| File name: | invivodentalviewer.exe |
| Full analysis: | https://app.any.run/tasks/bb931d8b-ab47-4a79-a028-081c91f0d91f |
| Verdict: | Malicious activity |
| Analysis date: | January 08, 2021, 20:02:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6A92584432FFCA055084011B5EA9B9BF |
| SHA1: | DD4A903F6F450953CD5FA2EDEA251C96D275A3E3 |
| SHA256: | 17829C433895A3F0F6EFEFF44F95E6B7C078FBA277A7925F39C4A1B320497F64 |
| SSDEEP: | 393216:UxfALNZlEwZv41mdS5BTXm3Rf8mBFiTjQ+Wzh/rQOV+:oeTlEwZv41m8m3Rf3Fujmzh/rQ |
MALICIOUS
Drops executable file immediately after starts
- invivodentalviewer.exe (PID: 2880)
SUSPICIOUS
Executable content was dropped or overwritten
- invivodentalviewer.exe (PID: 2880)
Drops a file with too old compile date
- invivodentalviewer.exe (PID: 2880)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:01:29 19:54:13+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 30720 |
| InitializedDataSize: | 771072 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x775e |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.1.1.0 |
| ProductVersionNumber: | 5.1.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | Anatomage Inc. |
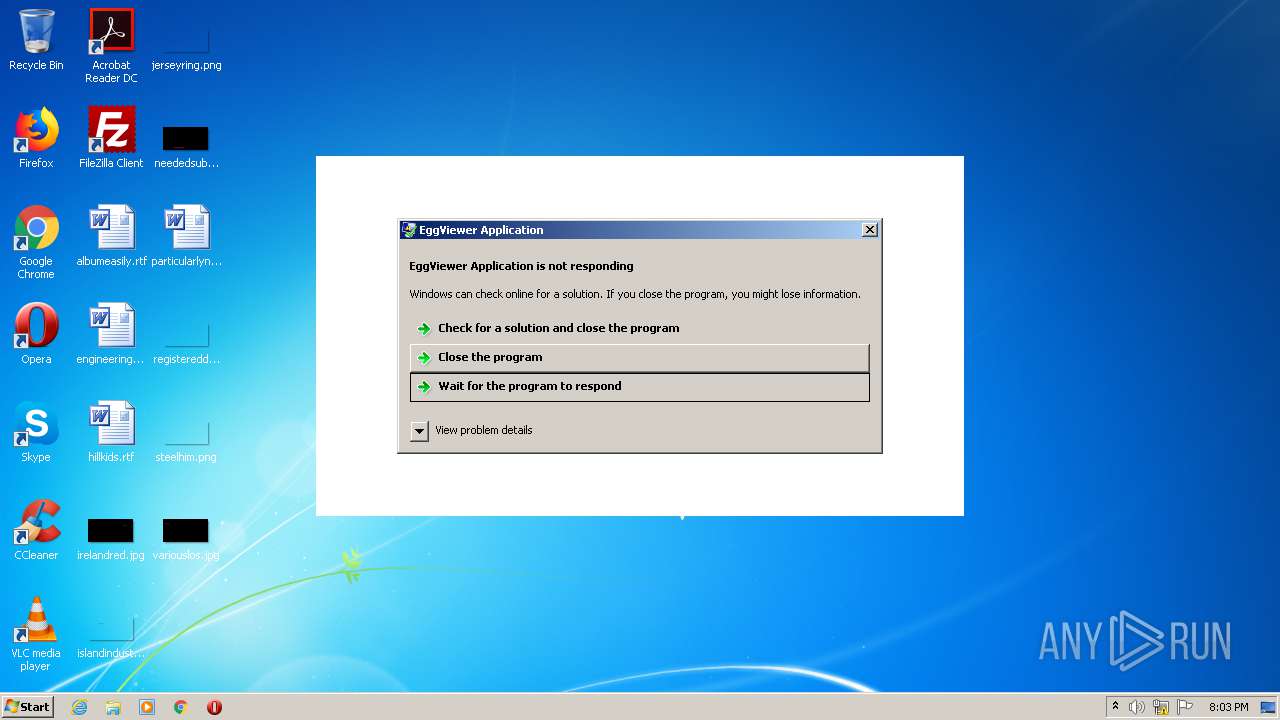
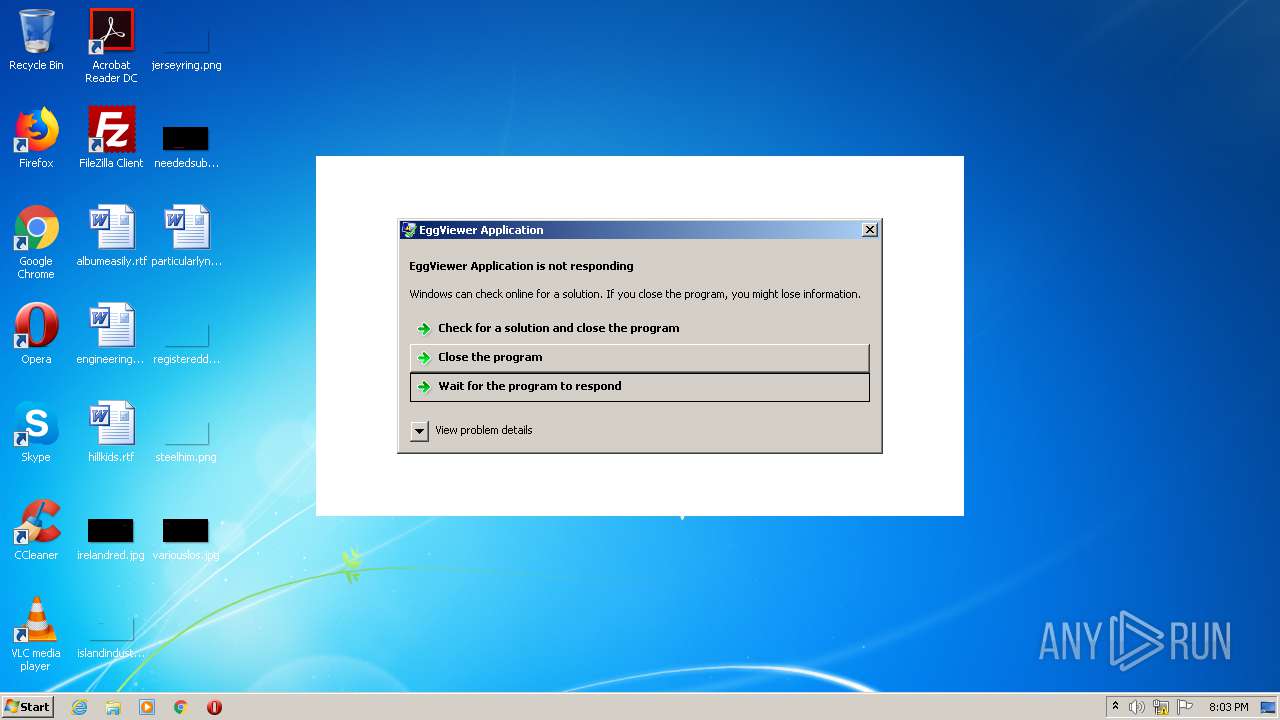
| FileDescription: | EggViewer Application |
| BuildDate: | 01/29/2015 - 10:54:13 |
| FileVersion: | 5.1.1.0 |
| InternalName: | EggViewer |
| LegalCopyright: | Copyright (C) 2004-2014 |
| LegalTrademarks: | - |
| OriginalFileName: | EggViewer.EXE |
| PrivateBuild: | - |
| ProductName: | TxSTUDIOViewer Application |
| ProductVersion: | 5.1.1.0 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Jan-2015 18:54:13 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Comments: | - |
| CompanyName: | Anatomage Inc. |
| FileDescription: | EggViewer Application |
| Build Date: | 01/29/2015 - 10:54:13 |
| FileVersion: | 5.1.1.0 |
| InternalName: | EggViewer |
| LegalCopyright: | Copyright (C) 2004-2014 |
| LegalTrademarks: | - |
| OriginalFilename: | EggViewer.EXE |
| PrivateBuild: | - |
| ProductName: | TxSTUDIOViewer Application |
| ProductVersion: | 5.1.1.0 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 29-Jan-2015 18:54:13 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000077BB | 0x00007800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.27358 |
.rdata | 0x00009000 | 0x00005E8A | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.39889 |
.data | 0x0000F000 | 0x00000A98 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.46567 |
.rsrc | 0x00010000 | 0x000B3DCC | 0x000B3E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.46851 |
.reloc | 0x000C4000 | 0x00001E24 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.06107 |
.enigma1 | 0x000C6000 | 0x00001000 | 0x00EF5000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.93579 |
.enigma2 | 0x000C7000 | 0x00041000 | 0x00041000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.05989 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.071 | 855 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.28332 | 872 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.00689 | 3240 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.14428 | 872 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 3.02695 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.74274 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 2.34038 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
8 | 2.34004 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
9 | 2.94881 | 234 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 2.45401 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
SHFolder.dll |
advapi32.dll |
kernel32.dll |
ntdll.dll |
ole32.dll |
oleaut32.dll |
shlwapi.dll |
user32.dll |
Total processes
35
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2880 | "C:\Users\admin\AppData\Local\Temp\invivodentalviewer.exe" | C:\Users\admin\AppData\Local\Temp\invivodentalviewer.exe | explorer.exe | ||||||||||||
User: admin Company: Anatomage Inc. Integrity Level: MEDIUM Description: EggViewer Application Exit code: 0 Version: 5.1.1.0 Modules
| |||||||||||||||
Total events
18
Read events
18
Write events
0
Delete events
0
Modification events
Executable files
36
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2880 | invivodentalviewer.exe | C:\Users\admin\AppData\Local\Temp\evb16B4.tmp | executable | |
MD5:— | SHA256:— | |||
| 2880 | invivodentalviewer.exe | C:\Users\admin\AppData\Local\Temp\evb1642.tmp | executable | |
MD5:6C1B6FD0BABF1B755C65A5FBF728F3FD | SHA256:0BF22A35F8732246470644A1E33055EA52CC026E36A808A36EC2C1D599766957 | |||
| 2880 | invivodentalviewer.exe | C:\Users\admin\AppData\Local\Temp\evb1755.tmp | executable | |
MD5:FF457902ACF59697BC883E3ACCB8CD92 | SHA256:6FD96250601398E5108B771DD645261F7815B9C6F42BCA238B50F034258D97F9 | |||
| 2880 | invivodentalviewer.exe | C:\Users\admin\AppData\Local\Temp\evb1745.tmp | executable | |
MD5:A37DCB89E31E6497D893A8FCCE4CC601 | SHA256:FD802133E0D7E20C309C3CEB22E62D1BB66B0E41A8DA53D10C5858C34DF4807B | |||
| 2880 | invivodentalviewer.exe | C:\Users\admin\AppData\Local\Temp\evb1724.tmp | executable | |
MD5:7BB2C7B7DBCE90397F32004D13D37167 | SHA256:07E9DC518B0A274028C15BC8224194DB0515396D4CBAC9736E16BD8D41CDE825 | |||
| 2880 | invivodentalviewer.exe | C:\Users\admin\AppData\Local\Temp\evb17A6.tmp | executable | |
MD5:4535261AB47459C501324F2457E7AC64 | SHA256:ED734DC7BA325E3D611ECF07E3D23EEB797028B1E882DC618F4CF9AE6C22FAD2 | |||
| 2880 | invivodentalviewer.exe | C:\Users\admin\AppData\Local\Temp\evb1786.tmp | executable | |
MD5:9A0CAF485D0CEB6D703FB8ABB54100AE | SHA256:4B58A9EE840A376EE334117BC8A56F66CD4B32F173B490CB9F9C71F6A6499BD5 | |||
| 2880 | invivodentalviewer.exe | C:\Users\admin\AppData\Local\Temp\evb1766.tmp | executable | |
MD5:FC37903B2E7BFDC0102E9F5956F067F1 | SHA256:2A4EADEB26061AFAC8F213BB2B6AAEAA23F476EA3F53203597A81CD4FAF932BF | |||
| 2880 | invivodentalviewer.exe | C:\Users\admin\AppData\Local\Temp\evb17A7.tmp | executable | |
MD5:3010DFA1B350EBF8915B37F7F8F625CD | SHA256:95872F810B91F3E1F7A6FDACA0B74B54CDA8C278994D4DBE33C59B7A50C98E8B | |||
| 2880 | invivodentalviewer.exe | C:\Users\admin\AppData\Local\Temp\evb1693.tmp | executable | |
MD5:FABB2CFEC71D832D31C8AB38D9419F0F | SHA256:CFC977C87E1A1CBB7B69A92FD5A06D57FB652F5DB1A934911C501AF7E758A8CD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report