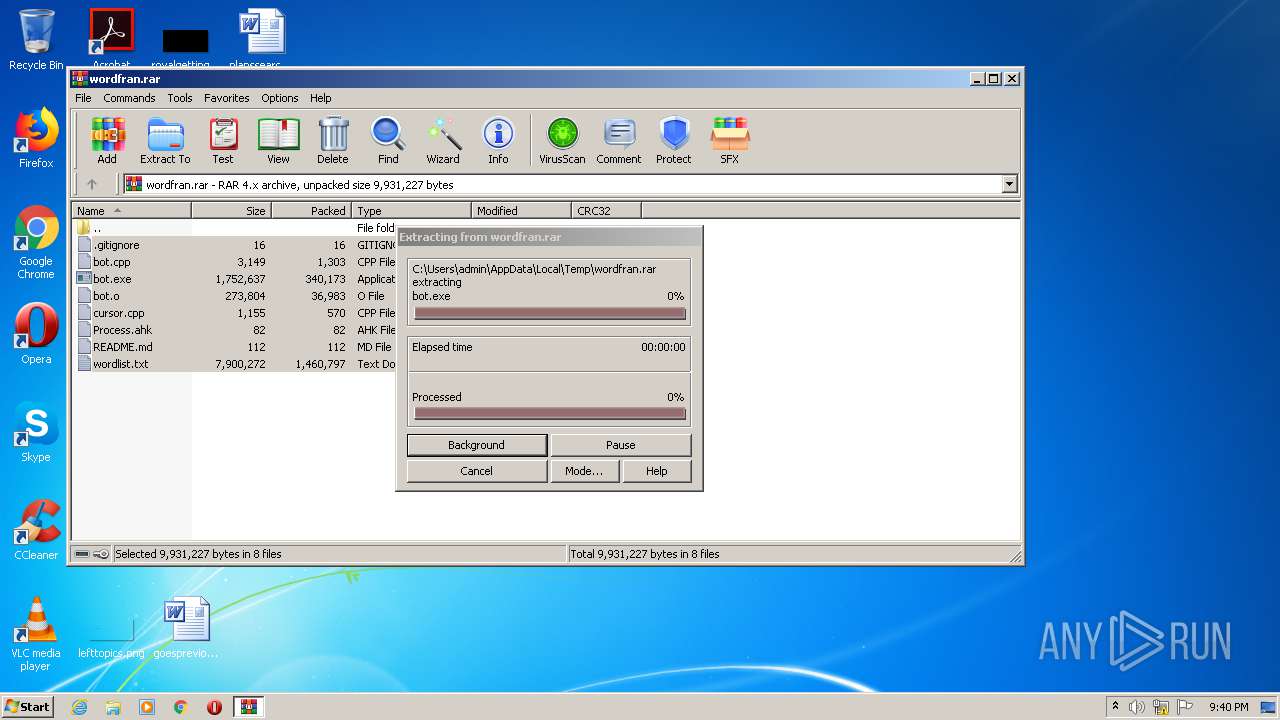
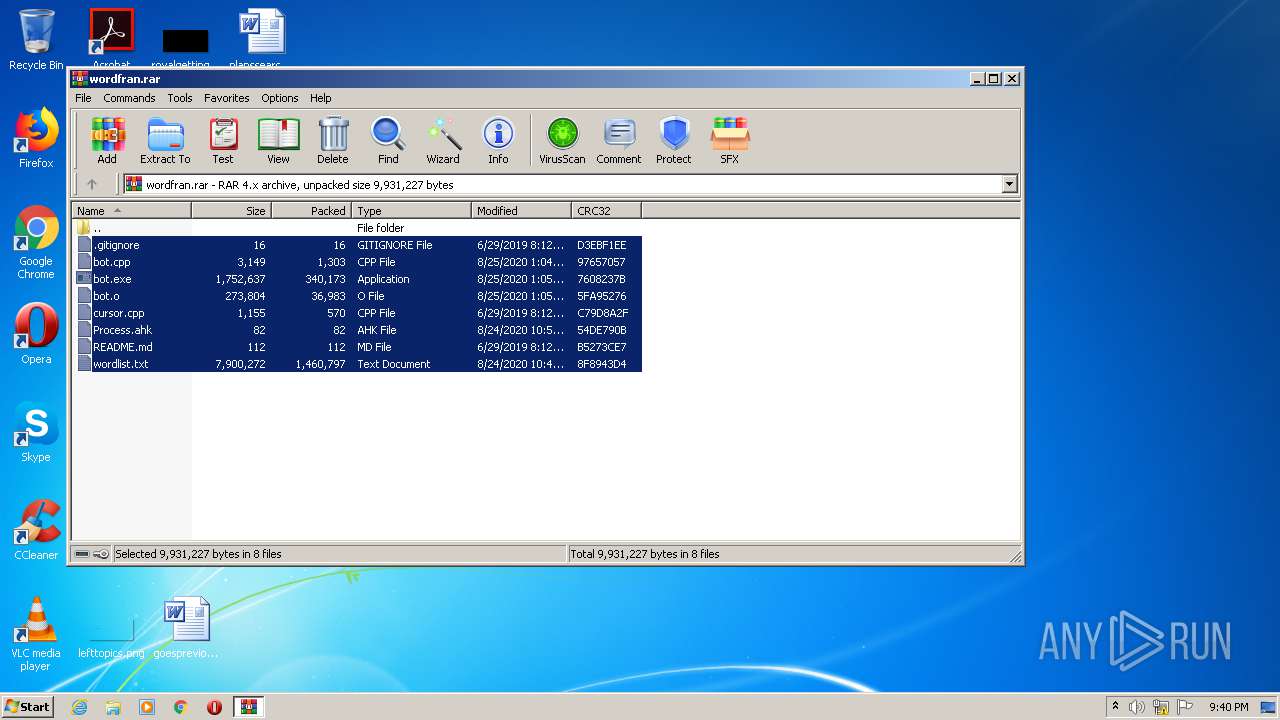
| File name: | wordfran.rar |
| Full analysis: | https://app.any.run/tasks/cdd3c4a7-d257-4c54-81d9-0af03485cb02 |
| Verdict: | Malicious activity |
| Analysis date: | August 25, 2020, 20:40:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | D8E3F620A209636F17C34437370337B5 |
| SHA1: | FA55A4CAEDB8035E2E595020763B8802DE89A920 |
| SHA256: | 174DC0FBA0913555AFDA4D70DA458F221B9BBE758F6538BAE9A407CDC48C7B03 |
| SSDEEP: | 49152:MngY+TXECwXDcGyw2Jlo9wTCG7PHTxtdwE4:DbbECwzcVw2JgwGG7PHTx94 |
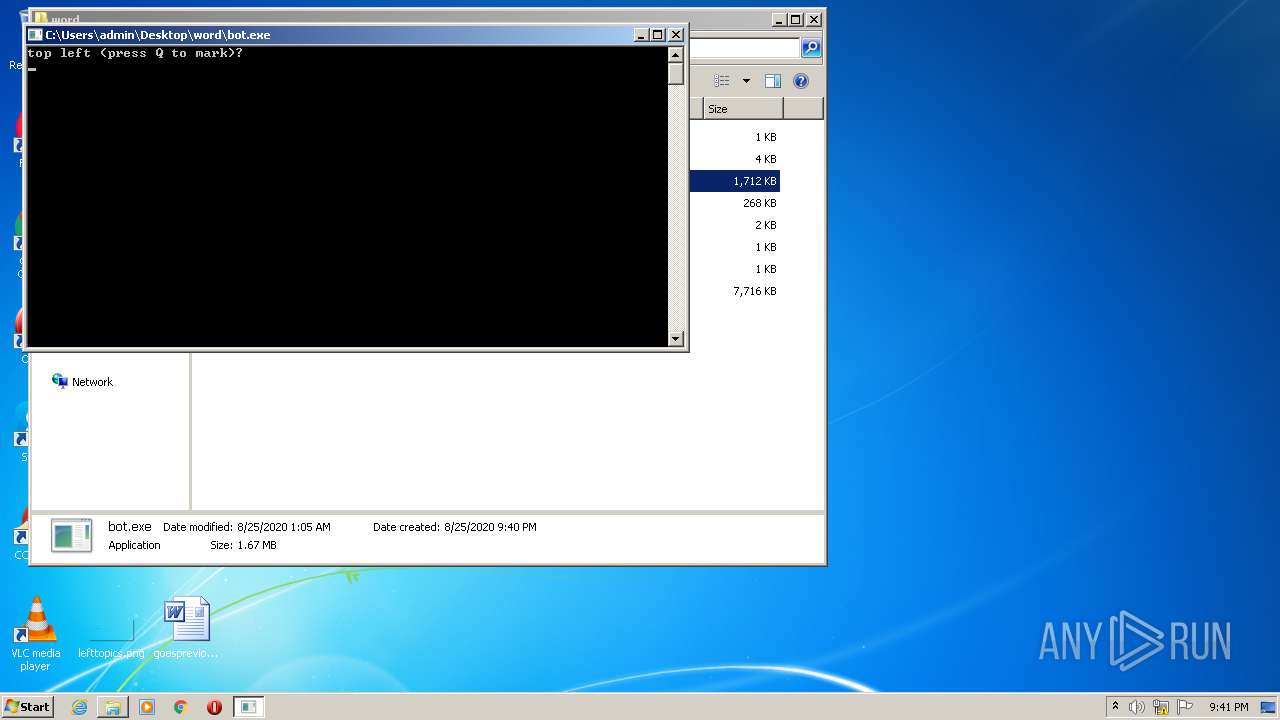
MALICIOUS
Application was dropped or rewritten from another process
- bot.exe (PID: 1296)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2240)
INFO
Manual execution by user
- bot.exe (PID: 1296)
- rundll32.exe (PID: 3732)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
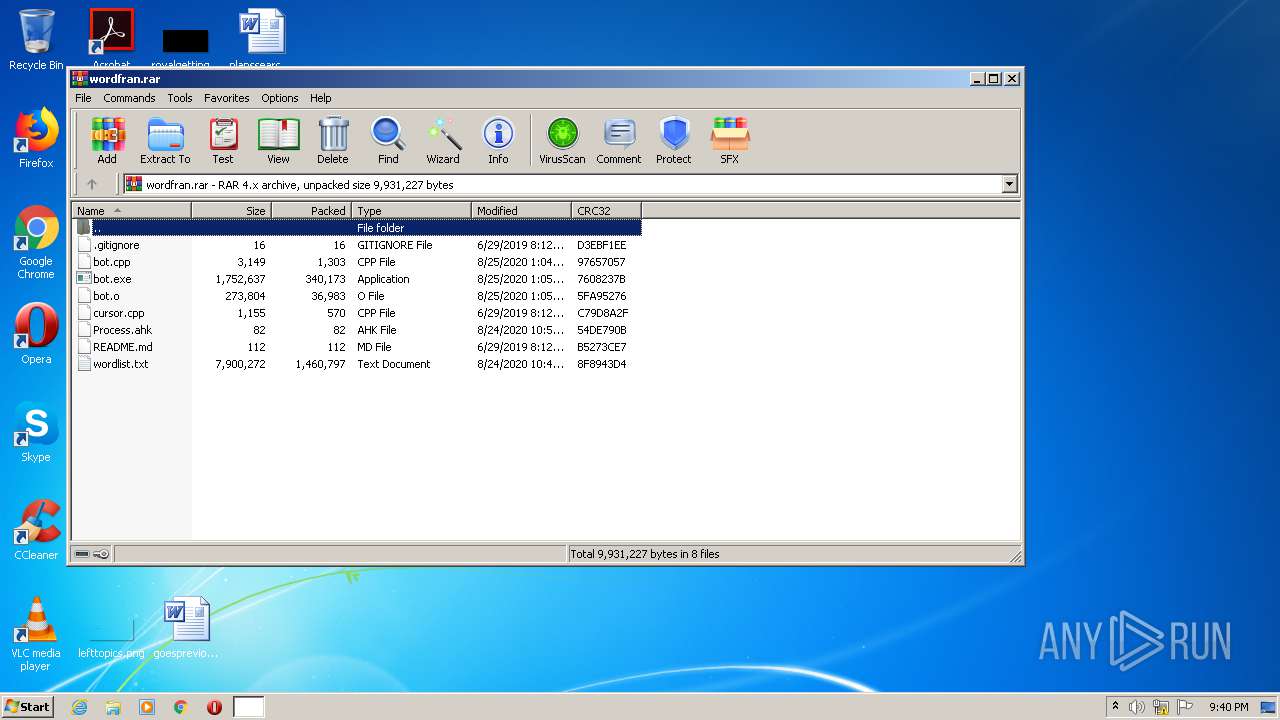
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 1336 |
|---|---|
| UncompressedSize: | 3149 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2020:08:25 01:04:25 |
| PackingMethod: | Normal |
| ArchivedFileName: | bot.cpp |
Total processes
42
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
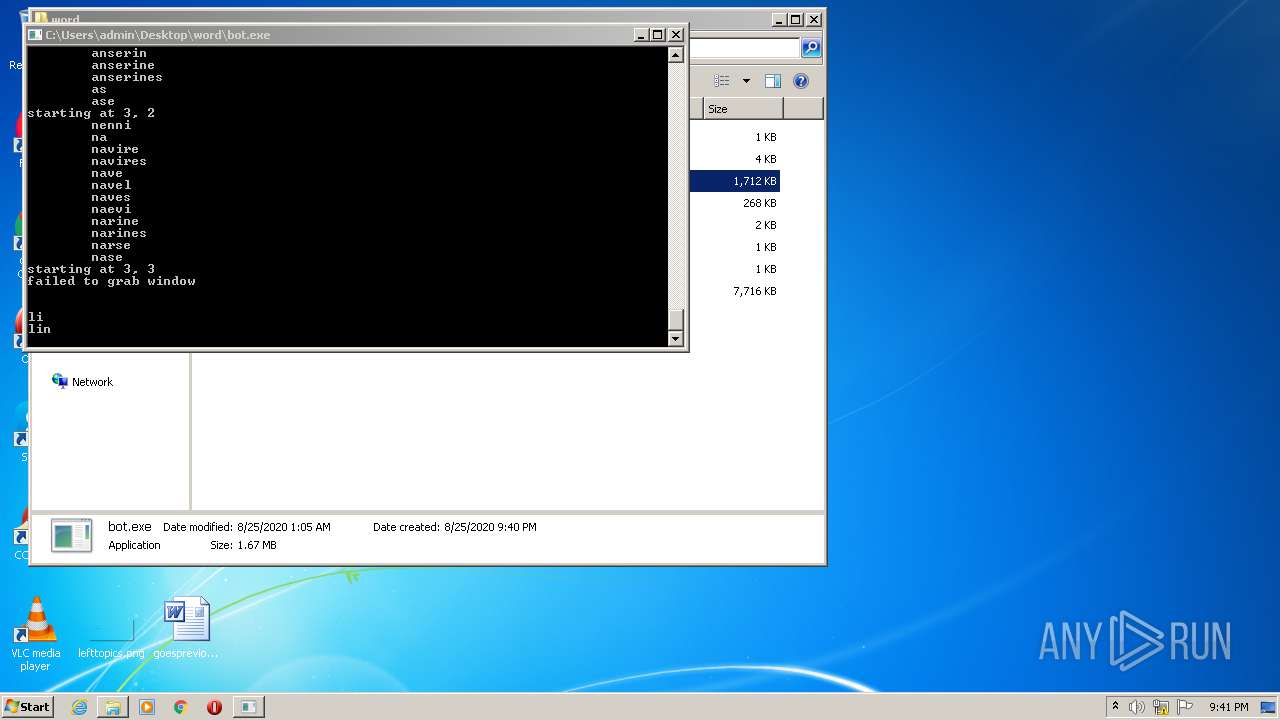
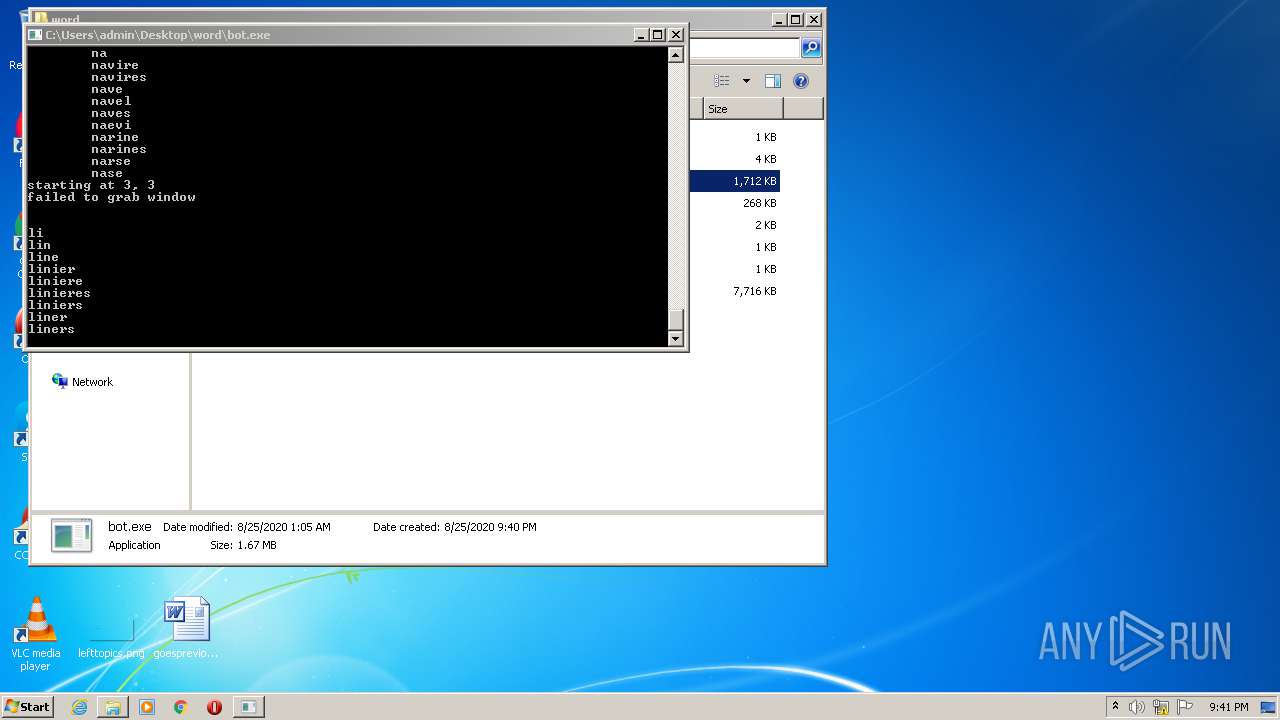
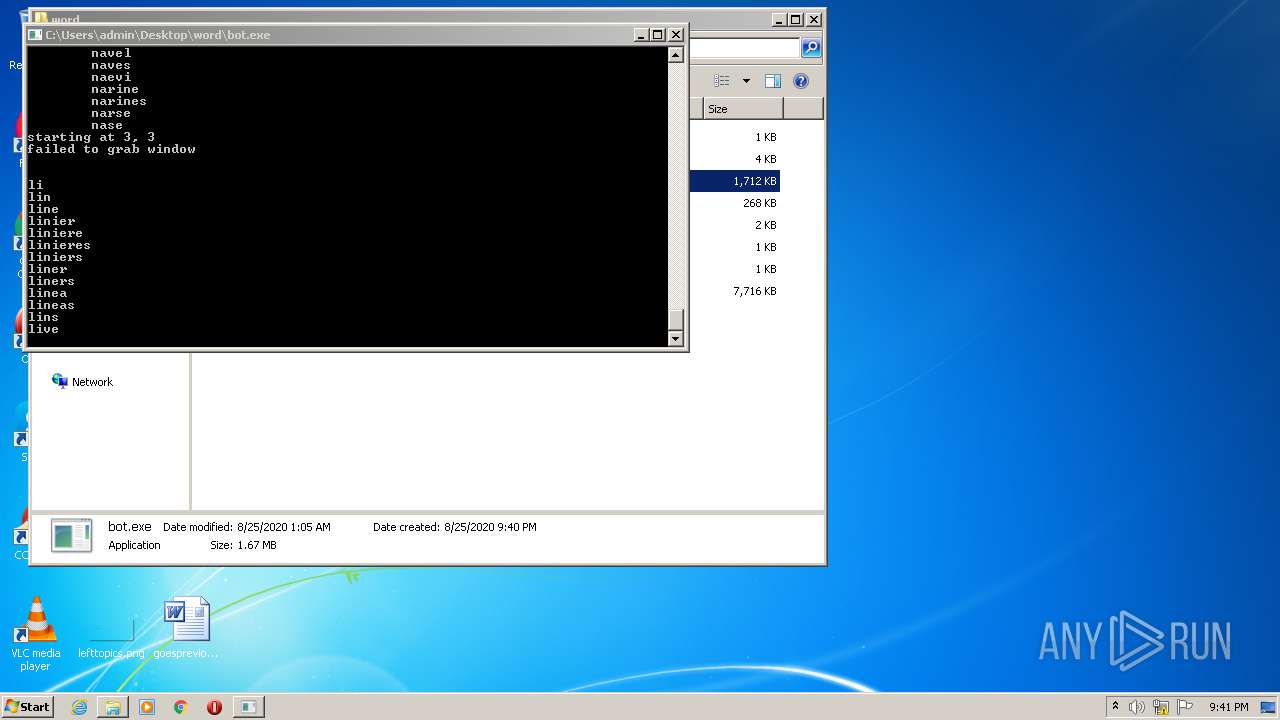
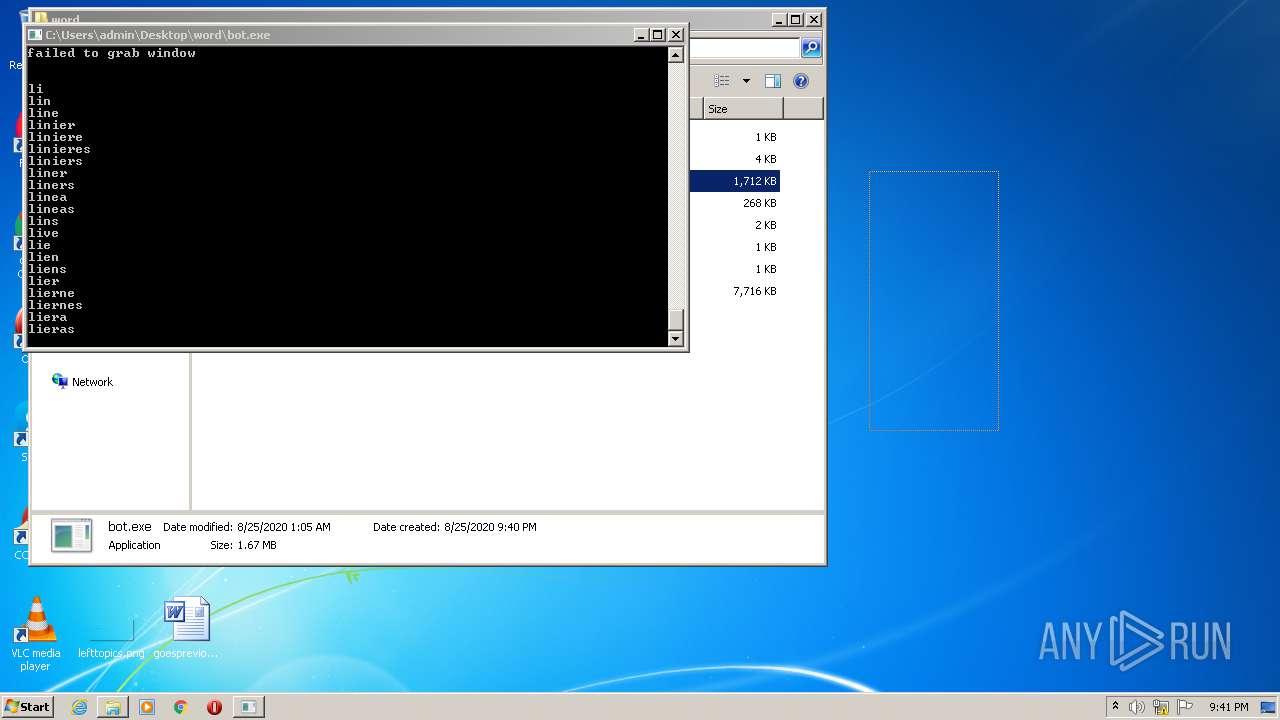
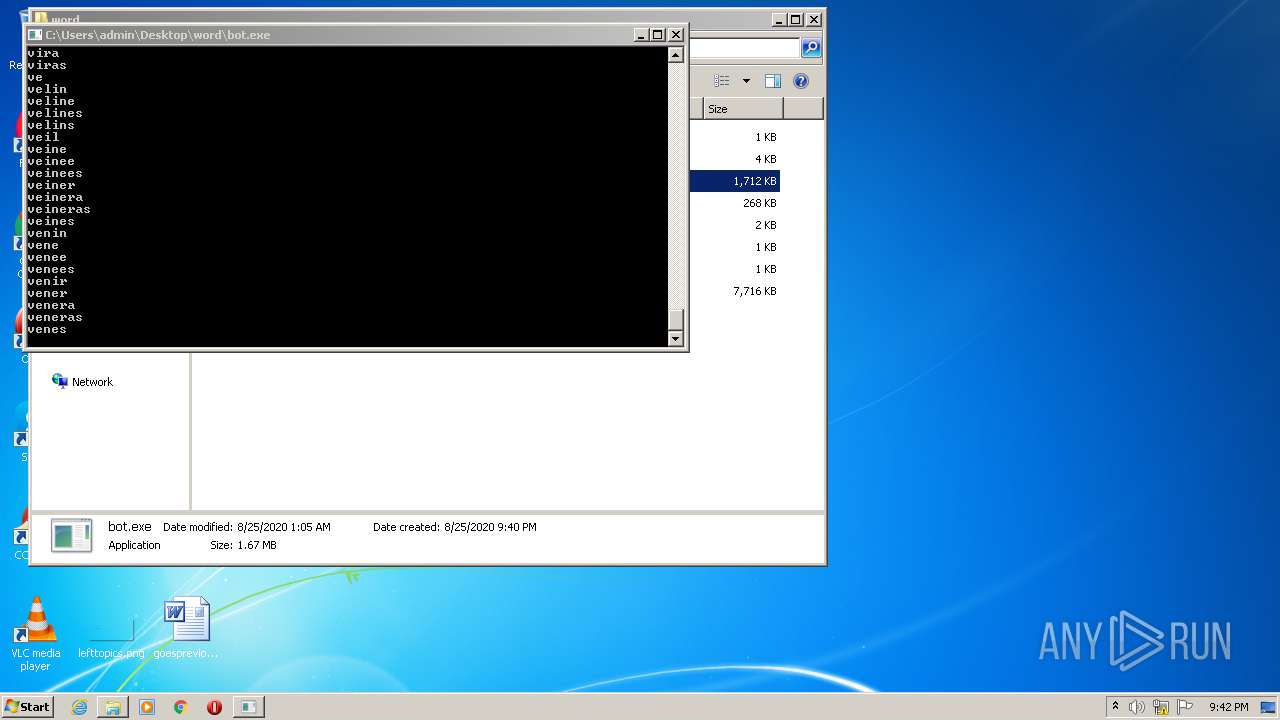
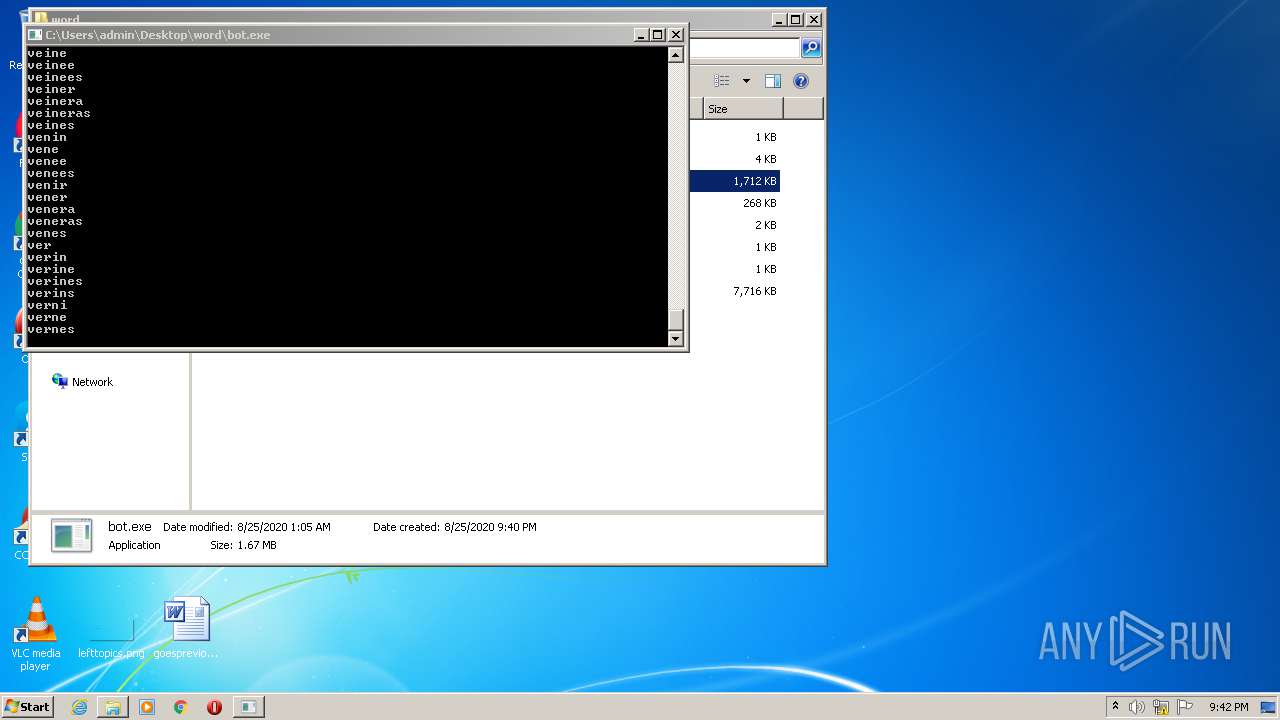
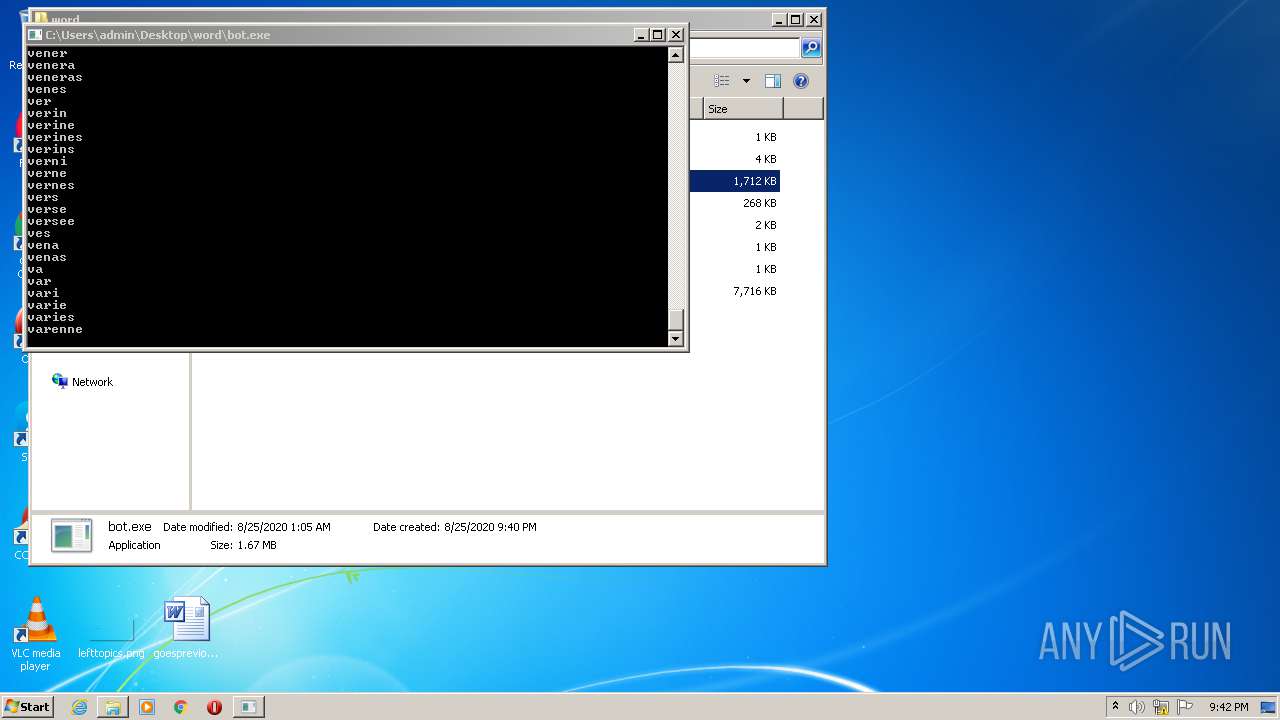
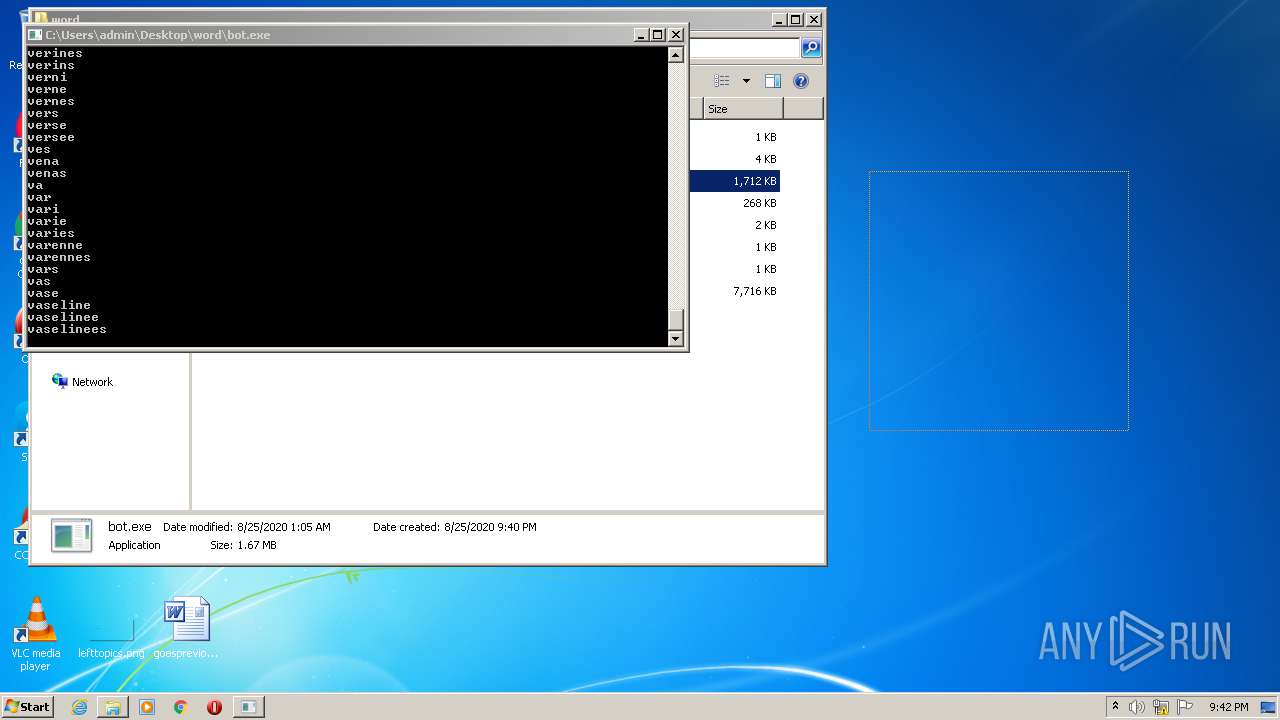
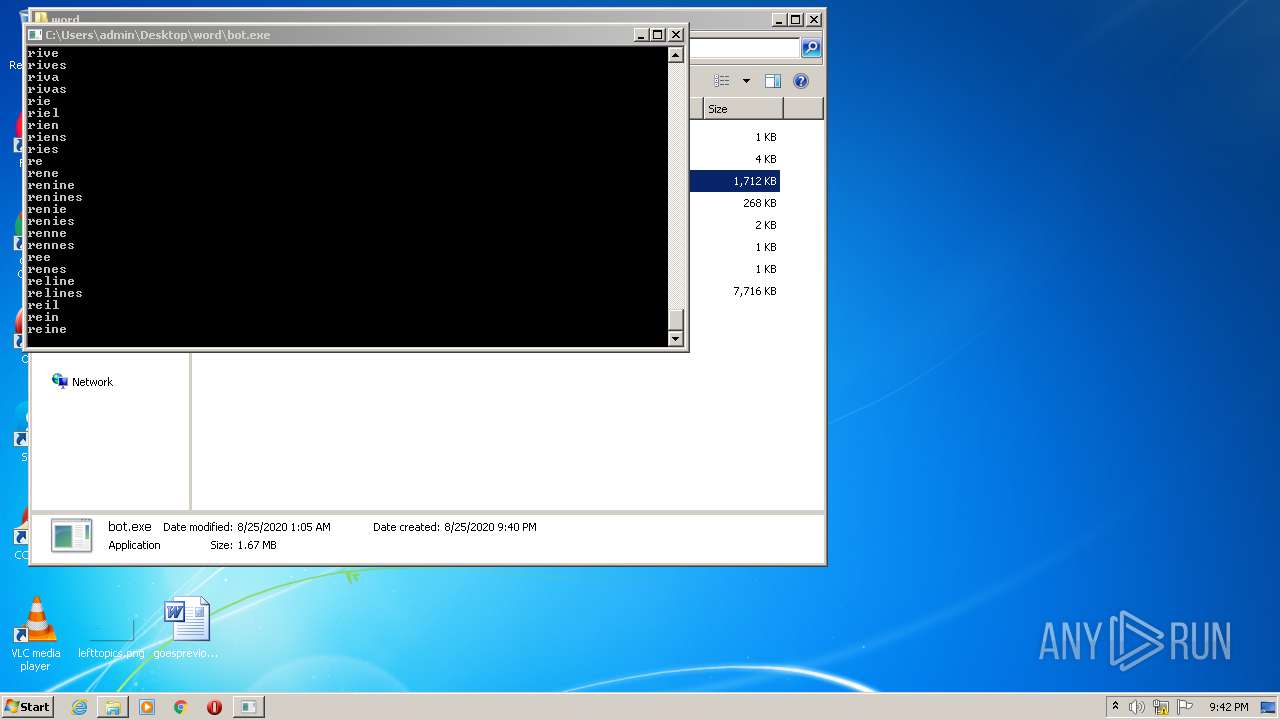
| 1296 | "C:\Users\admin\Desktop\word\bot.exe" | C:\Users\admin\Desktop\word\bot.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225786 Modules
| |||||||||||||||
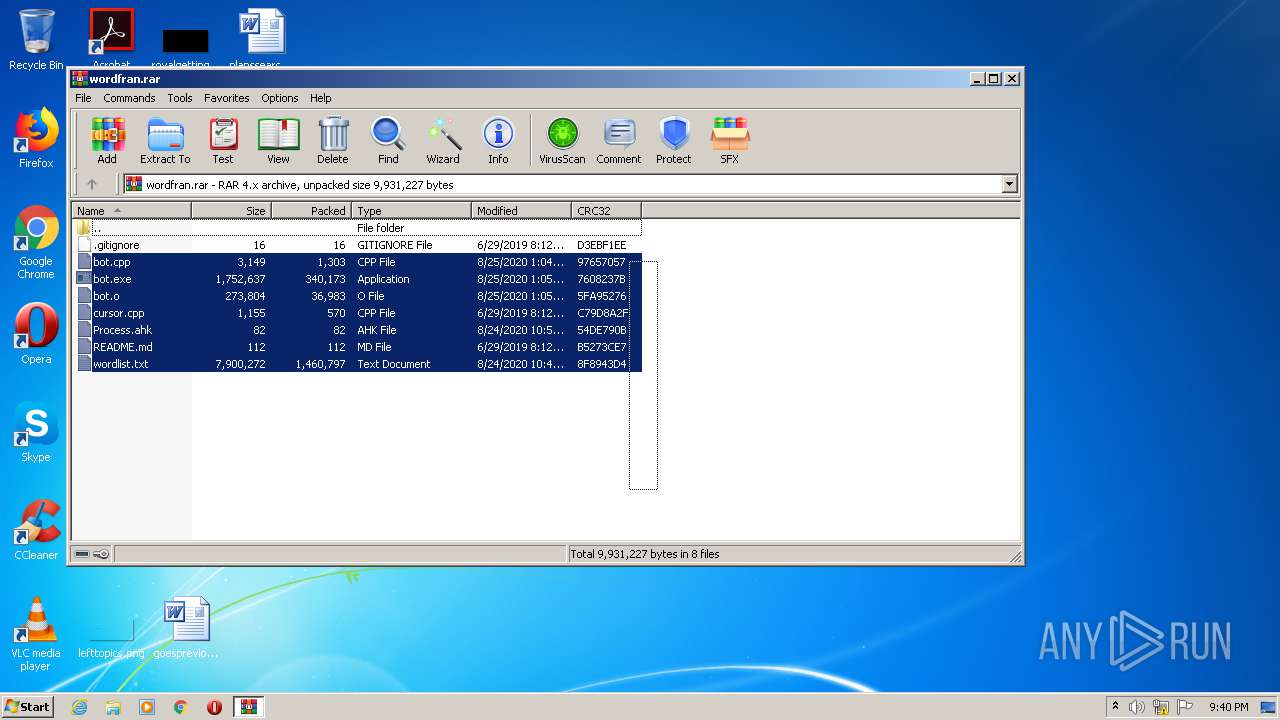
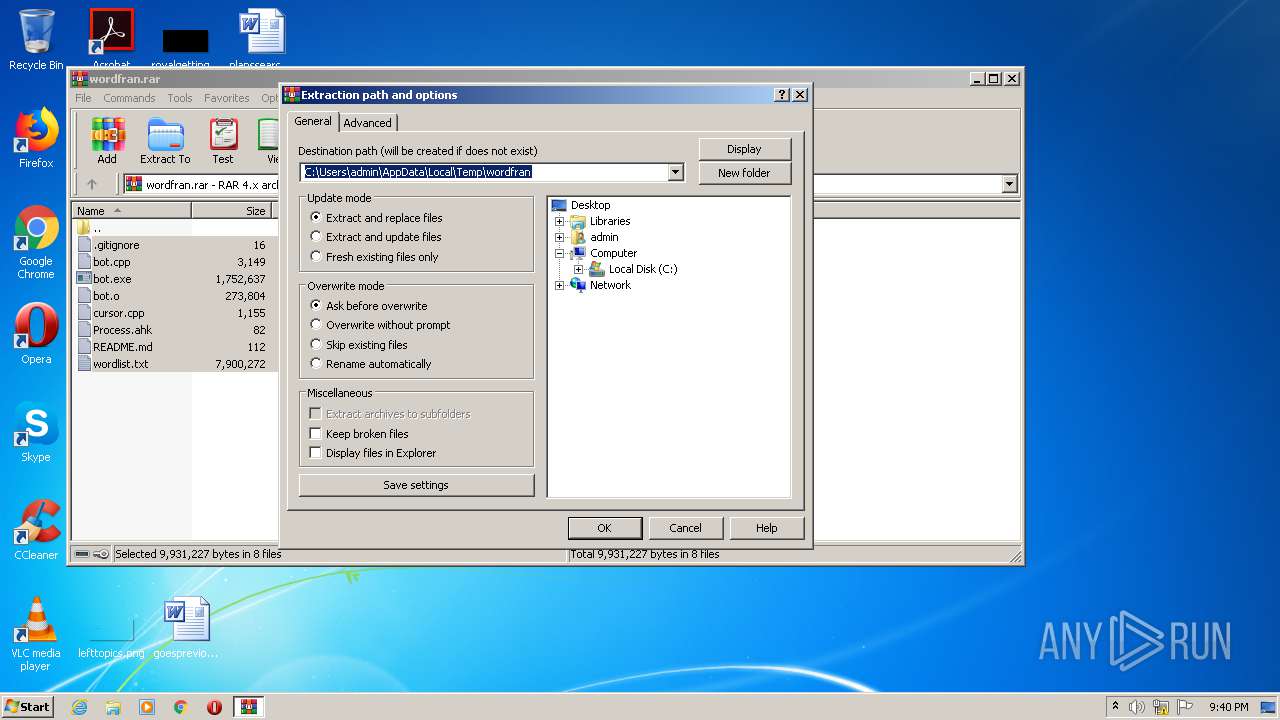
| 2240 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\wordfran.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
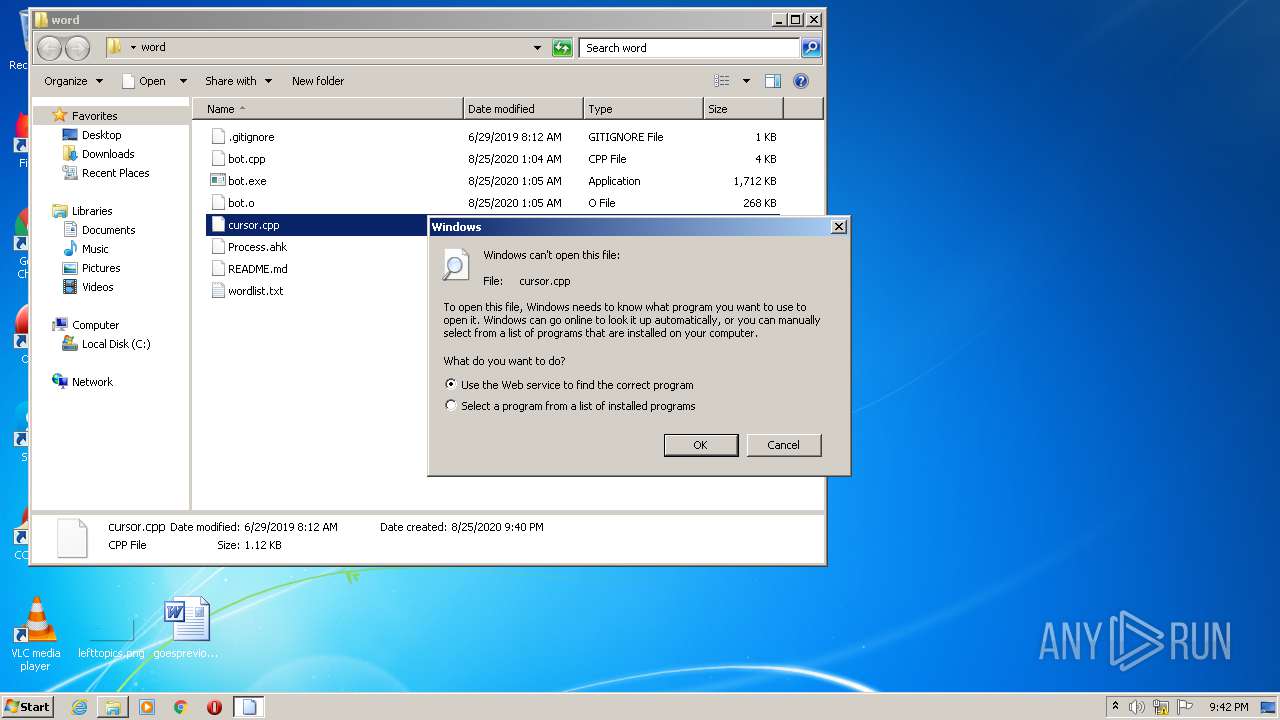
| 3732 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\word\cursor.cpp | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
451
Read events
422
Write events
29
Delete events
0
Modification events
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\NetworkExplorer.dll,-1 |
Value: Network | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\wordfran.rar | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2240) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\137\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
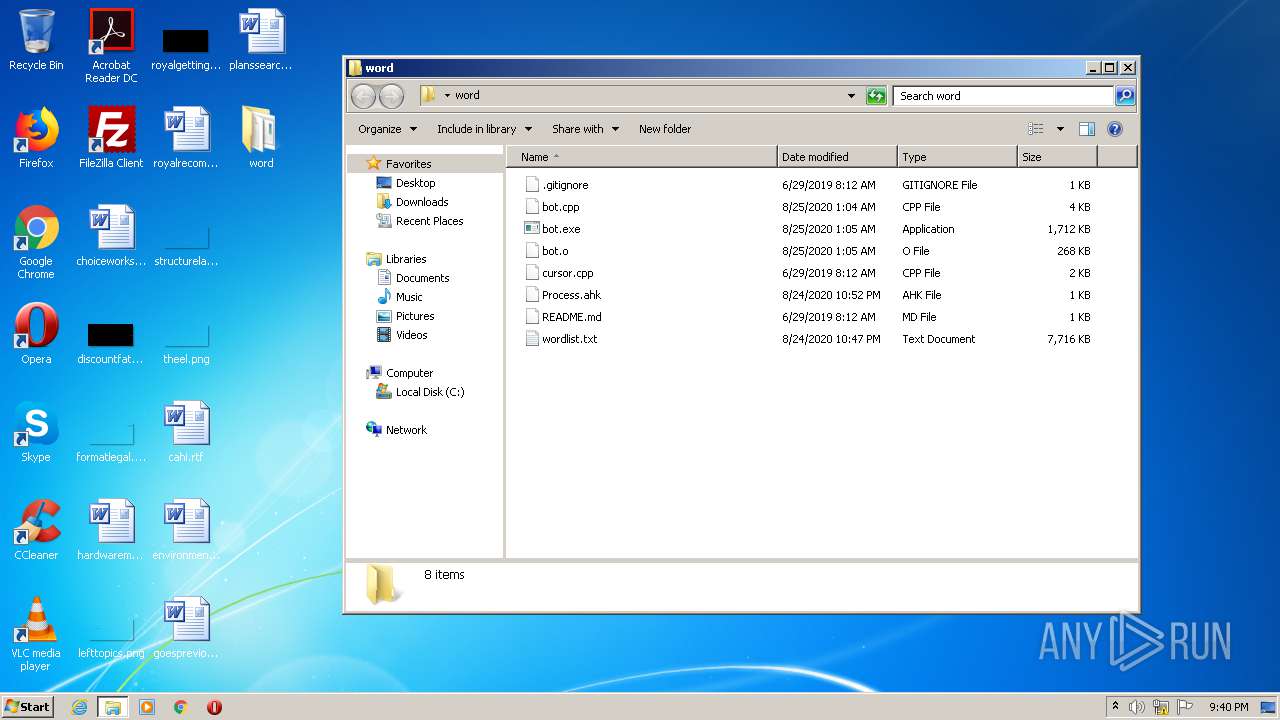
Executable files
1
Suspicious files
0
Text files
5
Unknown types
1
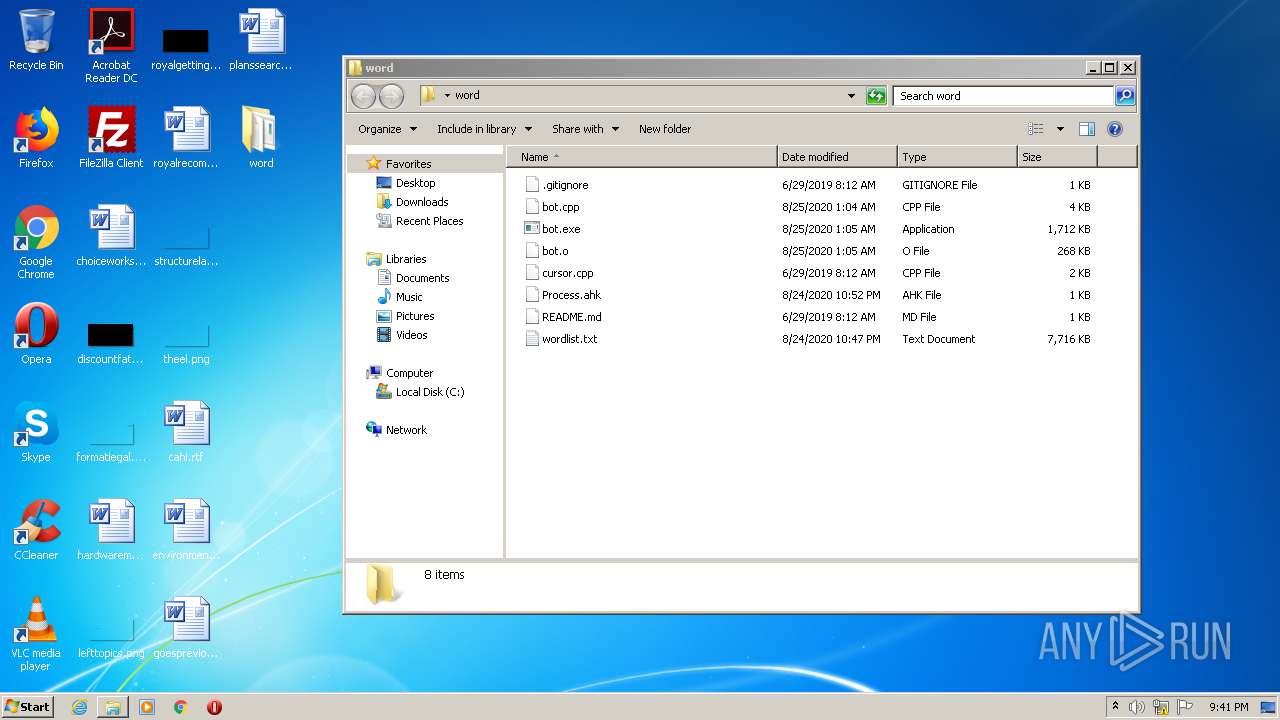
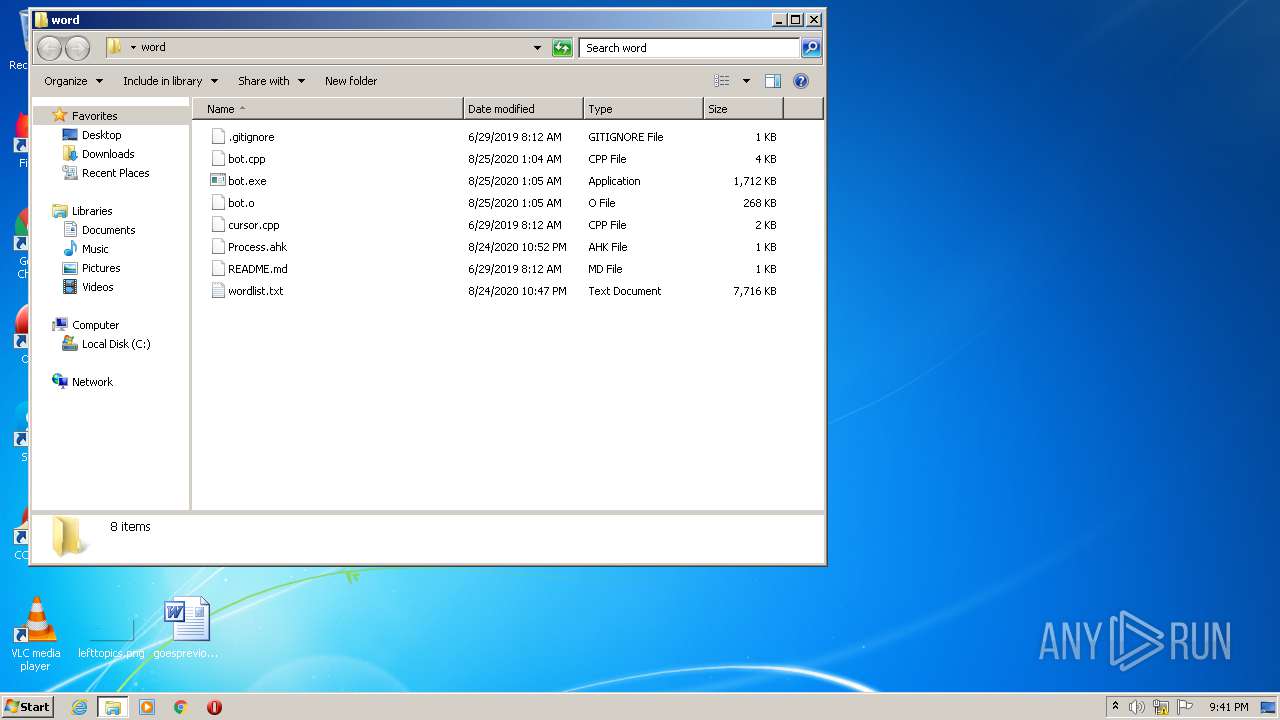
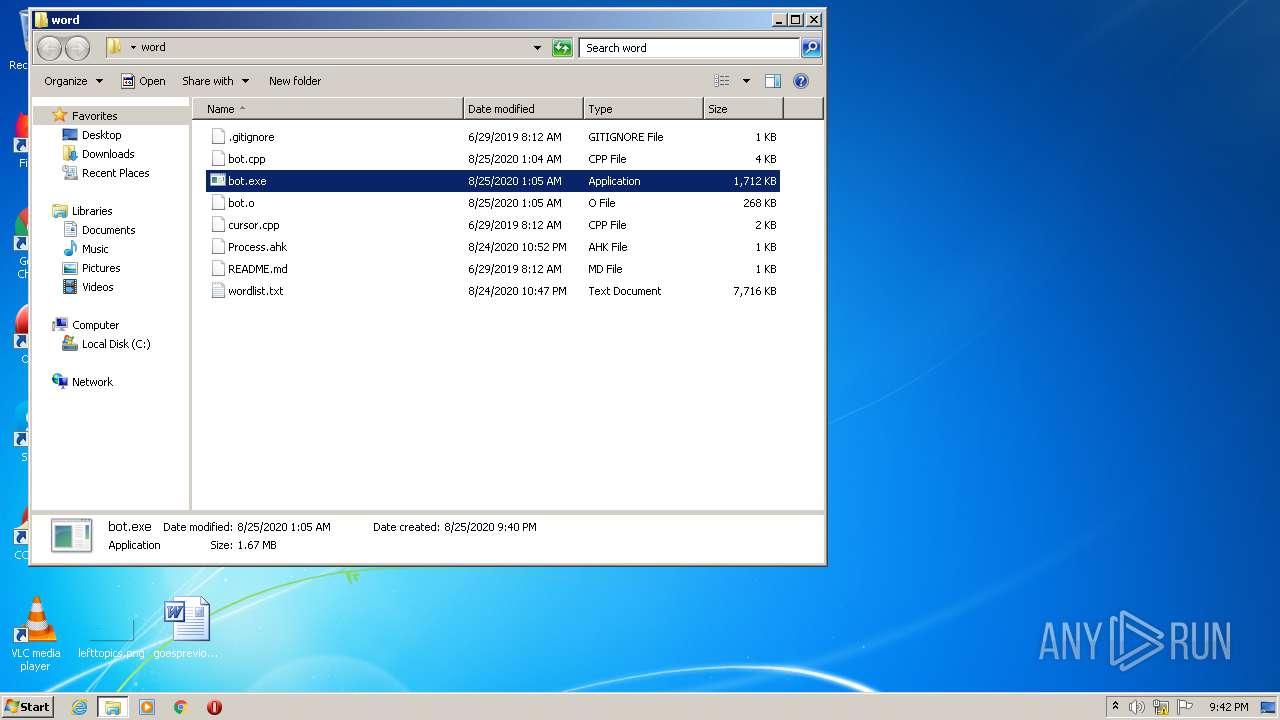
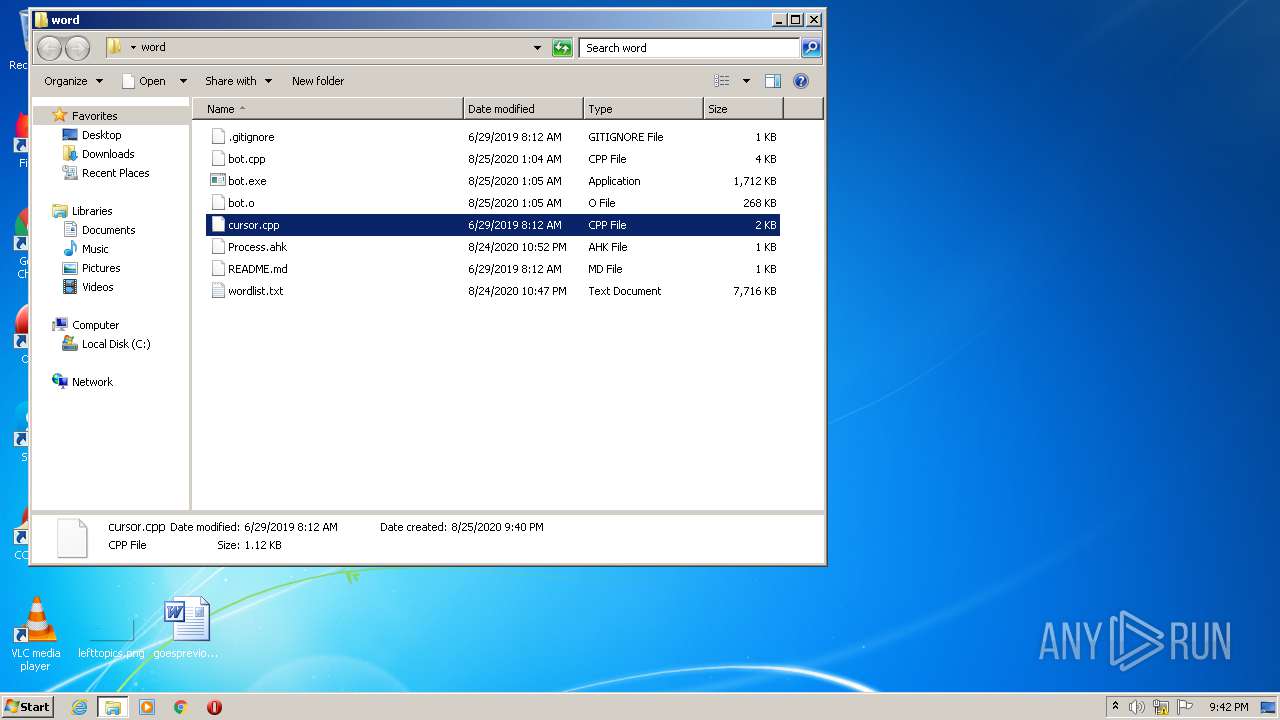
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2240 | WinRAR.exe | C:\Users\admin\Desktop\word\wordlist.txt | — | |
MD5:— | SHA256:— | |||
| 2240 | WinRAR.exe | C:\Users\admin\Desktop\word\.gitignore | text | |
MD5:406F0C0826BE7AC4E87AC0F305C6366C | SHA256:E4D51F68657C969CD570E3865C7CDA09D0F09453E546119553D3800CF4EFBD88 | |||
| 2240 | WinRAR.exe | C:\Users\admin\Desktop\word\Process.ahk | text | |
MD5:82068D2EF7FA6222179EF0922D8F3564 | SHA256:E9245CFA1D7FE18F4F5086ADE994A6F3ABCCC448D6CC762B6A3978FDC1D6362A | |||
| 2240 | WinRAR.exe | C:\Users\admin\Desktop\word\README.md | text | |
MD5:9F2EBE3059F5FA3E1CEB0E9DEDBE6055 | SHA256:6E2CCE23998D0C19E49727B439683639EEA3E81947637E54801660016B00F6DC | |||
| 2240 | WinRAR.exe | C:\Users\admin\Desktop\word\bot.cpp | text | |
MD5:C1015471CBB4E5D585D822119A689DBC | SHA256:E3ED4D5DEB52EB48EF3FF71B98FF32A12BAC1B567FE38BE6E68C08777F90576B | |||
| 2240 | WinRAR.exe | C:\Users\admin\Desktop\word\bot.o | o | |
MD5:98A01C859C8363A6287384E61572A77E | SHA256:D8B531D7540F8CD2A56F25DADE3D9C7E6EC736DE16AB3BC5878C1137FDE25D22 | |||
| 2240 | WinRAR.exe | C:\Users\admin\Desktop\word\cursor.cpp | text | |
MD5:2FF99E61E0100A05C9A857E1A4A06BD5 | SHA256:8F1FAB408A9842A757F461B69420A8341B1E38FFDB2C5146F61EEA44015AD884 | |||
| 2240 | WinRAR.exe | C:\Users\admin\Desktop\word\bot.exe | executable | |
MD5:3CC6FCD23FE217450775015CC10FBAAB | SHA256:B96BD0D0CE3CC51877855B10CAEBCEFD3C377717C71591ECF2739495D1AFC117 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report