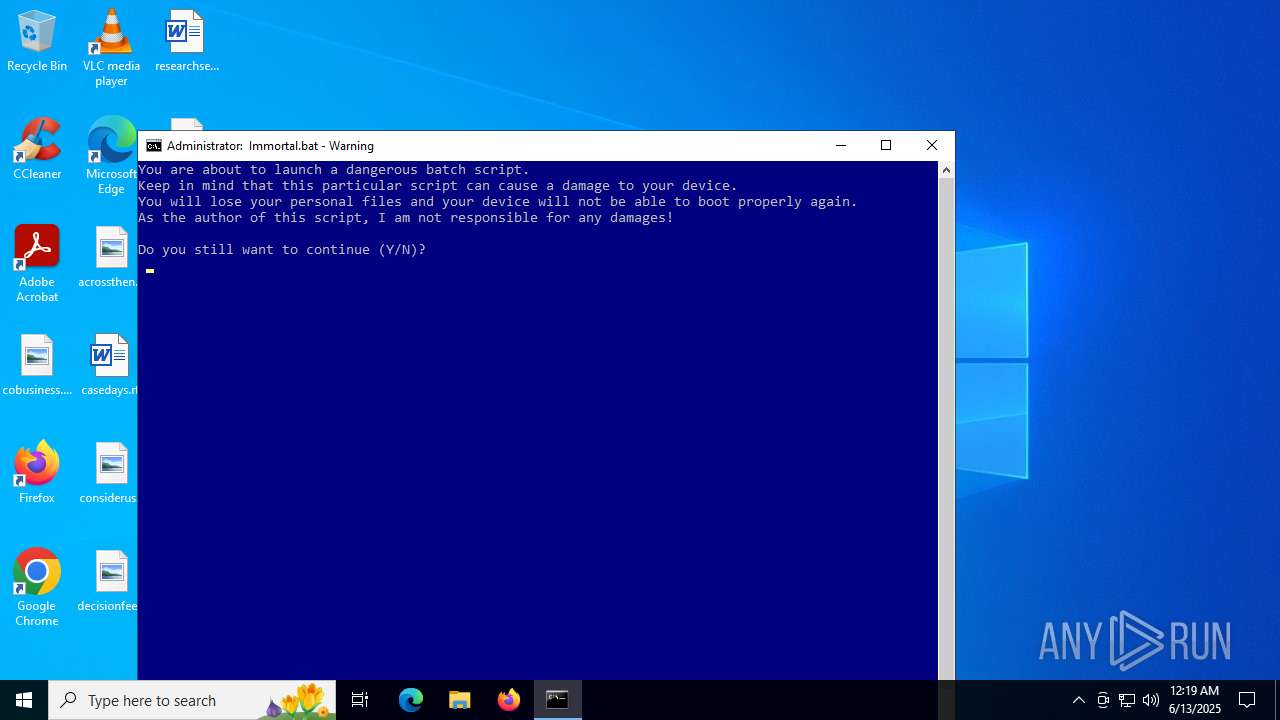
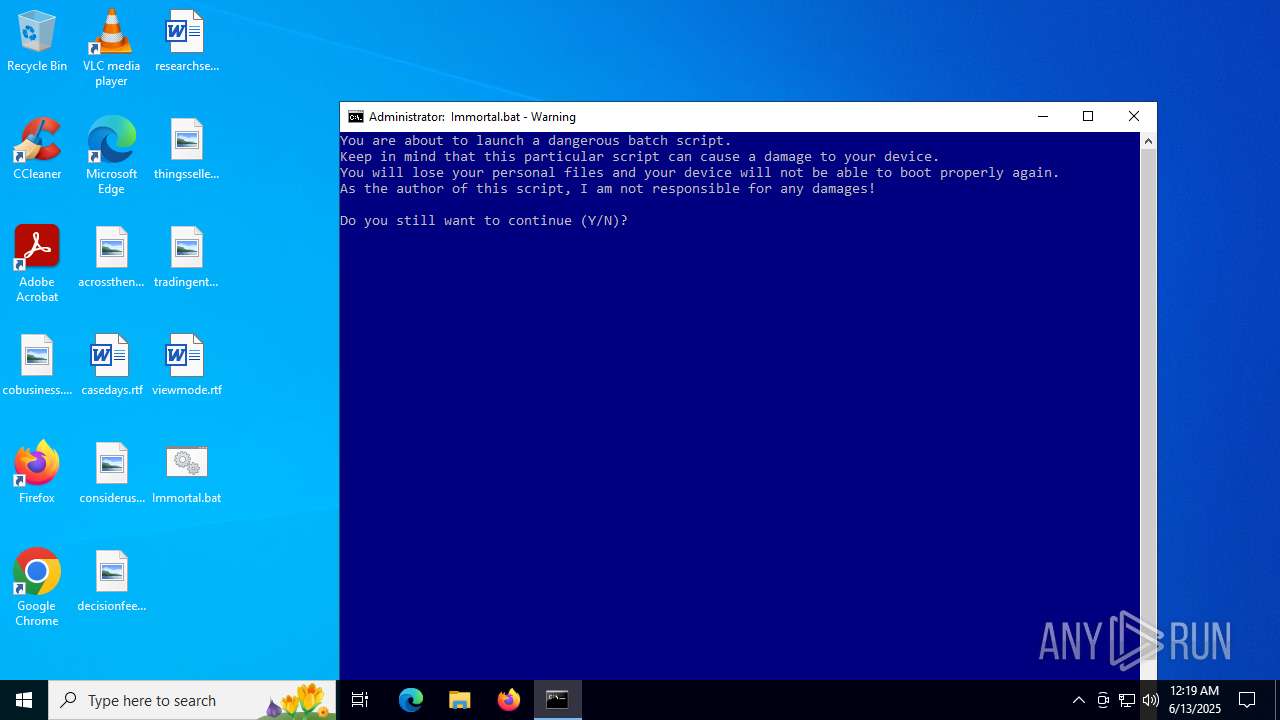
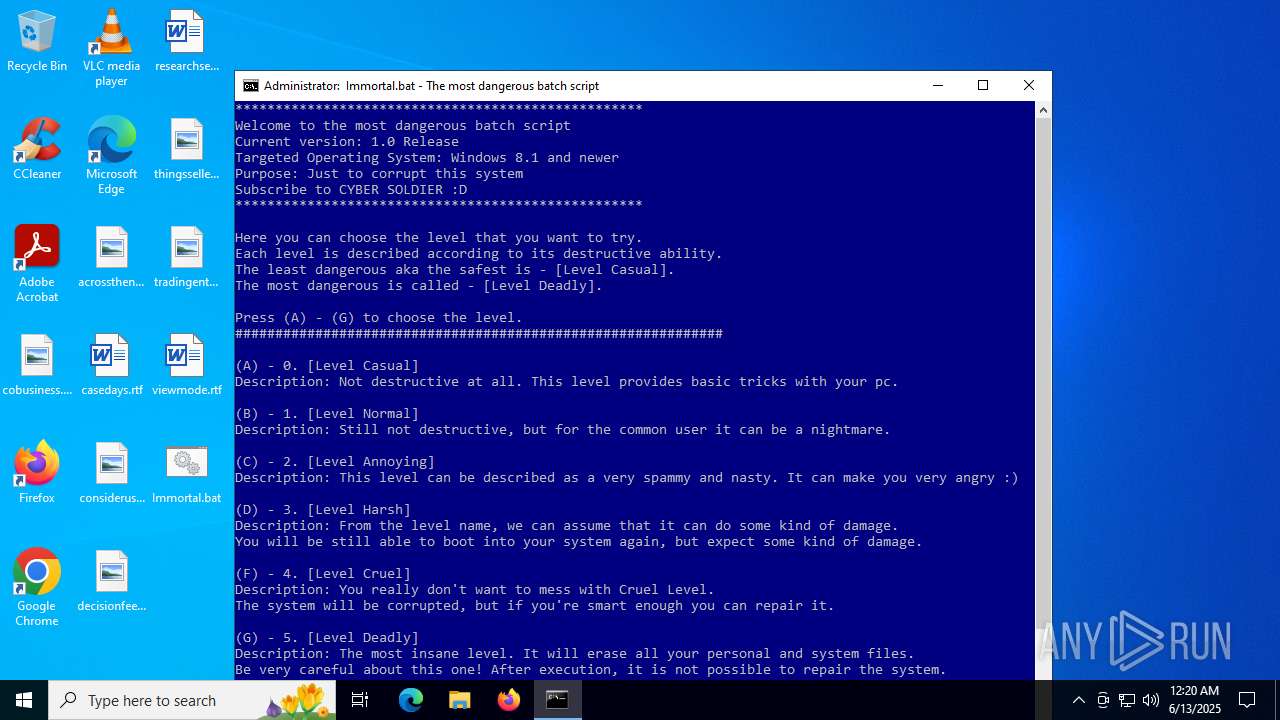
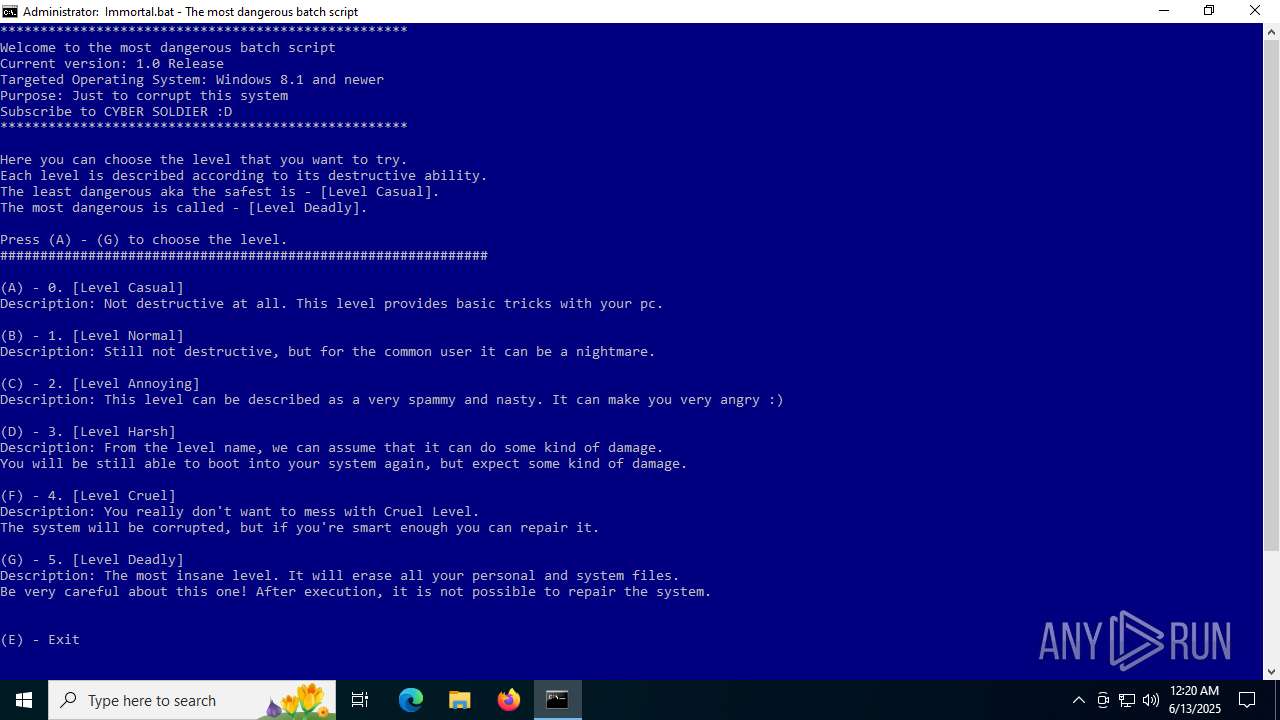
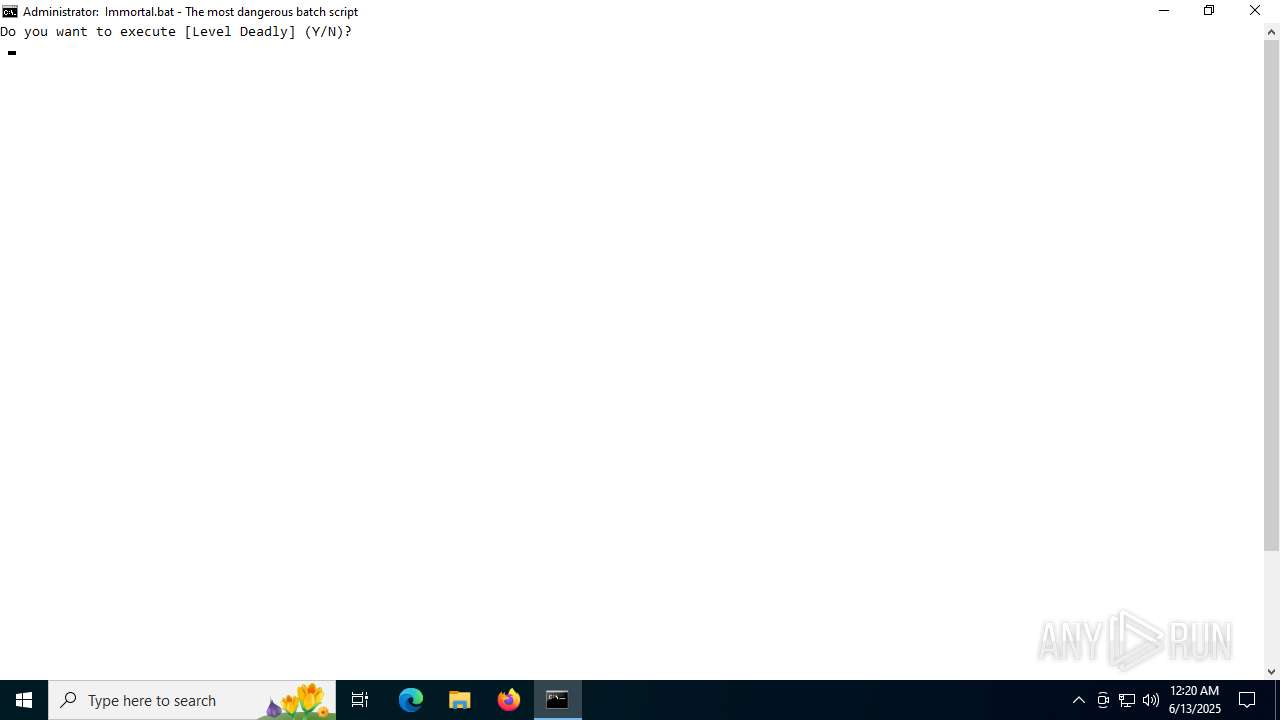
| File name: | Immortal.bat |
| Full analysis: | https://app.any.run/tasks/5ddc4d43-54e9-466e-8989-be3617390a00 |
| Verdict: | Malicious activity |
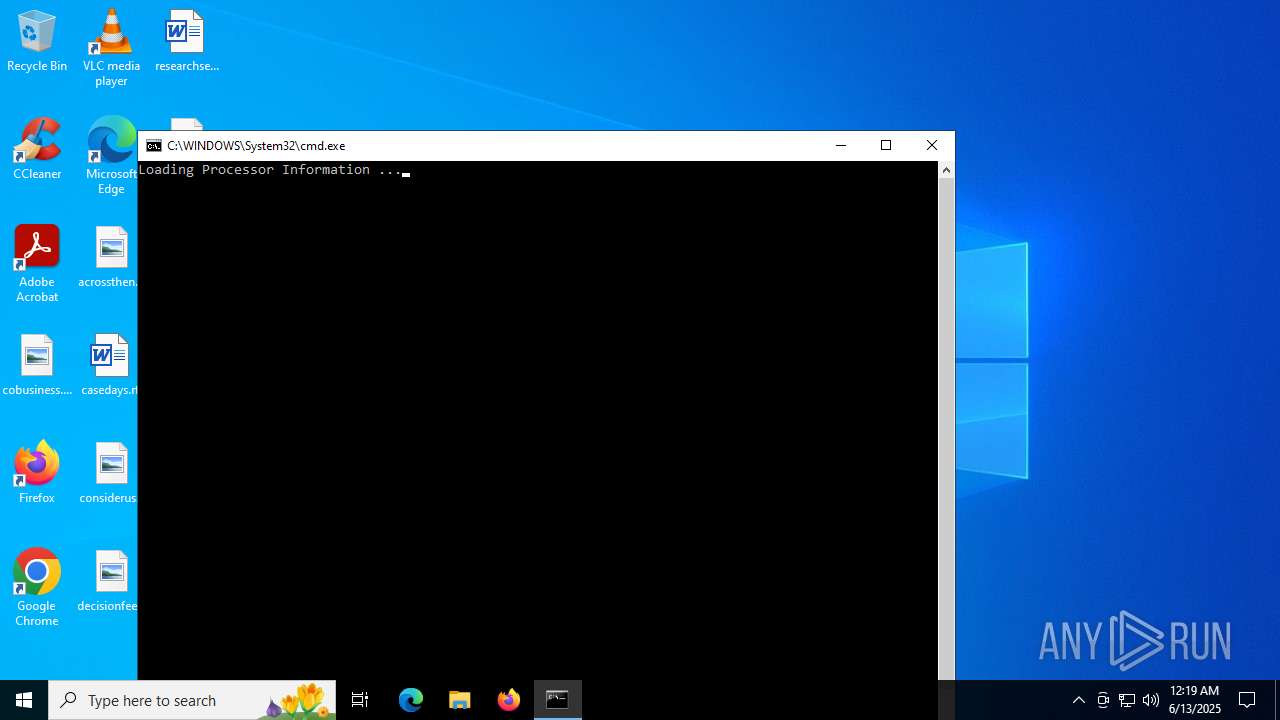
| Analysis date: | June 13, 2025, 00:19:15 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with CRLF line terminators |
| MD5: | 4B9EFCACE5E74954F45FA1C111C36B32 |
| SHA1: | 7DD15E5CE8B6B28EB941E6DF9ED1DB828BD66C3D |
| SHA256: | 173E8AE3A84A0AF1DC39BB0F4EEEE5423A20F61D5924485D89AD1B521CD43D7B |
| SSDEEP: | 768:a4b7q7LFMuchajH79KqIhQsys0/dJxdZPCH3gXN84kSENqaEtoEM1GeOPPsIrI6A:RXgXN8vSENqaEtoEM1GeOPUGXt7P4RRV |
MALICIOUS
GENERIC has been found (auto)
- cmd.exe (PID: 3756)
- cmd.exe (PID: 3556)
Changes the login/logoff helper path in the registry
- reg.exe (PID: 3396)
SUSPICIOUS
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 3756)
- net.exe (PID: 3864)
- cmd.exe (PID: 3556)
- net.exe (PID: 3864)
- cmd.exe (PID: 6160)
- net.exe (PID: 5744)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 3756)
- cmd.exe (PID: 3556)
- cmd.exe (PID: 6160)
Starts process via Powershell
- powershell.exe (PID: 2976)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 2976)
- cmd.exe (PID: 3556)
- cmd.exe (PID: 6160)
Executing commands from a ".bat" file
- powershell.exe (PID: 2976)
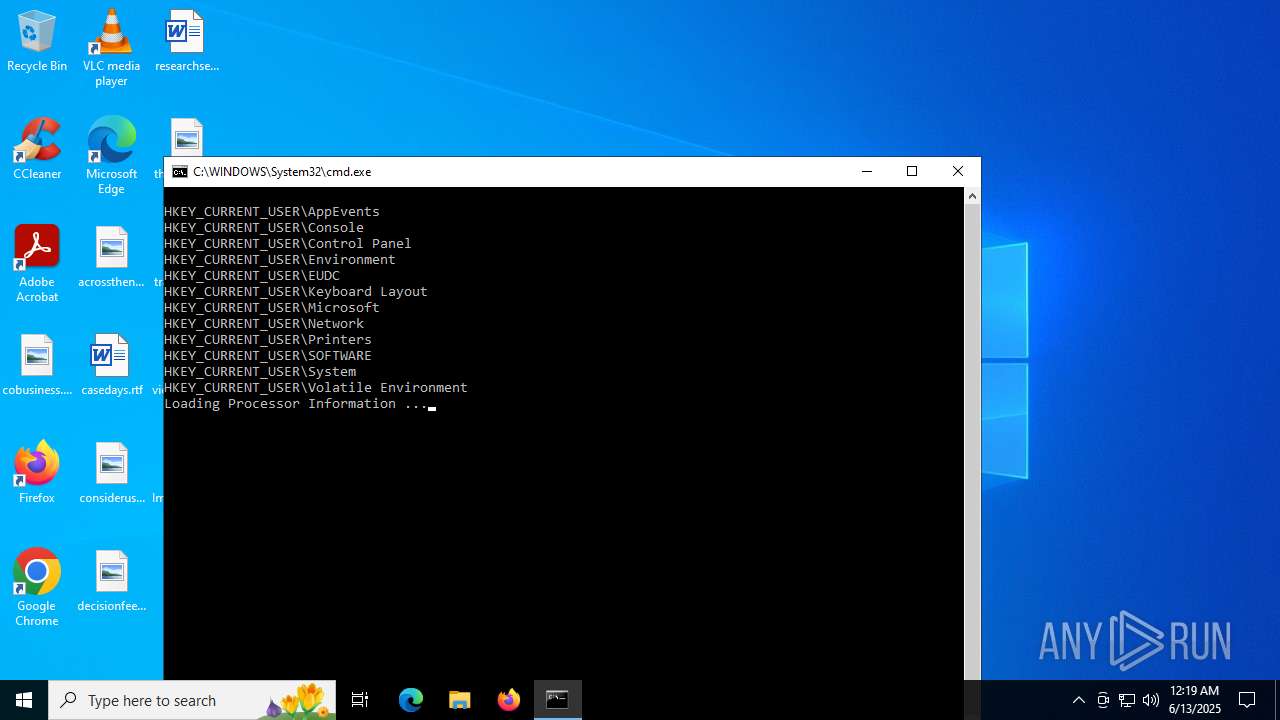
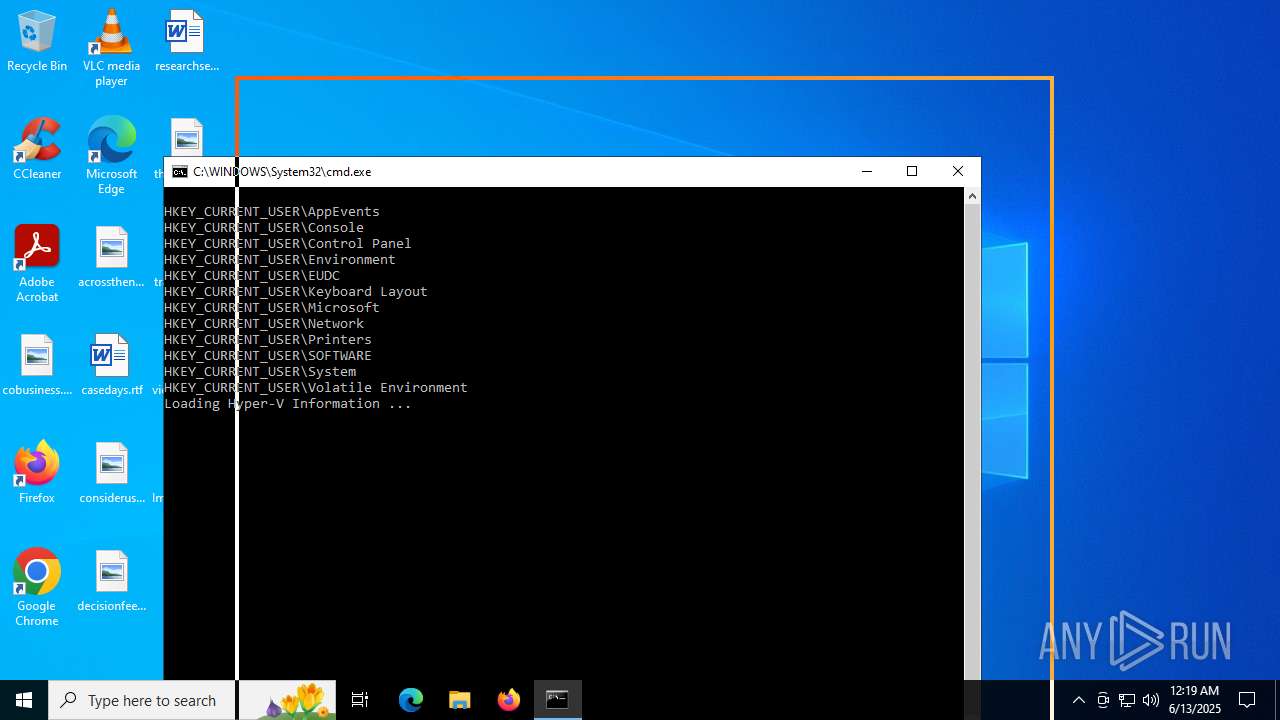
Uses SYSTEMINFO.EXE to read the environment
- cmd.exe (PID: 3556)
- cmd.exe (PID: 6160)
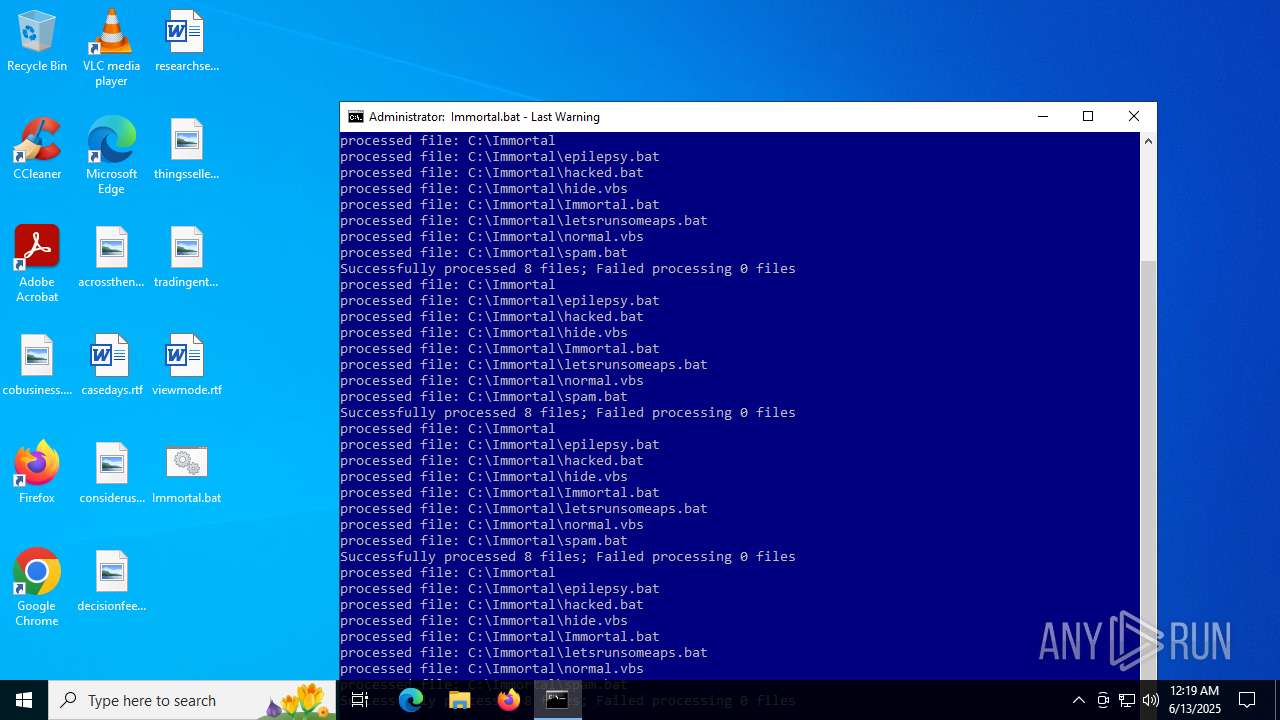
Application launched itself
- cmd.exe (PID: 3556)
- cmd.exe (PID: 6160)
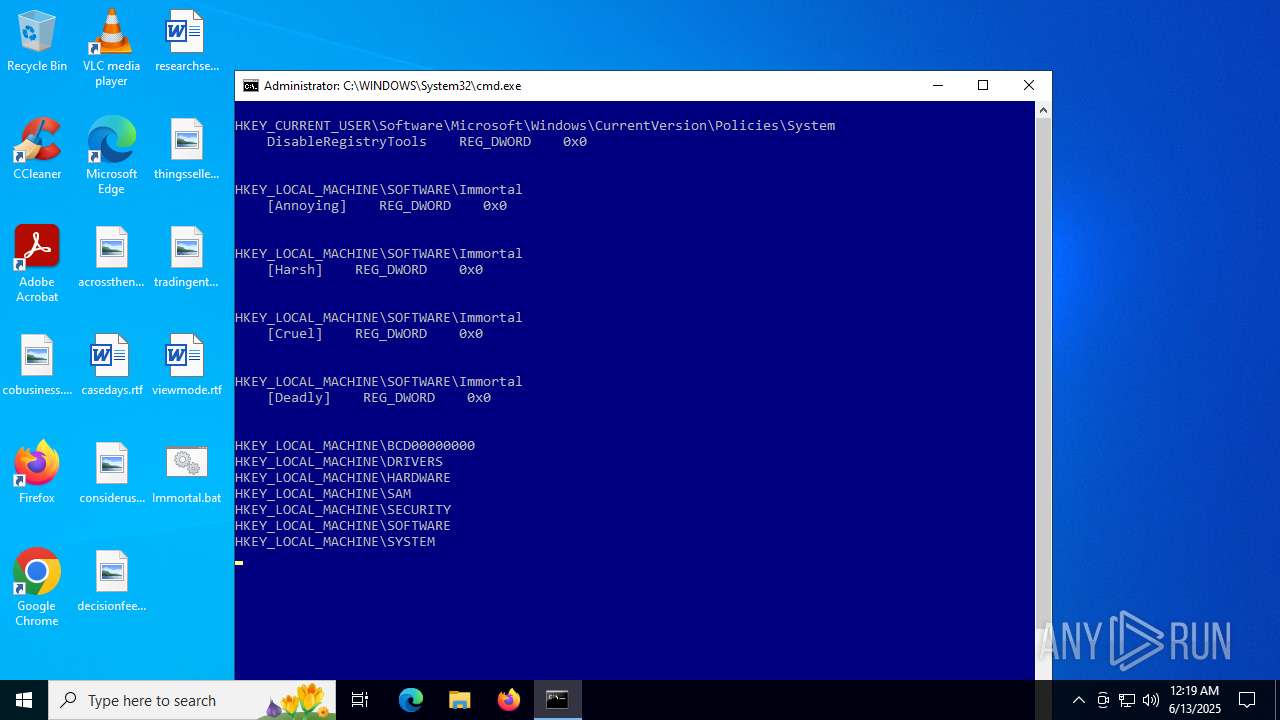
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3556)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3556)
Uses ICACLS.EXE to modify access control lists
- cmd.exe (PID: 3556)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 6160)
INFO
Starts MODE.COM to configure console settings
- mode.com (PID: 3028)
- mode.com (PID: 5168)
- mode.com (PID: 420)
Checks supported languages
- mode.com (PID: 3028)
- mode.com (PID: 5168)
- mode.com (PID: 420)
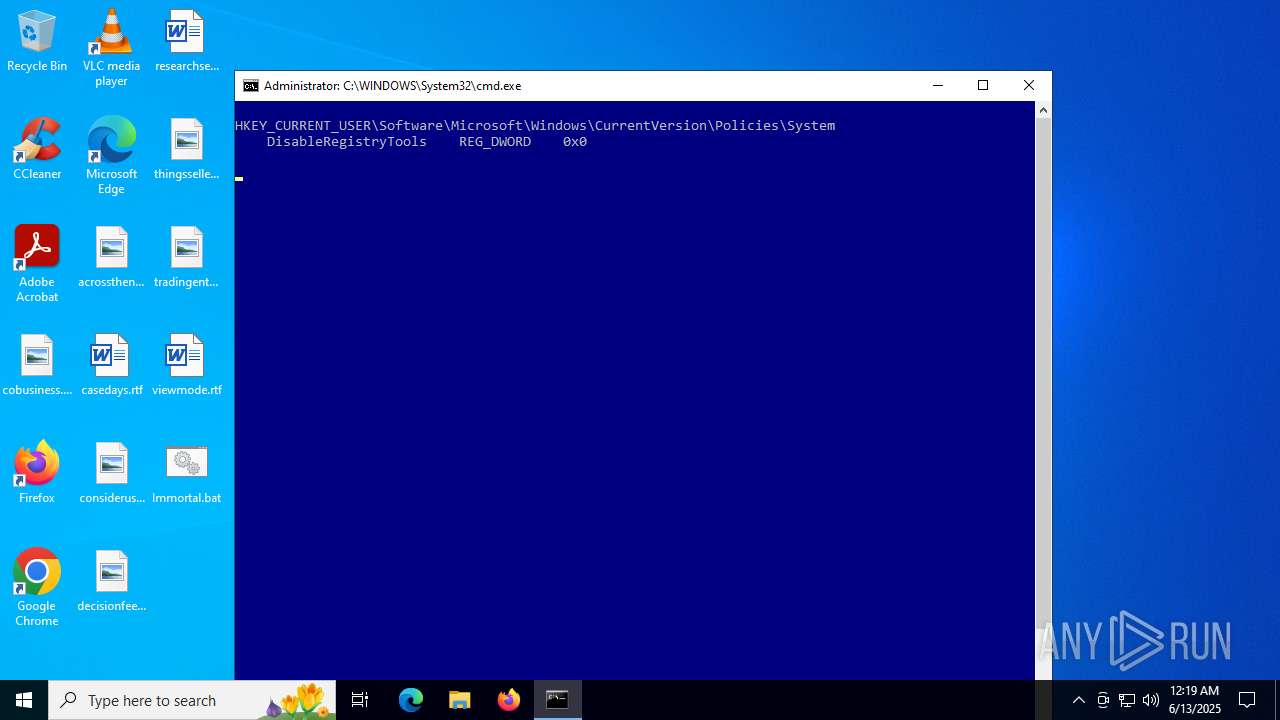
Changes the registry key values via Powershell
- cmd.exe (PID: 3556)
- cmd.exe (PID: 6160)
Manual execution by a user
- cmd.exe (PID: 6160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
252
Monitored processes
114
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 316 | reg query "HKEY_LOCAL_MACHINE\SOFTWARE\Immortal" /v [Annoying] | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 316 | reg query "HKEY_CURRENT_USER" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 420 | mode con: cols=100 lines=50 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 472 | powershell -command "& {Set-ItemProperty -Path 'HKCU:\Software\Microsoft\Windows\CurrentVersion\Policies\System' -Name 'DisableRegistryTools' -Value '0'}" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 768 | C:\WINDOWS\system32\net1 SESSION | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | reg query "HKEY_LOCAL_MACHINE" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | C:\WINDOWS\system32\cmd.exe /c reg query "HKEY_LOCAL_MACHINE\SOFTWARE\Immortal" /v [Cruel] | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1232 | icacls "C:\Immortal" /reset /t | C:\Windows\System32\icacls.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\WINDOWS\system32\net1 SESSION | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1324 | C:\WINDOWS\system32\cmd.exe /c echo 0x0 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
31 317
Read events
31 302
Write events
15
Delete events
0
Modification events
| (PID) Process: | (2976) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (2976) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
| (PID) Process: | (5780) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdHigh |
Value: 31185912 | |||
| (PID) Process: | (5780) TiWorker.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Component Based Servicing |
| Operation: | write | Name: | SessionIdLow |
Value: | |||
| (PID) Process: | (5528) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (5708) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableRegistryTools |
Value: 0 | |||
| (PID) Process: | (2620) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Immortal |
| Operation: | write | Name: | [Harsh] |
Value: 0 | |||
| (PID) Process: | (6336) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Immortal |
| Operation: | write | Name: | [Cruel] |
Value: 0 | |||
| (PID) Process: | (3960) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Immortal |
| Operation: | write | Name: | [Deadly] |
Value: 0 | |||
| (PID) Process: | (5020) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Immortal |
| Operation: | write | Name: | [Annoying] |
Value: 0 | |||
Executable files
0
Suspicious files
4
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2976 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:8B909FC8B98753CF3875B5B9B9466C63 | SHA256:6CDE12174C68F2F7348DF20DFEC9059BF8F529B619FE863CE36D3B84BA755115 | |||
| 2976 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\U0VJMHPYEQLGLTC34L97.temp | binary | |
MD5:8B909FC8B98753CF3875B5B9B9466C63 | SHA256:6CDE12174C68F2F7348DF20DFEC9059BF8F529B619FE863CE36D3B84BA755115 | |||
| 6336 | find.exe | C:\Windows\System32\osVersion.txt | text | |
MD5:DA737647DE9BEB7D73E47D0DB1573D22 | SHA256:8C1CB99116DE55EF9C3A69377922EA759482FC4CE59F3A72CDE2A5F0268F2E7B | |||
| 2976 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF175738.TMP | binary | |
MD5:00A03B286E6E0EBFF8D9C492365D5EC2 | SHA256:4DBFC417D053BA6867308671F1C61F4DCAFC61F058D4044DB532DA6D3BDE3615 | |||
| 2976 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_a4iiirby.4vv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2976 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_atttq5kg.eli.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5708 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ubcnfvg2.3my.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2976 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:7E102EF8D5D4824A523208F77E2F975F | SHA256:9CA440B4C4299D00500AA303EA79C0B063A91C5BD6E7E82DD8D702B93AB86196 | |||
| 5780 | TiWorker.exe | C:\Windows\Logs\CBS\CBS.log | text | |
MD5:1F8B705CA306016D79218E8D01EA2B47 | SHA256:807ADBECCD953493F05EB47DCDCAA6D0E7137EF6C2026B9CE253FF5358DD7C70 | |||
| 3556 | cmd.exe | C:\Immortal\Immortal.bat | text | |
MD5:4B9EFCACE5E74954F45FA1C111C36B32 | SHA256:173E8AE3A84A0AF1DC39BB0F4EEEE5423A20F61D5924485D89AD1B521CD43D7B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
21
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.48.23.166:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1740 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1740 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5848 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2028 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 23.48.23.166:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1740 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1740 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1740 | SIHClient.exe | 52.165.164.15:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |