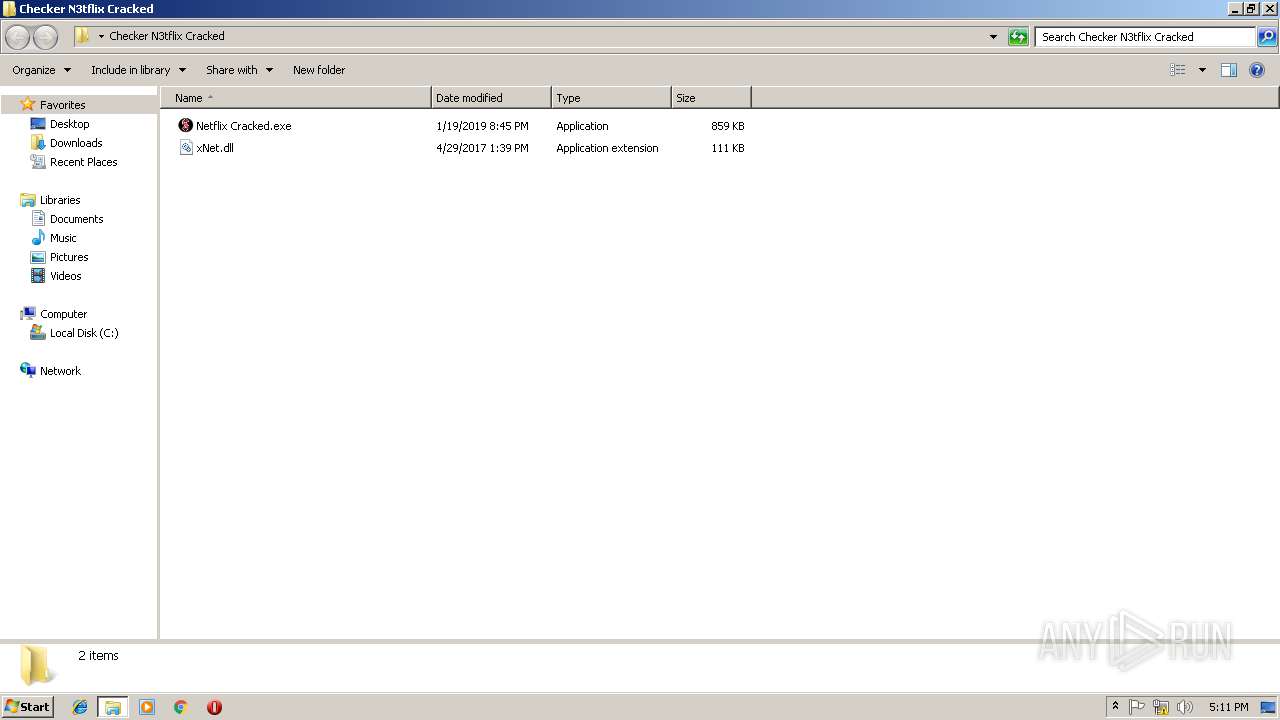
| File name: | Checker N3tflix Cracked.zip |
| Full analysis: | https://app.any.run/tasks/b0ab225f-45ac-41c1-b032-382a606bcf6a |
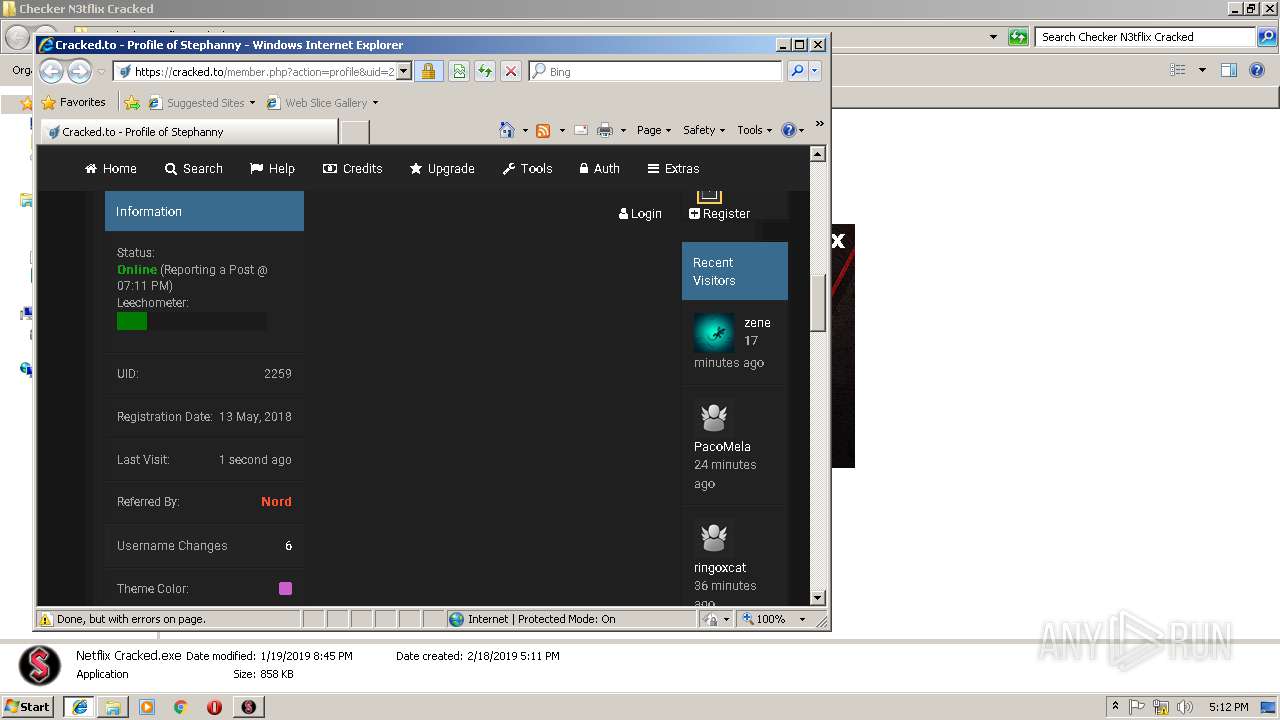
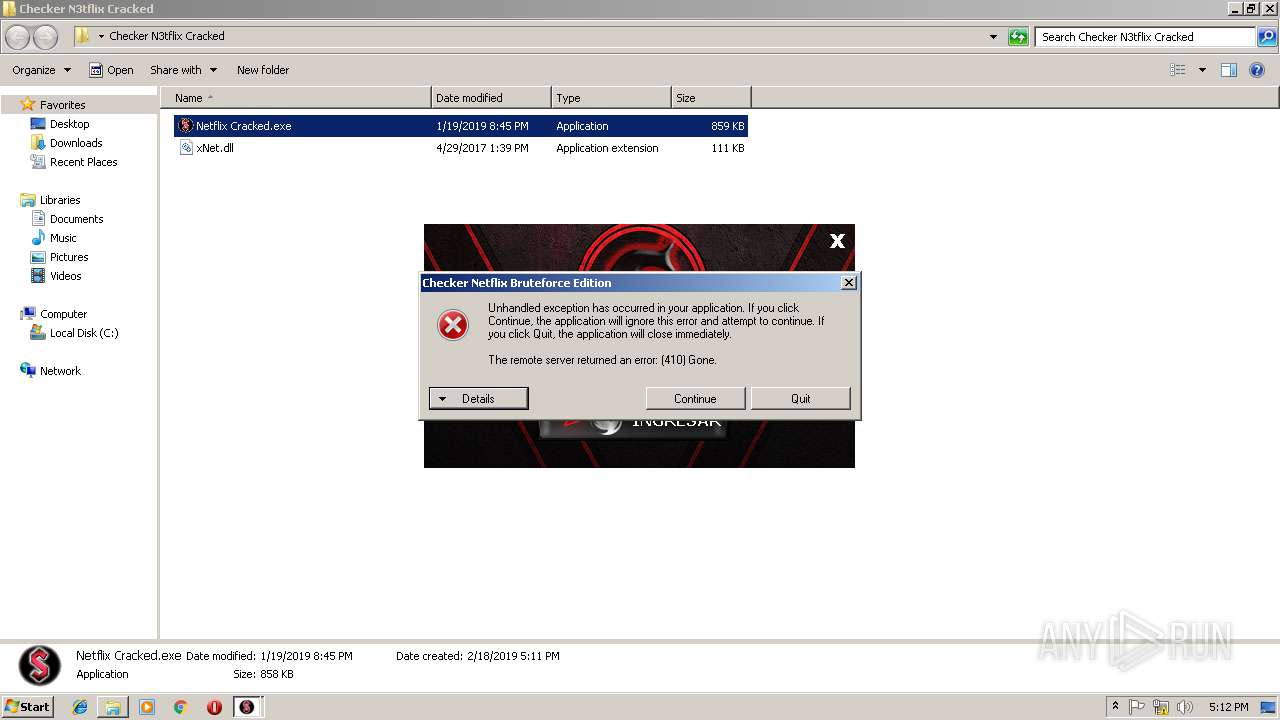
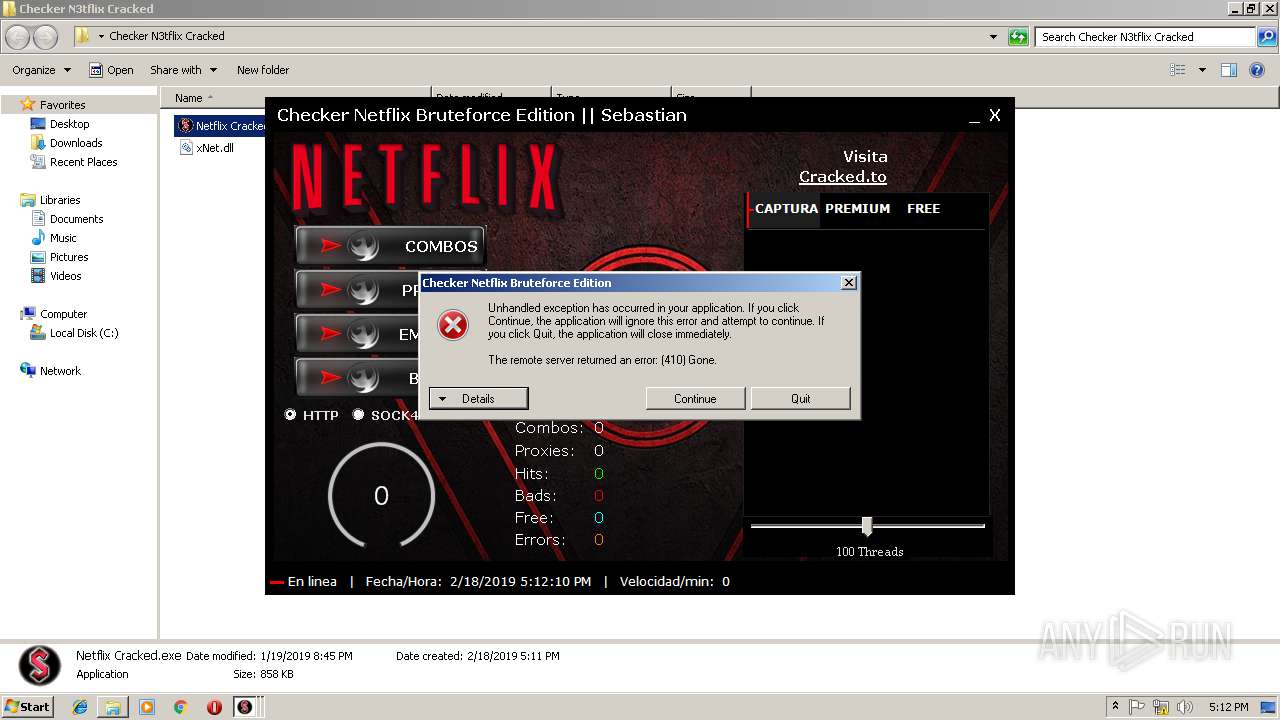
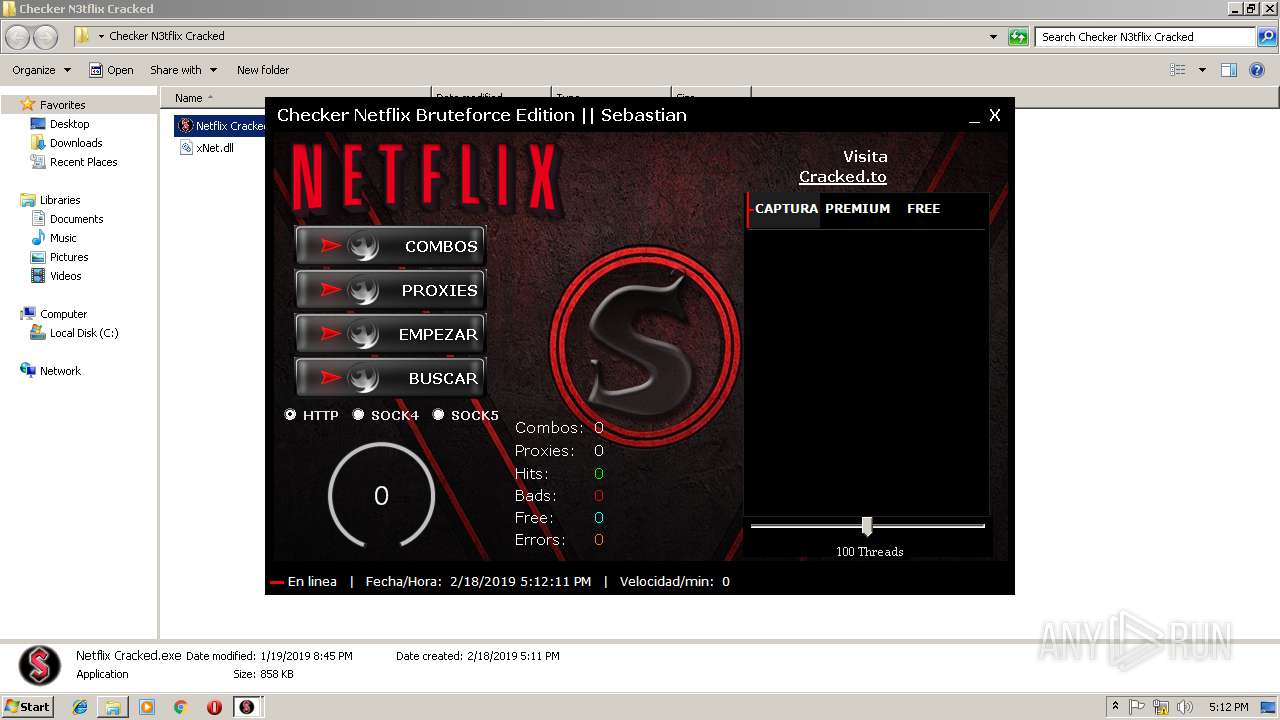
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 17:11:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 610B6700840D068715B25ABED12517B2 |
| SHA1: | ED60A401241745258ED7E68B60BC7858B5ADFBA5 |
| SHA256: | 173EE42A7A44A553B05765C2924CA57B2AC4E525FA0229F3DABFD16112E59386 |
| SSDEEP: | 12288:VrLcJliNKVF4kMPwwdMqLOq8QqNtsSqh84HWqg:VSlUMF4kMxFYt0XHW9 |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 952)
Application was dropped or rewritten from another process
- Netflix Cracked.exe (PID: 2804)
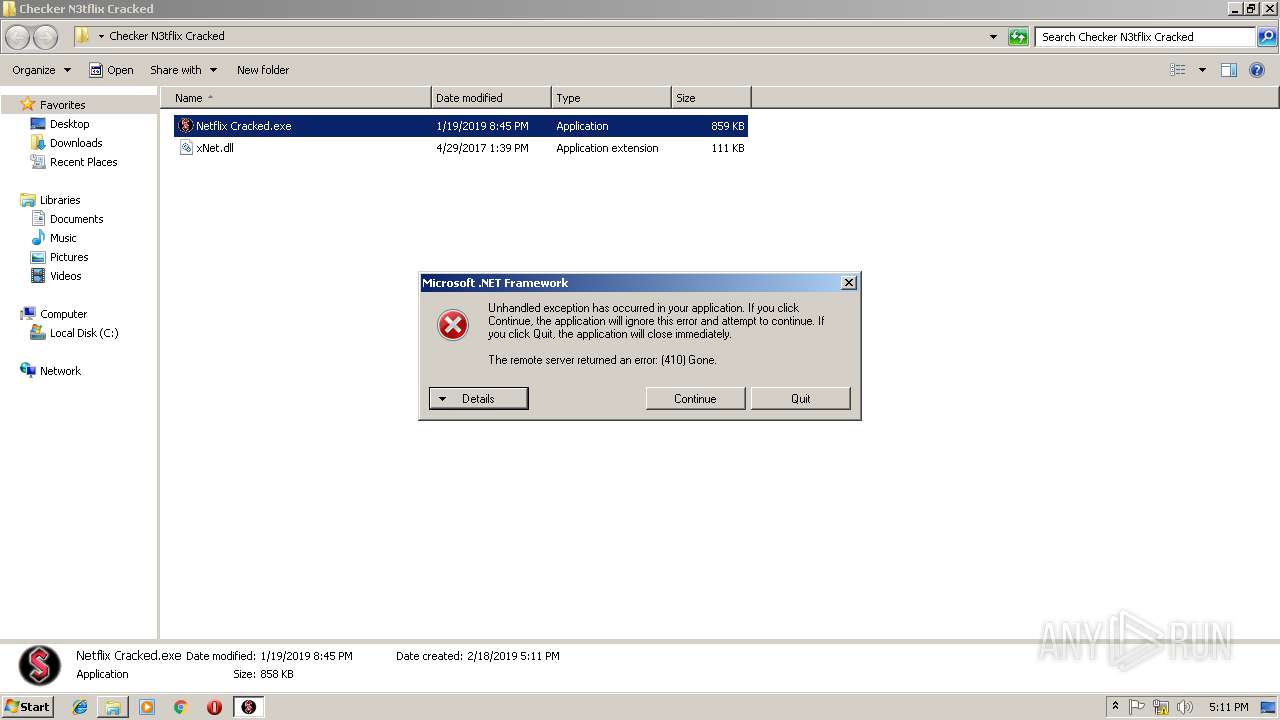
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2892)
Reads Environment values
- Netflix Cracked.exe (PID: 2804)
Reads Internet Cache Settings
- Netflix Cracked.exe (PID: 2804)
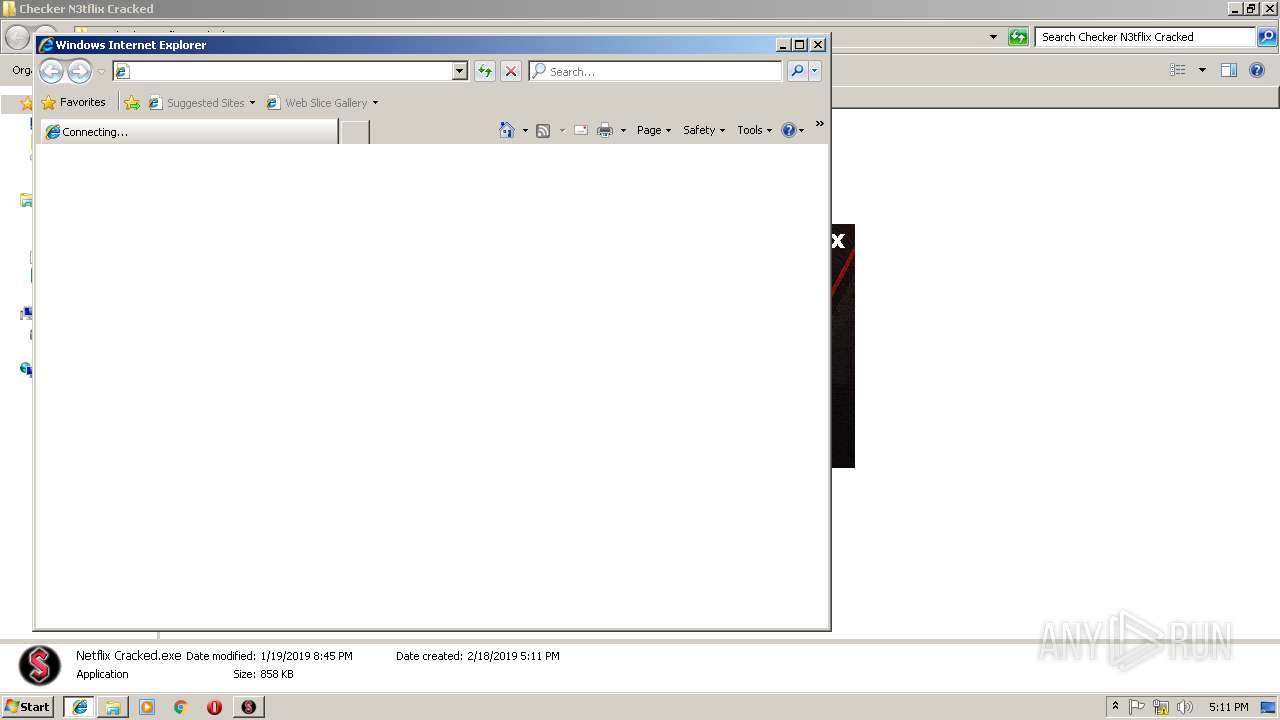
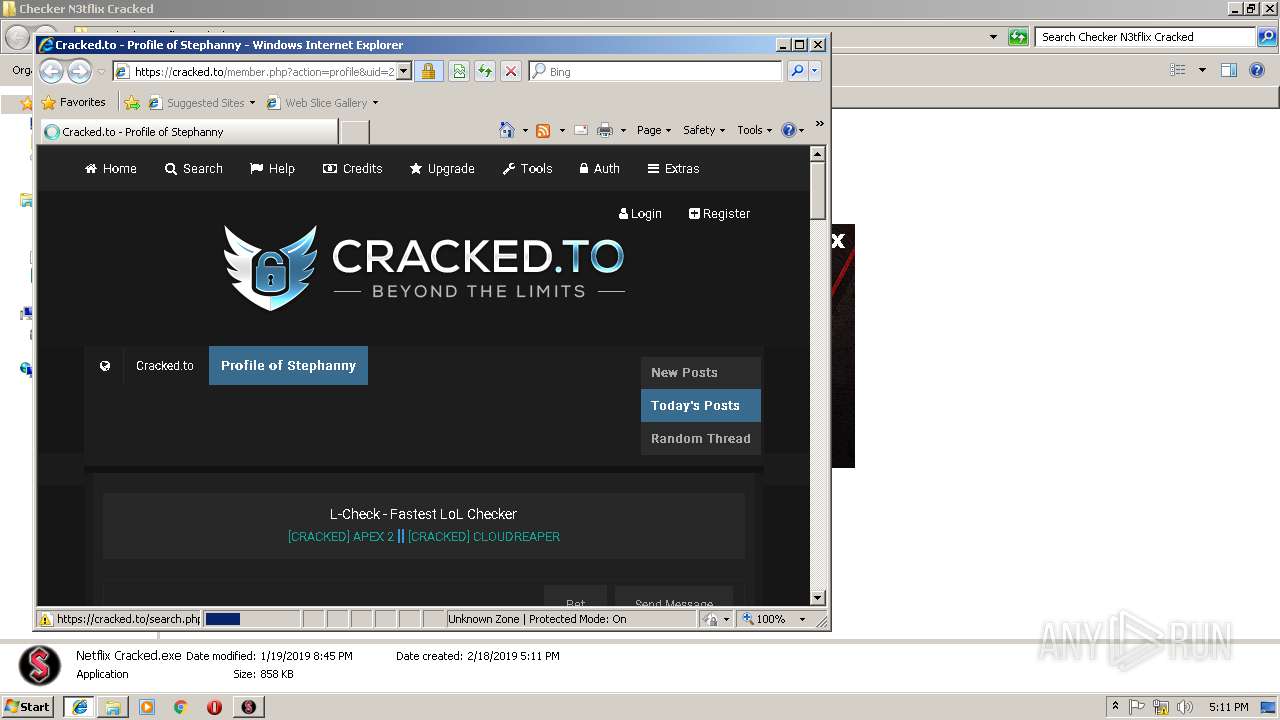
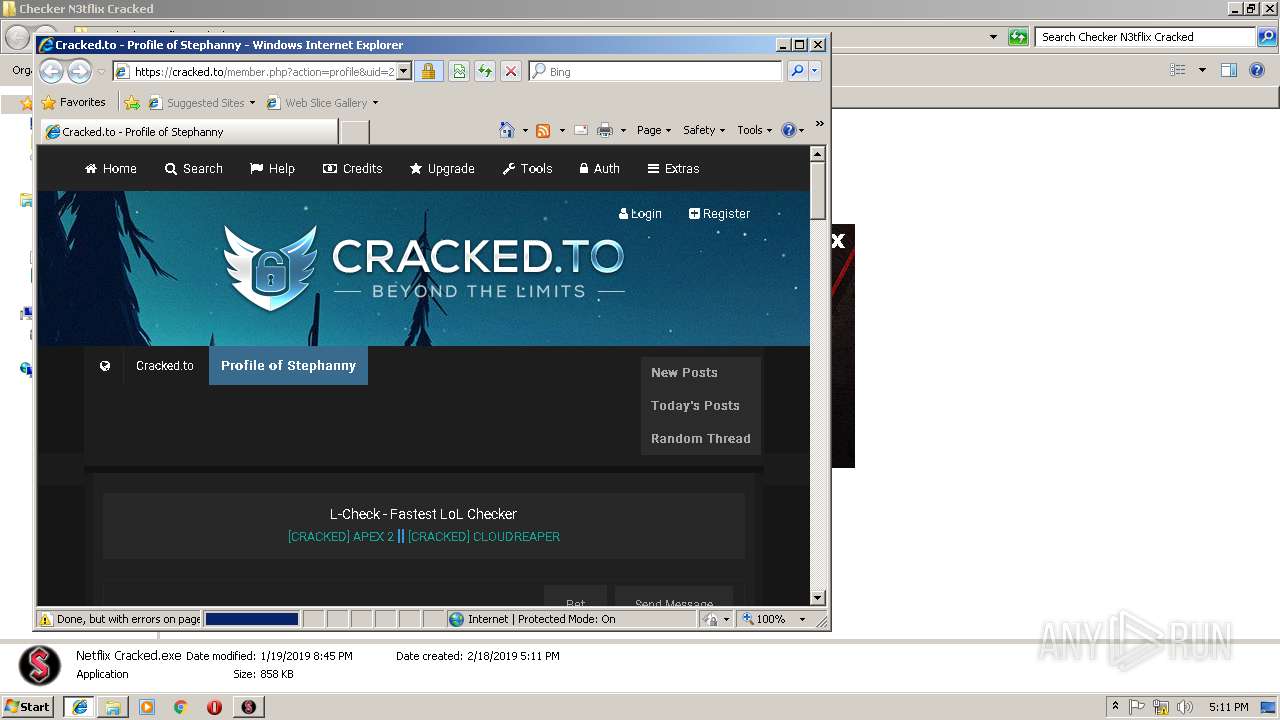
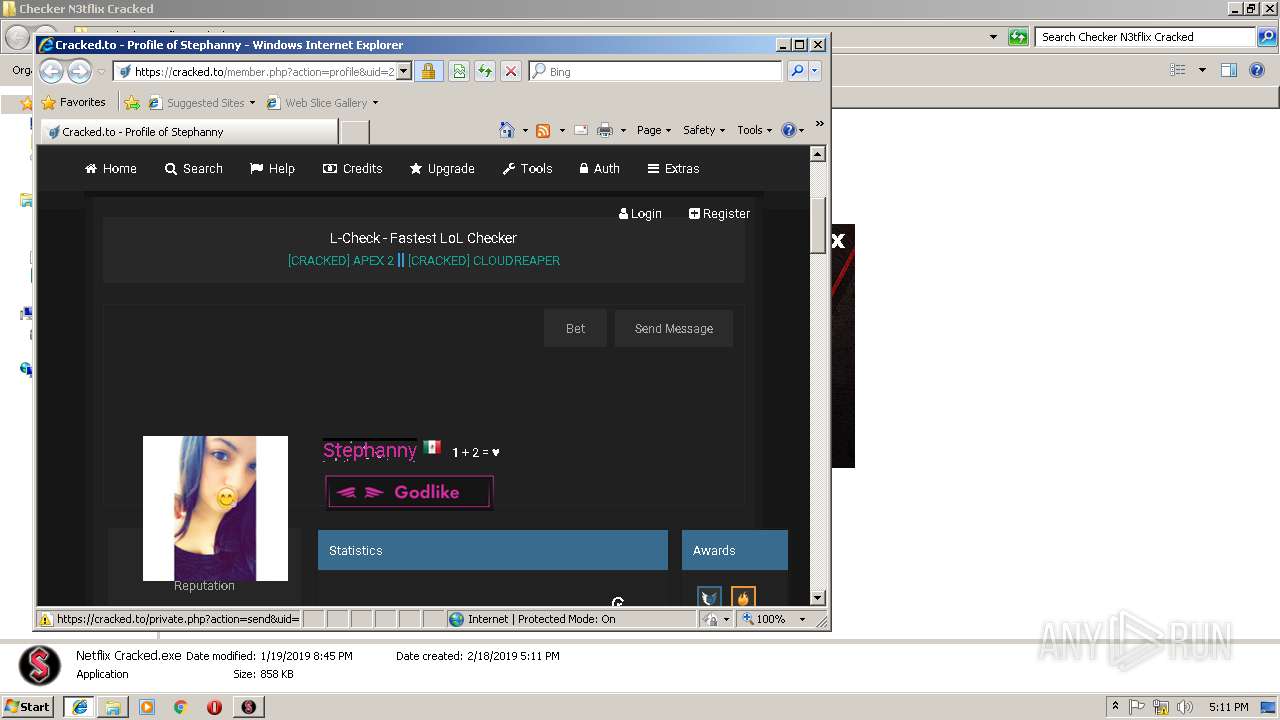
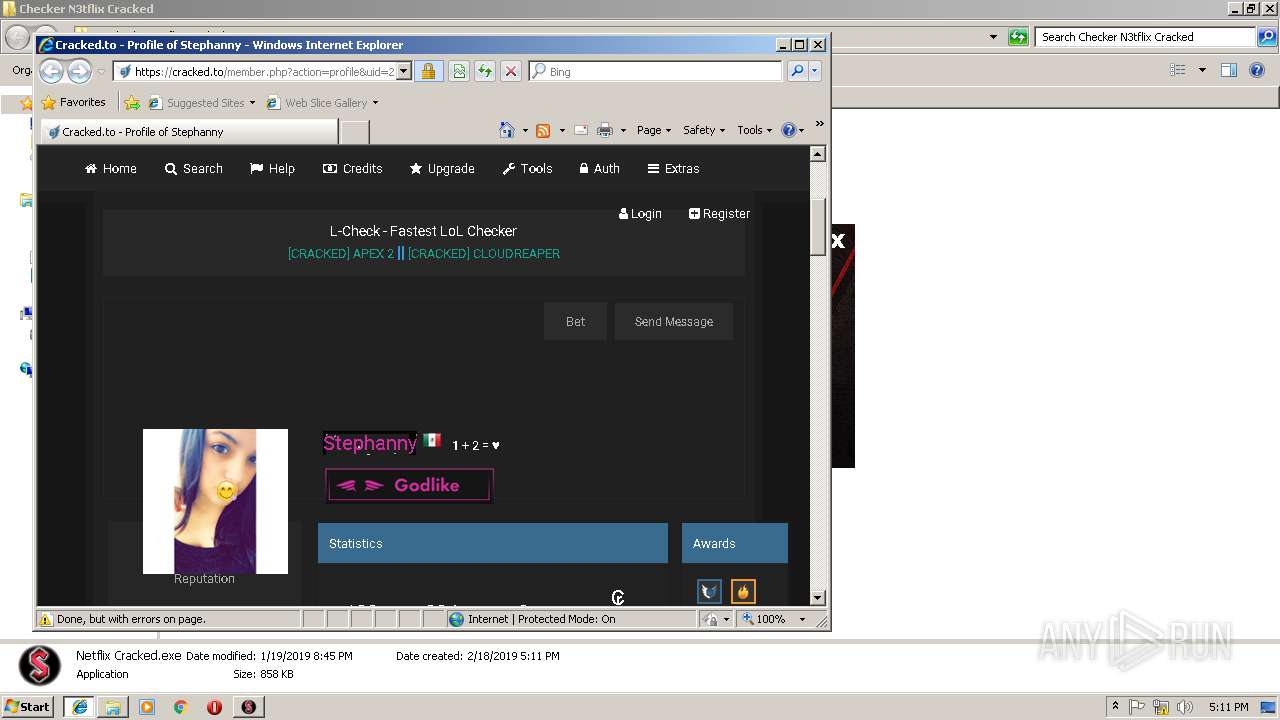
Starts Internet Explorer
- Netflix Cracked.exe (PID: 2804)
Creates files in the user directory
- Netflix Cracked.exe (PID: 2804)
INFO
Reads settings of System Certificates
- iexplore.exe (PID: 932)
Creates files in the user directory
- iexplore.exe (PID: 2628)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2560)
- iexplore.exe (PID: 932)
Reads internet explorer settings
- iexplore.exe (PID: 2628)
Changes internet zones settings
- iexplore.exe (PID: 932)
Application launched itself
- iexplore.exe (PID: 932)
Reads Internet Cache Settings
- iexplore.exe (PID: 2628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:01:20 00:14:28 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | Checker N3tflix Cracked/ |
Total processes
36
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 932 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Netflix Cracked.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 952 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe6_ Global\UsGthrCtrlFltPipeMssGthrPipe6 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2560 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:932 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
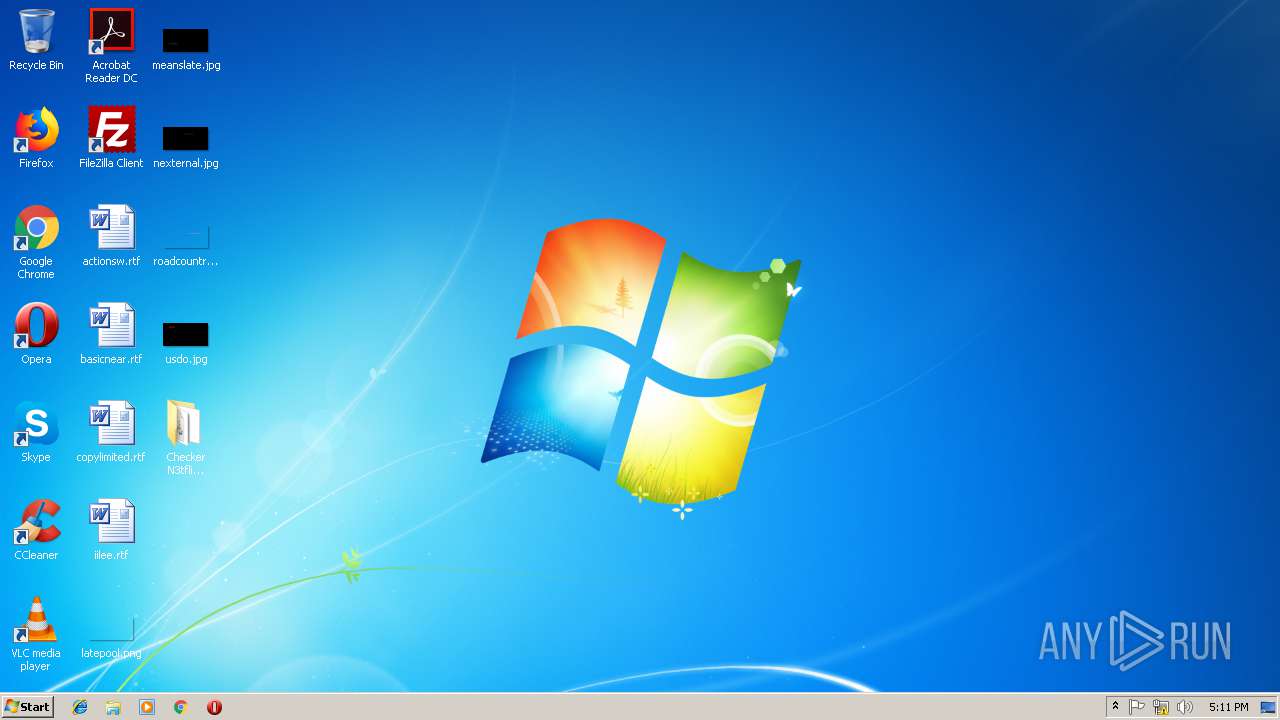
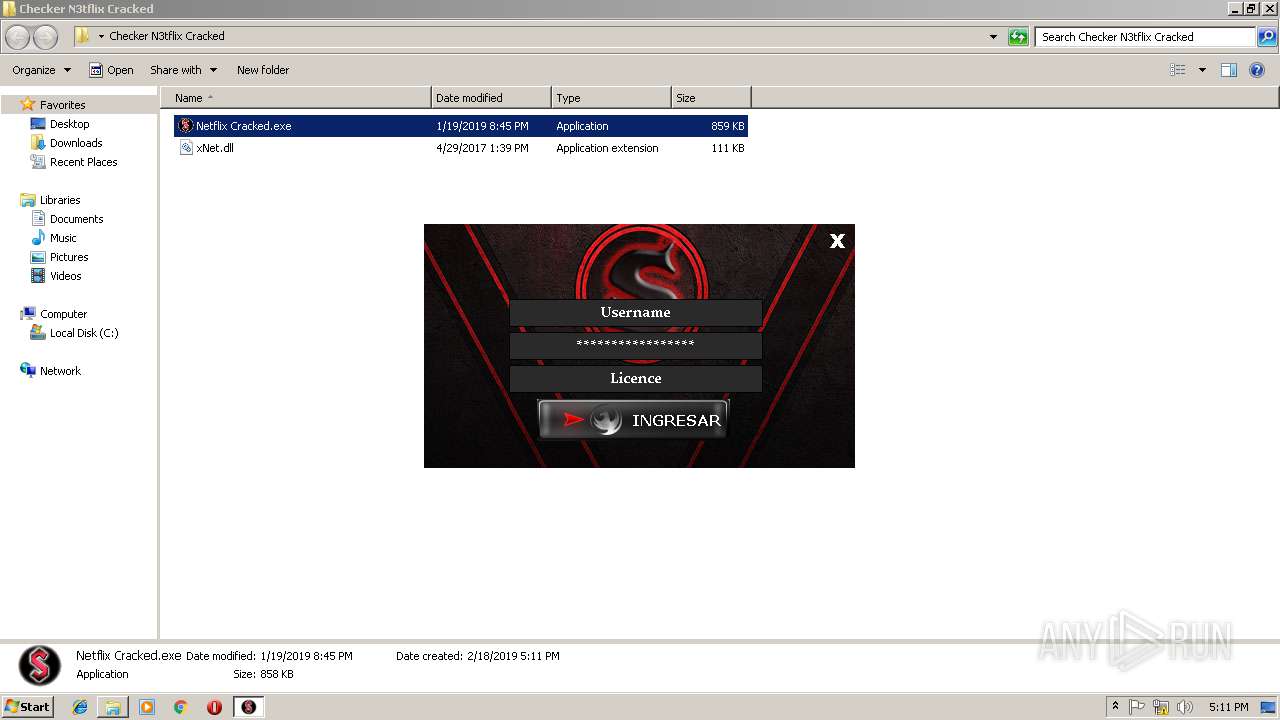
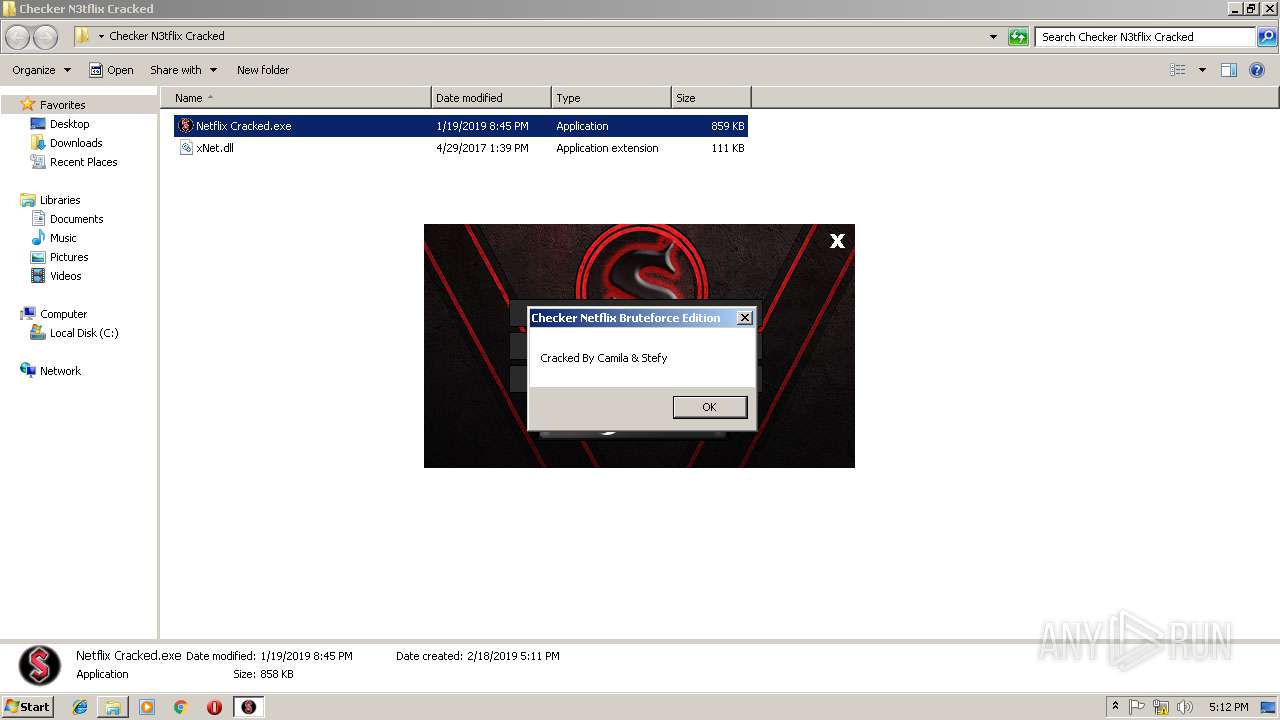
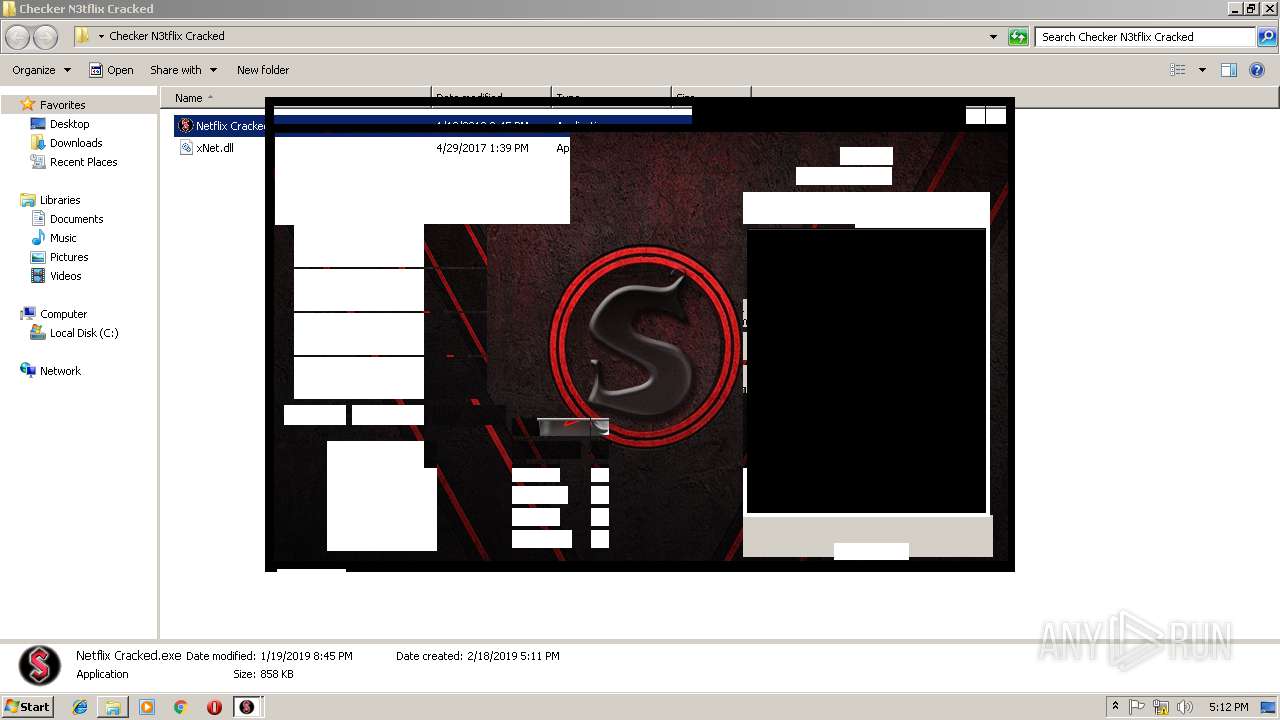
| 2804 | "C:\Users\admin\Desktop\Checker N3tflix Cracked\Netflix Cracked.exe" | C:\Users\admin\Desktop\Checker N3tflix Cracked\Netflix Cracked.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Checker Netflix Bruteforce Edition || Sebastian Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
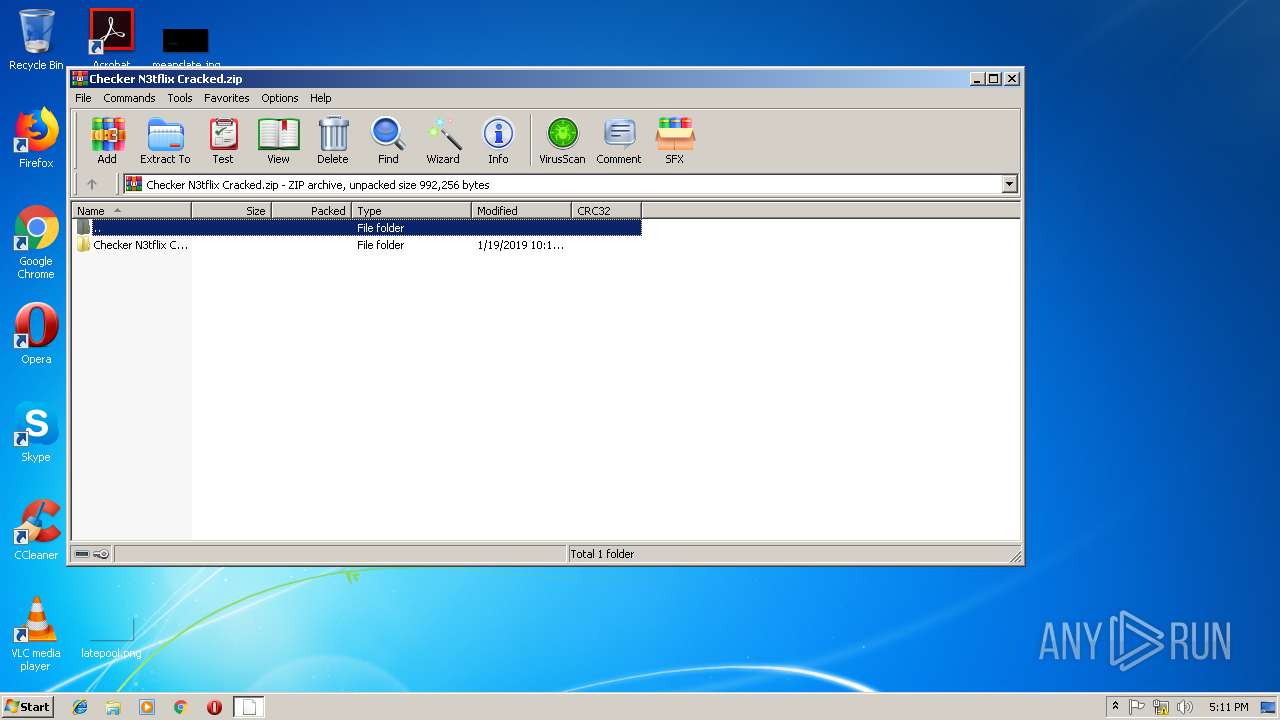
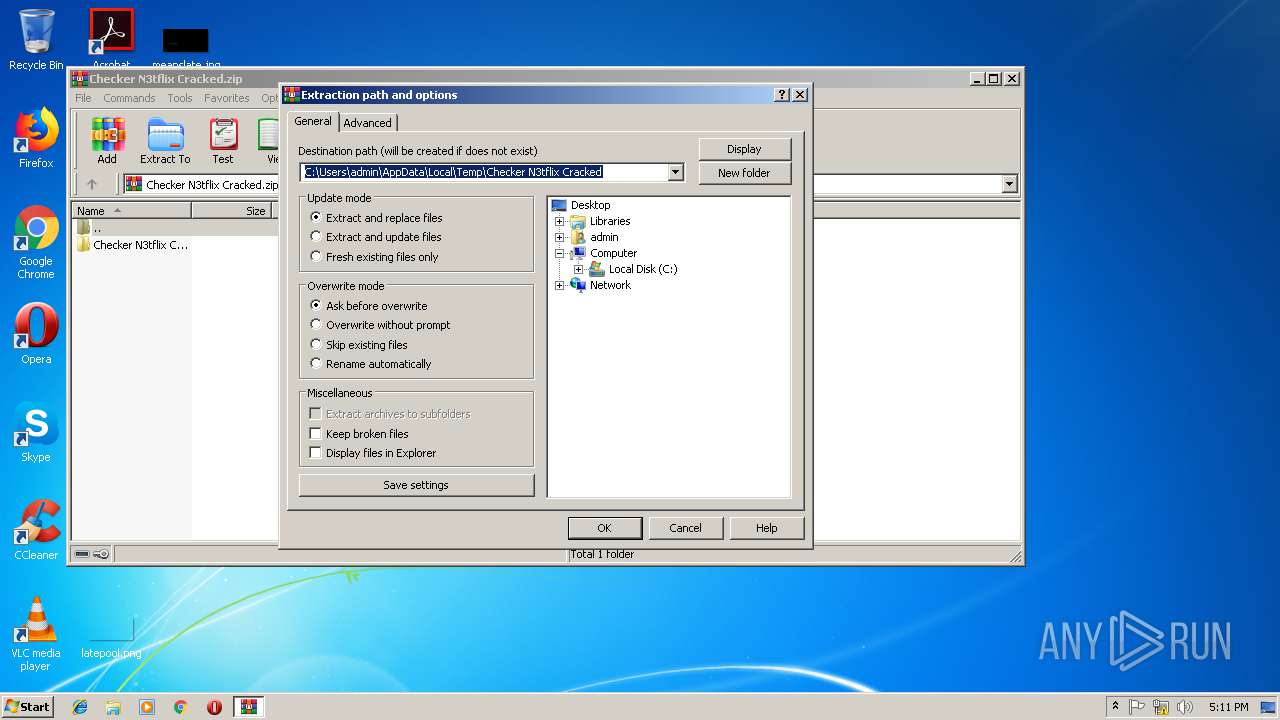
| 2892 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Checker N3tflix Cracked.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
1 326
Read events
1 212
Write events
110
Delete events
4
Modification events
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Checker N3tflix Cracked.zip | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
Executable files
2
Suspicious files
2
Text files
77
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 932 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 932 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@cracked[1].txt | — | |
MD5:— | SHA256:— | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\member[1].php | — | |
MD5:— | SHA256:— | |||
| 2892 | WinRAR.exe | C:\Users\admin\Desktop\Checker N3tflix Cracked\Netflix Cracked.exe | executable | |
MD5:— | SHA256:— | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@cracked[2].txt | text | |
MD5:— | SHA256:— | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\member[1].htm | html | |
MD5:— | SHA256:— | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\general[1].js | text | |
MD5:— | SHA256:— | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\tabbed.min[1].css | text | |
MD5:— | SHA256:— | |||
| 2628 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\js[1] | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
22
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
932 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2804 | Netflix Cracked.exe | 216.58.207.46:443 | docs.google.com | Google Inc. | US | whitelisted |
932 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2628 | iexplore.exe | 104.24.1.112:443 | cracked.to | Cloudflare Inc | US | shared |
2628 | iexplore.exe | 104.19.199.151:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | shared |
2628 | iexplore.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2628 | iexplore.exe | 172.217.22.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2628 | iexplore.exe | 172.217.22.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2628 | iexplore.exe | 172.217.22.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2628 | iexplore.exe | 172.217.16.194:443 | www.googleadservices.com | Google Inc. | US | whitelisted |
2628 | iexplore.exe | 172.217.21.226:443 | googleads.g.doubleclick.net | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
docs.google.com |
| shared |
www.bing.com |
| whitelisted |
cracked.to |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
maxcdn.bootstrapcdn.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |