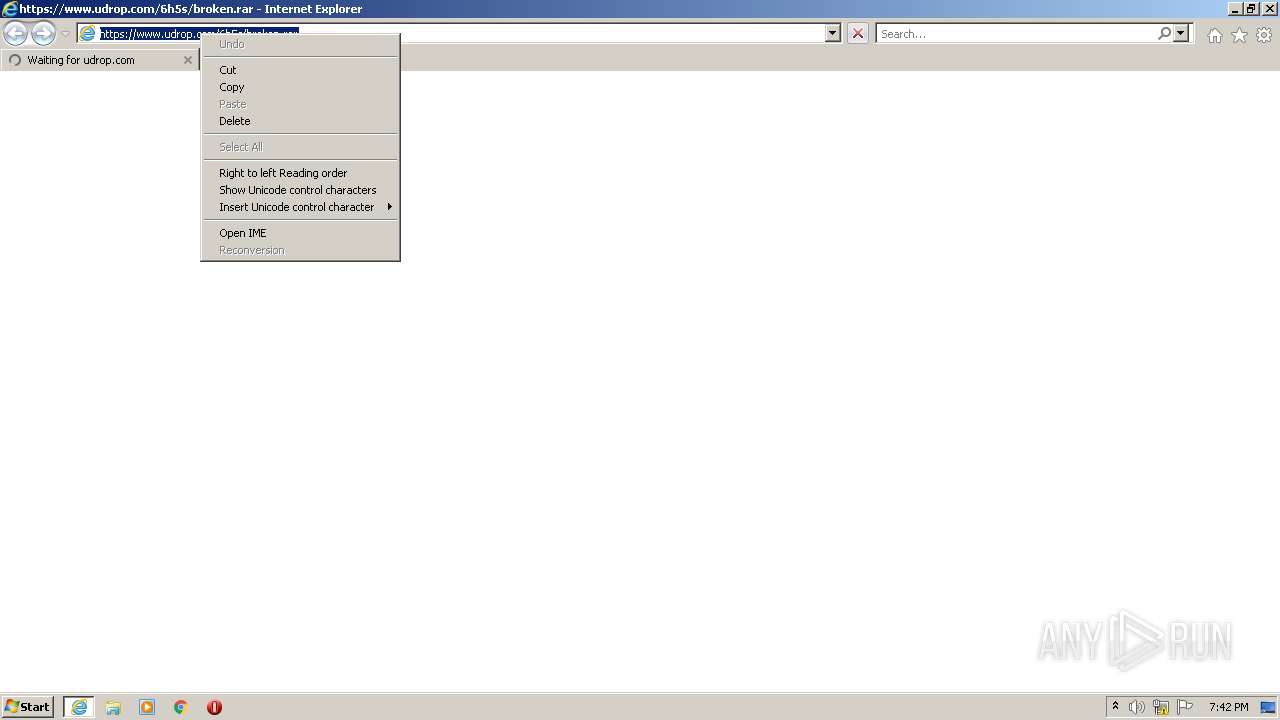
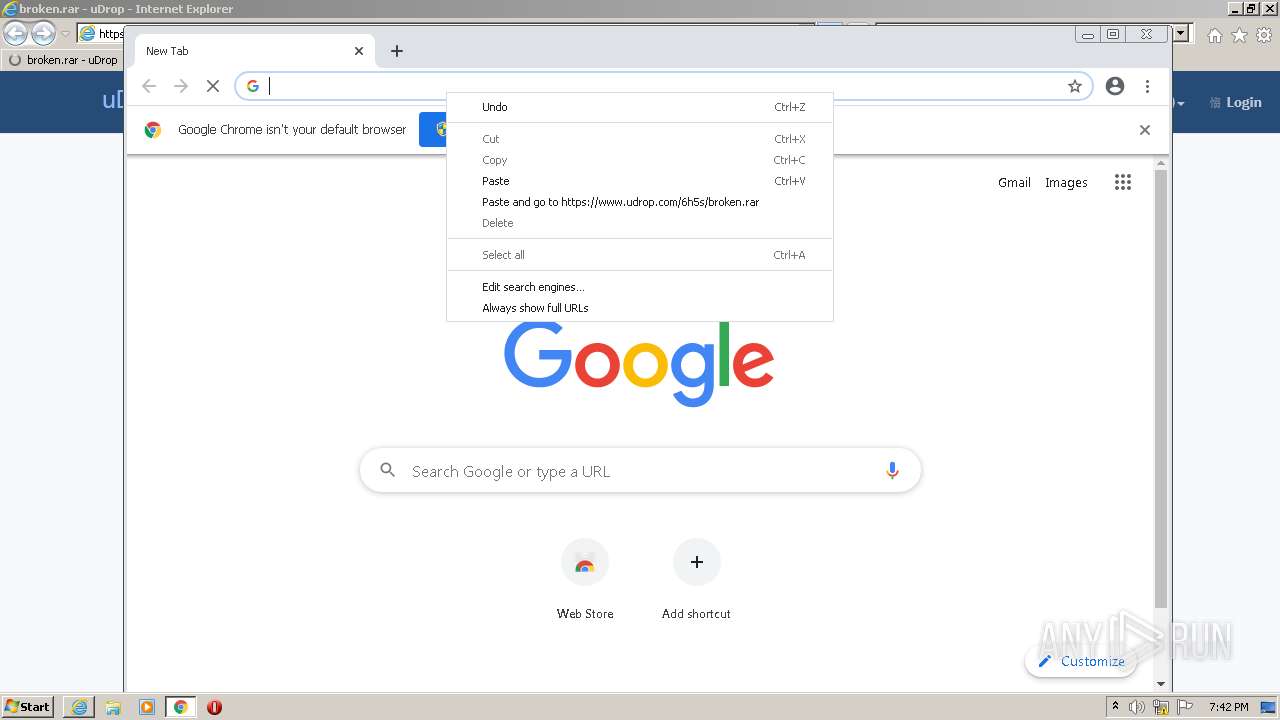
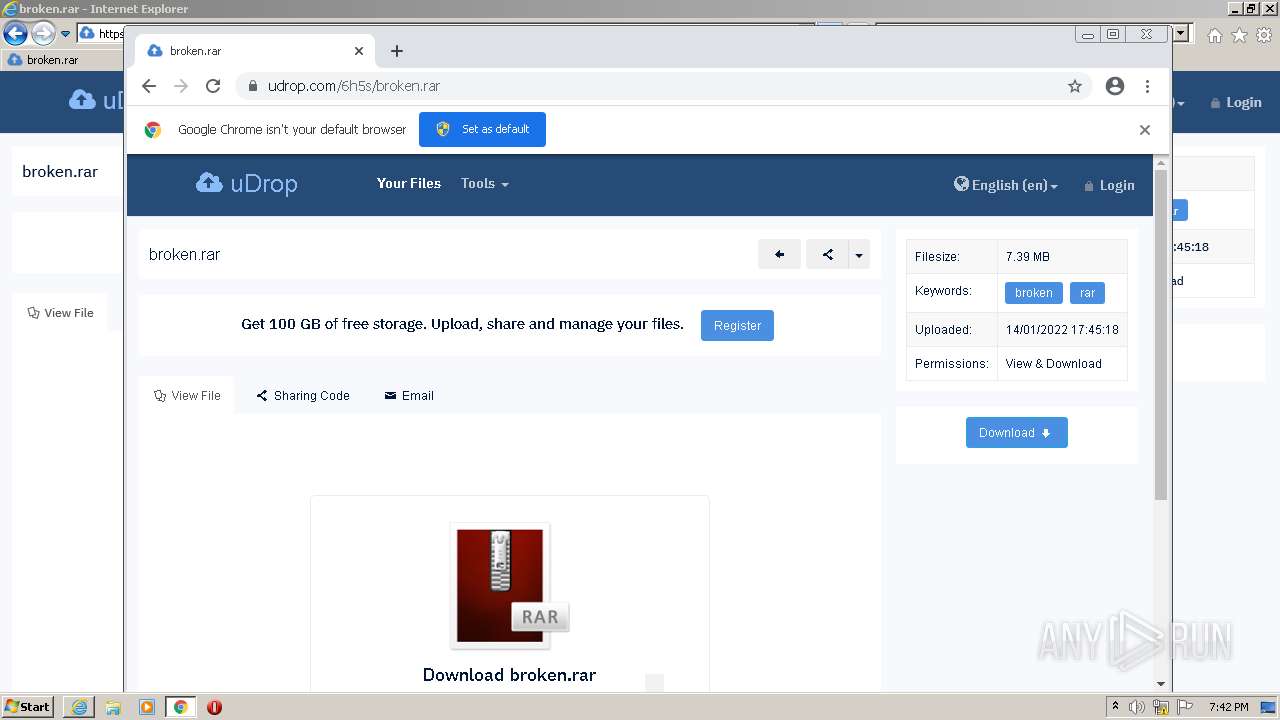
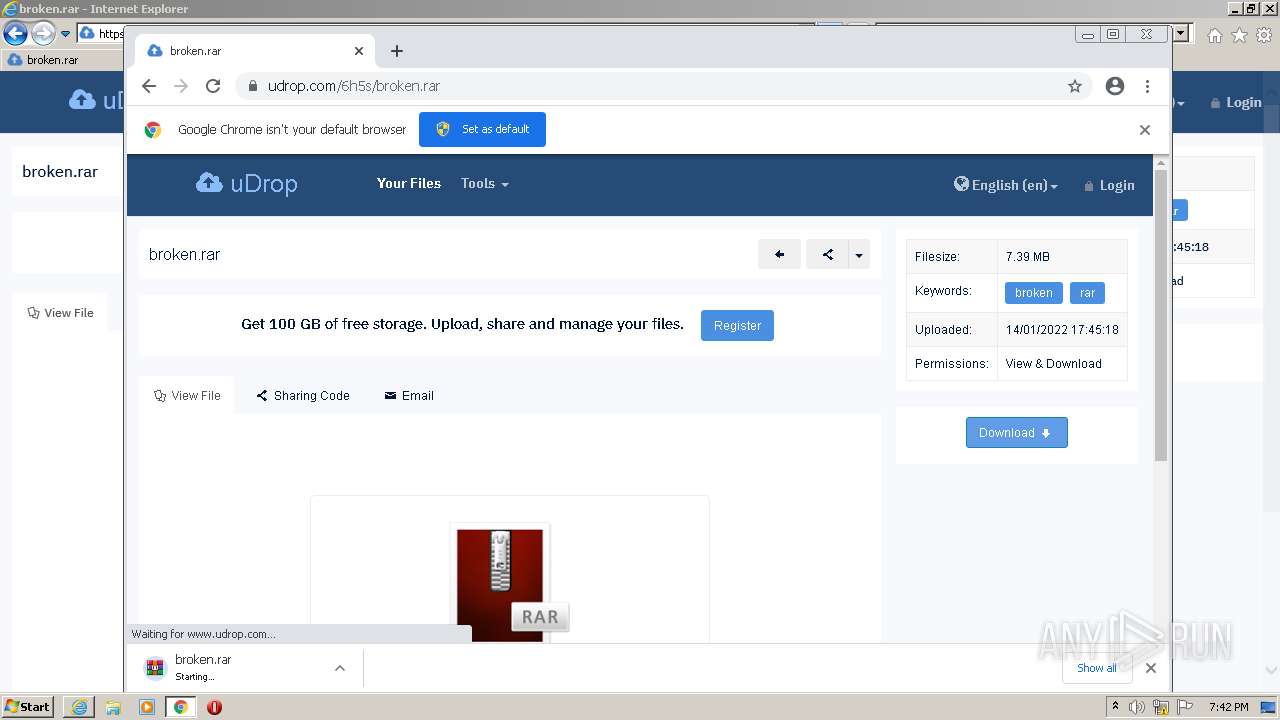
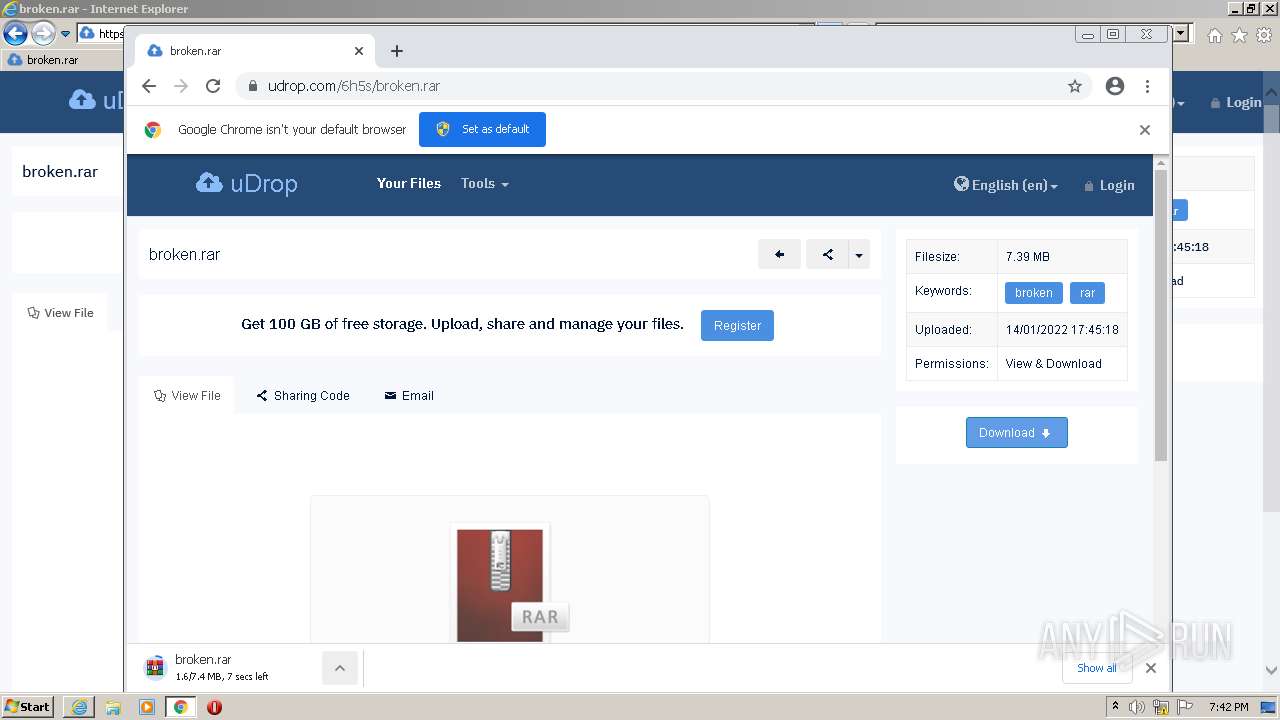
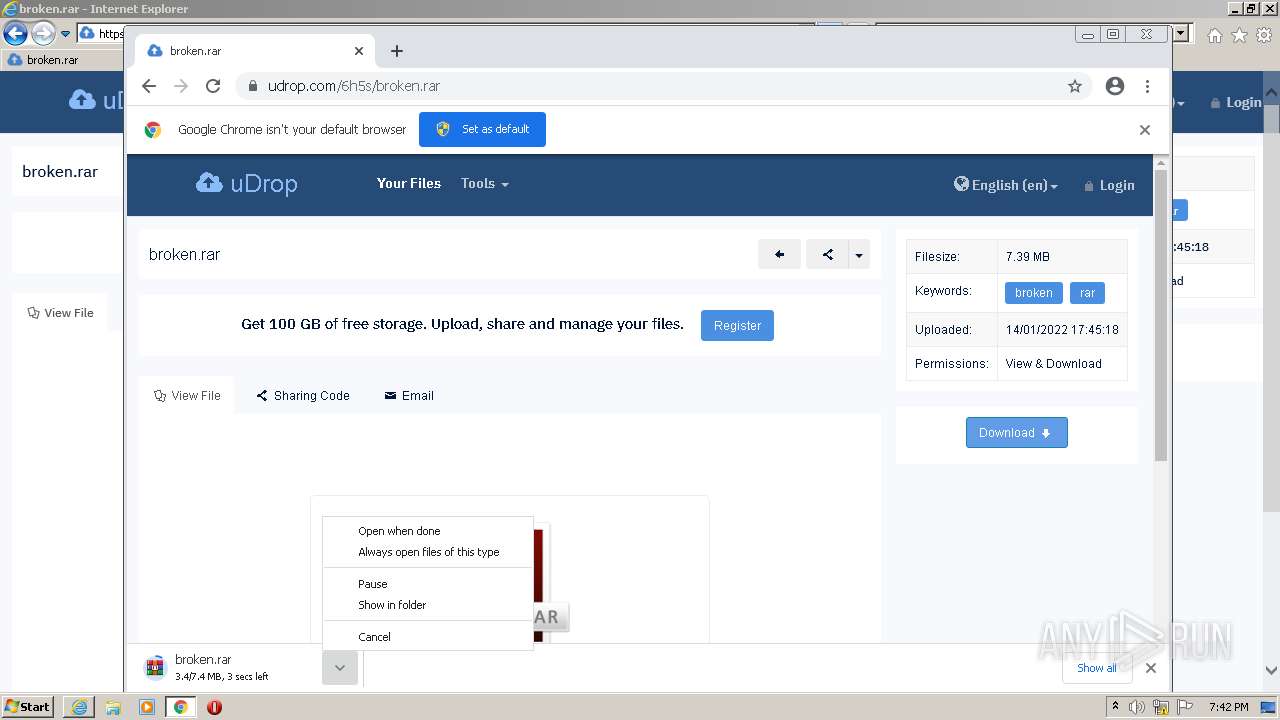
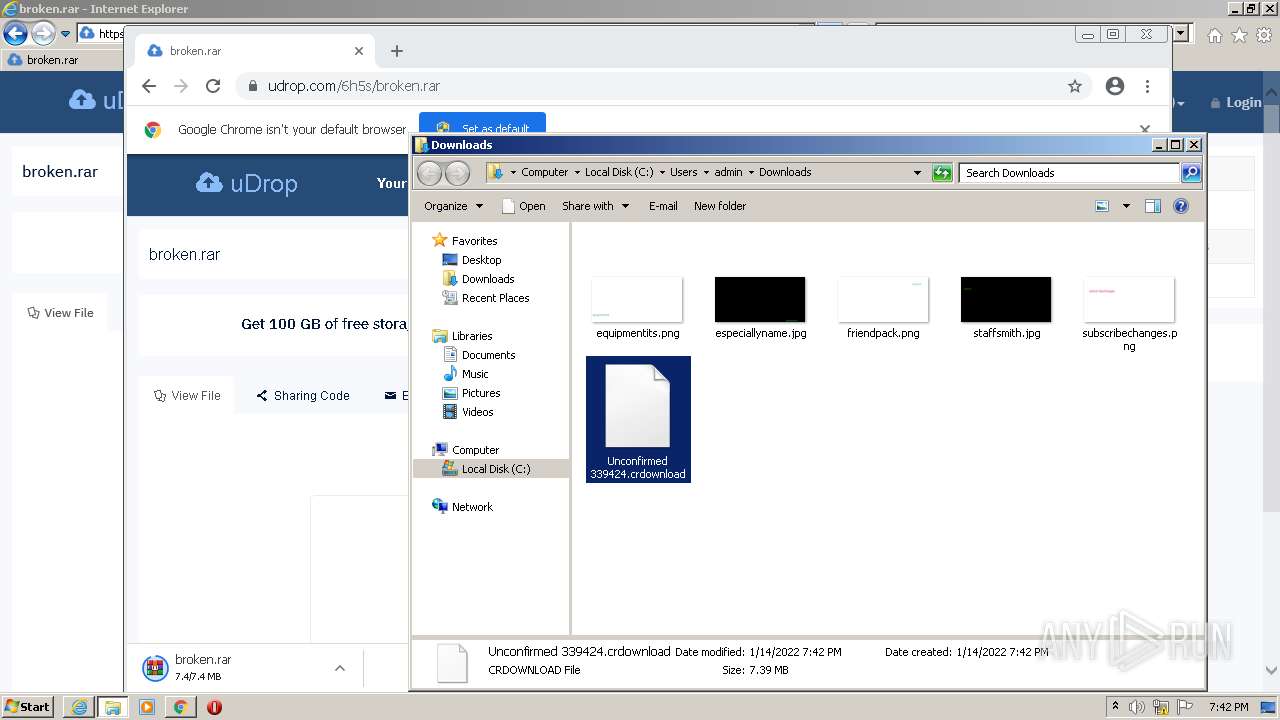
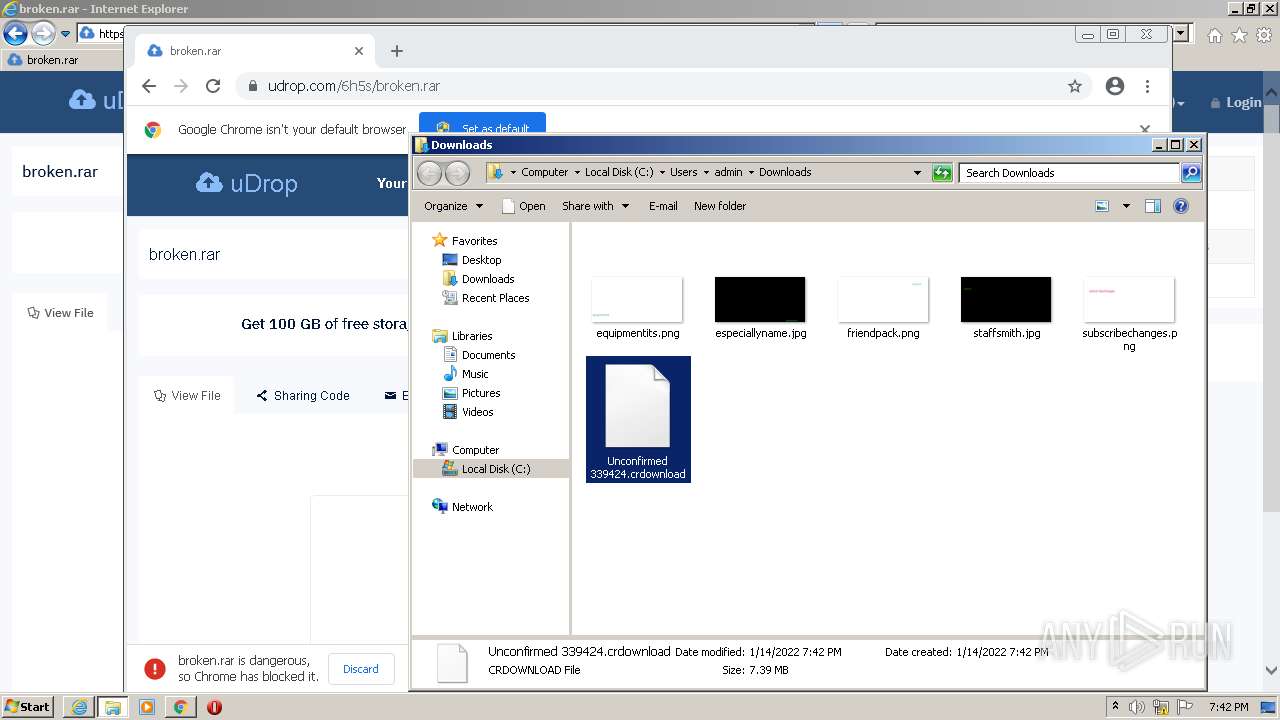
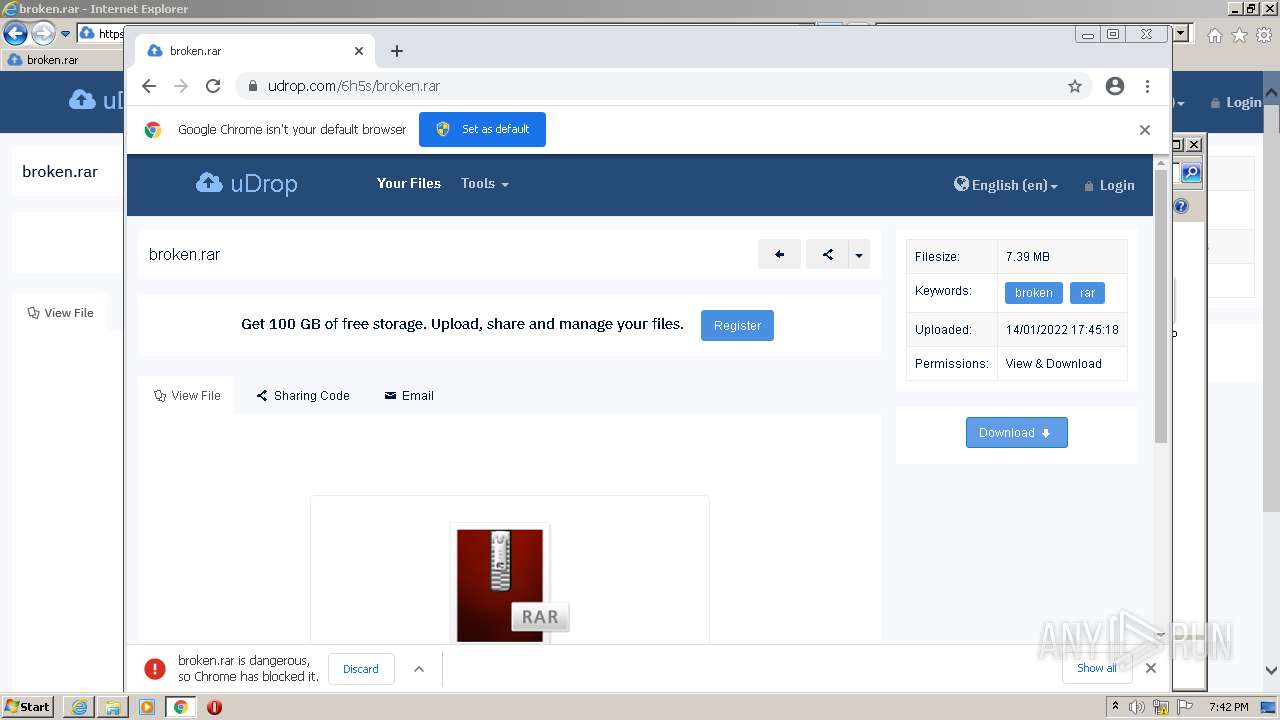
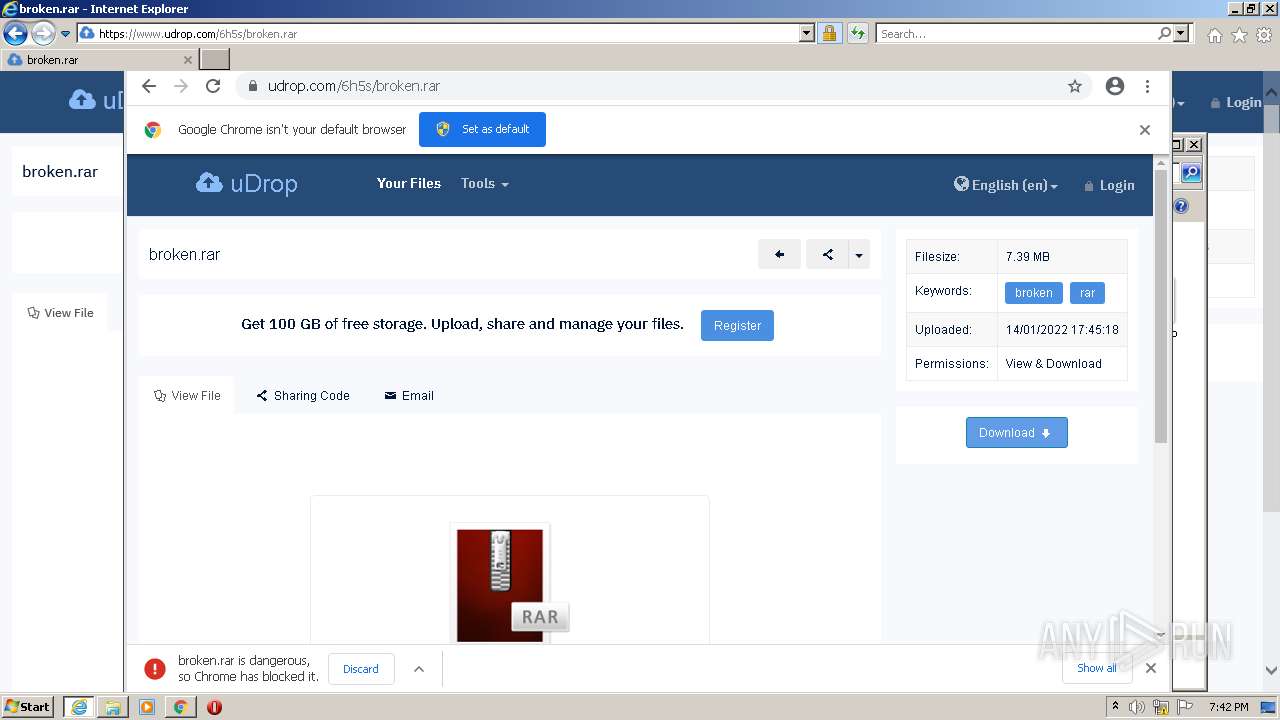
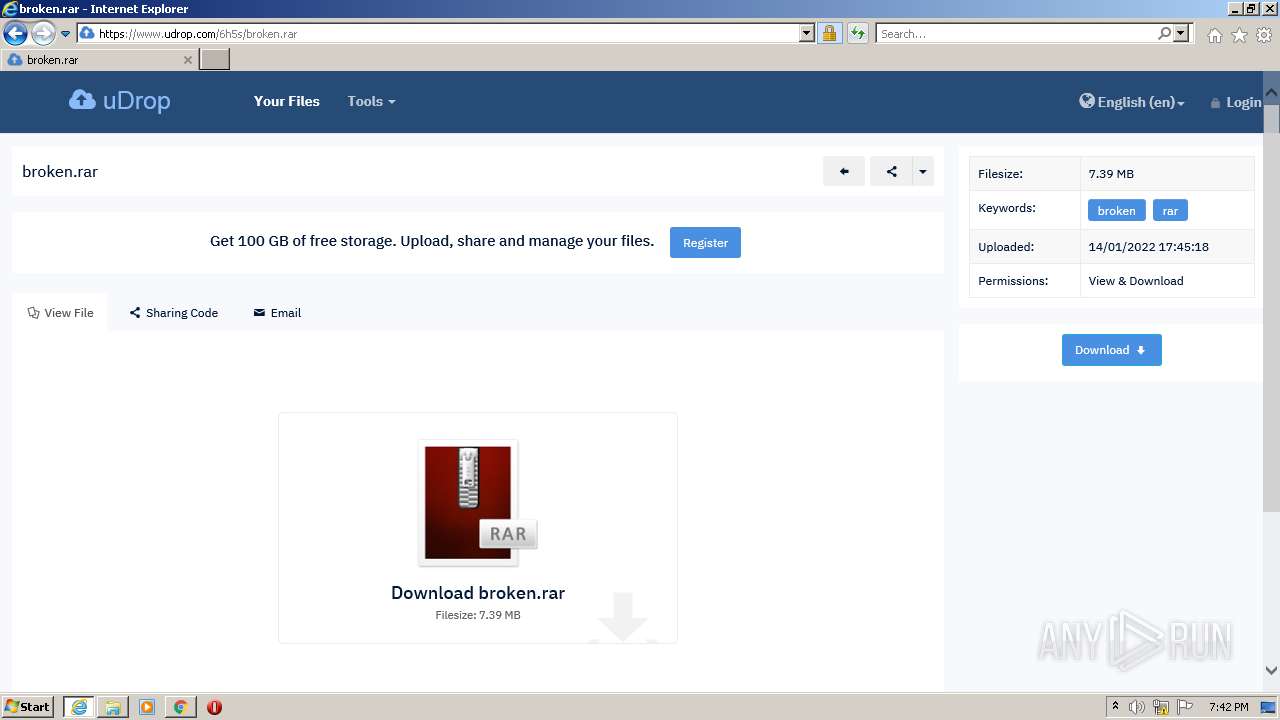
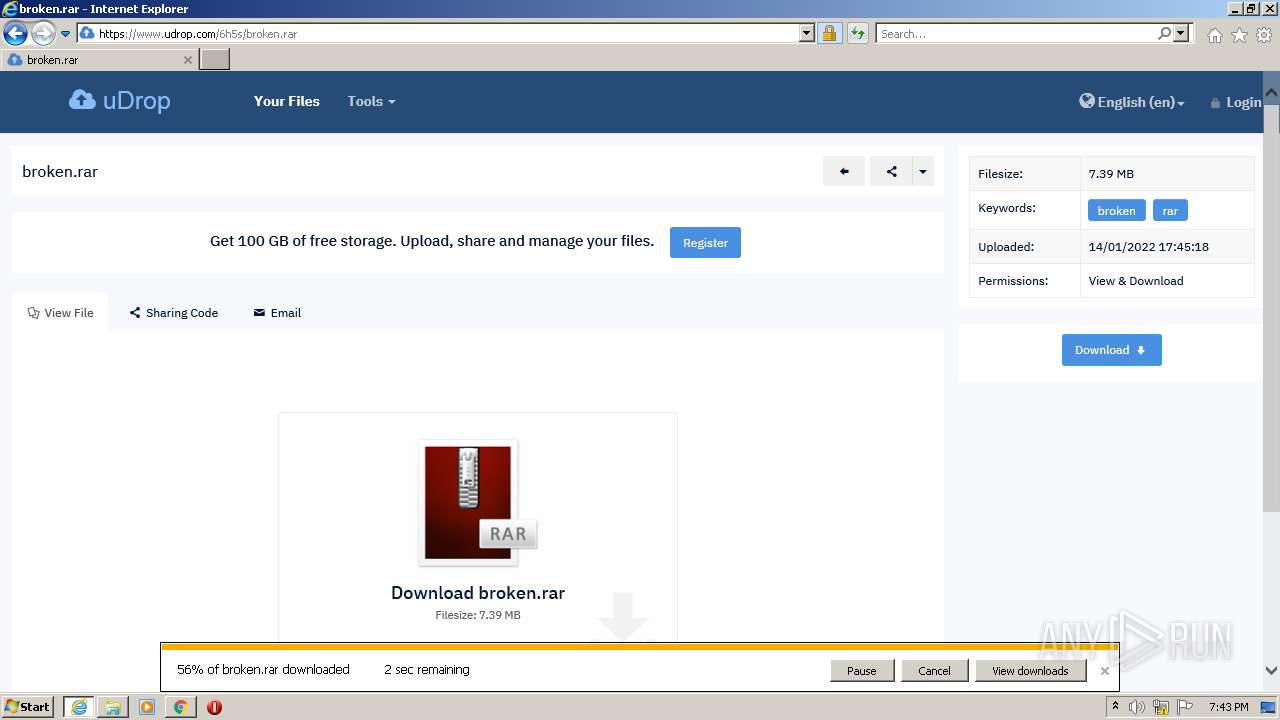
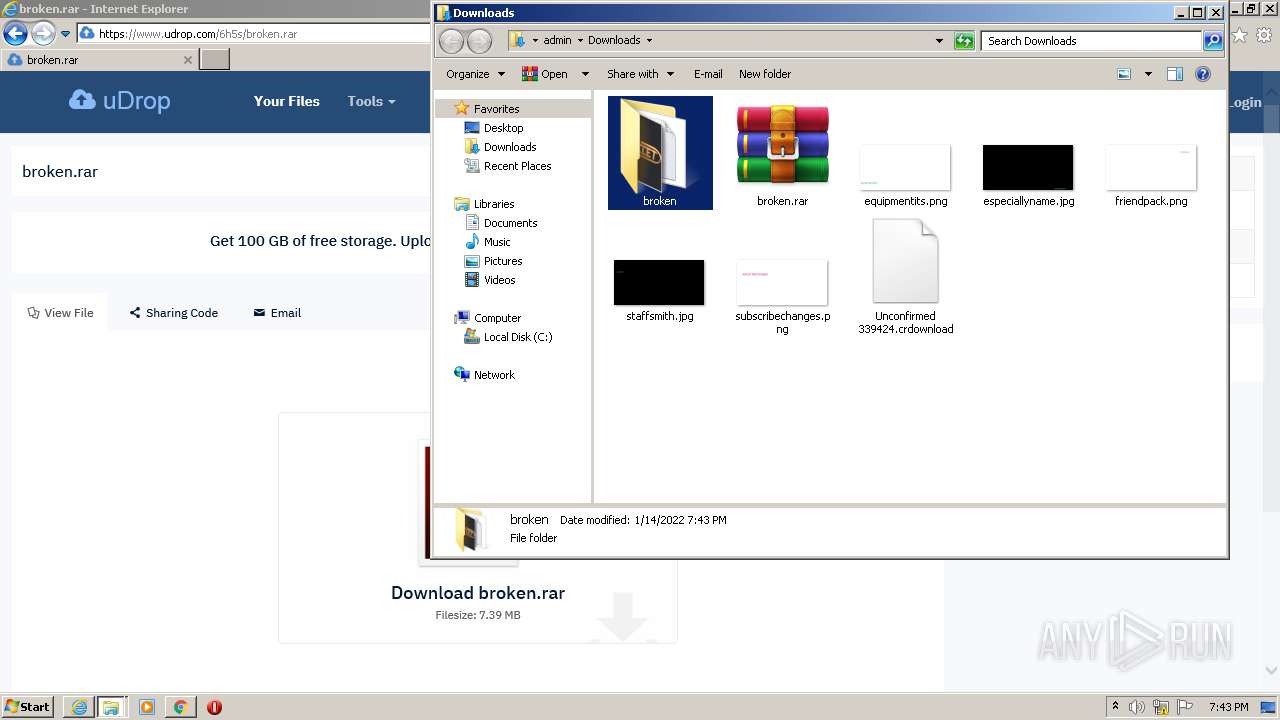
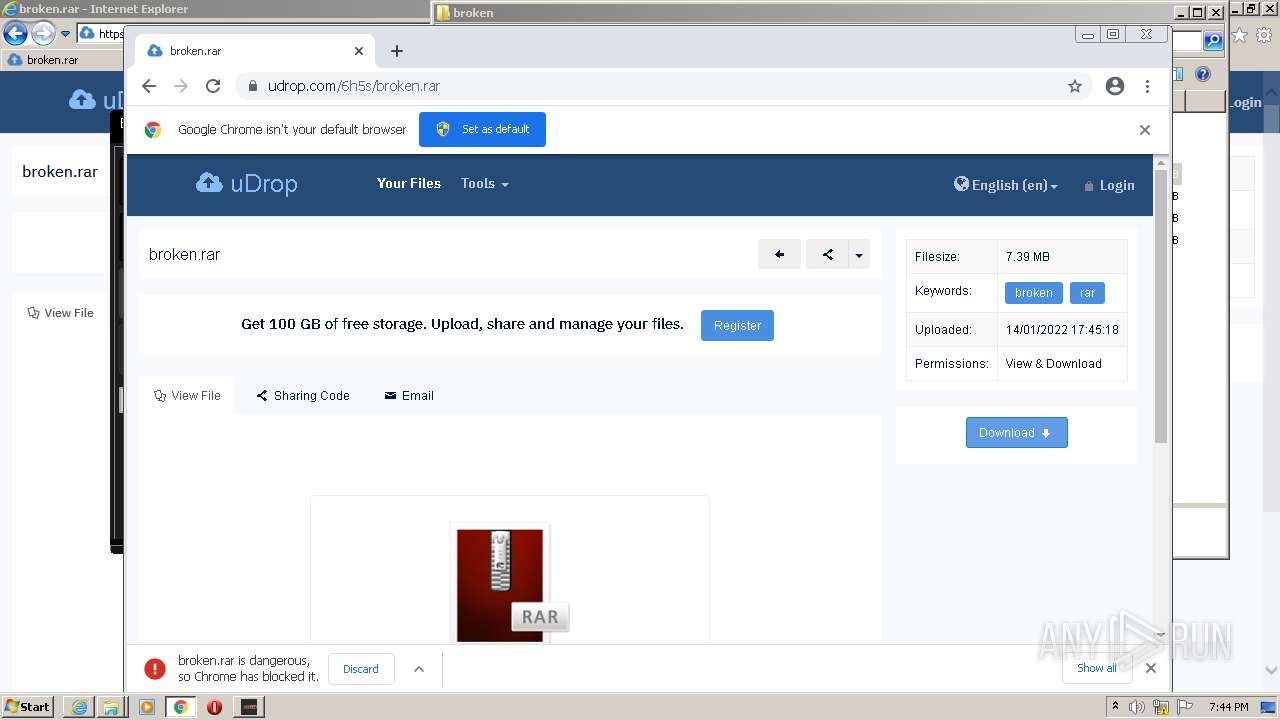
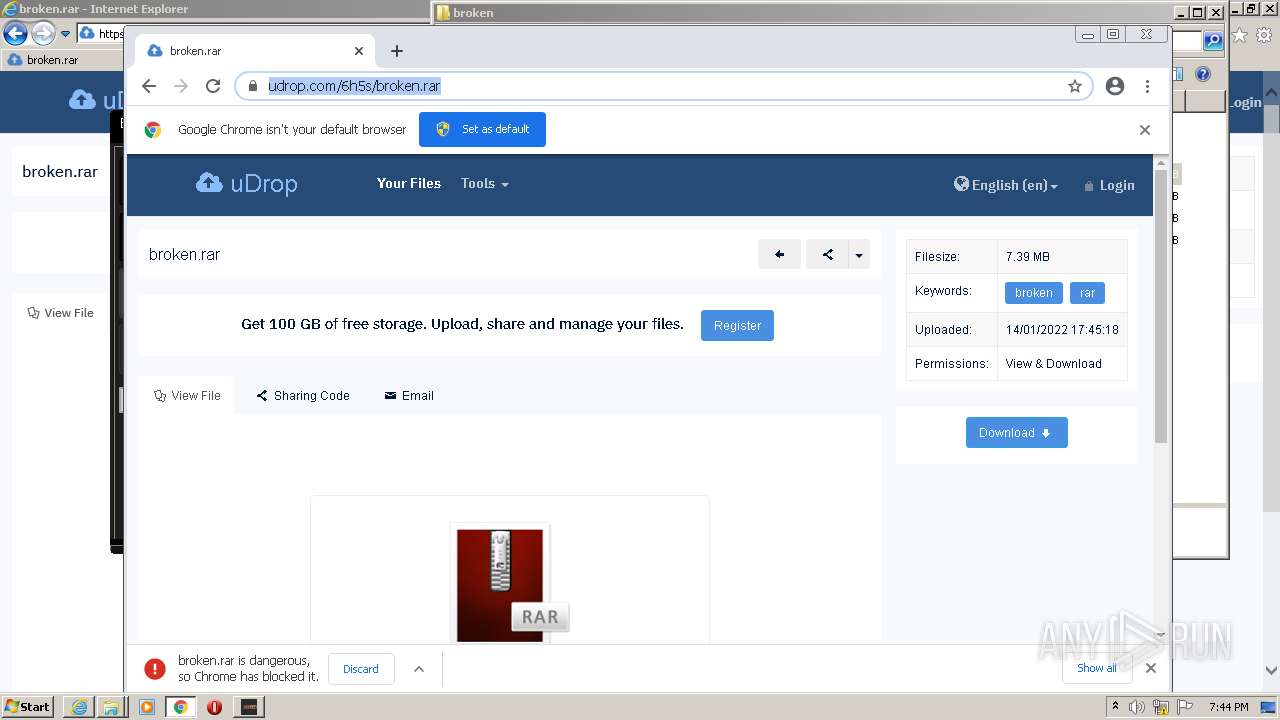
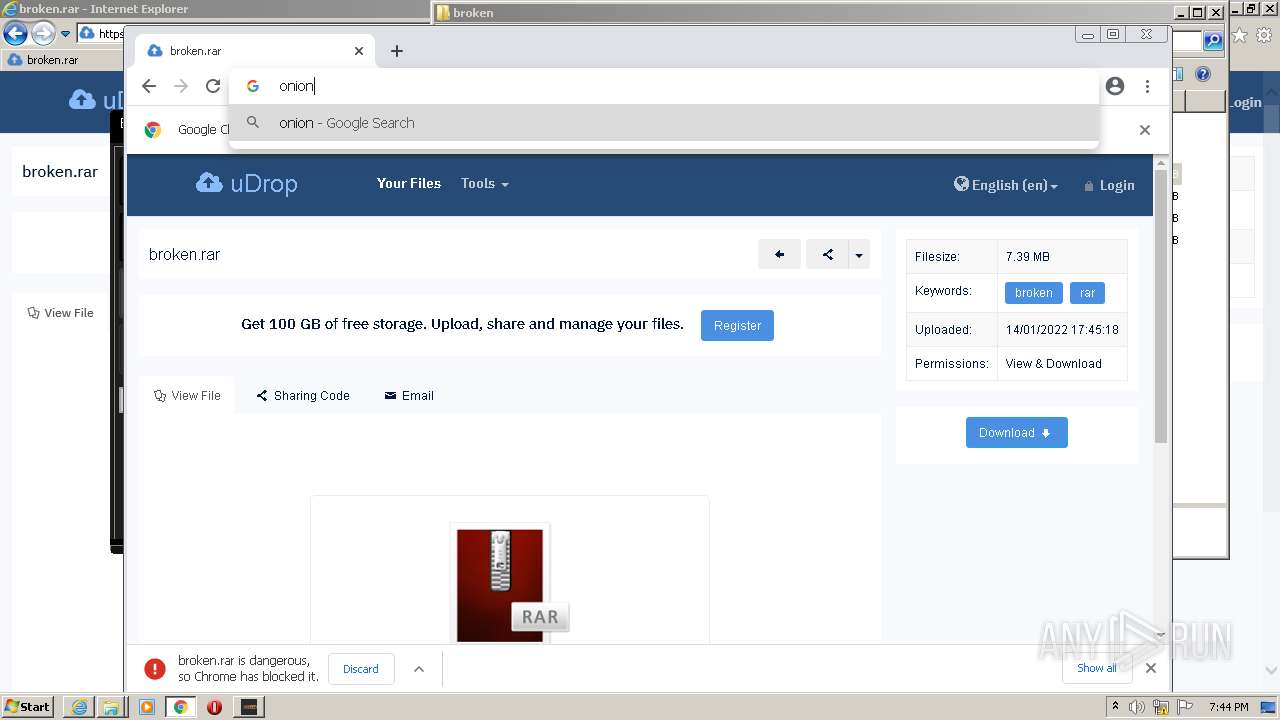
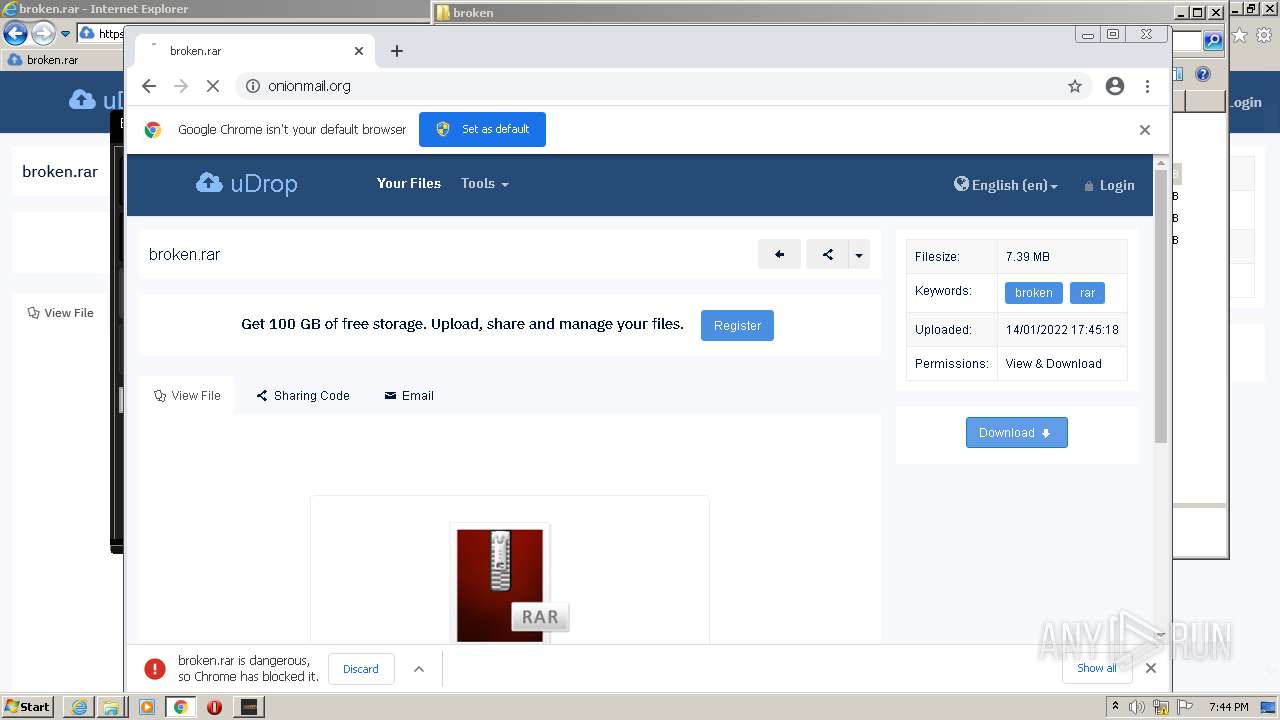
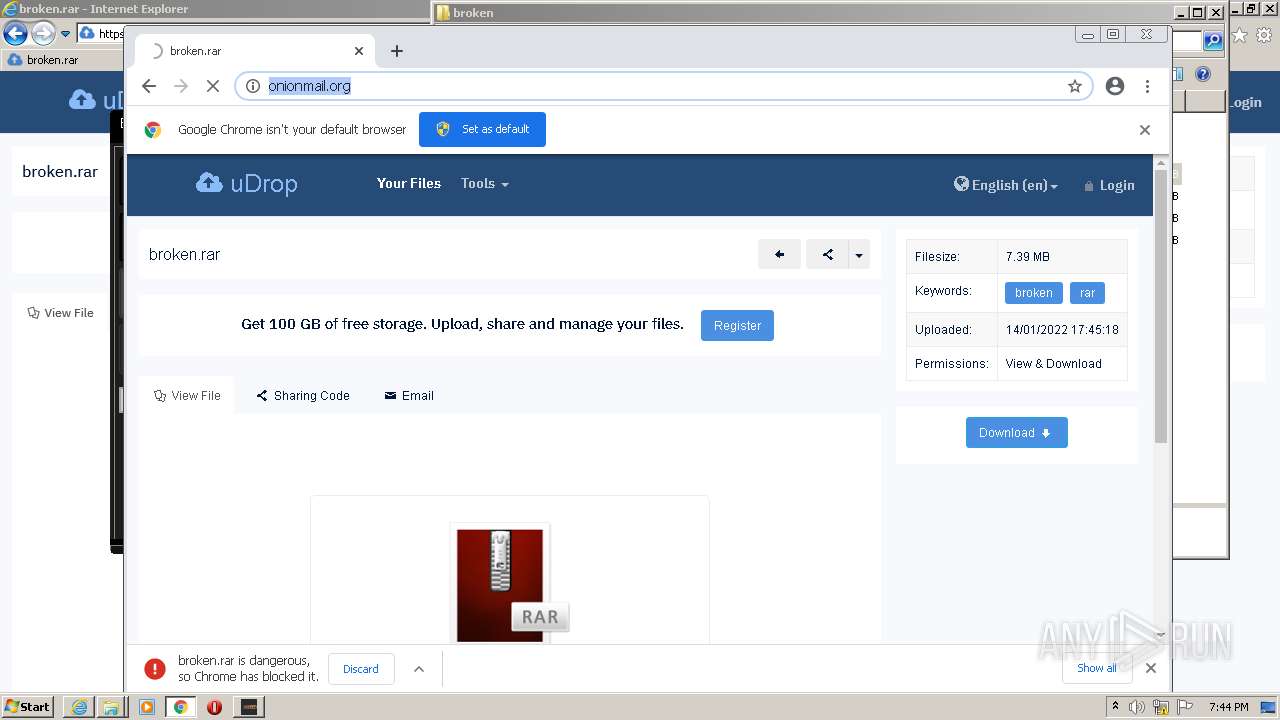
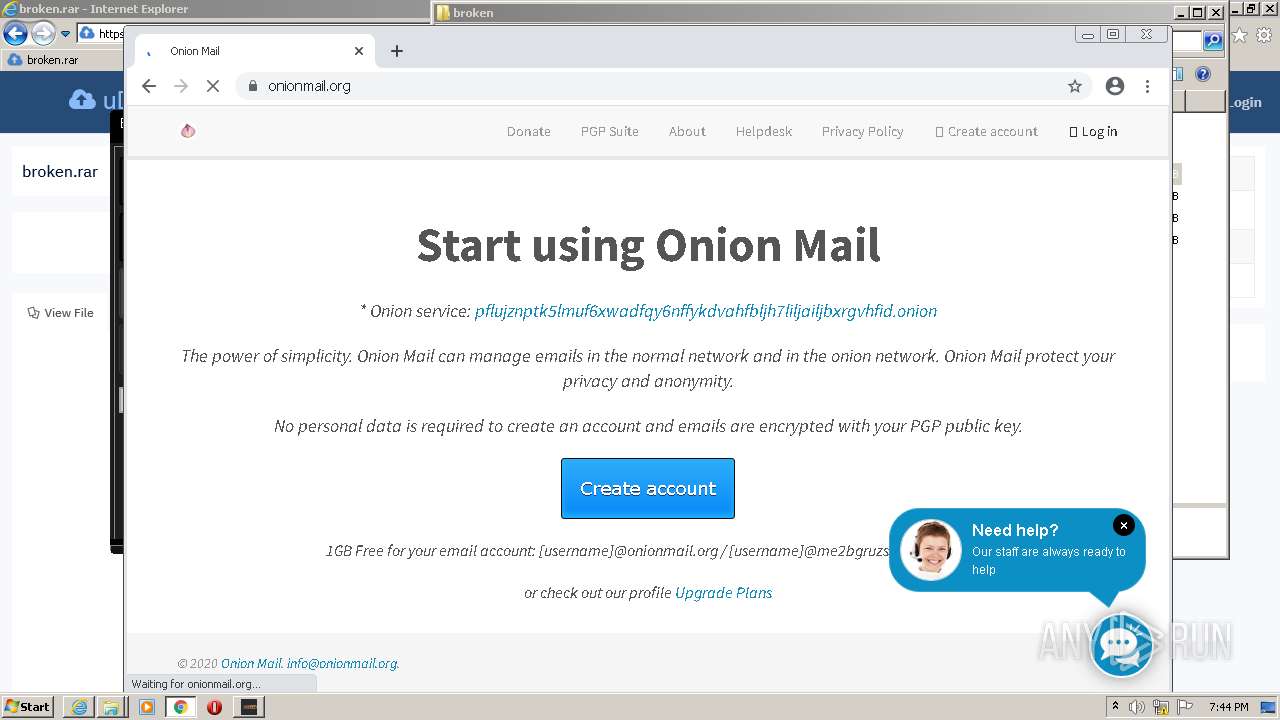
| URL: | https://www.udrop.com/6h5s/broken.rar |
| Full analysis: | https://app.any.run/tasks/a90b7b47-77f3-4dce-b6a3-654db9a24f84 |
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 19:42:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 09DF7BC55A422C5C4FF0E20BE0CF08AE |
| SHA1: | 21930A763C8DCDB6F20F9E46FB2653DD2B80DF3E |
| SHA256: | 170FD4943C30B0ACADE916287D79B60FDBF21E7929D3B7295220FCF4D4C8A6A7 |
| SSDEEP: | 3:N8DSLzGTKh9v/On:2OLzKKh9v/O |
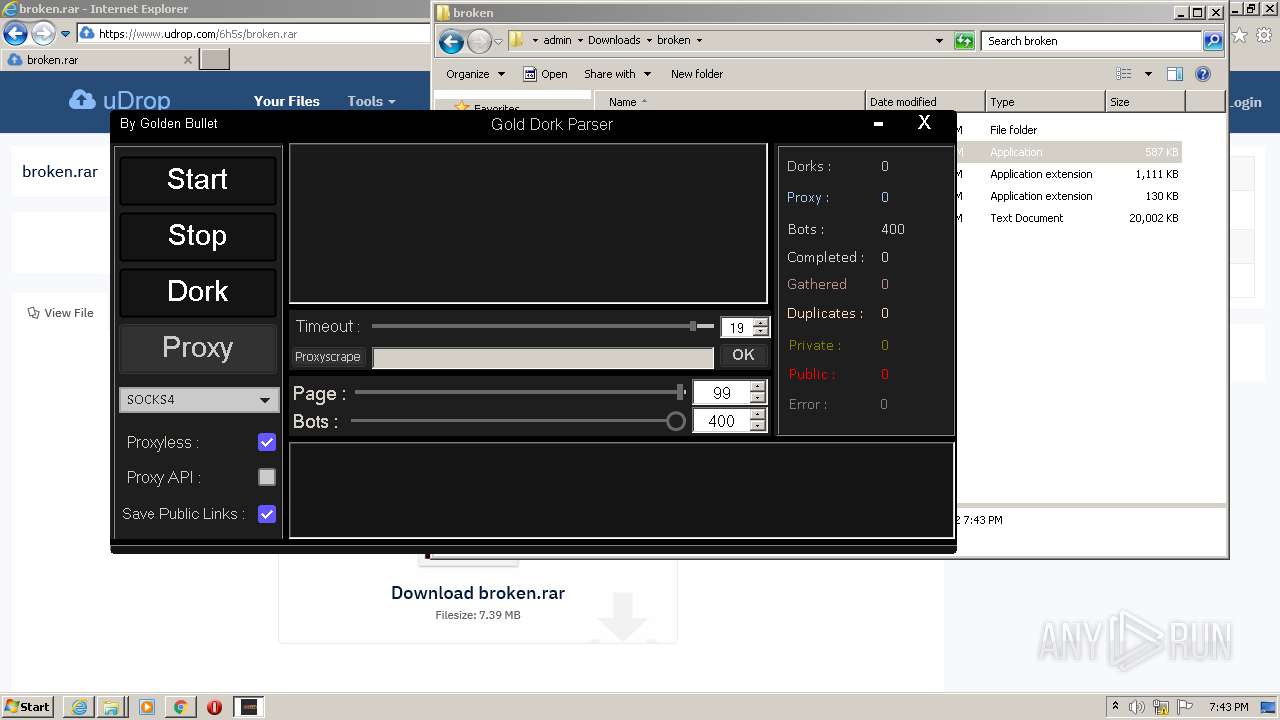
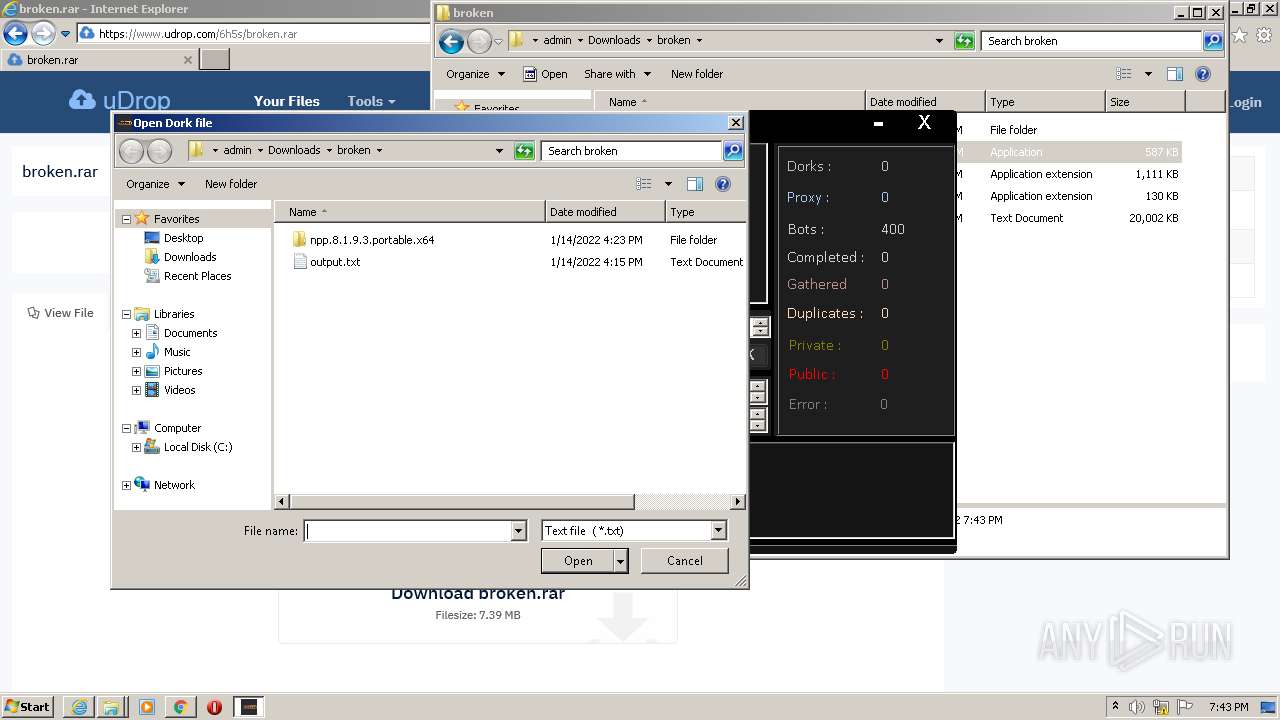
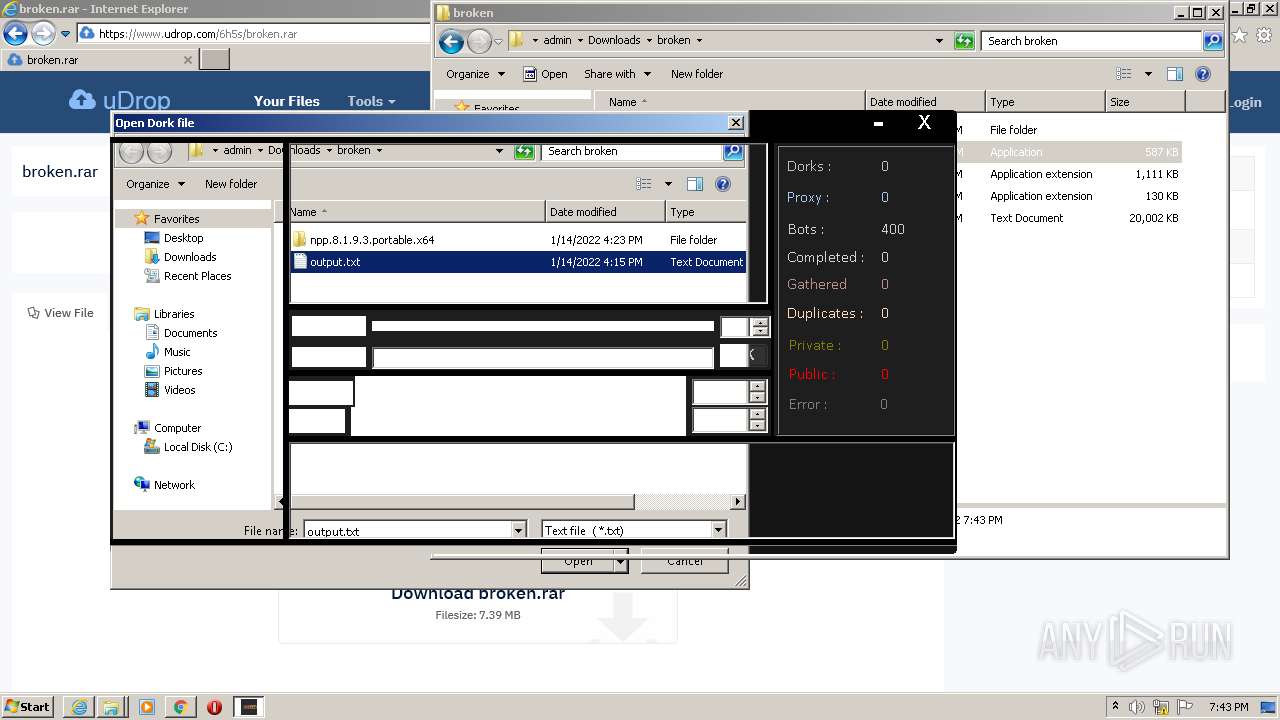
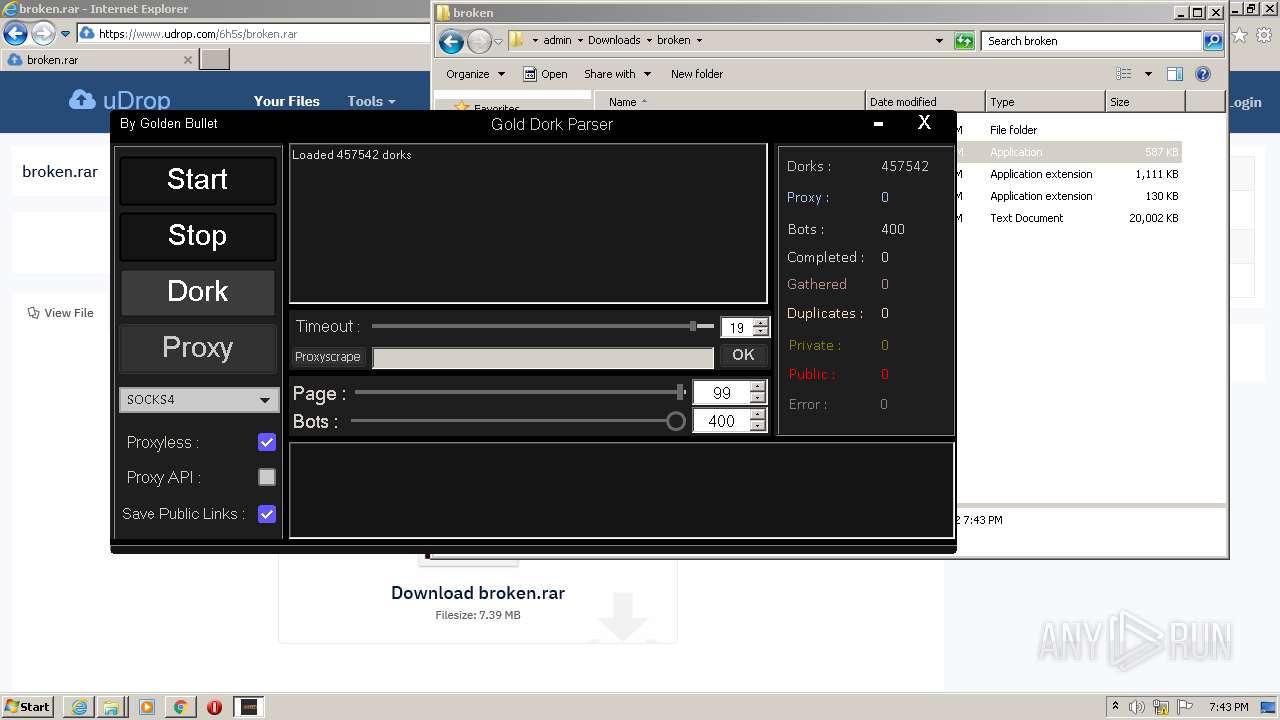
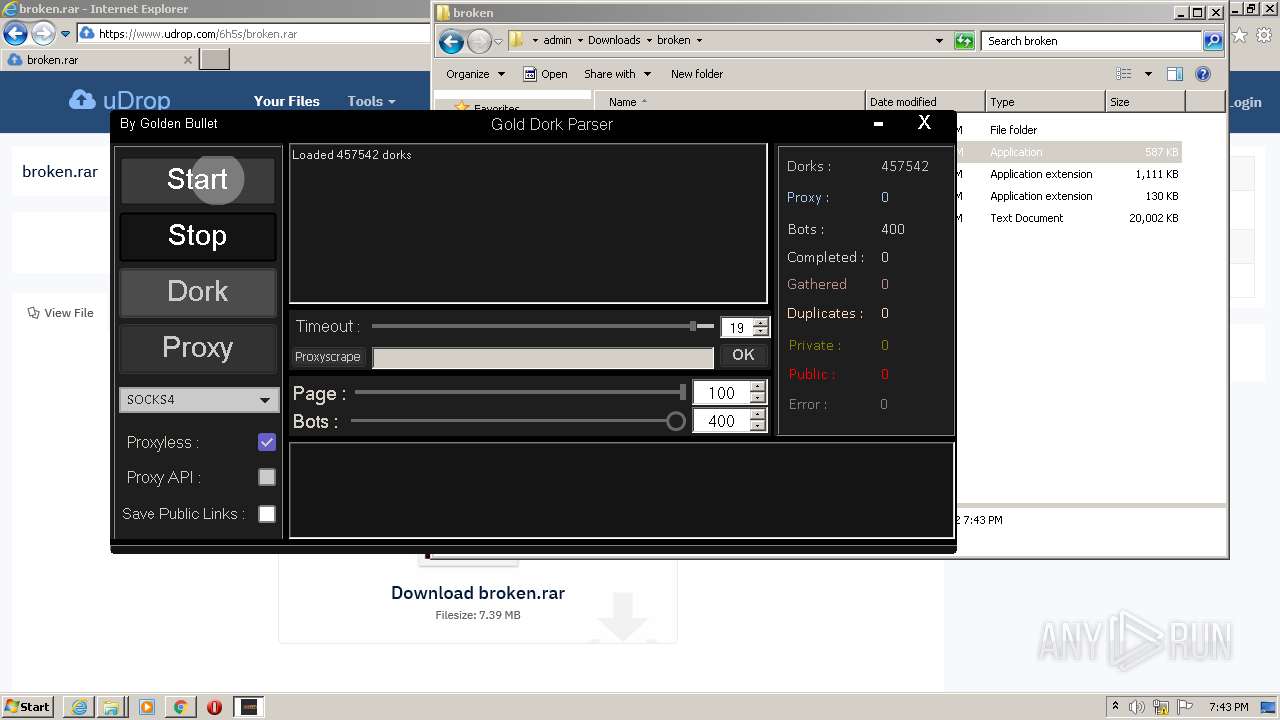
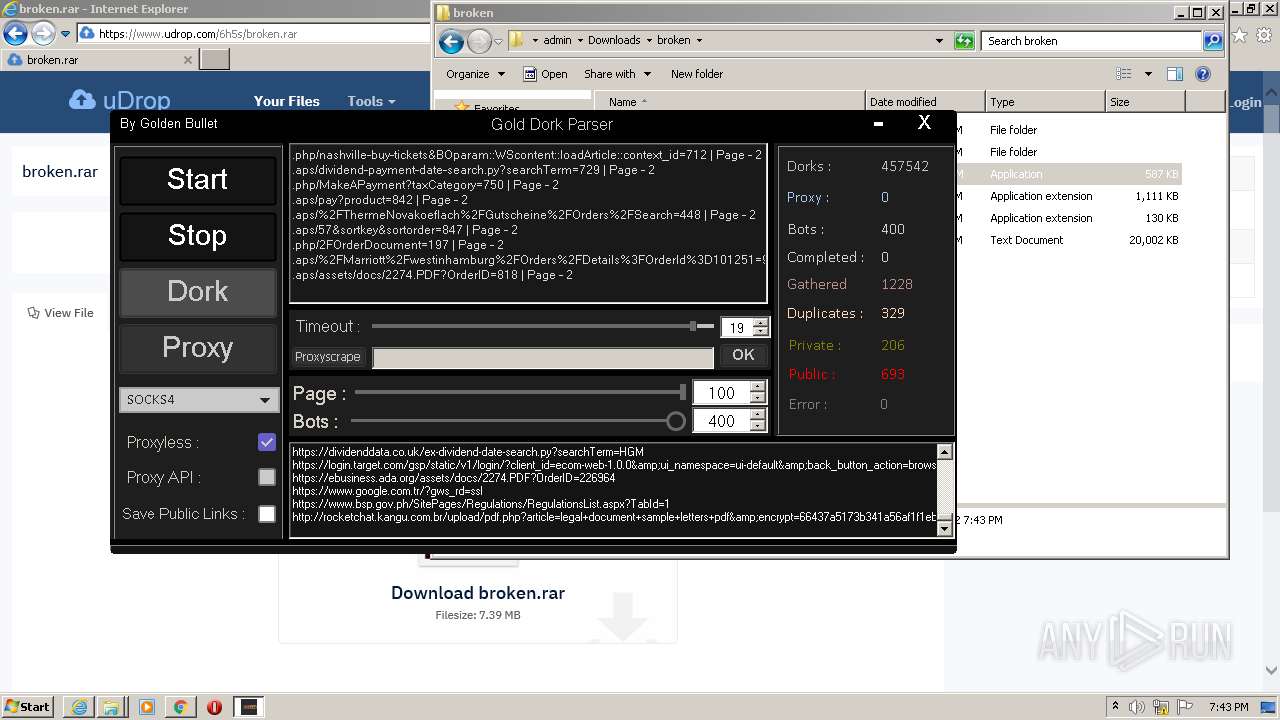
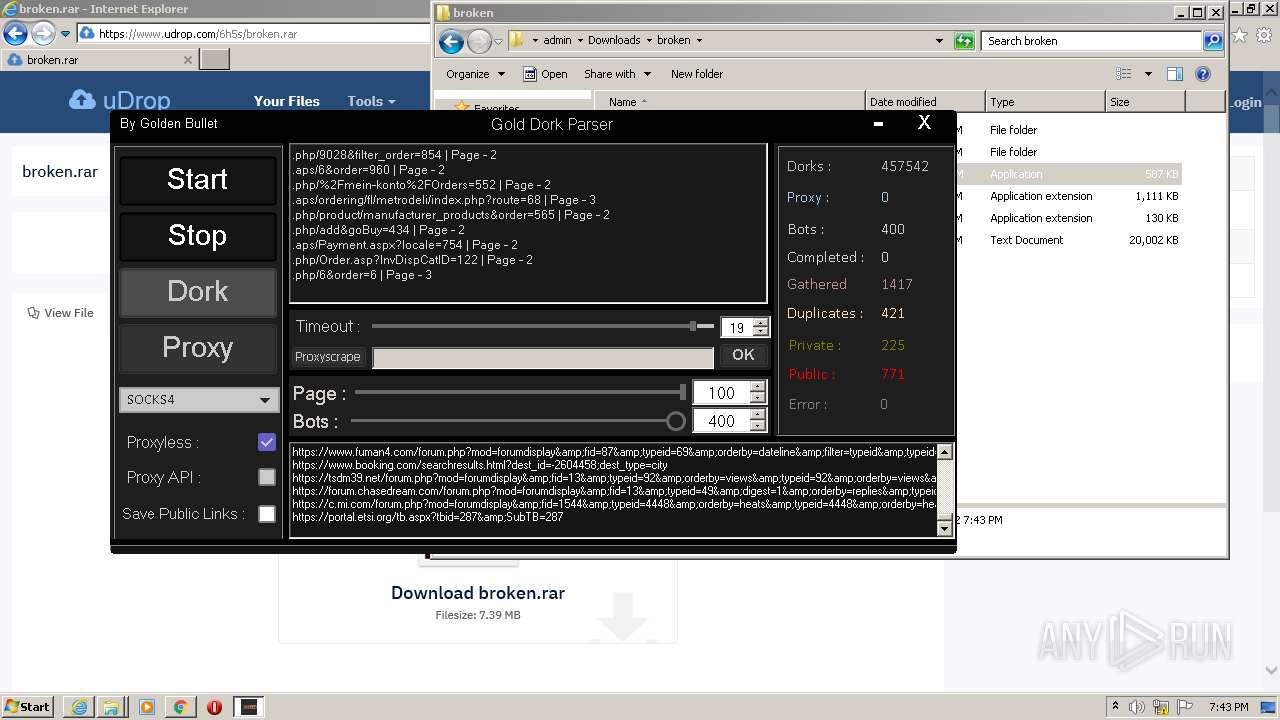
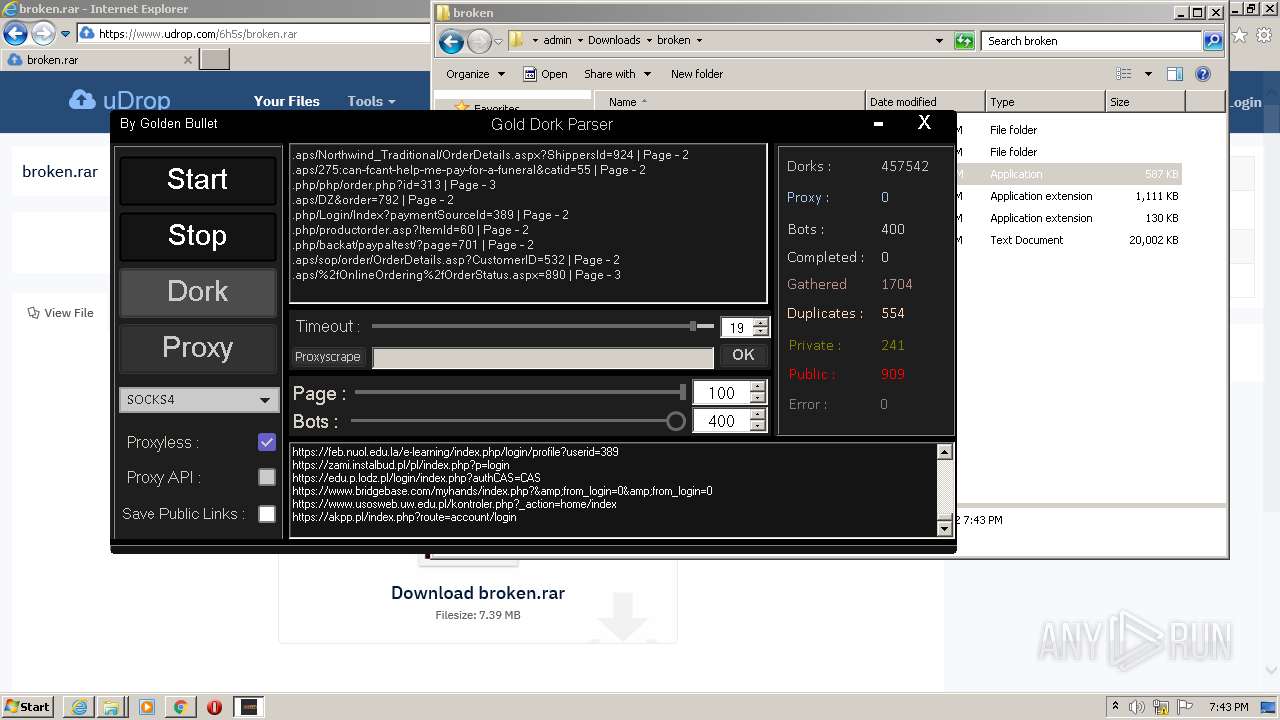
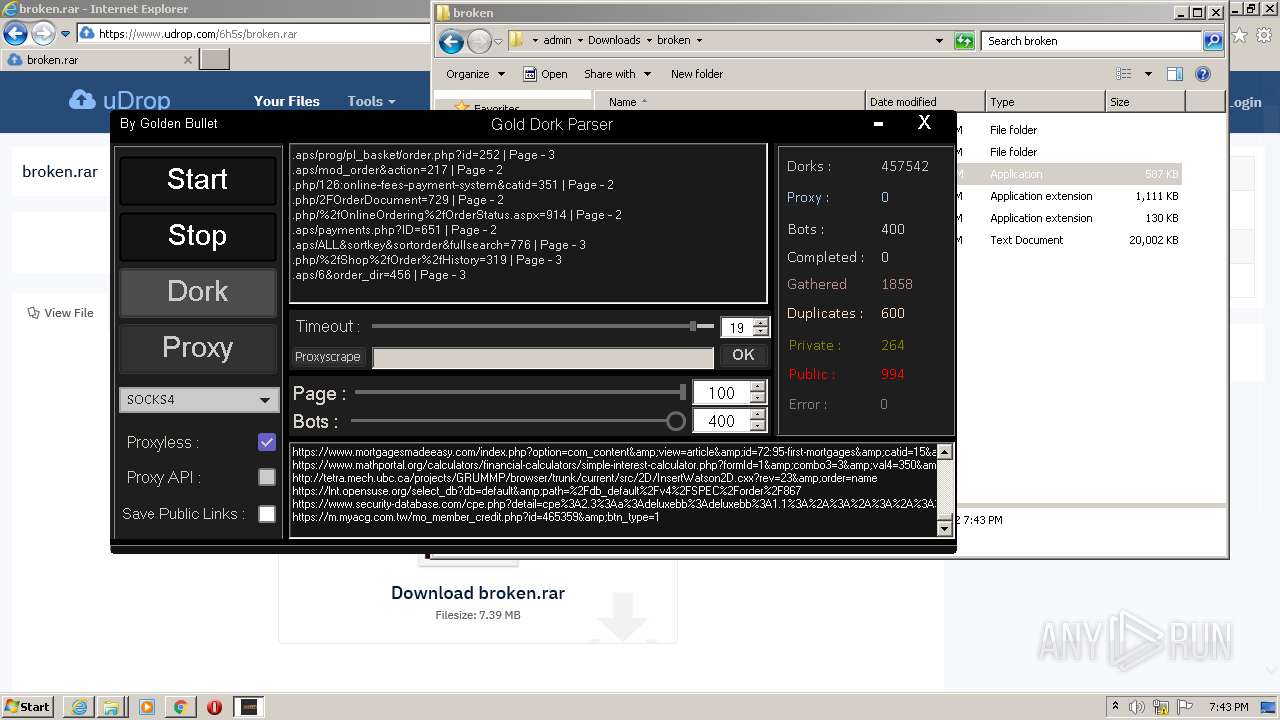
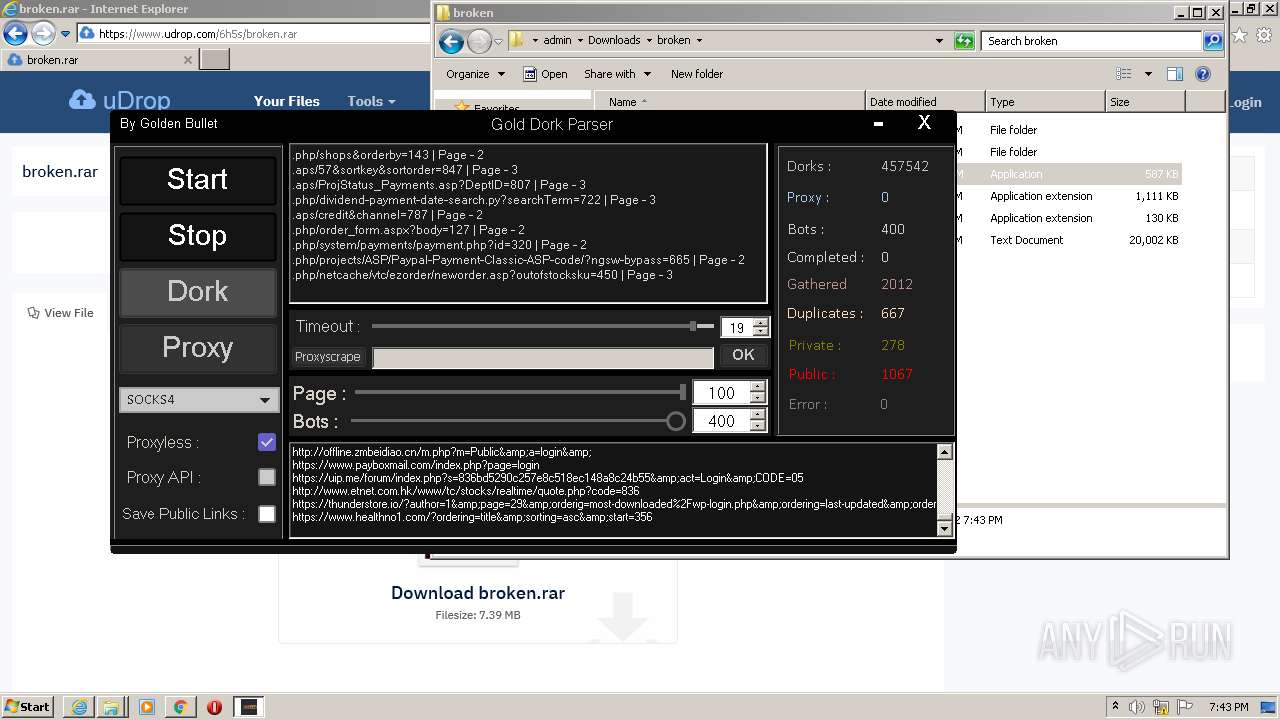
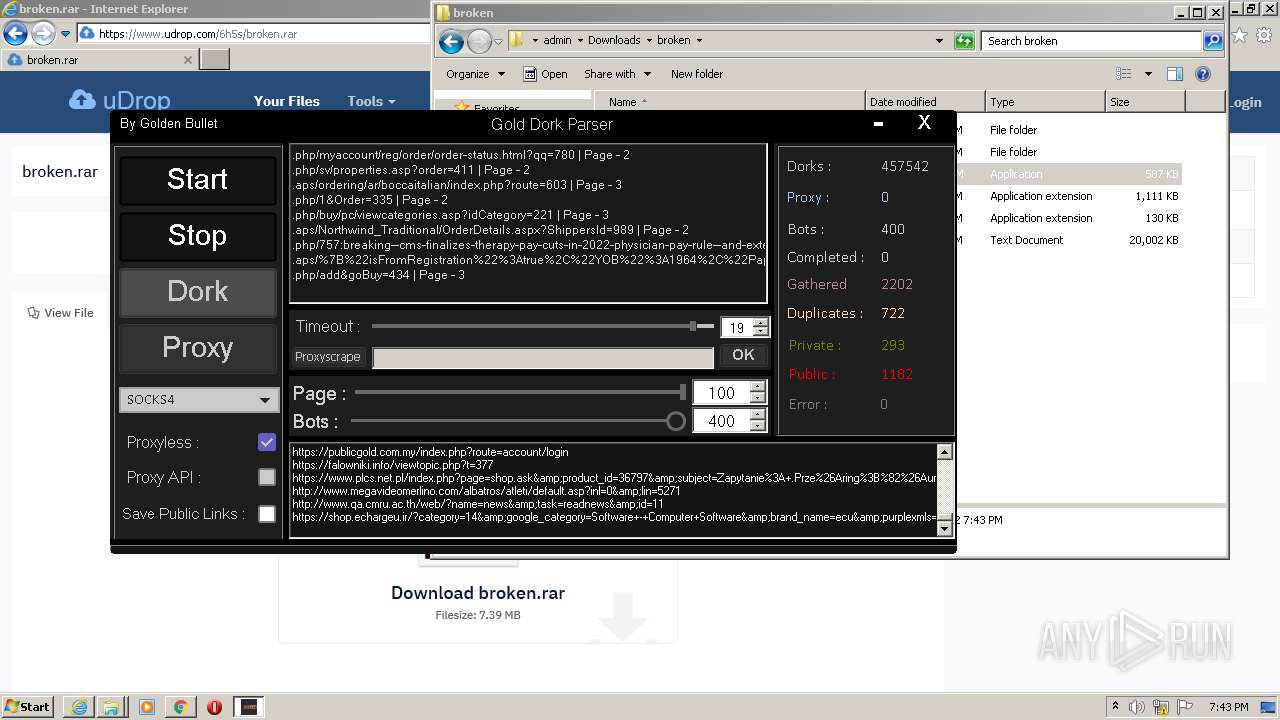
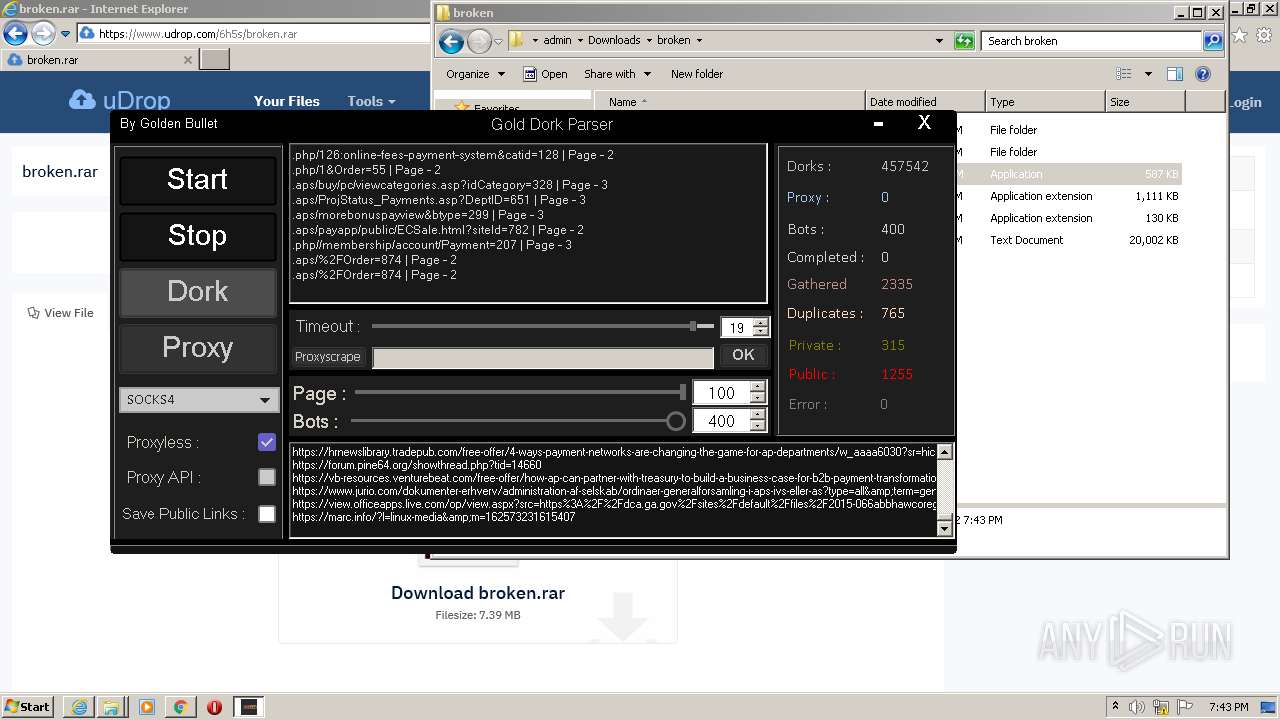
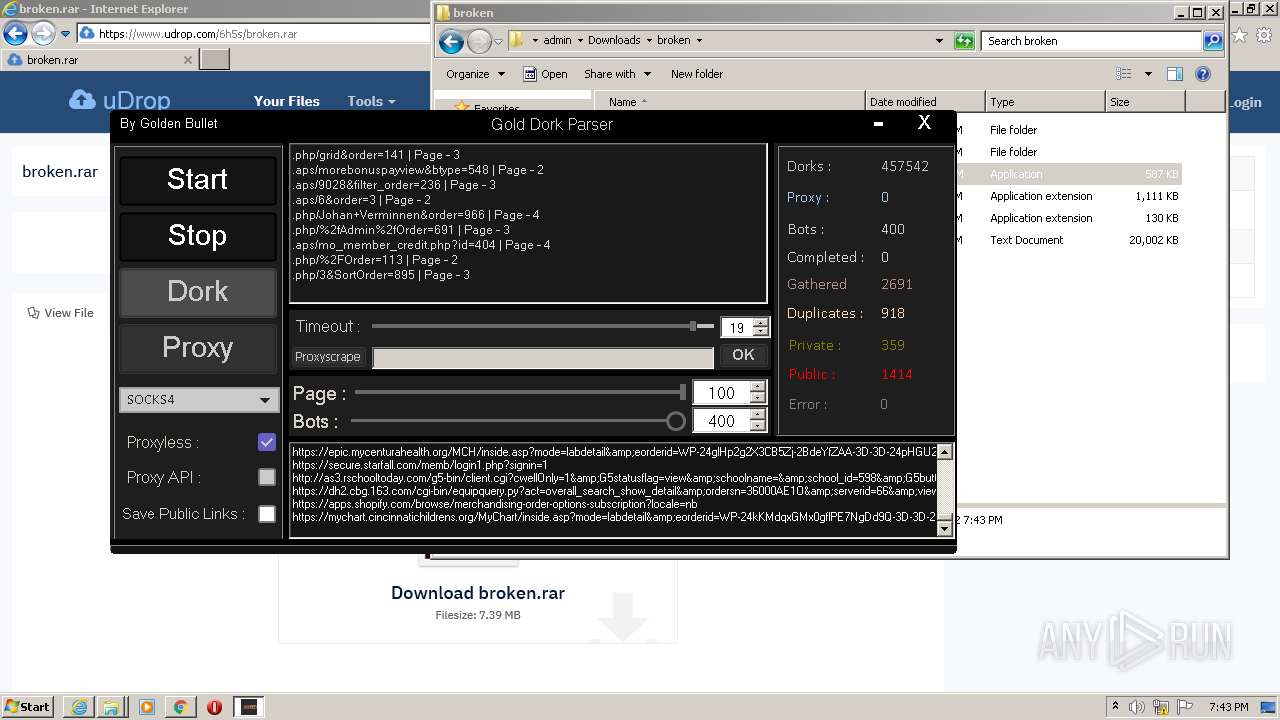
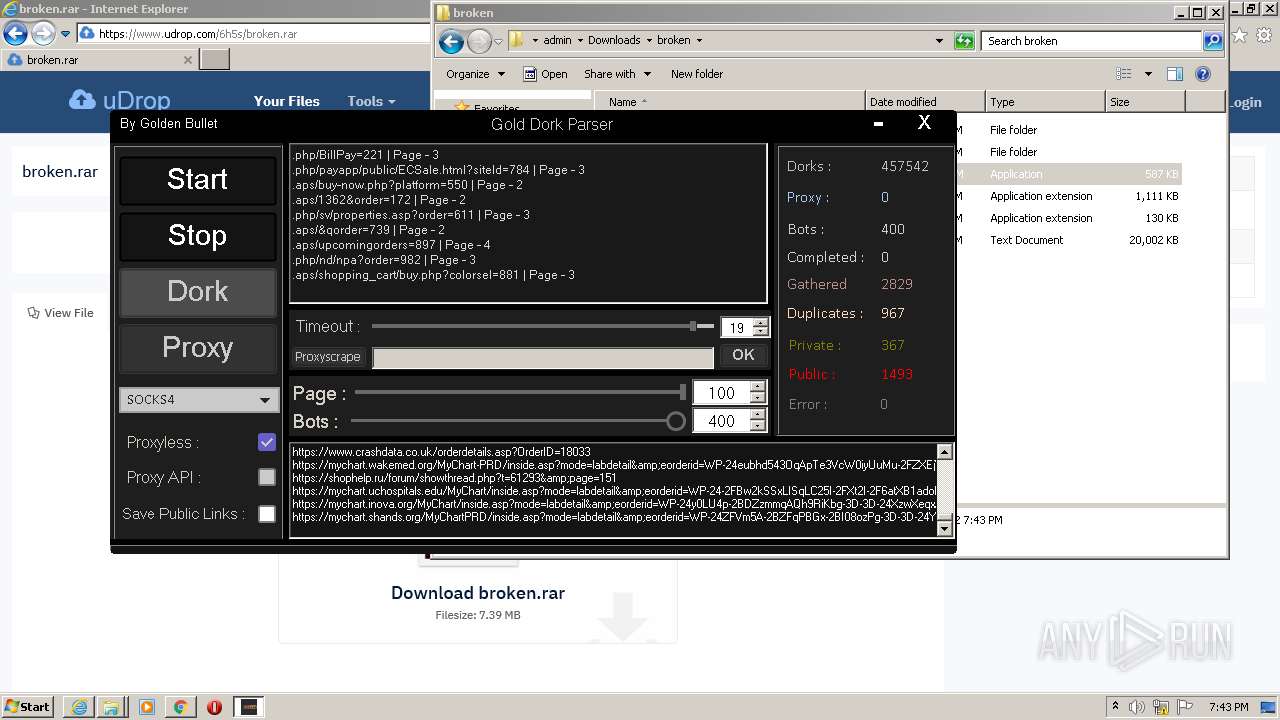
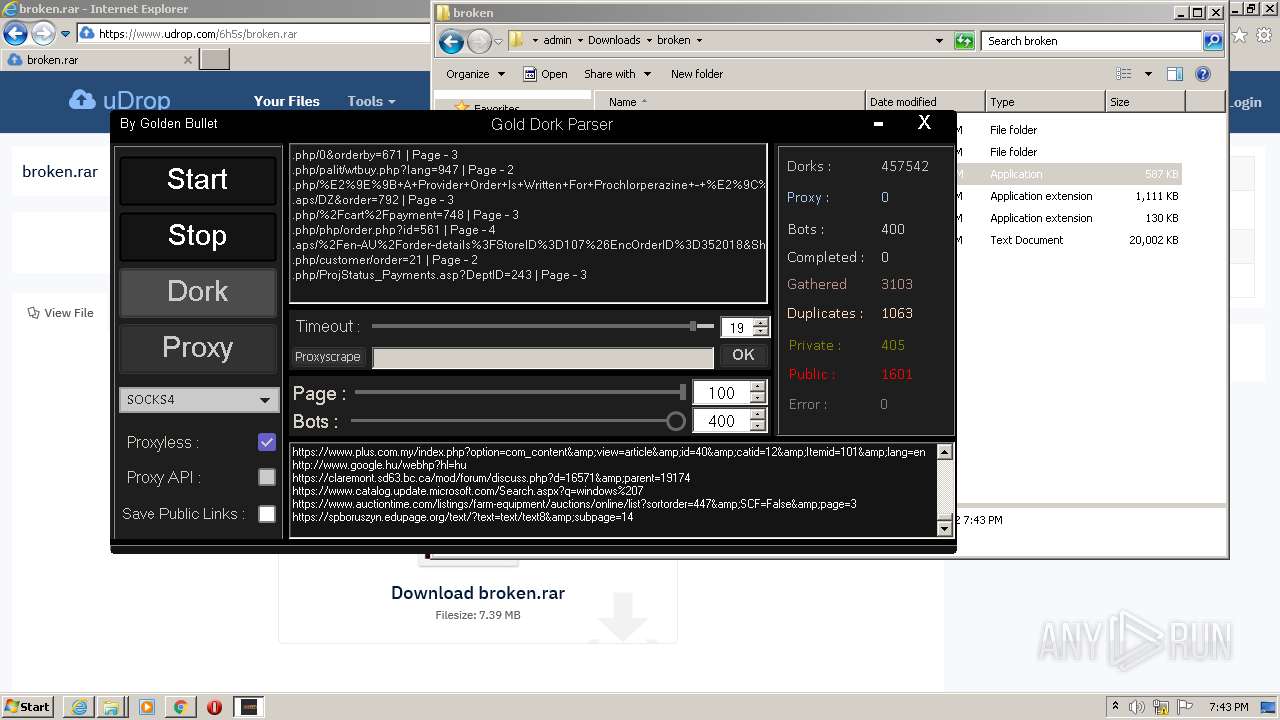
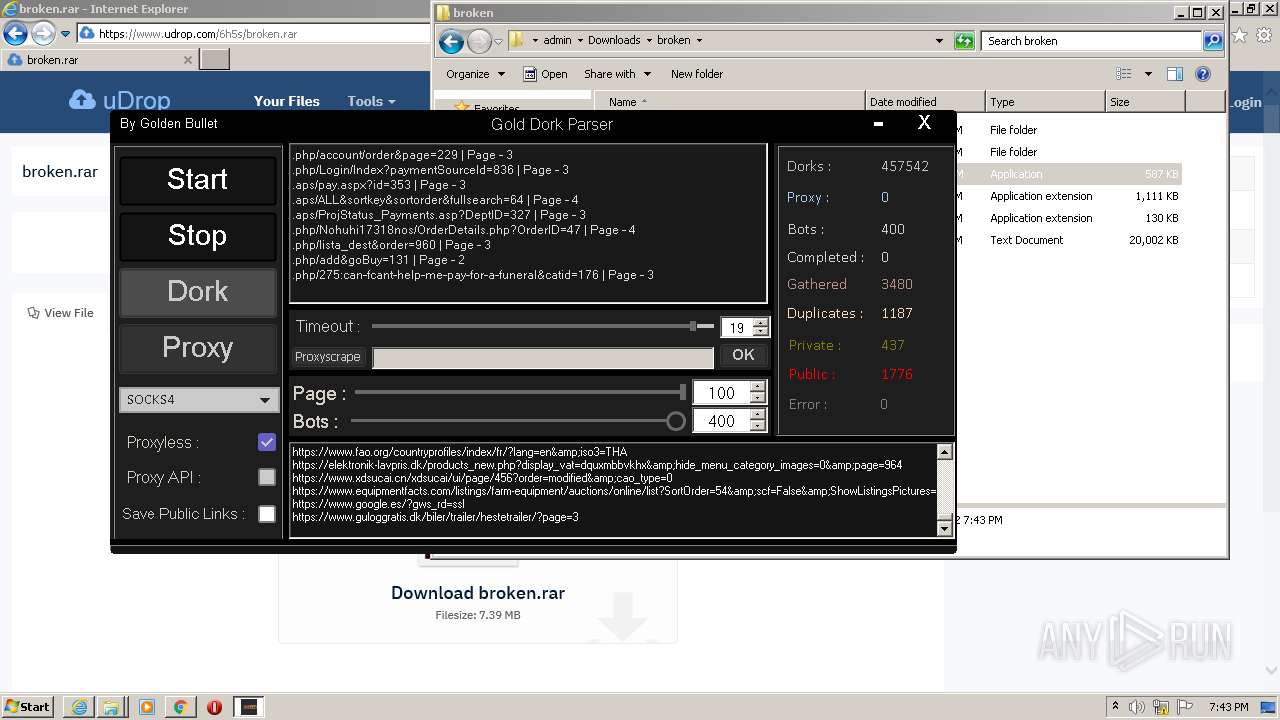
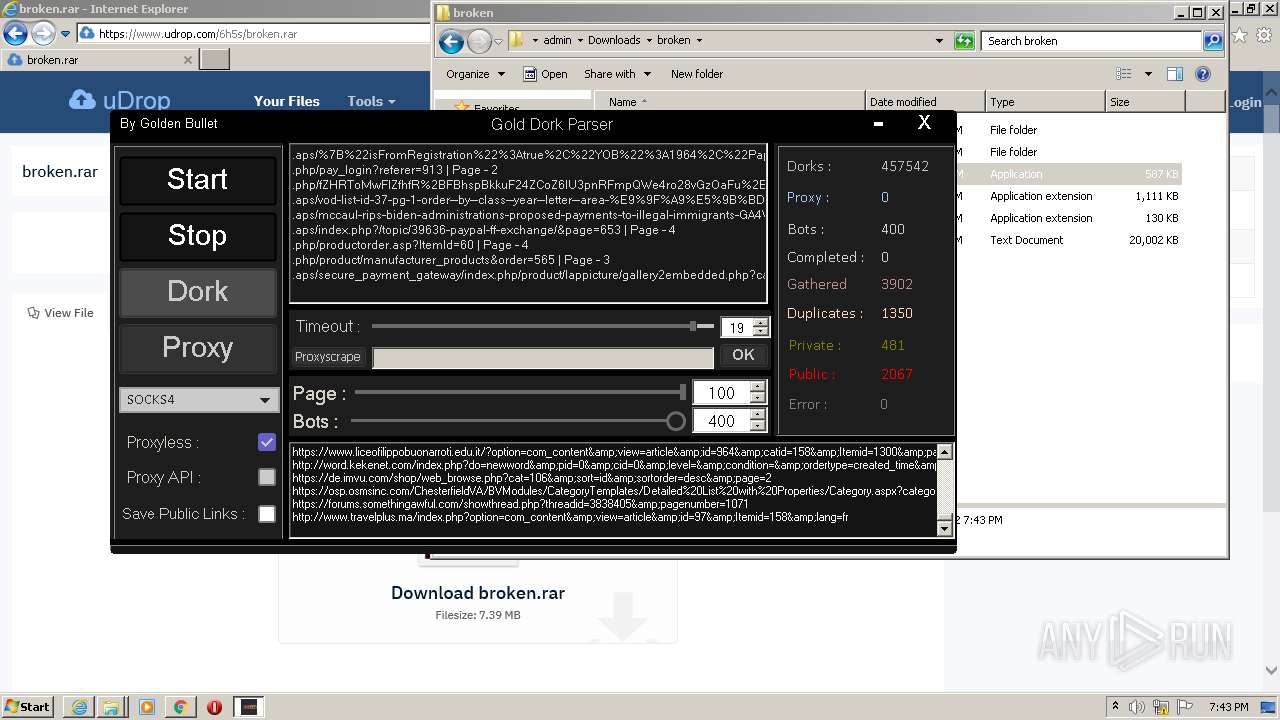
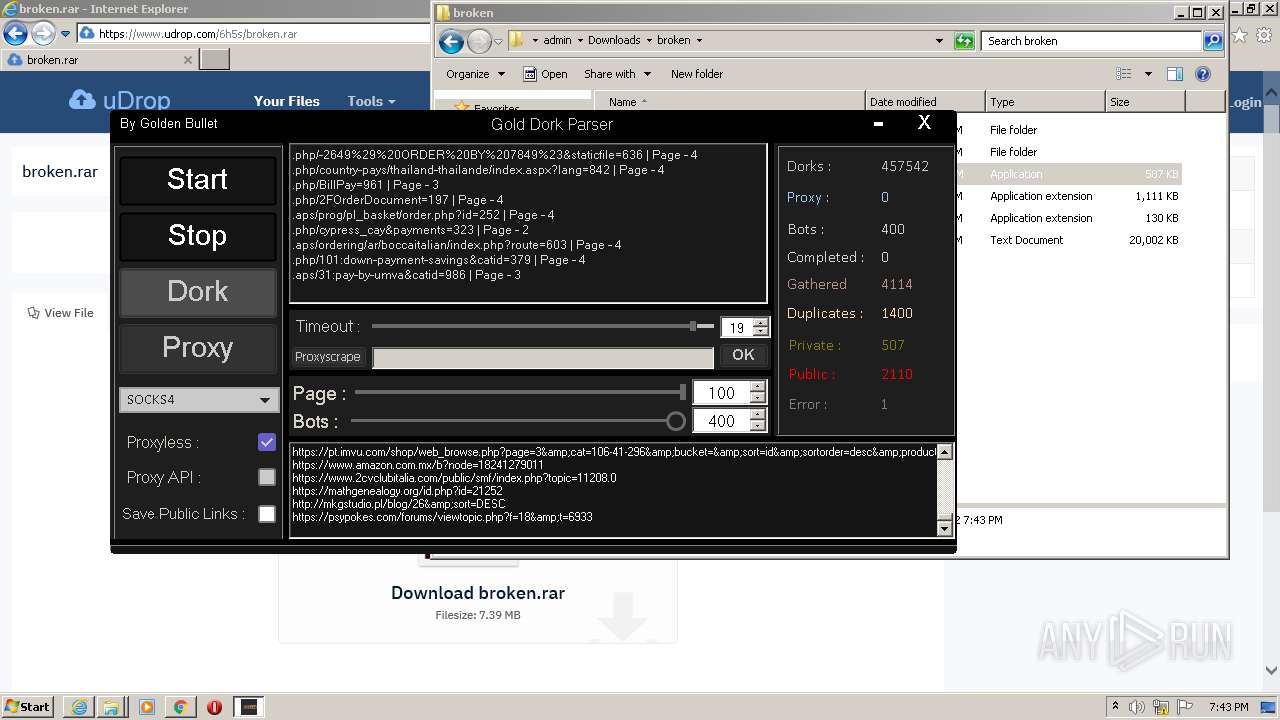
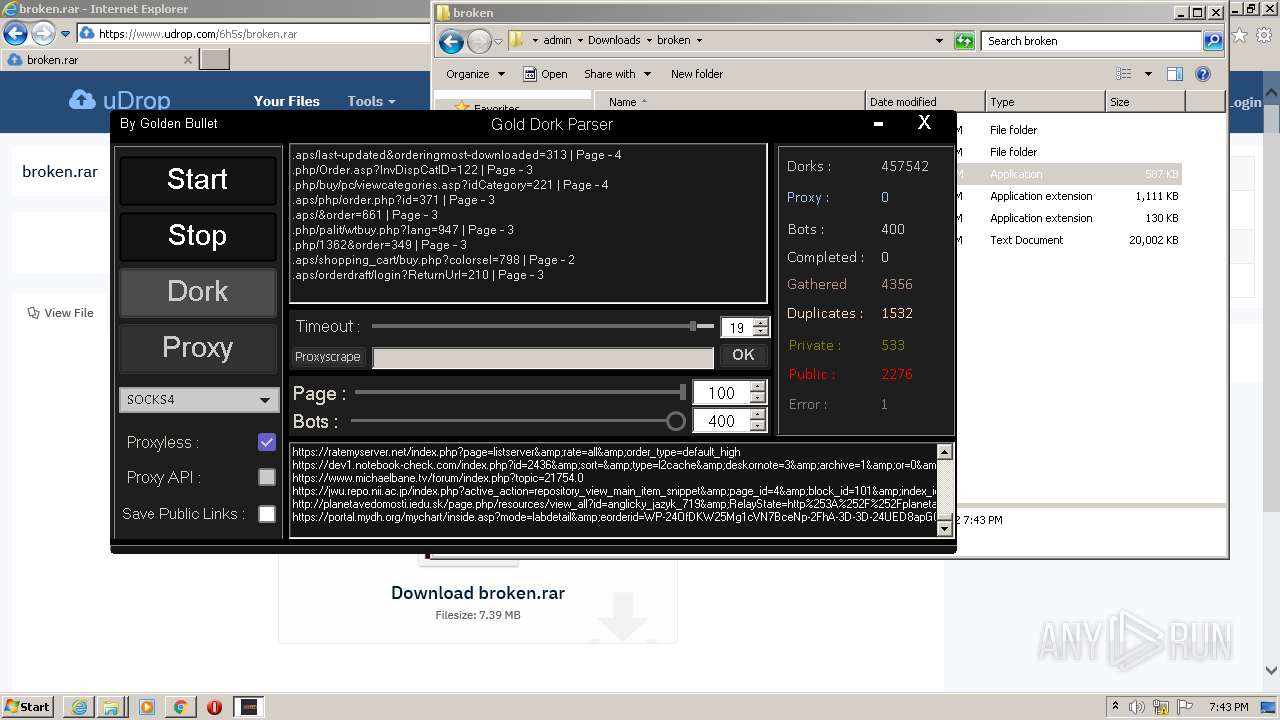
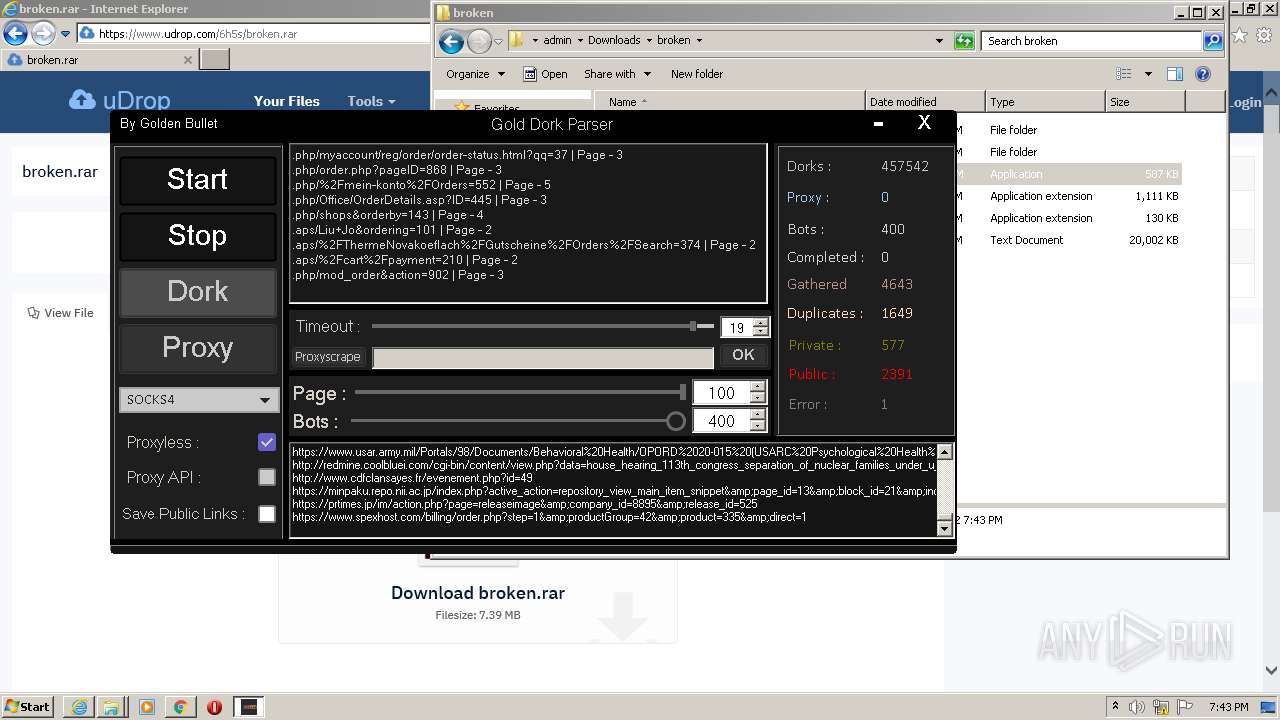
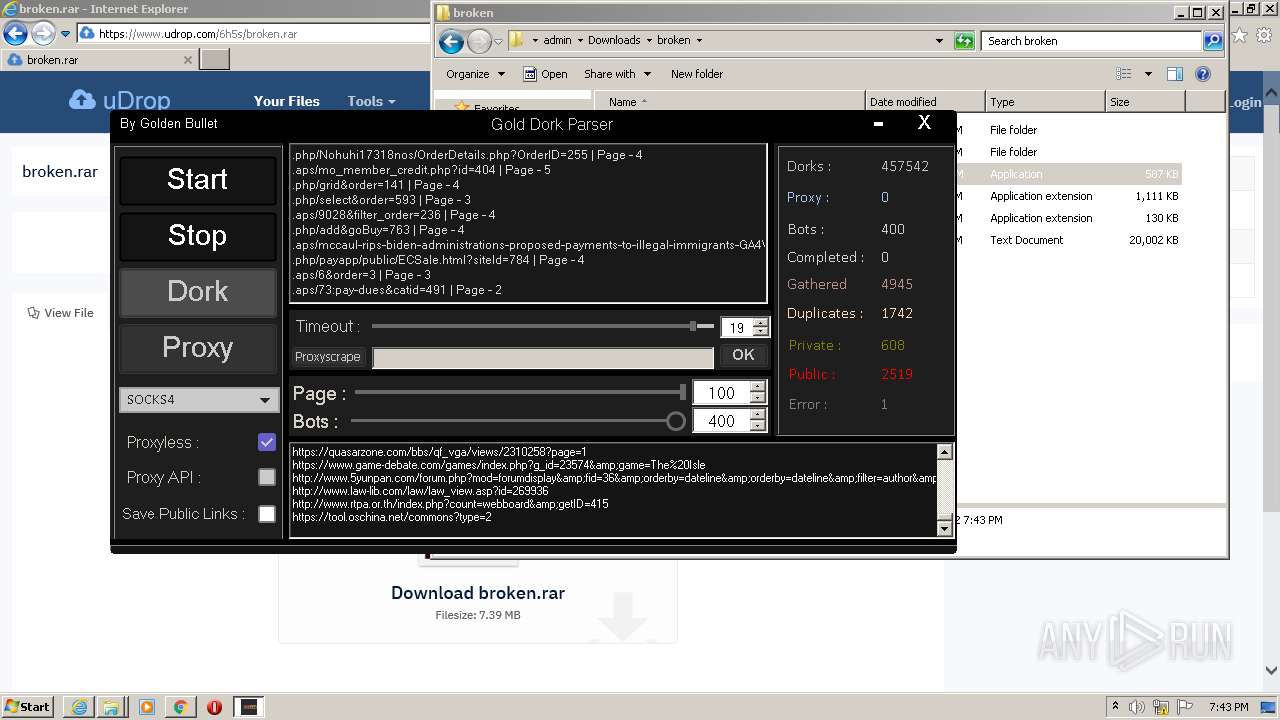
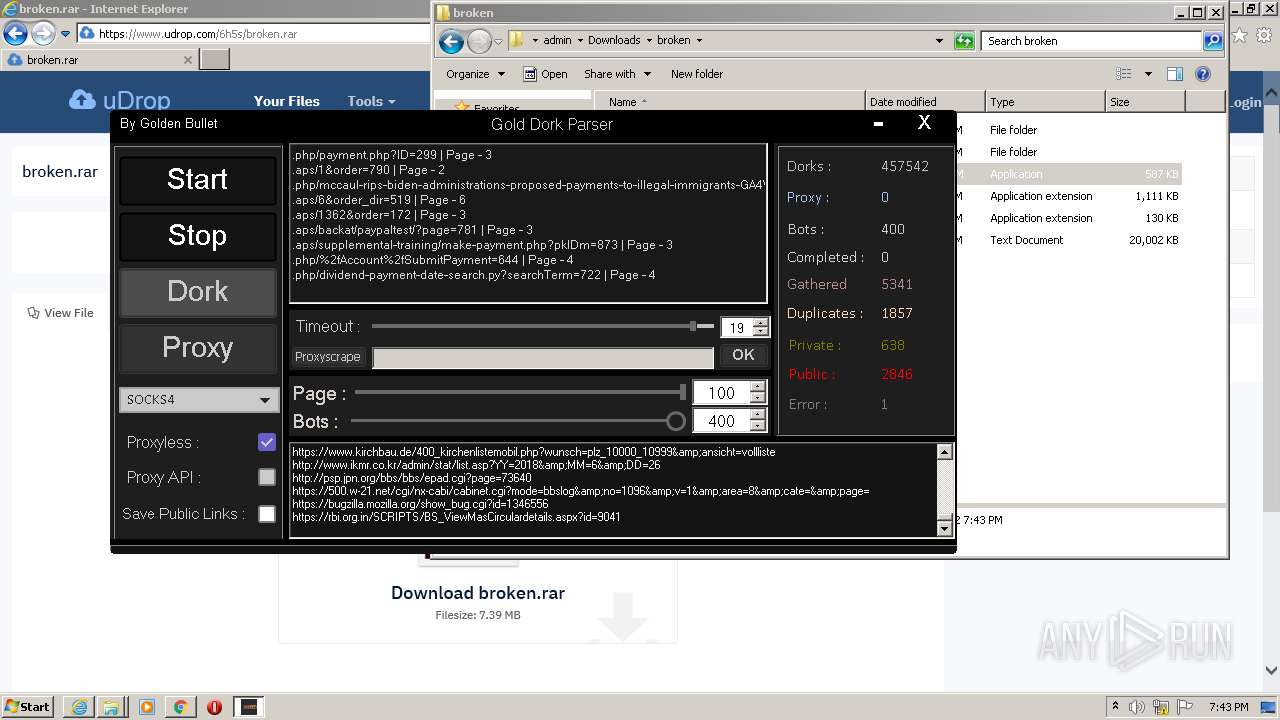
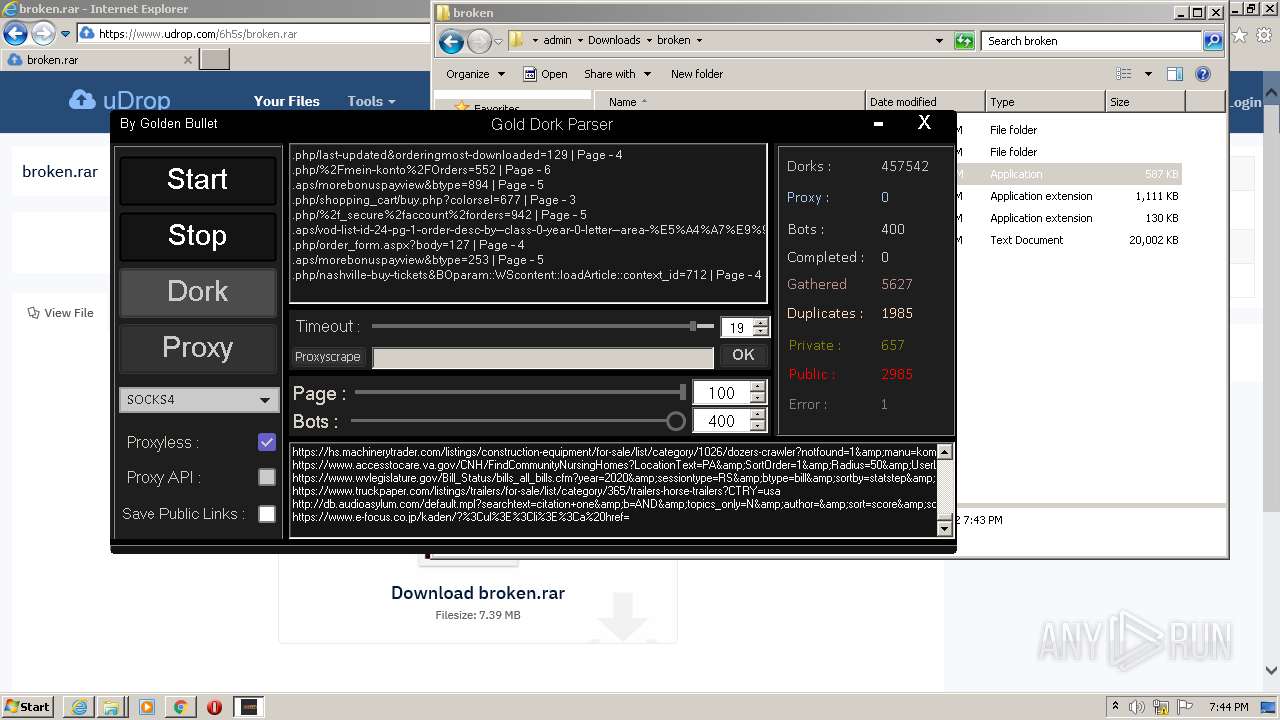
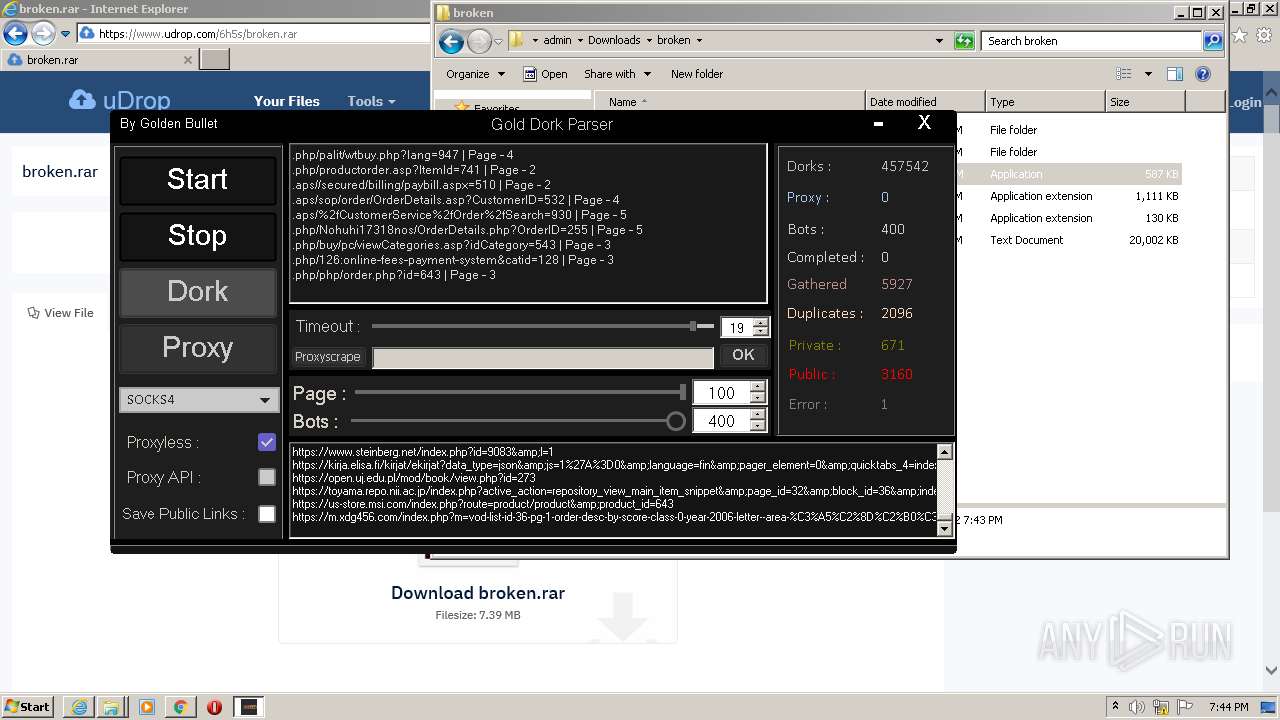
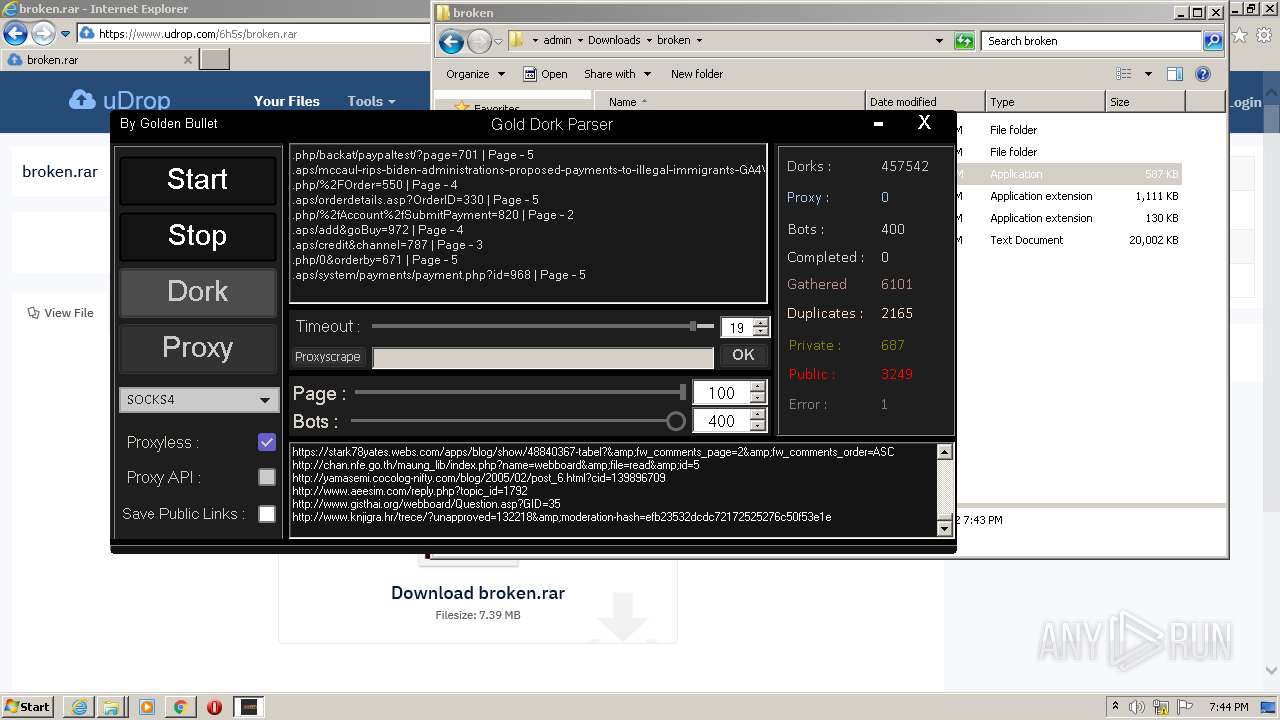
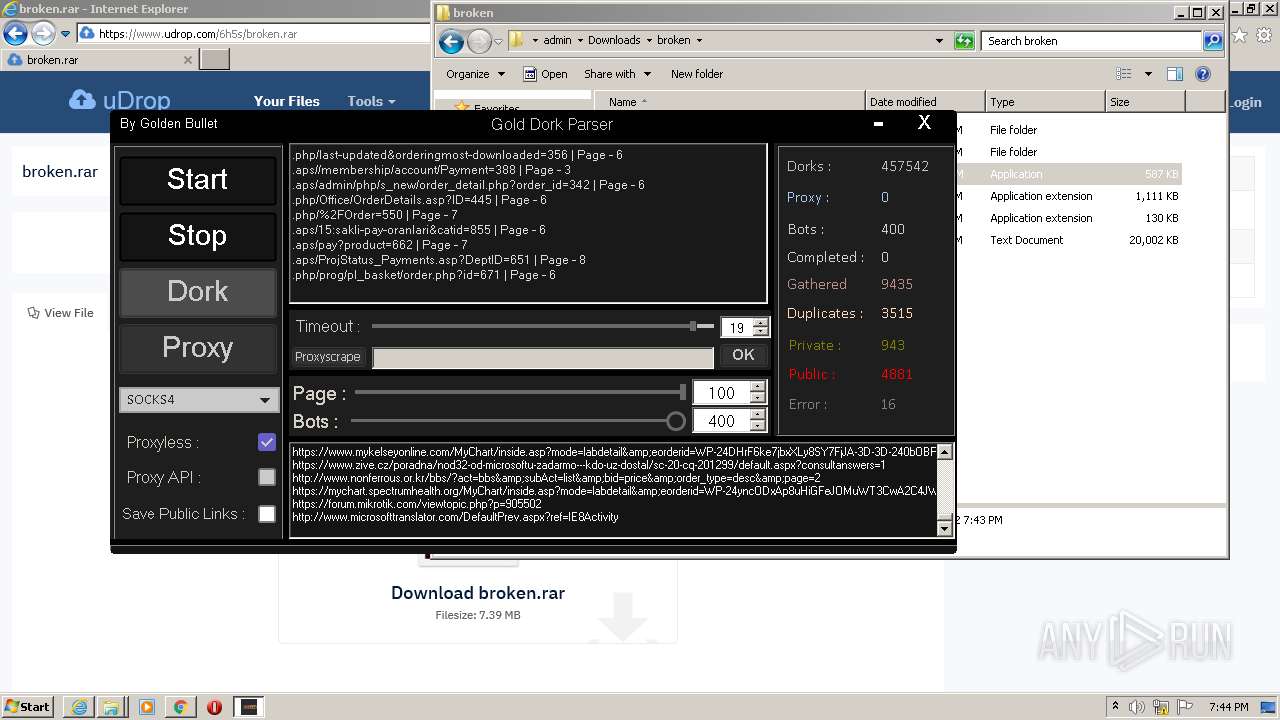
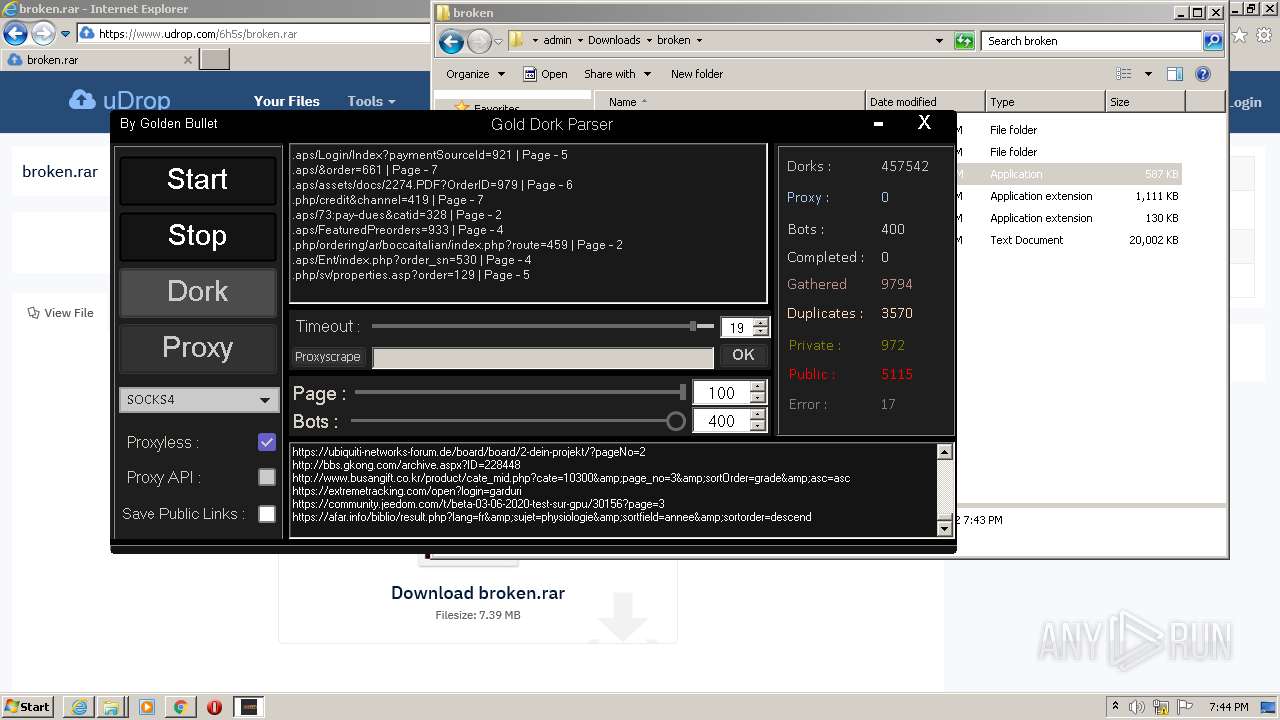
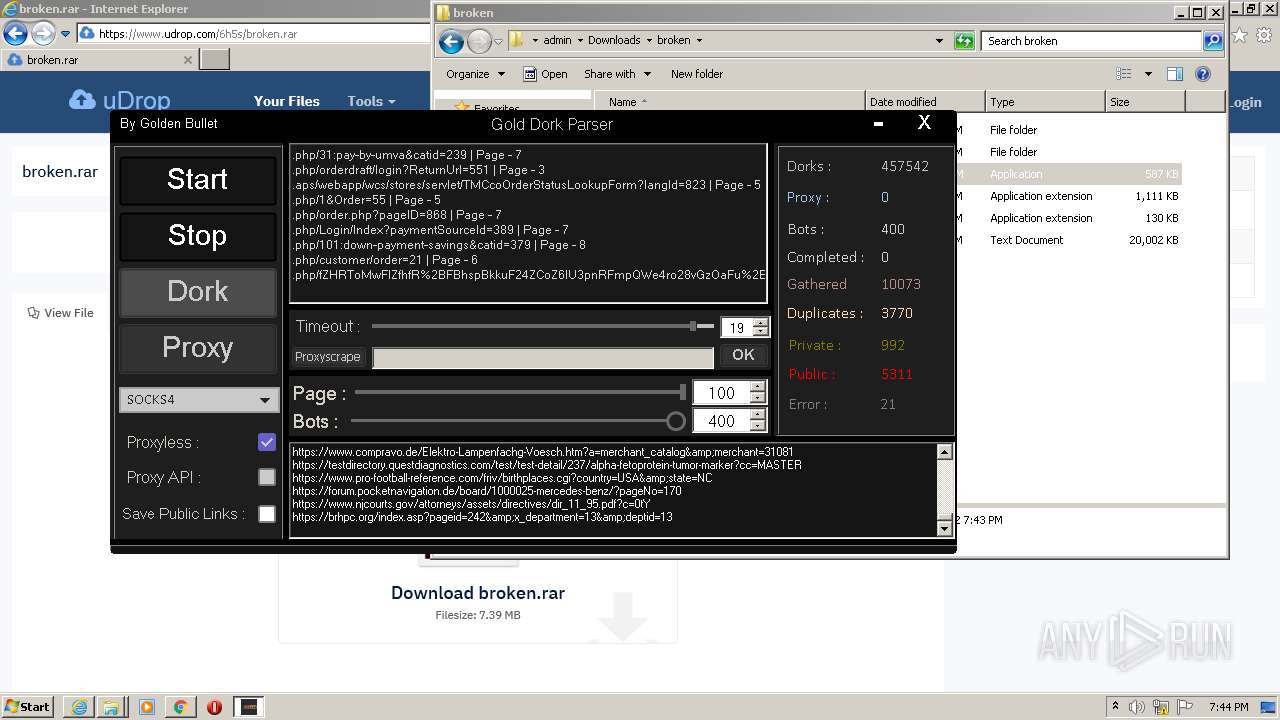
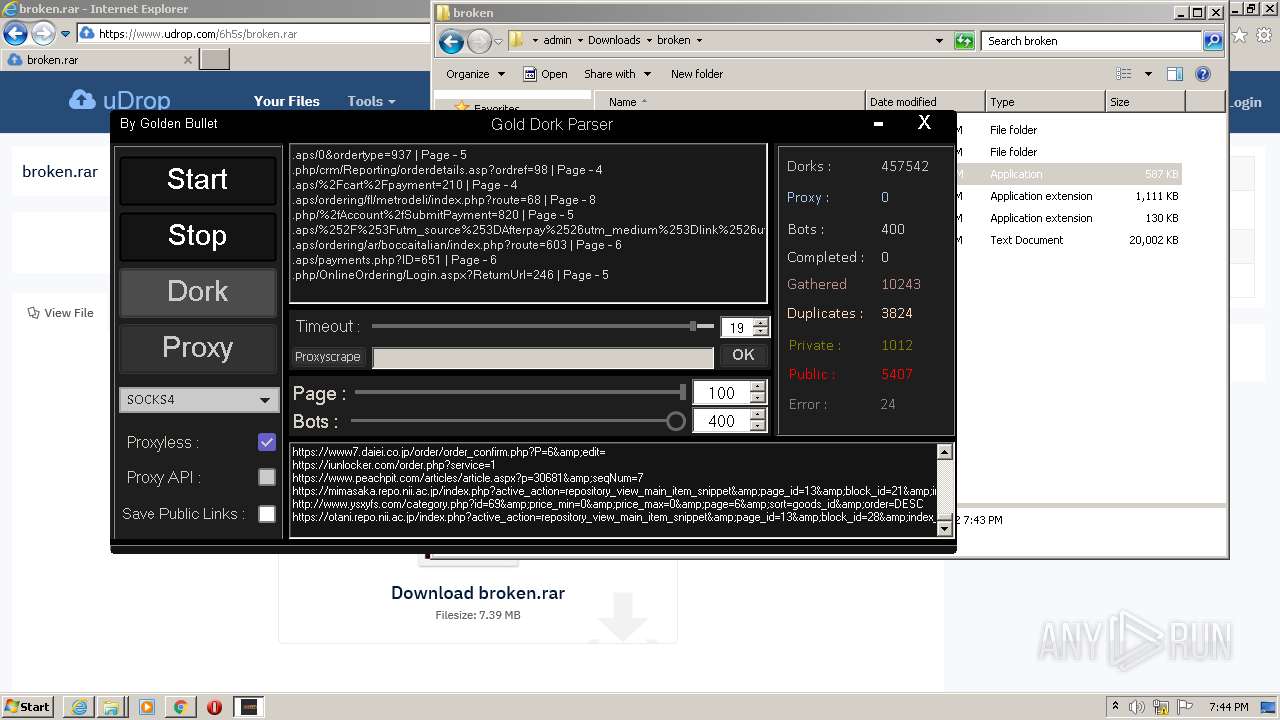
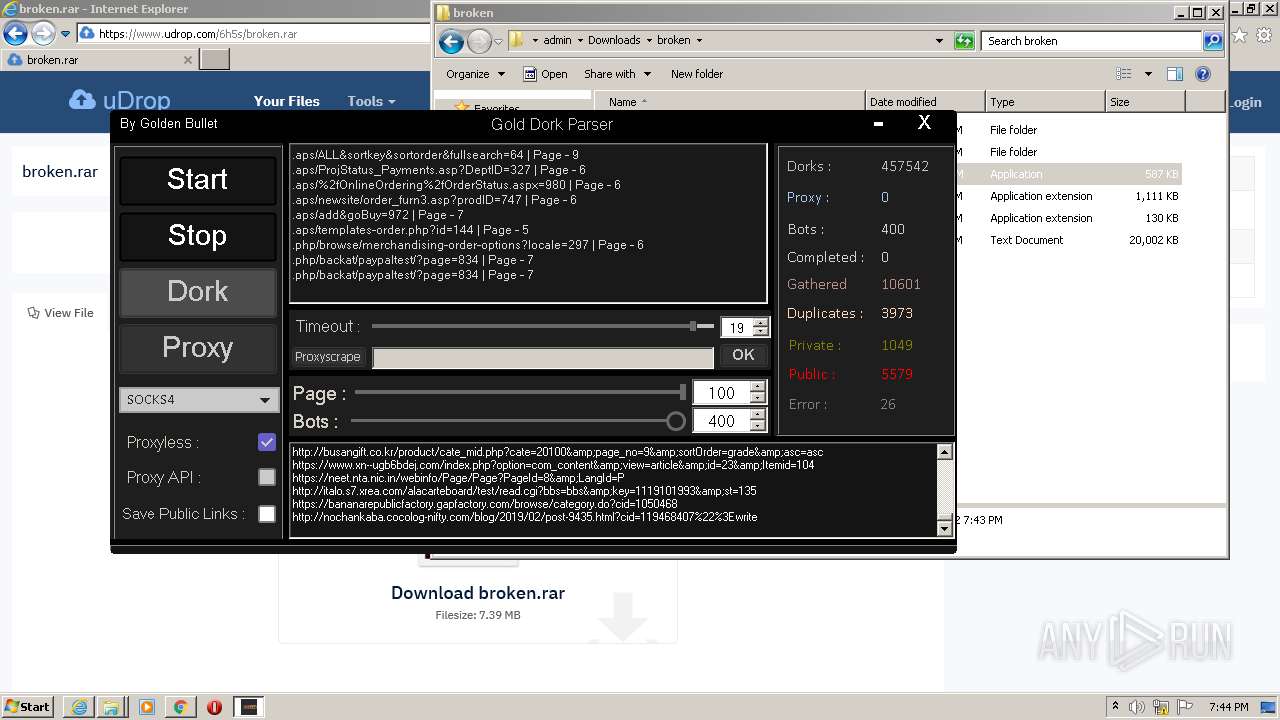
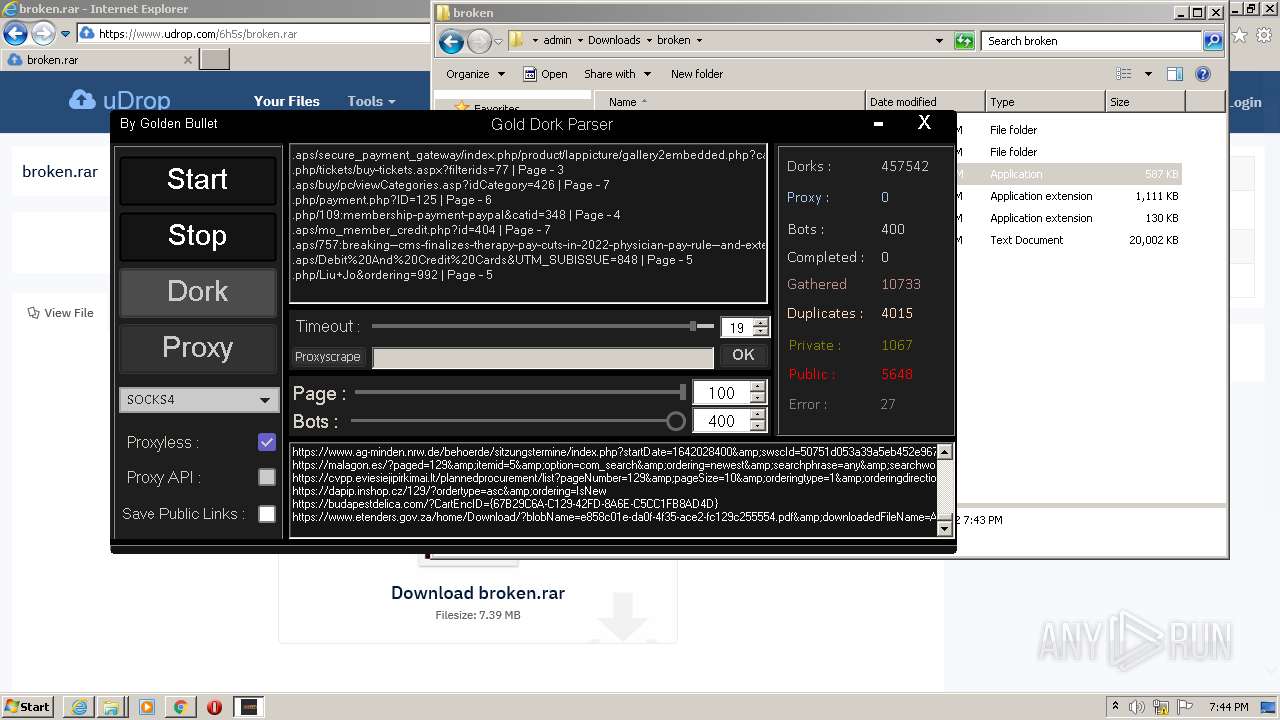
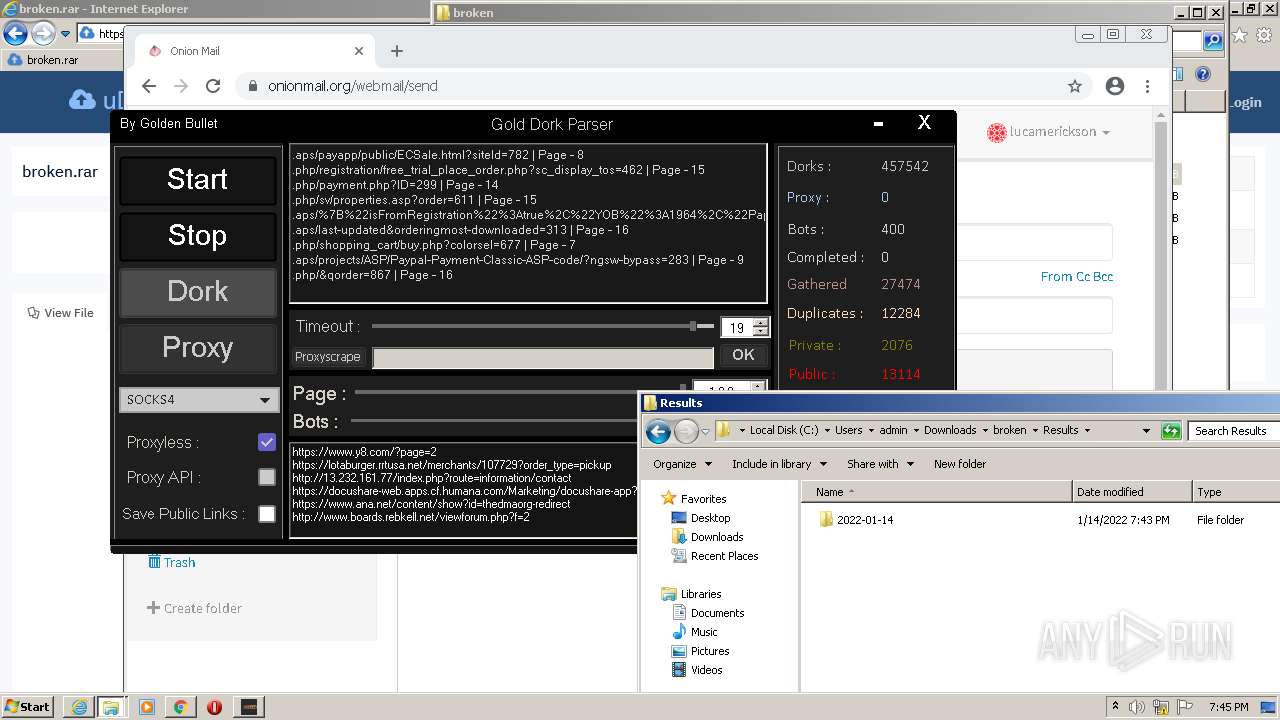
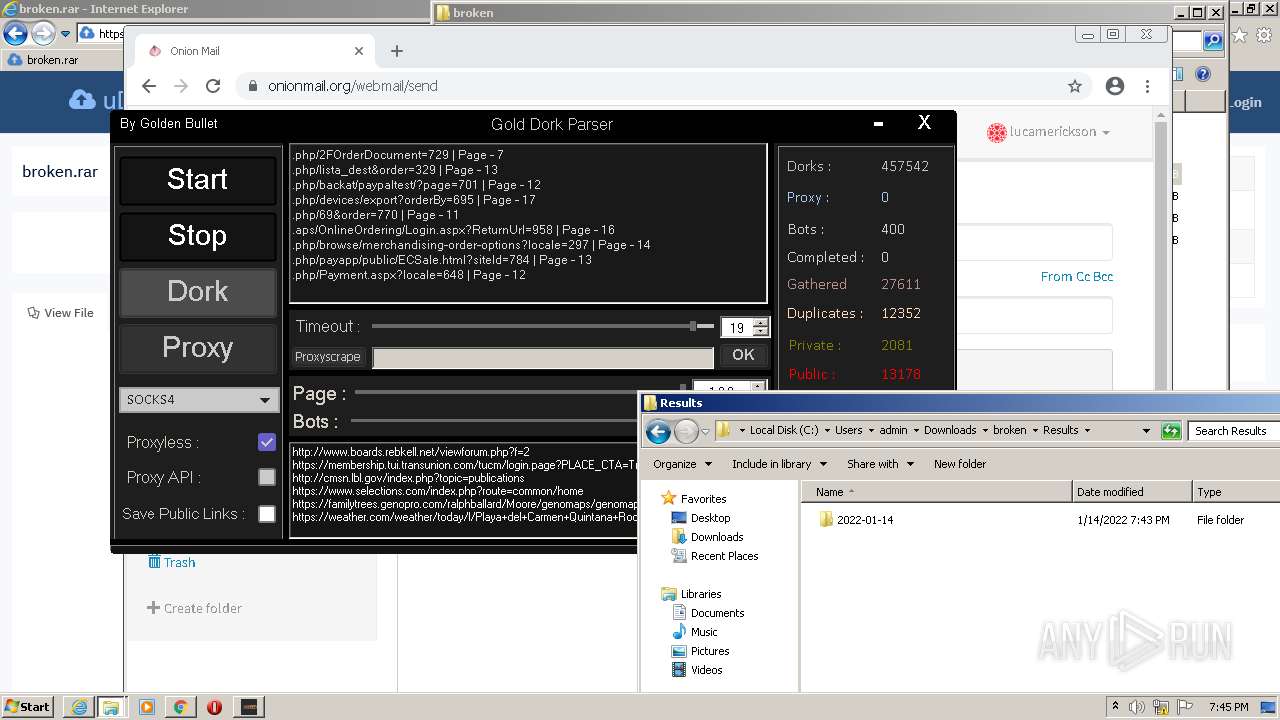
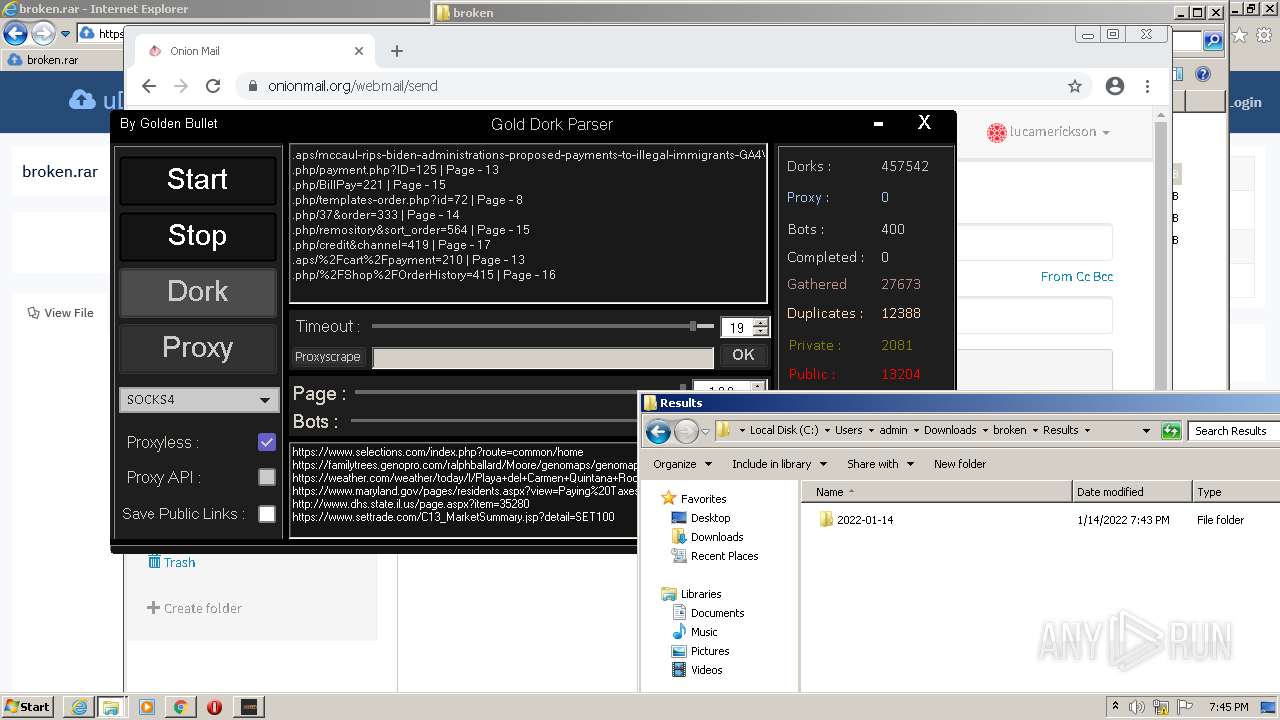
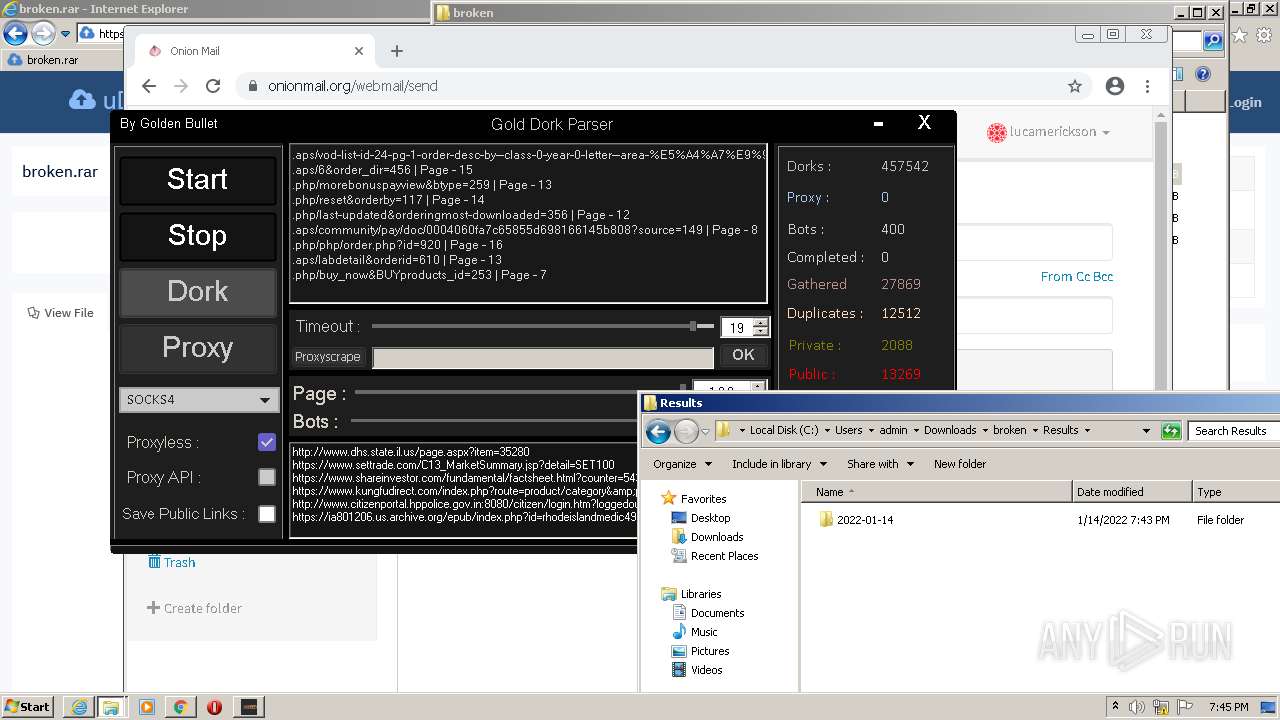
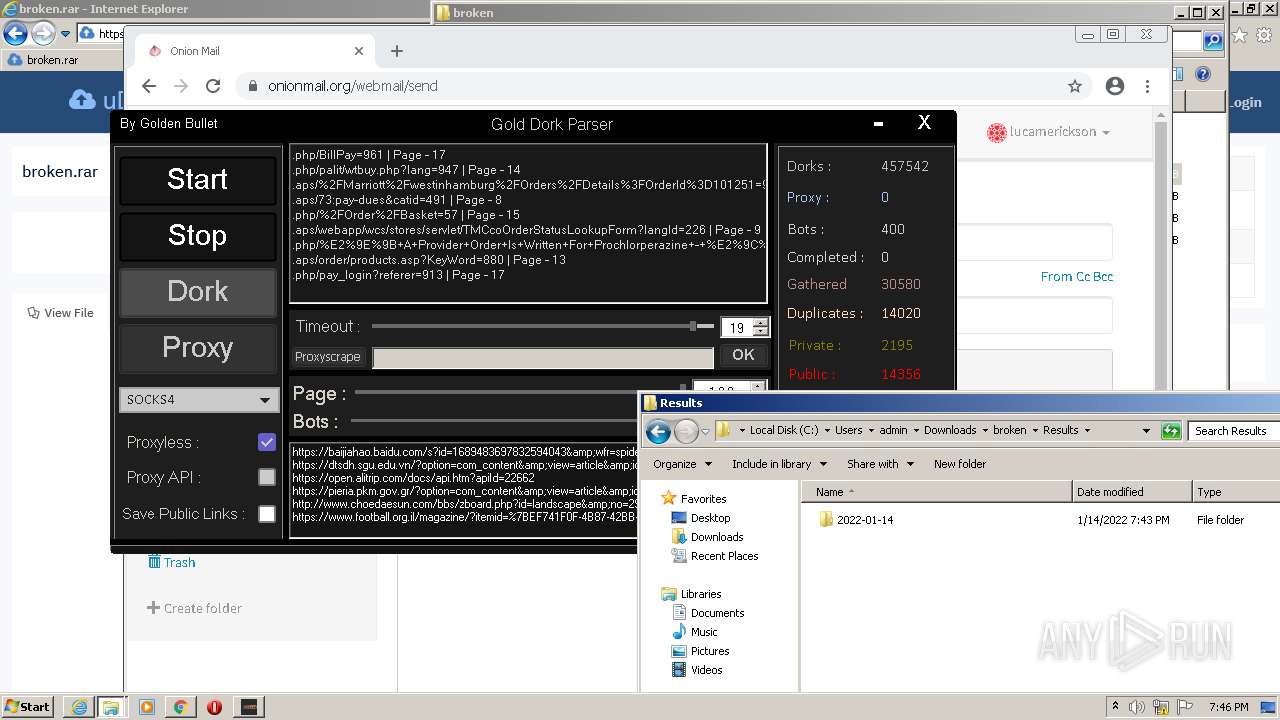
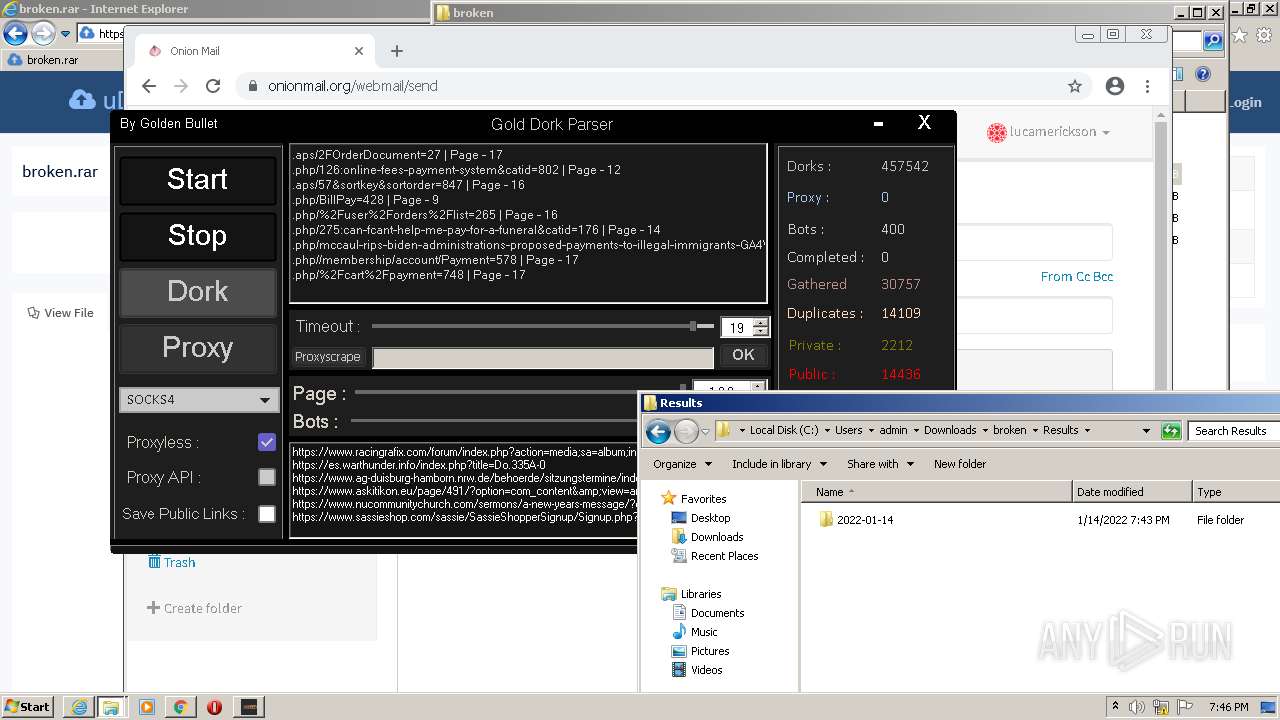
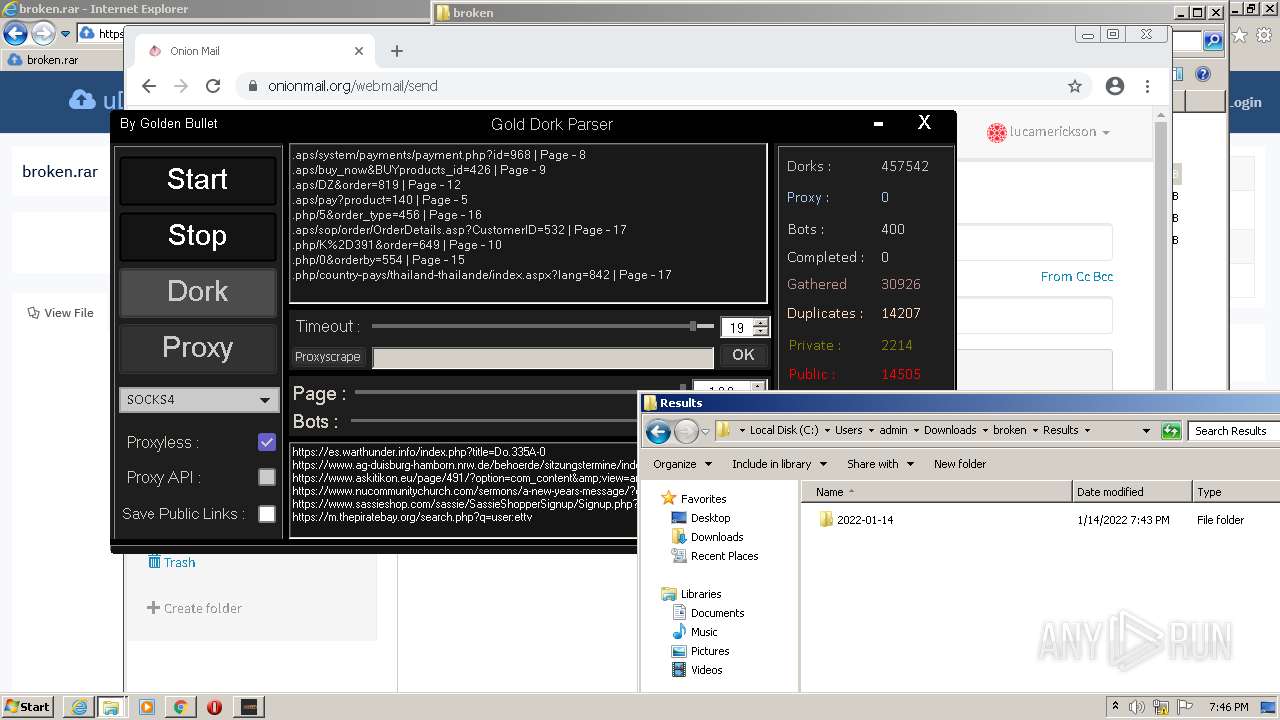
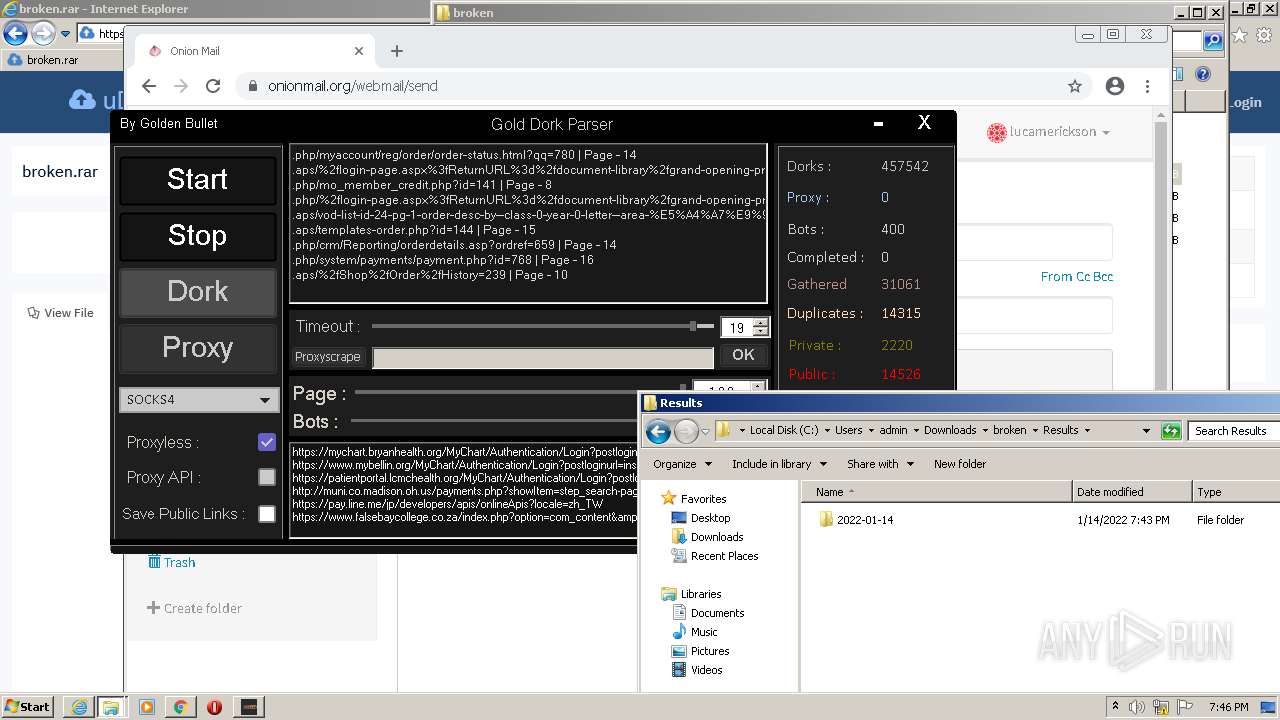
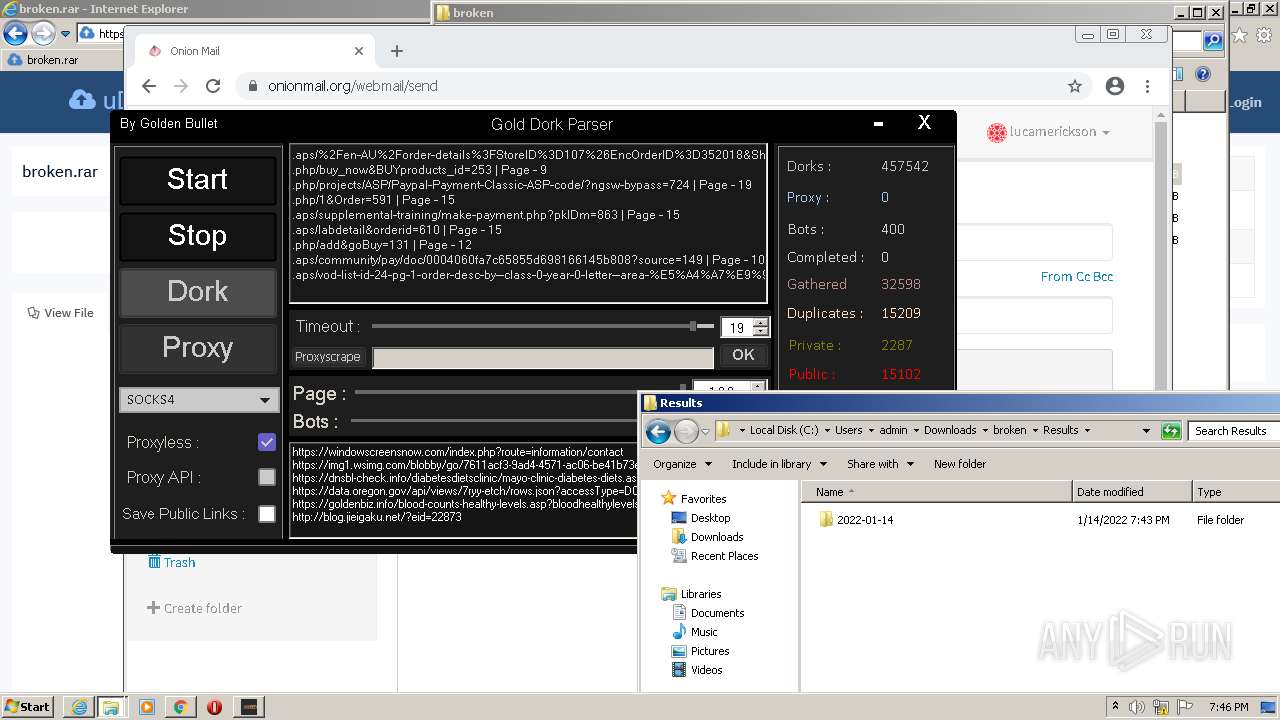
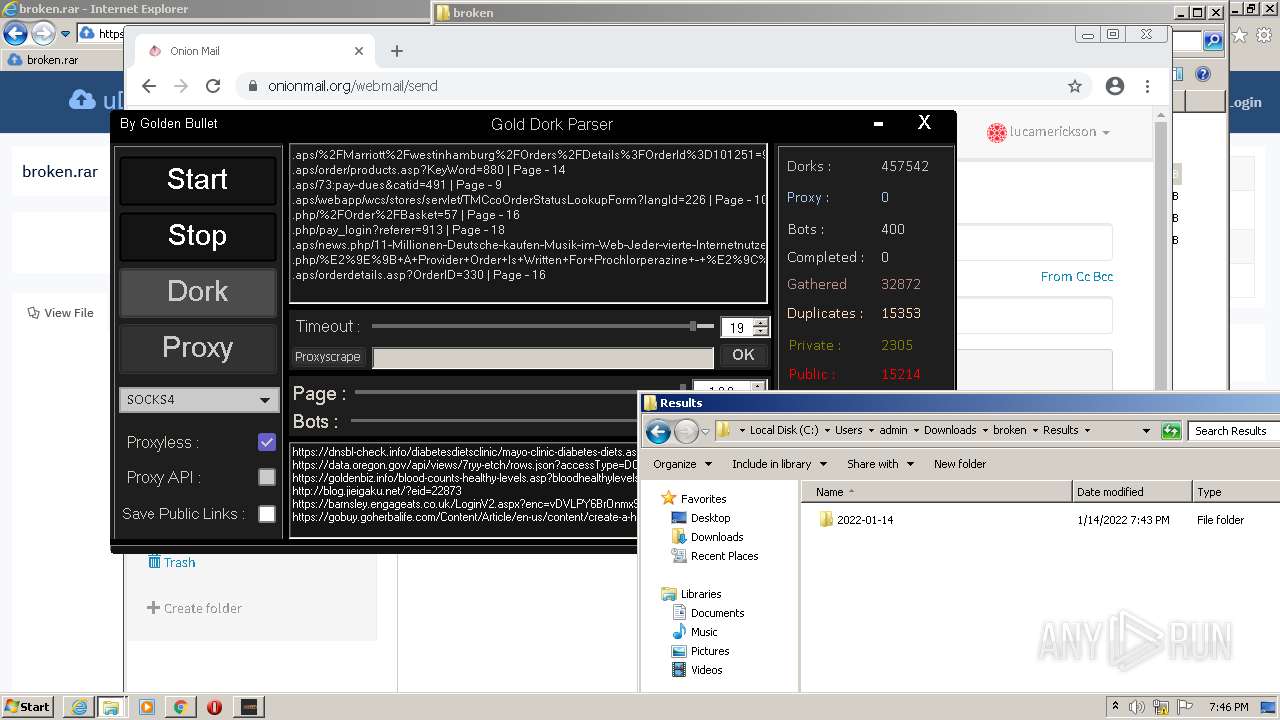
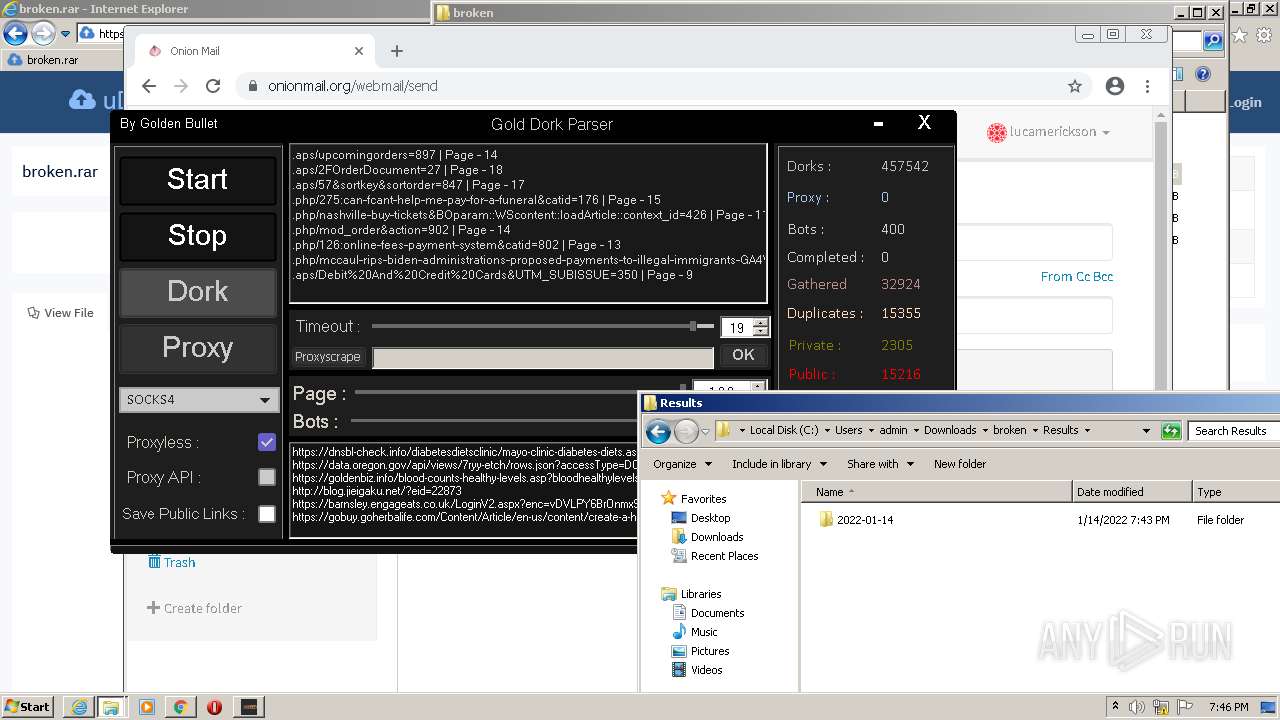
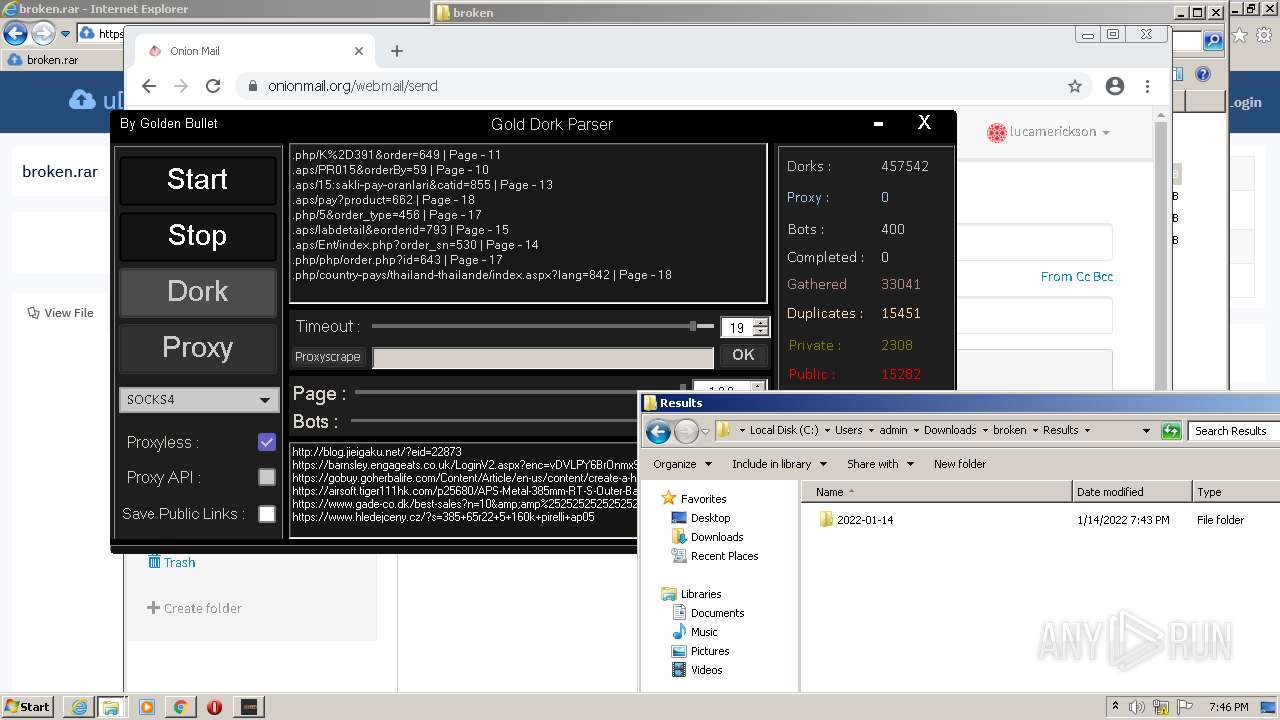
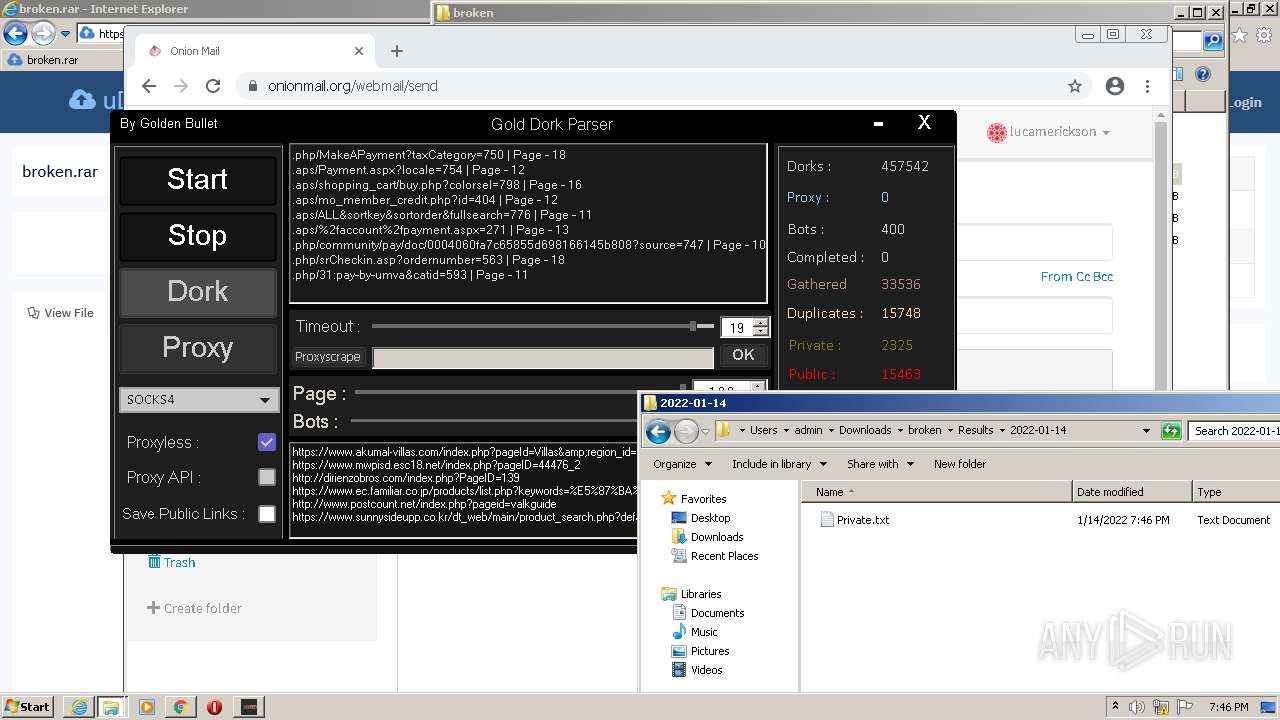
MALICIOUS
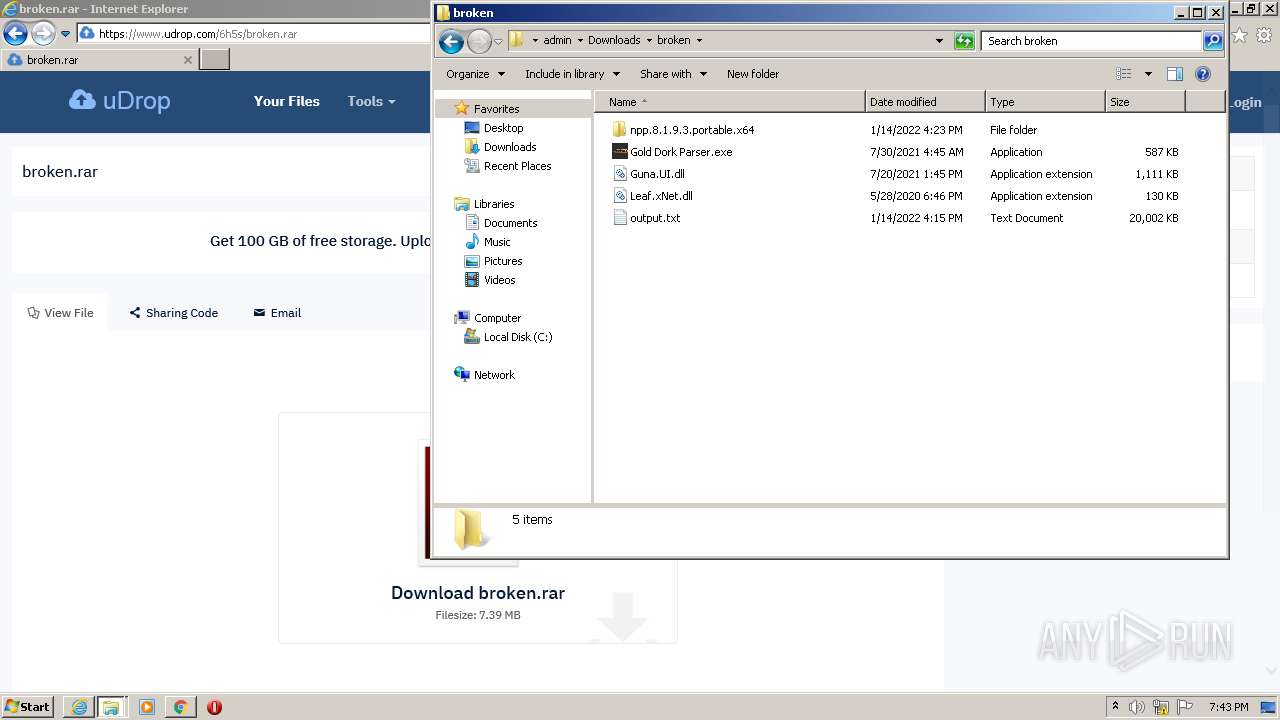
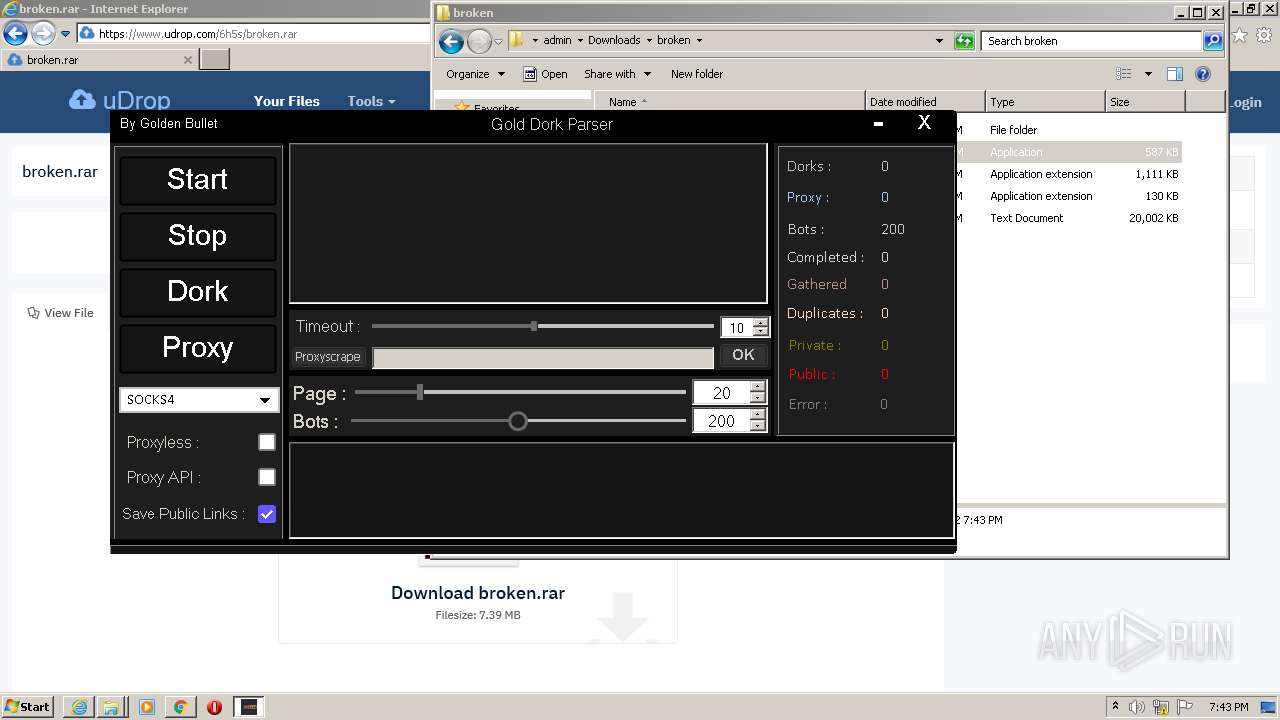
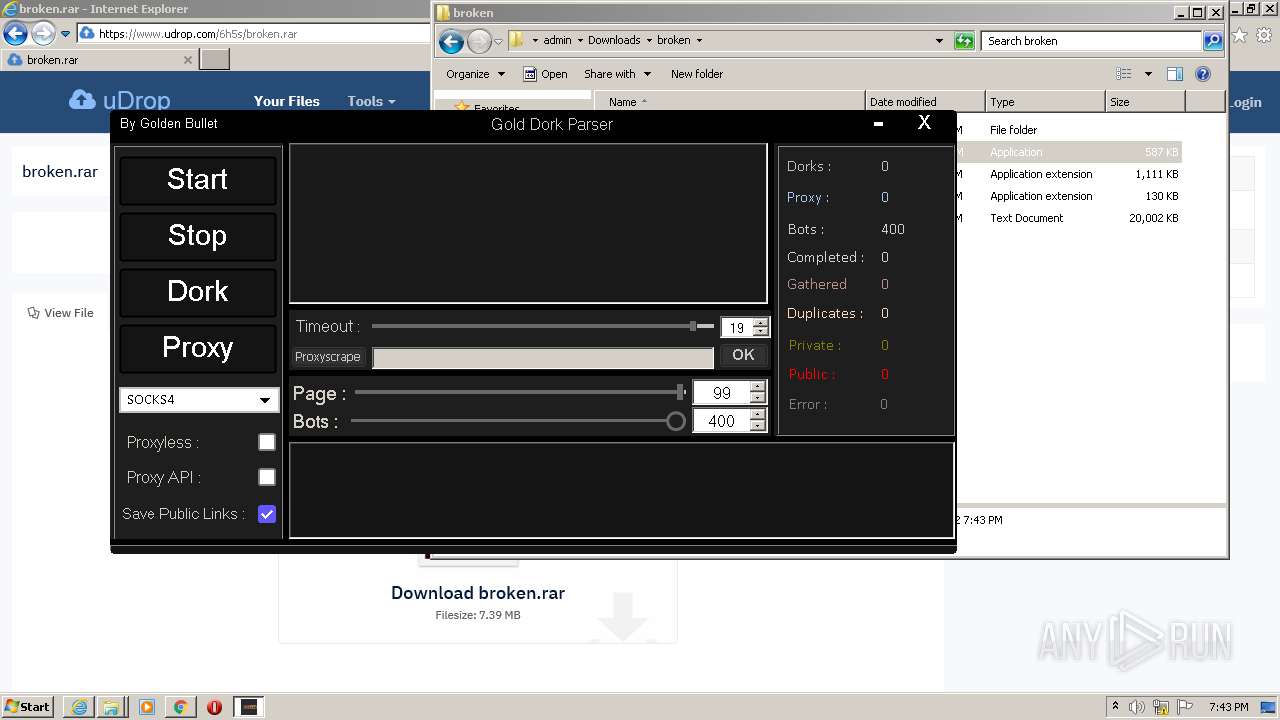
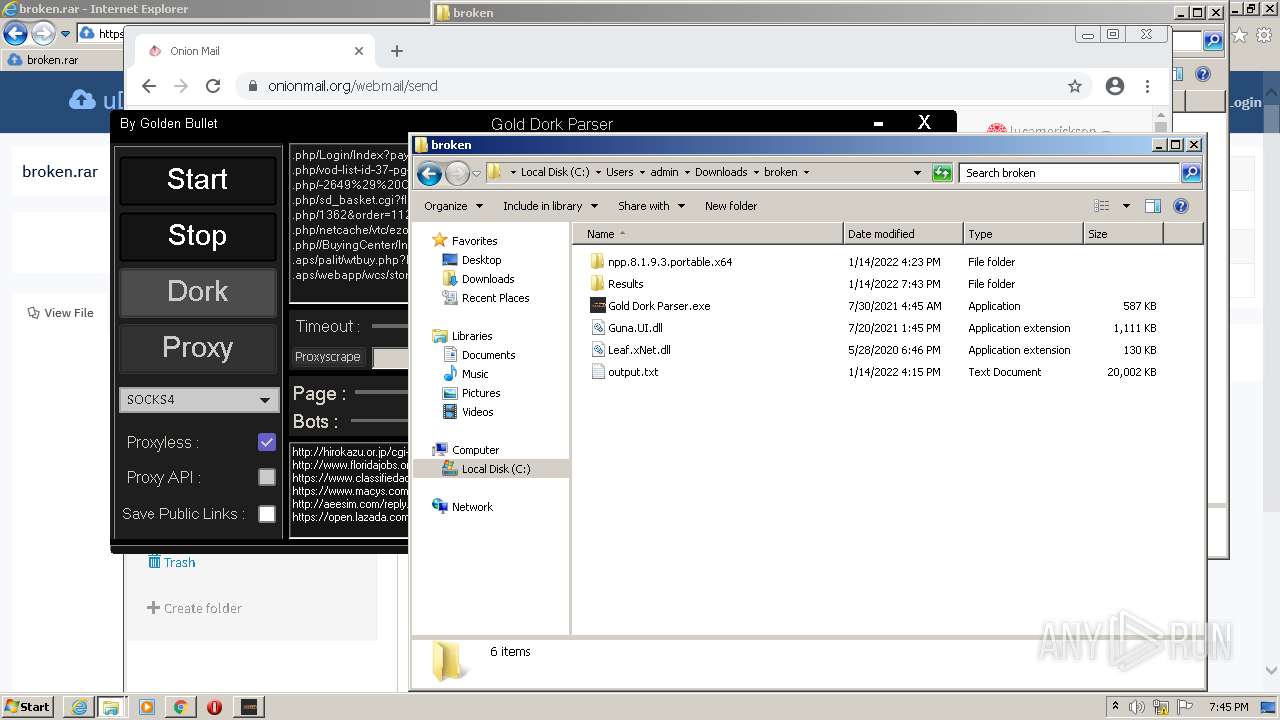
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2232)
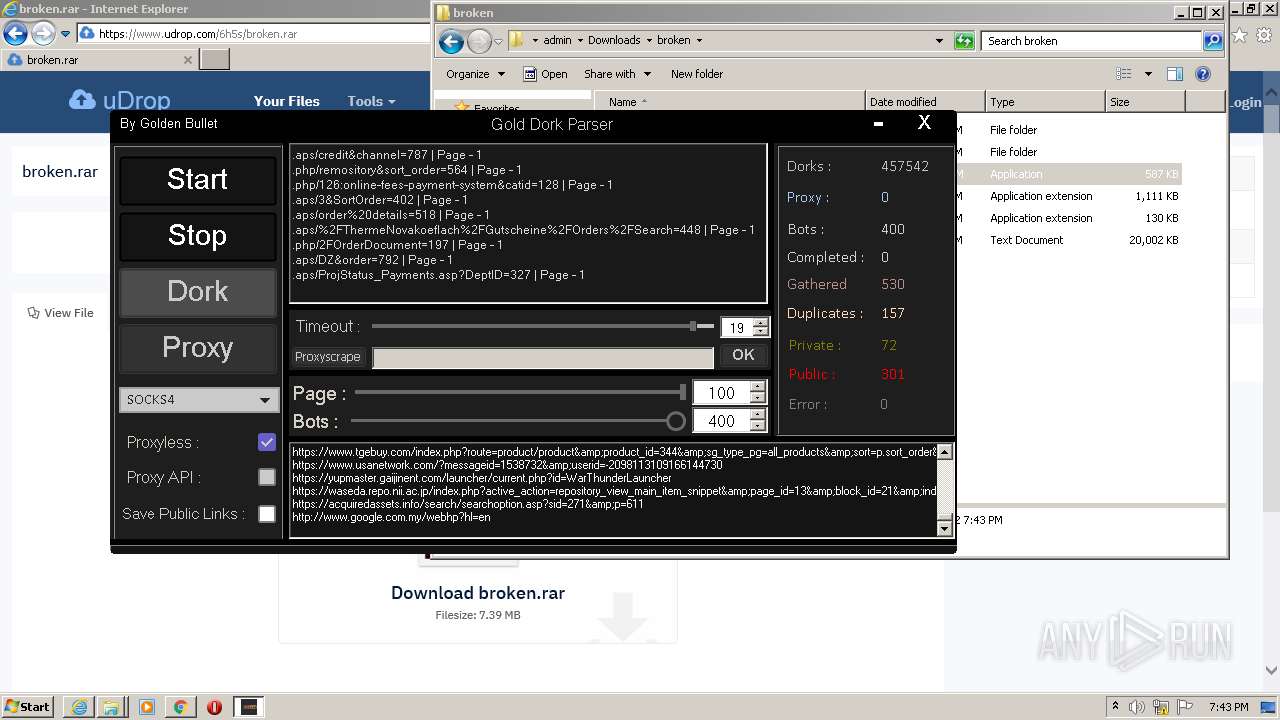
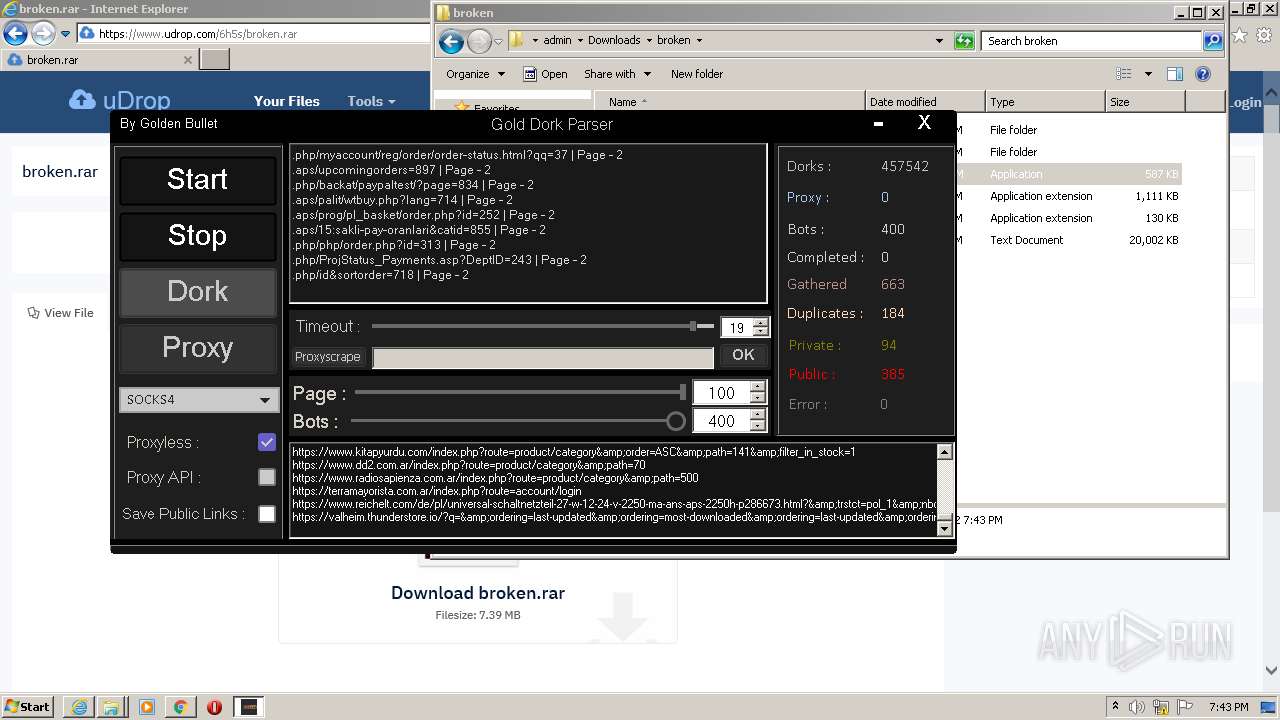
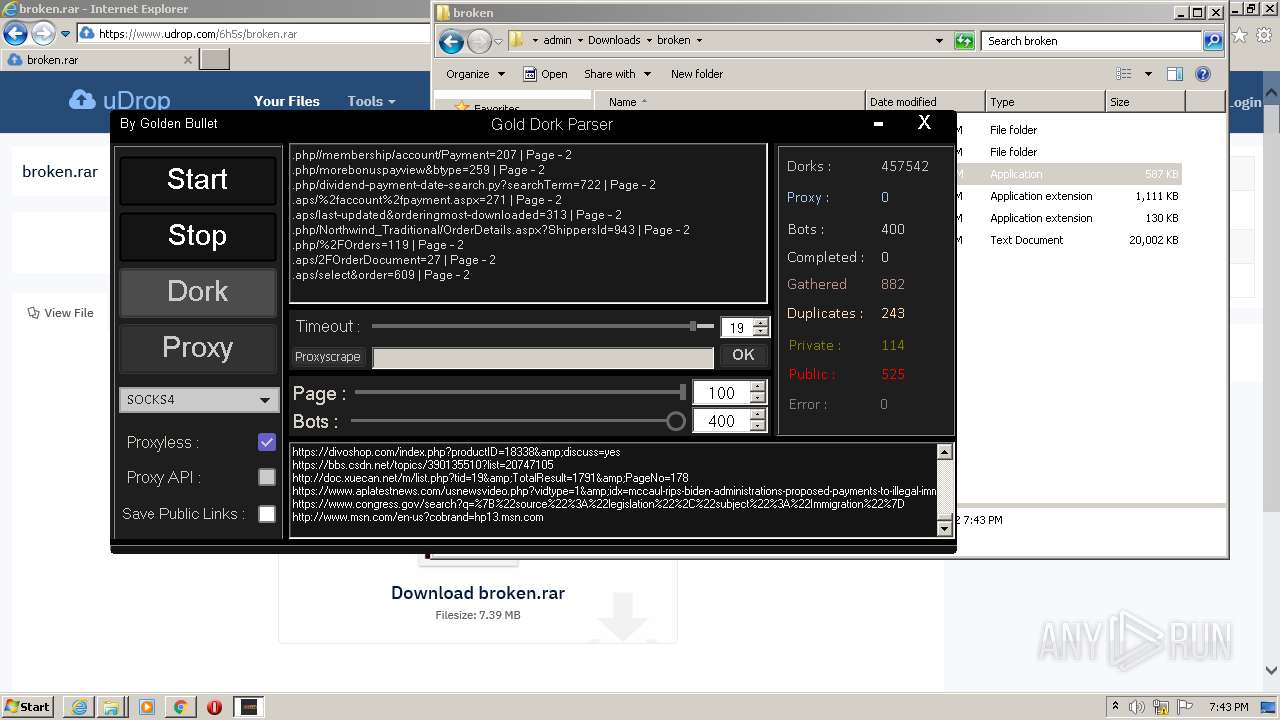
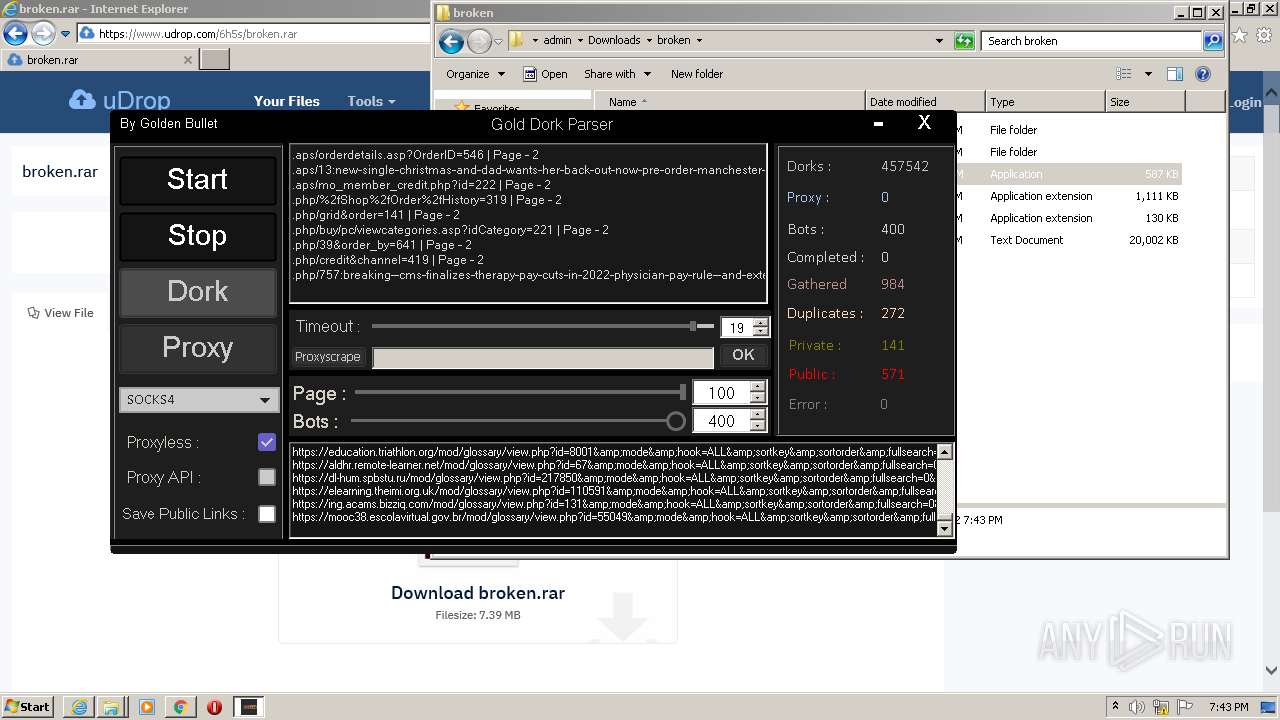
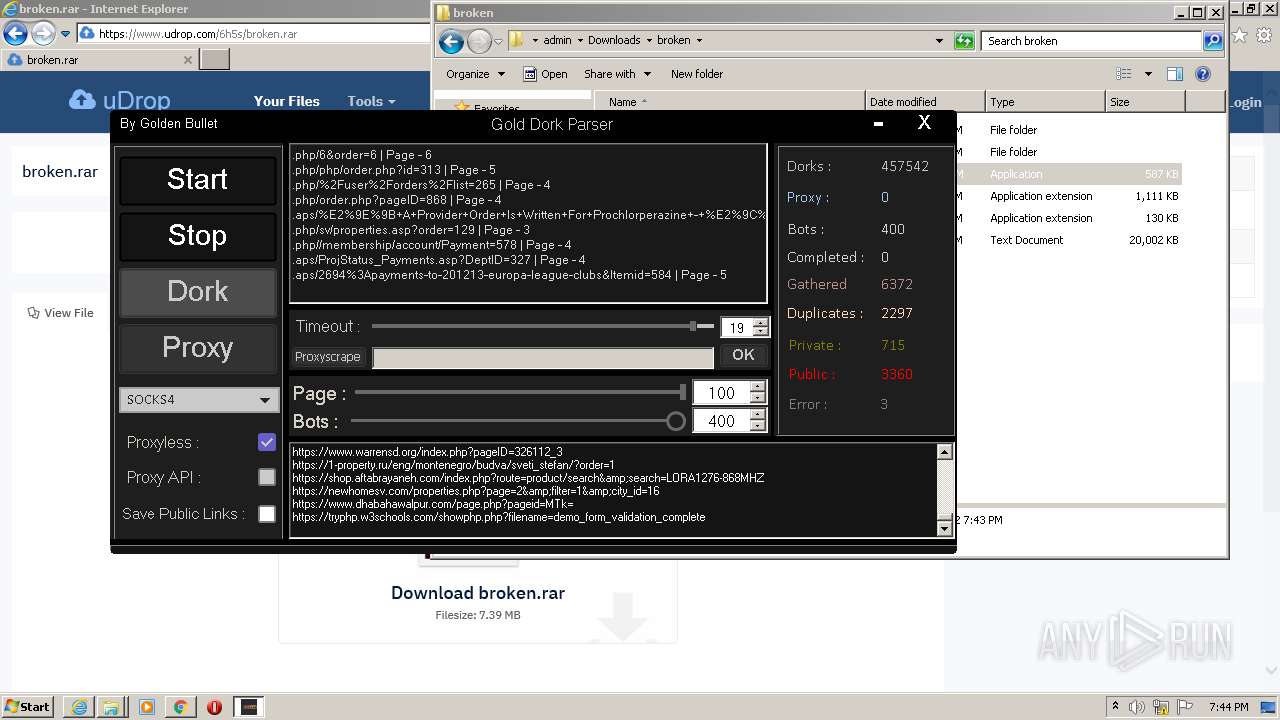
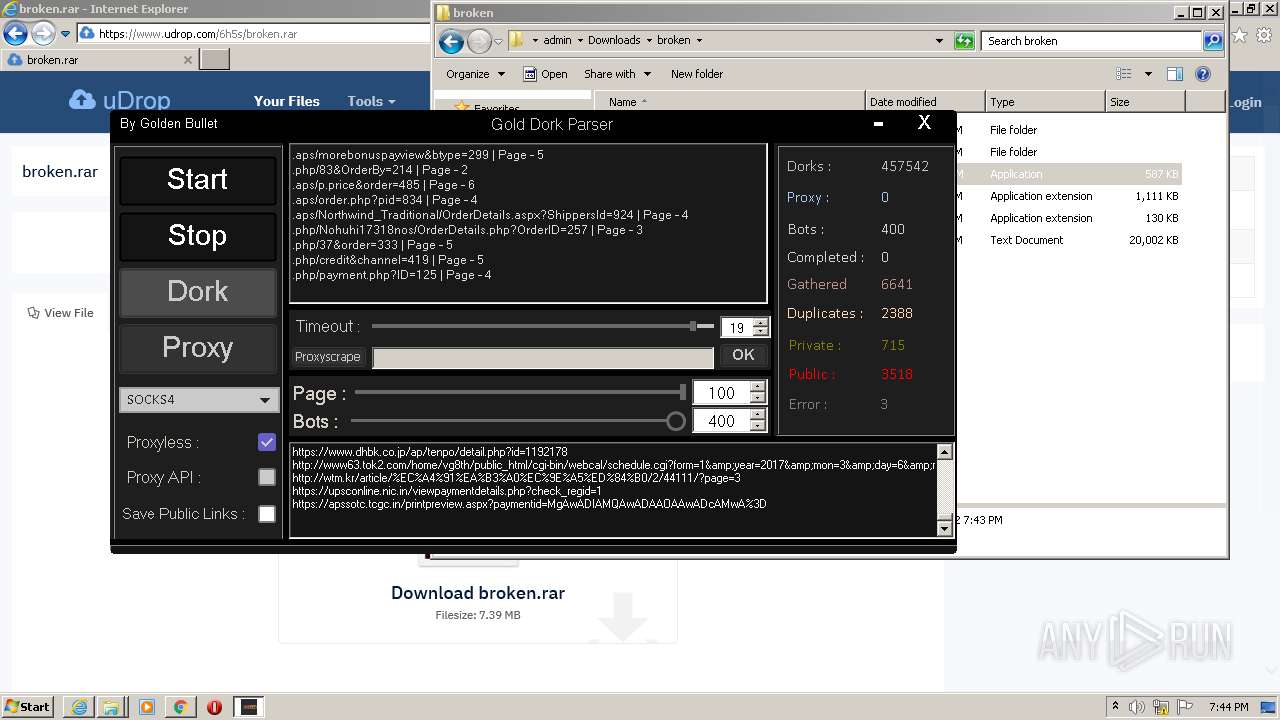
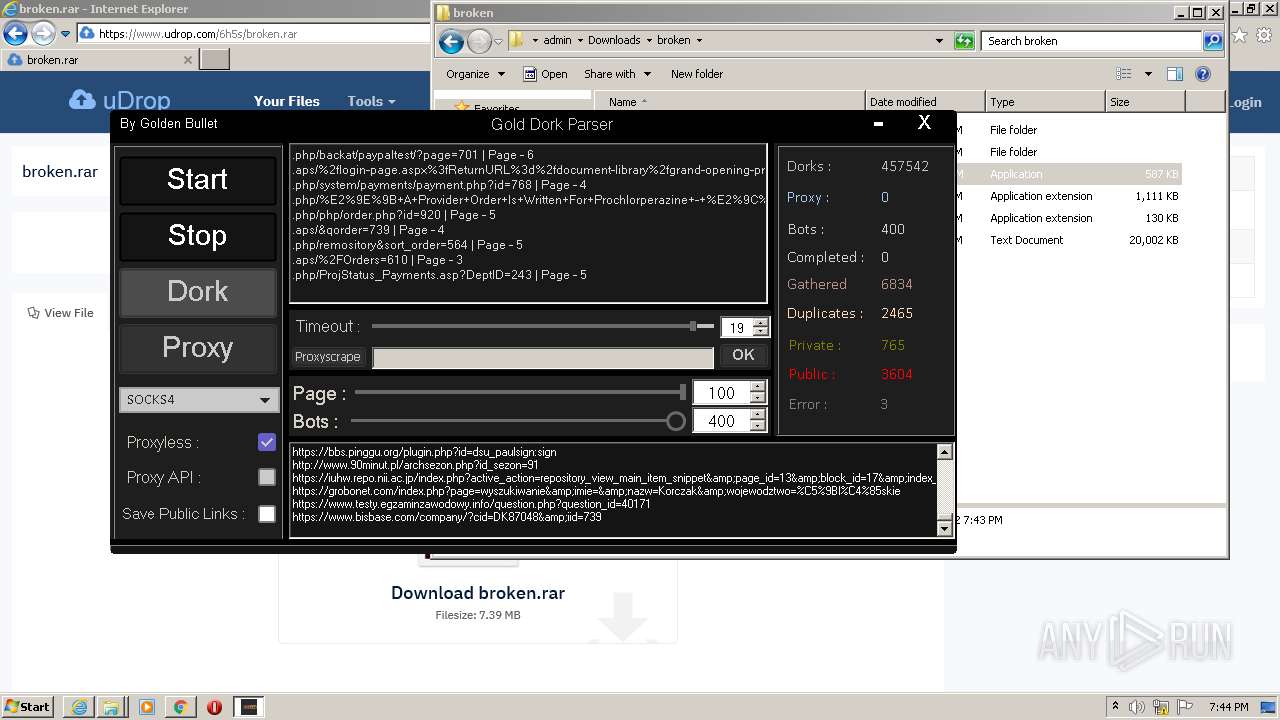
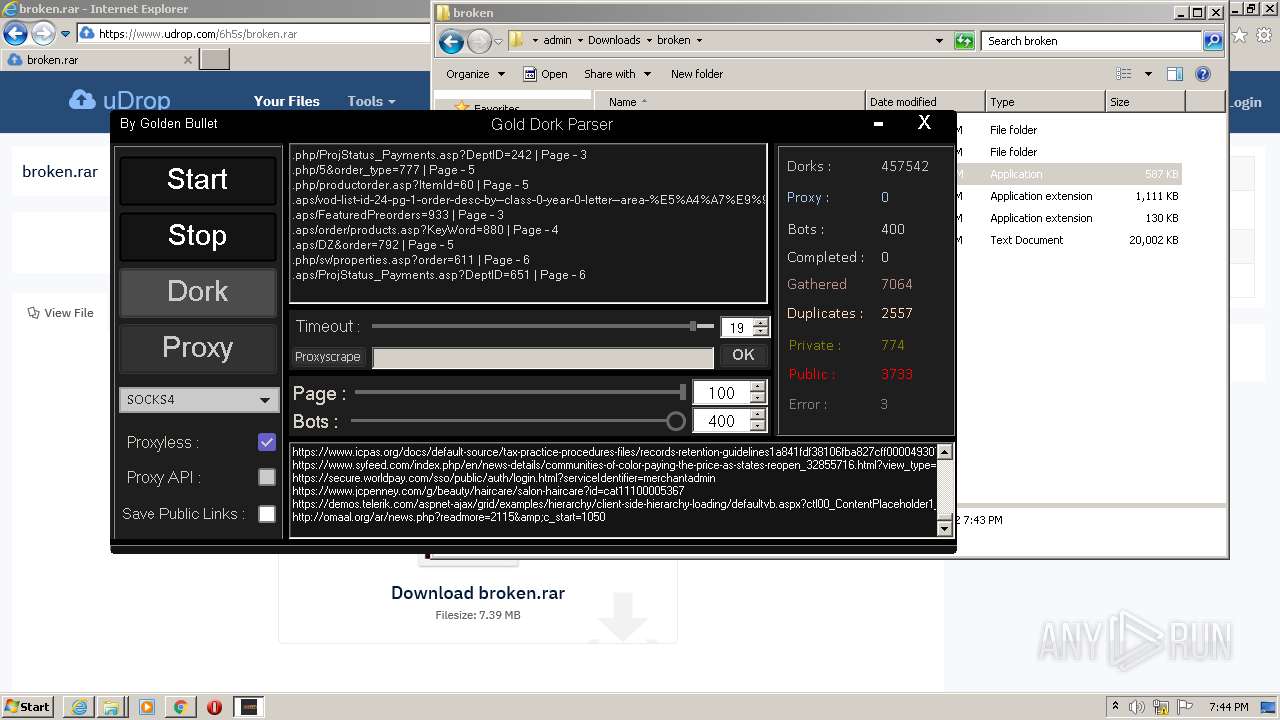
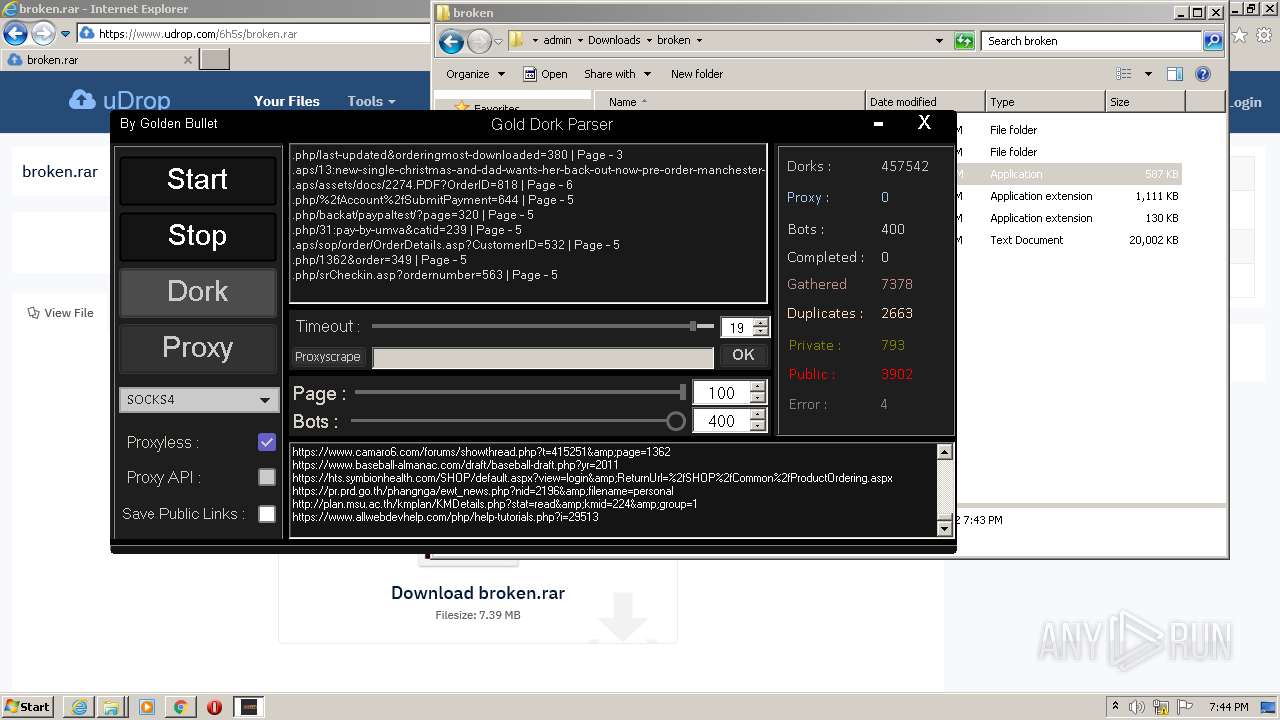
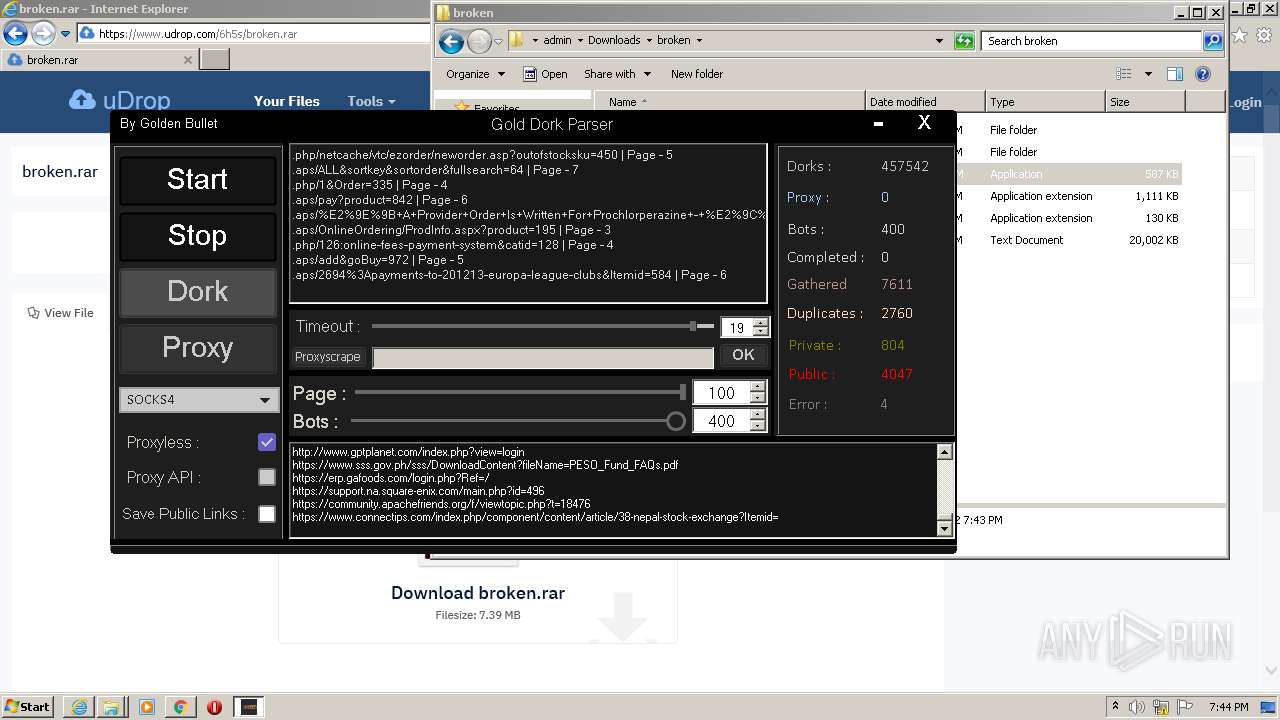
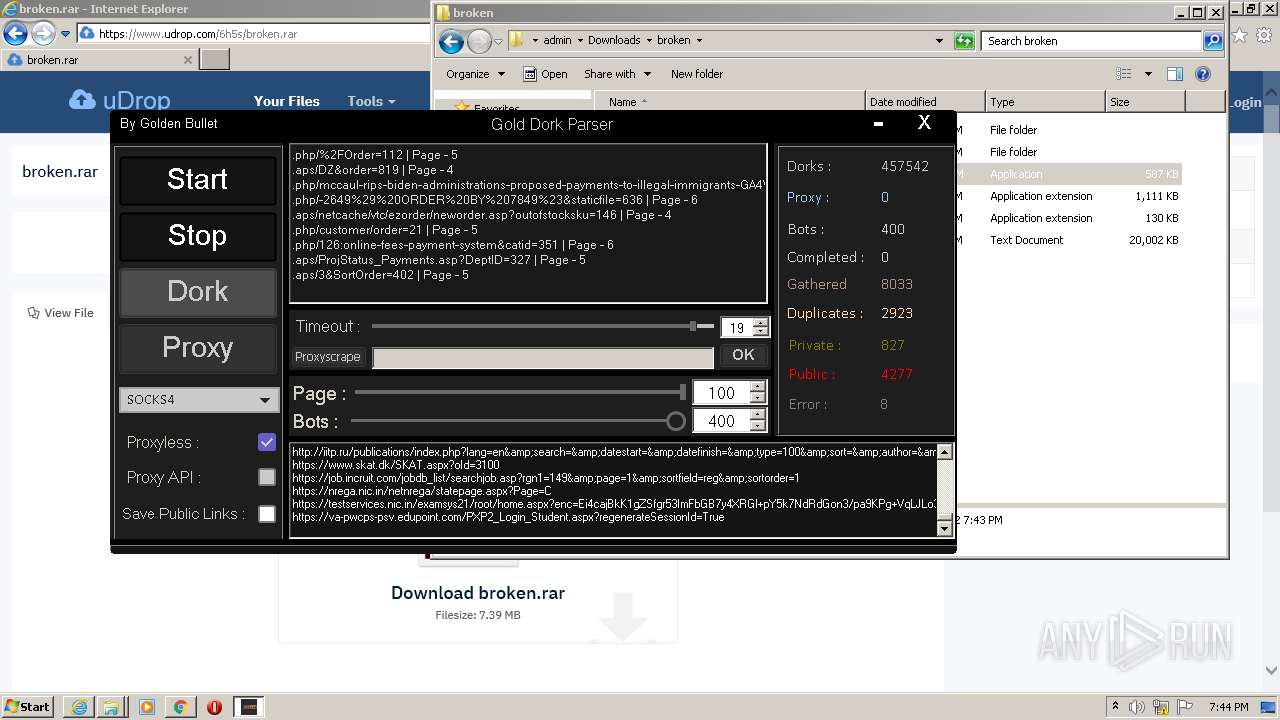
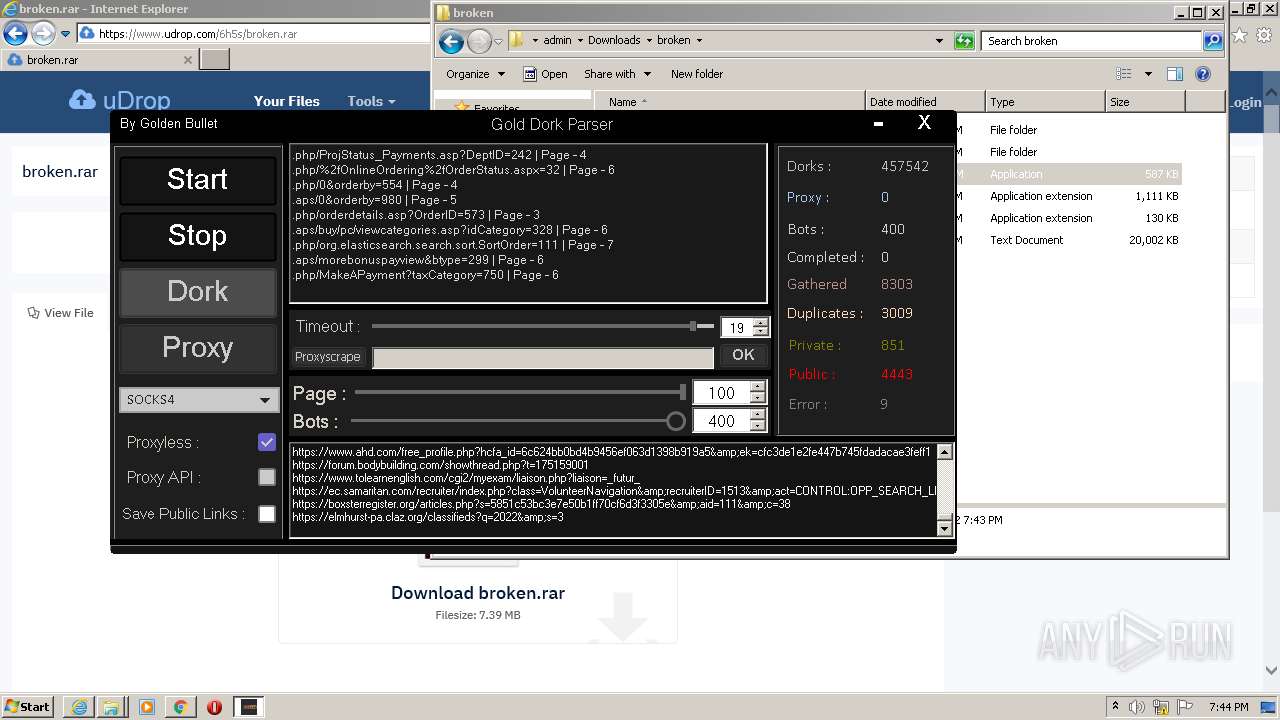
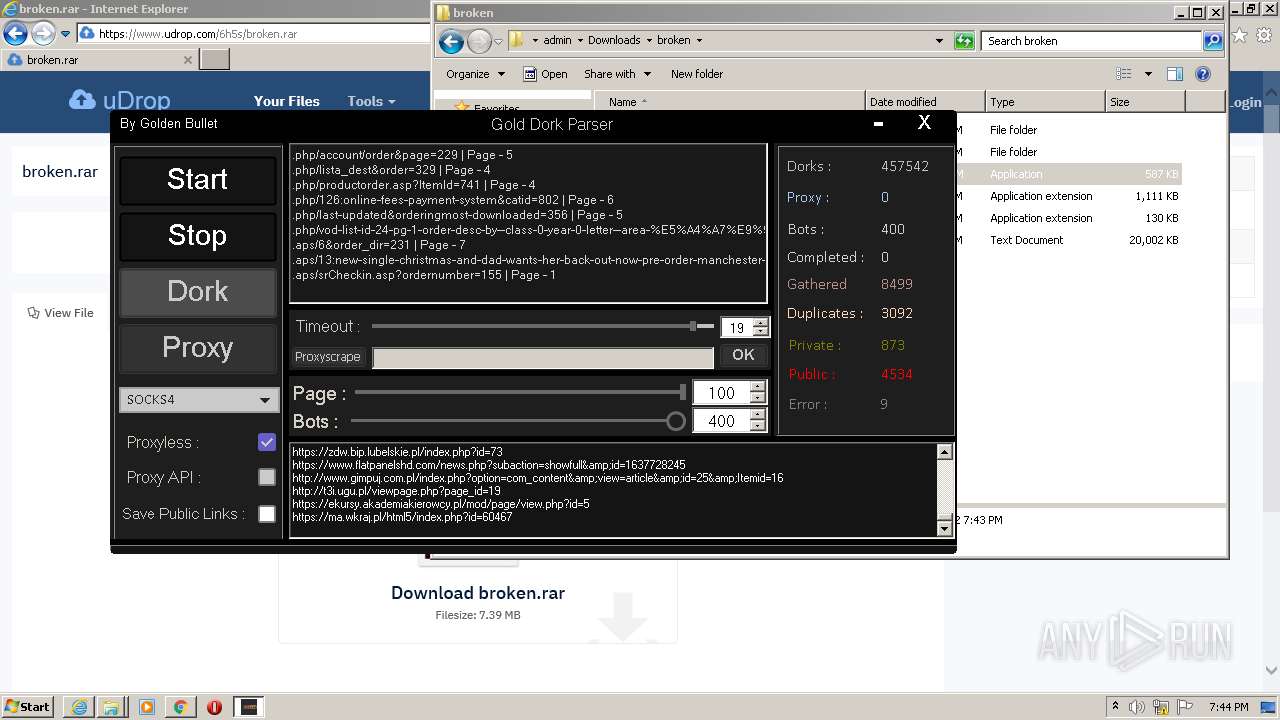
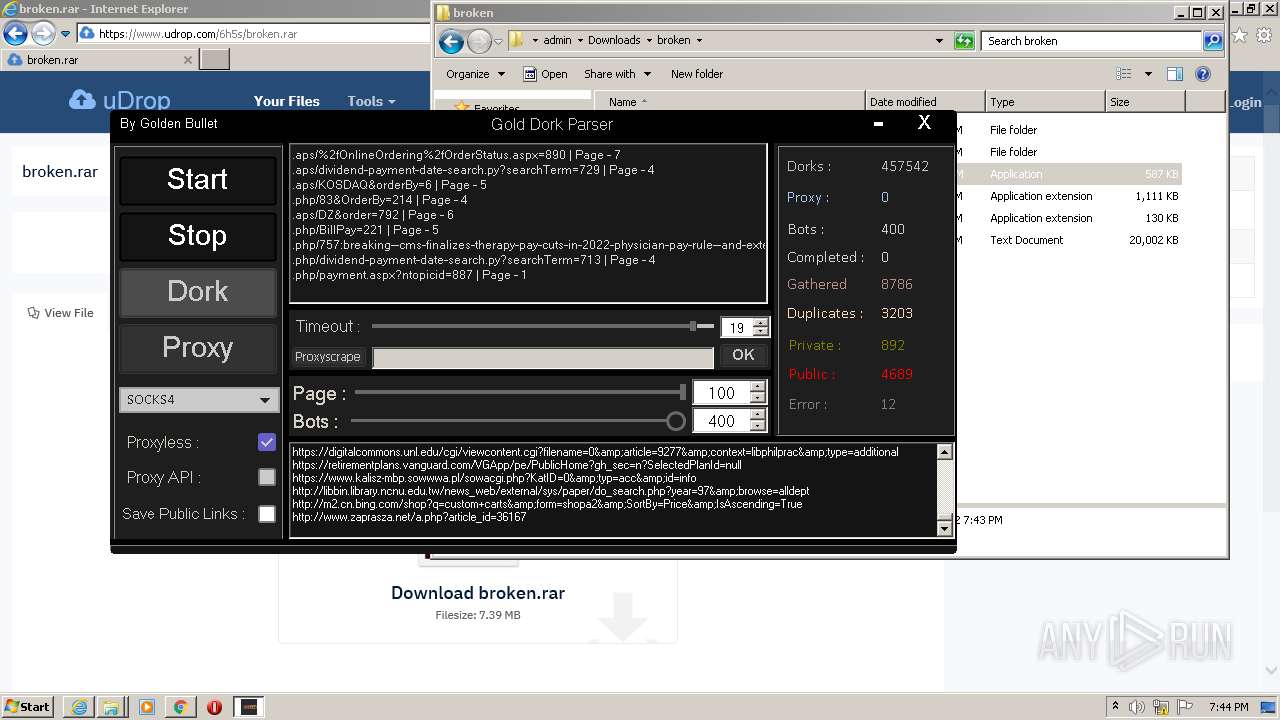
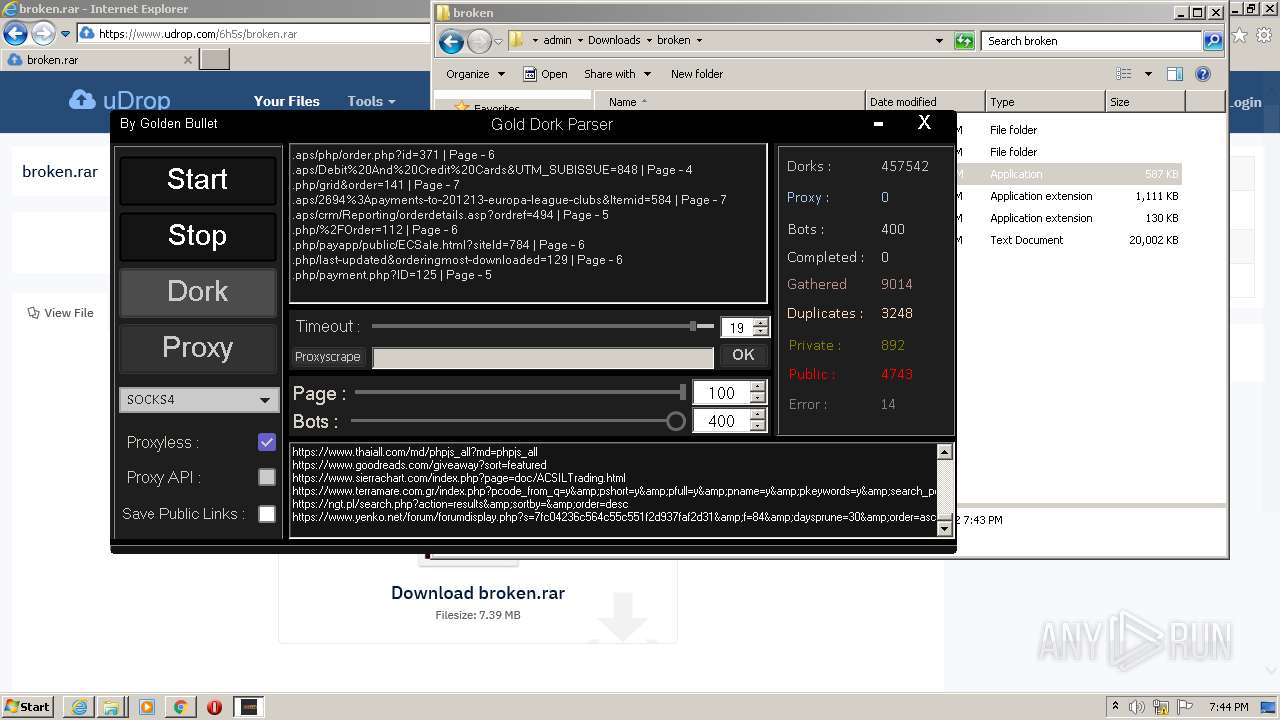
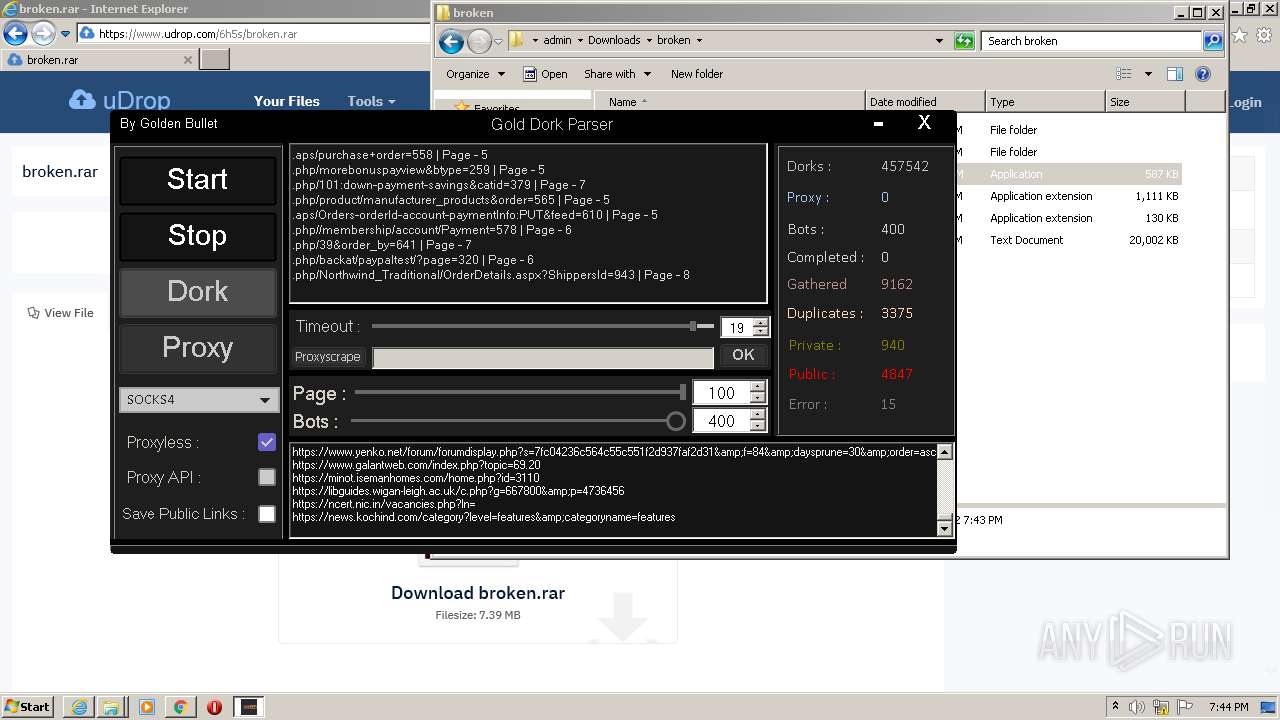
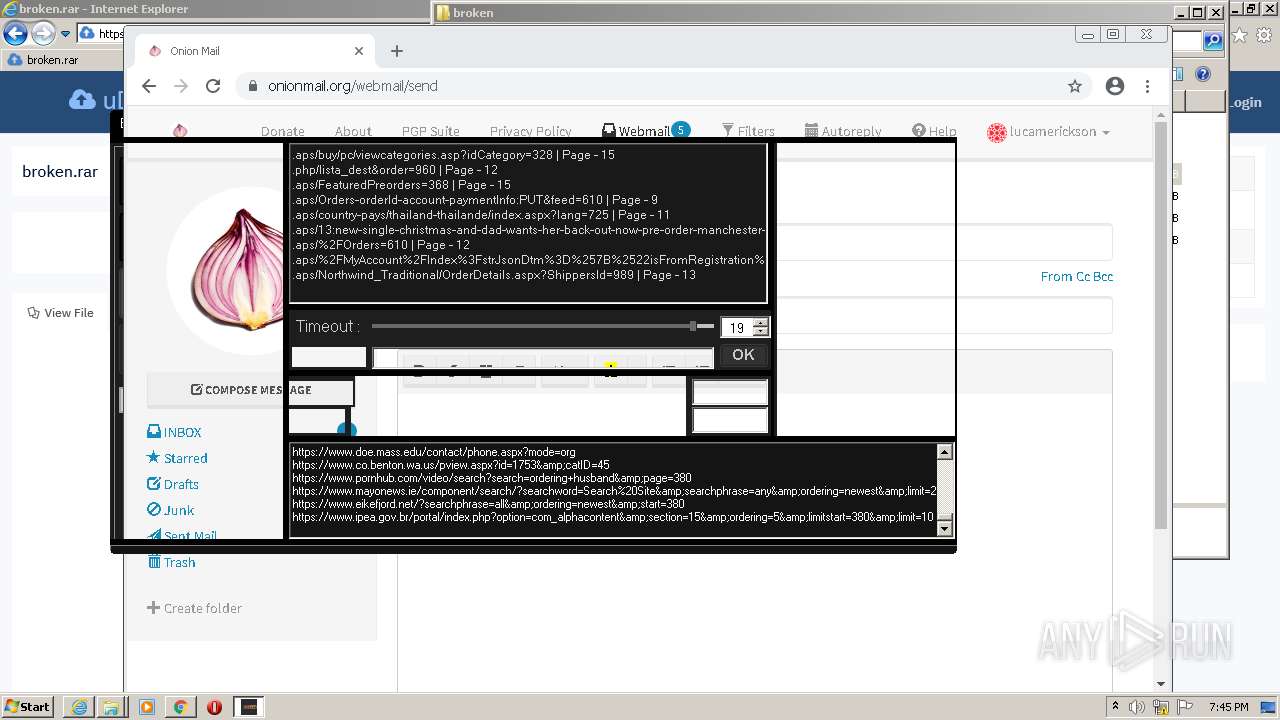
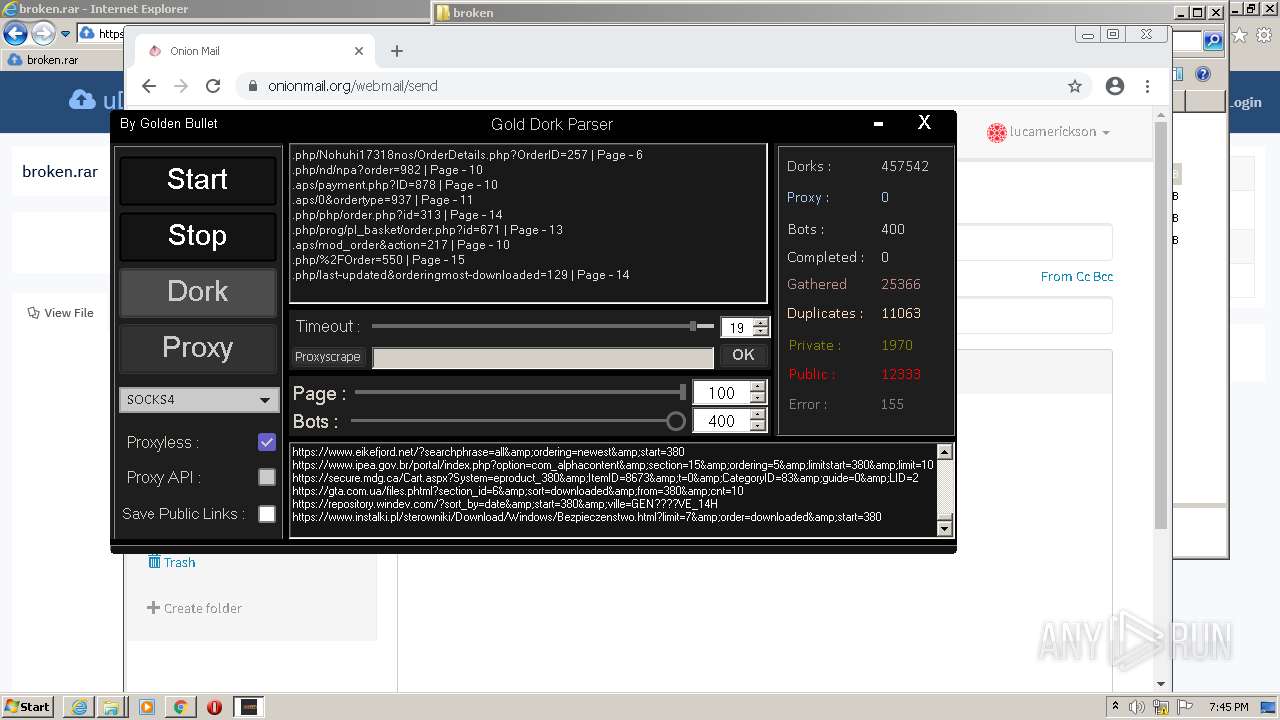
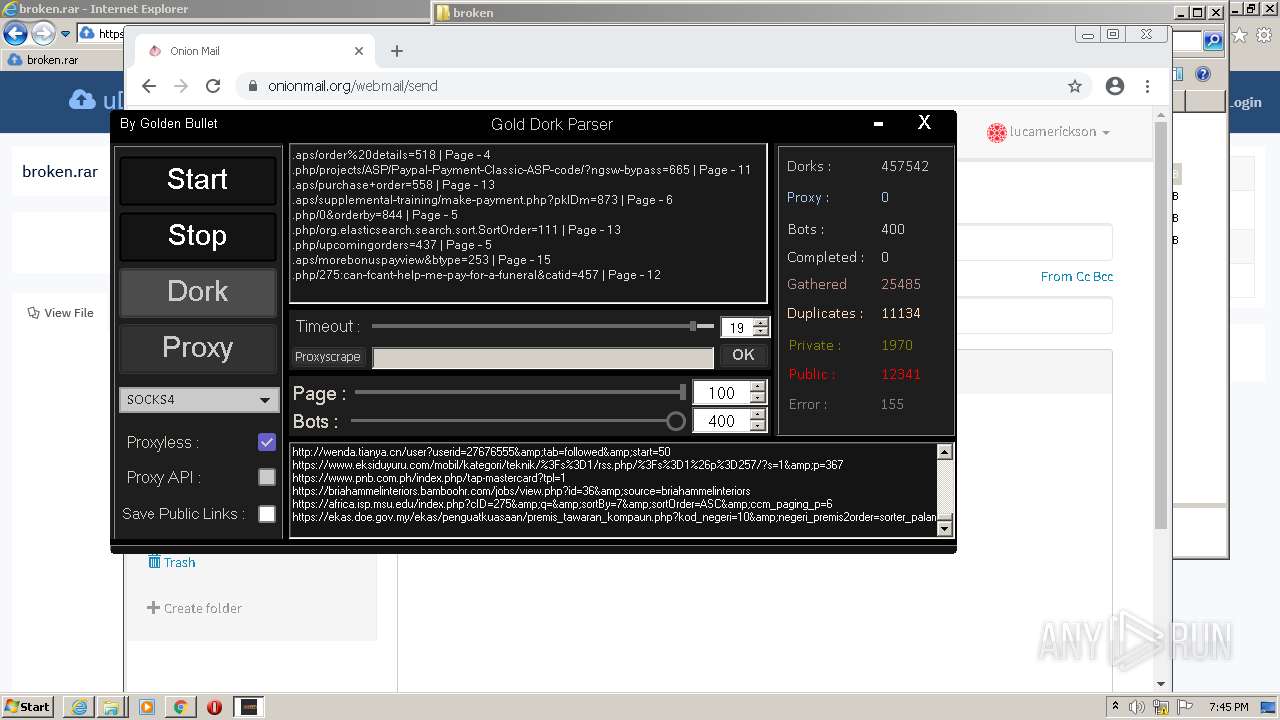
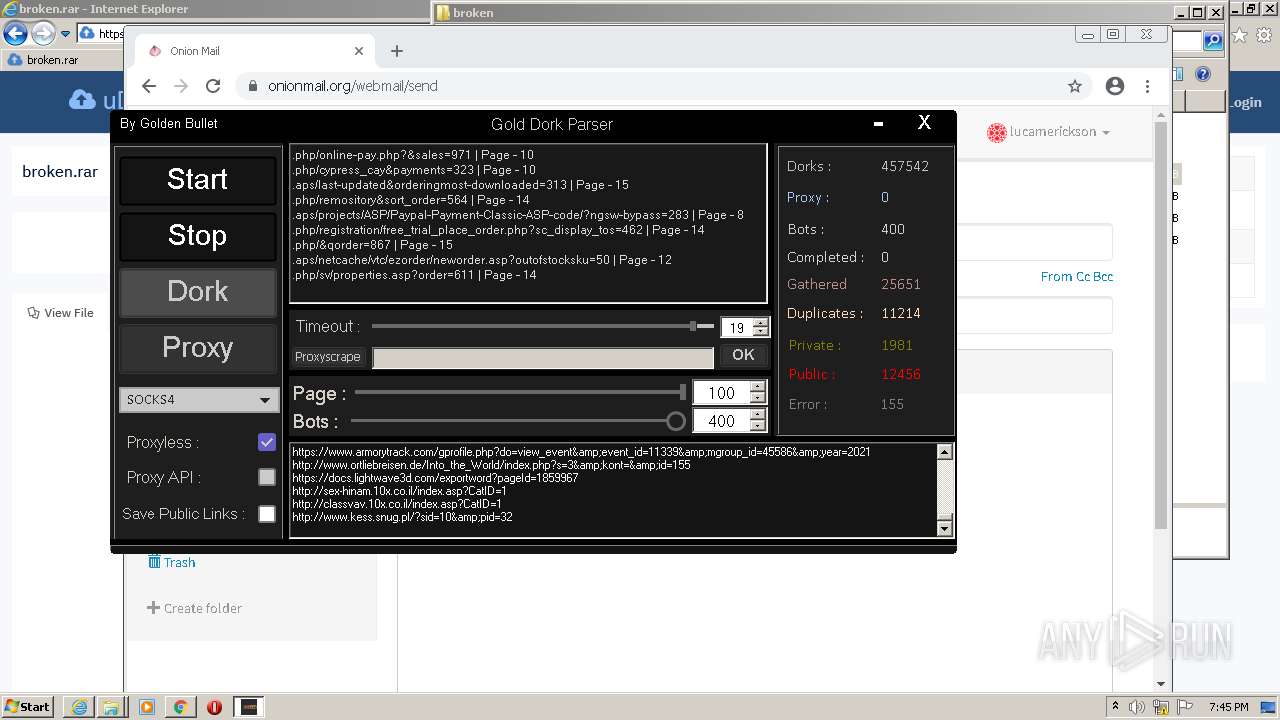
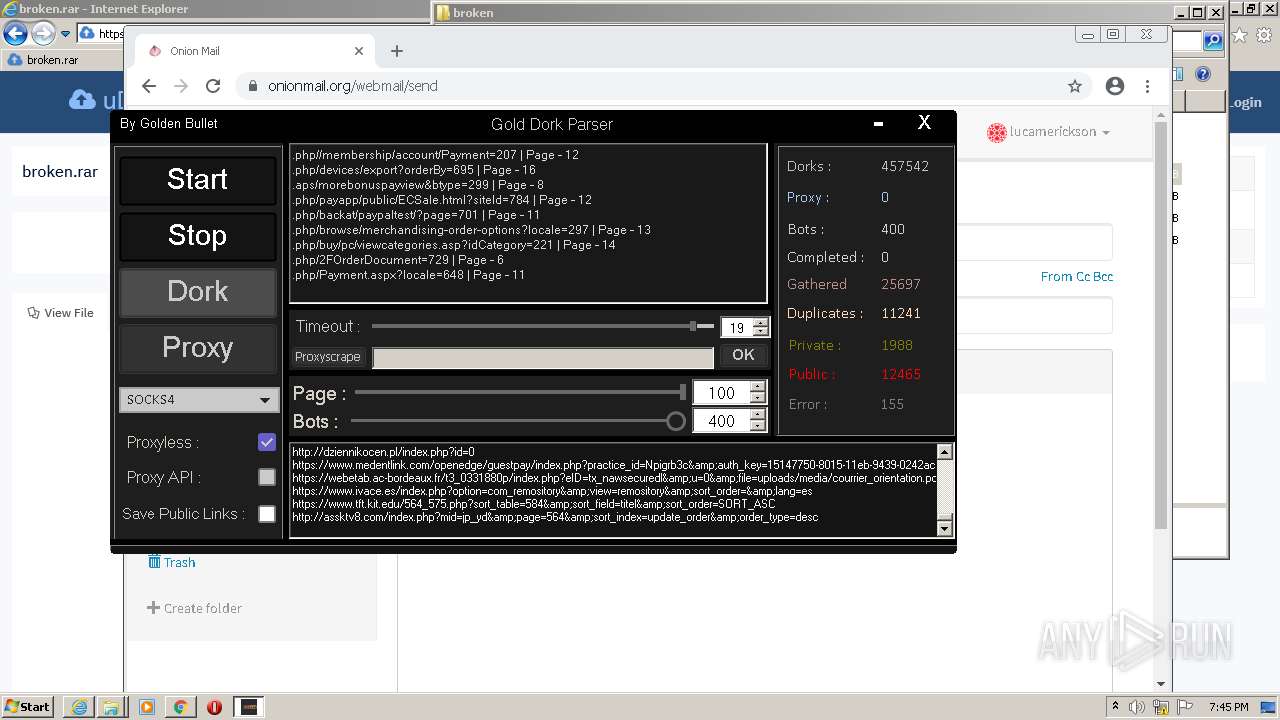
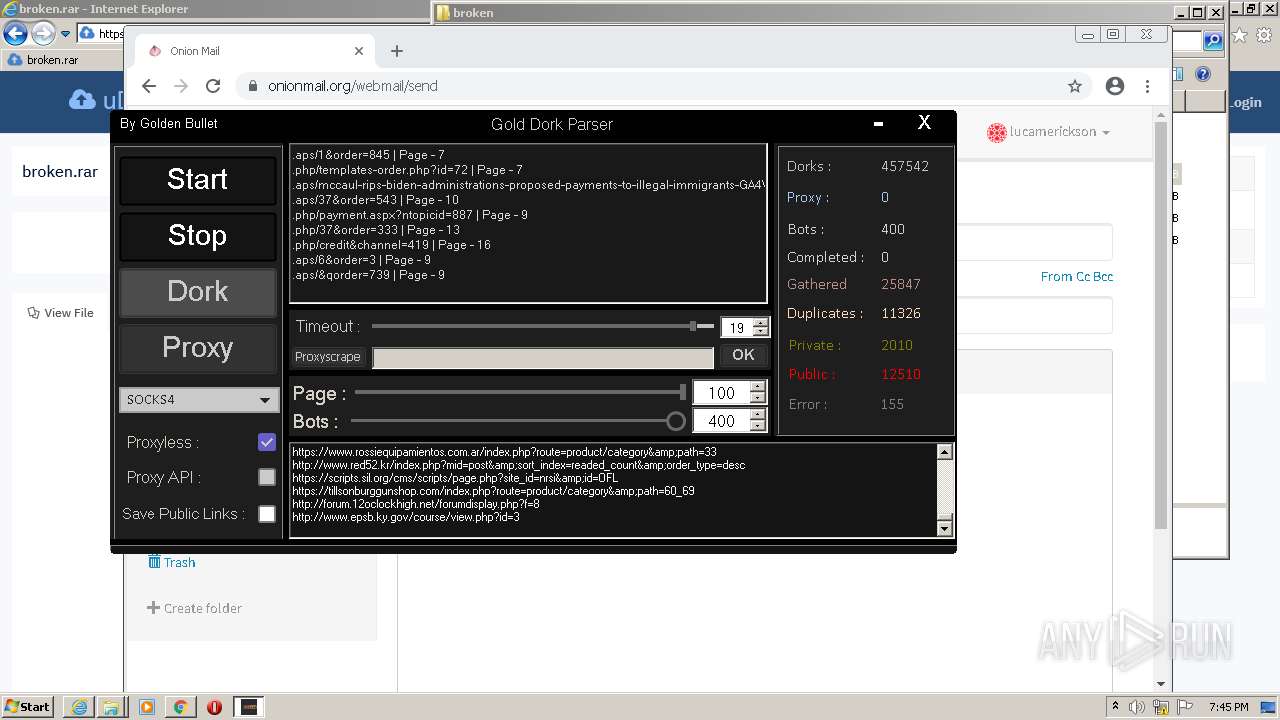
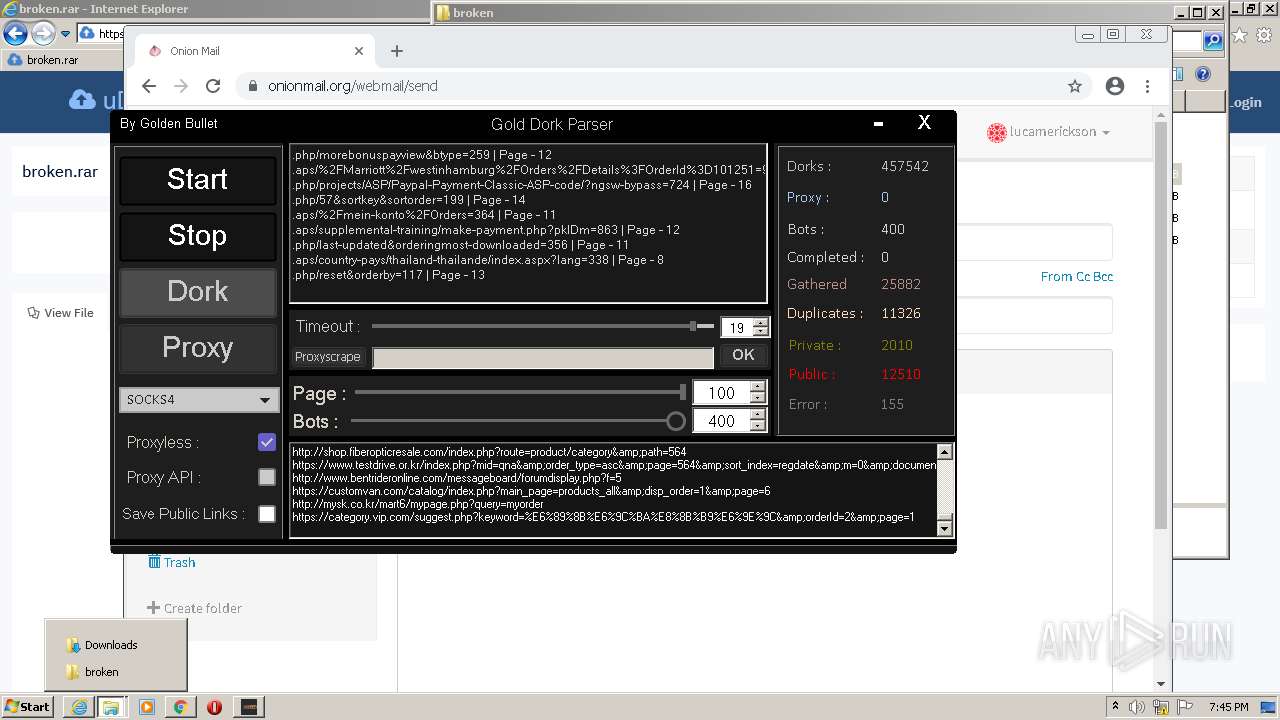
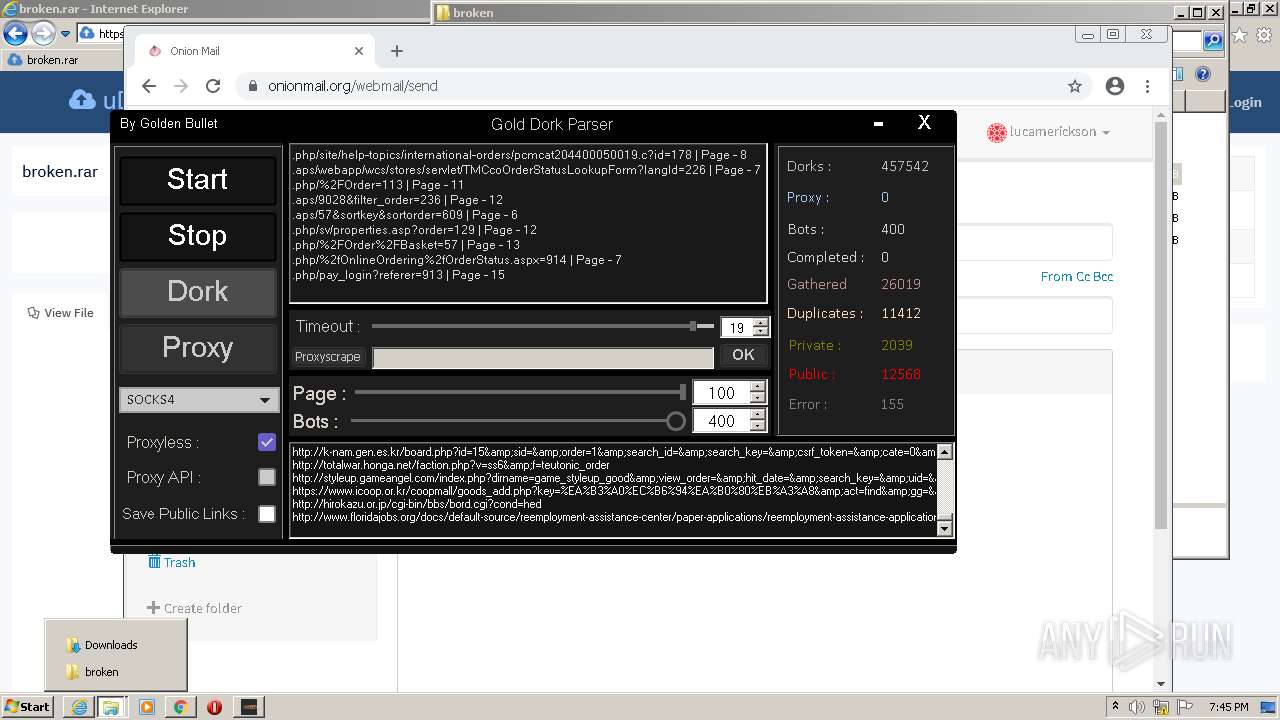
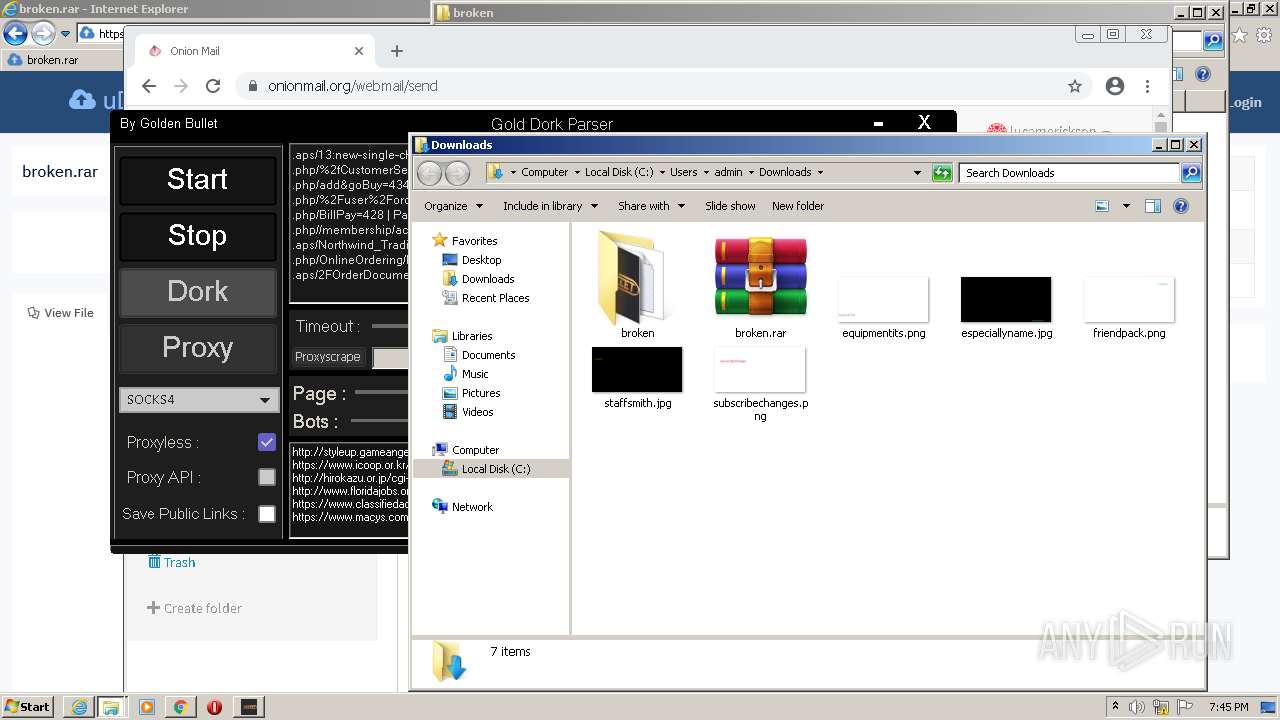
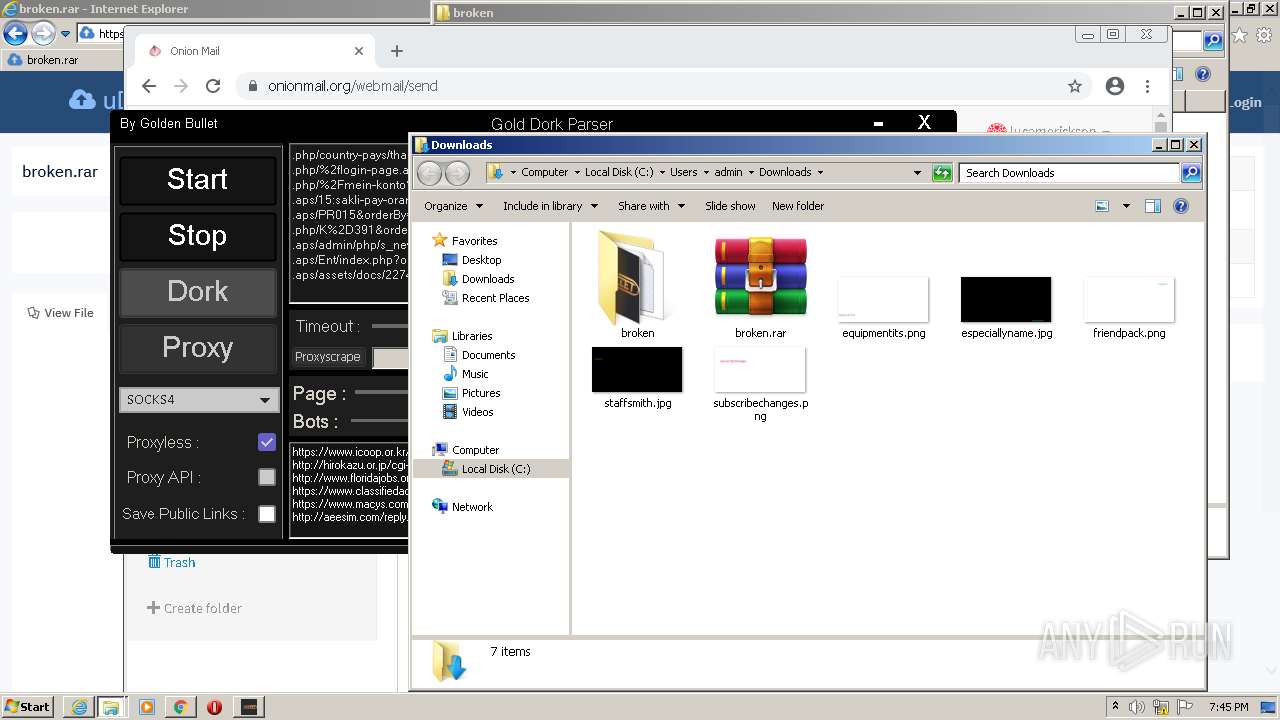
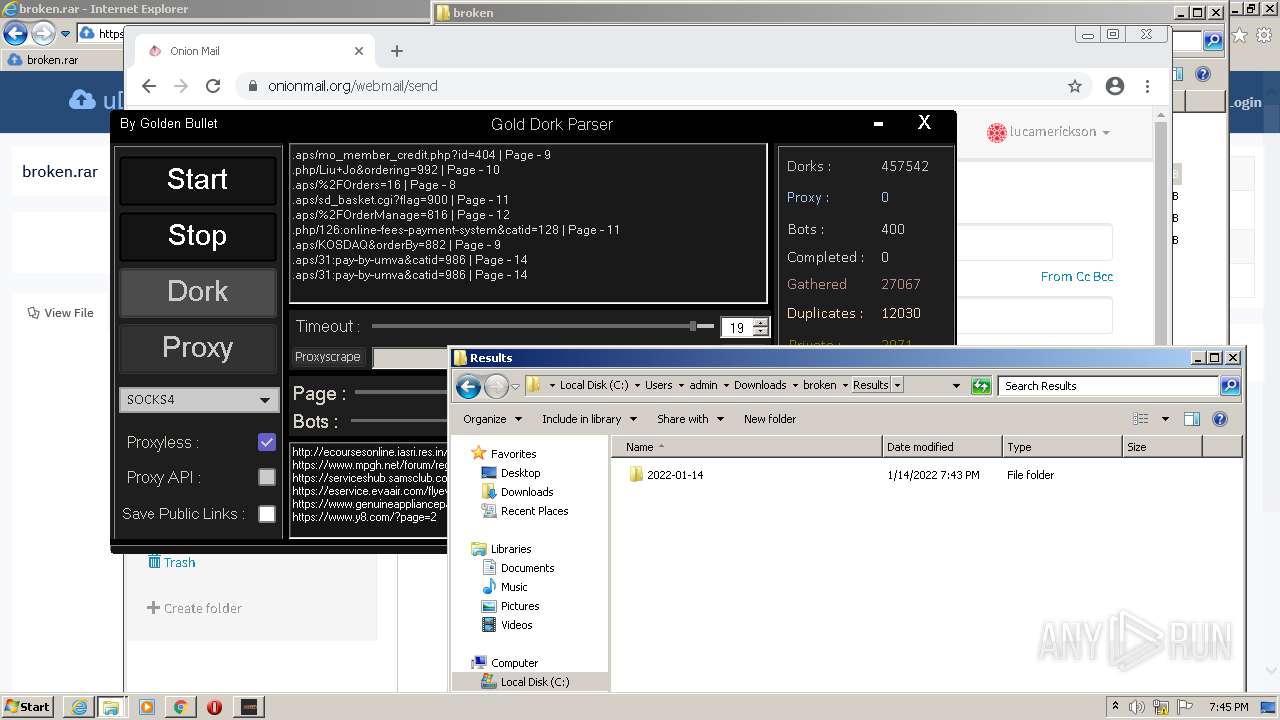
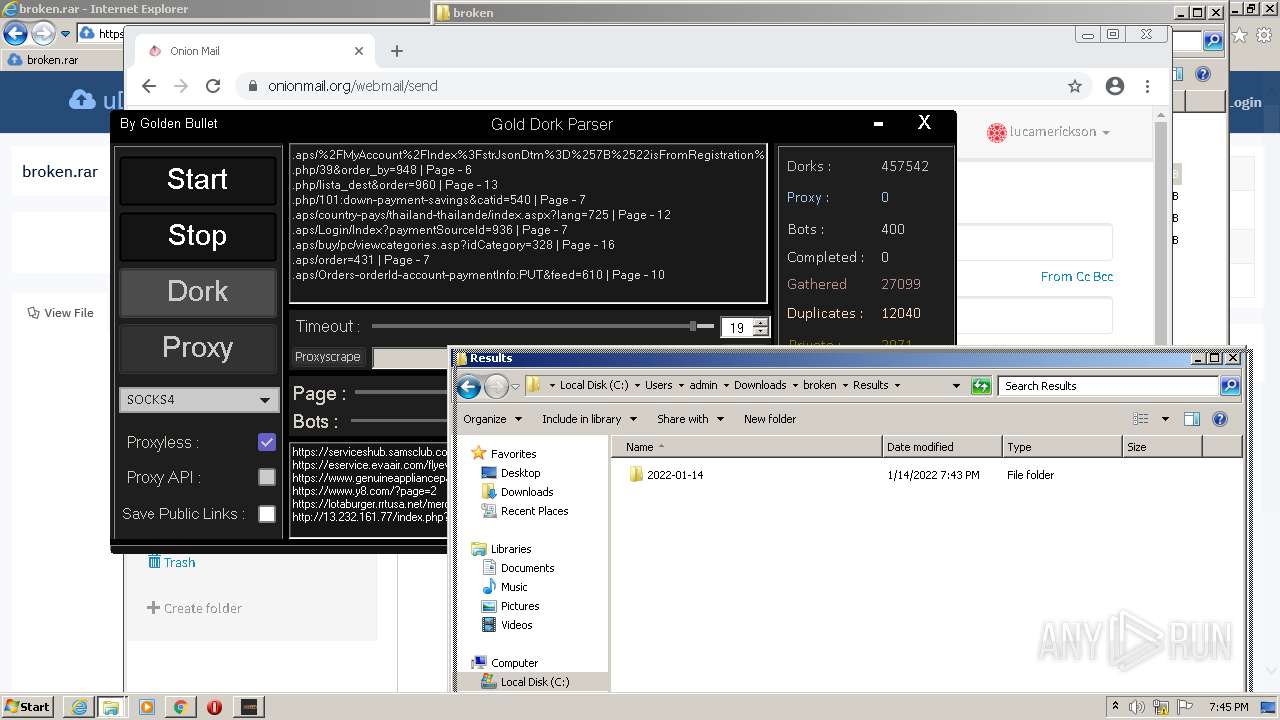
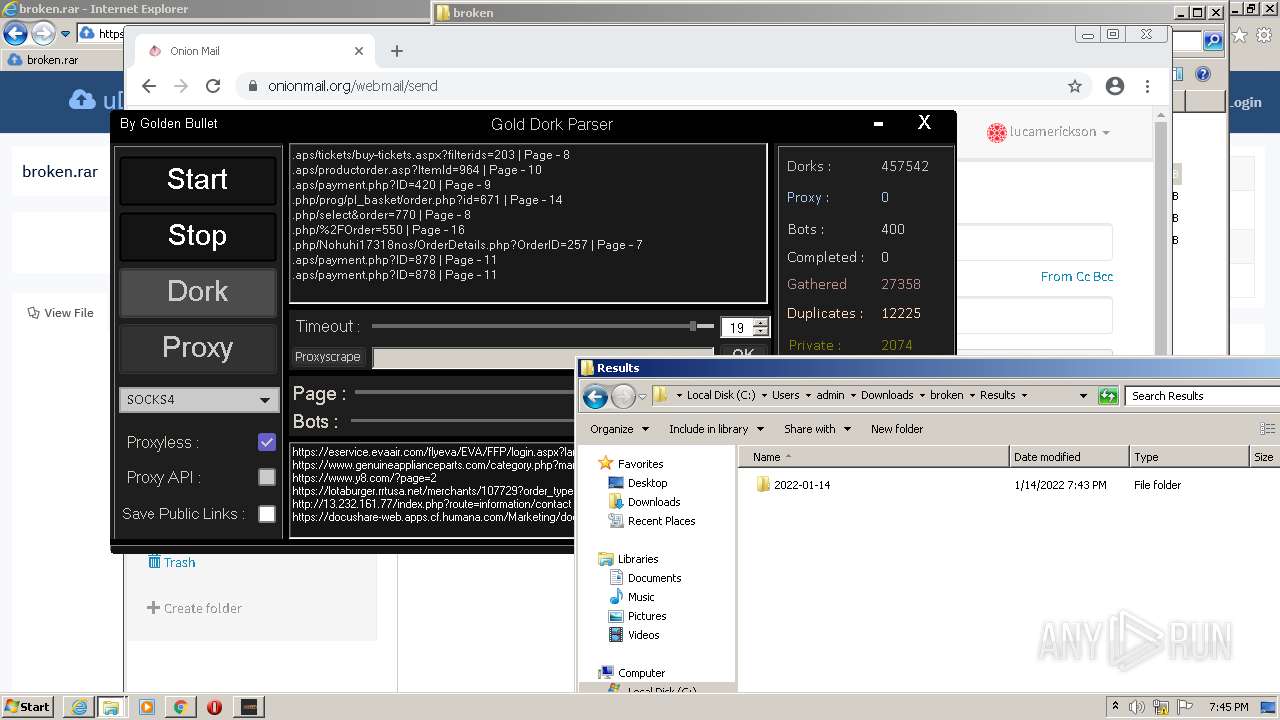
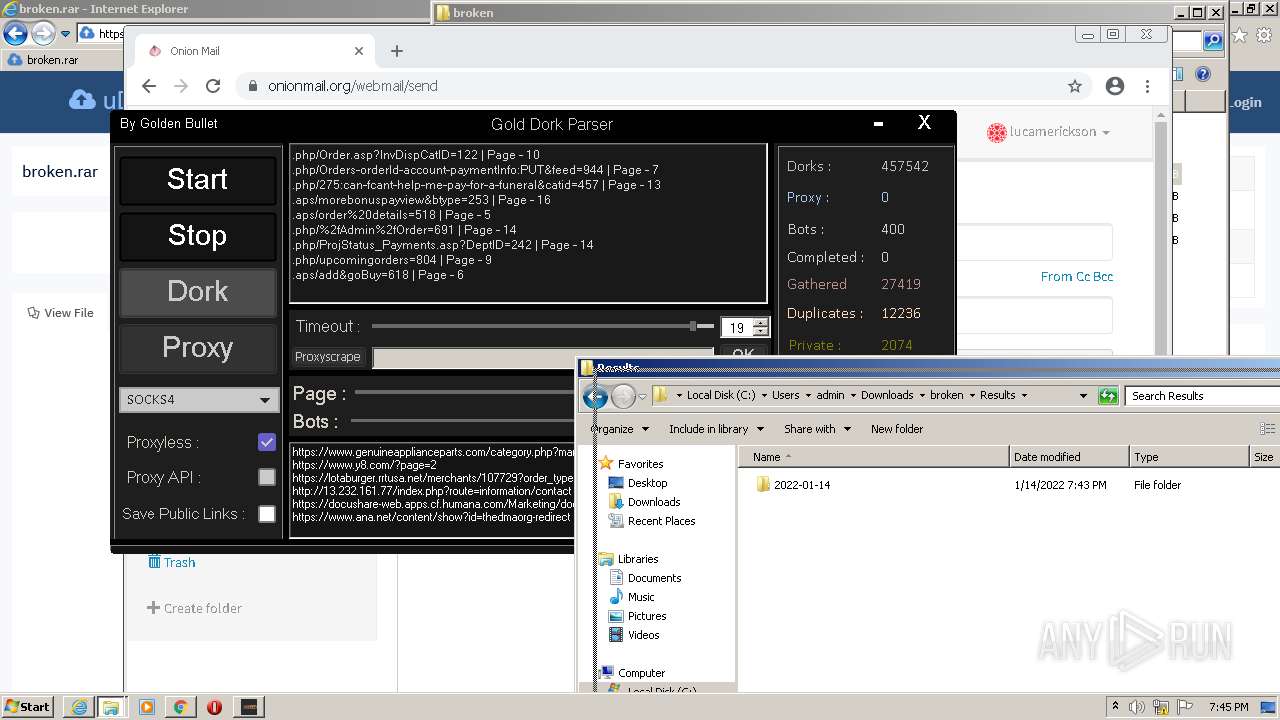
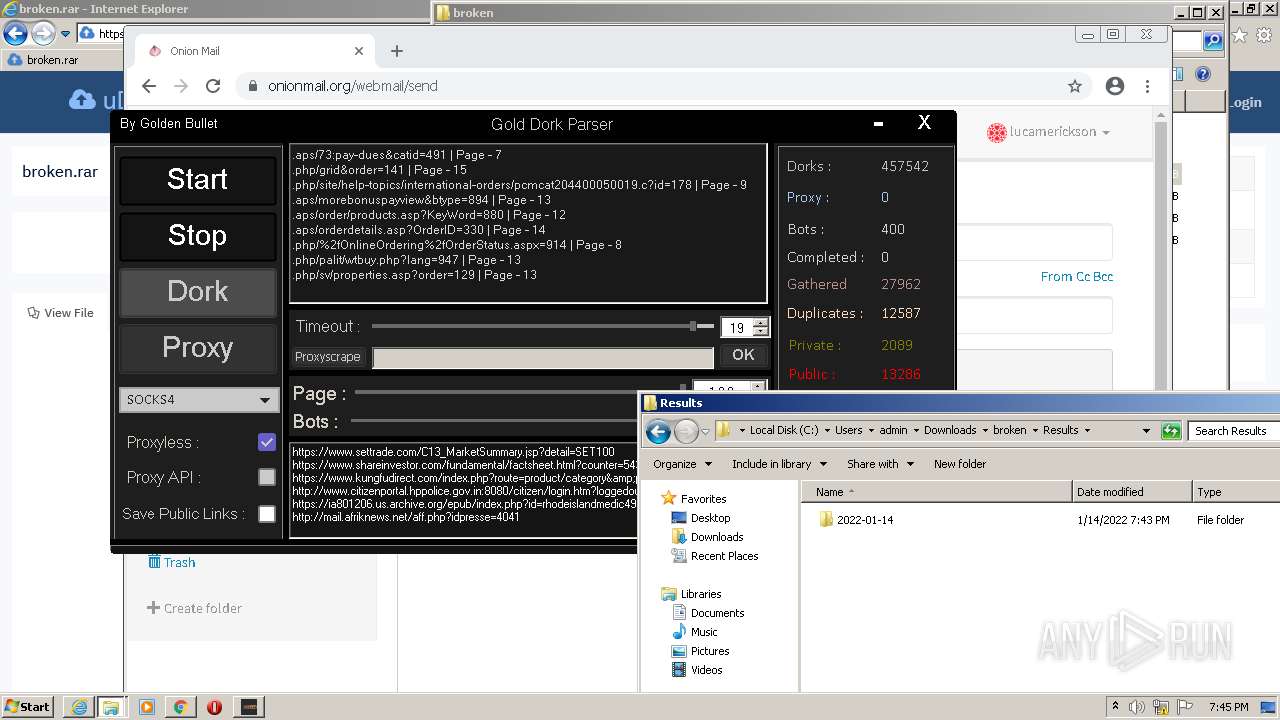
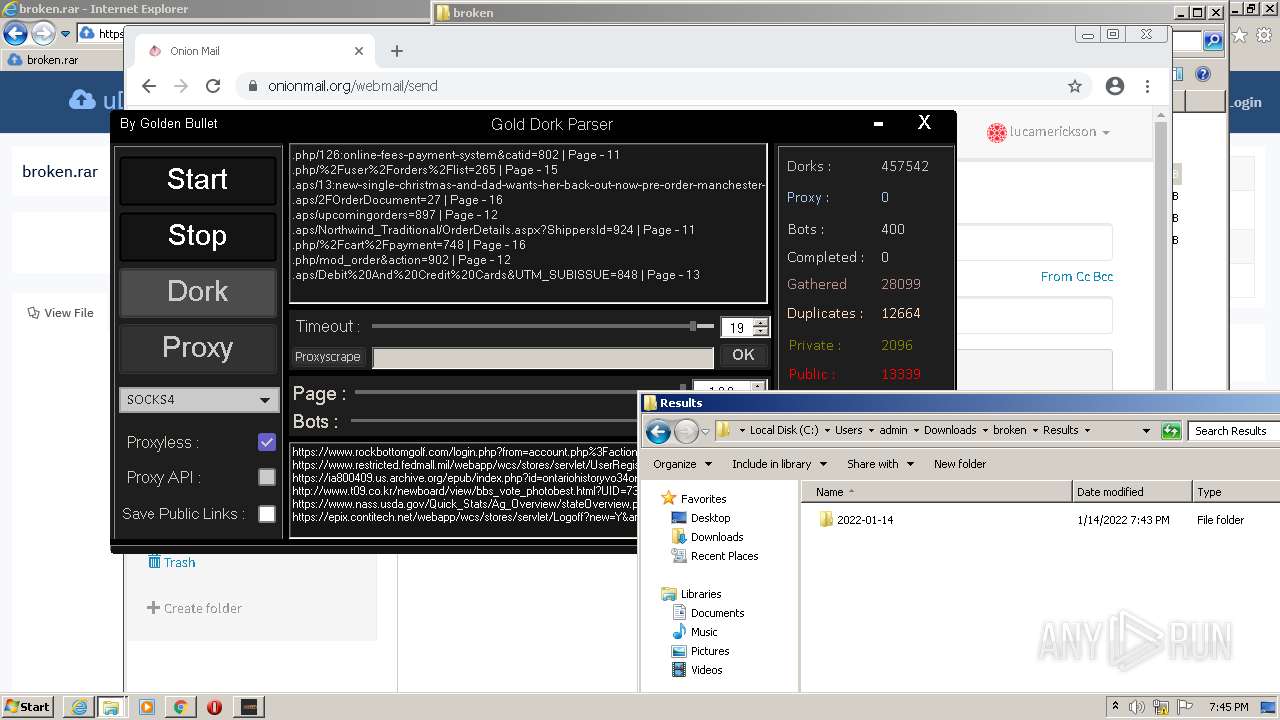
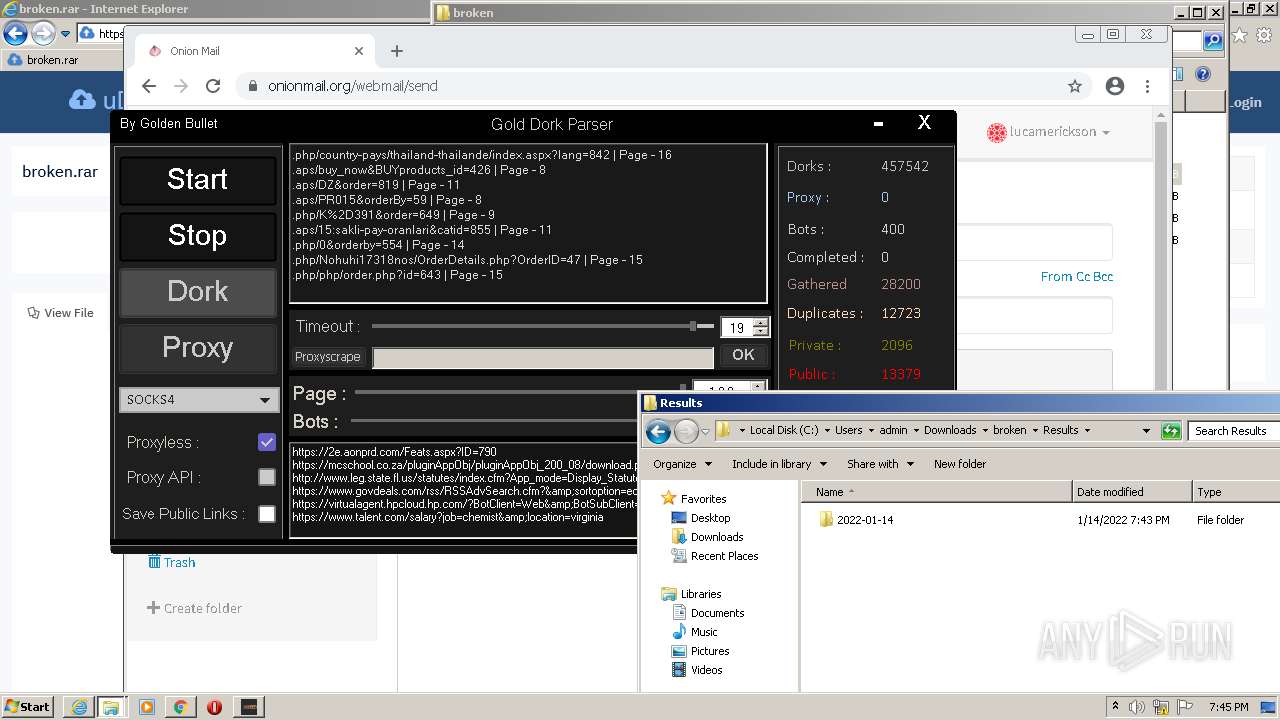
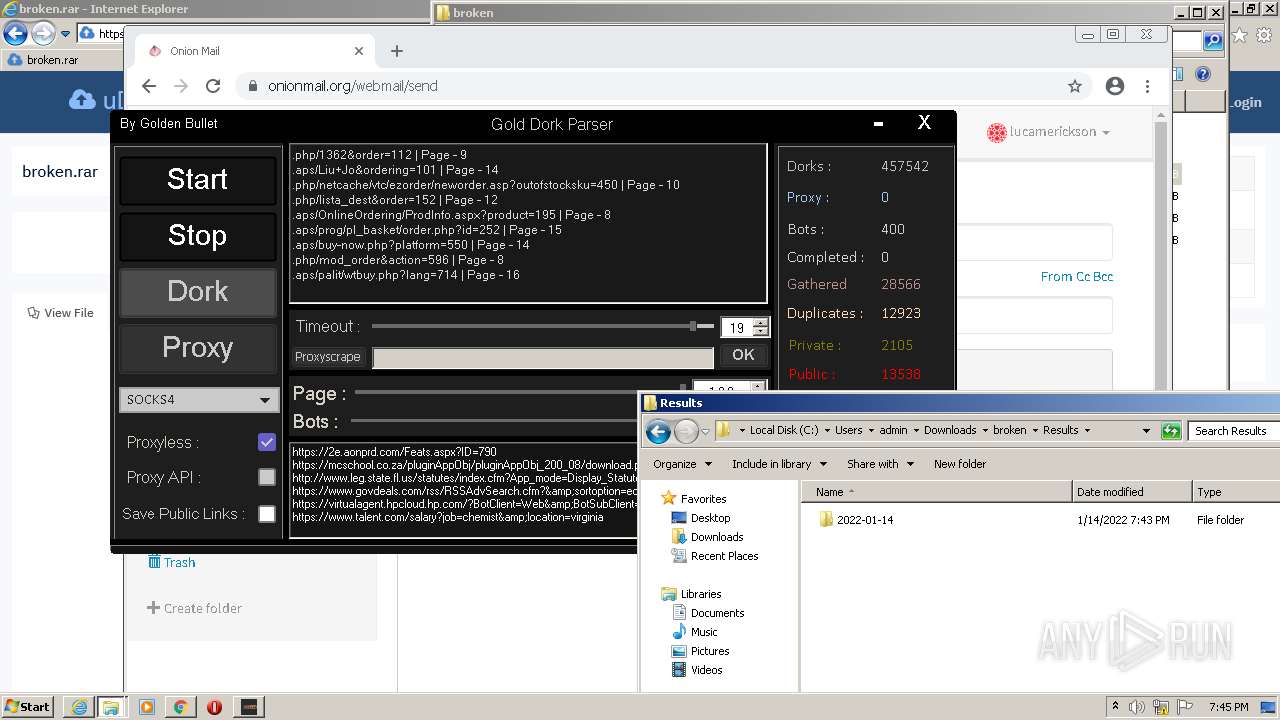
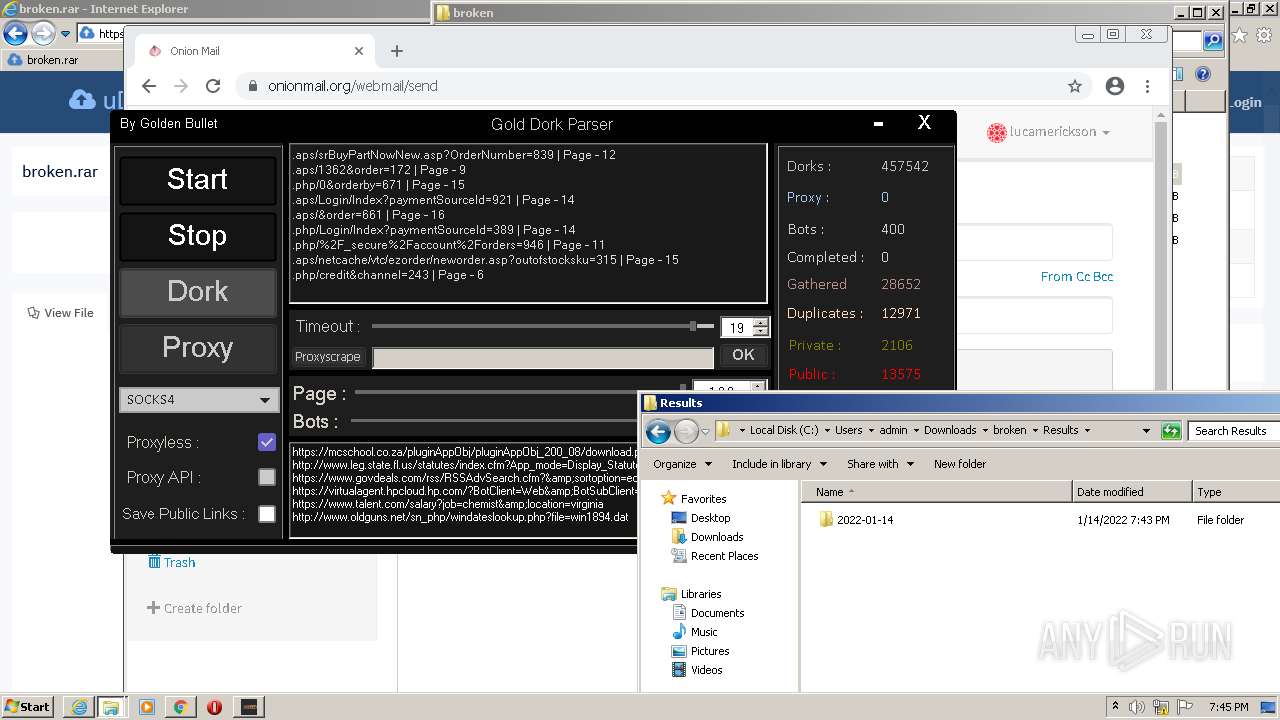
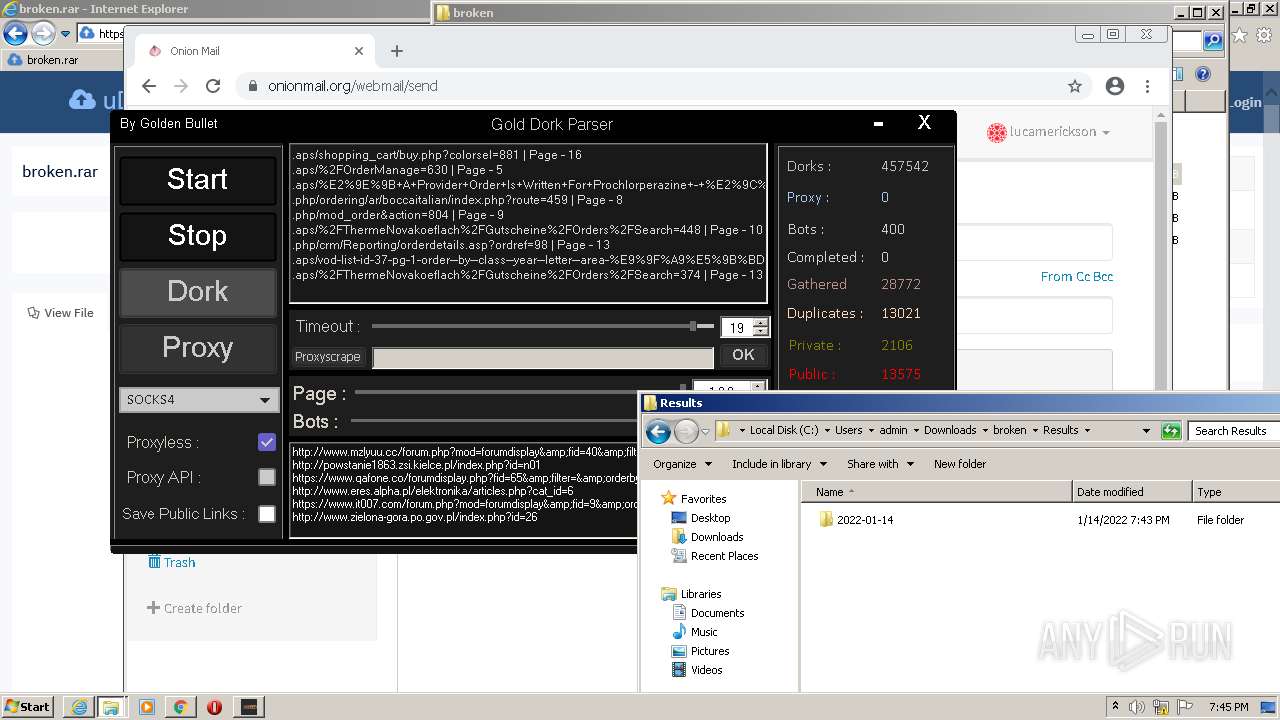
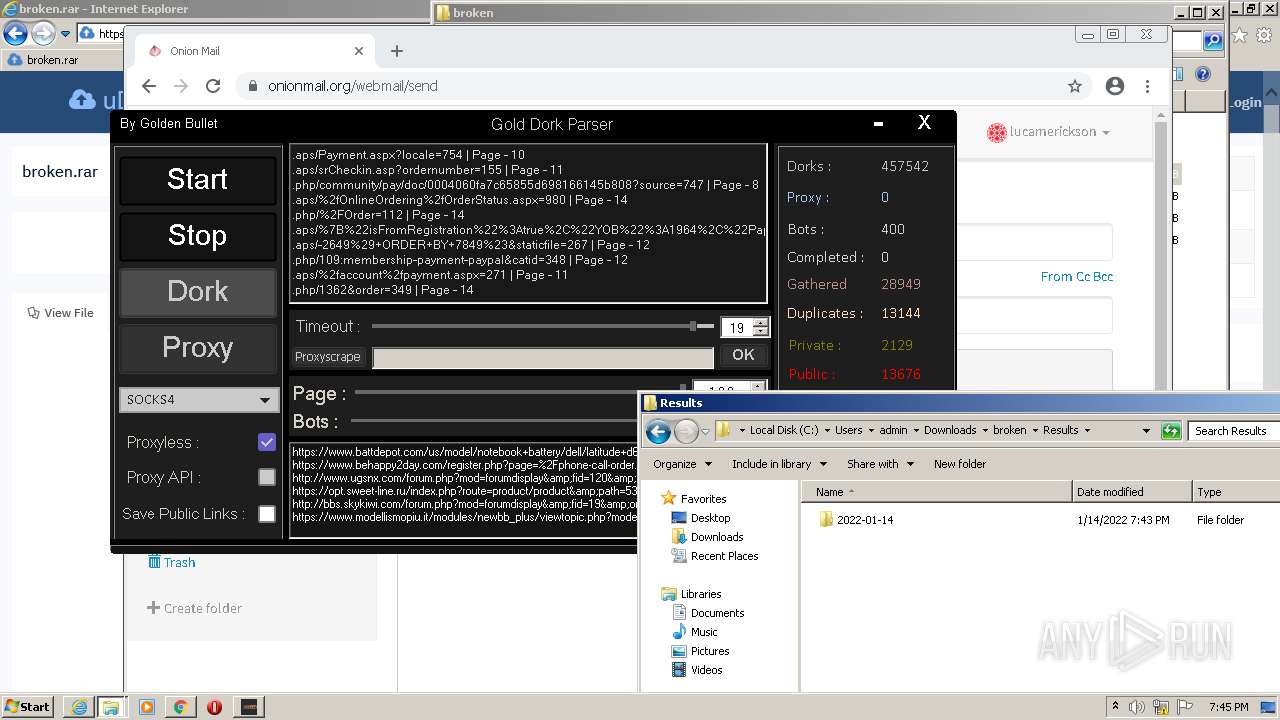
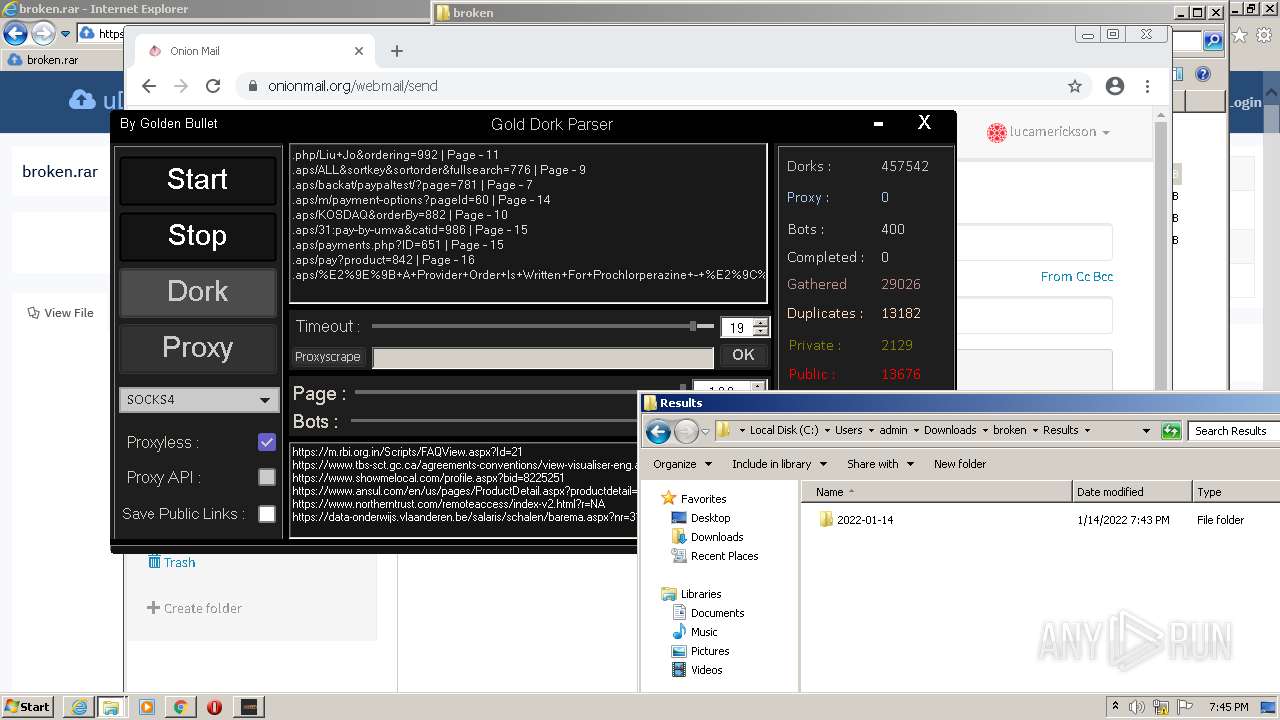
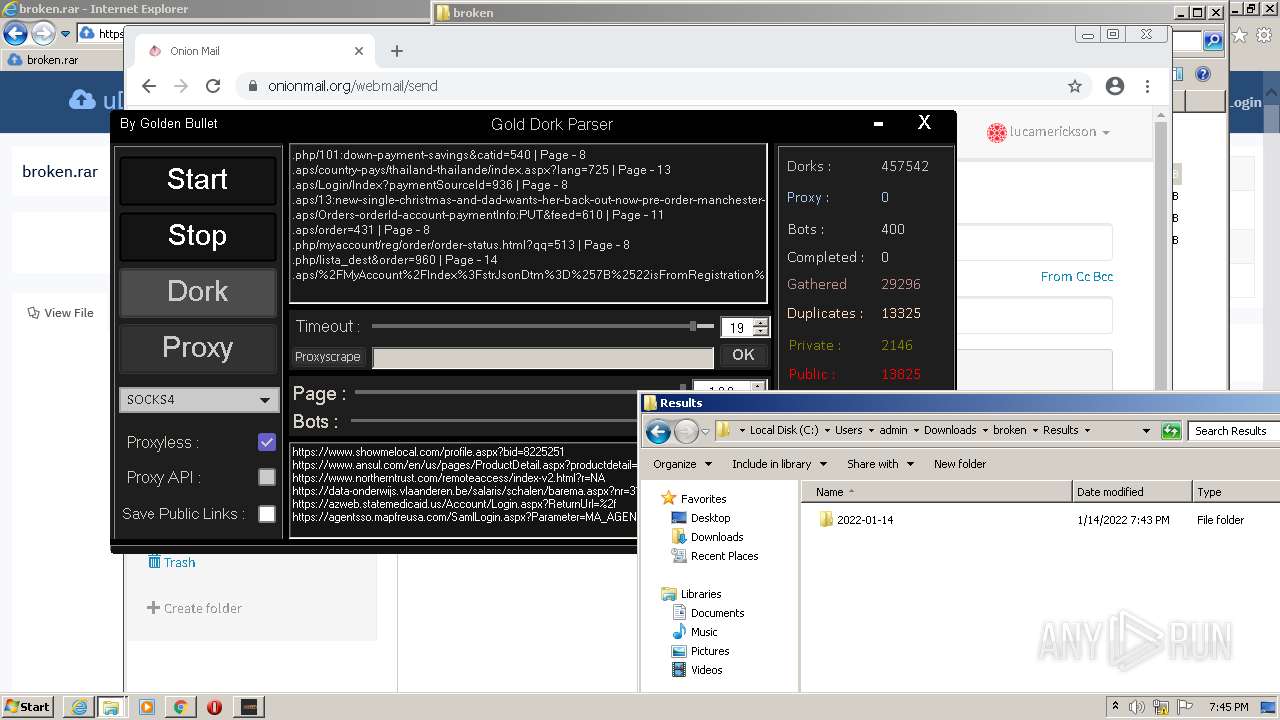
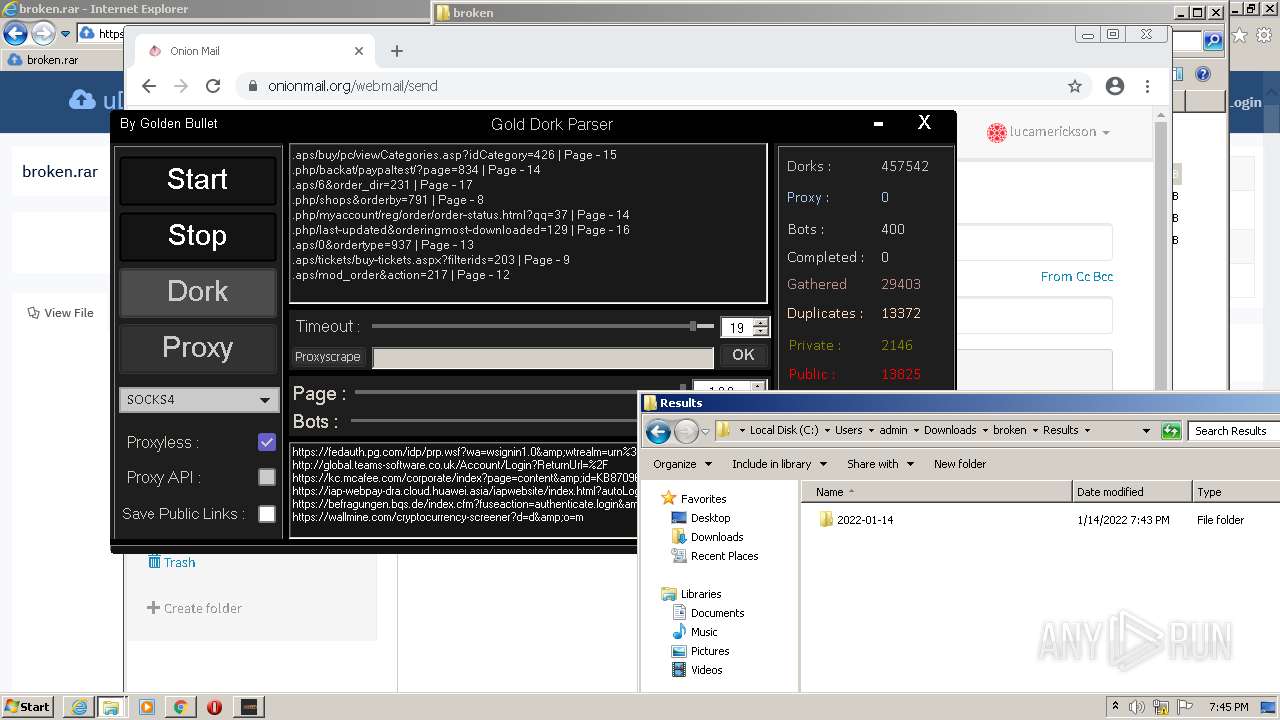
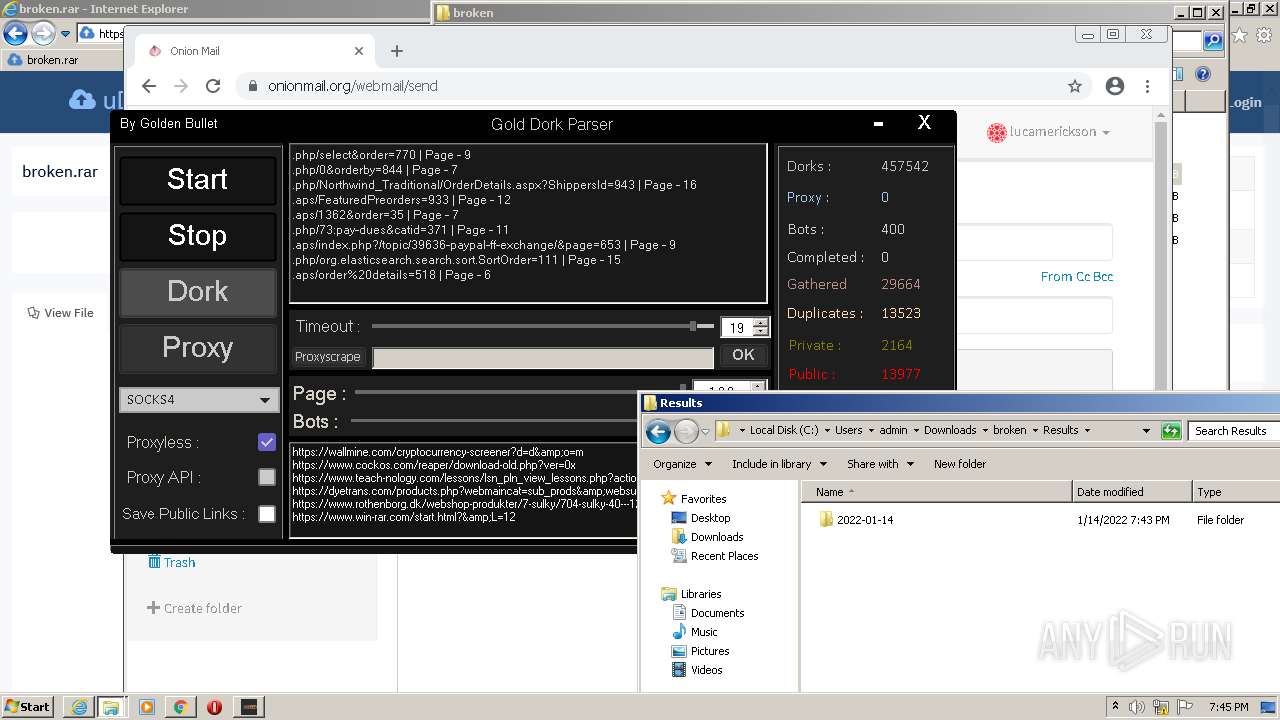
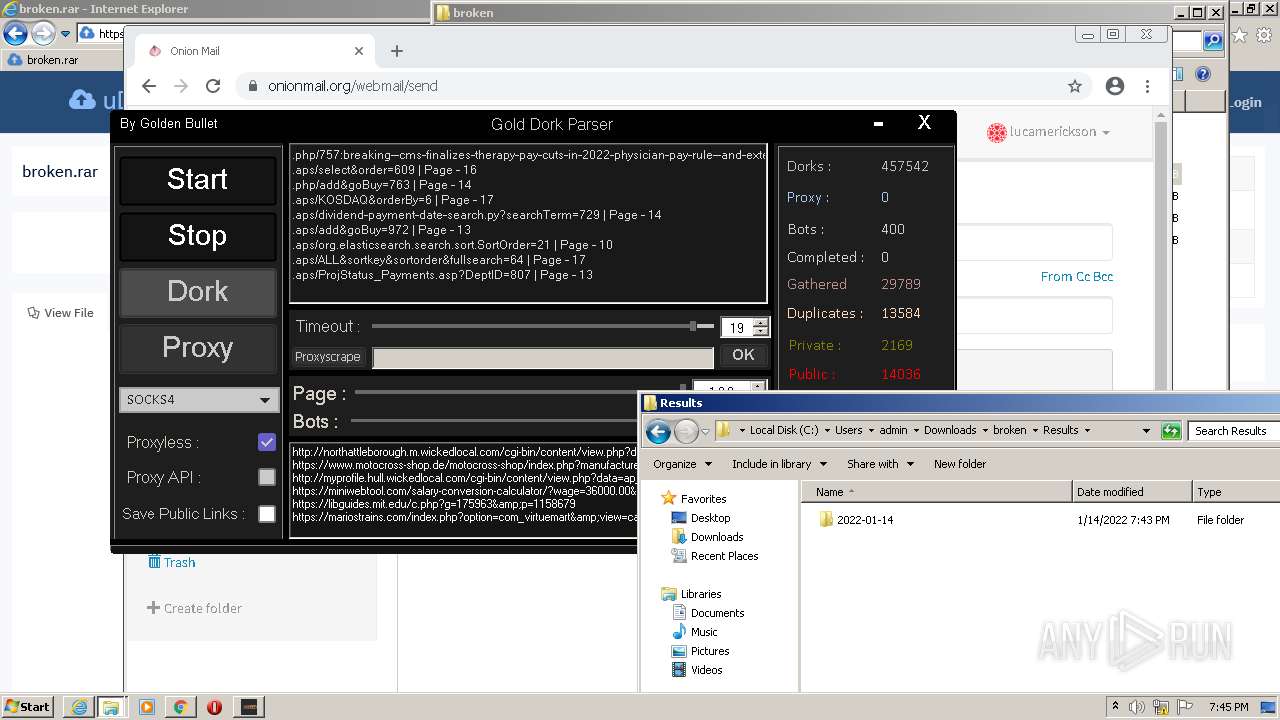
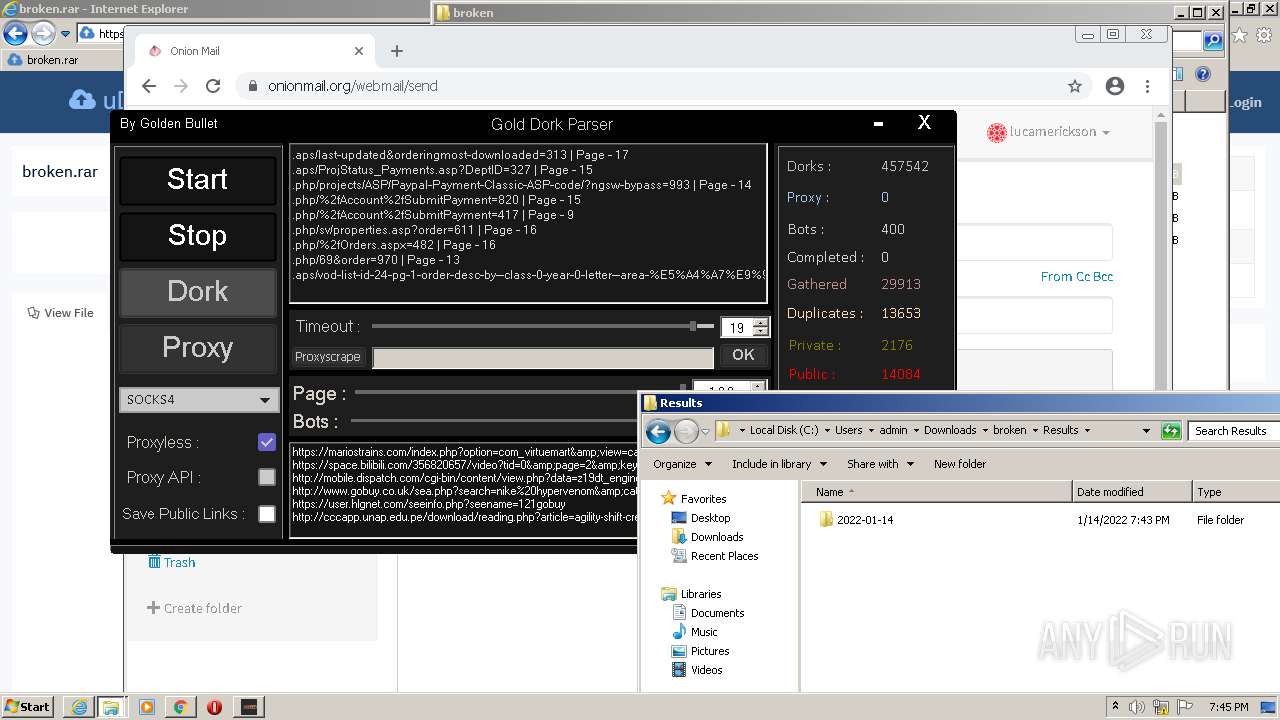
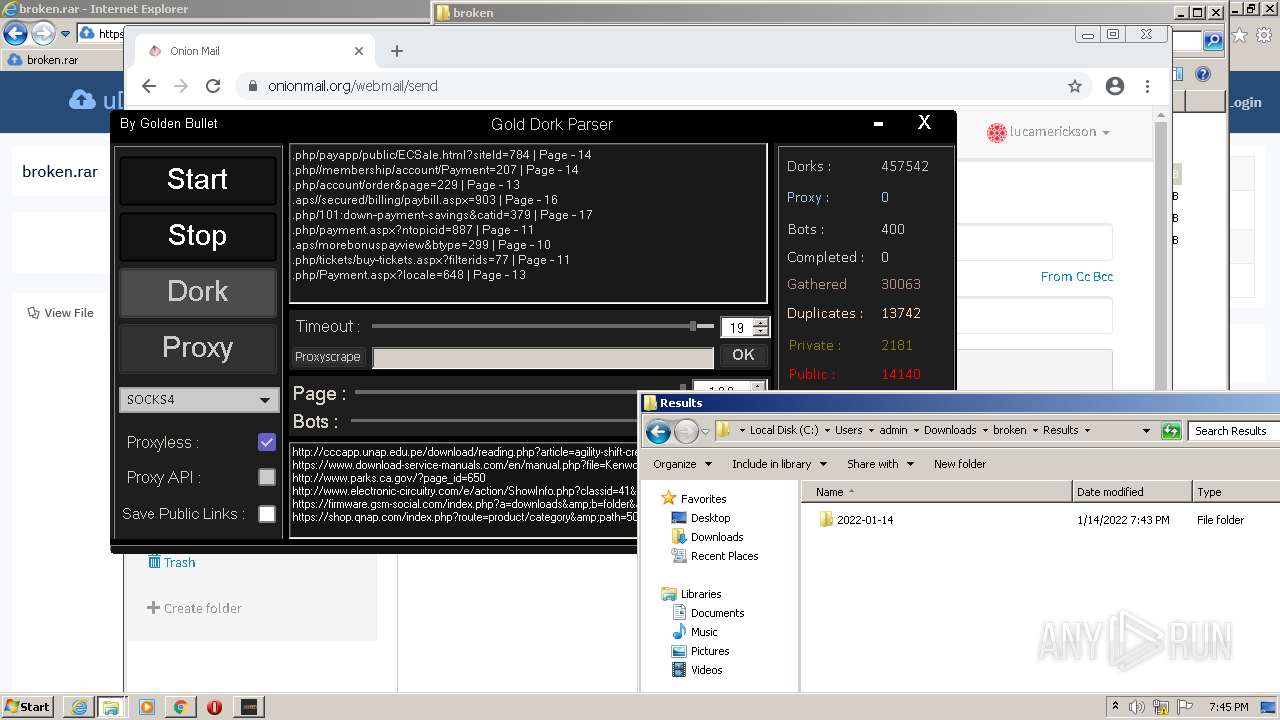
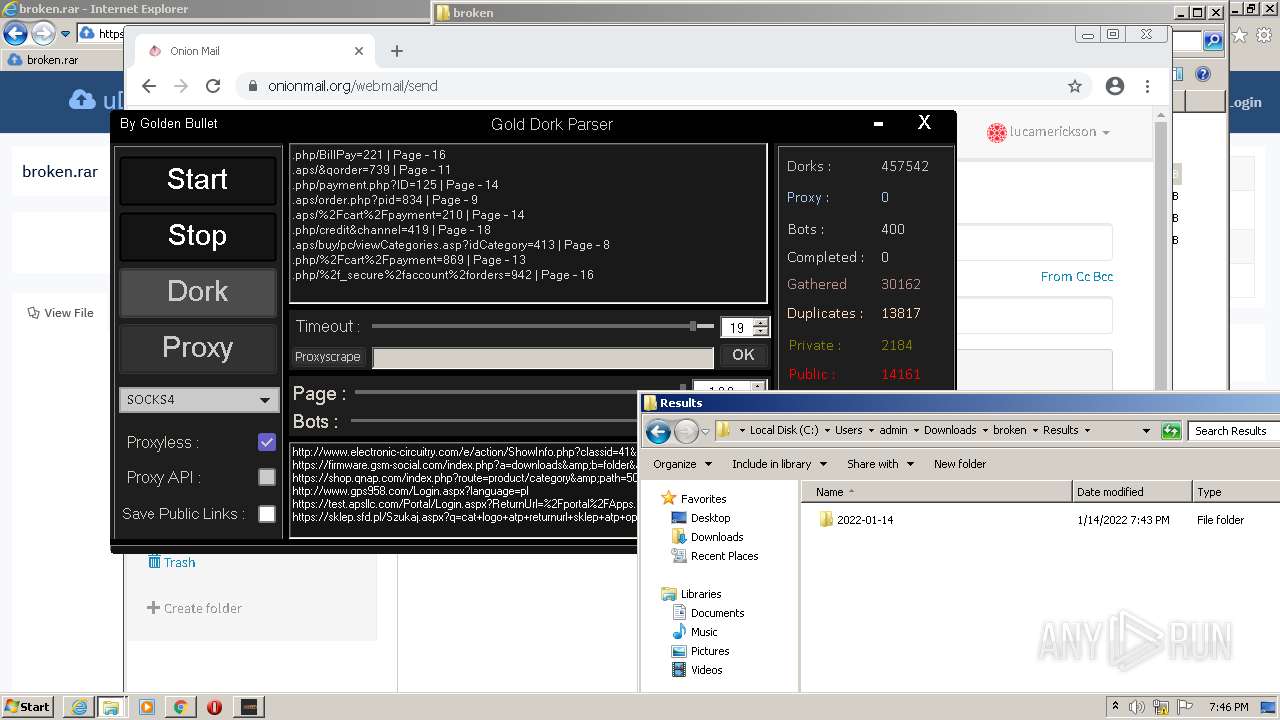
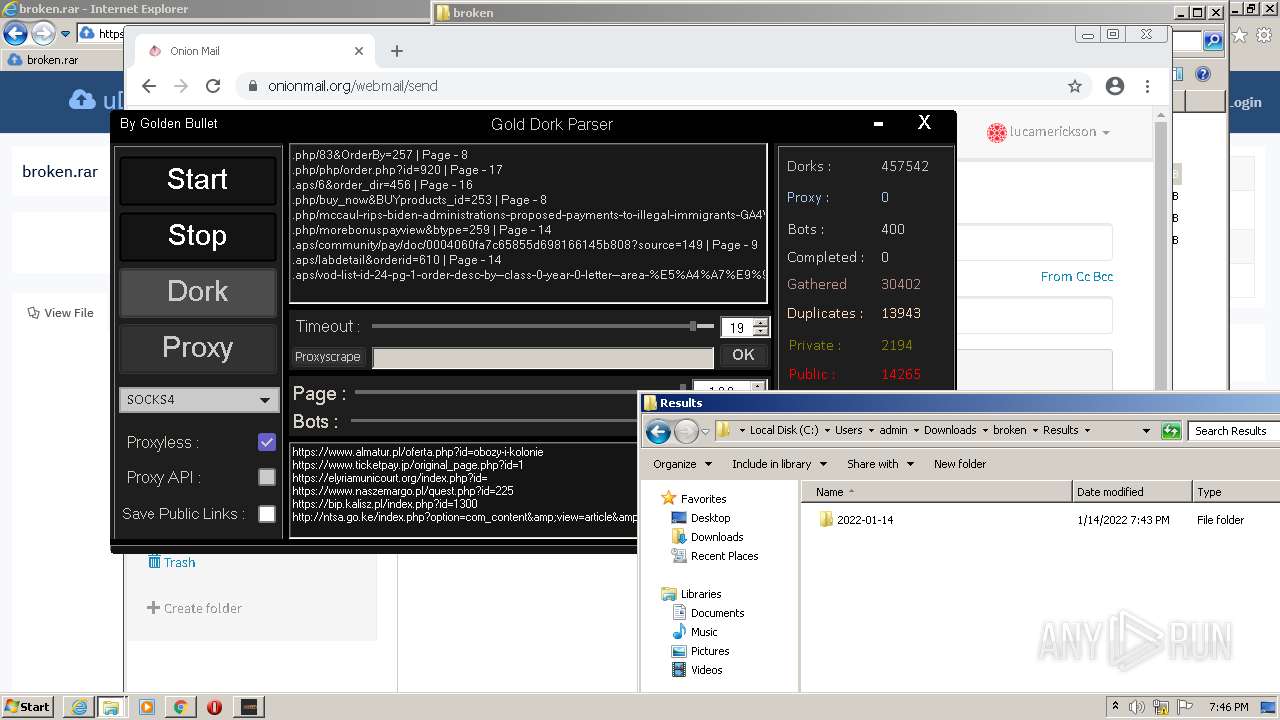
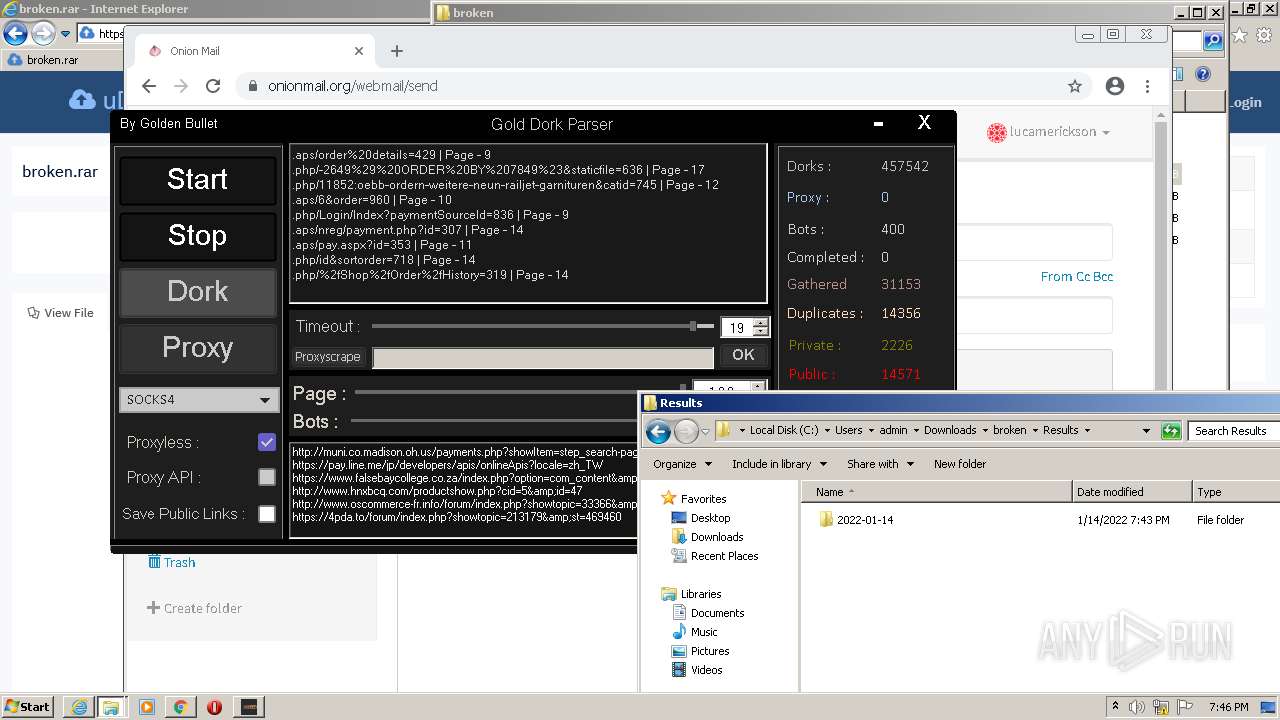
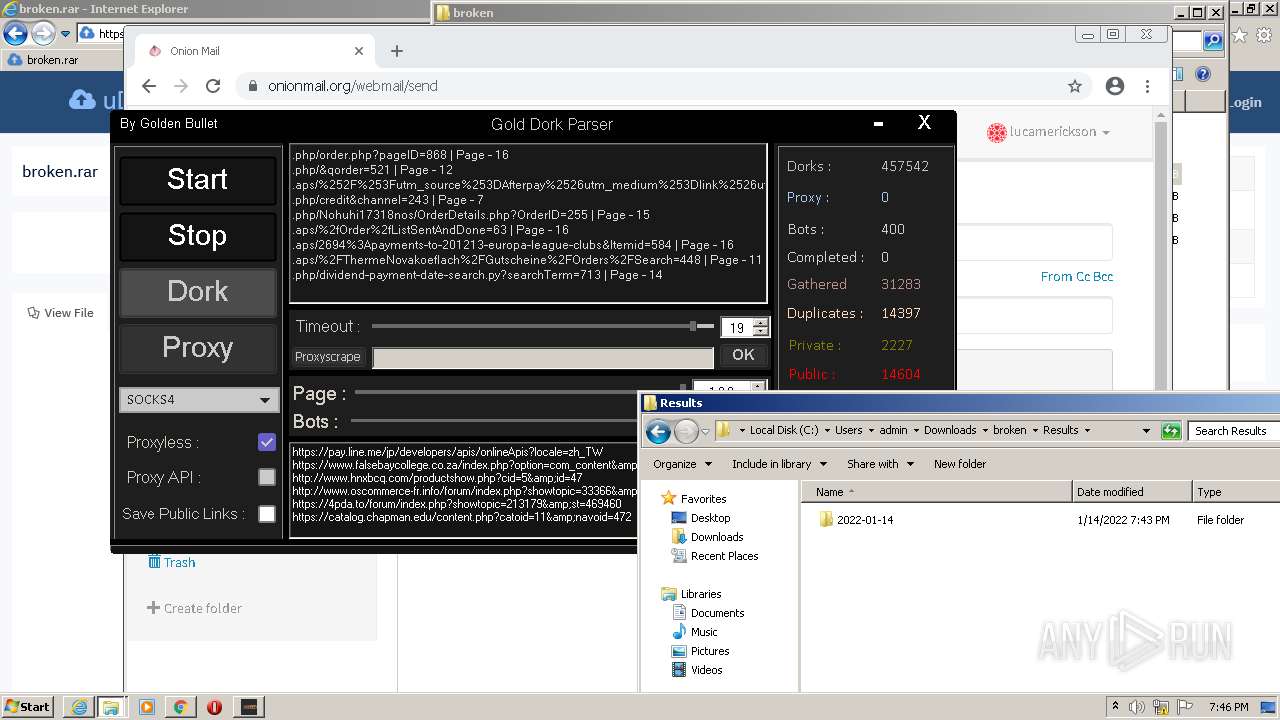
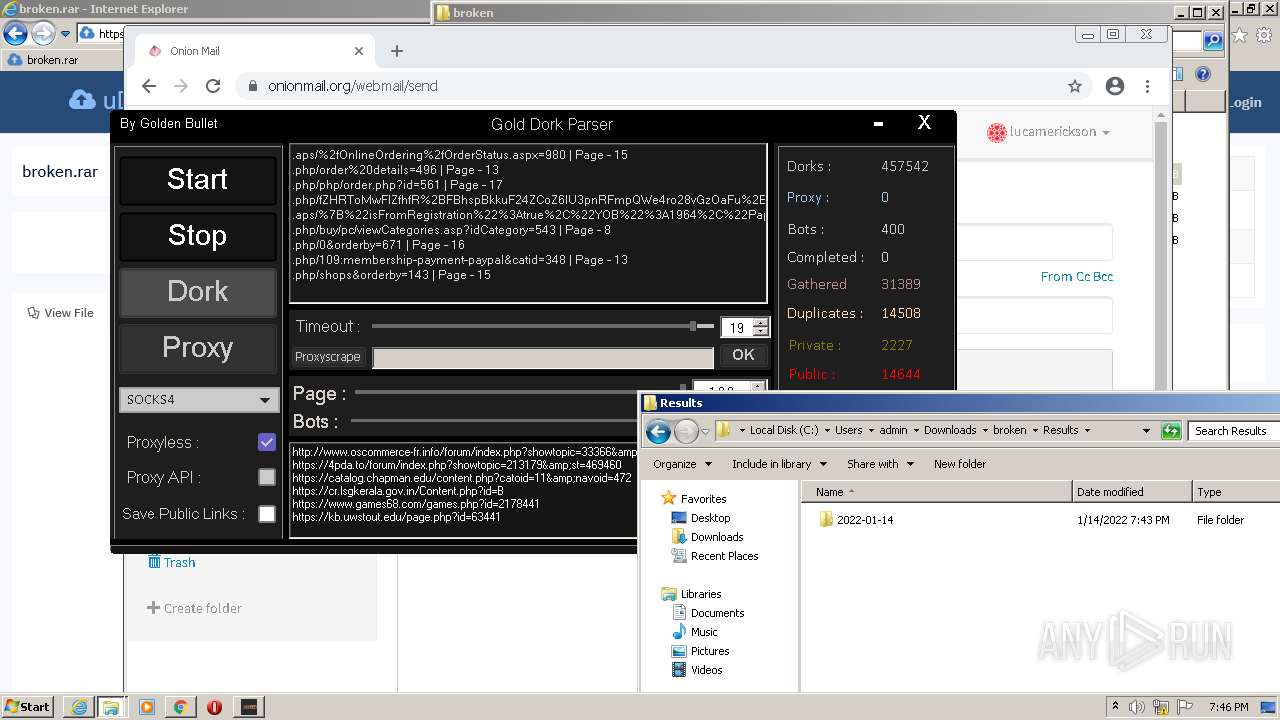
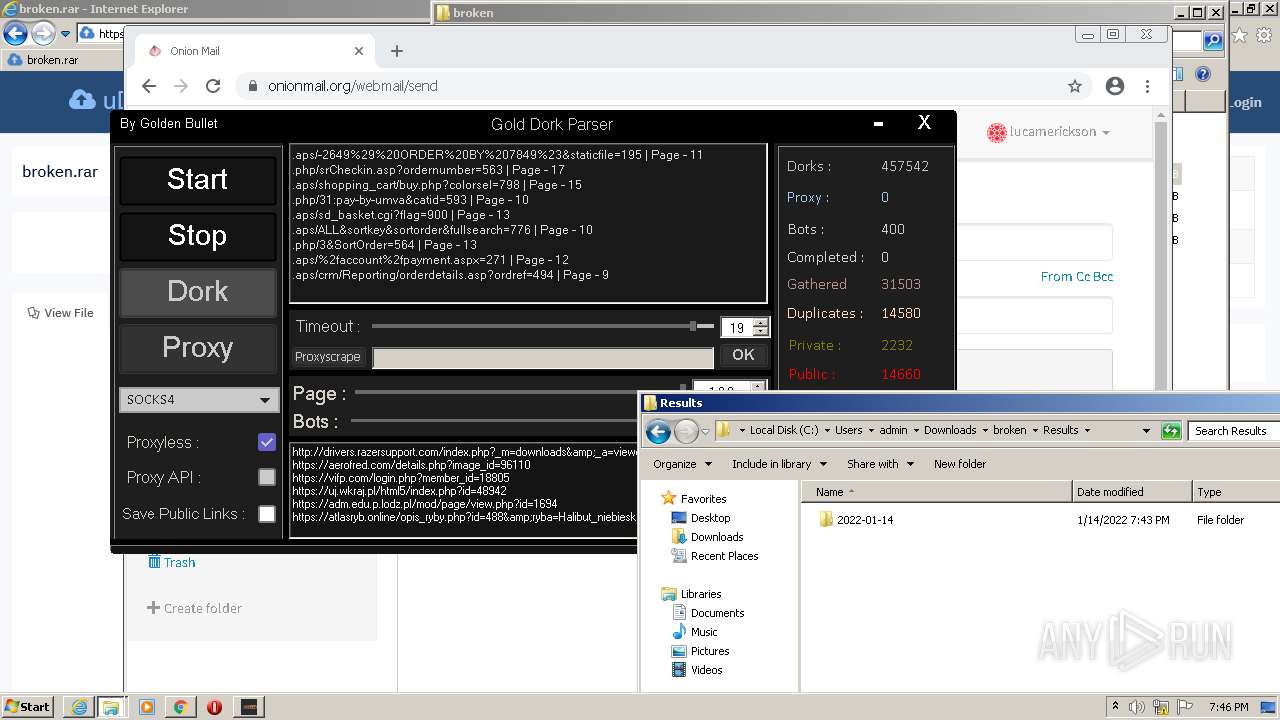
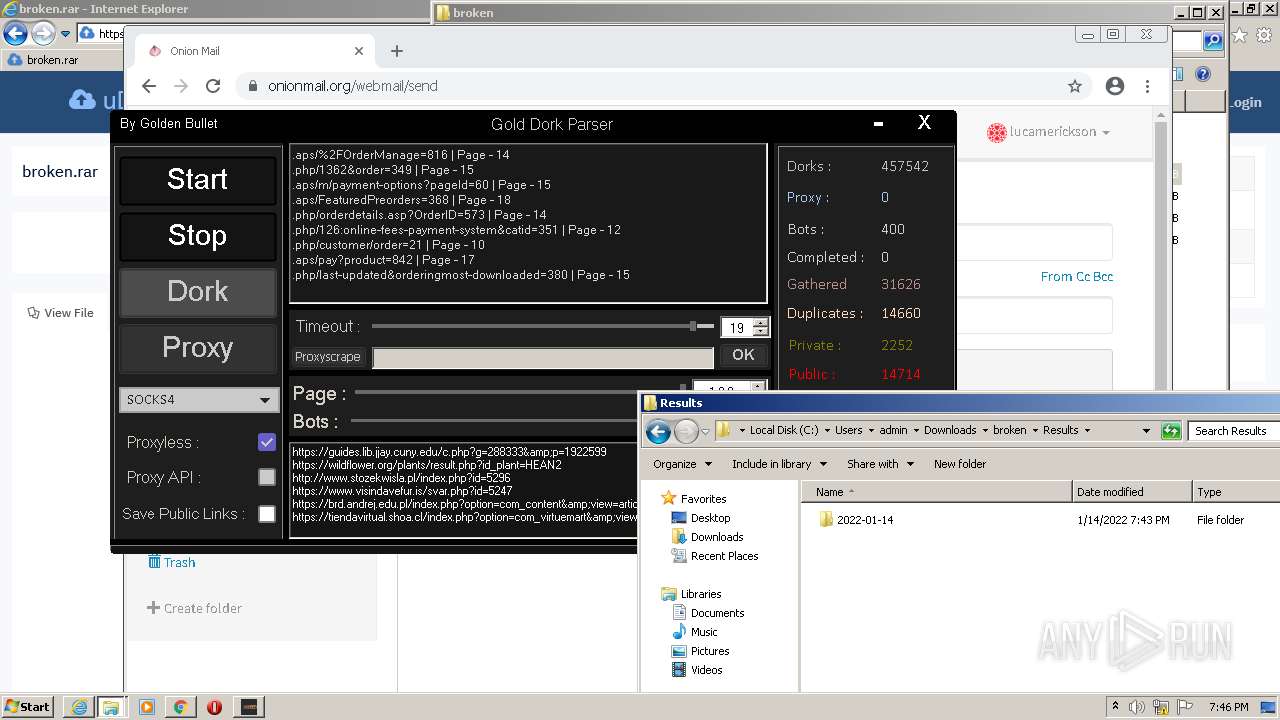
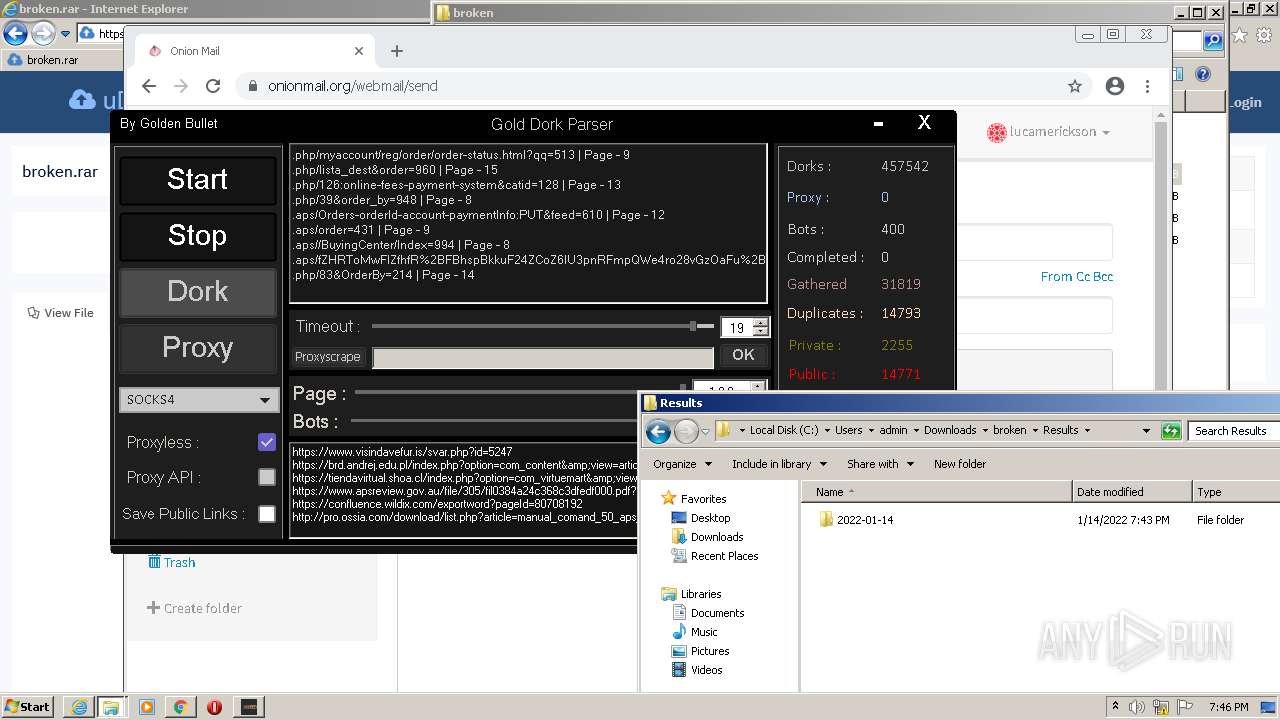
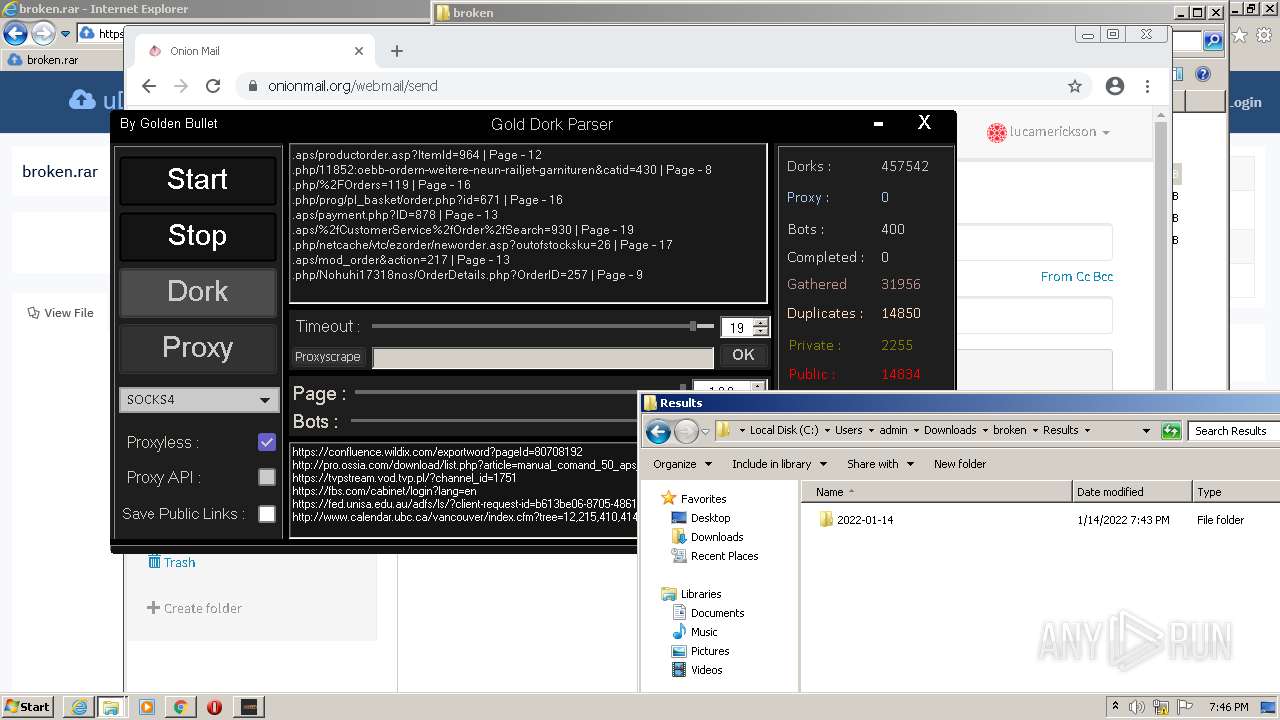
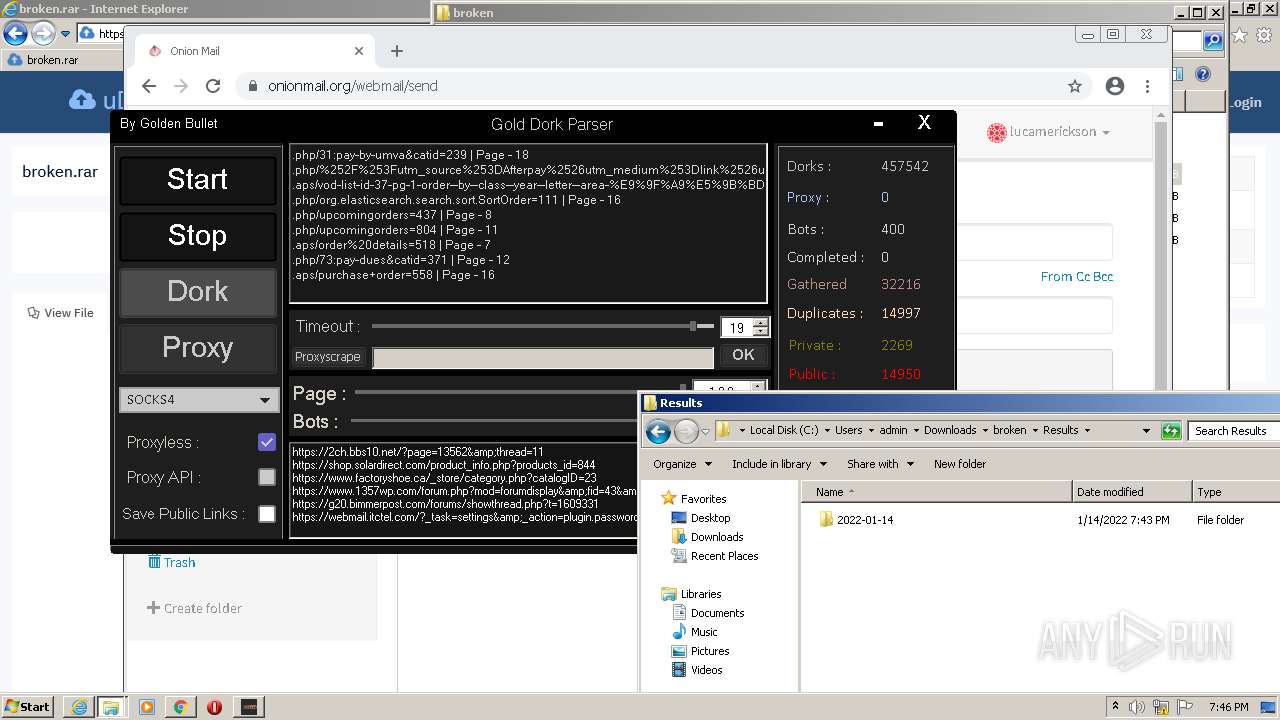
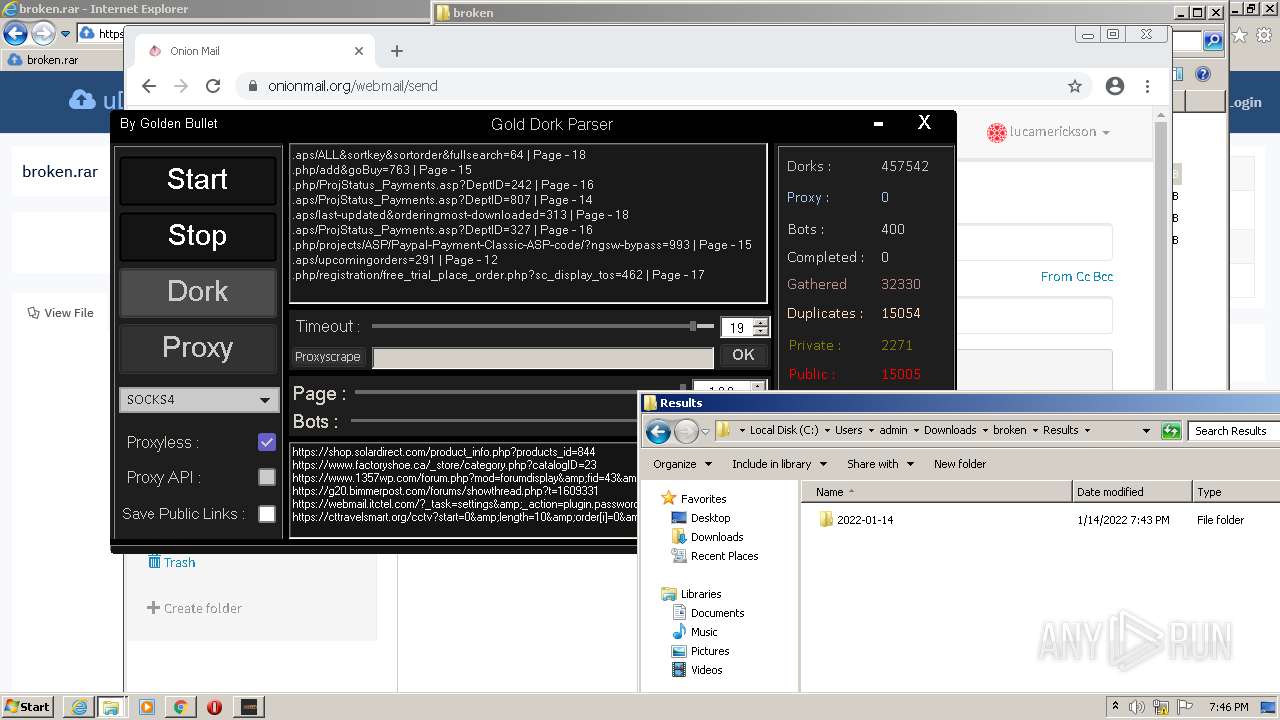
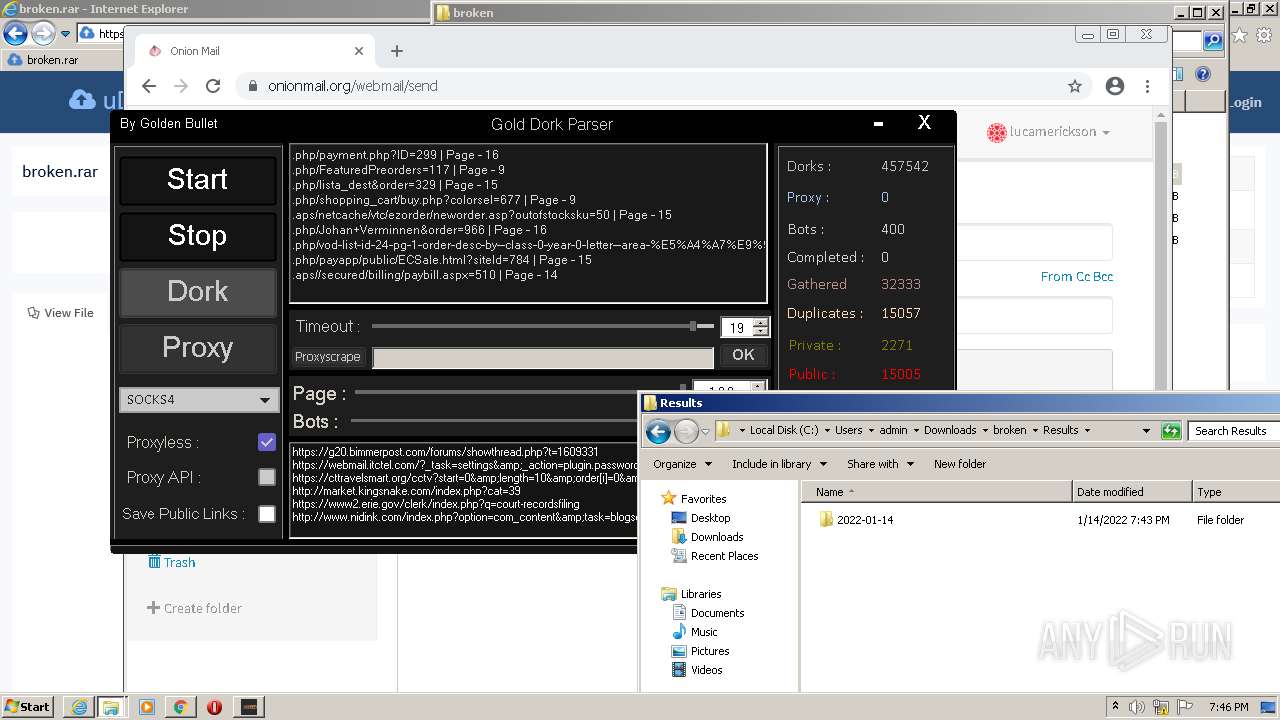
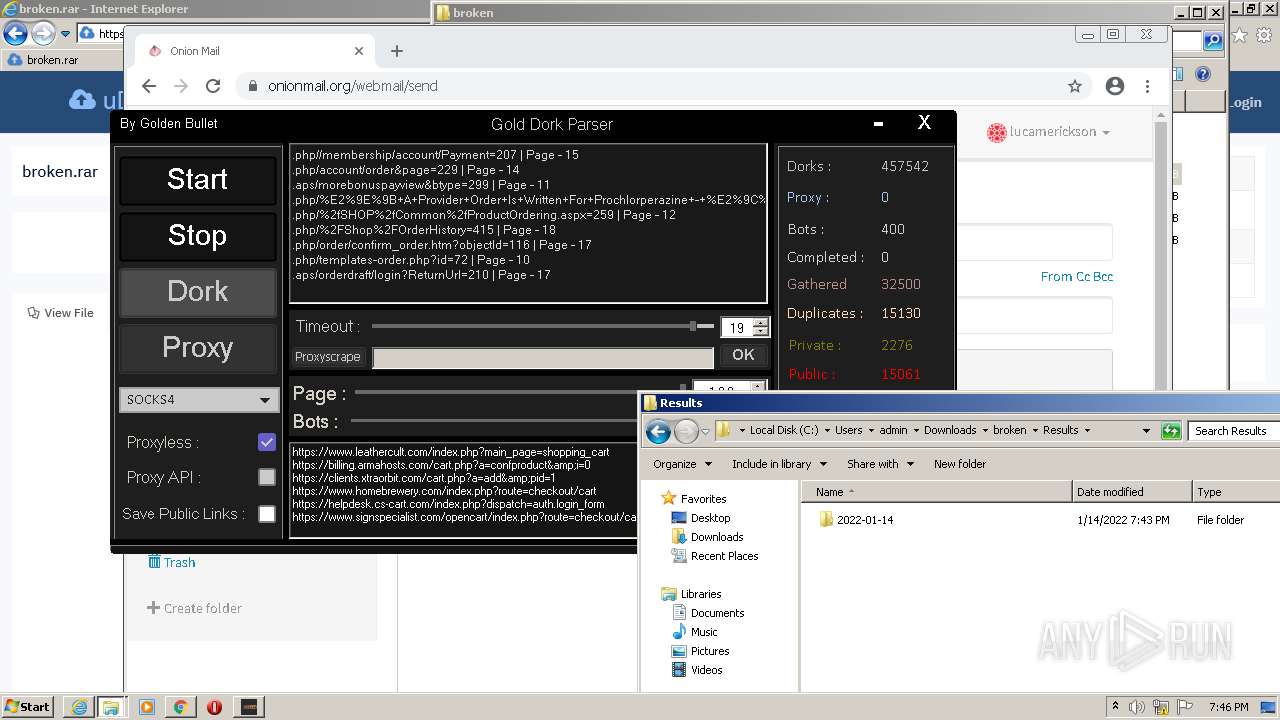
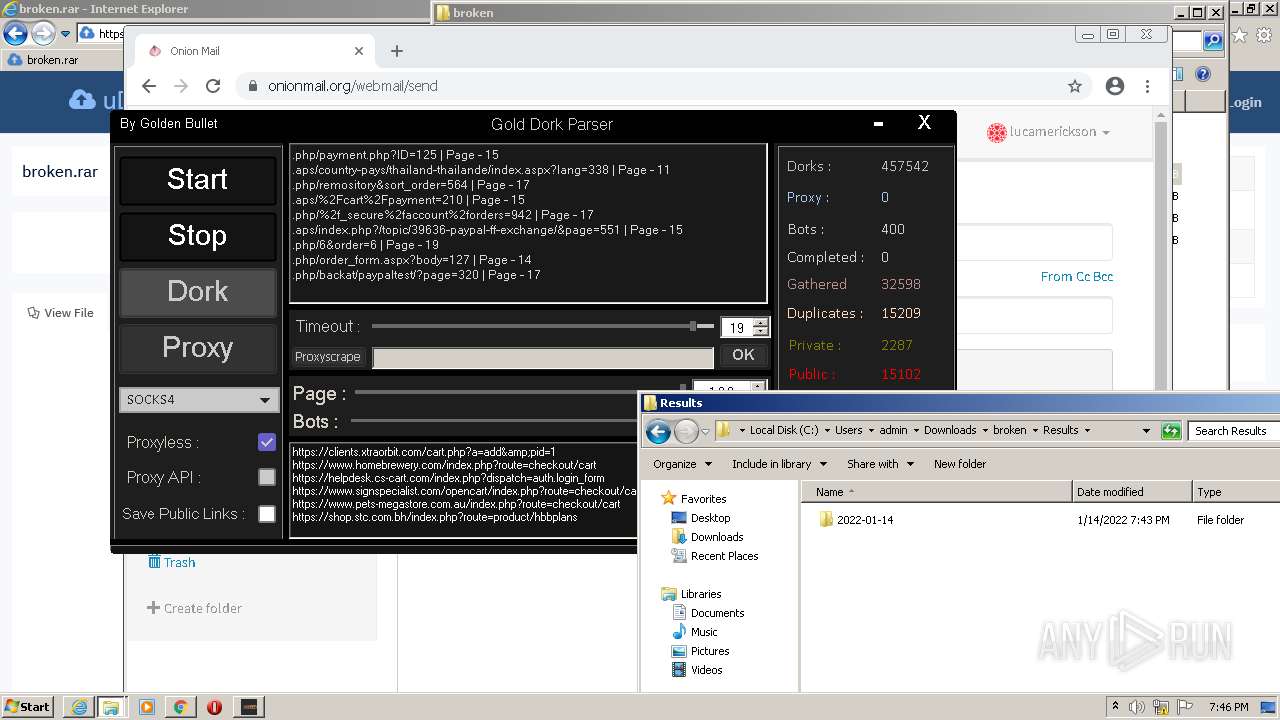
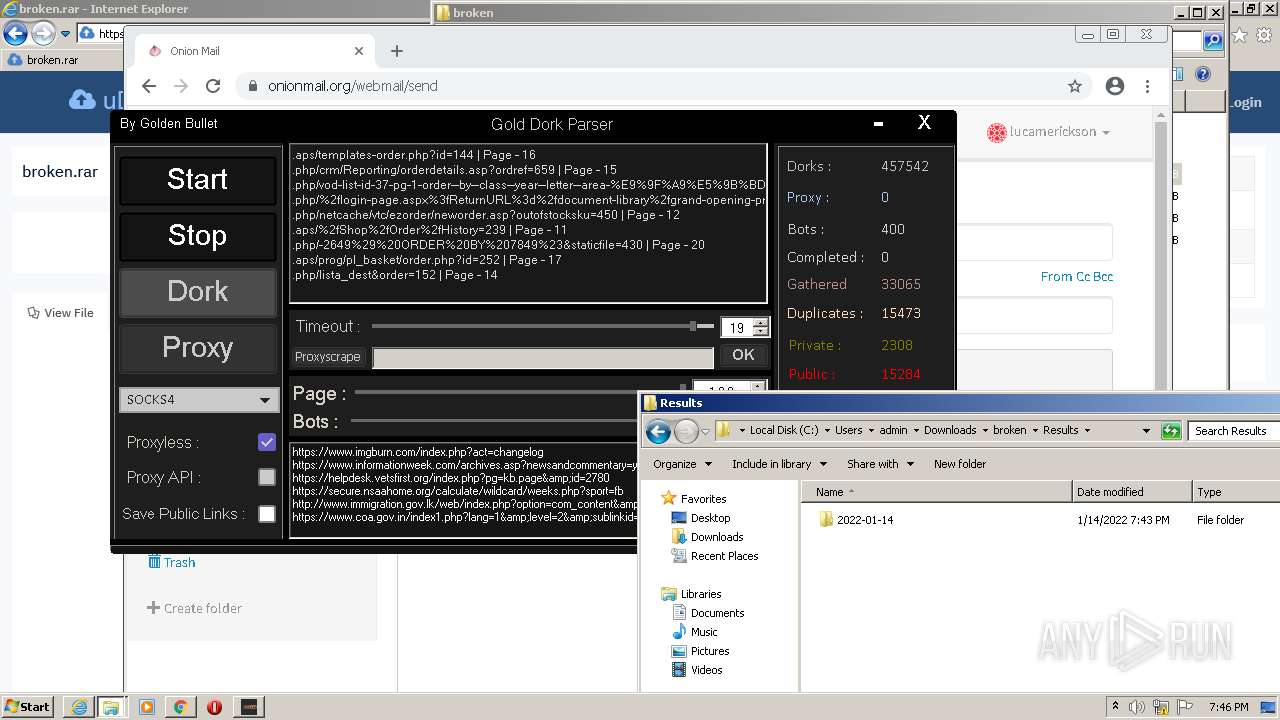
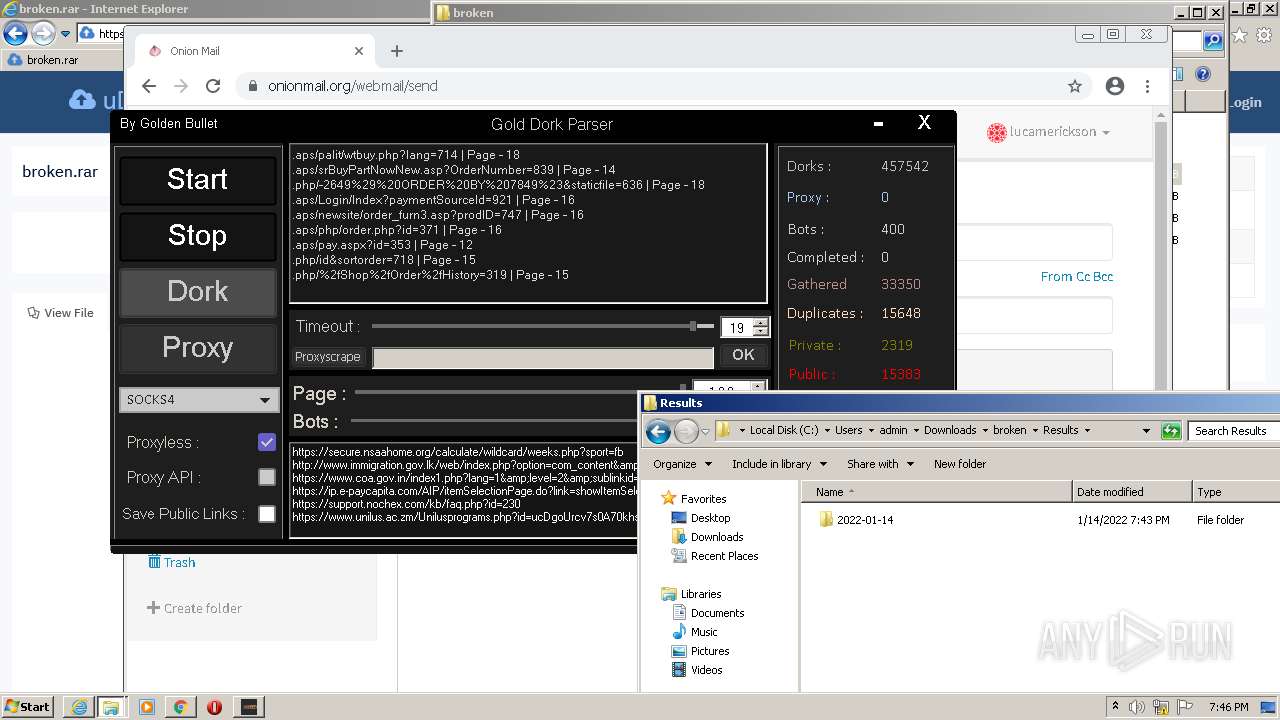
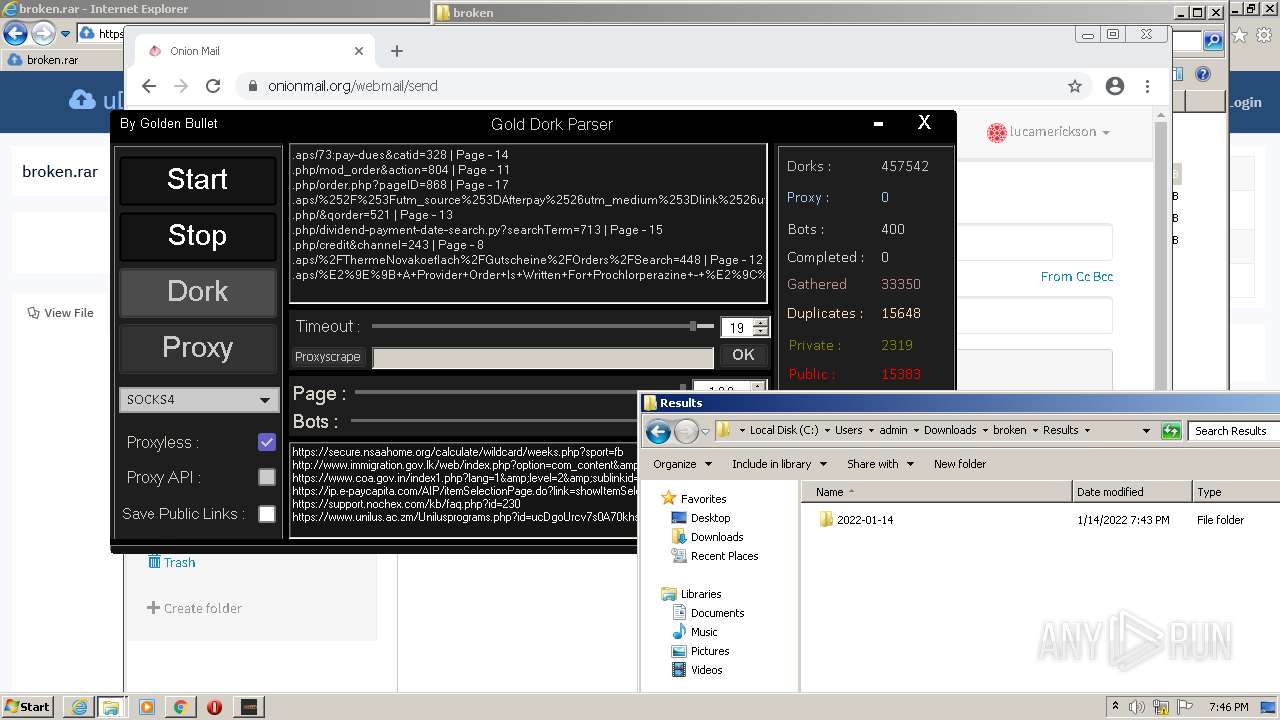
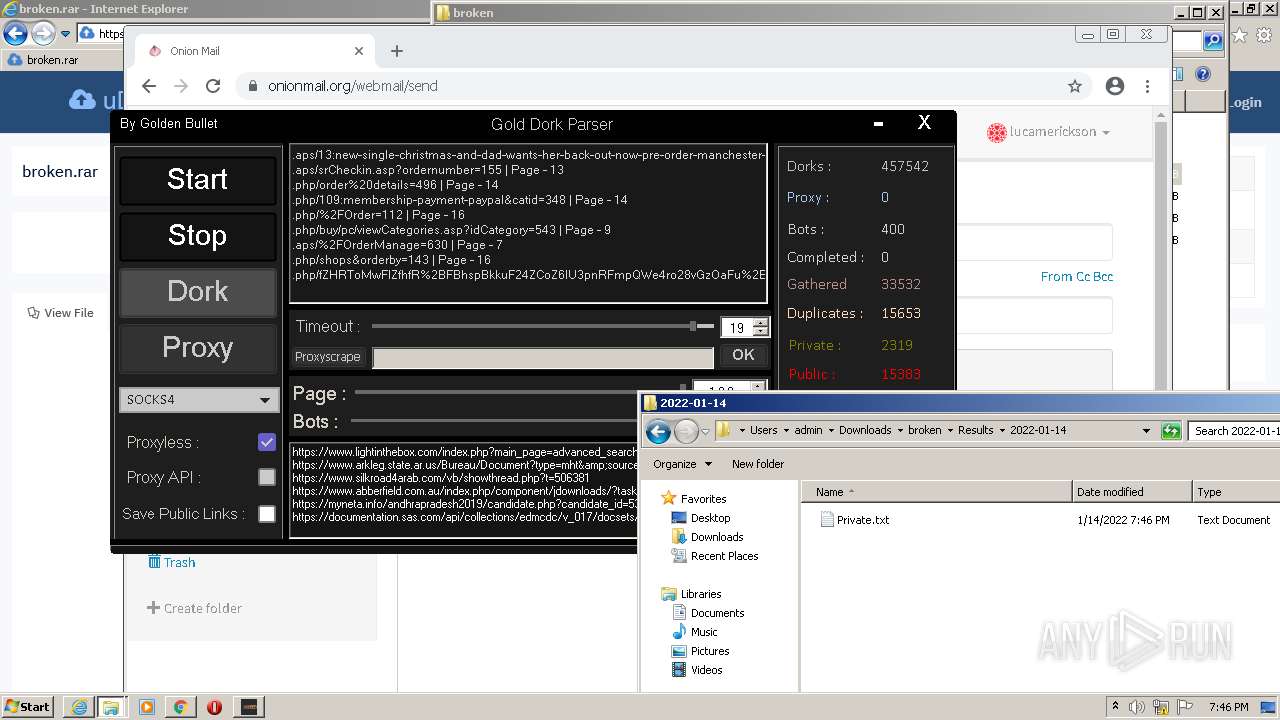
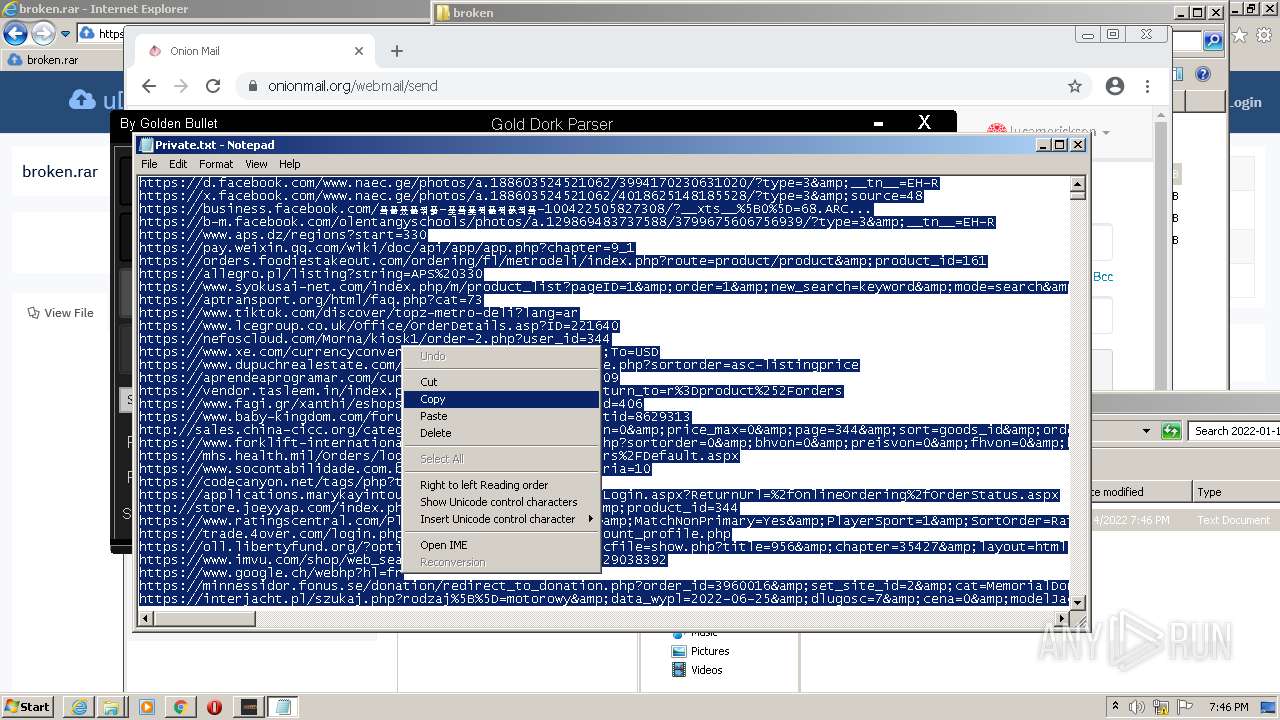
- Gold Dork Parser.exe (PID: 2044)
Application was dropped or rewritten from another process
- Gold Dork Parser.exe (PID: 2044)
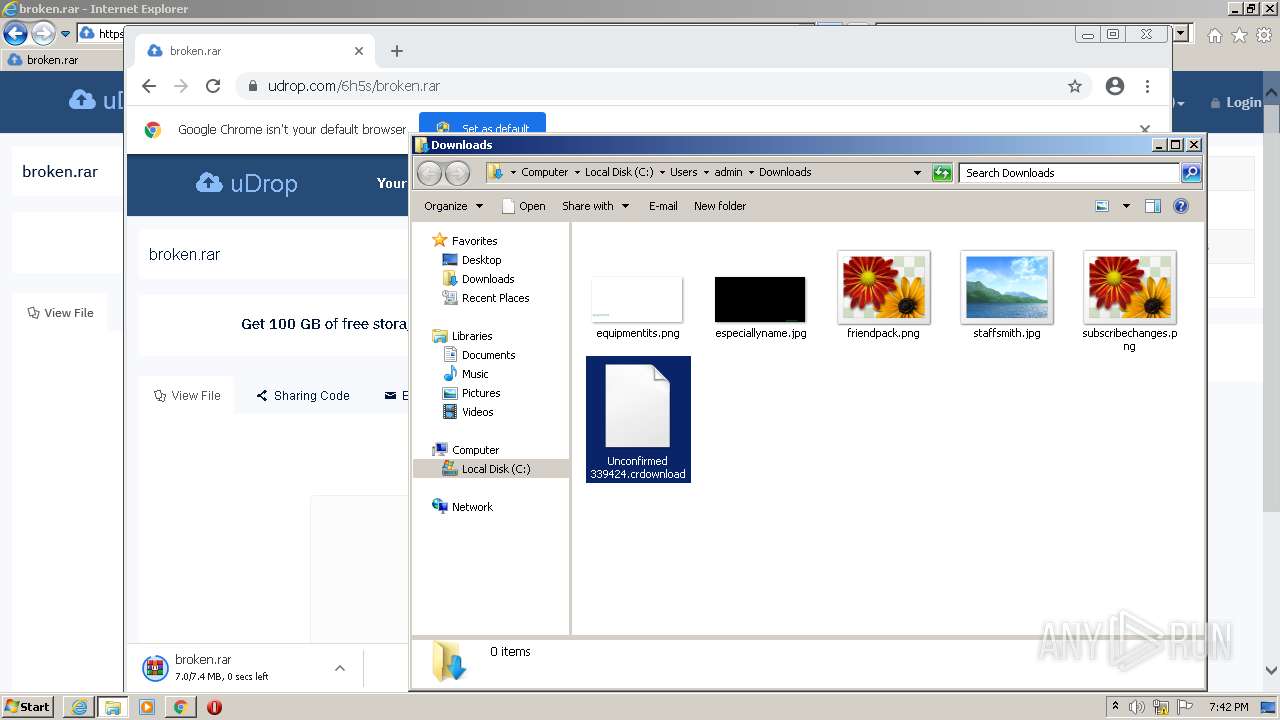
Drops executable file immediately after starts
- chrome.exe (PID: 2372)
SUSPICIOUS
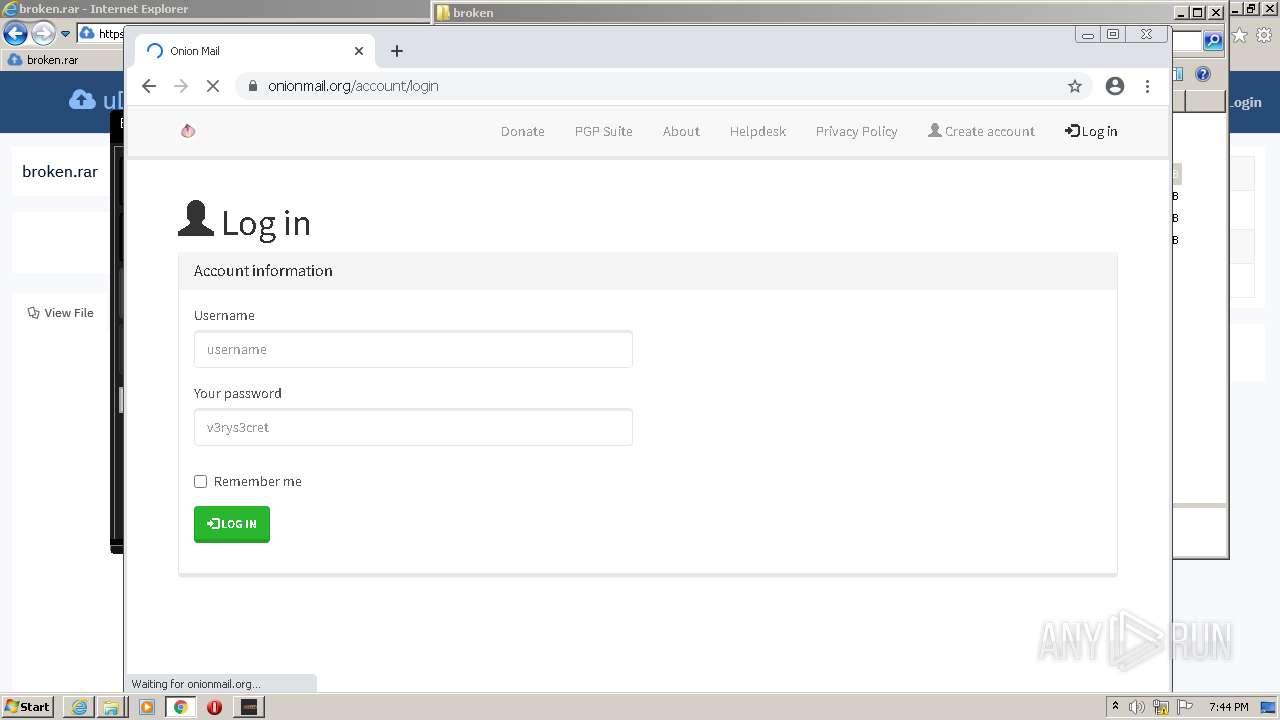
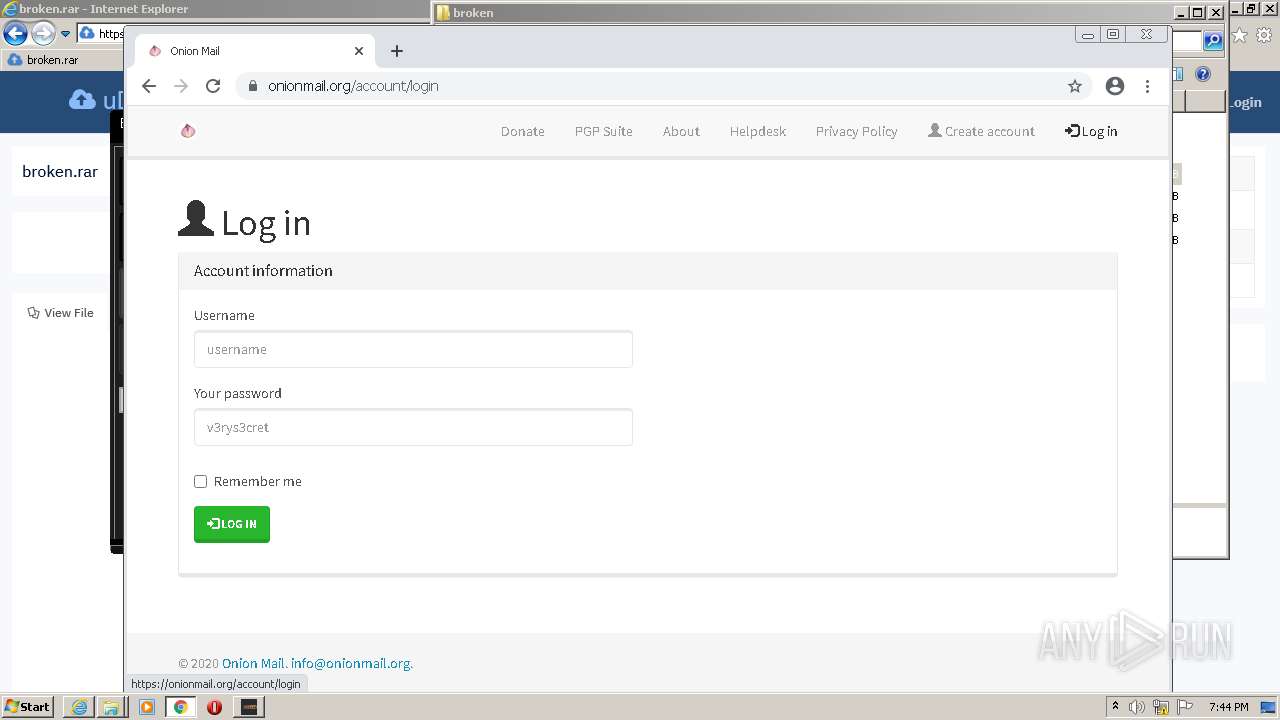
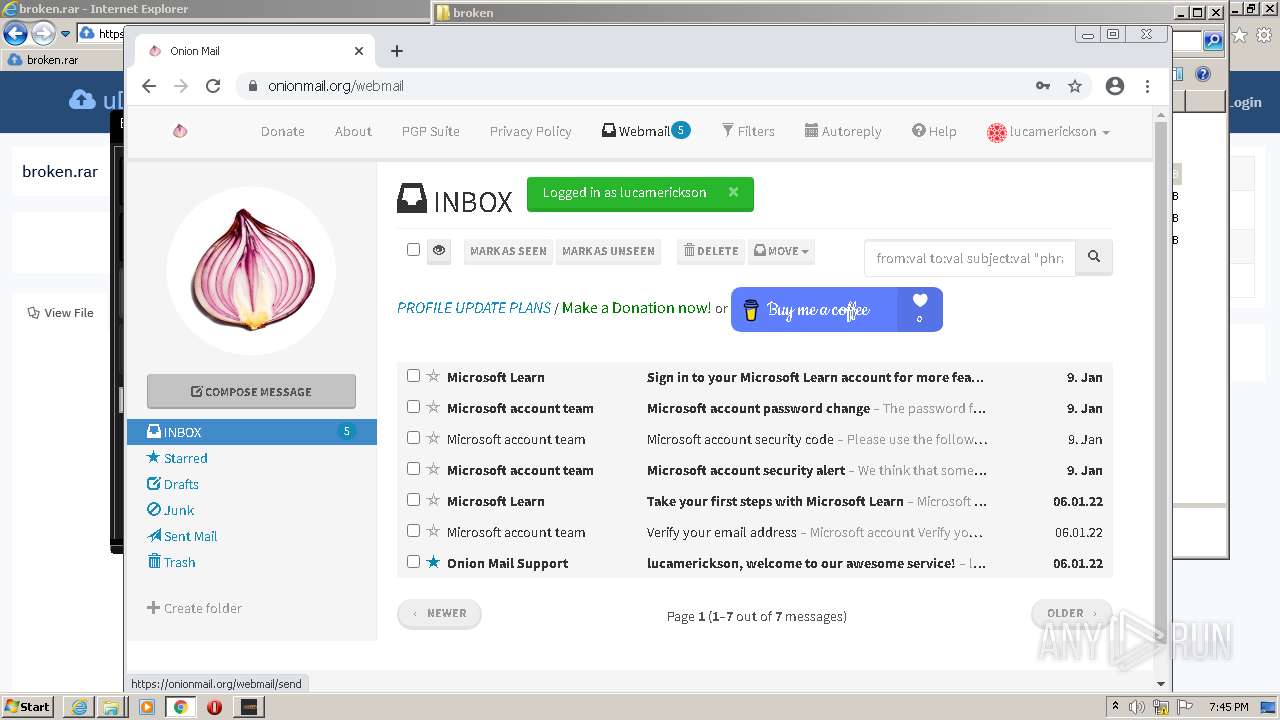
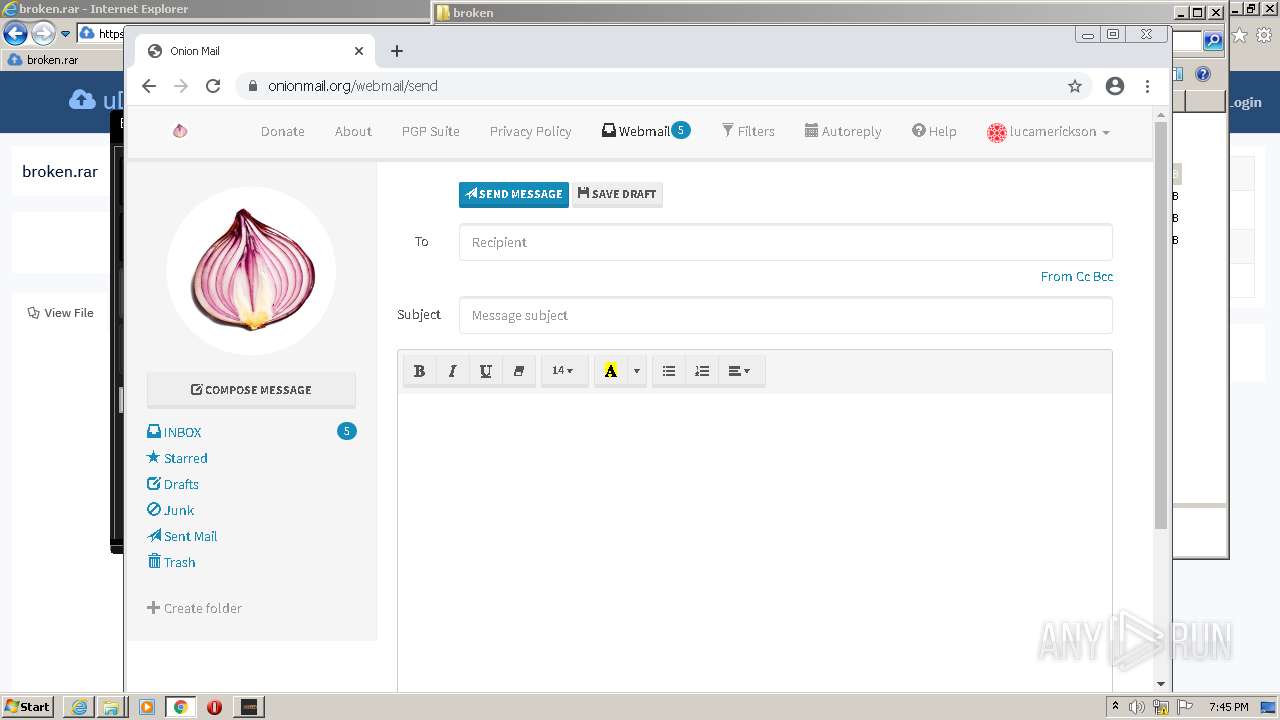
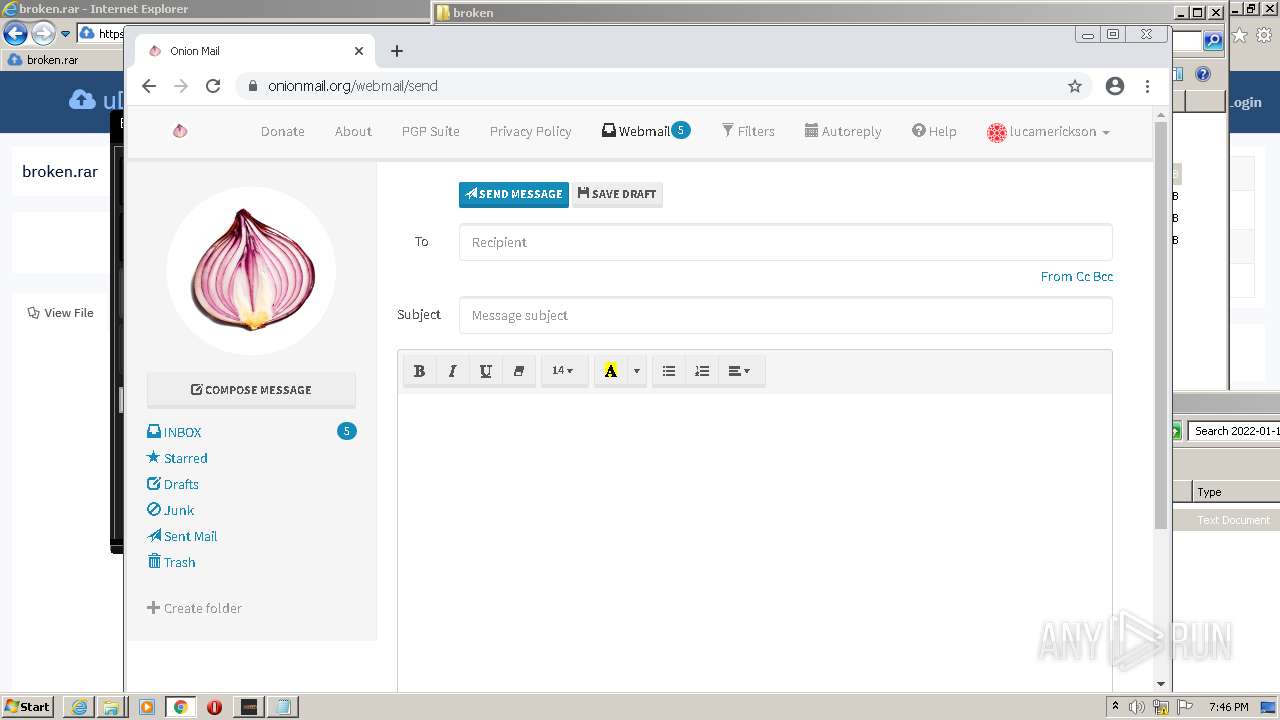
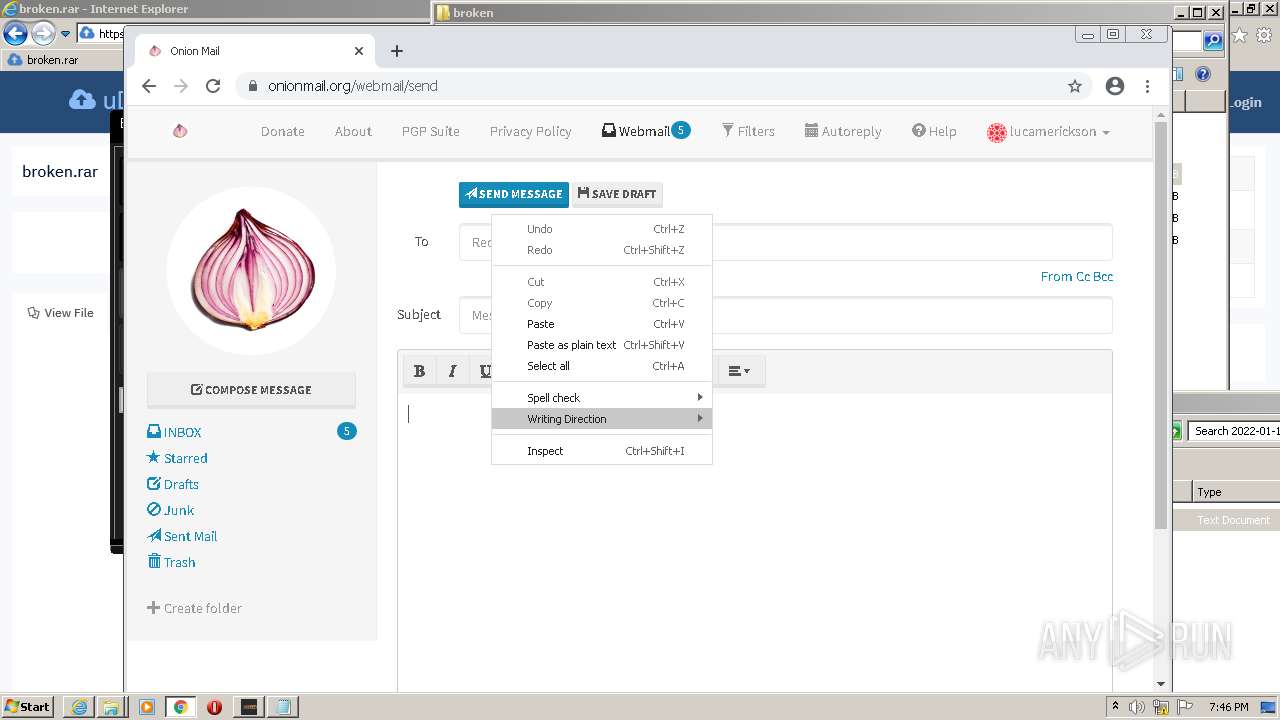
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2684)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1968)
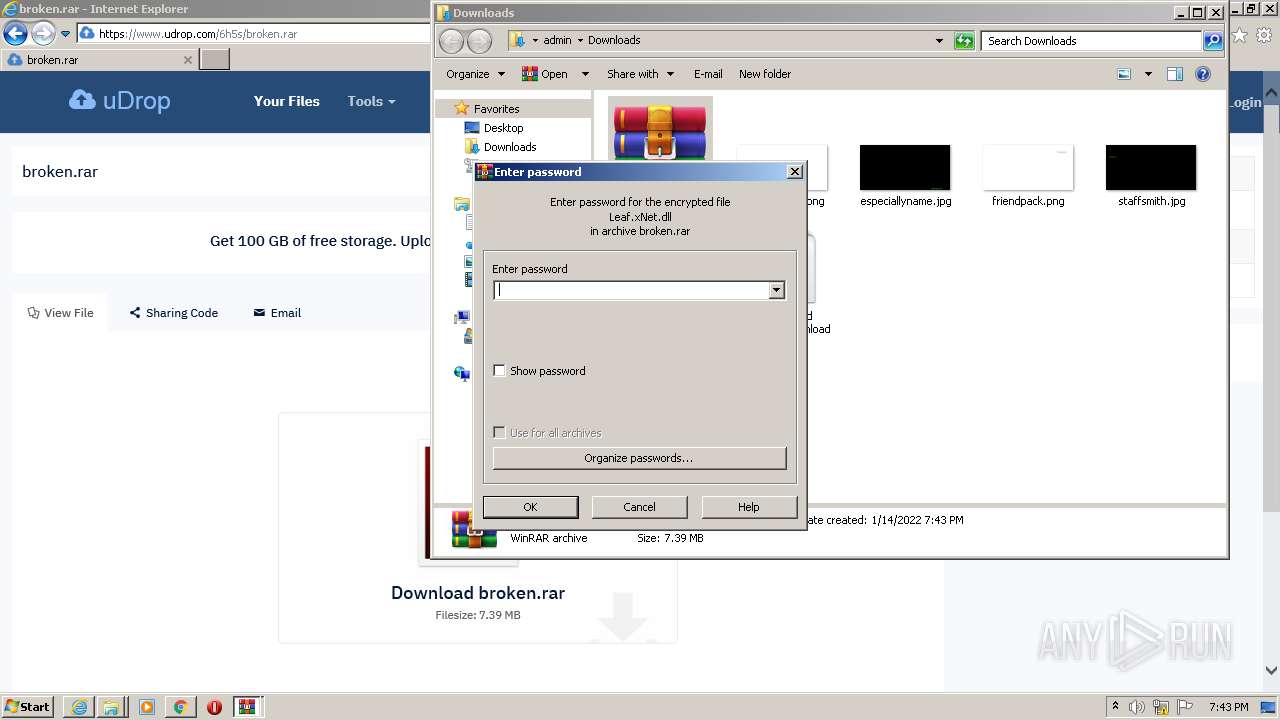
Checks supported languages
- WinRAR.exe (PID: 3440)
- Gold Dork Parser.exe (PID: 2044)
Reads the computer name
- WinRAR.exe (PID: 3440)
- Gold Dork Parser.exe (PID: 2044)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3440)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3440)
- chrome.exe (PID: 2372)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 3440)
- chrome.exe (PID: 2372)
Reads Environment values
- Gold Dork Parser.exe (PID: 2044)
INFO
Changes internet zones settings
- iexplore.exe (PID: 1408)
Checks supported languages
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 2684)
- chrome.exe (PID: 2340)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 1968)
- chrome.exe (PID: 1200)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 2736)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 3436)
- chrome.exe (PID: 1424)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 3264)
- chrome.exe (PID: 1144)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 2888)
- chrome.exe (PID: 1592)
- chrome.exe (PID: 4600)
- chrome.exe (PID: 5364)
- chrome.exe (PID: 5024)
- chrome.exe (PID: 6000)
- chrome.exe (PID: 5272)
- chrome.exe (PID: 3248)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 5680)
- chrome.exe (PID: 2424)
- NOTEPAD.EXE (PID: 5712)
- chrome.exe (PID: 5524)
- chrome.exe (PID: 5812)
- chrome.exe (PID: 4964)
- chrome.exe (PID: 3124)
Application launched itself
- iexplore.exe (PID: 1408)
- chrome.exe (PID: 1968)
Checks Windows Trust Settings
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 2684)
Reads the computer name
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 2684)
- chrome.exe (PID: 1968)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 1200)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 3880)
- chrome.exe (PID: 1236)
- chrome.exe (PID: 3232)
- chrome.exe (PID: 1592)
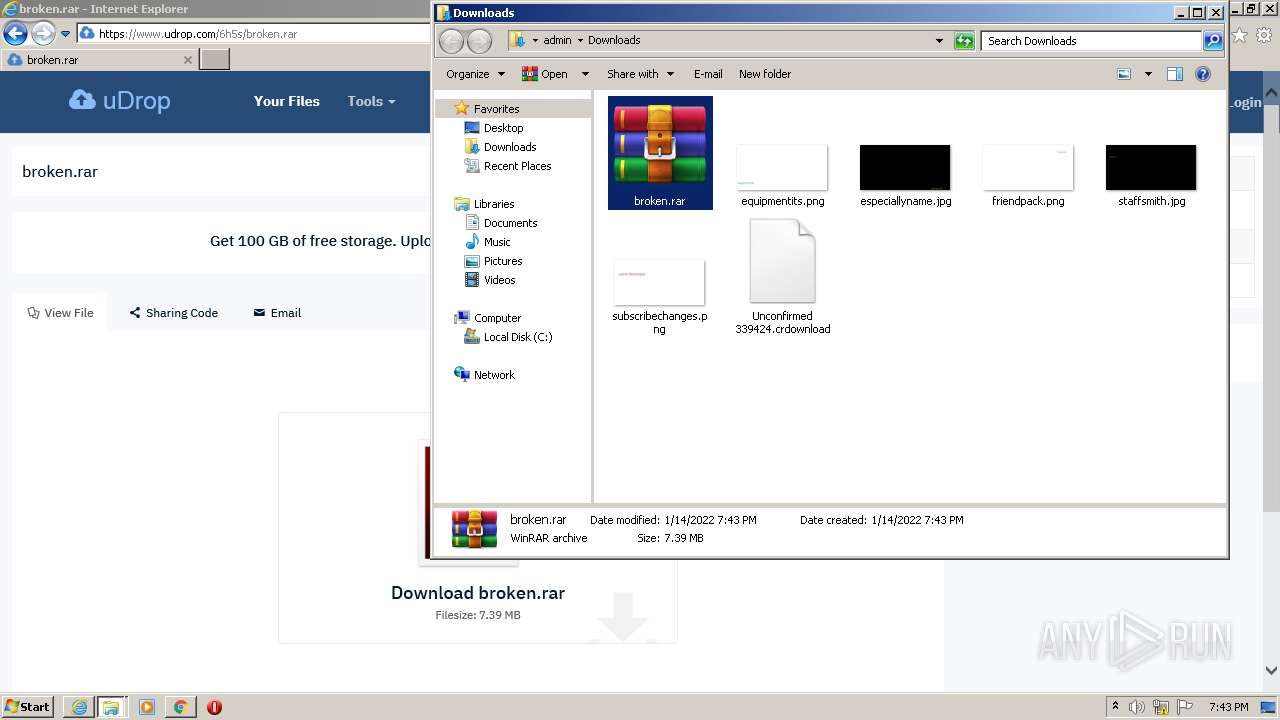
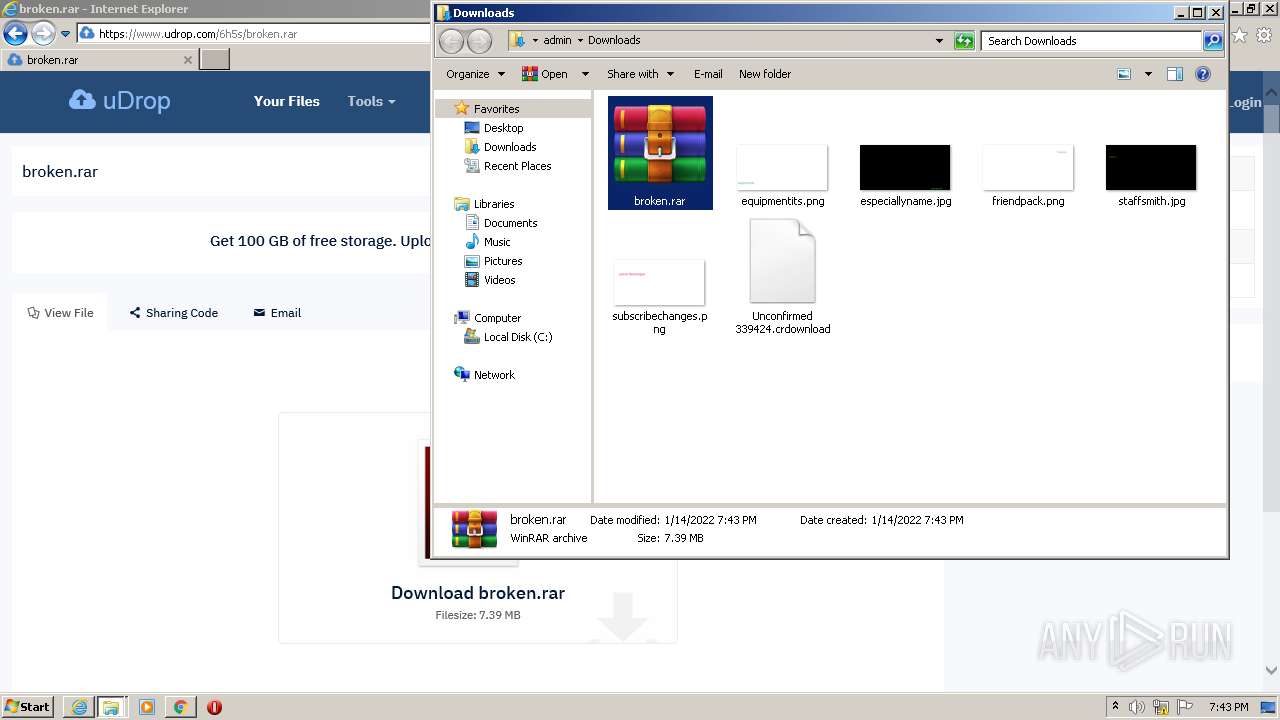
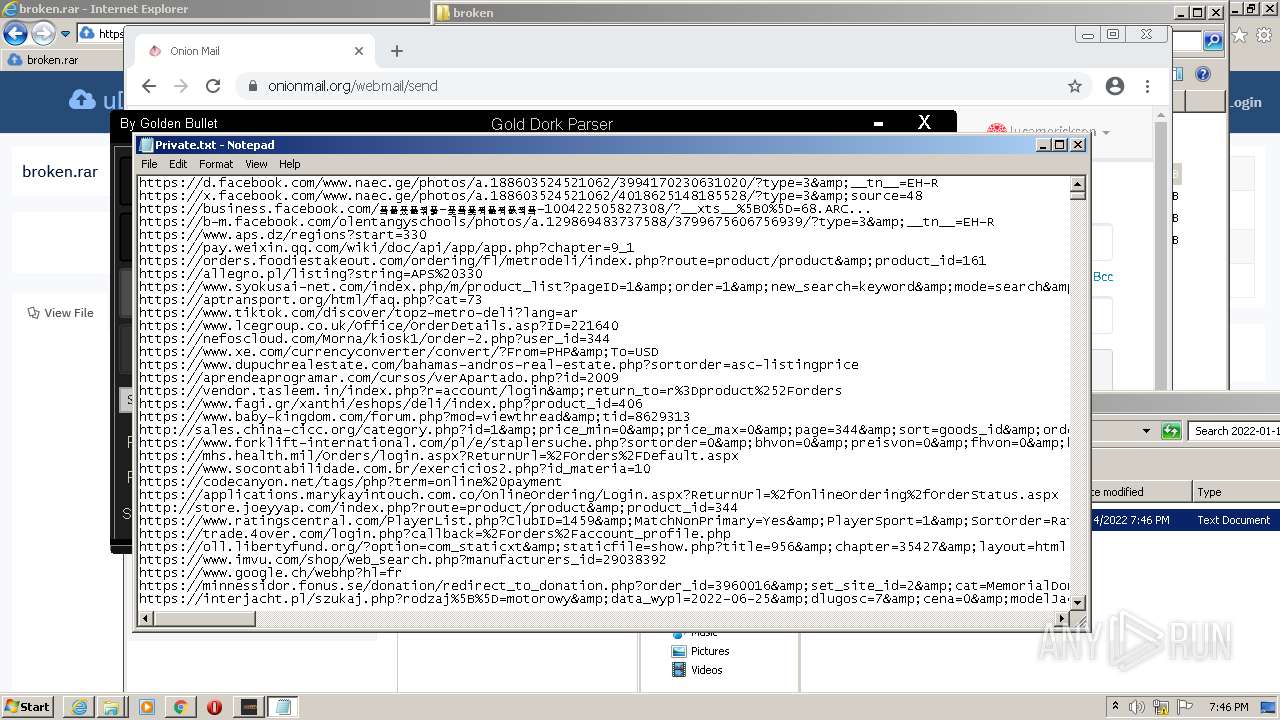
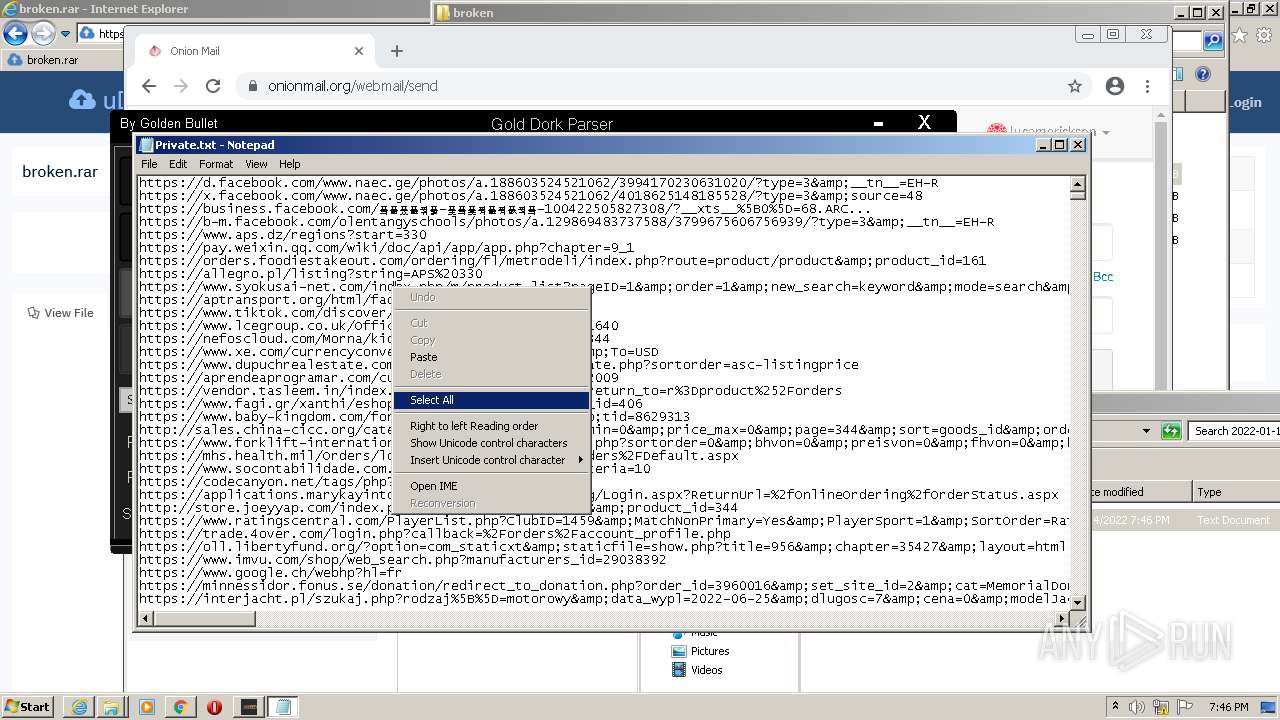
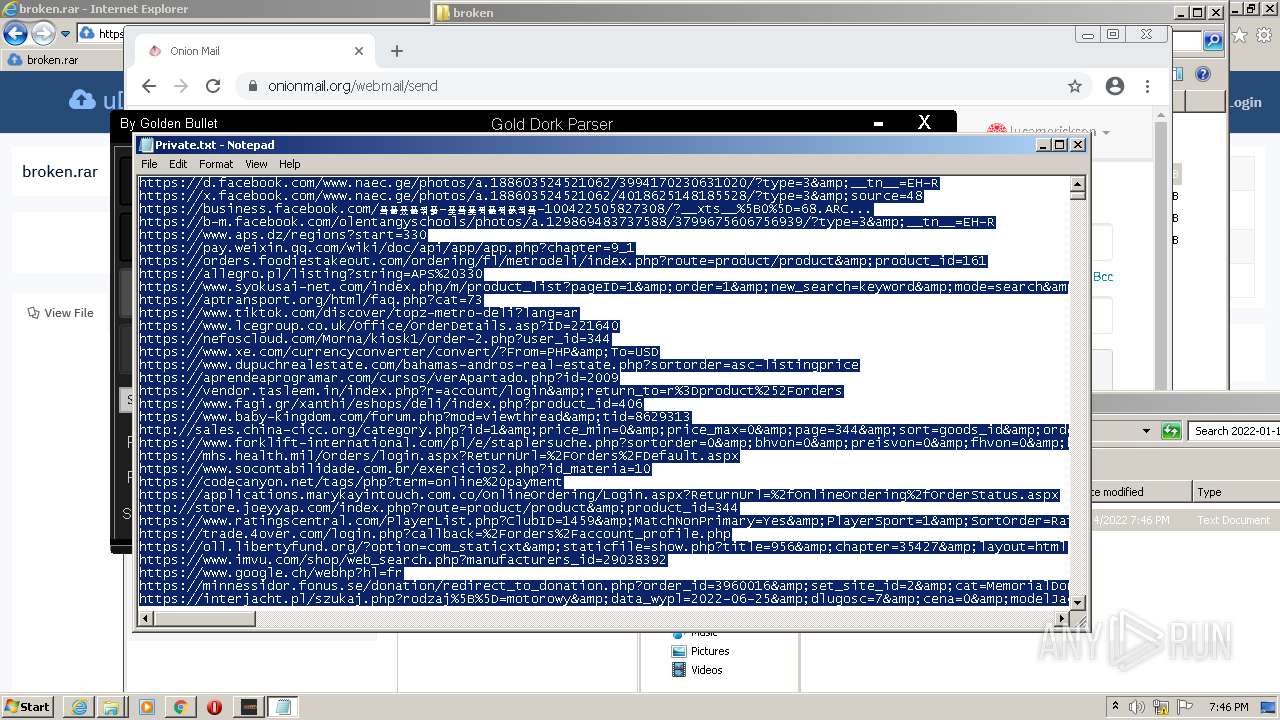
Manual execution by user
- chrome.exe (PID: 1968)
- WinRAR.exe (PID: 3440)
- Gold Dork Parser.exe (PID: 2044)
- NOTEPAD.EXE (PID: 5712)
Reads settings of System Certificates
- iexplore.exe (PID: 1408)
- iexplore.exe (PID: 2684)
- chrome.exe (PID: 1200)
- Gold Dork Parser.exe (PID: 2044)
Creates files in the user directory
- iexplore.exe (PID: 2684)
- iexplore.exe (PID: 1408)
Reads internet explorer settings
- iexplore.exe (PID: 2684)
Reads the hosts file
- chrome.exe (PID: 1968)
- chrome.exe (PID: 1200)
Reads the date of Windows installation
- chrome.exe (PID: 3232)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1408)
Changes settings of System certificates
- iexplore.exe (PID: 1408)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1408)
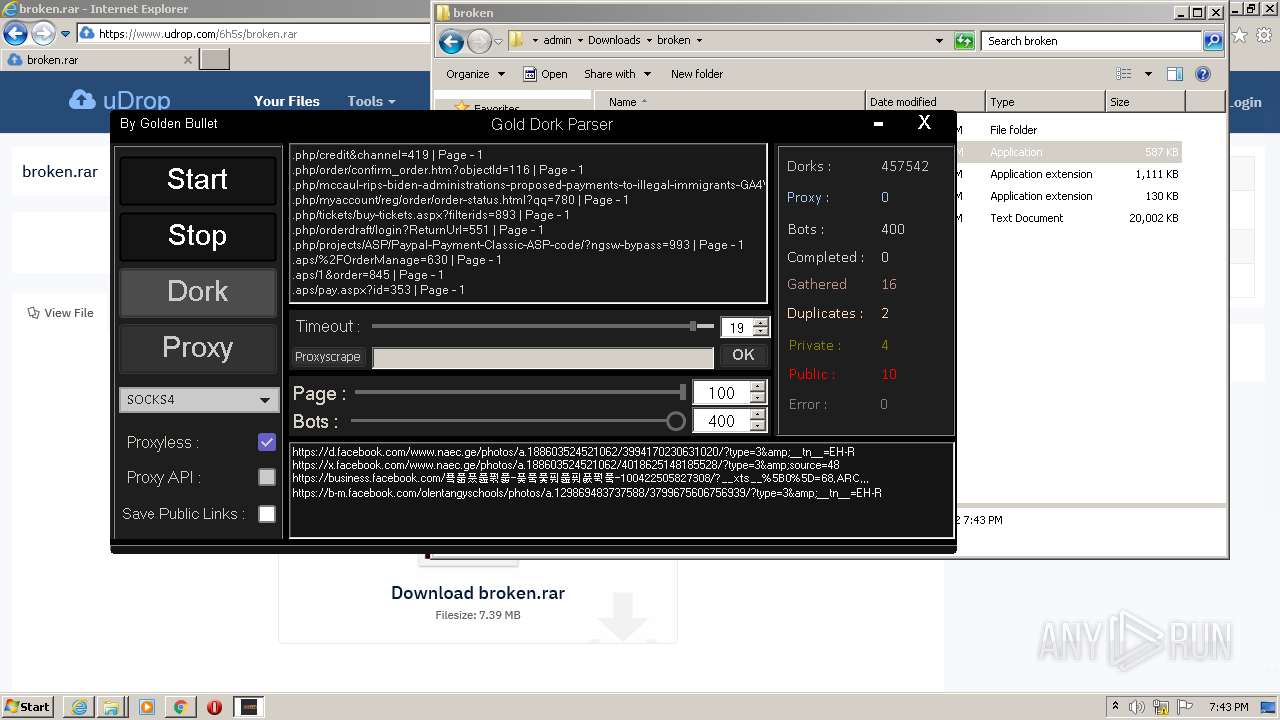
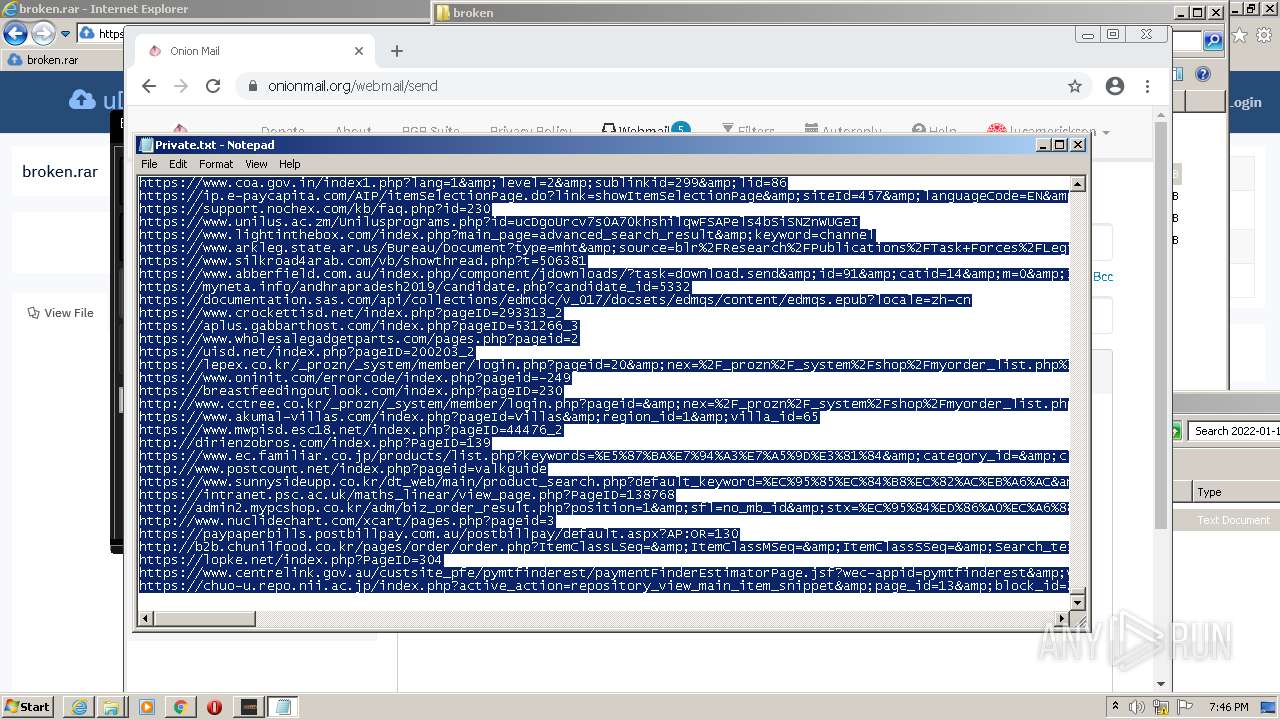
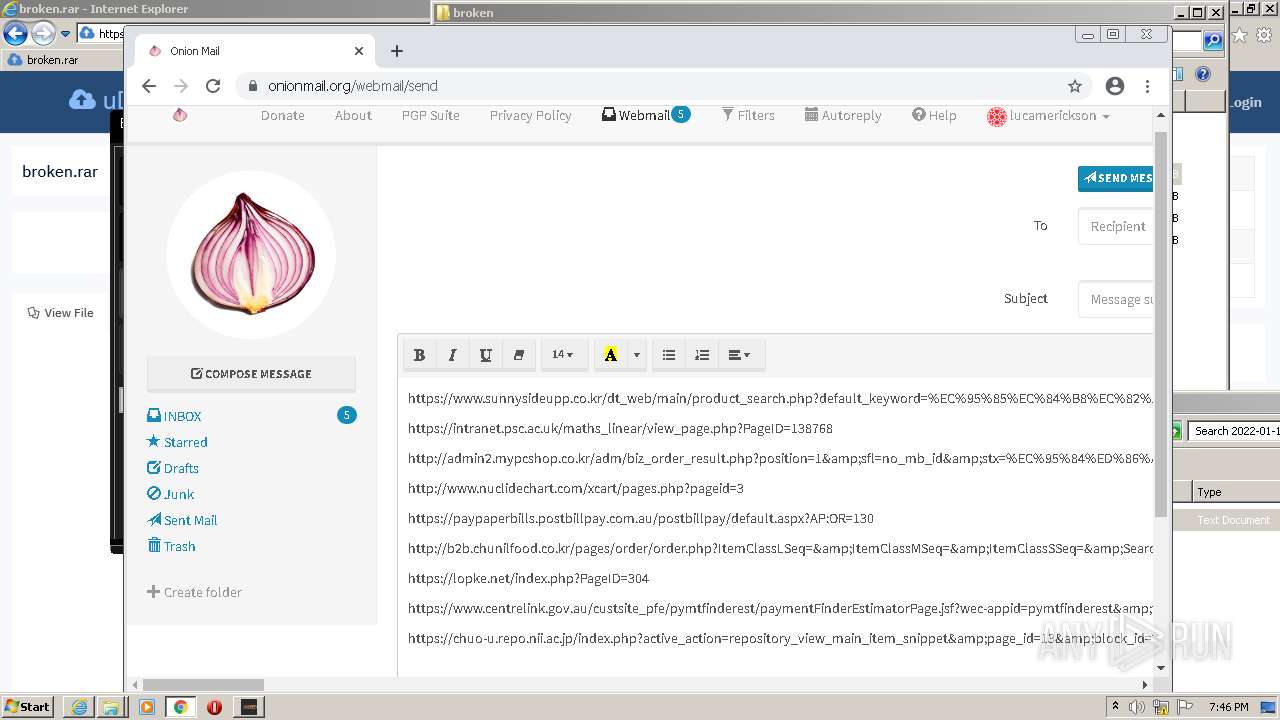
Drops Coronavirus (possible) decoy
- Gold Dork Parser.exe (PID: 2044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
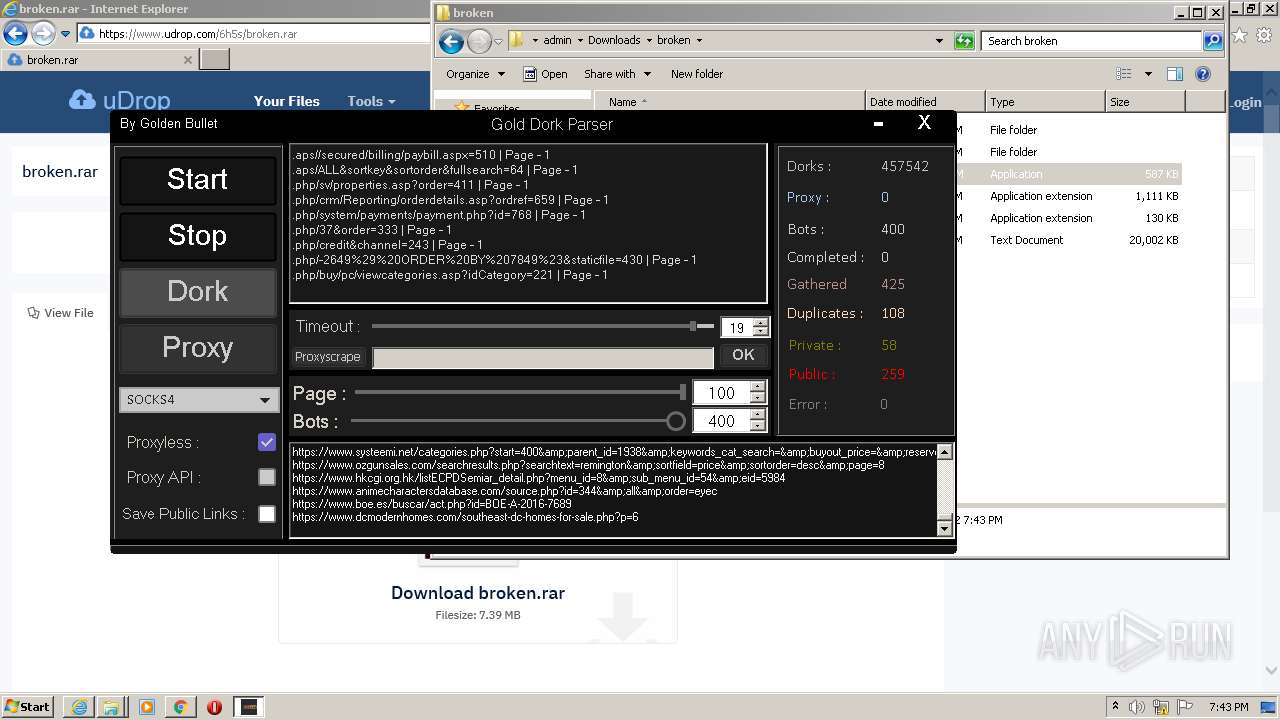
Total processes
146
Monitored processes
39
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2272 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1048,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1328 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=932 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1408 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.udrop.com/6h5s/broken.rar" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2916 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=664 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1076 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
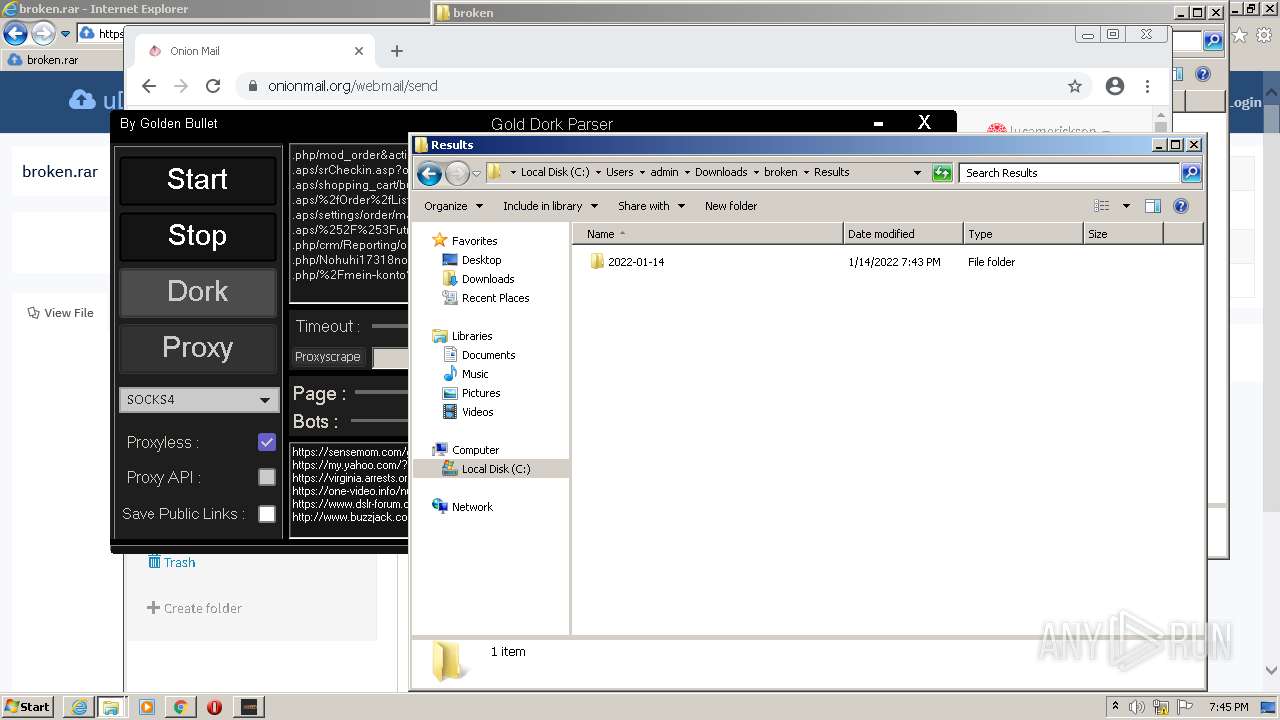
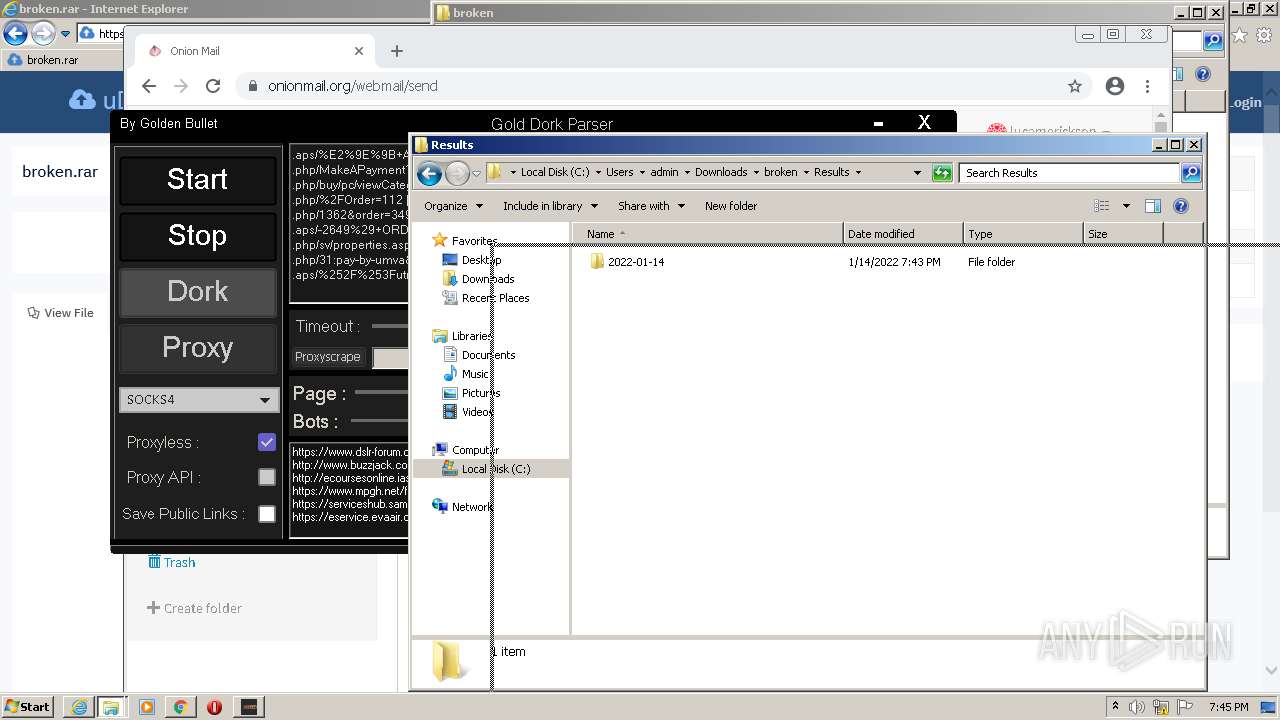
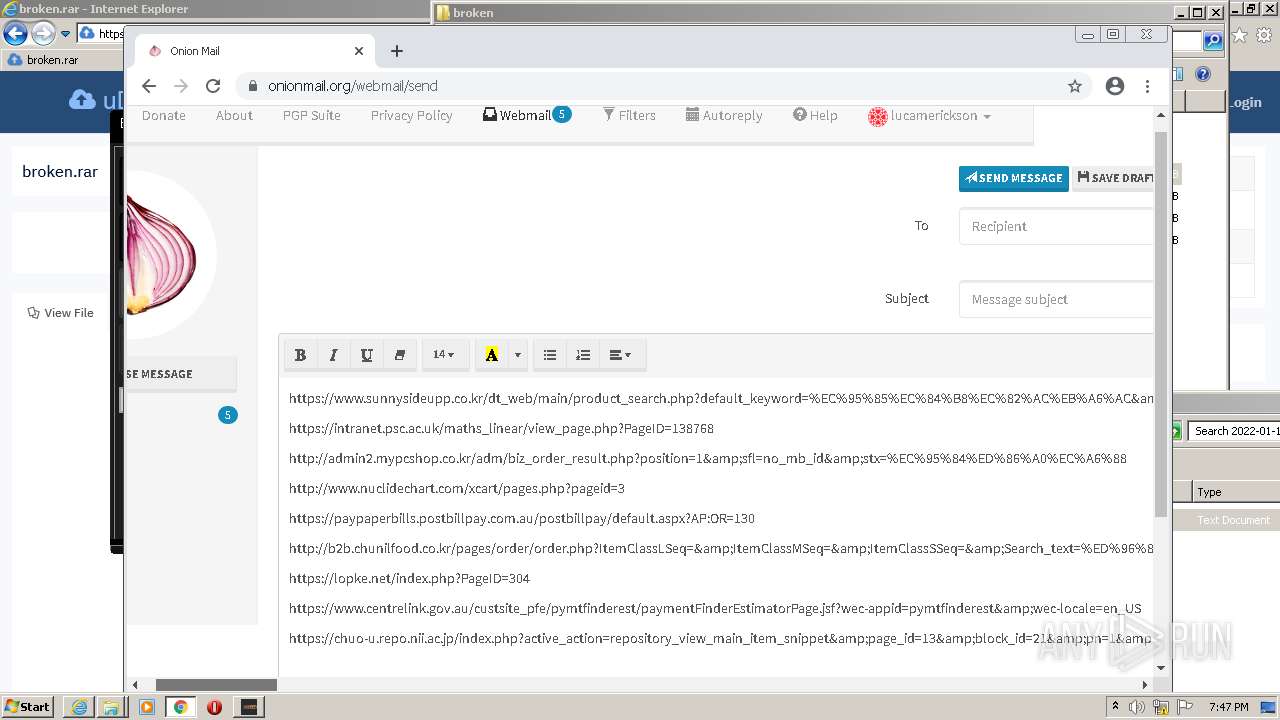
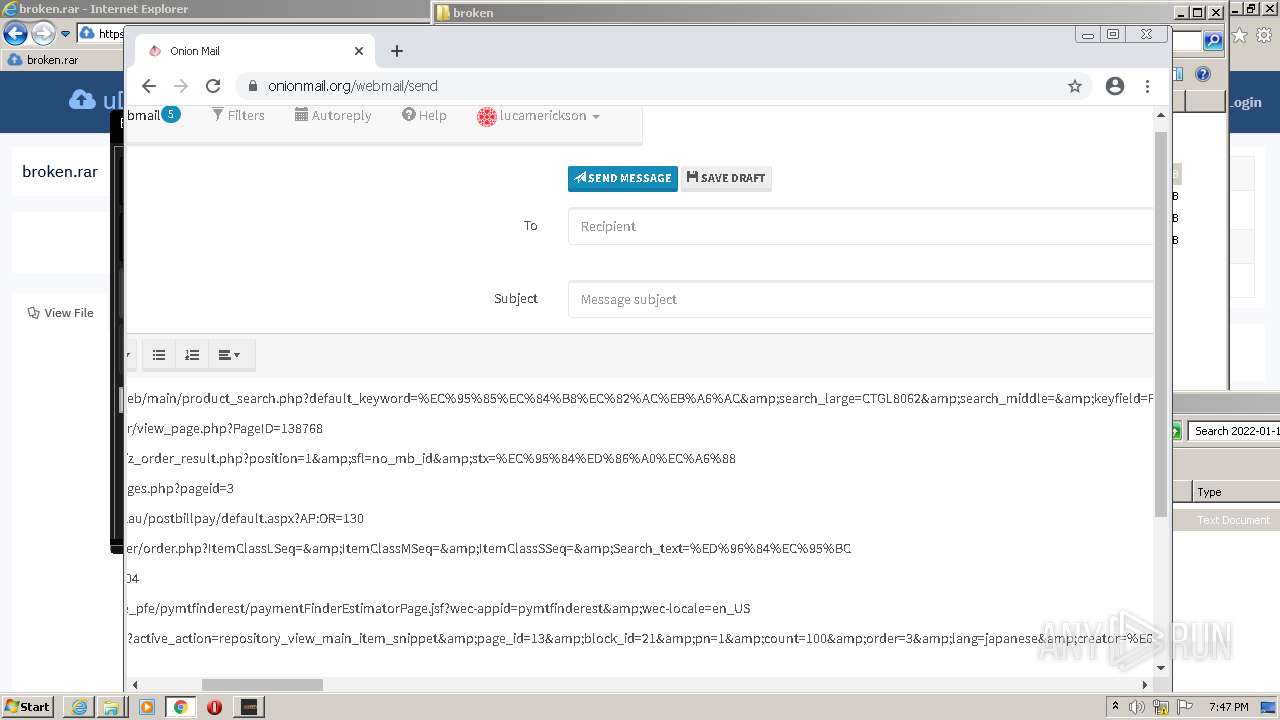
| 2044 | "C:\Users\admin\Downloads\broken\Gold Dork Parser.exe" | C:\Users\admin\Downloads\broken\Gold Dork Parser.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Gold Dork Parser Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=1048,11649160545672780859,8257128829790975961,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3340 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
44 025
Read events
43 692
Write events
323
Delete events
10
Modification events
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30935422 | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30935422 | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1408) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
11
Suspicious files
247
Text files
487
Unknown types
41
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:— | SHA256:— | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:— | SHA256:— | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 1968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61E1D21A-7B0.pma | — | |
MD5:— | SHA256:— | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\font-awesome.min[1].css | text | |
MD5:501BB354CA05847BE1617AB859F87BDF | SHA256:F070E2F2AC9D893726E9FDE3E146649850520AB05AC51576E31138D00BB582D6 | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\entypo[1].css | text | |
MD5:F67E1BD2E1584A2E50CF139375D2D03F | SHA256:58820CB68DFC11A83C4B797FCEF209DCD1352239DB0C29E001CE72F29D669211 | |||
| 1408 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\favicon[1].ico | image | |
MD5:DA597791BE3B6E732F0BC8B20E38EE62 | SHA256:5B2C34B3C4E8DD898B664DBA6C3786E2FF9869EFF55D673AA48361F11325ED07 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6 359
TCP/UDP connections
10 213
DNS requests
74
Threats
38
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | — | — | whitelisted |
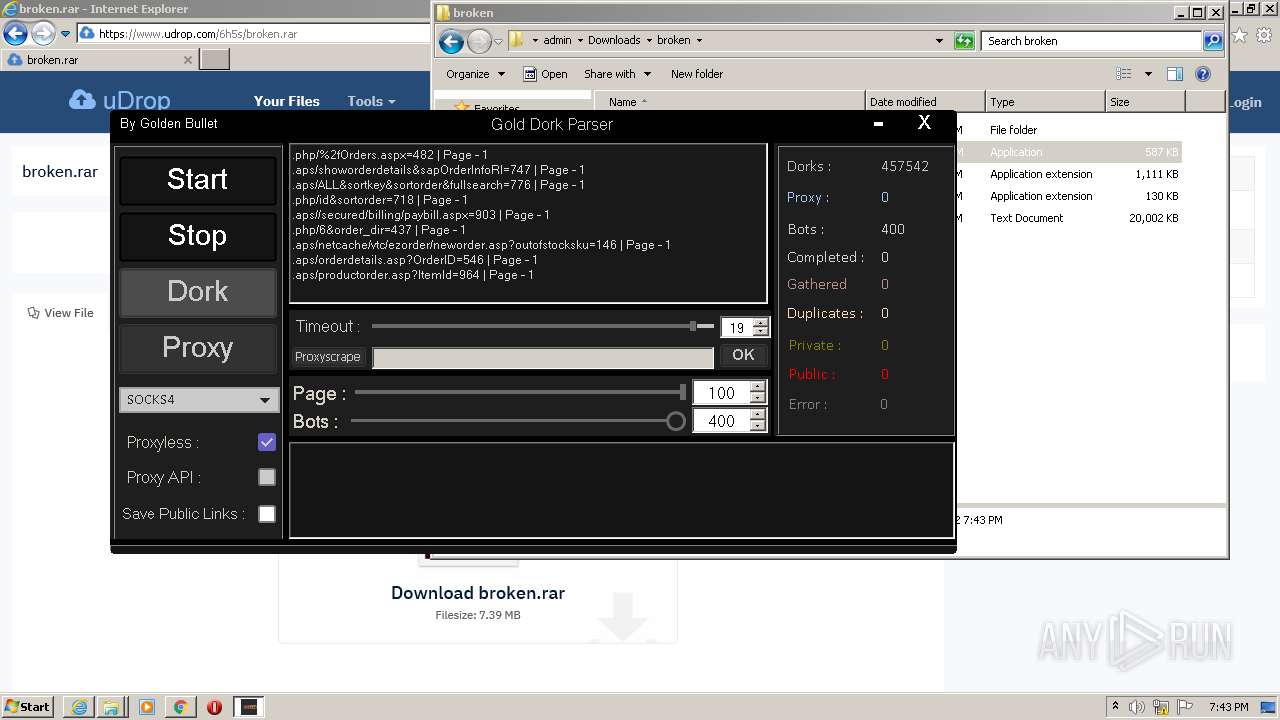
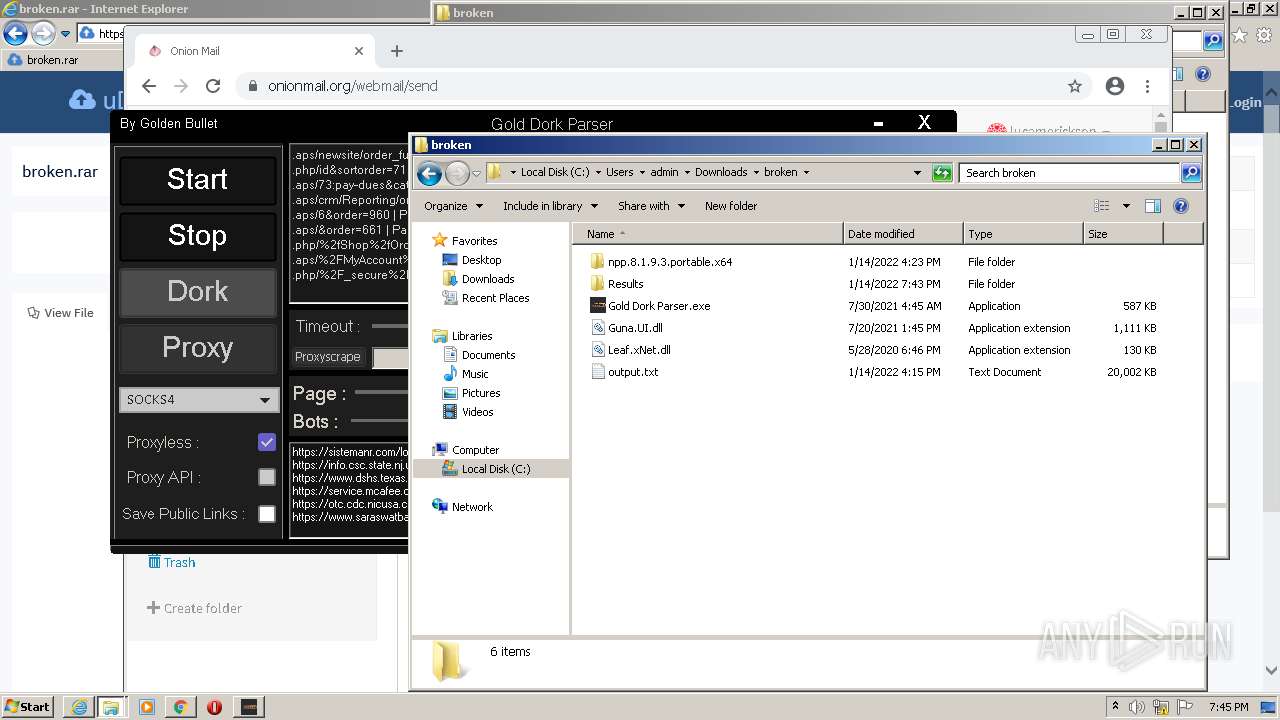
2044 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.php%2fJohan%2bVerminnen%26order%3d966&first=0&last=50&count=50 | US | — | — | whitelisted |
2044 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.php%2f%252FOrder%3d112&first=0&last=50&count=50 | US | — | — | whitelisted |
2044 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.php%2freset%26orderby%3d117&first=0&last=50&count=50 | US | — | — | whitelisted |
2044 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.php%2fphp%2forder.php%3fid%3d313&first=0&last=50&count=50 | US | — | — | whitelisted |
2044 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.aps%2fnetcache%2fvtc%2fezorder%2fneworder.asp%3foutofstocksku%3d315&first=0&last=50&count=50 | US | — | — | whitelisted |
2044 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.aps%2f%25E2%259E%259B%2bA%2bProvider%2bOrder%2bIs%2bWritten%2bFor%2bProchlorperazine%2b-%2b%25E2%259C%2585%2bwww.HealsPills.store%2b%25E2%259C%2585%2bLow%2bCost%2bProchlorperazine%2b%25E2%259E%259BProchlorperazine%2bBuy%2bAustralia%2bBuy%2bProchlorperazine%2bBuccal%3d289&first=0&last=50&count=50 | US | — | — | whitelisted |
2044 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.aps%2fOnlineOrdering%2fLogin.aspx%3fReturnUrl%3d958&first=0&last=50&count=50 | US | — | — | whitelisted |
2044 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.php%2f%252Fcart%252Fpayment%3d869&first=0&last=50&count=50 | US | — | — | whitelisted |
2684 | iexplore.exe | GET | 200 | 192.124.249.23:80 | http://ocsp.godaddy.com//MEIwQDA%2BMDwwOjAJBgUrDgMCGgUABBQdI2%2BOBkuXH93foRUj4a7lAr4rGwQUOpqFBxBnKLbv9r0FQW4gwZTaD94CAQc%3D | US | der | 1.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2684 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1408 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2684 | iexplore.exe | 192.124.249.23:80 | ocsp.godaddy.com | Sucuri | US | suspicious |
2684 | iexplore.exe | 65.103.40.169:443 | www.udrop.com | Qwest Communications Company, LLC | US | suspicious |
1200 | chrome.exe | 216.58.212.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
1408 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1200 | chrome.exe | 142.250.185.77:443 | accounts.google.com | Google Inc. | US | suspicious |
1200 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1200 | chrome.exe | 142.250.185.196:443 | www.google.com | Google Inc. | US | whitelisted |
1200 | chrome.exe | 65.103.40.169:443 | www.udrop.com | Qwest Communications Company, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.udrop.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2044 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
2044 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
2044 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
2044 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
2044 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
2044 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
2044 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
2044 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
2044 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
2044 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |