| File name: | 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader |
| Full analysis: | https://app.any.run/tasks/68006c24-e63e-4202-9b77-22ab79cb6e3d |
| Verdict: | Malicious activity |
| Analysis date: | May 28, 2025, 02:41:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 5A1617C0106BE0B52D441045841B8EC0 |
| SHA1: | 05B7768EE5274720E297BE423526EF7CD4FB8C79 |
| SHA256: | 170BE4EE3F10B30982F06B3B5962612C65DC9B942019DBDF77899EAB08C8C750 |
| SSDEEP: | 98304:zSYpVEm5sn6gNEkdfaTgmHihuRB3FKFfpRBVnf9D0ks+Zo8Y1F2qaVhKffn7YAxY:taABb/3utAkVZv2bxSfKlUcLdK |
MALICIOUS
Executing a file with an untrusted certificate
- 1984362017.exe (PID: 3176)
CANBIS mutex has been found
- 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe (PID: 3096)
SUSPICIOUS
Reads security settings of Internet Explorer
- 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe (PID: 3096)
Executable content was dropped or overwritten
- 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe (PID: 3096)
- 1984362017.exe (PID: 3176)
Process drops legitimate windows executable
- 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe (PID: 3096)
- 1984362017.exe (PID: 3176)
Starts a Microsoft application from unusual location
- 1984362017.exe (PID: 3176)
There is functionality for communication over UDP network (YARA)
- 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe (PID: 3096)
Searches for installed software
- 1984362017.exe (PID: 3176)
INFO
Reads the computer name
- 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe (PID: 3096)
- 1984362017.exe (PID: 3176)
Checks supported languages
- 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe (PID: 3096)
- 1984362017.exe (PID: 3176)
The sample compiled with english language support
- 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe (PID: 3096)
- 1984362017.exe (PID: 3176)
Process checks computer location settings
- 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe (PID: 3096)
Failed to create an executable file in Windows directory
- 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe (PID: 3096)
Create files in a temporary directory
- 1984362017.exe (PID: 3176)
Checks proxy server information
- slui.exe (PID: 1132)
Reads the software policy settings
- slui.exe (PID: 1132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (57.2) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (38.8) |
| .exe | | | Win32 Executable Delphi generic (1.2) |
| .scr | | | Windows screen saver (1.1) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 46080 |
| InitializedDataSize: | 7680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc254 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
122
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
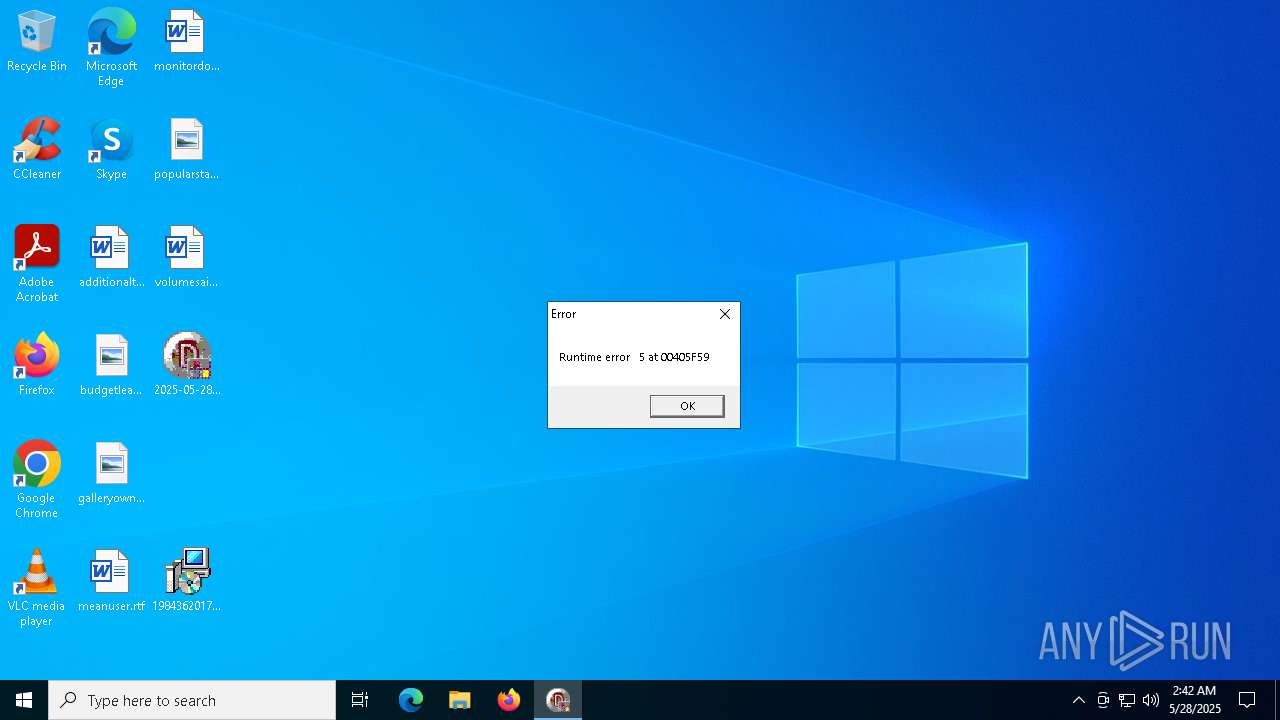
| 3096 | "C:\Users\admin\Desktop\2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe" | C:\Users\admin\Desktop\2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 5 Modules
| |||||||||||||||
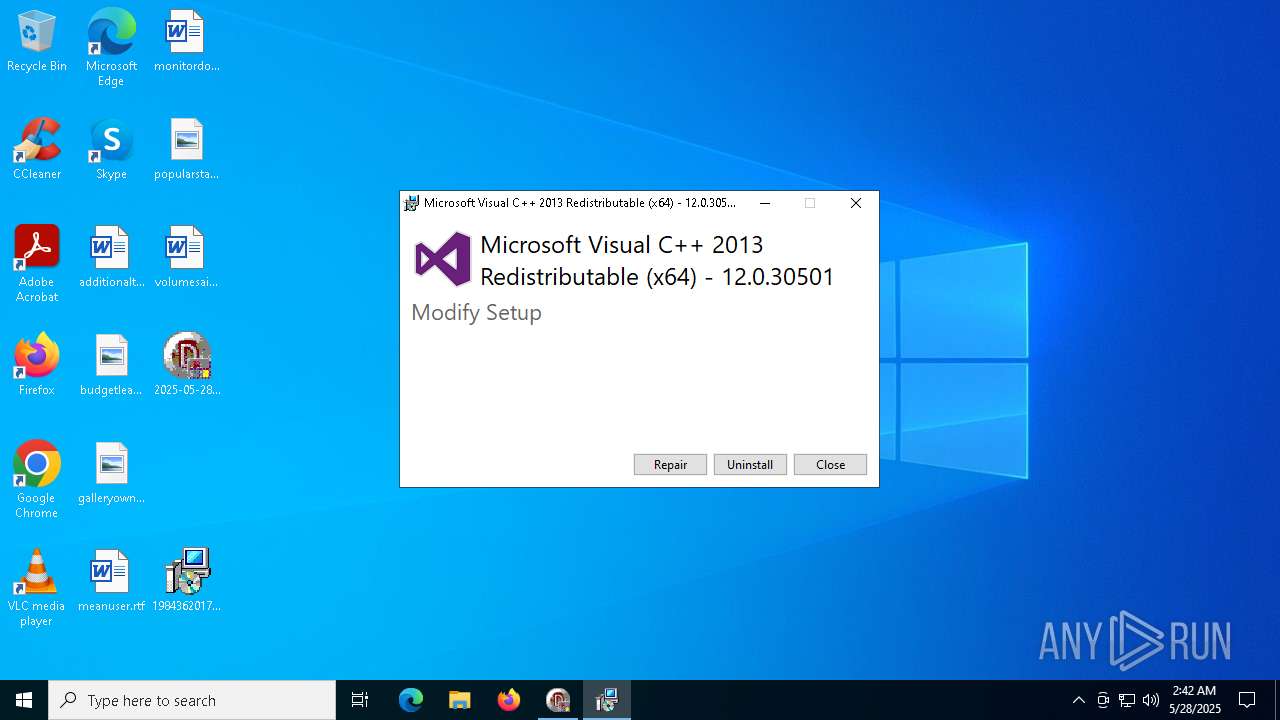
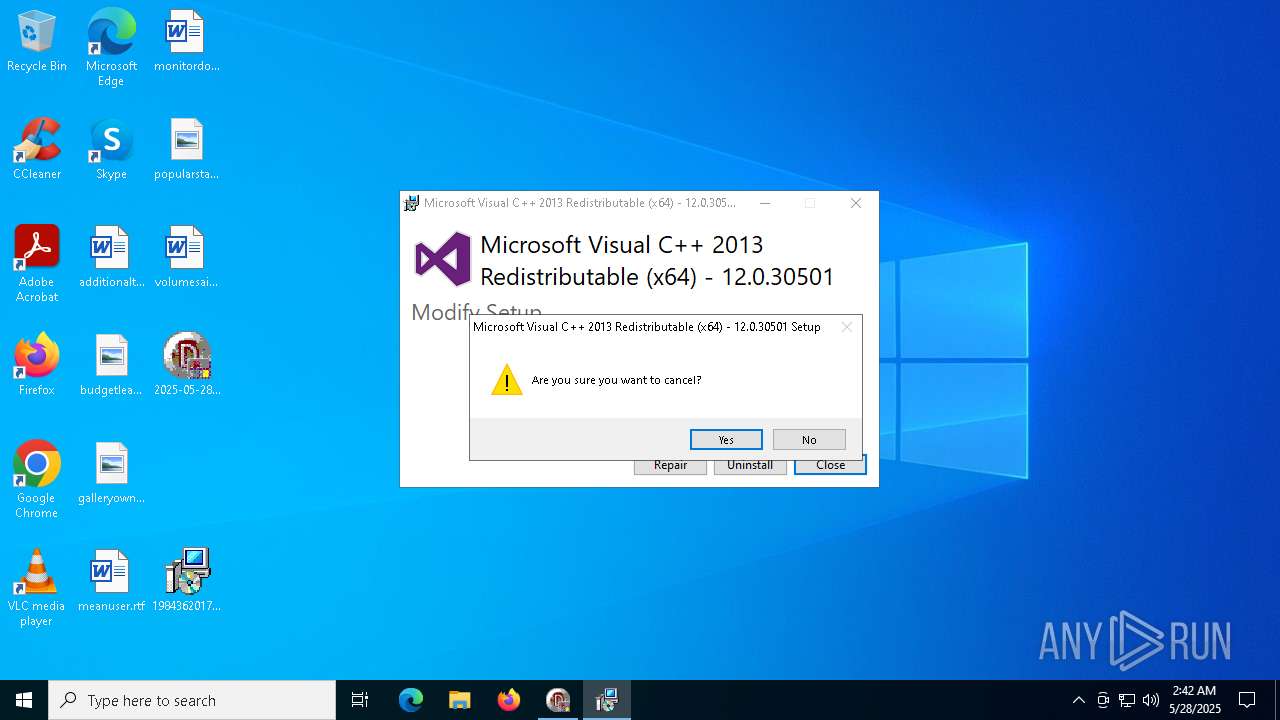
| 3176 | "C:\Users\admin\Desktop\1984362017.exe" | C:\Users\admin\Desktop\1984362017.exe | 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Visual C++ 2013 Redistributable (x64) - 12.0.30501 Exit code: 1602 Version: 12.0.30501.0 Modules
| |||||||||||||||
Total events
4 066
Read events
4 066
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3176 | 1984362017.exe | C:\Users\admin\AppData\Local\Temp\{050d4fc8-5d48-4b8f-8972-47c82c46020f}\.ba1\thm.xml | xml | |
MD5:0056F10A42638EA8B4BEFC614741DDD6 | SHA256:6B1BA0DEA830E556A58C883290FAA5D49C064E546CBFCD0451596A10CC693F87 | |||
| 3096 | 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe | C:\Users\admin\Desktop\1984362017.exe | executable | |
MD5:96B61B8E069832E6B809F24EA74567BA | SHA256:E554425243E3E8CA1CD5FE550DB41E6FA58A007C74FAD400274B128452F38FB8 | |||
| 3176 | 1984362017.exe | C:\Users\admin\AppData\Local\Temp\{050d4fc8-5d48-4b8f-8972-47c82c46020f}\.ba1\logo.png | image | |
MD5:D6BD210F227442B3362493D046CEA233 | SHA256:335A256D4779EC5DCF283D007FB56FD8211BBCAF47DCD70FE60DED6A112744EF | |||
| 3096 | 2025-05-28_5a1617c0106be0b52d441045841b8ec0_amadey_black-basta_elex_gcleaner_hijackloader_smoke-loader.exe | C:\Users\admin\Desktop\6507532887.exe | executable | |
MD5:5A1617C0106BE0B52D441045841B8EC0 | SHA256:170BE4EE3F10B30982F06B3B5962612C65DC9B942019DBDF77899EAB08C8C750 | |||
| 3176 | 1984362017.exe | C:\Users\admin\AppData\Local\Temp\{050d4fc8-5d48-4b8f-8972-47c82c46020f}\.ba1\BootstrapperApplicationData.xml | xml | |
MD5:0BD4FA44198EB101D1F070BB99A12C0B | SHA256:54BF9F4BC4ADCBBA99AEF3C048522C23822D3DDAB51891DCBA3B6F59192A2B28 | |||
| 3176 | 1984362017.exe | C:\Users\admin\AppData\Local\Temp\{050d4fc8-5d48-4b8f-8972-47c82c46020f}\.ba1\license.rtf | text | |
MD5:1E47EE7B71B22488068343DF4CE30534 | SHA256:8518F0420972C1DBE8A323FFC6F57863AF0B80C6A3B27FD0C6FC9BDABB7E2D13 | |||
| 3176 | 1984362017.exe | C:\Users\admin\AppData\Local\Temp\{050d4fc8-5d48-4b8f-8972-47c82c46020f}\.ba1\wixstdba.dll | executable | |
MD5:A52E5220EFB60813B31A82D101A97DCB | SHA256:E7C8E7EDD9112137895820E789BAAAECA41626B01FB99FEDE82968DDB66D02CF | |||
| 3176 | 1984362017.exe | C:\Users\admin\AppData\Local\Temp\dd_vcredist_amd64_20250528024206.log | text | |
MD5:67CC105FB0997A563F4C9A0DFC596F52 | SHA256:D97AA103C607542EDBF82F856791F2AAB7D65EBBC6C95D9C29DA28E7395268B0 | |||
| 3176 | 1984362017.exe | C:\Users\admin\AppData\Local\Temp\{050d4fc8-5d48-4b8f-8972-47c82c46020f}\.ba1\thm.wxl | xml | |
MD5:FBFCBC4DACC566A3C426F43CE10907B6 | SHA256:70400F181D00E1769774FF36BCD8B1AB5FBC431418067D31B876D18CC04EF4CE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
18
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5304 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1132 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
uk.undernet.org |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |