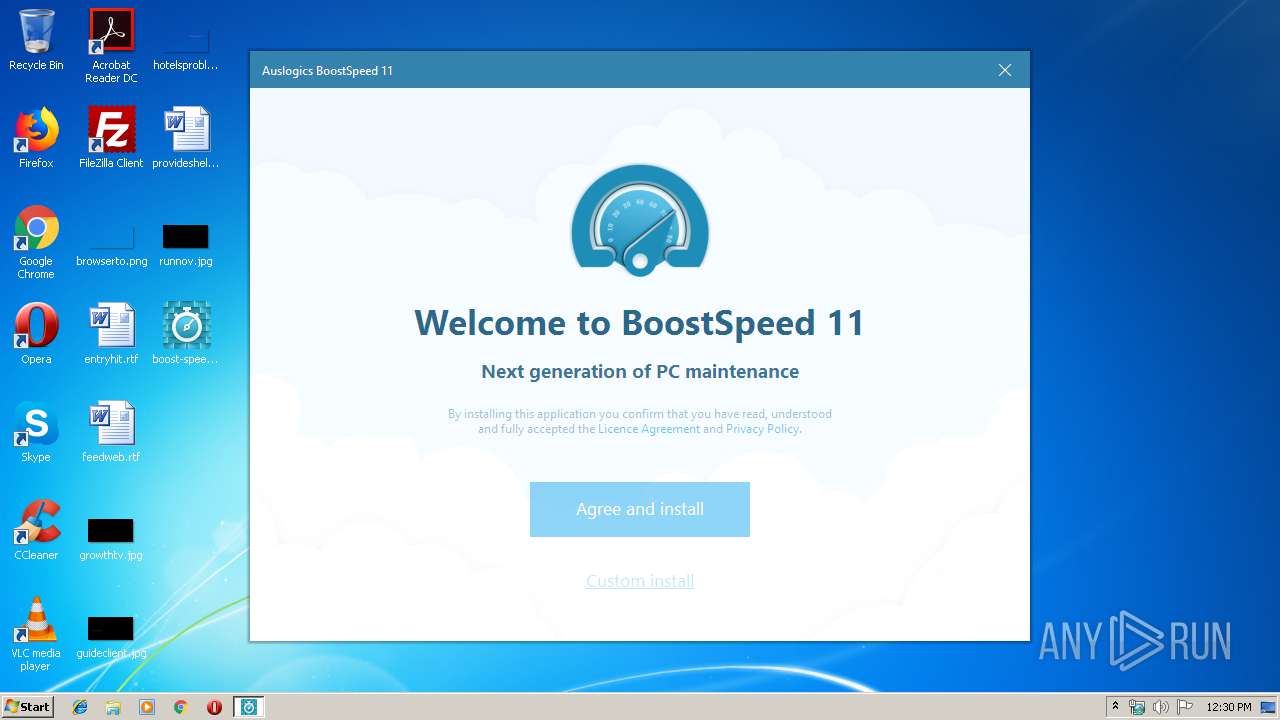
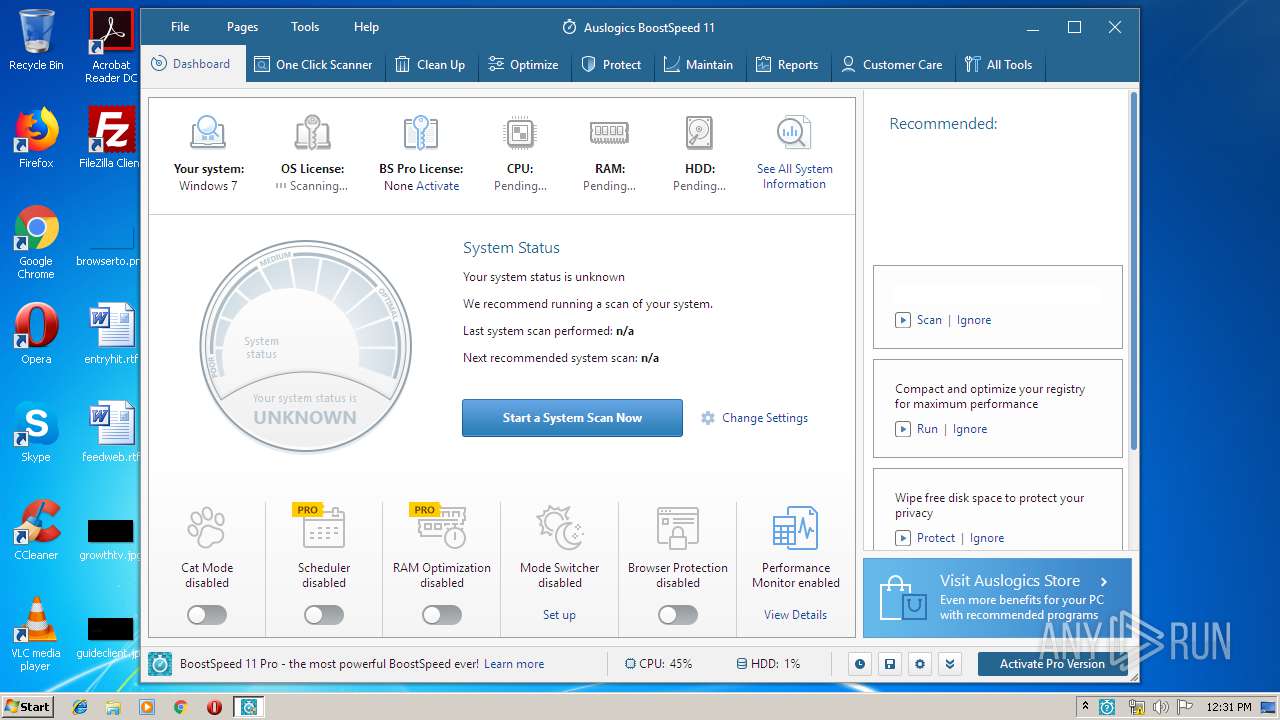
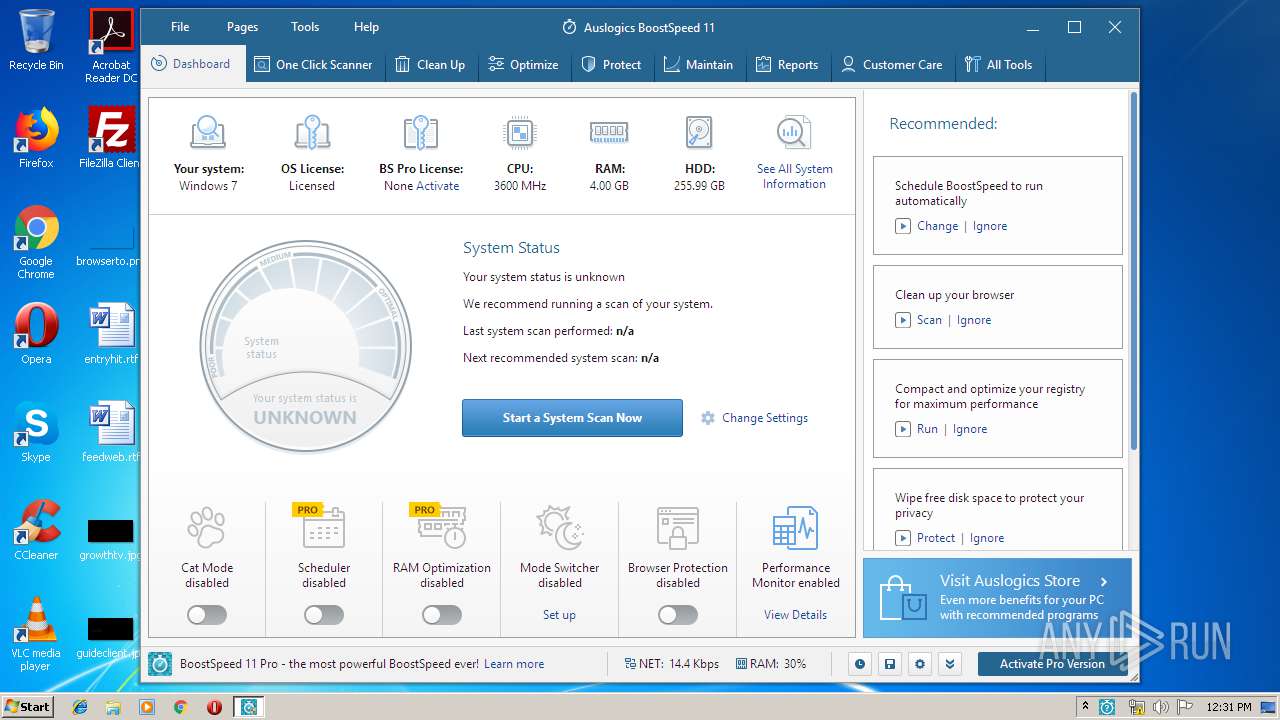
| download: | boost-speed-setup.exe |
| Full analysis: | https://app.any.run/tasks/309e0d89-45ac-4da3-835d-fd50ef5d3749 |
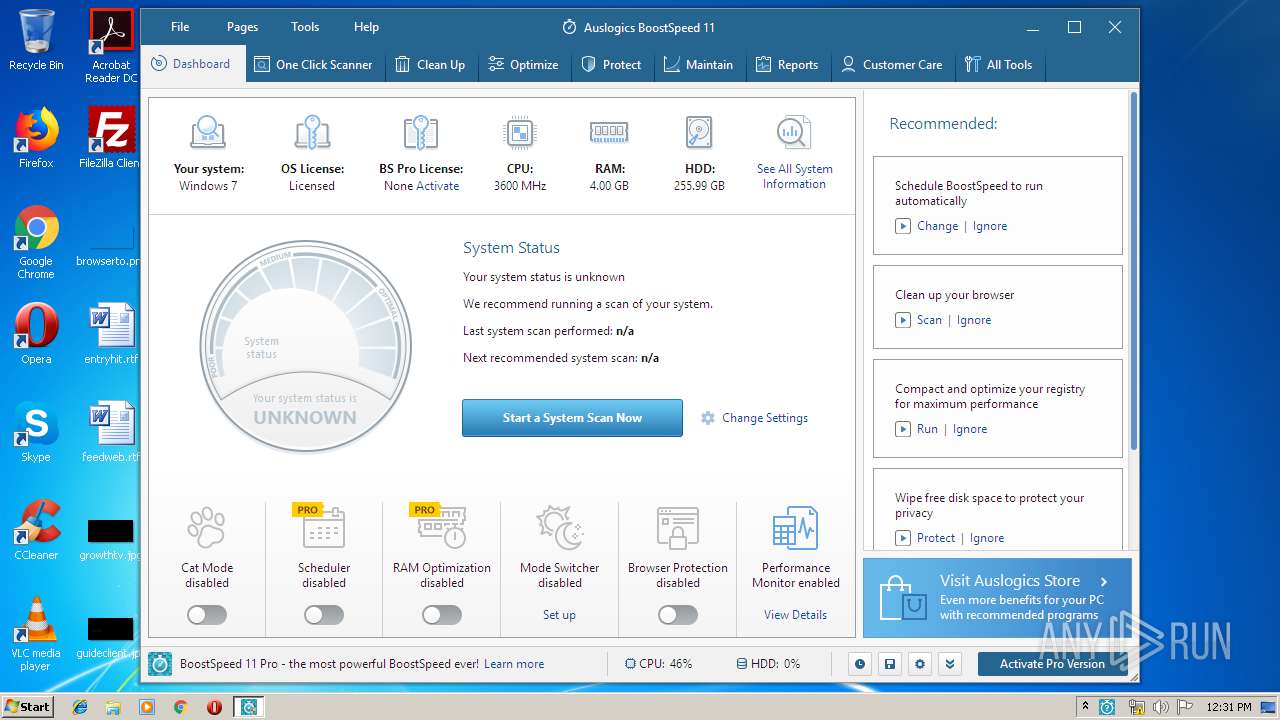
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 11:29:01 |
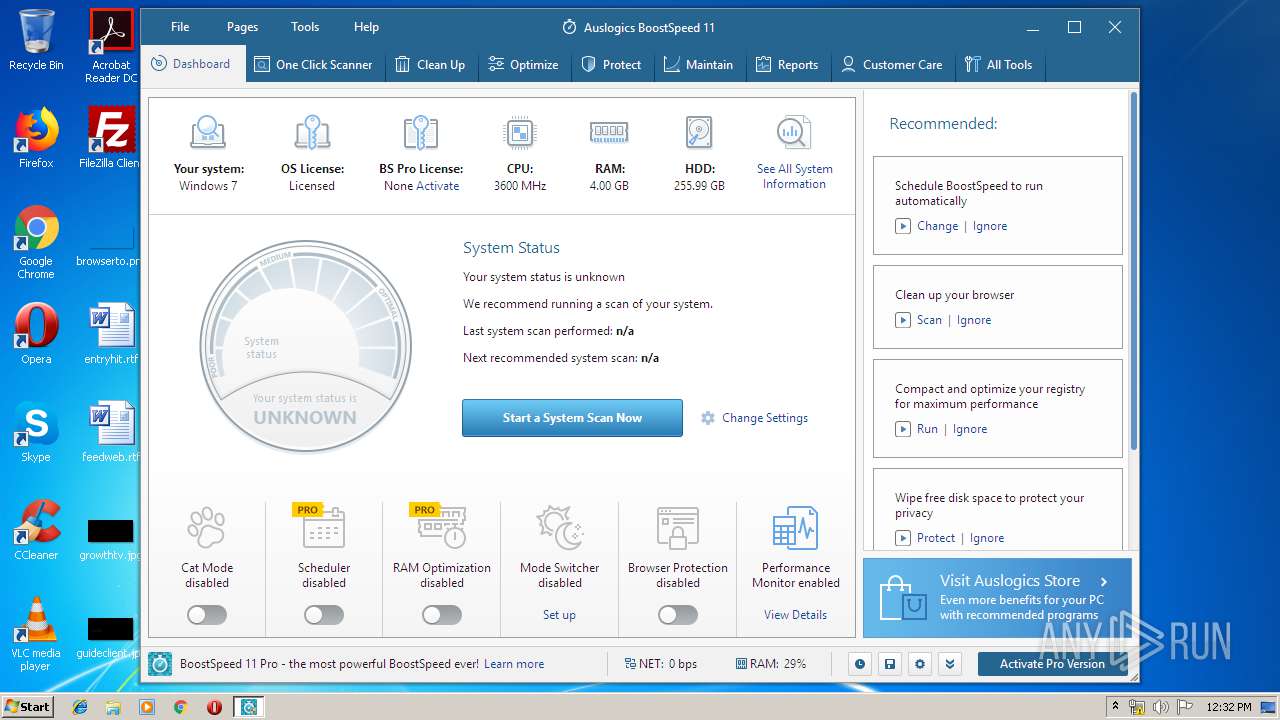
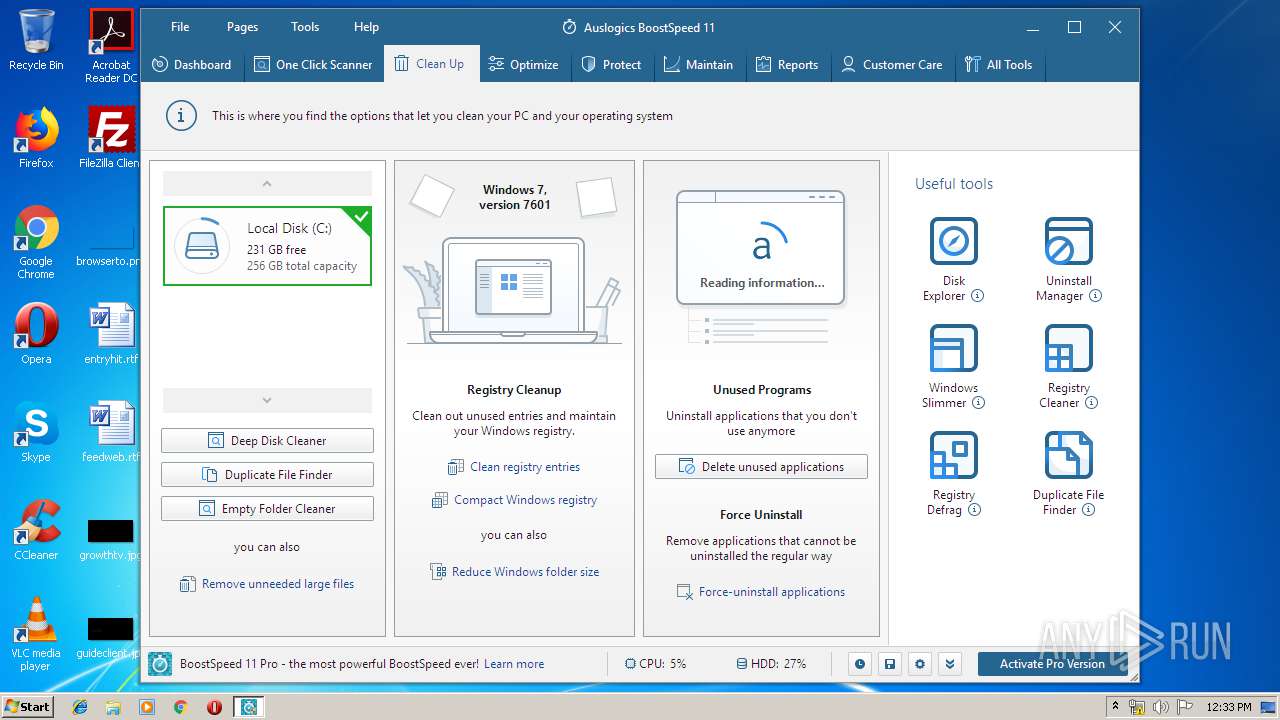
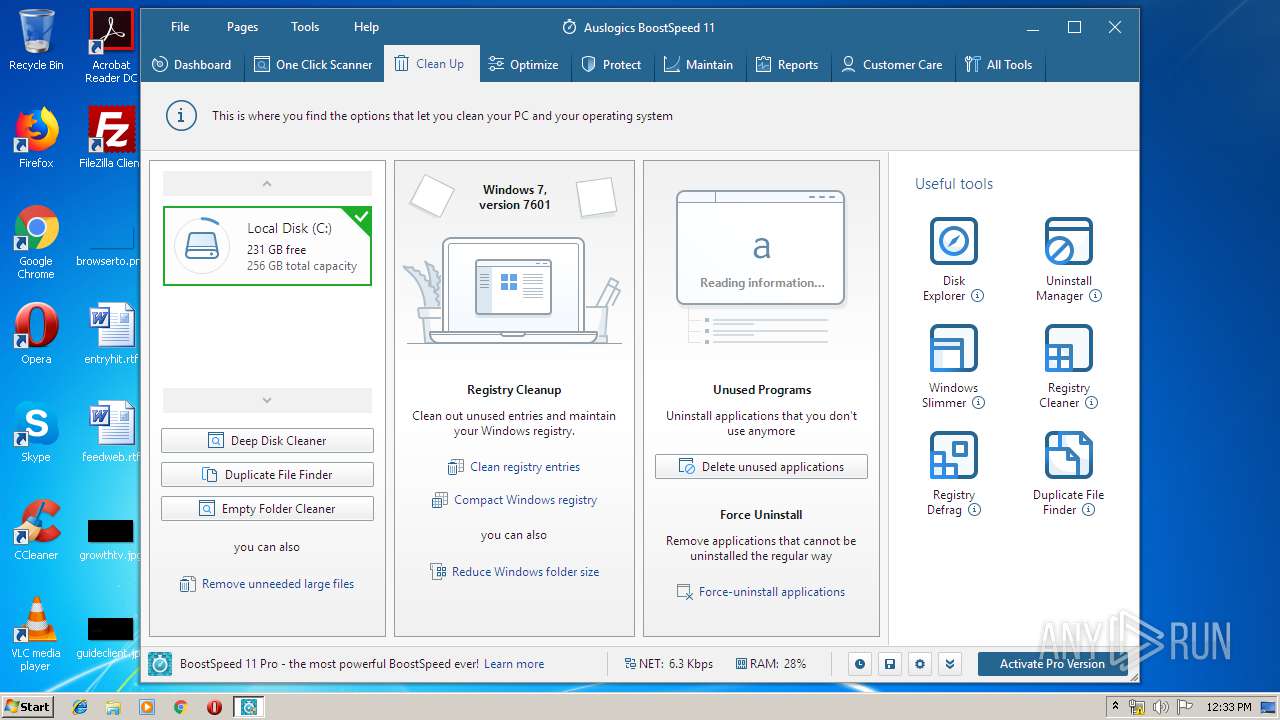
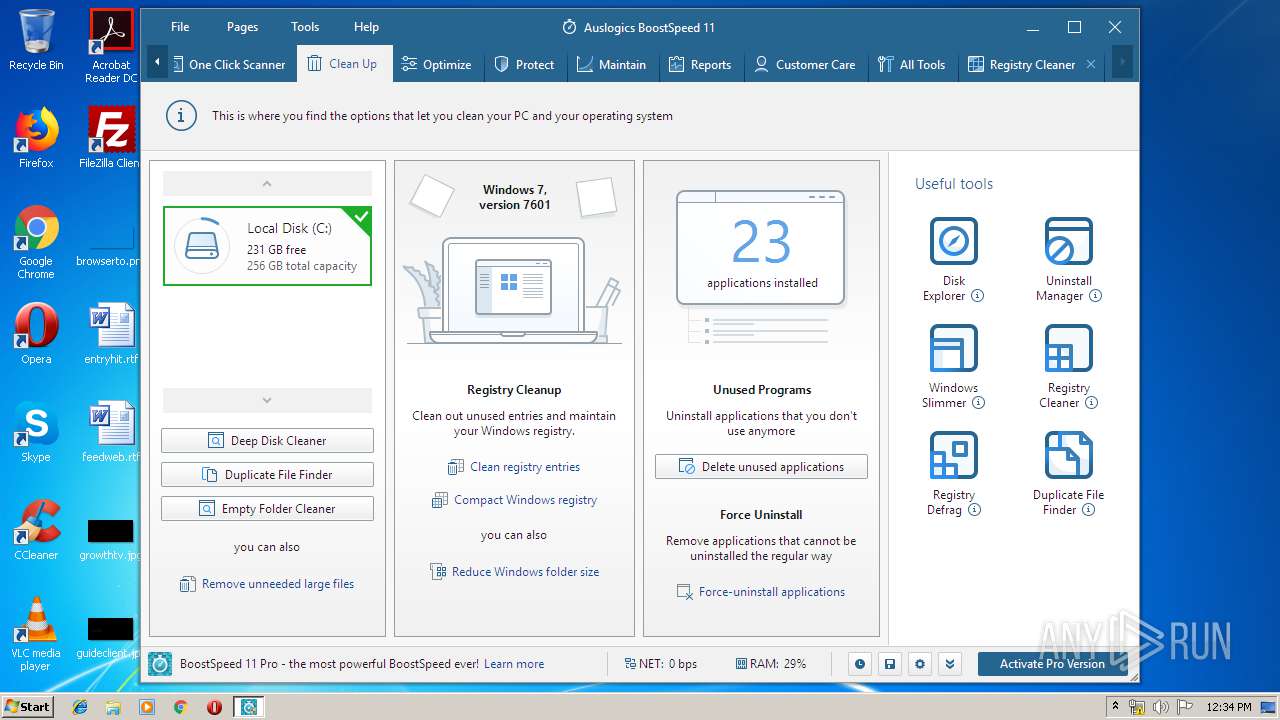
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | FBE4BDDB1CAD9B947FAEA380842425EC |
| SHA1: | DA6B1376BD31E59C3D8BB7E14819CE5EE65589C4 |
| SHA256: | 1776D7738B93E1E49B952638D23EE52C597FA6146B845B114860B14B05ACAE8B |
| SSDEEP: | 393216:O5oyqsih+lX6OYBYqBHPw708RwGlb5aK3jYGiPzHPmG81KdgX3D//kE5yMYwf0pp:olX6OYWqM2Glb5agiPzHed2U//V5/vuf |
MALICIOUS
Changes settings of System certificates
- boost-speed-setup.tmp (PID: 3240)
- Integrator.exe (PID: 2444)
- tabcleanup.exe (PID: 3984)
Registers / Runs the DLL via REGSVR32.EXE
- boost-speed-setup.tmp (PID: 3240)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3872)
- regsvr32.exe (PID: 2972)
- regsvr32.exe (PID: 2568)
- Integrator.exe (PID: 2444)
- Integrator.exe (PID: 3452)
- DiskDefrag.exe (PID: 4008)
- taboptimize.exe (PID: 3436)
- tabprotect.exe (PID: 2540)
- tabreports.exe (PID: 2884)
- tabcarecenter.exe (PID: 3652)
- taballtools.exe (PID: 2788)
- tabdashboard.exe (PID: 3128)
- taboneclickscanner.exe (PID: 3256)
- tabcleanup.exe (PID: 3984)
- tabmaintain.exe (PID: 4060)
- DllHost.exe (PID: 2768)
- TabOneClickScanner.exe (PID: 3316)
- TrustedInstaller.exe (PID: 4092)
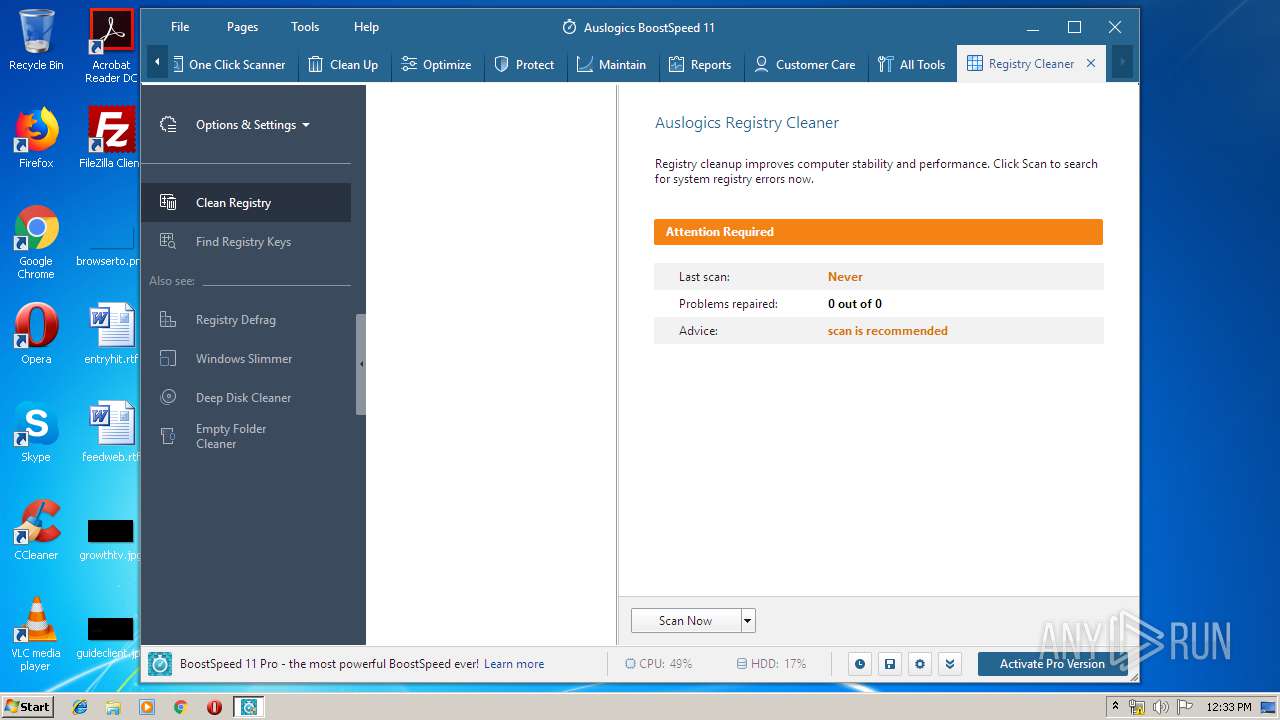
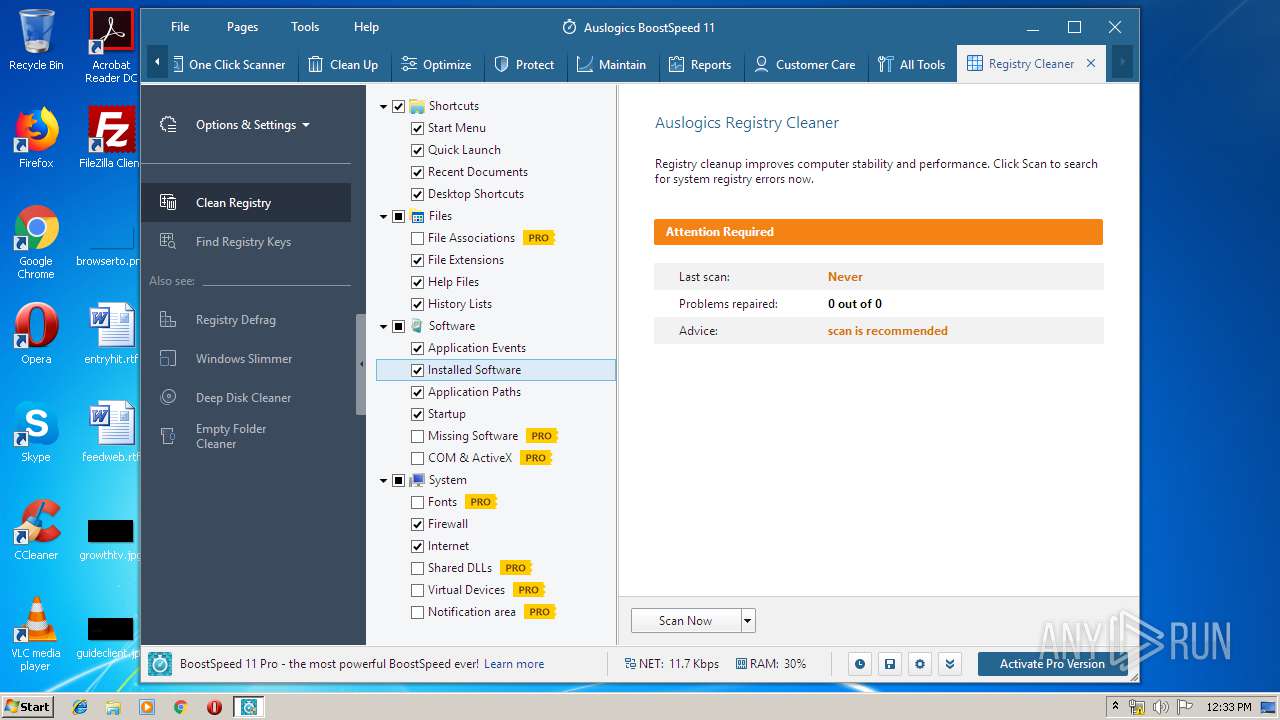
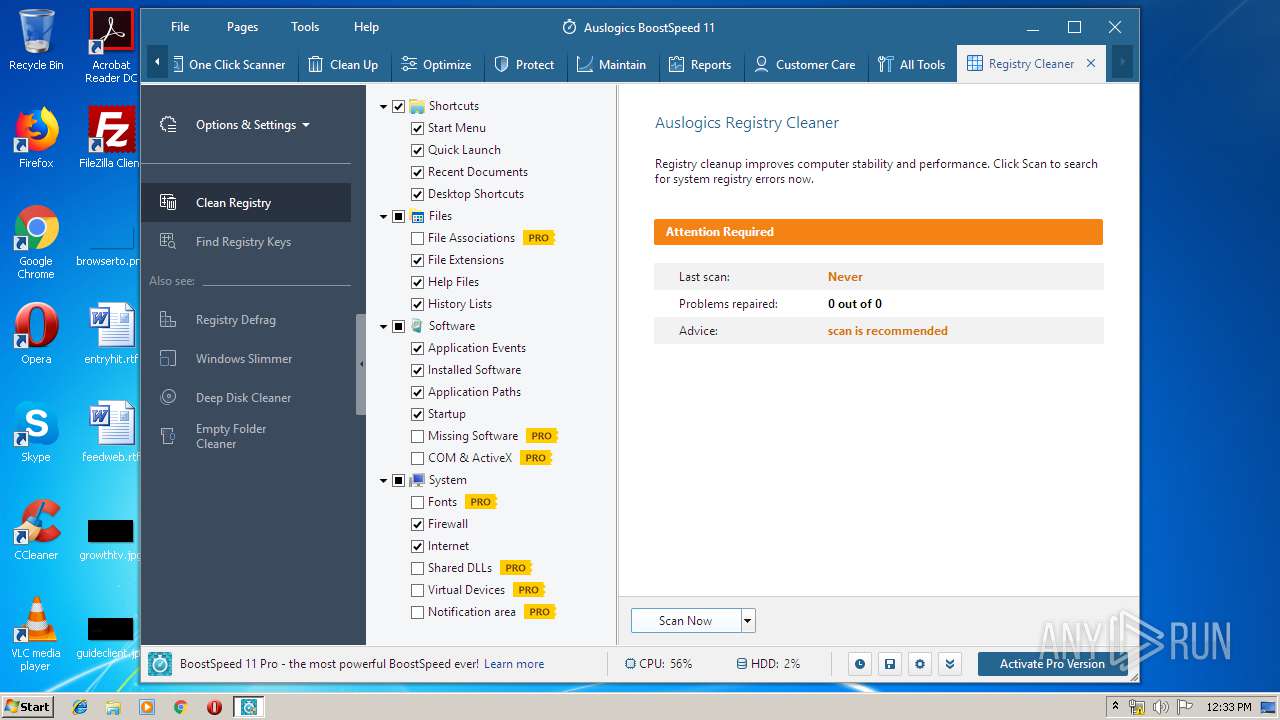
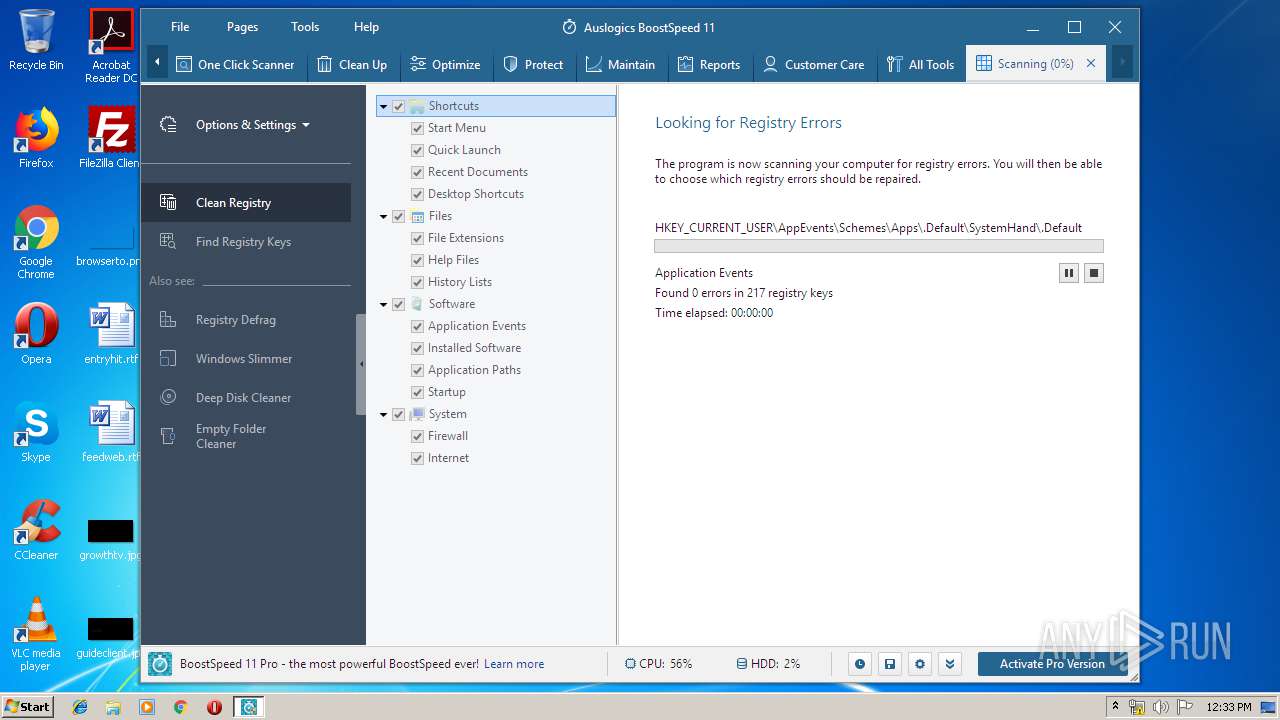
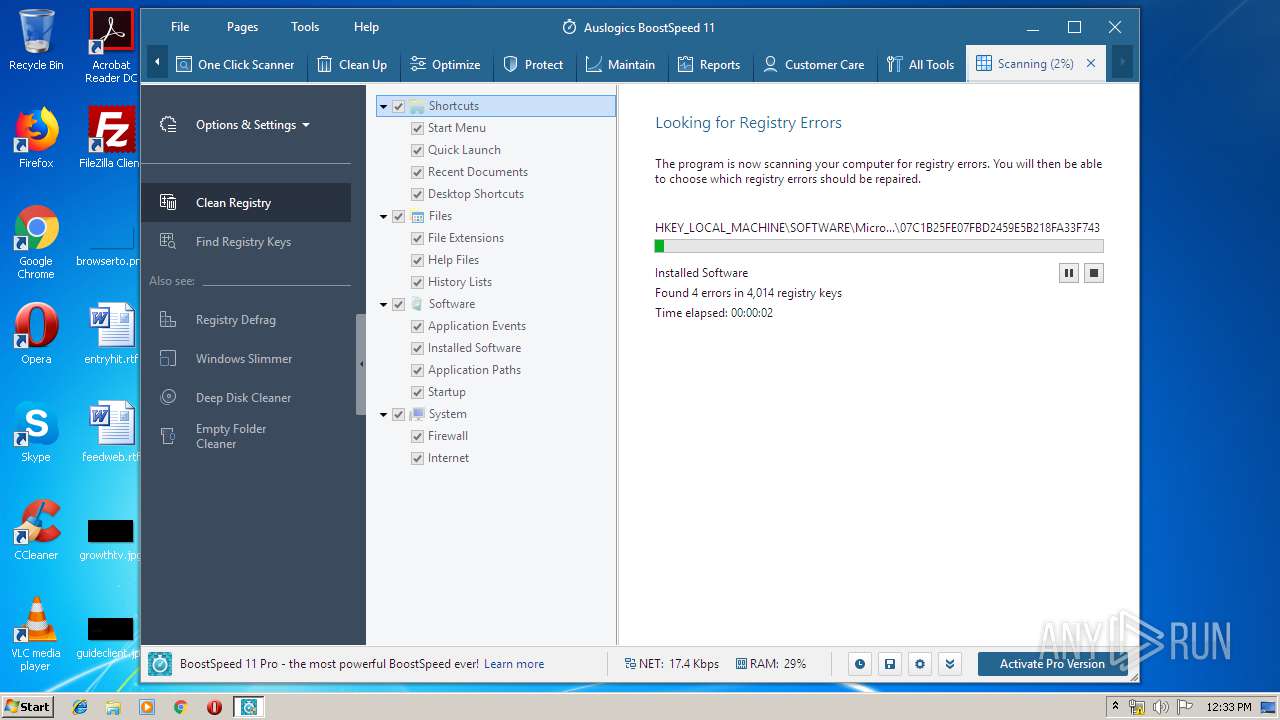
- registrycleaner.exe (PID: 2864)
- dismhost.exe (PID: 4004)
- DISM.exe (PID: 3448)
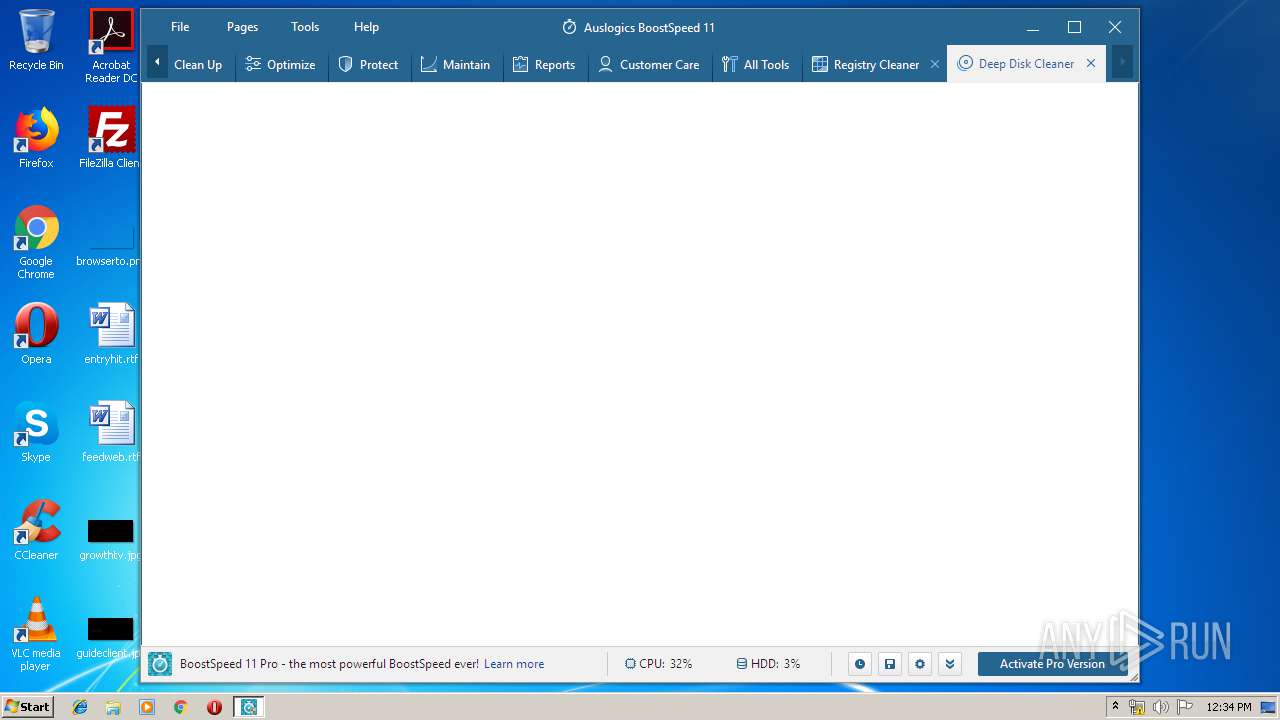
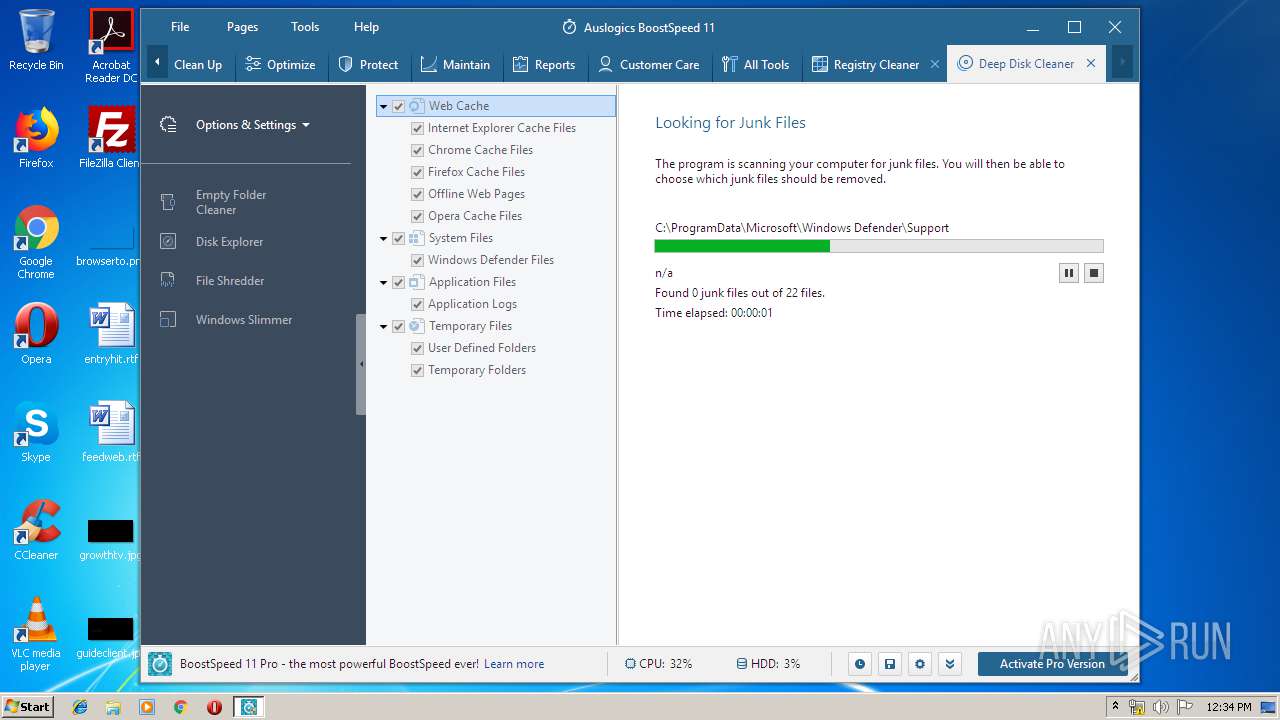
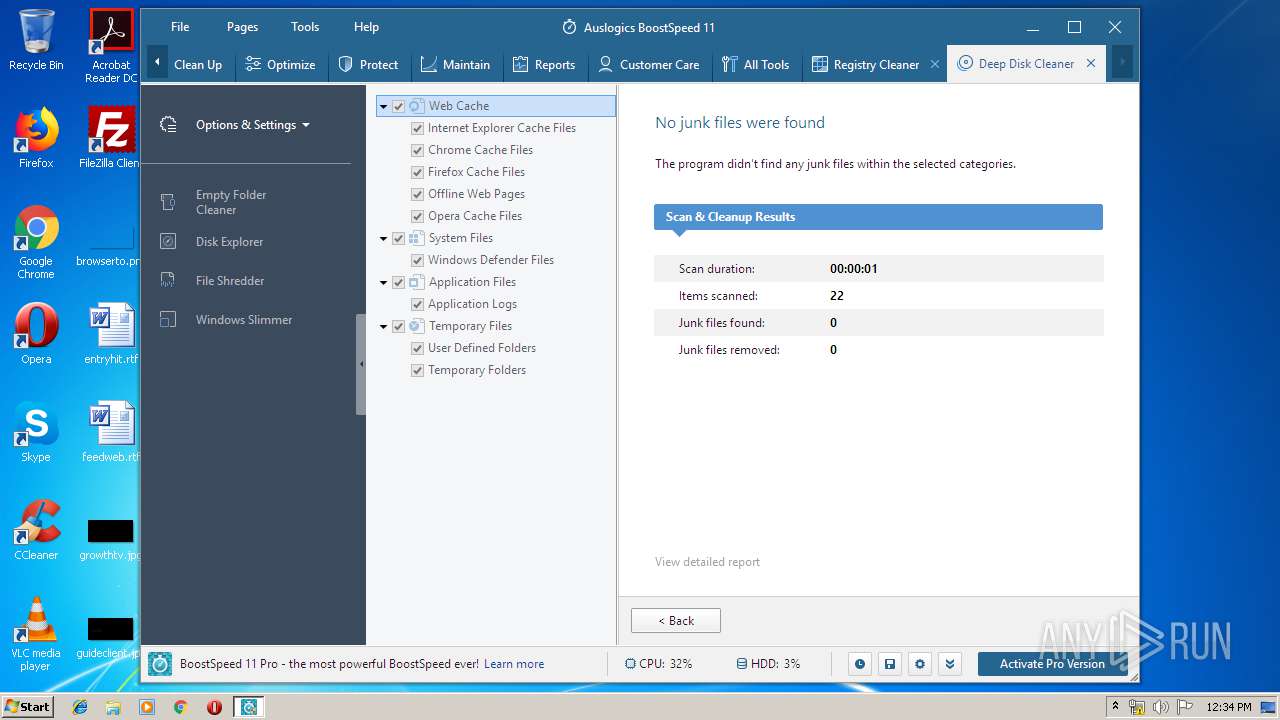
- DeepDiskCleaner.exe (PID: 2420)
- TabMaintain.exe (PID: 756)
Application was dropped or rewritten from another process
- Integrator.exe (PID: 2444)
- DiskDefrag.exe (PID: 4008)
- Integrator.exe (PID: 3452)
- tabcleanup.exe (PID: 3984)
- tabcarecenter.exe (PID: 3652)
- tabmaintain.exe (PID: 4060)
- taboptimize.exe (PID: 3436)
- tabprotect.exe (PID: 2540)
- taballtools.exe (PID: 2788)
- tabreports.exe (PID: 2884)
- taboneclickscanner.exe (PID: 3256)
- tabdashboard.exe (PID: 3128)
- TabOneClickScanner.exe (PID: 3316)
- dismhost.exe (PID: 4004)
- registrycleaner.exe (PID: 2864)
- DeepDiskCleaner.exe (PID: 2420)
- TabMaintain.exe (PID: 756)
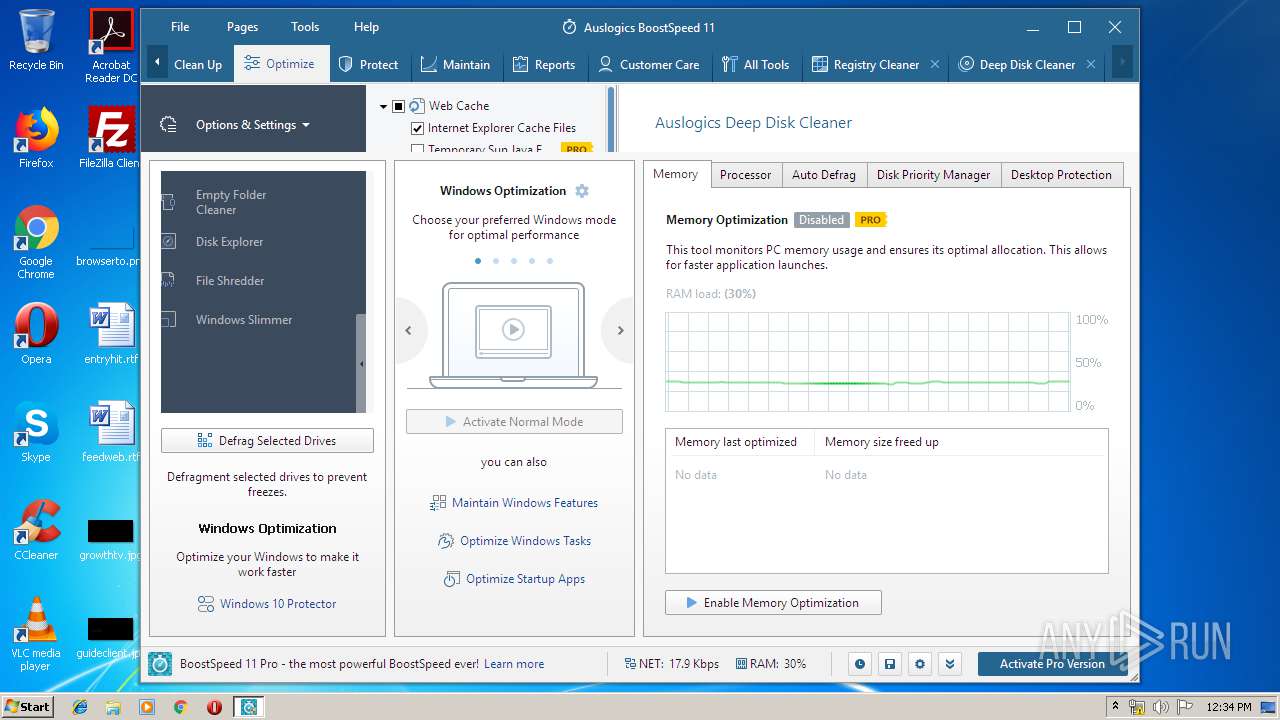
Loads the Task Scheduler COM API
- Integrator.exe (PID: 2444)
- DiskDefrag.exe (PID: 4008)
- Integrator.exe (PID: 3452)
- tabdashboard.exe (PID: 3128)
- taboptimize.exe (PID: 3436)
Loads the Task Scheduler DLL interface
- taboneclickscanner.exe (PID: 3256)
- registrycleaner.exe (PID: 2864)
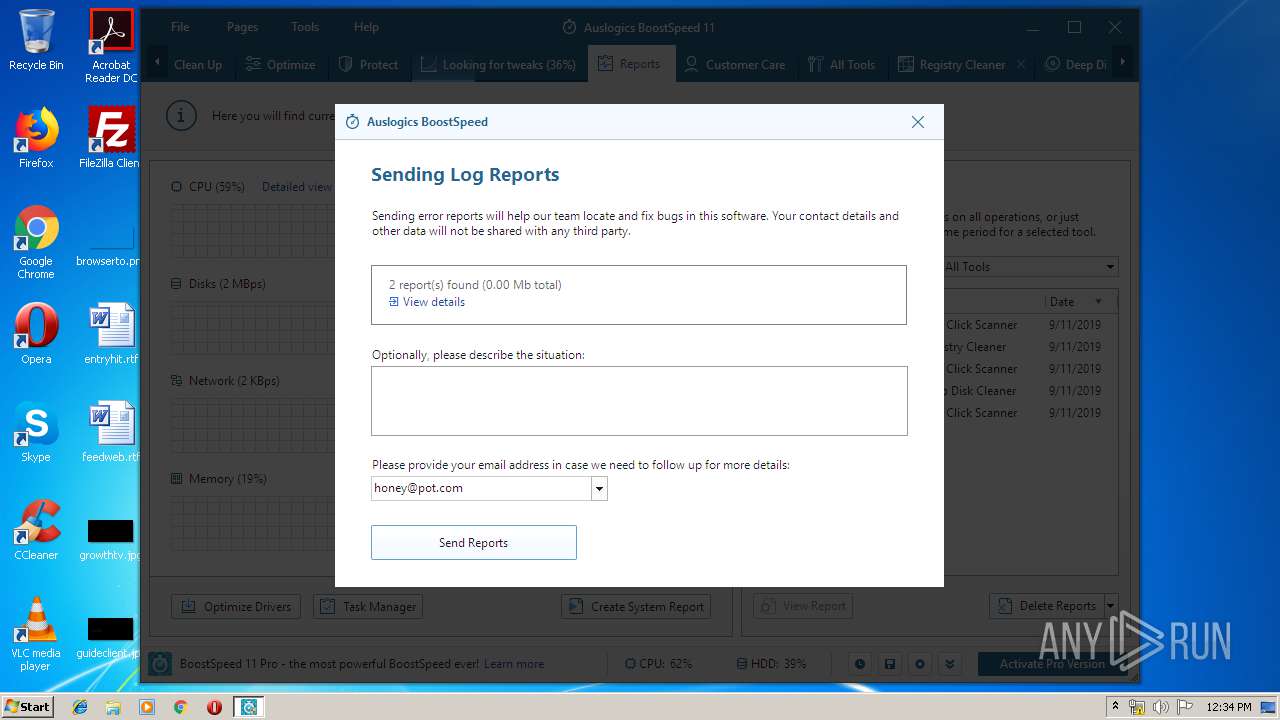
Actions looks like stealing of personal data
- tabprotect.exe (PID: 2540)
SUSPICIOUS
Executable content was dropped or overwritten
- boost-speed-setup.exe (PID: 2928)
- boost-speed-setup.exe (PID: 2644)
- boost-speed-setup.tmp (PID: 3240)
- DISM.exe (PID: 3448)
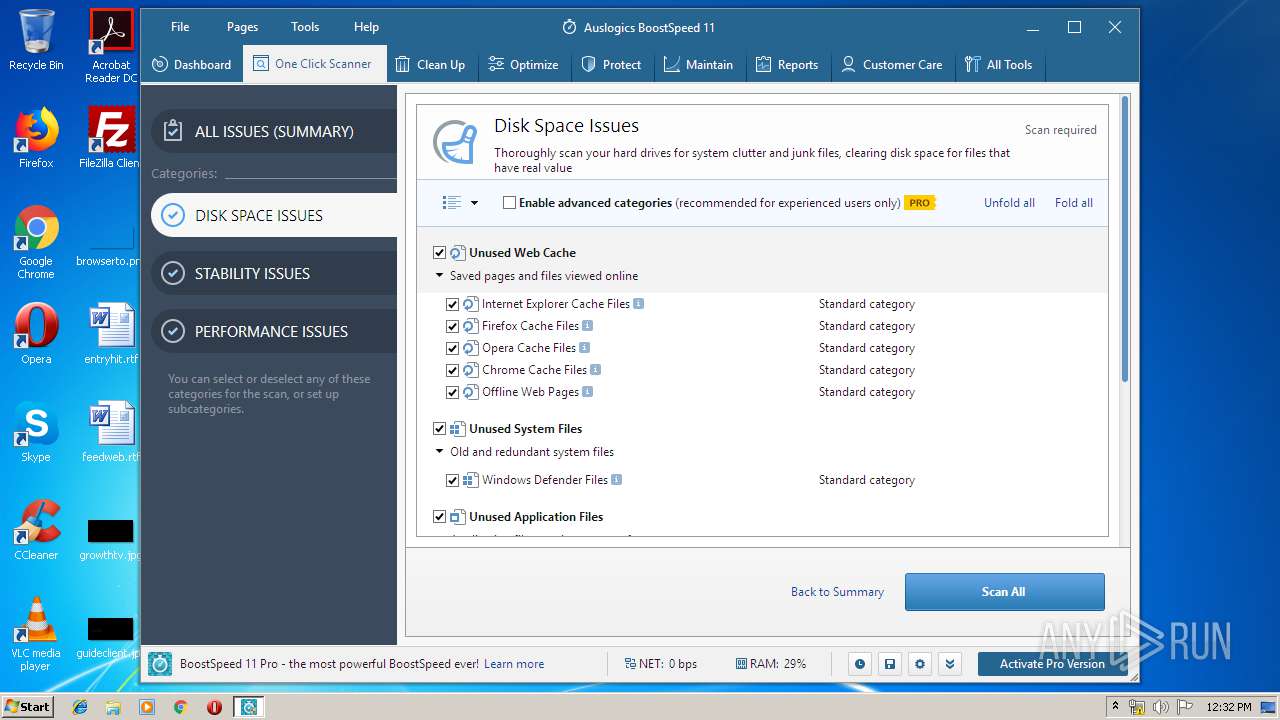
Reads the cookies of Mozilla Firefox
- boost-speed-setup.tmp (PID: 3240)
Reads the cookies of Google Chrome
- boost-speed-setup.tmp (PID: 3240)
Creates files in the user directory
- boost-speed-setup.tmp (PID: 3240)
- Integrator.exe (PID: 2444)
Reads Windows owner or organization settings
- boost-speed-setup.tmp (PID: 3240)
Reads the Windows organization settings
- boost-speed-setup.tmp (PID: 3240)
Creates COM task schedule object
- regsvr32.exe (PID: 3872)
- regsvr32.exe (PID: 2972)
- regsvr32.exe (PID: 2568)
Adds / modifies Windows certificates
- Integrator.exe (PID: 2444)
- boost-speed-setup.tmp (PID: 3240)
- tabcleanup.exe (PID: 3984)
Reads Windows Product ID
- Integrator.exe (PID: 2444)
- DiskDefrag.exe (PID: 4008)
- Integrator.exe (PID: 3452)
- tabdashboard.exe (PID: 3128)
- tabcleanup.exe (PID: 3984)
- tabreports.exe (PID: 2884)
- taballtools.exe (PID: 2788)
- tabprotect.exe (PID: 2540)
- tabmaintain.exe (PID: 4060)
- taboneclickscanner.exe (PID: 3256)
- taboptimize.exe (PID: 3436)
- tabcarecenter.exe (PID: 3652)
- boost-speed-setup.tmp (PID: 3240)
- TabOneClickScanner.exe (PID: 3316)
- registrycleaner.exe (PID: 2864)
- TabMaintain.exe (PID: 756)
- DeepDiskCleaner.exe (PID: 2420)
Reads the machine GUID from the registry
- Integrator.exe (PID: 2444)
- DiskDefrag.exe (PID: 4008)
- Integrator.exe (PID: 3452)
- tabcleanup.exe (PID: 3984)
- tabreports.exe (PID: 2884)
- tabdashboard.exe (PID: 3128)
- taboneclickscanner.exe (PID: 3256)
- taballtools.exe (PID: 2788)
- tabprotect.exe (PID: 2540)
- tabcarecenter.exe (PID: 3652)
- taboptimize.exe (PID: 3436)
- tabmaintain.exe (PID: 4060)
- boost-speed-setup.tmp (PID: 3240)
- TabOneClickScanner.exe (PID: 3316)
- registrycleaner.exe (PID: 2864)
- TabMaintain.exe (PID: 756)
- DeepDiskCleaner.exe (PID: 2420)
Reads the BIOS version
- Integrator.exe (PID: 3452)
- tabcarecenter.exe (PID: 3652)
- taboptimize.exe (PID: 3436)
- tabdashboard.exe (PID: 3128)
- taboneclickscanner.exe (PID: 3256)
- registrycleaner.exe (PID: 2864)
Low-level read access rights to disk partition
- Integrator.exe (PID: 3452)
- tabcleanup.exe (PID: 3984)
- tabmaintain.exe (PID: 4060)
- taboptimize.exe (PID: 3436)
- tabdashboard.exe (PID: 3128)
- DeepDiskCleaner.exe (PID: 2420)
Creates files in the program directory
- tabmaintain.exe (PID: 4060)
- tabcarecenter.exe (PID: 3652)
- tabprotect.exe (PID: 2540)
- taboptimize.exe (PID: 3436)
- Integrator.exe (PID: 3452)
- taboneclickscanner.exe (PID: 3256)
- registrycleaner.exe (PID: 2864)
- DeepDiskCleaner.exe (PID: 2420)
Executed via COM
- DllHost.exe (PID: 2768)
Reads Internet Cache Settings
- Integrator.exe (PID: 3452)
- tabcarecenter.exe (PID: 3652)
- DeepDiskCleaner.exe (PID: 2420)
- tabmaintain.exe (PID: 4060)
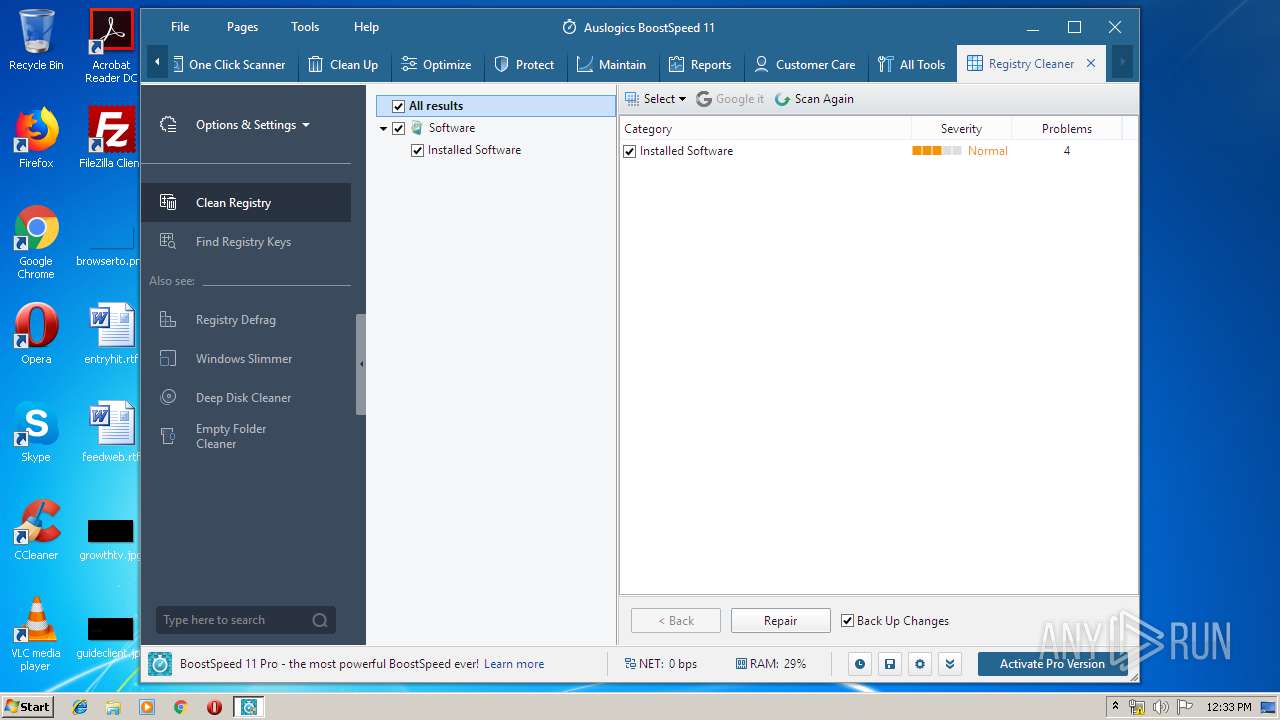
Searches for installed software
- taboptimize.exe (PID: 3436)
- Integrator.exe (PID: 3452)
- tabmaintain.exe (PID: 4060)
- taboneclickscanner.exe (PID: 3256)
- tabcleanup.exe (PID: 3984)
- DeepDiskCleaner.exe (PID: 2420)
- registrycleaner.exe (PID: 2864)
Reads Microsoft Outlook installation path
- taboneclickscanner.exe (PID: 3256)
- registrycleaner.exe (PID: 2864)
Removes files from Windows directory
- taboneclickscanner.exe (PID: 3256)
Creates a software uninstall entry
- tabcleanup.exe (PID: 3984)
- taboneclickscanner.exe (PID: 3256)
Creates files in the Windows directory
- TrustedInstaller.exe (PID: 4092)
- tabmaintain.exe (PID: 4060)
Reads mouse settings
- tabmaintain.exe (PID: 4060)
Uses NETSH.EXE for network configuration
- tabmaintain.exe (PID: 4060)
INFO
Application was dropped or rewritten from another process
- boost-speed-setup.tmp (PID: 3240)
- boost-speed-setup.tmp (PID: 3948)
- reader.exe (PID: 2584)
Dropped object may contain Bitcoin addresses
- boost-speed-setup.tmp (PID: 3240)
Loads dropped or rewritten executable
- boost-speed-setup.tmp (PID: 3240)
Creates files in the program directory
- boost-speed-setup.tmp (PID: 3240)
Creates a software uninstall entry
- boost-speed-setup.tmp (PID: 3240)
Reads settings of System Certificates
- tabdashboard.exe (PID: 3128)
Reads Microsoft Office registry keys
- taboneclickscanner.exe (PID: 3256)
- tabmaintain.exe (PID: 4060)
- taboptimize.exe (PID: 3436)
- Integrator.exe (PID: 3452)
- registrycleaner.exe (PID: 2864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:04:06 16:39:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 438272 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x117dc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 11.0.1.2 |
| ProductVersionNumber: | 11.0.1.2 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Auslogics |
| FileDescription: | Auslogics BoostSpeed Installation File |
| FileVersion: | 11.x |
| LegalCopyright: | Copyright © 2008-2019 Auslogics Labs Pty Ltd |
| ProductName: | Auslogics BoostSpeed |
| ProductVersion: | 11.0.1.2 |
| OriginalFileName: | boost-speed-setup.exe |
| InternalName: | boost-speed-setup |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Apr-2016 14:39:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Auslogics |
| FileDescription: | Auslogics BoostSpeed Installation File |
| FileVersion: | 11.x |
| LegalCopyright: | Copyright © 2008-2019 Auslogics Labs Pty Ltd |
| ProductName: | Auslogics BoostSpeed |
| ProductVersion: | 11.0.1.2 |
| OriginalFilename: | boost-speed-setup.exe |
| InternalName: | boost-speed-setup |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Apr-2016 14:39:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F244 | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37521 |
.itext | 0x00011000 | 0x00000F64 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.7322 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.29672 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00068F68 | 0x00069000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.46287 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.04236 | 1720 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.92044 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.43388 | 2848 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.30676 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 6.40418 | 4936 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 6.37889 | 6760 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 6.33423 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 6.39285 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 6.35555 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
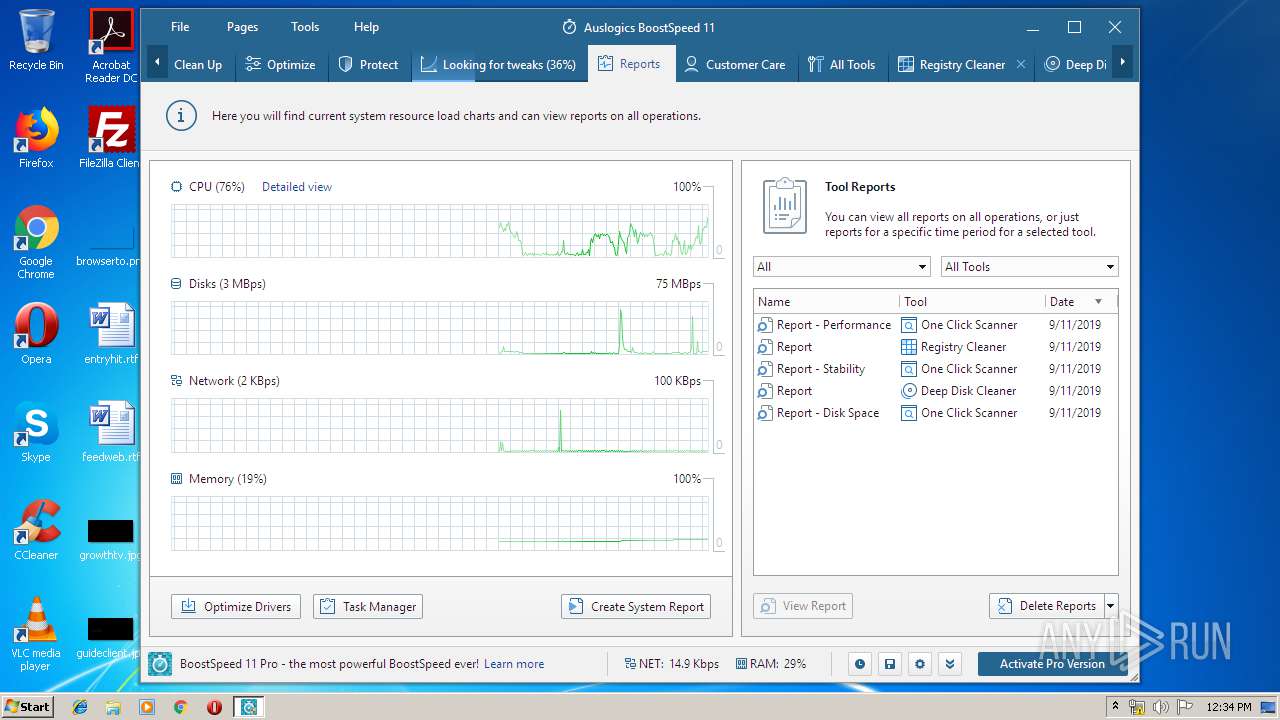
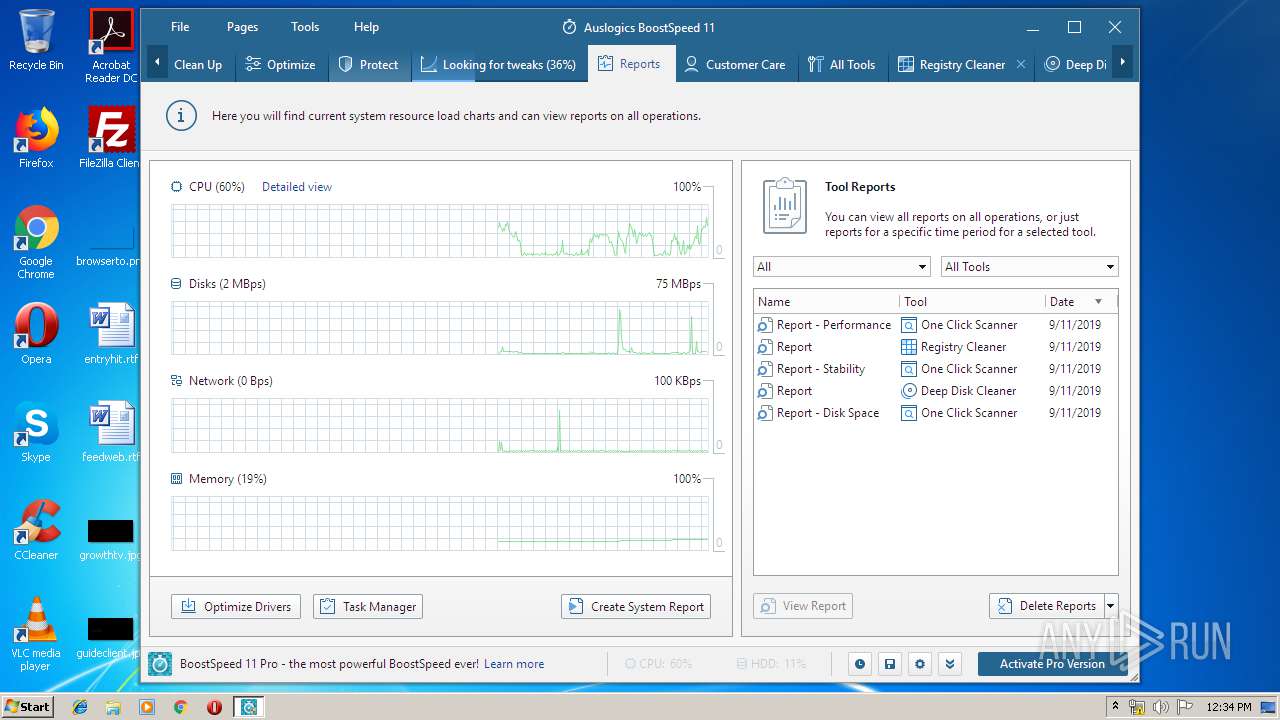
Total processes
93
Monitored processes
38
Malicious processes
23
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 756 | "C:\Program Files\Auslogics\BoostSpeed\TabMaintain.exe" | C:\Program Files\Auslogics\BoostSpeed\TabMaintain.exe | — | taboptimize.exe | |||||||||||
User: admin Company: Auslogics Integrity Level: HIGH Description: Maintain Exit code: 0 Version: 11.0.1.2 Modules
| |||||||||||||||
| 848 | C:\Windows\system32\netsh.exe interface tcp show global | C:\Windows\system32\netsh.exe | — | tabmaintain.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1632 | C:\Windows\system32\netsh.exe interface tcp show global | C:\Windows\system32\netsh.exe | — | tabmaintain.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1820 | C:\Windows\system32\netsh.exe interface tcp show global | C:\Windows\system32\netsh.exe | — | tabmaintain.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | "C:\Program Files\Auslogics\BoostSpeed\DeepDiskCleaner.exe" /StartDiskOperation:"C" | C:\Program Files\Auslogics\BoostSpeed\DeepDiskCleaner.exe | — | tabcleanup.exe | |||||||||||
User: admin Company: Auslogics Integrity Level: HIGH Description: Deep Disk Cleaner Exit code: 0 Version: 11.0.1.2 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Auslogics\BoostSpeed\Integrator.exe" /install /setscheduledefault /setautostart | C:\Program Files\Auslogics\BoostSpeed\Integrator.exe | — | boost-speed-setup.tmp | |||||||||||
User: admin Company: Auslogics Integrity Level: HIGH Description: BoostSpeed Exit code: 0 Version: 11.0.1.2 Modules
| |||||||||||||||
| 2540 | "C:\Program Files\Auslogics\BoostSpeed\tabprotect.exe" /FromInstall | C:\Program Files\Auslogics\BoostSpeed\tabprotect.exe | Integrator.exe | ||||||||||||
User: admin Company: Auslogics Integrity Level: HIGH Description: Protect Exit code: 0 Version: 11.0.1.2 Modules
| |||||||||||||||
| 2560 | C:\Windows\system32\netsh.exe interface teredo show state | C:\Windows\system32\netsh.exe | — | tabmaintain.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2568 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\Auslogics\BoostSpeed\BrowserPluginsHelper.Agent.x32.dll" | C:\Windows\system32\regsvr32.exe | — | boost-speed-setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2584 | "C:\Users\admin\AppData\Local\Temp\is-QQ782.tmp\reader.exe" "C:\Users\admin\Desktop\boost-speed-setup.exe" "(x32)HKEY_LOCAL_MACHINE\\Software\\Auslogics\\BoostSpeed\\11.x\\Settings" | C:\Users\admin\AppData\Local\Temp\is-QQ782.tmp\reader.exe | — | boost-speed-setup.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
87 163
Read events
86 009
Write events
1 025
Delete events
129
Modification events
| (PID) Process: | (3240) boost-speed-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: A80C0000FE21B43E9468D501 | |||
| (PID) Process: | (3240) boost-speed-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 8DF1DB93F3977E6DB33F75F0377E6C9684587C0BC390DDEDACD0A8F44E1E639A | |||
| (PID) Process: | (3240) boost-speed-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3240) boost-speed-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auslogics\BoostSpeed\11.x\Settings |
| Operation: | write | Name: | General.Tracking.URLMarkers |
Value: | |||
| (PID) Process: | (3240) boost-speed-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3240) boost-speed-setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3240) boost-speed-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auslogics\BoostSpeed\11.x\Settings |
| Operation: | write | Name: | General.Tracking.Param_Source |
Value: boost-speed-11 | |||
| (PID) Process: | (3240) boost-speed-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auslogics\BoostSpeed\11.x\Settings |
| Operation: | write | Name: | General.Language |
Value: ENU | |||
| (PID) Process: | (3240) boost-speed-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Auslogics |
| Operation: | write | Name: | ClientID |
Value: {AB0D40C4-6014-410C-A995-428EC54FAB78} | |||
| (PID) Process: | (3240) boost-speed-setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\boost-speed-setup_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
144
Suspicious files
19
Text files
108
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3240 | boost-speed-setup.tmp | C:\ProgramData\Auslogics\BoostSpeed\11.x\$$Cookies131410623 | — | |
MD5:— | SHA256:— | |||
| 3240 | boost-speed-setup.tmp | C:\ProgramData\Auslogics\BoostSpeed\11.x\$$Databases.db131410623 | — | |
MD5:— | SHA256:— | |||
| 3240 | boost-speed-setup.tmp | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 3240 | boost-speed-setup.tmp | C:\ProgramData\Auslogics\BoostSpeed\11.x\$$Cookies131410639 | — | |
MD5:— | SHA256:— | |||
| 3240 | boost-speed-setup.tmp | C:\ProgramData\Auslogics\BoostSpeed\11.x\$$Databases.db131410655 | — | |
MD5:— | SHA256:— | |||
| 3240 | boost-speed-setup.tmp | C:\ProgramData\Auslogics\BoostSpeed\11.x\$$Cookies131410670 | — | |
MD5:— | SHA256:— | |||
| 3240 | boost-speed-setup.tmp | C:\ProgramData\Auslogics\BoostSpeed\11.x\$$Databases.db131410670 | — | |
MD5:— | SHA256:— | |||
| 3240 | boost-speed-setup.tmp | C:\Program Files\Auslogics\BoostSpeed\is-S9NHP.tmp | — | |
MD5:— | SHA256:— | |||
| 2644 | boost-speed-setup.exe | C:\Users\admin\AppData\Local\Temp\is-5844M.tmp\boost-speed-setup.tmp | executable | |
MD5:— | SHA256:— | |||
| 3240 | boost-speed-setup.tmp | C:\Program Files\Auslogics\BoostSpeed\is-IBAGL.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
6
Threats
6
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
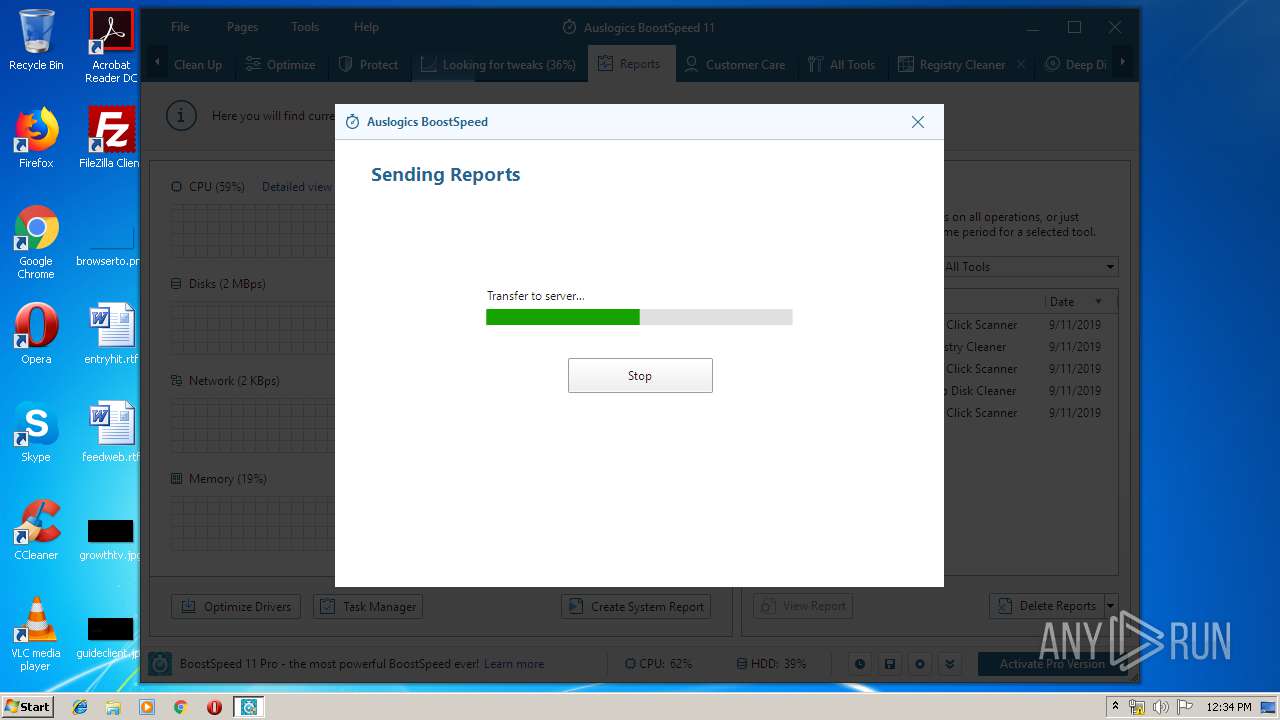
3240 | boost-speed-setup.tmp | 45.33.8.241:443 | www.auslogics.com | Linode, LLC | US | malicious |
3240 | boost-speed-setup.tmp | 172.217.16.206:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3652 | tabcarecenter.exe | 45.33.8.241:443 | www.auslogics.com | Linode, LLC | US | malicious |
3452 | Integrator.exe | 45.33.8.241:443 | www.auslogics.com | Linode, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google-analytics.com |
| whitelisted |
www.auslogics.com |
| whitelisted |
ads.auslogics.com |
| whitelisted |
qa.auslogics.com |
| malicious |
www.google.com |
| malicious |
Threats
6 ETPRO signatures available at the full report
Process | Message |
|---|---|
DISM.exe | PID=3448 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
DISM.exe | PID=3448 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
DISM.exe | PID=3448 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
DISM.exe | PID=3448 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
DISM.exe | PID=3448 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
DISM.exe | PID=3448 Connecting to the provider located at C:\Windows\System32\Dism\LogProvider.dll. - CDISMProviderStore::Internal_LoadProvider |
DISM.exe | PID=3448 Getting Provider OSServices - CDISMProviderStore::GetProvider |
DISM.exe | PID=3448 The requested provider was not found in the Provider Store. - CDISMProviderStore::Internal_GetProvider(hr:0x80004005) |
DISM.exe | PID=3448 Failed to get an OSServices provider. Must be running in local store. Falling back to checking alongside the log provider for wdscore.dll. - CDISMLogger::FindWdsCore(hr:0x80004005) |
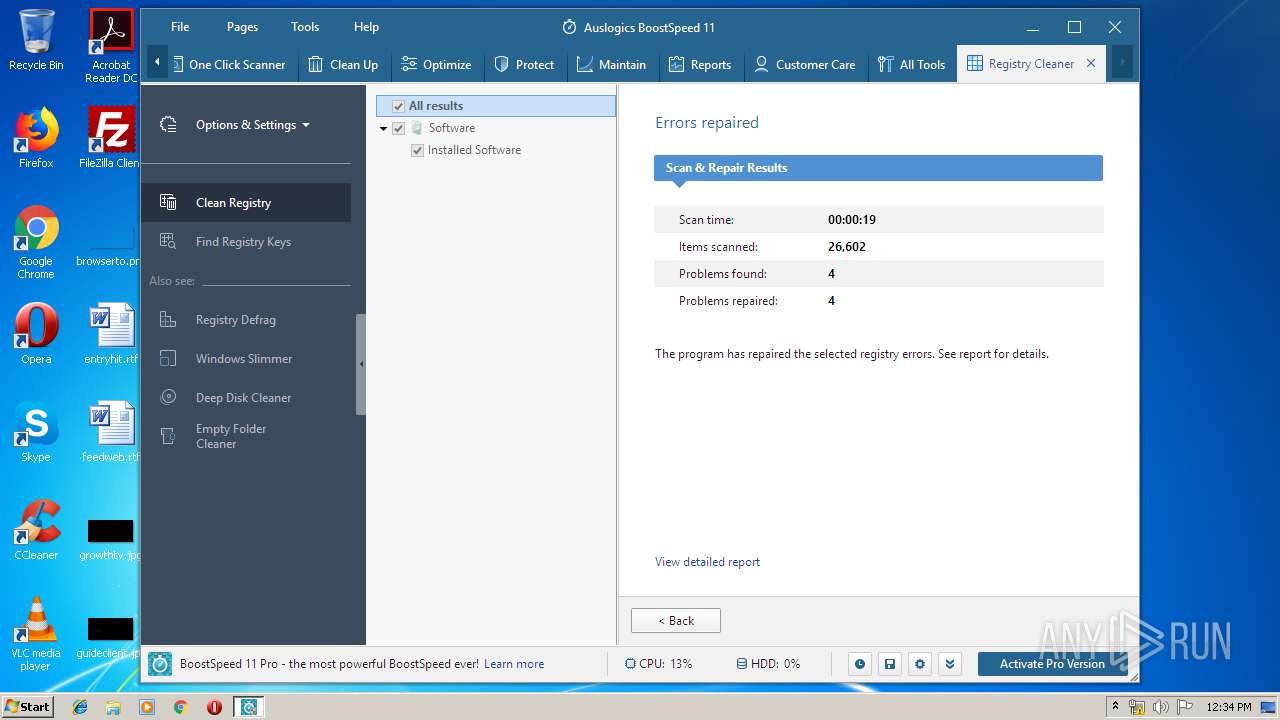
registrycleaner.exe | 24 |