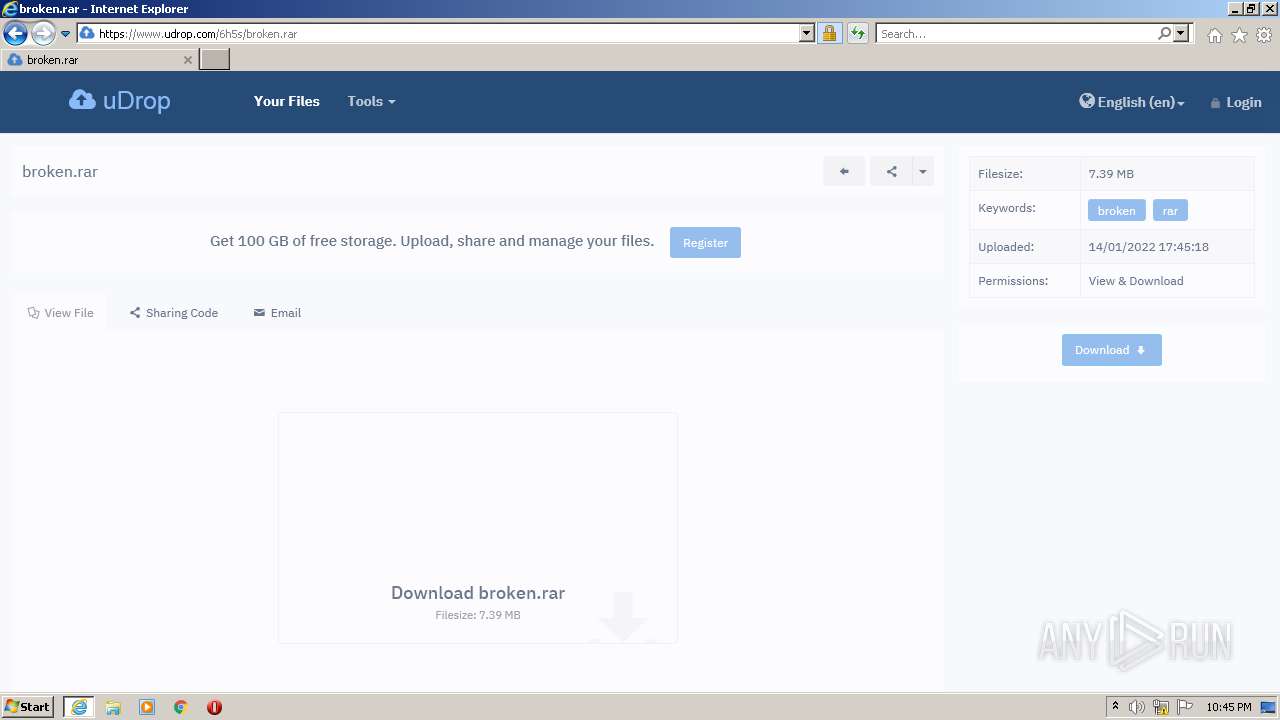
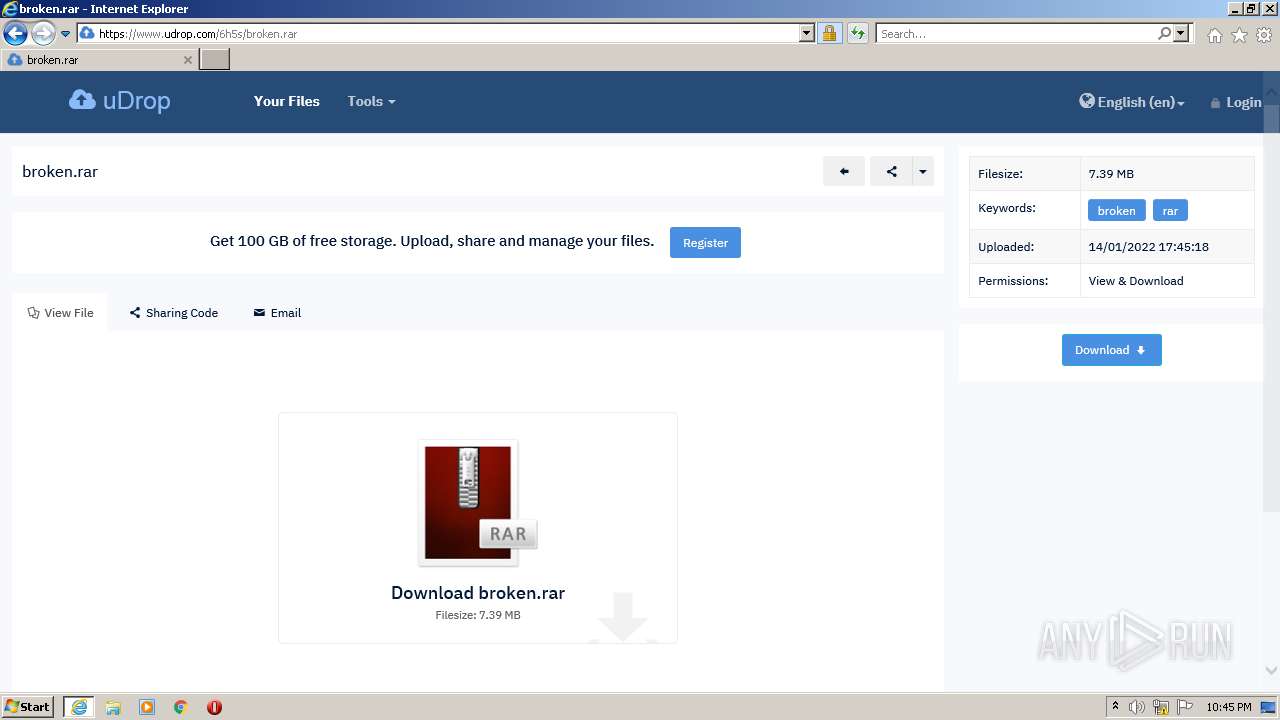
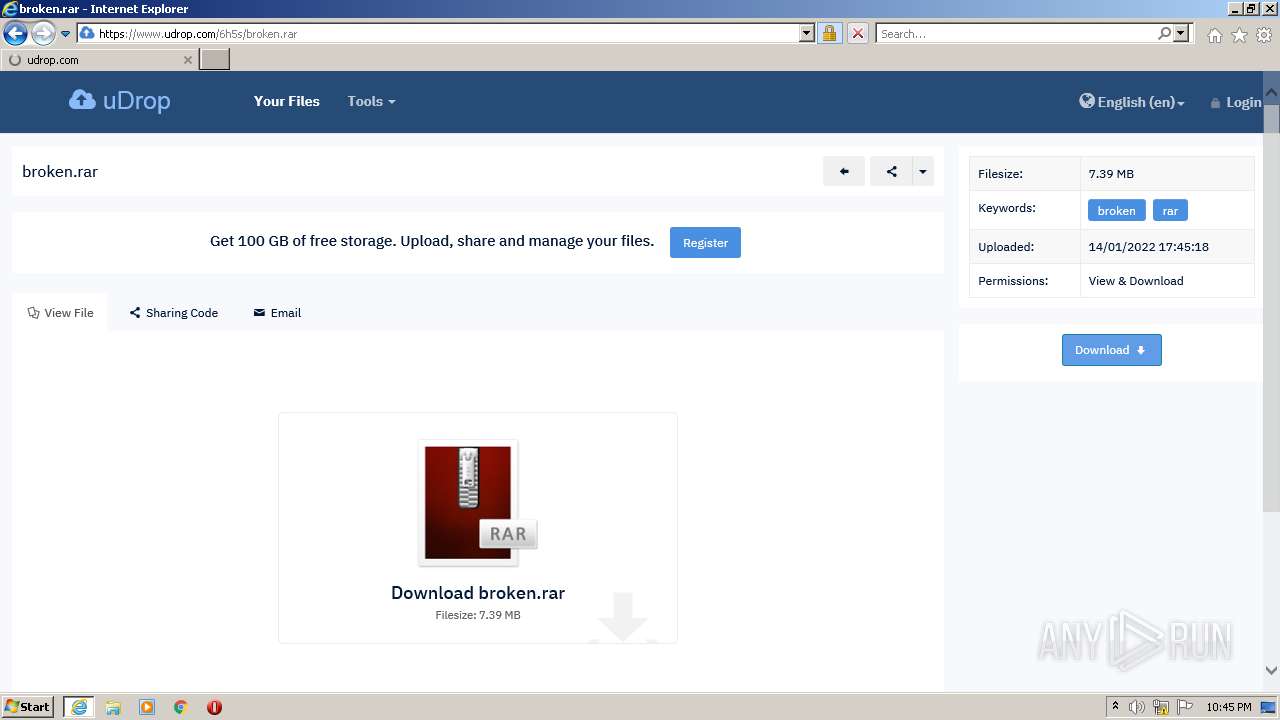
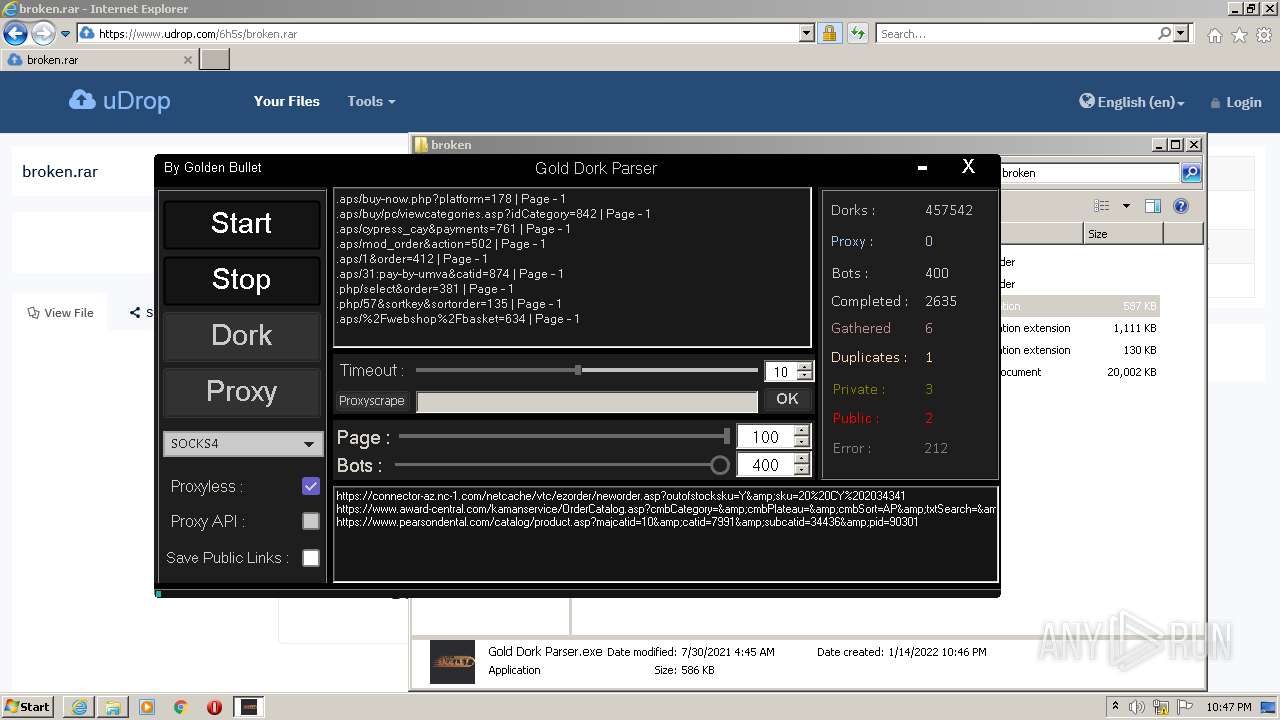
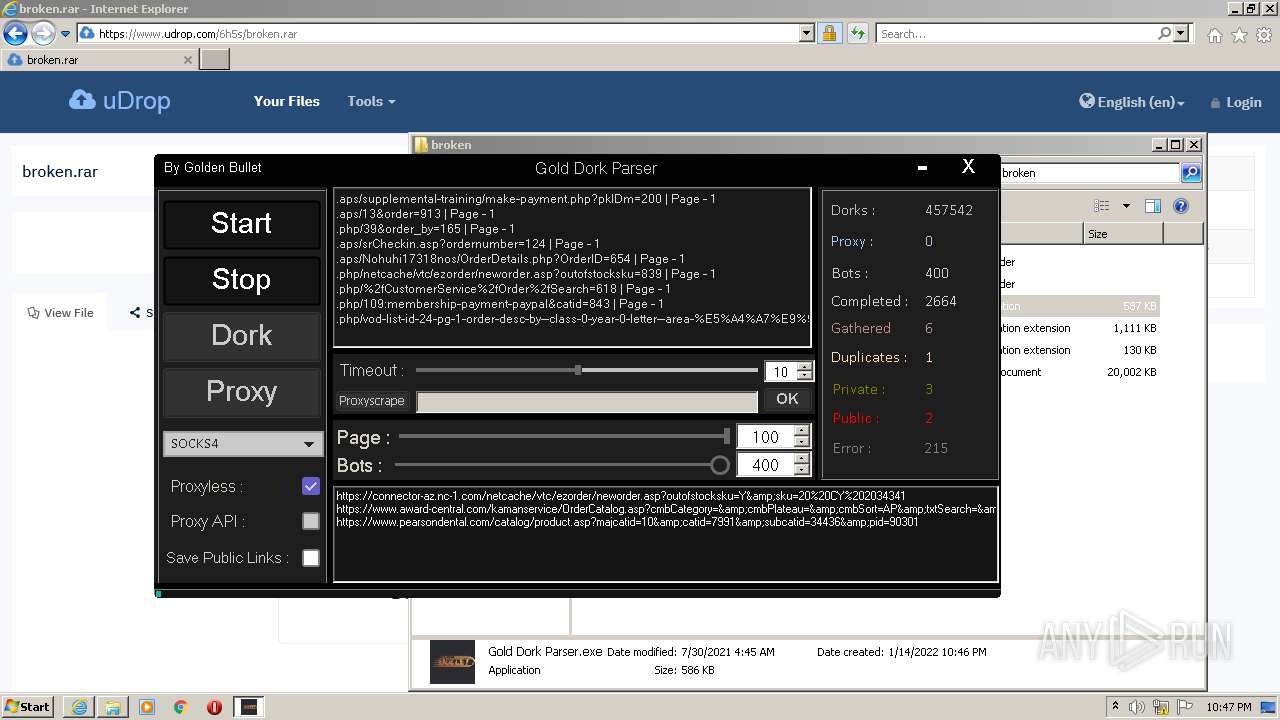
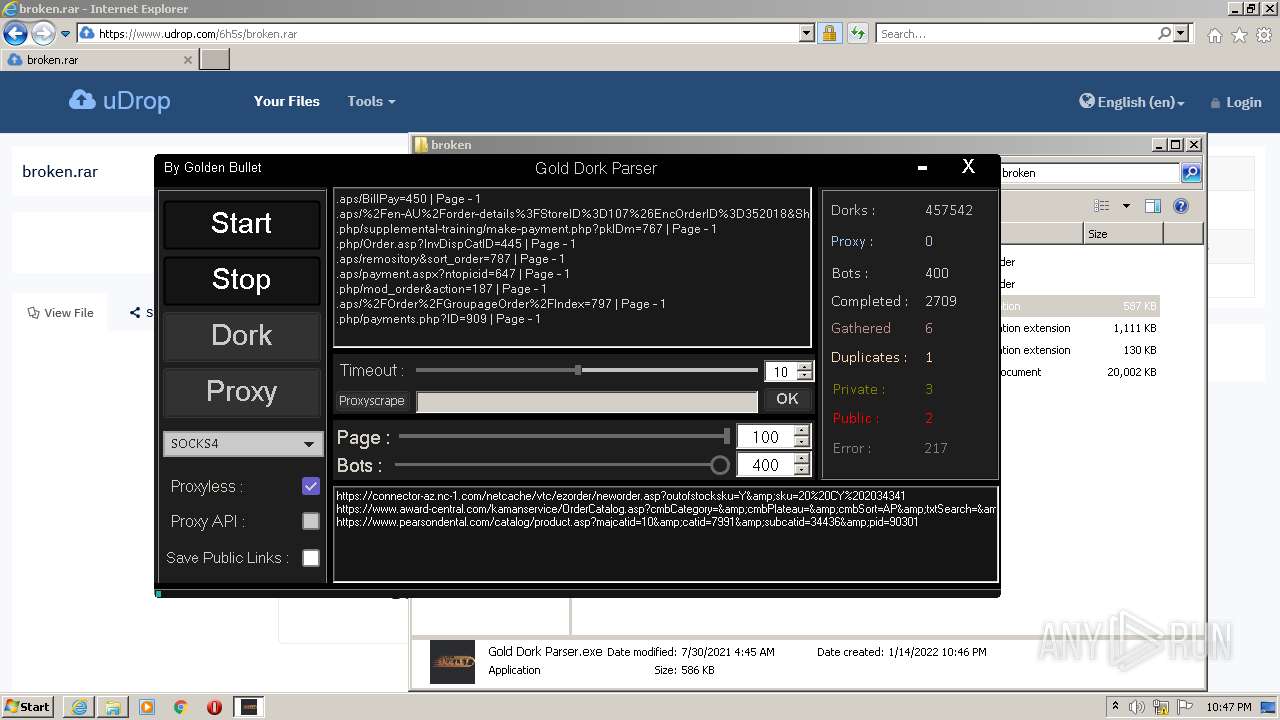
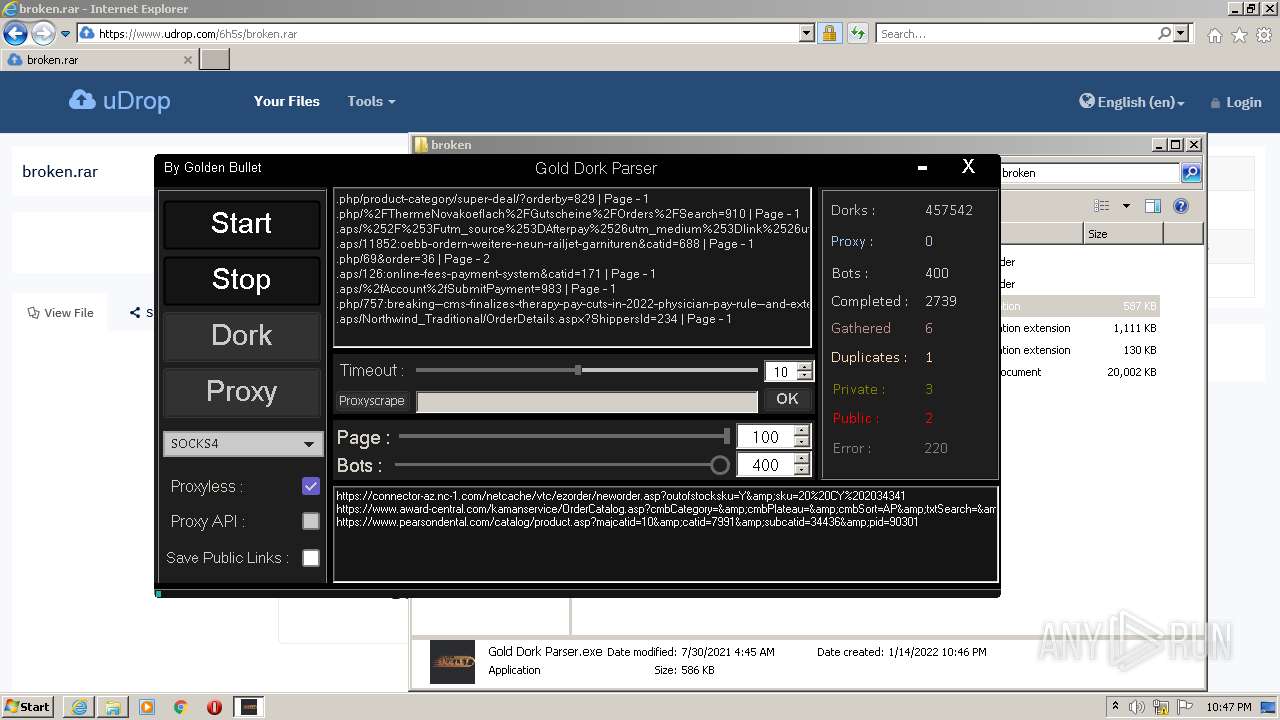
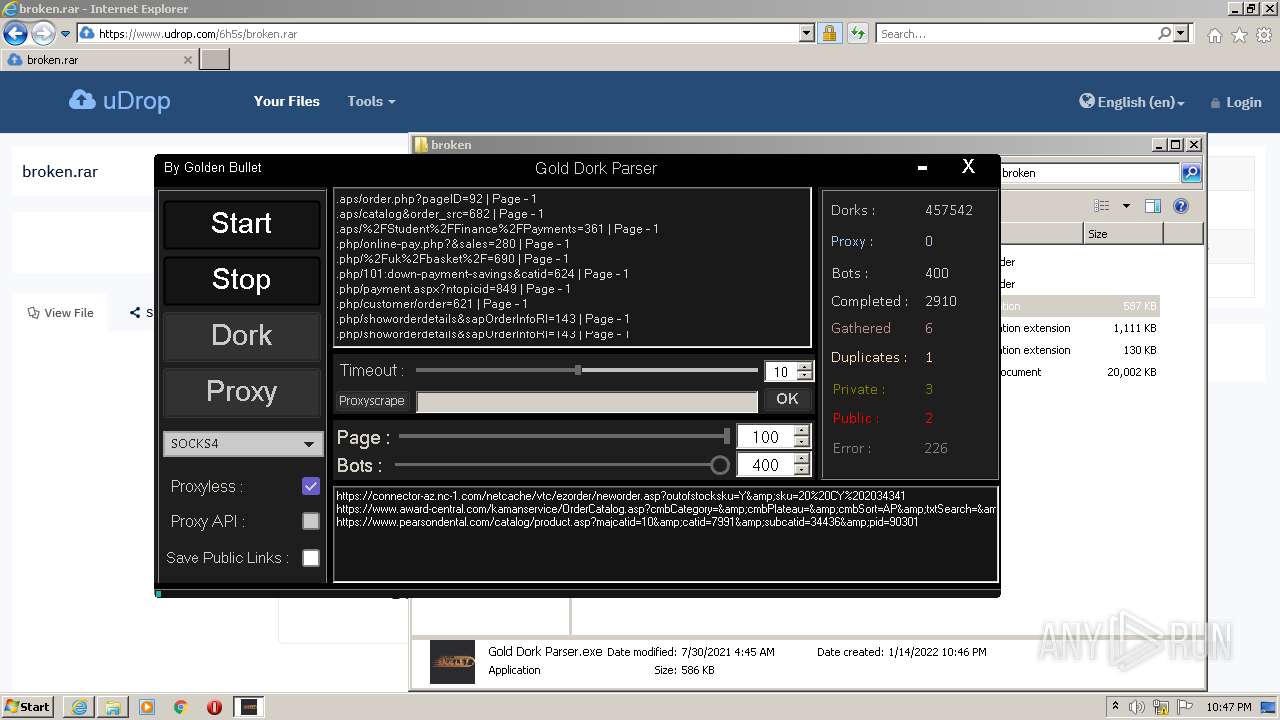
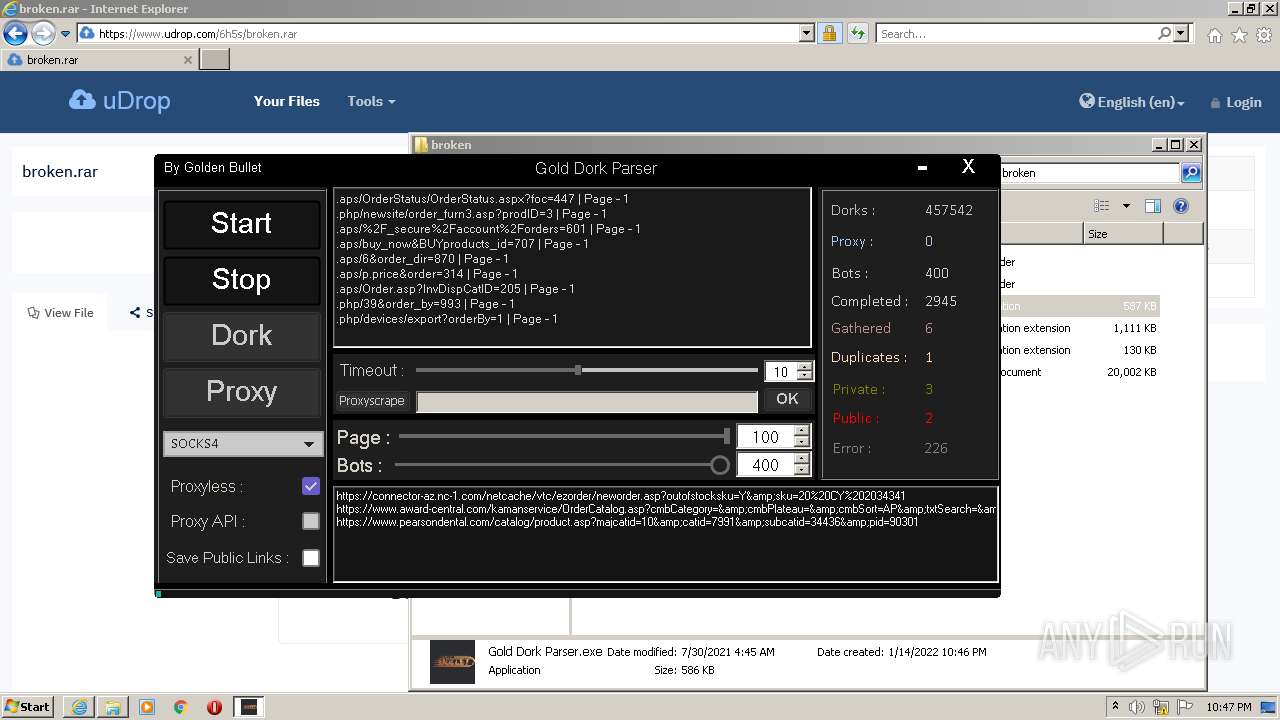
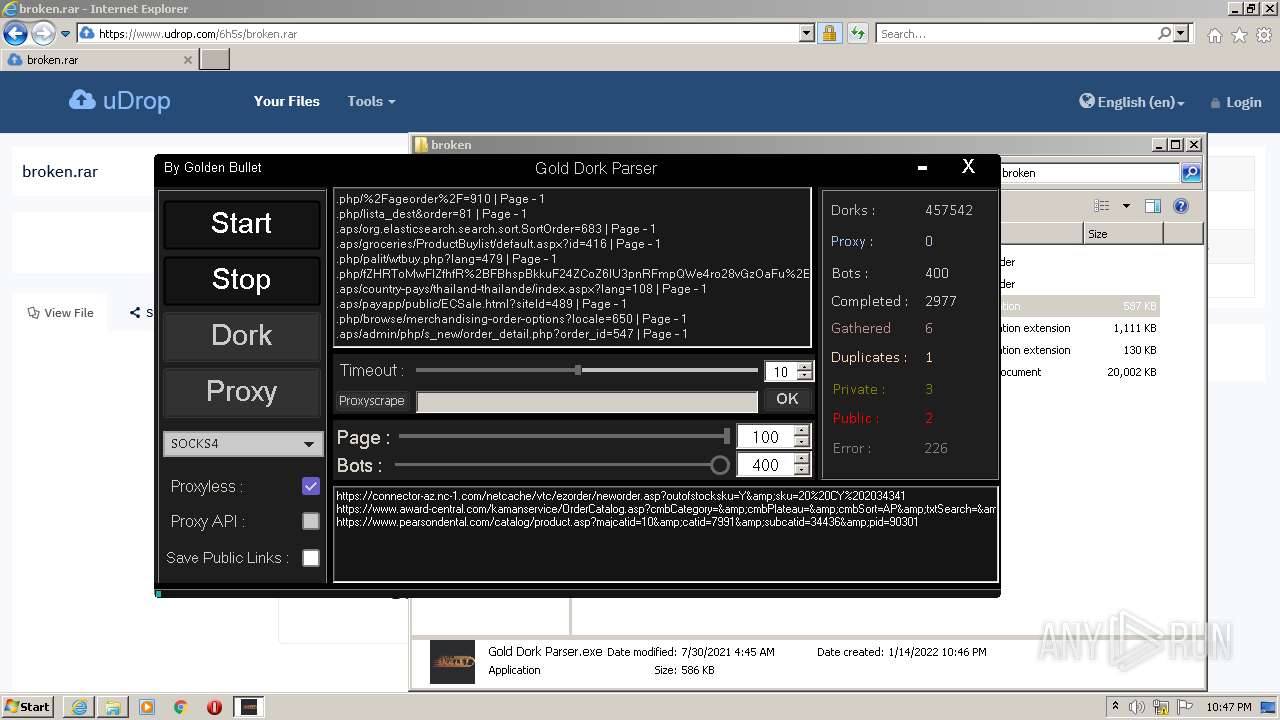
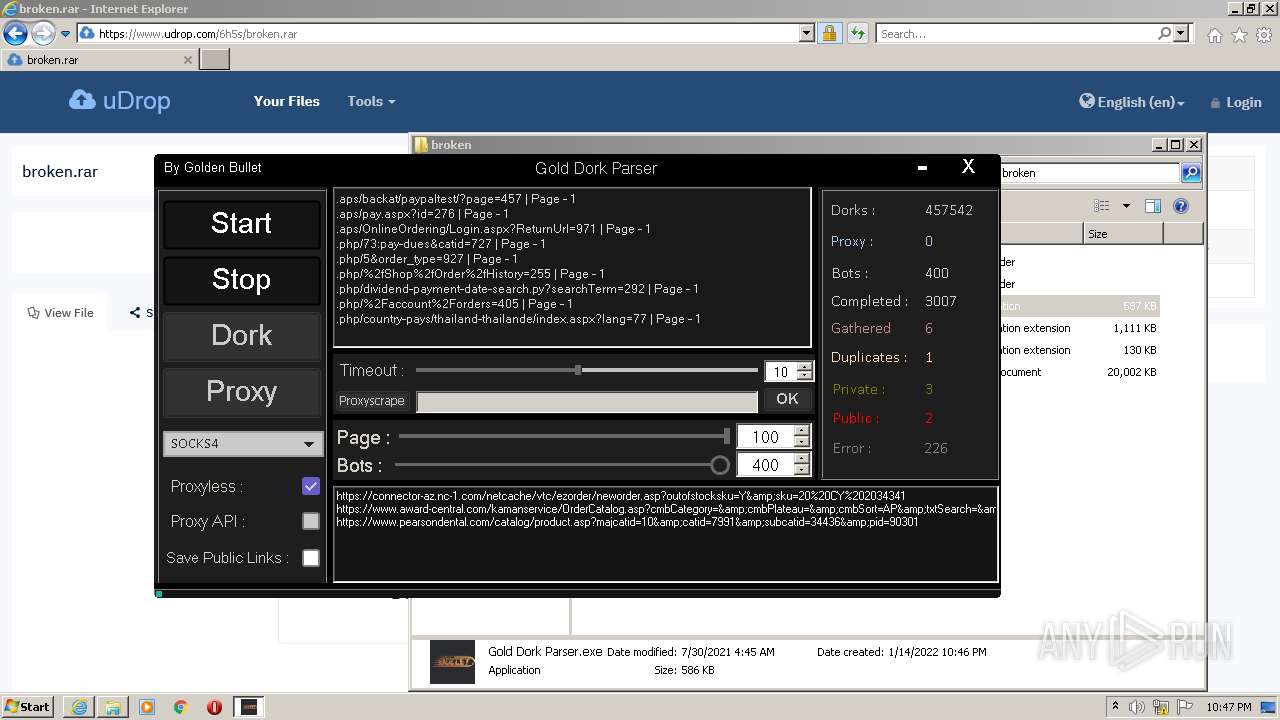
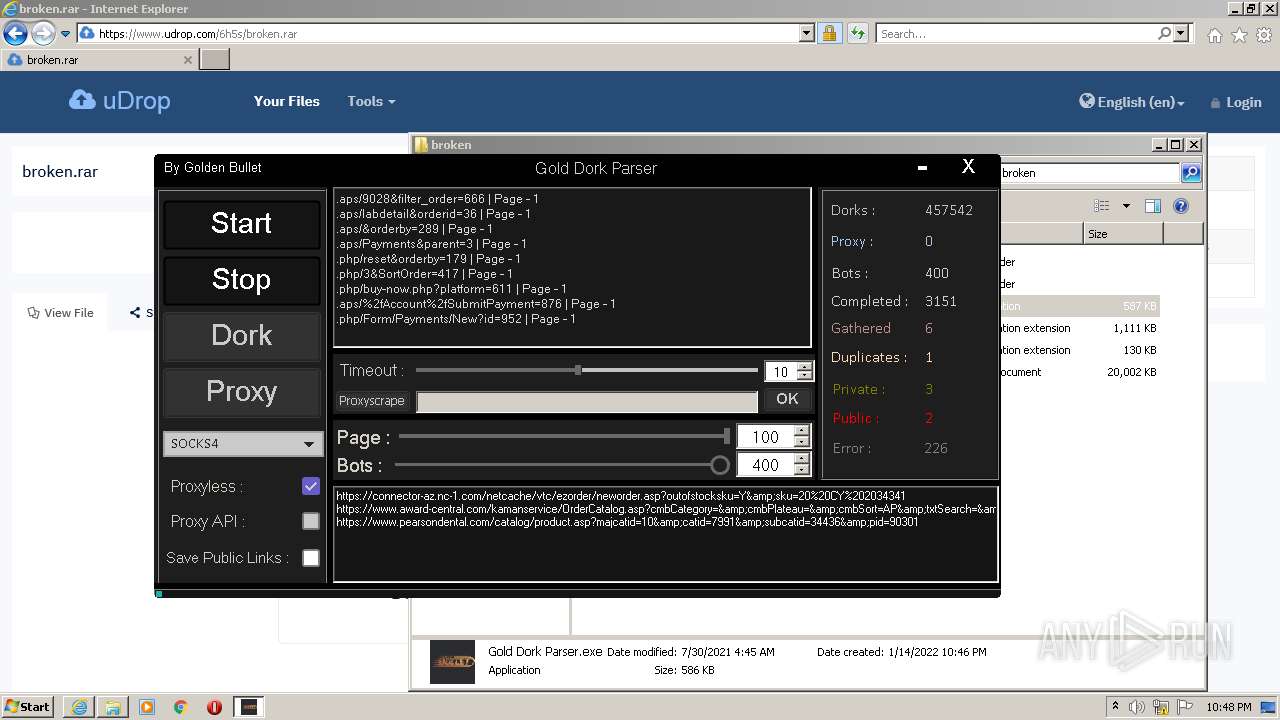
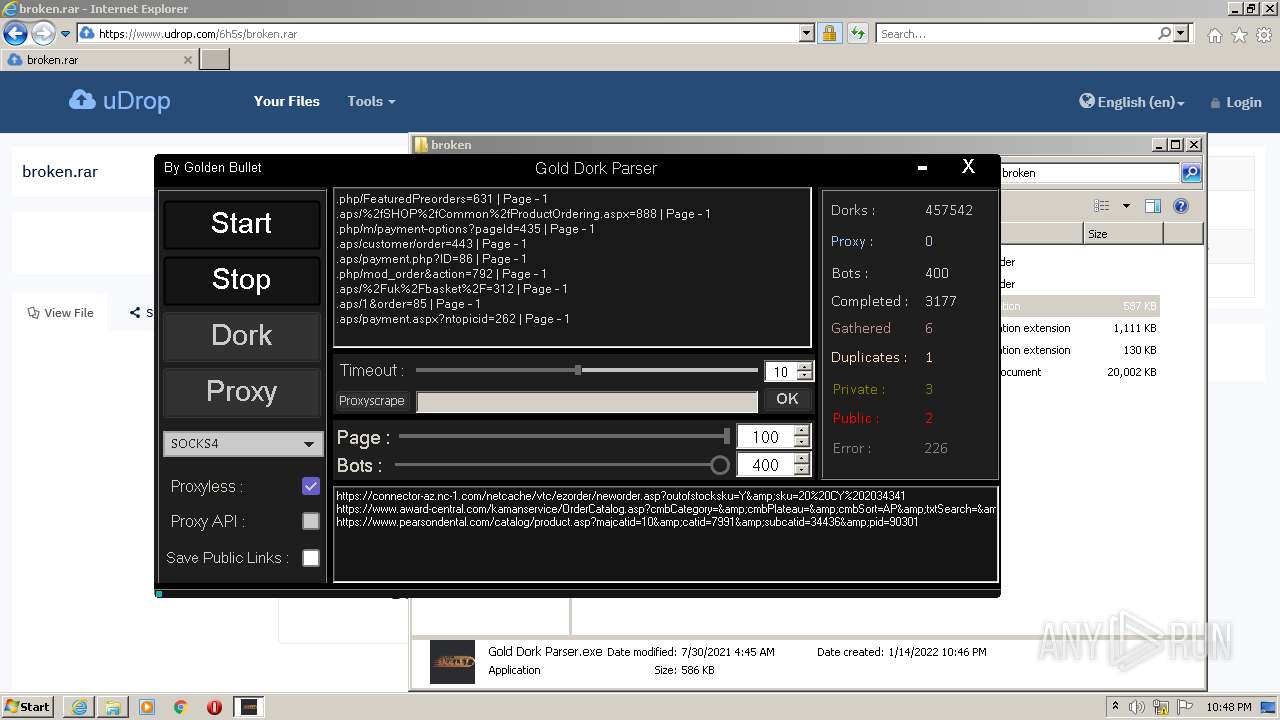
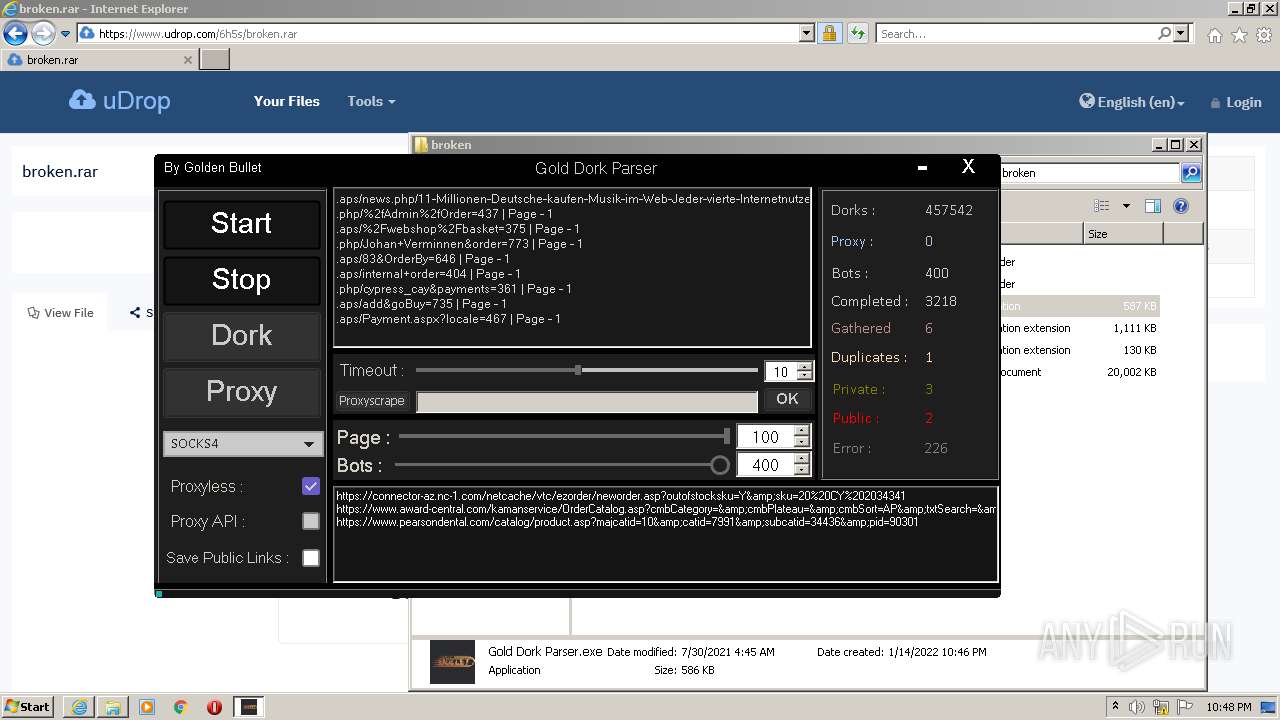
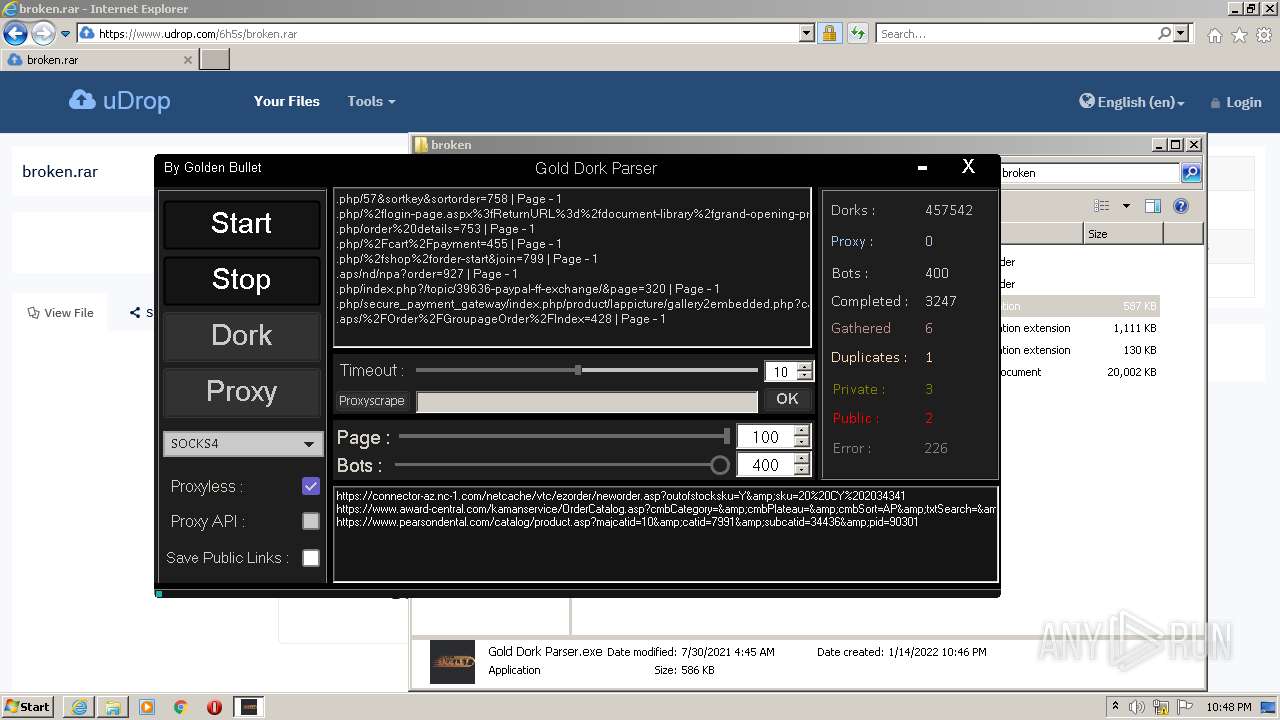
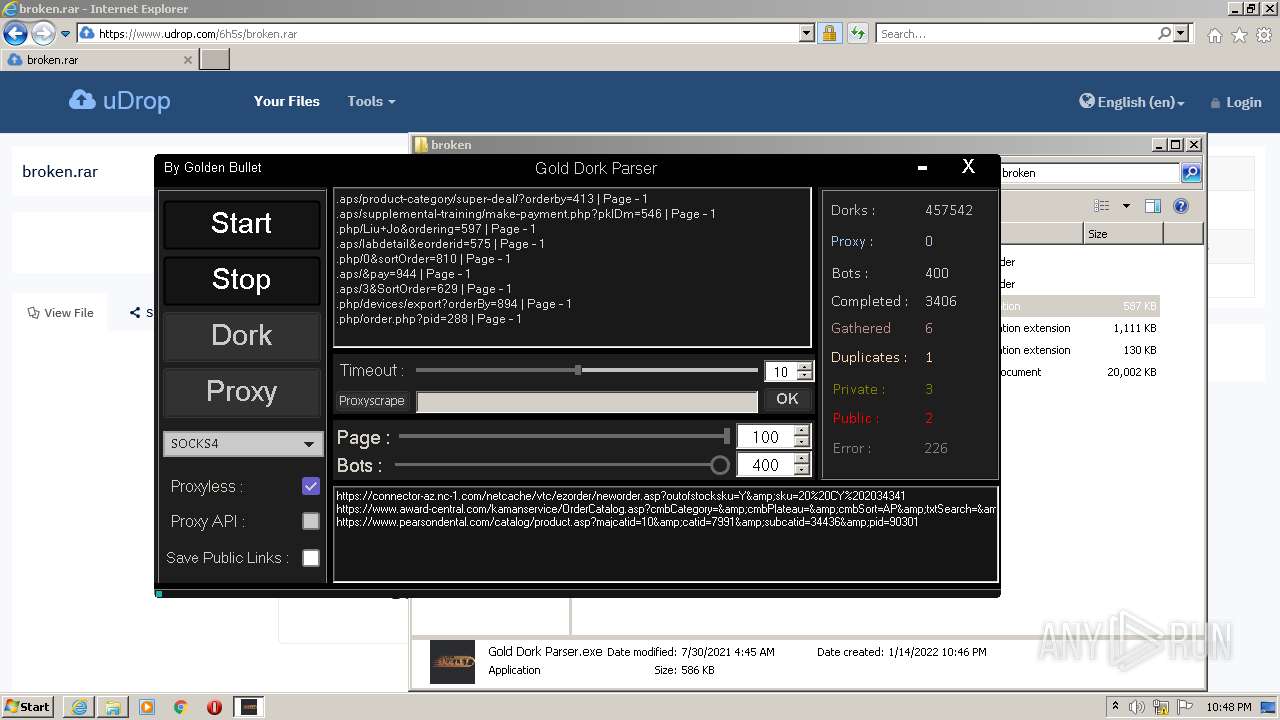
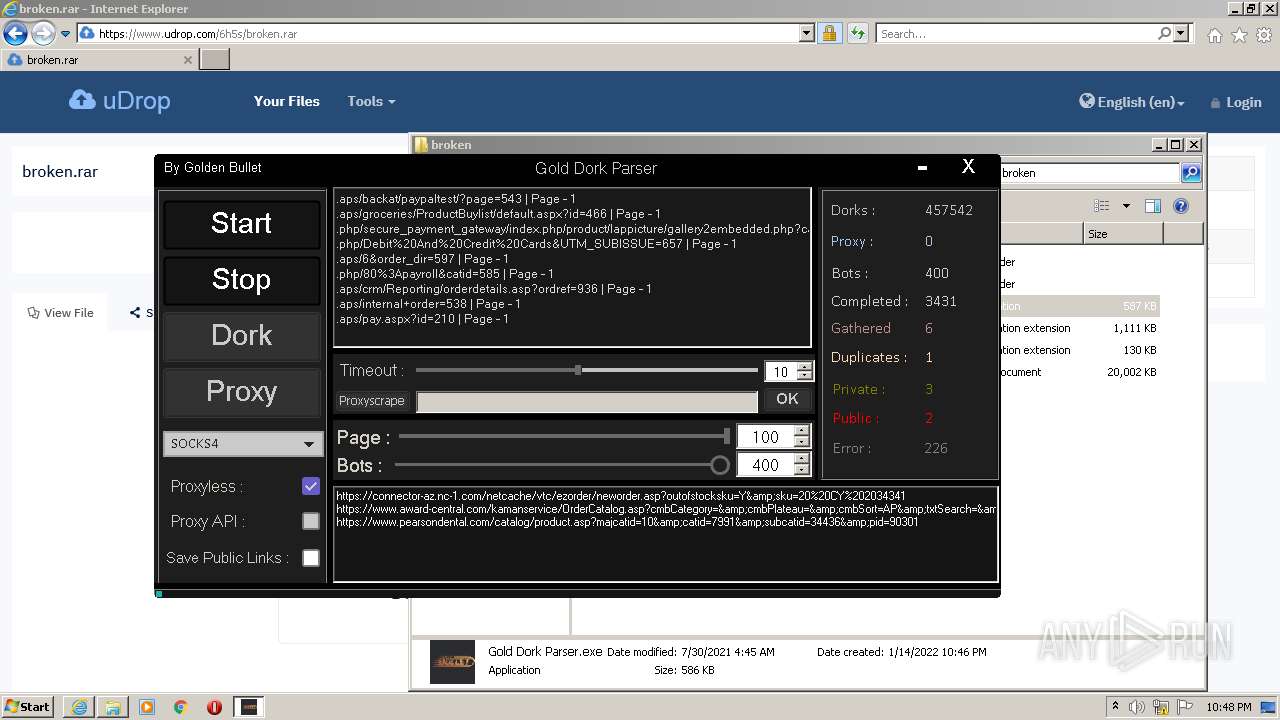
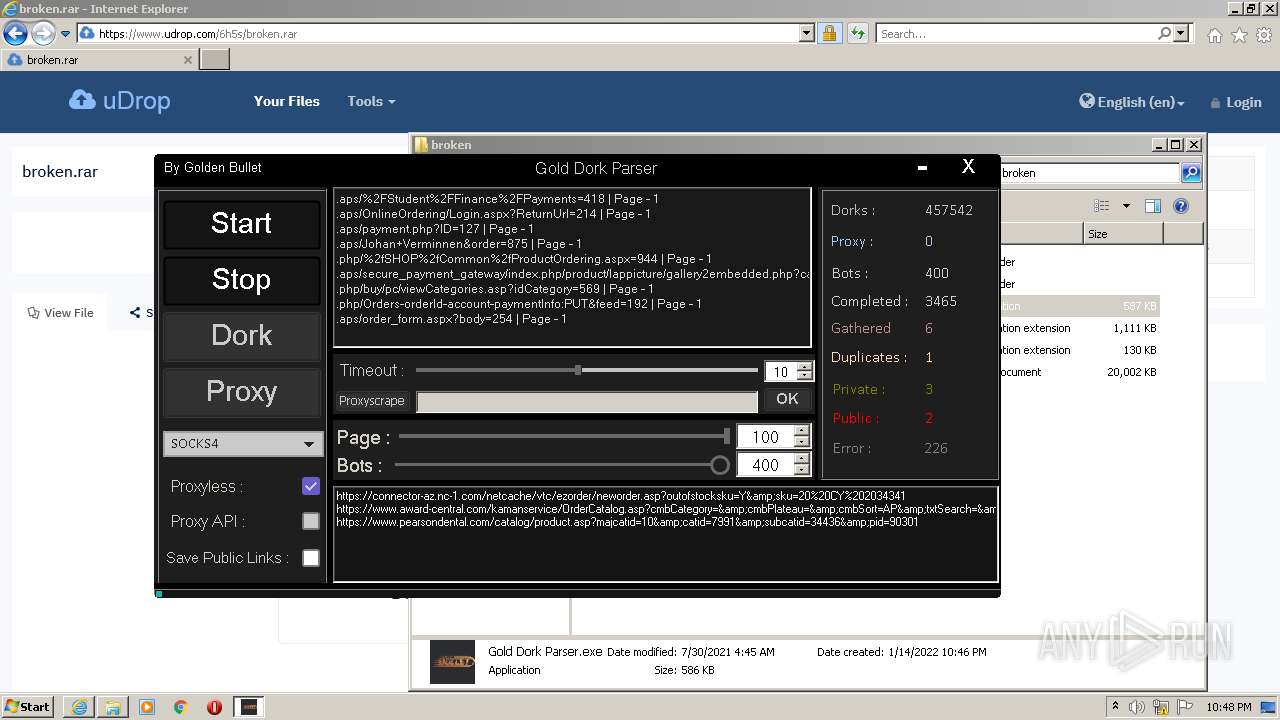
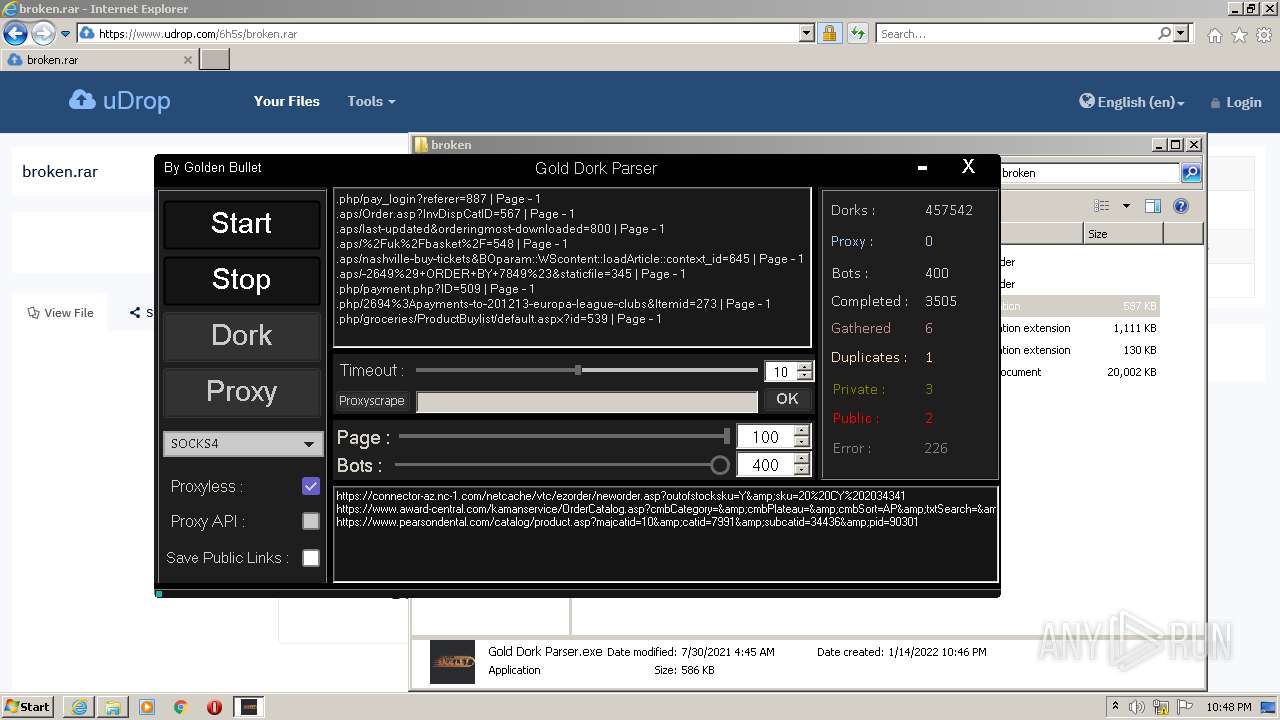
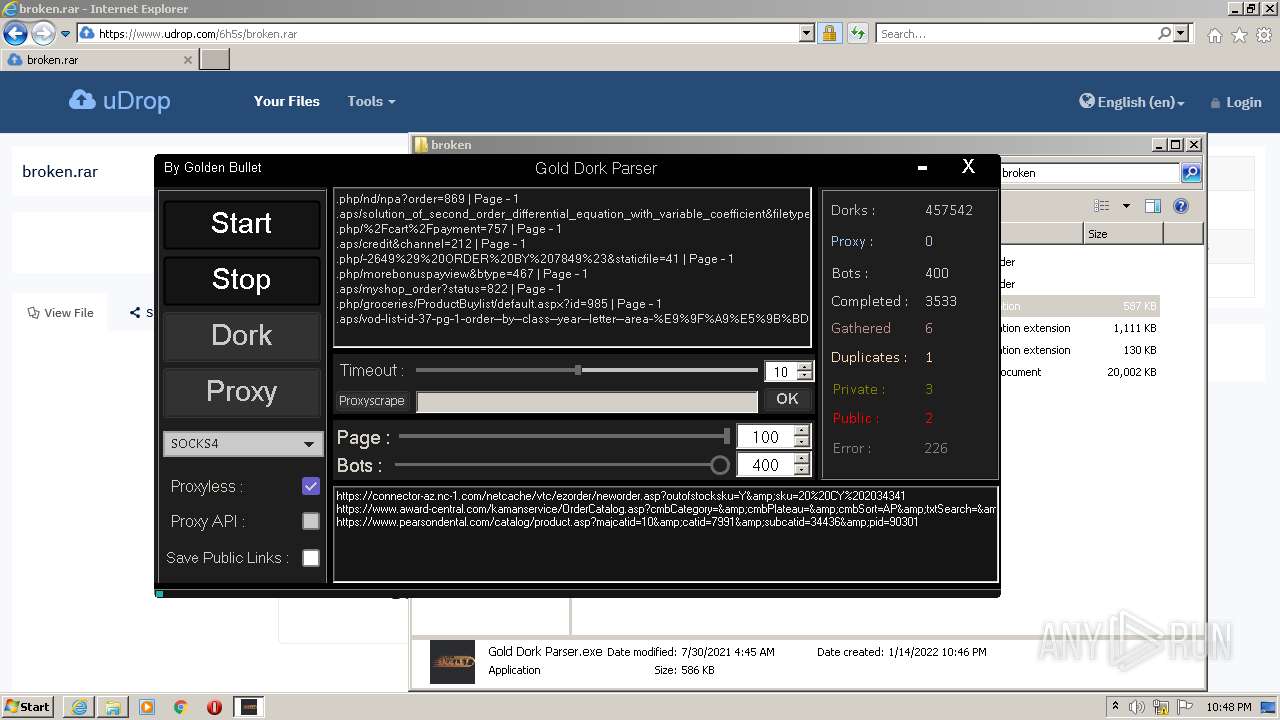
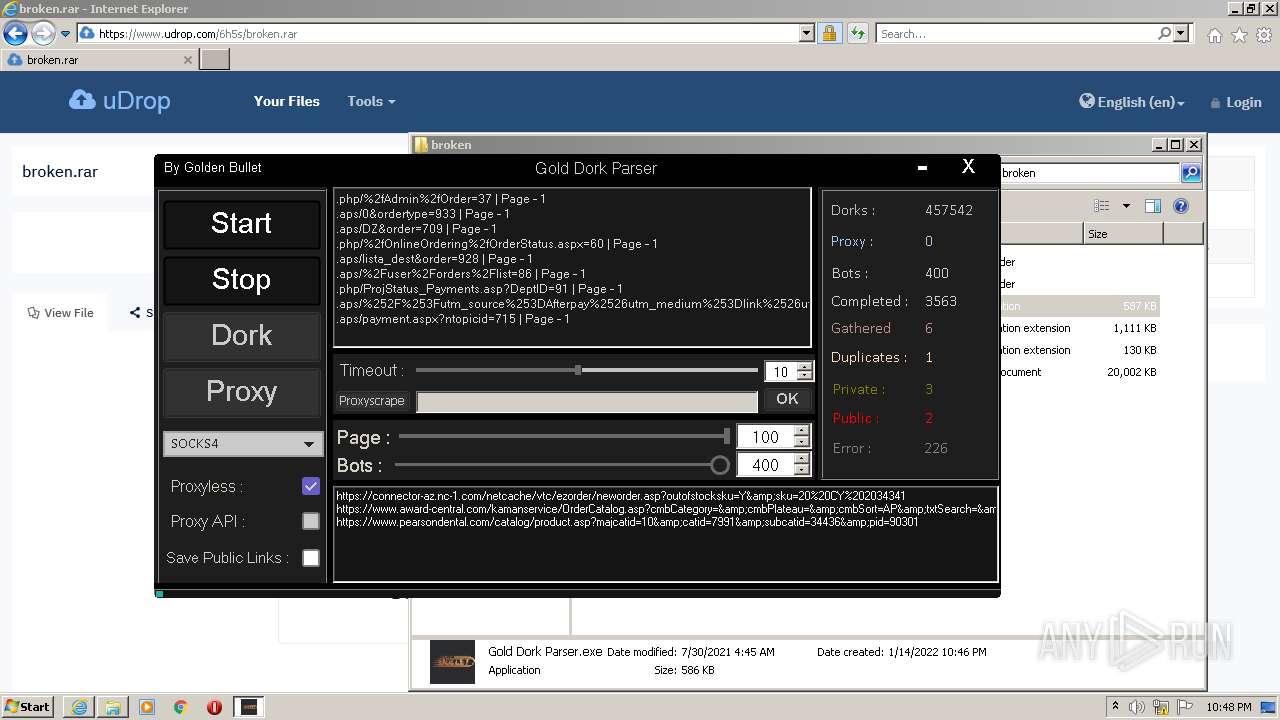
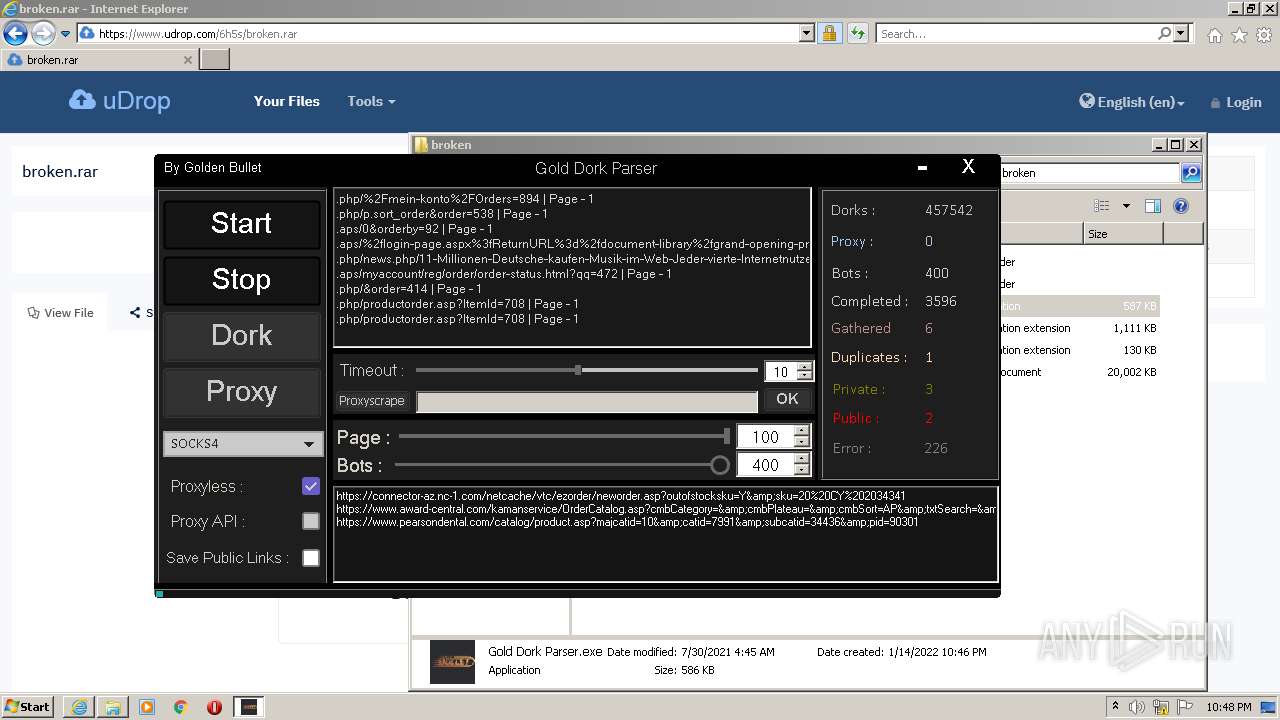
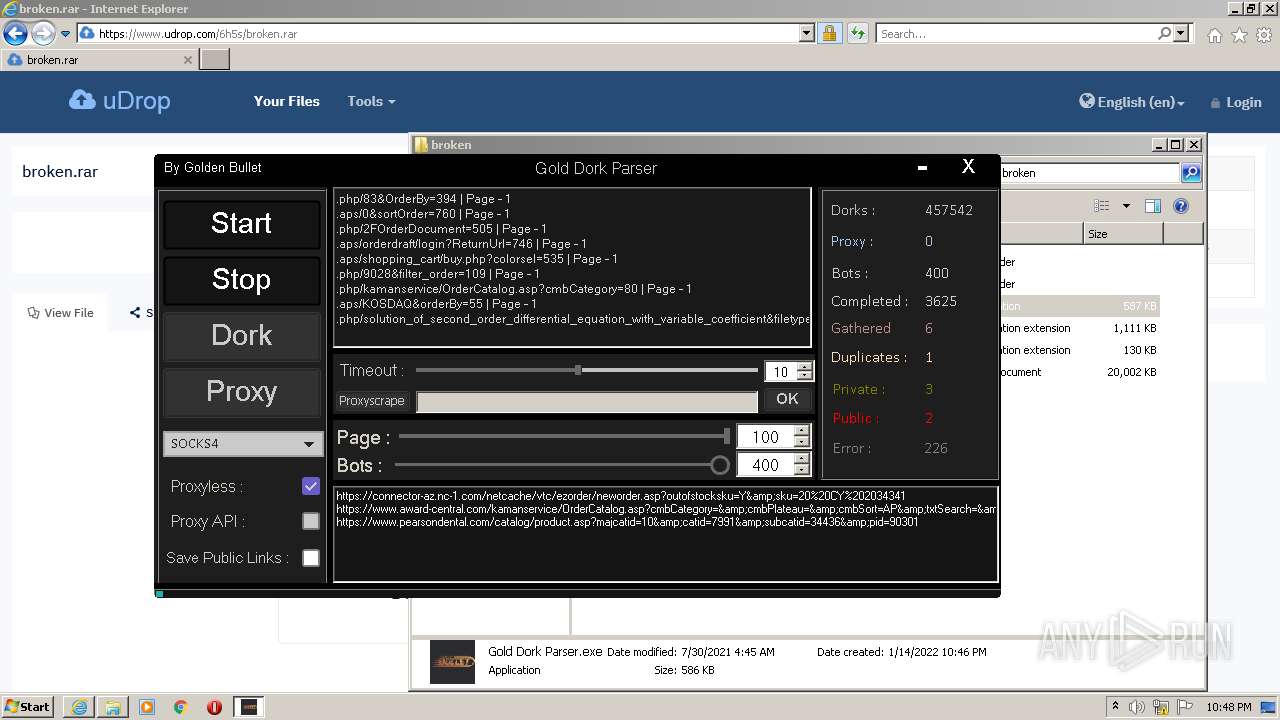
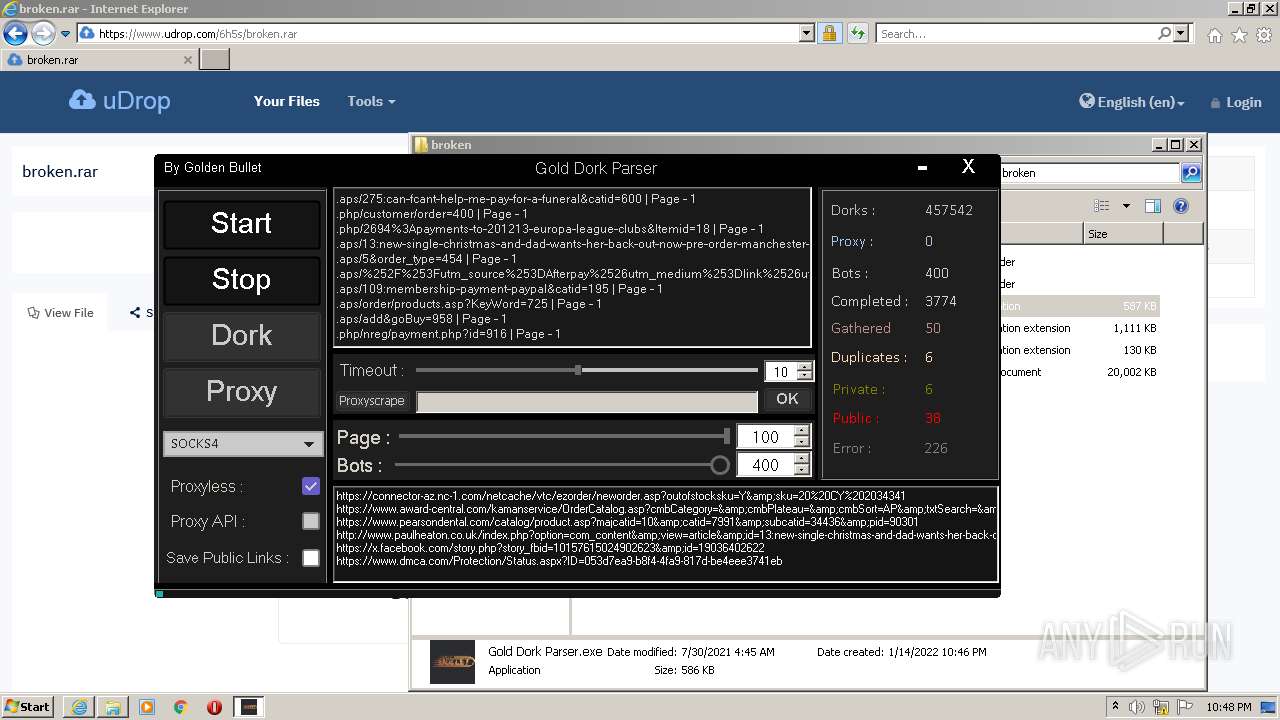
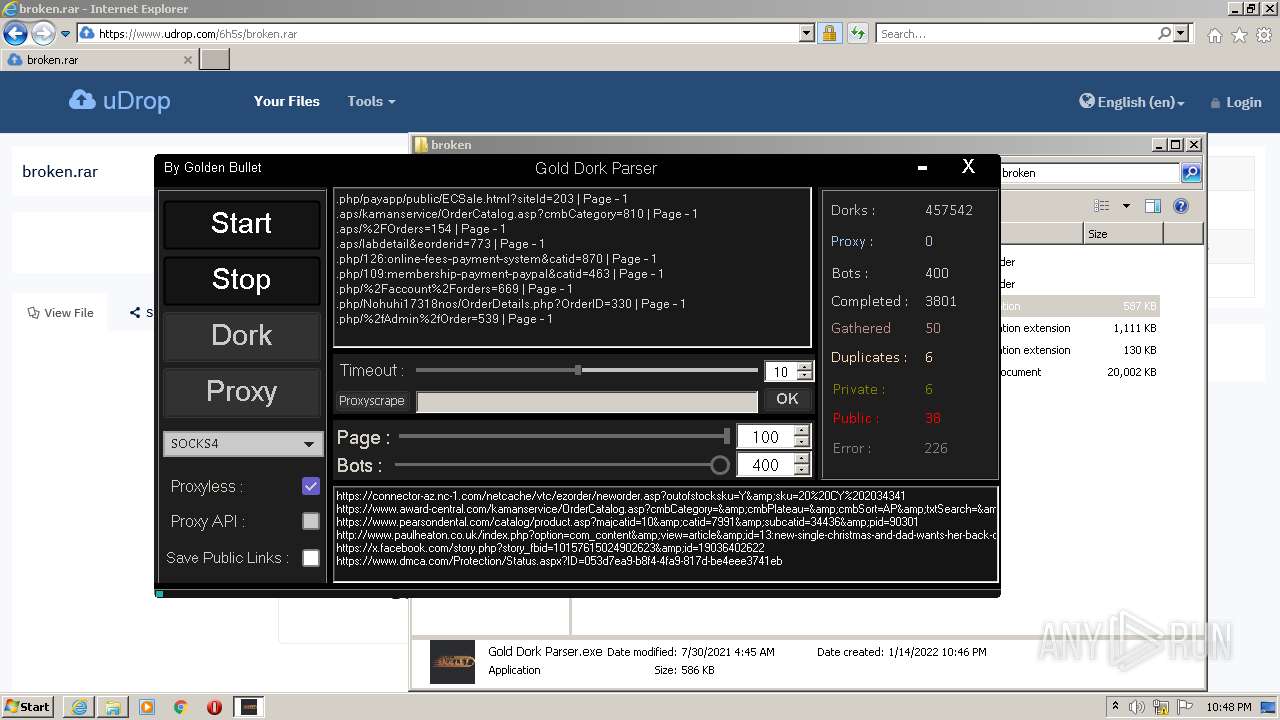
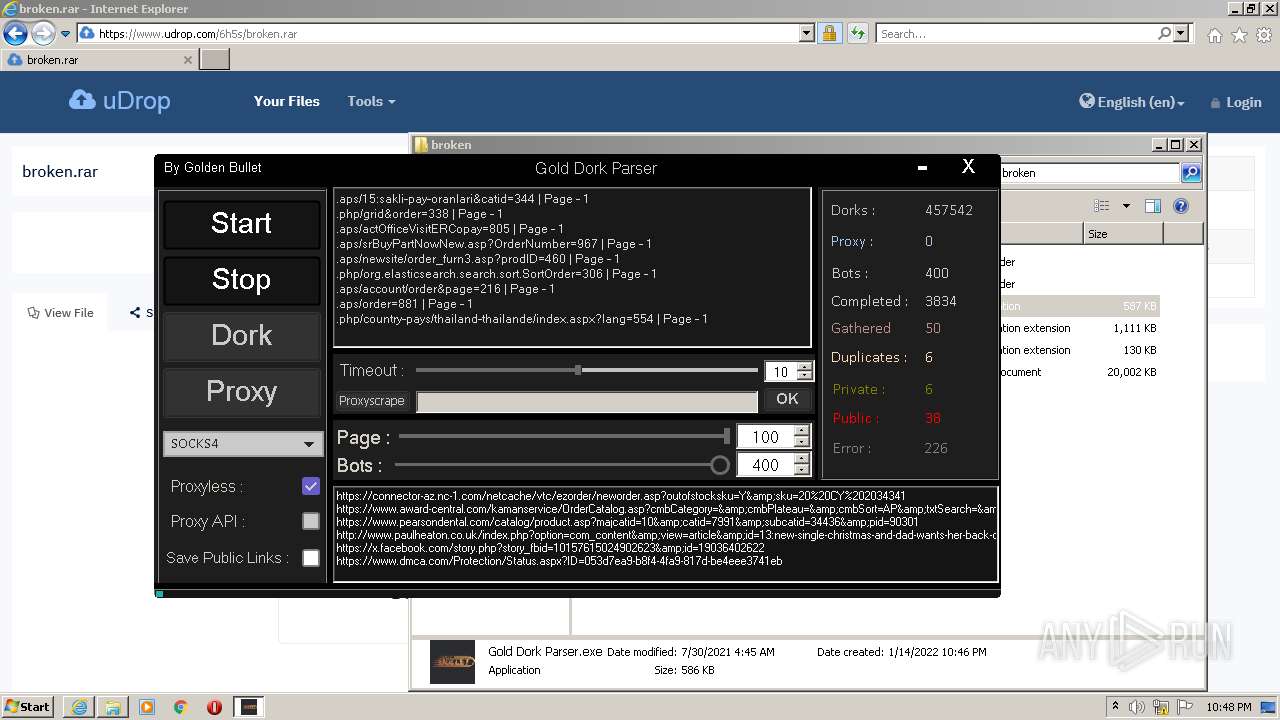
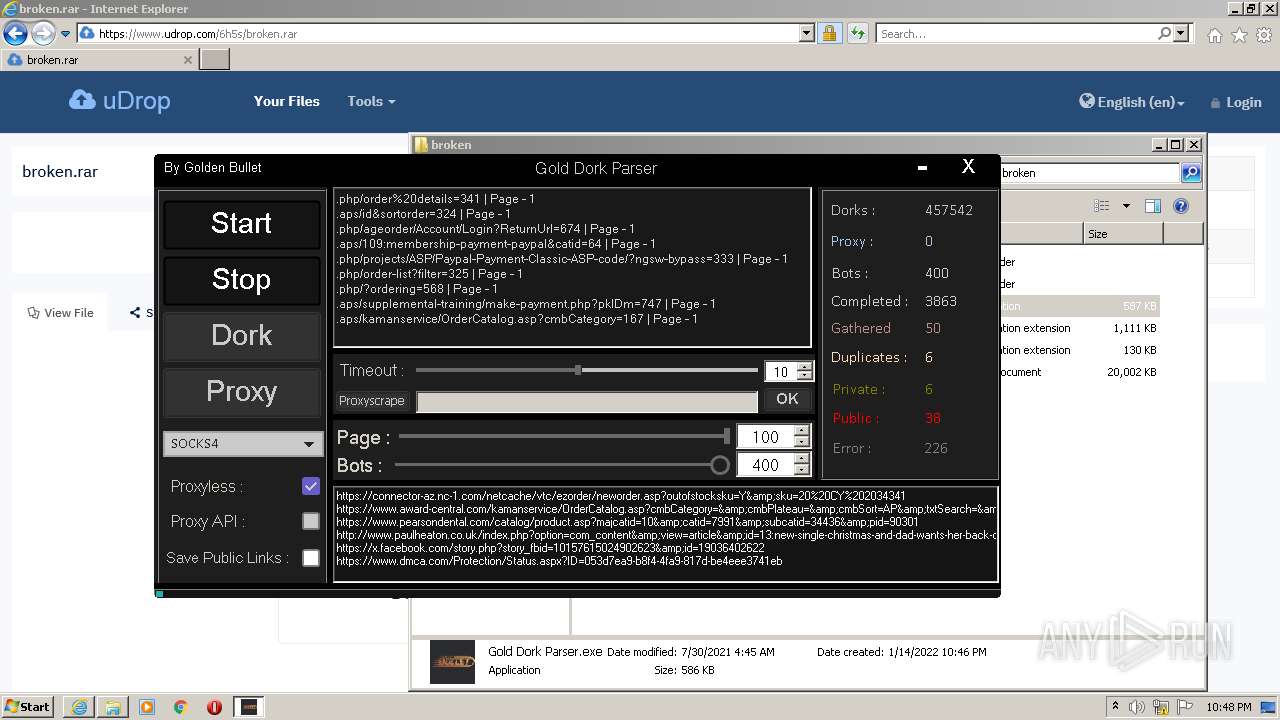
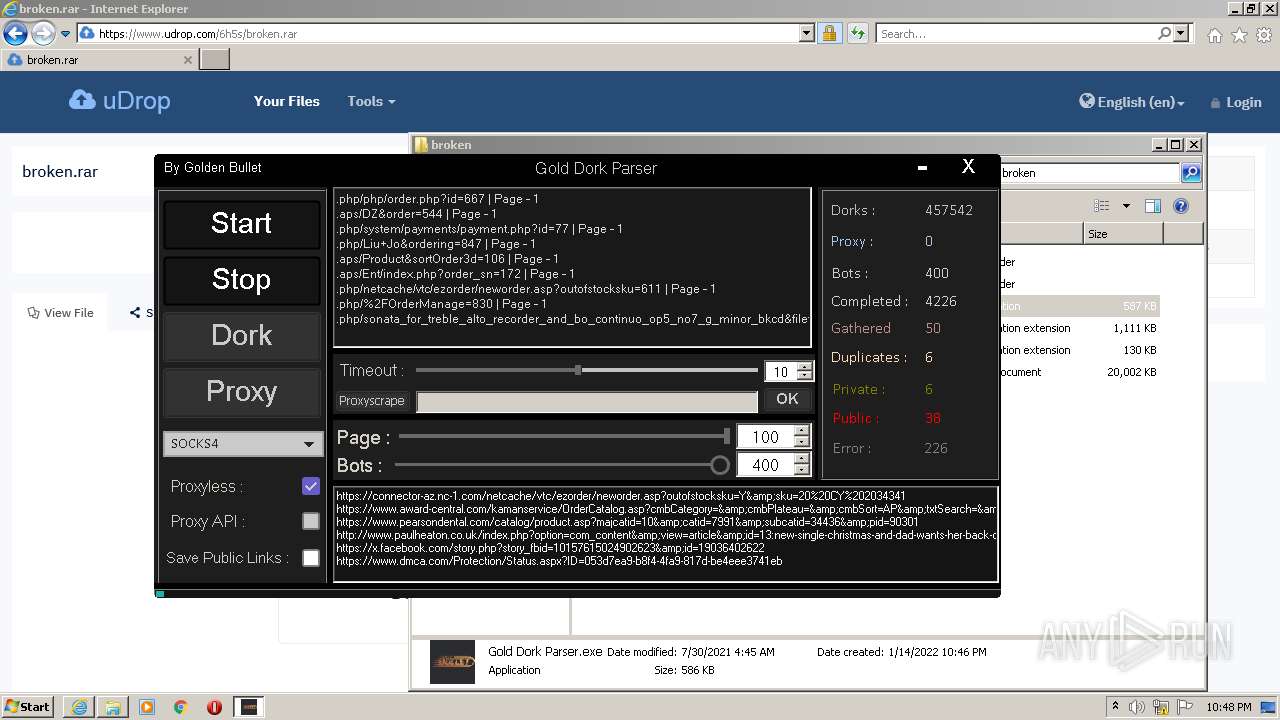
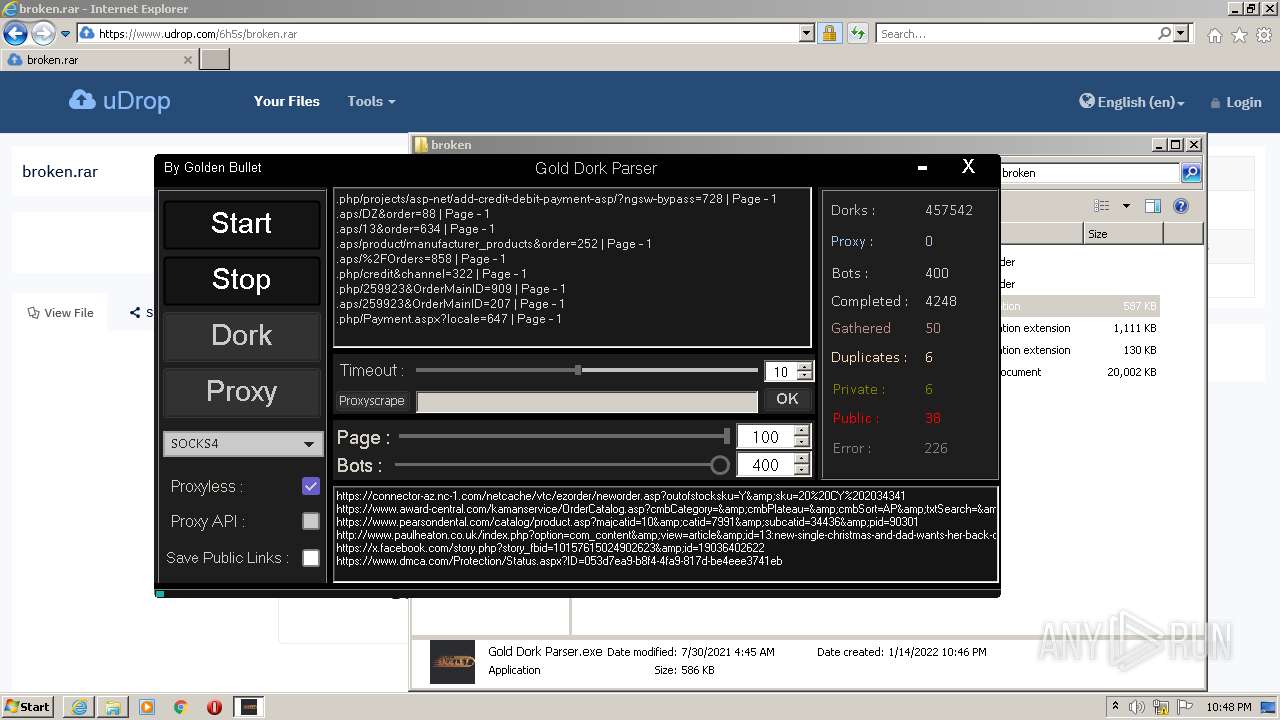
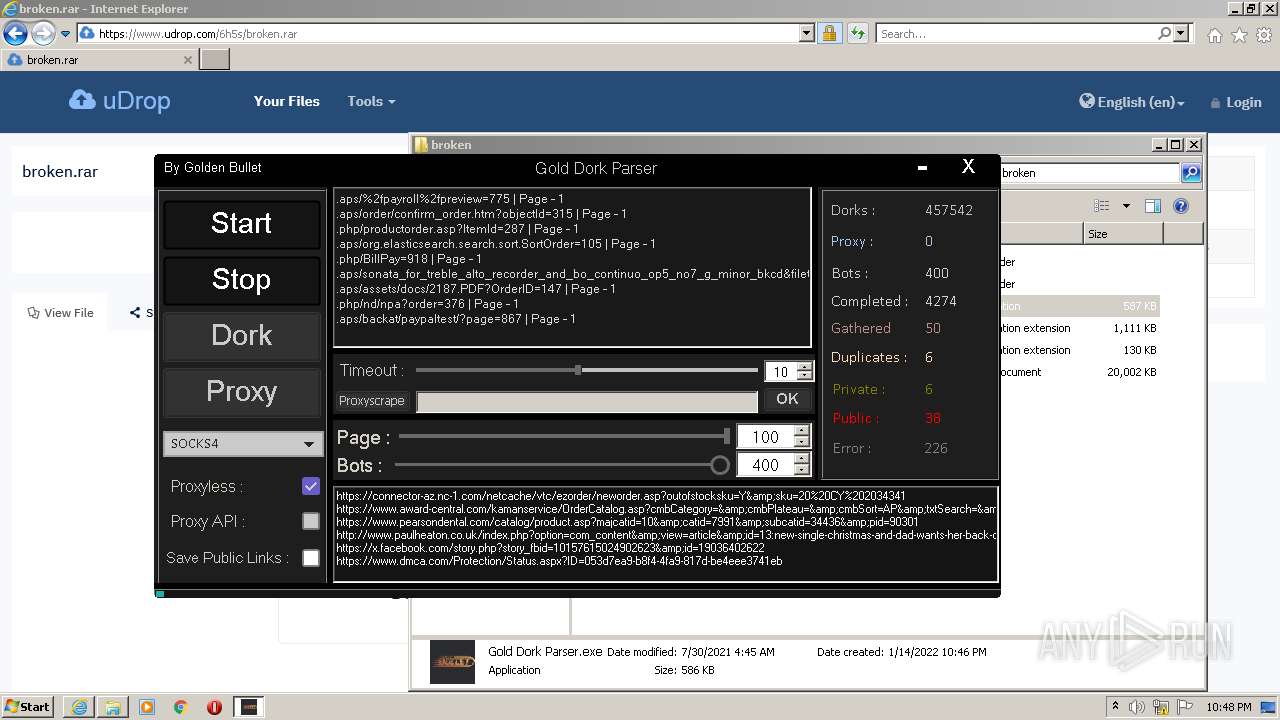
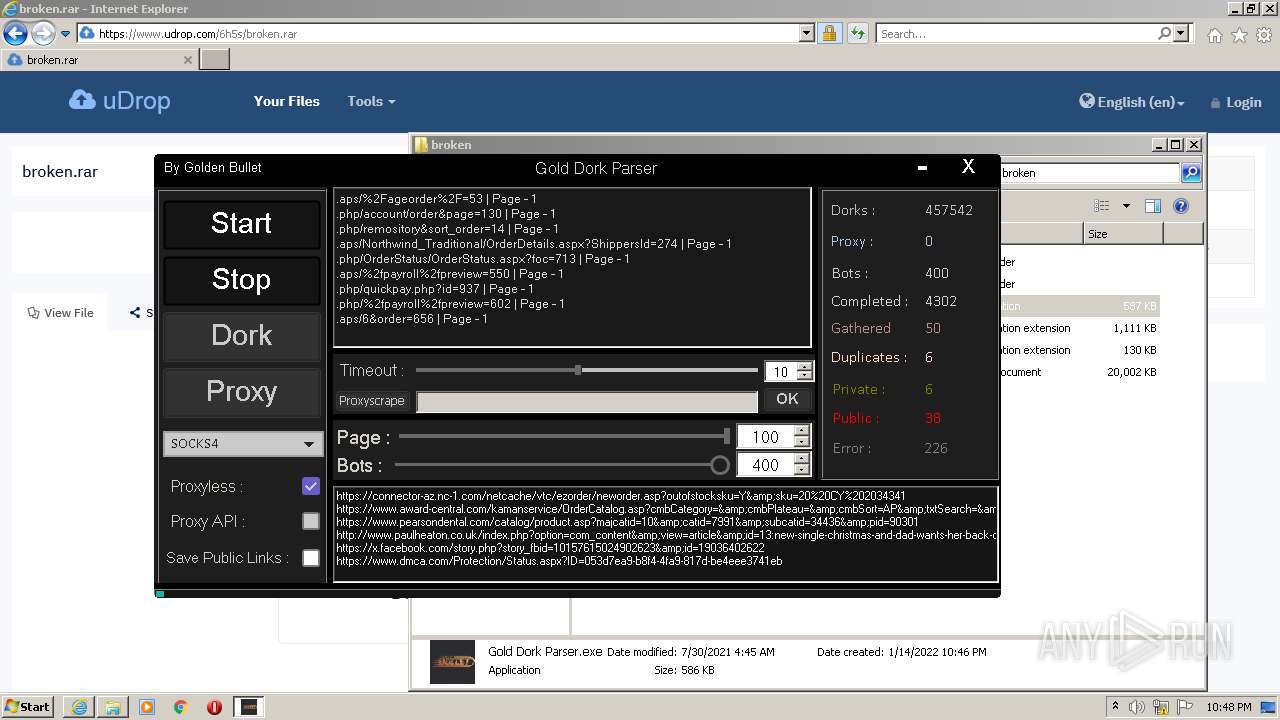
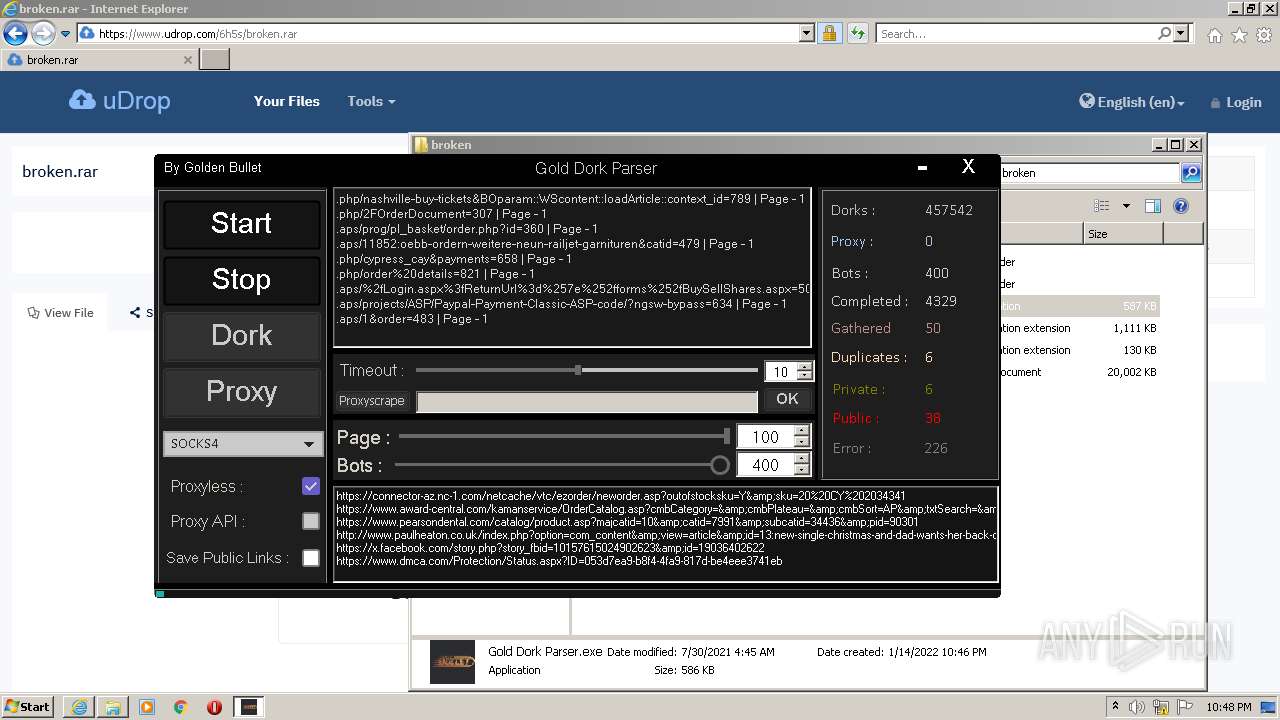
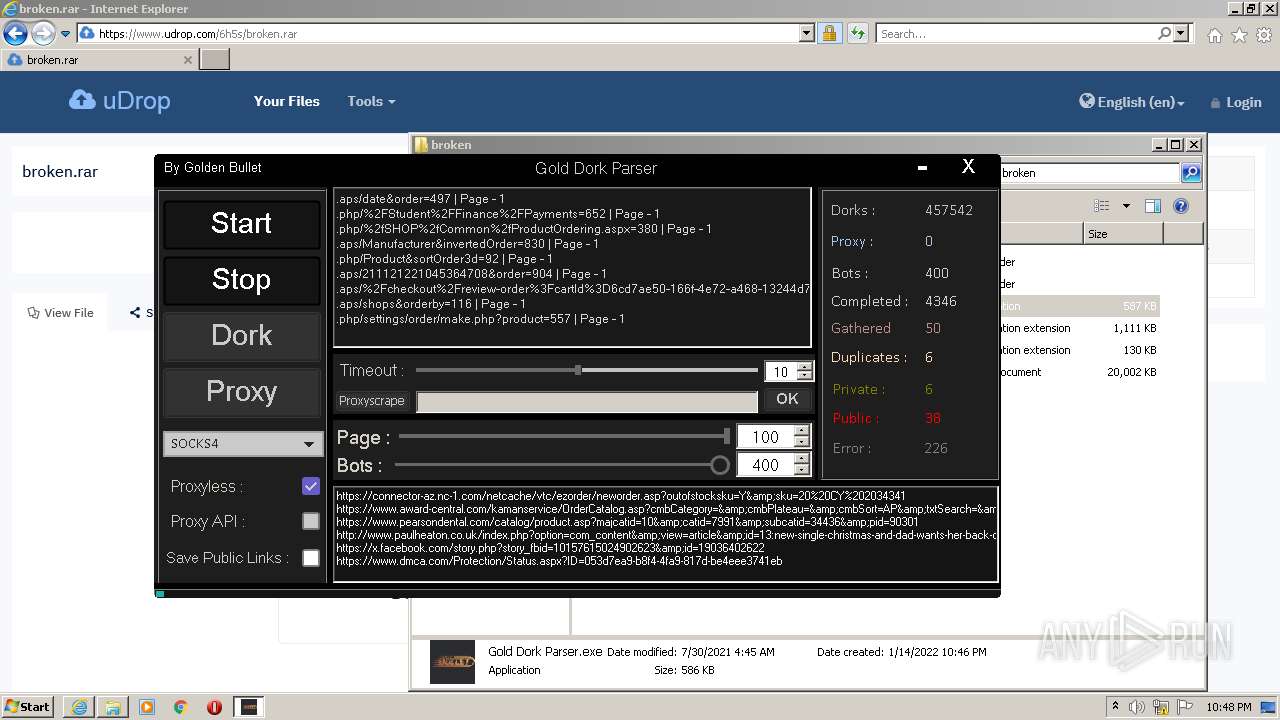
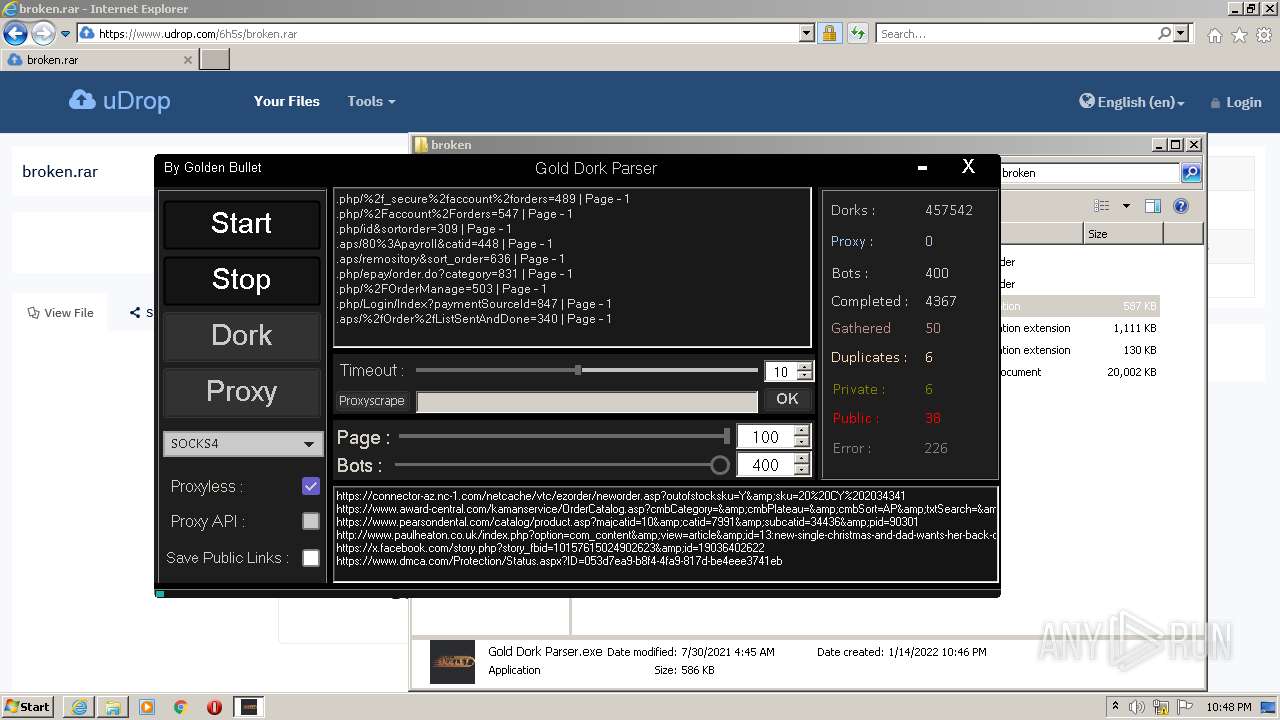
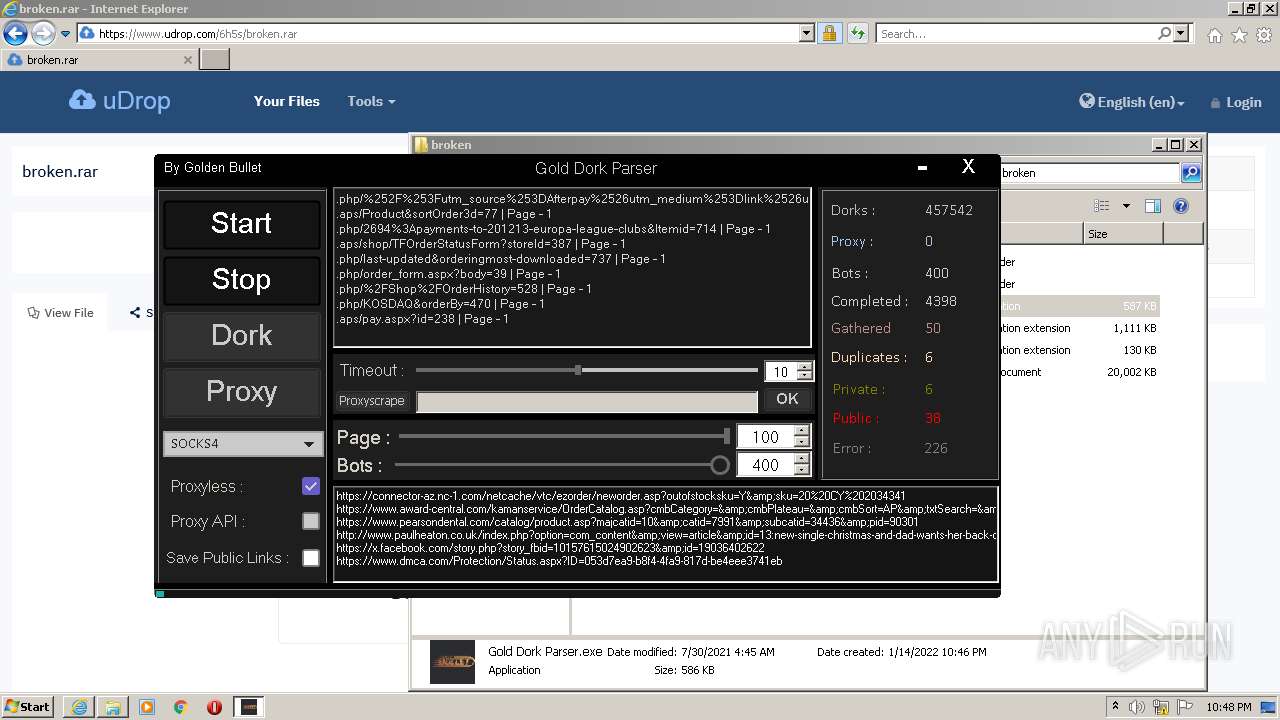
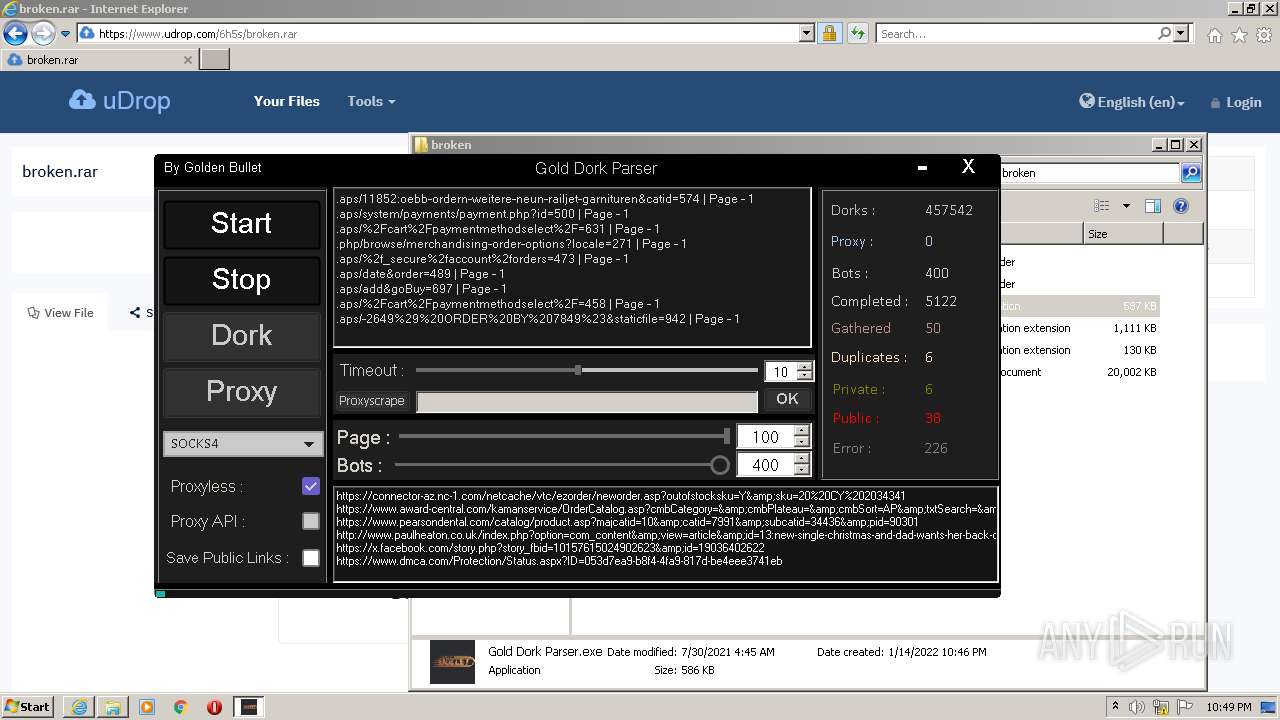
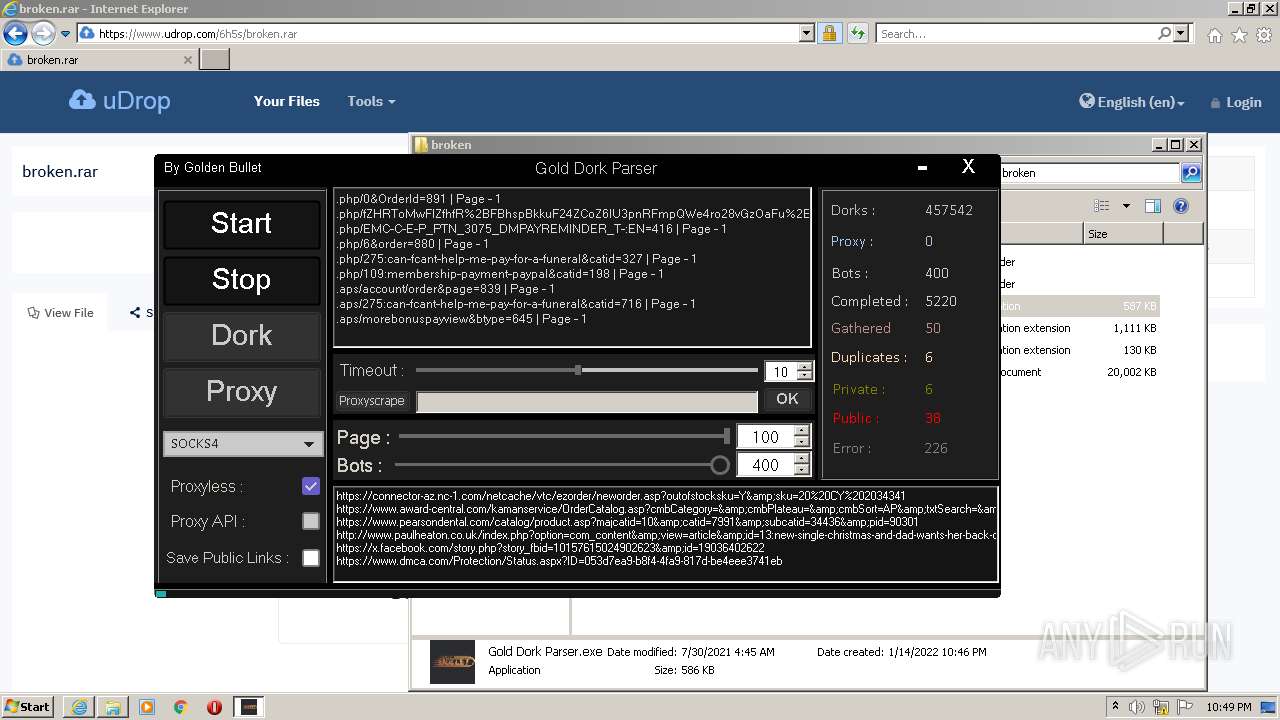
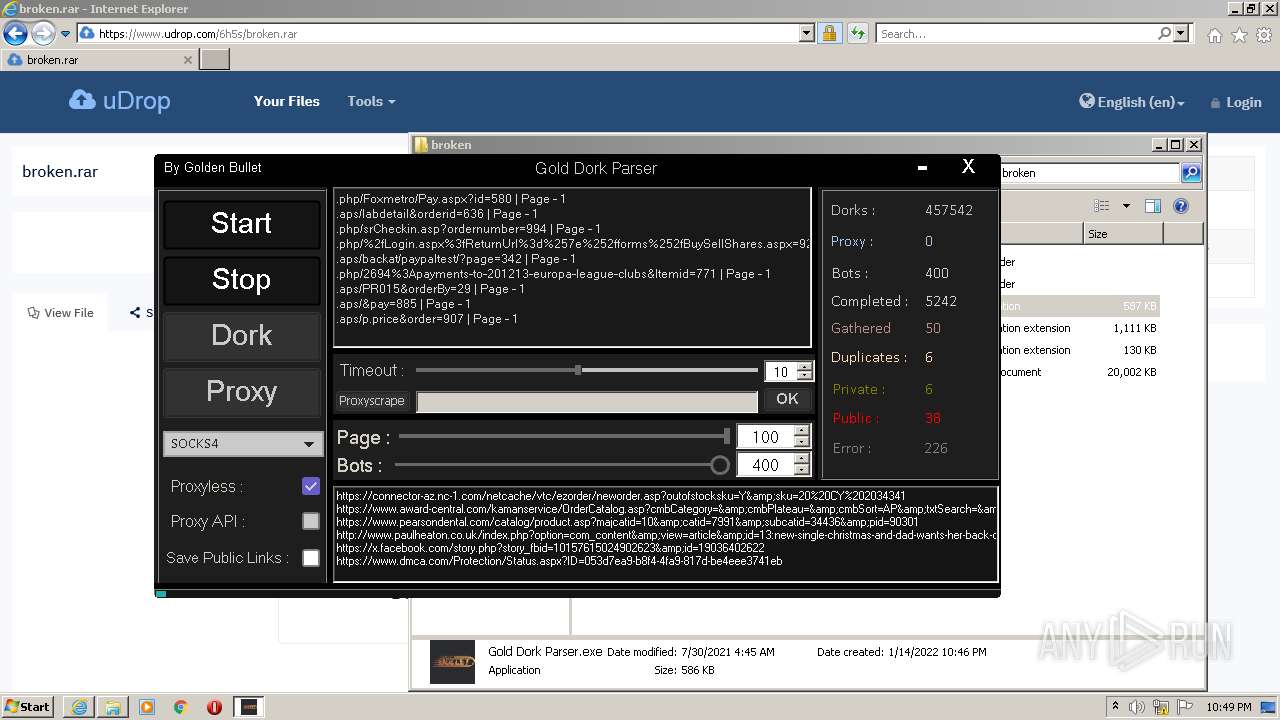
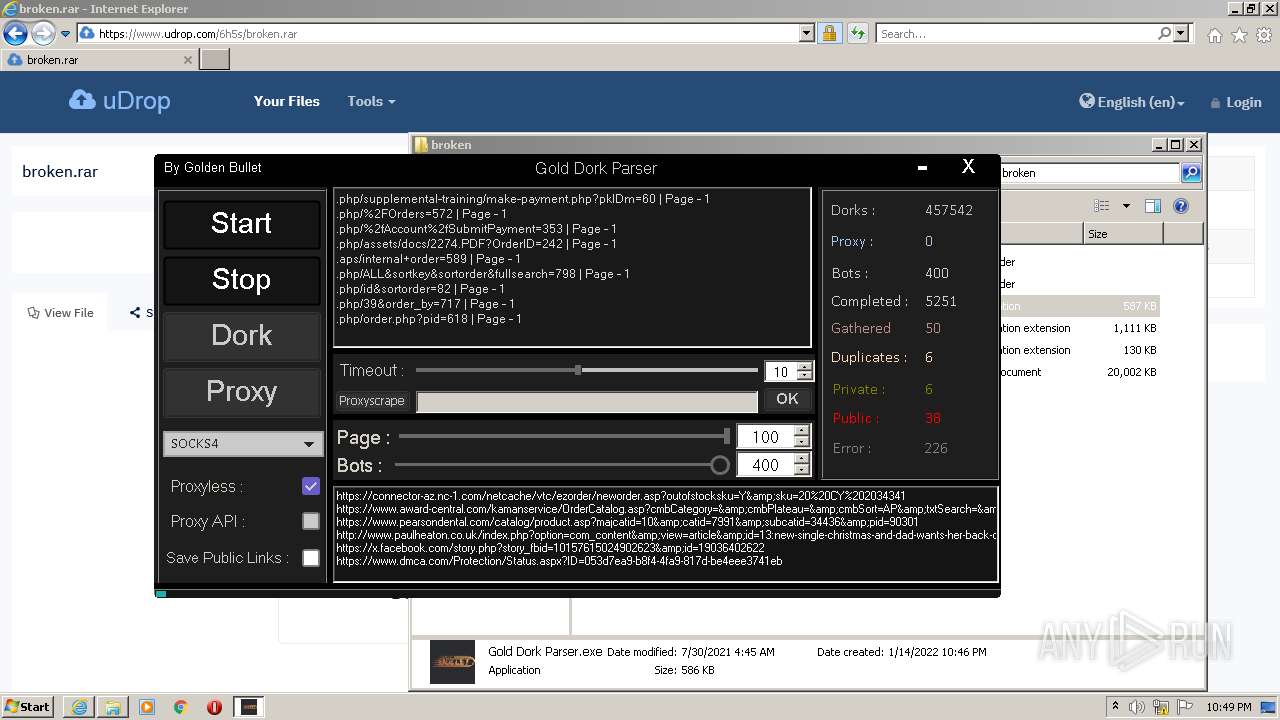
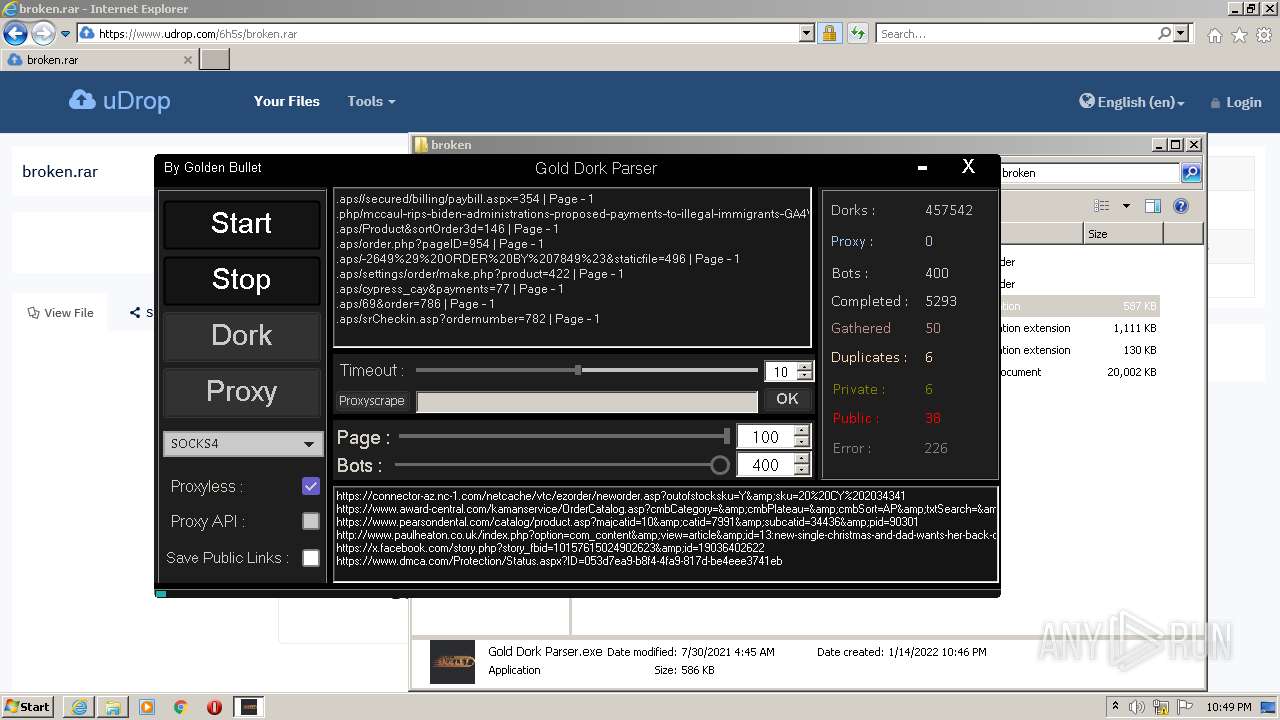
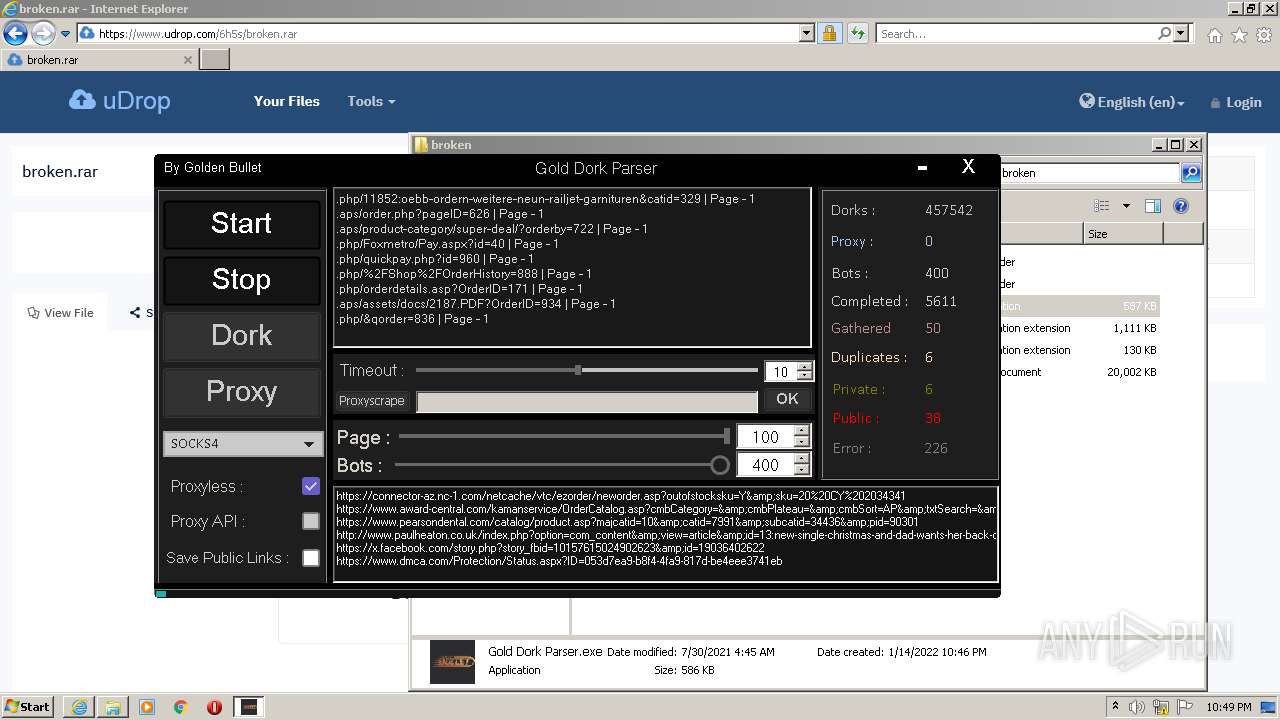
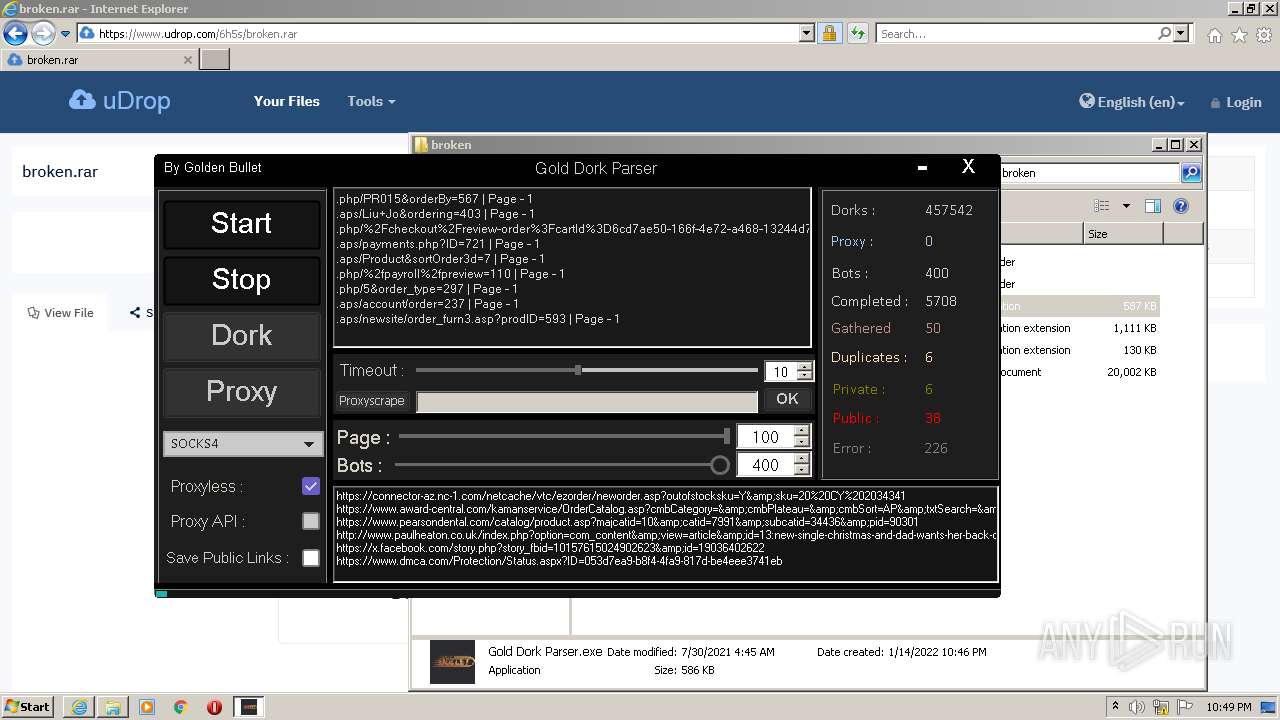
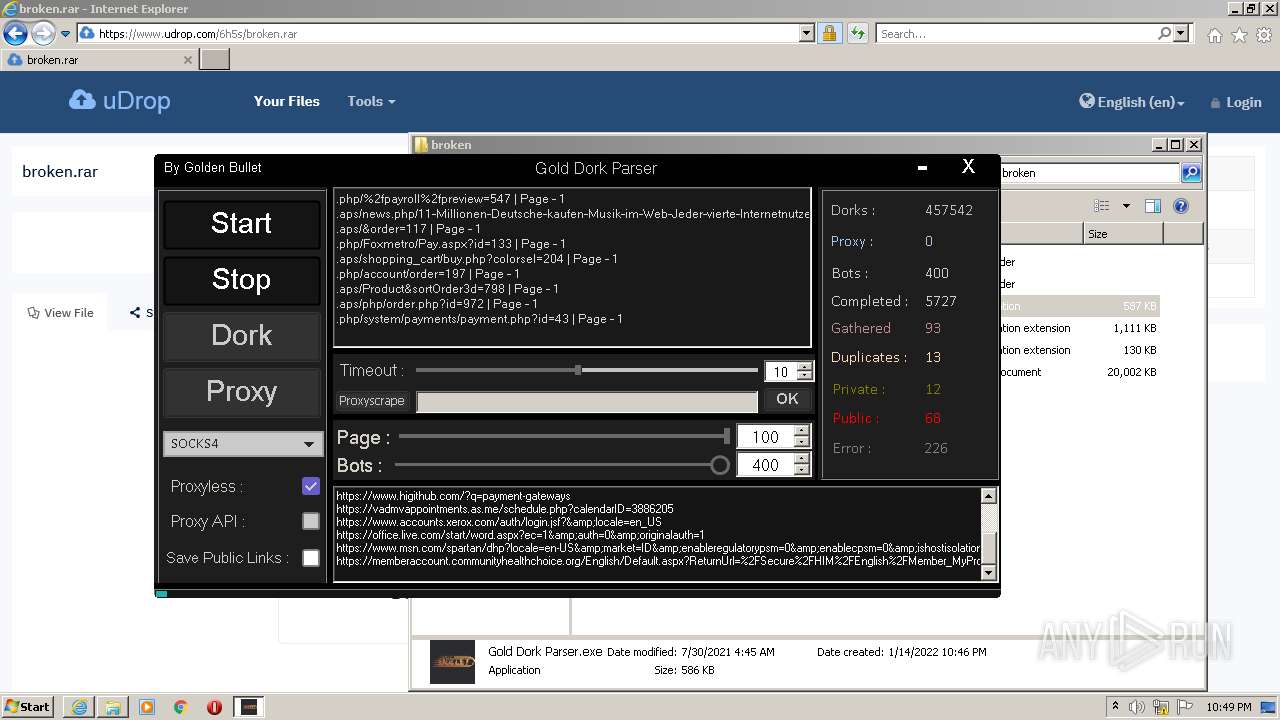
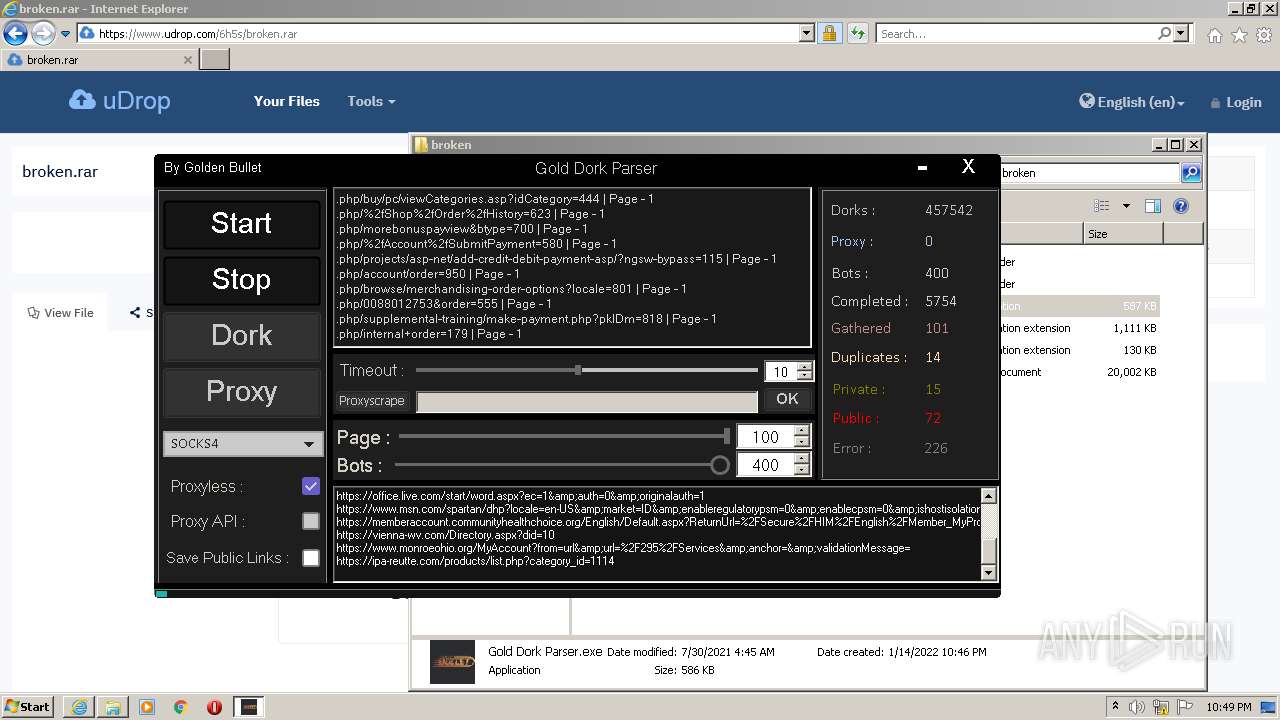
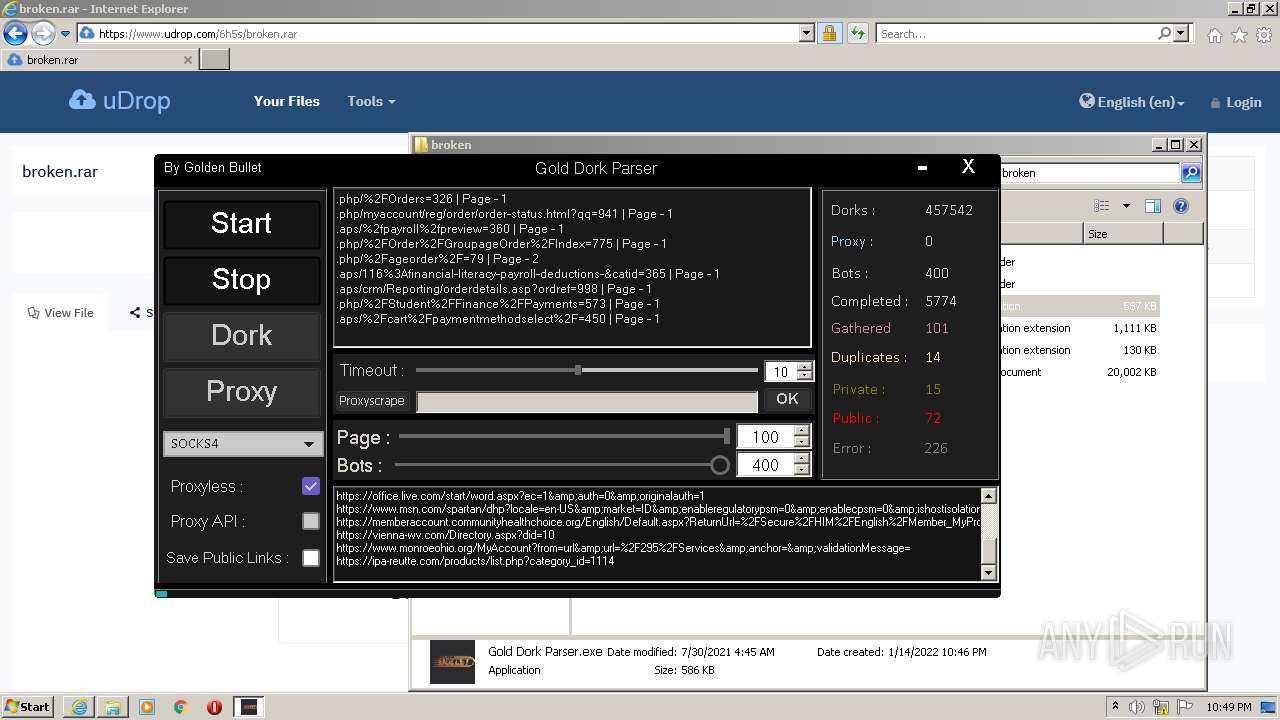
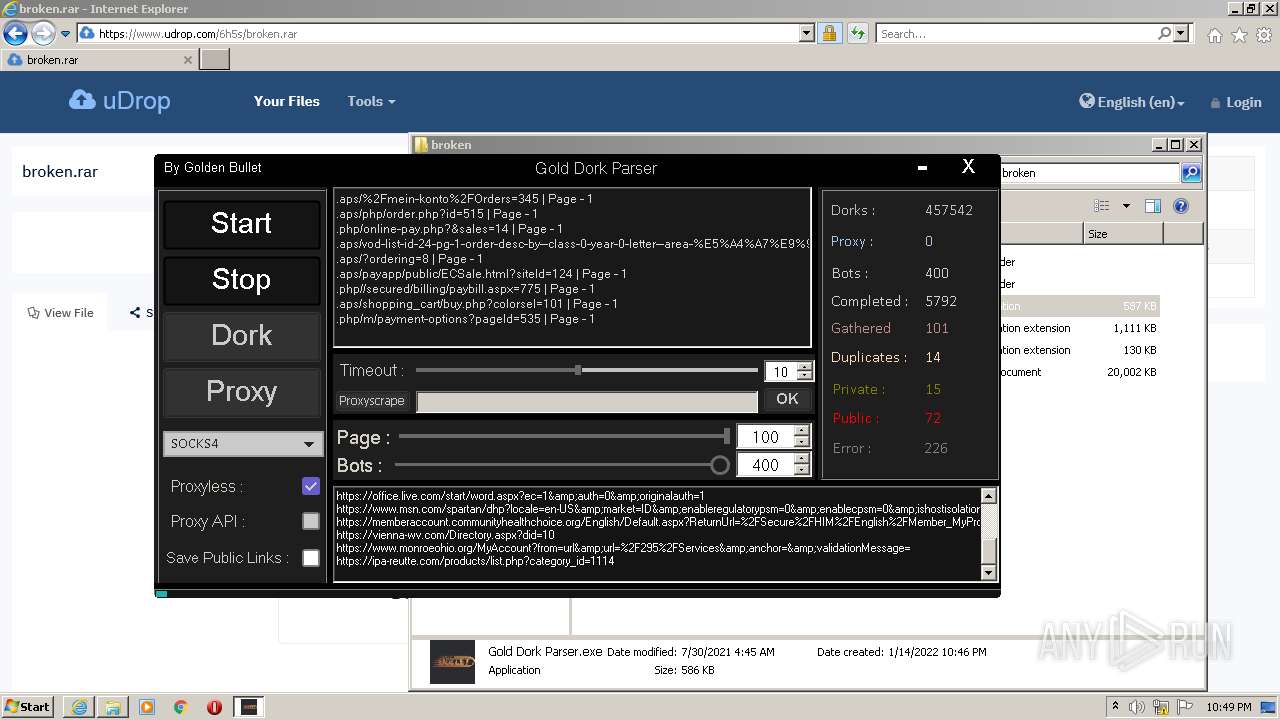
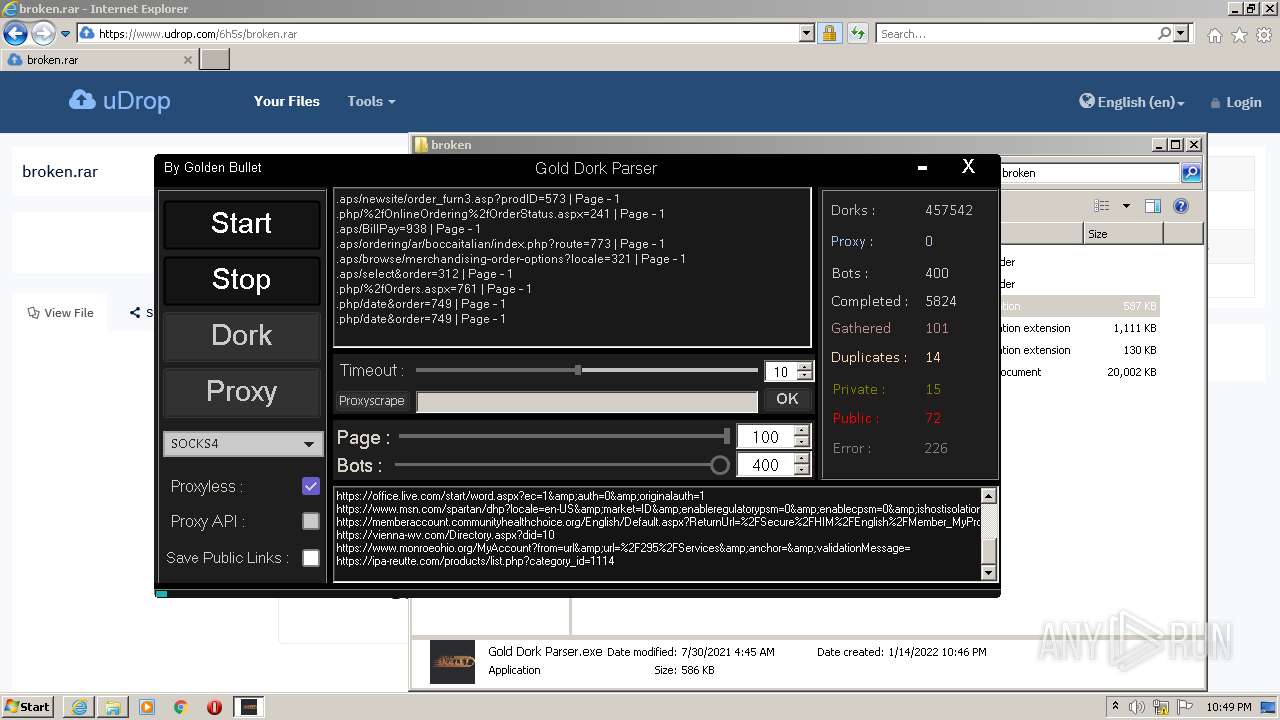
| URL: | https://www.udrop.com/6h5s/broken.rar |
| Full analysis: | https://app.any.run/tasks/13986140-e7da-4ce4-a2d9-9189df8f36f9 |
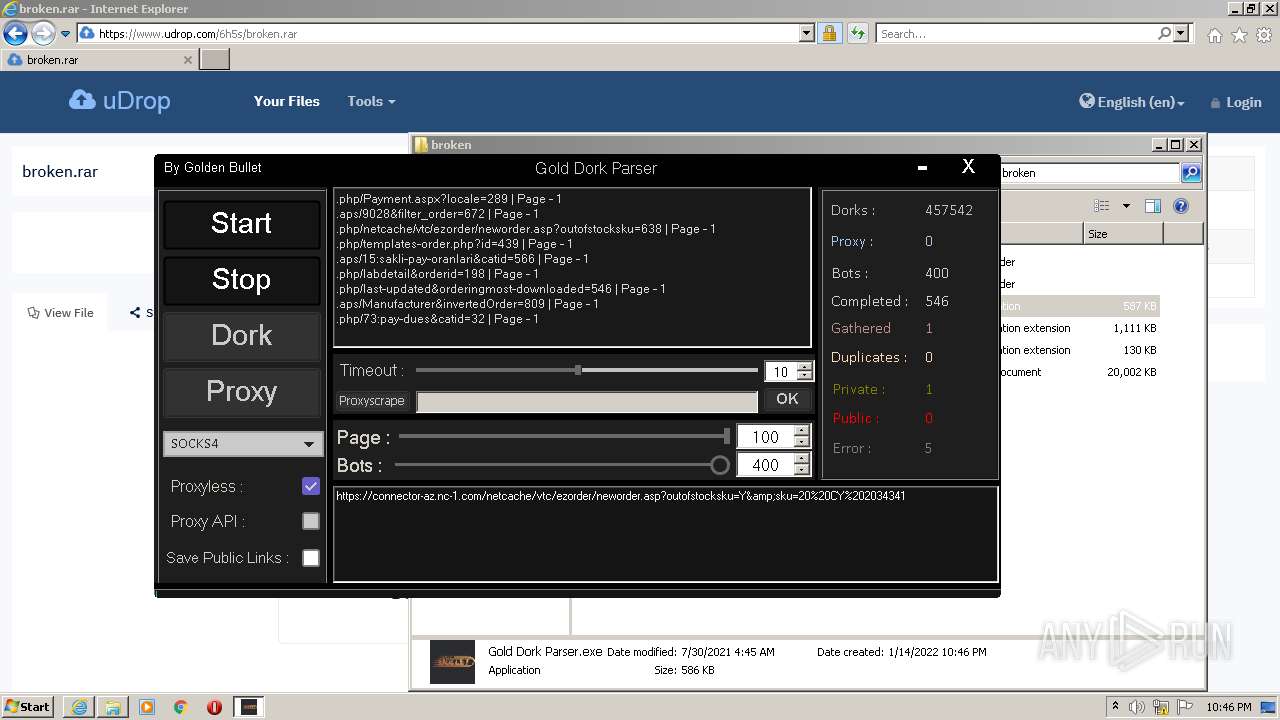
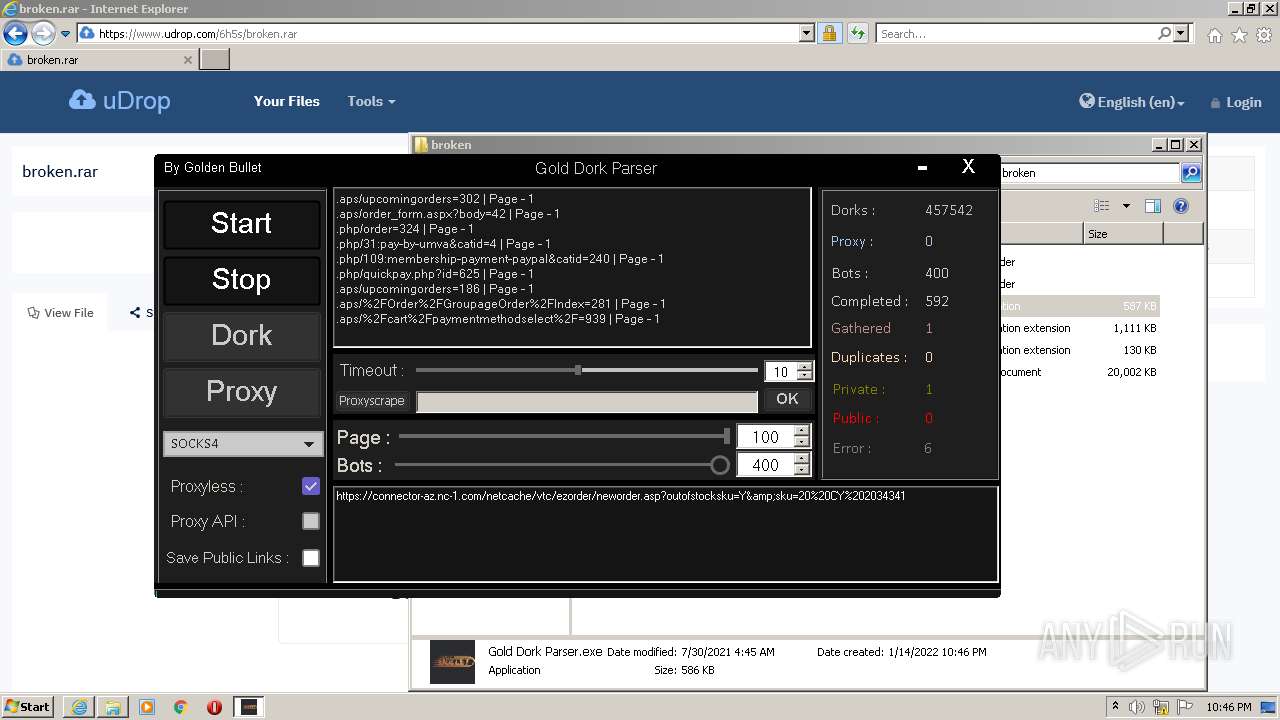
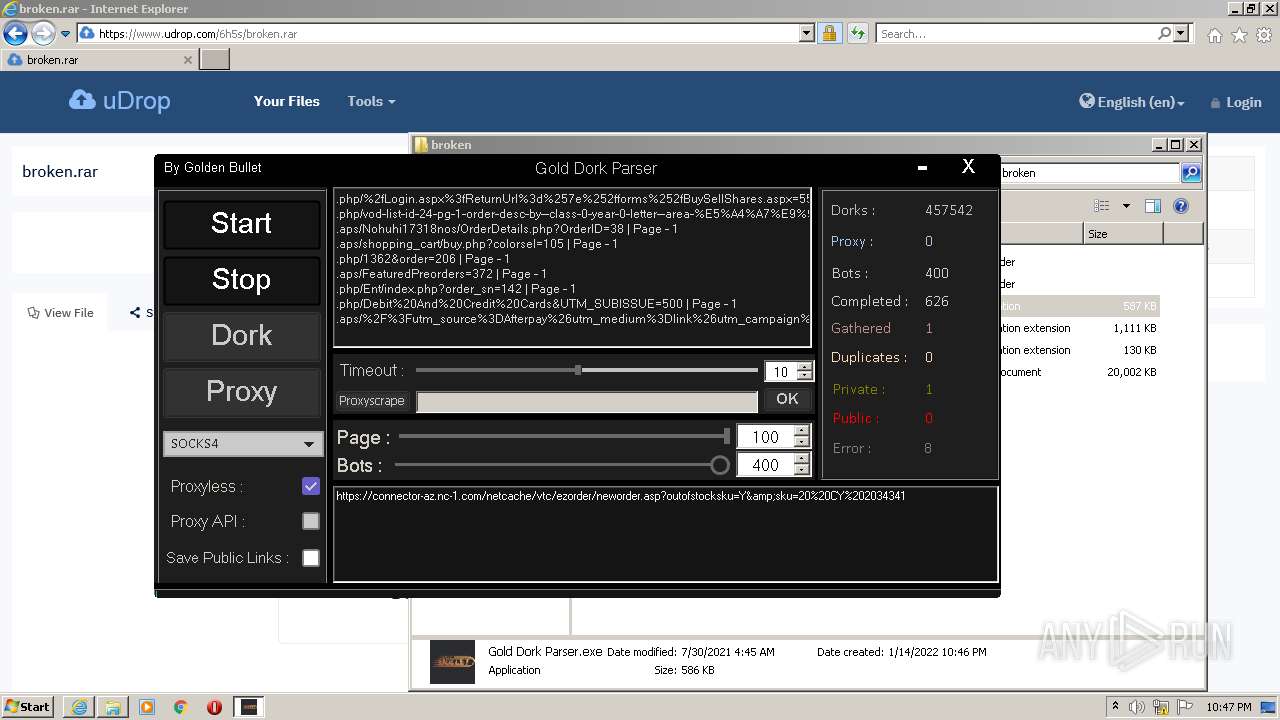
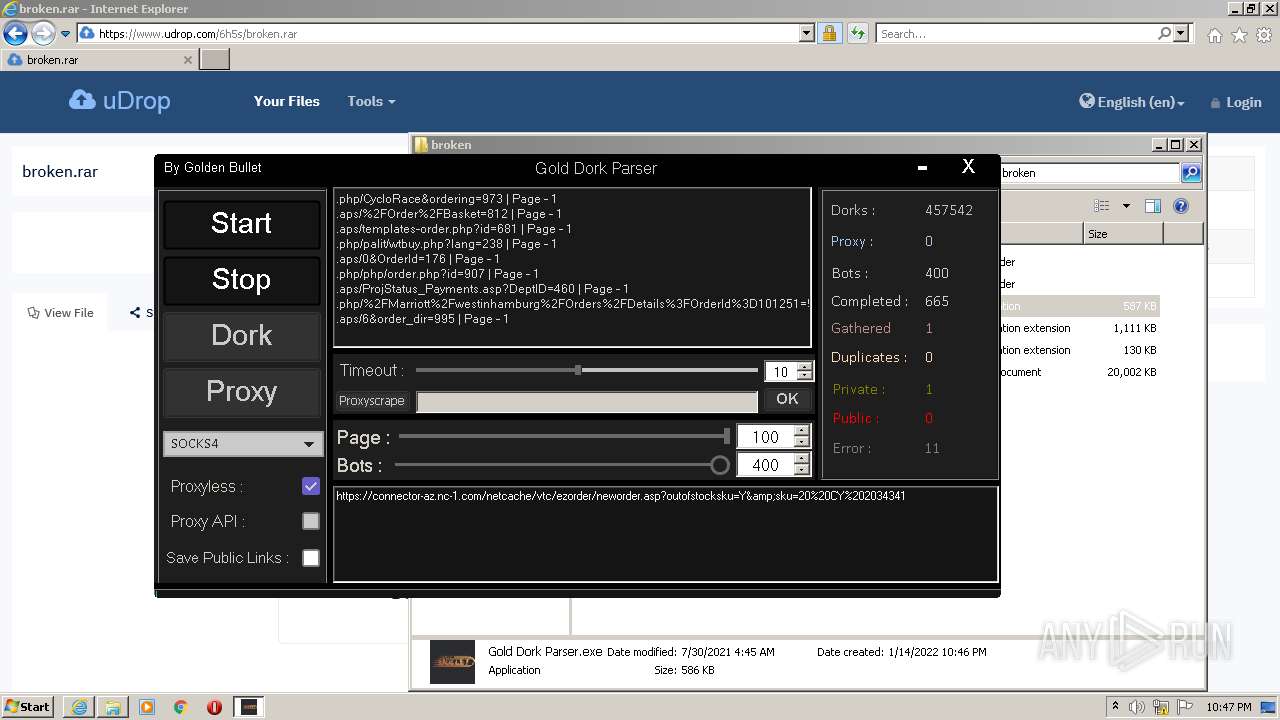
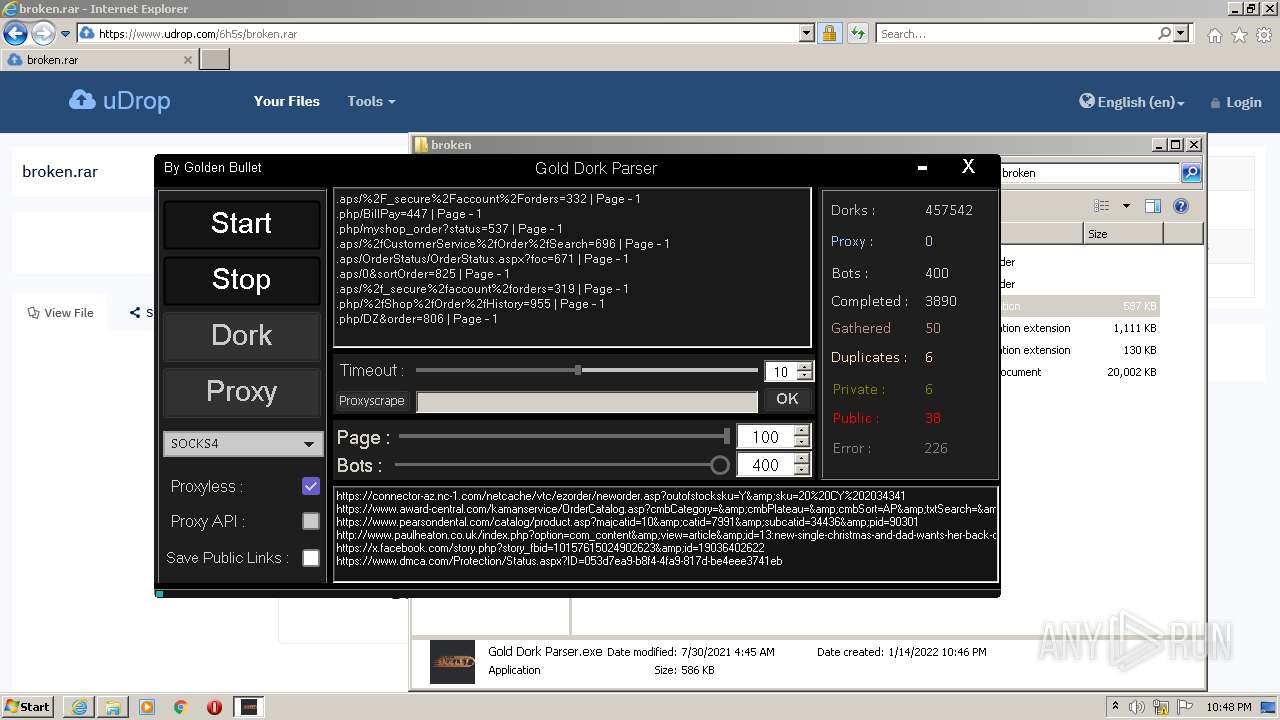
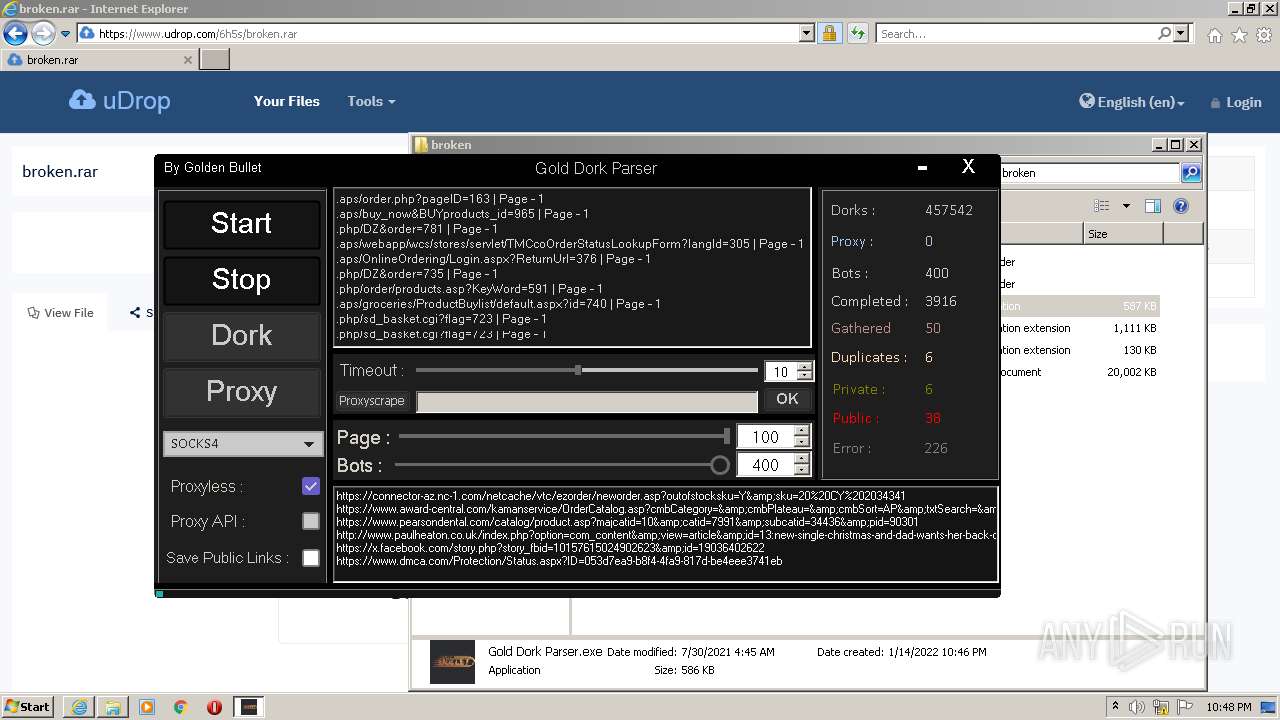
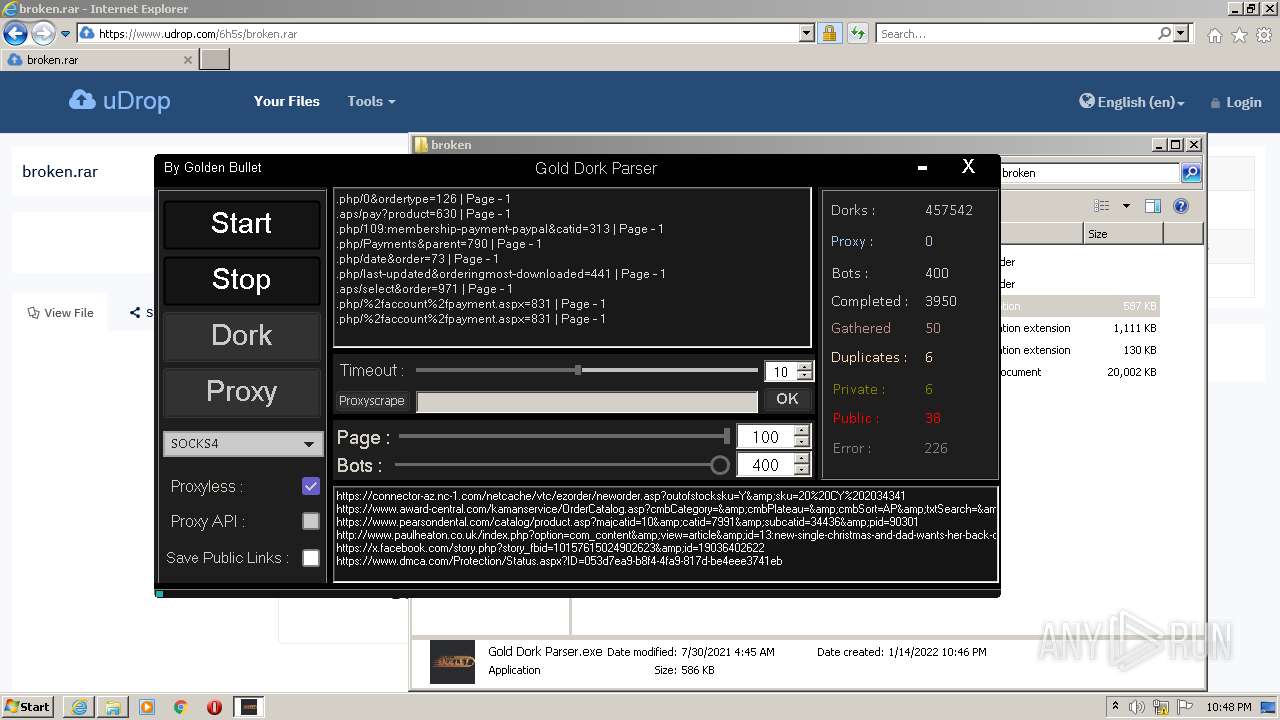
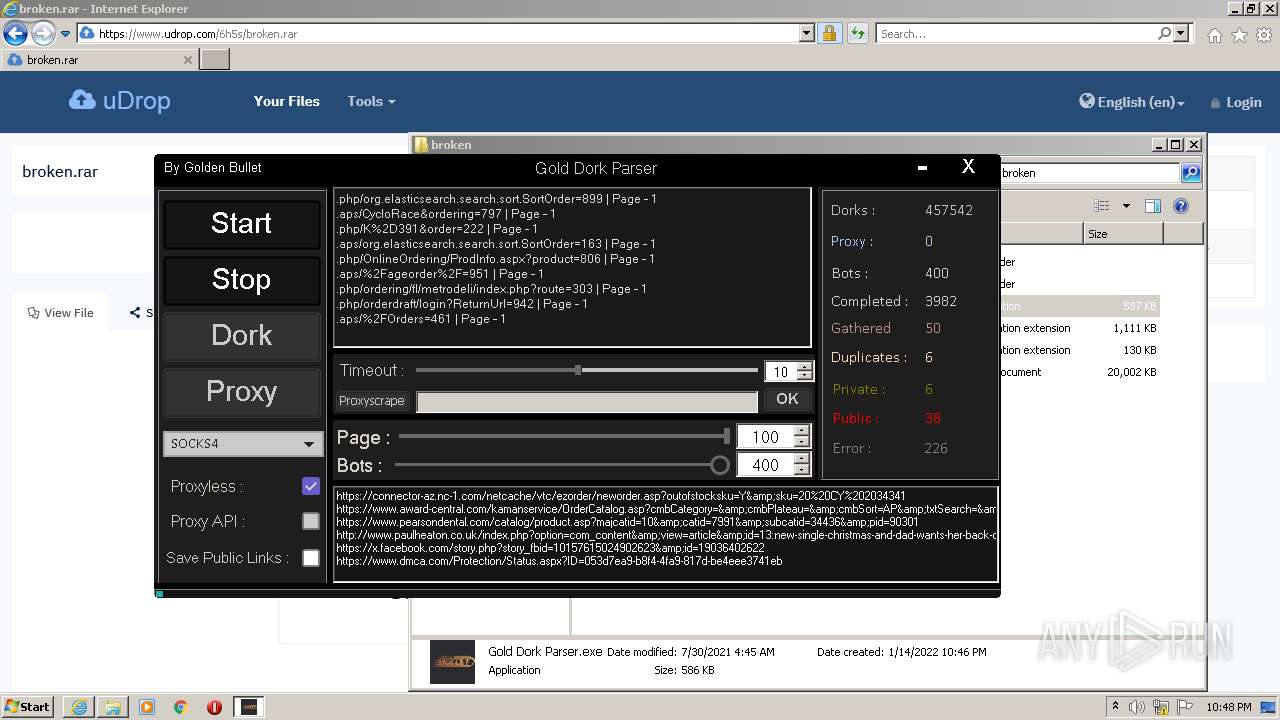
| Verdict: | Malicious activity |
| Analysis date: | January 14, 2022, 22:44:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 09DF7BC55A422C5C4FF0E20BE0CF08AE |
| SHA1: | 21930A763C8DCDB6F20F9E46FB2653DD2B80DF3E |
| SHA256: | 170FD4943C30B0ACADE916287D79B60FDBF21E7929D3B7295220FCF4D4C8A6A7 |
| SSDEEP: | 3:N8DSLzGTKh9v/On:2OLzKKh9v/O |
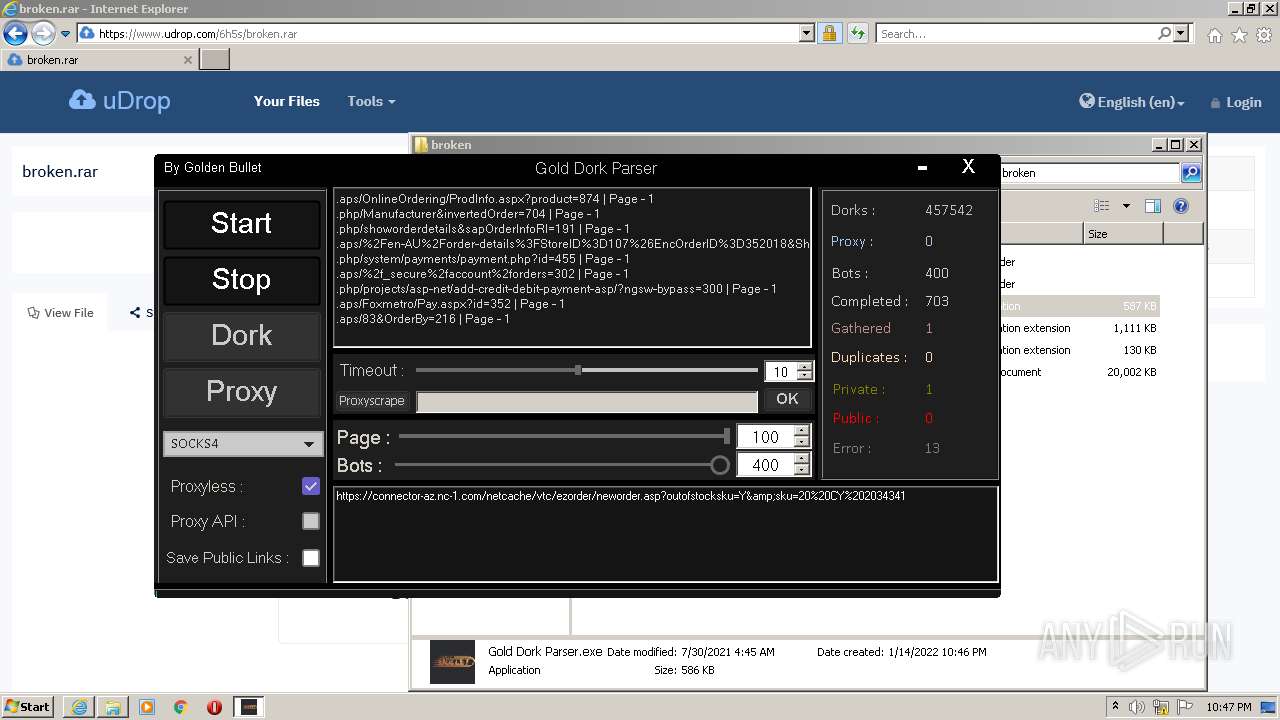
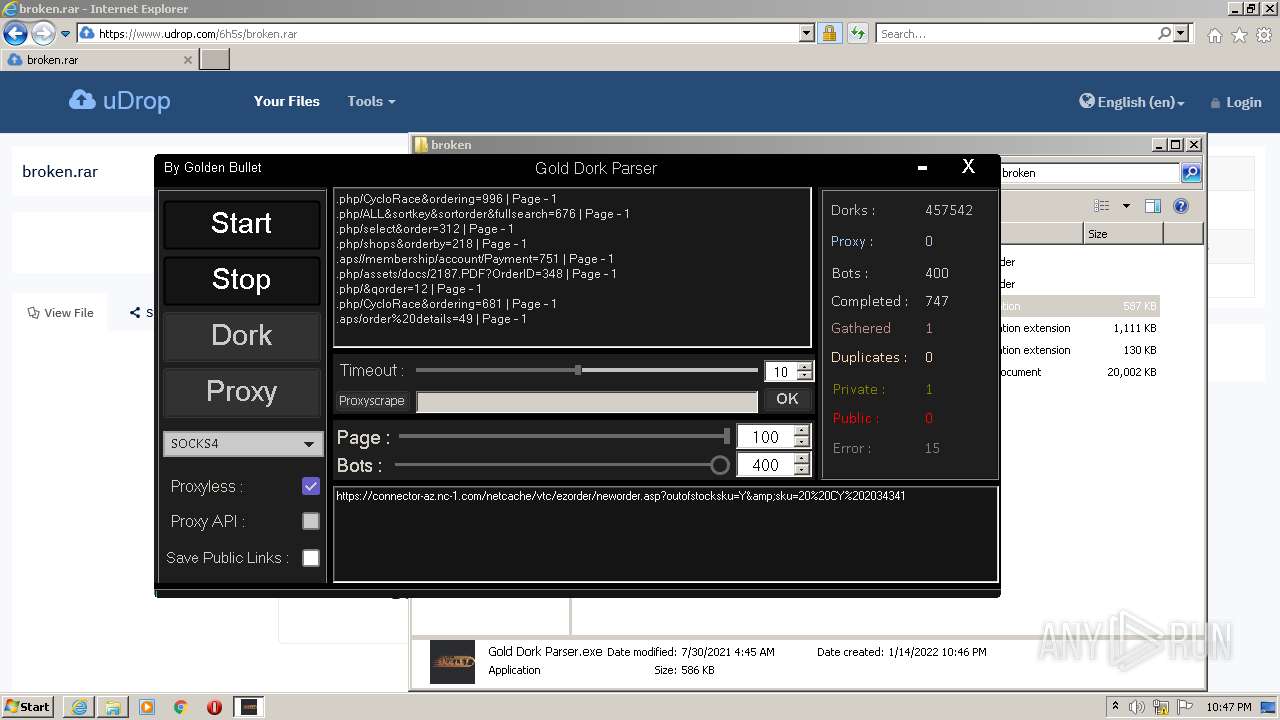
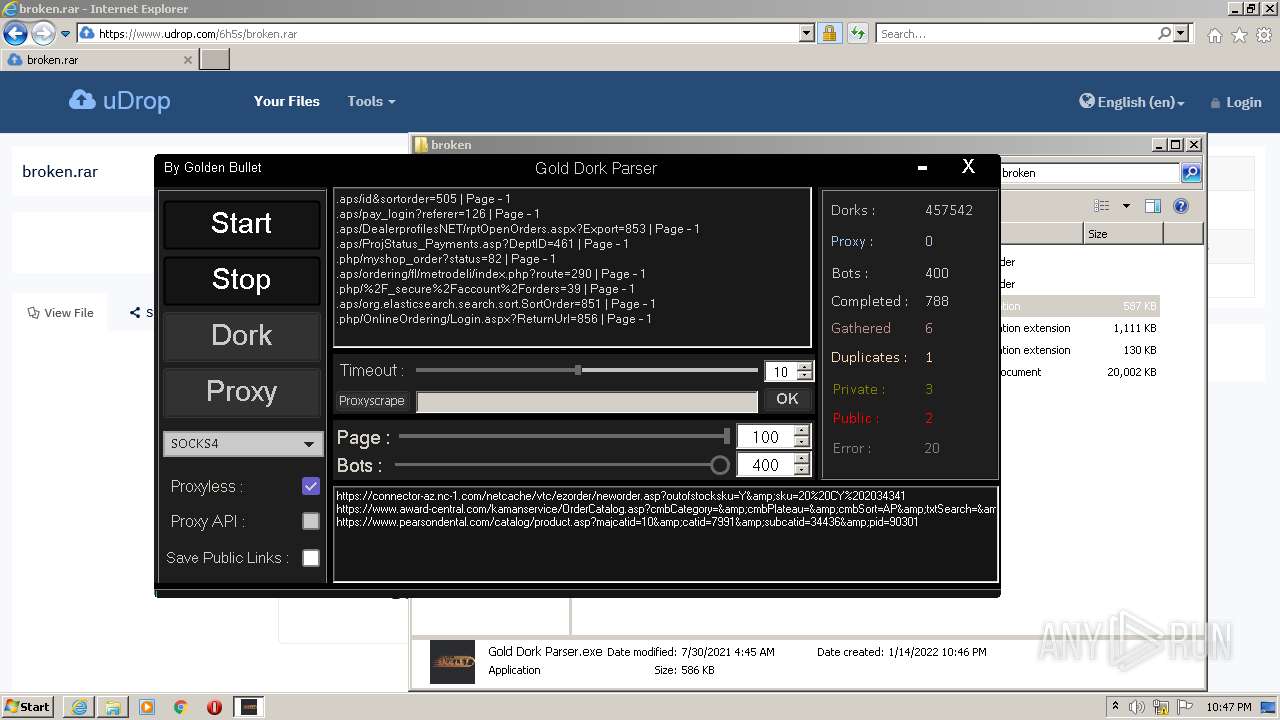
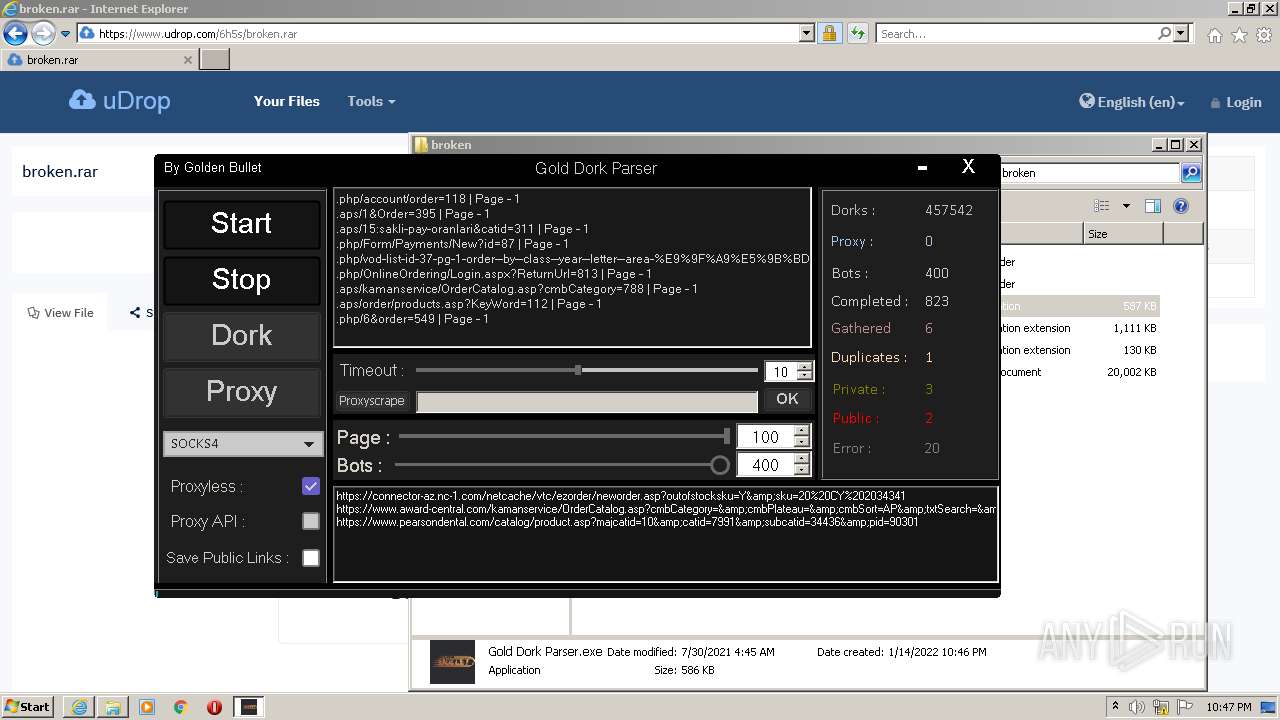
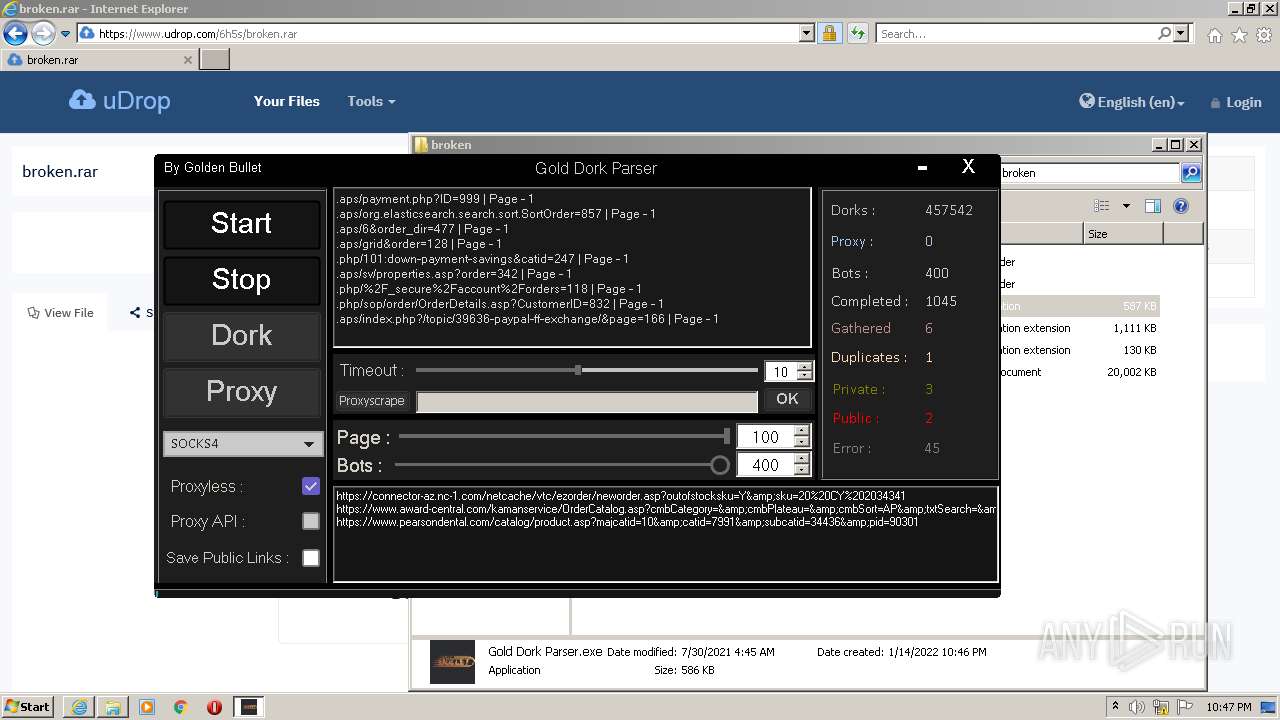
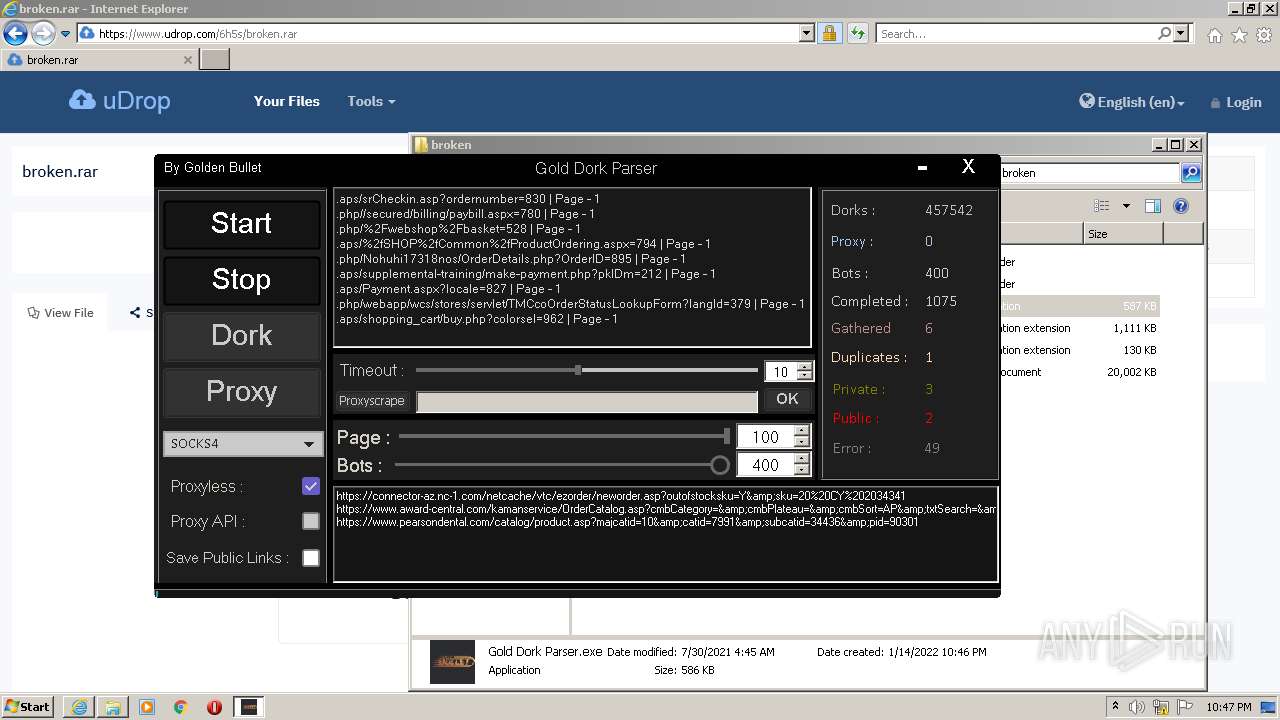
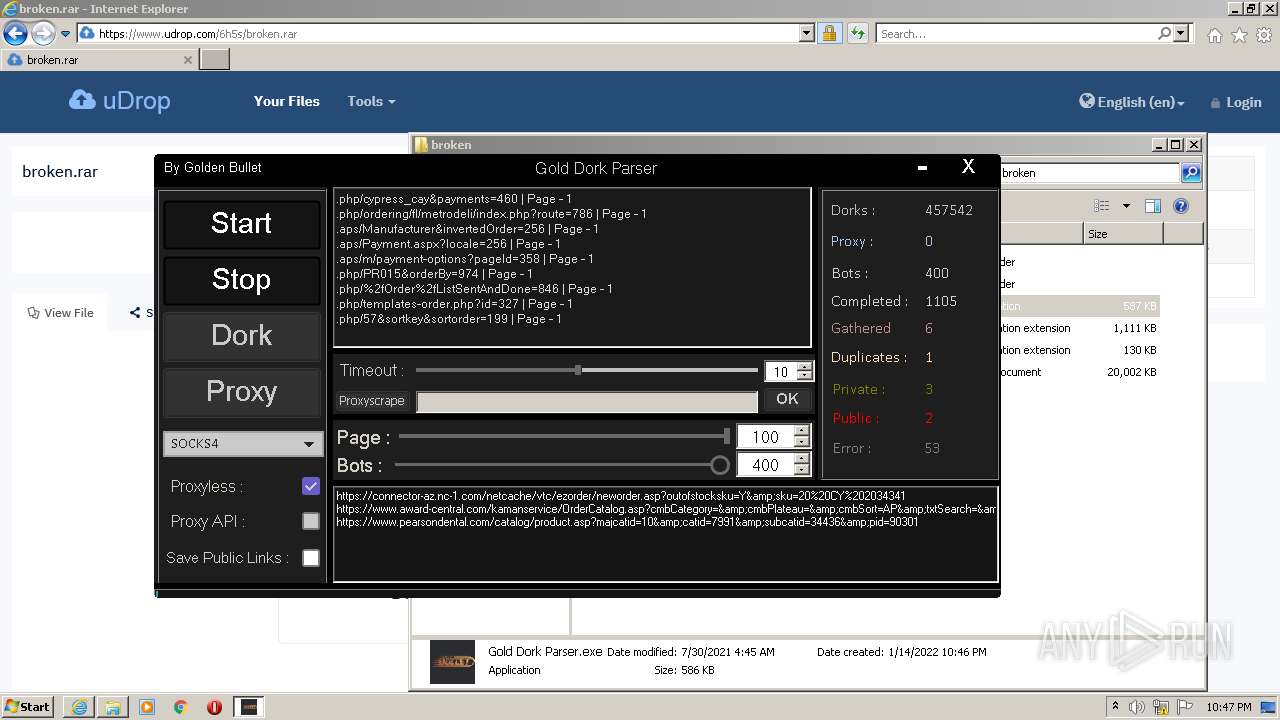
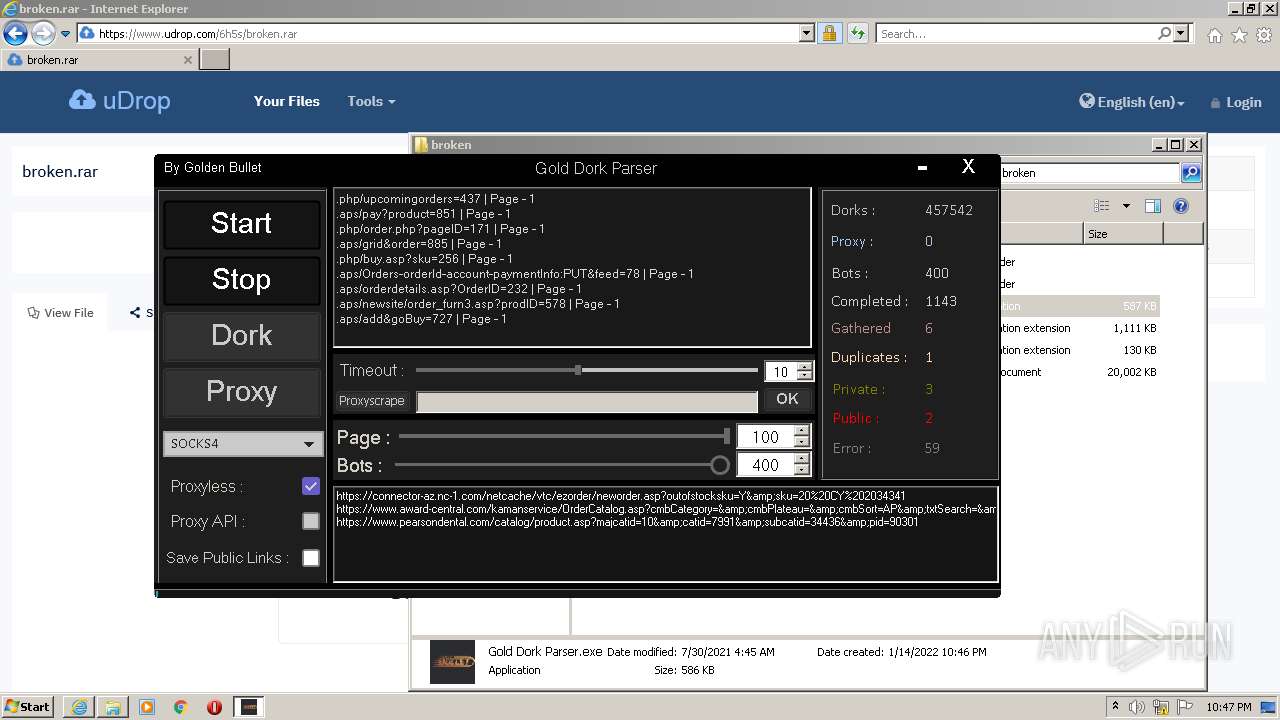
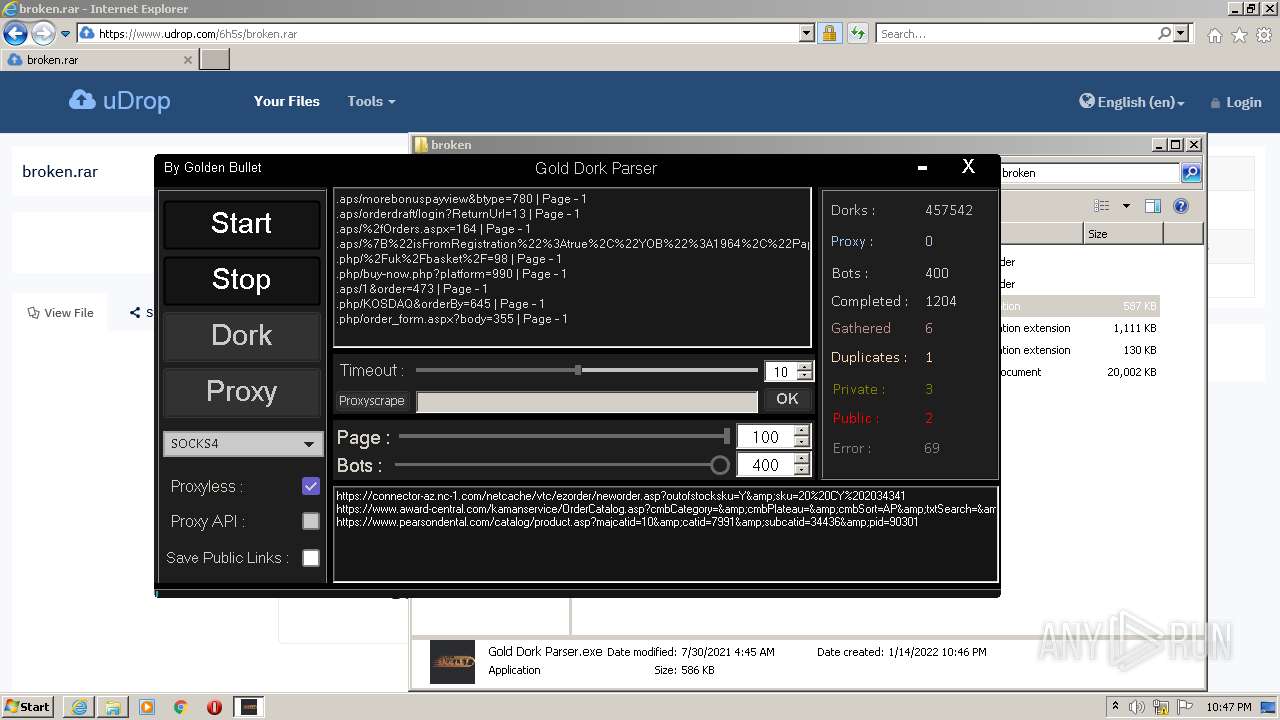
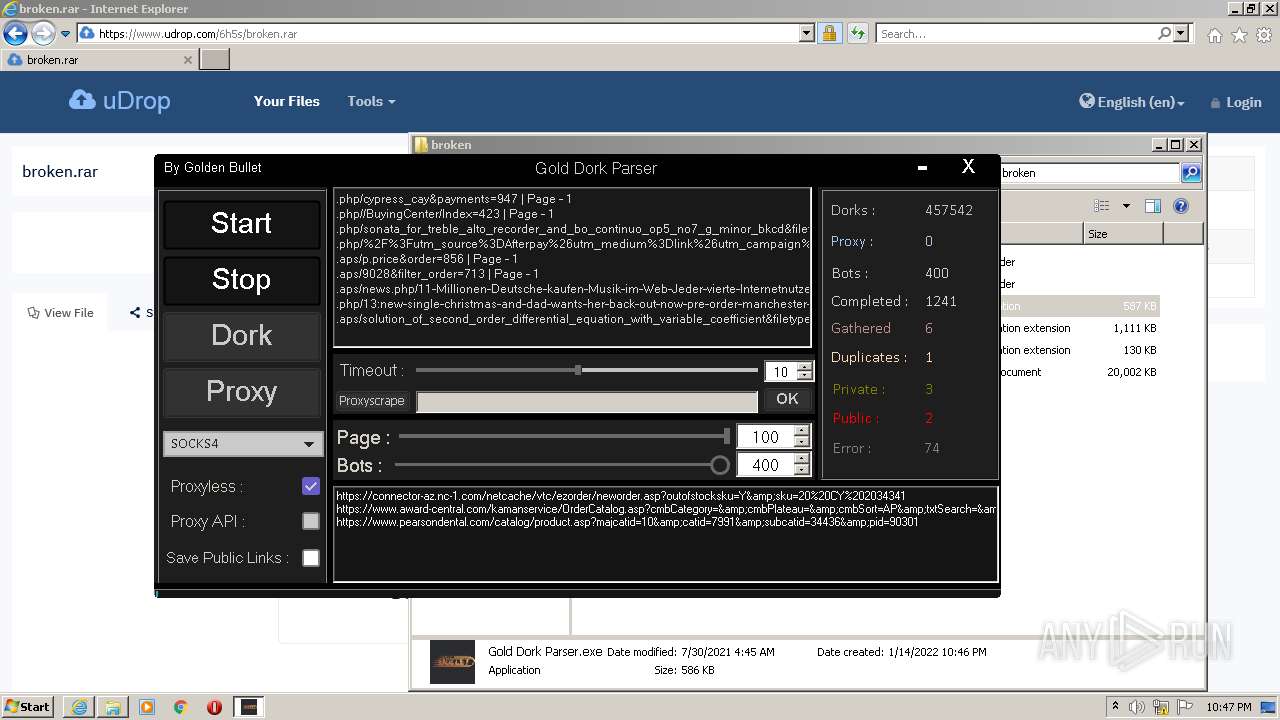
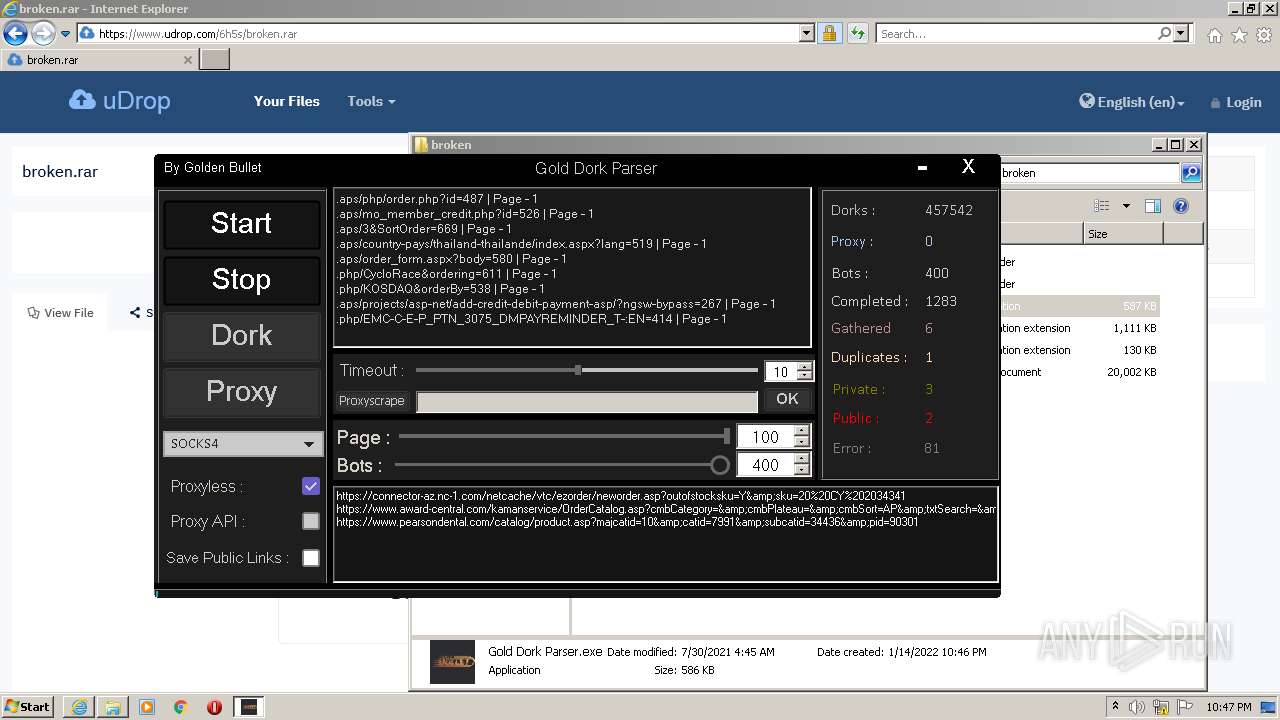
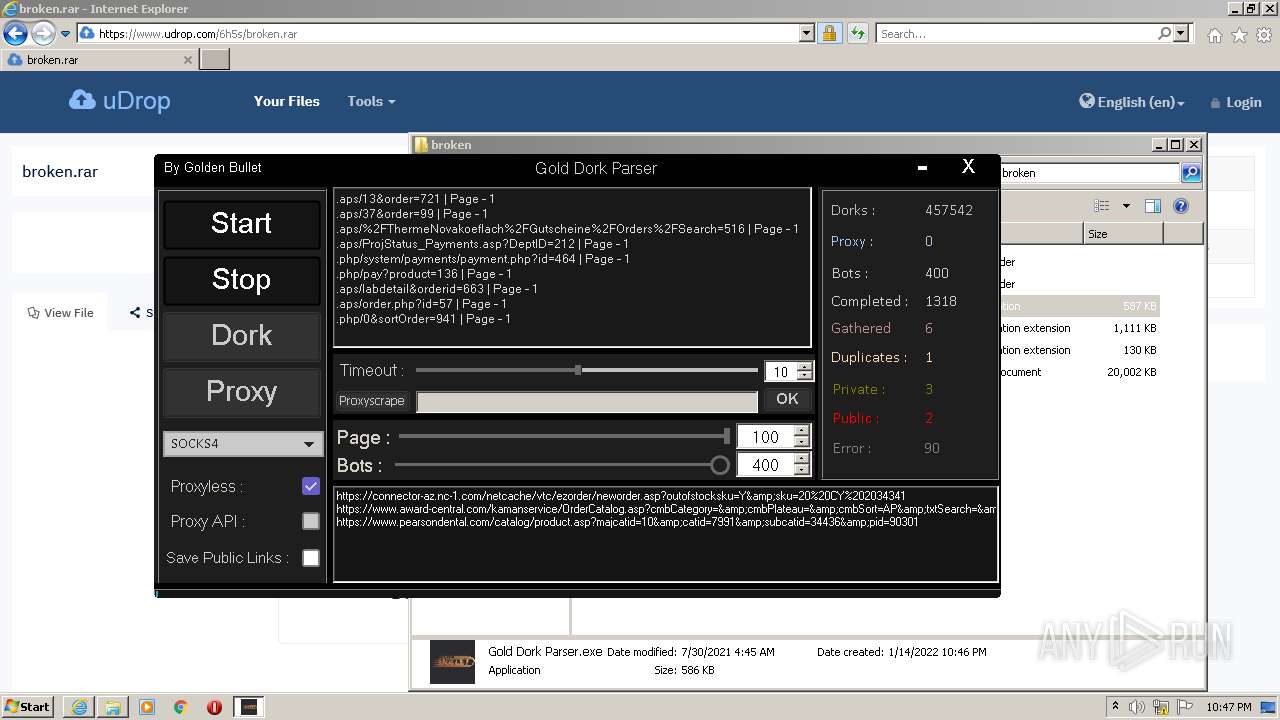
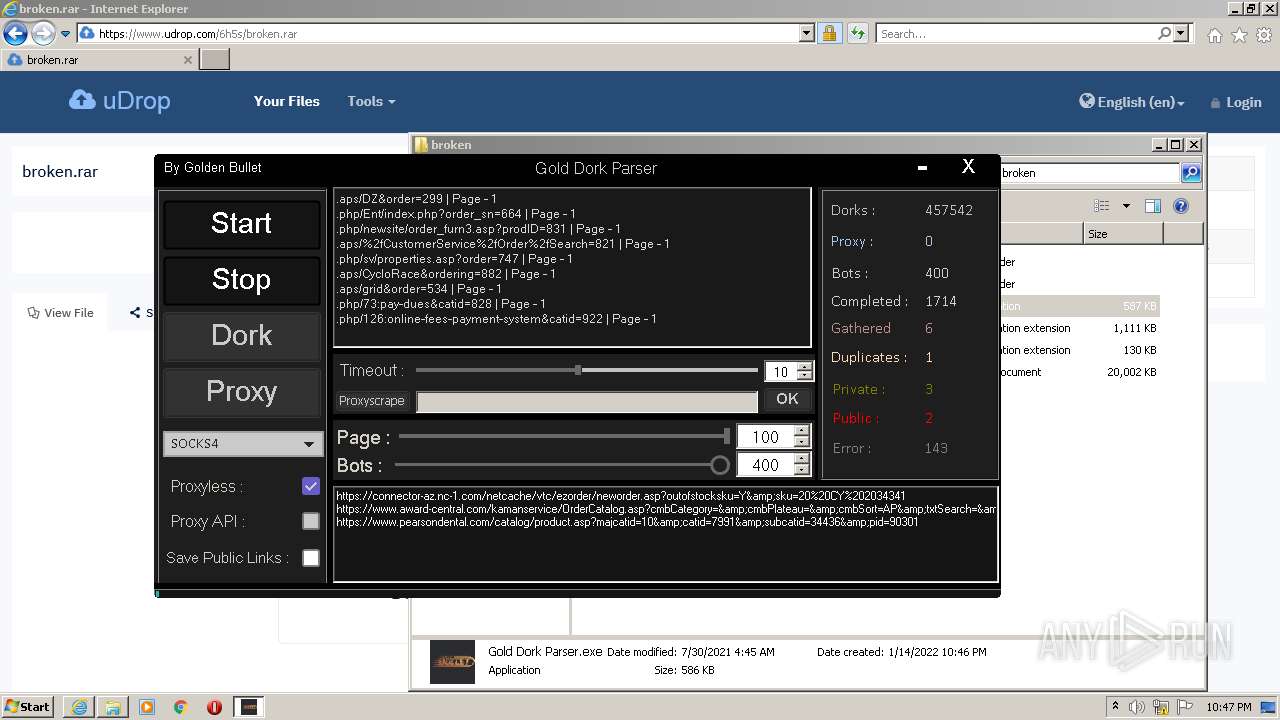
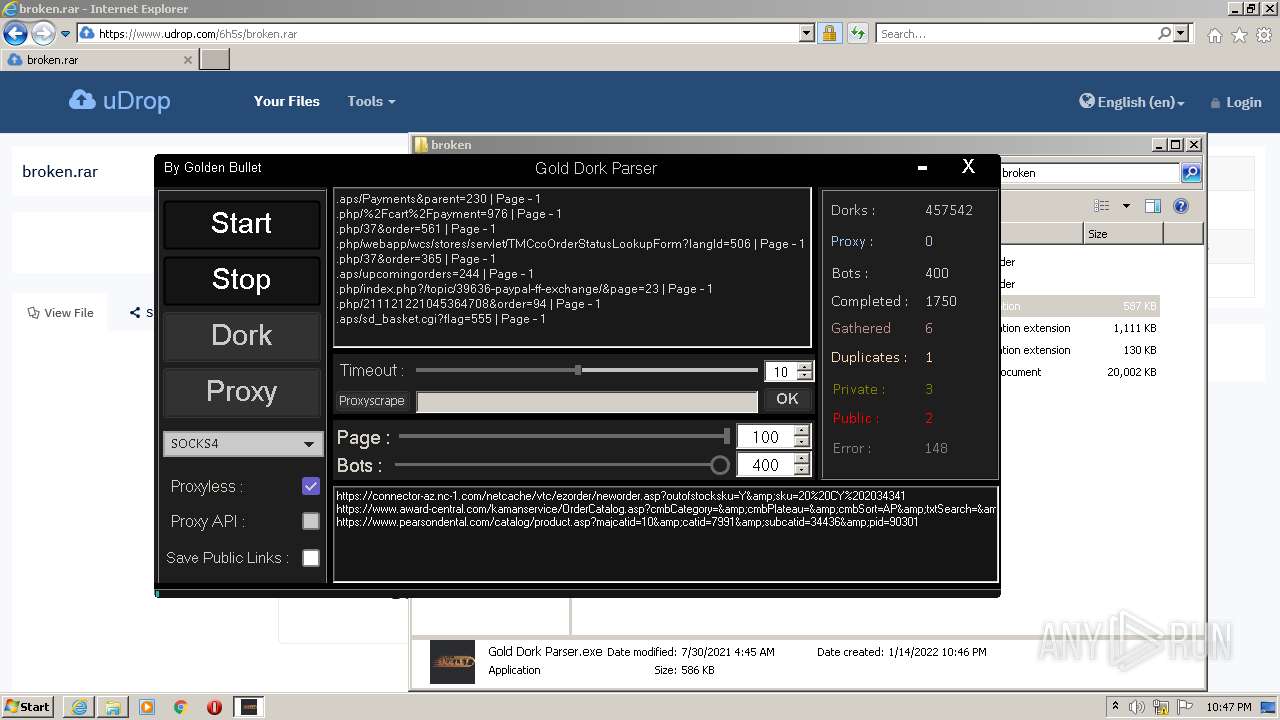
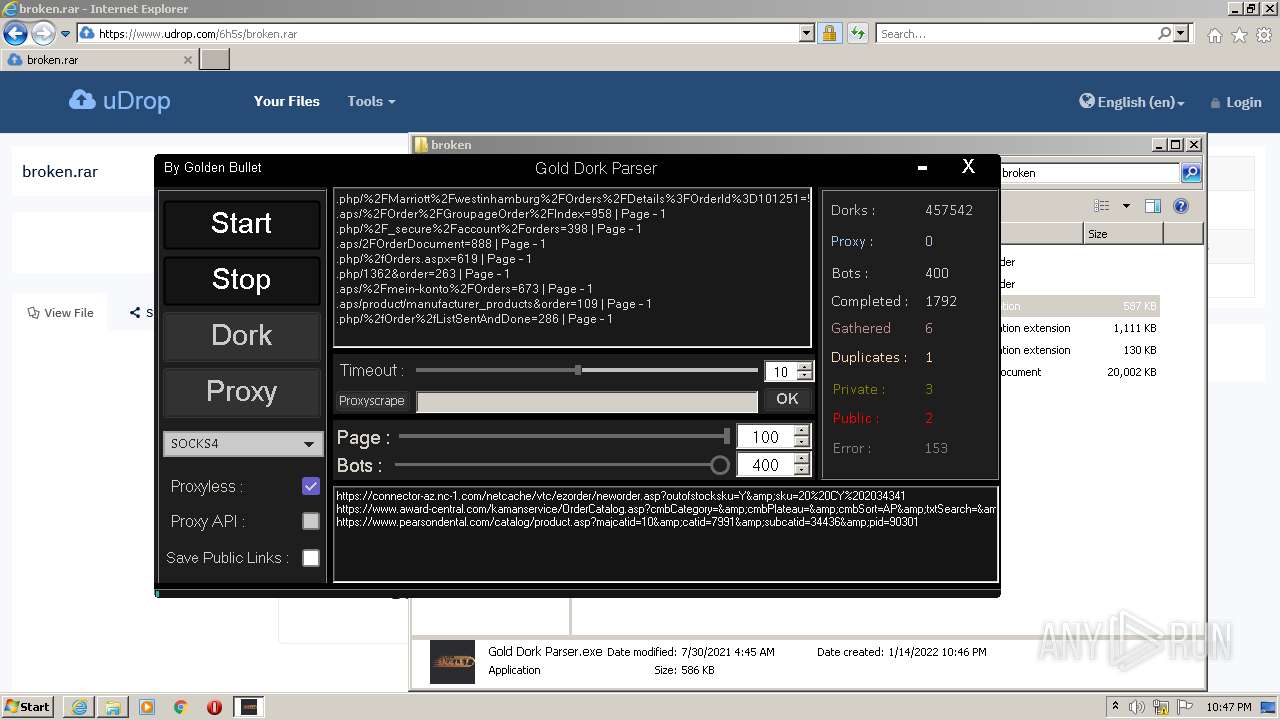
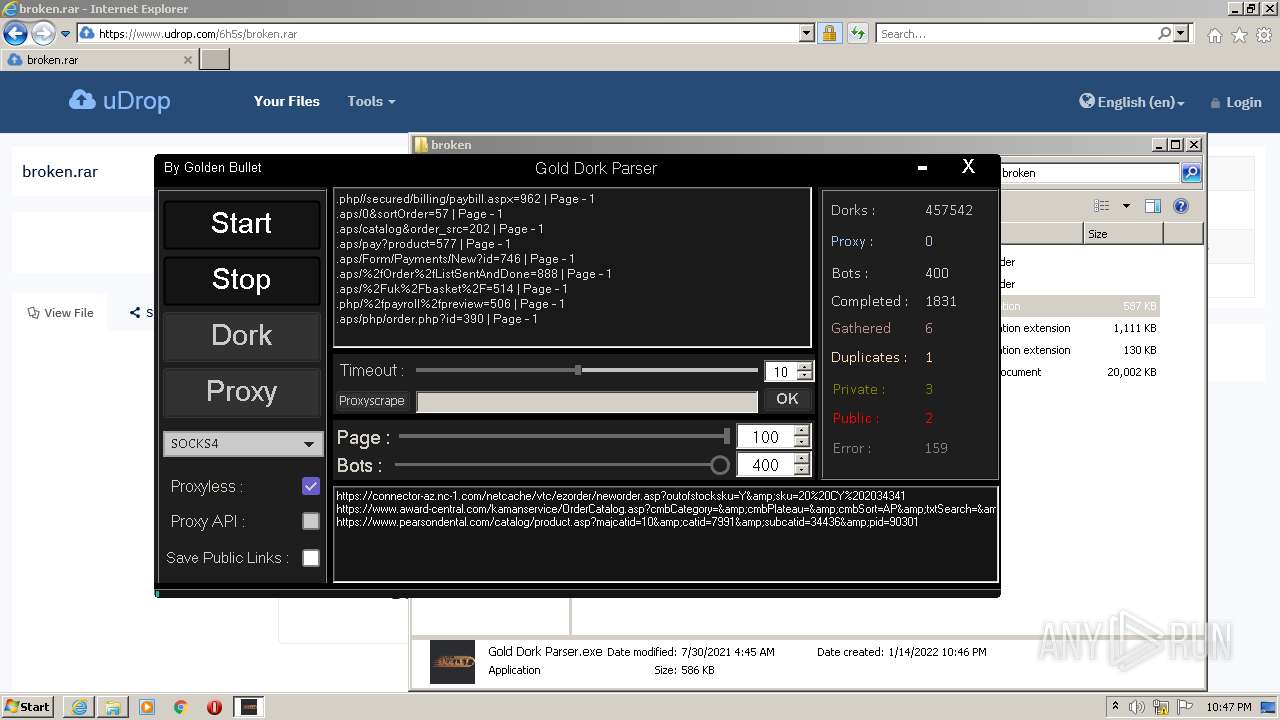
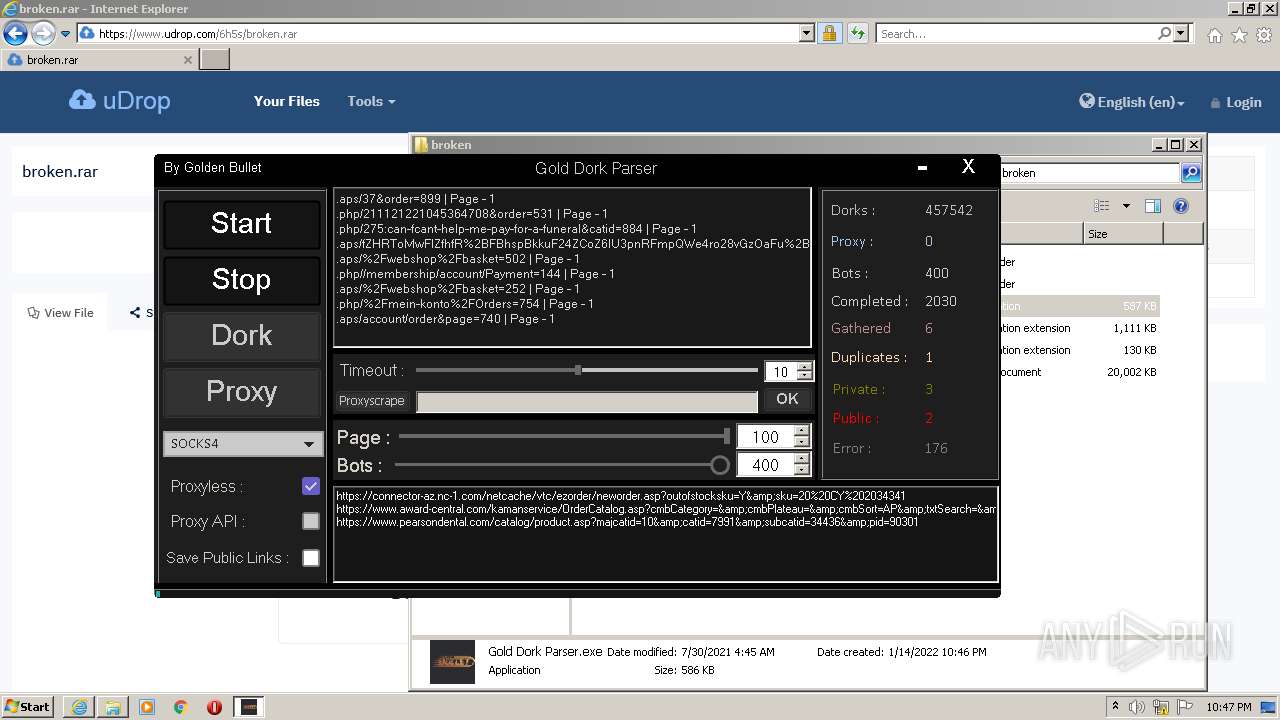
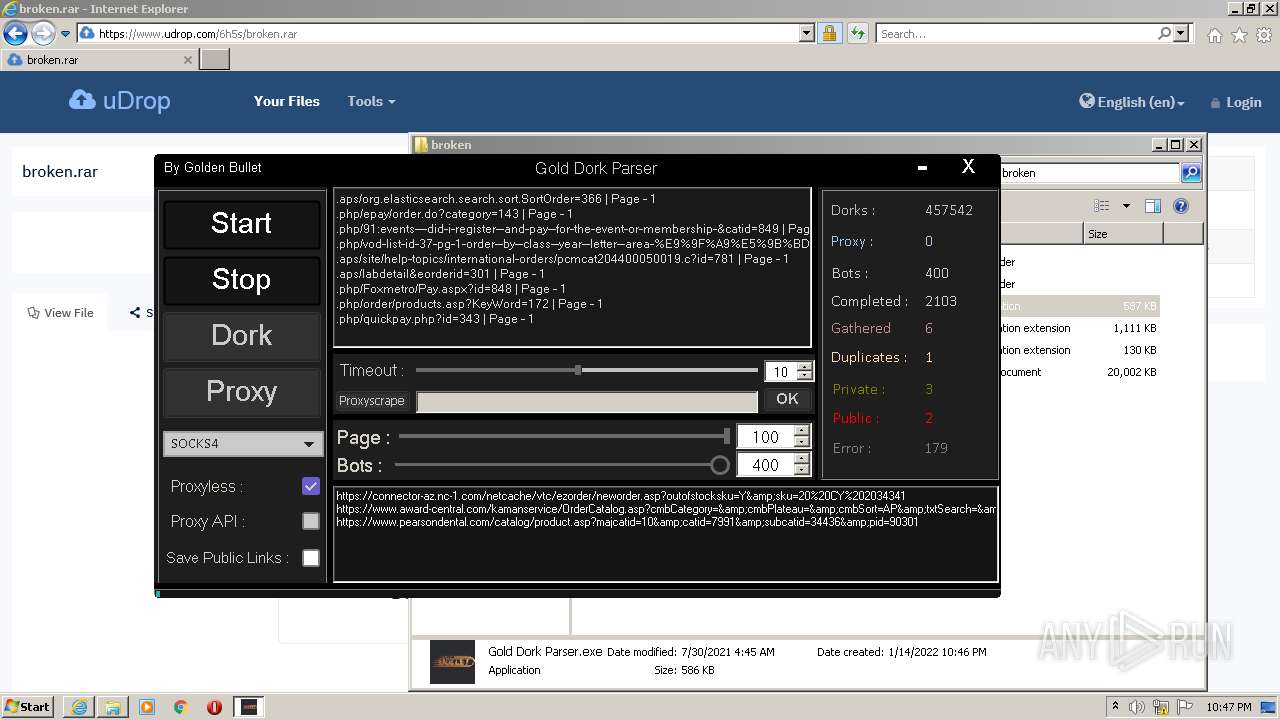
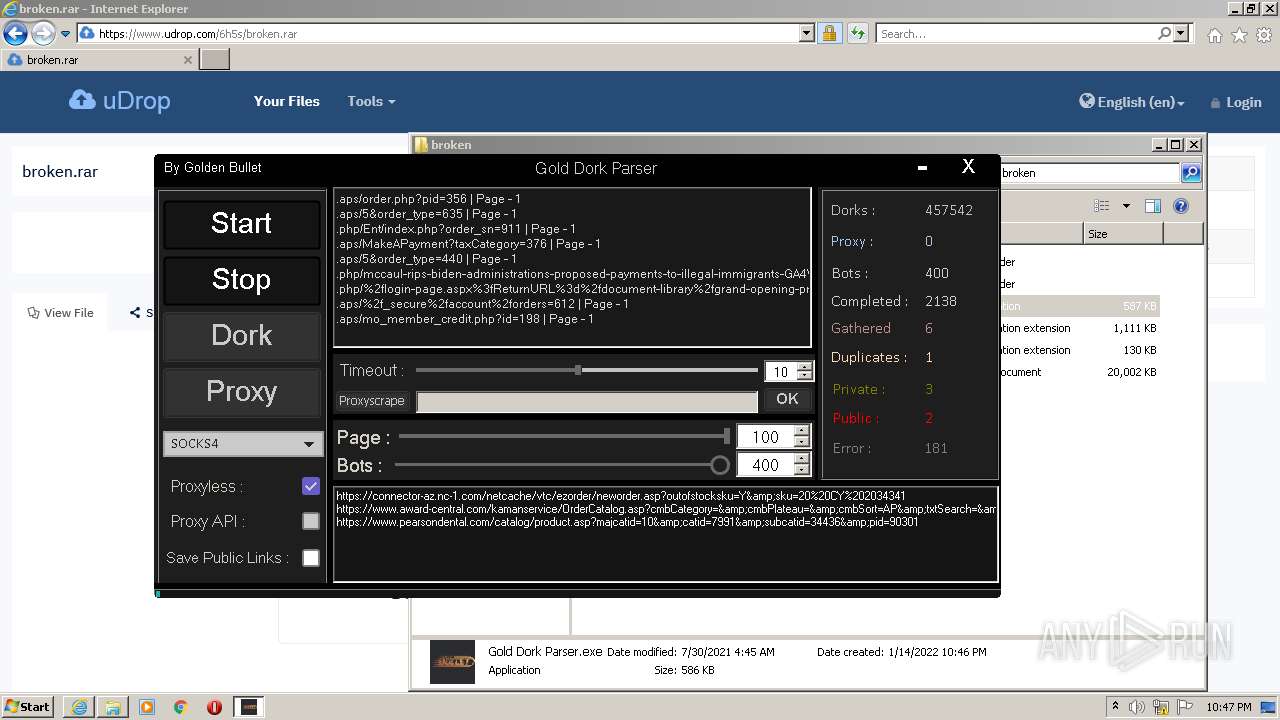
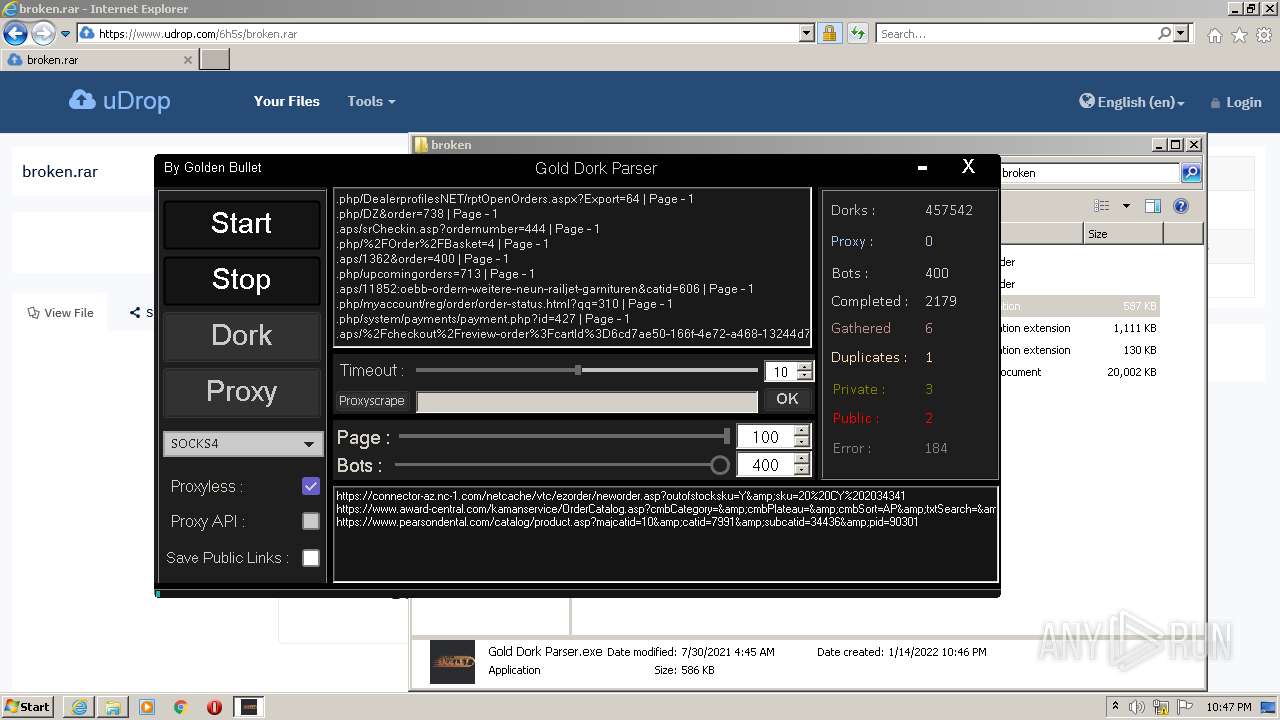
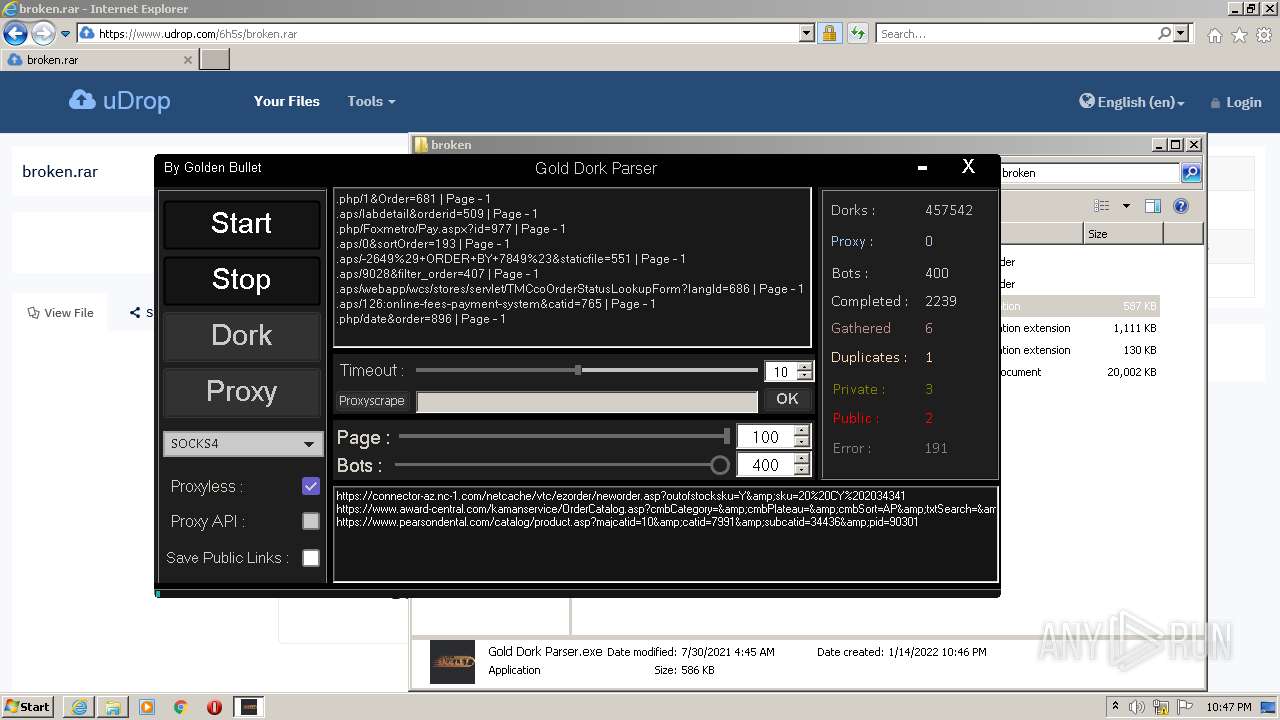
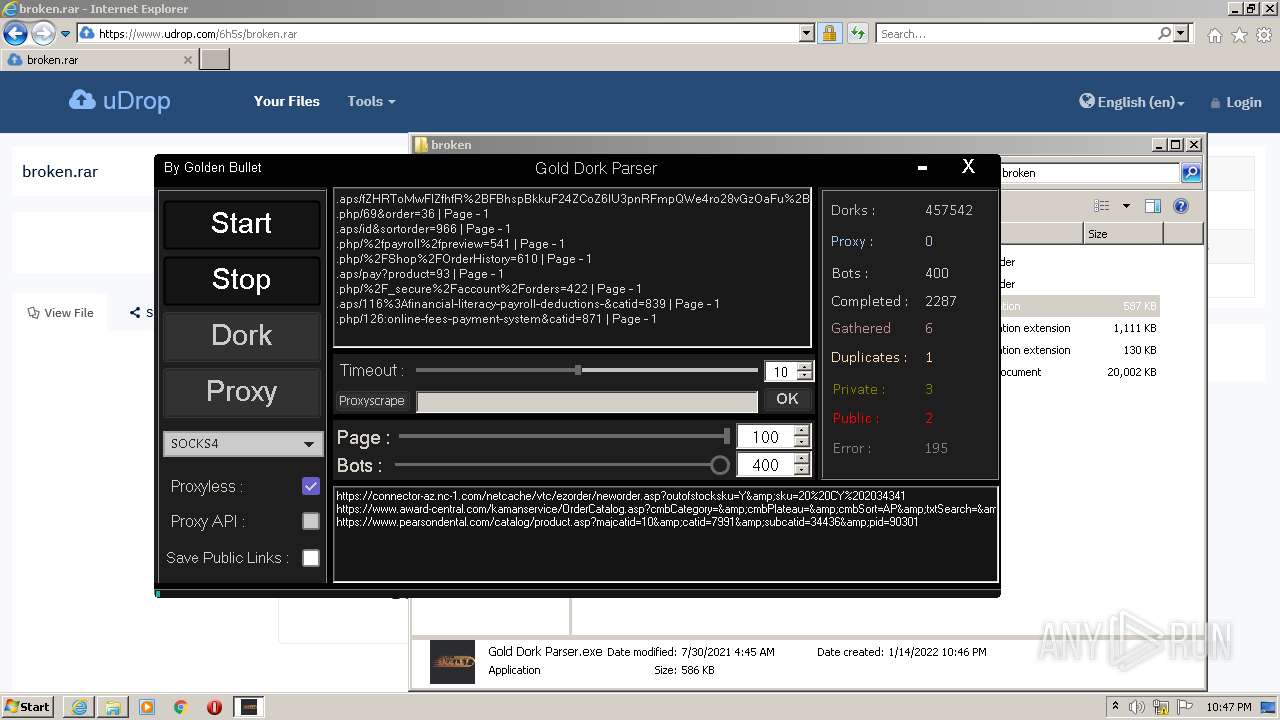
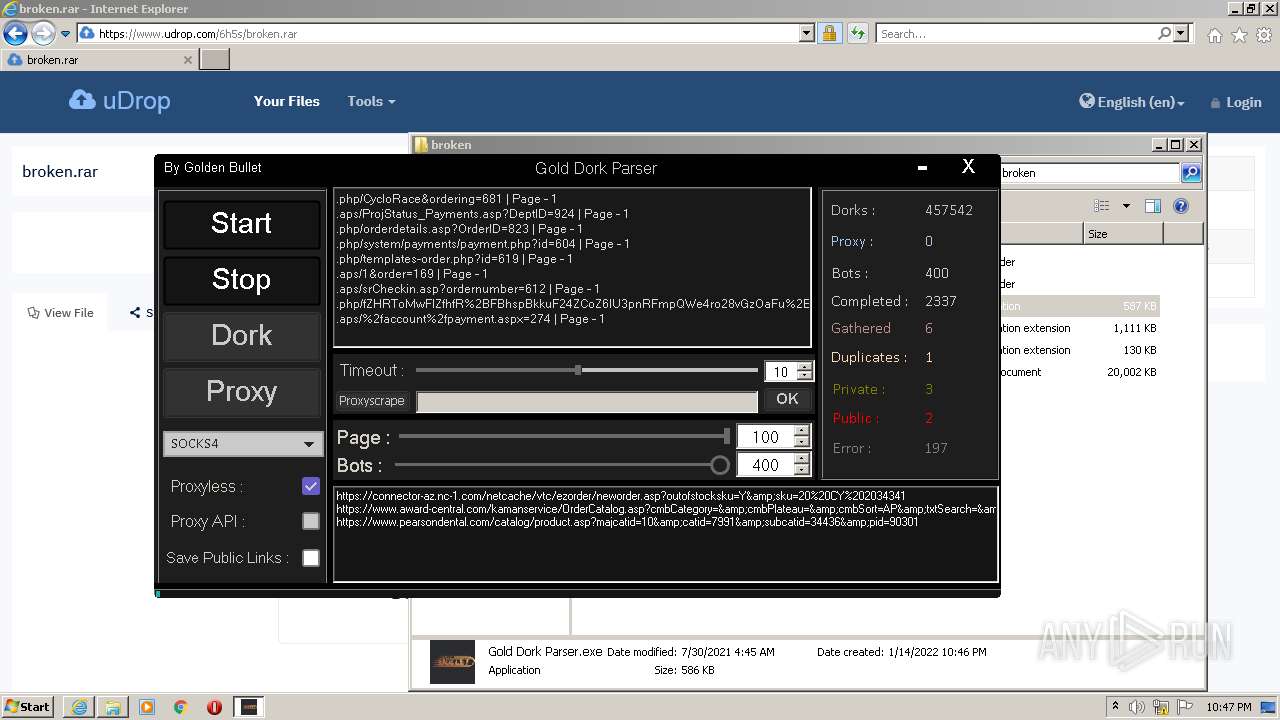
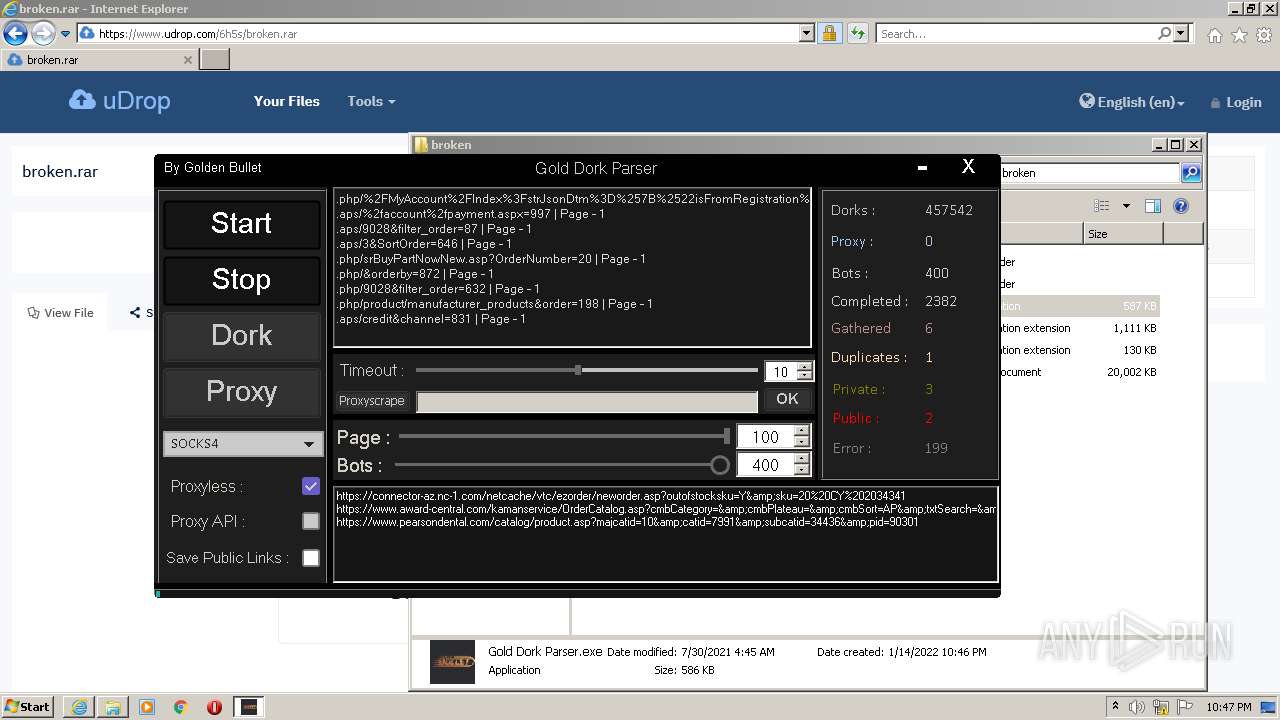
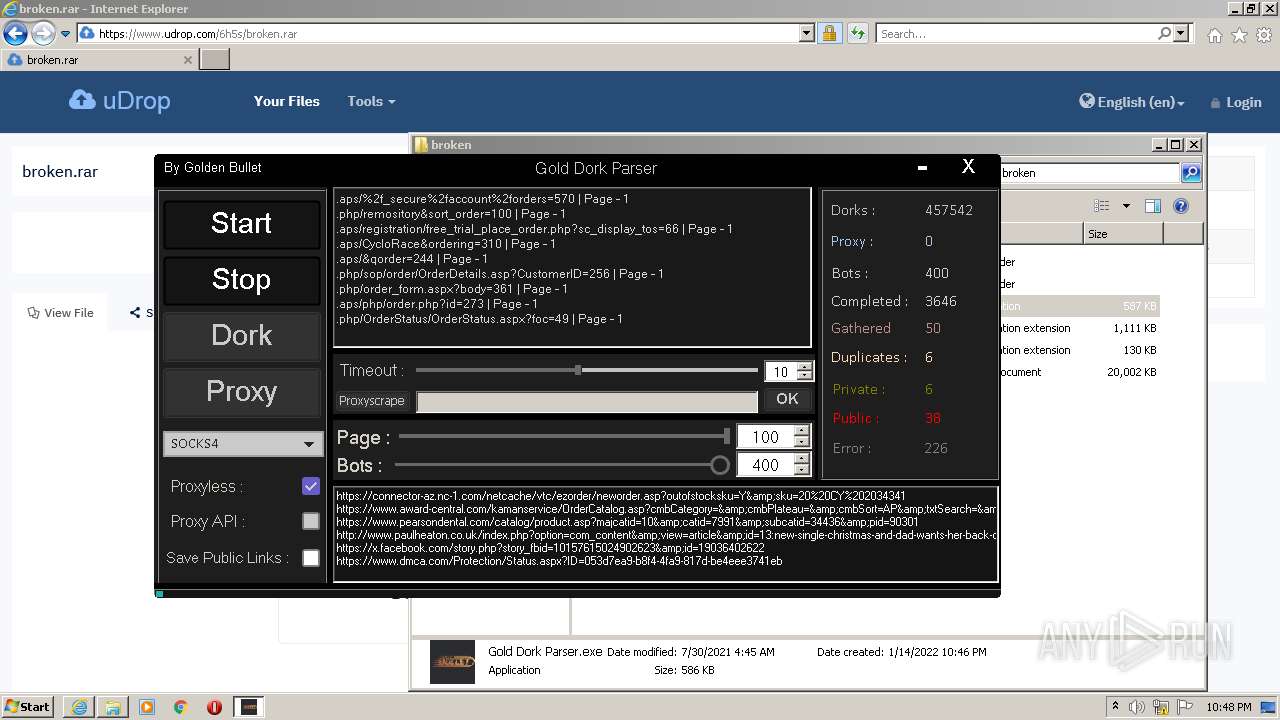
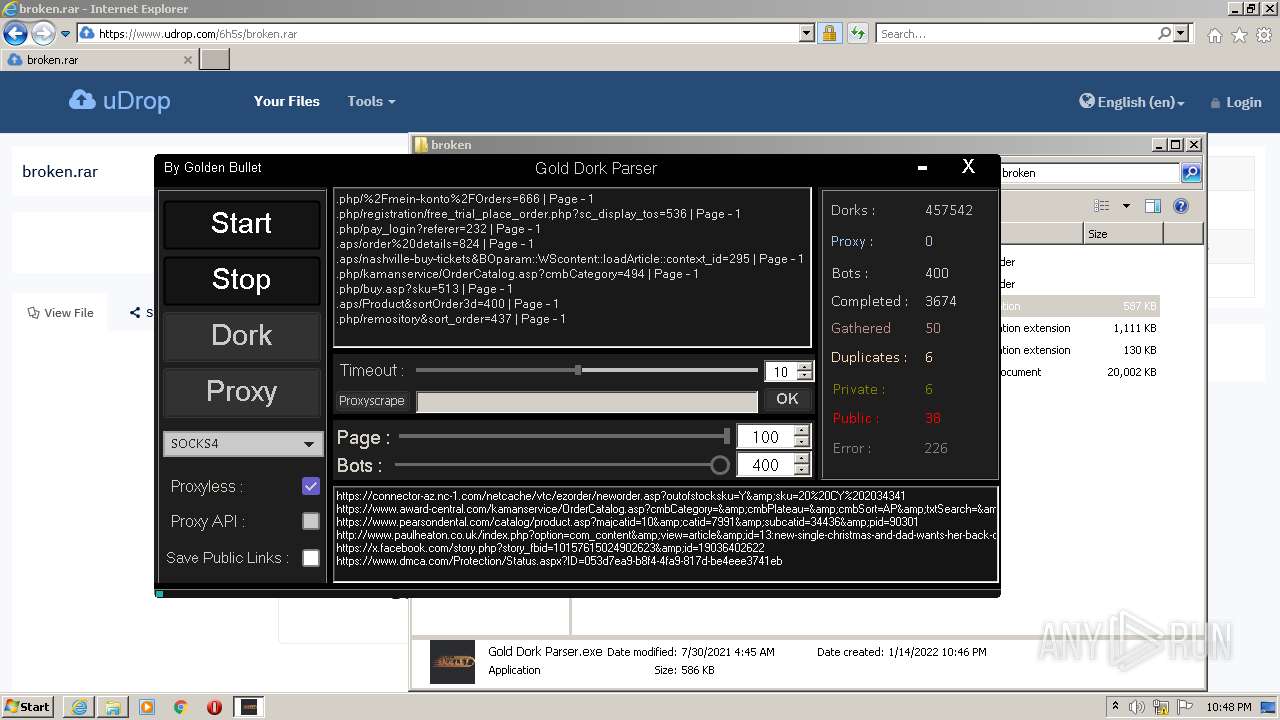
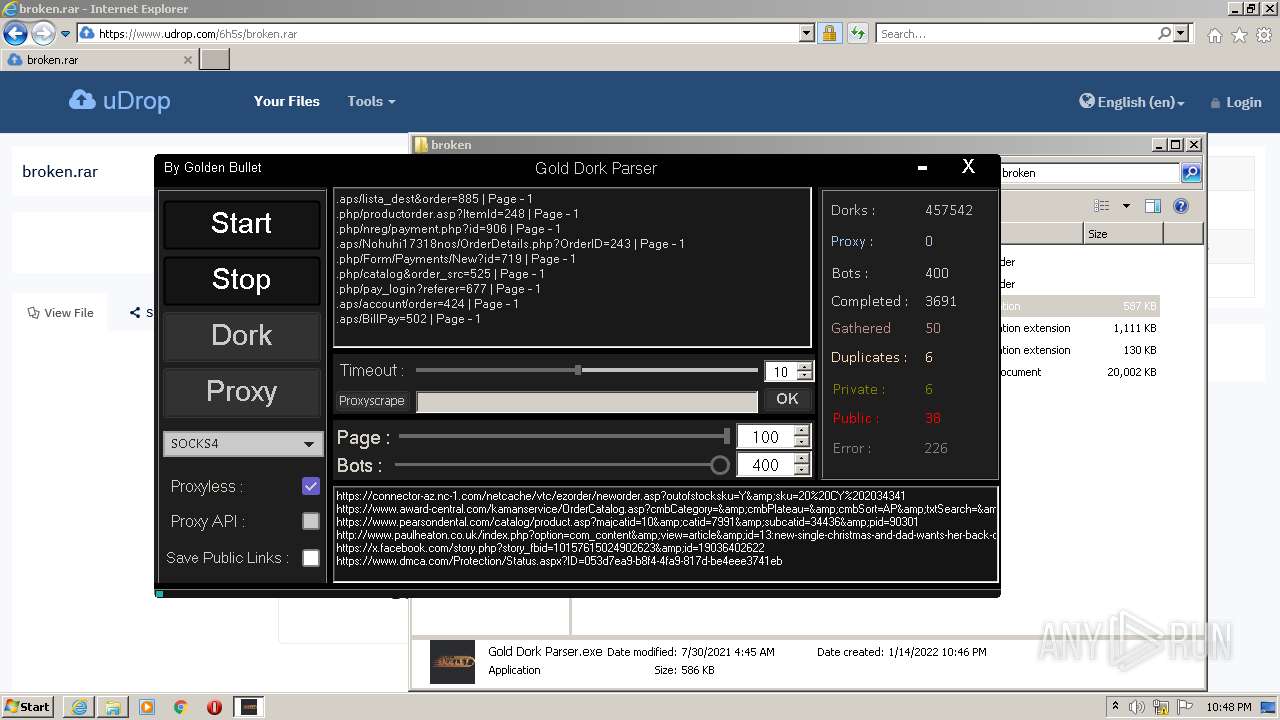
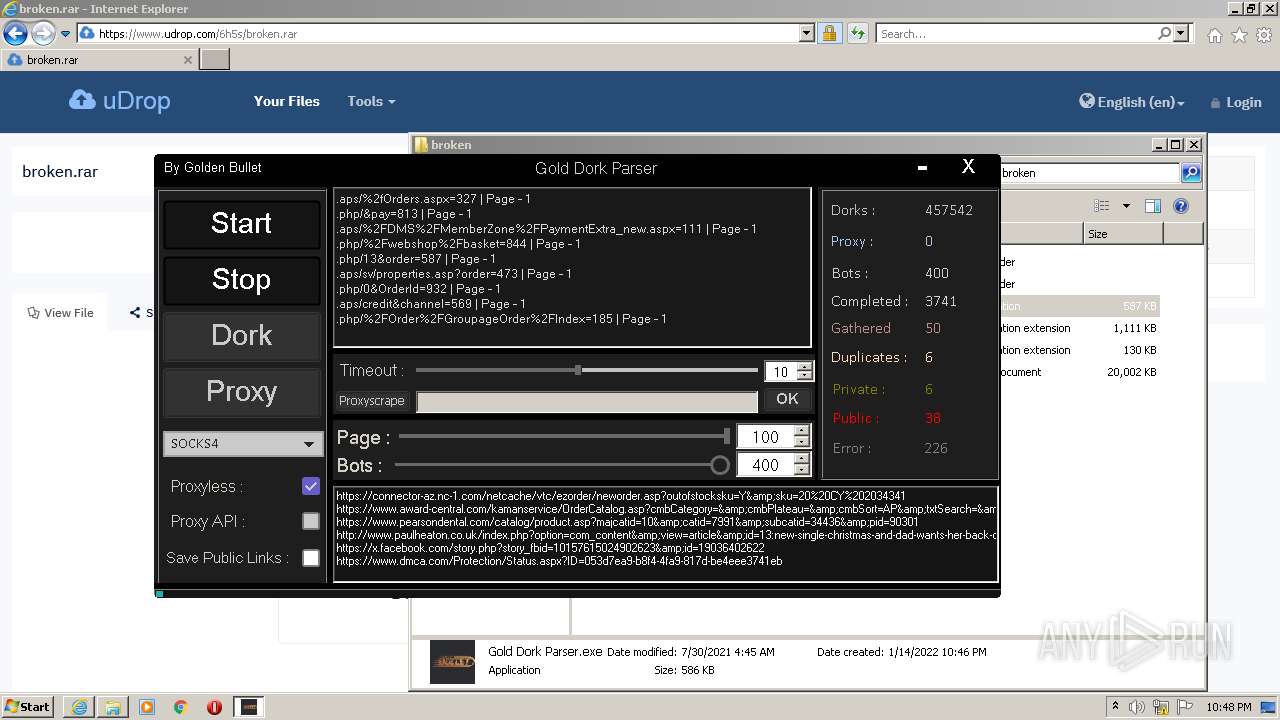
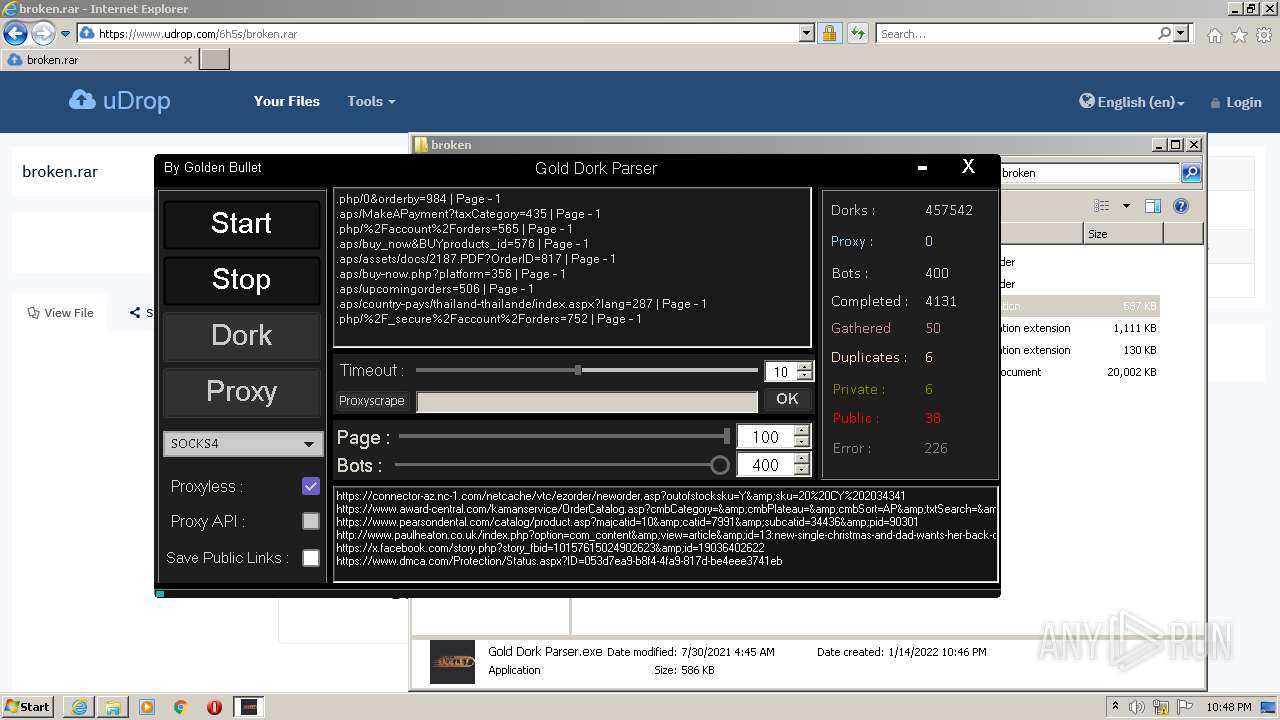
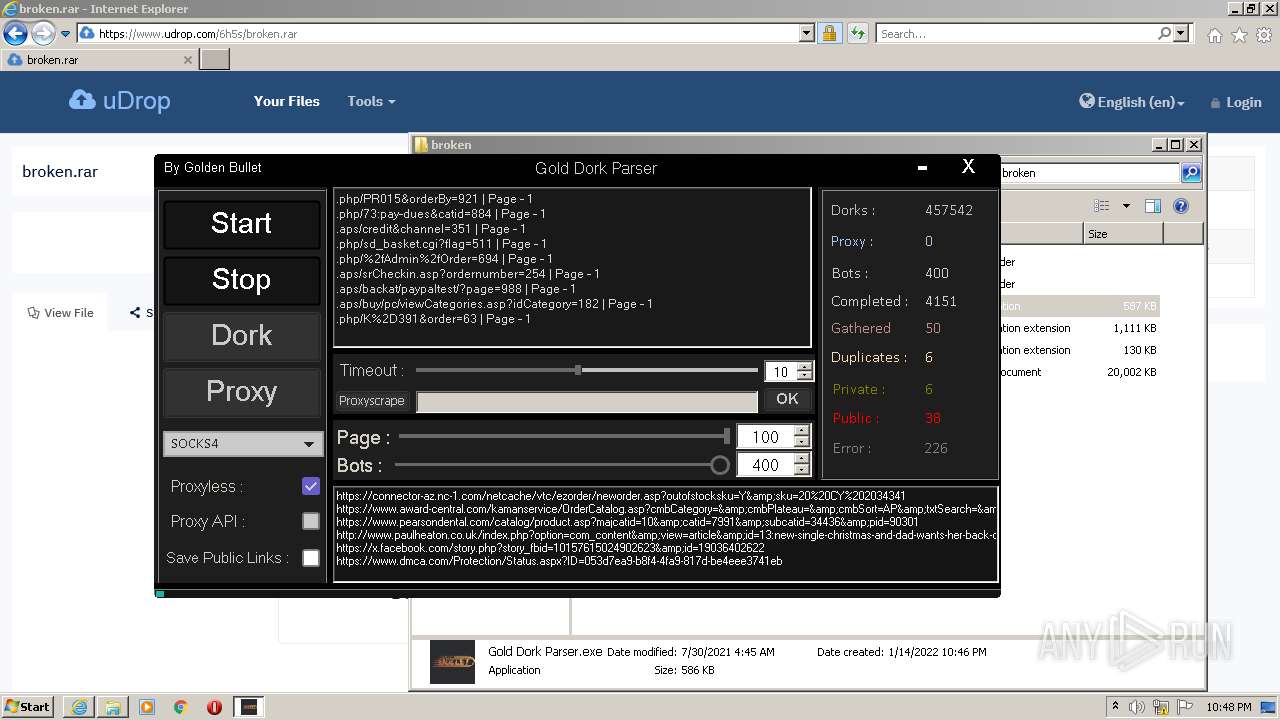
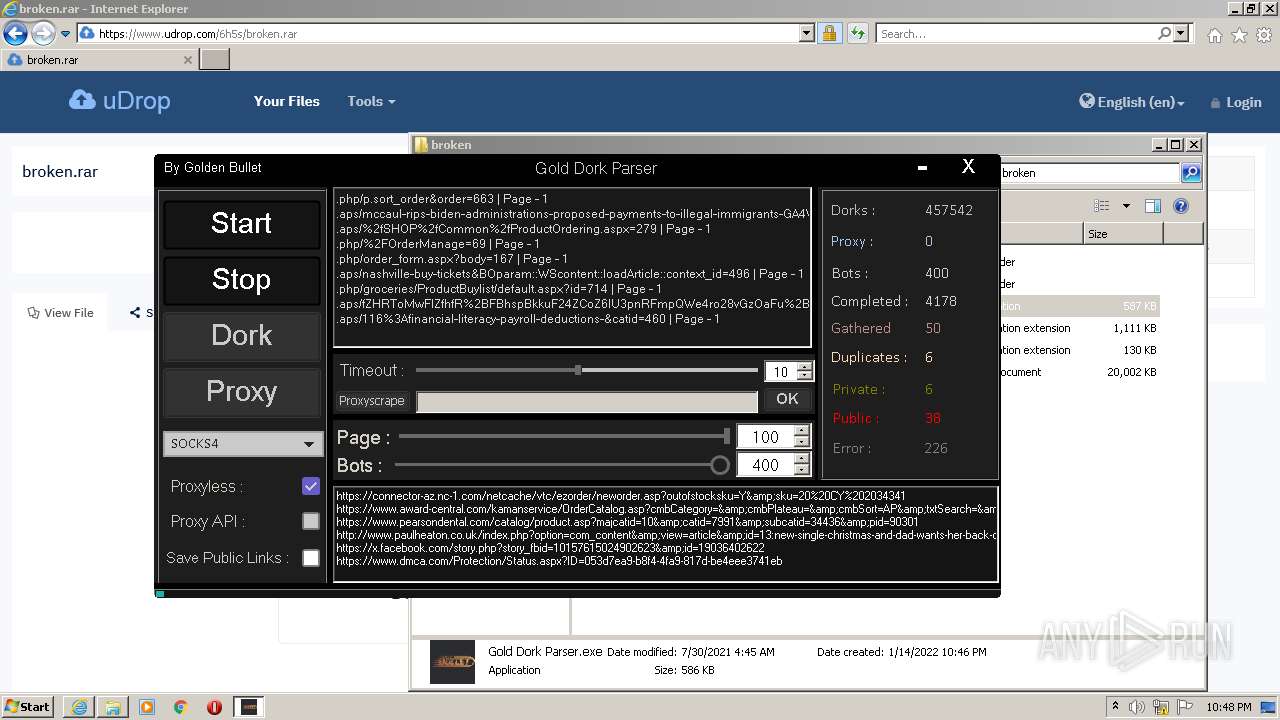
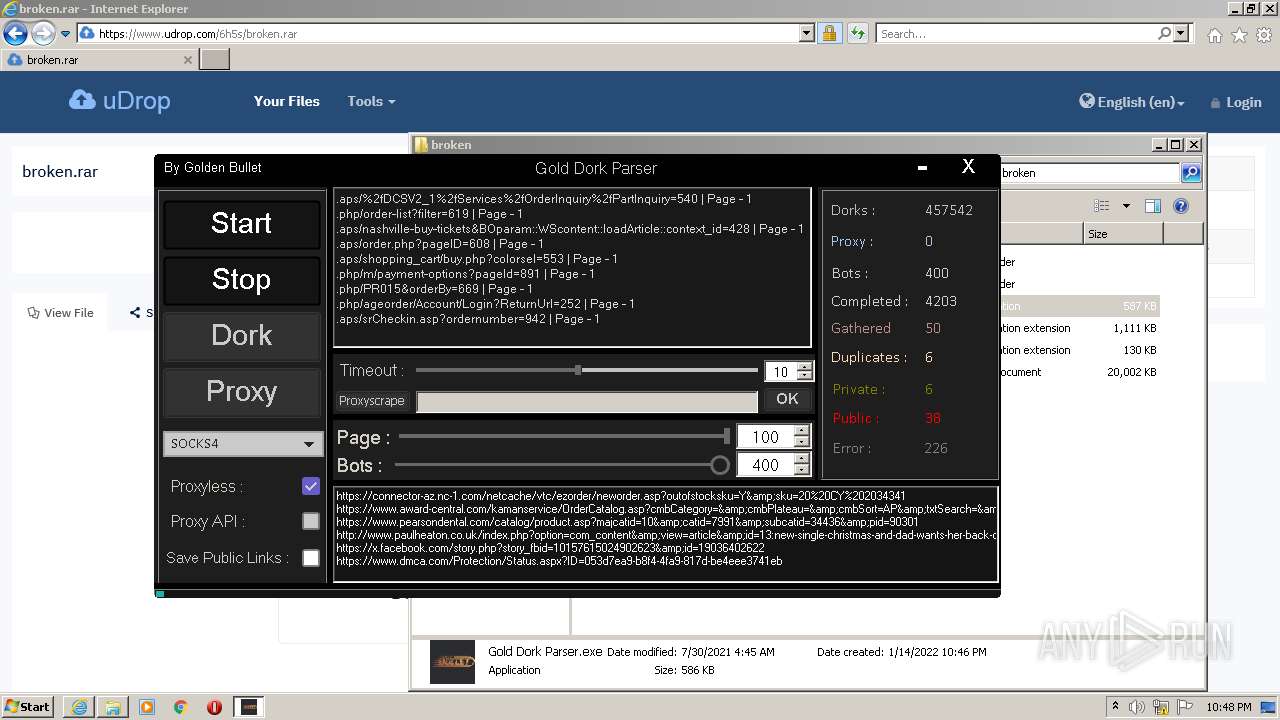
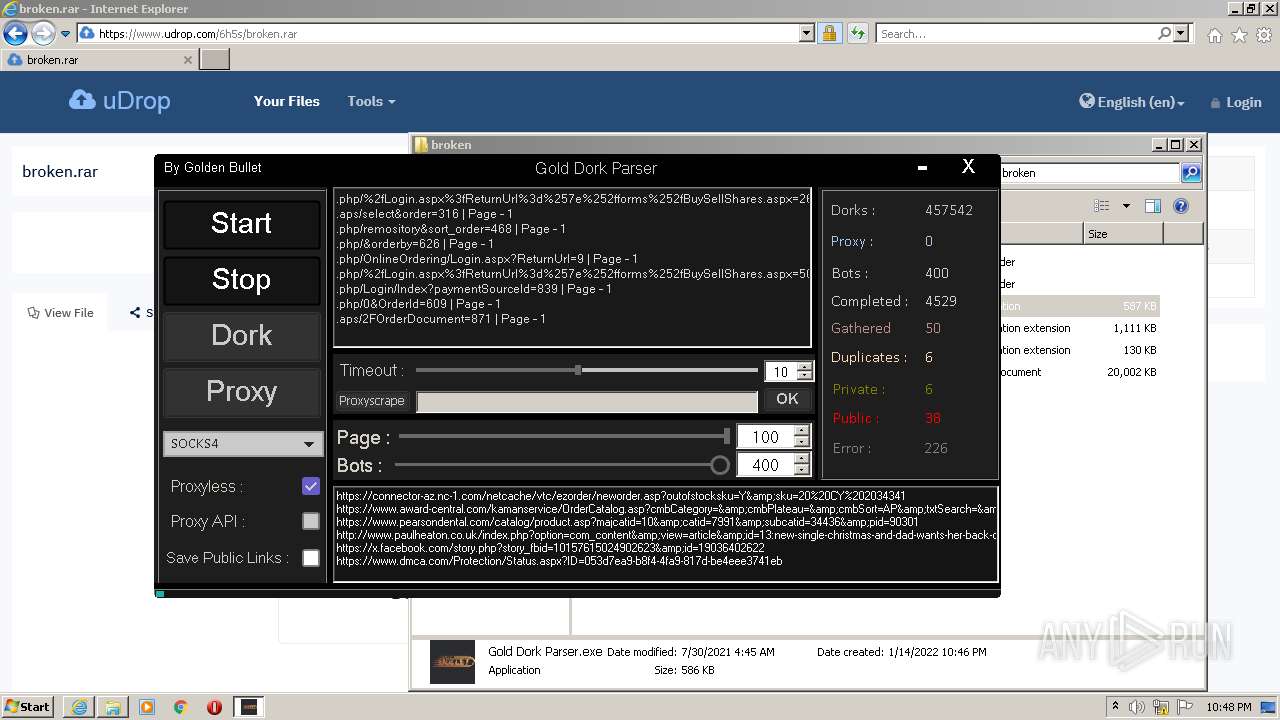
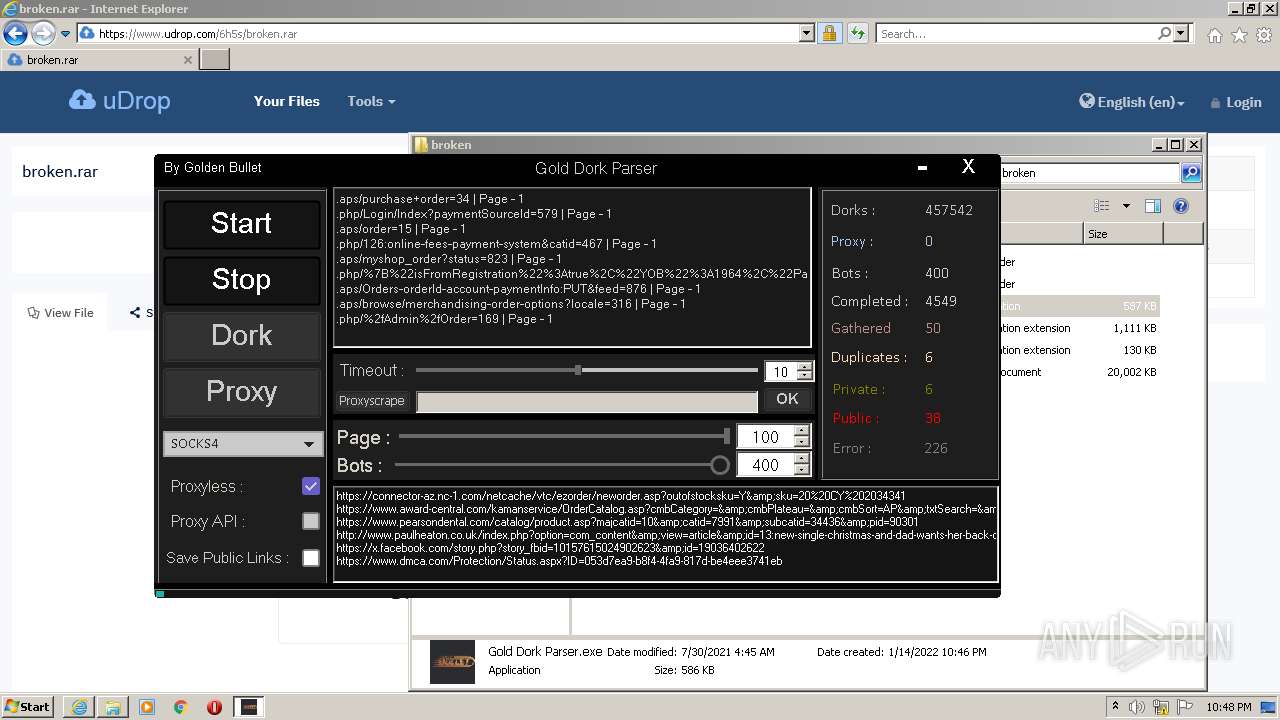
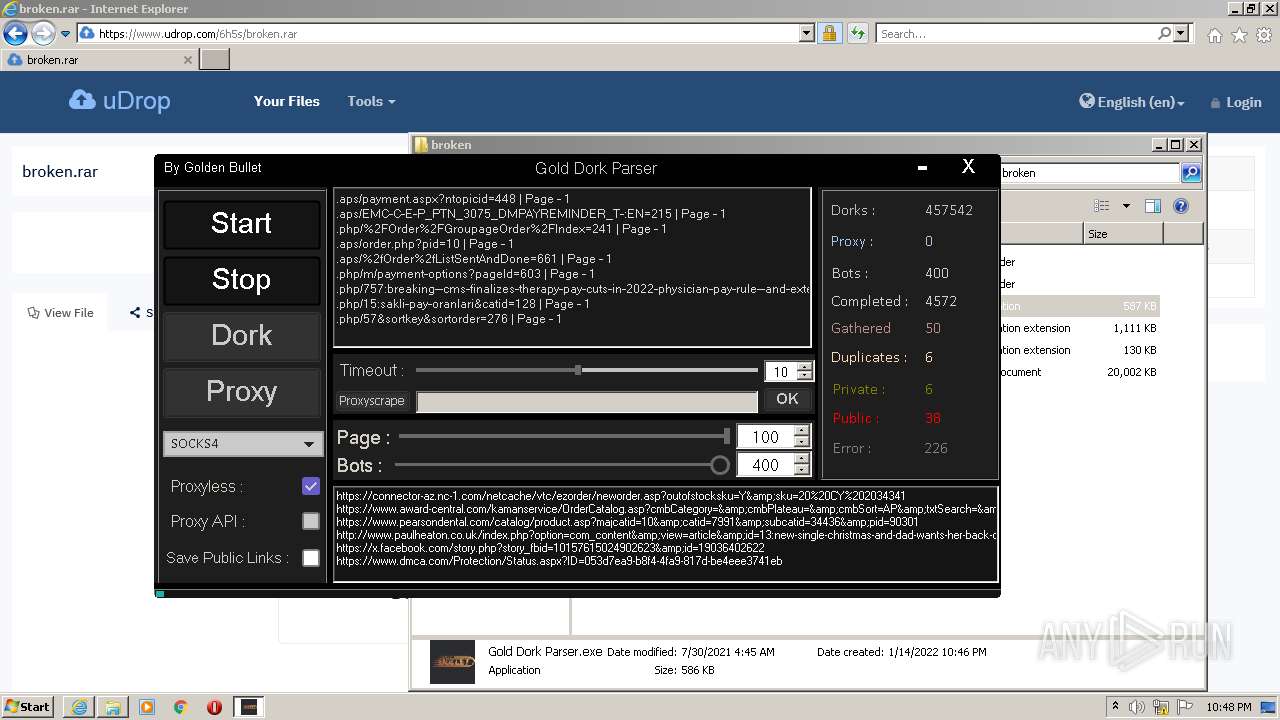
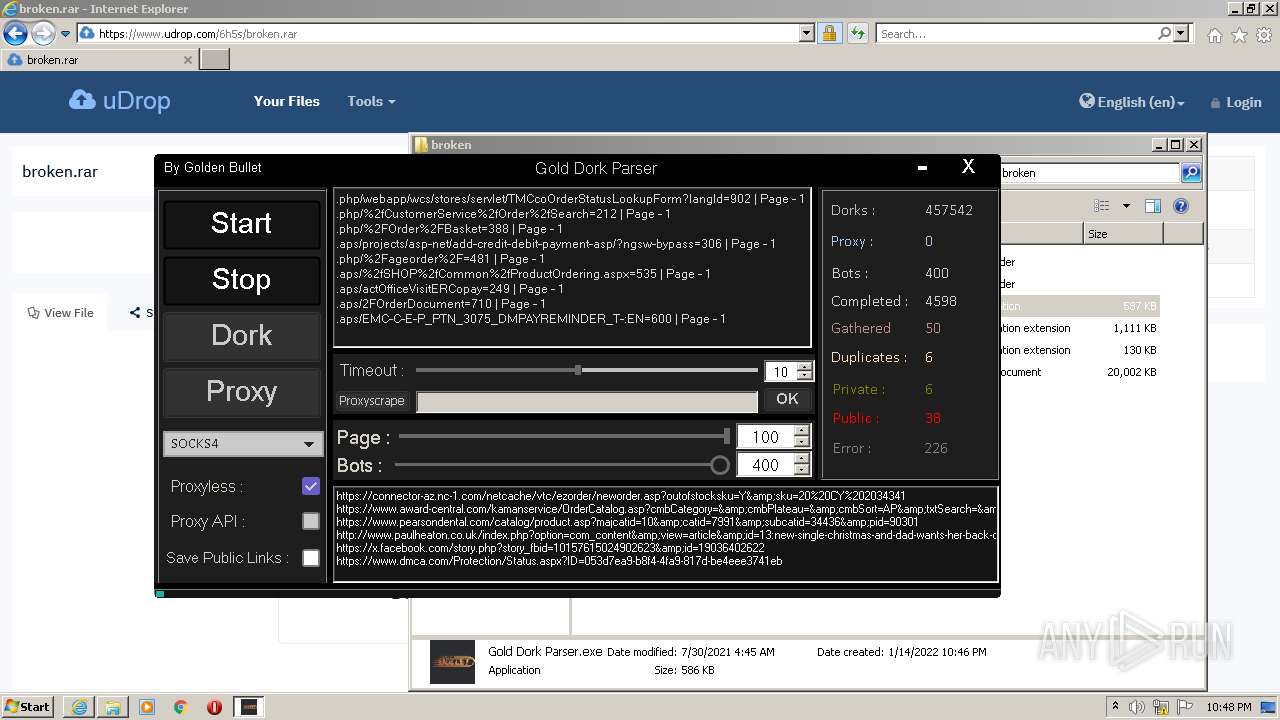
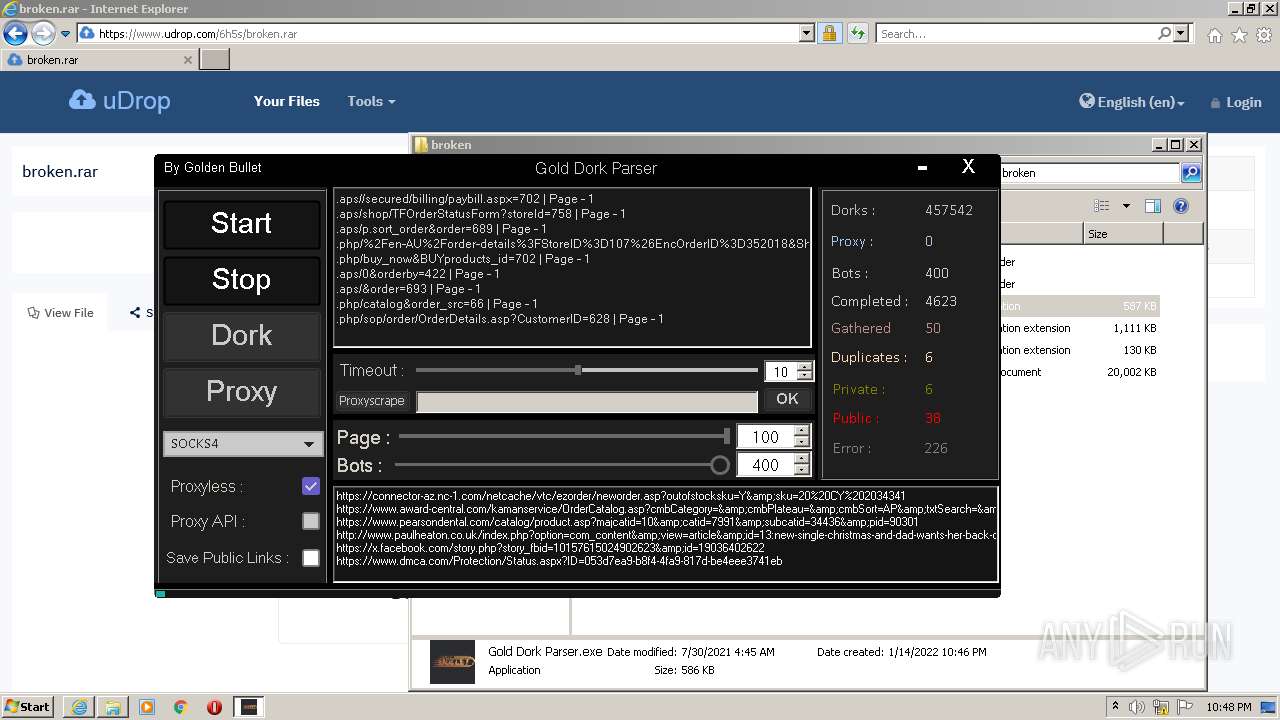
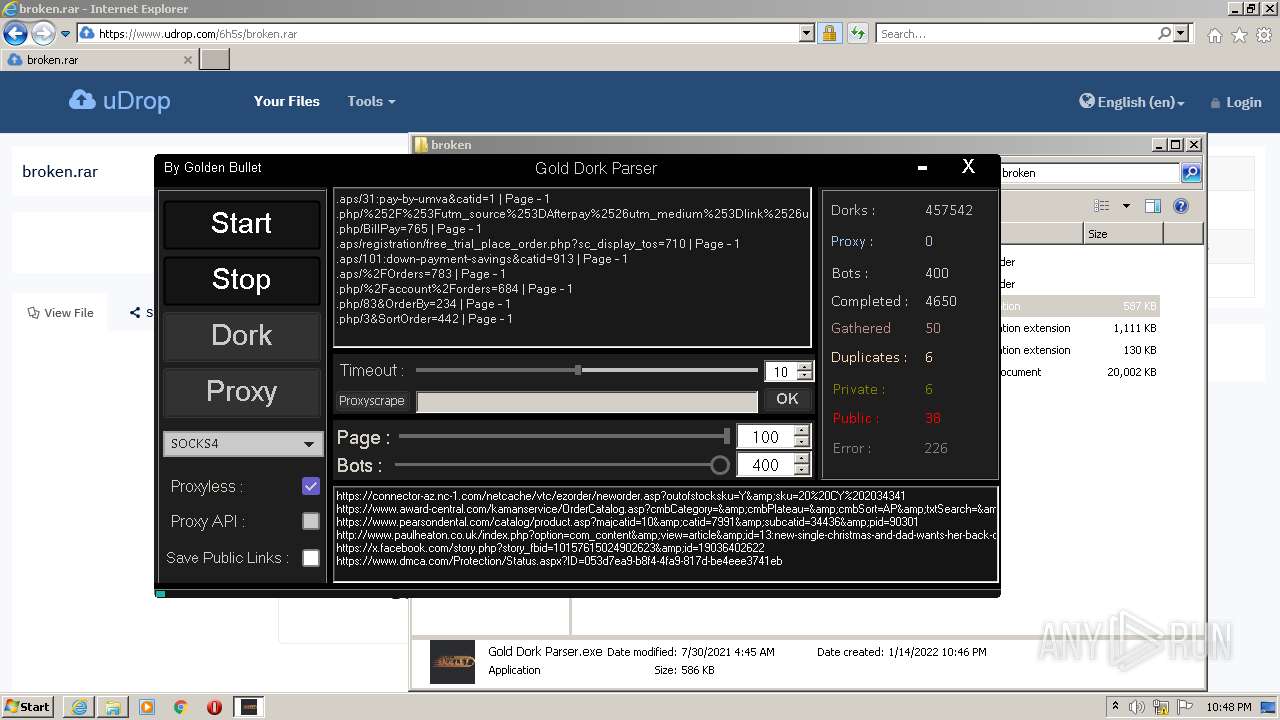
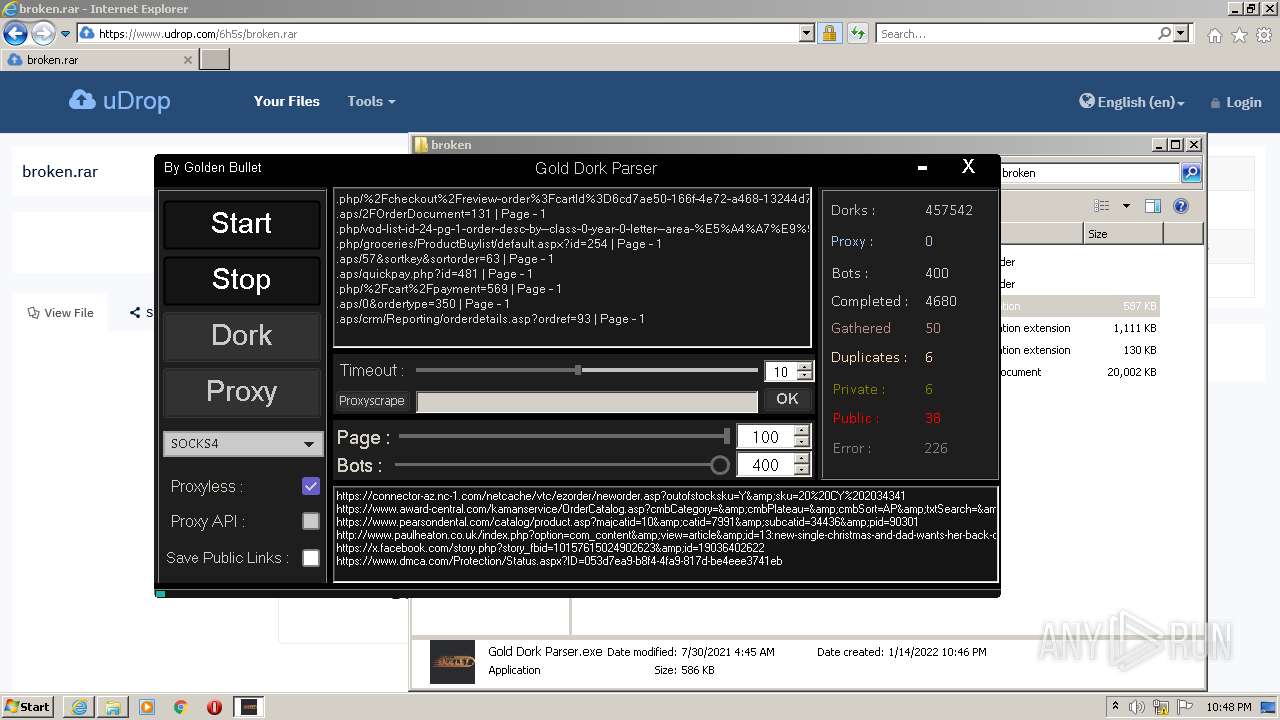
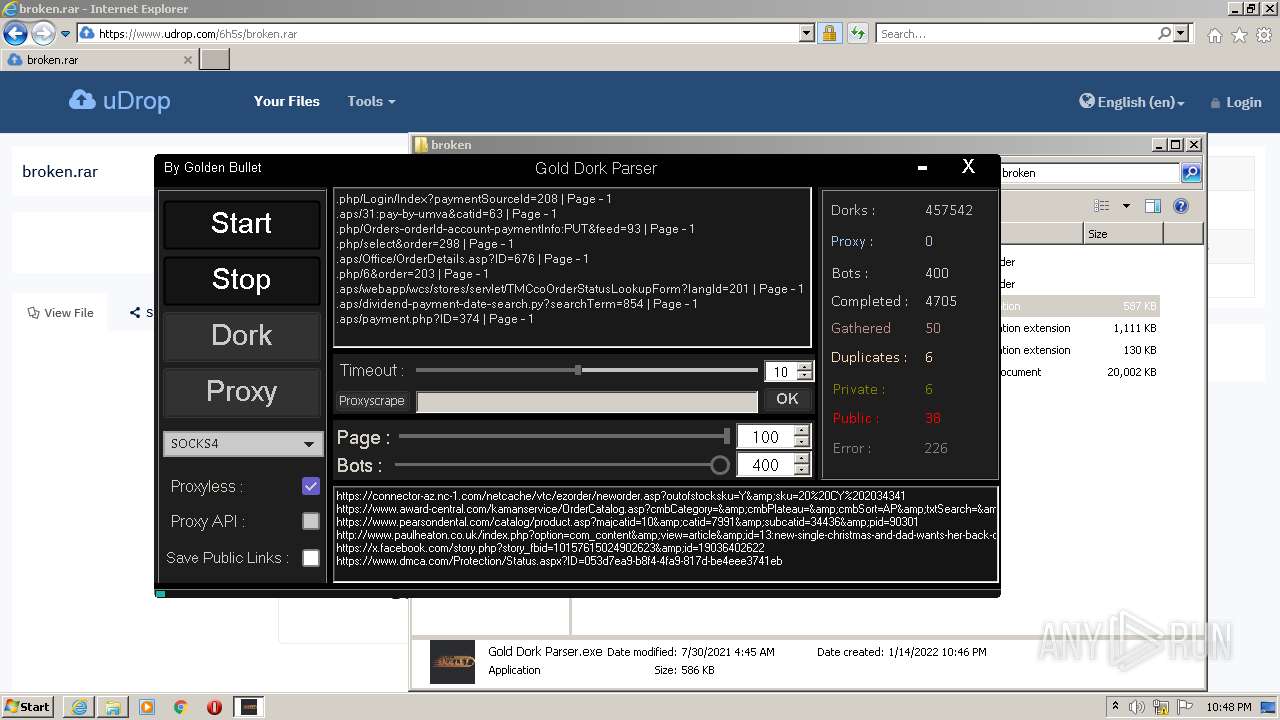
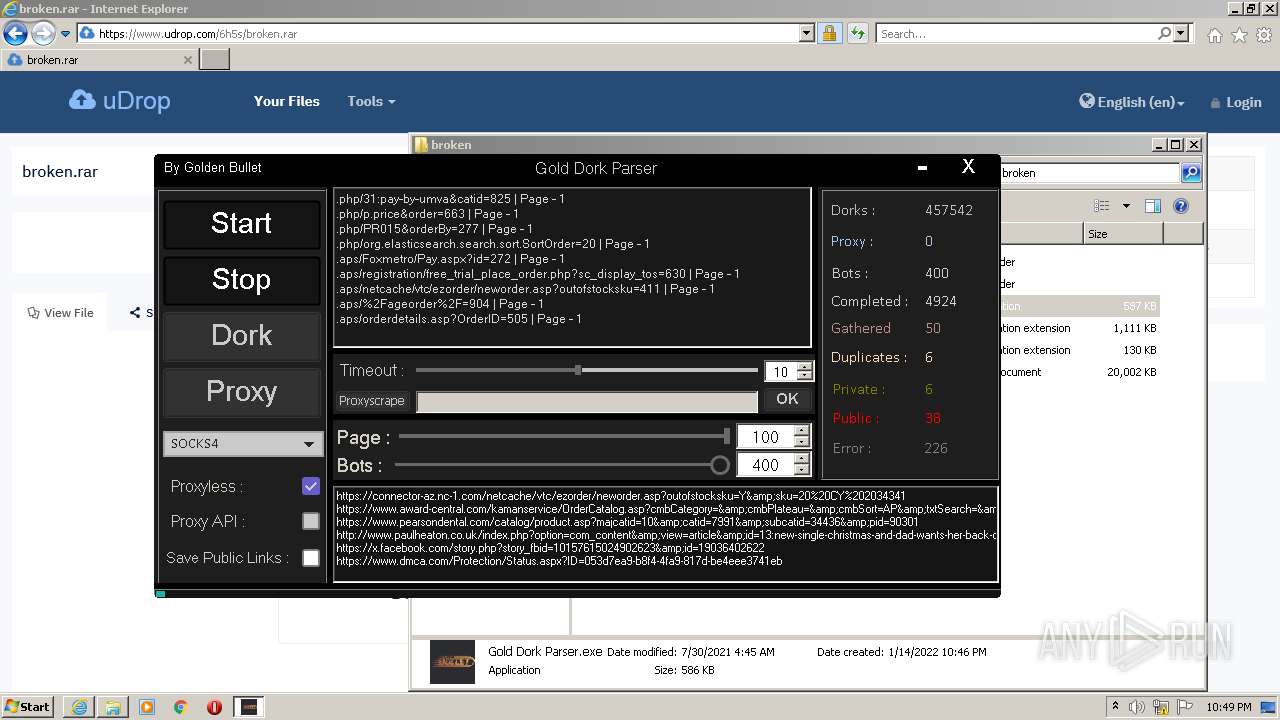
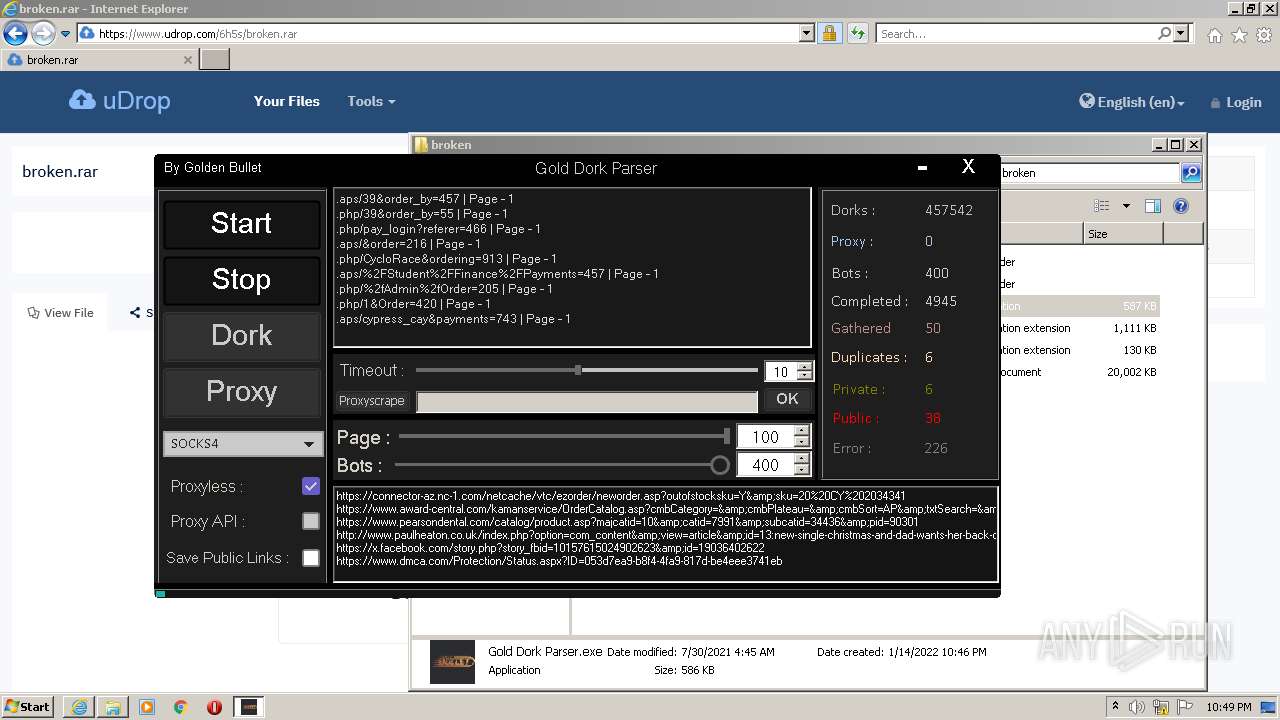
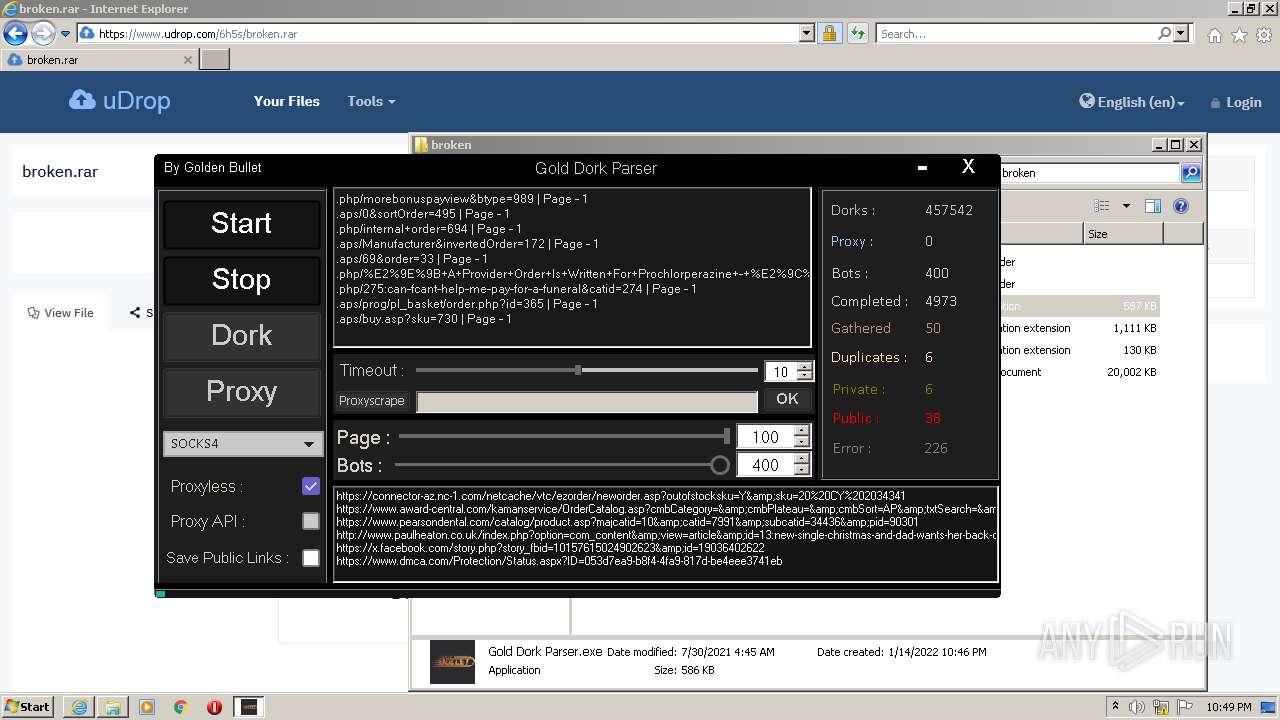
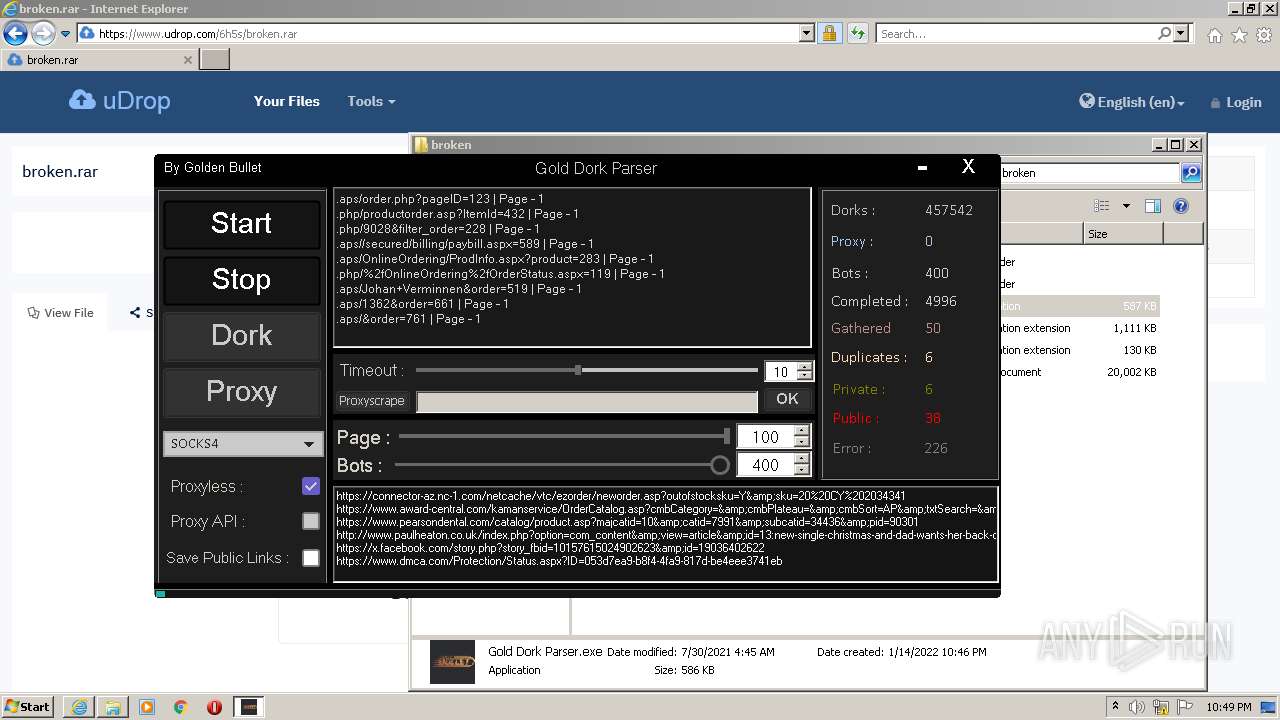
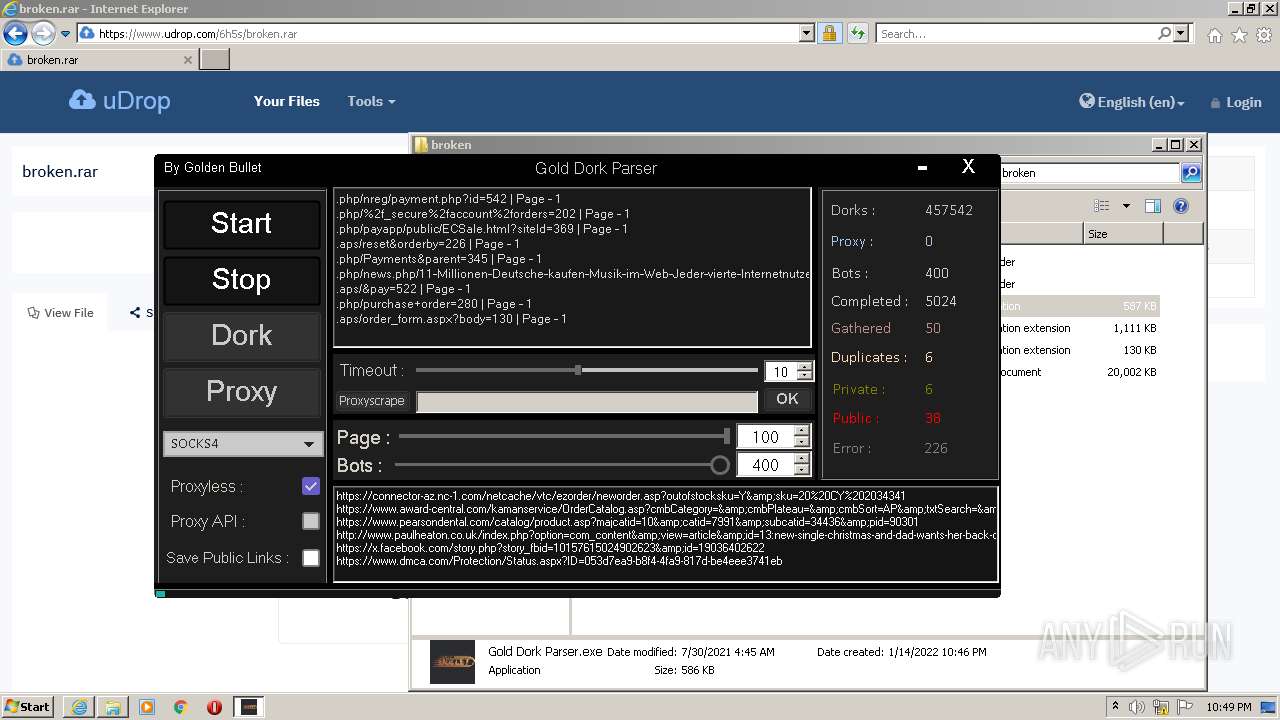
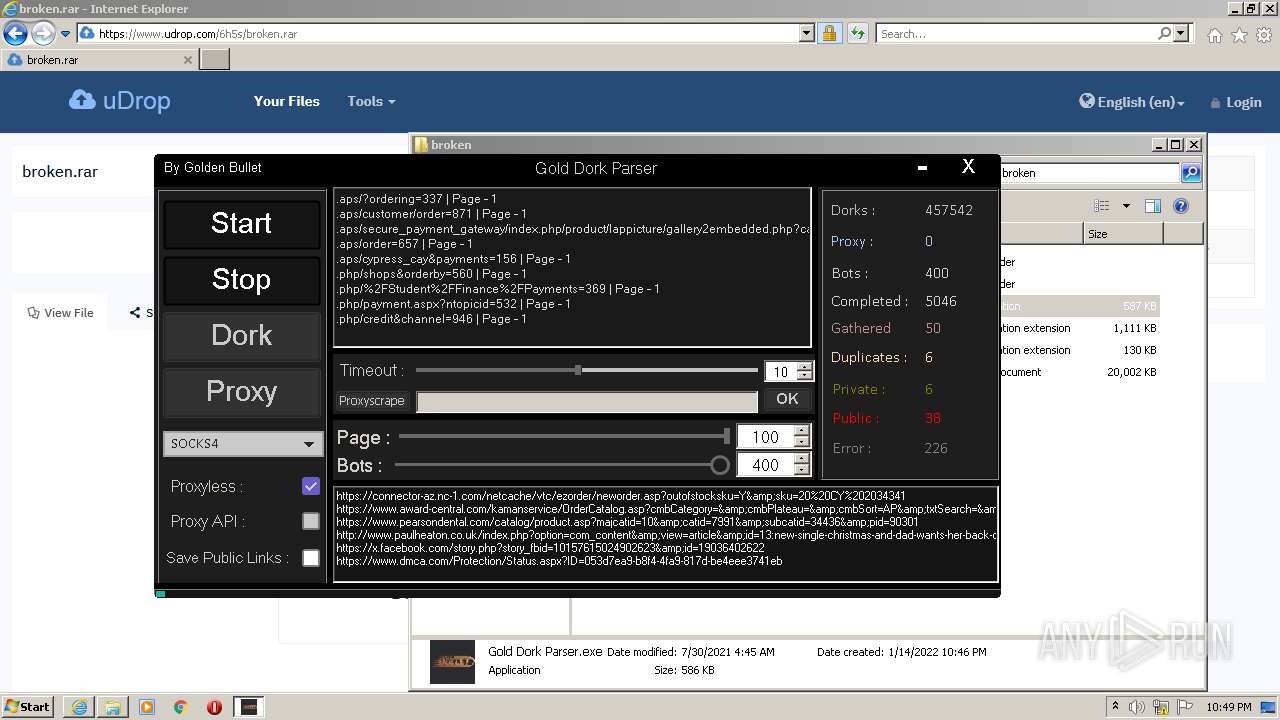
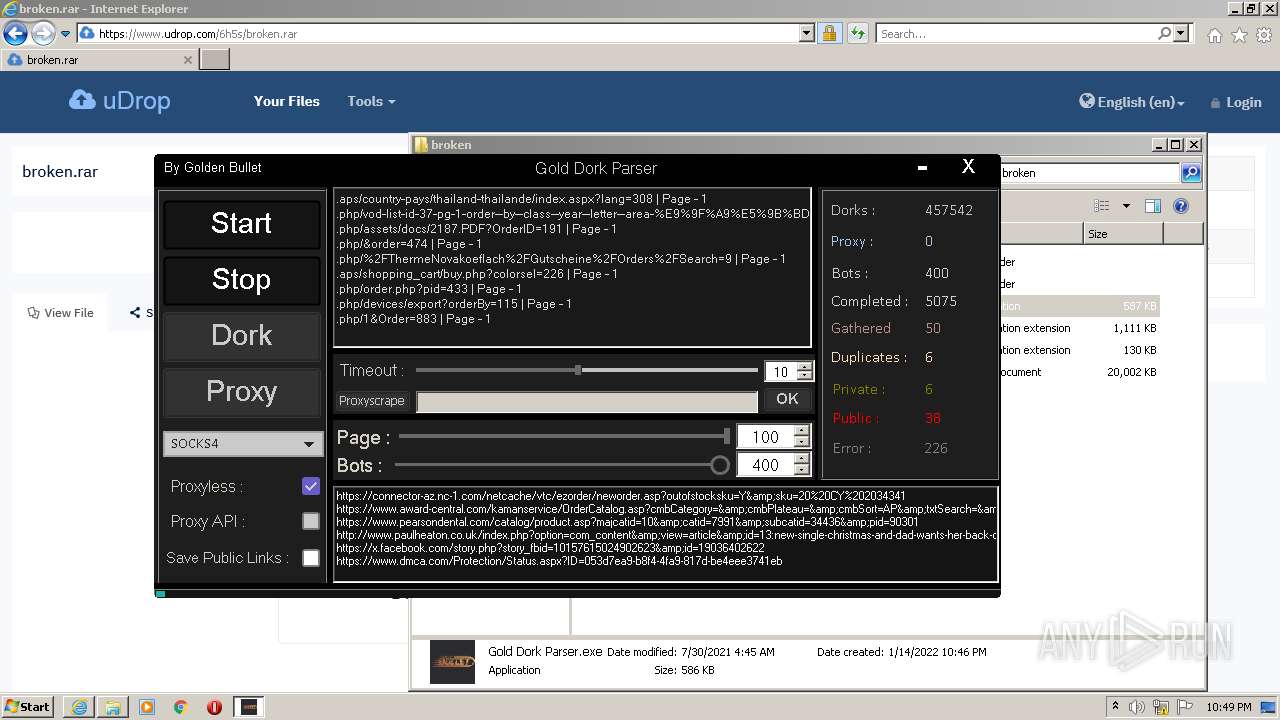
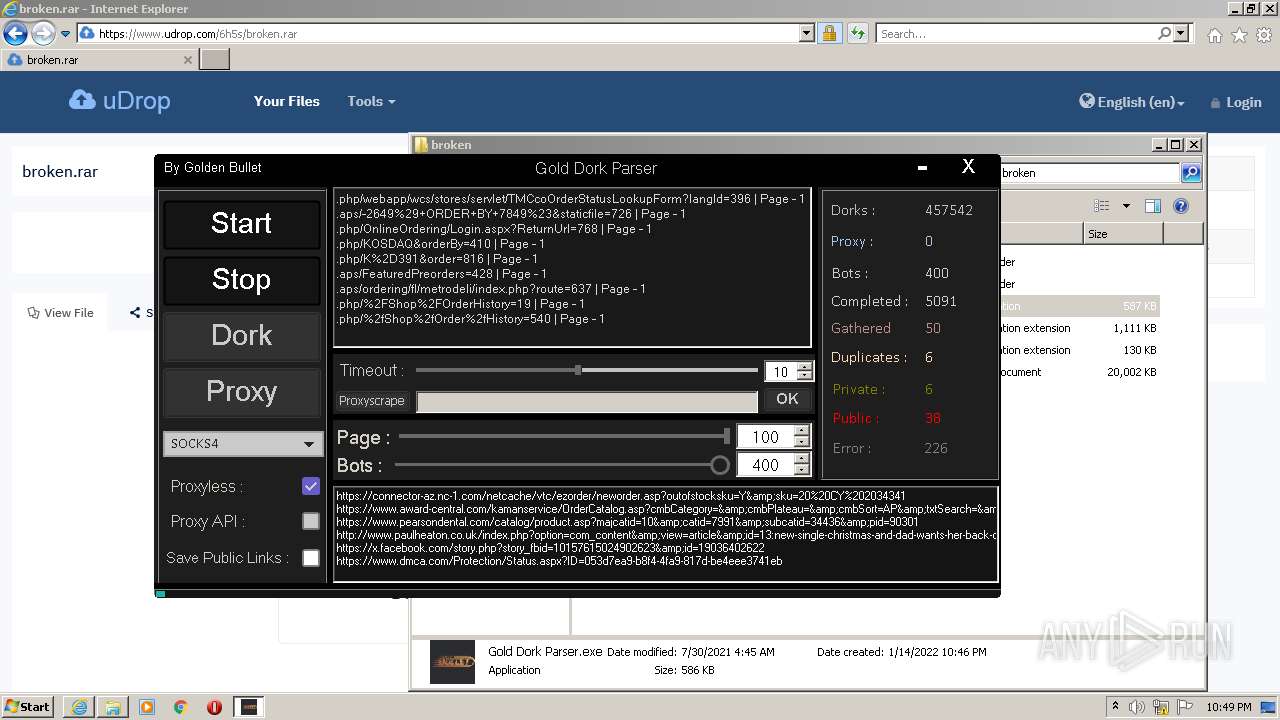
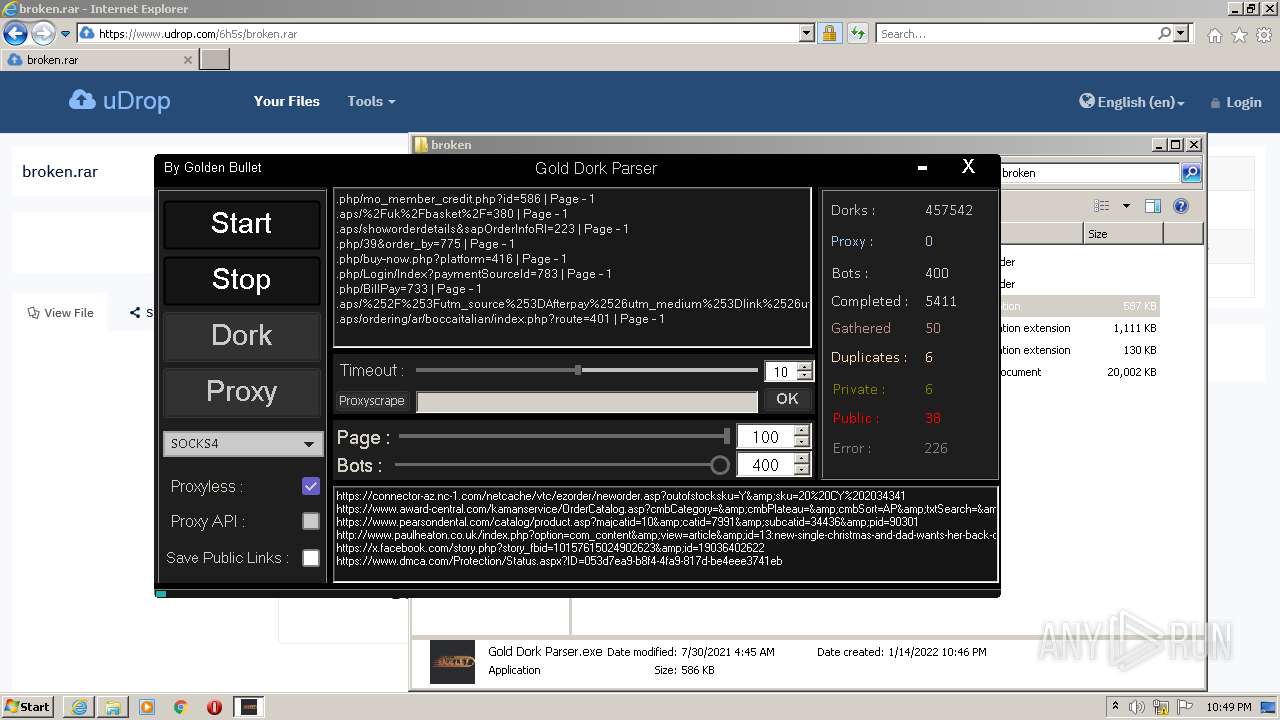
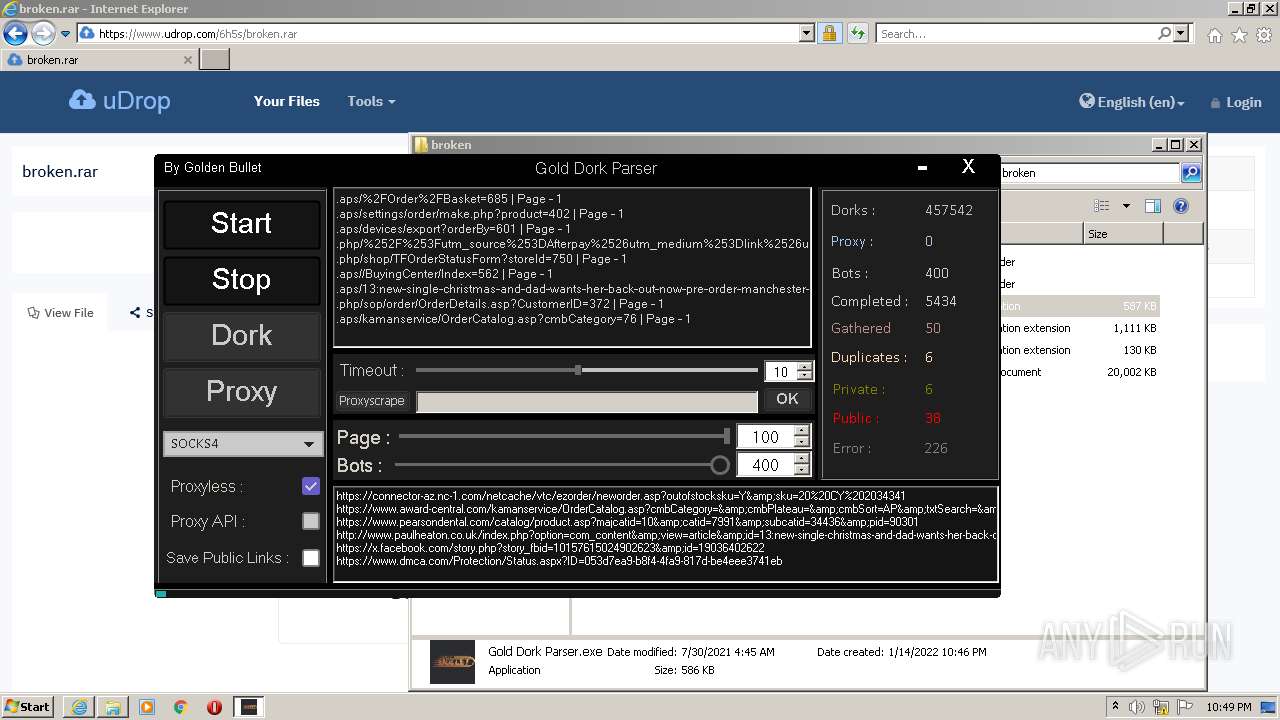
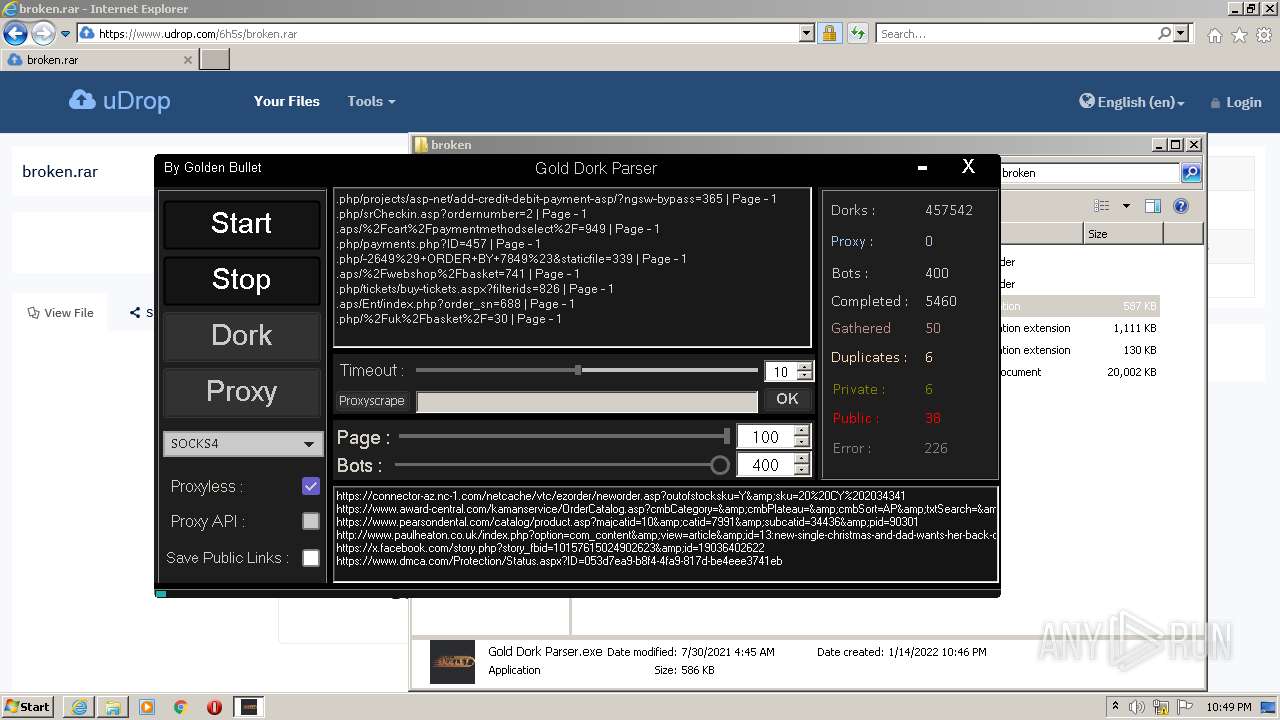
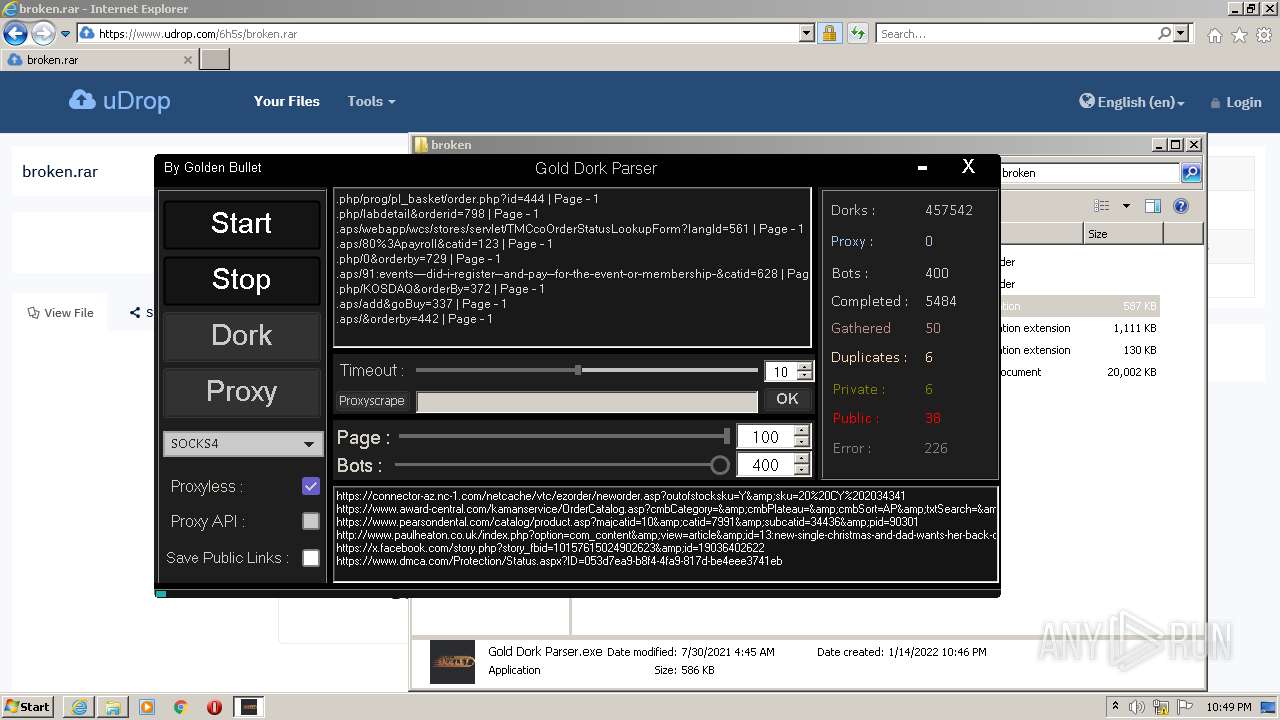
MALICIOUS
Application was dropped or rewritten from another process
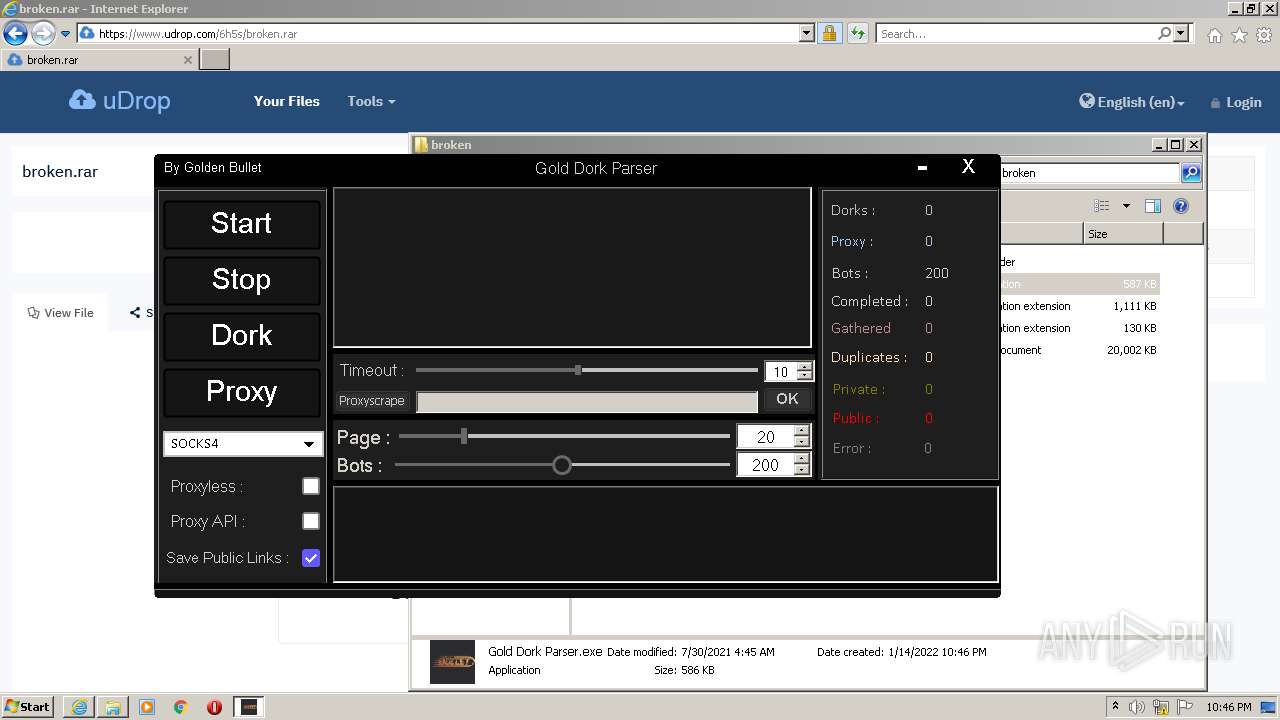
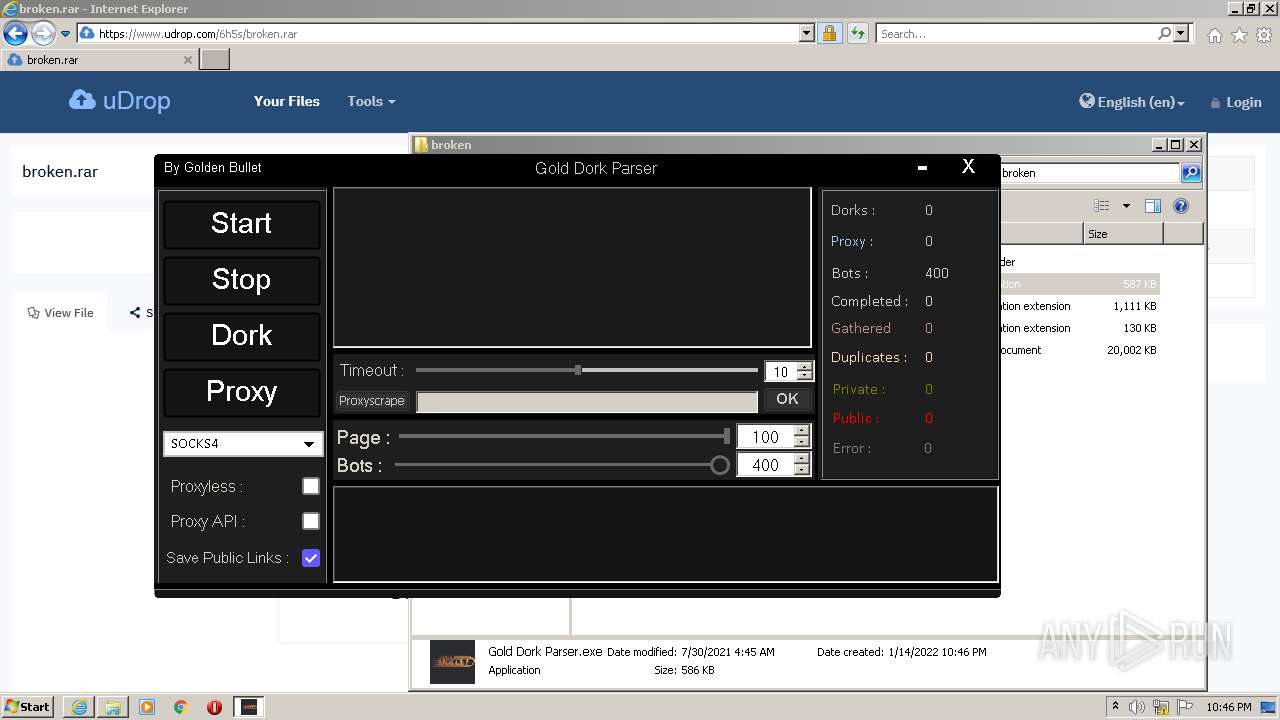
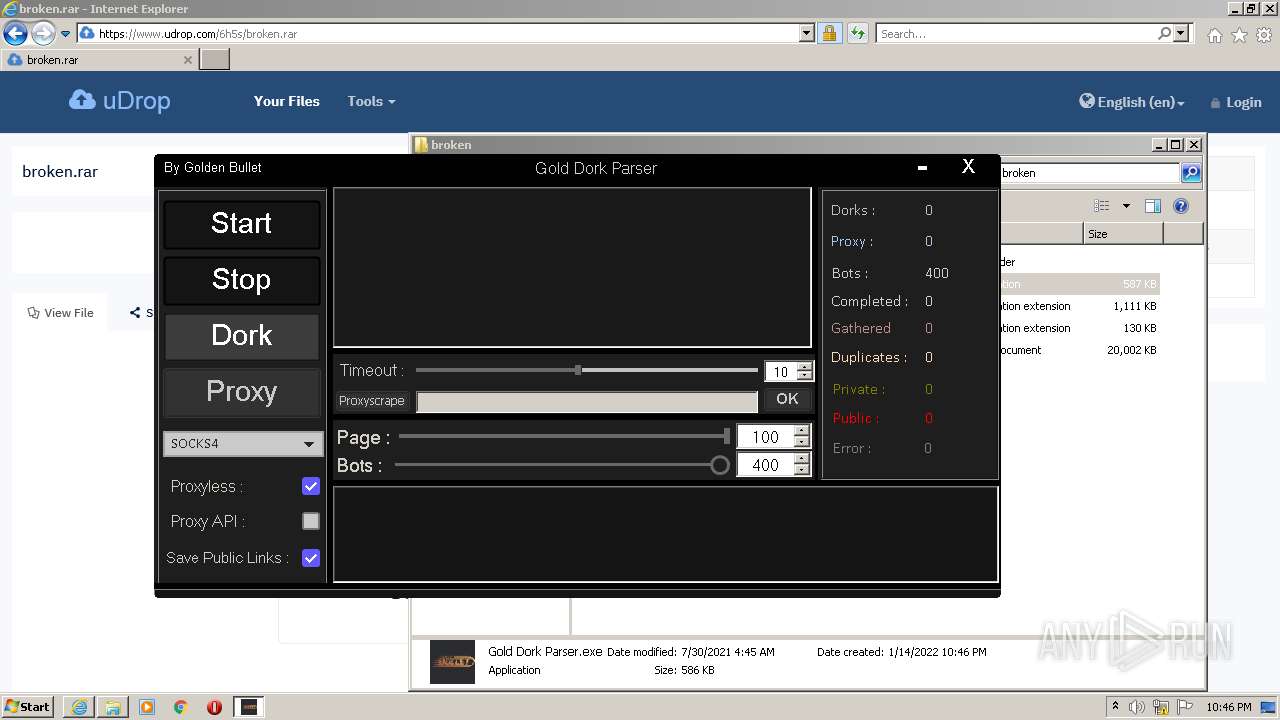
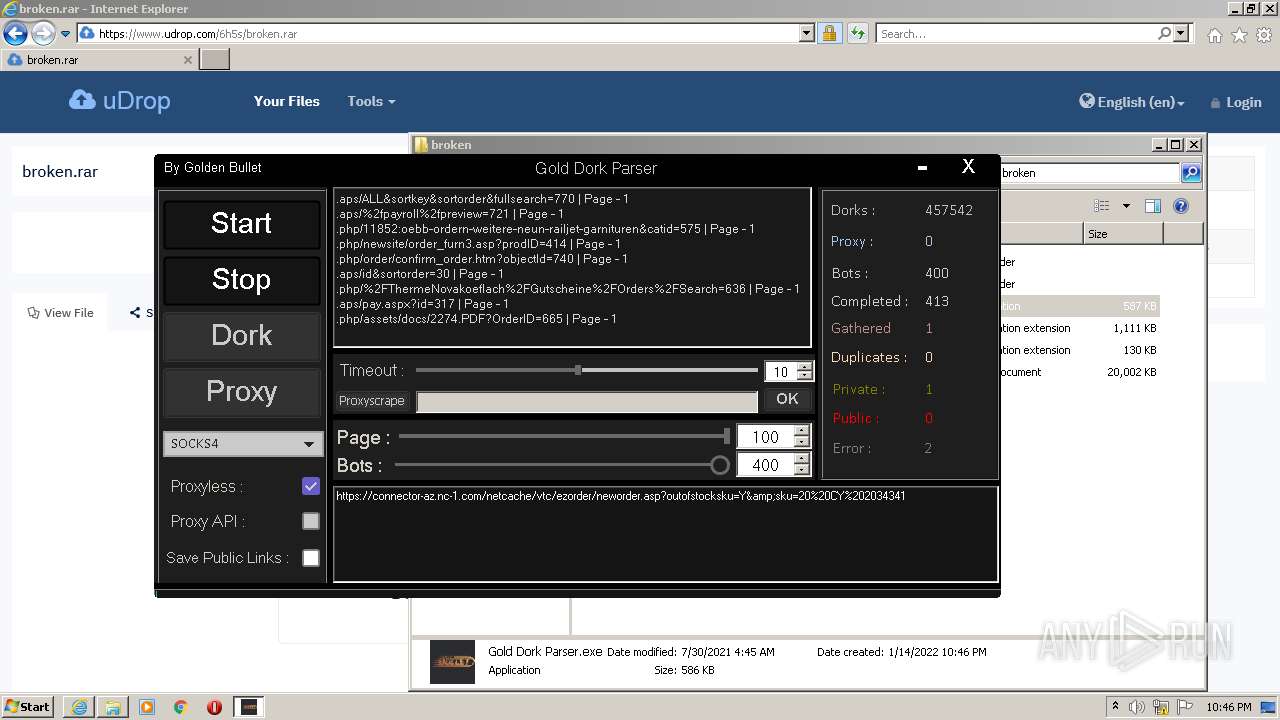
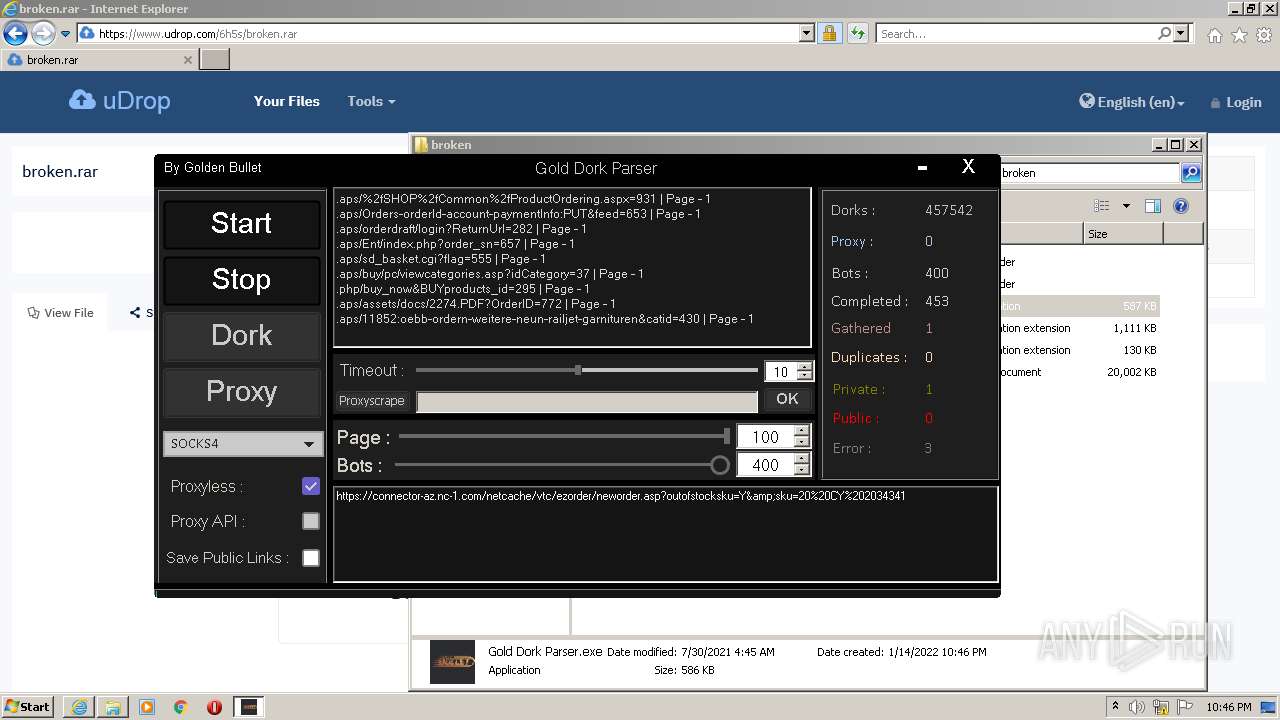
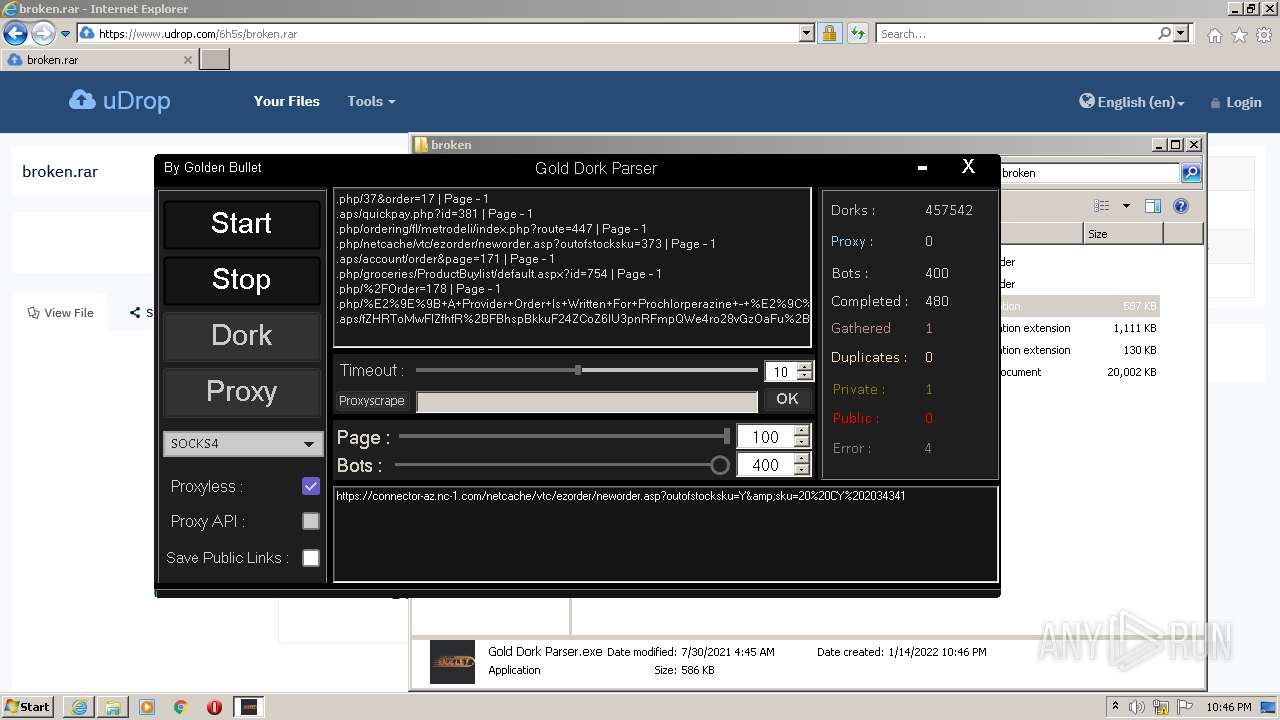
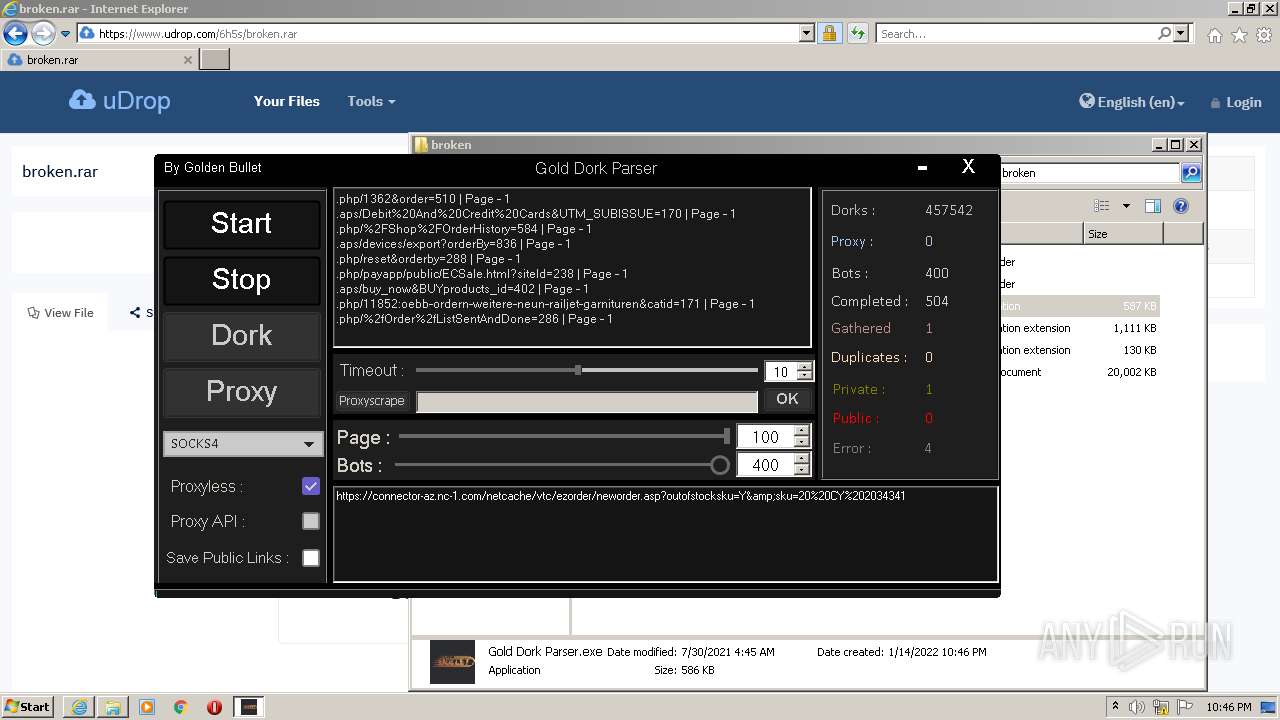
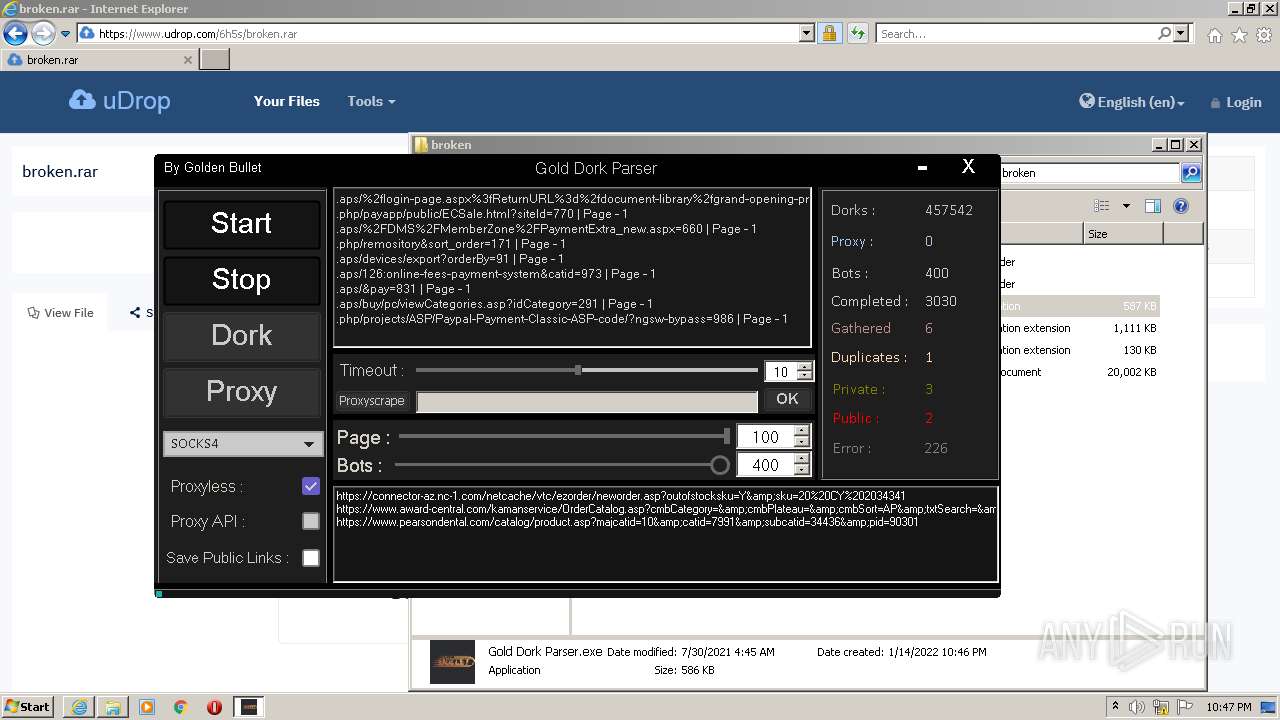
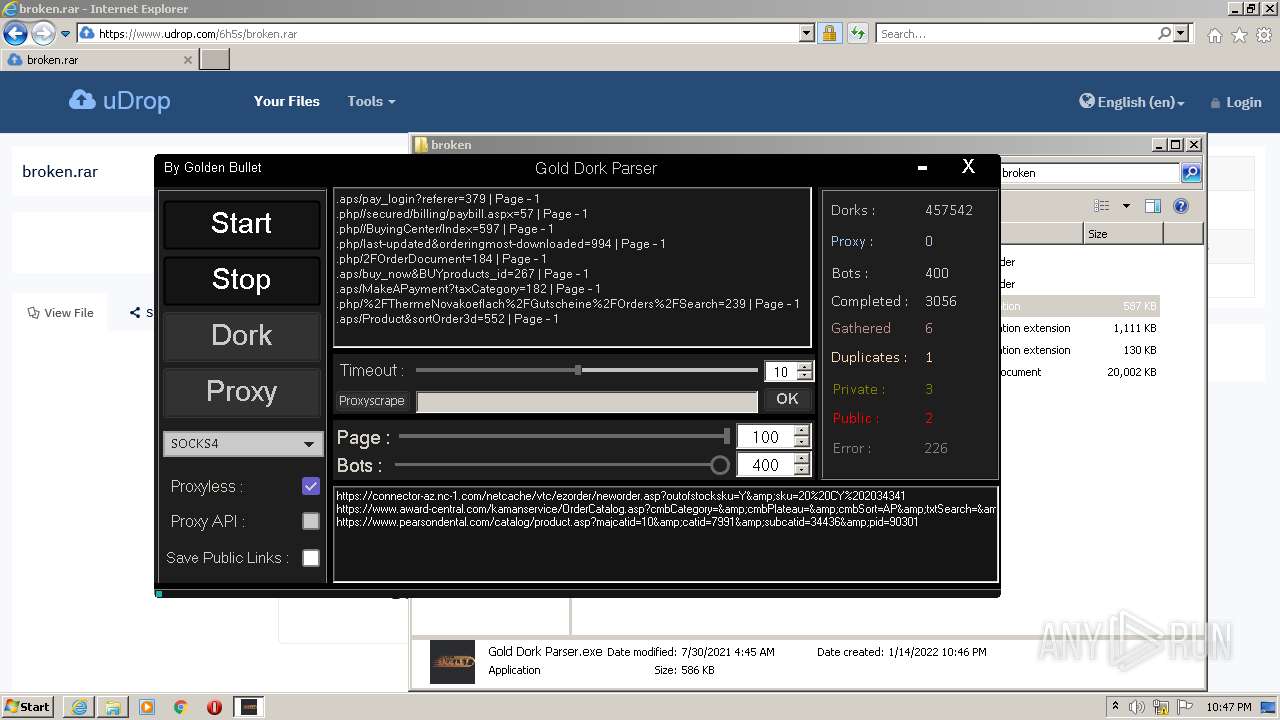
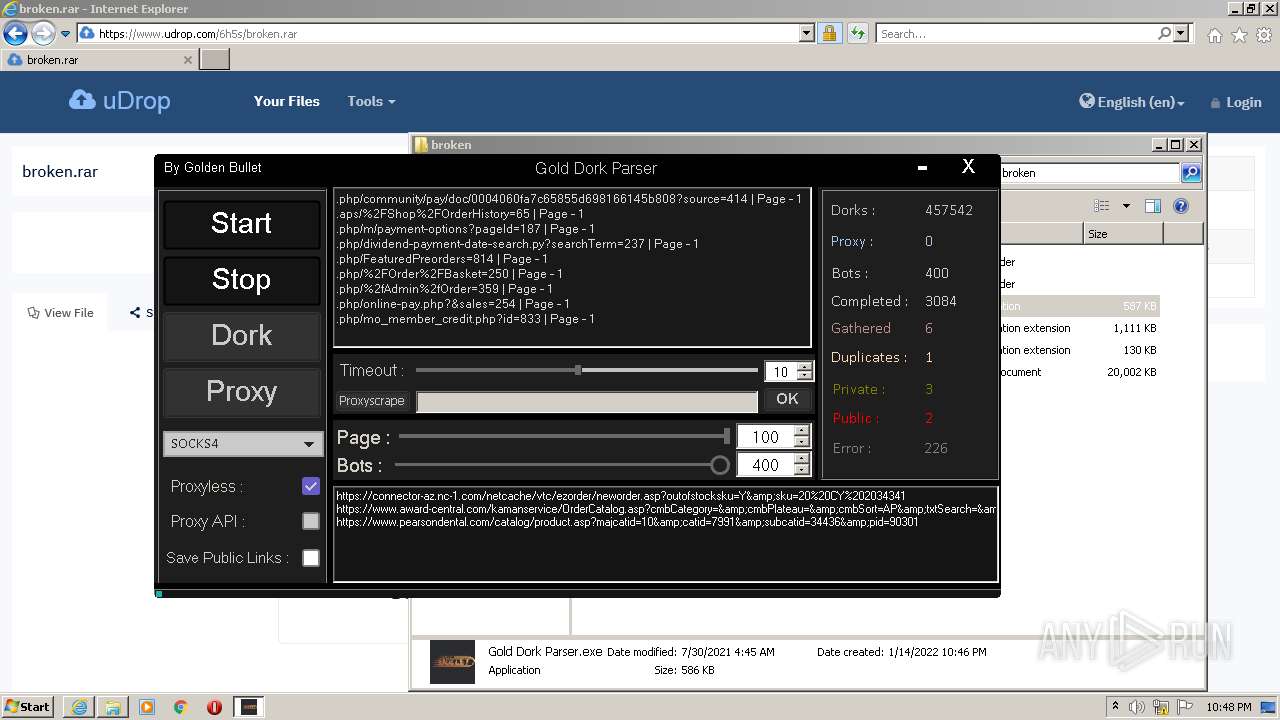
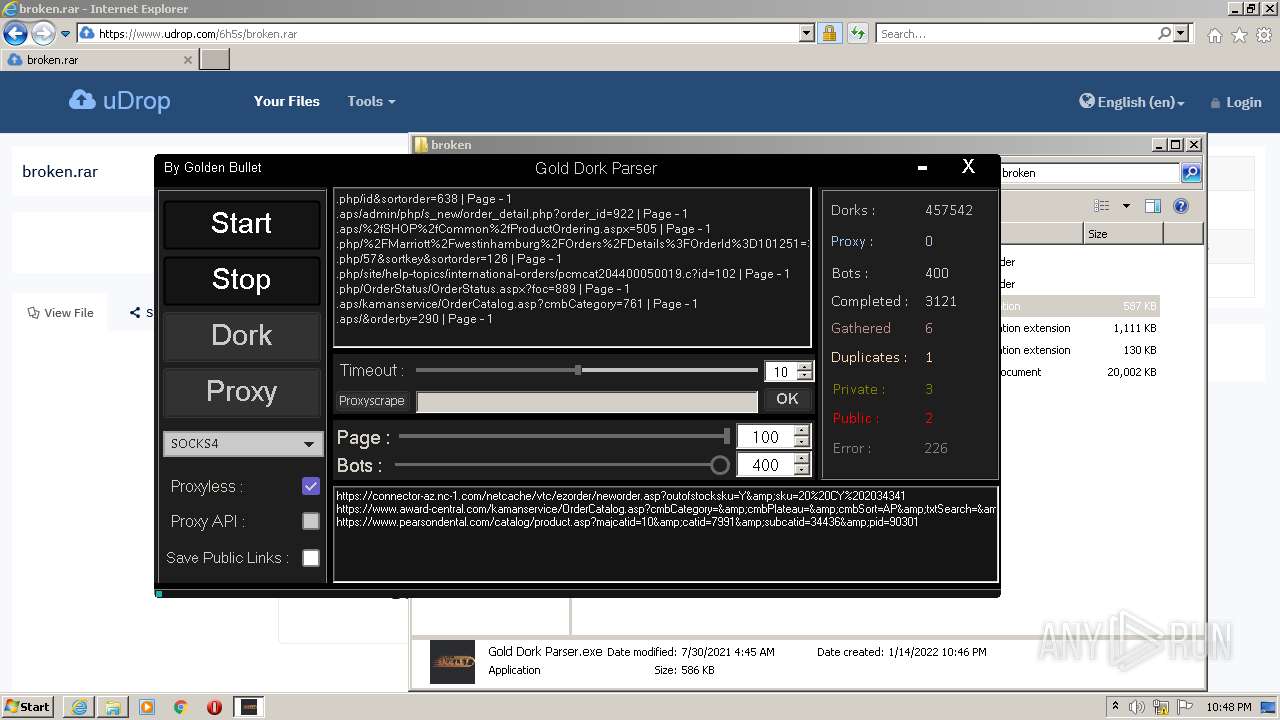
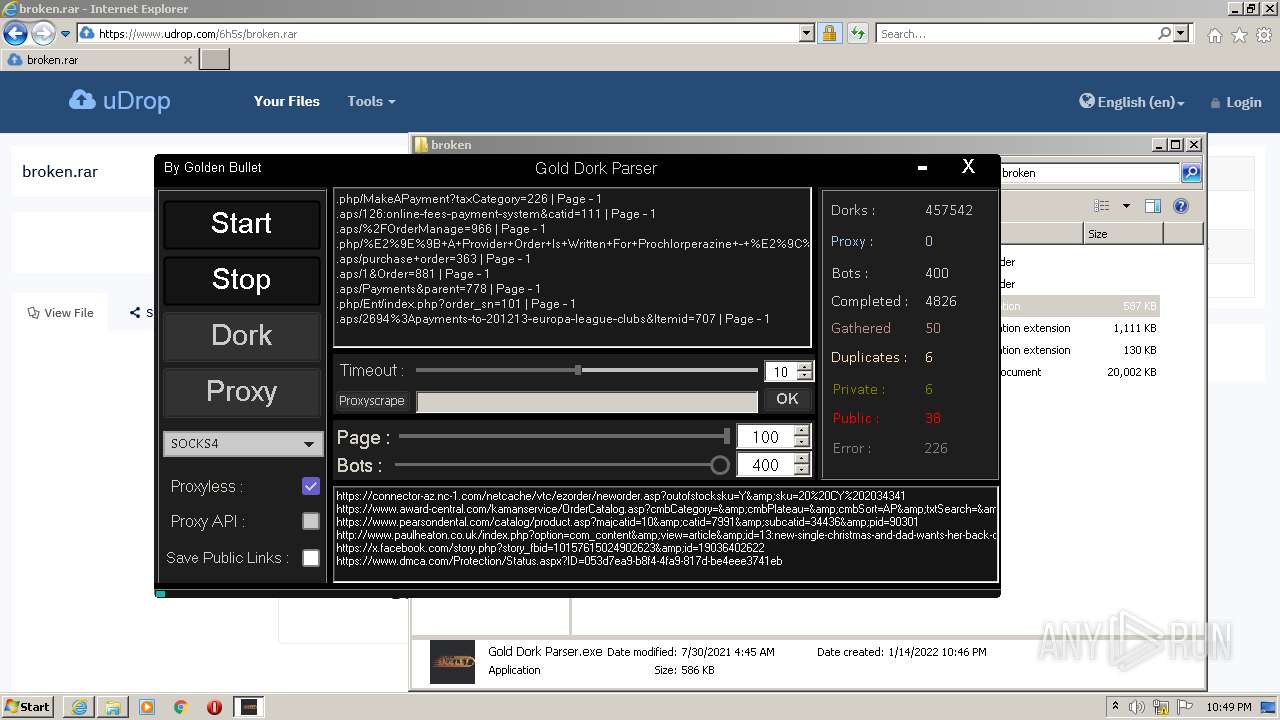
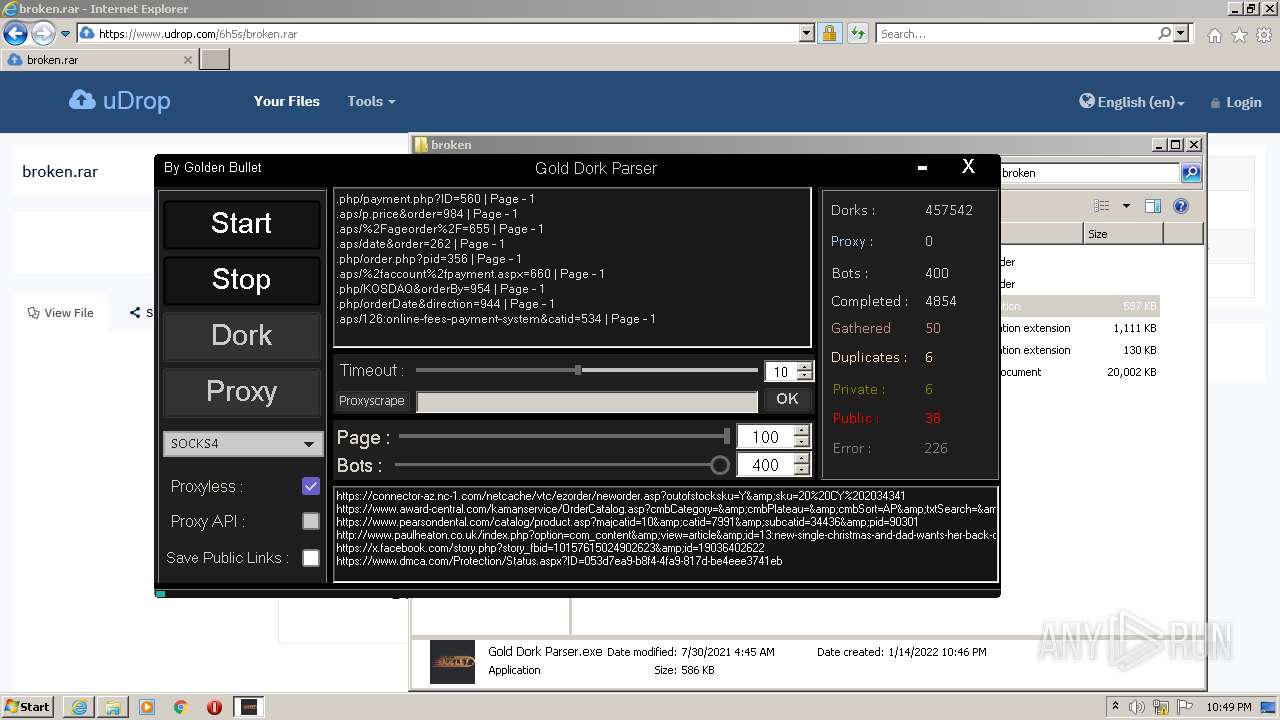
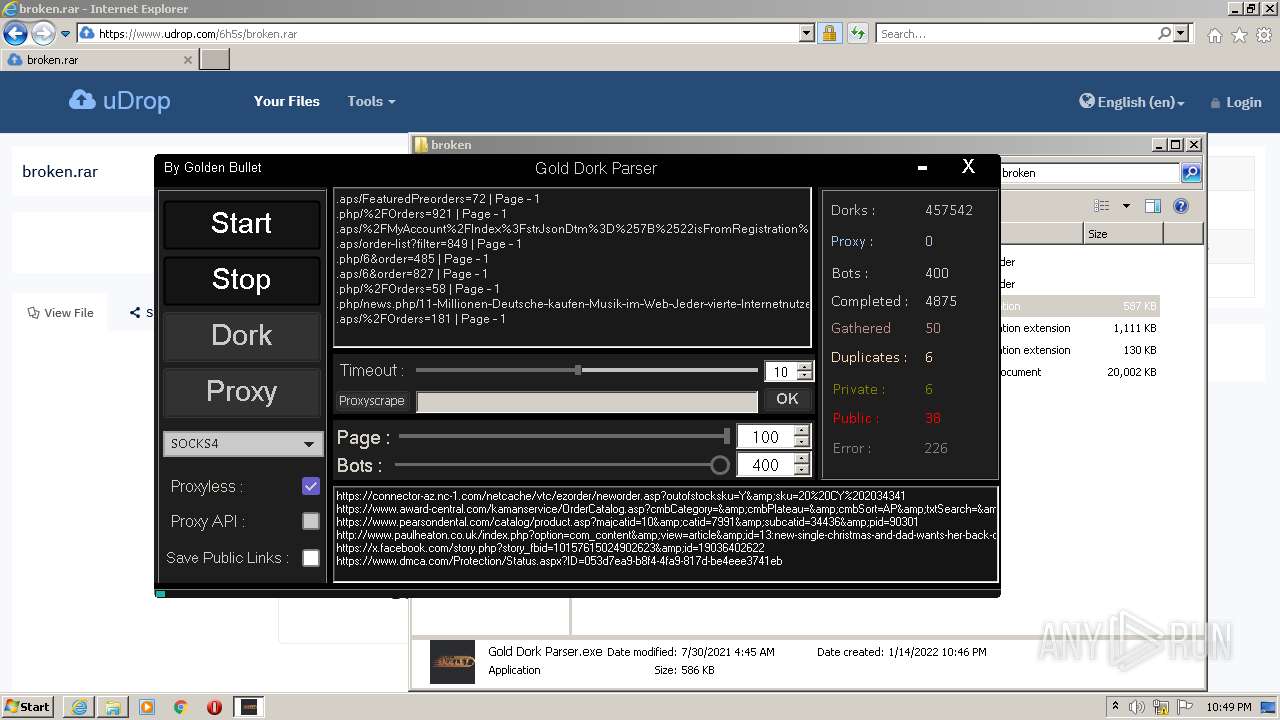
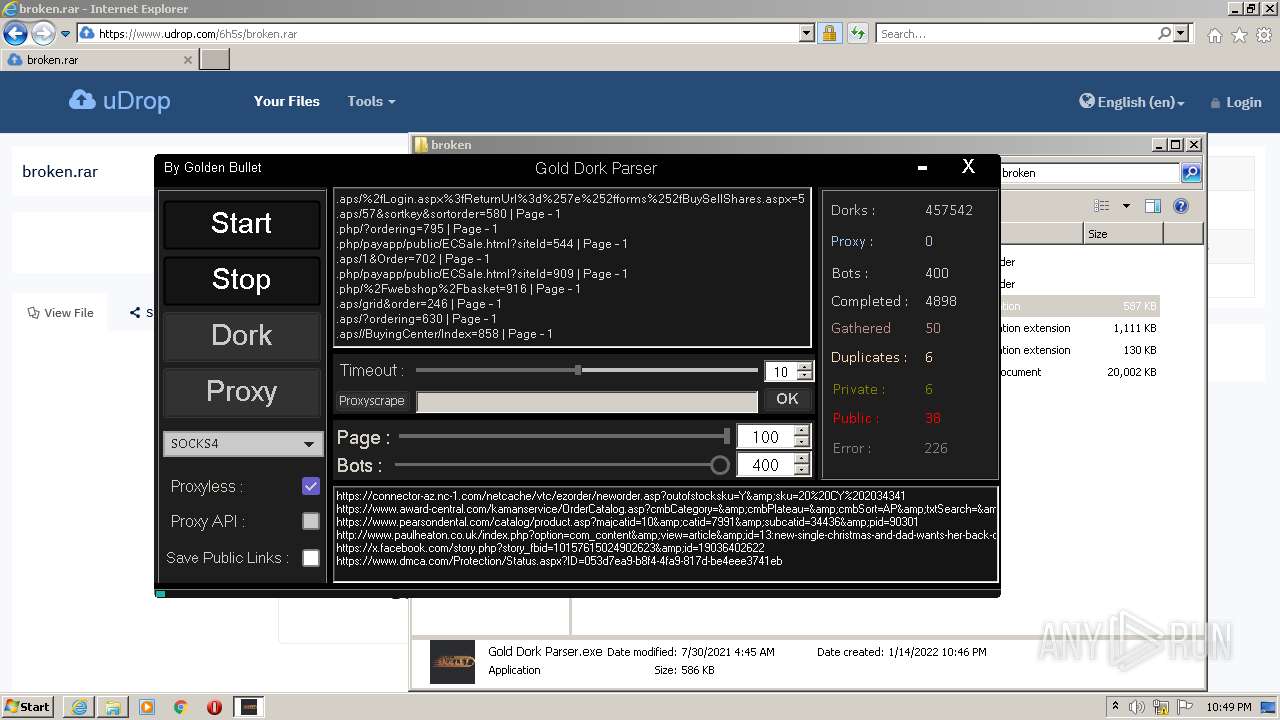
- Gold Dork Parser.exe (PID: 3168)
Loads dropped or rewritten executable
- Gold Dork Parser.exe (PID: 3168)
- SearchProtocolHost.exe (PID: 1128)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3856)
Reads the computer name
- WinRAR.exe (PID: 120)
- Gold Dork Parser.exe (PID: 3168)
Checks supported languages
- Gold Dork Parser.exe (PID: 3168)
- WinRAR.exe (PID: 120)
Reads Environment values
- Gold Dork Parser.exe (PID: 3168)
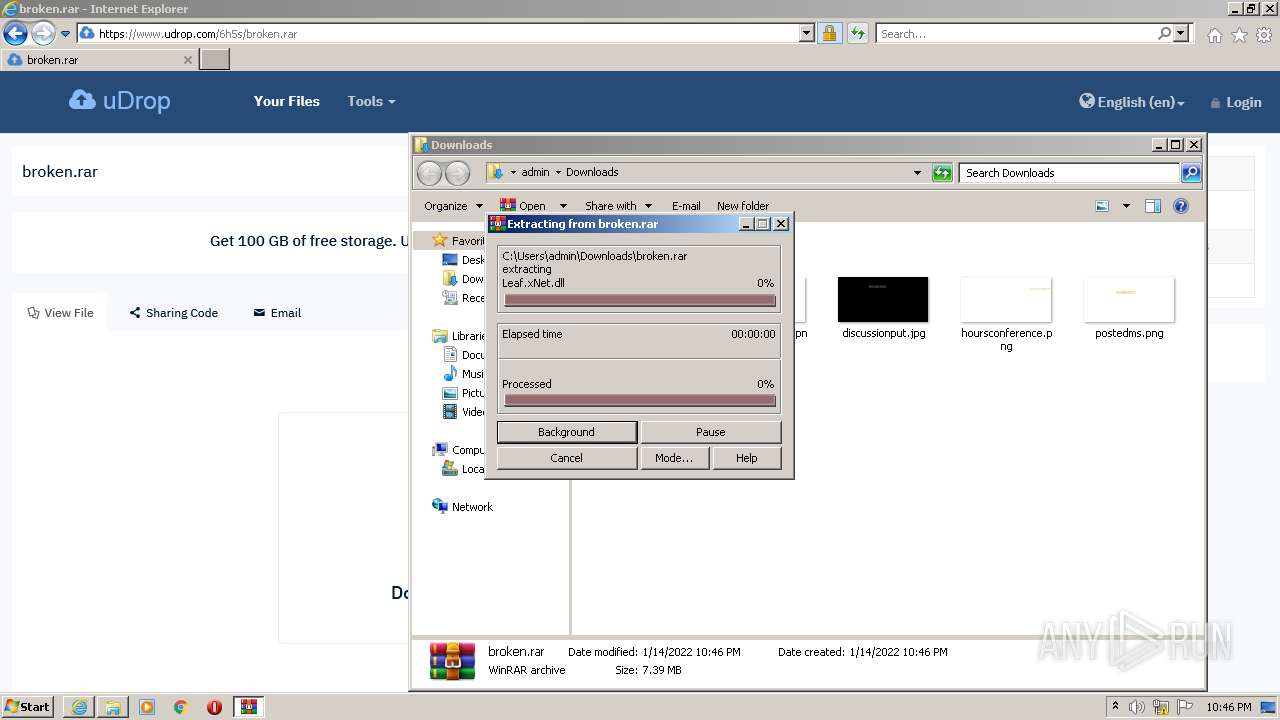
Drops a file with a compile date too recent
- WinRAR.exe (PID: 120)
Drops a file that was compiled in debug mode
- WinRAR.exe (PID: 120)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 120)
INFO
Checks supported languages
- iexplore.exe (PID: 3276)
- iexplore.exe (PID: 3856)
- SearchProtocolHost.exe (PID: 1128)
Reads the computer name
- iexplore.exe (PID: 3276)
- iexplore.exe (PID: 3856)
- SearchProtocolHost.exe (PID: 1128)
Changes internet zones settings
- iexplore.exe (PID: 3276)
Creates files in the user directory
- iexplore.exe (PID: 3856)
- iexplore.exe (PID: 3276)
Checks Windows Trust Settings
- iexplore.exe (PID: 3856)
- iexplore.exe (PID: 3276)
Reads internet explorer settings
- iexplore.exe (PID: 3856)
Reads settings of System Certificates
- iexplore.exe (PID: 3276)
- iexplore.exe (PID: 3856)
- Gold Dork Parser.exe (PID: 3168)
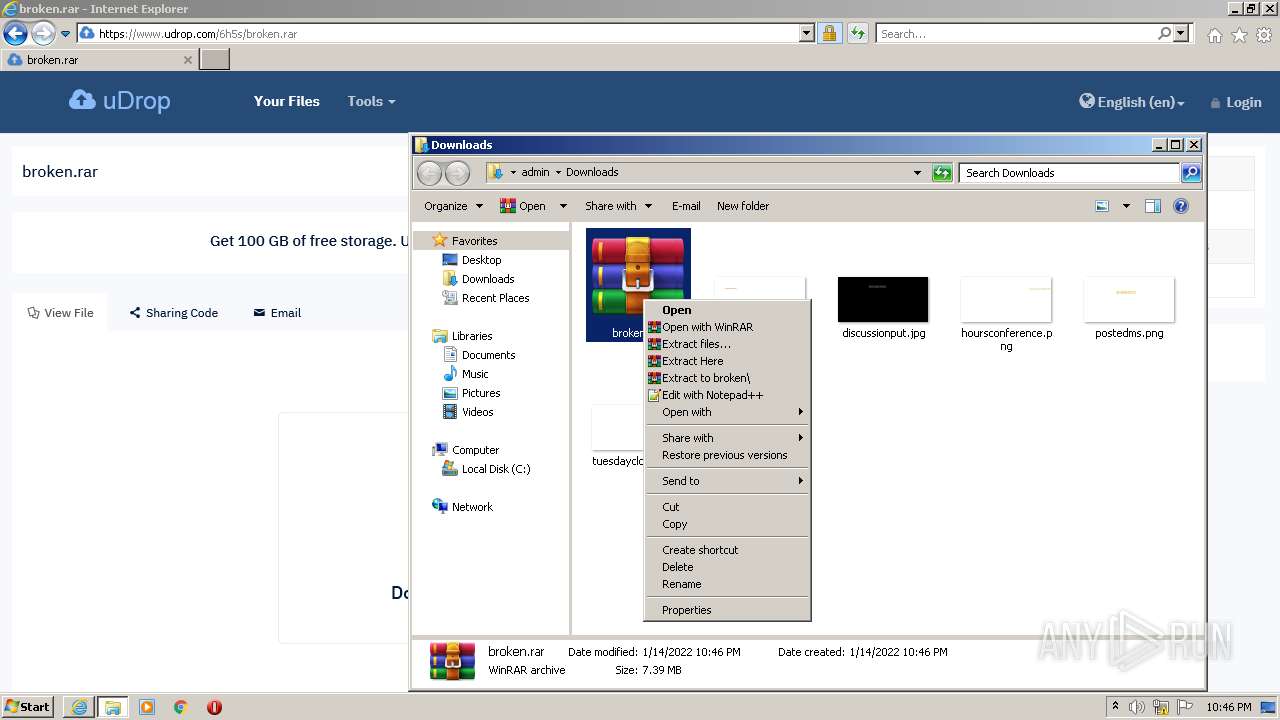
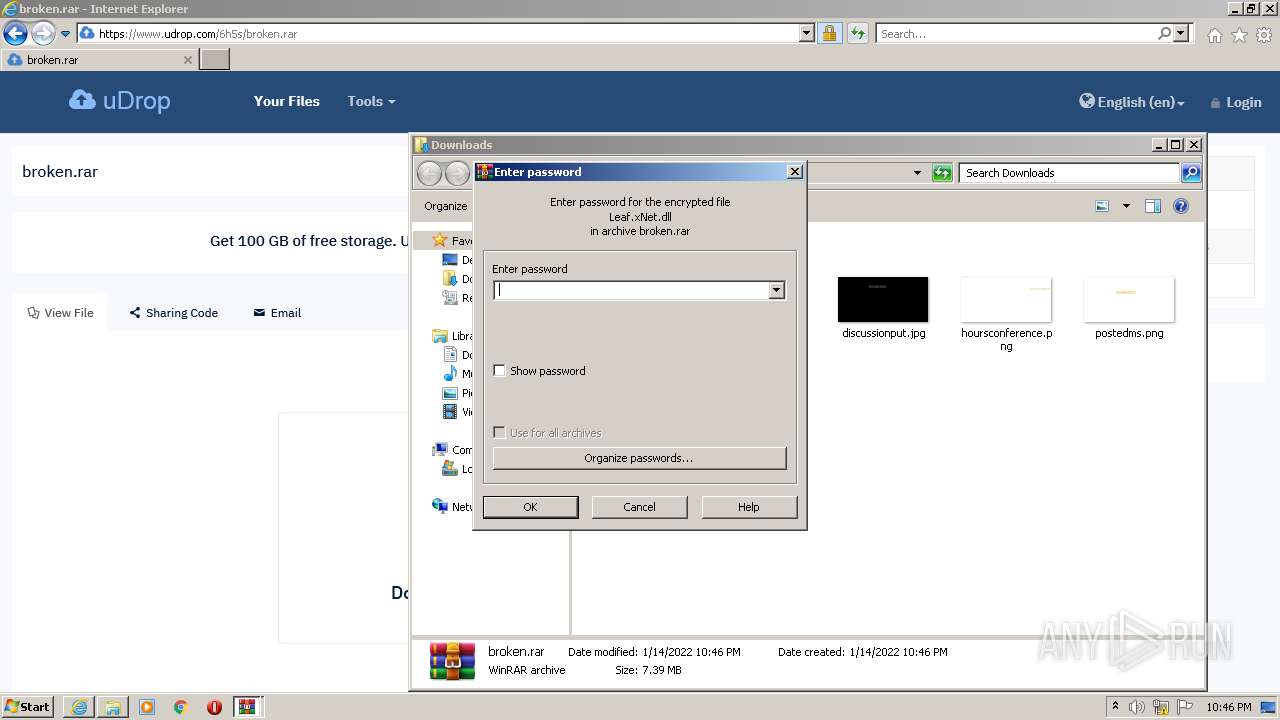
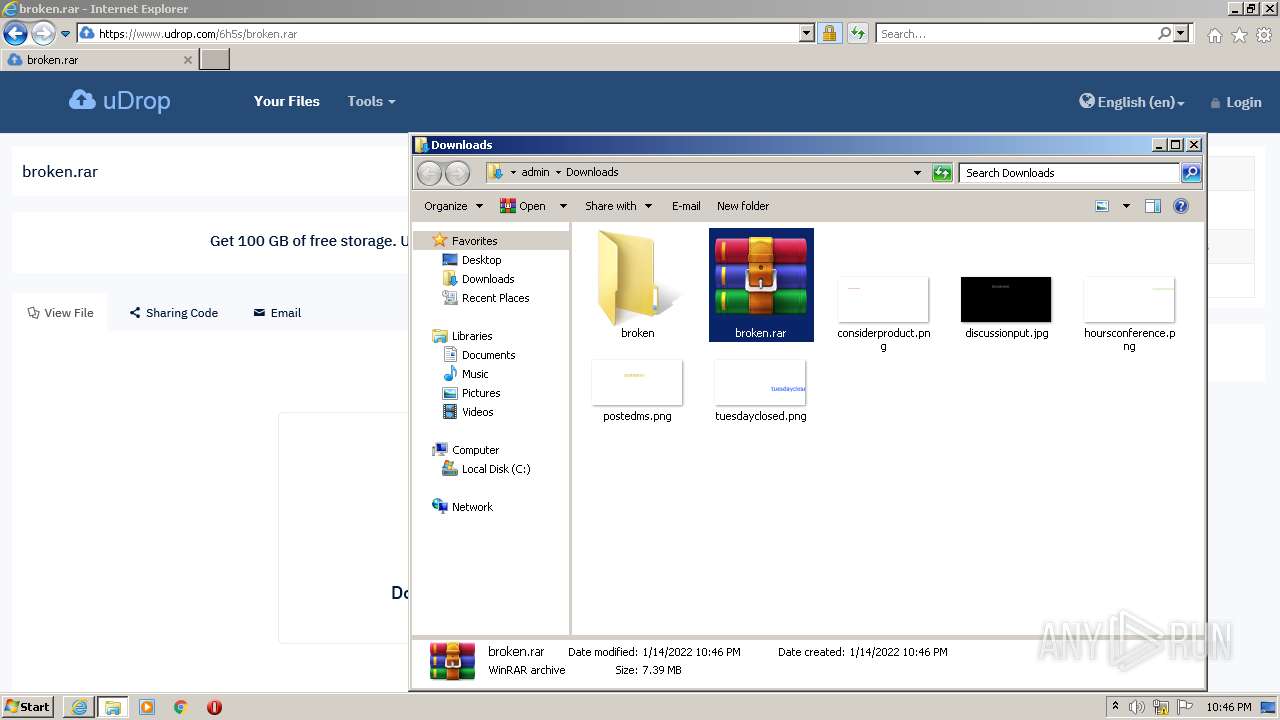
Manual execution by user
- WinRAR.exe (PID: 120)
- Gold Dork Parser.exe (PID: 3168)
Changes settings of System certificates
- iexplore.exe (PID: 3276)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3276)
Application launched itself
- iexplore.exe (PID: 3276)
Modifies the phishing filter of IE
- iexplore.exe (PID: 3276)
Drops Coronavirus (possible) decoy
- Gold Dork Parser.exe (PID: 3168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
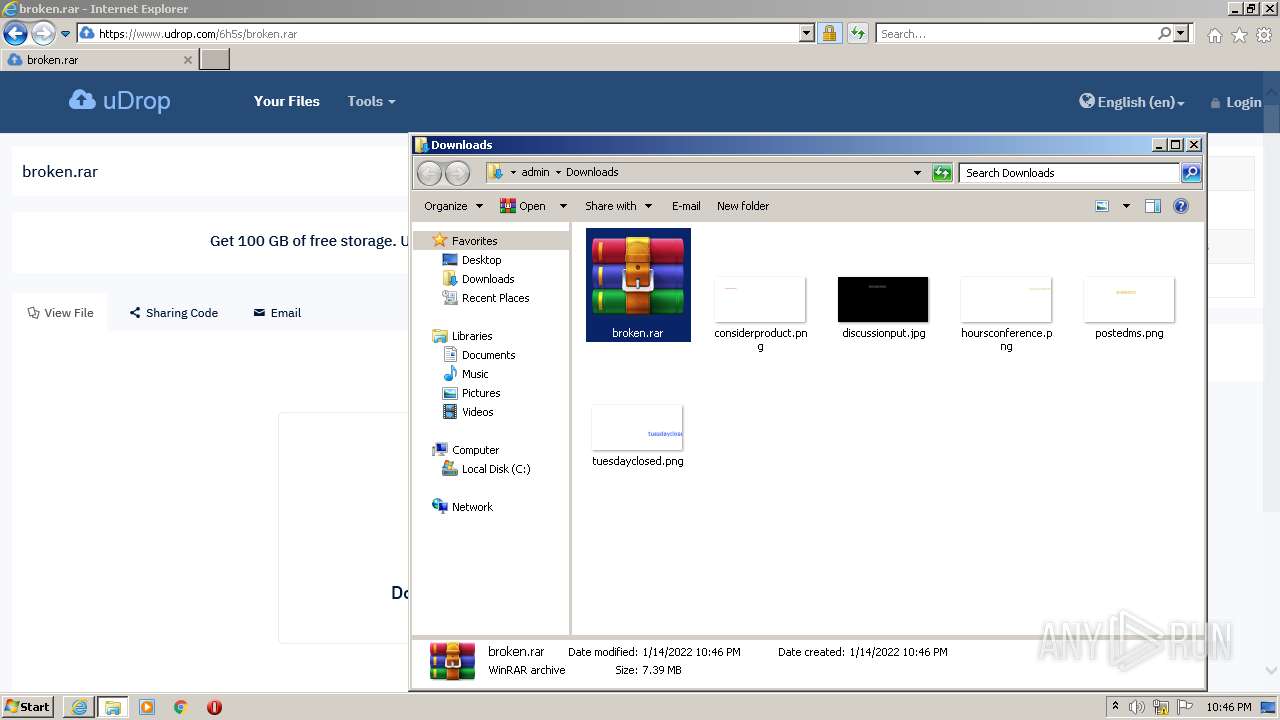
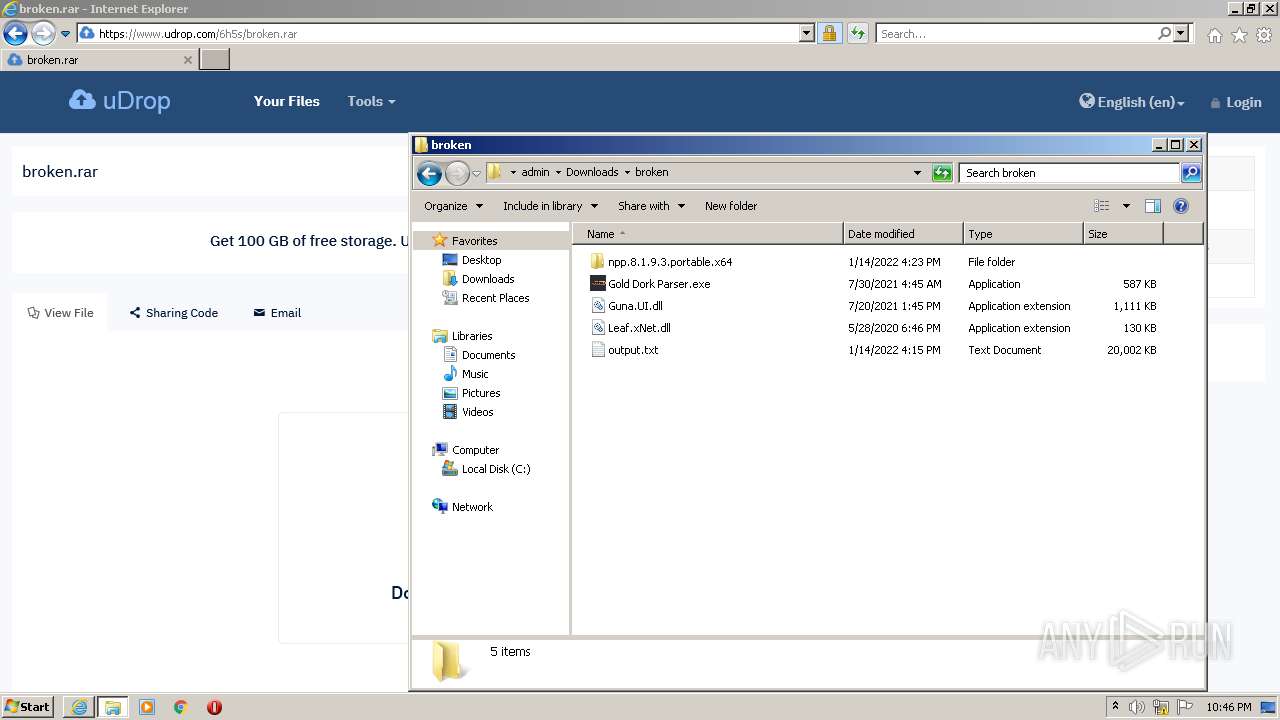
| 120 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\broken.rar" C:\Users\admin\Downloads\broken\ | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 1128 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe4_ Global\UsGthrCtrlFltPipeMssGthrPipe4 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7601.24542 (win7sp1_ldr_escrow.191209-2211) Modules
| |||||||||||||||
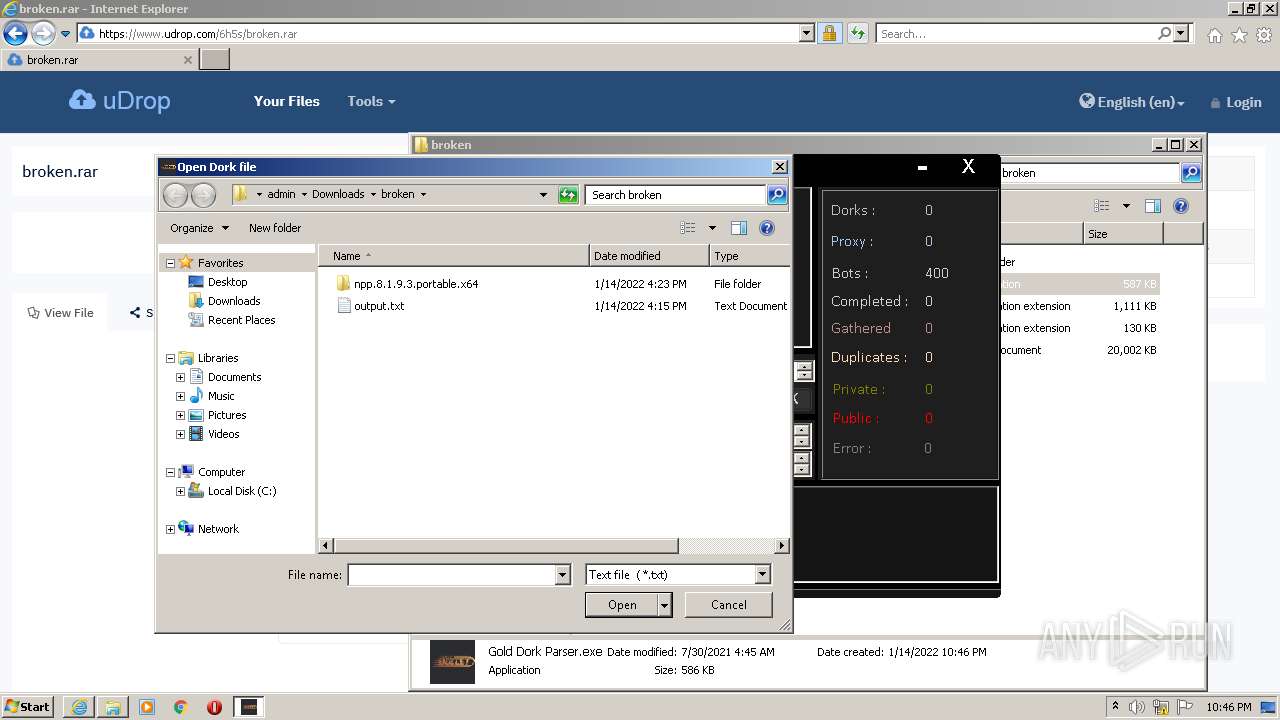
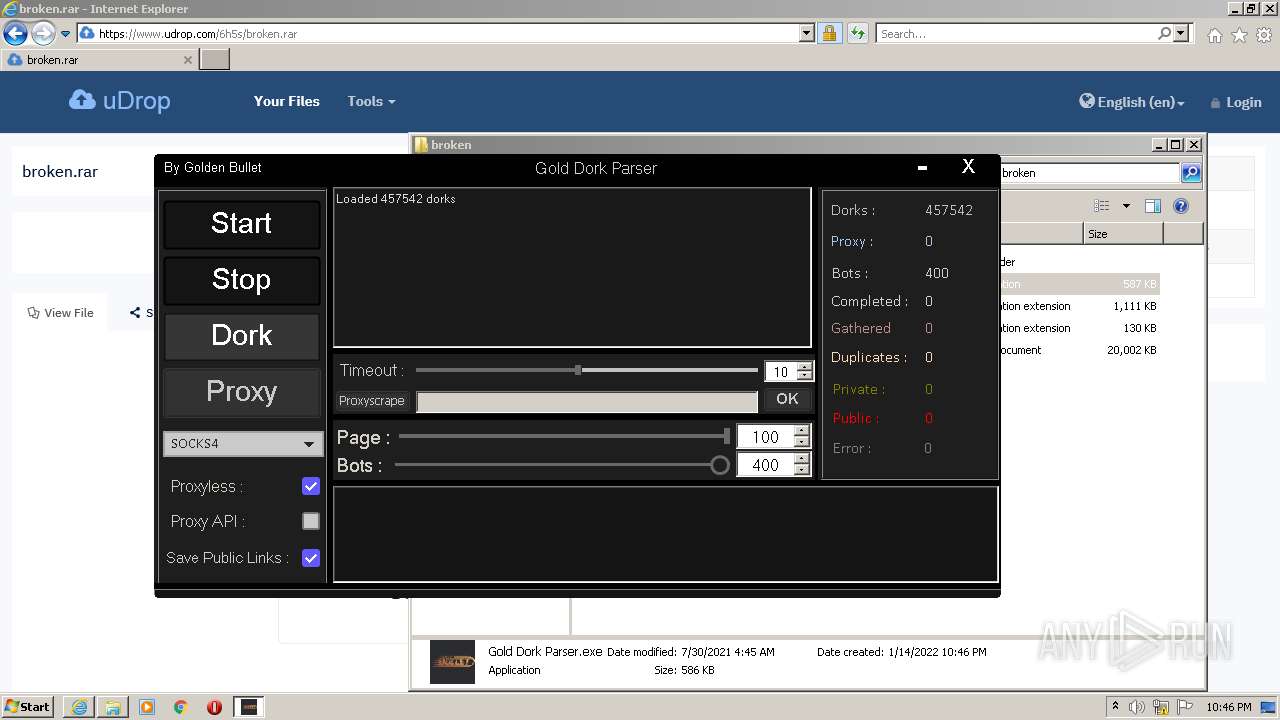
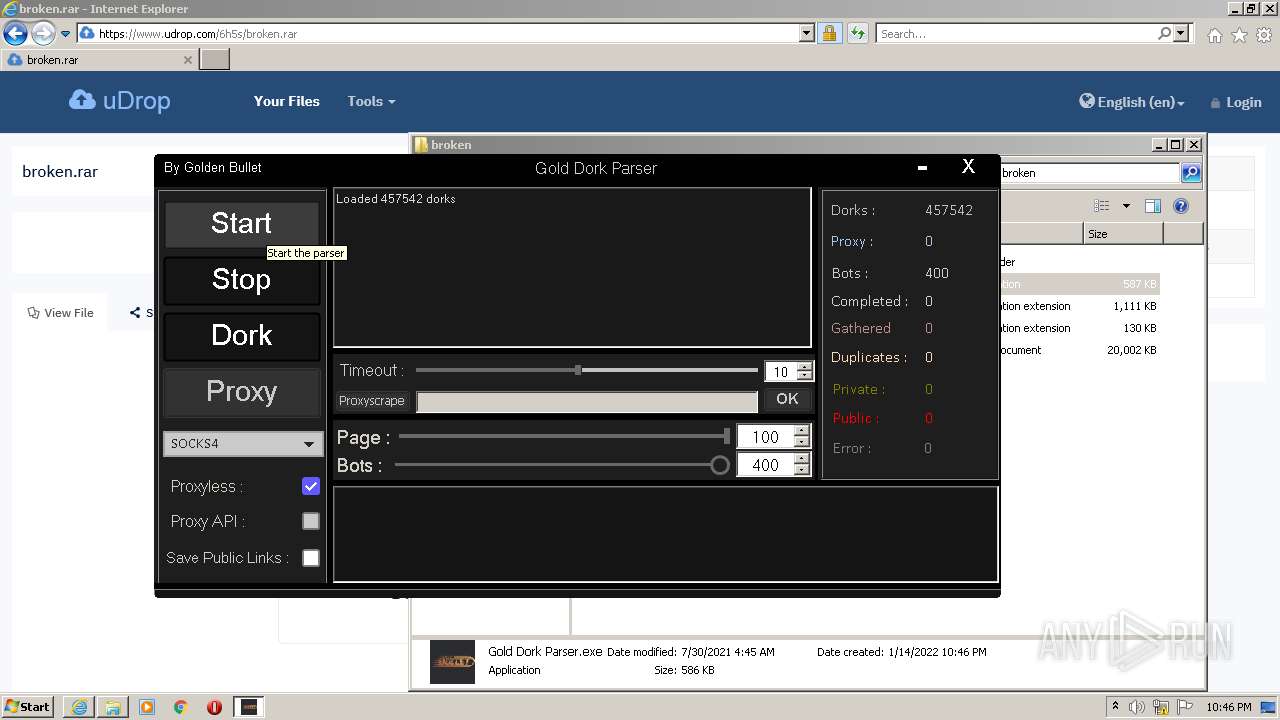
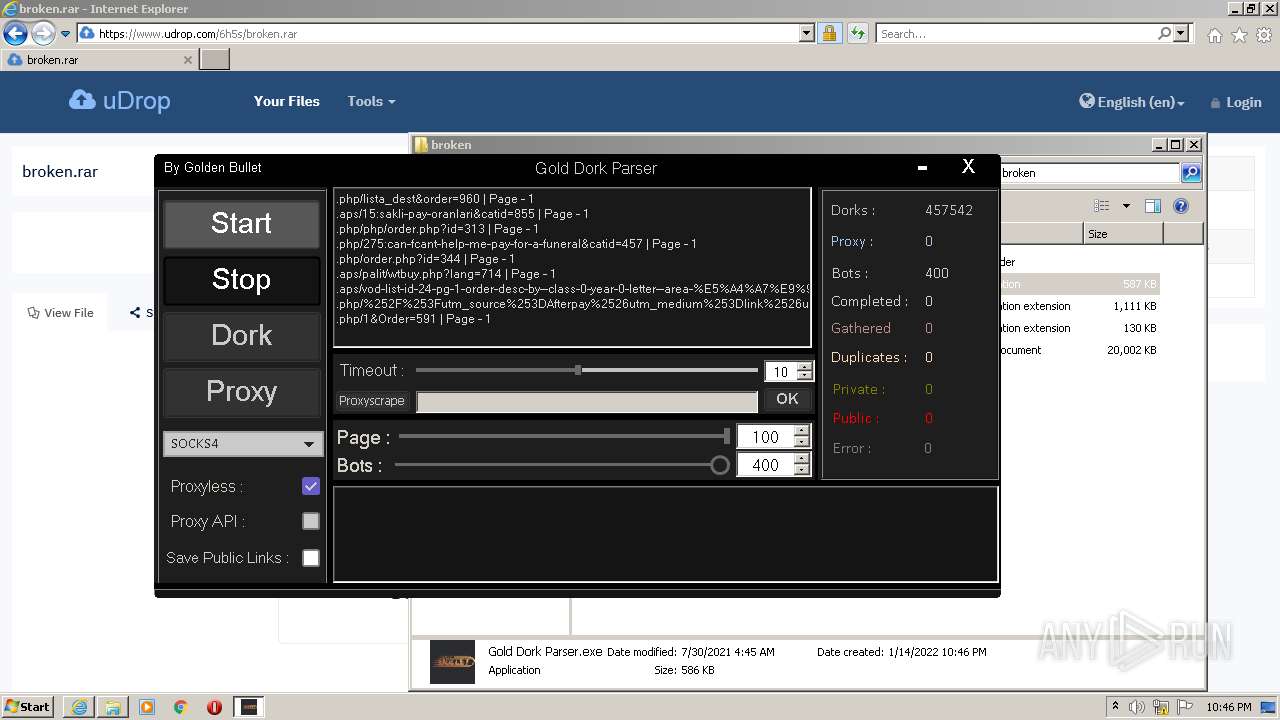
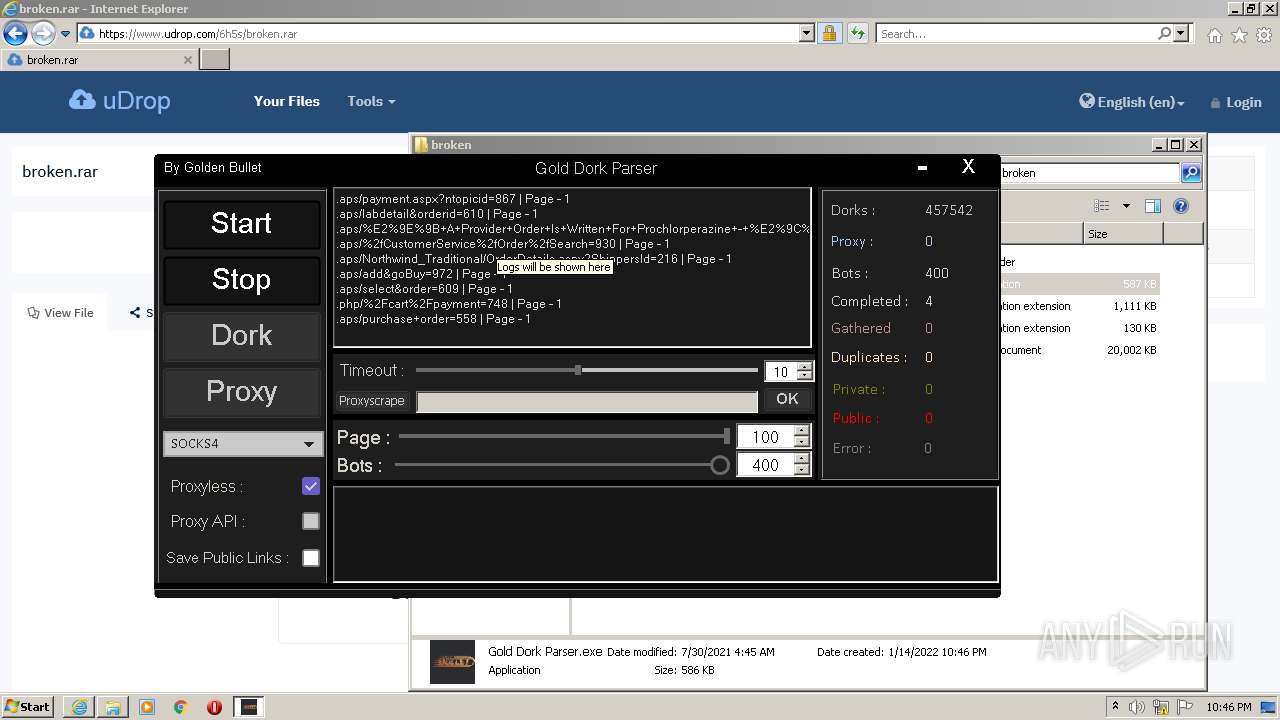
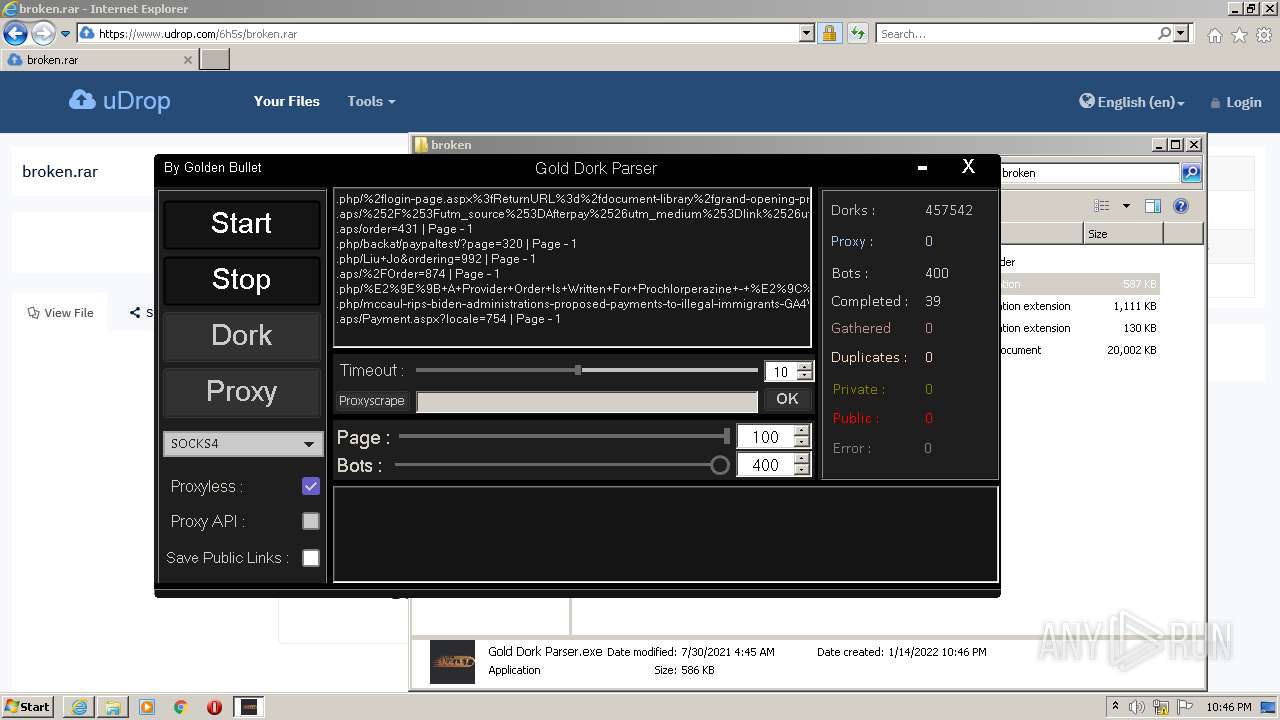
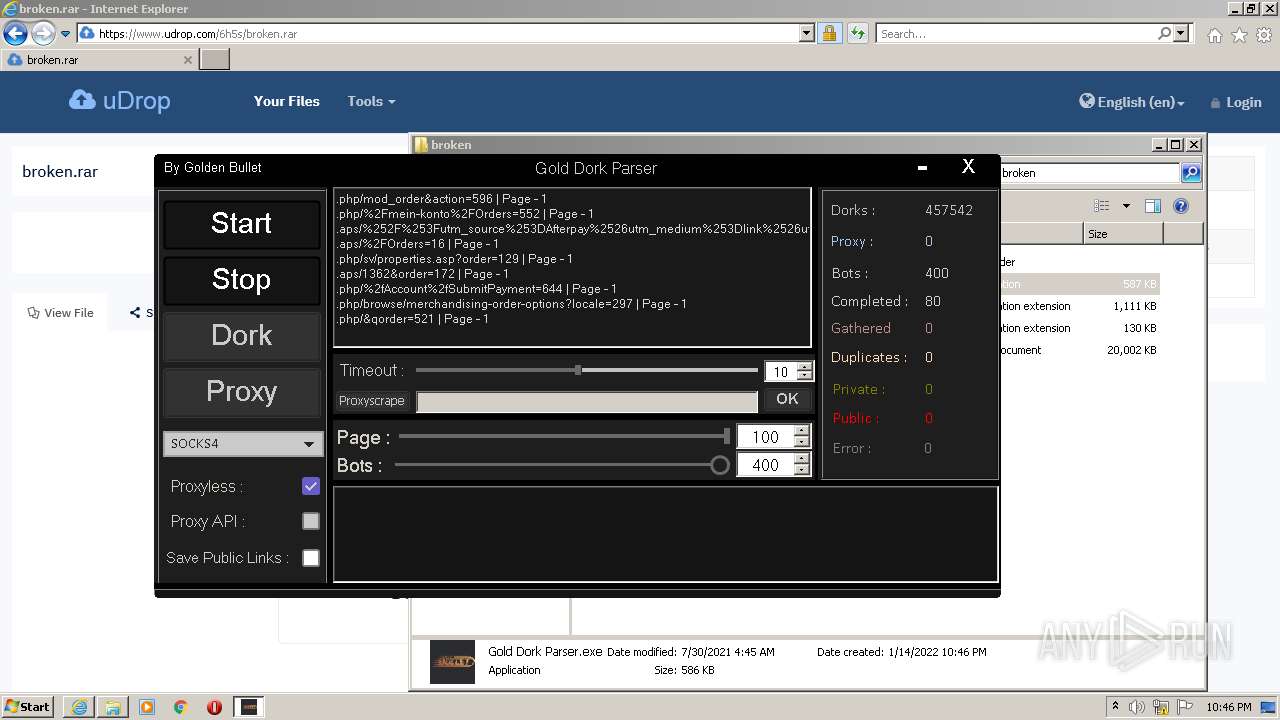
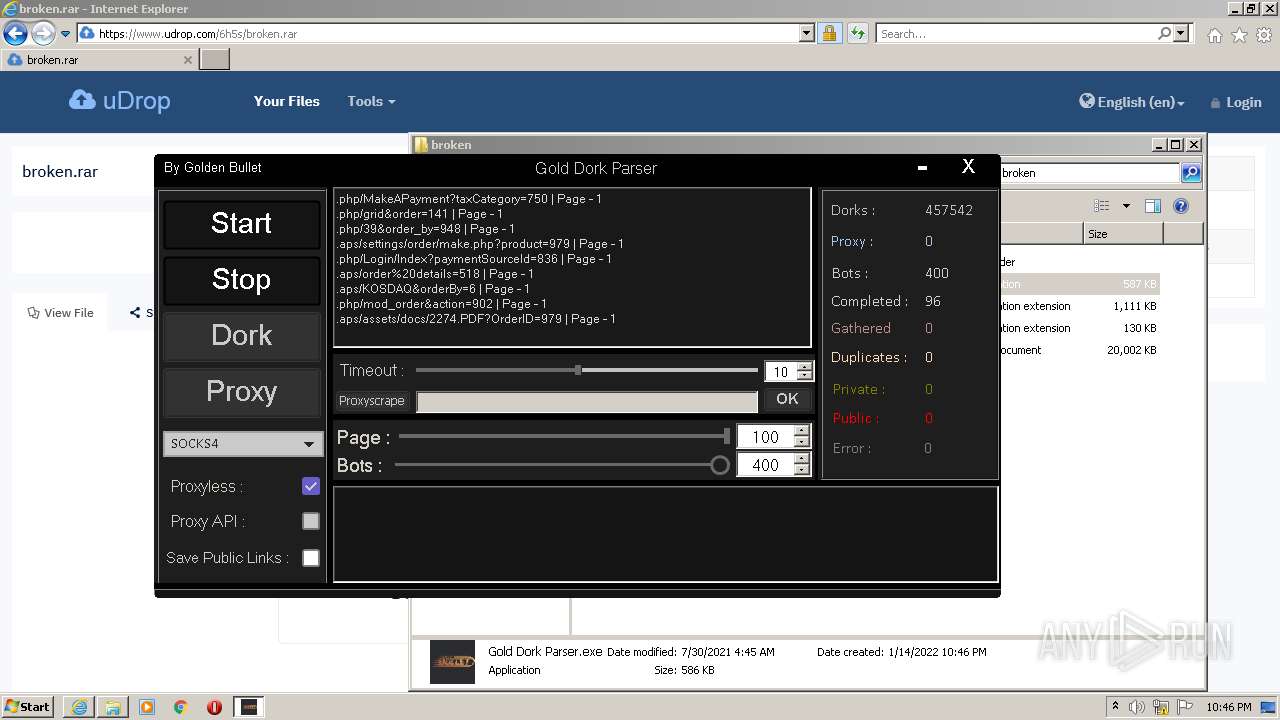
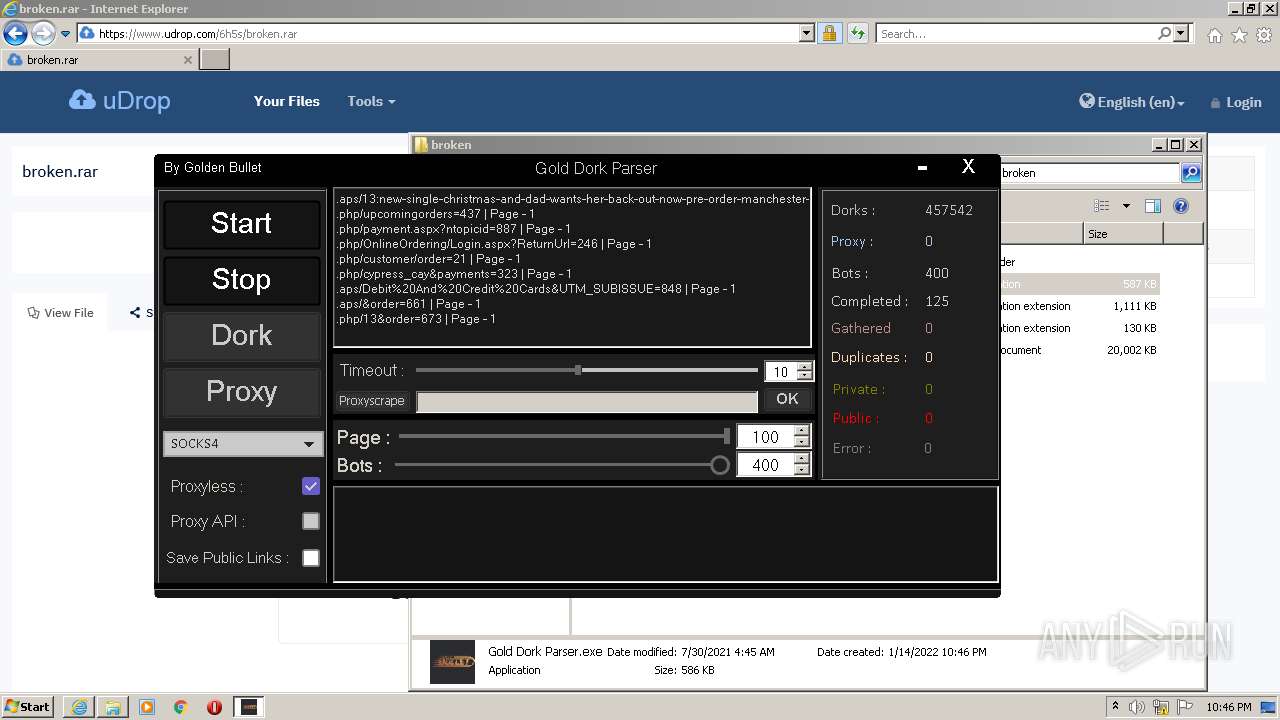
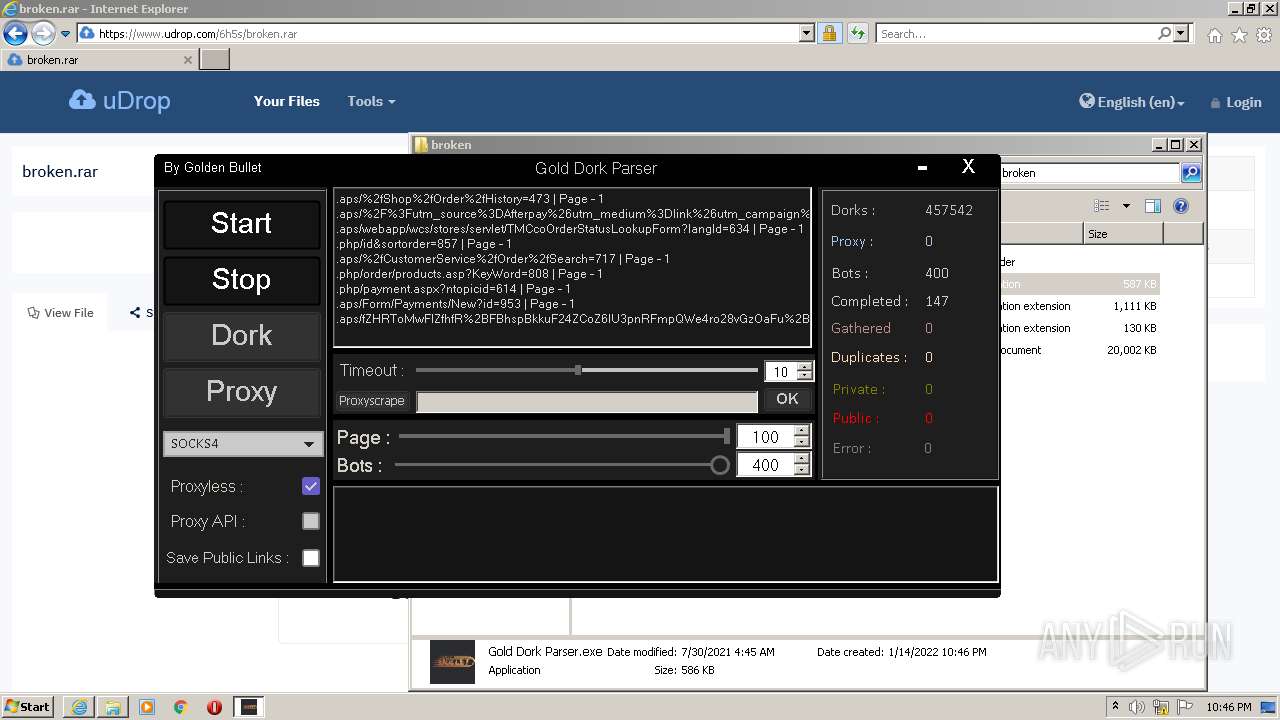
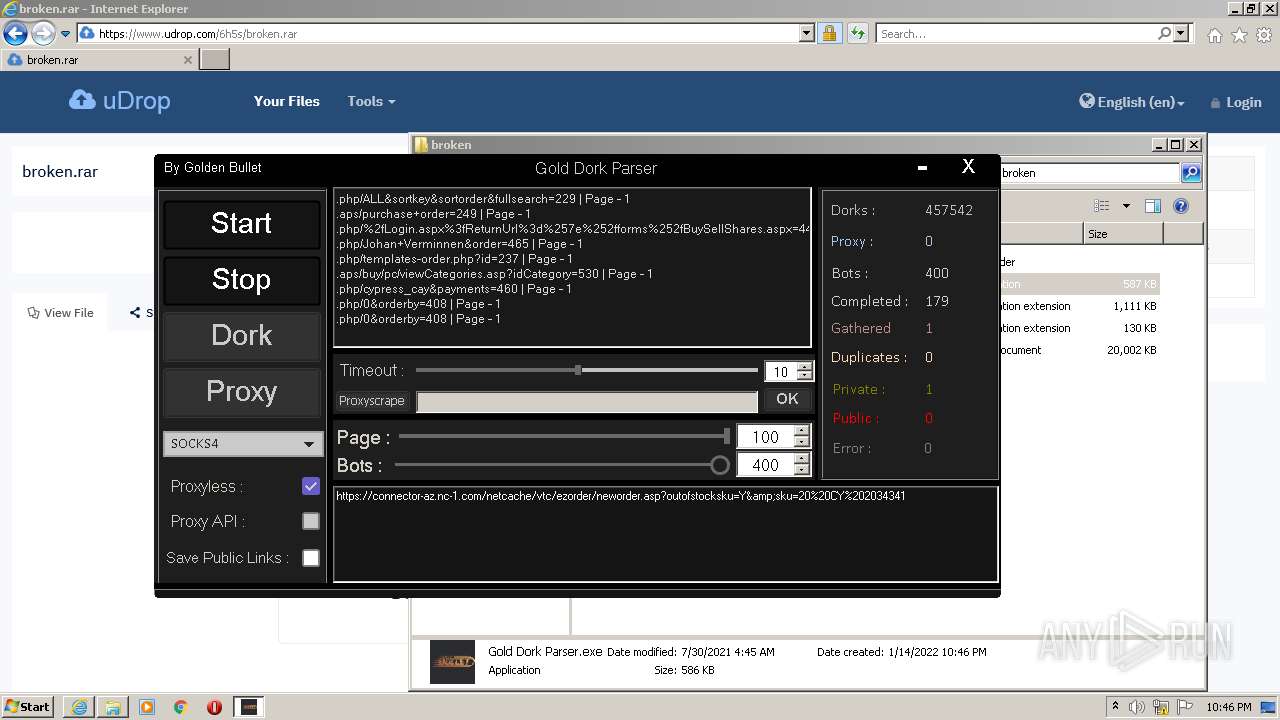
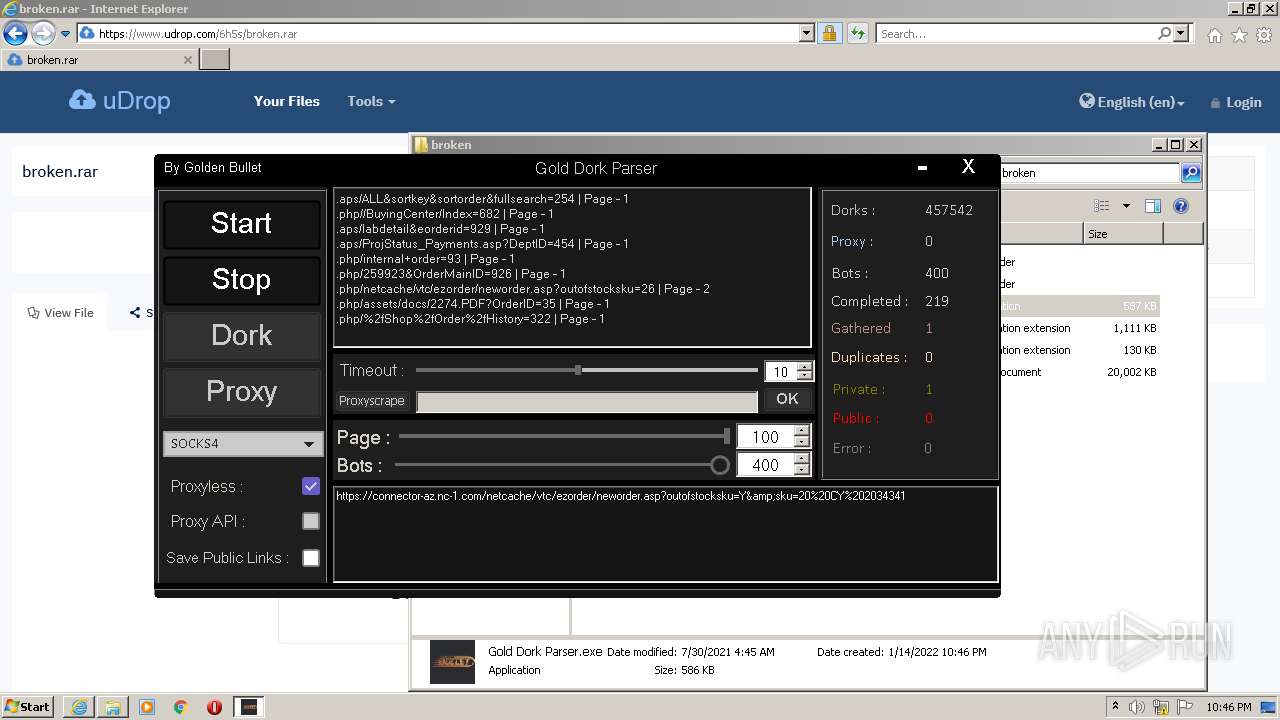
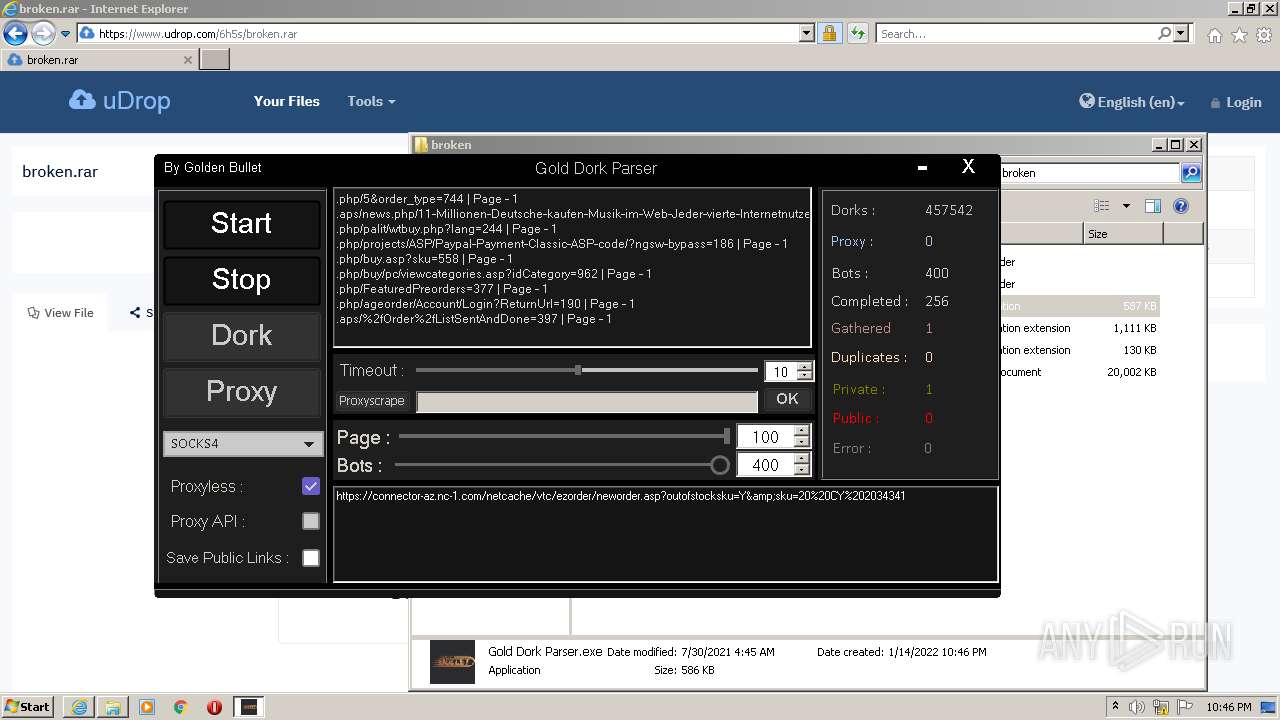
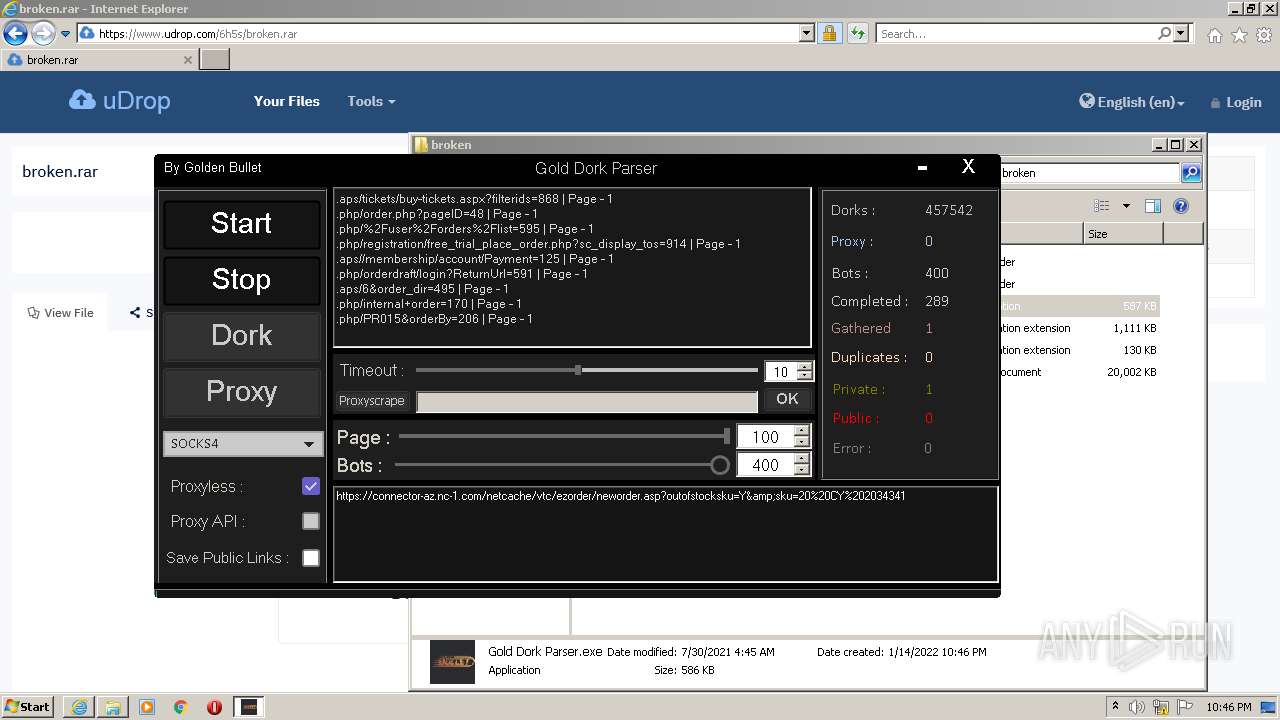
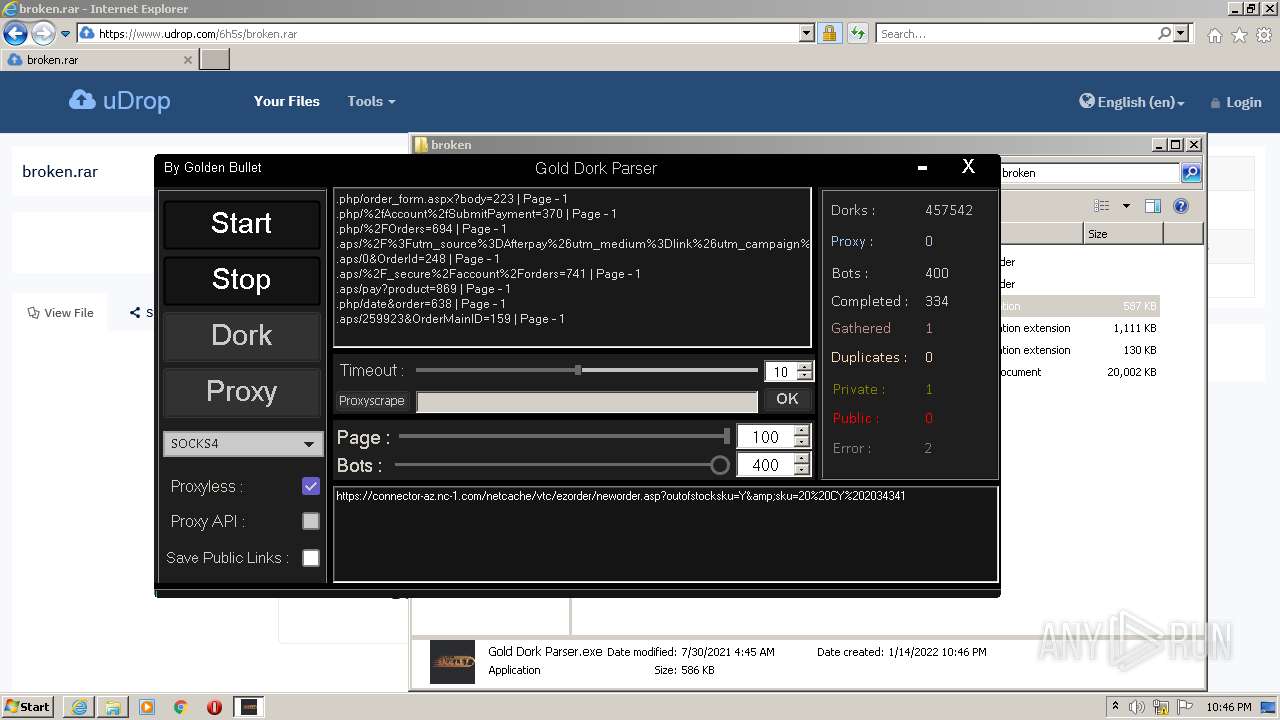
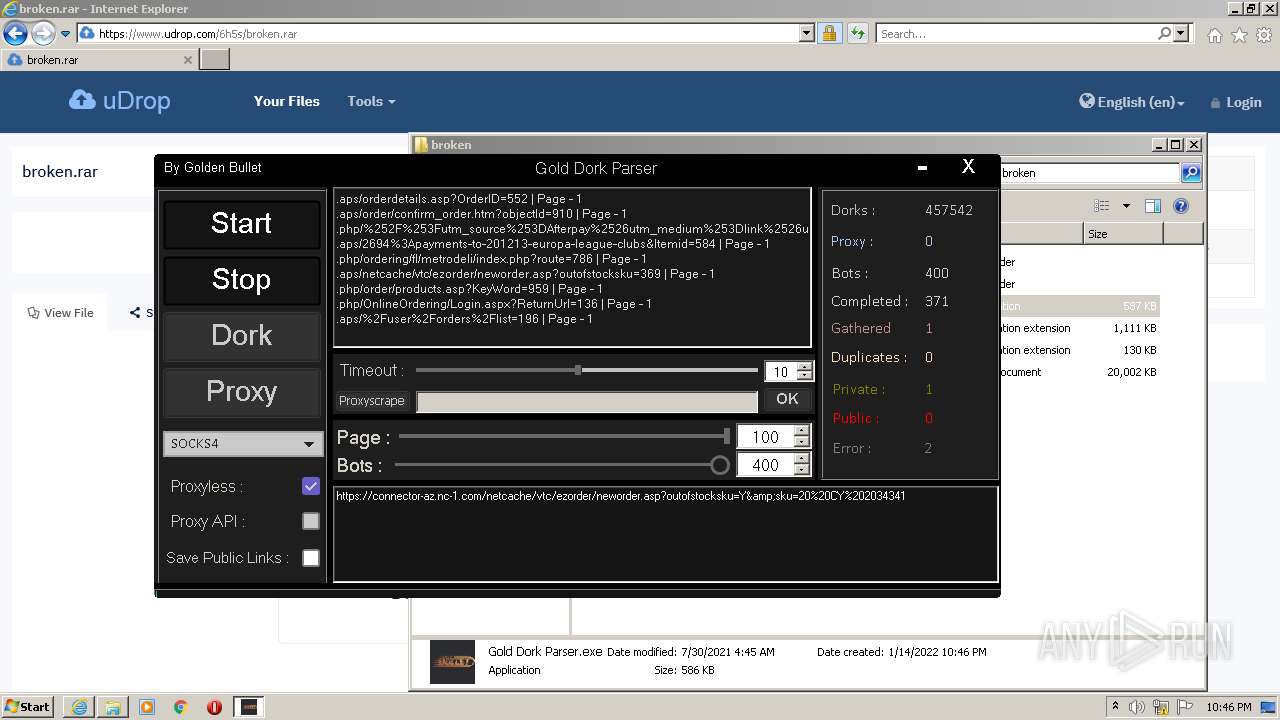
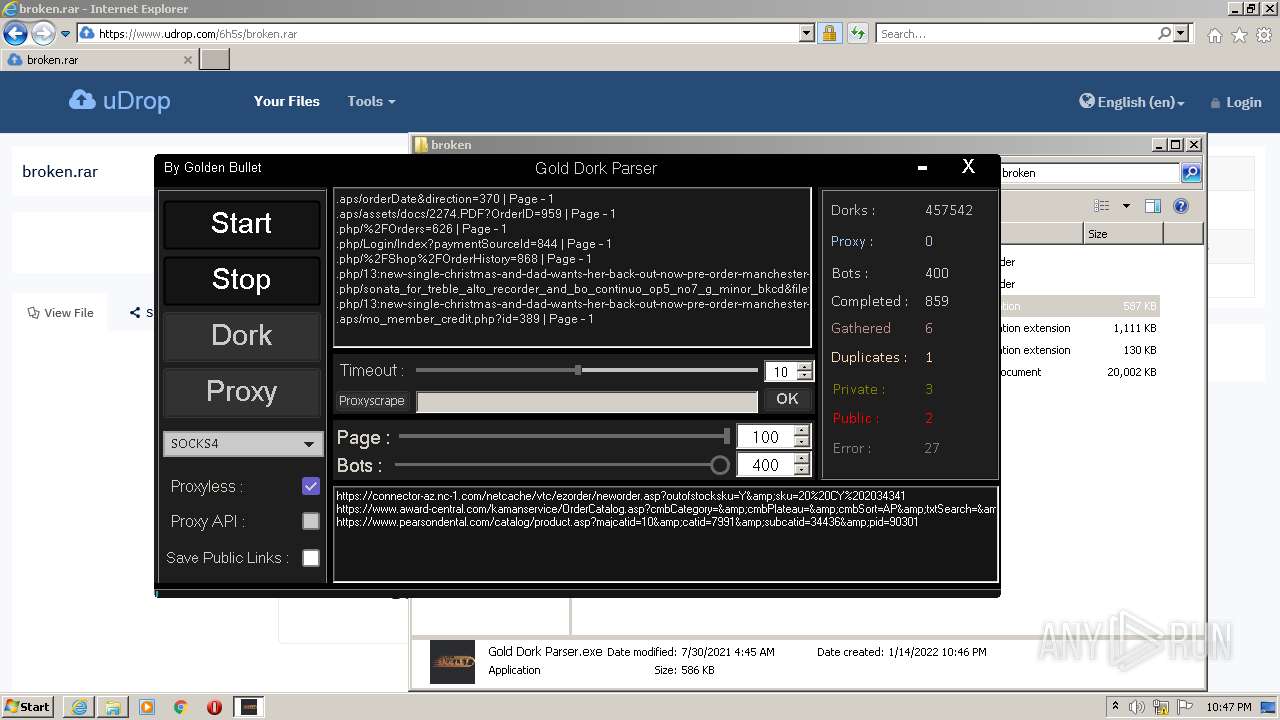
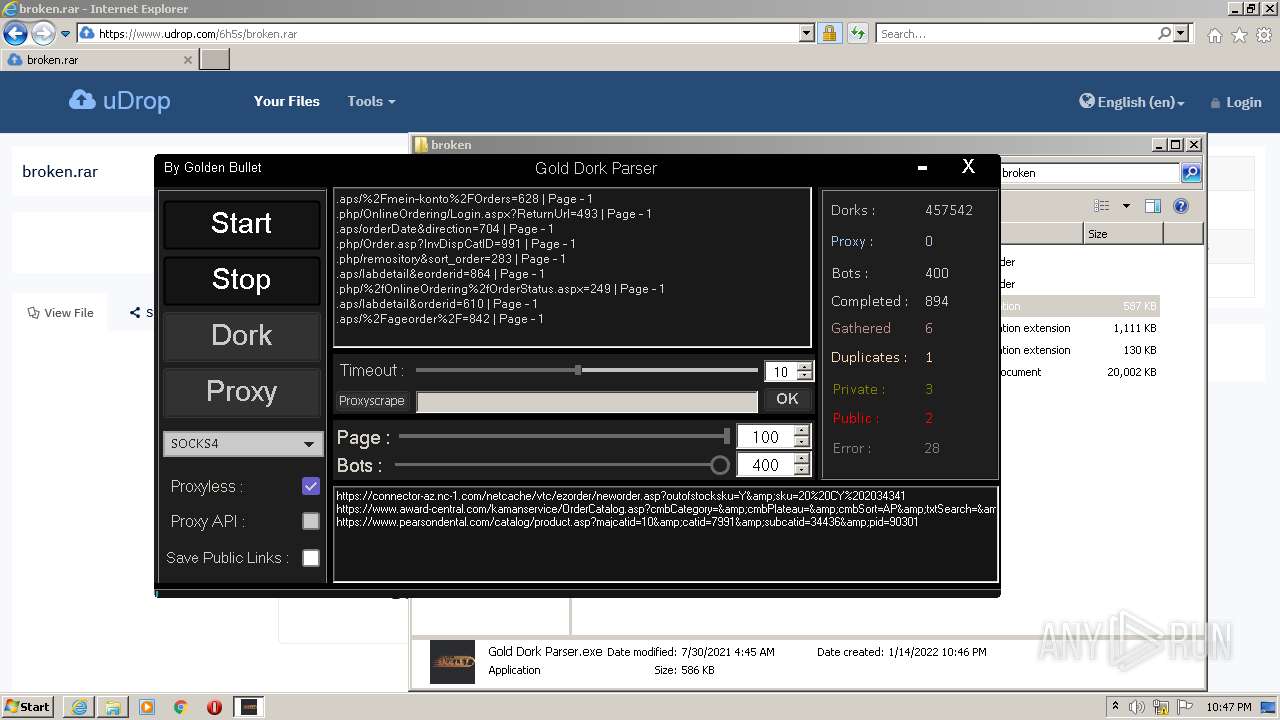
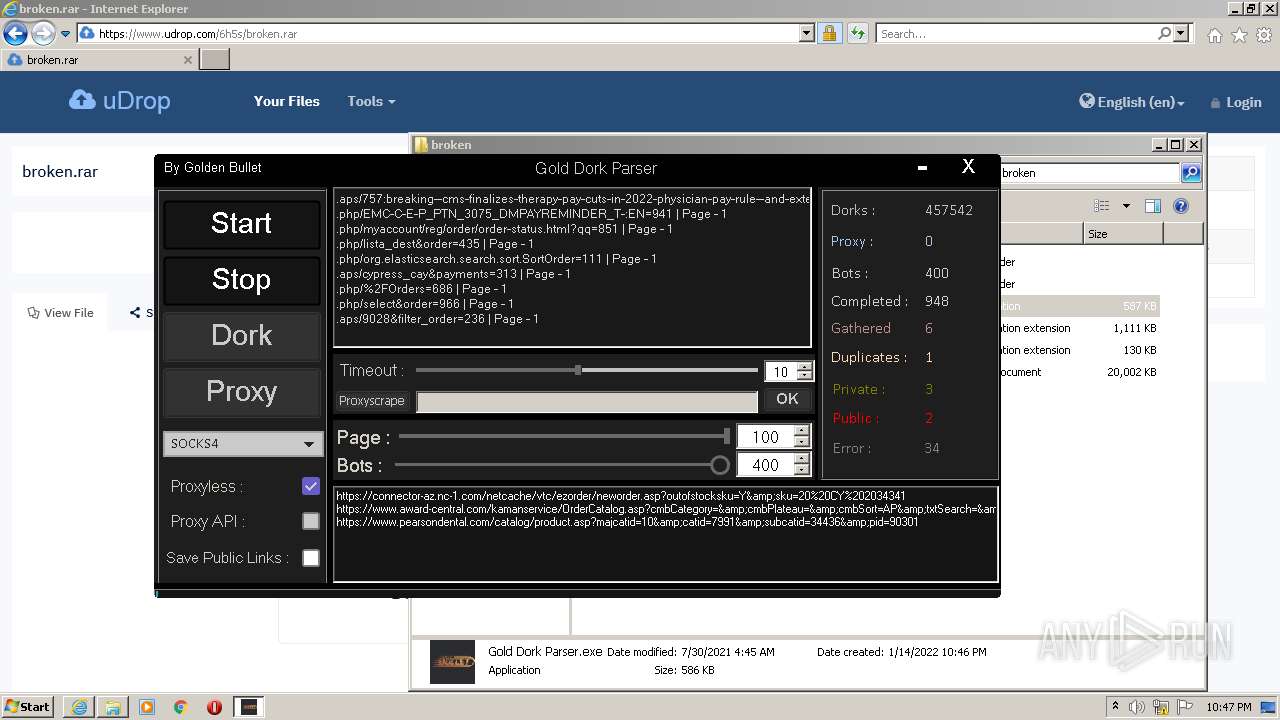
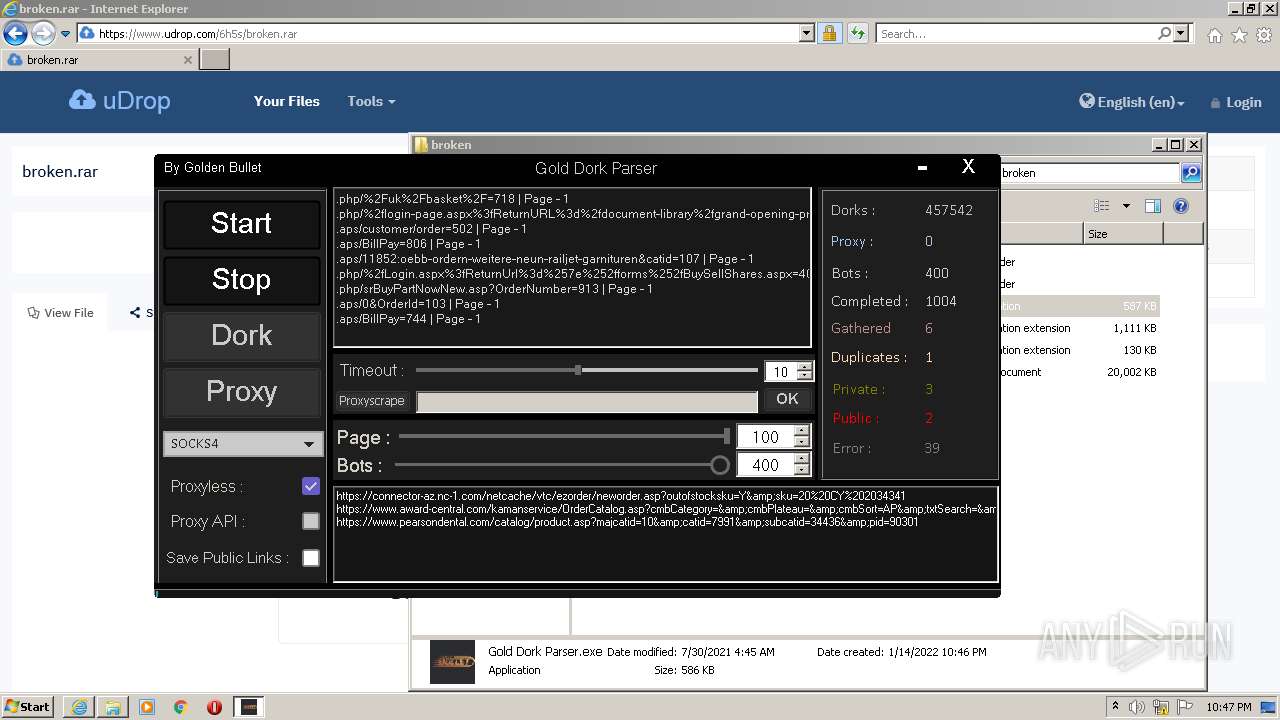
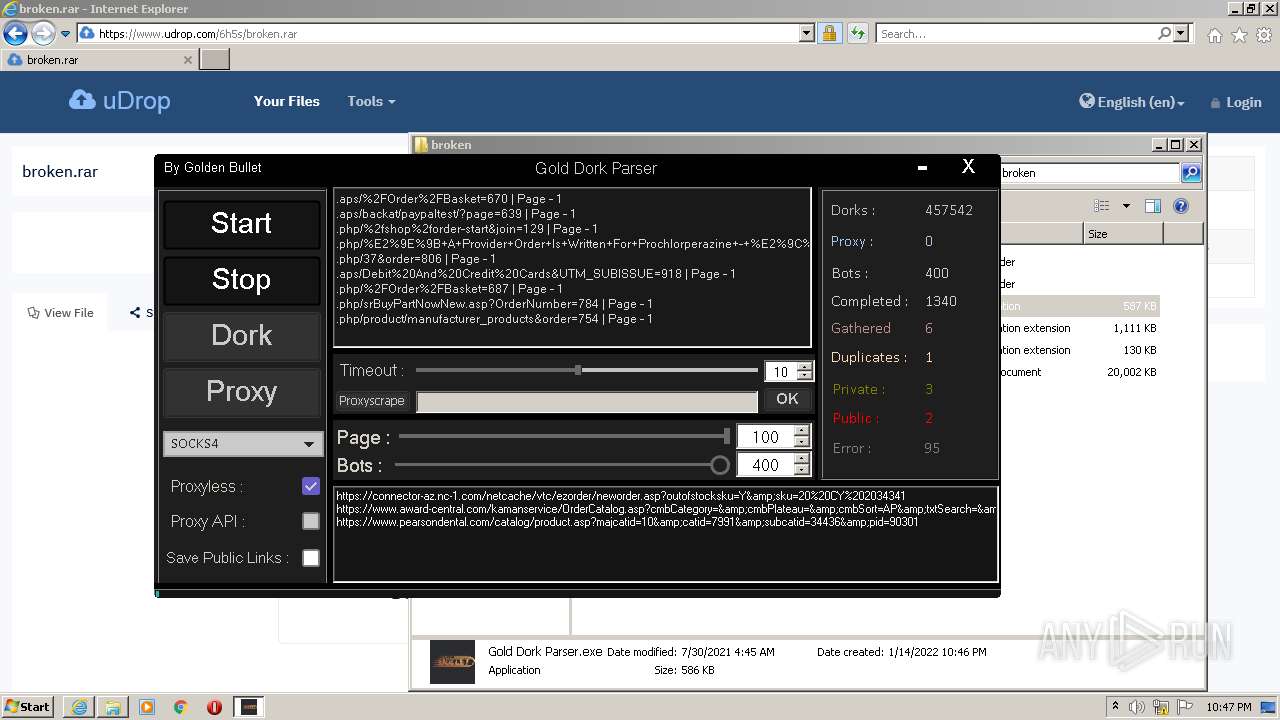
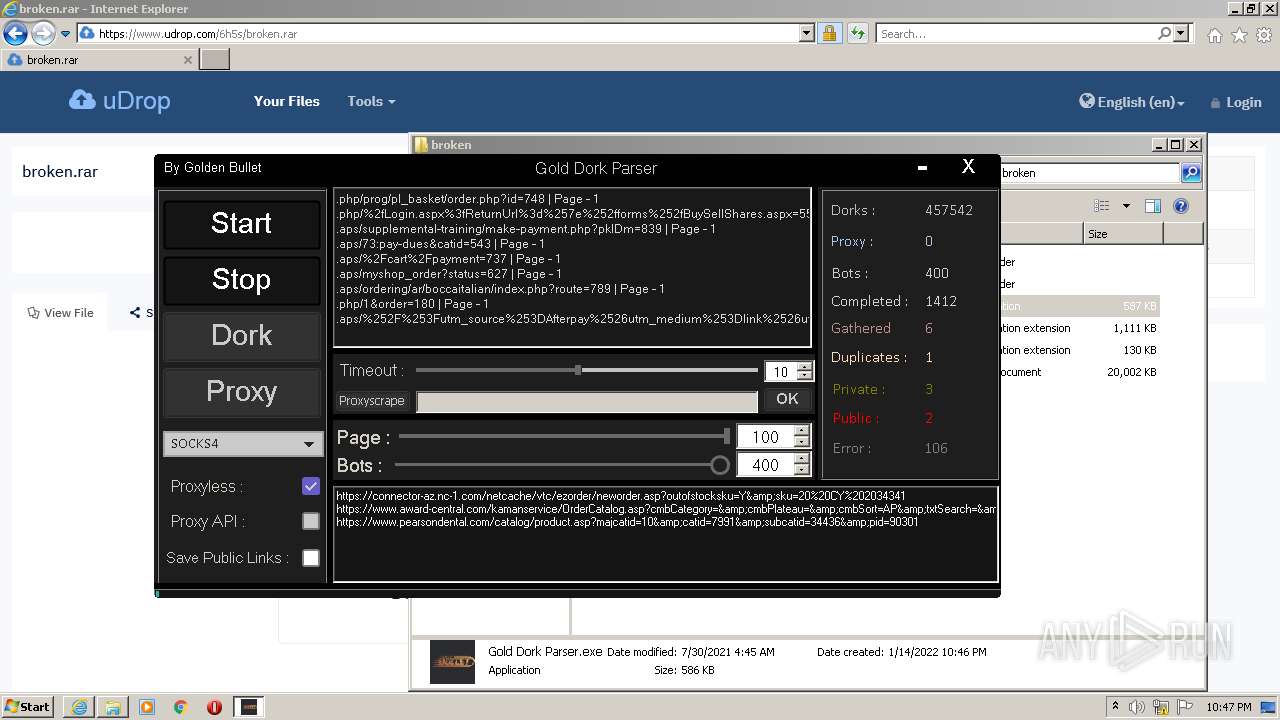
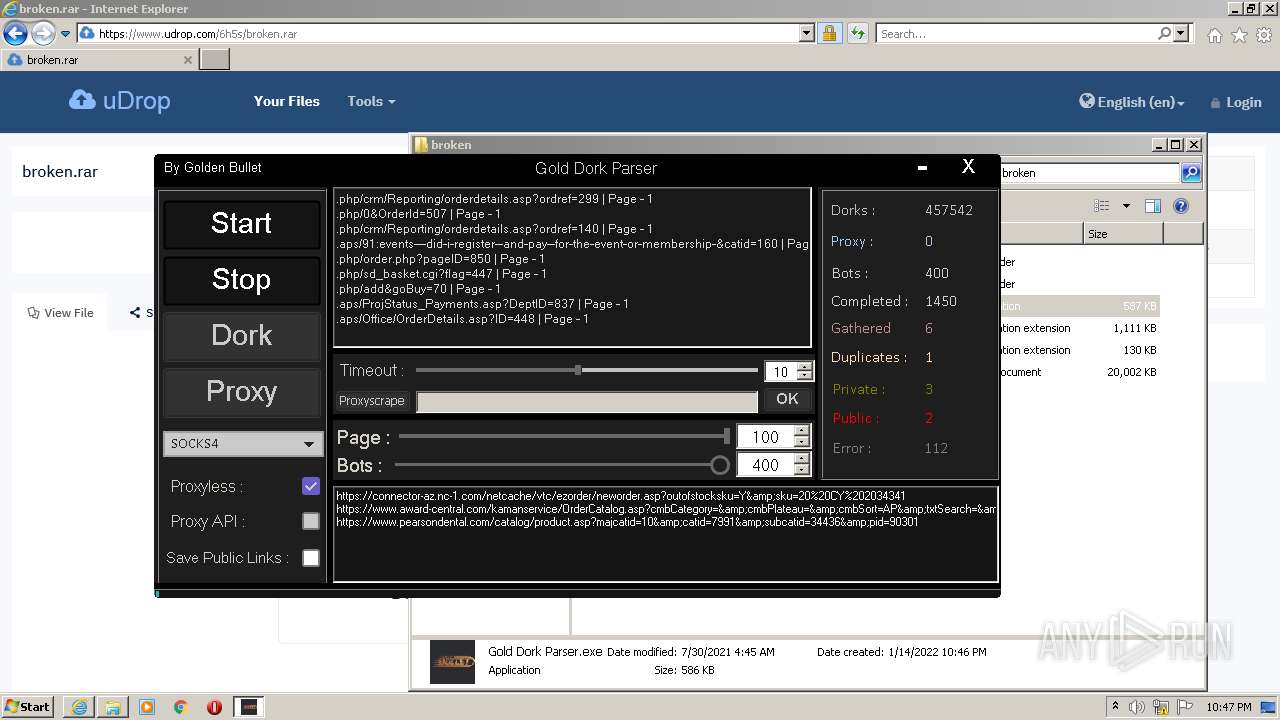
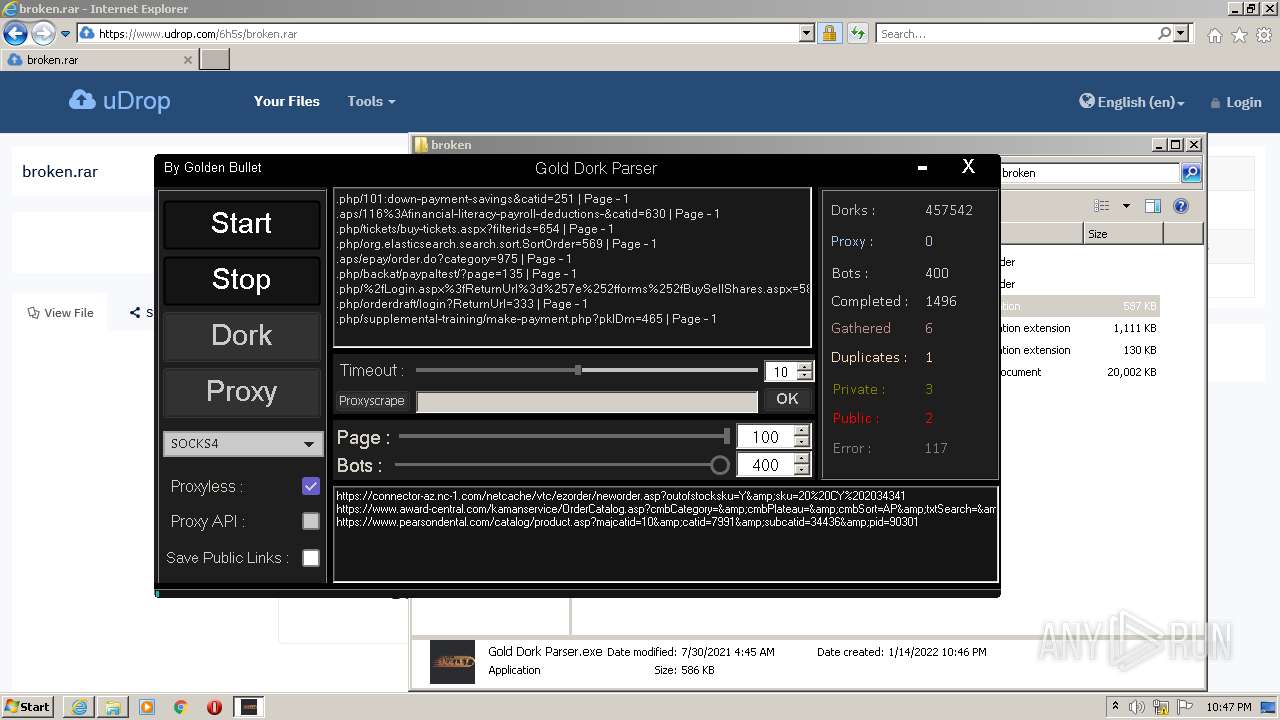
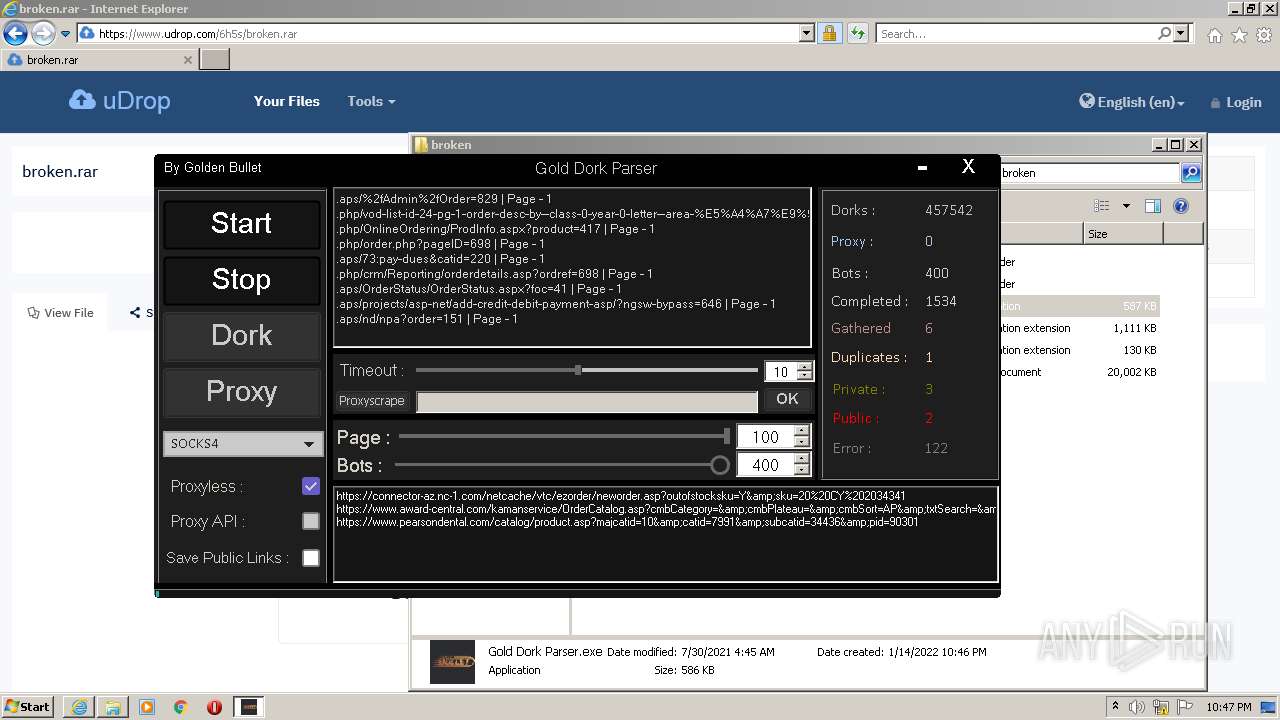
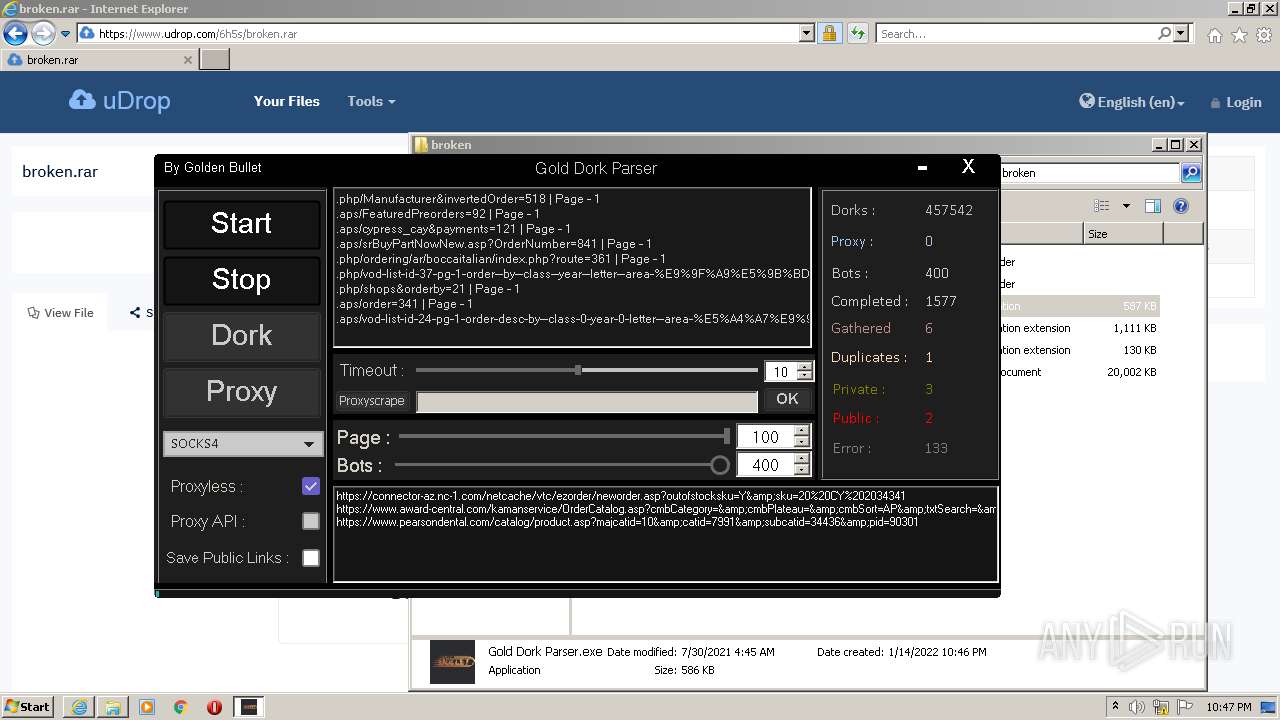
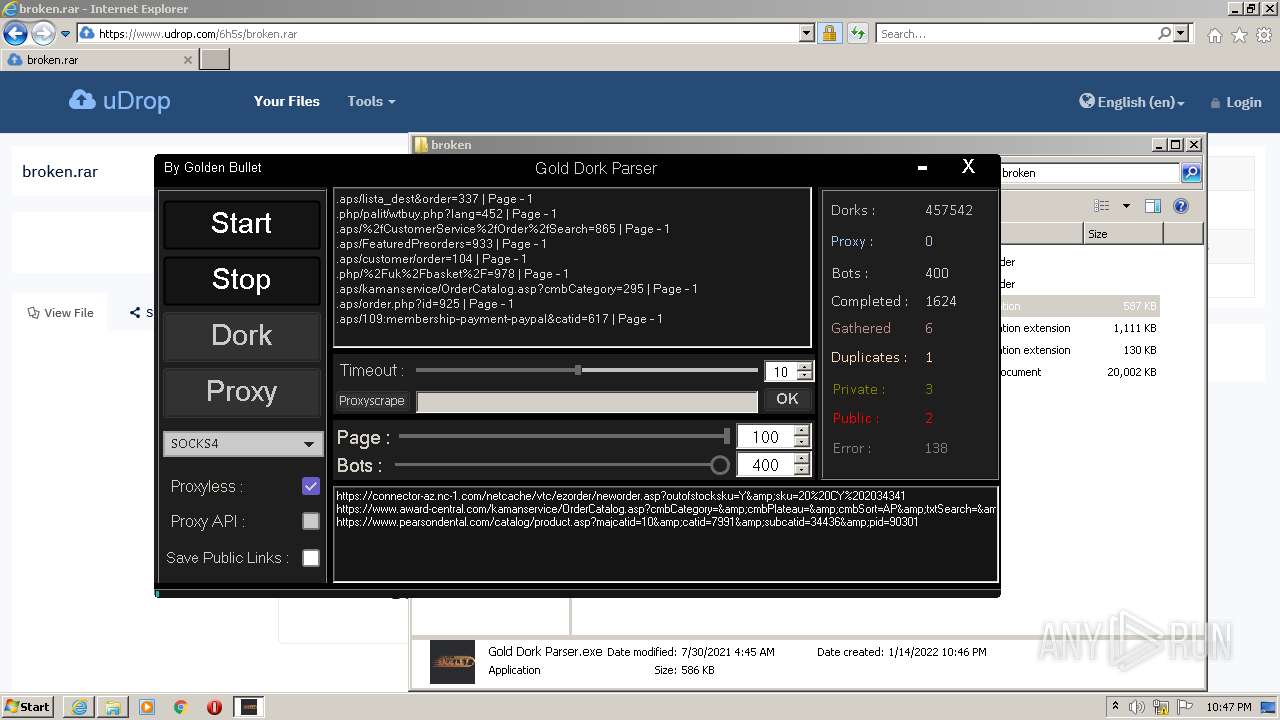
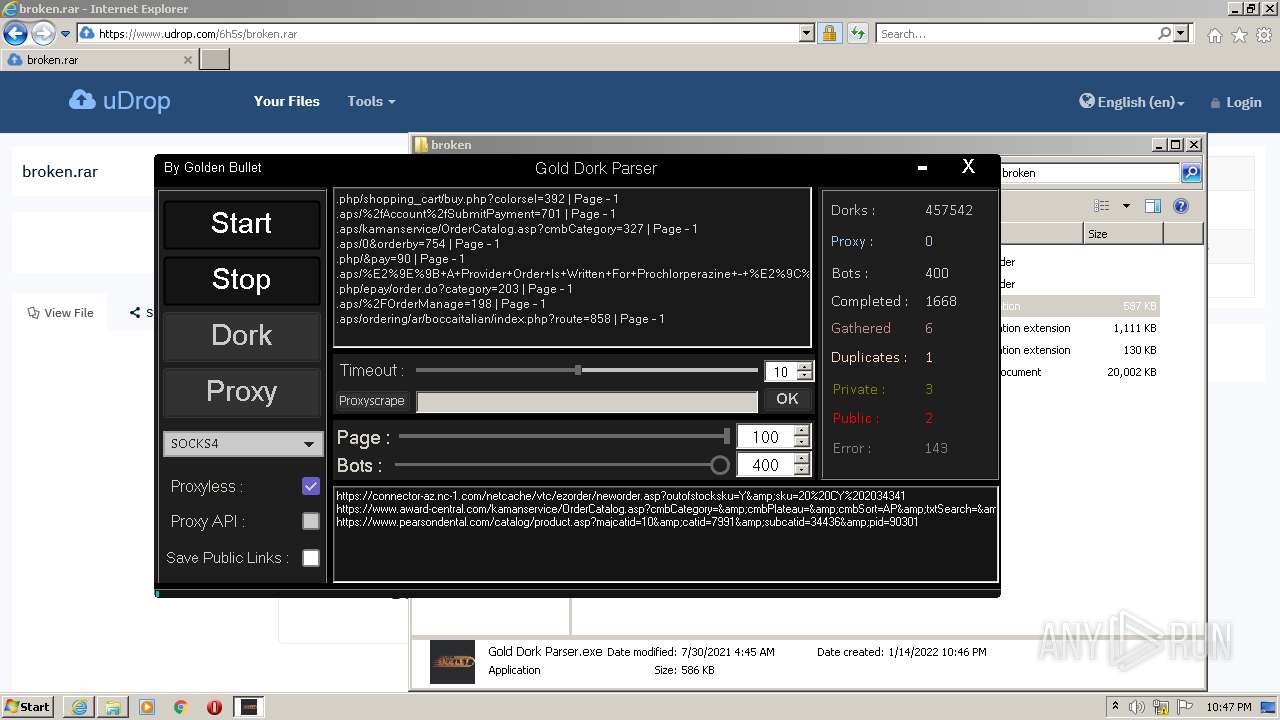
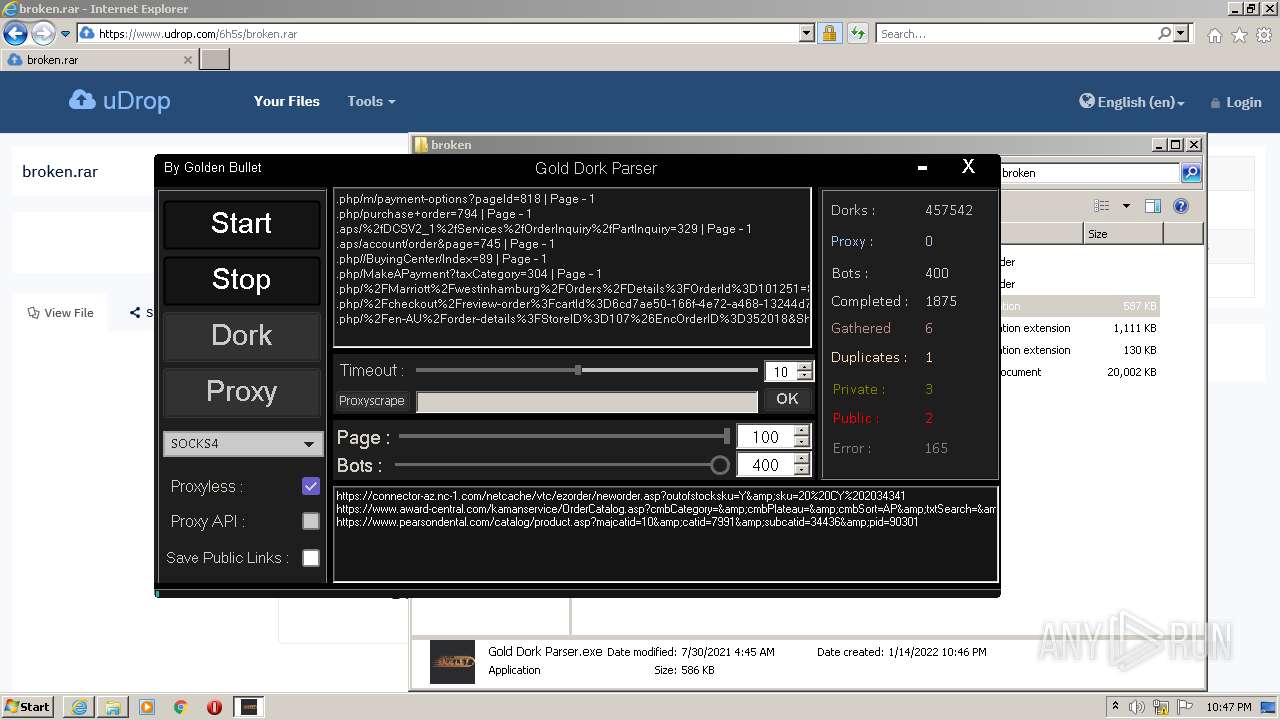
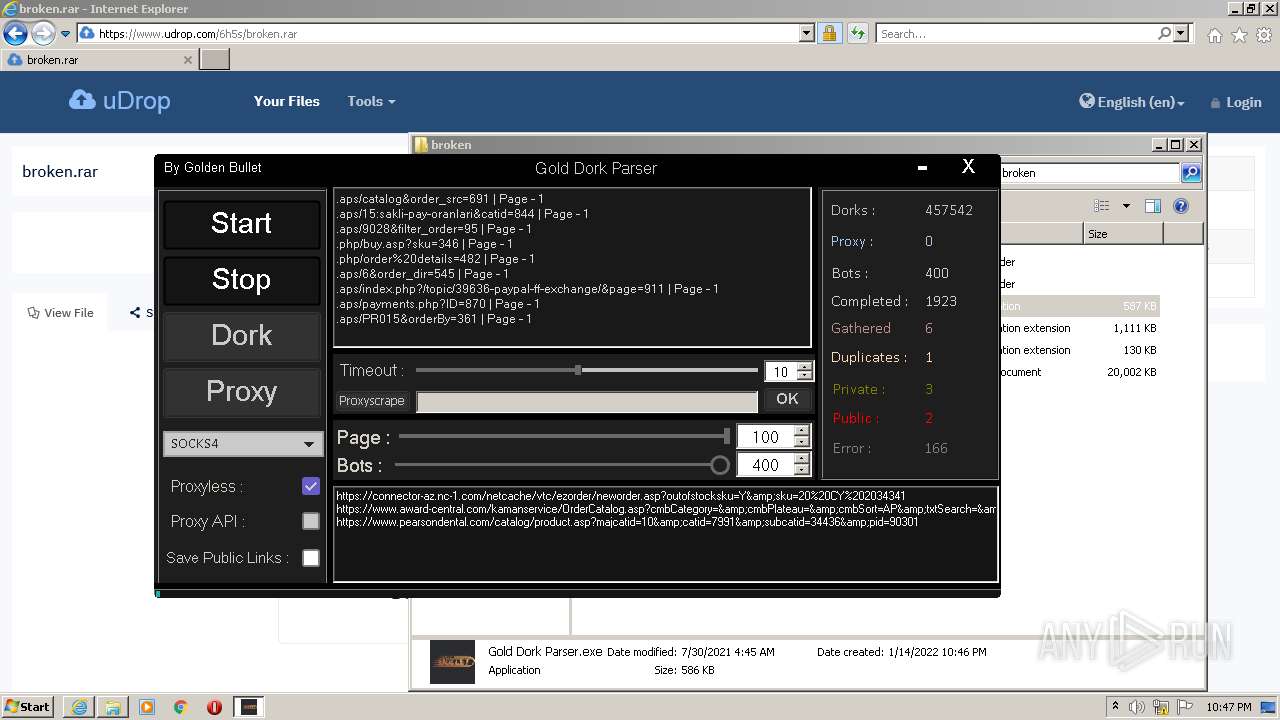
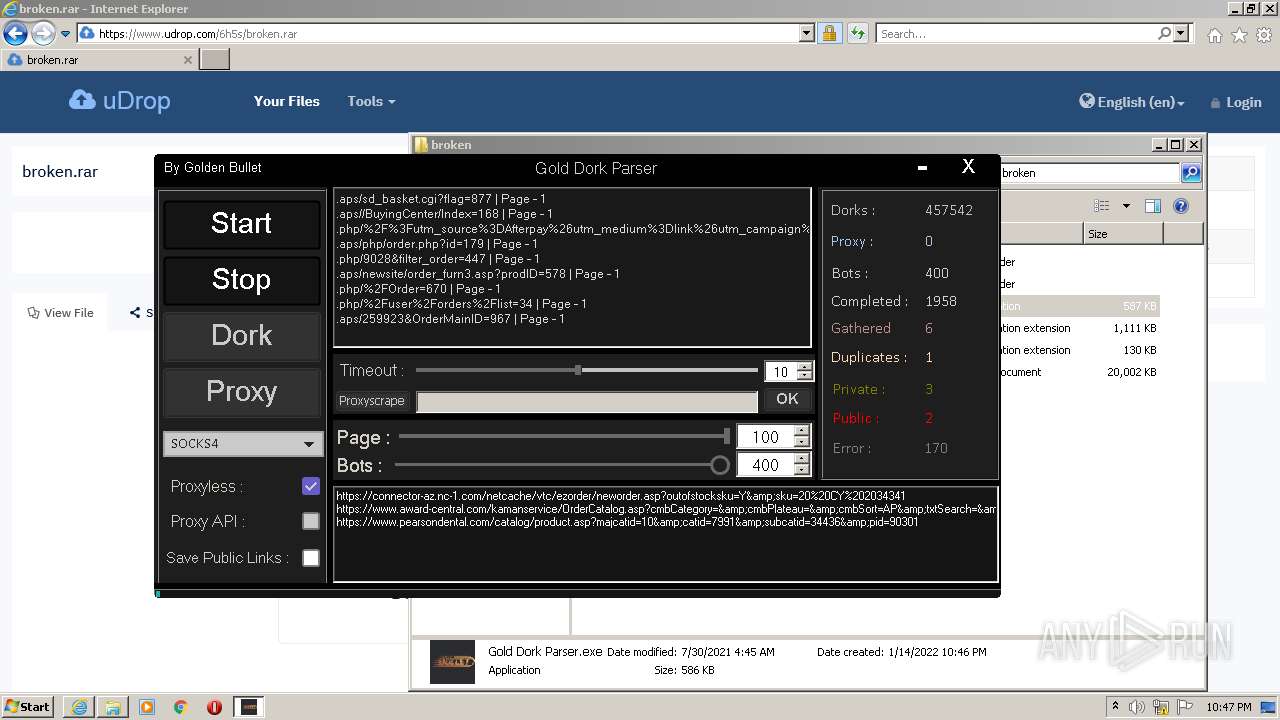
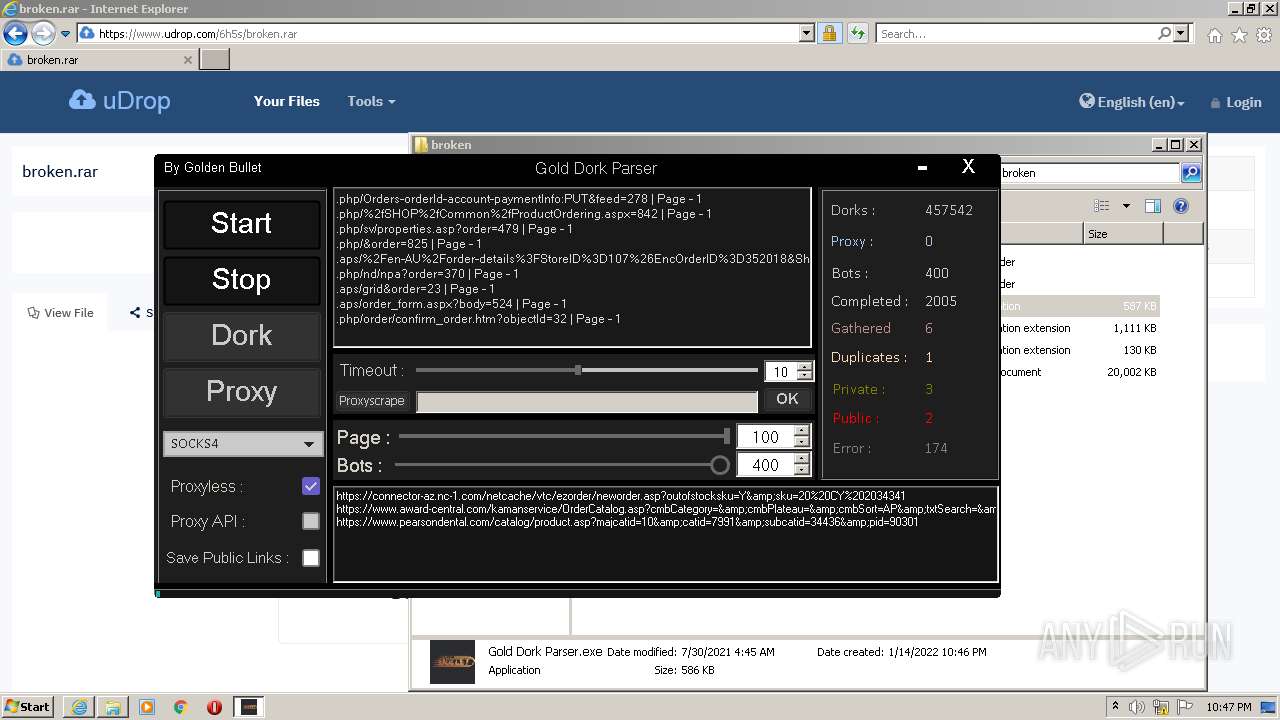
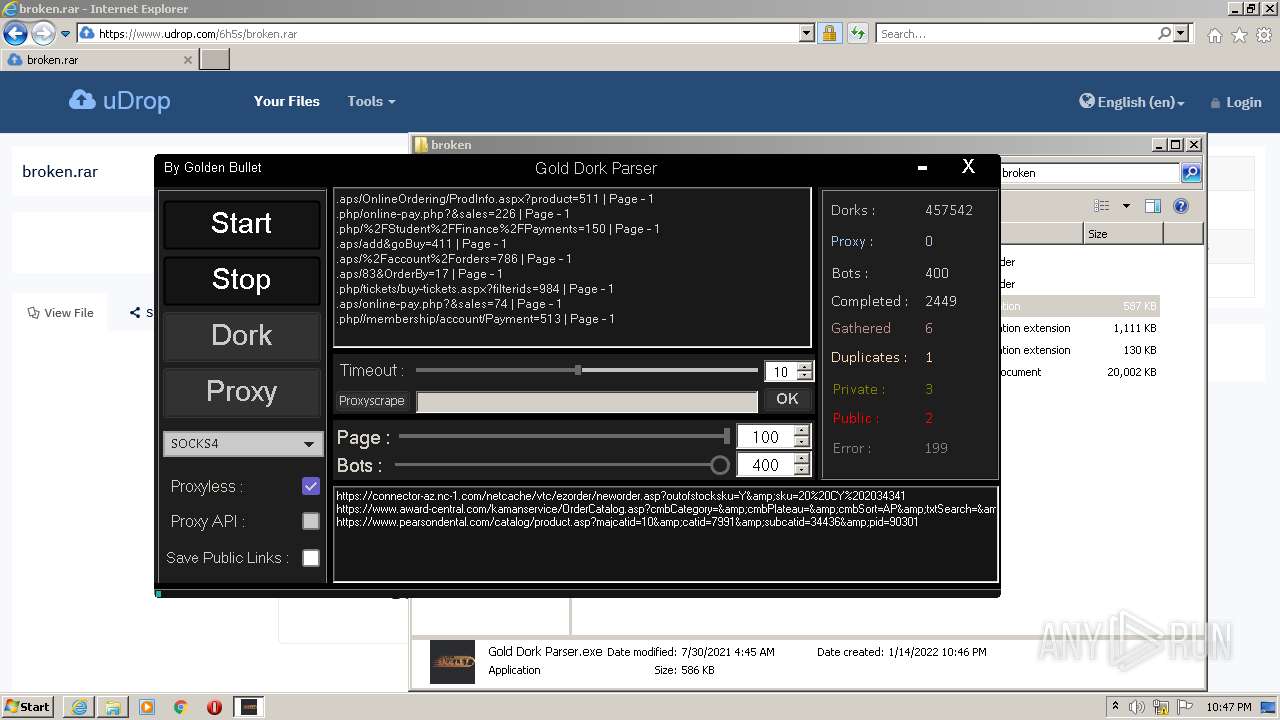
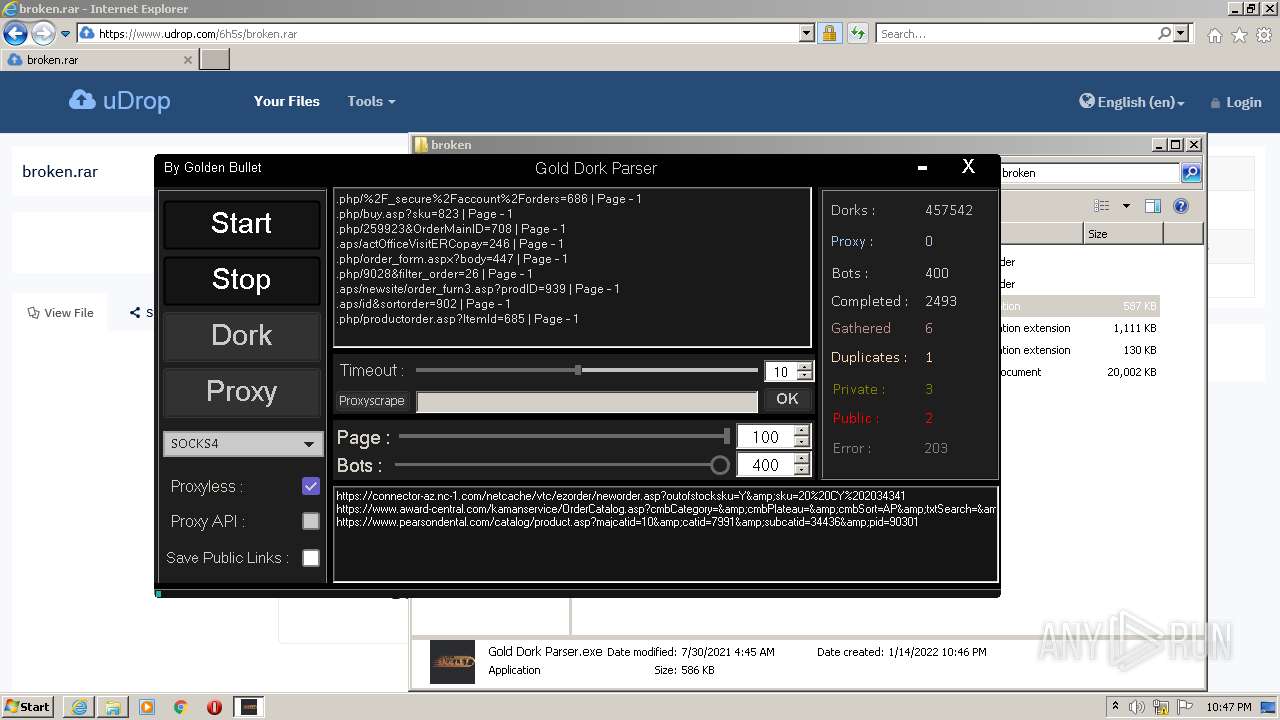
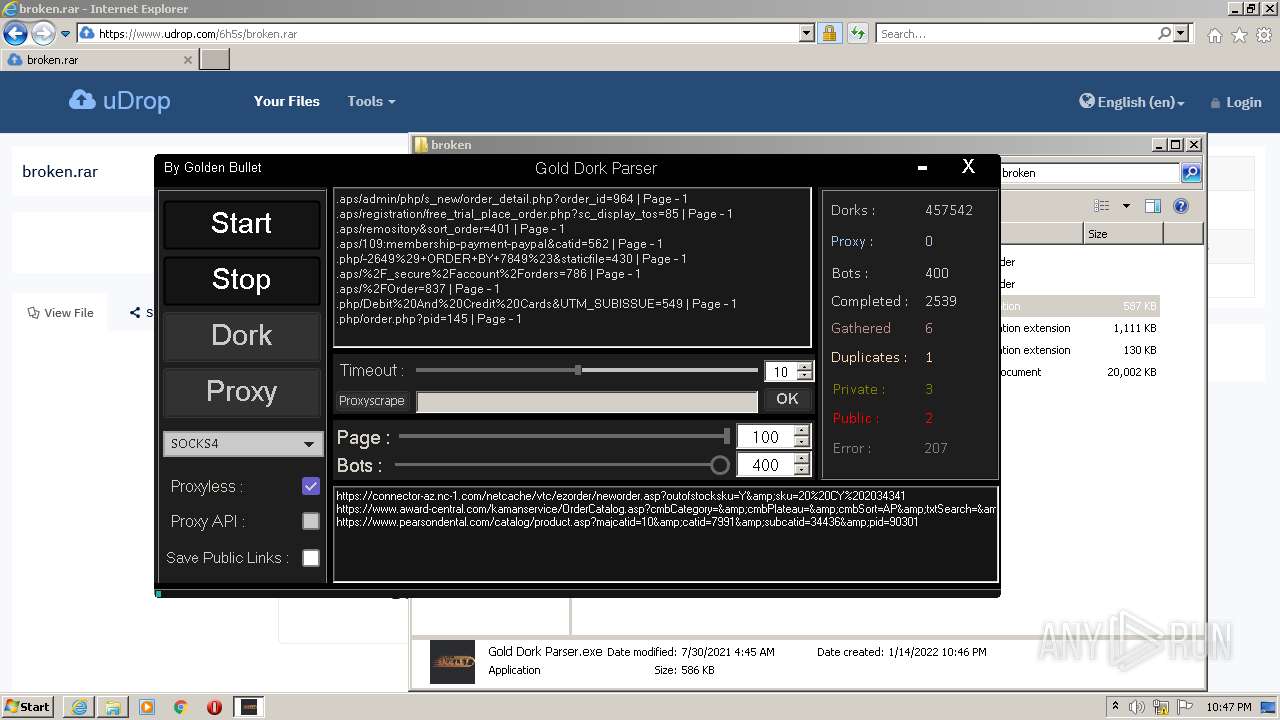
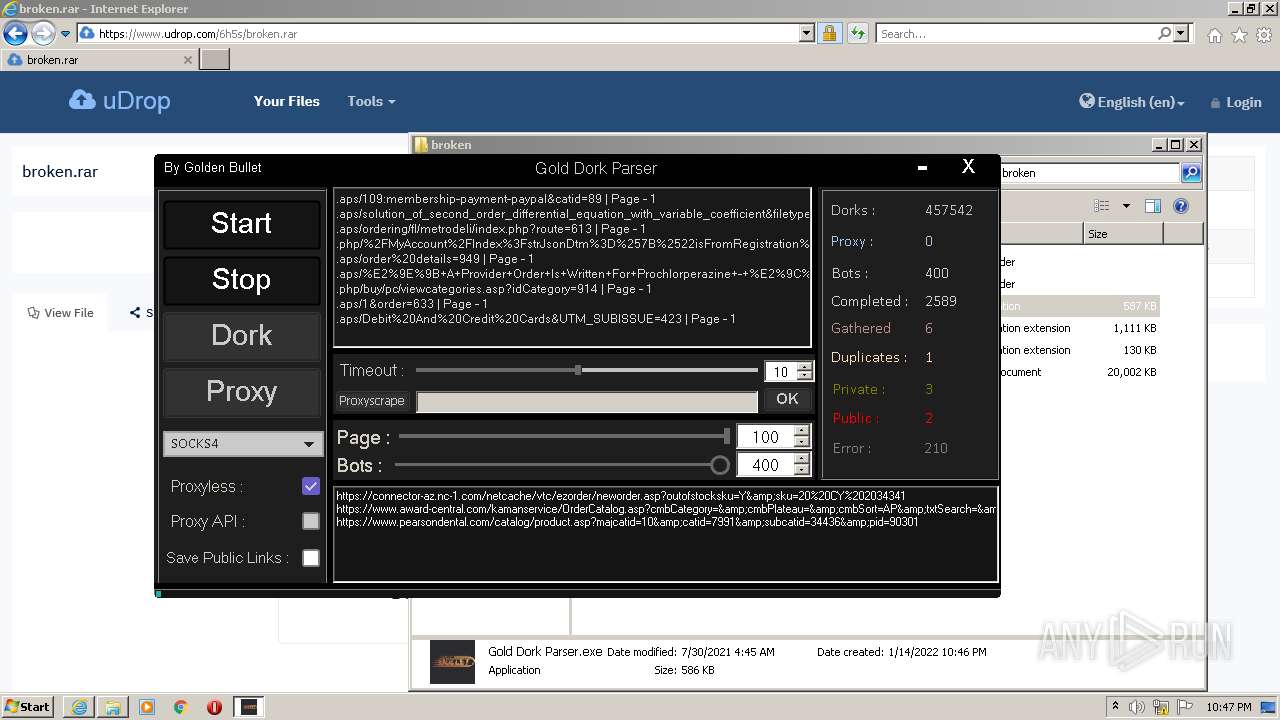
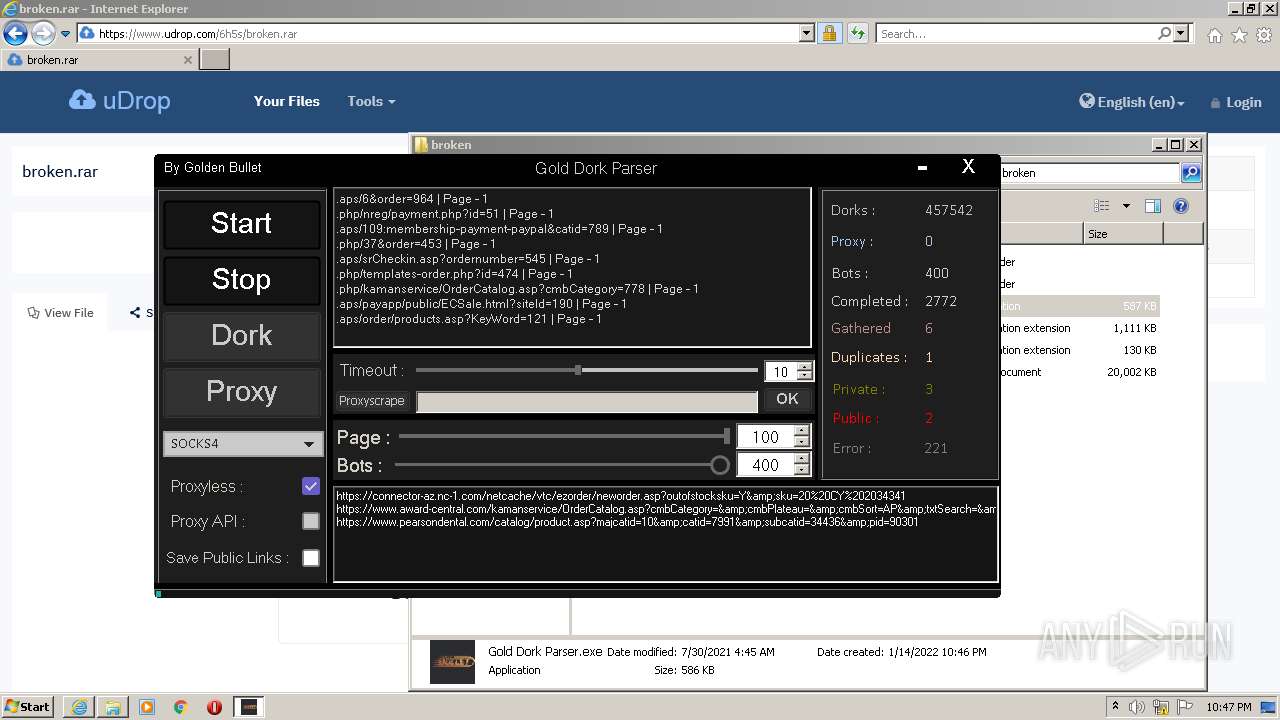
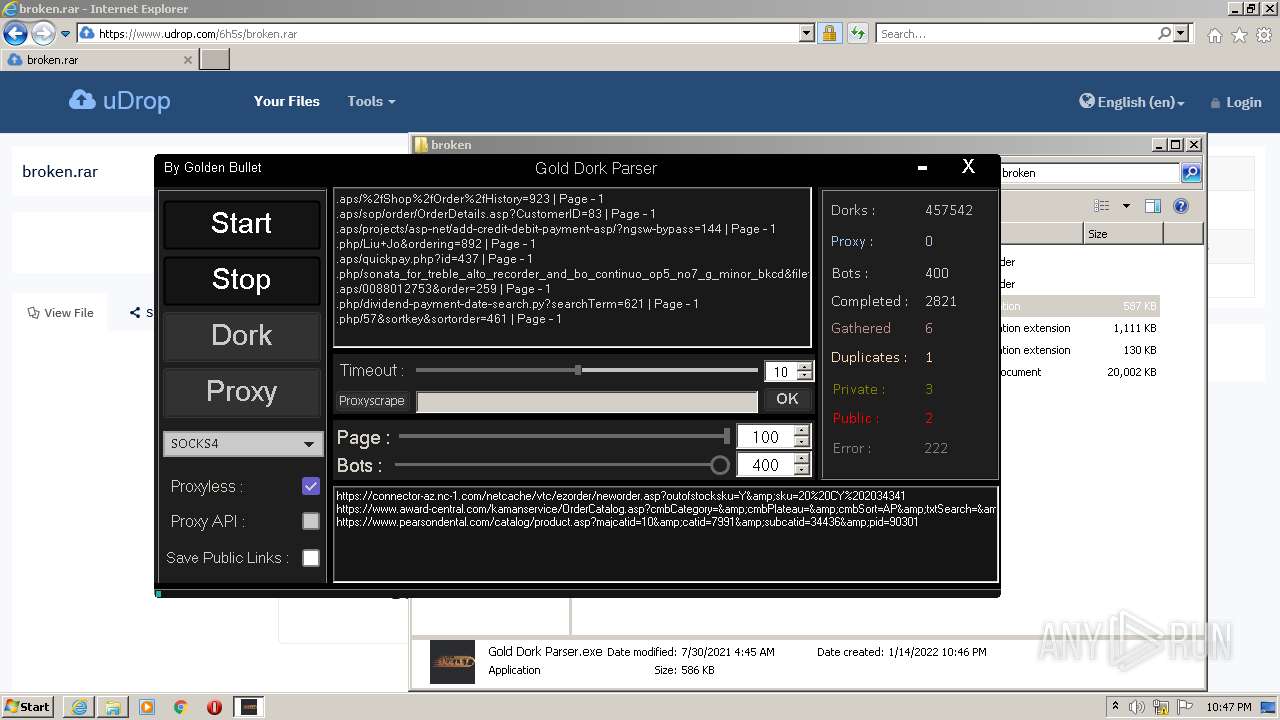
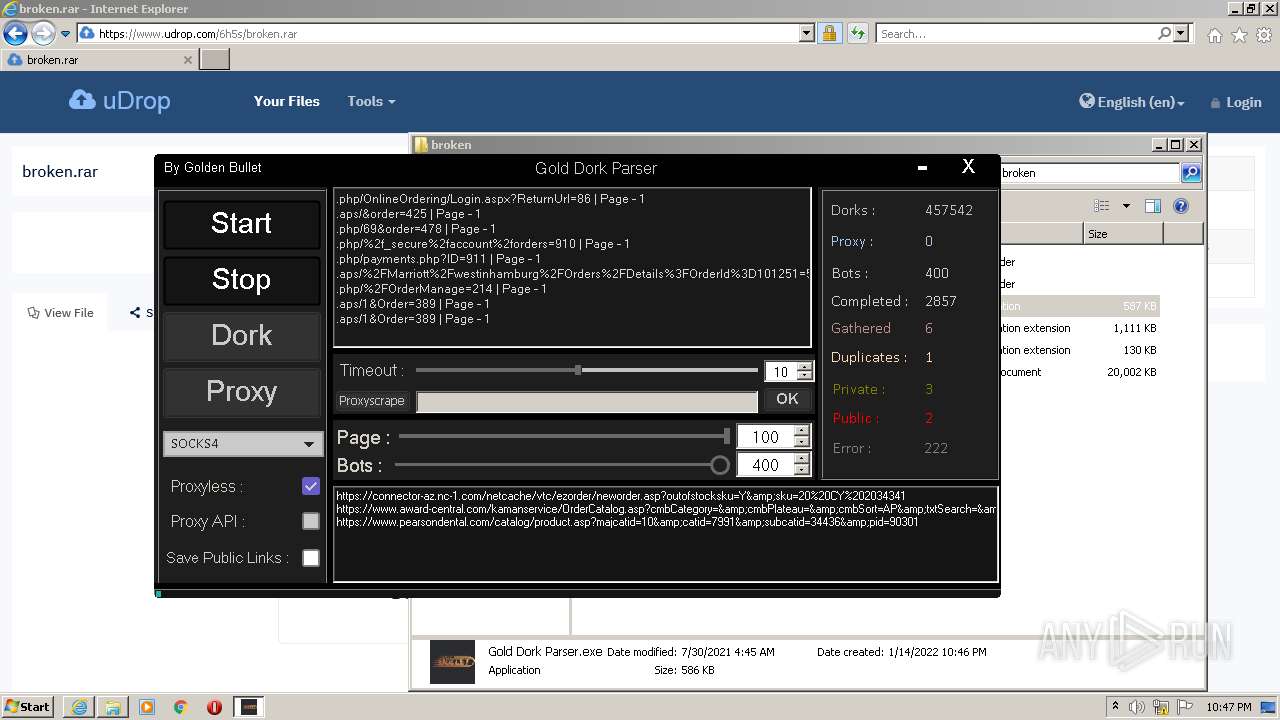
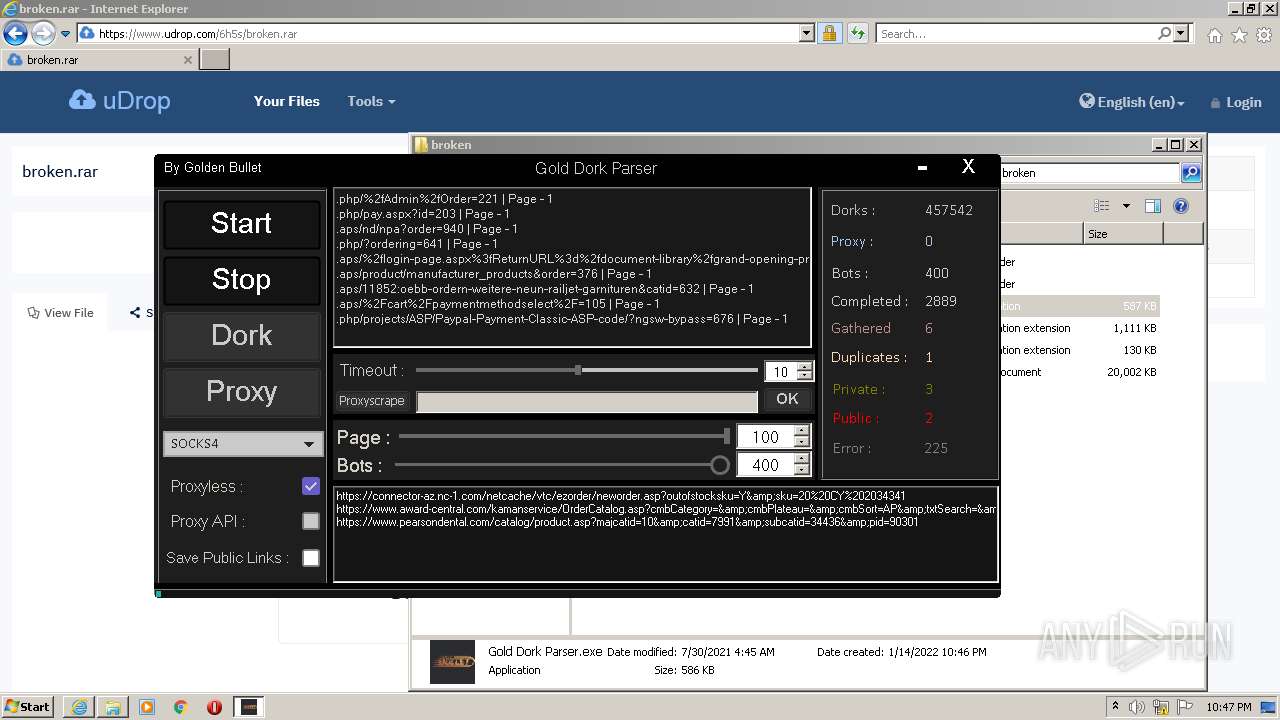
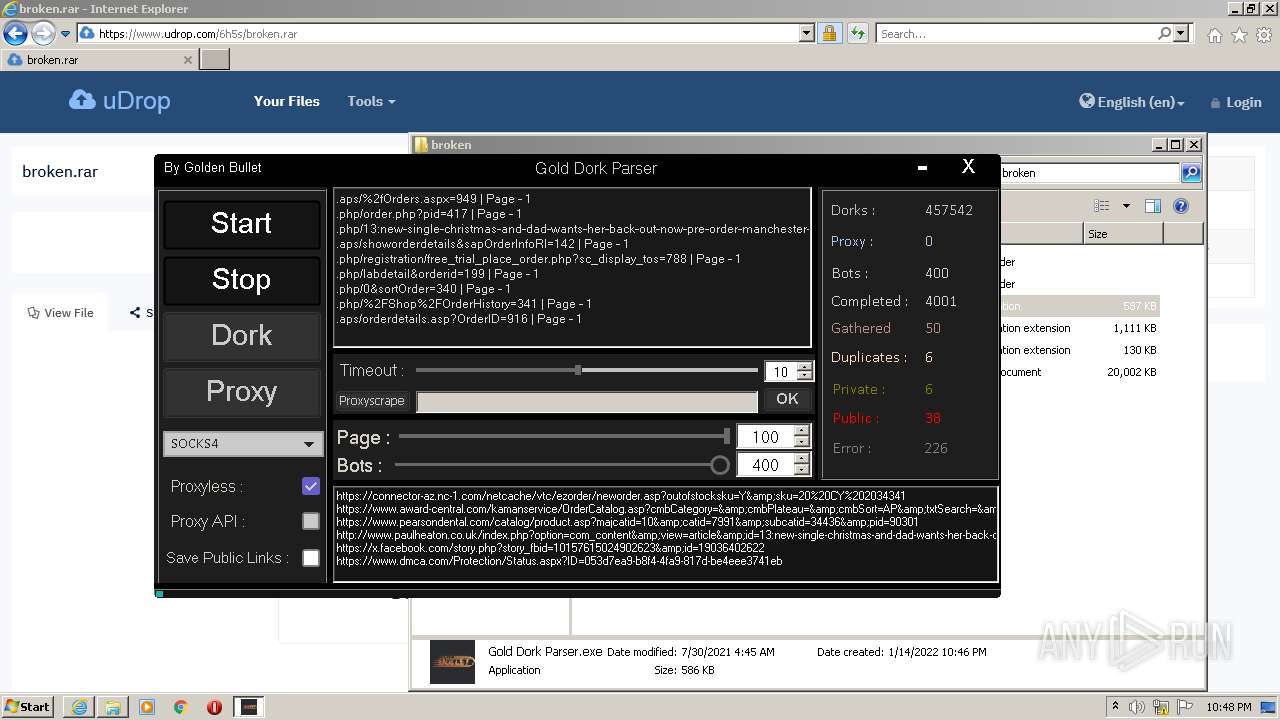
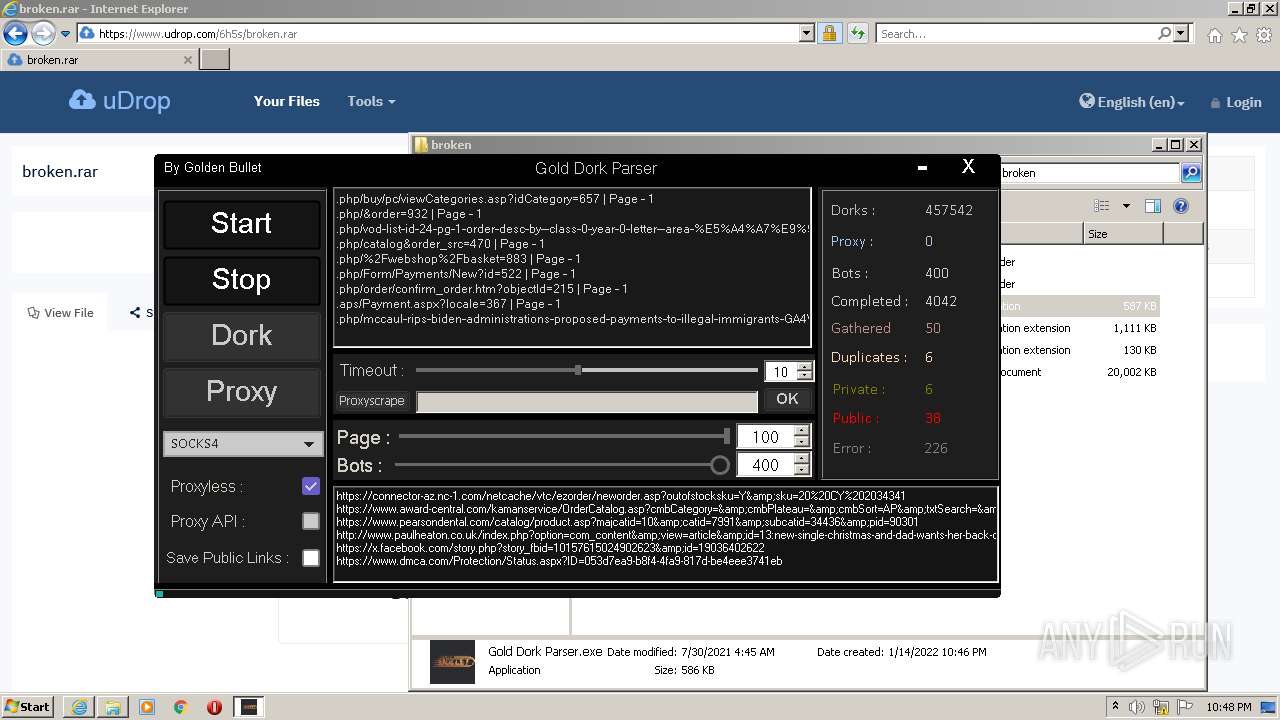
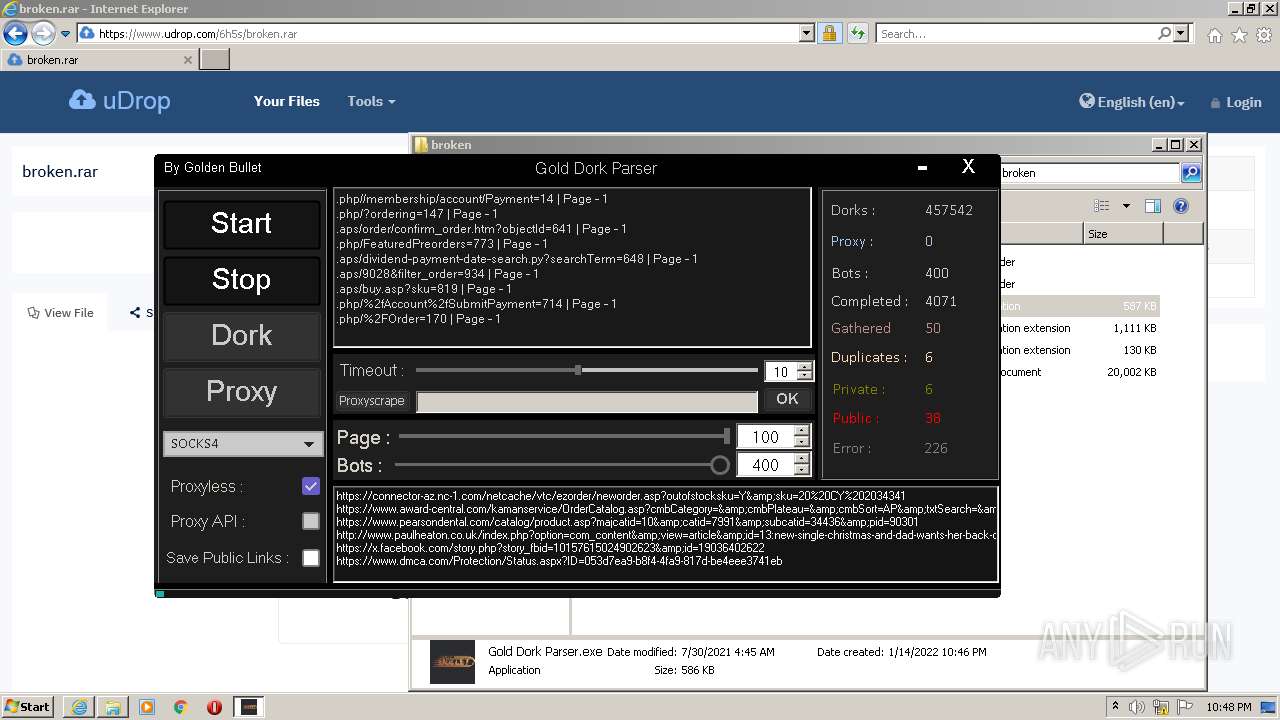
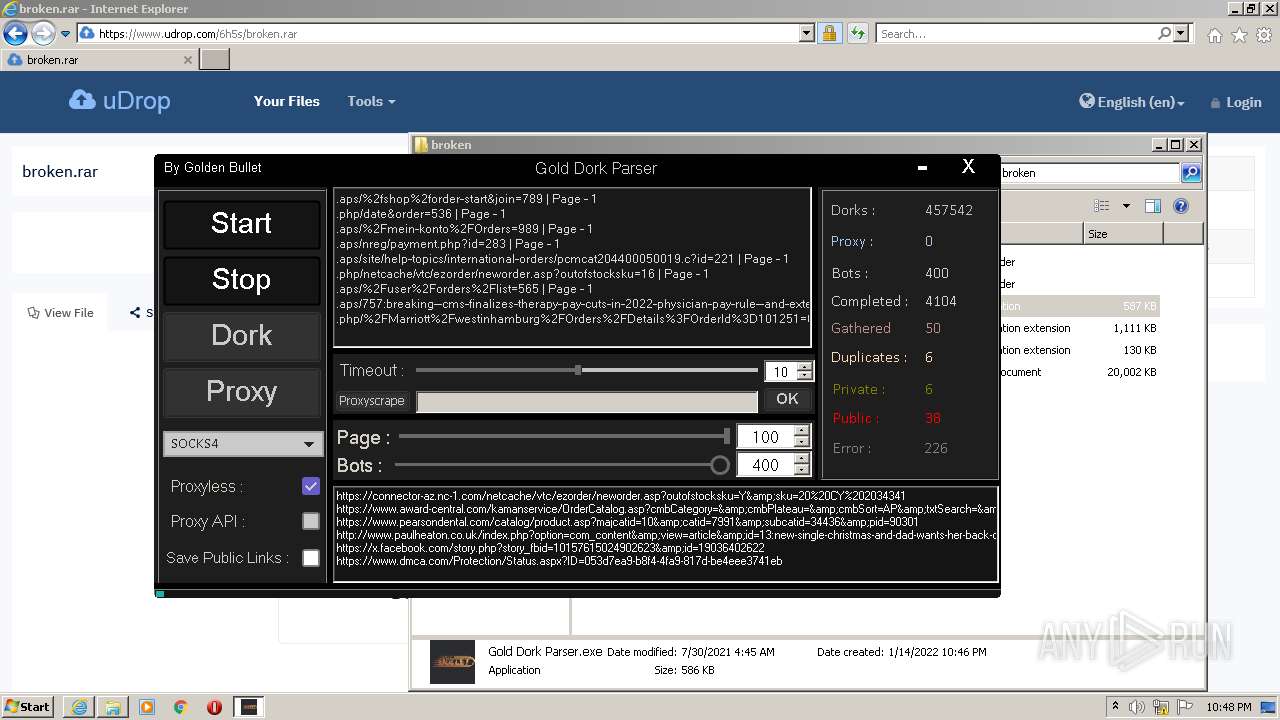
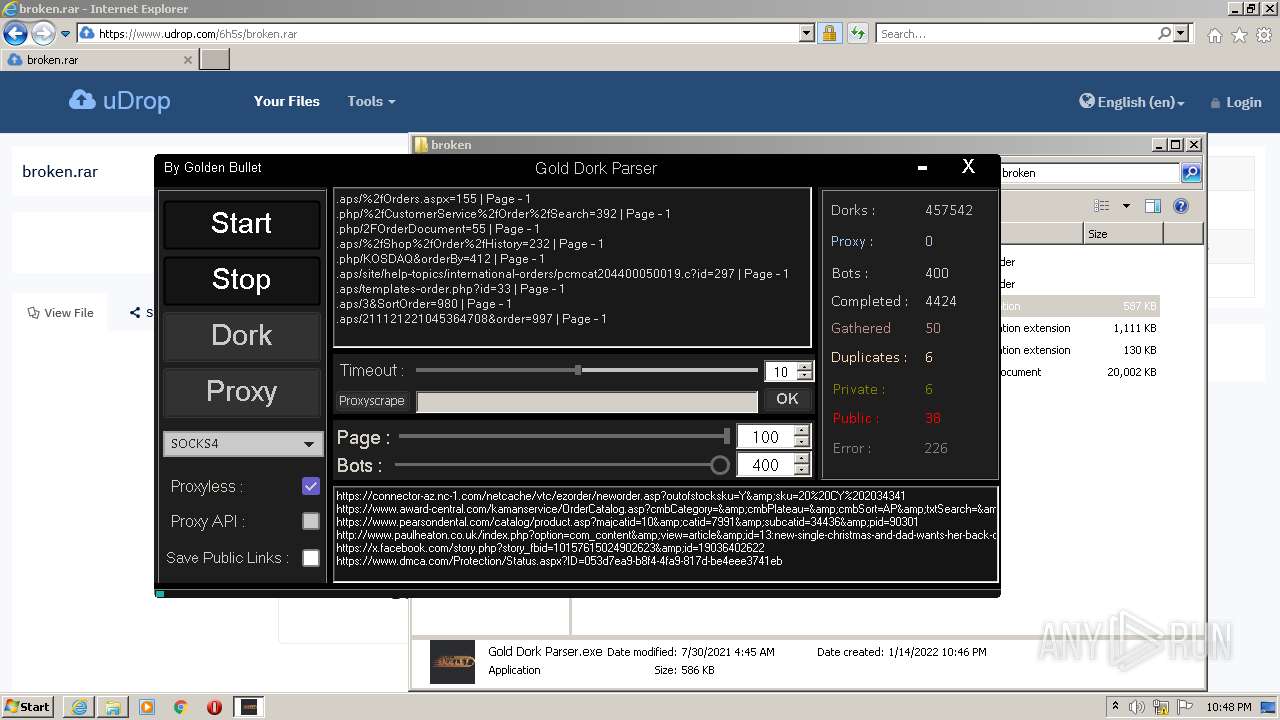
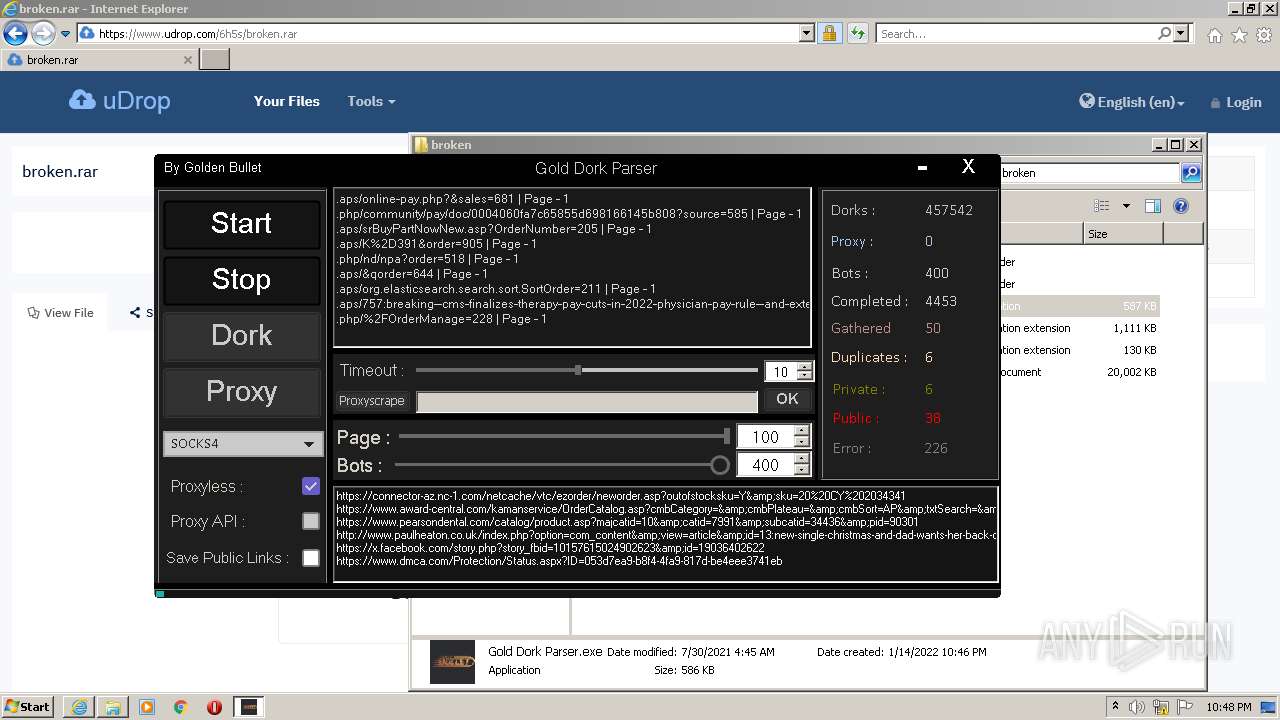
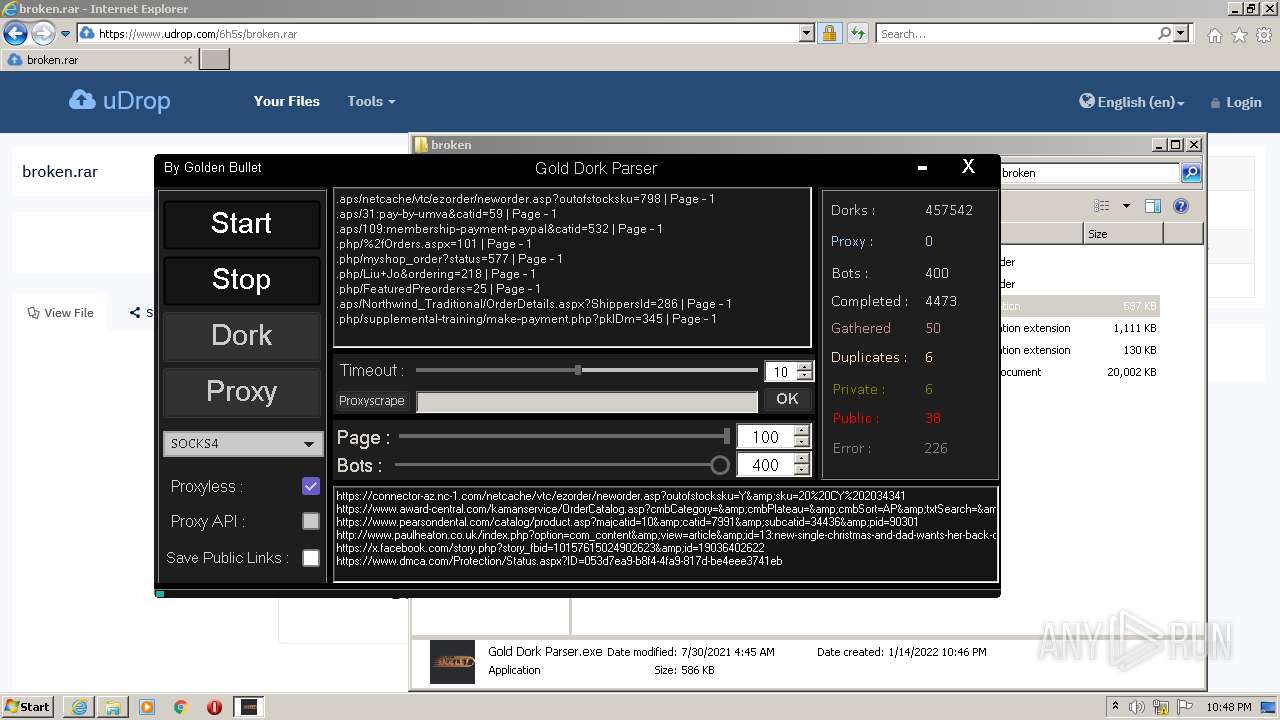
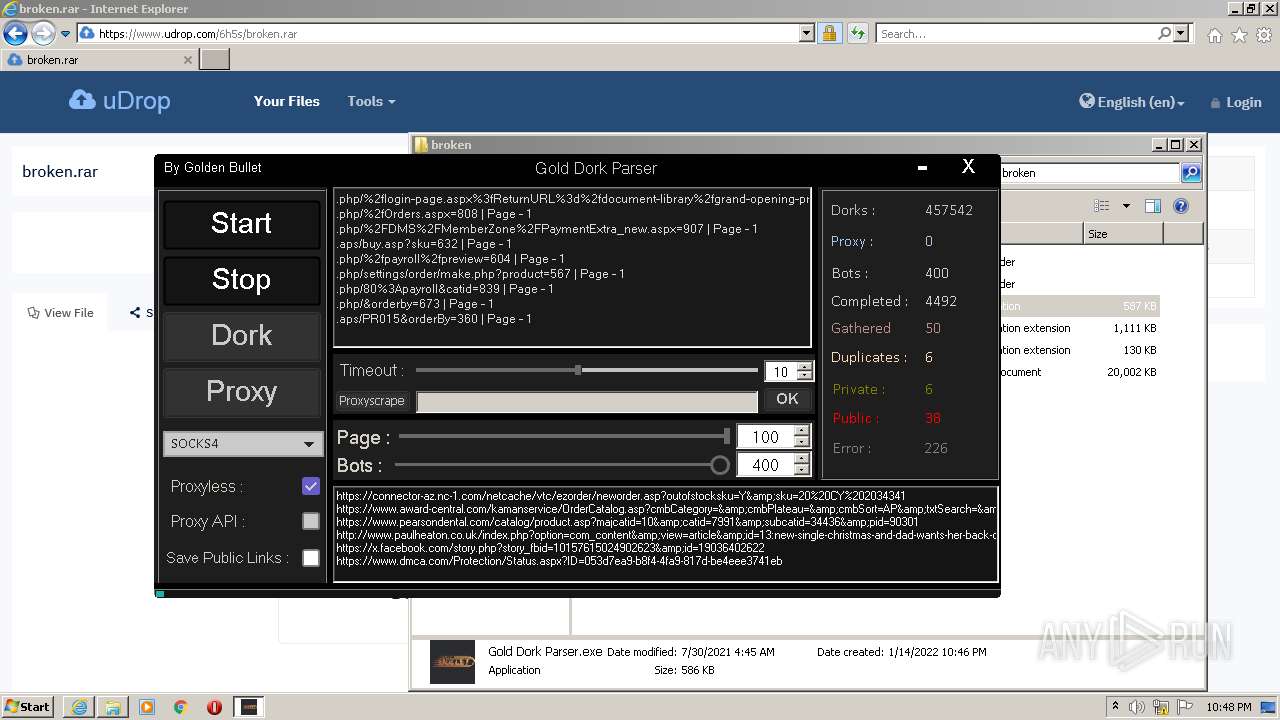
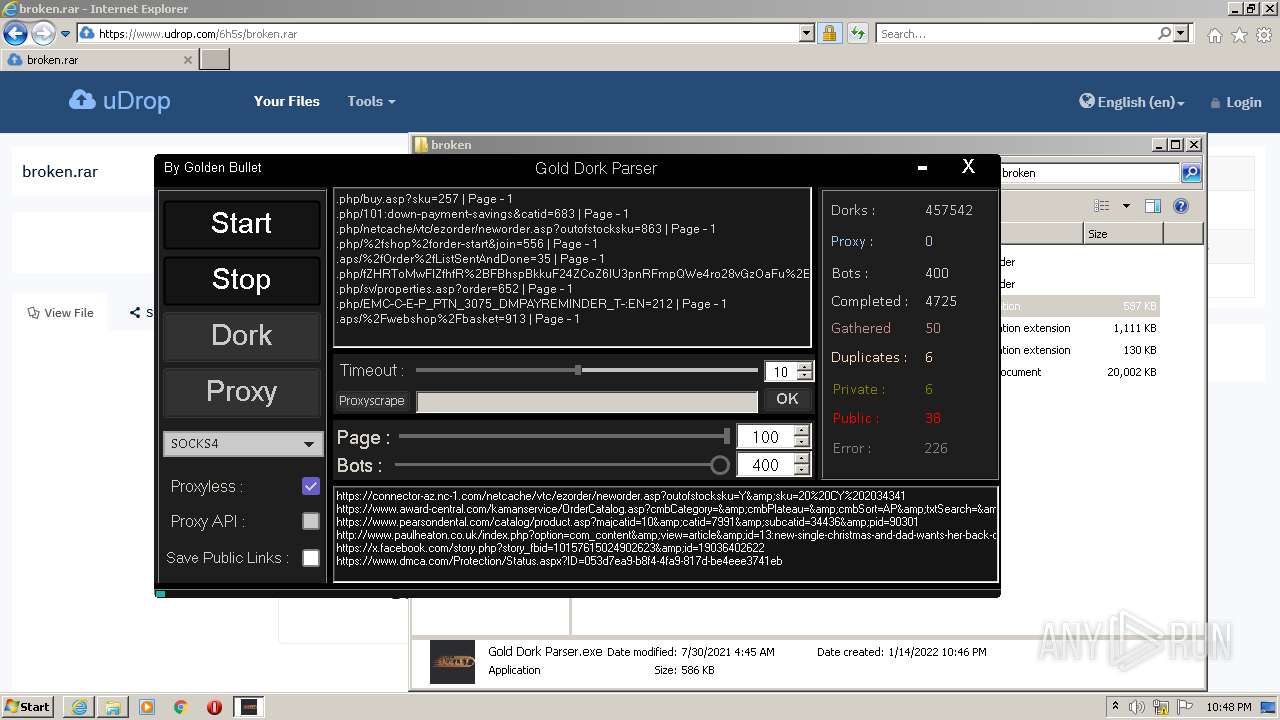
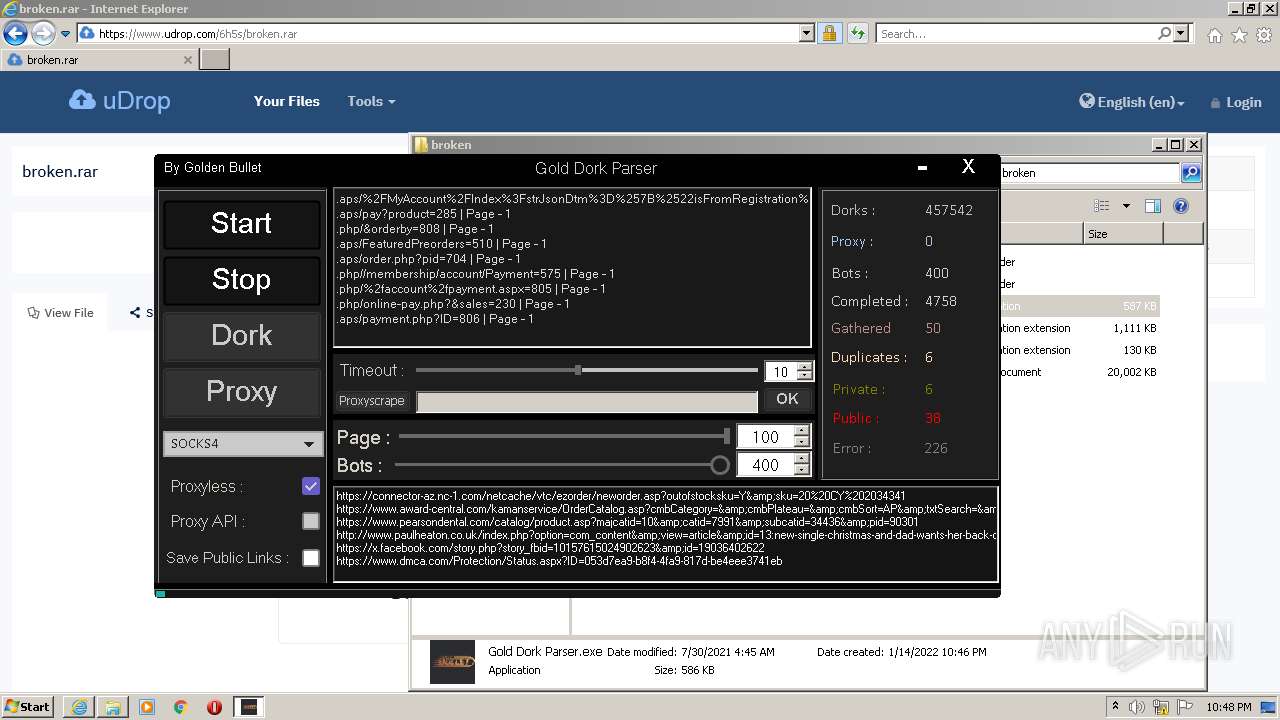
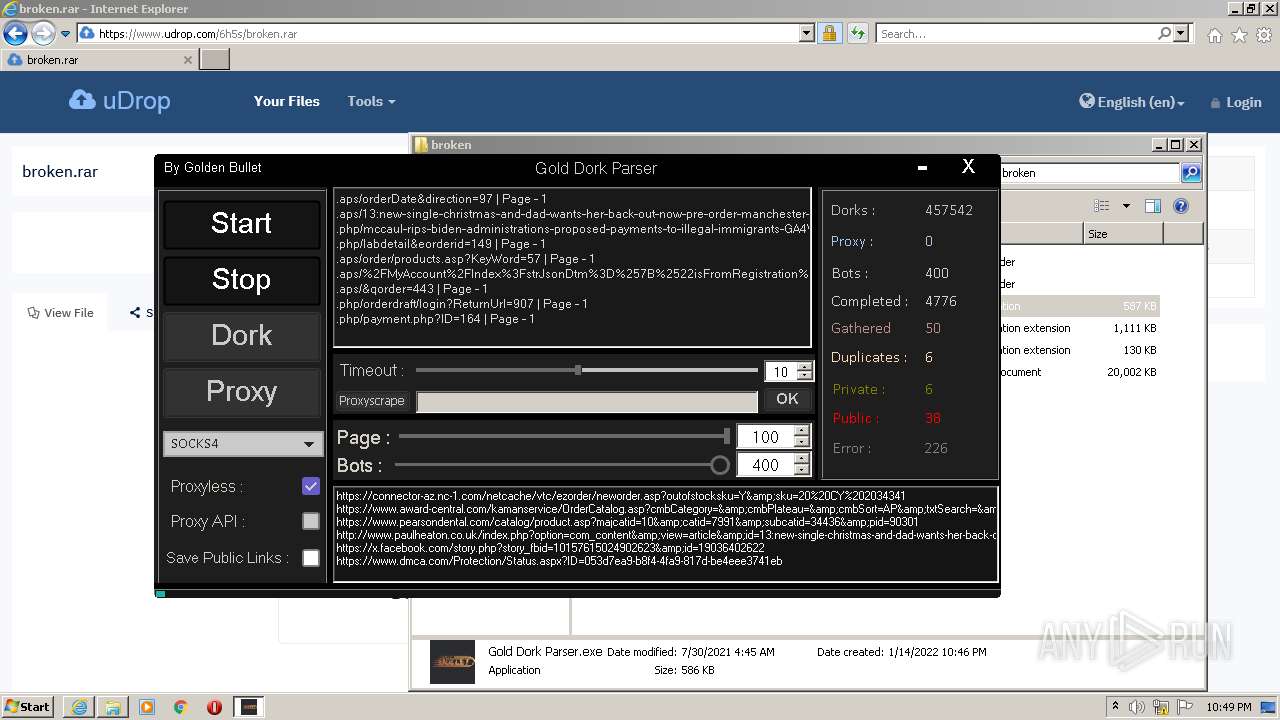
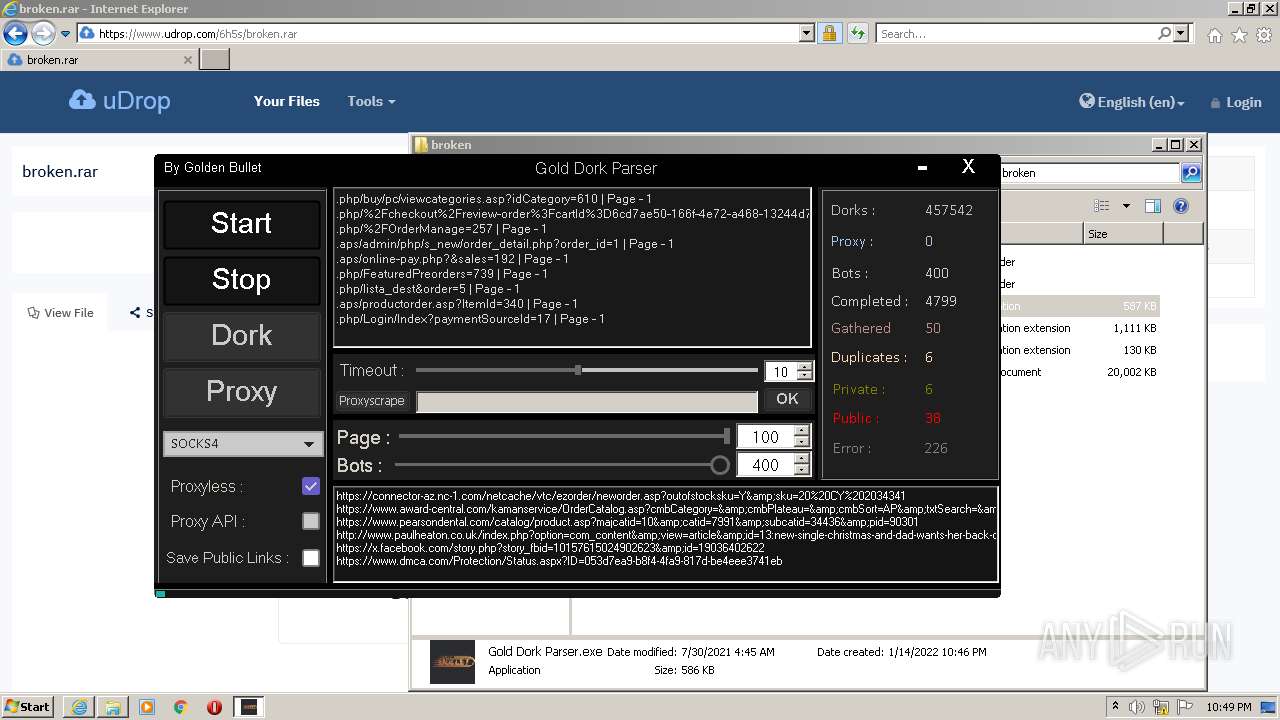
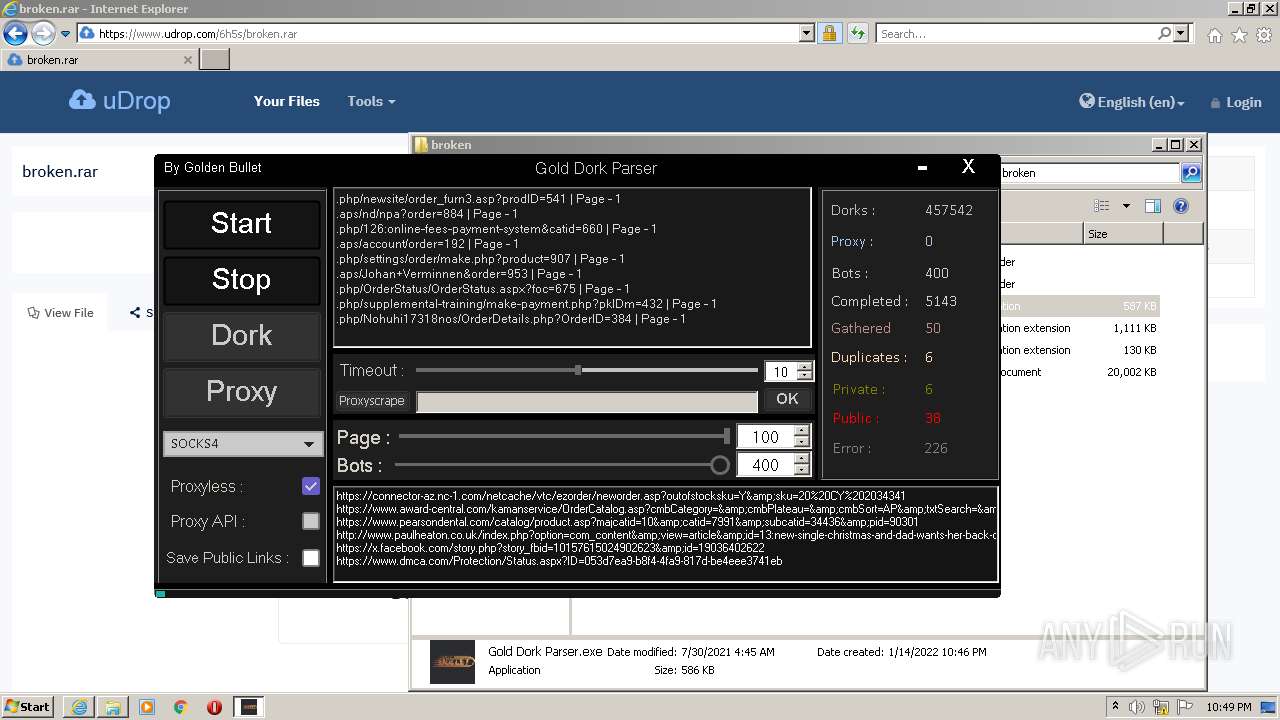
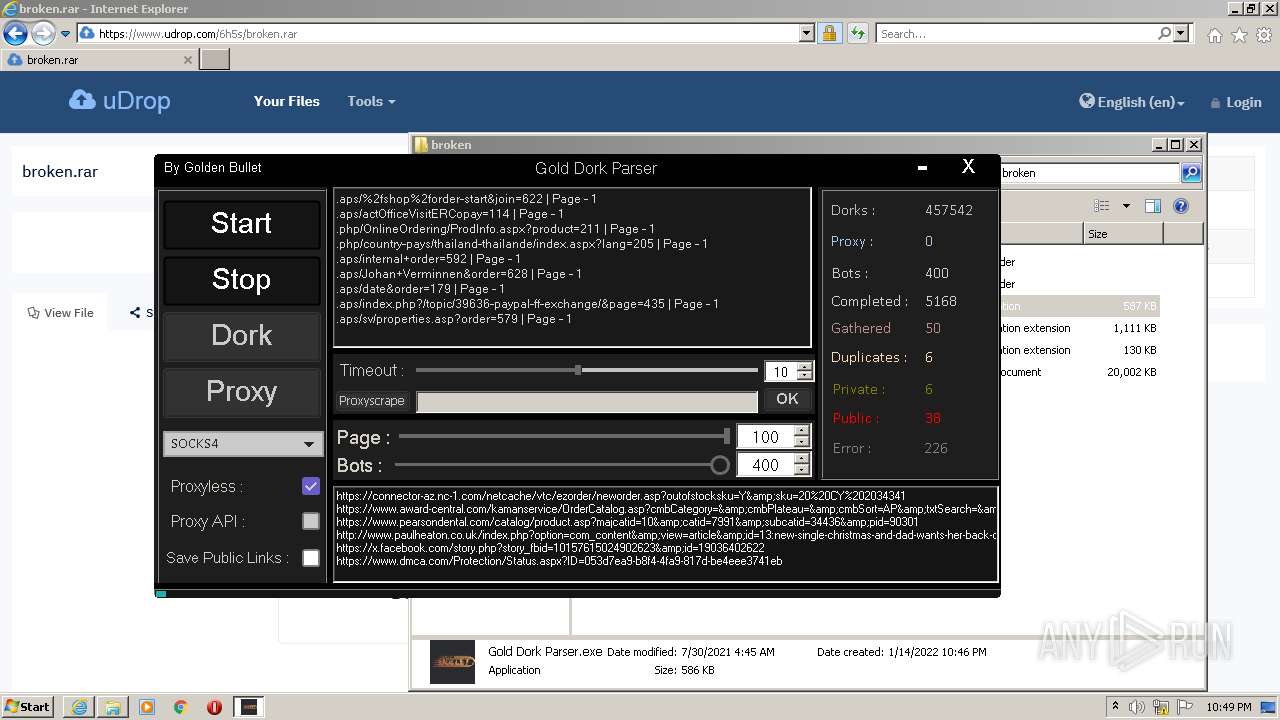
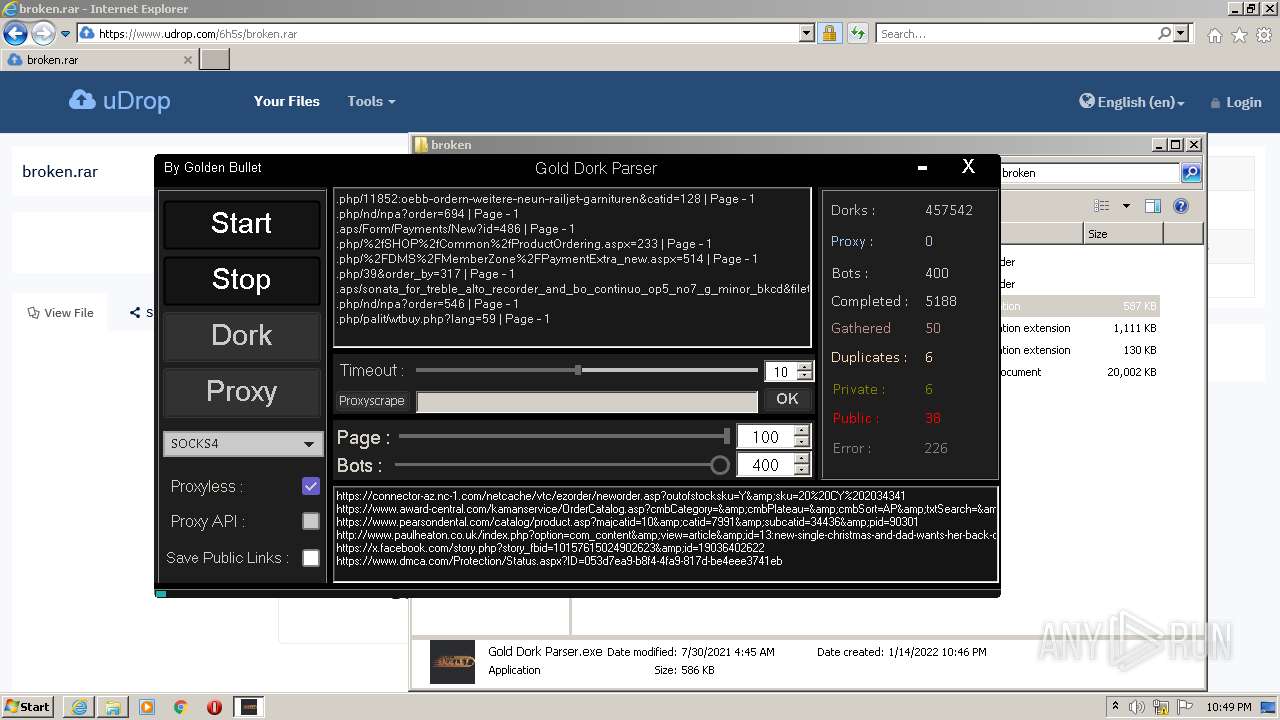
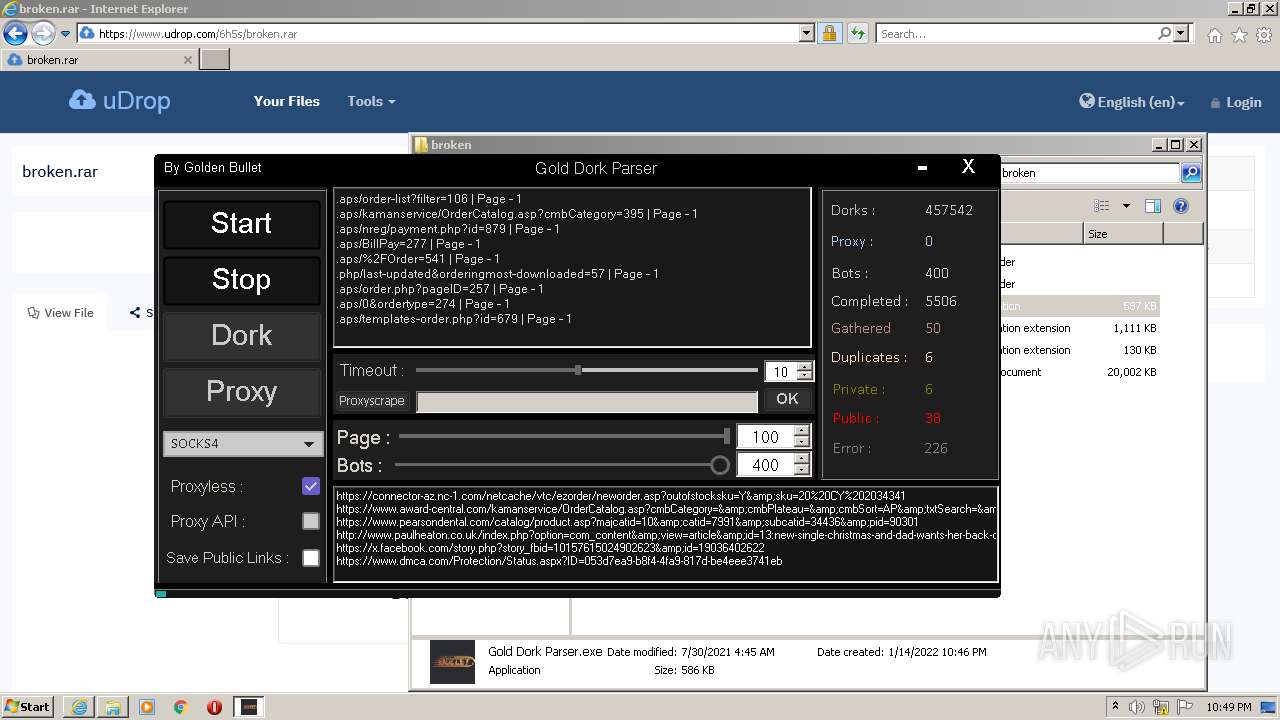
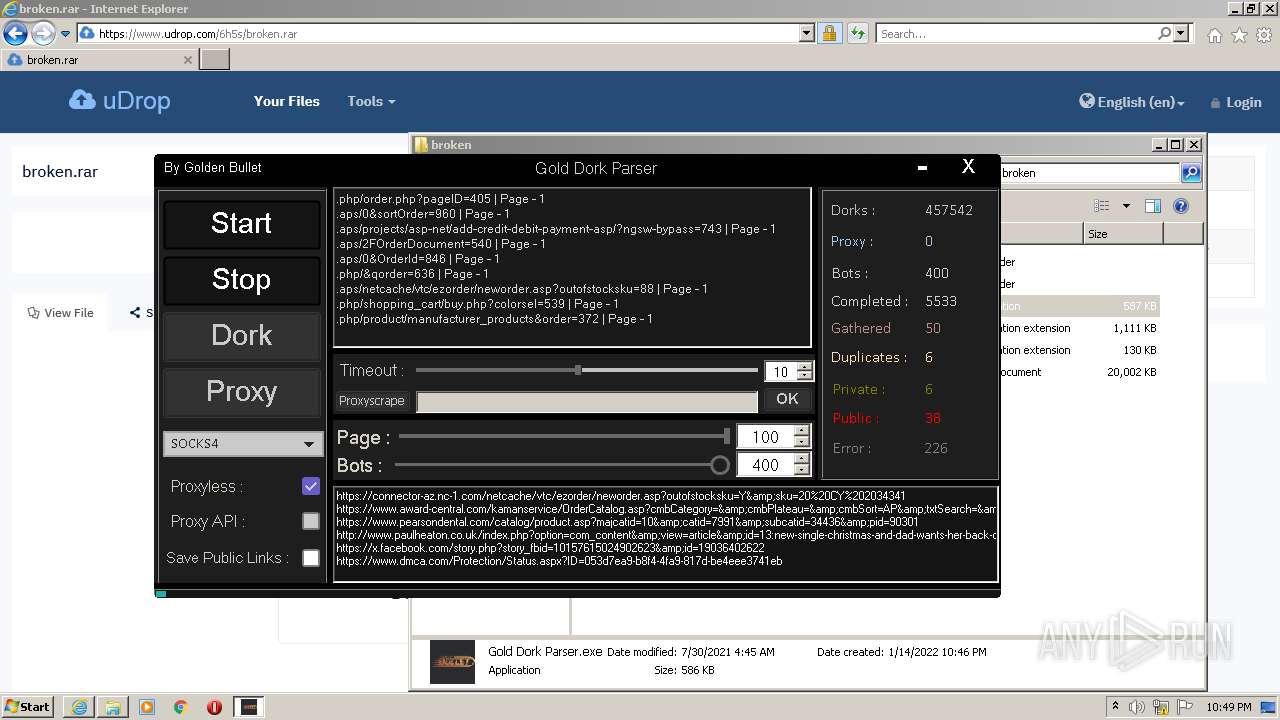
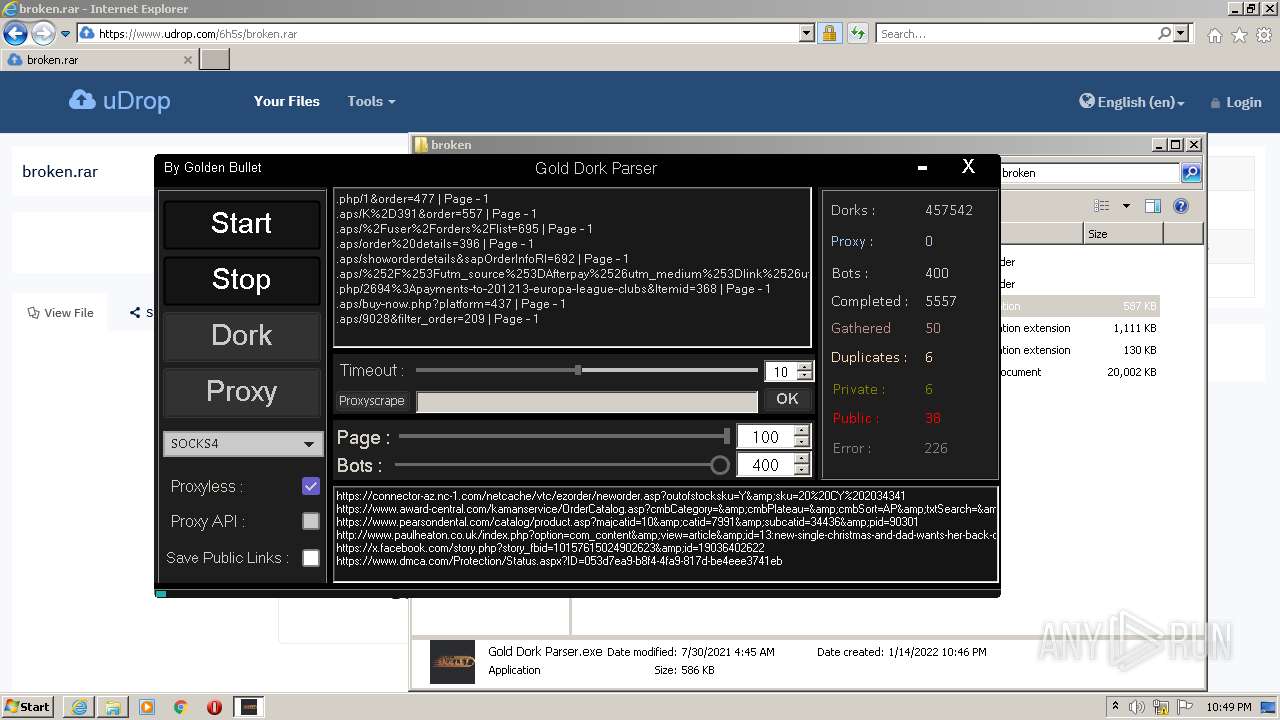
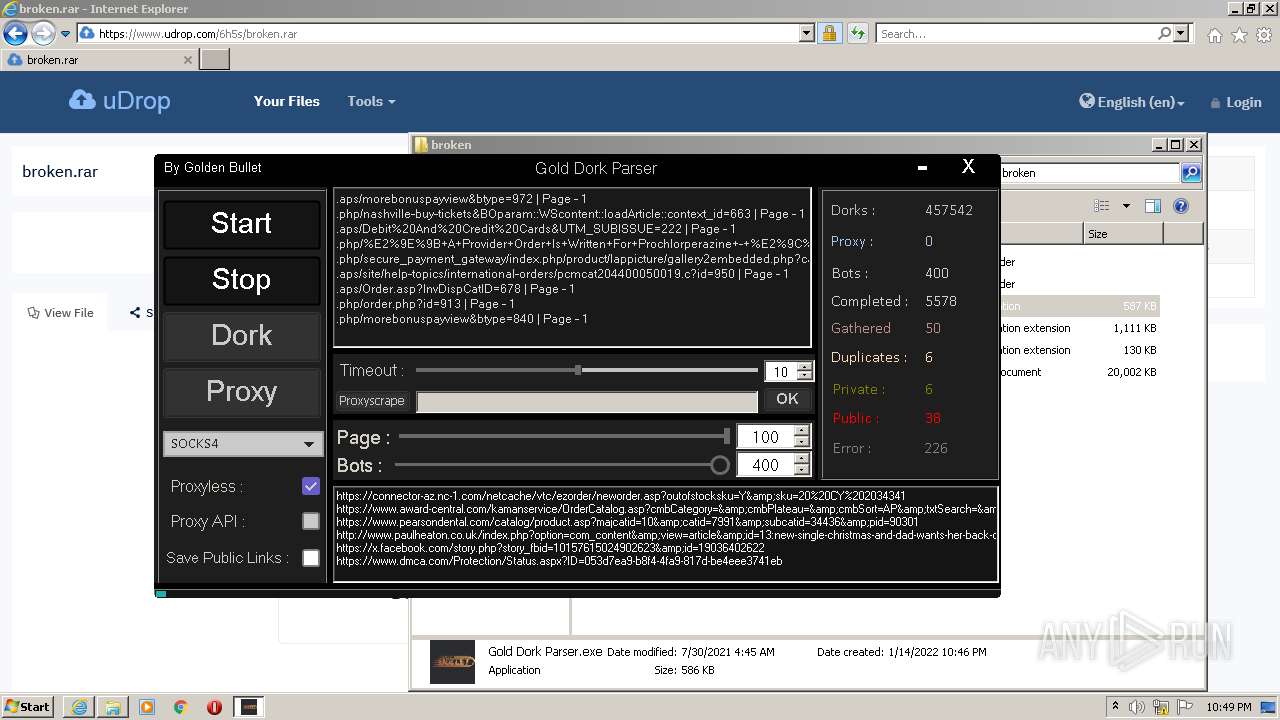
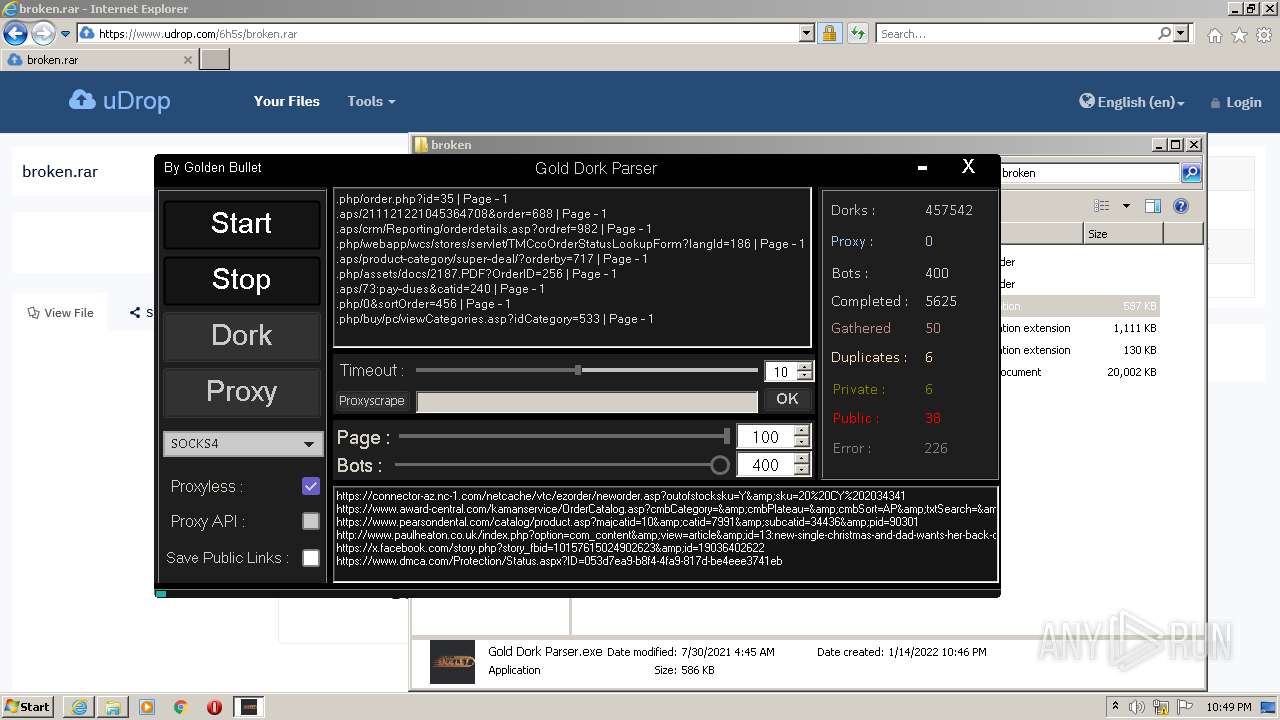
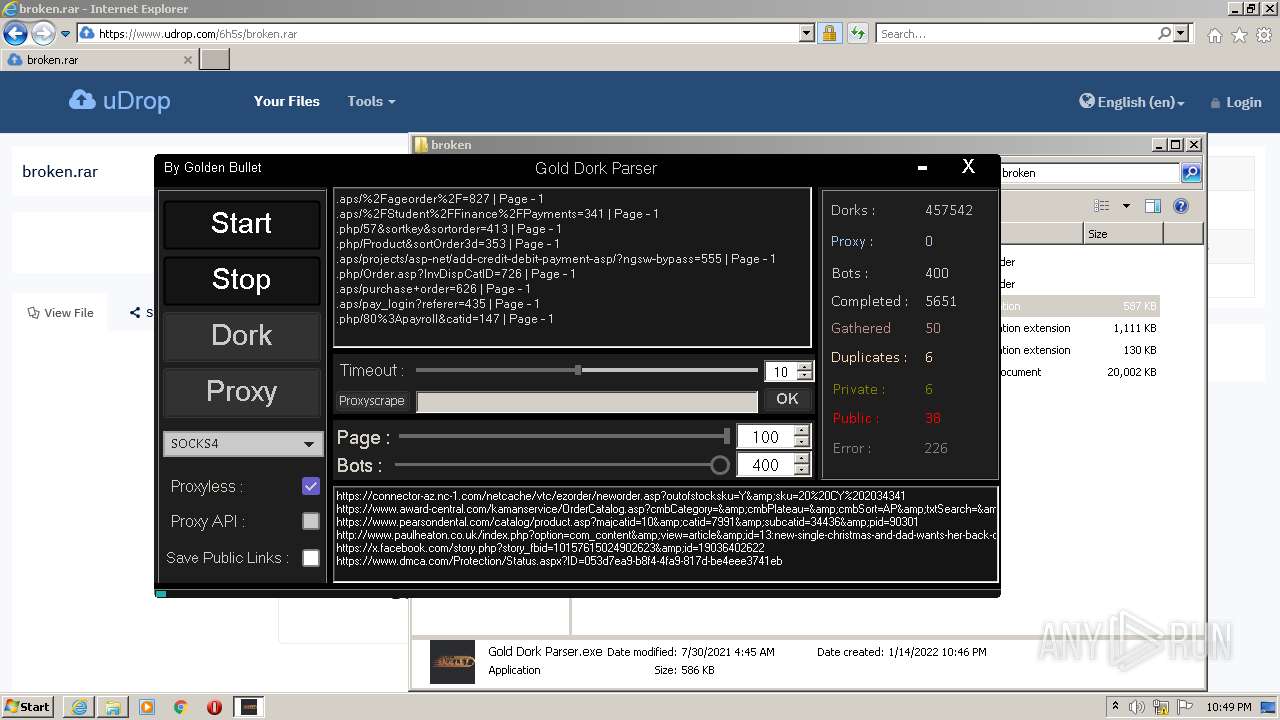
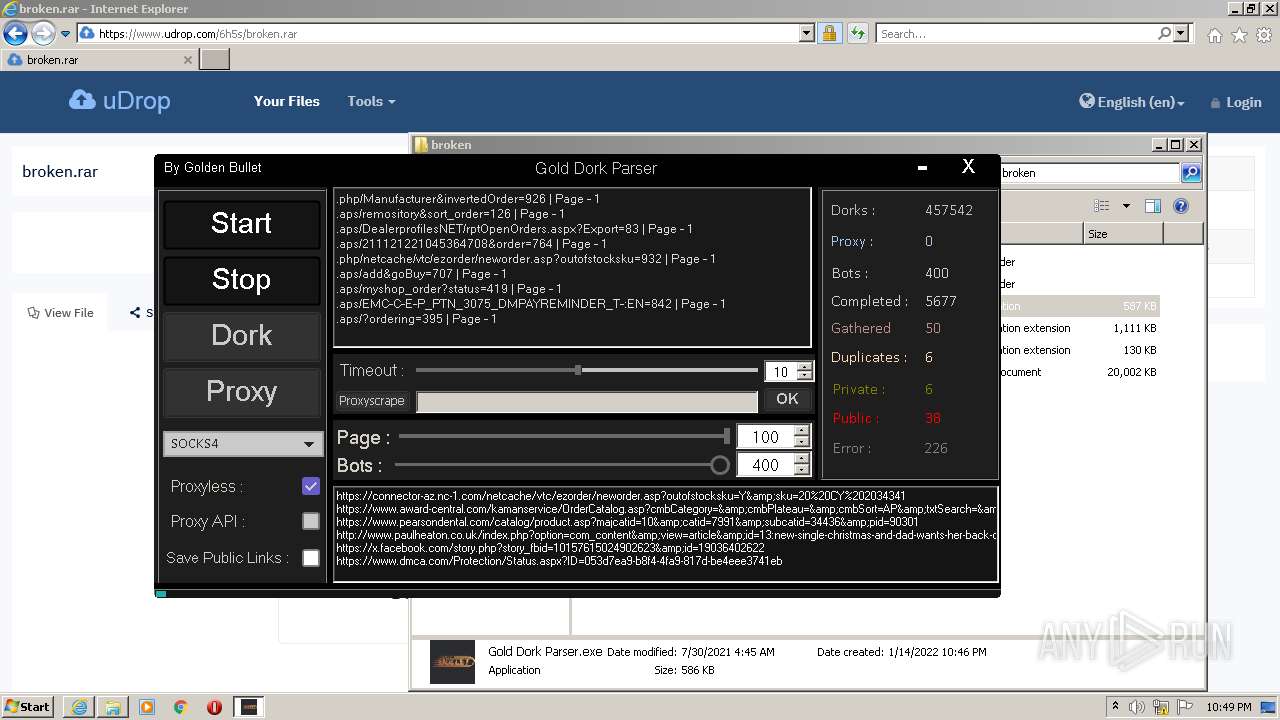
| 3168 | "C:\Users\admin\Downloads\broken\Gold Dork Parser.exe" | C:\Users\admin\Downloads\broken\Gold Dork Parser.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Gold Dork Parser Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3276 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.udrop.com/6h5s/broken.rar" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3856 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3276 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
31 942
Read events
31 714
Write events
225
Delete events
3
Modification events
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30935448 | |||
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30935448 | |||
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3276) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
10
Suspicious files
12
Text files
284
Unknown types
28
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | der | |
MD5:— | SHA256:— | |||
| 3856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3856 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\72SSBRVM.txt | text | |
MD5:— | SHA256:— | |||
| 3856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EB2C4AB8B68FFA4B7733A9139239A396_D76DB901EE986B889F30D8CC06229E2D | binary | |
MD5:— | SHA256:— | |||
| 3856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5BC0F345944148EB6CA31E060E457F9D_DEFB822B92348051F4B31FFEA0106719 | der | |
MD5:— | SHA256:— | |||
| 3856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | der | |
MD5:— | SHA256:— | |||
| 3856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\broken[1].htm | html | |
MD5:— | SHA256:— | |||
| 3856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\223DE96EE265046957A660ED7C9DD9E7_EFF9B9BA98DEAA773F261FA85A0B1771 | binary | |
MD5:— | SHA256:— | |||
| 3856 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5BC0F345944148EB6CA31E060E457F9D_DEFB822B92348051F4B31FFEA0106719 | binary | |
MD5:— | SHA256:— | |||
| 3856 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\fonts[1].css | text | |
MD5:C5BAC7EBCE91E9D35F1C28600E4279FA | SHA256:34976D79D70E6ADED7CA681558CF11187E0A40B9FF68BC92D97D731F53AB74EC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5 798
TCP/UDP connections
9 391
DNS requests
34
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
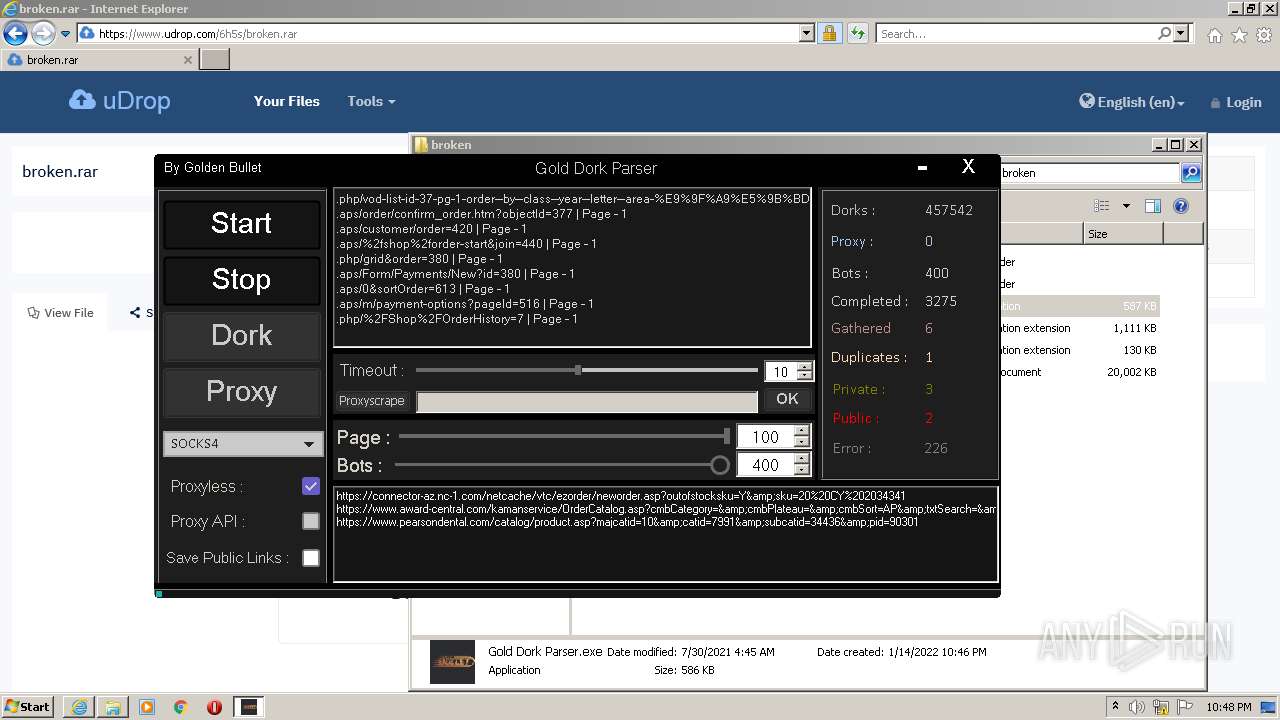
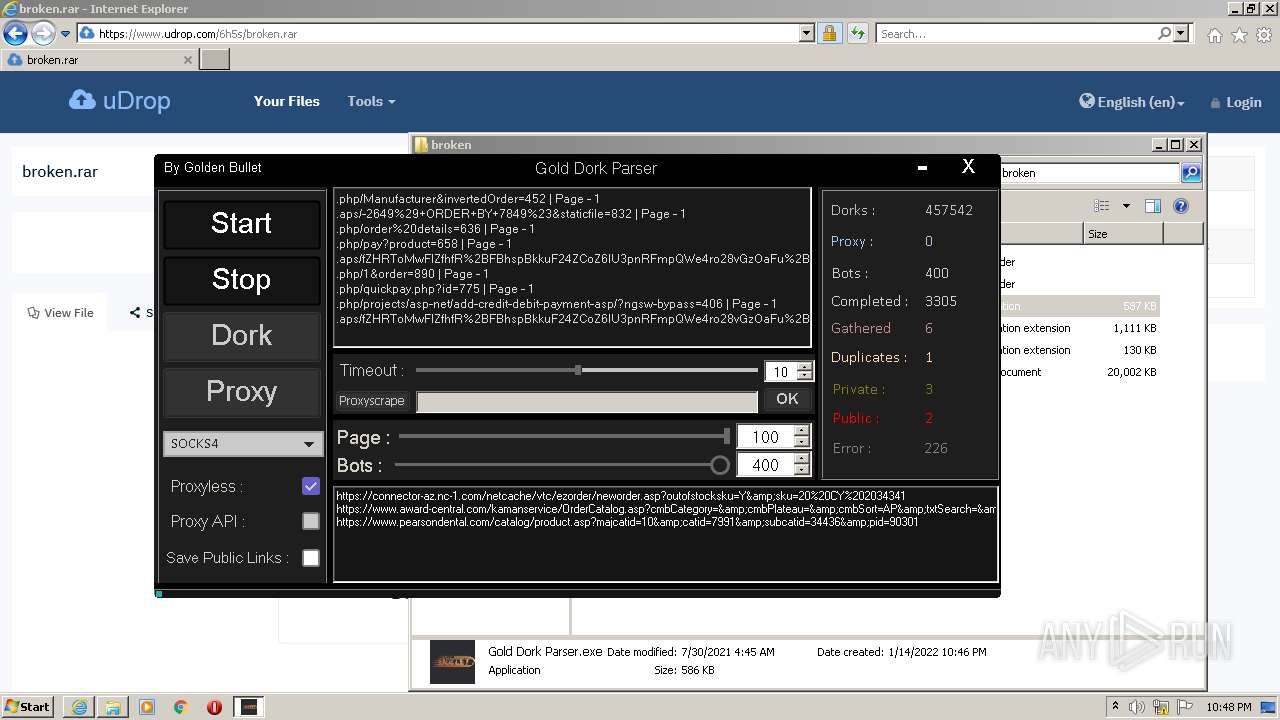
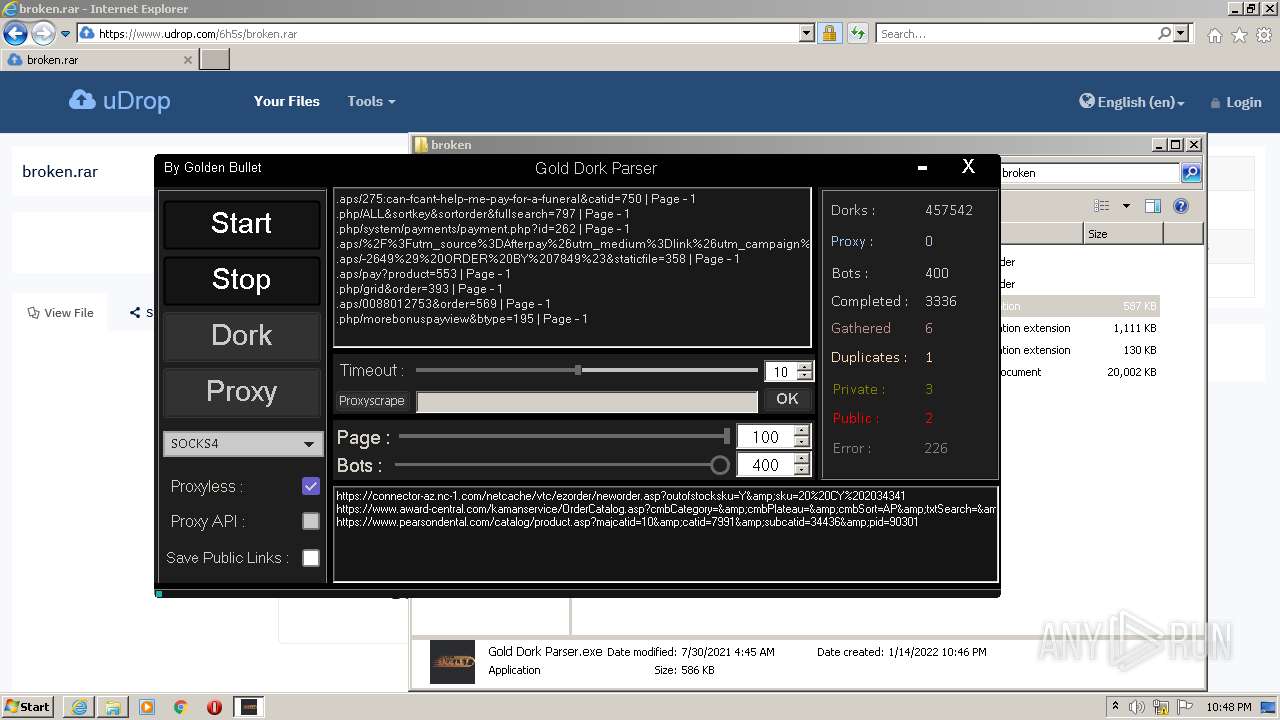
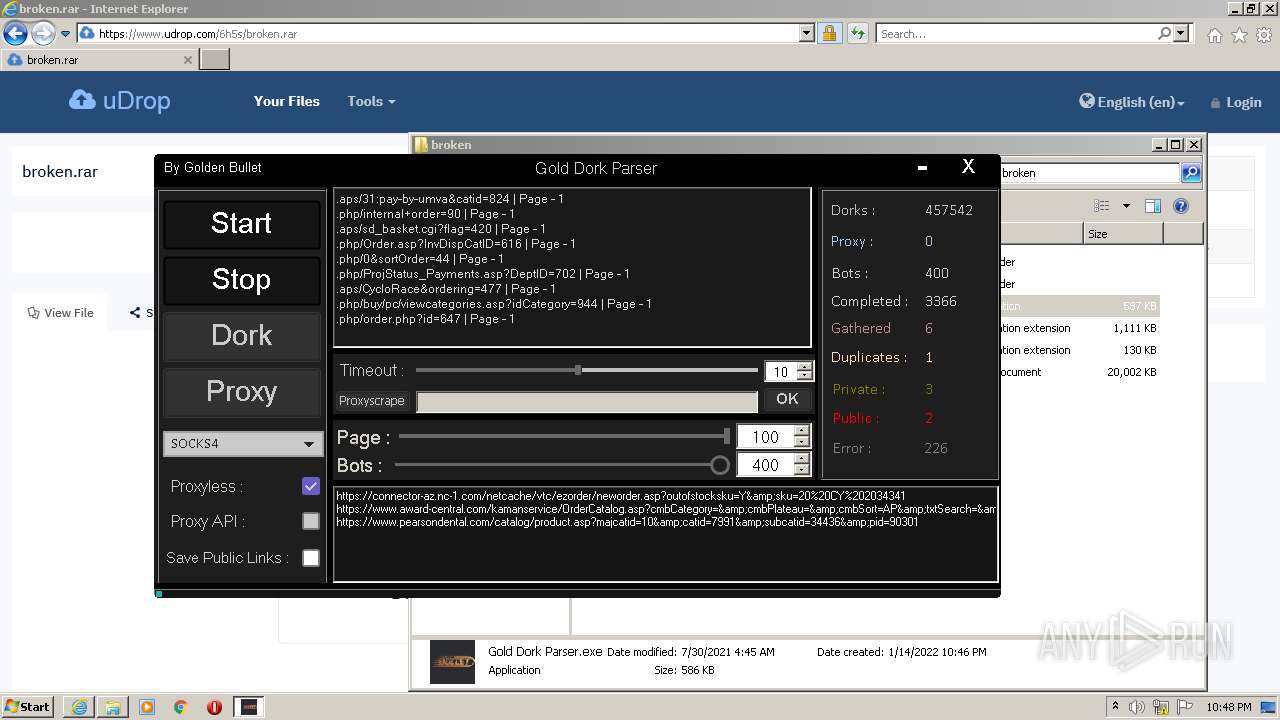
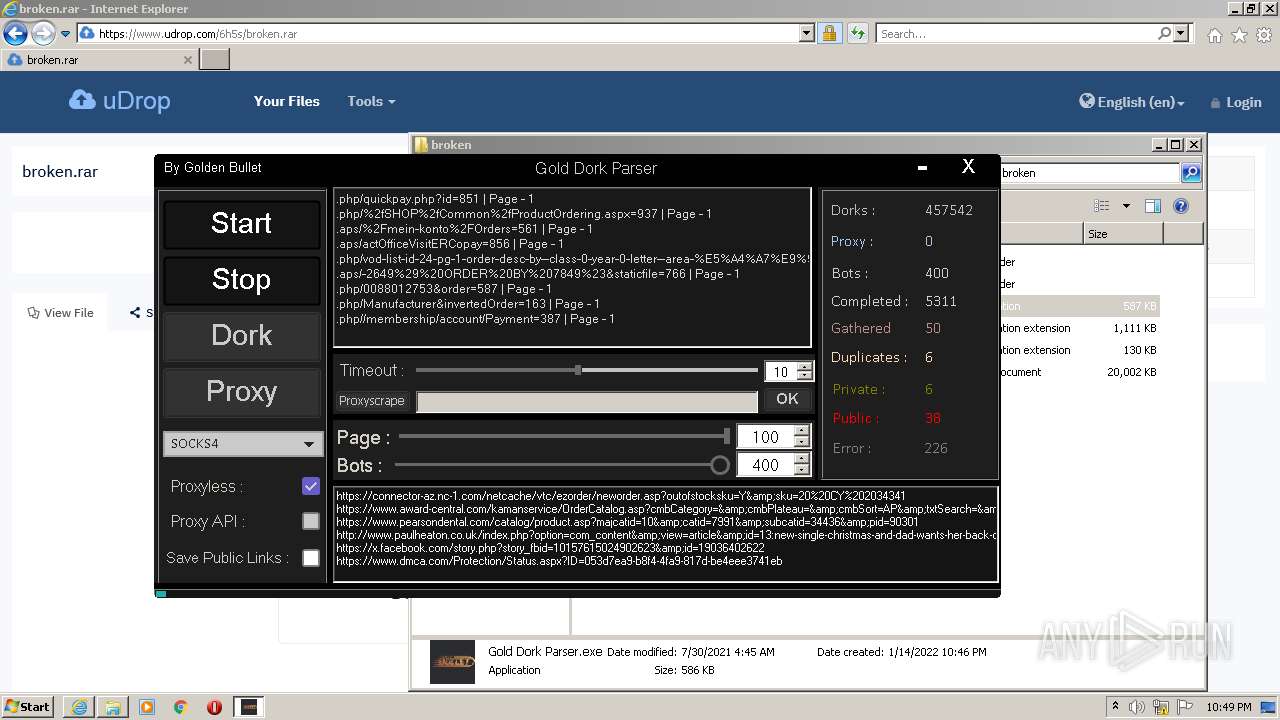
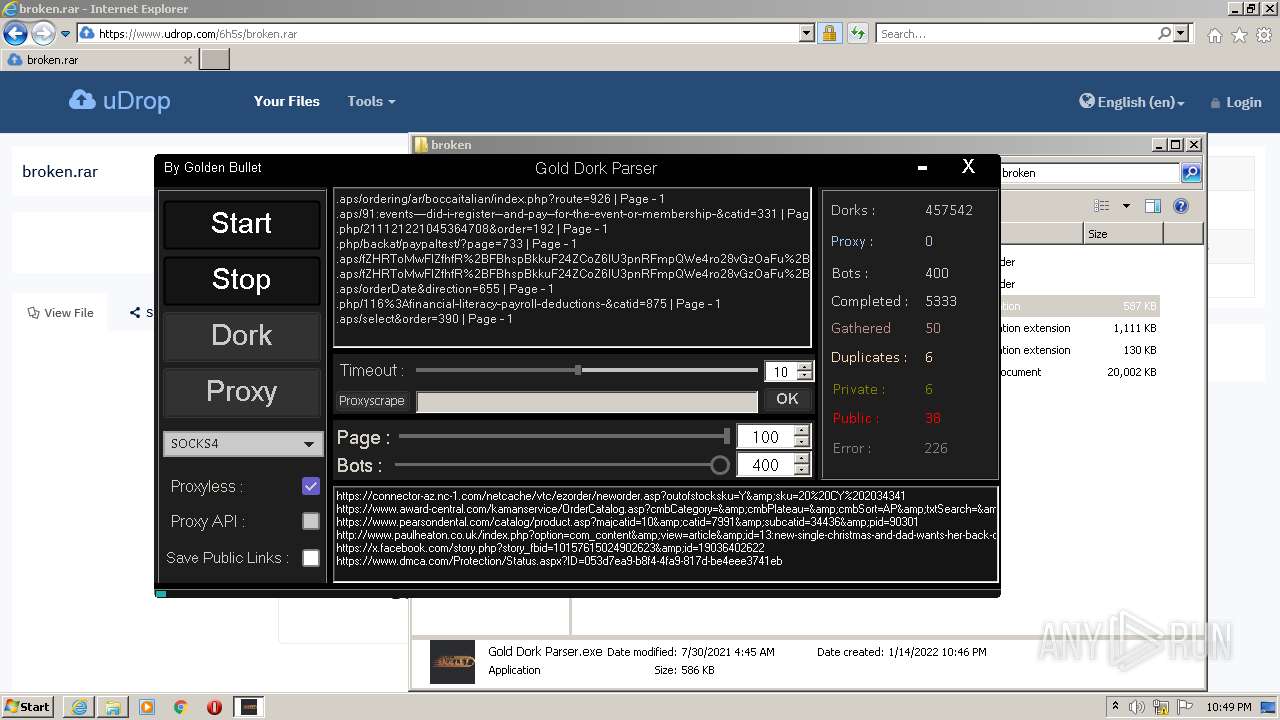
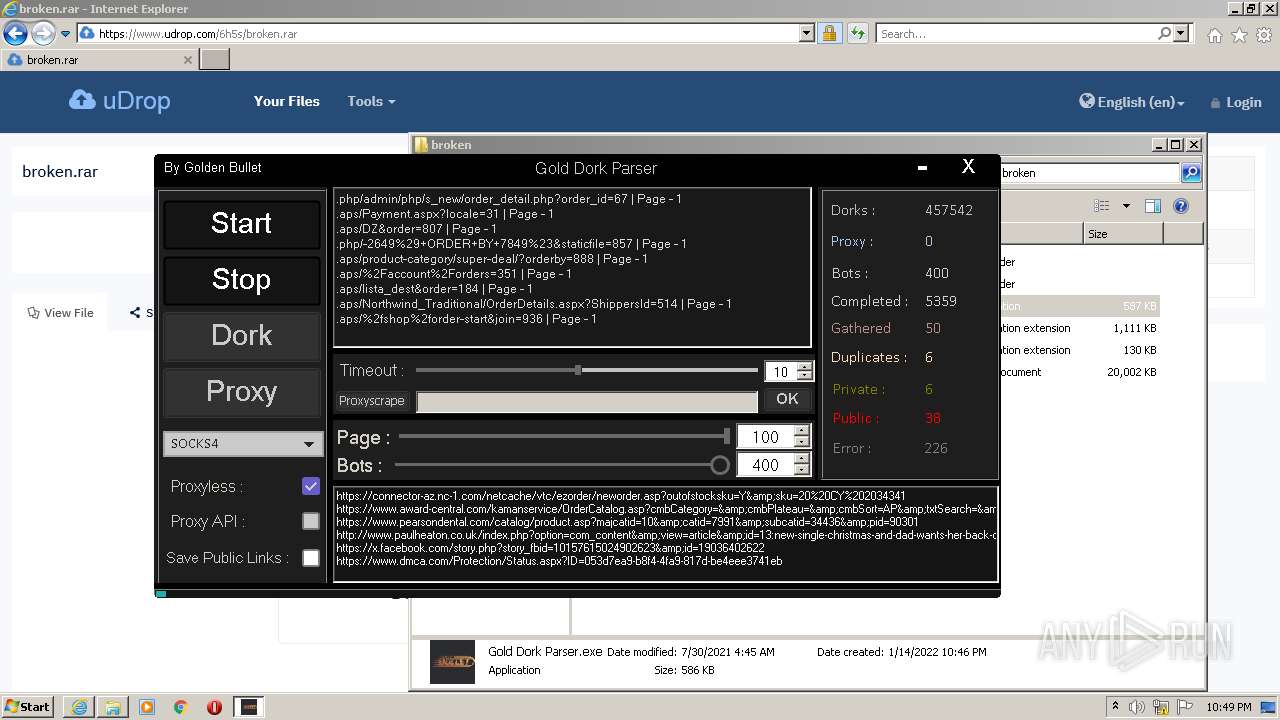
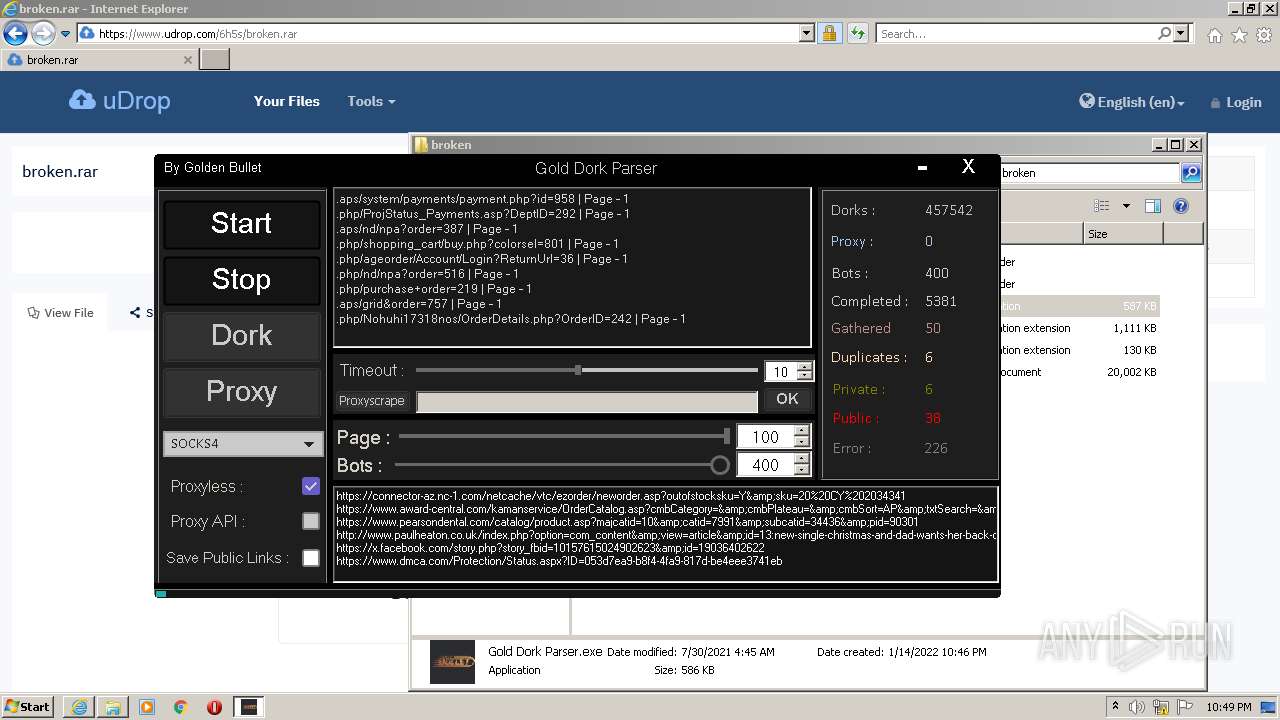
3168 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.php%2f83%26OrderBy%3d214&first=0&last=50&count=50 | US | — | — | whitelisted |
3168 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.php%2f5%26order_type%3d456&first=0&last=50&count=50 | US | — | — | whitelisted |
3168 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.aps%2forder%2fproducts.asp%3fKeyWord%3d880&first=0&last=50&count=50 | US | — | — | whitelisted |
3168 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.aps%2ffZHRToMwFIZfhfR%252BFBhspBkkuF24ZCoZ6IU3pnRFmpQWe4ro28vGzOaFu%252B5%252FvvP3OyugrexI1ttG7flHz8E6X61UQE4PCeqNIpqCAKJoy4FYRorsYUcC1yOd0VYzLZGTAXBjhVZrraBvuSm4%252BRSMP%252B93CWqs7YBgPAyDS61ba3NwmW5x0Yiq0pLbxgXQ%252BIgNcP5UlMjZjD2EokfiZZ5p07lg4UKghxqwBIyc7SZBb3FdRVEY16yOwmixXHpVHSwXfEHrOIjCMBpjAD3fKrBU2QQFXuDNvPnM90o%252FJoFP5vErcvLzr%252B6EOgj1fltBNYWA3JdlPpvKv3ADp%252BJjAKWro0hyWmyu1N7G0l%252BfKP3H3gpfcaclHXkcQdtNrqVg304mpR7WhlPLE%252BQjnE4jf4%252Bd%252FgA%253D%26RelayState%3d332&first=0&last=50&count=50 | US | — | — | whitelisted |
3168 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.aps%2f2694%253Apayments-to-201213-europa-league-clubs%26Itemid%3d584&first=0&last=50&count=50 | US | — | — | whitelisted |
3168 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.php%2f%252FOrder%252FBasket%3d57&first=0&last=50&count=50 | US | — | — | whitelisted |
3168 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.aps%2fpay%3fproduct%3d140&first=0&last=50&count=50 | US | — | — | whitelisted |
3168 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.php%2f%252FOrder%3d112&first=0&last=50&count=50 | US | — | — | whitelisted |
3168 | Gold Dork Parser.exe | GET | — | 204.79.197.200:80 | http://www.bing.com/search?q=.aps%2fsupplemental-training%2fmake-payment.php%3fpkIDm%3d863&first=0&last=50&count=50 | US | — | — | whitelisted |
3276 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3276 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 192.168.100.2:53 | — | — | — | whitelisted |
3856 | iexplore.exe | 65.103.40.169:443 | www.udrop.com | Qwest Communications Company, LLC | US | suspicious |
3856 | iexplore.exe | 2.16.106.186:80 | ctldl.windowsupdate.com | Akamai International B.V. | — | whitelisted |
— | — | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3276 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
3276 | iexplore.exe | 13.92.246.37:443 | query.prod.cms.msn.com | Microsoft Corporation | US | whitelisted |
3168 | Gold Dork Parser.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3276 | iexplore.exe | 65.103.40.169:443 | www.udrop.com | Qwest Communications Company, LLC | US | suspicious |
3276 | iexplore.exe | 104.89.38.104:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
www.udrop.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.godaddy.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3168 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3168 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3168 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3168 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3168 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3168 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3168 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3168 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3168 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |
3168 | Gold Dork Parser.exe | Potentially Bad Traffic | ET INFO Suspicious GET Request with Possible COVID-19 URI M1 |