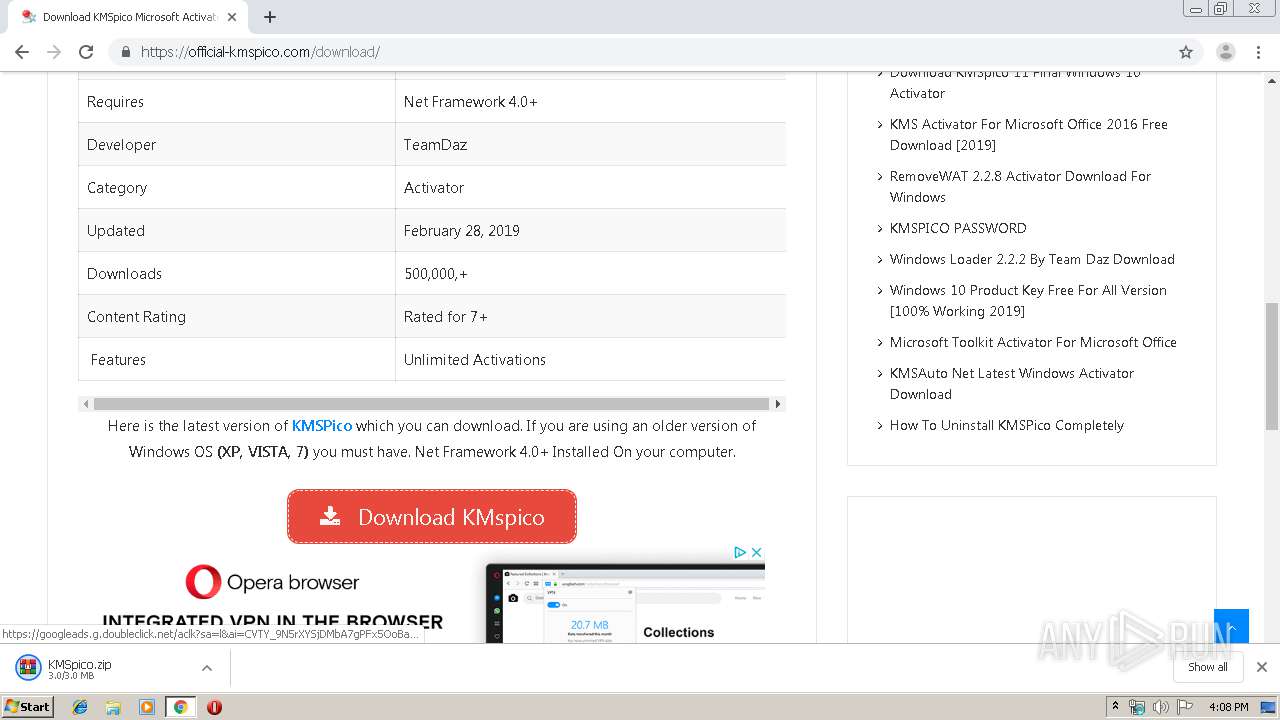
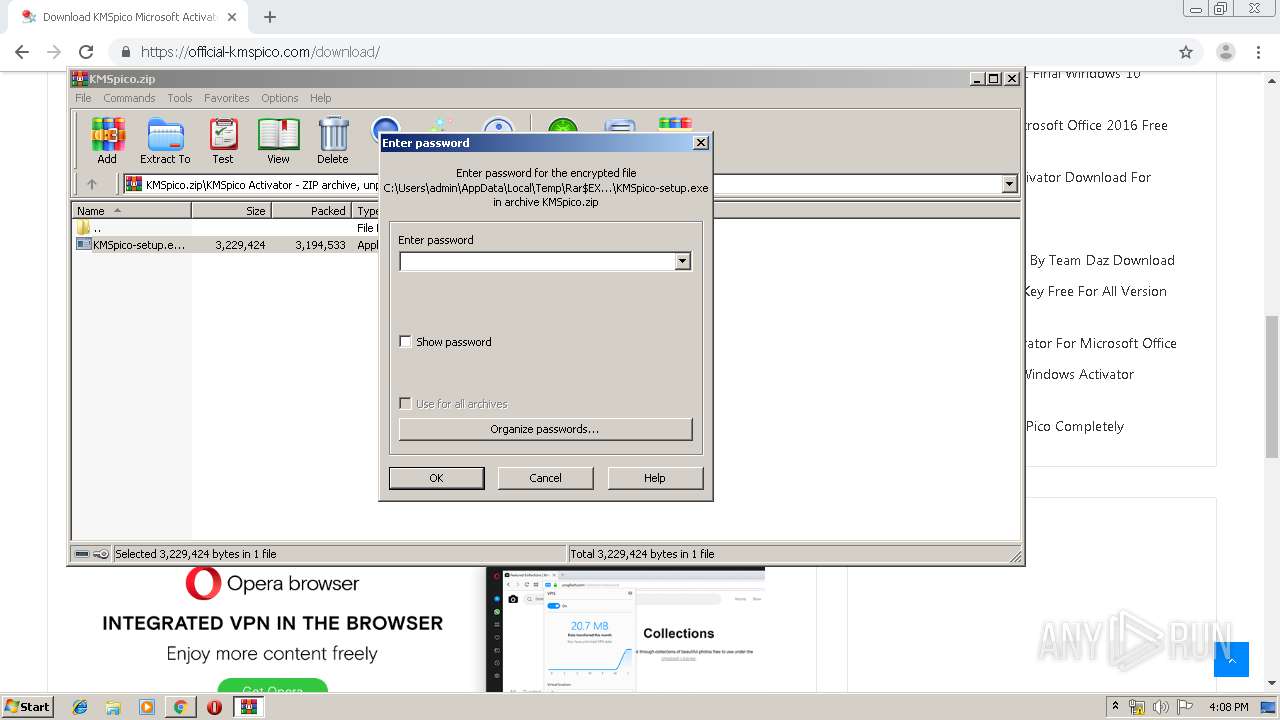
| URL: | https://official-kmspico.com/download-kmspico-windows-10-activator/ |
| Full analysis: | https://app.any.run/tasks/130b9f87-7d17-4341-a09e-7a8b7189ced0 |
| Verdict: | Malicious activity |
| Analysis date: | September 01, 2019, 15:07:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 162E1C9E0B61D60A0CAF172EED0A7B67 |
| SHA1: | 2CF2A477739B232FE2F2D92ECB4C4DDC680D6F75 |
| SHA256: | 177B47E2F958B0595F9F8927D334B738B1384B2C79D403FB6412098E8A180F83 |
| SSDEEP: | 3:N8KQGMcpK8JOIS+kxEGqW:2KQGMOBAIhkxvD |
MALICIOUS
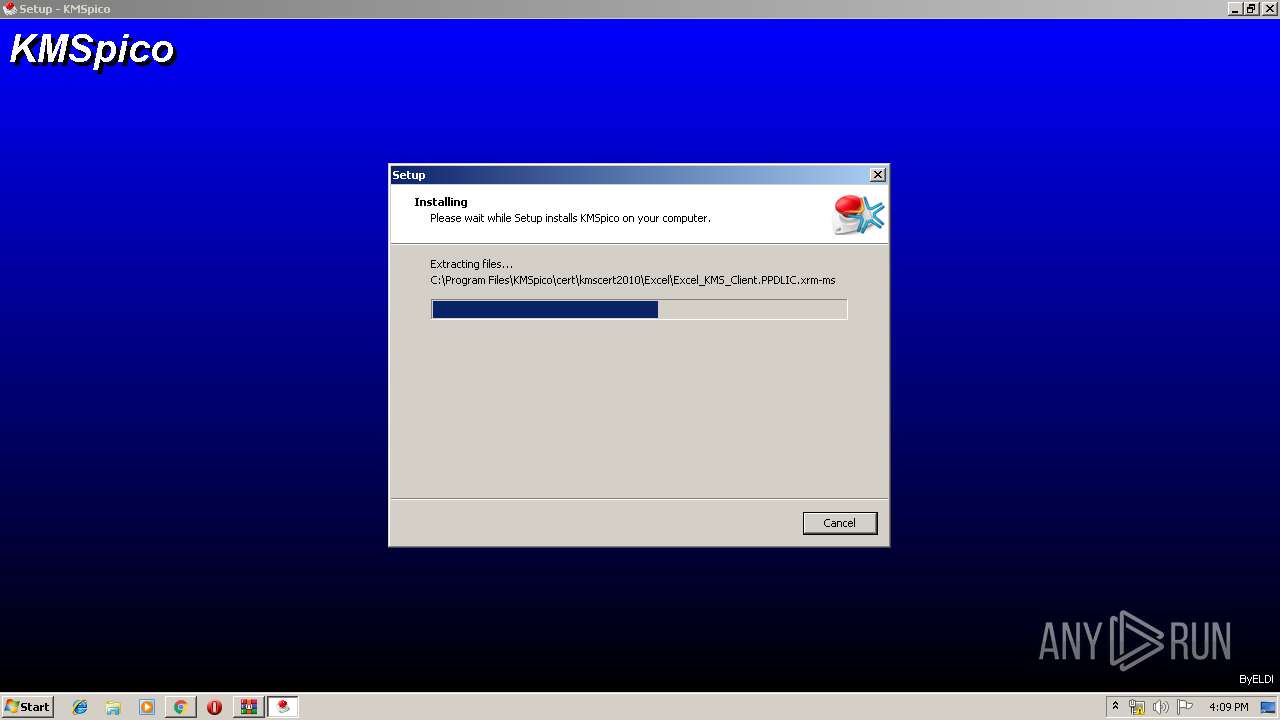
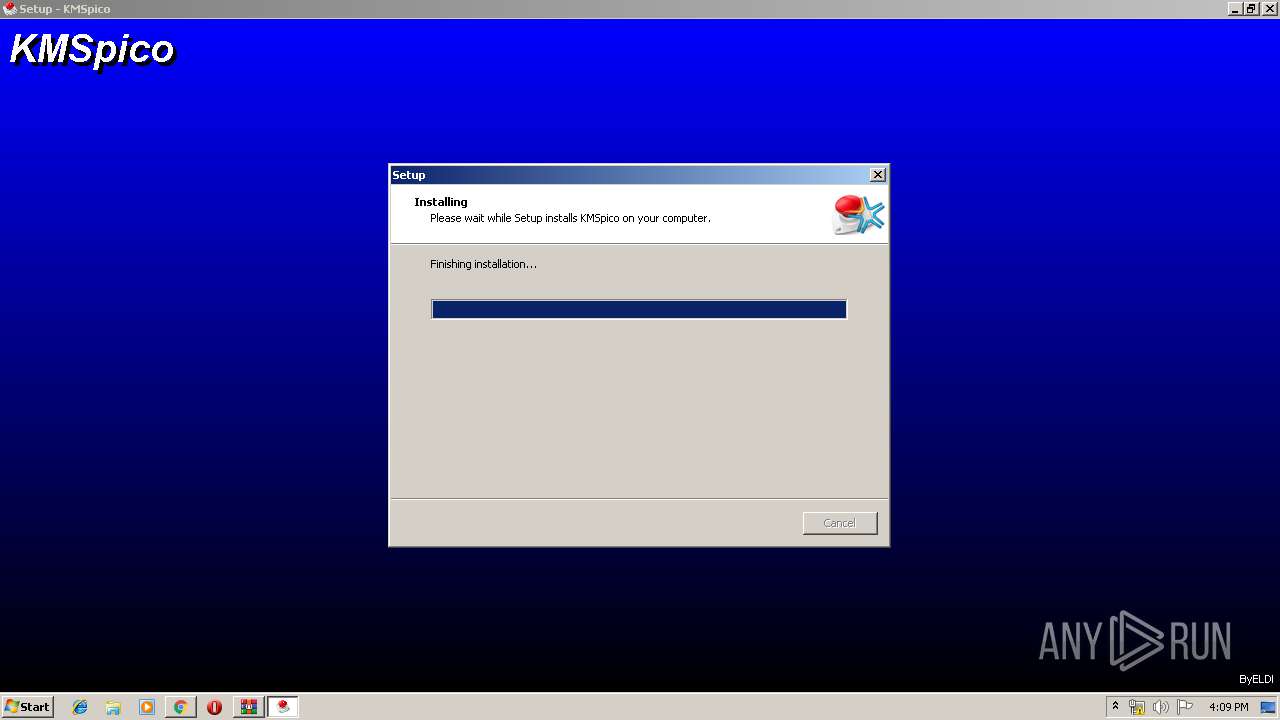
Application was dropped or rewritten from another process
- KMSpico-setup.exe (PID: 3616)
- KMSpico-setup.exe (PID: 1000)
- KMSELDI.exe (PID: 3732)
- AutoPico.exe (PID: 2928)
- UninsHs.exe (PID: 3444)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 628)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 324)
Loads dropped or rewritten executable
- KMSELDI.exe (PID: 3732)
SUSPICIOUS
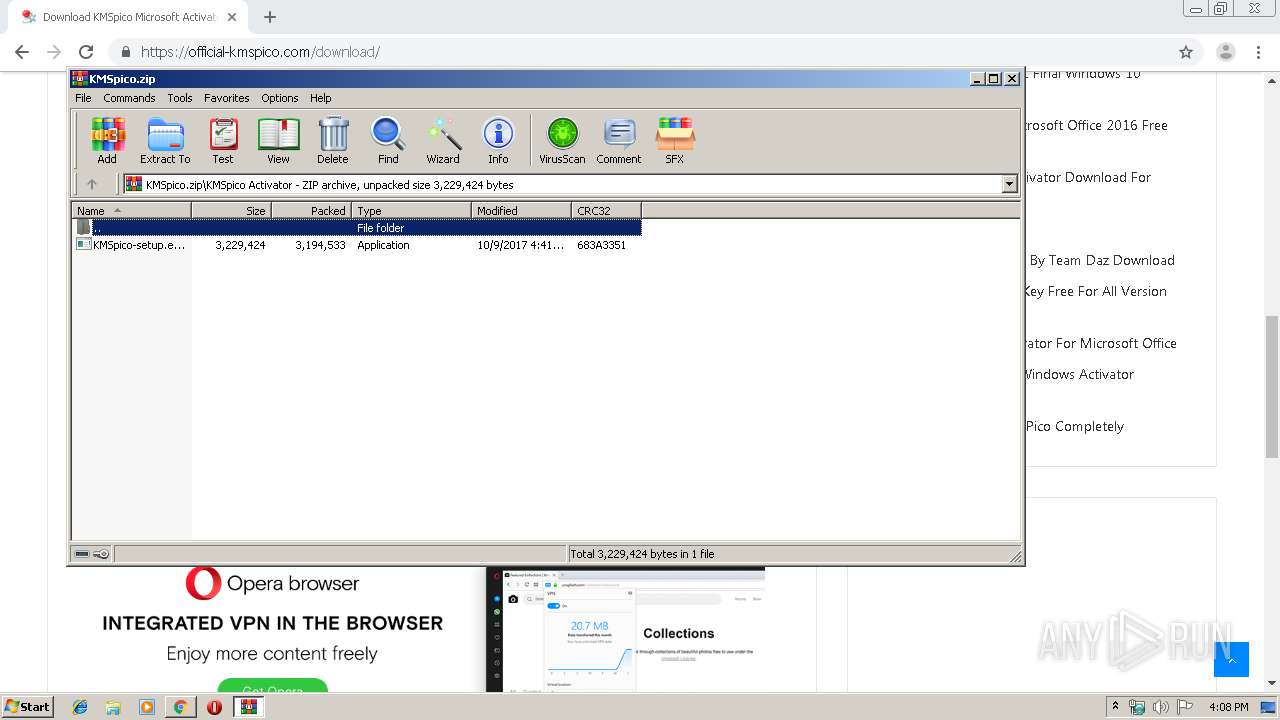
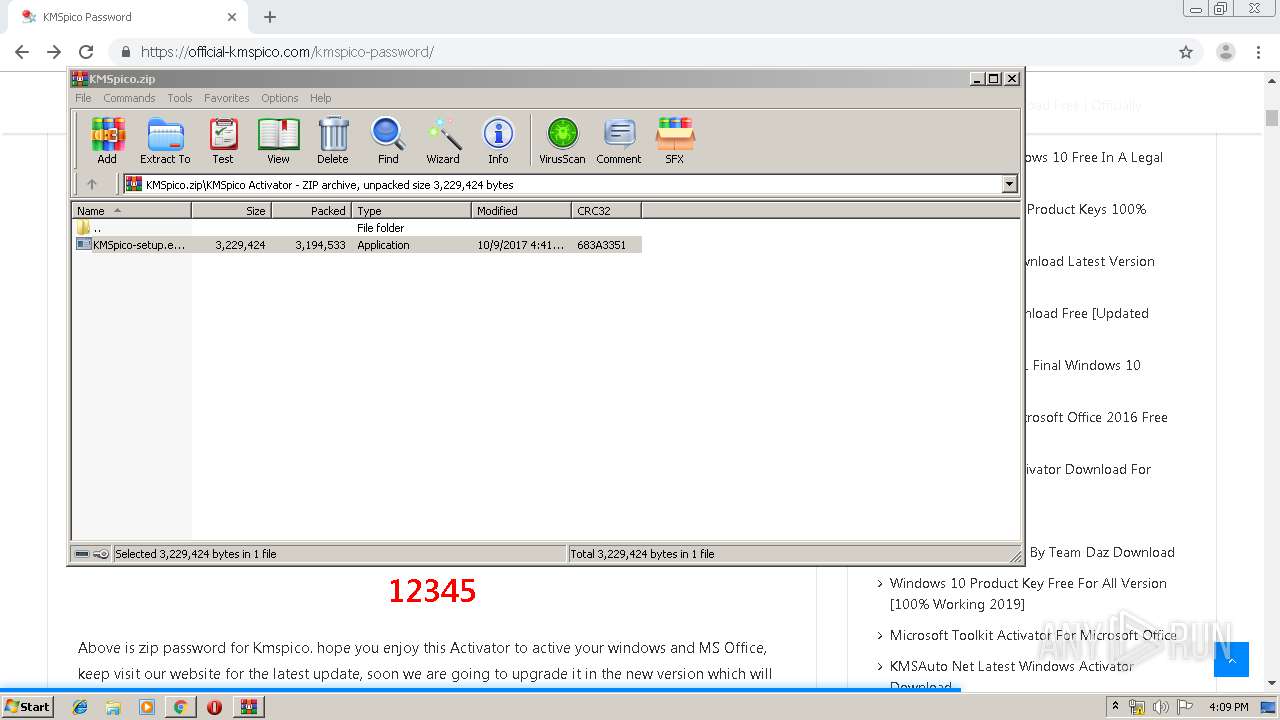
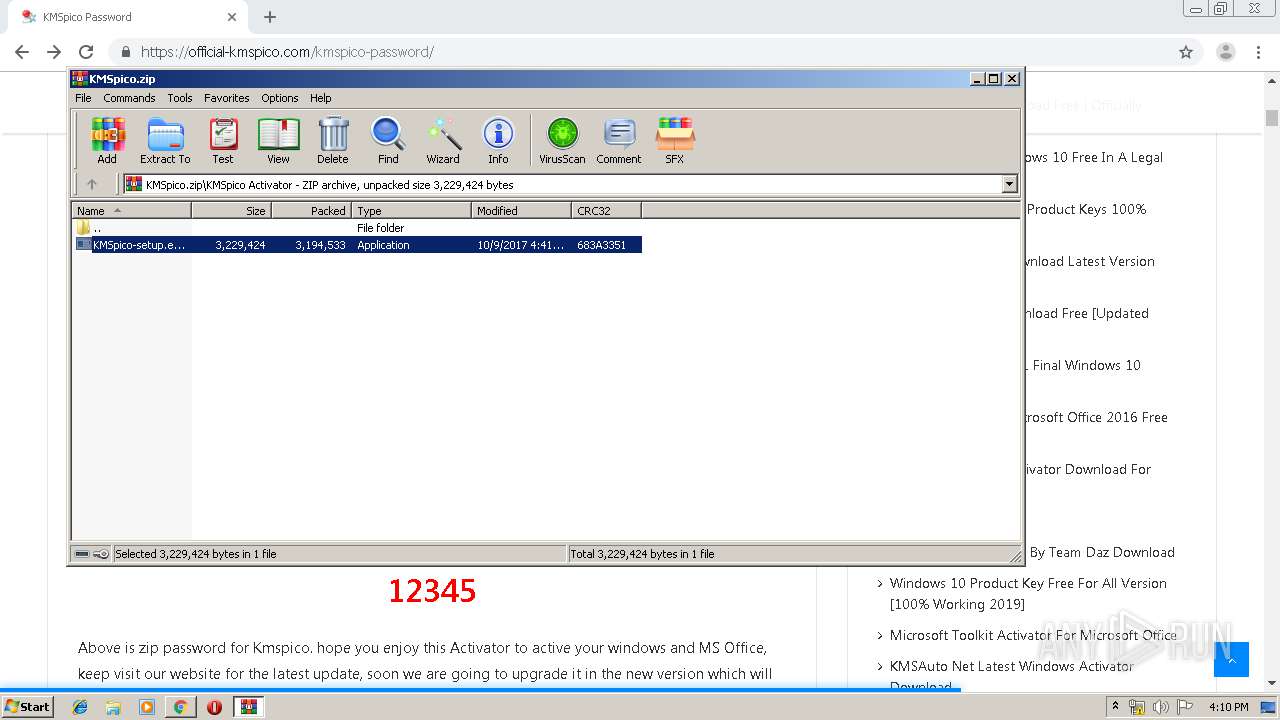
Executable content was dropped or overwritten
- KMSpico-setup.exe (PID: 3616)
- WinRAR.exe (PID: 3896)
- KMSpico-setup.exe (PID: 1000)
- KMSpico-setup.tmp (PID: 3548)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3424)
Creates files in the Windows directory
- KMSpico-setup.tmp (PID: 3548)
Modifies the phishing filter of IE
- KMSpico-setup.tmp (PID: 3548)
Starts CMD.EXE for commands execution
- KMSpico-setup.tmp (PID: 3548)
Starts SC.EXE for service management
- cmd.exe (PID: 2820)
Reads Environment values
- KMSELDI.exe (PID: 3732)
- AutoPico.exe (PID: 2928)
Creates or modifies windows services
- KMSELDI.exe (PID: 3732)
Creates files in the program directory
- KMSELDI.exe (PID: 3732)
- AutoPico.exe (PID: 2928)
INFO
Application was dropped or rewritten from another process
- KMSpico-setup.tmp (PID: 1108)
- KMSpico-setup.tmp (PID: 3548)
Changes settings of System certificates
- chrome.exe (PID: 2868)
Loads dropped or rewritten executable
- KMSpico-setup.tmp (PID: 3548)
Application launched itself
- chrome.exe (PID: 3424)
Reads Internet Cache Settings
- chrome.exe (PID: 3424)
Creates a software uninstall entry
- KMSpico-setup.tmp (PID: 3548)
Reads Microsoft Office registry keys
- KMSELDI.exe (PID: 3732)
- AutoPico.exe (PID: 2928)
Creates files in the program directory
- KMSpico-setup.tmp (PID: 3548)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
90
Monitored processes
44
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | SCHTASKS /Create /TN "AutoPico Daily Restart" /TR "'C:\Program Files\KMSpico\AutoPico.exe' /silent" /SC DAILY /ST 23:59:59 /RU "NT AUTHORITY\SYSTEM" /RL Highest /F | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 628 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Task.cmd"" | C:\Windows\system32\cmd.exe | — | KMSpico-setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4205378013265670701,9091007127673169903,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3737871387190835553 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2464 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
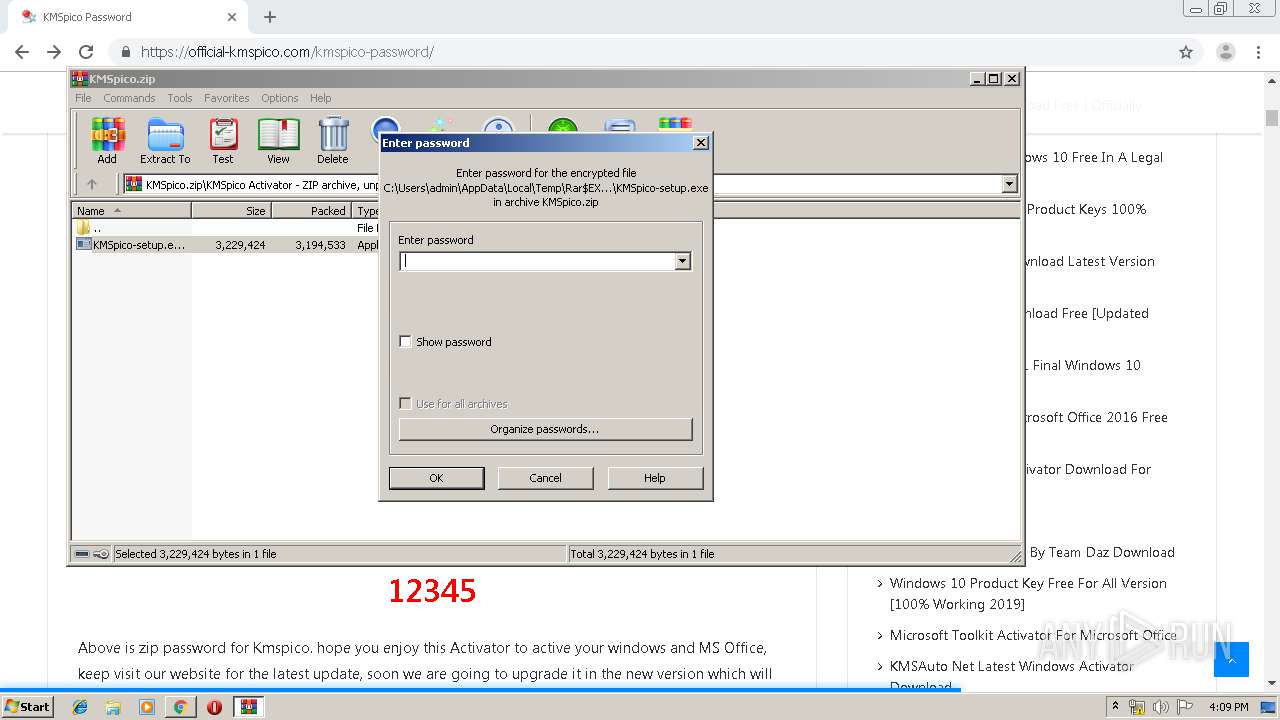
| 1000 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb3896.3747\KMSpico Activator\KMSpico-setup.exe" /SPAWNWND=$201A8 /NOTIFYWND=$40134 | C:\Users\admin\AppData\Local\Temp\Rar$EXb3896.3747\KMSpico Activator\KMSpico-setup.exe | KMSpico-setup.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: KMSpico Setup Exit code: 0 Version: 10.2.0 Modules
| |||||||||||||||
| 1108 | "C:\Users\admin\AppData\Local\Temp\is-DPT58.tmp\KMSpico-setup.tmp" /SL5="$40134,2952592,69120,C:\Users\admin\AppData\Local\Temp\Rar$EXb3896.3747\KMSpico Activator\KMSpico-setup.exe" | C:\Users\admin\AppData\Local\Temp\is-DPT58.tmp\KMSpico-setup.tmp | — | KMSpico-setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4205378013265670701,9091007127673169903,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13440918929410074146 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1684 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4205378013265670701,9091007127673169903,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8342313191586760953 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2352 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fdea9d0,0x6fdea9e0,0x6fdea9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4205378013265670701,9091007127673169903,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4384971668360292968 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2548 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,4205378013265670701,9091007127673169903,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2241105738762848095 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2196 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 166
Read events
2 021
Write events
135
Delete events
10
Modification events
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3304) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3424-13211824079633000 |
Value: 259 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3424) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
13
Suspicious files
166
Text files
632
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\afc0b4d9-c600-4f44-8547-675d209aab5f.tmp | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF169743.TMP | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF1697a1.TMP | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3424 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
107
DNS requests
60
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2868 | chrome.exe | GET | 200 | 91.199.212.52:80 | http://crt.usertrust.com/USERTrustRSAAddTrustCA.crt | GB | der | 1.37 Kb | whitelisted |
2868 | chrome.exe | GET | 302 | 216.58.210.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
2868 | chrome.exe | GET | 200 | 74.125.168.9:80 | http://r4---sn-q0cedn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=78.153.204.5&mm=28&mn=sn-q0cedn7s&ms=nvh&mt=1567350442&mv=m&mvi=3&pl=19&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2868 | chrome.exe | 172.217.23.130:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 192.0.77.32:443 | s0.wp.com | Automattic, Inc | US | suspicious |
2868 | chrome.exe | 192.0.73.2:443 | secure.gravatar.com | Automattic, Inc | US | whitelisted |
2868 | chrome.exe | 192.0.76.3:443 | stats.wp.com | Automattic, Inc | US | suspicious |
2868 | chrome.exe | 172.217.16.174:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 216.58.206.22:443 | i.ytimg.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 172.217.22.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
2868 | chrome.exe | 74.125.133.157:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2868 | chrome.exe | 172.217.22.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
official-kmspico.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
c0.wp.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
s0.wp.com |
| whitelisted |
secure.gravatar.com |
| whitelisted |
stats.wp.com |
| whitelisted |