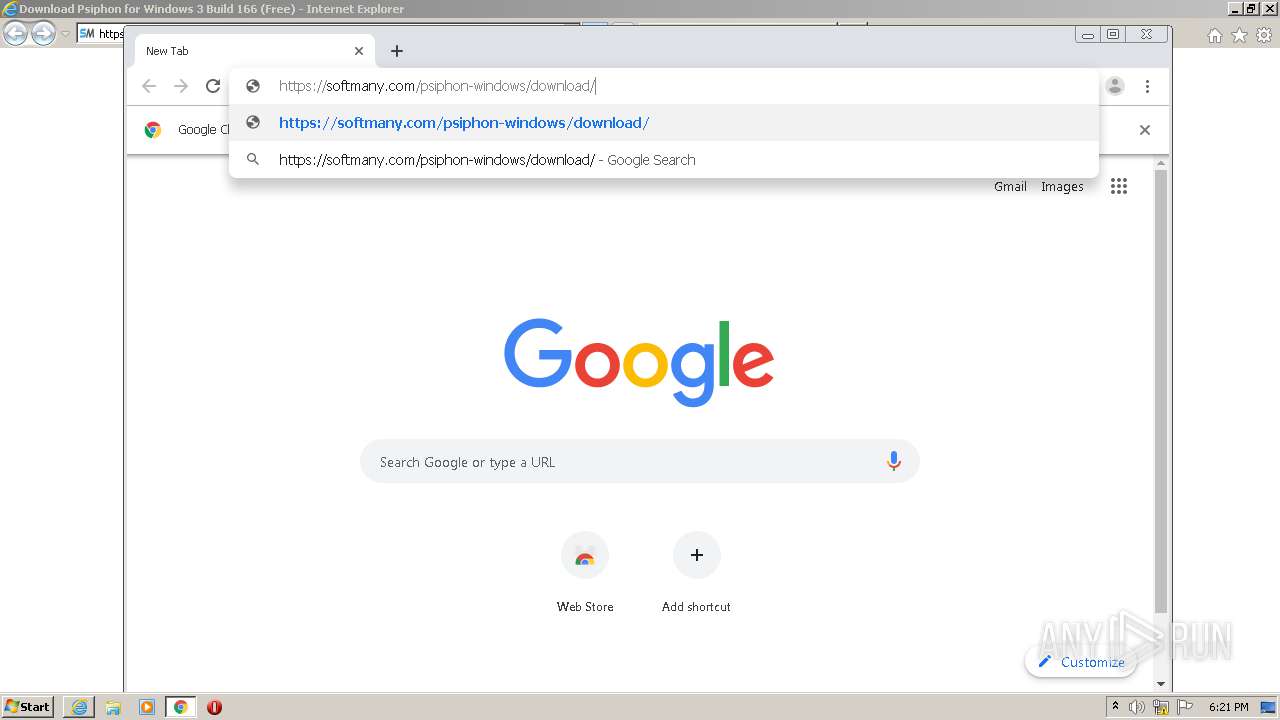
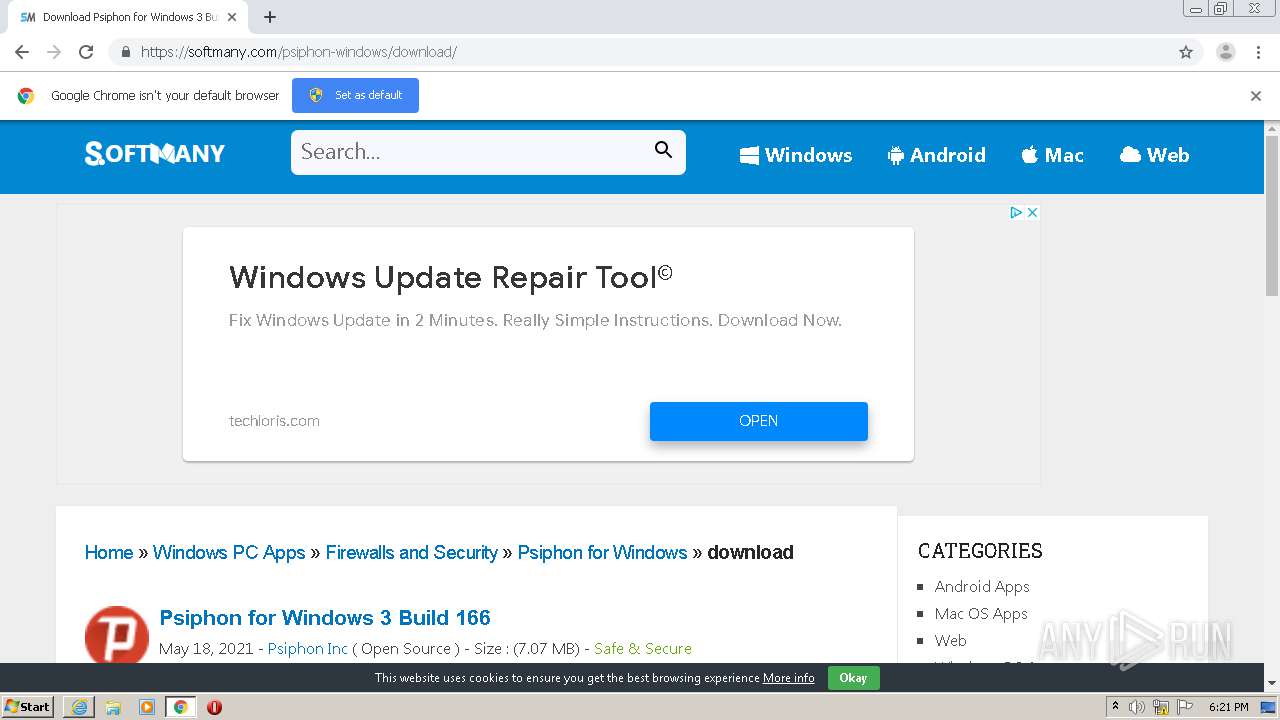
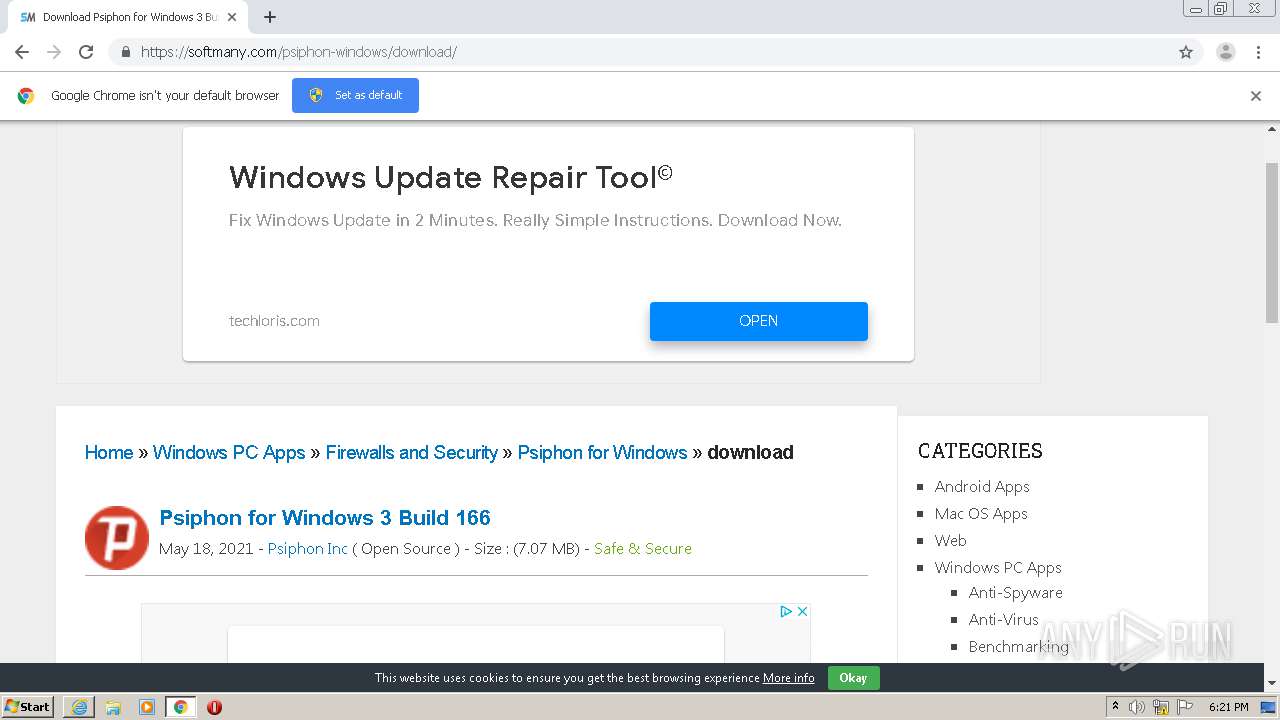
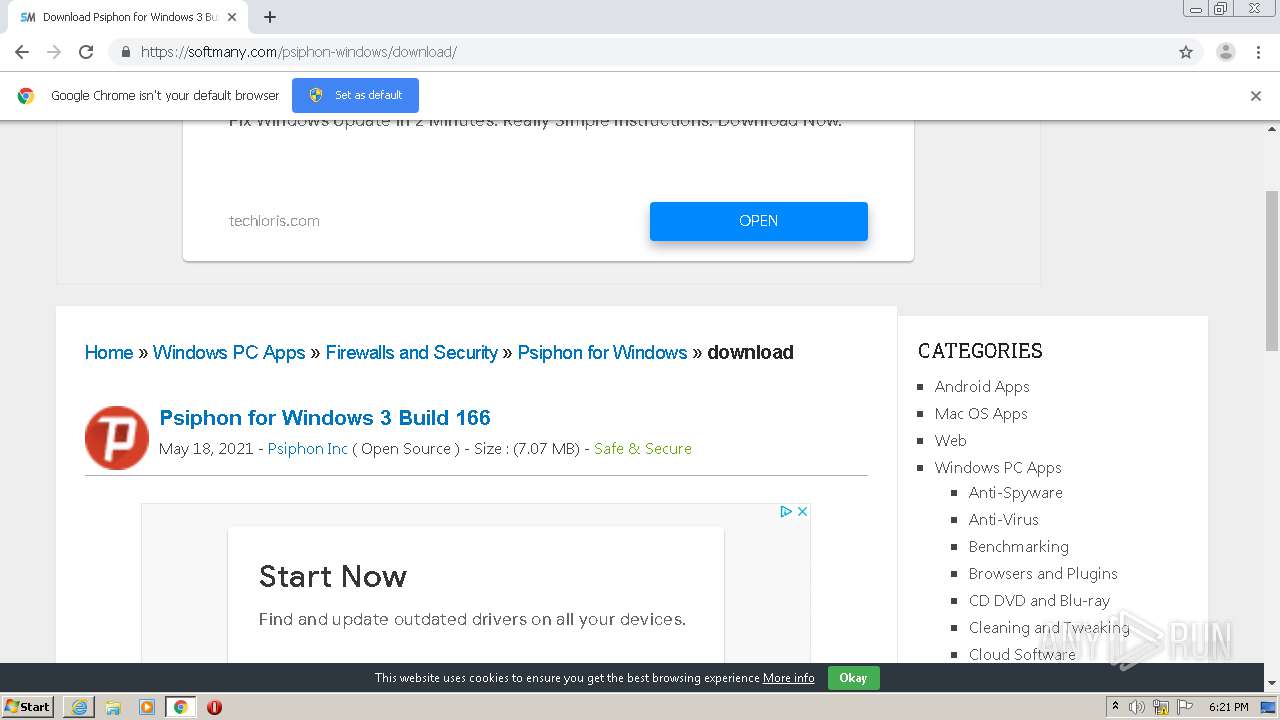
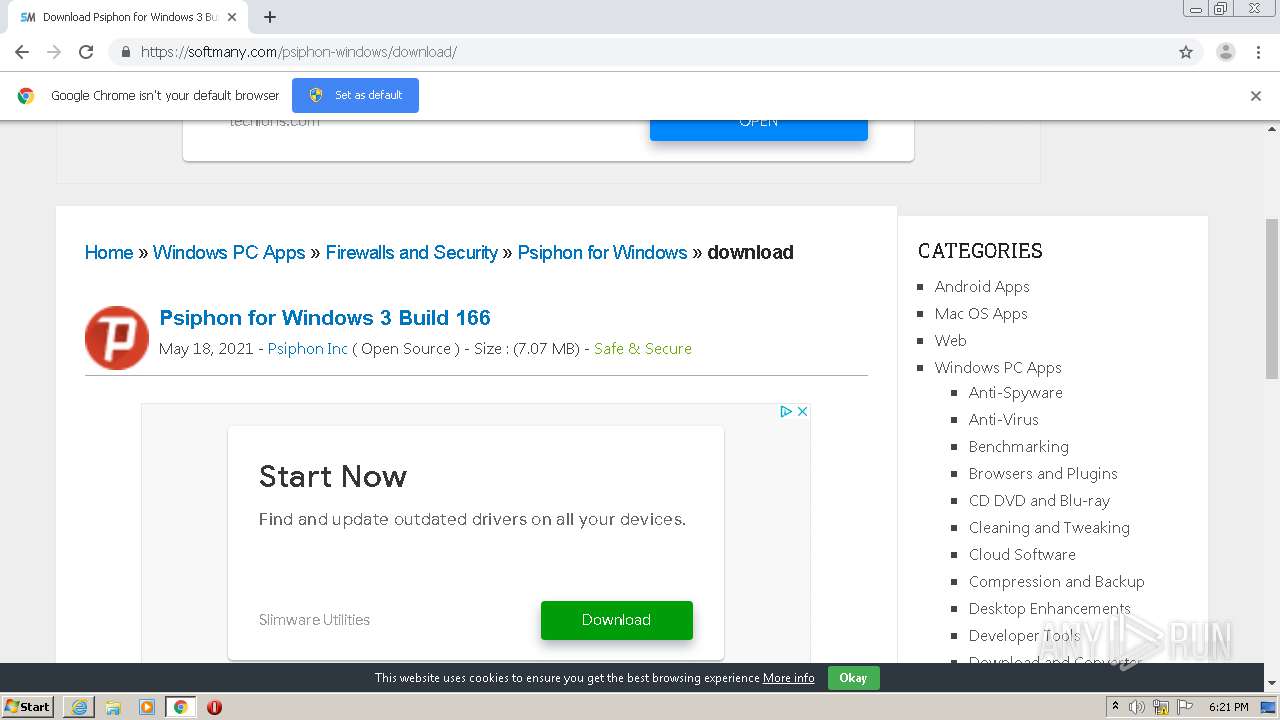
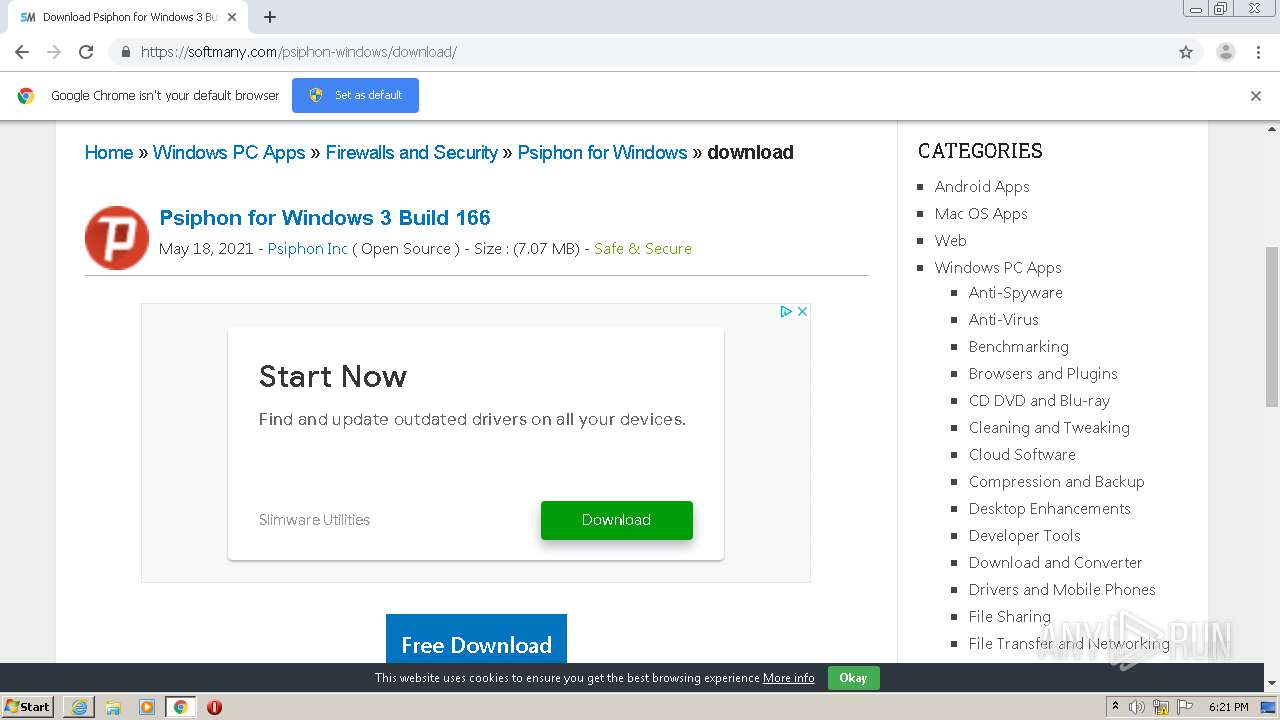
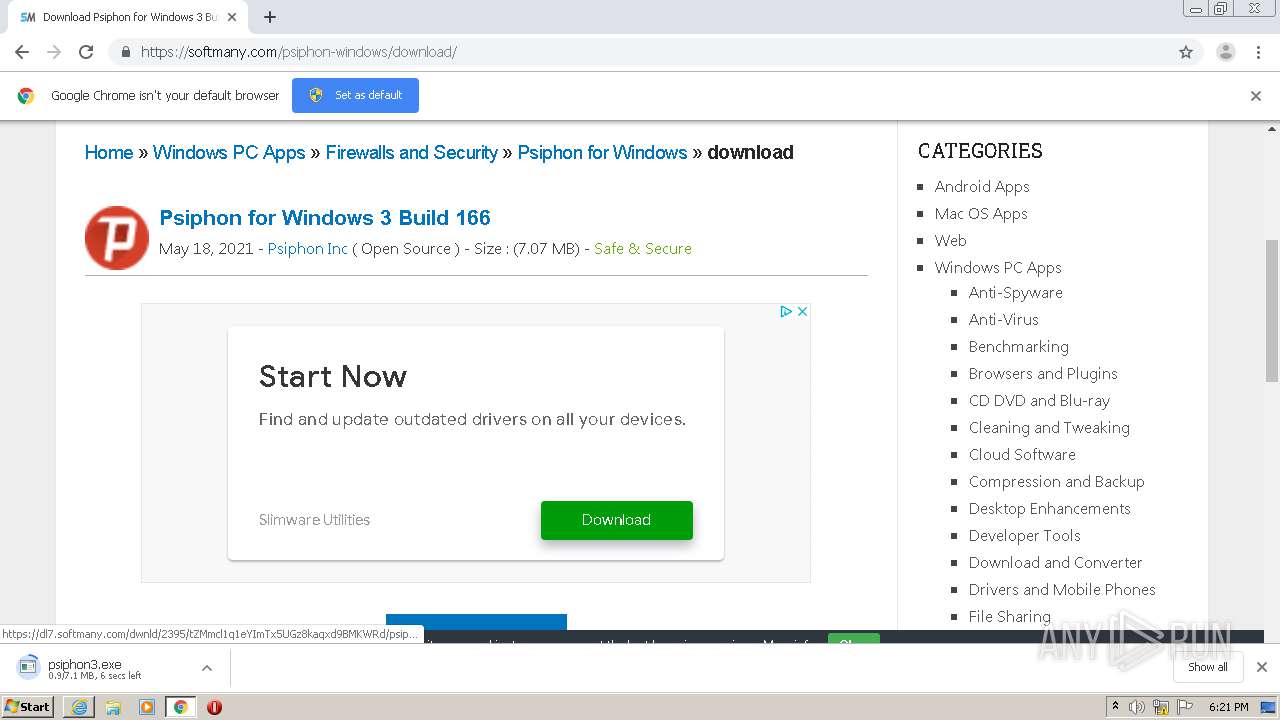
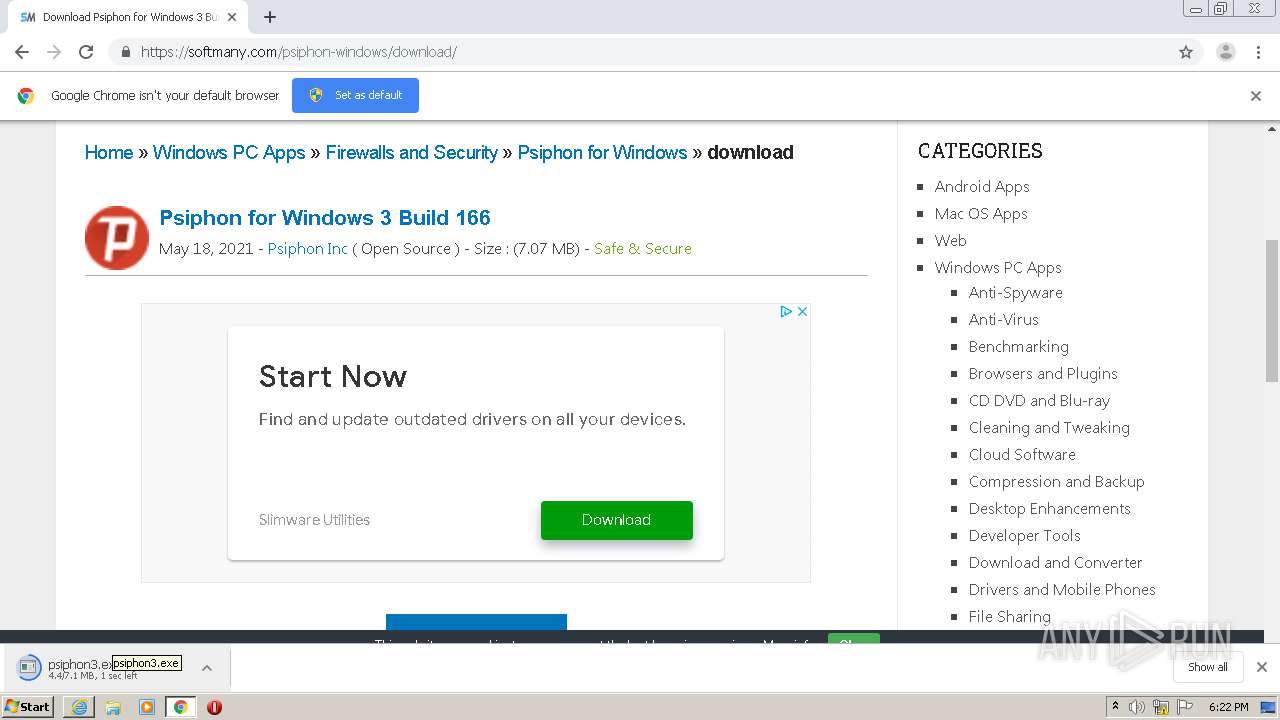
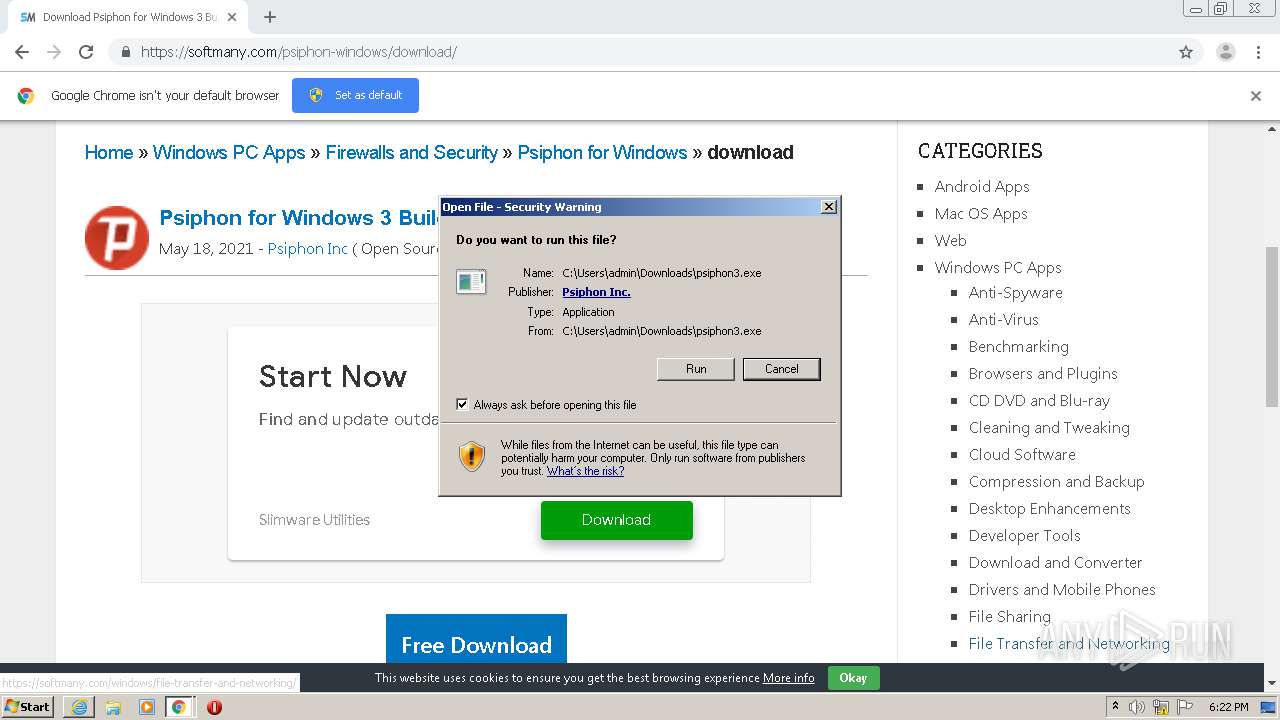
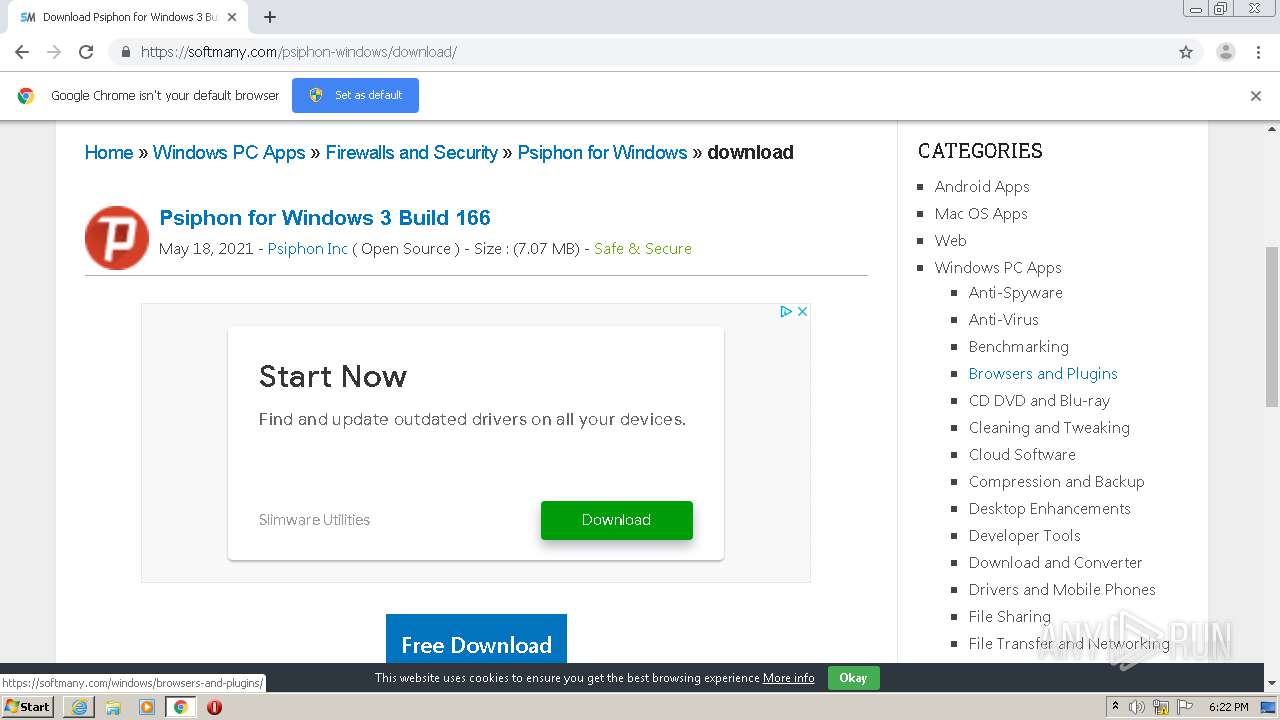
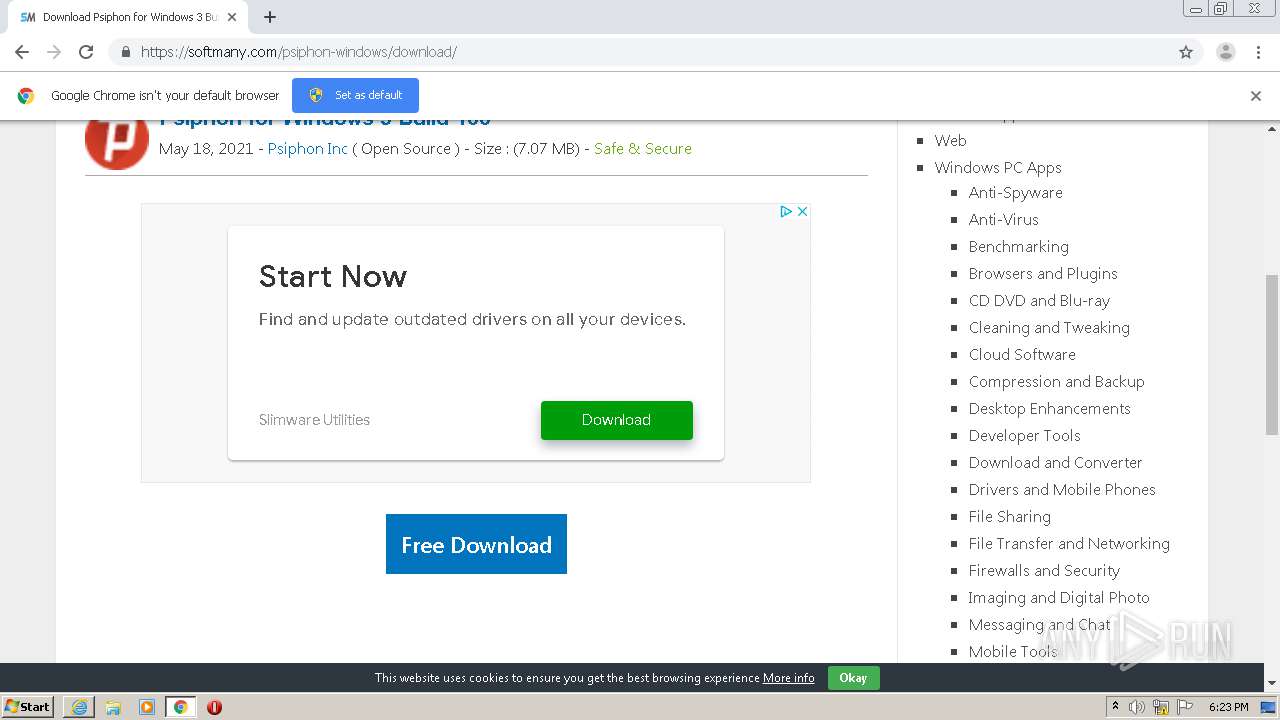
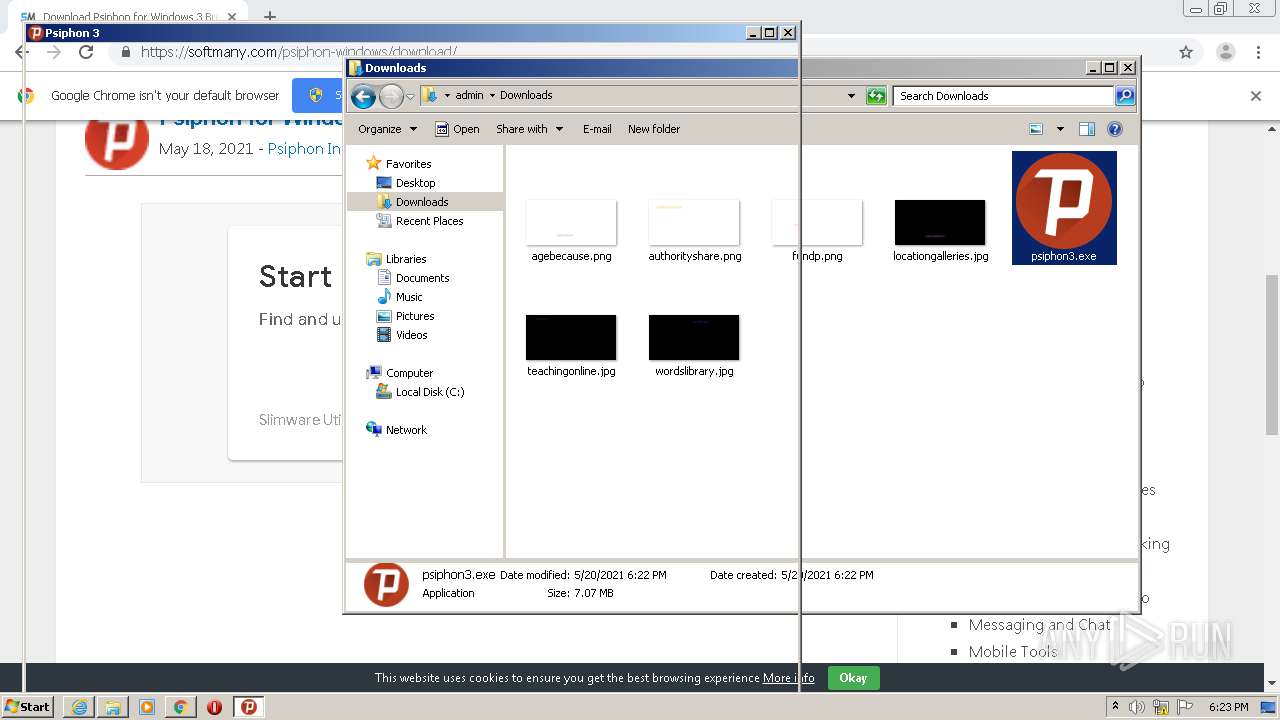
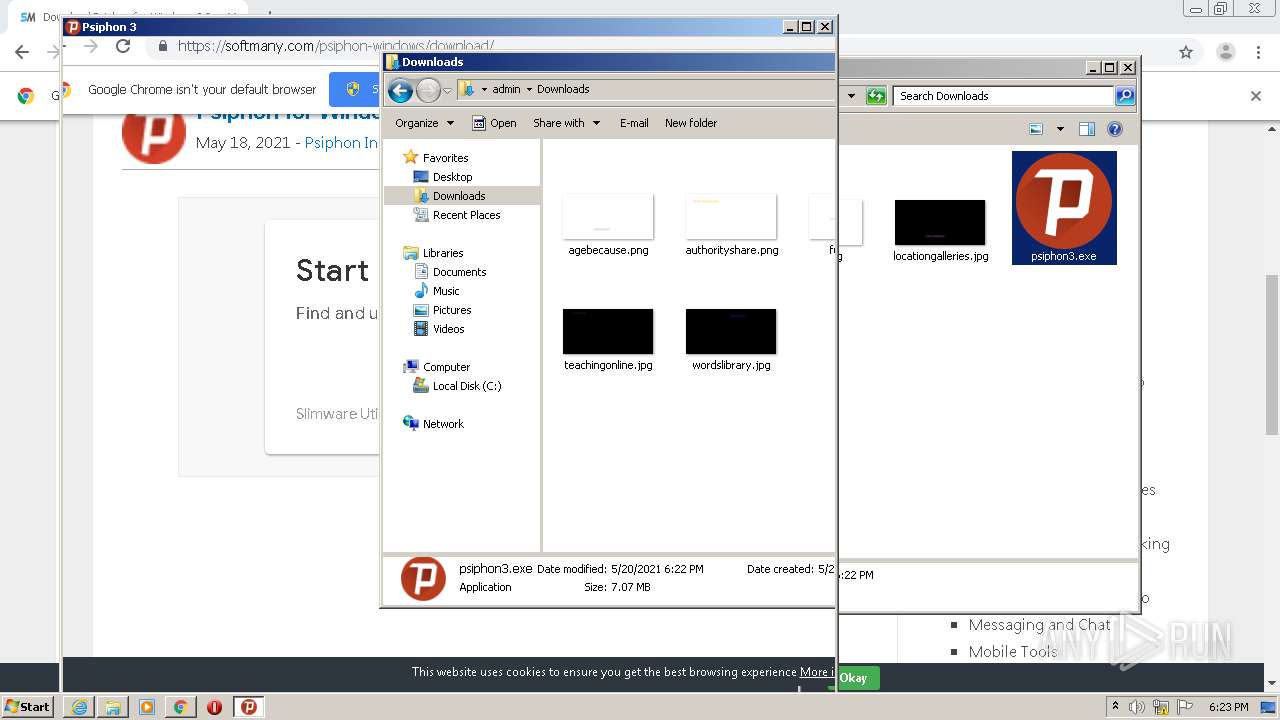
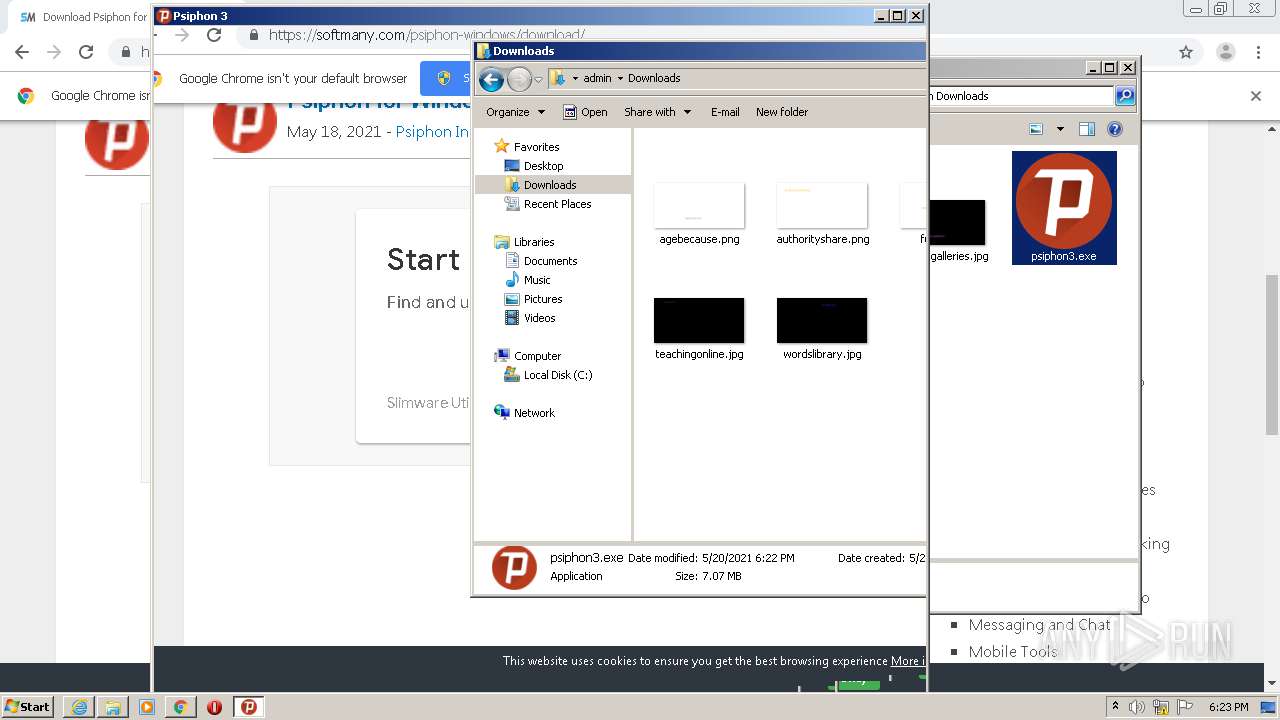
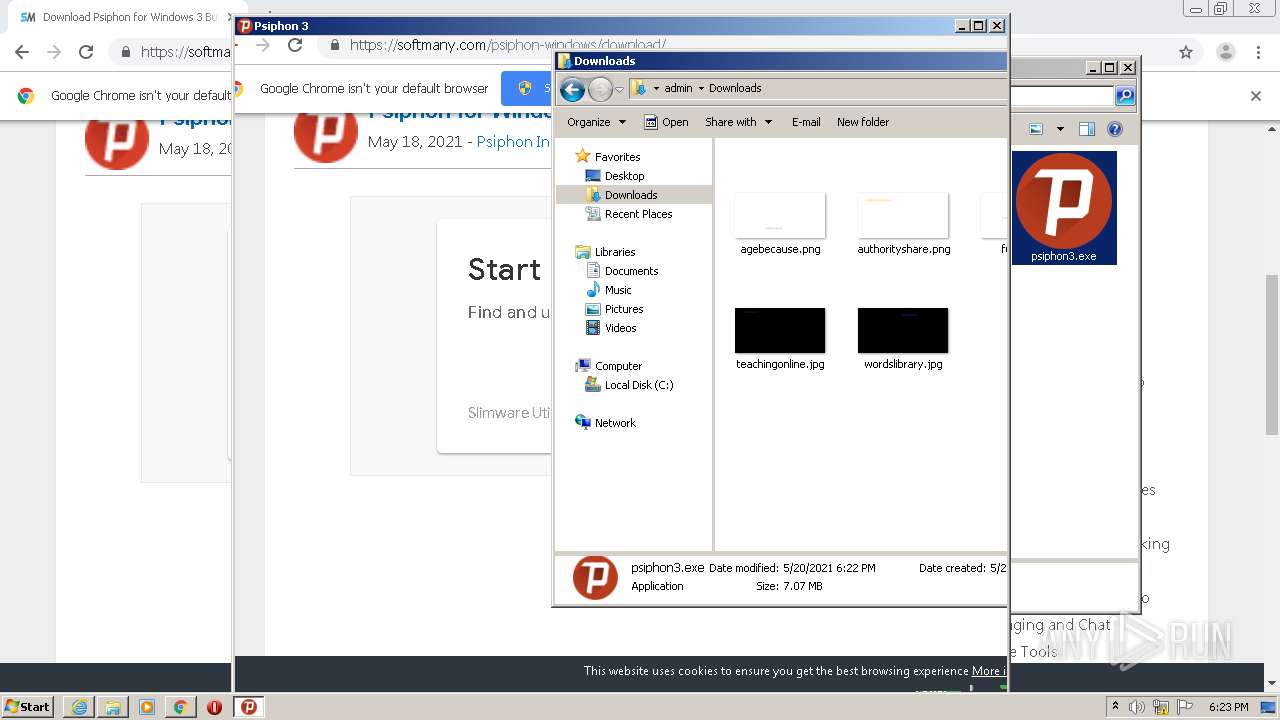
| URL: | https://softmany.com/psiphon-windows/download/ |
| Full analysis: | https://app.any.run/tasks/ee3d5984-a083-4aca-900d-4a74446a601c |
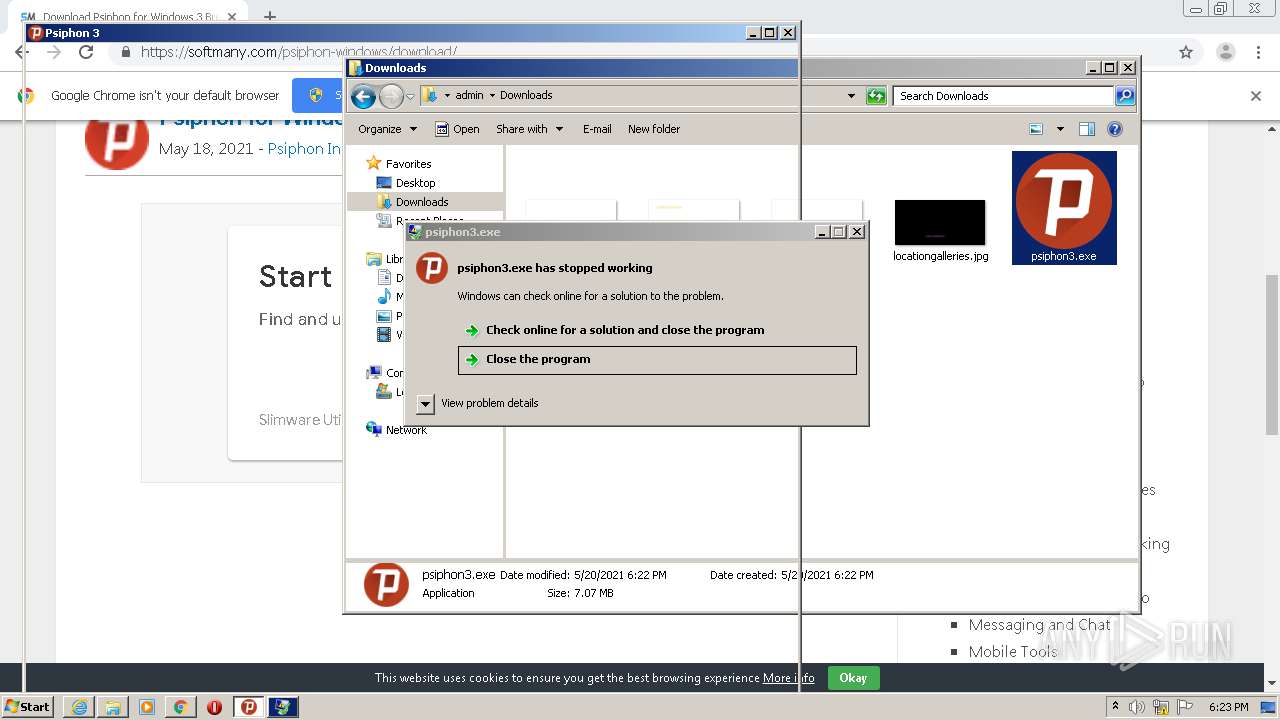
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2021, 17:20:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B9B6C57916D74F916272CBD4913C599F |
| SHA1: | C8F92E257B914C794FE7028ADF57BA789B9F852E |
| SHA256: | 170EF3295E2D5D6190807E76A4202894511B2D5C547E5695DF92DD6371692454 |
| SSDEEP: | 3:N8HPoLGKI5TLIDDTKLn:2v3yDGL |
MALICIOUS
Application was dropped or rewritten from another process
- psiphon3.exe (PID: 2752)
- psiphon3.exe (PID: 2248)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 3896)
- chrome.exe (PID: 3080)
Drops a file with a compile date too recent
- chrome.exe (PID: 3896)
- chrome.exe (PID: 3080)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3896)
Reads internet explorer settings
- psiphon3.exe (PID: 2752)
INFO
Application launched itself
- iexplore.exe (PID: 3952)
- chrome.exe (PID: 3896)
Reads settings of System Certificates
- iexplore.exe (PID: 3160)
- iexplore.exe (PID: 3952)
- chrome.exe (PID: 3896)
Changes internet zones settings
- iexplore.exe (PID: 3952)
Changes settings of System certificates
- iexplore.exe (PID: 3952)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3952)
Reads internet explorer settings
- iexplore.exe (PID: 3160)
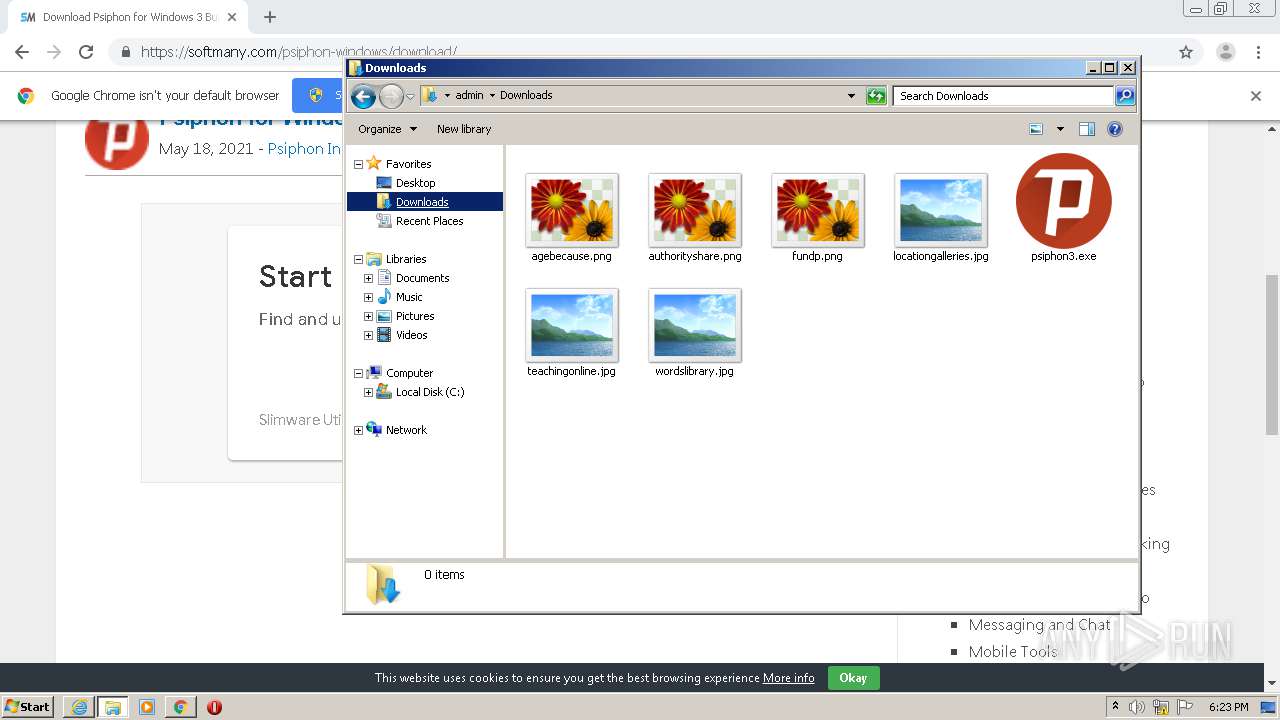
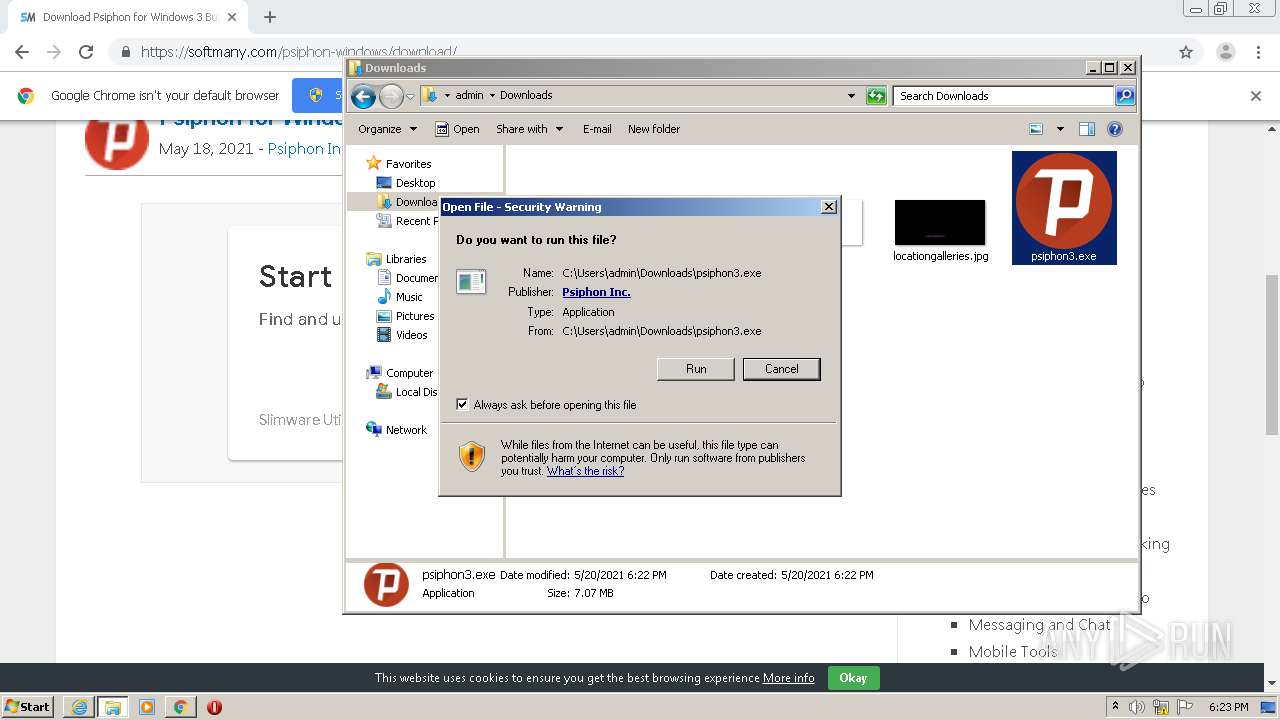
Manual execution by user
- chrome.exe (PID: 3896)
- explorer.exe (PID: 3660)
- psiphon3.exe (PID: 2248)
Reads the hosts file
- chrome.exe (PID: 3896)
- chrome.exe (PID: 3080)
Creates files in the user directory
- iexplore.exe (PID: 3952)
- iexplore.exe (PID: 3160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
44
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17338100776544943615,13404262239750894955,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15466287488838531294 --mojo-platform-channel-handle=4564 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17338100776544943615,13404262239750894955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9602038056217788618 --mojo-platform-channel-handle=3232 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17338100776544943615,13404262239750894955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17253300831407626193 --mojo-platform-channel-handle=4520 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17338100776544943615,13404262239750894955,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1805066206531160284 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3488 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17338100776544943615,13404262239750894955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15397657216958515870 --mojo-platform-channel-handle=3012 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17338100776544943615,13404262239750894955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1530149179314191680 --mojo-platform-channel-handle=3404 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6ef1a9d0,0x6ef1a9e0,0x6ef1a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2200 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,17338100776544943615,13404262239750894955,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1467652232973233752 --renderer-client-id=36 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4592 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1040,17338100776544943615,13404262239750894955,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10360331437449107081 --mojo-platform-channel-handle=2864 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2248 | "C:\Users\admin\Downloads\psiphon3.exe" | C:\Users\admin\Downloads\psiphon3.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
Total events
1 953
Read events
1 622
Write events
323
Delete events
8
Modification events
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3160) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\LowCache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2187584096 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30887324 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
5
Suspicious files
122
Text files
326
Unknown types
49
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab368C.tmp | — | |
MD5:— | SHA256:— | |||
| 3160 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar368D.tmp | — | |
MD5:— | SHA256:— | |||
| 3160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\download[1].htm | html | |
MD5:06E397CCF97F5563FE1BB268C0BE6D50 | SHA256:E5ECB113BCC9448E25F3FCB5975066A12DA9C3F0B3447DA0458F1115C143B33E | |||
| 3160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\MSIMGSIZ.DAT | smt | |
MD5:1E25A85557B3DC809B76007D4C3285D0 | SHA256:E4F358766C5F96D59B9722A12FA04D4272E6DF1778EE115F7A6DE840282F003B | |||
| 3160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:EB9738CC12ED22DAA90F2F44A4EE6A7F | SHA256:2902436D4D4064E7DC1BC405F5CF44067F738A3F2F338F255F4179B2F3317879 | |||
| 3160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:8CC55FA670A7F461764B67604533F7CE | SHA256:07FE00F2F840C062FD13D10AFAA640487B0D6762CC52A87C1A433F76786781EF | |||
| 3160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\jquery.min[1].js | text | |
MD5:B6F7093369A0E8B83703914CE731B13C | SHA256:60240D5A27EDE94FD35FEA44BD110B88C7D8CFC08127F032D13B0C622B8BE827 | |||
| 3160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | binary | |
MD5:3F89F213F85955552052C1AE30B56B02 | SHA256:5AADD5B03A2EFFCBD78C08E903F6077316CD5FD993676F403EE79125A8E4C818 | |||
| 3160 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\lazy_placeholder[1].gif | image | |
MD5:D89746888DA2D9510B64A9F031EAECD5 | SHA256:EF1955AE757C8B966C83248350331BD3A30F658CED11F387F8EBF05AB3368629 | |||
| 3160 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | der | |
MD5:EEAB28491F6C5D9FC13DD59C1909BC27 | SHA256:8BB83D1796BA1AE6C8965B37DAB85DC68EBA4DAAAA891B375BDD8FEF7AAE7788 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
132
DNS requests
67
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3160 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCyLOF%2BWIn0QAMAAAAAzA6w | US | der | 472 b | whitelisted |
3160 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3160 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3952 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
3080 | chrome.exe | GET | 302 | 142.250.184.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 519 b | whitelisted |
3160 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQCyLOF%2BWIn0QAMAAAAAzA6w | US | der | 472 b | whitelisted |
3080 | chrome.exe | GET | 200 | 173.194.135.102:80 | http://r1---sn-aigzrn7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=46.244.28.133&mm=28&mn=sn-aigzrn7z&ms=nvh&mt=1621530977&mv=m&mvi=1&pl=24&shardbypass=yes | US | crx | 242 Kb | whitelisted |
3160 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEAMIci25scQVCgAAAADOU6Y%3D | US | der | 471 b | whitelisted |
3160 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEBaL4OfTp%2BeHAwAAAADL91k%3D | US | der | 471 b | whitelisted |
3160 | iexplore.exe | GET | 200 | 142.250.185.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCED3Gqd238XeICgAAAADOUNY%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3160 | iexplore.exe | 142.250.184.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3952 | iexplore.exe | 104.21.75.195:443 | softmany.com | Cloudflare Inc | US | unknown |
3160 | iexplore.exe | 104.21.75.195:443 | softmany.com | Cloudflare Inc | US | unknown |
3160 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3160 | iexplore.exe | 172.217.3.238:443 | www.google-analytics.com | Google Inc. | US | unknown |
3160 | iexplore.exe | 104.16.18.94:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
3160 | iexplore.exe | 142.250.185.194:443 | pagead2.googlesyndication.com | Google Inc. | US | suspicious |
3160 | iexplore.exe | 142.250.185.99:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3160 | iexplore.exe | 142.250.185.234:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3160 | iexplore.exe | 199.232.192.134:443 | softmany.disqus.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
softmany.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
softmany.disqus.com |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |