| File name: | contract.doc |
| Full analysis: | https://app.any.run/tasks/04d6a905-813c-4feb-ad55-b5ff63ba96cb |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 13:10:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: JBrq, Subject: joHE, Author: U, Template: Normal, Last Saved By: J, Revision Number: 2, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Nov 8 11:46:00 2019, Last Saved Time/Date: Fri Nov 8 11:46:00 2019, Number of Pages: 1, Number of Words: 6, Number of Characters: 37, Security: 0 |
| MD5: | C9449751C89B9DB16915737B4F765890 |
| SHA1: | 141783D0D9DDC75453972FD549733C391C08996E |
| SHA256: | 1753B2A7FC978A75FB08C92B902D3EC33A61D8AC5FD8B0F6F4E61E6324A363B3 |
| SSDEEP: | 12288:hRQ6X9GDapm47H+9vo4karcaXv2CAwz0NASBY196ID+9atk:hRQ6tlb/4kc/vAi0NASi650O |
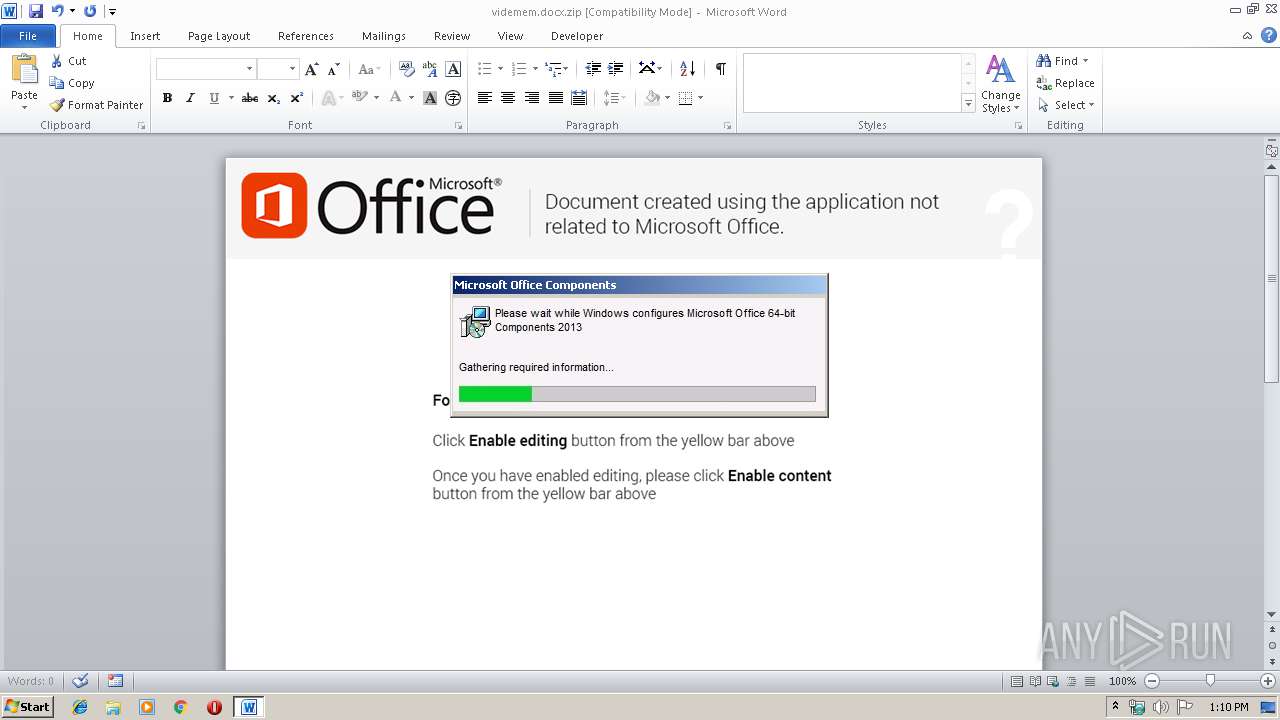
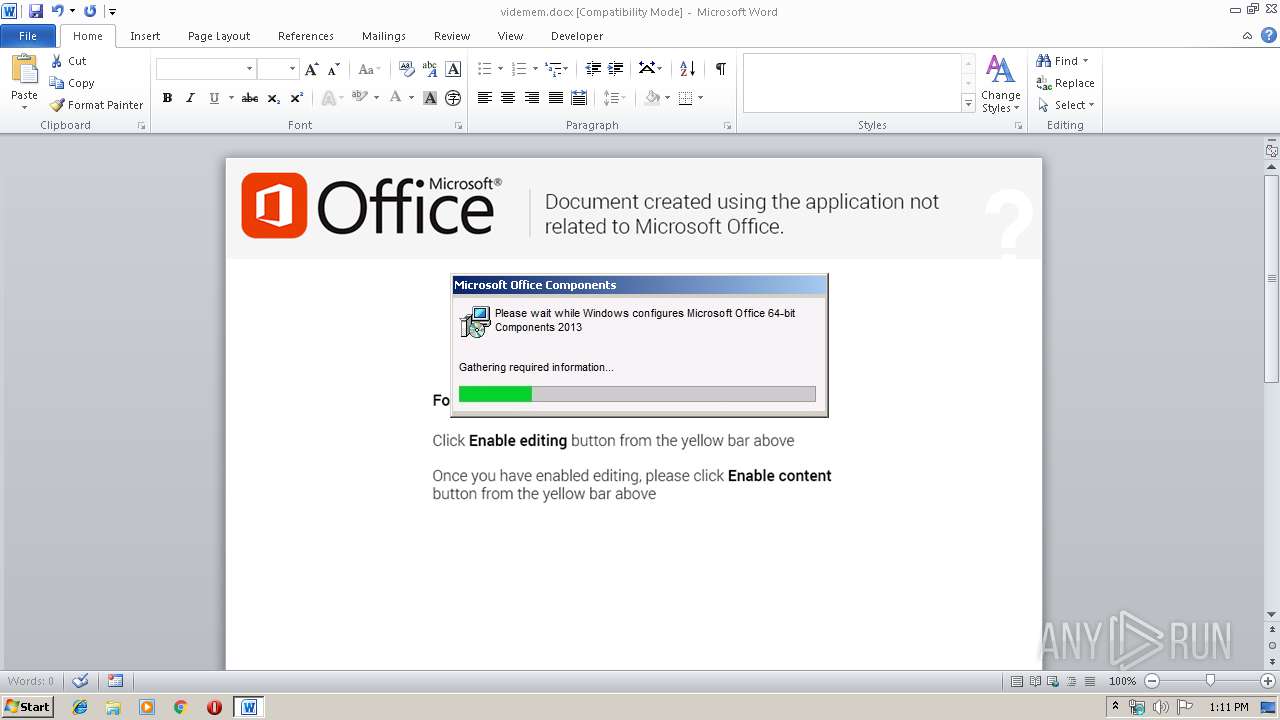
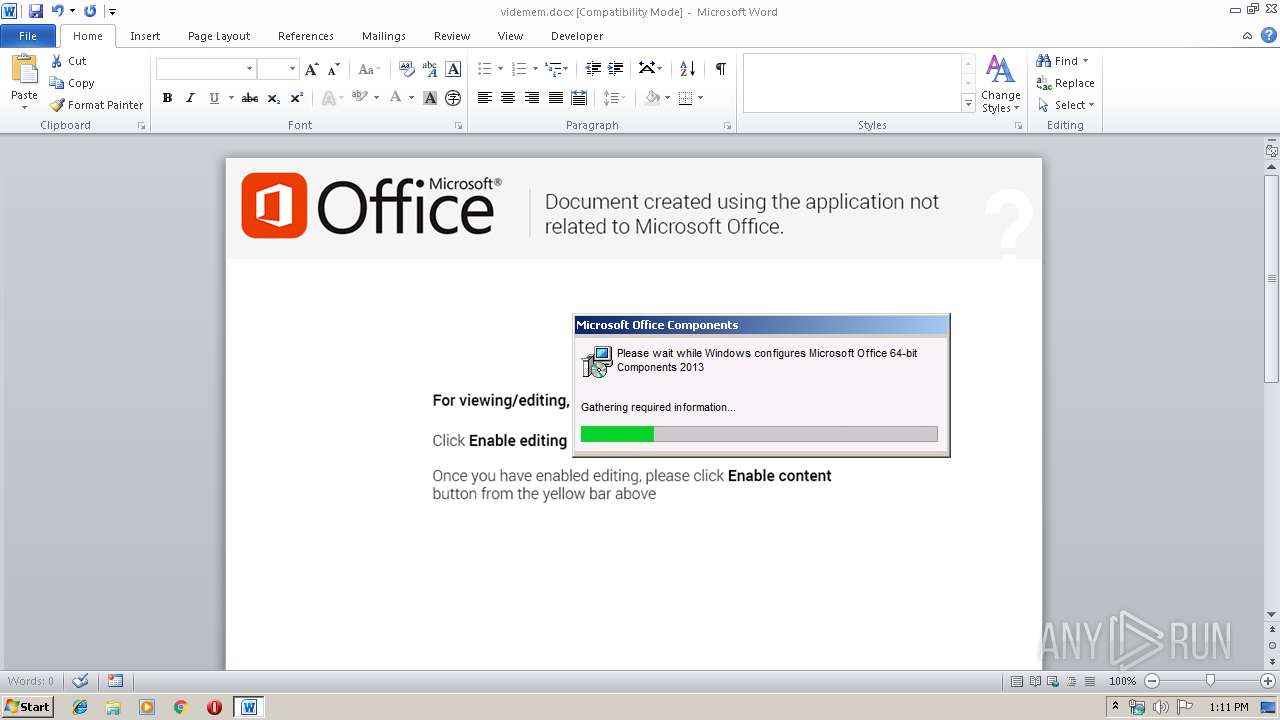
MALICIOUS
Loads dropped or rewritten executable
- WINWORD.EXE (PID: 2420)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2420)
SUSPICIOUS
No suspicious indicators.INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2420)
Reads settings of System Certificates
- WINWORD.EXE (PID: 2420)
Creates files in the user directory
- WINWORD.EXE (PID: 2420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | JBrq |
|---|---|
| Subject: | joHE |
| Author: | U |
| Keywords: | - |
| Comments: | - |
| Template: | Normal |
| LastModifiedBy: | J |
| RevisionNumber: | 2 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:11:08 11:46:00 |
| ModifyDate: | 2019:11:08 11:46:00 |
| Pages: | 1 |
| Words: | 6 |
| Characters: | 37 |
| Security: | None |
| Company: | - |
| Bytes: | 96851 |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 42 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Windows Latin 1 (Western European) |
| HEfJCyLh: | #$CUF~_,-(bA*R.OQ-]KY%J |
| MsDjXcKj: | -]pa){-(ccA$w |
| EjldFL: | i}E%%]l6:_i(a.S@O5|jZV#i^ |
| BzYMXfxC: | b(uf{#ofqr;vJYN#L~3mWtw]x: |
| IkSYsxhy: | tY?FLPW|)w3/V]UH)Jt&Xv&cjR_AsZ |
| NeBBRPnKd: | FnaD!ltE2Te.9E{^-w,3w8u |
| SPaxICD: | mlrh^9HF3:Zg!DIpVf,a^MJ8 |
| BXUgMHcWsN: | m|]q=Xazho@cK)/23X?9 |
| AinKymSpB: | FX_d6g#l |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
35
Monitored processes
1
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2420 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\contract.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
976
Read events
726
Write events
186
Delete events
64
Modification events
| (PID) Process: | (2420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | )uc |
Value: 2975630074090000010000000000000000000000 | |||
| (PID) Process: | (2420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2420) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2420) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
1
Suspicious files
3
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA989.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$demem.docx.zip | — | |
MD5:— | SHA256:— | |||
| 2420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~WRD0001.tmp | — | |
MD5:— | SHA256:— | |||
| 2420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ntract.doc | pgc | |
MD5:— | SHA256:— | |||
| 2420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\14914FD5.emf | emf | |
MD5:— | SHA256:— | |||
| 2420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\videmem.docx.zip | document | |
MD5:— | SHA256:— | |||
| 2420 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\oleObject1.bin | binary | |
MD5:— | SHA256:— | |||
| 2420 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$idemem.docx | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2420 | WINWORD.EXE | 195.123.246.12:443 | microsoft-hub-us.com | — | UA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
microsoft-hub-us.com |
| unknown |