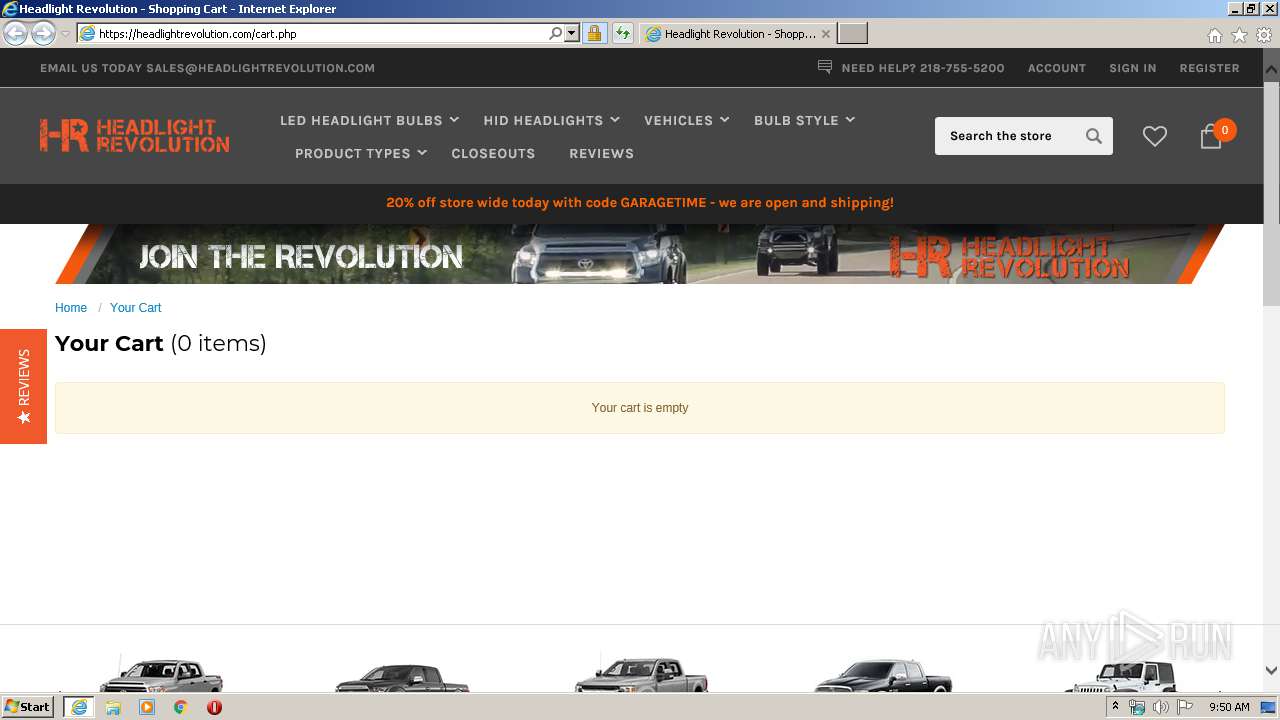
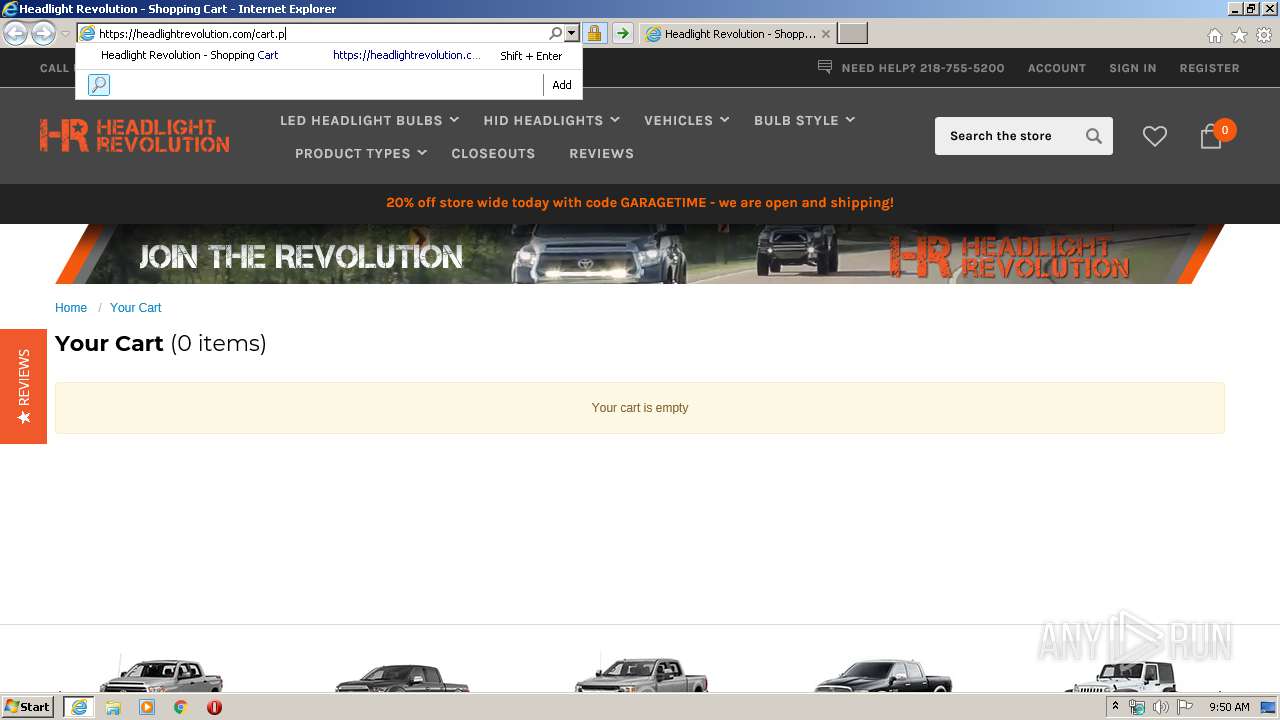
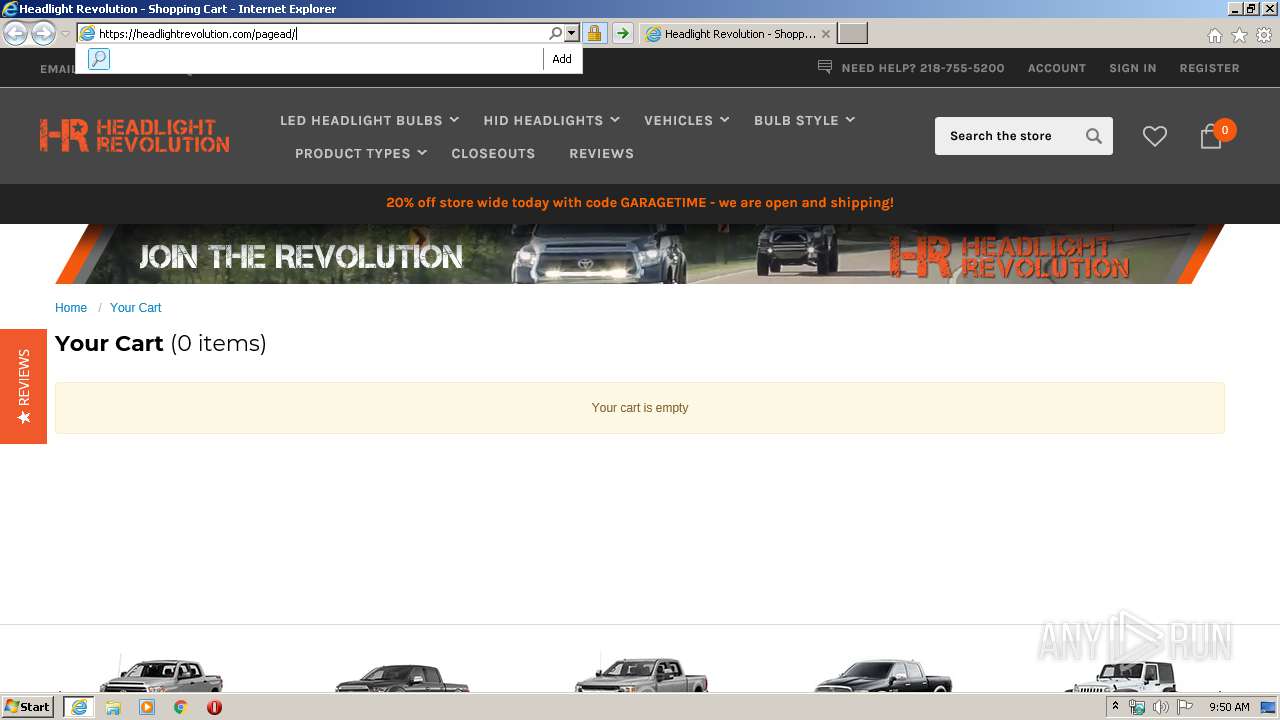
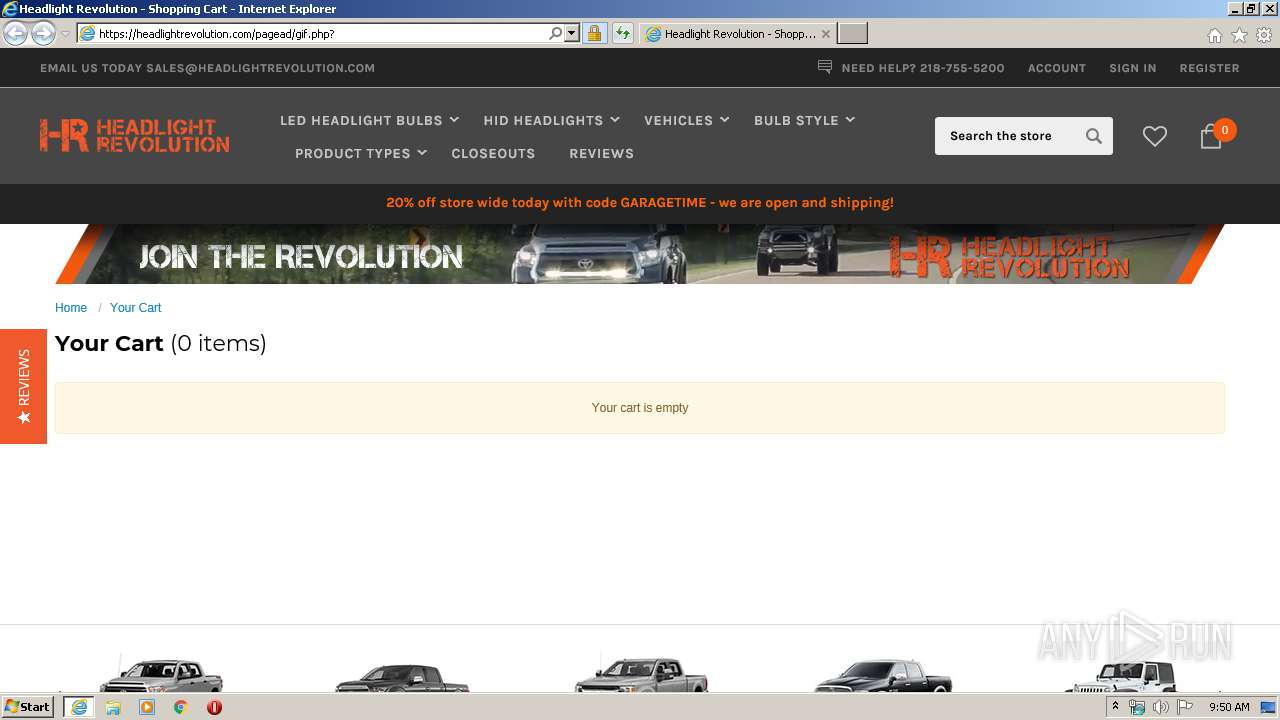
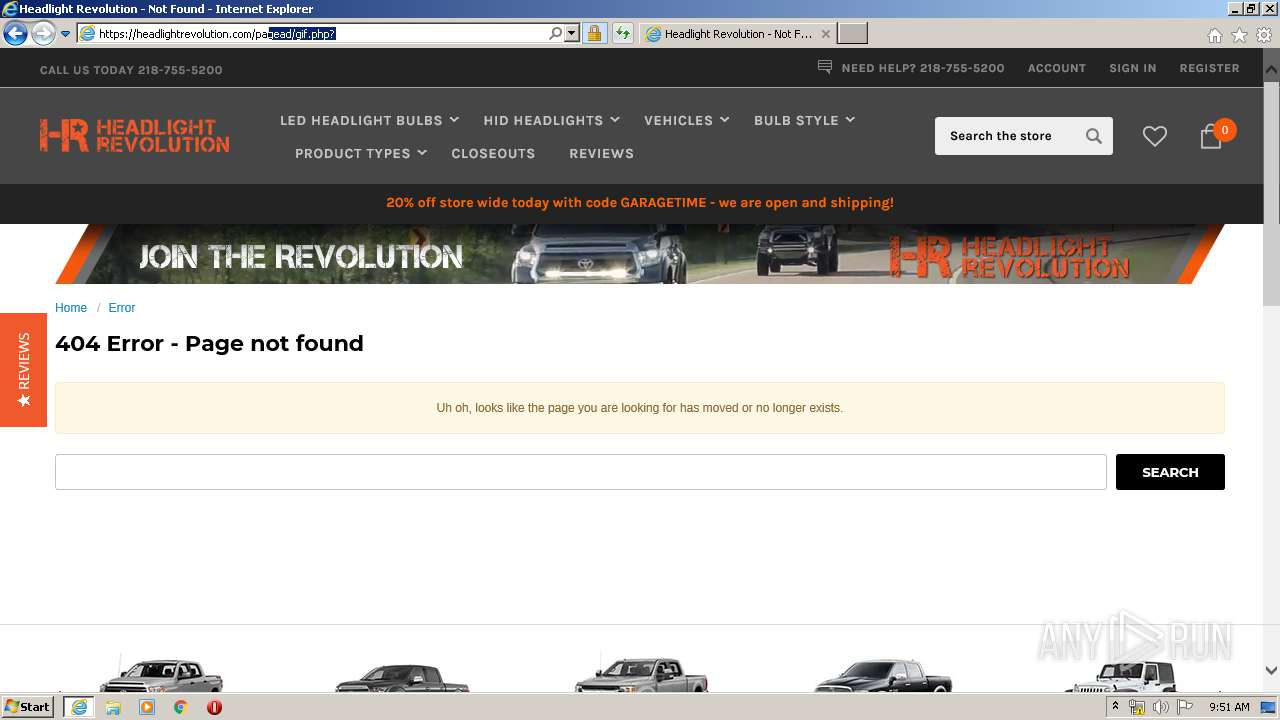
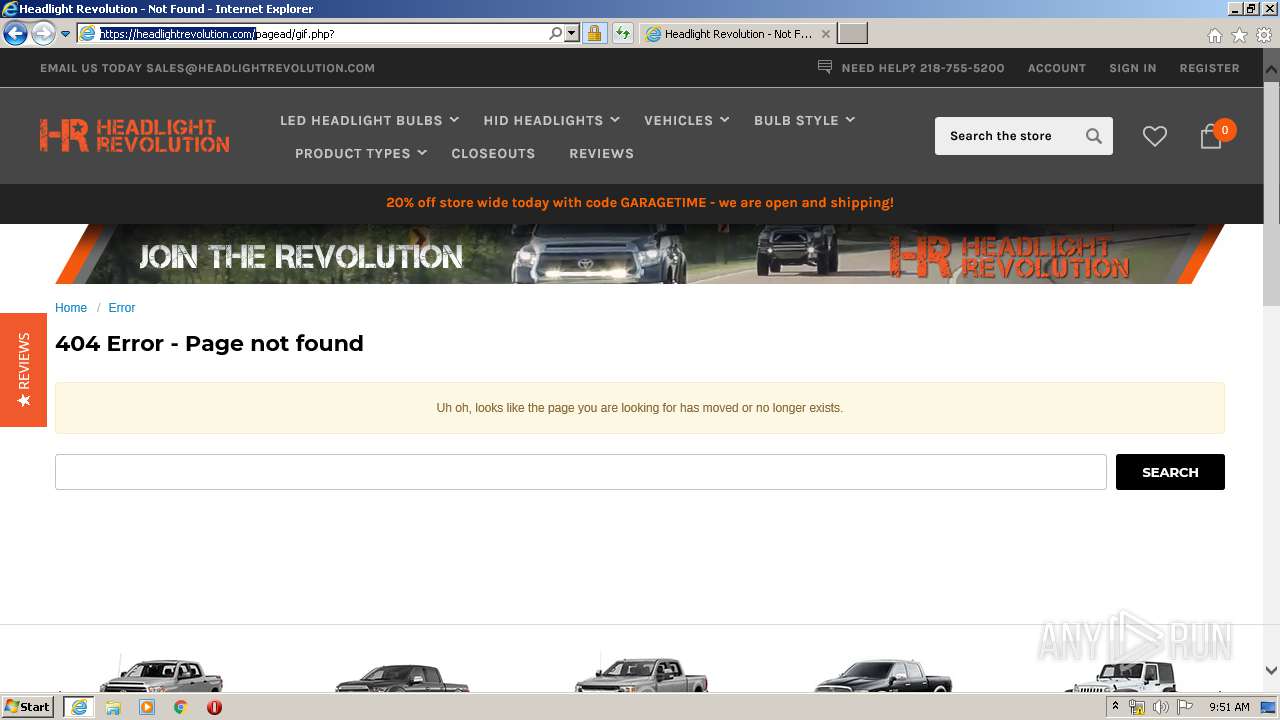
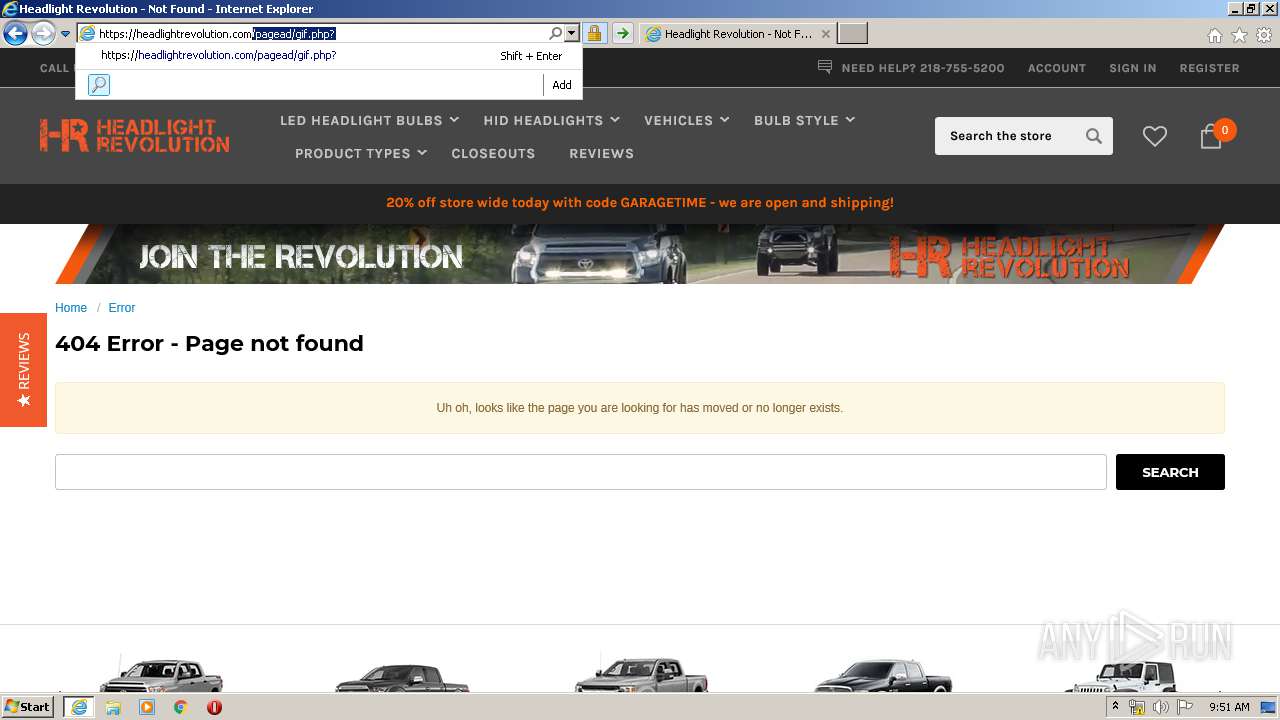
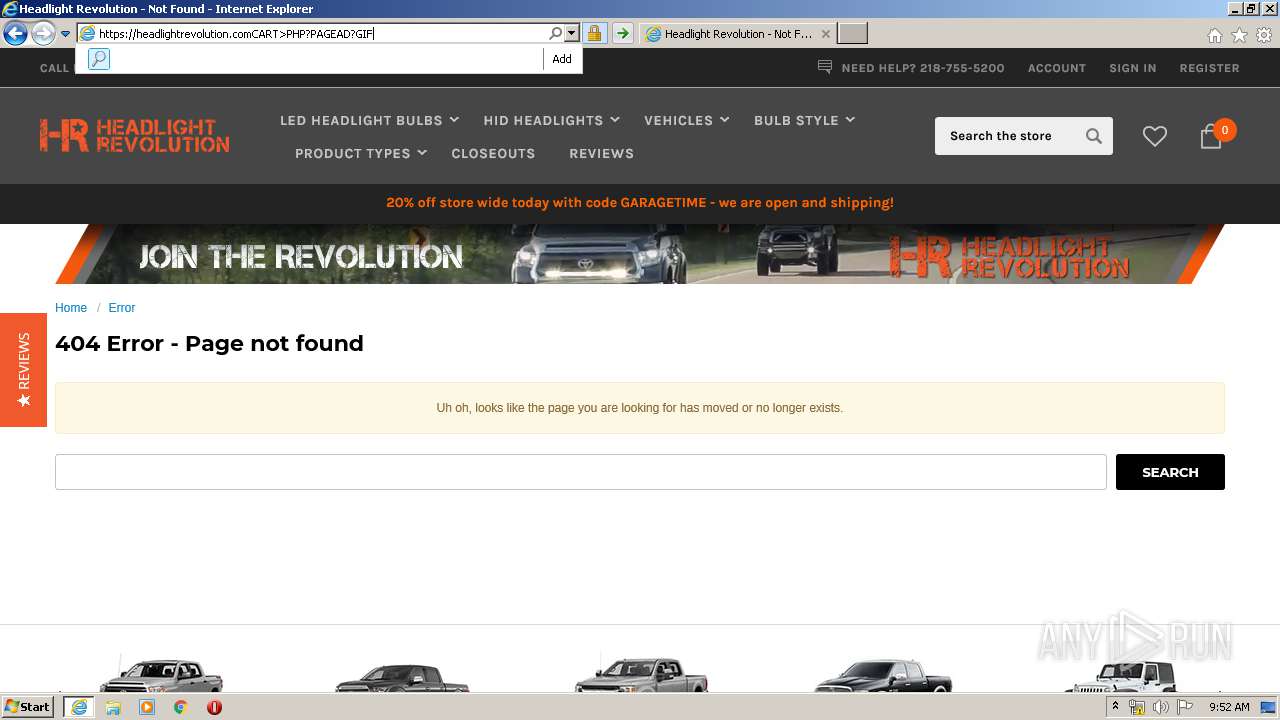
| URL: | https://headlightrevolution.com/cart.php |
| Full analysis: | https://app.any.run/tasks/97173ccc-a88f-47da-ab6a-a4469fa72d33 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 08:49:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 23742ABE1F494CBB87753735E6EFDAF7 |
| SHA1: | 71B32B9D08188CC7CEF40EC3DE9600FAEFC501A3 |
| SHA256: | 170A32A95D15BB2B2ABDD64758D25A06D45DBE417F23ACE047DCFDF070534082 |
| SSDEEP: | 3:N88VRSUdIdEBhNV:28nId8NV |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
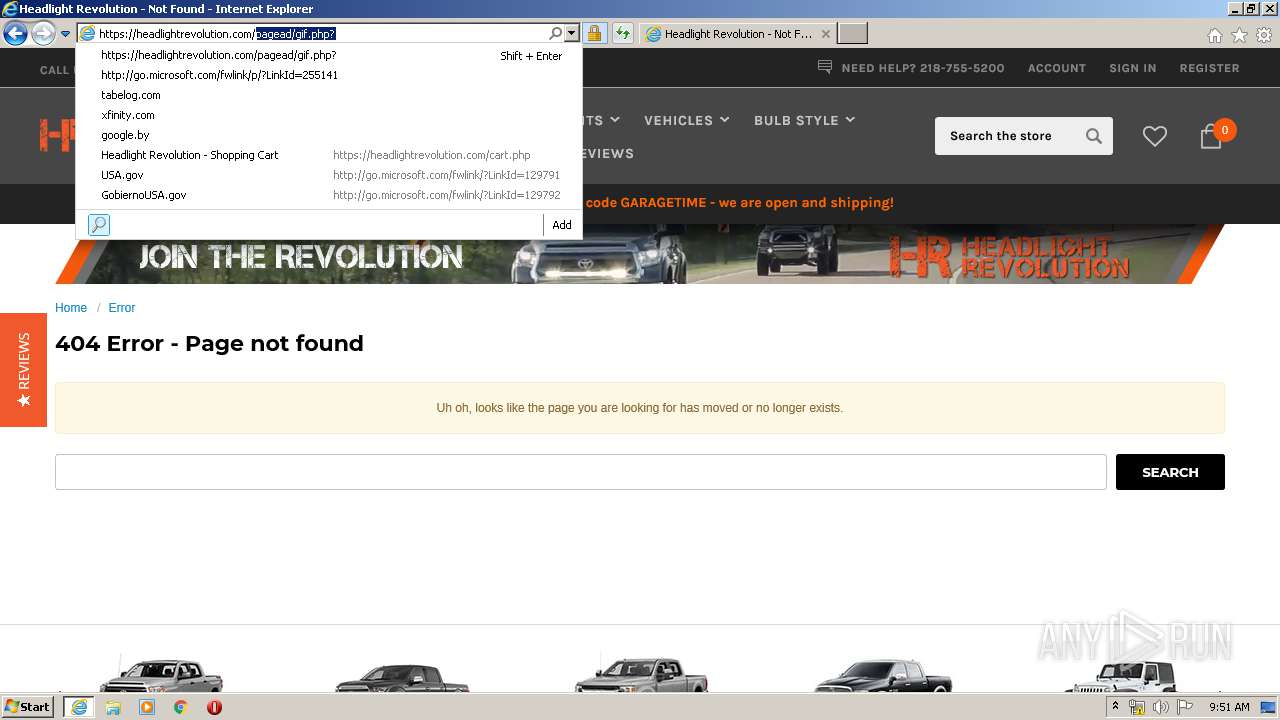
Reads Internet Cache Settings
- iexplore.exe (PID: 3144)
- iexplore.exe (PID: 3436)
Changes internet zones settings
- iexplore.exe (PID: 3144)
Creates files in the user directory
- iexplore.exe (PID: 3144)
- iexplore.exe (PID: 3436)
Reads internet explorer settings
- iexplore.exe (PID: 3436)
Reads settings of System Certificates
- iexplore.exe (PID: 3436)
- iexplore.exe (PID: 3144)
Changes settings of System certificates
- iexplore.exe (PID: 3144)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3144)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3144 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://headlightrevolution.com/cart.php" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3436 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3144 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
6 344
Read events
822
Write events
3 804
Delete events
1 718
Modification events
| (PID) Process: | (3144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1961617626 | |||
| (PID) Process: | (3144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30803769 | |||
| (PID) Process: | (3144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3144) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
112
Text files
175
Unknown types
71
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab7085.tmp | — | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar7086.tmp | — | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\WQ37RWQU.txt | — | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\4344B8AF97AF3A423D9EE52899963CDE_78849AF2BCA6F2FB97DE2940460ADC6A | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | der | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | binary | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EDC238BFF48A31D55A97E1E93892934B_C20E0DA2D0F89FE526E1490F4A2EE5AB | der | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\contivio-chat[1].js | text | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\cart[1].htm | html | |
MD5:— | SHA256:— | |||
| 3436 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4344B8AF97AF3A423D9EE52899963CDE_78849AF2BCA6F2FB97DE2940460ADC6A | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
109
DNS requests
45
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAez3RP7hyTB6WlLwXG2xOk%3D | US | der | 471 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://status.geotrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR3enuod9bxDxzpICGW%2B2sabjf17QQUkFj%2FsJx1qFFUd7Ht8qNDFjiebMUCEAez3RP7hyTB6WlLwXG2xOk%3D | US | der | 471 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
3436 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 1.47 Kb | whitelisted |
3436 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
3436 | iexplore.exe | GET | 200 | 172.217.21.227:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3436 | iexplore.exe | 204.79.197.200:443 | bat.bing.com | Microsoft Corporation | US | whitelisted |
3436 | iexplore.exe | 35.186.228.254:443 | headlightrevolution.com | Google Inc. | US | unknown |
3436 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3436 | iexplore.exe | 23.210.248.160:443 | cdn11.bigcommerce.com | Akamai International B.V. | NL | whitelisted |
3436 | iexplore.exe | 104.22.51.245:443 | www.powr.io | Cloudflare Inc | US | suspicious |
3436 | iexplore.exe | 216.58.206.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3436 | iexplore.exe | 54.241.86.195:443 | uschat3.contivio.com | Amazon.com, Inc. | US | unknown |
3436 | iexplore.exe | 172.217.22.52:443 | acp-magento.appspot.com | Google Inc. | US | whitelisted |
3436 | iexplore.exe | 143.204.94.29:443 | js.adsrvr.org | — | US | suspicious |
— | — | 13.225.87.20:443 | d3ryumxhbd2uw7.cloudfront.net | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
headlightrevolution.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
status.geotrust.com |
| whitelisted |
cdn11.bigcommerce.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.powr.io |
| shared |
uschat3.contivio.com |
| unknown |
acp-magento.appspot.com |
| whitelisted |
js.adsrvr.org |
| whitelisted |
chimpstatic.com |
| whitelisted |