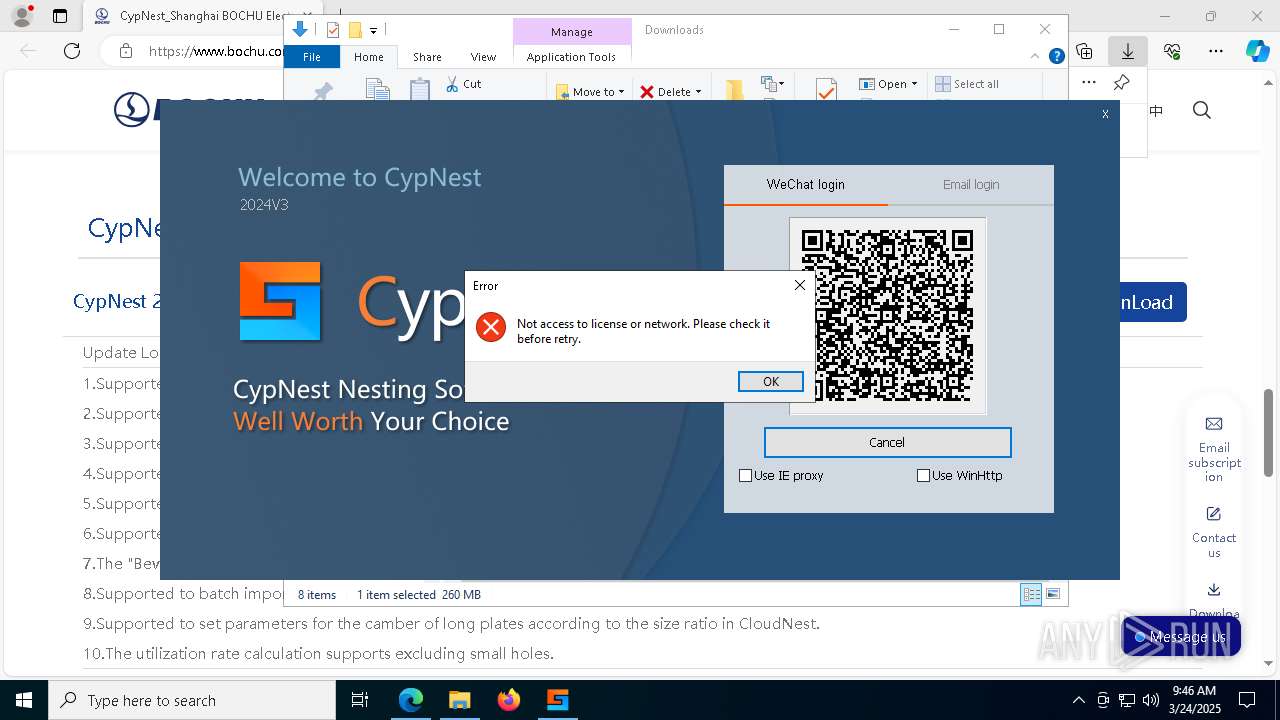
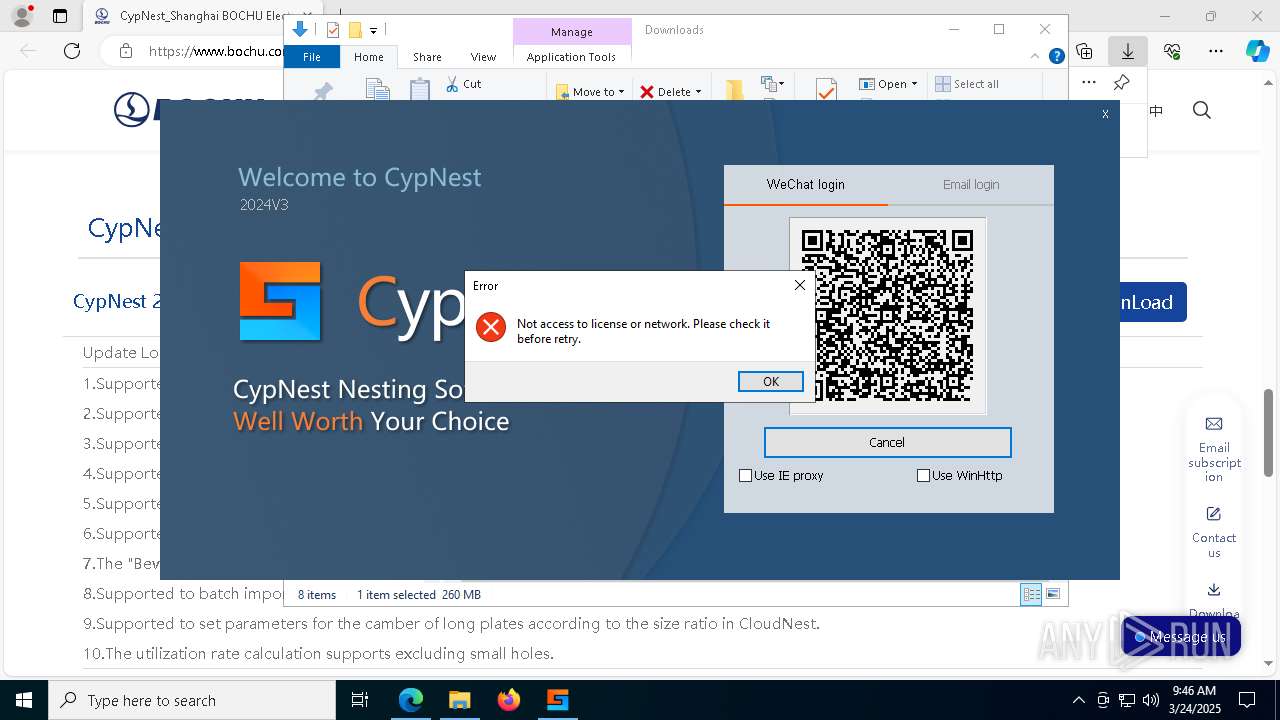
| URL: | https://www.bochu.com/en/soft/cypnest/#download |
| Full analysis: | https://app.any.run/tasks/75973b47-6b2d-417f-bf1e-ffc971a190ca |
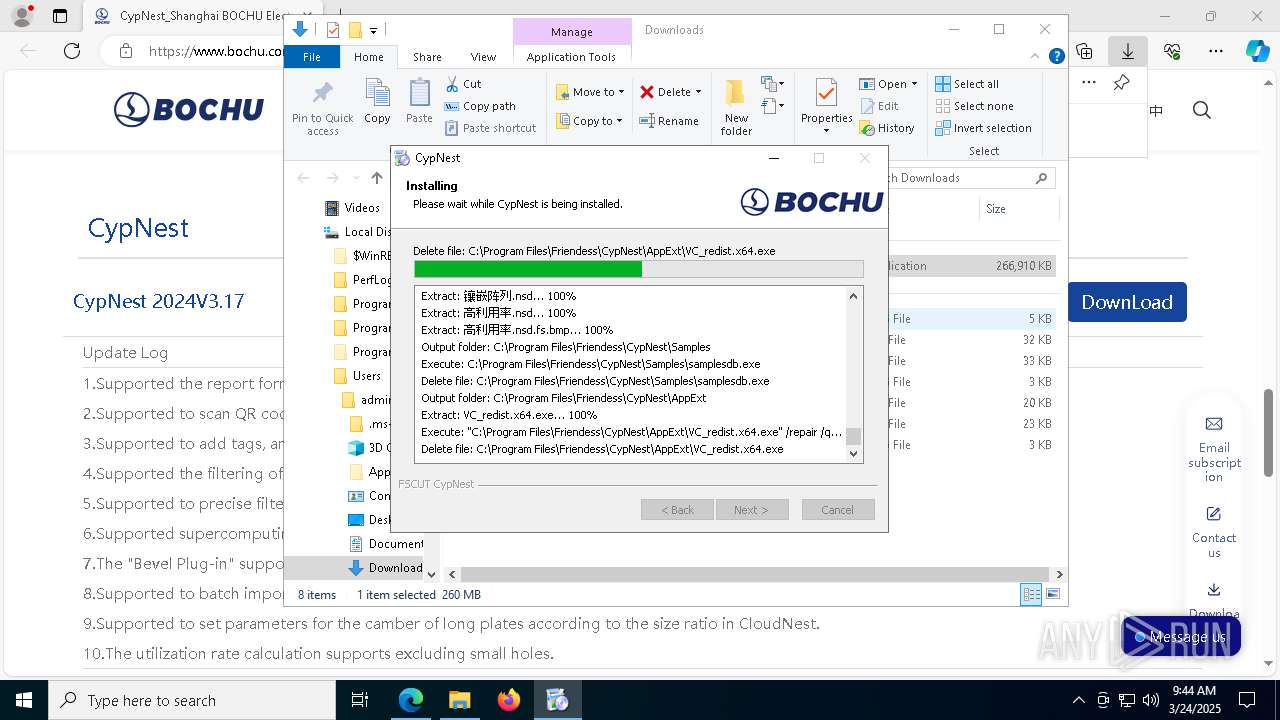
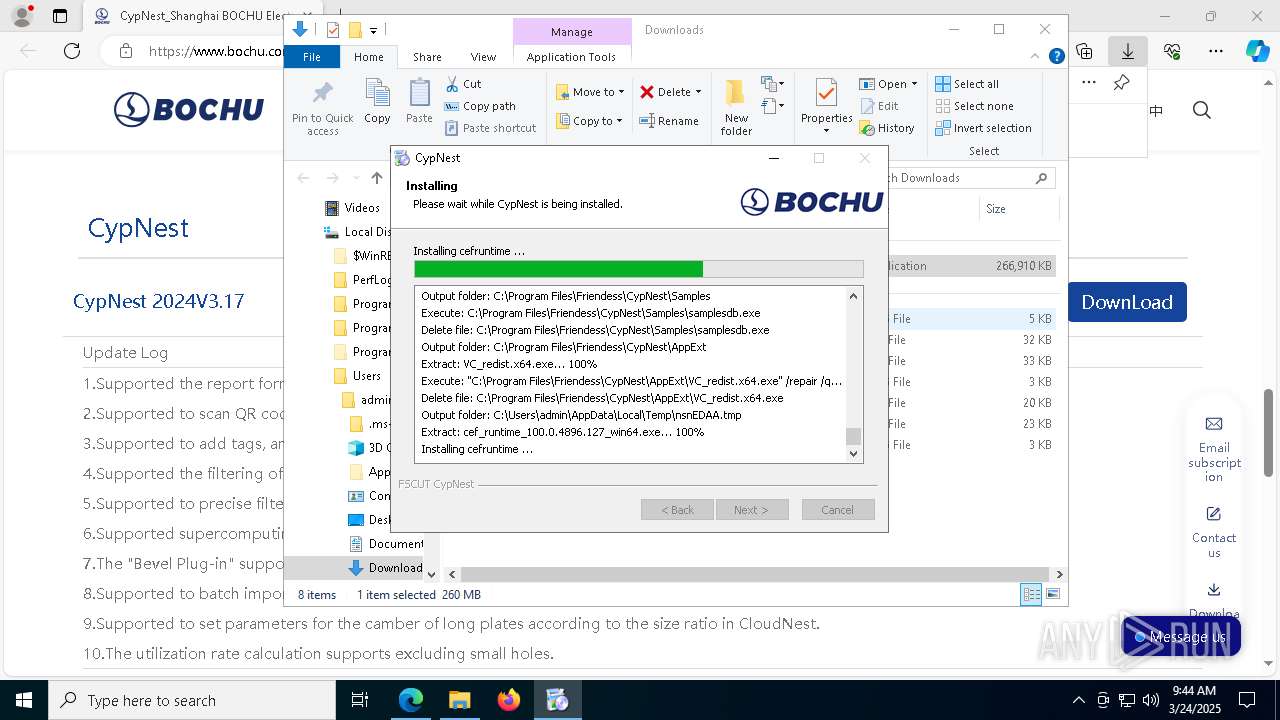
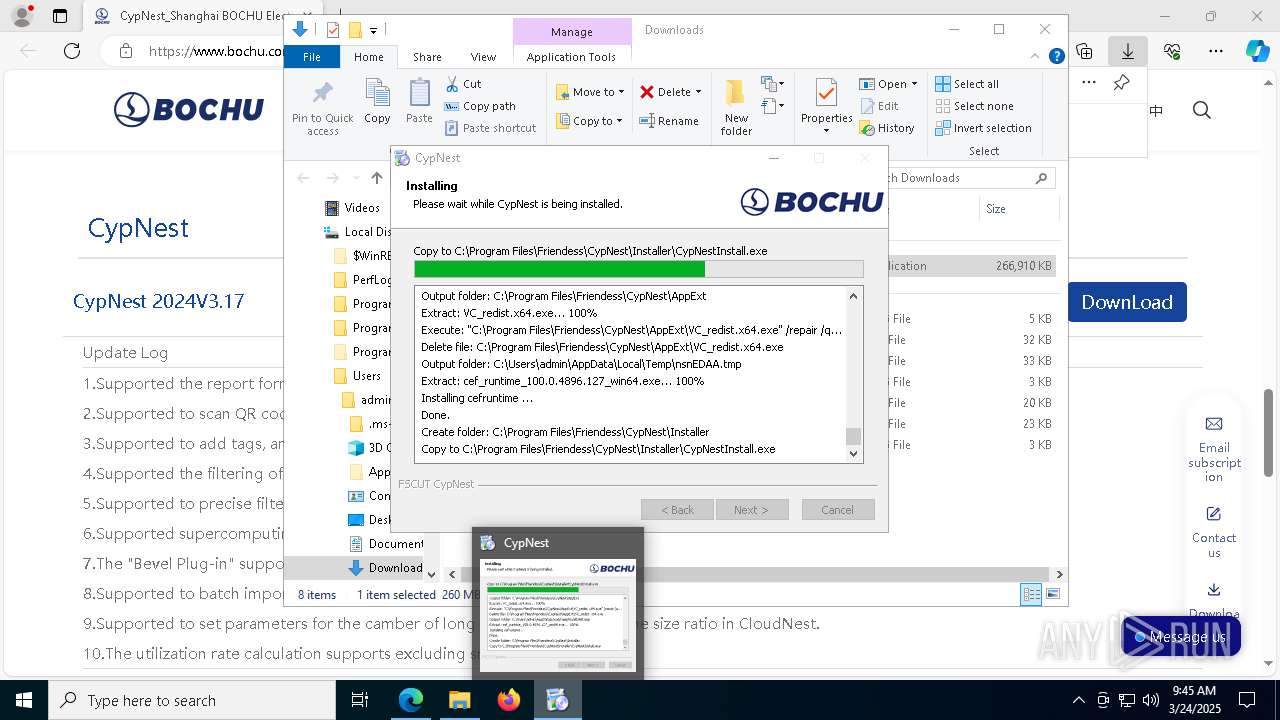
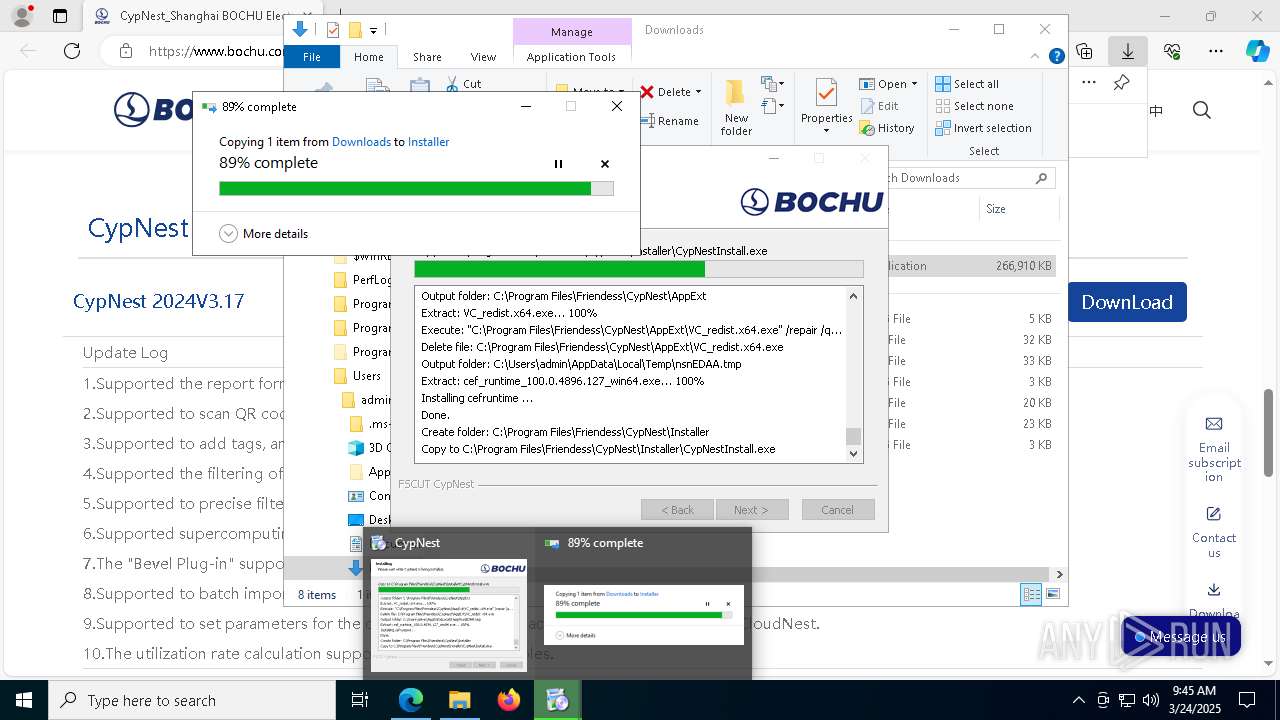
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 09:42:03 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1D81F5823FC731CB04576C2849E96DFE |
| SHA1: | 01E9FA986ECF187FF38DB46E47B8DB3465B18804 |
| SHA256: | 17861274BB9D367BB4E65DD749FFCDCF36743FC32473396A434B6333D050FCB5 |
| SSDEEP: | 3:N8DSLqaQnWKDsLhzsGD9p:2OLqjNDsLhznD/ |
MALICIOUS
Changes the autorun value in the registry
- VC_redist.x64.exe (PID: 5408)
Starts NET.EXE for service management
- cmd.exe (PID: 5204)
- net.exe (PID: 8852)
Executing a file with an untrusted certificate
- setup.exe (PID: 4108)
- setup.exe (PID: 5400)
- setup.exe (PID: 8312)
- setup.exe (PID: 8340)
- setup.exe (PID: 5588)
- setup.exe (PID: 8252)
- setup.exe (PID: 2408)
- setup.exe (PID: 6904)
- InstWiz3.exe (PID: 4188)
- setup.exe (PID: 7604)
- setup.exe (PID: 2152)
- setup.exe (PID: 1196)
- setup.exe (PID: 5024)
- setup.exe (PID: 3304)
- setup.exe (PID: 5640)
- setup.exe (PID: 7264)
- setup.exe (PID: 8552)
- setup.exe (PID: 668)
- setup.exe (PID: 2392)
- setup.exe (PID: 8496)
- setup.exe (PID: 6256)
- setup.exe (PID: 8504)
- setup.exe (PID: 5740)
- setup.exe (PID: 9008)
- setup.exe (PID: 6656)
- setup.exe (PID: 7612)
- setup.exe (PID: 6584)
- setup.exe (PID: 7192)
- setup.exe (PID: 7236)
- setup.exe (PID: 1004)
- setup.exe (PID: 2984)
- setup.exe (PID: 8596)
- setup.exe (PID: 5244)
- setup.exe (PID: 2776)
- setup.exe (PID: 5136)
- setup.exe (PID: 8804)
- setup.exe (PID: 8600)
- setup.exe (PID: 7420)
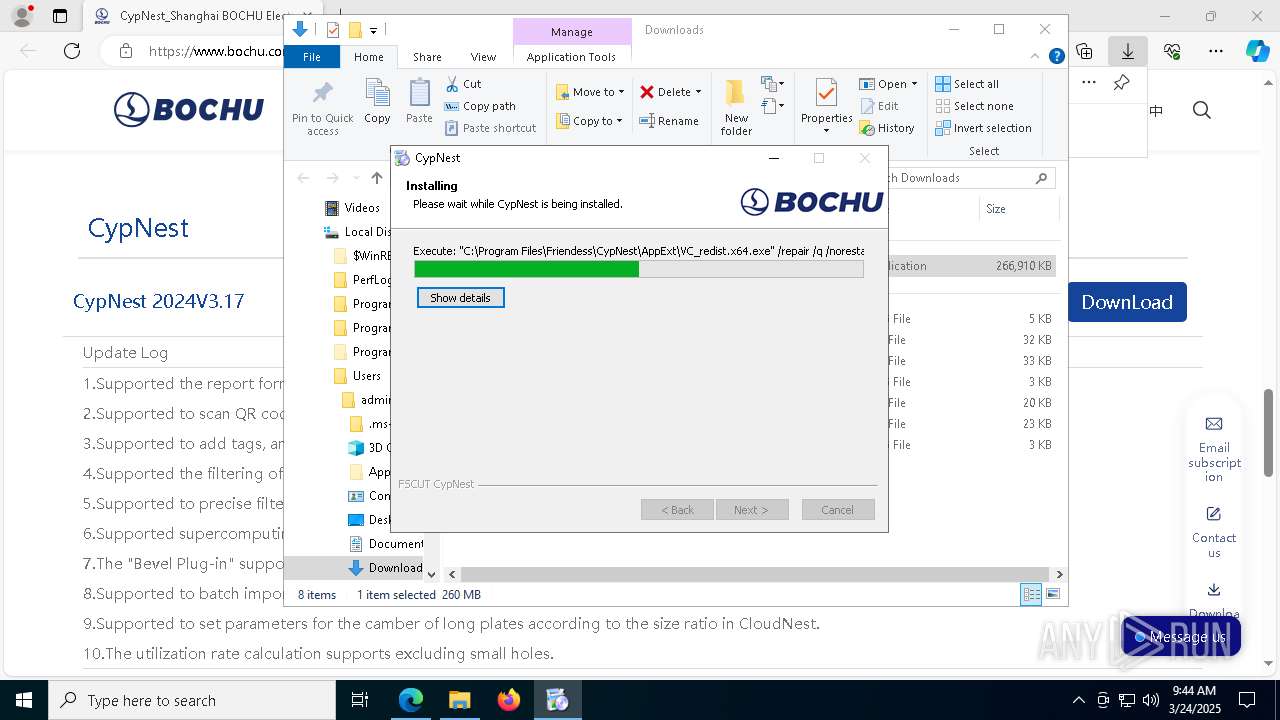
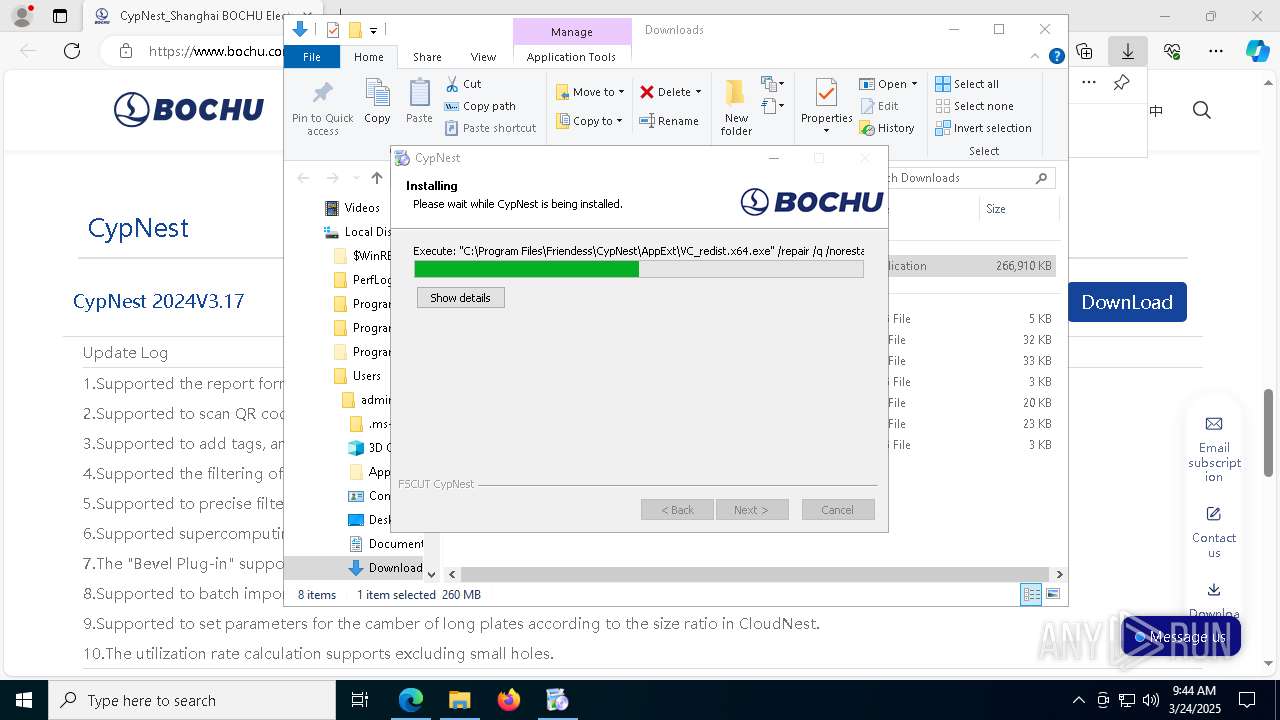
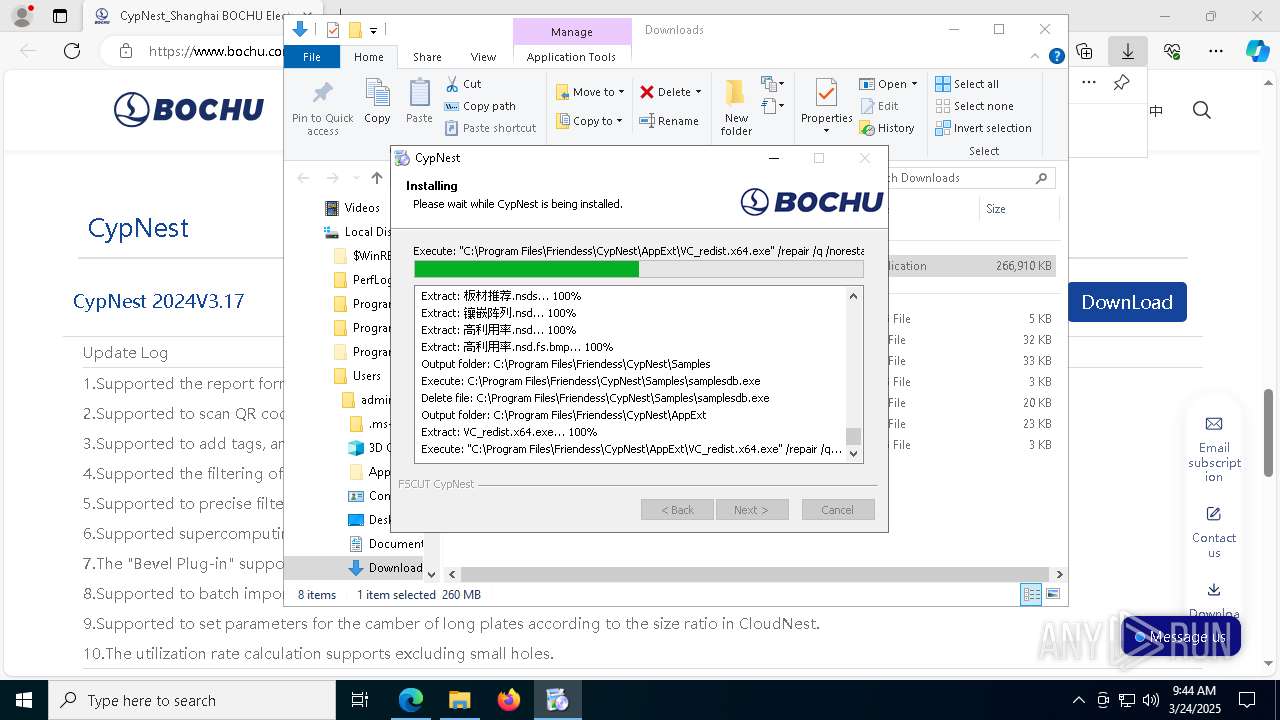
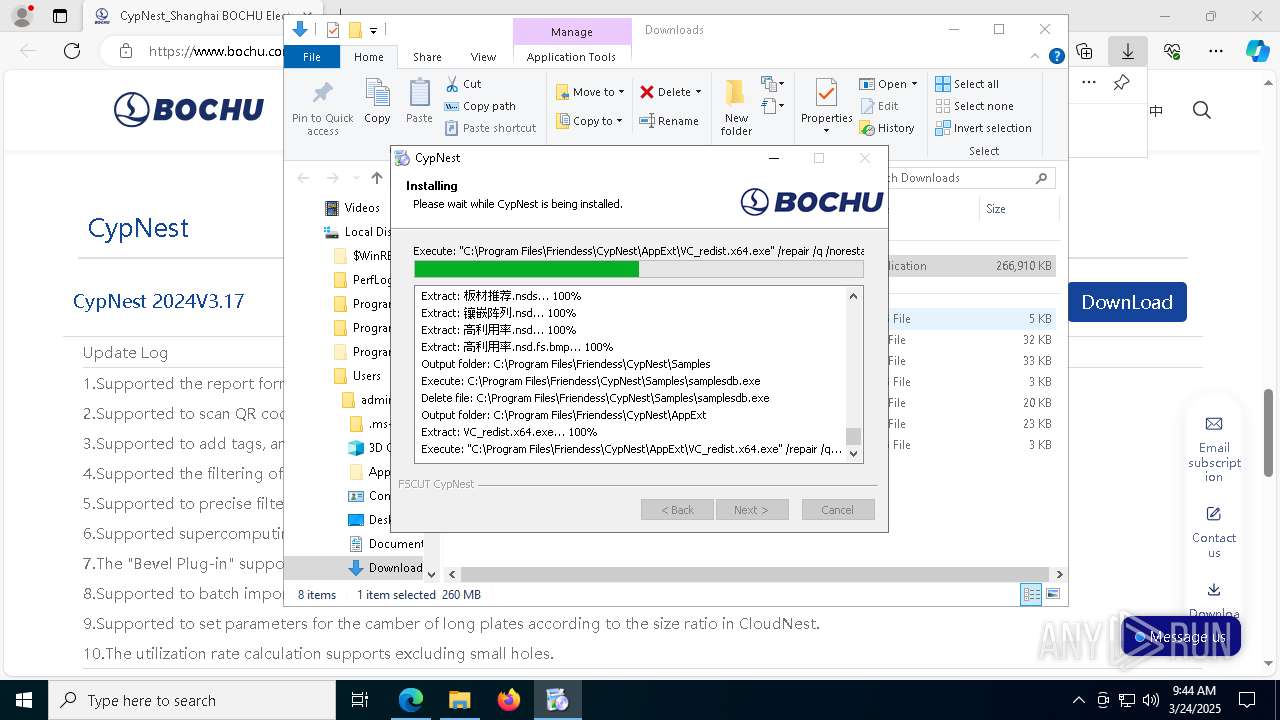
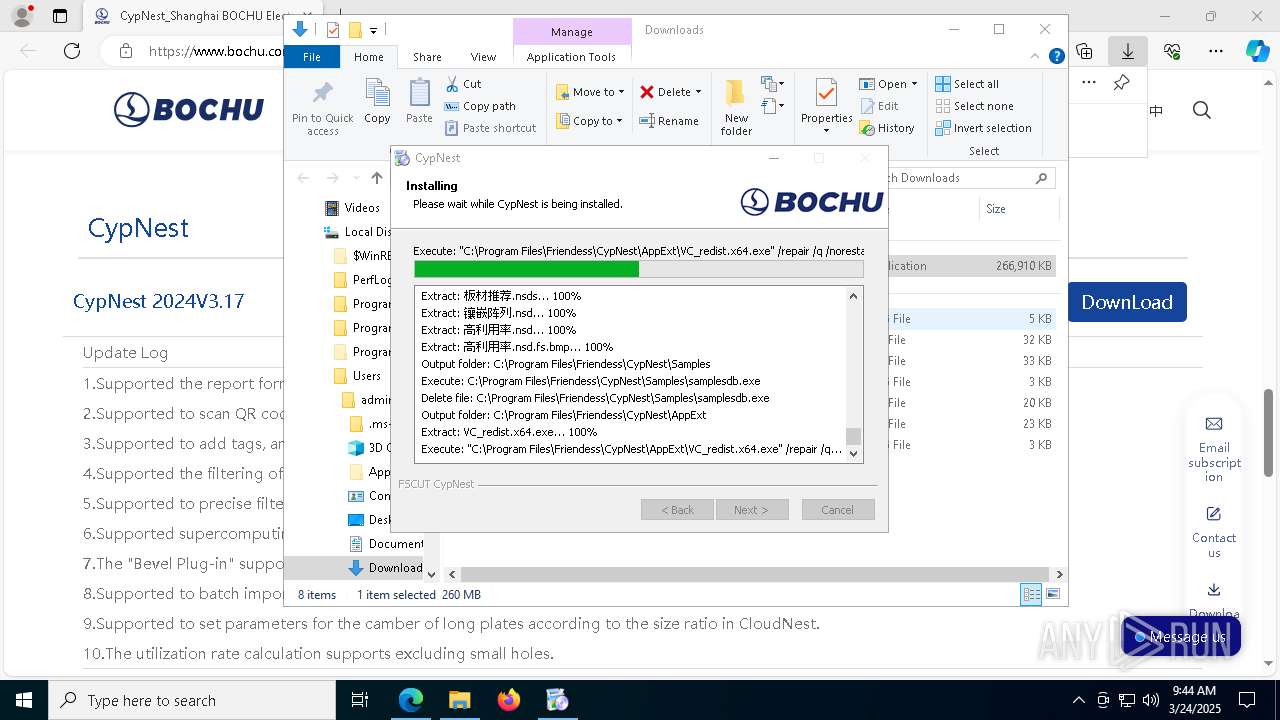
Registers / Runs the DLL via REGSVR32.EXE
- CypNest_2024V3.17.exe (PID: 5384)
SUSPICIOUS
Malware-specific behavior (creating "System.dll" in Temp)
- CypNest_2024V3.17.exe (PID: 5384)
- cef_runtime_100.0.4896.127_win64.exe (PID: 5172)
Uses TASKKILL.EXE to kill process
- CypNest_2024V3.17.exe (PID: 5384)
Process drops legitimate windows executable
- CypNest_2024V3.17.exe (PID: 5384)
- VC_redist.x64.exe (PID: 2896)
- VC_redist.x64.exe (PID: 2776)
- VC_redist.x64.exe (PID: 5408)
- msiexec.exe (PID: 8736)
- VC_redist.x64.exe (PID: 7600)
- cef_runtime_100.0.4896.127_win64.exe (PID: 5172)
The process drops C-runtime libraries
- CypNest_2024V3.17.exe (PID: 5384)
- msiexec.exe (PID: 8736)
Executable content was dropped or overwritten
- CypNest_2024V3.17.exe (PID: 5384)
- VC_redist.x64.exe (PID: 2896)
- VC_redist.x64.exe (PID: 2776)
- VC_redist.x64.exe (PID: 5408)
- VC_redist.x64.exe (PID: 8880)
- VC_redist.x64.exe (PID: 7600)
- cef_runtime_100.0.4896.127_win64.exe (PID: 5172)
- setup.exe (PID: 5244)
- setup.exe (PID: 2776)
- drvinst.exe (PID: 2064)
Drops 7-zip archiver for unpacking
- CypNest_2024V3.17.exe (PID: 5384)
There is functionality for taking screenshot (YARA)
- CypNest_2024V3.17.exe (PID: 5384)
Searches for installed software
- VC_redist.x64.exe (PID: 2776)
- dllhost.exe (PID: 1012)
- VC_redist.x64.exe (PID: 8880)
- VC_redist.x64.exe (PID: 7600)
Starts a Microsoft application from unusual location
- VC_redist.x64.exe (PID: 2776)
- VC_redist.x64.exe (PID: 5408)
Reads security settings of Internet Explorer
- VC_redist.x64.exe (PID: 2776)
- VC_redist.x64.exe (PID: 8880)
- cef_runtime_100.0.4896.127_win64.exe (PID: 5172)
- CypNestSvc.exe (PID: 8164)
- gxjc.exe (PID: 644)
Starts itself from another location
- VC_redist.x64.exe (PID: 2776)
Executes as Windows Service
- VSSVC.exe (PID: 6980)
- CypDrawSvc.exe (PID: 3156)
- CypNestSvc.exe (PID: 8164)
Creates a software uninstall entry
- VC_redist.x64.exe (PID: 5408)
- cef_runtime_100.0.4896.127_win64.exe (PID: 5172)
- CypNest_2024V3.17.exe (PID: 5384)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 8736)
Application launched itself
- VC_redist.x64.exe (PID: 8728)
- VC_redist.x64.exe (PID: 8880)
Creates or modifies Windows services
- CypNestSvc.exe (PID: 660)
Starts CMD.EXE for commands execution
- CypNestSvc.exe (PID: 660)
- CypNest.exe (PID: 6048)
- CypNest.exe (PID: 7144)
Reads the date of Windows installation
- CypNestSvc.exe (PID: 8164)
- CypNestWeb.exe (PID: 5868)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- CypNest_2024V3.17.exe (PID: 5384)
Uses NETSH.EXE to add a firewall rule or allowed programs
- CypNest_2024V3.17.exe (PID: 5384)
Uses NETSH.EXE to change the status of the firewall
- CypNest_2024V3.17.exe (PID: 5384)
Drops a system driver (possible attempt to evade defenses)
- CypNest_2024V3.17.exe (PID: 5384)
- setup.exe (PID: 5244)
- setup.exe (PID: 2776)
- drvinst.exe (PID: 2064)
Uses REG/REGEDIT.EXE to modify registry
- CypNest_2024V3.17.exe (PID: 5384)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 924)
Process uses ARP to discover network configuration
- cmd.exe (PID: 7412)
- cmd.exe (PID: 4208)
INFO
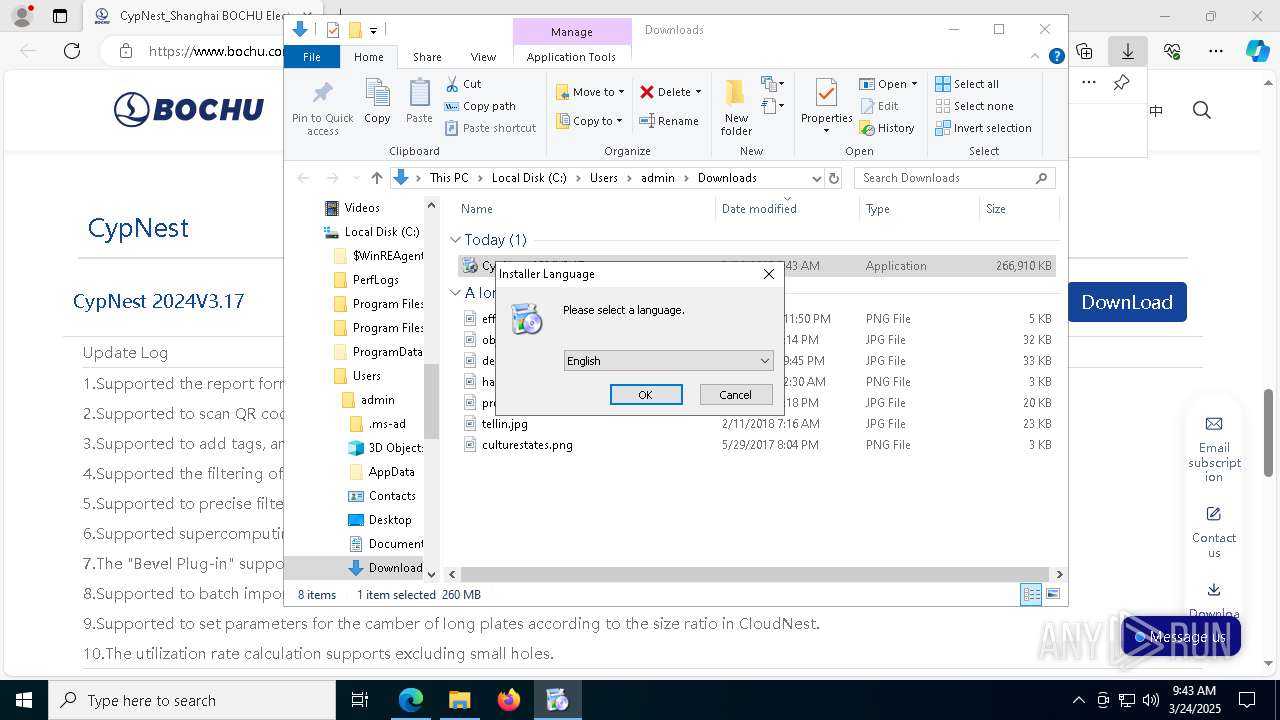
Checks supported languages
- identity_helper.exe (PID: 5260)
- CypNest_2024V3.17.exe (PID: 5384)
- SetACL.exe (PID: 3676)
- SetACL.exe (PID: 7856)
- VC_redist.x64.exe (PID: 5408)
- VC_redist.x64.exe (PID: 2776)
- samplesdb.exe (PID: 8940)
- VC_redist.x64.exe (PID: 2896)
- msiexec.exe (PID: 8736)
- VC_redist.x64.exe (PID: 8728)
- VC_redist.x64.exe (PID: 8880)
- VC_redist.x64.exe (PID: 7600)
- CypDrawSvc.exe (PID: 872)
- CypDrawSvc.exe (PID: 3156)
- CypNestSvc.exe (PID: 8164)
- CypDrawSvcApp.exe (PID: 5116)
- CypNestSvc.exe (PID: 660)
- cef_runtime_100.0.4896.127_win64.exe (PID: 5172)
- CypNestDbSvc.exe (PID: 8980)
- setup.exe (PID: 4108)
- setup.exe (PID: 8340)
- setup.exe (PID: 5400)
- setup.exe (PID: 8252)
- setup.exe (PID: 2408)
- setup.exe (PID: 3304)
- setup.exe (PID: 5024)
- setup.exe (PID: 7264)
- setup.exe (PID: 668)
- setup.exe (PID: 7604)
- setup.exe (PID: 8504)
- setup.exe (PID: 1004)
- setup.exe (PID: 9008)
- setup.exe (PID: 6656)
- setup.exe (PID: 6584)
- setup.exe (PID: 2984)
- setup.exe (PID: 7612)
- setup.exe (PID: 7192)
- setup.exe (PID: 8600)
- setup.exe (PID: 8596)
- setup.exe (PID: 2776)
- startapp.exe (PID: 5548)
- CypNest.exe (PID: 6048)
- gxjc.exe (PID: 644)
- CypNestWeb.exe (PID: 5868)
- CypWebSvcApp.exe (PID: 6344)
- CypWebSvcApp.exe (PID: 4740)
The sample compiled with english language support
- msedge.exe (PID: 7564)
- CypNest_2024V3.17.exe (PID: 5384)
- VC_redist.x64.exe (PID: 2896)
- VC_redist.x64.exe (PID: 2776)
- VC_redist.x64.exe (PID: 5408)
- msiexec.exe (PID: 8736)
- VC_redist.x64.exe (PID: 8880)
- VC_redist.x64.exe (PID: 7600)
- cef_runtime_100.0.4896.127_win64.exe (PID: 5172)
- setup.exe (PID: 5244)
- setup.exe (PID: 2776)
- drvinst.exe (PID: 2064)
Reads Environment values
- identity_helper.exe (PID: 5260)
- CypDrawSvc.exe (PID: 872)
- CypDrawSvc.exe (PID: 3156)
- CypNestSvc.exe (PID: 660)
- CypNestSvc.exe (PID: 8164)
- CypDrawSvcApp.exe (PID: 5116)
- CypNestDbSvc.exe (PID: 8980)
- startapp.exe (PID: 5548)
- gxjc.exe (PID: 644)
- CypWebSvcApp.exe (PID: 4740)
- CypWebSvcApp.exe (PID: 6344)
- CypNest.exe (PID: 7144)
Reads the computer name
- identity_helper.exe (PID: 5260)
- SetACL.exe (PID: 3676)
- CypNest_2024V3.17.exe (PID: 5384)
- msiexec.exe (PID: 8736)
- VC_redist.x64.exe (PID: 7600)
- VC_redist.x64.exe (PID: 8880)
- CypDrawSvc.exe (PID: 872)
- CypNestSvc.exe (PID: 660)
- CypDrawSvc.exe (PID: 3156)
- CypNestSvc.exe (PID: 8164)
- CypNestDbSvc.exe (PID: 8980)
- setup.exe (PID: 2776)
- drvinst.exe (PID: 2064)
- startapp.exe (PID: 5548)
- CypNest.exe (PID: 7144)
- CypWebSvcApp.exe (PID: 4348)
Reads the software policy settings
- slui.exe (PID: 7012)
- slui.exe (PID: 8236)
- msiexec.exe (PID: 8736)
Executable content was dropped or overwritten
- msedge.exe (PID: 7564)
- msiexec.exe (PID: 8736)
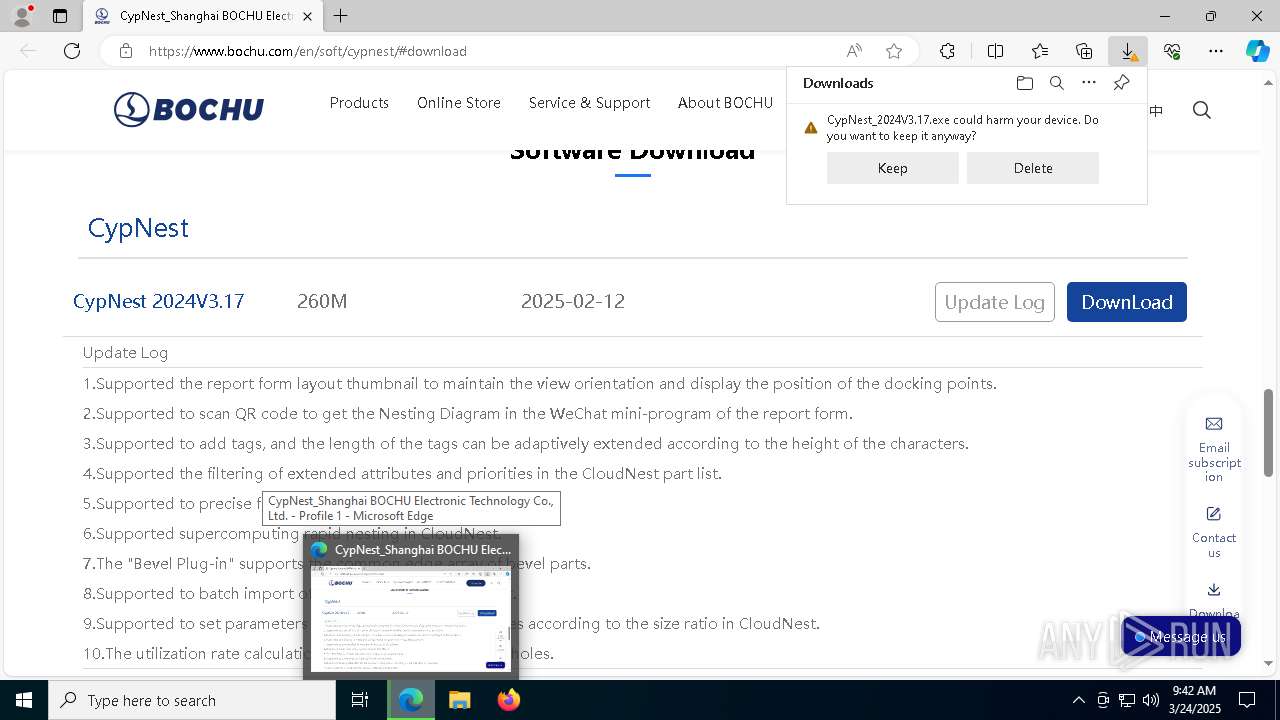
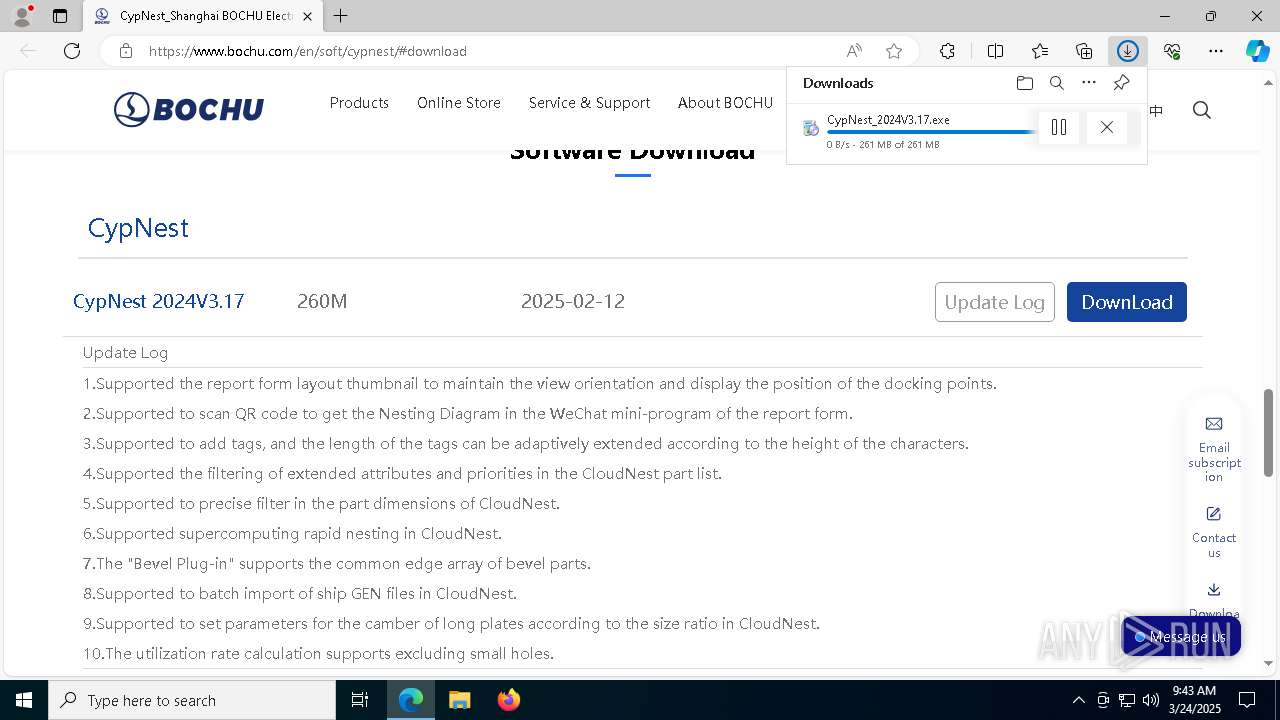
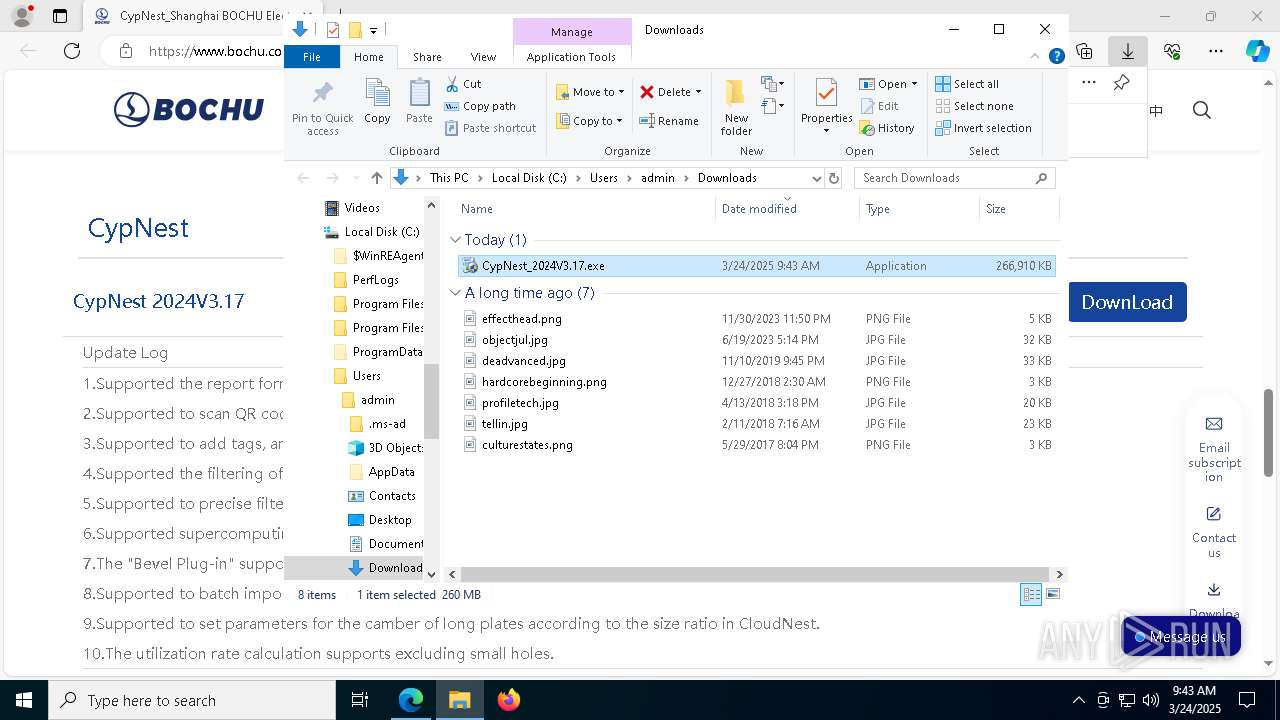
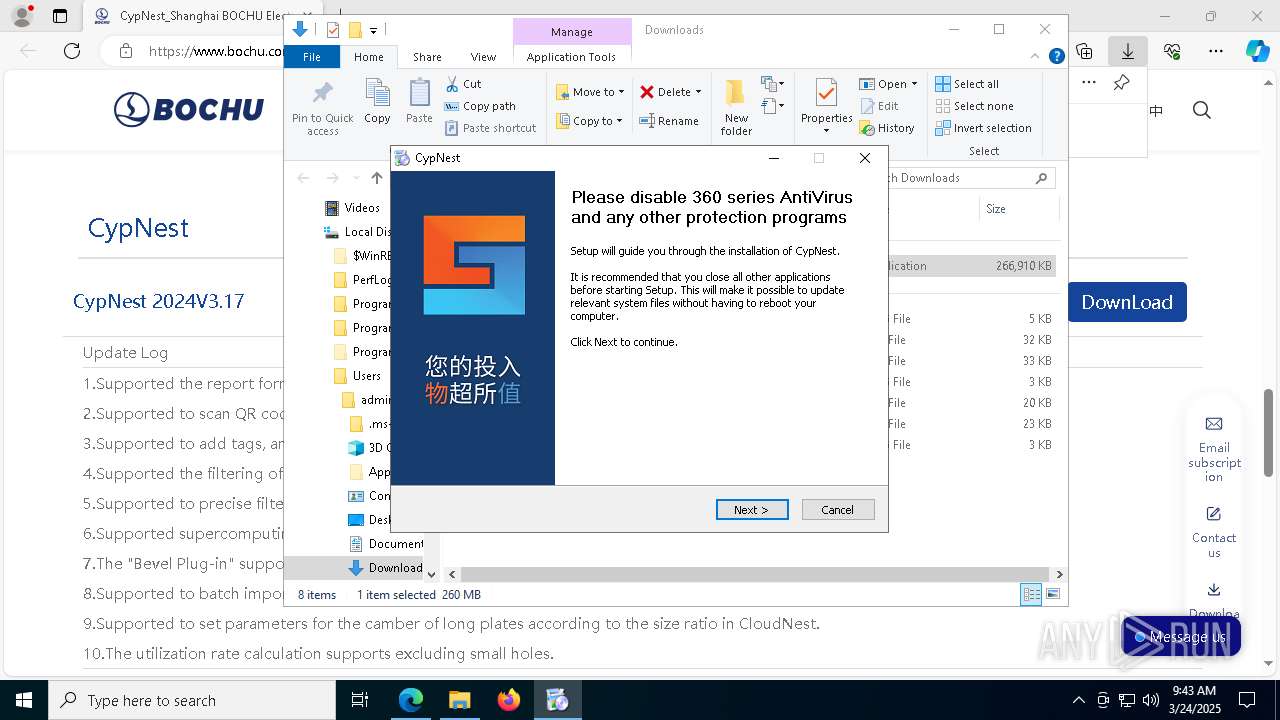
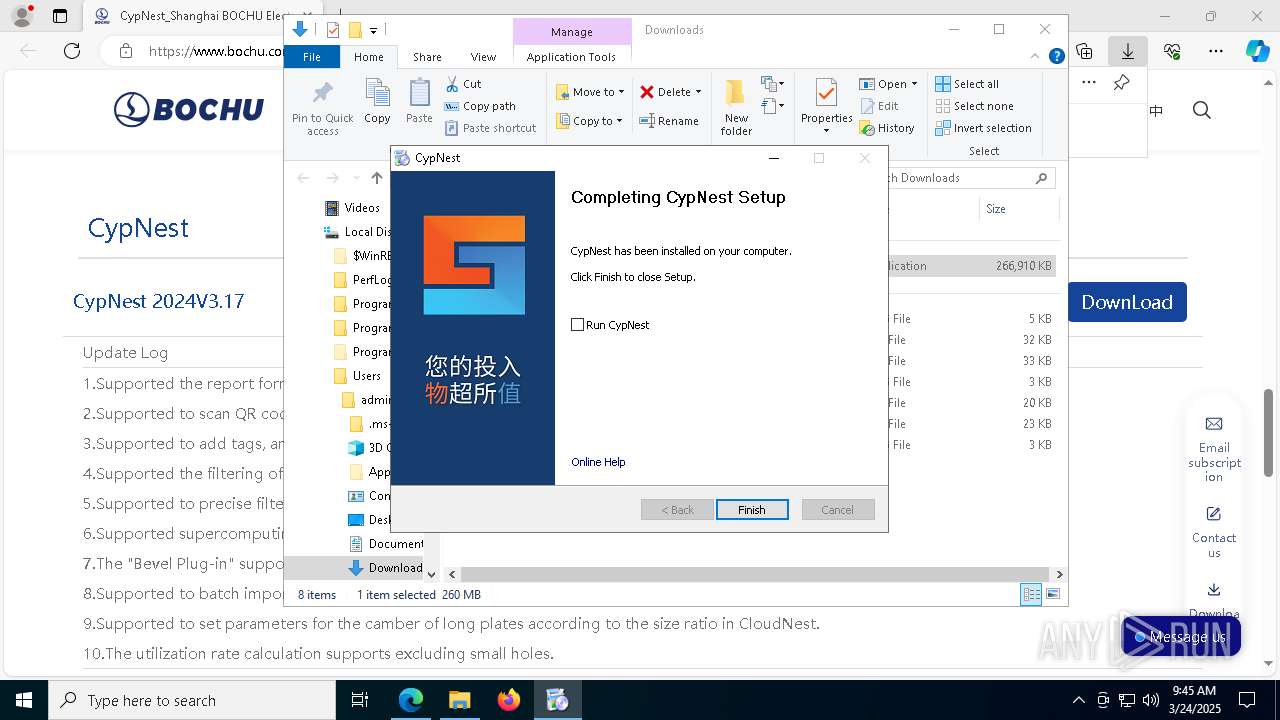
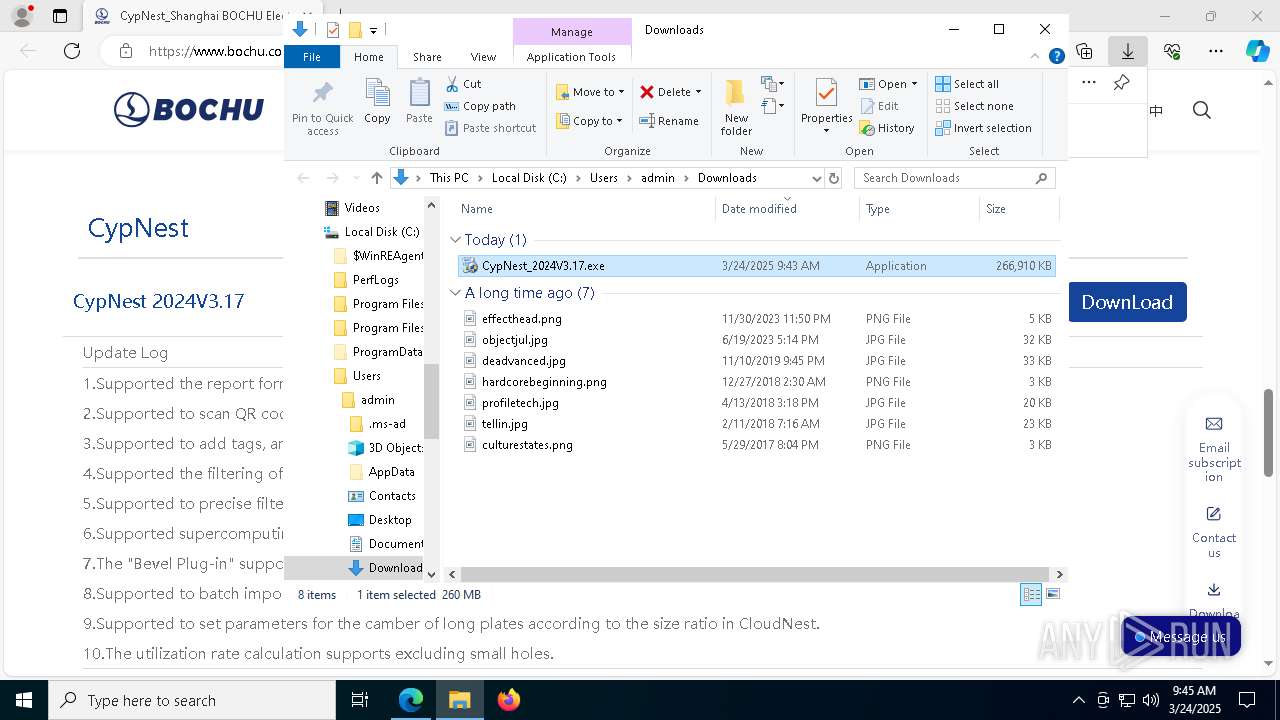
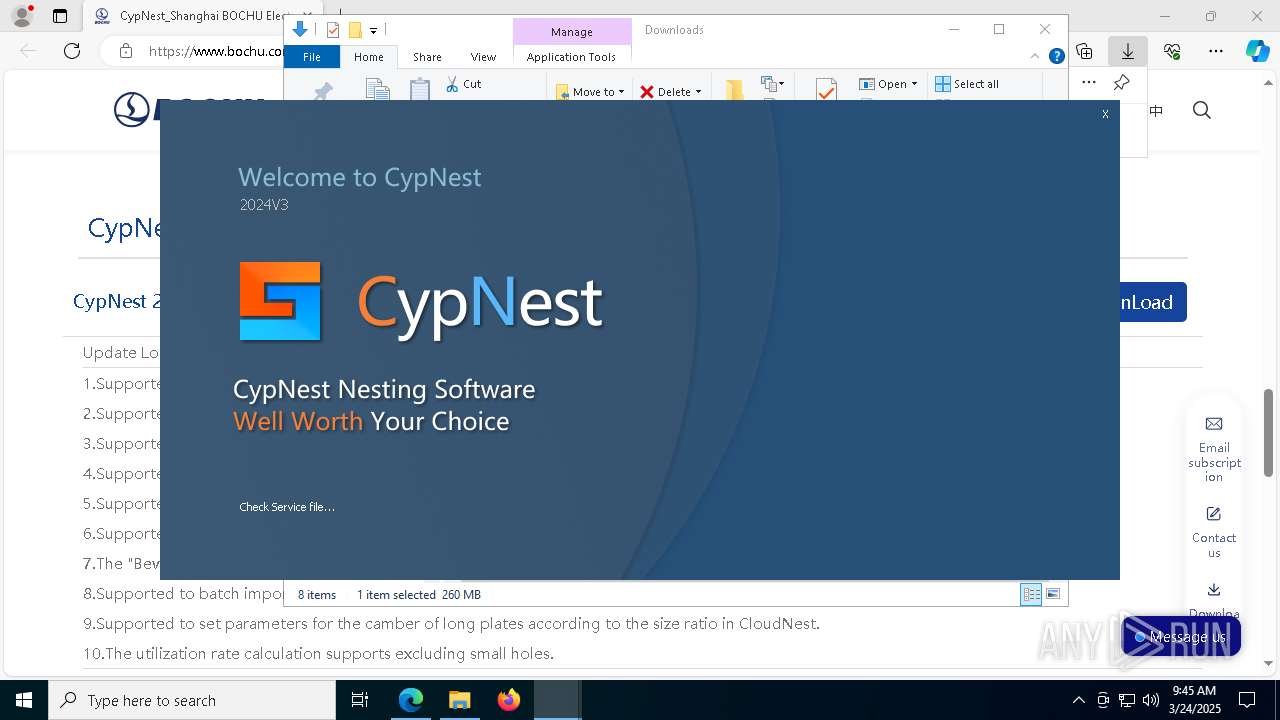
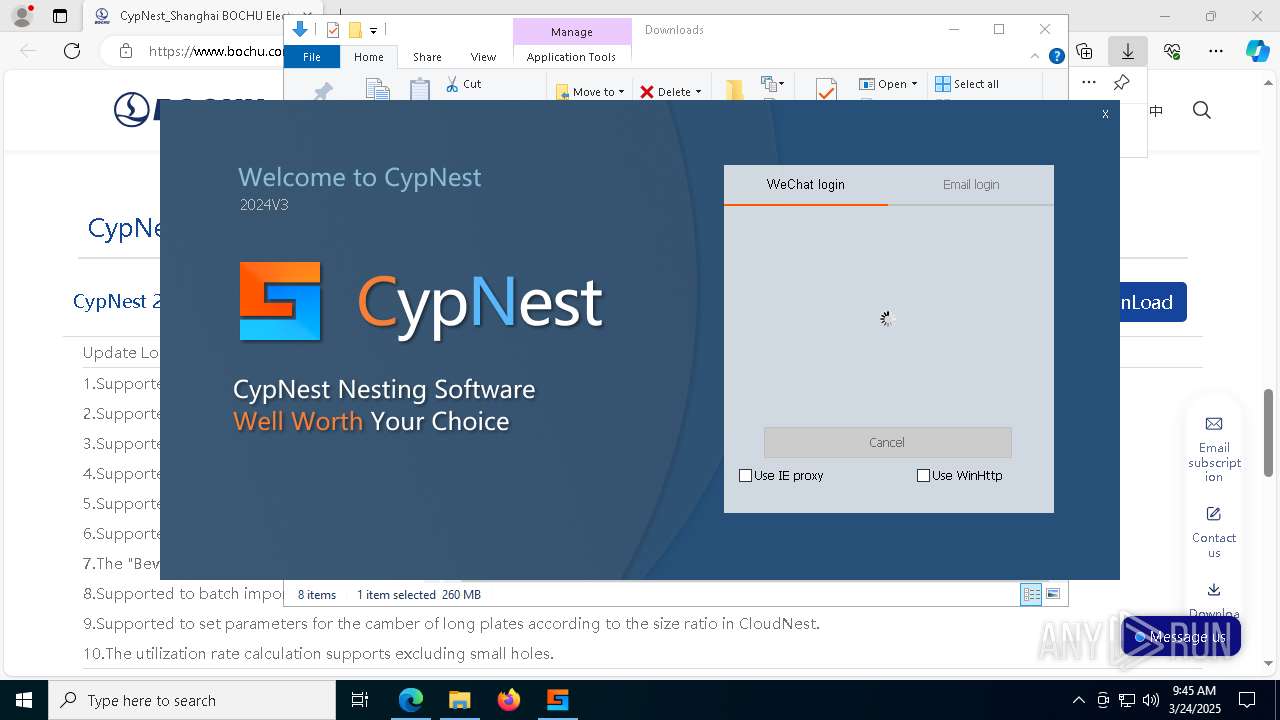
Manual execution by a user
- CypNest_2024V3.17.exe (PID: 5384)
- CypNest_2024V3.17.exe (PID: 2568)
Autorun file from Downloads
- msedge.exe (PID: 8228)
Checks proxy server information
- slui.exe (PID: 8236)
- gxjc.exe (PID: 644)
- CypNest.exe (PID: 7144)
The sample compiled with chinese language support
- CypNest_2024V3.17.exe (PID: 5384)
Creates files in the program directory
- CypNest_2024V3.17.exe (PID: 5384)
- samplesdb.exe (PID: 8940)
- cef_runtime_100.0.4896.127_win64.exe (PID: 5172)
- CypDrawSvcApp.exe (PID: 5116)
Create files in a temporary directory
- CypNest_2024V3.17.exe (PID: 5384)
- VC_redist.x64.exe (PID: 2776)
Application launched itself
- msedge.exe (PID: 7564)
Process checks computer location settings
- VC_redist.x64.exe (PID: 2776)
- VC_redist.x64.exe (PID: 8880)
- CypNestWeb.exe (PID: 5868)
Manages system restore points
- SrTasks.exe (PID: 8532)
Reads the machine GUID from the registry
- VC_redist.x64.exe (PID: 5408)
- msiexec.exe (PID: 8736)
- CypDrawSvcApp.exe (PID: 5116)
- CypNestWeb.exe (PID: 5868)
- drvinst.exe (PID: 2064)
- CypNest.exe (PID: 7144)
Creates a software uninstall entry
- msiexec.exe (PID: 8736)
Reads CPU info
- CypDrawSvcApp.exe (PID: 5116)
Creates files or folders in the user directory
- CypNest.exe (PID: 7144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
385
Monitored processes
241
Malicious processes
9
Suspicious processes
40
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 536 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "C:\Program Files\Friendess\CypNest\gxjc.exe" {"LocaleID":1033,"Ver":"6.3.910.17","App":"CypNest"} | C:\Program Files\Friendess\CypNest\gxjc.exe | CypNestWeb.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 660 | "C:\Program Files\Friendess\CypNest\CypNestSvc" -install -silent | C:\Program Files\Friendess\CypNest\CypNestSvc.exe | — | CypNest_2024V3.17.exe | |||||||||||
User: admin Integrity Level: HIGH Description: CypNestSvc Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 664 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | .\winlh64\setup -u "readerenum.inf" | C:\Program Files\Friendess\CypNest\drivers\winlh64\setup.exe | — | InstWiz3.exe | |||||||||||
User: admin Integrity Level: HIGH Description: setuplh6 Application Exit code: 0 Version: 5, 3, 0, 0 Modules
| |||||||||||||||
| 684 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 776 | netsh advfirewall firewall delete rule name = "UDP_7117" | C:\Windows\SysWOW64\netsh.exe | — | CypNest_2024V3.17.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | "C:\Program Files\Friendess\CypNest\CypDrawSvc" -install -silent | C:\Program Files\Friendess\CypNest\CypDrawSvc.exe | — | CypNest_2024V3.17.exe | |||||||||||
User: admin Integrity Level: HIGH Description: CypDrawSvc Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
52 003
Read events
50 845
Write events
780
Delete events
378
Modification events
| (PID) Process: | (7432) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7432) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7432) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7432) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (7432) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (7432) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7564) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
Executable files
321
Suspicious files
584
Text files
269
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bd37.TMP | — | |
MD5:— | SHA256:— | |||
| 7564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bd37.TMP | — | |
MD5:— | SHA256:— | |||
| 7564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bd56.TMP | — | |
MD5:— | SHA256:— | |||
| 7564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bd56.TMP | — | |
MD5:— | SHA256:— | |||
| 7564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bd56.TMP | — | |
MD5:— | SHA256:— | |||
| 7564 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
147
DNS requests
111
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
9116 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1742983753&P2=404&P3=2&P4=mjQO5H3EBfGXNs9BTOBmQlEv54vyqy0%2fXYIovrwJzB7PBzBebxz5mqVFmRh530XgMEN%2fL%2f3GeR404Wdmx0R1bw%3d%3d | unknown | — | — | whitelisted |
3896 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8556 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
9116 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1742983753&P2=404&P3=2&P4=mjQO5H3EBfGXNs9BTOBmQlEv54vyqy0%2fXYIovrwJzB7PBzBebxz5mqVFmRh530XgMEN%2fL%2f3GeR404Wdmx0R1bw%3d%3d | unknown | — | — | whitelisted |
8556 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
9116 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1742983753&P2=404&P3=2&P4=mjQO5H3EBfGXNs9BTOBmQlEv54vyqy0%2fXYIovrwJzB7PBzBebxz5mqVFmRh530XgMEN%2fL%2f3GeR404Wdmx0R1bw%3d%3d | unknown | — | — | whitelisted |
9116 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1742987358&P2=404&P3=2&P4=Fid8rC2jfrfl26WZsEgyBFsp3aQnyvY%2bRKZY1NjvvUpuvkAzpdE1GfDe%2b1xHBhln9LrfEiwbeXFV5fbH%2bv9WxQ%3d%3d | unknown | — | — | whitelisted |
9116 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1742987358&P2=404&P3=2&P4=Fid8rC2jfrfl26WZsEgyBFsp3aQnyvY%2bRKZY1NjvvUpuvkAzpdE1GfDe%2b1xHBhln9LrfEiwbeXFV5fbH%2bv9WxQ%3d%3d | unknown | — | — | whitelisted |
9116 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1742987358&P2=404&P3=2&P4=Fid8rC2jfrfl26WZsEgyBFsp3aQnyvY%2bRKZY1NjvvUpuvkAzpdE1GfDe%2b1xHBhln9LrfEiwbeXFV5fbH%2bv9WxQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7800 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7564 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7800 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7800 | msedge.exe | 40.90.65.8:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7800 | msedge.exe | 47.103.37.176:443 | www.bochu.com | Hangzhou Alibaba Advertising Co.,Ltd. | CN | unknown |
7800 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7800 | msedge.exe | 23.50.131.74:443 | bzib.nelreports.net | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.bochu.com |
| unknown |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
www.bing.com |
| whitelisted |
d.fscut.com |
| unknown |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
2196 | svchost.exe | Misc activity | ET INFO DNS Query to Alibaba Cloud CDN Domain (aliyuncs .com) |
Process | Message |
|---|---|
msiexec.exe | Failed to release Service
|
CypDrawSvcApp.exe | TcpConnectThread |
CypDrawSvcApp.exe | Connected |
CypDrawSvc.exe | TcpConnectThread |
CypDrawSvc.exe | Connected |