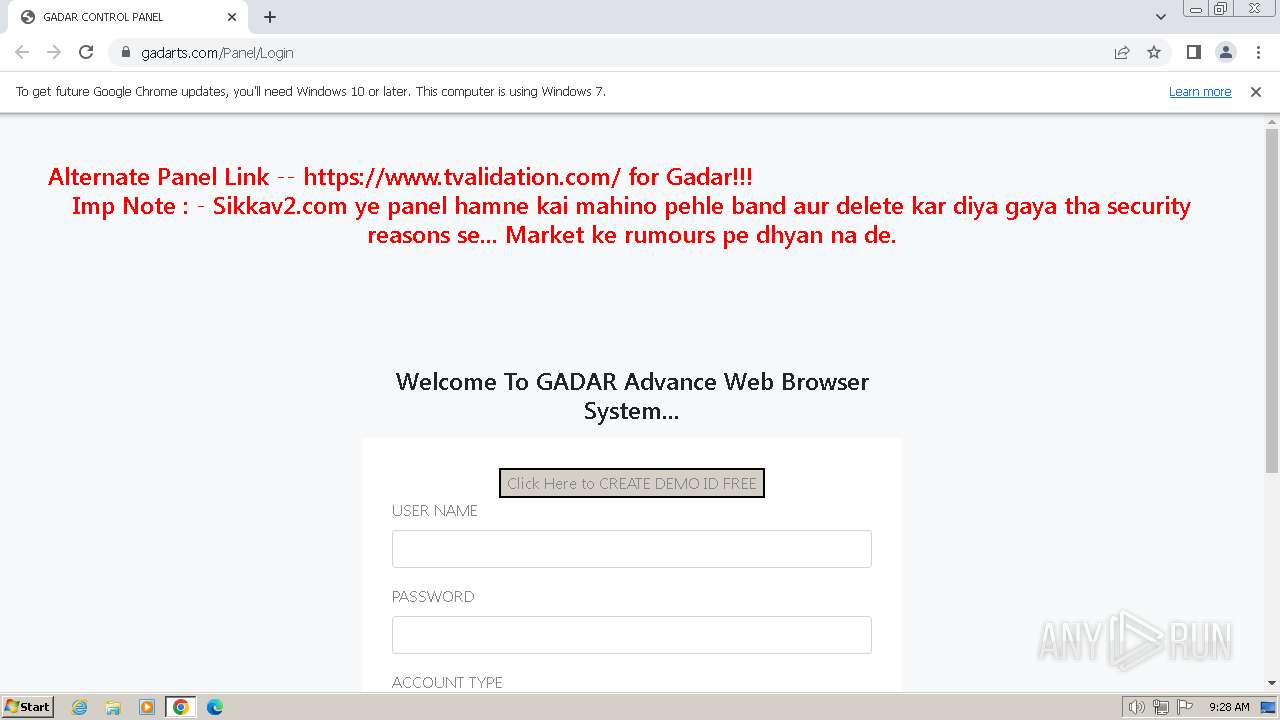
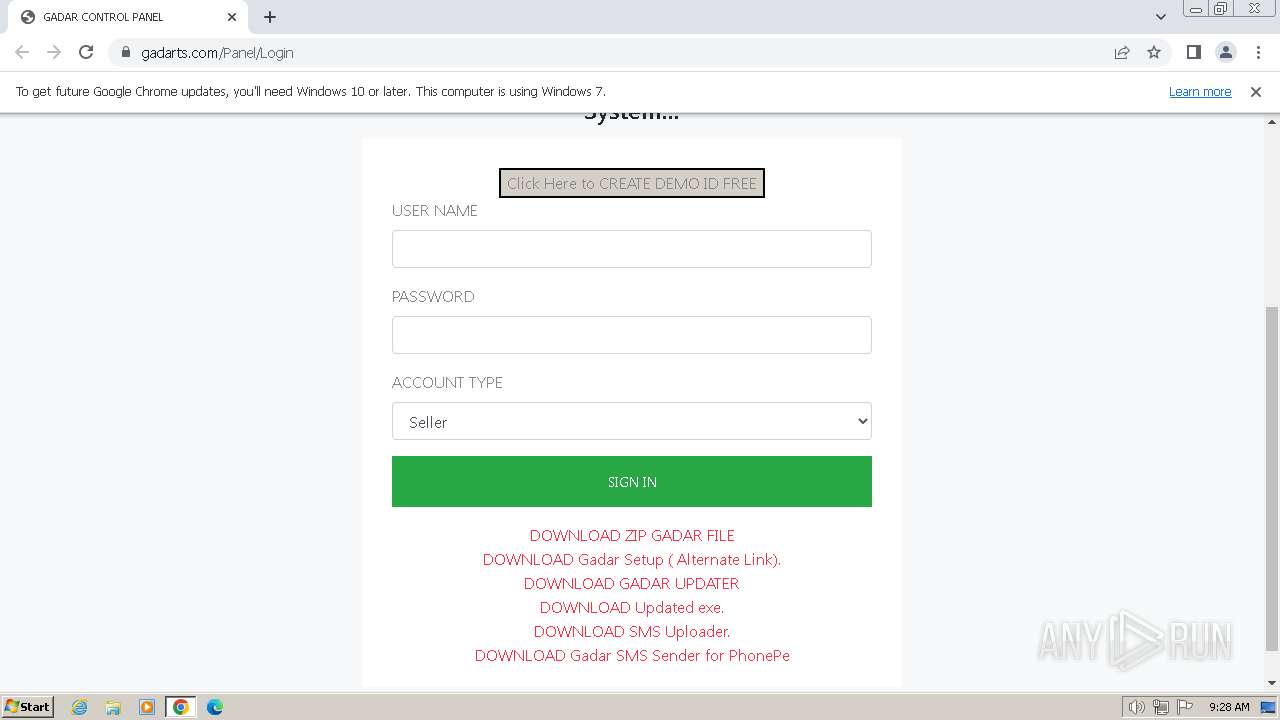
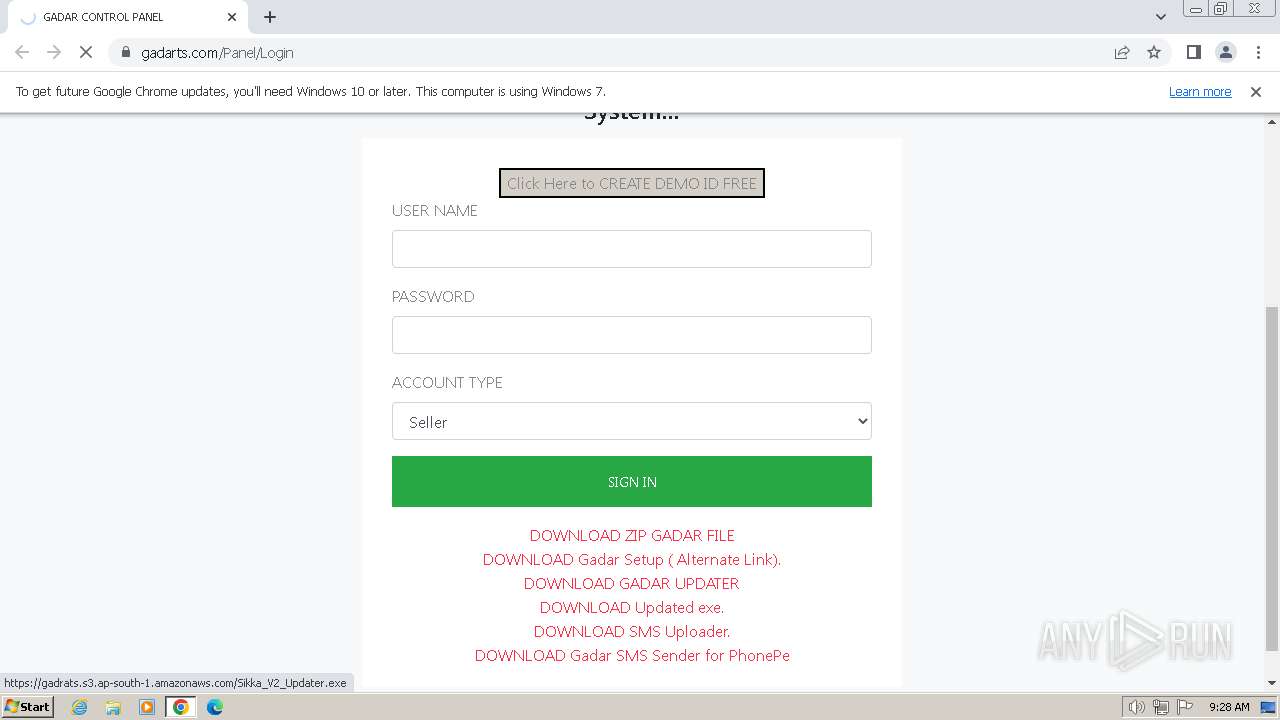
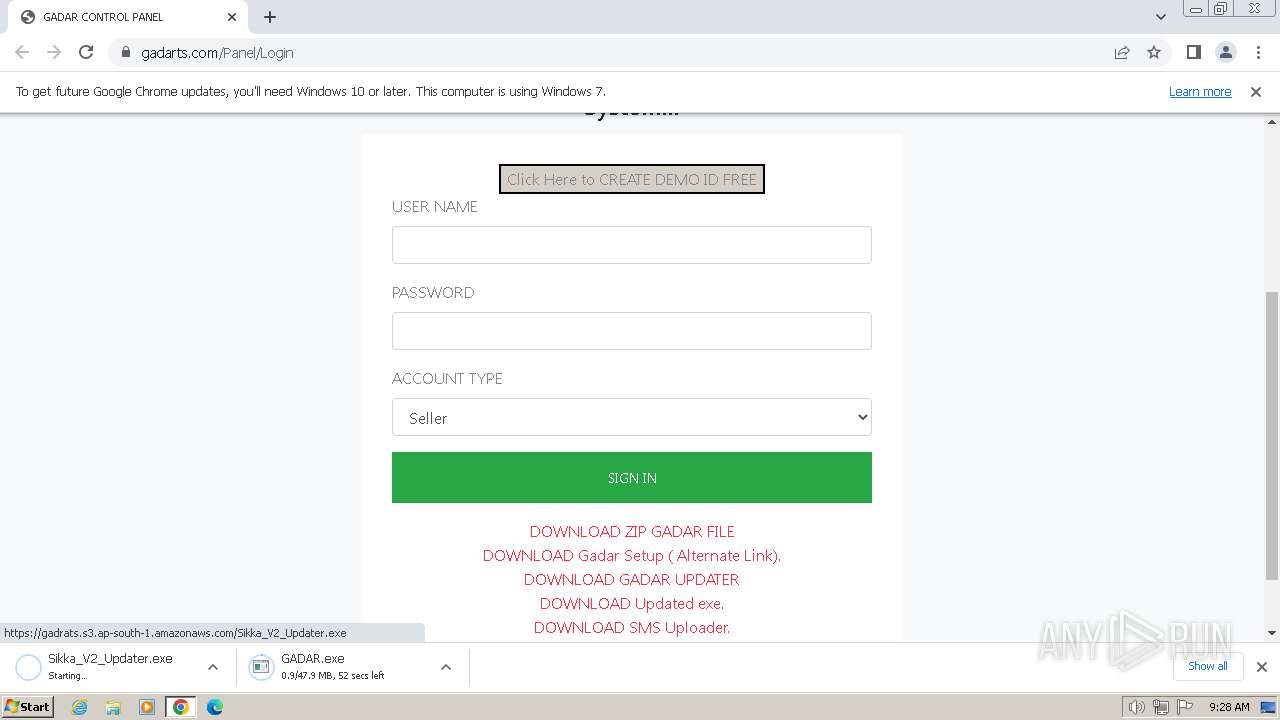
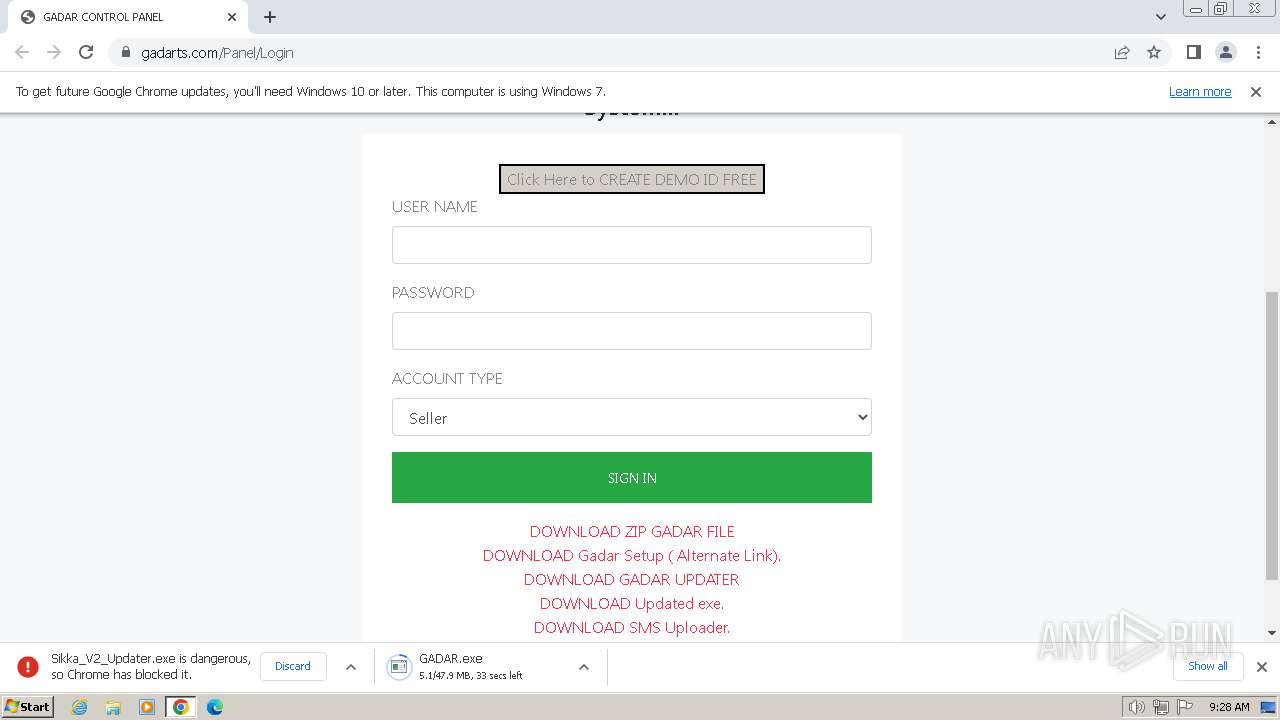
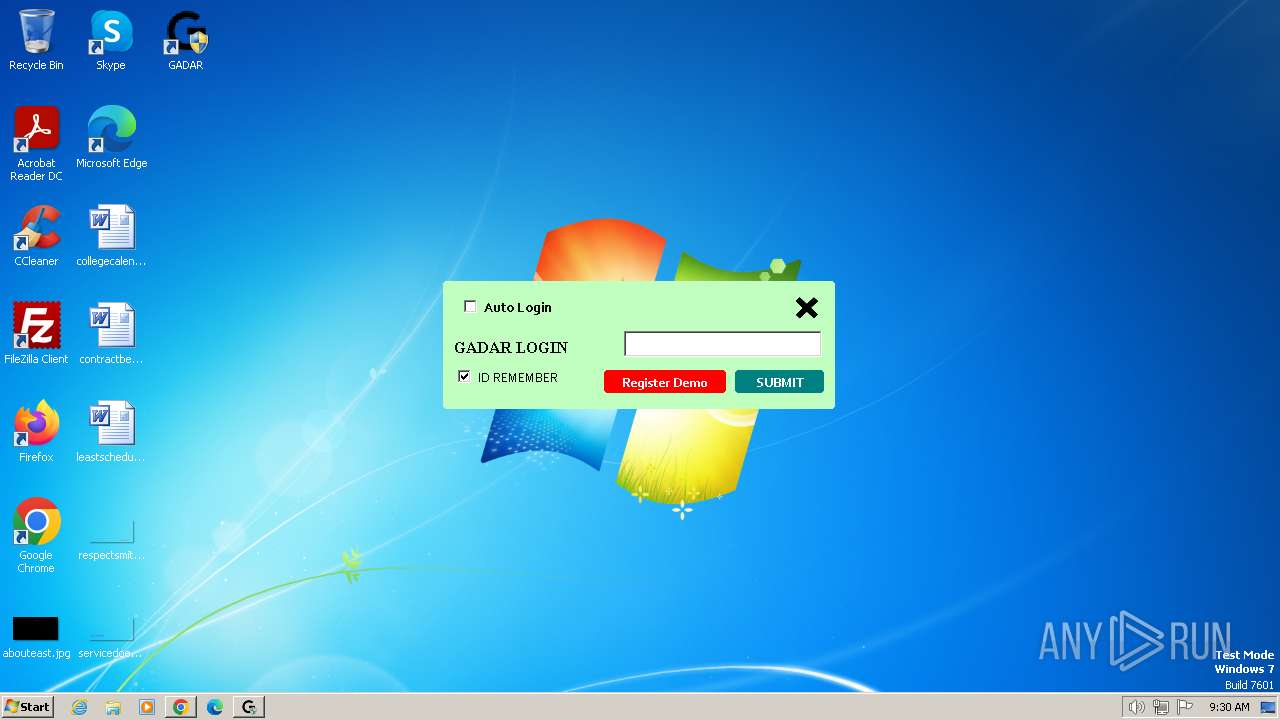
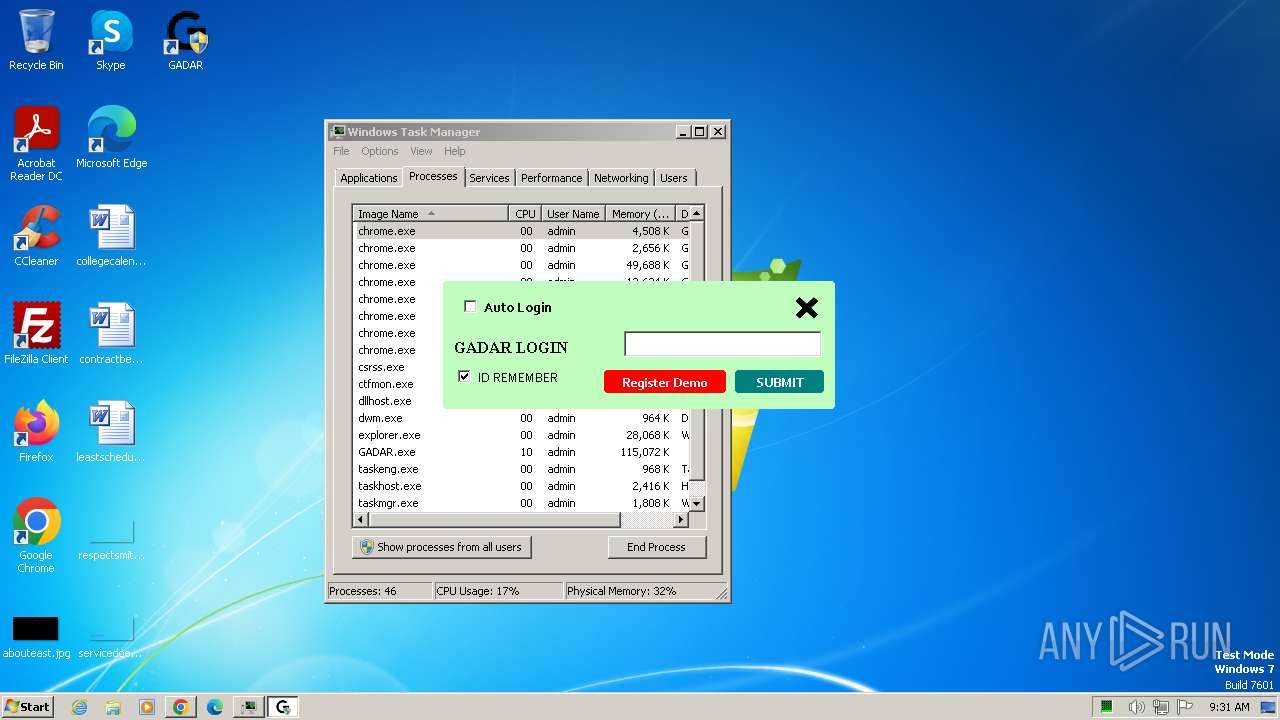
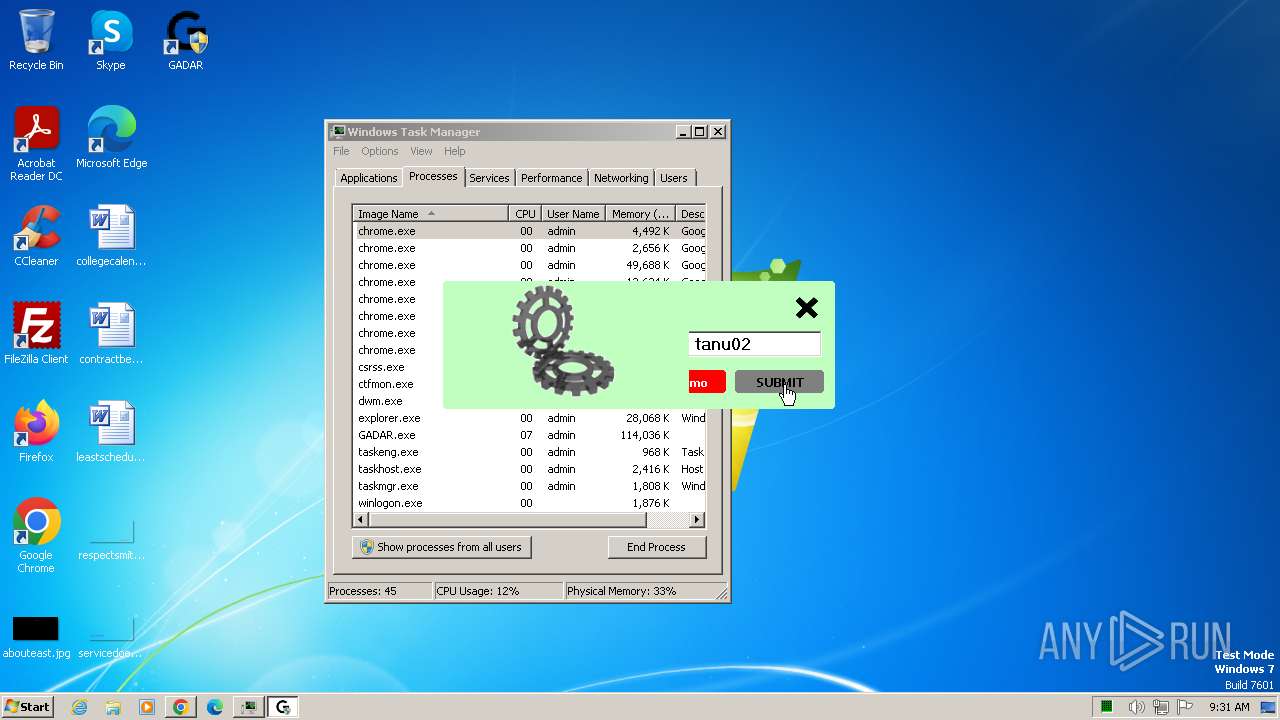
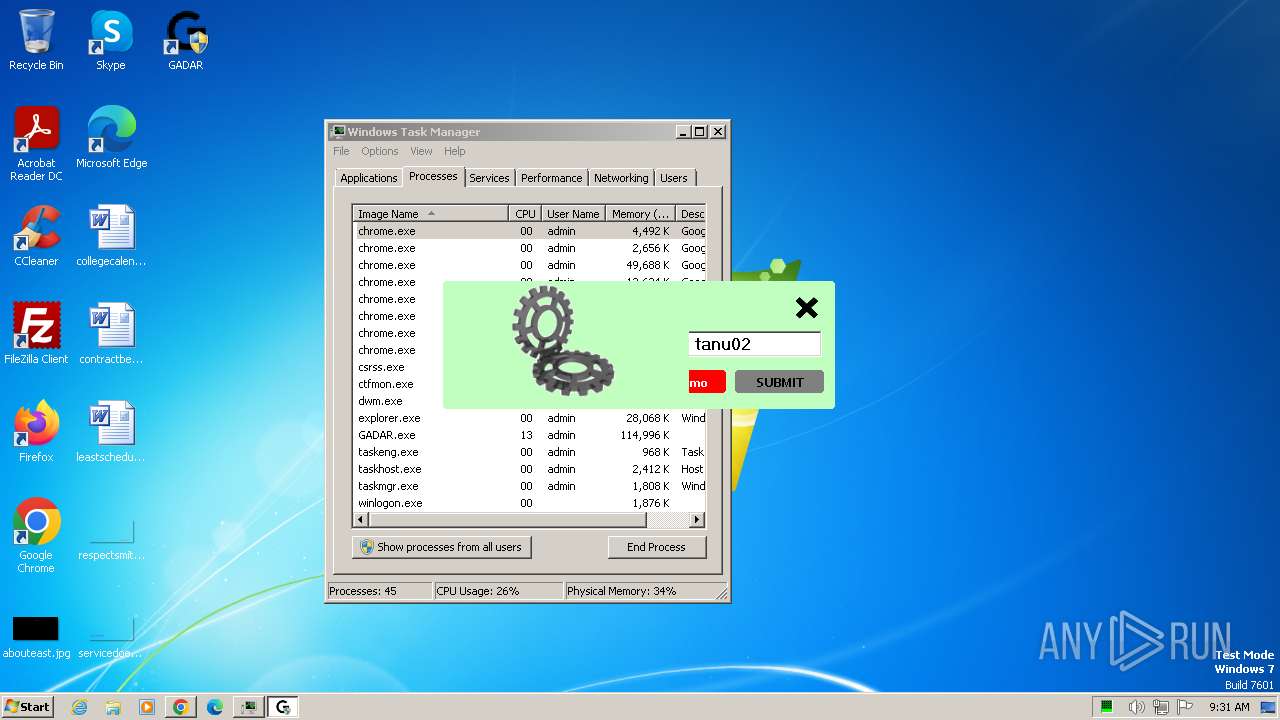
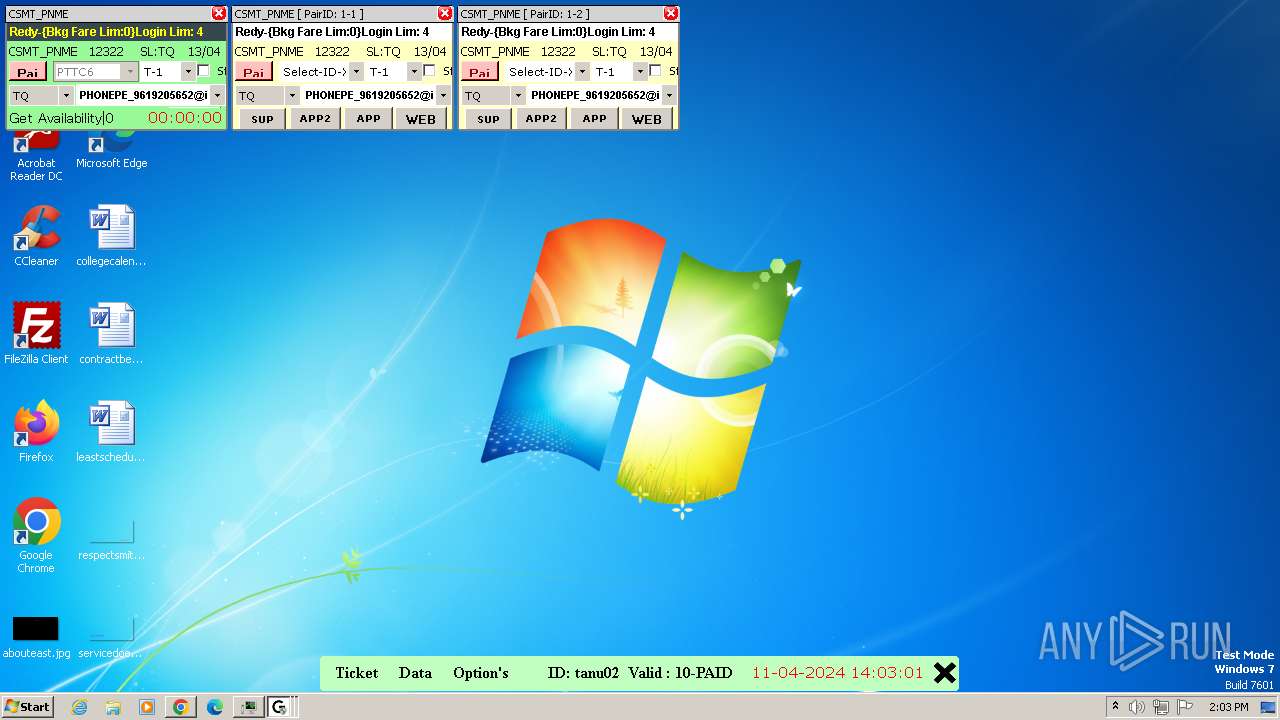
| URL: | https://gadarts.com/Panel/Login |
| Full analysis: | https://app.any.run/tasks/29763ad0-233f-497e-b5f5-18343803a24d |
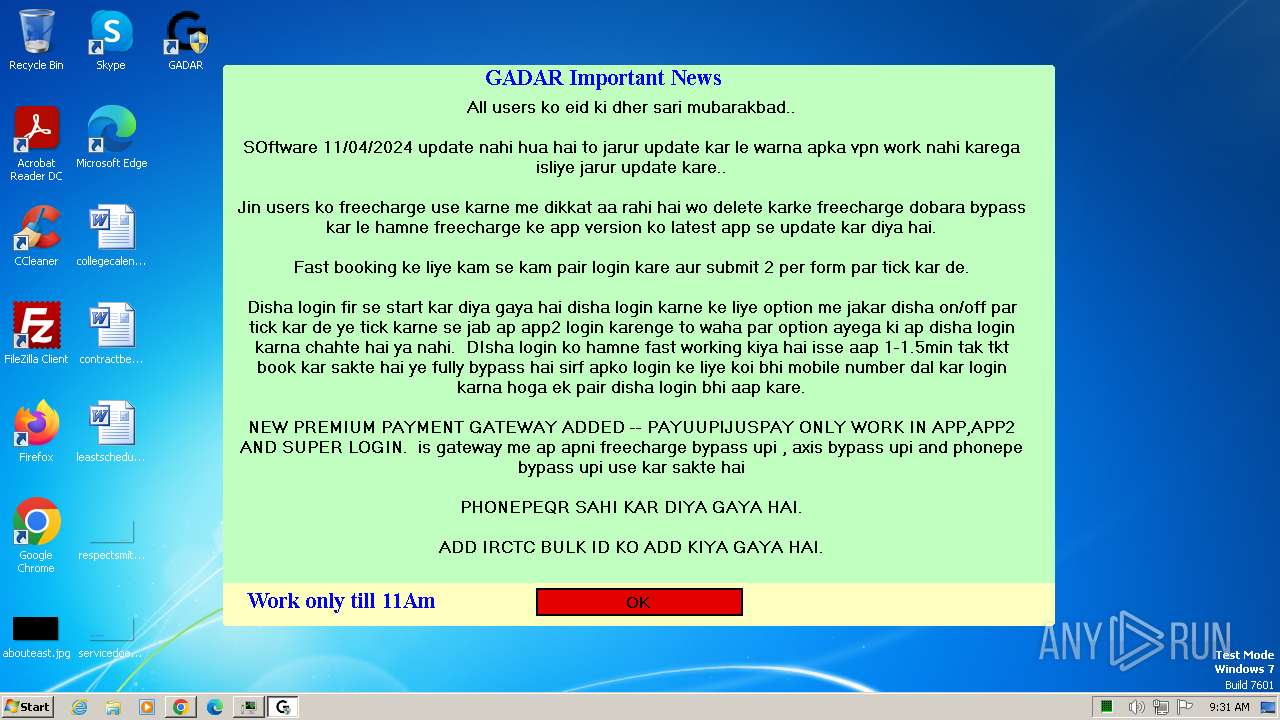
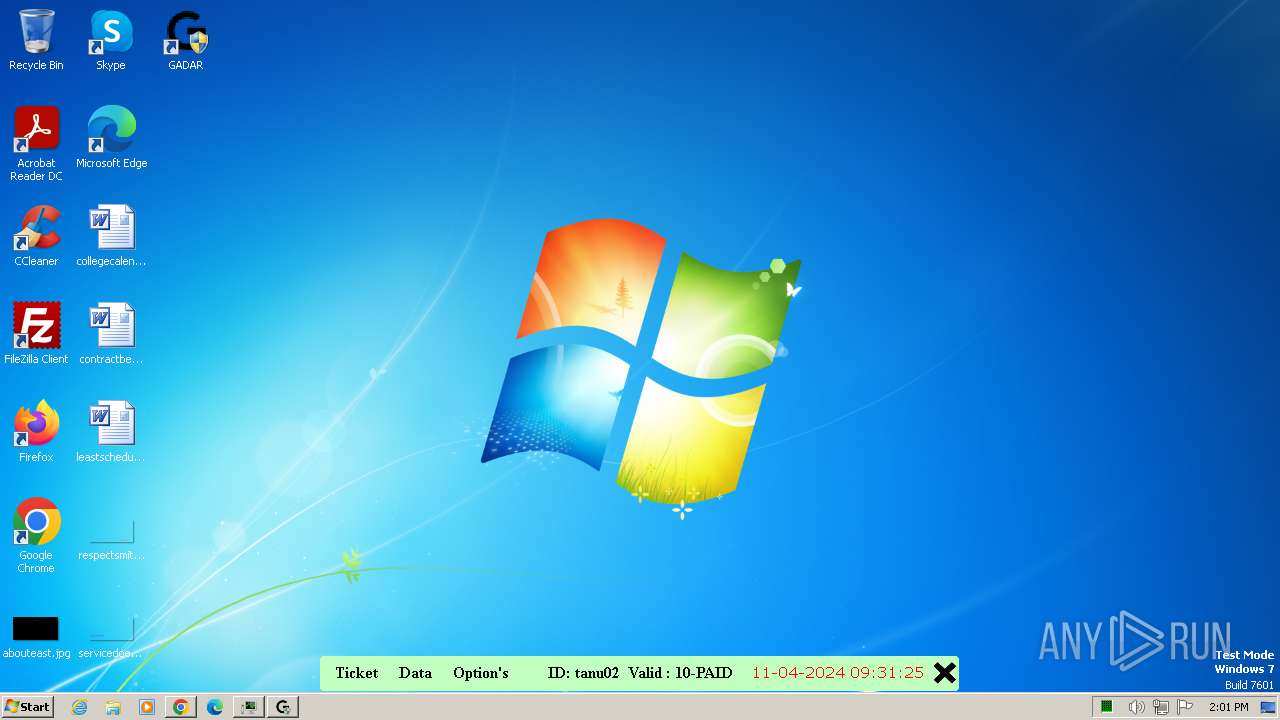
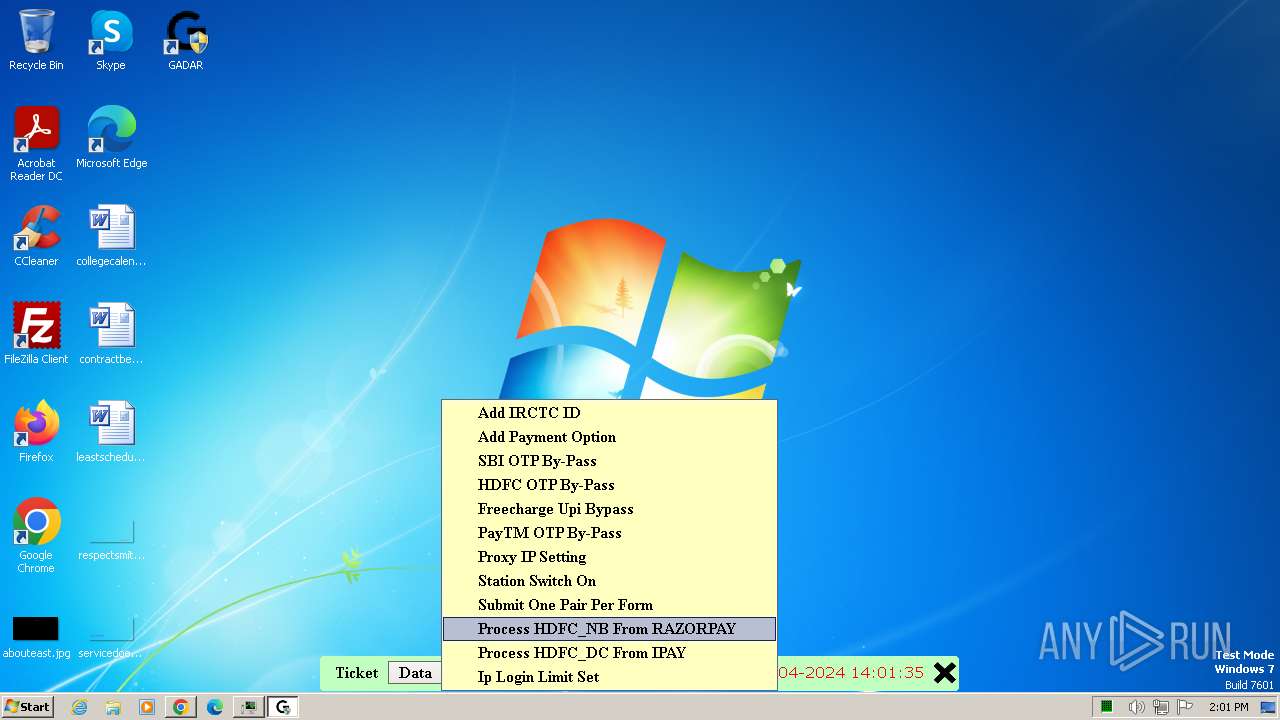
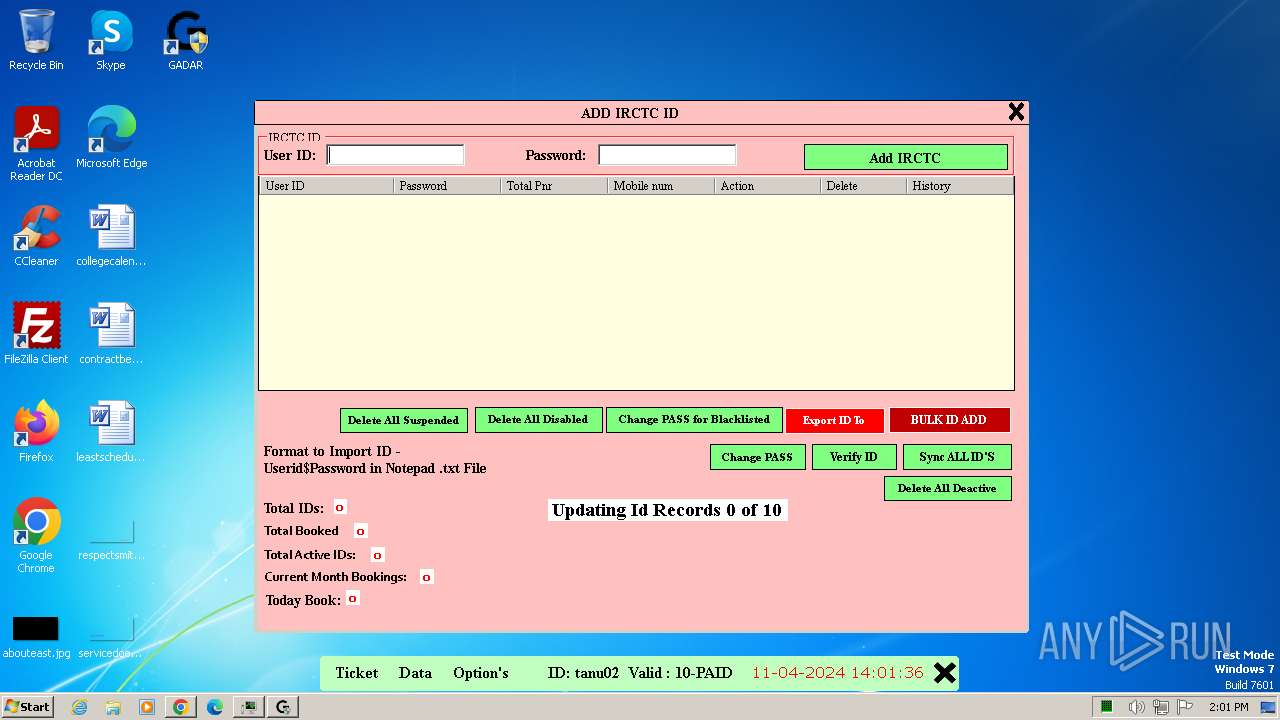
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2024, 08:28:06 |
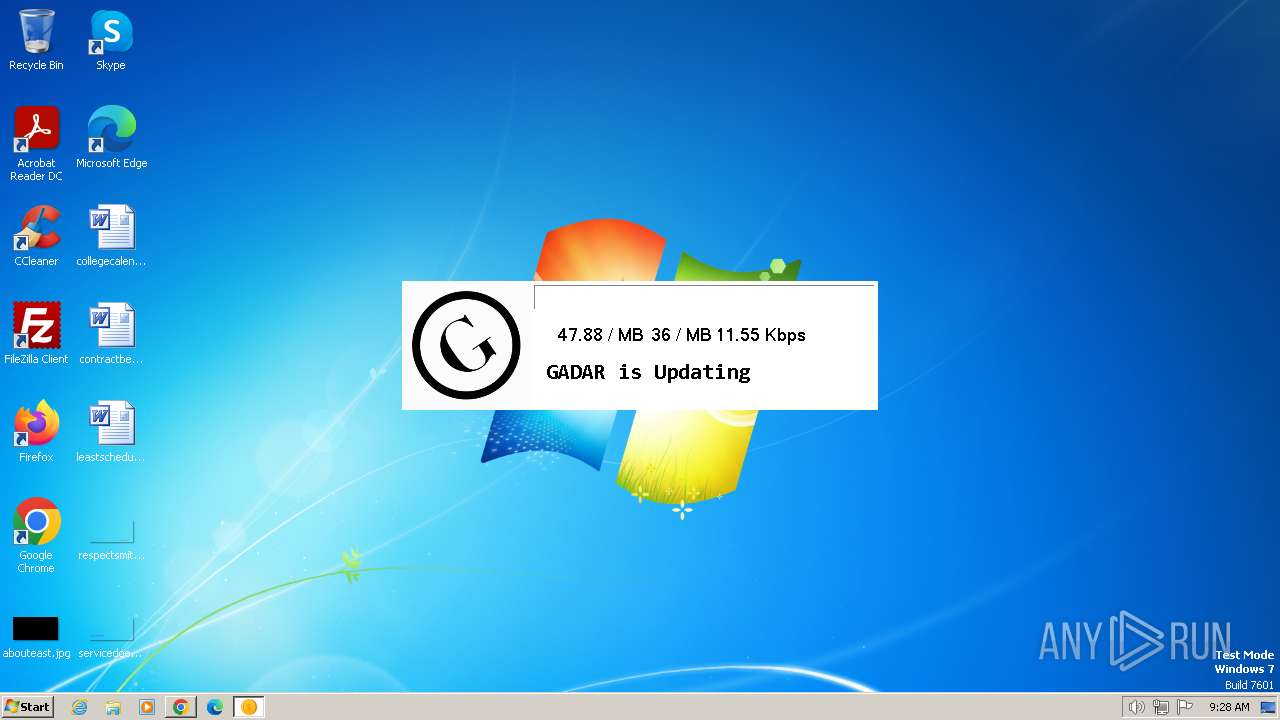
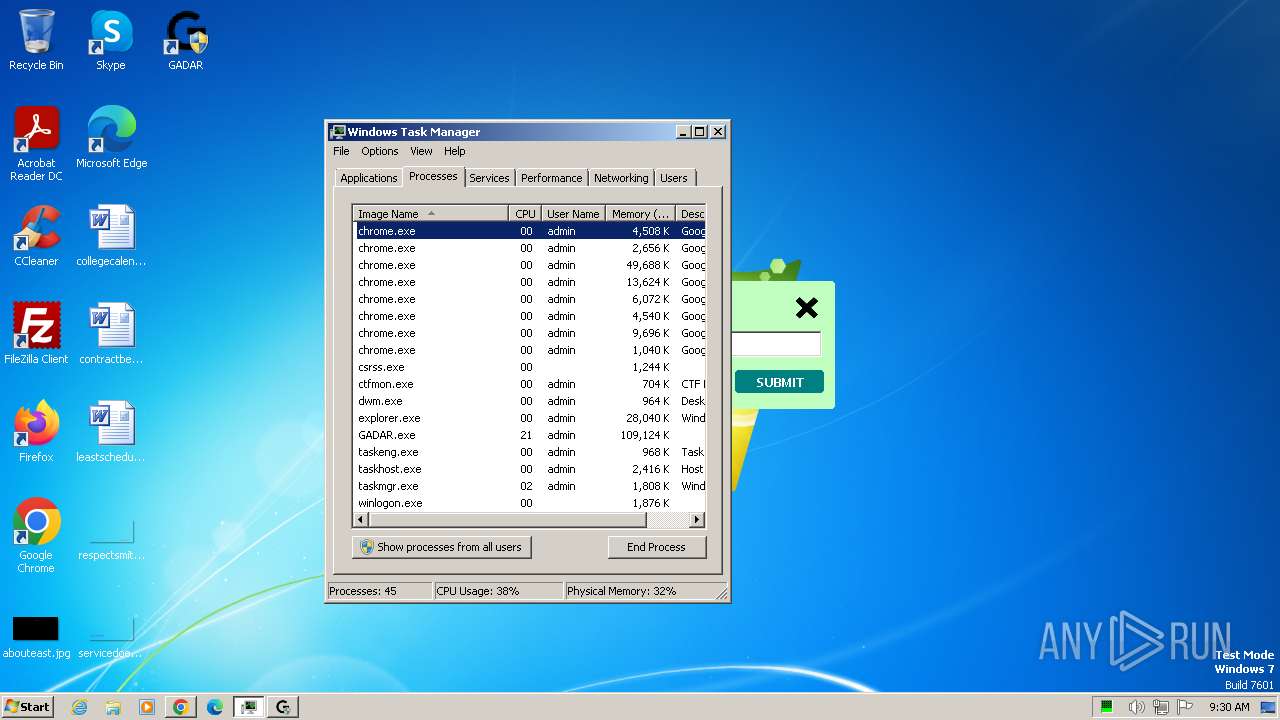
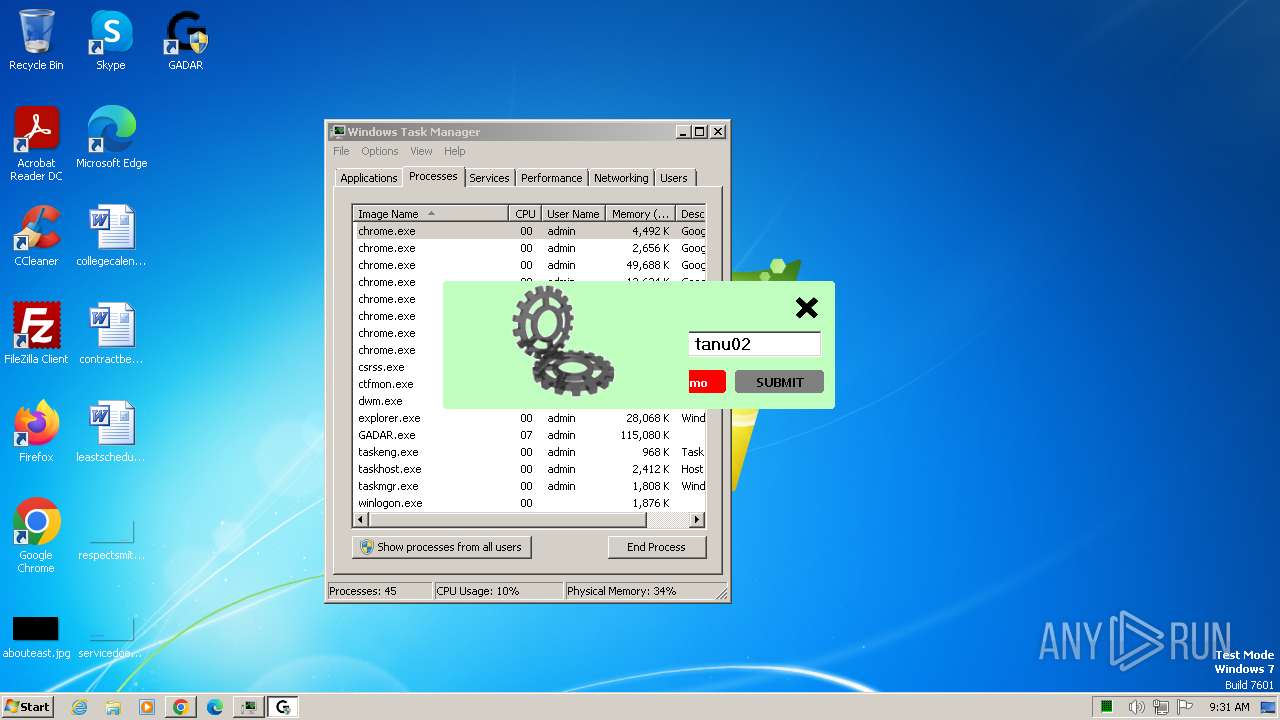
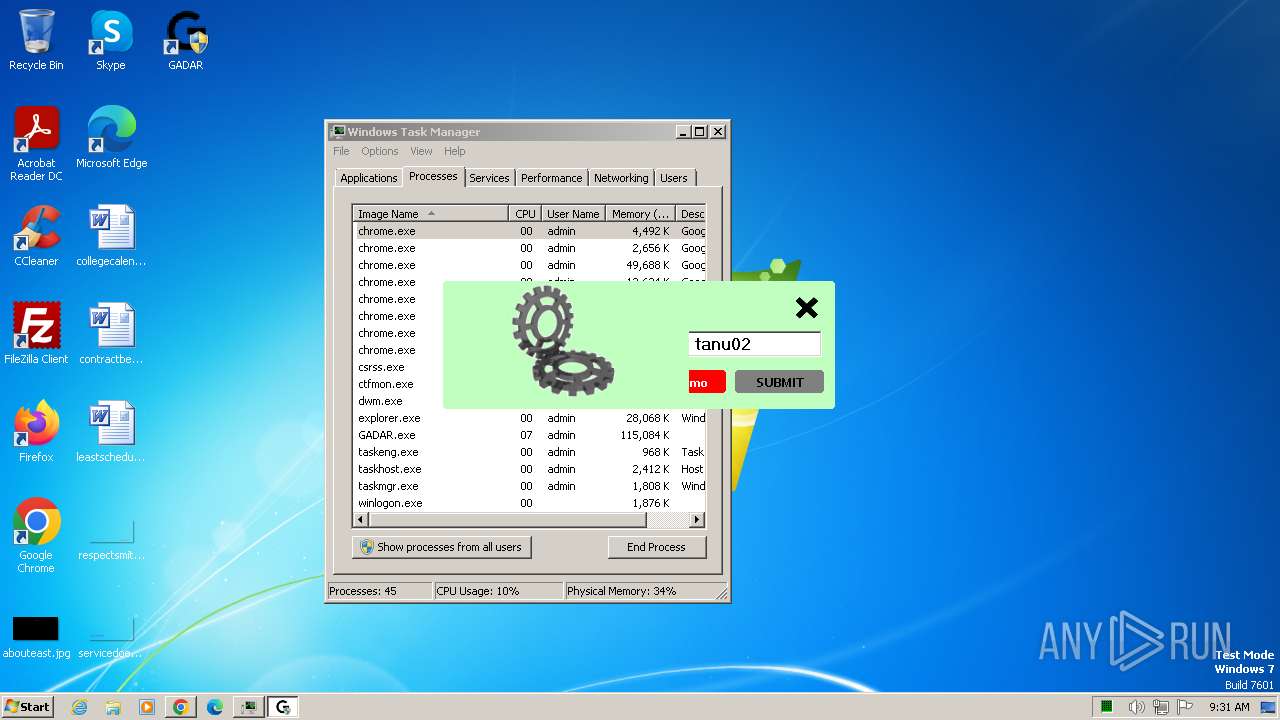
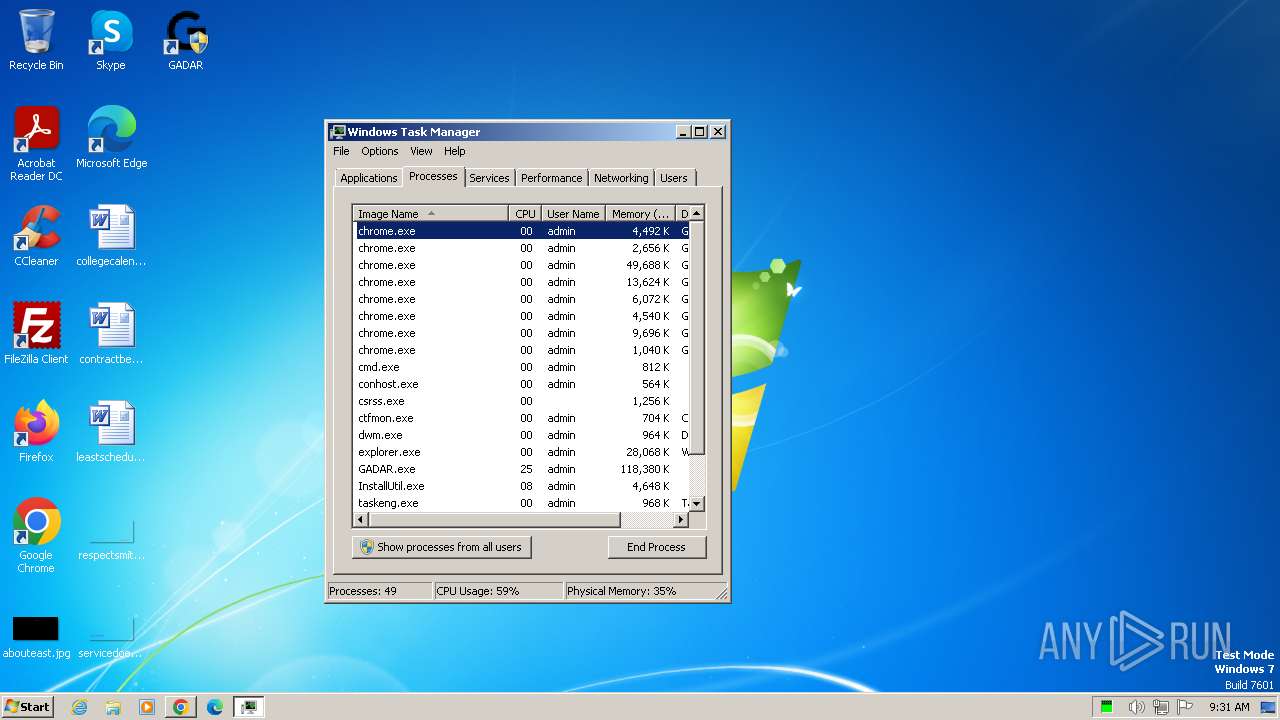
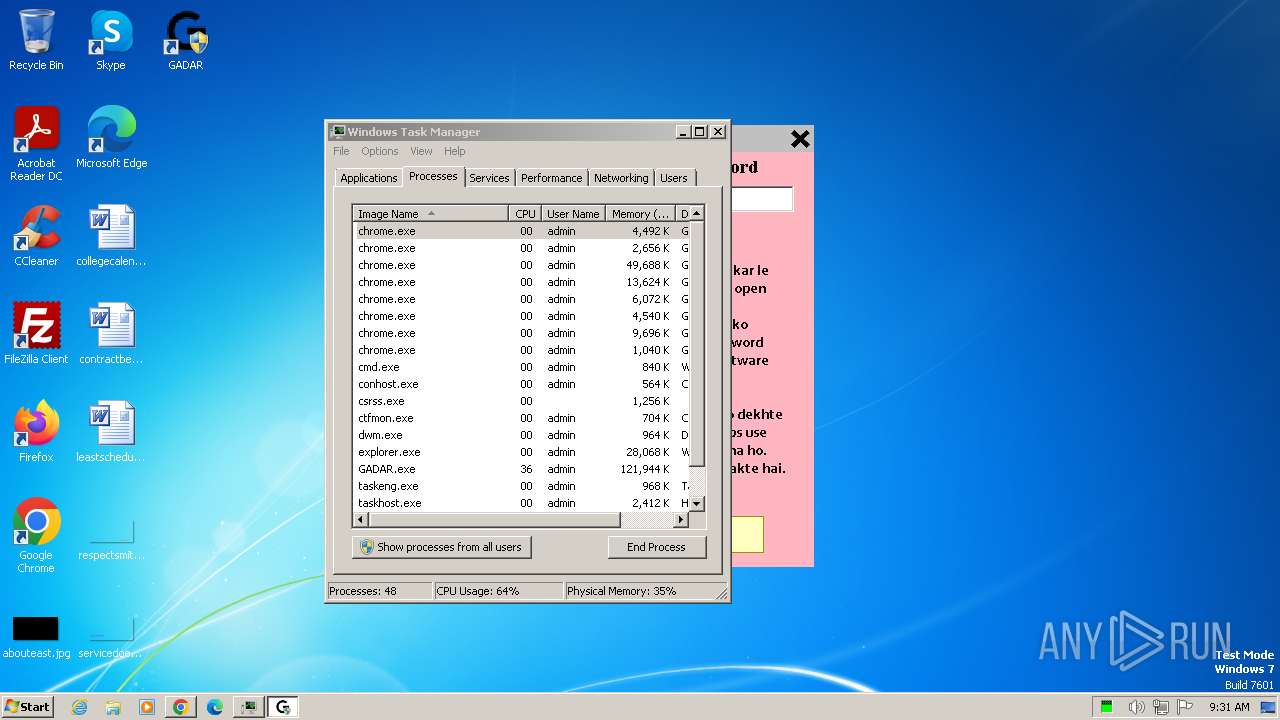
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7BCAFCF7684208FD851D613B7A9A4694 |
| SHA1: | 4FB9A2DB91CFFAFAE10E2F7CE972AE00C9B5485A |
| SHA256: | 171DCBDFB3B7E6BC48C72AA3CCA3A873DE07D8999584619C37E5841875037D87 |
| SSDEEP: | 3:N8lyX+Rp:2gX+r |
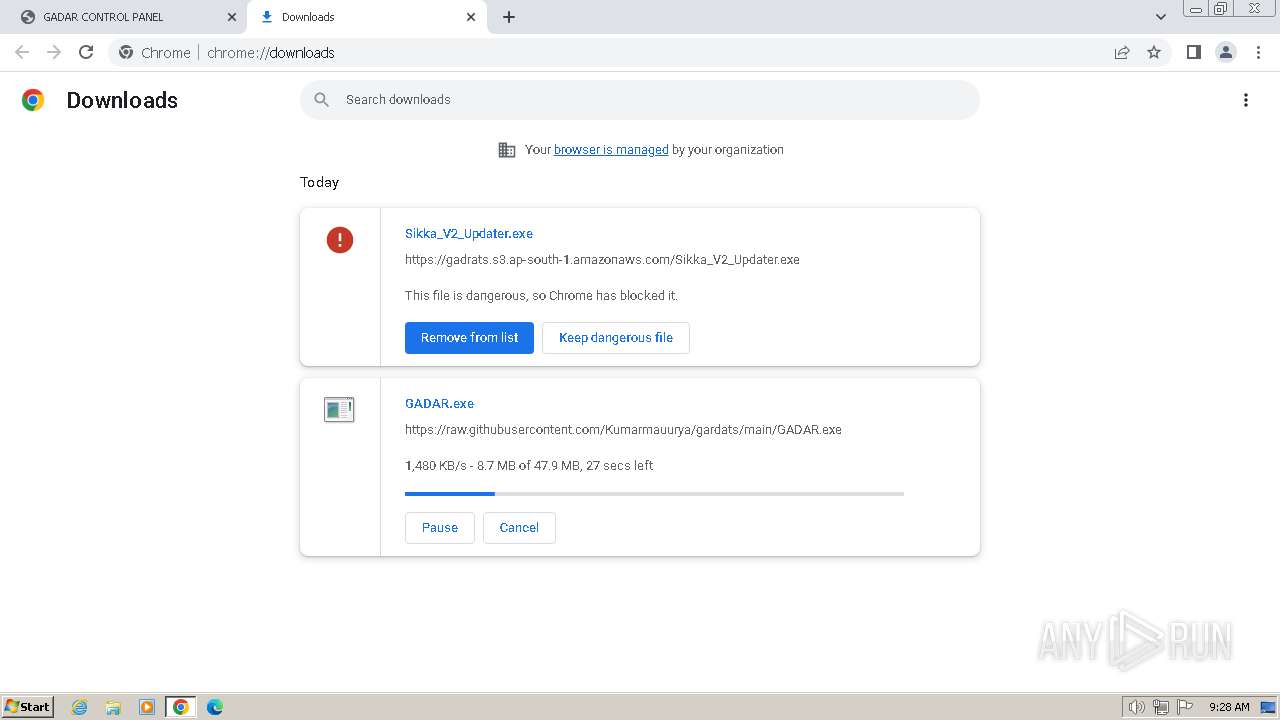
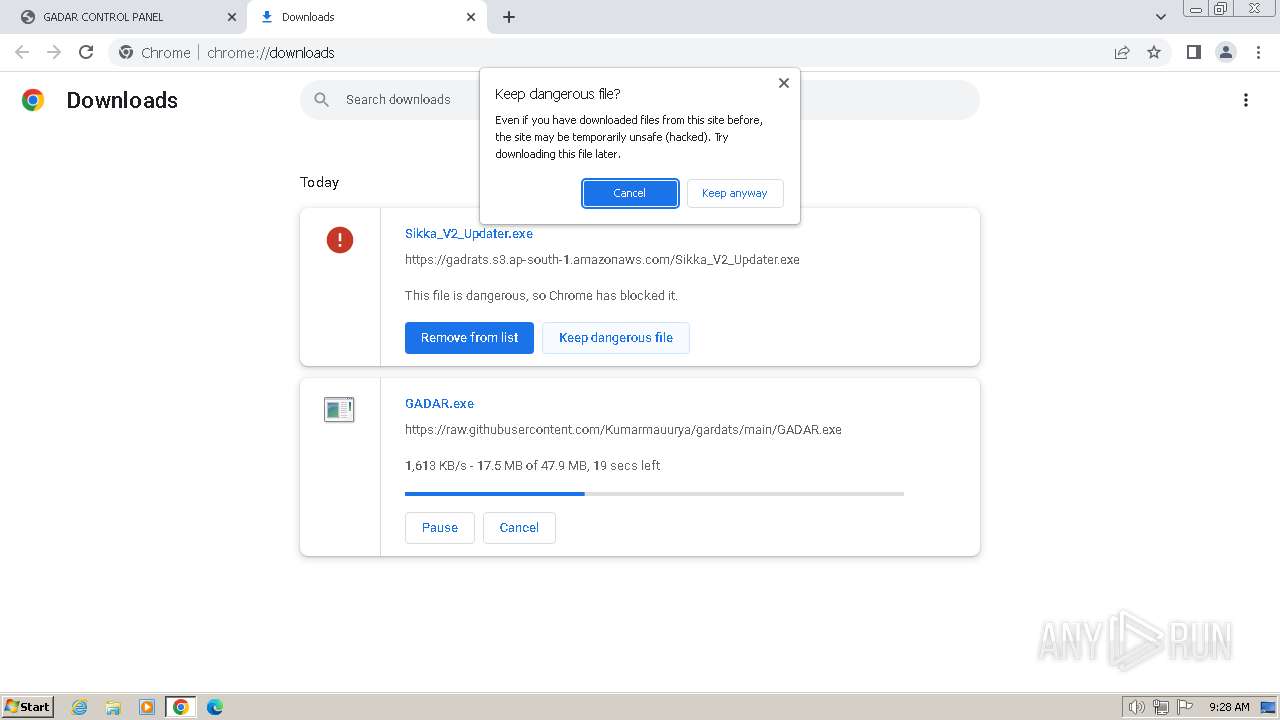
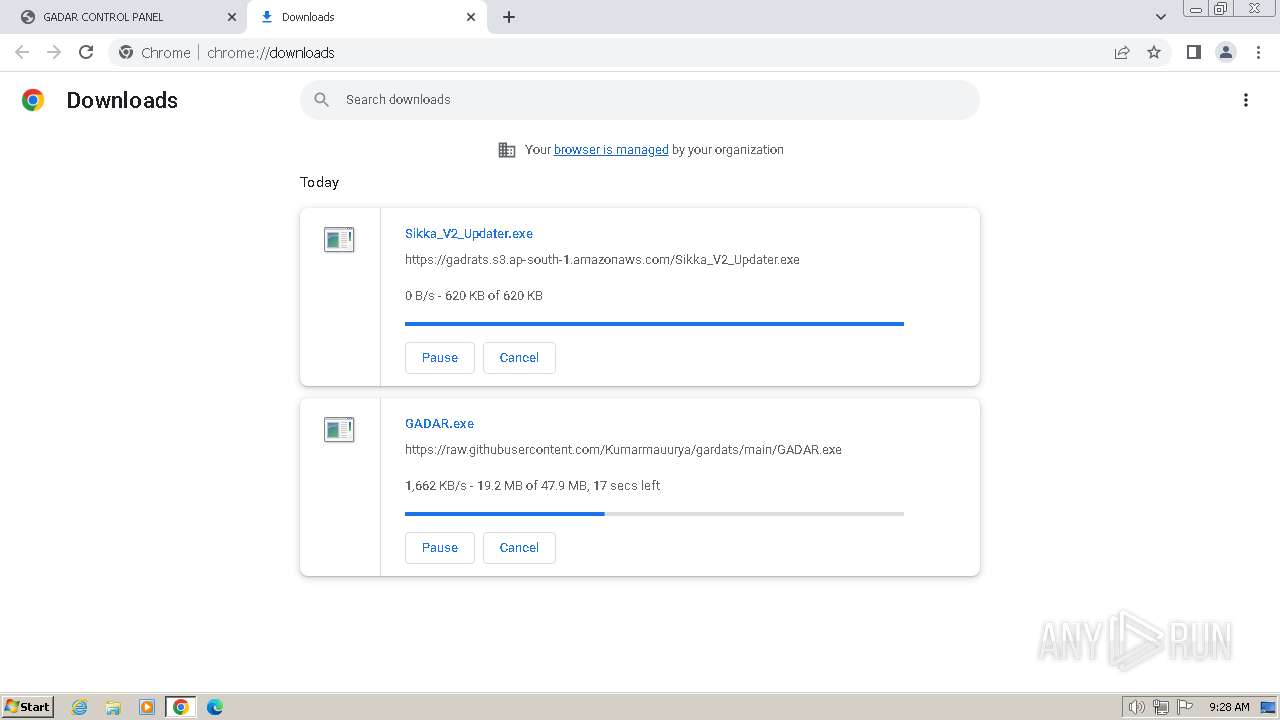
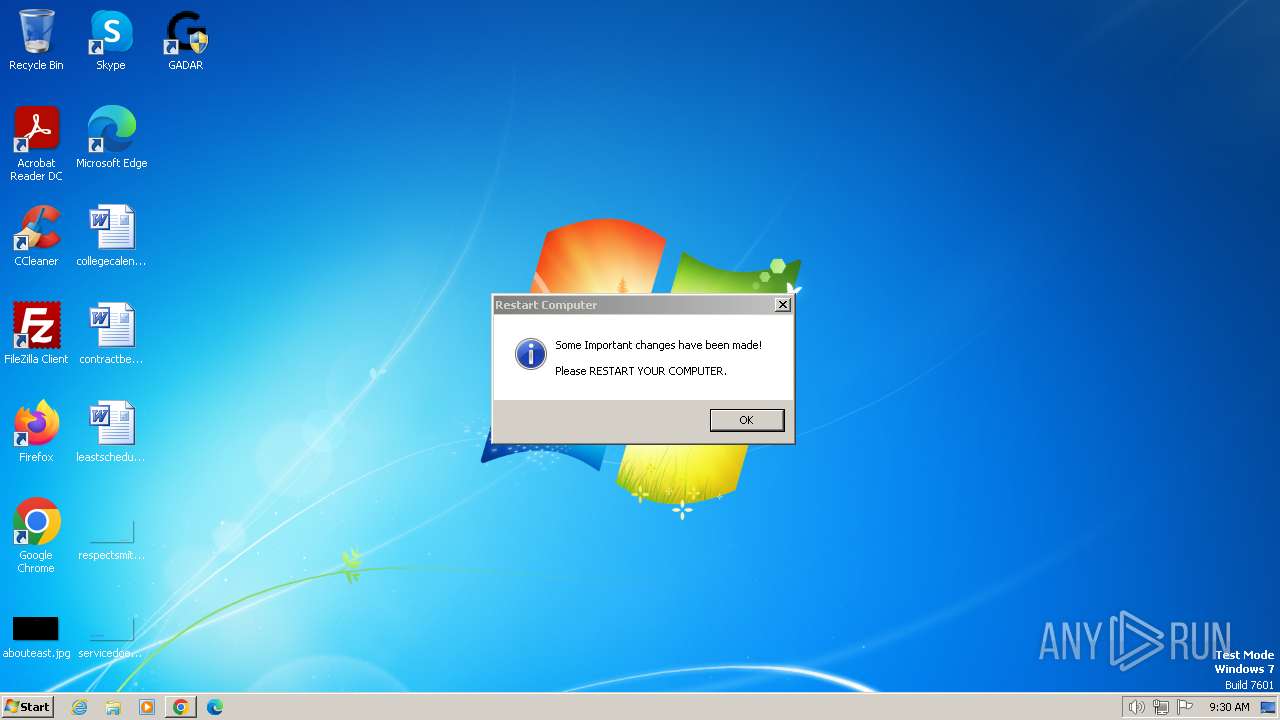
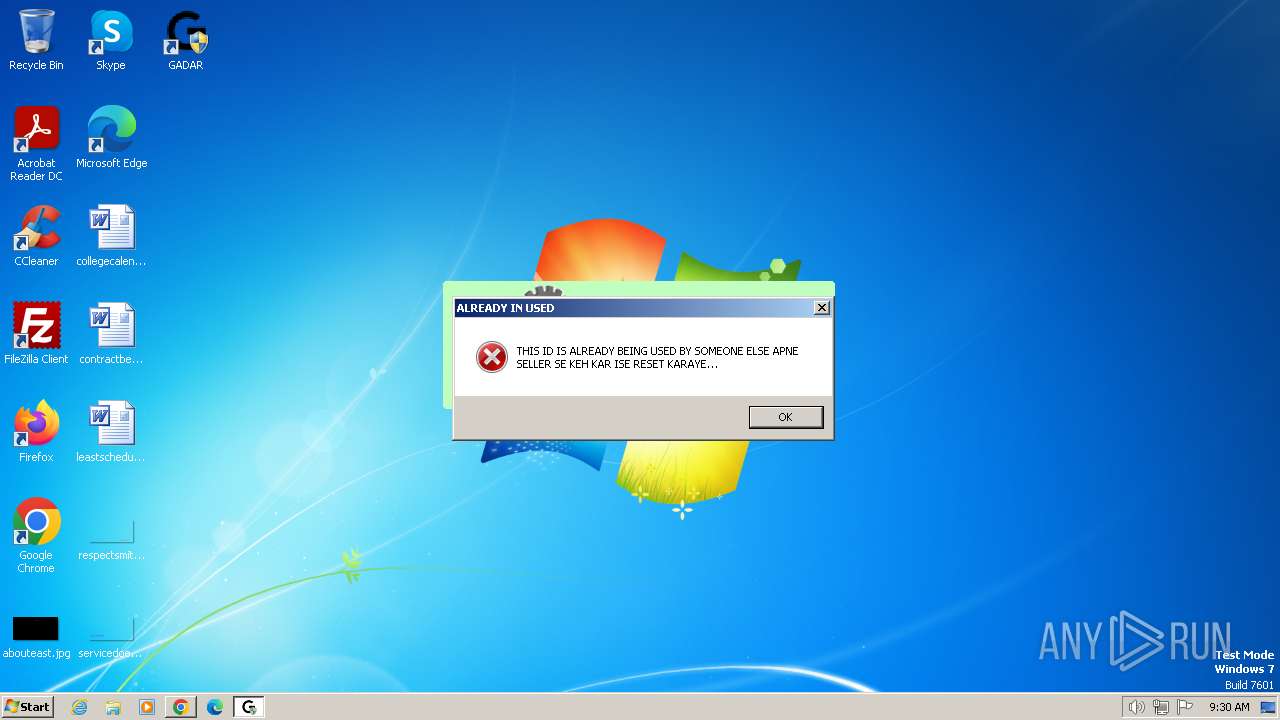
MALICIOUS
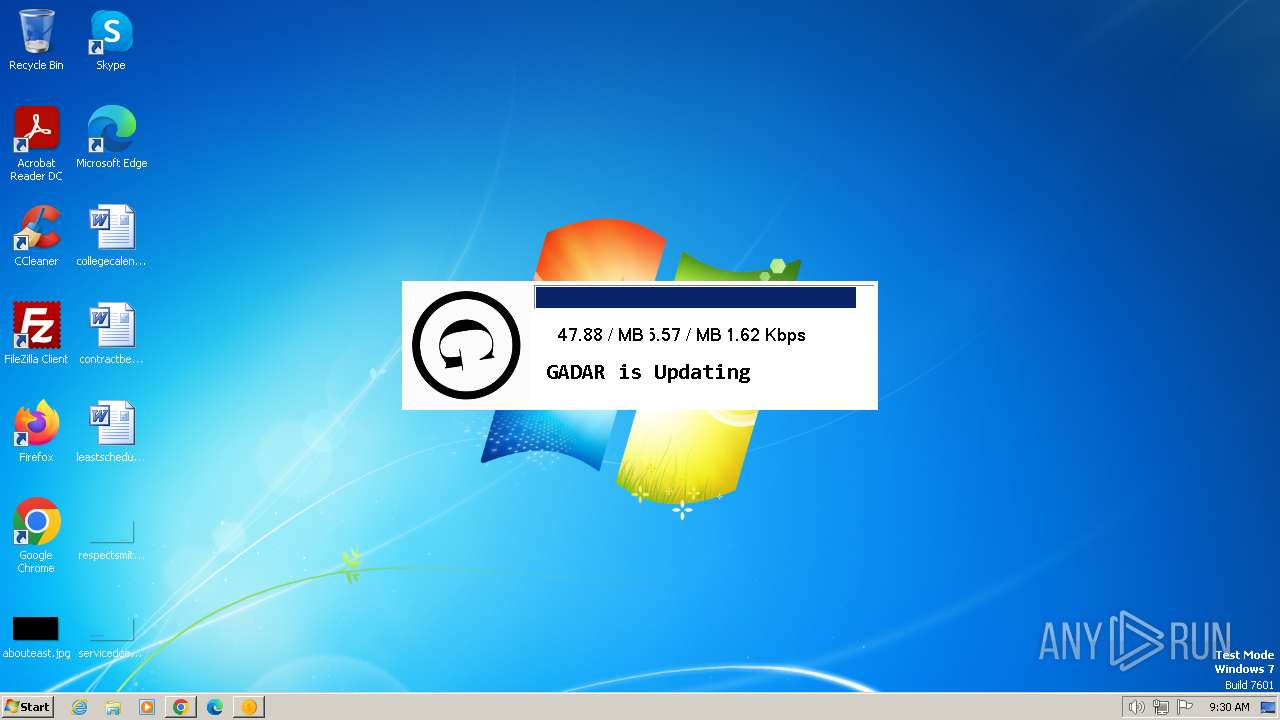
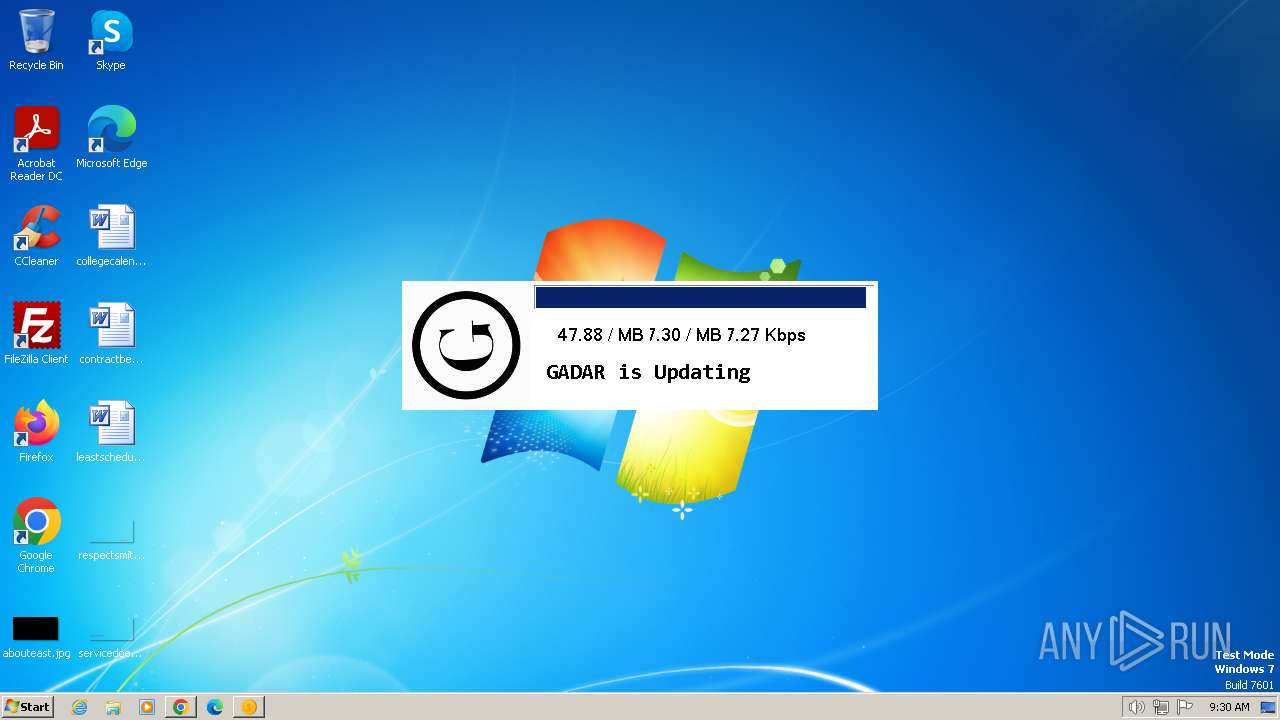
Drops the executable file immediately after the start
- GADAR.exe (PID: 2172)
- GADAR.exe (PID: 2892)
- GADAR.exe (PID: 1236)
SUSPICIOUS
Reads the Internet Settings
- Sikka_V2_Updater.exe (PID: 2088)
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2172)
- GADAR.exe (PID: 2892)
- InstallUtil.exe (PID: 3632)
Reads settings of System Certificates
- Sikka_V2_Updater.exe (PID: 2088)
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2892)
Reads security settings of Internet Explorer
- Sikka_V2_Updater.exe (PID: 2088)
- GADAR.exe (PID: 1236)
- InstallUtil.exe (PID: 3632)
Executable content was dropped or overwritten
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2172)
- GADAR.exe (PID: 2892)
Reads the BIOS version
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2172)
- GADAR.exe (PID: 2892)
Application launched itself
- GADAR.exe (PID: 1236)
Suspicious use of NETSH.EXE
- GADAR.exe (PID: 1236)
Connects to unusual port
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2892)
Starts CMD.EXE for commands execution
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2892)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 3228)
- cmd.exe (PID: 1352)
Adds/modifies Windows certificates
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2892)
Found strings related to reading or modifying Windows Defender settings
- GADAR.exe (PID: 2892)
The process creates files with name similar to system file names
- GADAR.exe (PID: 2892)
Executing commands from a ".bat" file
- GADAR.exe (PID: 2892)
Executes as Windows Service
- SQLServices.exe (PID: 1804)
Reads Internet Explorer settings
- GADAR.exe (PID: 2892)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 2544)
INFO
Application launched itself
- chrome.exe (PID: 2120)
Executable content was dropped or overwritten
- chrome.exe (PID: 2120)
- chrome.exe (PID: 3304)
Drops the executable file immediately after the start
- chrome.exe (PID: 2120)
- chrome.exe (PID: 3304)
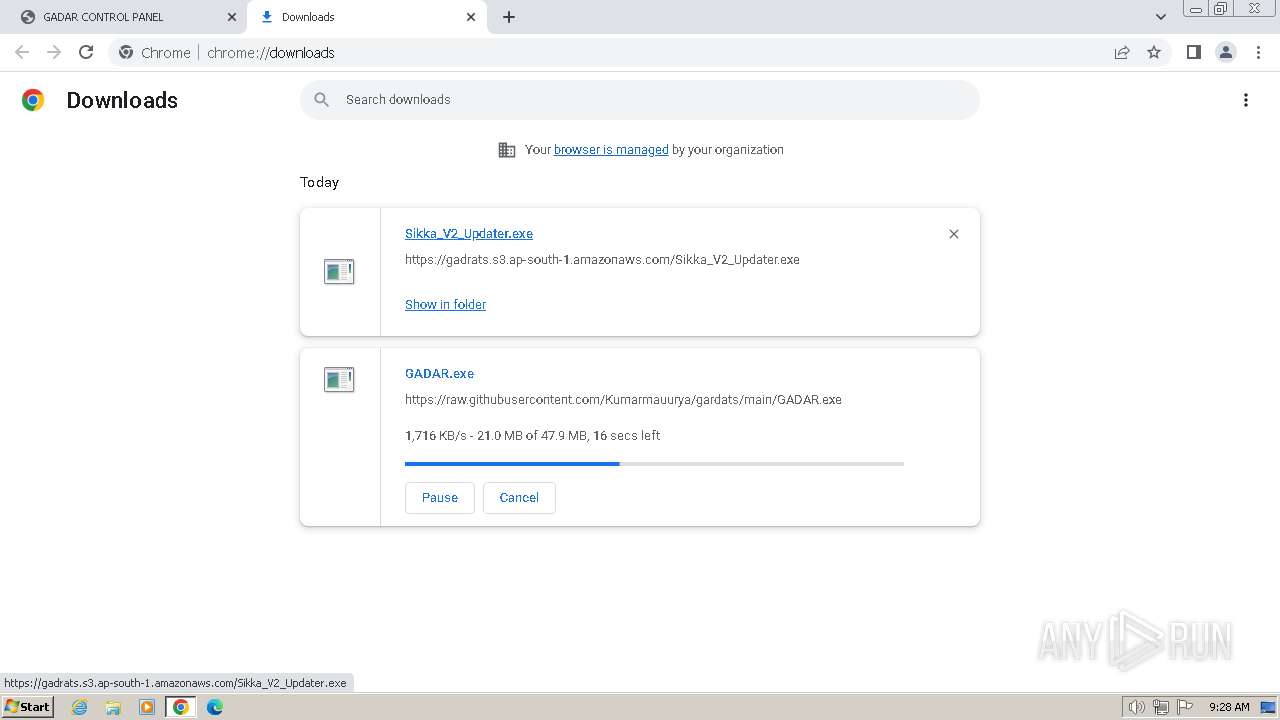
The process uses the downloaded file
- chrome.exe (PID: 4084)
- chrome.exe (PID: 2120)
- chrome.exe (PID: 4036)
Checks supported languages
- Sikka_V2_Updater.exe (PID: 2088)
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2172)
- GADAR.exe (PID: 2892)
- InstallUtil.exe (PID: 3632)
- SQLServices.exe (PID: 1804)
Reads the computer name
- Sikka_V2_Updater.exe (PID: 2088)
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2172)
- GADAR.exe (PID: 2892)
- InstallUtil.exe (PID: 3632)
- SQLServices.exe (PID: 1804)
Reads the machine GUID from the registry
- Sikka_V2_Updater.exe (PID: 2088)
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2172)
- GADAR.exe (PID: 2892)
- InstallUtil.exe (PID: 3632)
- SQLServices.exe (PID: 1804)
Reads Environment values
- Sikka_V2_Updater.exe (PID: 2088)
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2892)
Create files in a temporary directory
- Sikka_V2_Updater.exe (PID: 2088)
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2172)
- GADAR.exe (PID: 2892)
Reads the software policy settings
- Sikka_V2_Updater.exe (PID: 2088)
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2892)
Creates files or folders in the user directory
- Sikka_V2_Updater.exe (PID: 2088)
- GADAR.exe (PID: 2892)
- InstallUtil.exe (PID: 3632)
Checks proxy server information
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2172)
- GADAR.exe (PID: 2892)
Process checks whether UAC notifications are on
- GADAR.exe (PID: 2172)
- GADAR.exe (PID: 1236)
- GADAR.exe (PID: 2892)
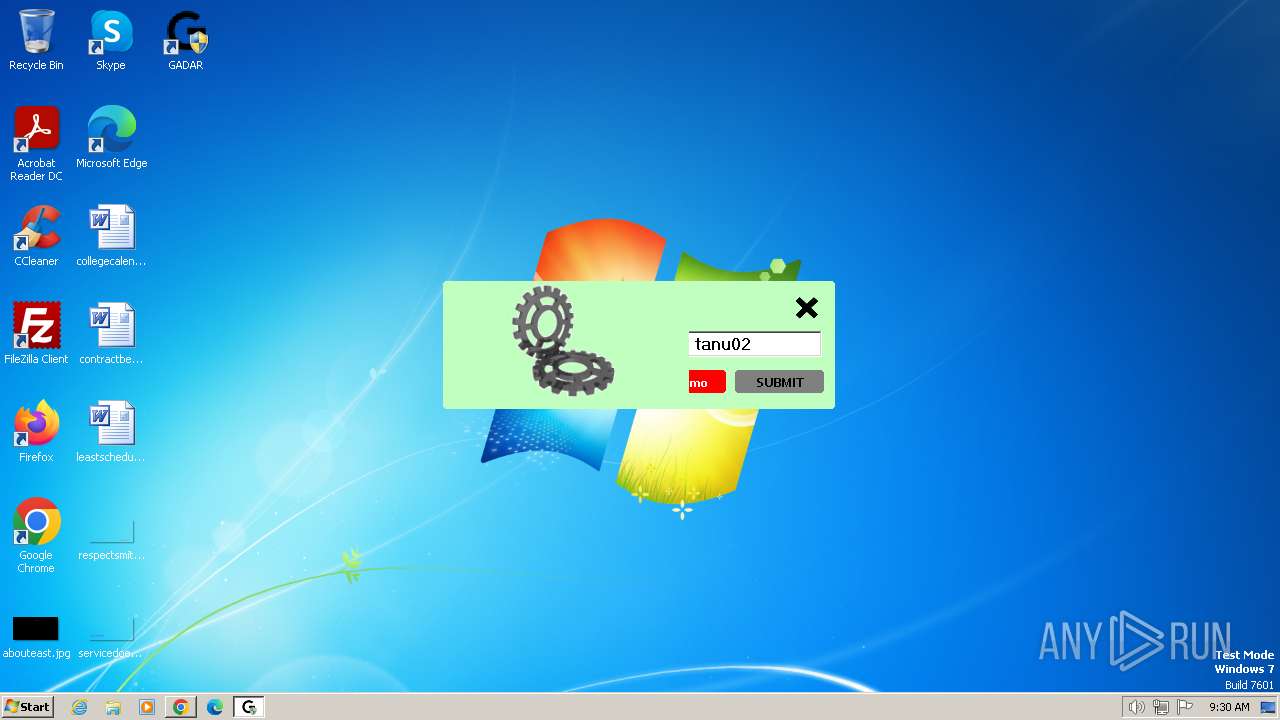
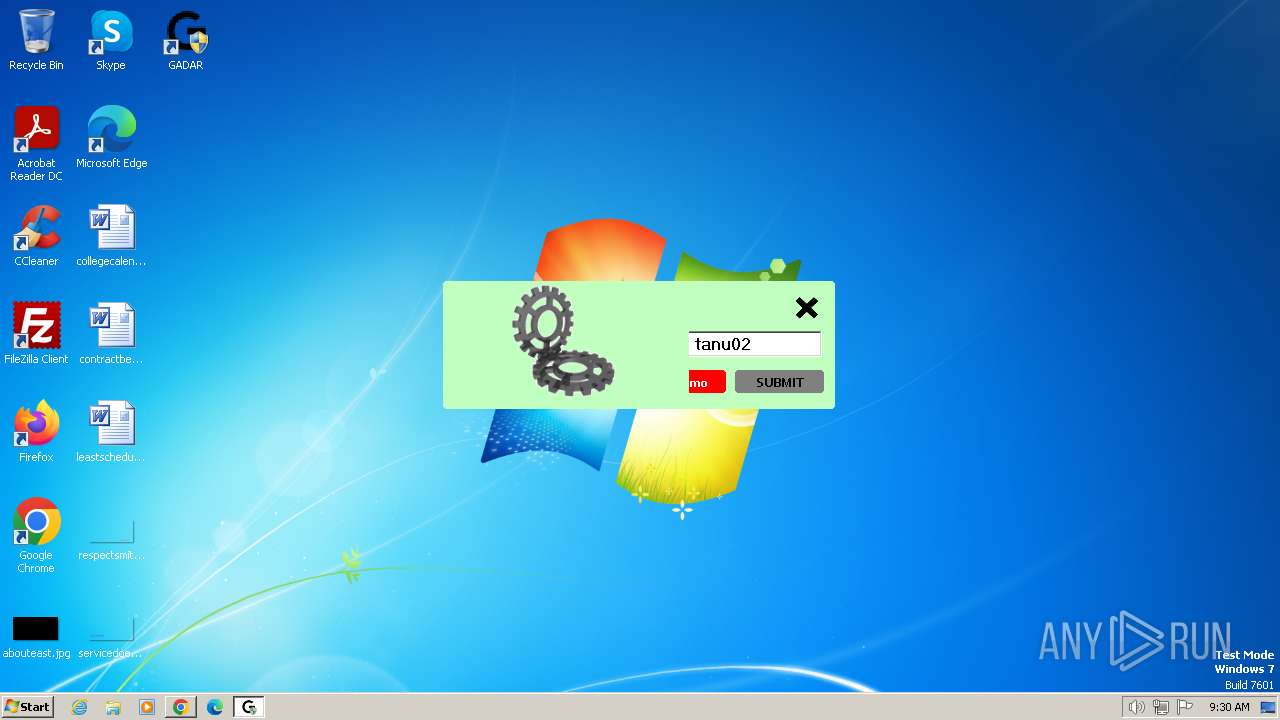
Manual execution by a user
- GADAR.exe (PID: 3916)
- GADAR.exe (PID: 2892)
- taskmgr.exe (PID: 3880)
Creates files in the program directory
- GADAR.exe (PID: 2892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
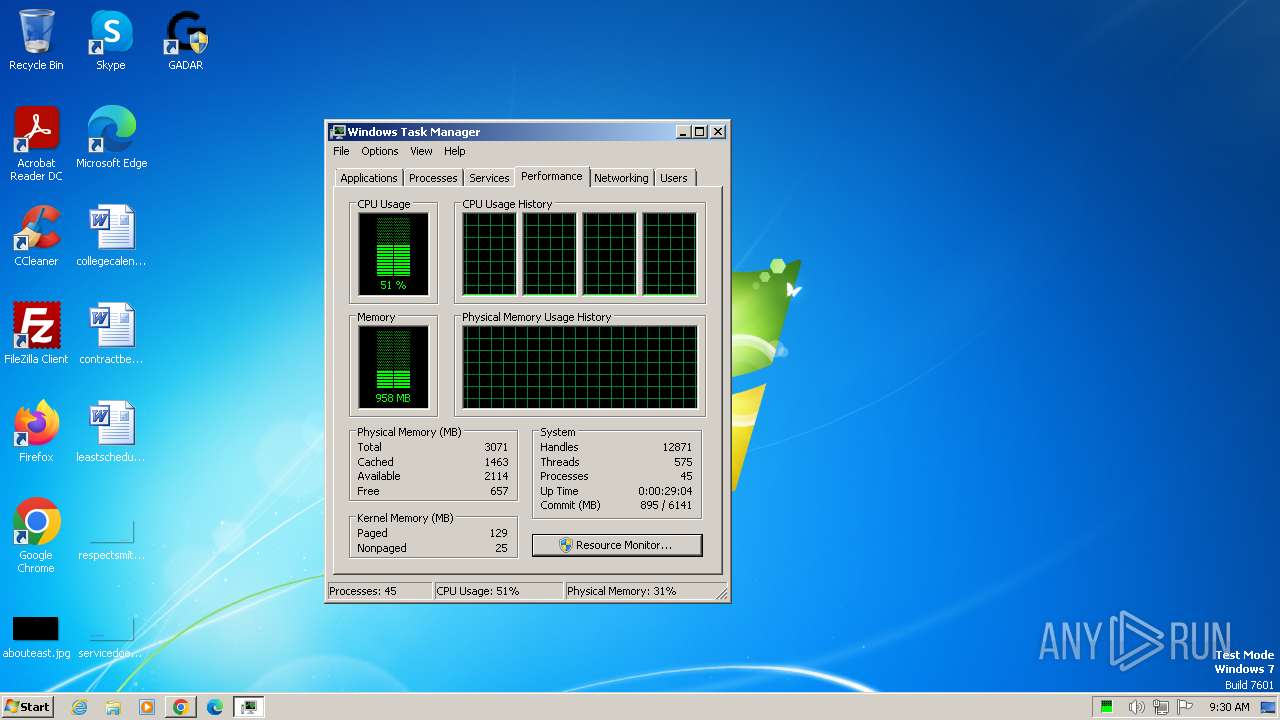
Total processes
120
Monitored processes
56
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --first-renderer-process --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2020 --field-trial-handle=1136,i,16625616334756687350,16177600908220511209,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 316 | "netsh" int tcp set global timestamps=disabled | C:\Windows\System32\netsh.exe | — | GADAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3524 --field-trial-handle=1136,i,16625616334756687350,16177600908220511209,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 848 | "tzutil.exe" /s "India Standard Time" | C:\Windows\System32\tzutil.exe | — | GADAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Time Zone Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 920 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3300 --field-trial-handle=1136,i,16625616334756687350,16177600908220511209,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 920 | "netsh" int tcp set global chimney=disabled | C:\Windows\System32\netsh.exe | — | GADAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | "netsh" int tcp set global congestionprovider=ctcp | C:\Windows\System32\netsh.exe | — | GADAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | "netsh" int tcp set global ecncapability=default | C:\Windows\System32\netsh.exe | — | GADAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1232 | "netsh" int tcp set heuristics disabled | C:\Windows\System32\netsh.exe | — | GADAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | "C:\Users\admin\Downloads\GADAR.exe" | C:\Users\admin\Downloads\GADAR.exe | Sikka_V2_Updater.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
Total events
53 428
Read events
52 605
Write events
801
Delete events
22
Modification events
| (PID) Process: | (2120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2120) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2120) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
79
Suspicious files
168
Text files
76
Unknown types
269
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:— | SHA256:— | |||
| 2120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:— | SHA256:— | |||
| 2120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF1824f8.TMP | text | |
MD5:— | SHA256:— | |||
| 2120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1824f8.TMP | text | |
MD5:— | SHA256:— | |||
| 2120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF182507.TMP | — | |
MD5:— | SHA256:— | |||
| 2120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d38d7467-fc69-4b5a-b42a-c2c9ca795272.tmp | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
52
TCP/UDP connections
58
DNS requests
59
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/k4ldha5kevpu7qn7k4s3mznvgu_4.10.2710.0/oimompecagnajdejgnnjijobebaeigek_4.10.2710.0_win32_ad2kbvs6jks3au5dsxn7cqflsiiq.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2120 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
1348 | chrome.exe | 64.233.167.84:443 | accounts.google.com | GOOGLE | US | unknown |
1348 | chrome.exe | 185.178.208.173:443 | gadarts.com | Ddos-guard Ltd | RU | unknown |
1348 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
1348 | chrome.exe | 142.250.185.99:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
1348 | chrome.exe | 142.250.181.234:443 | content-autofill.googleapis.com | GOOGLE | US | whitelisted |
1348 | chrome.exe | 142.250.185.132:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
gadarts.com |
| unknown |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
www.google.com |
| whitelisted |
raw.githubusercontent.com |
| shared |
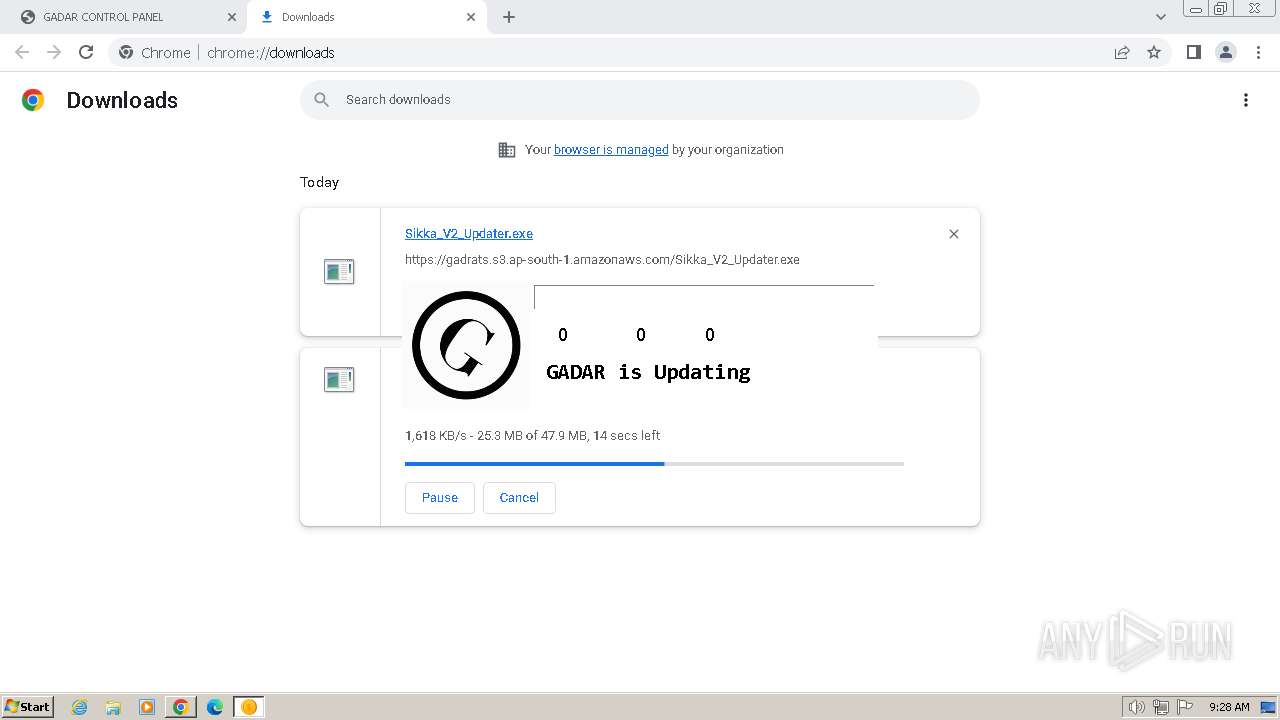
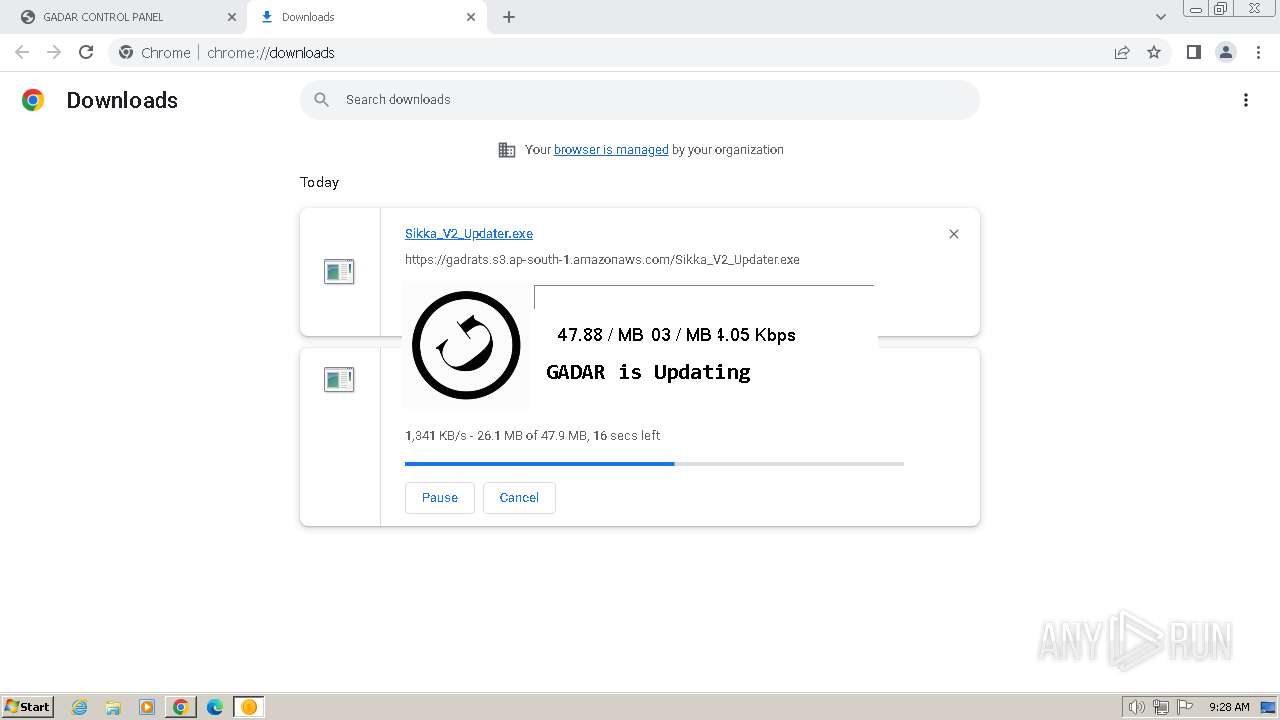
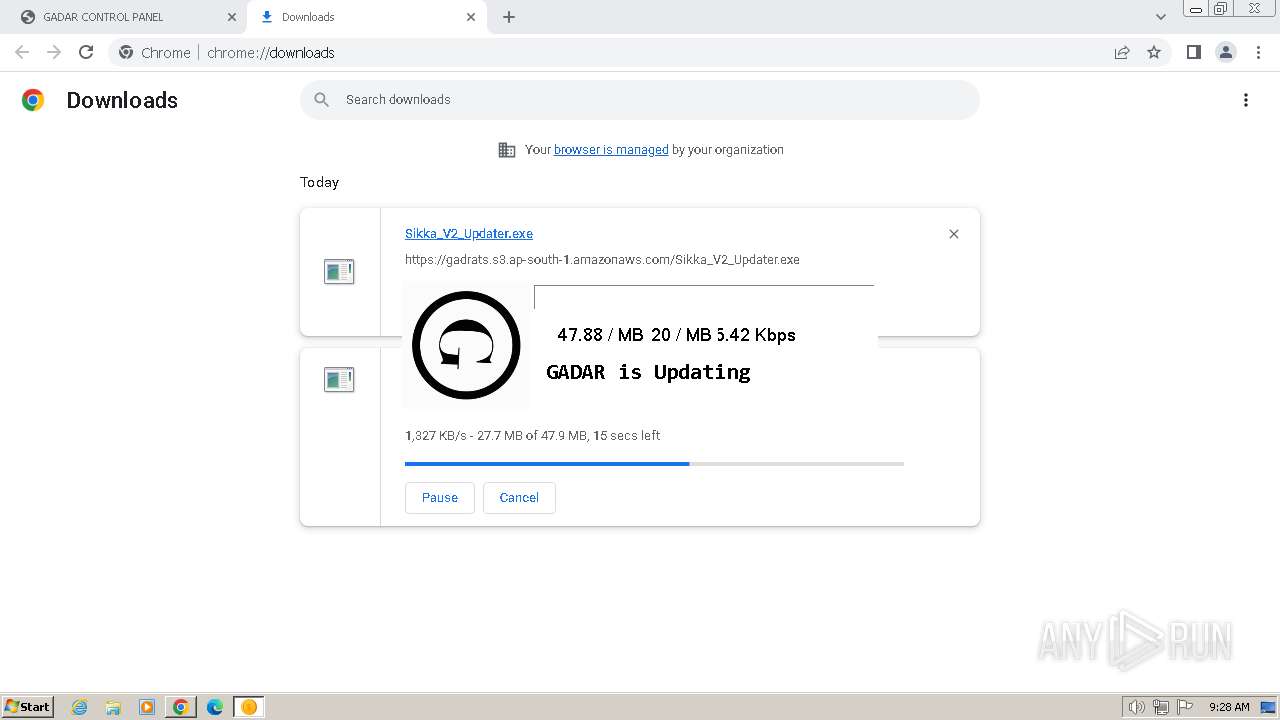
gadrats.s3.ap-south-1.amazonaws.com |
| unknown |
sb-ssl.google.com |
| whitelisted |
www.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
GADAR.exe | Native library pre-loader is trying to load native SQLite library "C:\Users\admin\Downloads\x86\SQLite.Interop.dll"...
|