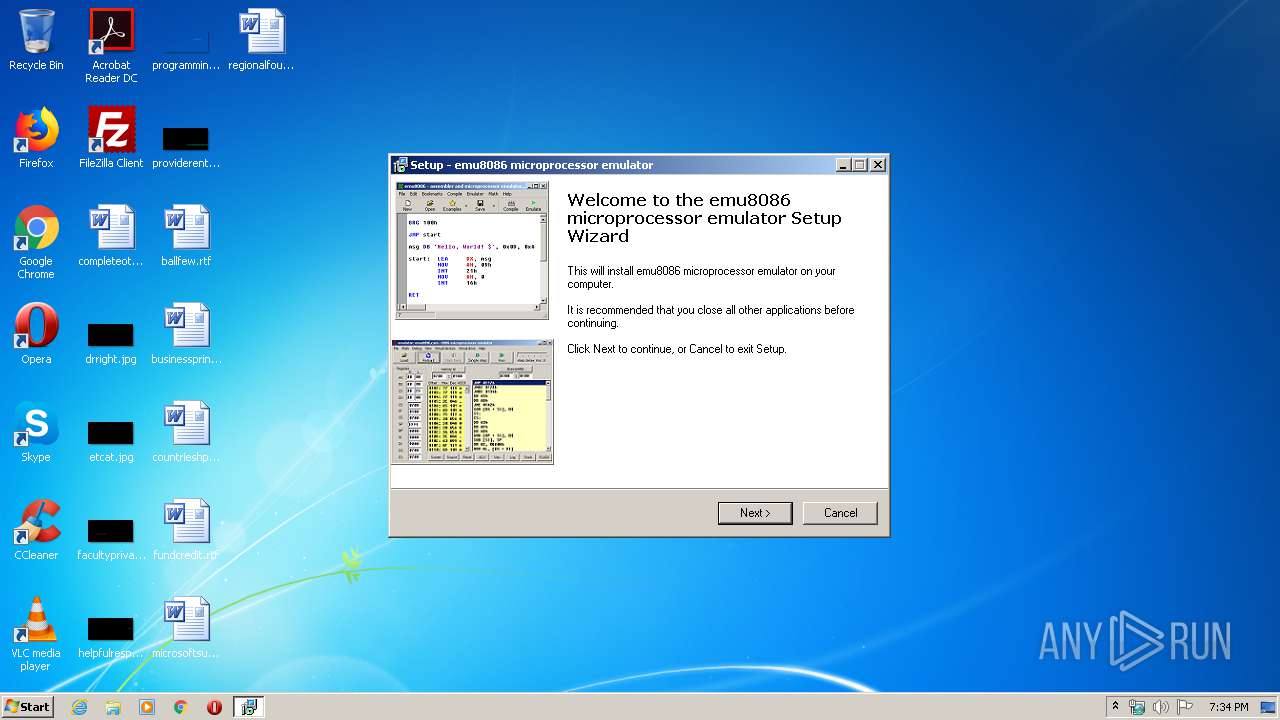
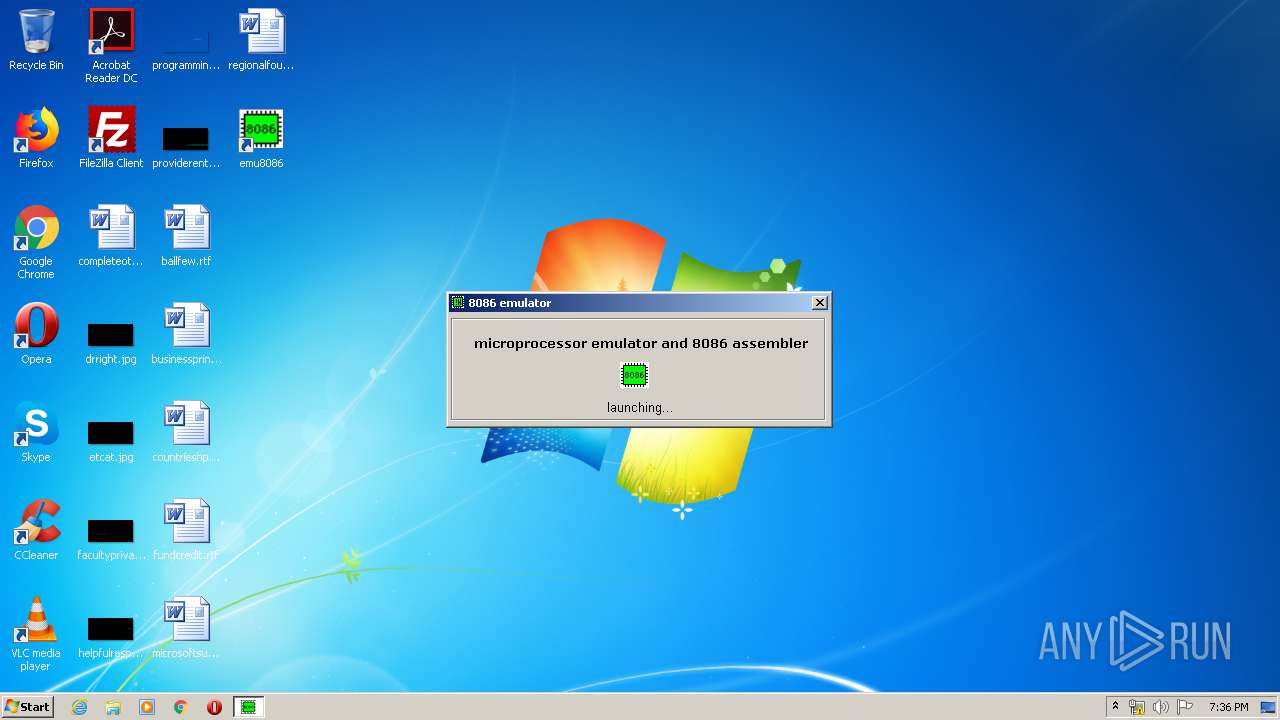
| File name: | emu8086v408r.exe |
| Full analysis: | https://app.any.run/tasks/43143b1d-906e-4c14-b65e-f81fa7d26fa5 |
| Verdict: | Malicious activity |
| Analysis date: | March 09, 2020, 19:34:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AE66BED5389BC27903CA80C80A2E5A84 |
| SHA1: | 40D0DBD8B388FB9F4C0E21D3FA3A72200ABEEBF0 |
| SHA256: | 175061D9F03A56DE25E867FD4AAF16925E6FB03AFDFB3B403C05BDA49EA716E7 |
| SSDEEP: | 98304:BuPPCK2yMyHgjP3AUm1pkv94KaOfUKx7xTyFK:BuCK2yFgL3rm18sGxTyFK |
MALICIOUS
Loads dropped or rewritten executable
- regsvr32.exe (PID: 2628)
- emu8086.exe (PID: 2976)
- emu8086.exe (PID: 2212)
Application was dropped or rewritten from another process
- emu8086.exe (PID: 2212)
- emu8086.exe (PID: 2976)
Registers / Runs the DLL via REGSVR32.EXE
- emu8086v408r.tmp (PID: 3992)
SUSPICIOUS
Reads the Windows organization settings
- emu8086v408r.tmp (PID: 3992)
Reads Windows owner or organization settings
- emu8086v408r.tmp (PID: 3992)
Executable content was dropped or overwritten
- emu8086v408r.exe (PID: 3048)
- emu8086v408r.exe (PID: 3248)
- emu8086v408r.tmp (PID: 3992)
Creates files in the Windows directory
- emu8086v408r.tmp (PID: 3992)
Creates files in the user directory
- emu8086v408r.tmp (PID: 3992)
Modifies the open verb of a shell class
- emu8086v408r.tmp (PID: 3992)
- emu8086.exe (PID: 2976)
Creates COM task schedule object
- regsvr32.exe (PID: 2932)
INFO
Application was dropped or rewritten from another process
- emu8086v408r.tmp (PID: 2148)
- emu8086v408r.tmp (PID: 3992)
Loads dropped or rewritten executable
- emu8086v408r.tmp (PID: 3992)
Creates files in the program directory
- emu8086v408r.tmp (PID: 3992)
Creates a software uninstall entry
- emu8086v408r.tmp (PID: 3992)
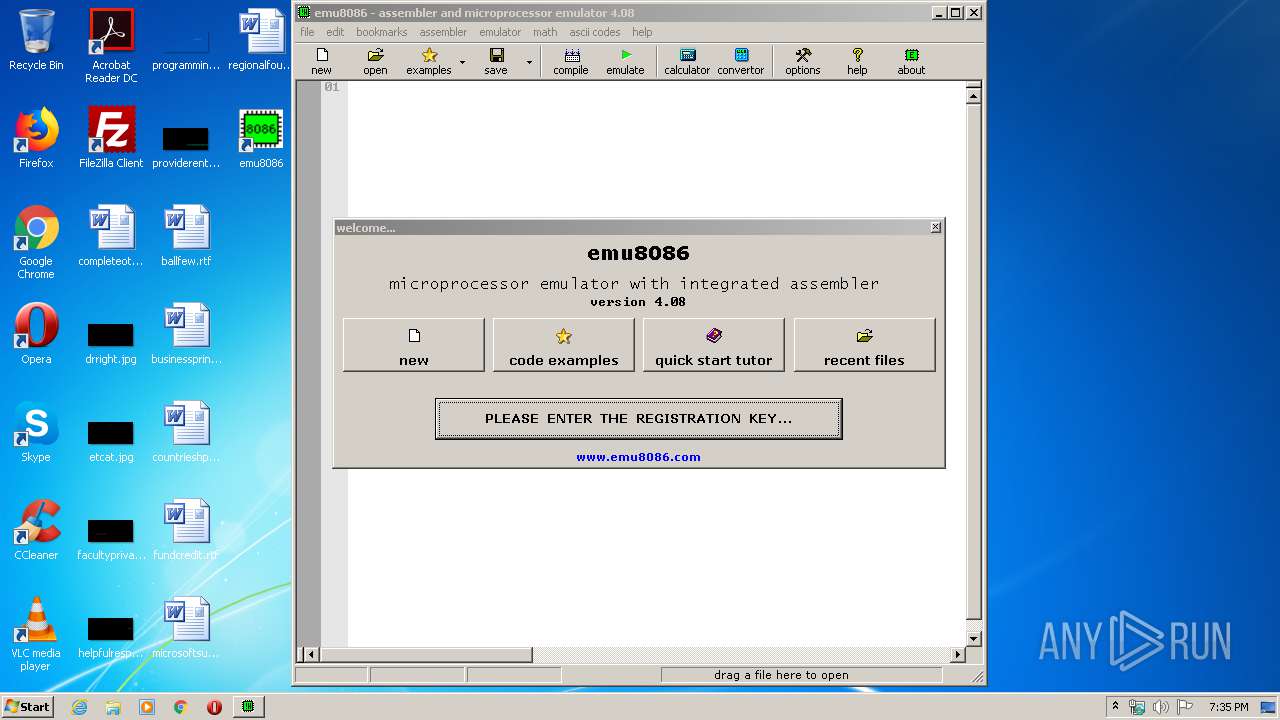
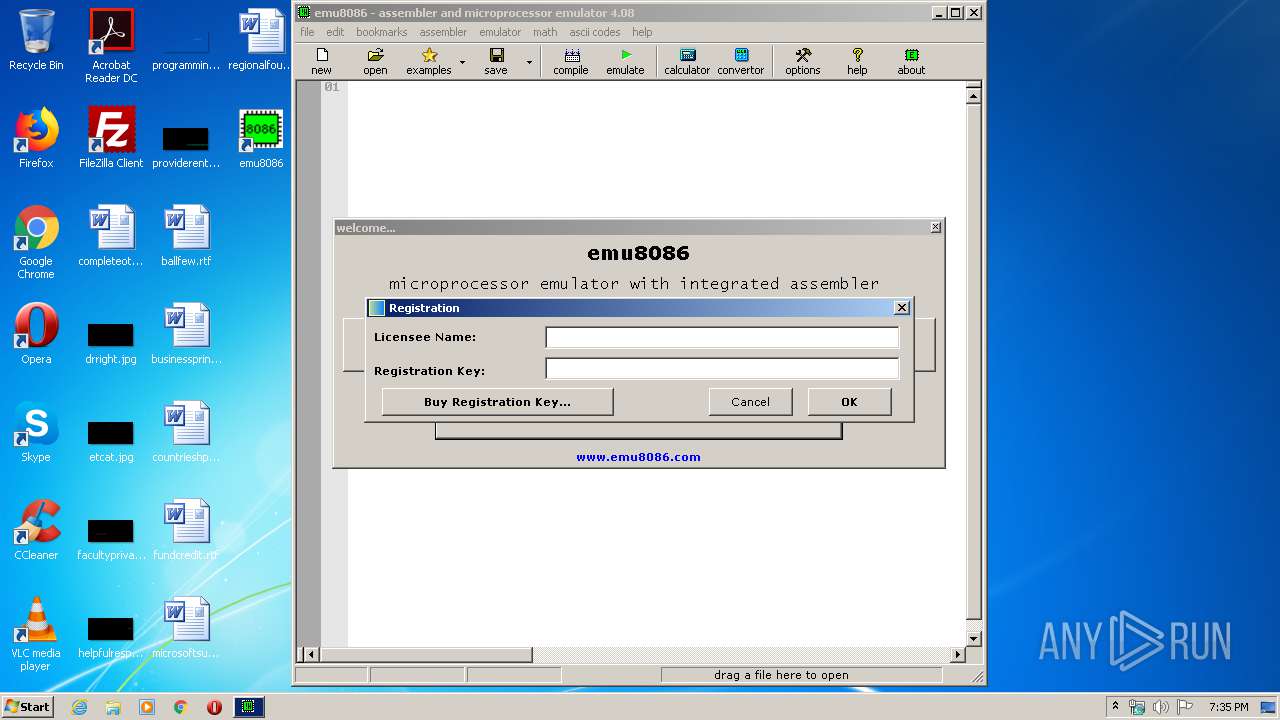
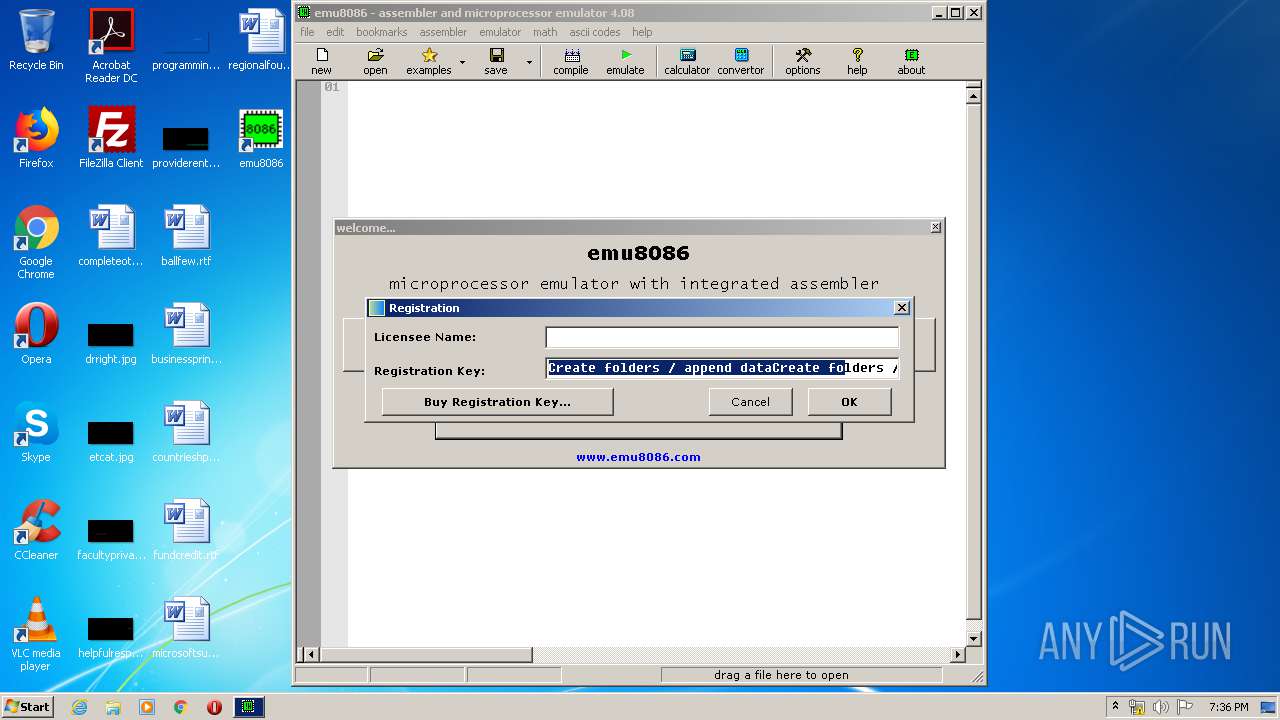
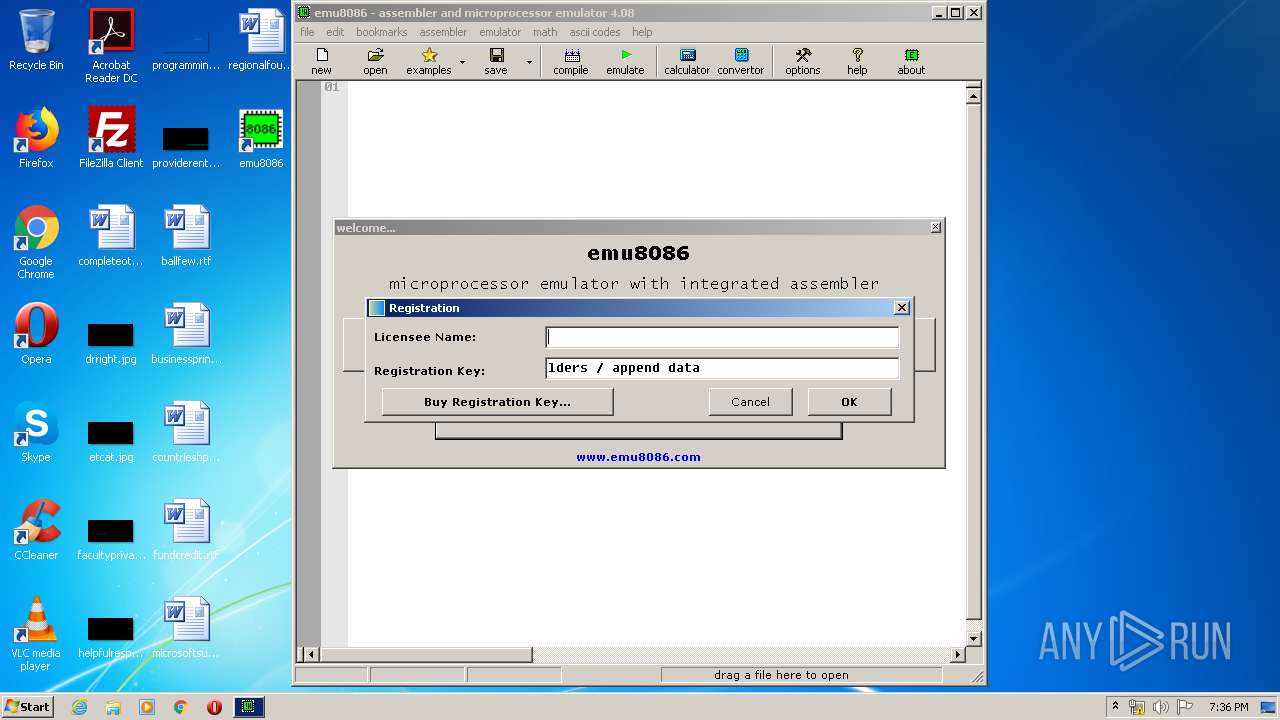
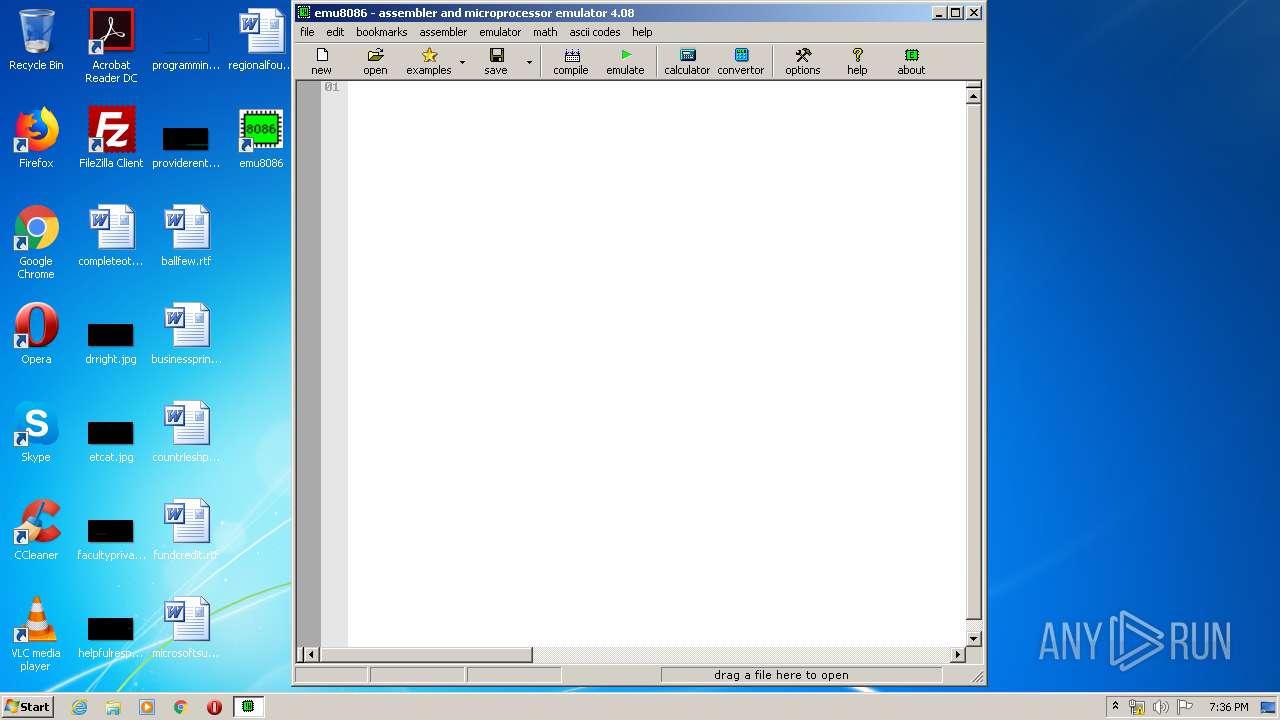
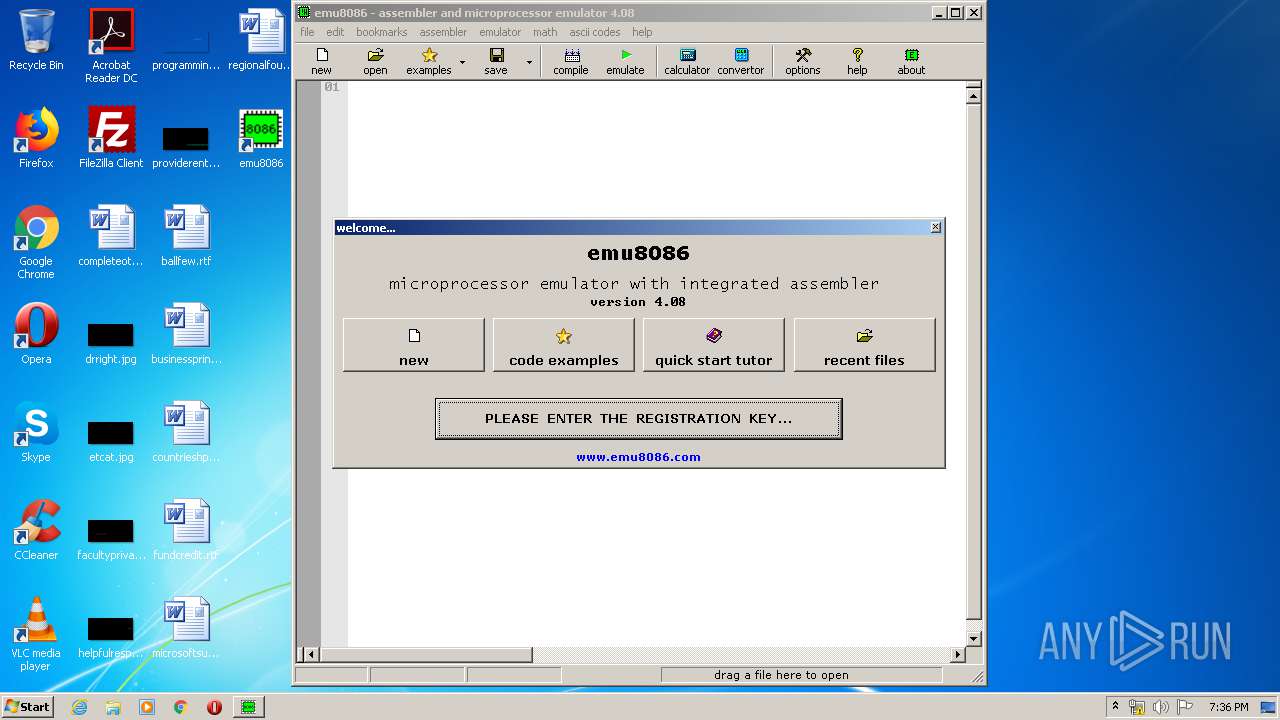
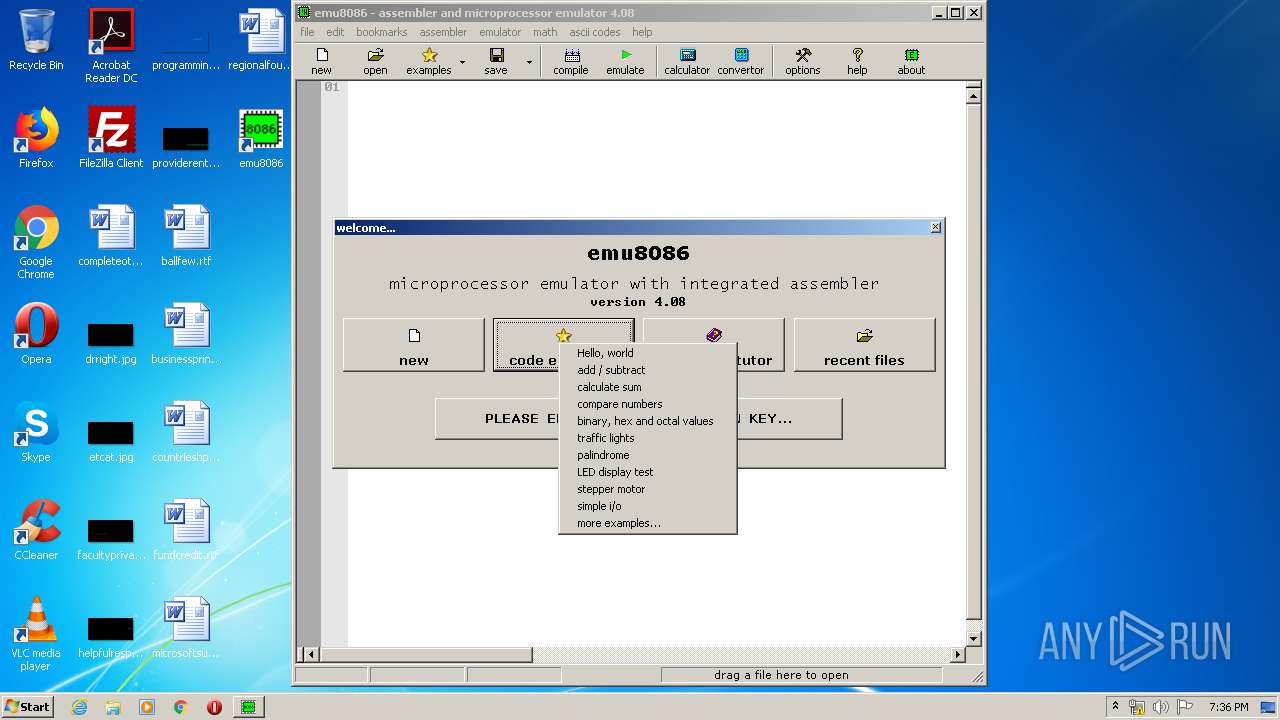
Manual execution by user
- emu8086.exe (PID: 2212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:01:06 10:56:24+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 87040 |
| InitializedDataSize: | 60416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x163c4 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
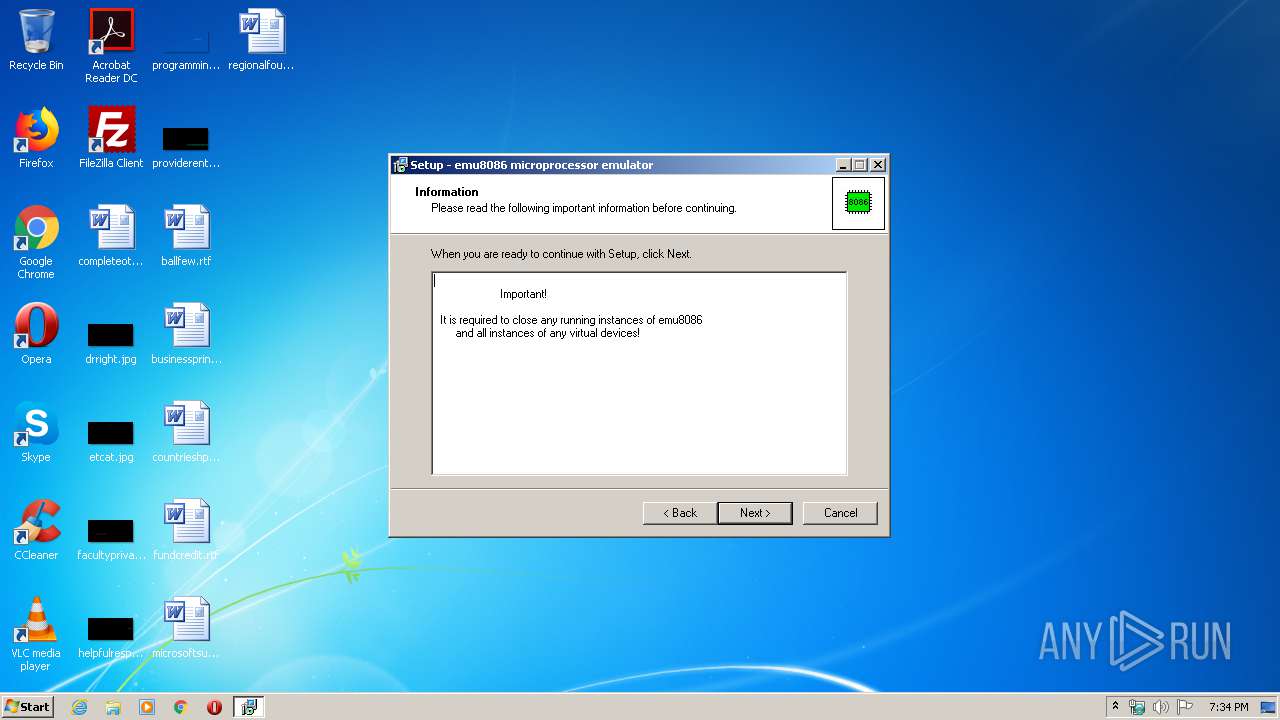
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | emu8086 |
| FileDescription: | emu8086 microprocessor emulator Setup |
| FileVersion: | |
| LegalCopyright: | Copyright © 2010 |
| ProductName: | emu8086 microprocessor emulator |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jan-2010 09:56:24 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | emu8086 |
| FileDescription: | emu8086 microprocessor emulator Setup |
| FileVersion: | - |
| LegalCopyright: | Copyright © 2010 |
| ProductName: | emu8086 microprocessor emulator |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 06-Jan-2010 09:56:24 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00014618 | 0x00014800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46109 |
.itext | 0x00016000 | 0x00000B34 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.80234 |
.data | 0x00017000 | 0x00000D9C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.67574 |
.bss | 0x00018000 | 0x0000570C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001E000 | 0x00000F9E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96778 |
.tls | 0x0001F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00020000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.190489 |
.reloc | 0x00021000 | 0x00001948 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0 |
.rsrc | 0x00023000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.15066 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.05007 | 1376 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 3.13038 | 196 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.36196 | 204 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.34841 | 372 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.29351 | 924 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
48
Monitored processes
12
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
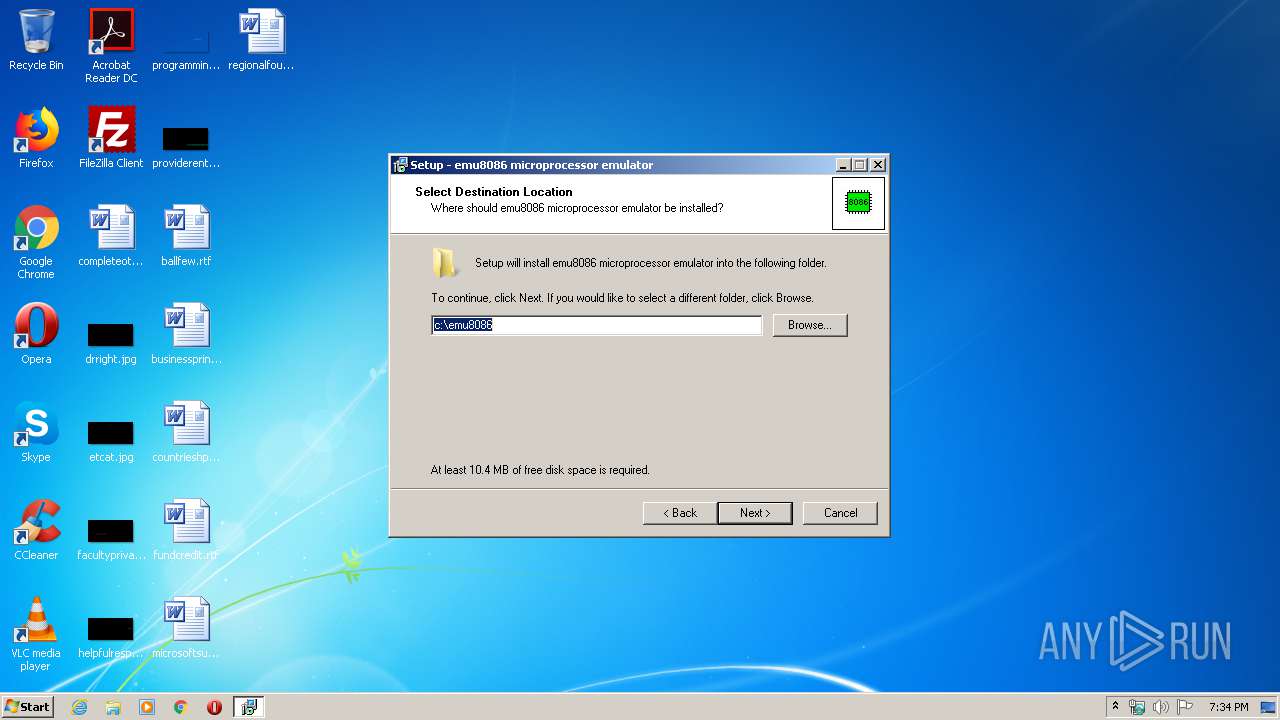
| 2148 | "C:\Users\admin\AppData\Local\Temp\is-OAKJE.tmp\emu8086v408r.tmp" /SL5="$90140,2799136,141824,C:\Users\admin\Downloads\emu8086v408r.exe" | C:\Users\admin\AppData\Local\Temp\is-OAKJE.tmp\emu8086v408r.tmp | — | emu8086v408r.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1050.0.0 Modules
| |||||||||||||||
| 2212 | "C:\emu8086\emu8086.exe" | C:\emu8086\emu8086.exe | — | explorer.exe | |||||||||||
User: admin Company: www.emu8086.com Integrity Level: MEDIUM Description: emu8086 Exit code: 0 Version: 4.00.0008 Modules
| |||||||||||||||
| 2620 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\comcat.dll" | C:\Windows\system32\regsvr32.exe | — | emu8086v408r.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\cmax20.ocx" | C:\Windows\system32\regsvr32.exe | — | emu8086v408r.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2932 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\msvbvm60.dll" | C:\Windows\system32\regsvr32.exe | — | emu8086v408r.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2976 | "c:\emu8086\emu8086.exe" | c:\emu8086\emu8086.exe | — | emu8086v408r.tmp | |||||||||||
User: admin Company: www.emu8086.com Integrity Level: HIGH Description: emu8086 Exit code: 0 Version: 4.00.0008 Modules
| |||||||||||||||
| 3044 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\olepro32.dll" | C:\Windows\system32\regsvr32.exe | — | emu8086v408r.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3048 | "C:\Users\admin\Downloads\emu8086v408r.exe" /SPAWNWND=$601CA /NOTIFYWND=$90140 | C:\Users\admin\Downloads\emu8086v408r.exe | emu8086v408r.tmp | ||||||||||||
User: admin Company: emu8086 Integrity Level: HIGH Description: emu8086 microprocessor emulator Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3052 | "C:\Windows\system32\regsvr32.exe" /s "C:\Windows\system32\Mscomctl.ocx" | C:\Windows\system32\regsvr32.exe | — | emu8086v408r.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3248 | "C:\Users\admin\Downloads\emu8086v408r.exe" | C:\Users\admin\Downloads\emu8086v408r.exe | explorer.exe | ||||||||||||
User: admin Company: emu8086 Integrity Level: MEDIUM Description: emu8086 microprocessor emulator Setup Exit code: 0 Version: Modules
| |||||||||||||||
Total events
3 837
Read events
3 128
Write events
656
Delete events
53
Modification events
| (PID) Process: | (3992) emu8086v408r.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\cmax20.ocx |
Value: 1 | |||
| (PID) Process: | (3992) emu8086v408r.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\stdole2.tlb |
Value: 2 | |||
| (PID) Process: | (3992) emu8086v408r.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\msvbvm60.dll |
Value: 2 | |||
| (PID) Process: | (3992) emu8086v408r.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\oleaut32.dll |
Value: 2 | |||
| (PID) Process: | (3992) emu8086v408r.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\olepro32.dll |
Value: 2 | |||
| (PID) Process: | (3992) emu8086v408r.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\asycfilt.dll |
Value: 2 | |||
| (PID) Process: | (3992) emu8086v408r.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\comcat.dll |
Value: 2 | |||
| (PID) Process: | (3992) emu8086v408r.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\SharedDLLs |
| Operation: | write | Name: | C:\Windows\system32\Mscomctl.ocx |
Value: 2 | |||
| (PID) Process: | (3992) emu8086v408r.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.com_ |
| Operation: | write | Name: | |
Value: emu8086 | |||
| (PID) Process: | (3992) emu8086v408r.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\.exe_ |
| Operation: | write | Name: | |
Value: emu8086 | |||
Executable files
17
Suspicious files
12
Text files
283
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3992 | emu8086v408r.tmp | C:\emu8086\is-U7V48.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | emu8086v408r.tmp | C:\emu8086\is-0BRLM.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | emu8086v408r.tmp | C:\emu8086\is-OVUN4.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | emu8086v408r.tmp | C:\emu8086\is-SPRHK.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | emu8086v408r.tmp | C:\emu8086\is-G1NMB.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | emu8086v408r.tmp | C:\emu8086\is-1H8F5.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | emu8086v408r.tmp | C:\emu8086\is-8GOHF.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | emu8086v408r.tmp | C:\emu8086\is-VLTS7.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | emu8086v408r.tmp | C:\emu8086\is-0T9EA.tmp | — | |
MD5:— | SHA256:— | |||
| 3992 | emu8086v408r.tmp | C:\emu8086\is-R9VM2.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report